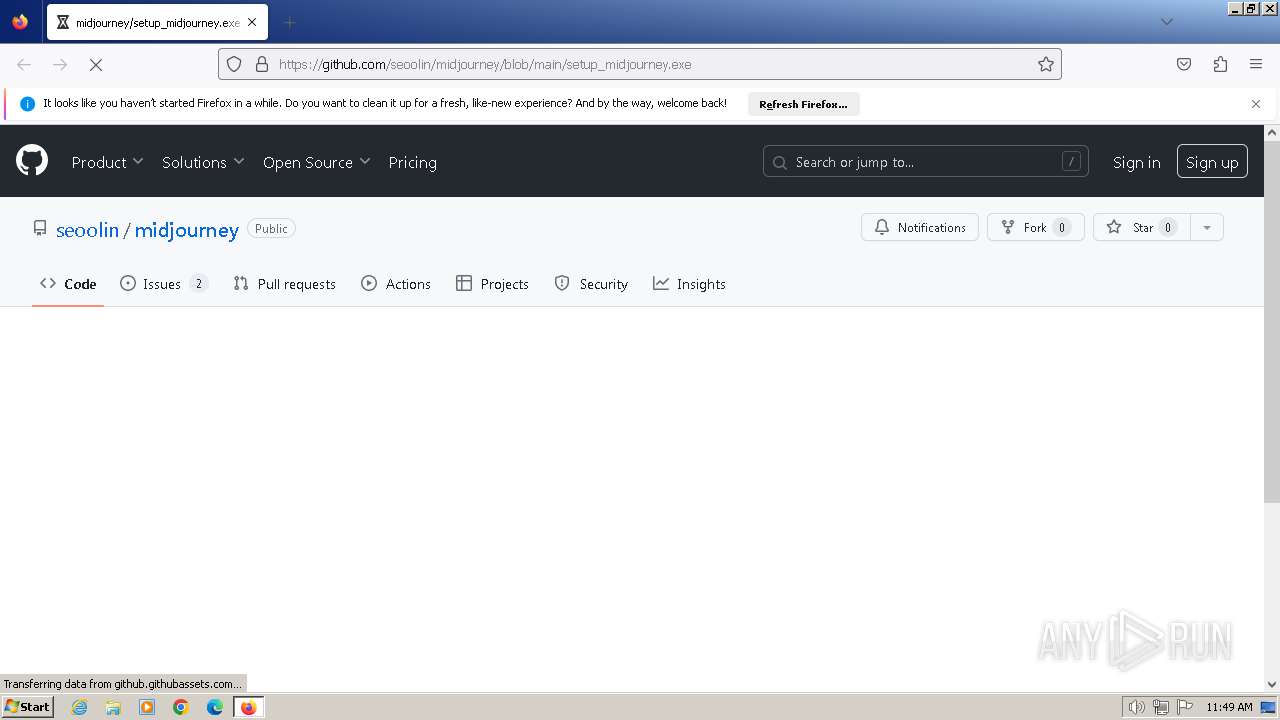
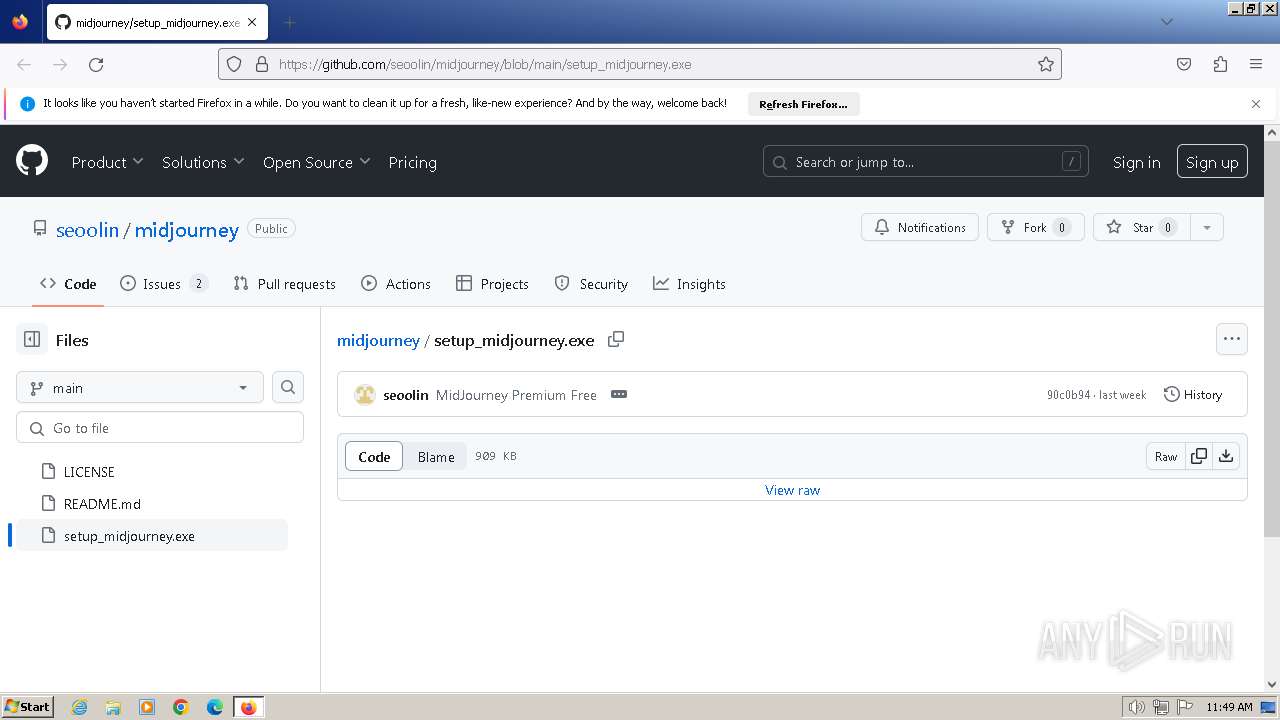
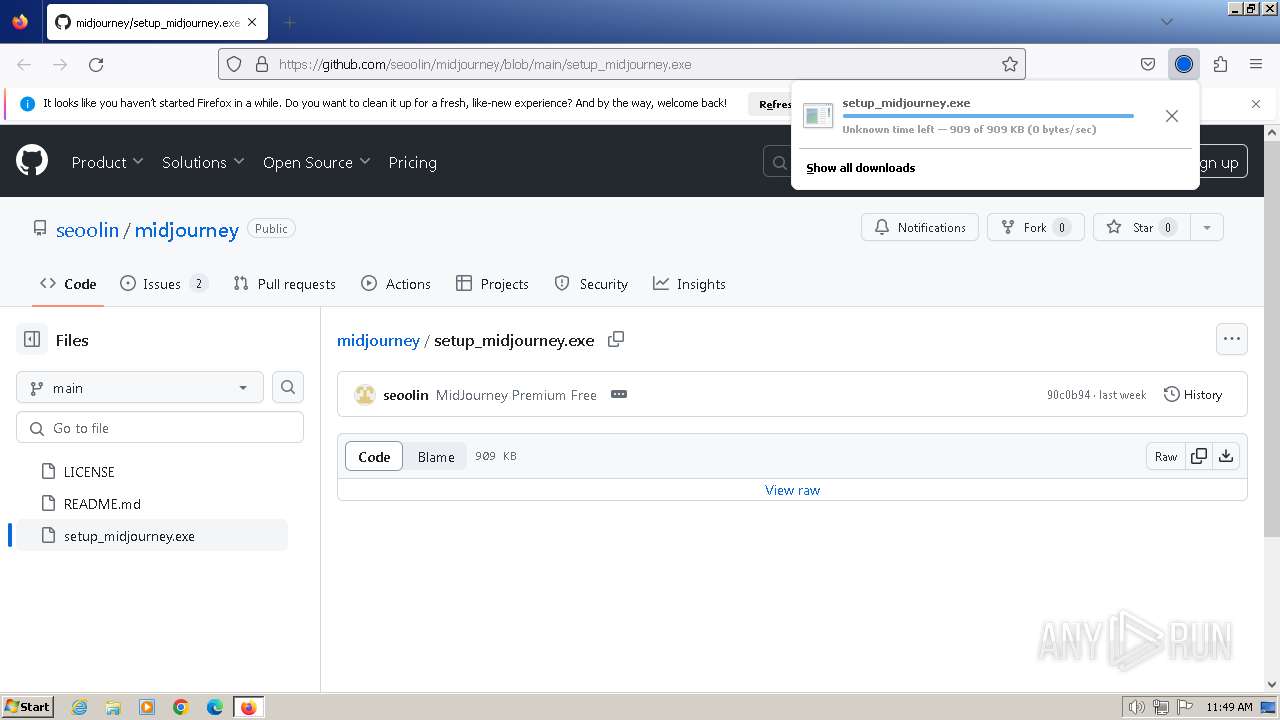
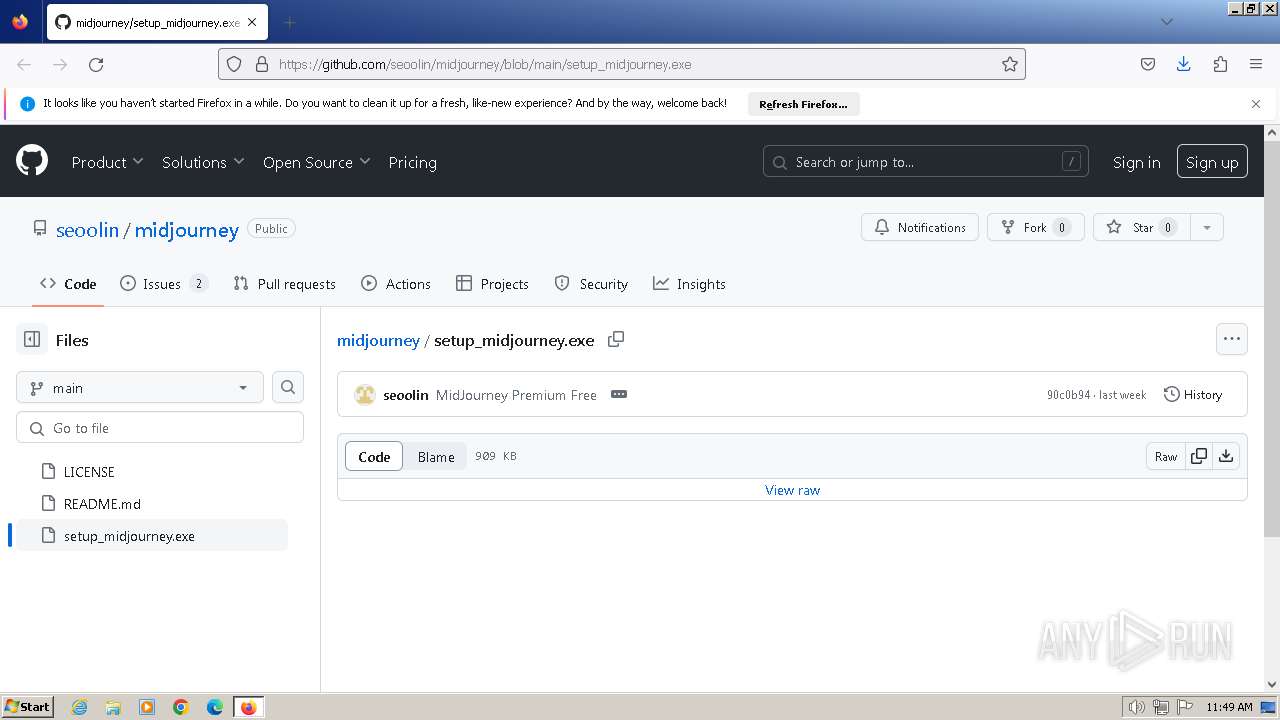
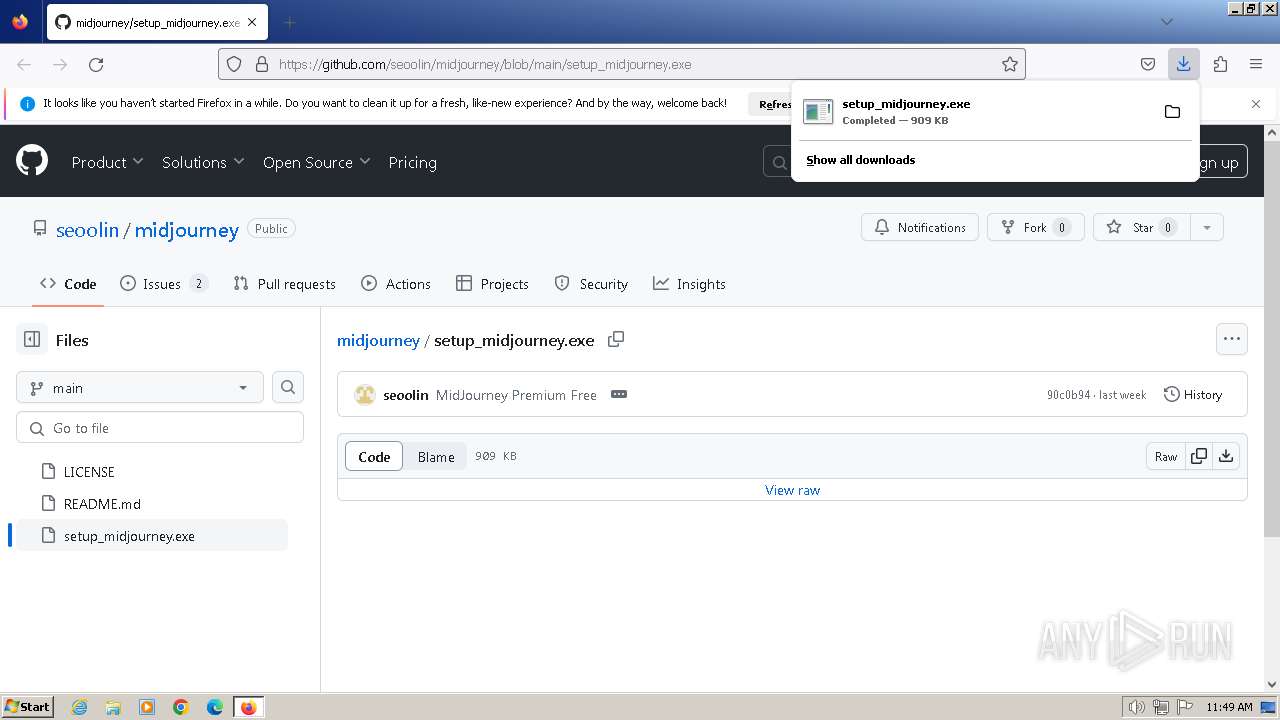
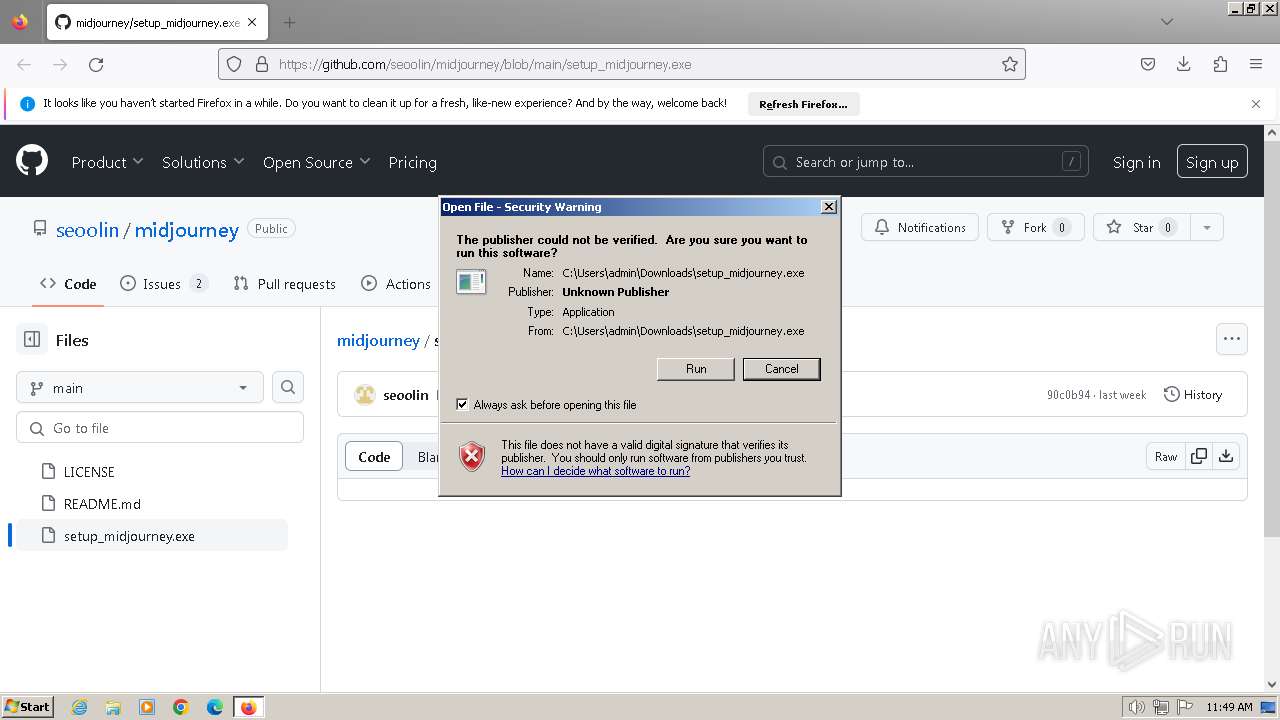
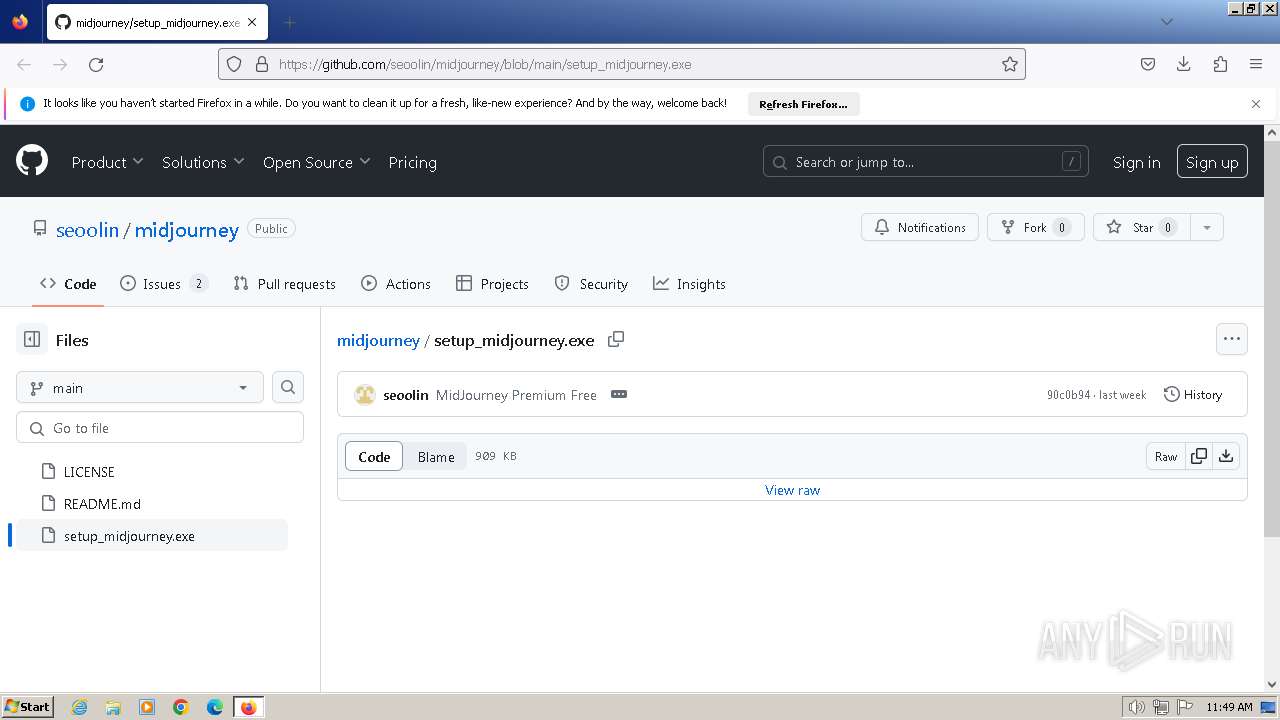
| URL: | https://github.com/seoolin/midjourney/blob/main/setup_midjourney.exe |
| Full analysis: | https://app.any.run/tasks/a2752890-0096-418b-bca7-a2a2e9962ffb |
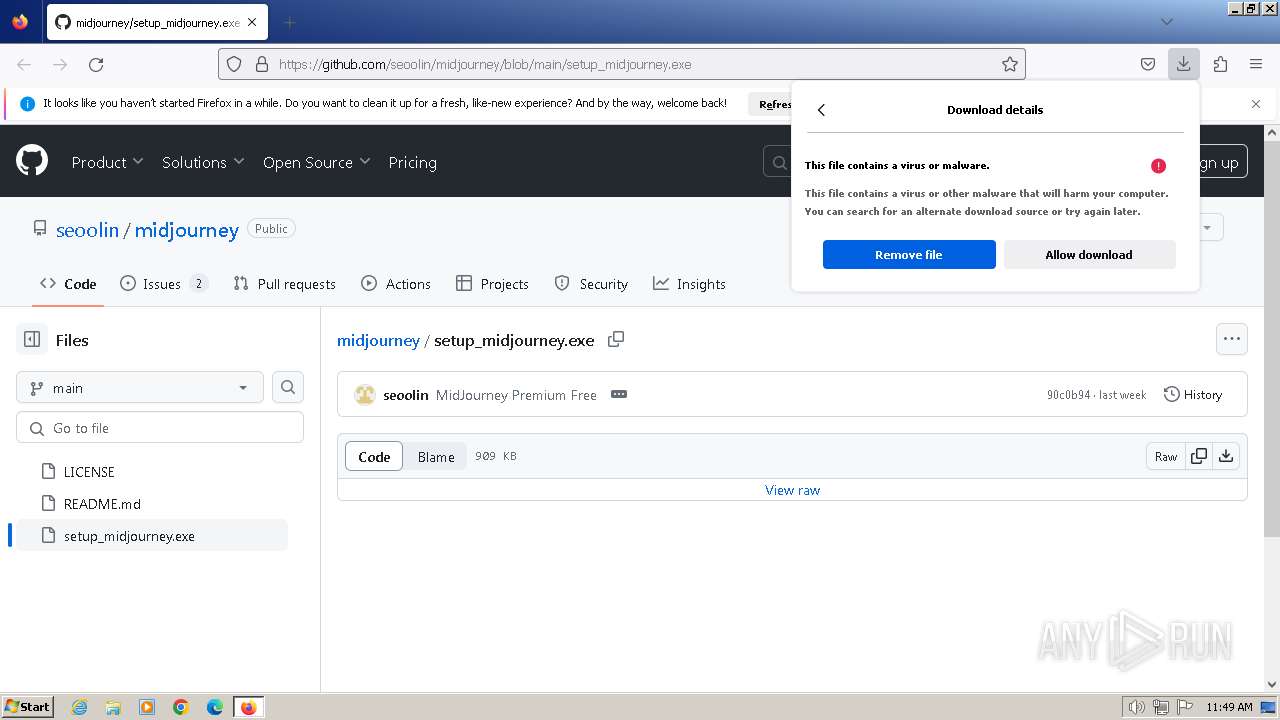
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | March 11, 2024, 11:49:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1B38A0BD84939FE84FA3DEE8316745AF |
| SHA1: | 511894D3435D00B41D9EBAF477D6492337630CB4 |
| SHA256: | C39CB3307F601995877A18F18406846682BC984A5481FBC345C24422BF5B98CB |
| SSDEEP: | 3:N8tEdmAKSMaK+4KHKIERWV6HhJ:2uw6MaK+4KzsS0hJ |
MALICIOUS
Drops the executable file immediately after the start
- setup_midjourney.exe (PID: 1172)
- cmd.exe (PID: 3372)
- setup_midjourney.exe (PID: 2940)
- cmd.exe (PID: 3088)
Antivirus name has been found in the command line (generic signature)
- findstr.exe (PID: 3108)
- findstr.exe (PID: 2764)
- findstr.exe (PID: 3960)
- findstr.exe (PID: 3164)
RHADAMANTHYS has been detected (SURICATA)
- dialer.exe (PID: 3376)
Actions looks like stealing of personal data
- dialer.exe (PID: 3376)
SUSPICIOUS
Executable content was dropped or overwritten
- setup_midjourney.exe (PID: 1172)
- cmd.exe (PID: 3372)
- setup_midjourney.exe (PID: 2940)
- cmd.exe (PID: 3088)
Malware-specific behavior (creating "System.dll" in Temp)
- setup_midjourney.exe (PID: 1172)
- setup_midjourney.exe (PID: 2940)
The process creates files with name similar to system file names
- setup_midjourney.exe (PID: 1172)
- setup_midjourney.exe (PID: 2940)
Reads the Internet Settings
- setup_midjourney.exe (PID: 1172)
- Also.pif (PID: 292)
- setup_midjourney.exe (PID: 2940)
Reads security settings of Internet Explorer
- setup_midjourney.exe (PID: 1172)
- Also.pif (PID: 292)
- setup_midjourney.exe (PID: 2940)
Starts CMD.EXE for commands execution
- setup_midjourney.exe (PID: 1172)
- cmd.exe (PID: 1604)
- Also.pif (PID: 292)
- setup_midjourney.exe (PID: 2940)
- cmd.exe (PID: 1432)
Executing commands from a ".bat" file
- setup_midjourney.exe (PID: 1172)
- setup_midjourney.exe (PID: 2940)
Get information on the list of running processes
- cmd.exe (PID: 1604)
- cmd.exe (PID: 1432)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1604)
- cmd.exe (PID: 1432)
Application launched itself
- cmd.exe (PID: 1604)
- cmd.exe (PID: 1432)
Suspicious file concatenation
- cmd.exe (PID: 3372)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 3088)
- cmd.exe (PID: 1624)
Drops a file with a rarely used extension (PIF)
- cmd.exe (PID: 3372)
- cmd.exe (PID: 3088)
Starts application with an unusual extension
- cmd.exe (PID: 1604)
- cmd.exe (PID: 1432)
The executable file from the user directory is run by the CMD process
- Also.pif (PID: 292)
- setup_midjourney.exe (PID: 2940)
- Also.pif (PID: 1936)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 1604)
- cmd.exe (PID: 1432)
Connects to unusual port
- dialer.exe (PID: 3376)
The process checks if it is being run in the virtual environment
- dialer.exe (PID: 3376)
Loads DLL from Mozilla Firefox
- dialer.exe (PID: 3376)
Searches for installed software
- dialer.exe (PID: 3376)
Accesses Microsoft Outlook profiles
- dialer.exe (PID: 3376)
INFO
The process uses the downloaded file
- firefox.exe (PID: 3536)
Application launched itself
- firefox.exe (PID: 3536)
- firefox.exe (PID: 3652)
Executable content was dropped or overwritten
- firefox.exe (PID: 3536)
Checks supported languages
- setup_midjourney.exe (PID: 1172)
- Also.pif (PID: 292)
- setup_midjourney.exe (PID: 2940)
- Also.pif (PID: 1936)
Drops the executable file immediately after the start
- firefox.exe (PID: 3536)
Reads the computer name
- setup_midjourney.exe (PID: 1172)
- Also.pif (PID: 292)
- setup_midjourney.exe (PID: 2940)
- Also.pif (PID: 1936)
Create files in a temporary directory
- setup_midjourney.exe (PID: 1172)
- setup_midjourney.exe (PID: 2940)
Reads mouse settings
- Also.pif (PID: 292)
- Also.pif (PID: 1936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
77
Monitored processes
34
Malicious processes
9
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | 5494\Also.pif 5494\p | C:\Users\admin\AppData\Local\Temp\5494\Also.pif | — | cmd.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 4 Modules
| |||||||||||||||
| 1172 | "C:\Users\admin\Downloads\setup_midjourney.exe" | C:\Users\admin\Downloads\setup_midjourney.exe | firefox.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1388 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\Downloads\setup_midjourney.exe | C:\Windows\System32\cmd.exe | Also.pif | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1432 | "C:\Windows\System32\cmd.exe" /k move Practical Practical.bat & Practical.bat & exit | C:\Windows\System32\cmd.exe | — | setup_midjourney.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3536.6.1396918717\789122315" -childID 5 -isForBrowser -prefsHandle 3784 -prefMapHandle 3780 -prefsLen 29209 -prefMapSize 244195 -jsInitHandle 940 -jsInitLen 240908 -parentBuildID 20230710165010 -appDir "C:\Program Files\Mozilla Firefox\browser" - {eba08e5f-4233-4168-bddb-5ff10e5bb5fc} 3536 "\\.\pipe\gecko-crash-server-pipe.3536" 3892 21f7b840 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1604 | "C:\Windows\System32\cmd.exe" /k move Practical Practical.bat & Practical.bat & exit | C:\Windows\System32\cmd.exe | — | setup_midjourney.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1624 | cmd /c copy /b Points + Sandwich + Mongolia + Fairly + Hotels 5504\p | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3536.4.1589902522\1386418126" -childID 3 -isForBrowser -prefsHandle 3476 -prefMapHandle 3796 -prefsLen 29209 -prefMapSize 244195 -jsInitHandle 940 -jsInitLen 240908 -parentBuildID 20230710165010 -appDir "C:\Program Files\Mozilla Firefox\browser" - {b99eb3e1-47e9-417c-96f2-66bc521f028b} 3536 "\\.\pipe\gecko-crash-server-pipe.3536" 3492 21f7b3f0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3536.0.1704017318\622146418" -parentBuildID 20230710165010 -prefsHandle 1116 -prefMapHandle 1108 -prefsLen 28523 -prefMapSize 244195 -appDir "C:\Program Files\Mozilla Firefox\browser" - {0b437a46-0aae-4770-9f37-268211702b89} 3536 "\\.\pipe\gecko-crash-server-pipe.3536" 1204 caab6b0 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1936 | 5504\Also.pif 5504\p | C:\Users\admin\AppData\Local\Temp\5504\Also.pif | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: HIGH Description: AutoIt v3 Script (Beta) Exit code: 3221225477 Version: 3, 3, 15, 4 Modules
| |||||||||||||||
Total events
24 227
Read events
24 140
Write events
82
Delete events
5
Modification events
| (PID) Process: | (3652) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: DC53C74F01000000 | |||
| (PID) Process: | (3536) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 97C2C84F01000000 | |||
| (PID) Process: | (3536) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Installer\308046B0AF4A39CB |
| Operation: | delete value | Name: | installer.taskbarpin.win10.enabled |
Value: | |||
| (PID) Process: | (3536) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (3536) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (3536) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Theme |
Value: 1 | |||
| (PID) Process: | (3536) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Enabled |
Value: 1 | |||
| (PID) Process: | (3536) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (3536) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (3536) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SetDefaultBrowserUserChoice |
Value: 1 | |||
Executable files
7
Suspicious files
45
Text files
40
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3536 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:B7A3C61D0C144CC5E166B1E769CA8F8C | SHA256:7FADCB77FFACA6B9E9F15C6F1CD3AAD4C20DCD90FA92429A627A3A7110CA2644 | |||
| 3536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:60E0DE9E05EC76C749D80F0D15A81B21 | SHA256:08252FA62CCCCD316474E20CC7317A6B5C932B2C972234318E8CCDA39EC2EF48 | |||
| 3536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 3536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:60E0DE9E05EC76C749D80F0D15A81B21 | SHA256:08252FA62CCCCD316474E20CC7317A6B5C932B2C972234318E8CCDA39EC2EF48 | |||
| 3536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 3536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
39
DNS requests
89
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3536 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | text | 90 b | unknown |
3536 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | text | 8 b | unknown |
3536 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | binary | 281 b | unknown |
3536 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | binary | 281 b | unknown |
3536 | firefox.exe | POST | 200 | 2.18.121.17:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
3536 | firefox.exe | POST | 200 | 2.18.121.17:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
3536 | firefox.exe | POST | 200 | 2.18.121.17:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
3536 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3 | unknown | binary | 471 b | unknown |
3536 | firefox.exe | POST | 200 | 2.18.121.17:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
3536 | firefox.exe | POST | 200 | 2.18.121.17:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
3536 | firefox.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
3536 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
3536 | firefox.exe | 34.117.237.239:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
3536 | firefox.exe | 34.117.188.166:443 | spocs.getpocket.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
3536 | firefox.exe | 104.18.38.233:80 | ocsp.sectigo.com | CLOUDFLARENET | — | shared |
3536 | firefox.exe | 2.18.121.17:80 | r3.o.lencr.org | AKAMAI-AS | FR | unknown |
3536 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| shared |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
ipv4only.arpa |
| whitelisted |
spocs.getpocket.com |
| shared |
ocsp.sectigo.com |
| whitelisted |
prod.ads.prod.webservices.mozgcp.net |
| unknown |
r3.o.lencr.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3376 | dialer.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
4 ETPRO signatures available at the full report