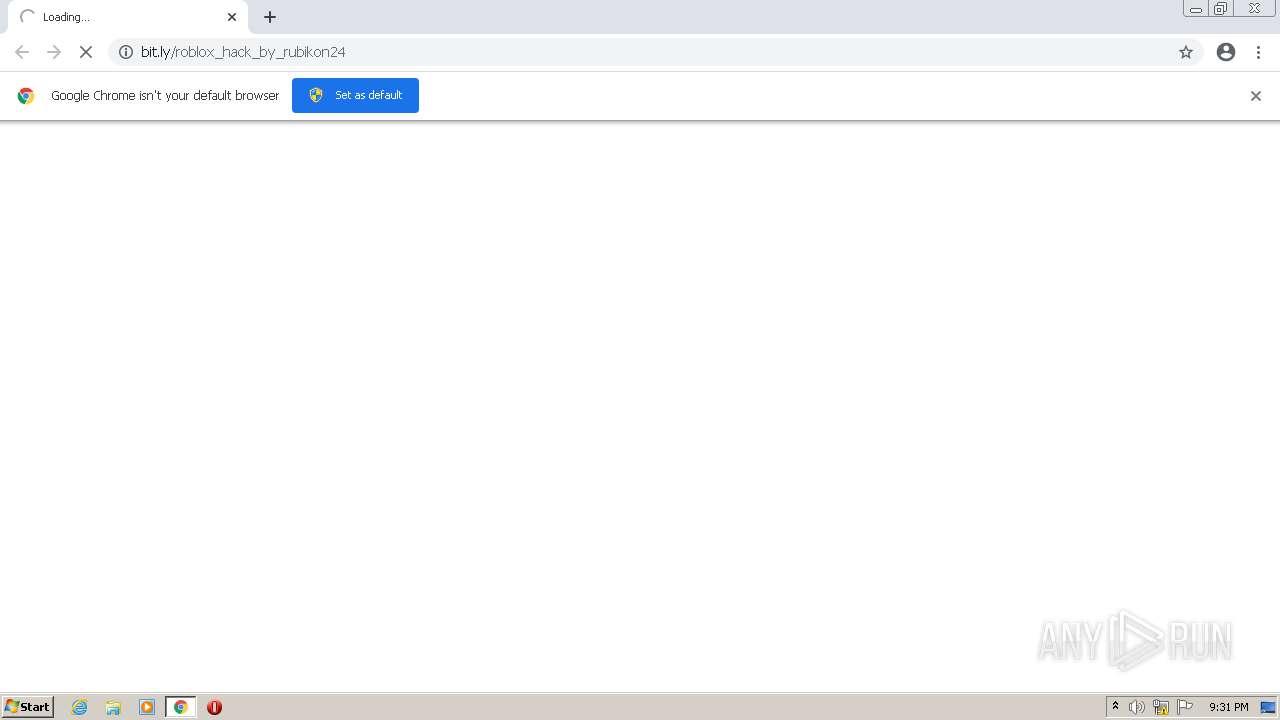
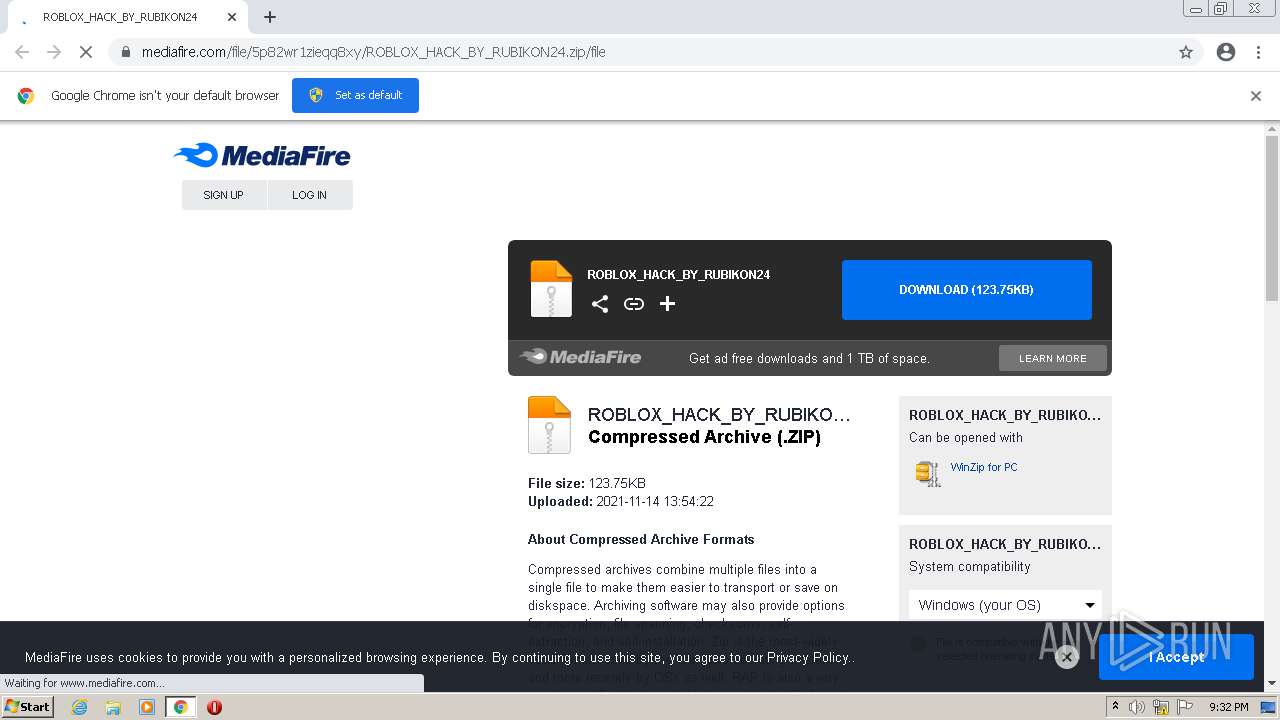
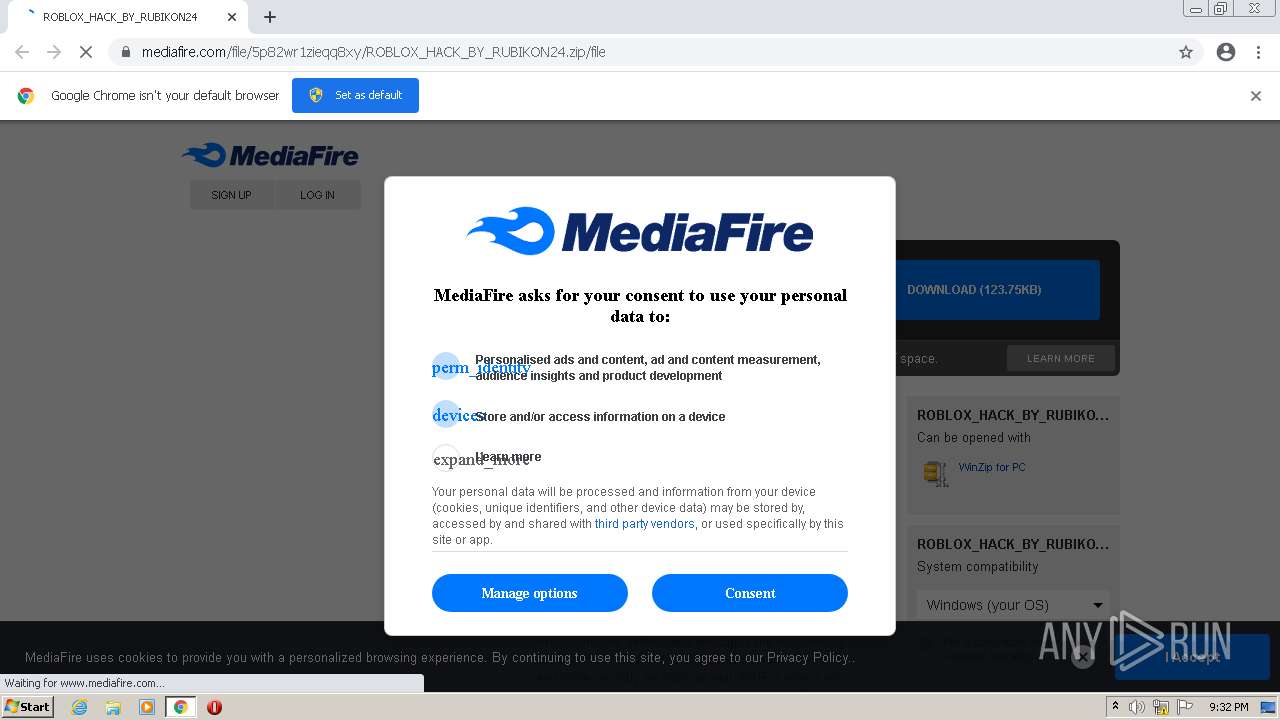
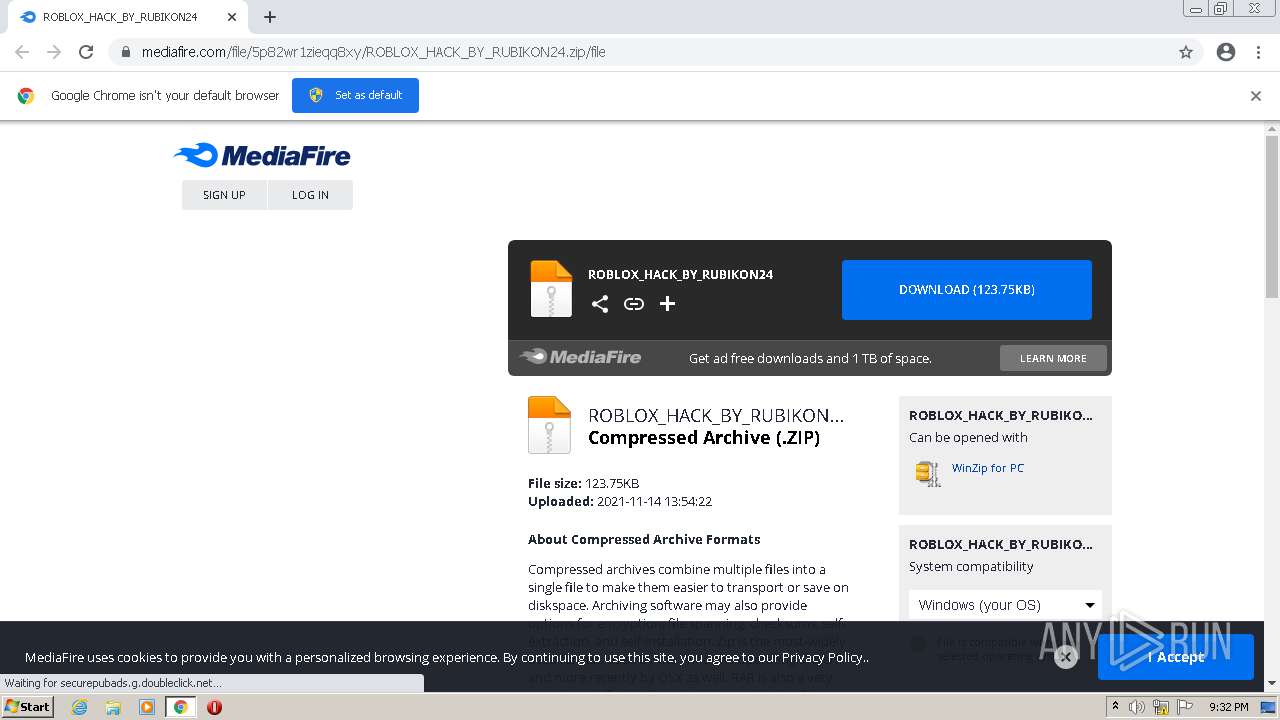
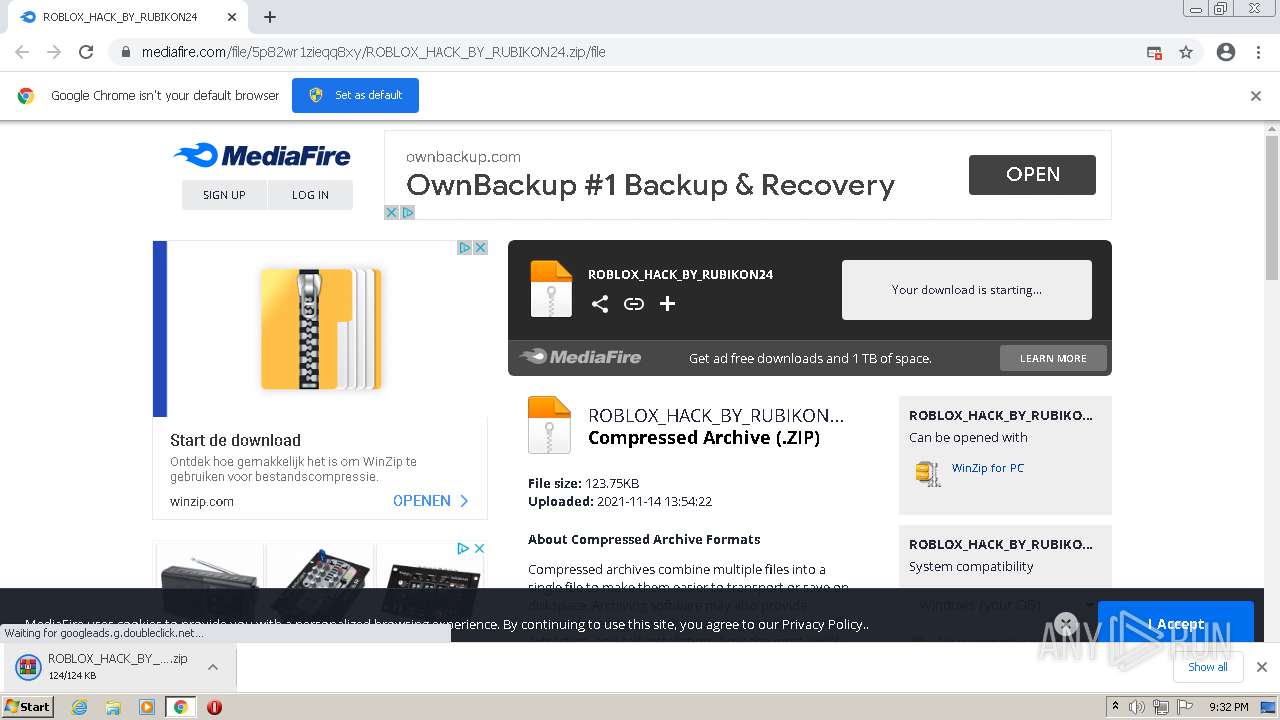
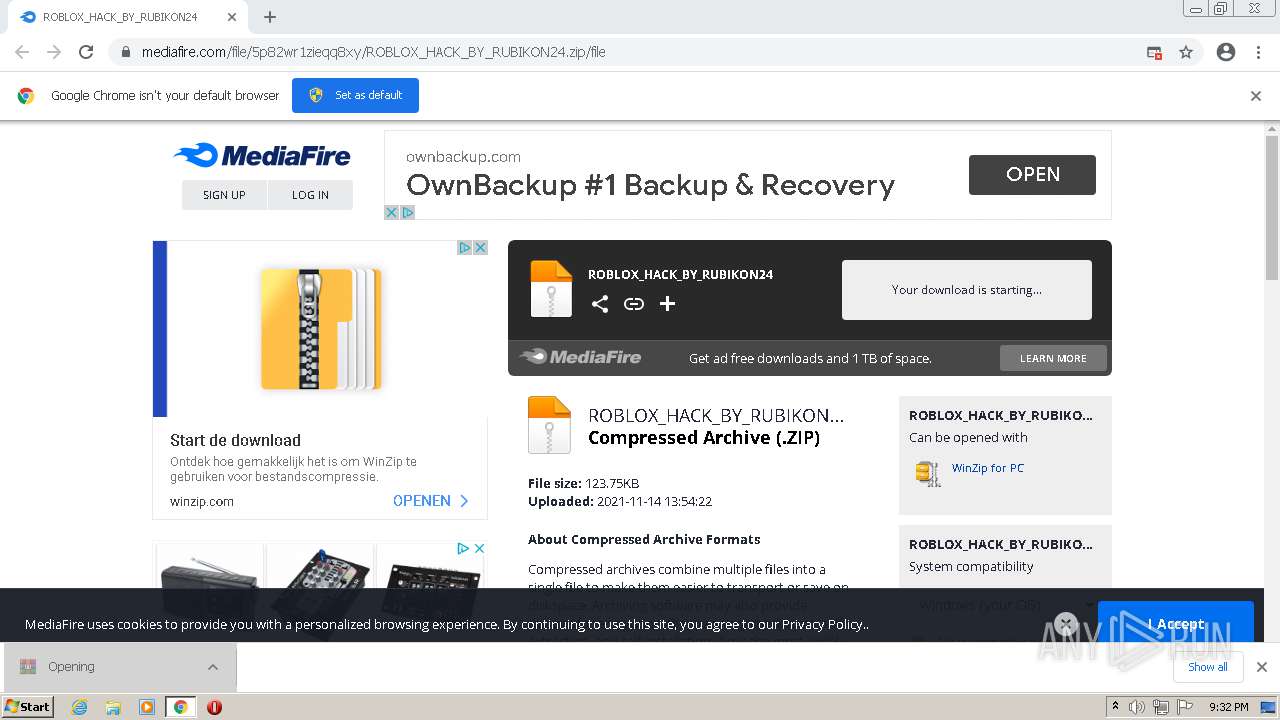
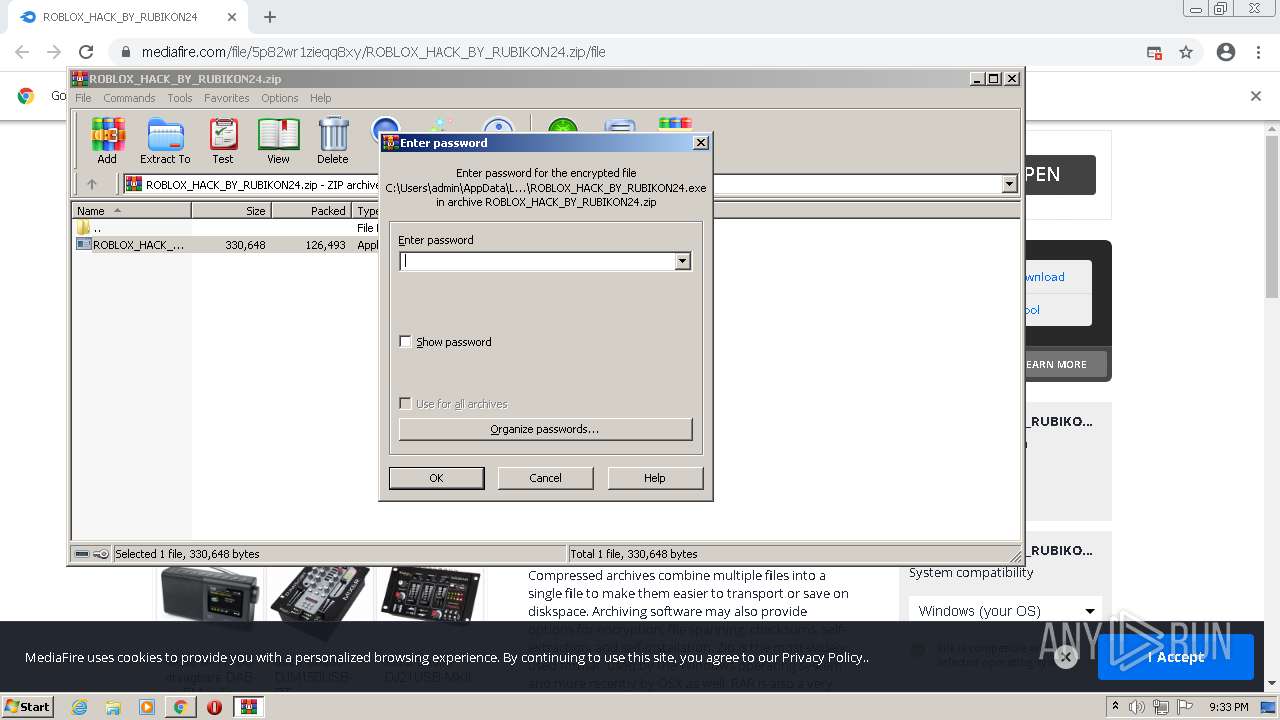
| URL: | https://bit.ly/roblox_hack_by_rubikon24 |
| Full analysis: | https://app.any.run/tasks/286ee547-0837-4583-afdd-4d9716c18886 |
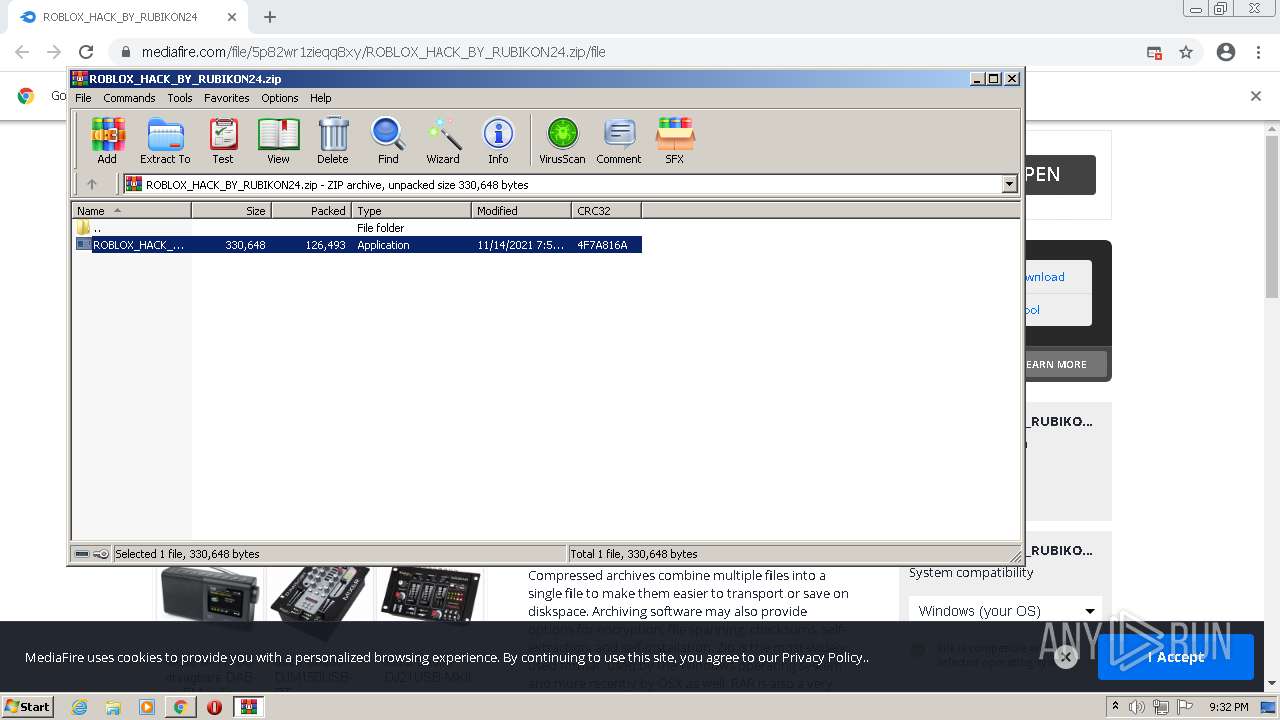
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | November 14, 2021, 21:31:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
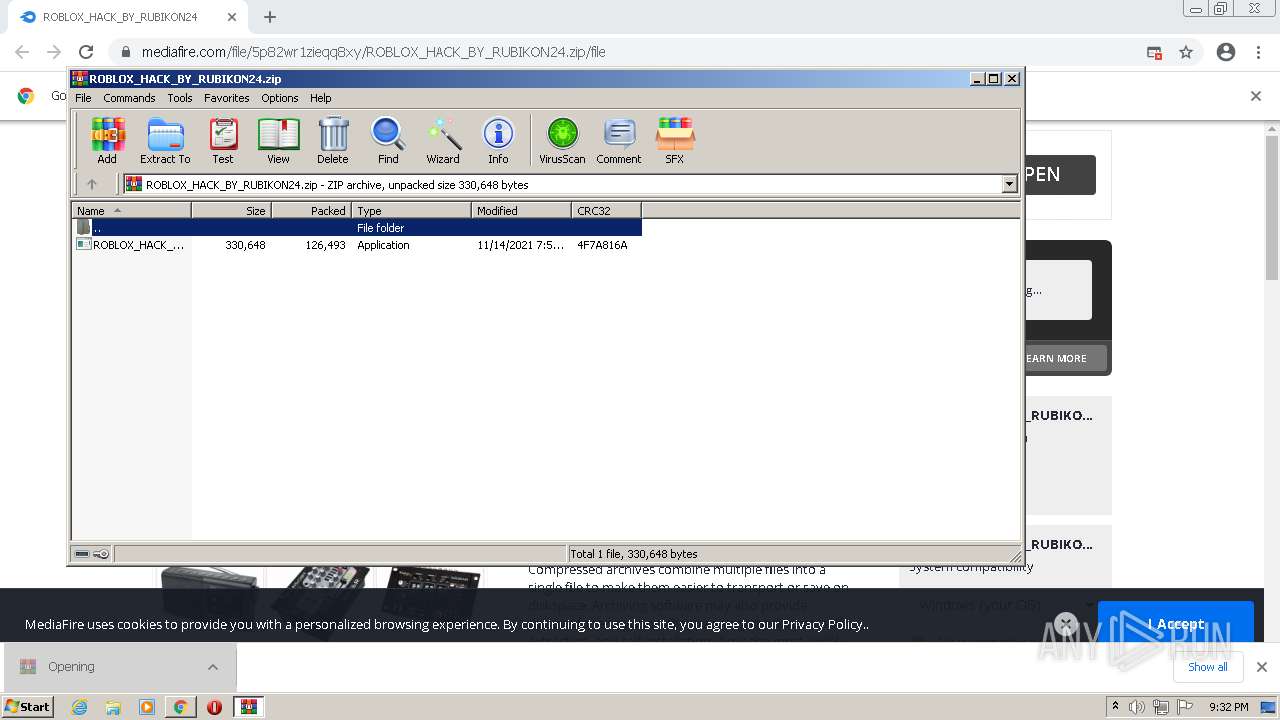
| MD5: | 6D06280B80EC380FE30B294A916ED6E1 |
| SHA1: | 1ABF1B9ACA2BAF007553B87A0BFA018C49EA4F09 |
| SHA256: | C398056F7181A4178636A98CFB3068689C3726309C0499331AD923A6ADF19D56 |
| SSDEEP: | 3:N8k7dmW9BHMOS:26dPBa |
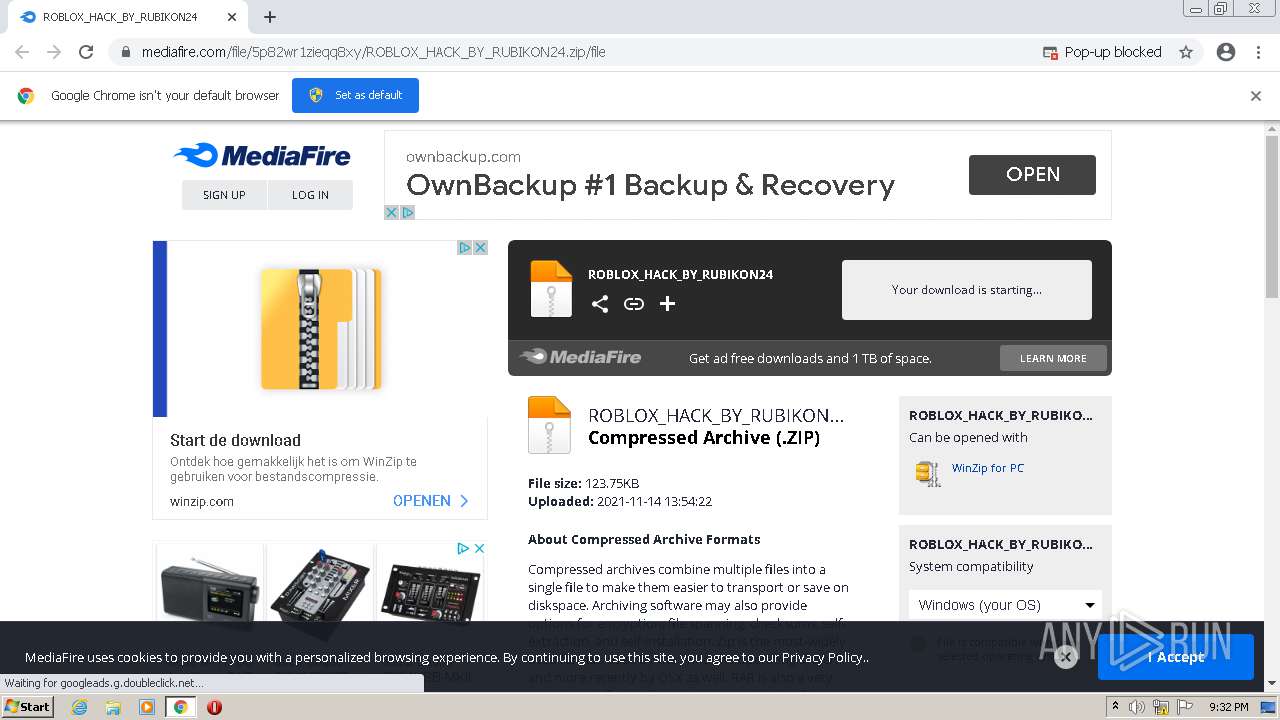
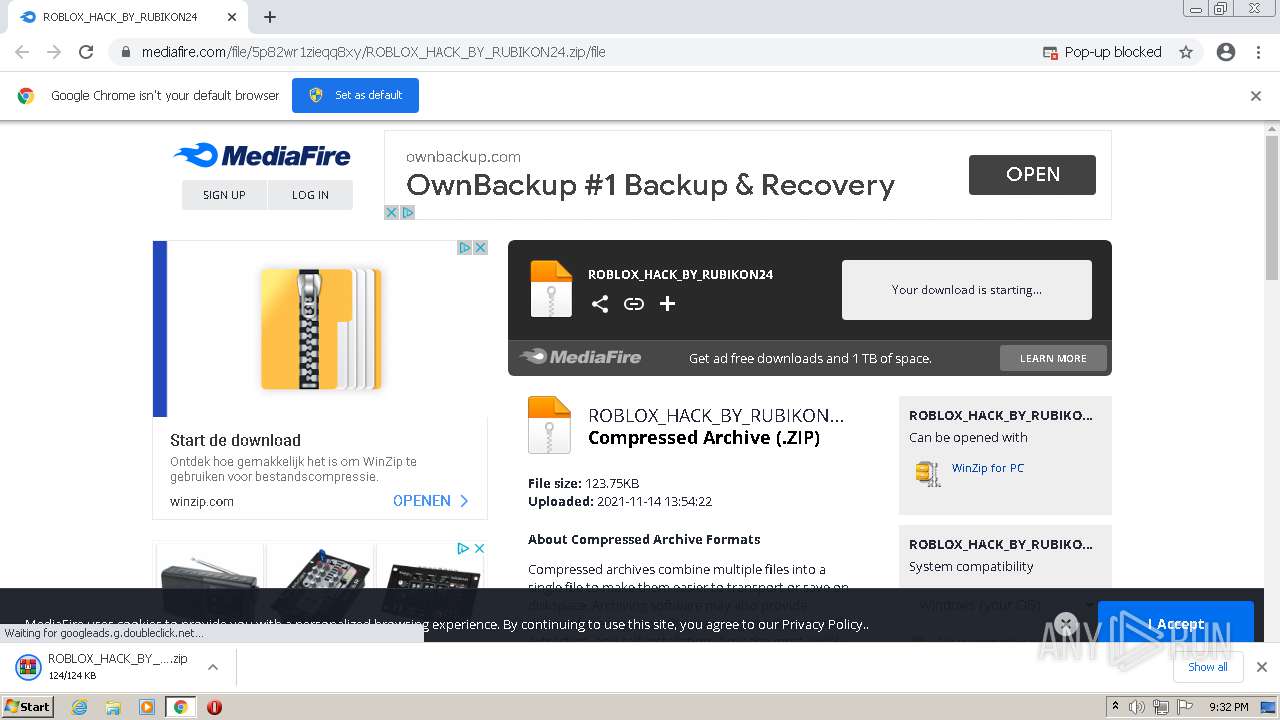
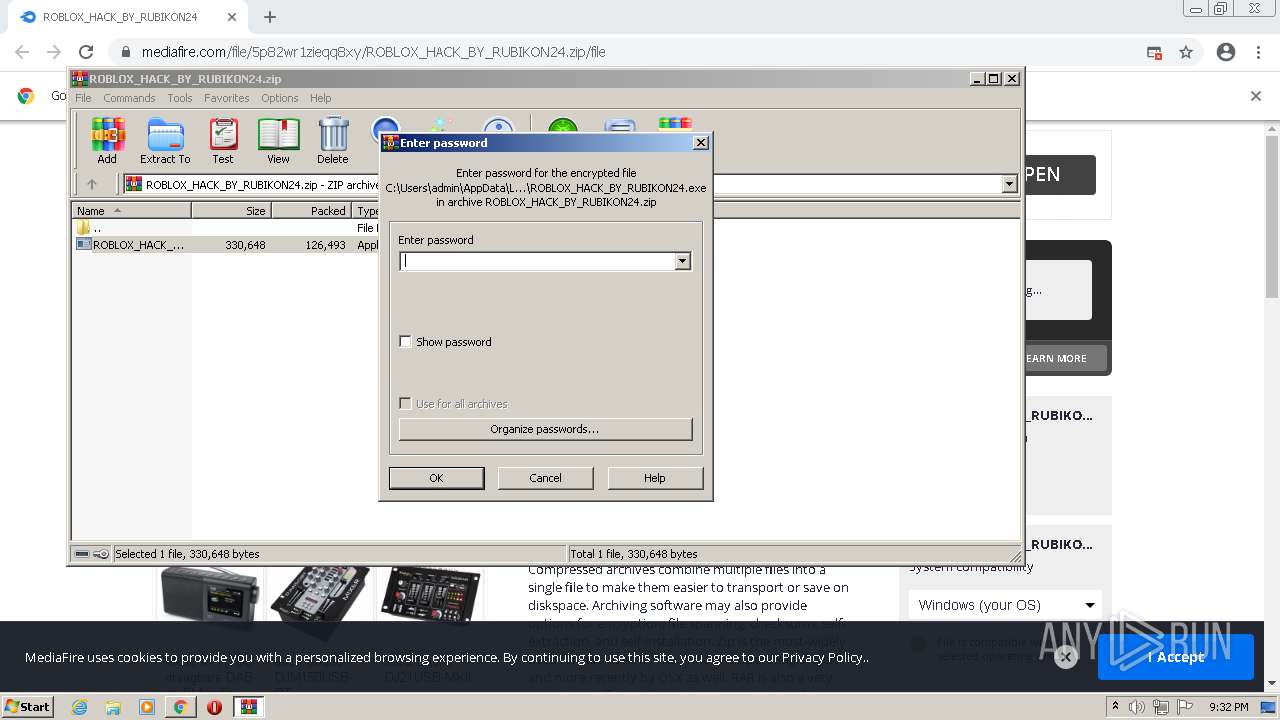
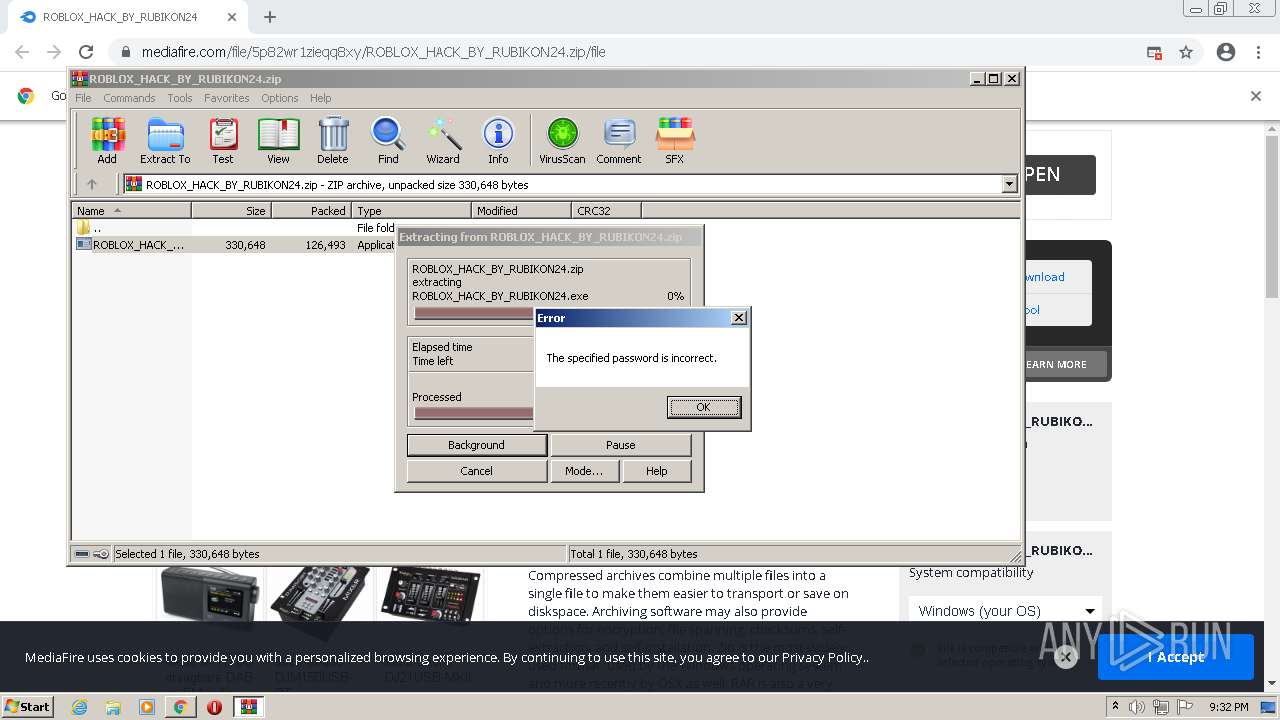
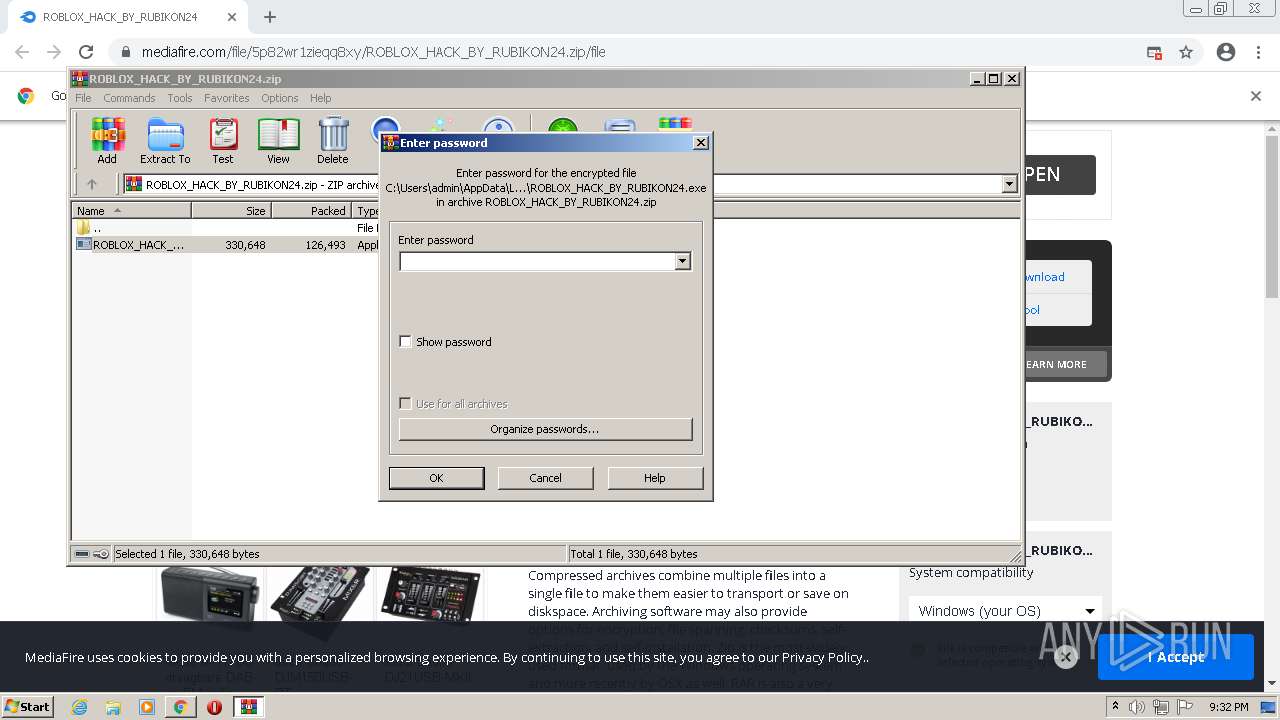
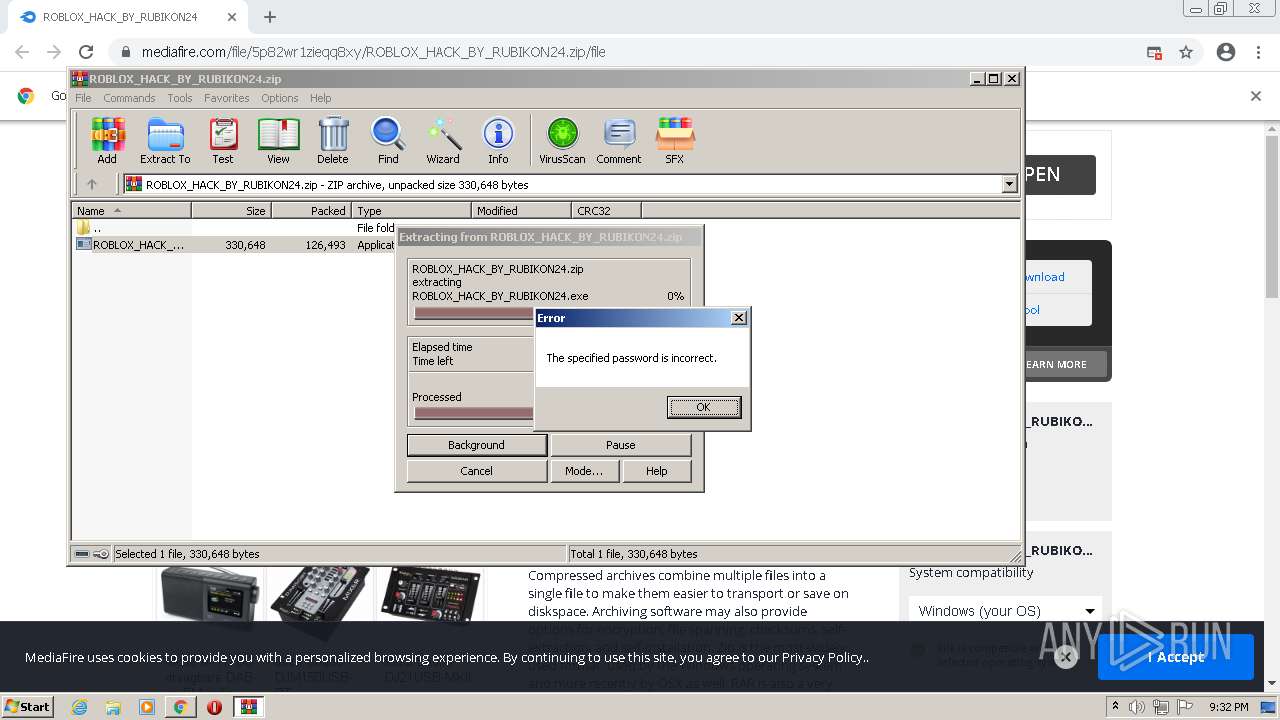
MALICIOUS
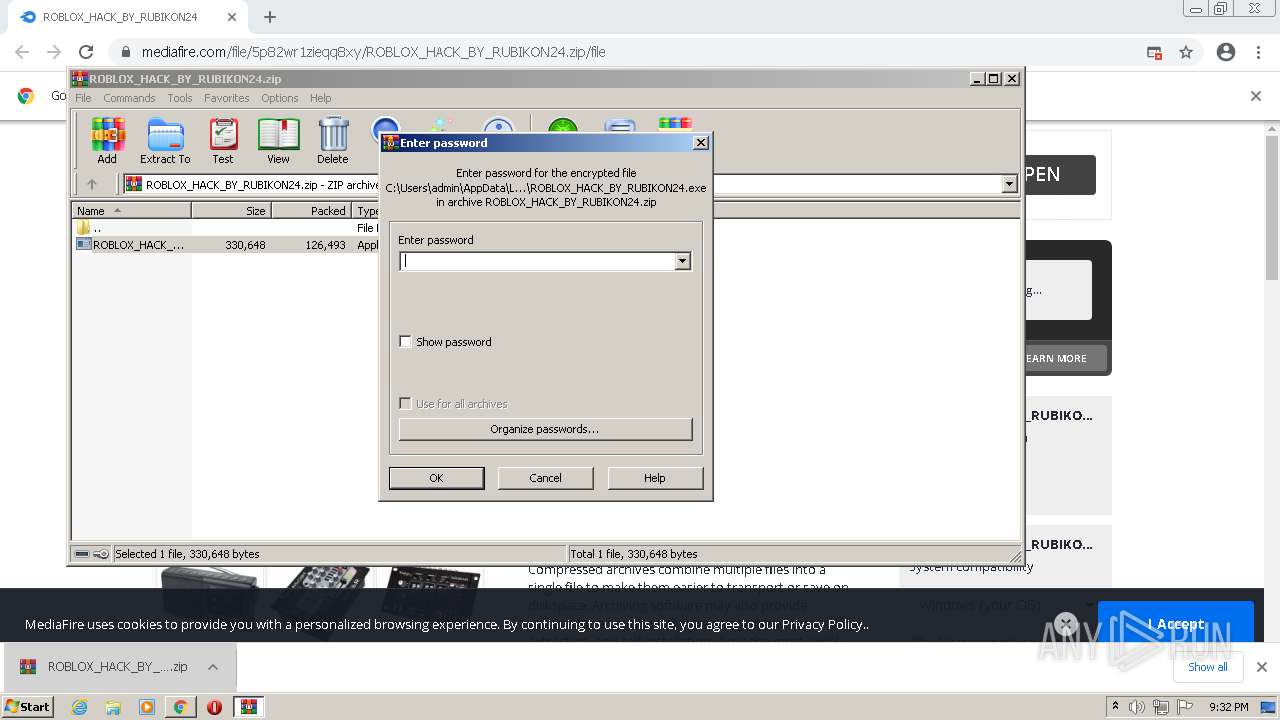
Application was dropped or rewritten from another process
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3292)
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
- asfasf.exe (PID: 3424)
REDLINE was detected
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
- asfasf.exe (PID: 3424)
Steals credentials from Web Browsers
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
Connects to CnC server
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
Actions looks like stealing of personal data
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
- asfasf.exe (PID: 3424)
Stealing of credential data
- asfasf.exe (PID: 3424)
Drops executable file immediately after starts
- chrome.exe (PID: 3548)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3672)
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3292)
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
- asfasf.exe (PID: 3424)
Reads the computer name
- WinRAR.exe (PID: 3672)
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3292)
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
- asfasf.exe (PID: 3424)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3672)
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
- chrome.exe (PID: 3548)
Drops a file with too old compile date
- WinRAR.exe (PID: 3672)
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
Application launched itself
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3292)
Reads Environment values
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
- asfasf.exe (PID: 3424)
Reads the cookies of Google Chrome
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
Reads the cookies of Mozilla Firefox
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
Drops a file with a compile date too recent
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
Creates files in the user directory
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
Reads CPU info
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
Searches for installed software
- asfasf.exe (PID: 3424)
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 3548)
INFO
Checks supported languages
- chrome.exe (PID: 1868)
- chrome.exe (PID: 2744)
- chrome.exe (PID: 464)
- chrome.exe (PID: 784)
- chrome.exe (PID: 2504)
- chrome.exe (PID: 680)
- chrome.exe (PID: 508)
- chrome.exe (PID: 2612)
- chrome.exe (PID: 2700)
- chrome.exe (PID: 2008)
- chrome.exe (PID: 2828)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 2564)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 3420)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 3296)
- chrome.exe (PID: 1068)
- chrome.exe (PID: 1948)
- chrome.exe (PID: 3884)
- chrome.exe (PID: 3496)
- chrome.exe (PID: 2888)
- chrome.exe (PID: 3148)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 2312)
- chrome.exe (PID: 784)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 3496)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 3208)
- chrome.exe (PID: 1128)
- chrome.exe (PID: 3488)
Reads the hosts file
- chrome.exe (PID: 464)
- chrome.exe (PID: 1868)
Reads the computer name
- chrome.exe (PID: 464)
- chrome.exe (PID: 508)
- chrome.exe (PID: 1868)
- chrome.exe (PID: 2008)
- chrome.exe (PID: 2828)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 3296)
- chrome.exe (PID: 1068)
- chrome.exe (PID: 784)
- chrome.exe (PID: 3840)
Application launched itself
- chrome.exe (PID: 1868)
Reads settings of System Certificates
- chrome.exe (PID: 464)
- ROBLOX_HACK_BY_RUBIKON24.exe (PID: 3448)
- asfasf.exe (PID: 3424)
Reads the date of Windows installation
- chrome.exe (PID: 784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
73
Monitored processes
38
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1044,8033658560105299971,5267040691911725871,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1252 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,8033658560105299971,5267040691911725871,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1064 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,8033658560105299971,5267040691911725871,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,8033658560105299971,5267040691911725871,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1836 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,8033658560105299971,5267040691911725871,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3924 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,8033658560105299971,5267040691911725871,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2992 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,8033658560105299971,5267040691911725871,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1460 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://bit.ly/roblox_hack_by_rubikon24" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,8033658560105299971,5267040691911725871,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,8033658560105299971,5267040691911725871,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1076 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
28 477
Read events
28 283
Write events
189
Delete events
5
Modification events
| (PID) Process: | (1868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1868) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
6
Suspicious files
40
Text files
125
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61918040-74C.pma | — | |
MD5:— | SHA256:— | |||
| 1868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ba619f0d-7d6d-4f7b-91f1-2ddde644fdc4.tmp | text | |
MD5:— | SHA256:— | |||
| 1868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 1868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 1868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 1868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RFf1498.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 1868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RFf1861.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
| 1868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
66
TCP/UDP connections
142
DNS requests
95
Threats
44
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
932 | svchost.exe | HEAD | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
464 | chrome.exe | GET | 301 | 185.15.209.141:80 | http://gg.gg/roblox_hack | NL | — | — | shared |
464 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAtIgyHhzCAgf0Woj6GgeOA%3D | US | der | 471 b | whitelisted |
932 | svchost.exe | GET | 206 | 188.120.127.77:80 | http://r2---sn-nvm-cxbs.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=45.86.200.60&mm=28&mn=sn-nvm-cxbs&ms=nvh&mt=1636925055&mv=m&mvi=2&pl=24&rmhost=r3---sn-nvm-cxbs.gvt1.com&shardbypass=yes&smhost=r3---sn-nvm-cxbz.gvt1.com | RS | binary | 20.8 Kb | whitelisted |
932 | svchost.exe | GET | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 613 b | whitelisted |
932 | svchost.exe | GET | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 613 b | whitelisted |
464 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
932 | svchost.exe | GET | 206 | 188.120.127.77:80 | http://r2---sn-nvm-cxbs.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=45.86.200.60&mm=28&mn=sn-nvm-cxbs&ms=nvh&mt=1636925055&mv=m&mvi=2&pl=24&rmhost=r3---sn-nvm-cxbs.gvt1.com&shardbypass=yes&smhost=r3---sn-nvm-cxbz.gvt1.com | RS | binary | 5.63 Kb | whitelisted |
932 | svchost.exe | GET | 206 | 188.120.127.77:80 | http://r2---sn-nvm-cxbs.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=45.86.200.60&mm=28&mn=sn-nvm-cxbs&ms=nvh&mt=1636925055&mv=m&mvi=2&pl=24&rmhost=r3---sn-nvm-cxbs.gvt1.com&shardbypass=yes&smhost=r3---sn-nvm-cxbz.gvt1.com | RS | binary | 9.61 Kb | whitelisted |
932 | svchost.exe | GET | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 613 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
464 | chrome.exe | 142.250.185.77:443 | accounts.google.com | Google Inc. | US | suspicious |
464 | chrome.exe | 67.199.248.10:443 | bit.ly | Bitly Inc | US | shared |
464 | chrome.exe | 142.250.186.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
464 | chrome.exe | 67.26.81.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
464 | chrome.exe | 185.15.209.141:80 | gg.gg | Innovation IT Solutions LTD | NL | suspicious |
464 | chrome.exe | 104.16.202.237:443 | www.mediafire.com | Cloudflare Inc | US | unknown |
464 | chrome.exe | 142.250.185.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
464 | chrome.exe | 142.250.186.72:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
464 | chrome.exe | 142.250.186.130:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
464 | chrome.exe | 142.250.186.78:443 | fundingchoicesmessages.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
bit.ly |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
gg.gg |
| shared |
www.mediafire.com |
| shared |
ssl.gstatic.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY GG Url Shortener Observed in DNS Query |
464 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
464 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3448 | ROBLOX_HACK_BY_RUBIKON24.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 25 |
— | — | Potentially Bad Traffic | ET POLICY Observed DNS Query to File Transfer Service Domain (transfer .sh) |
3448 | ROBLOX_HACK_BY_RUBIKON24.exe | Potential Corporate Privacy Violation | ET POLICY Observed File Transfer Service SSL/TLS Certificate (transfer .sh) |
32 ETPRO signatures available at the full report