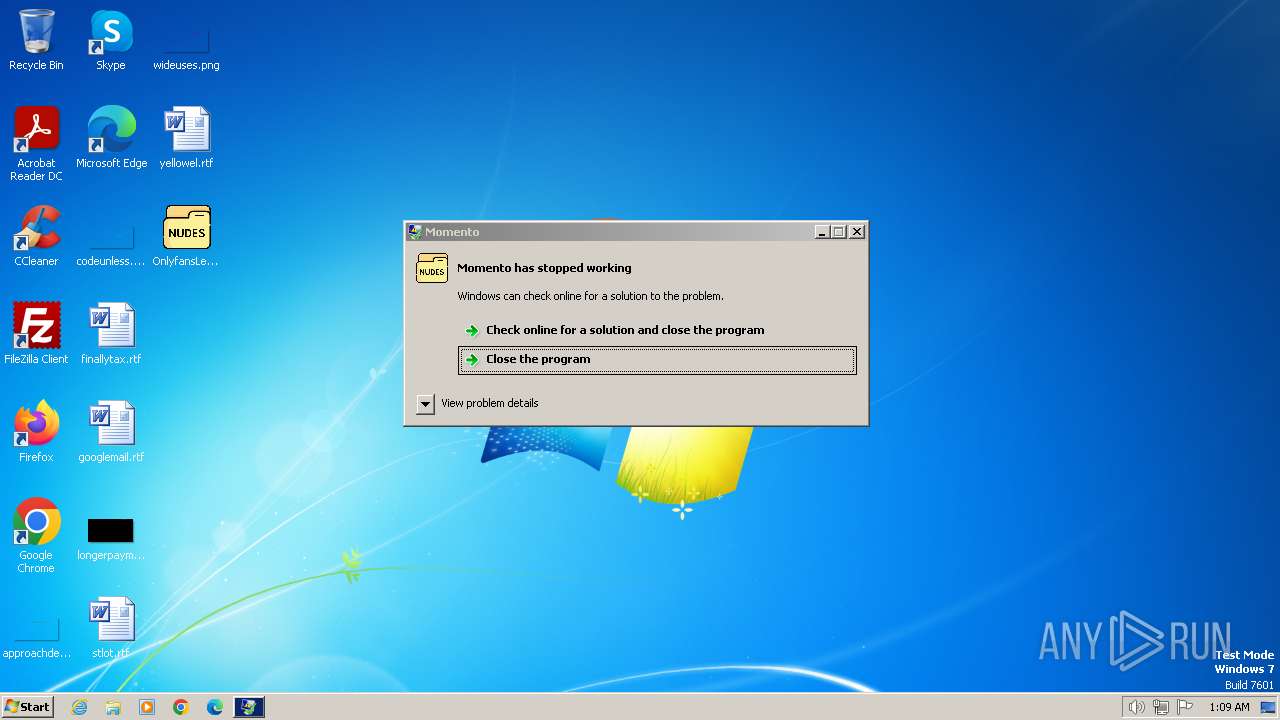
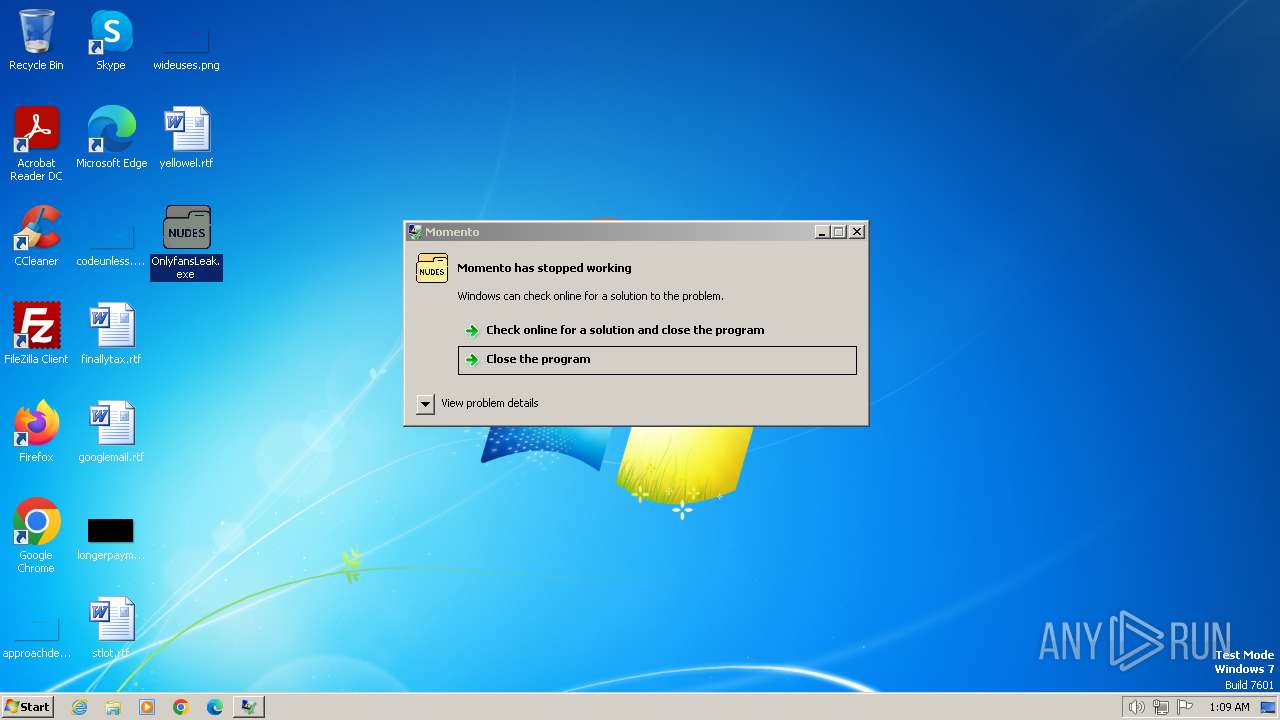
| File name: | OnlyfansLeak.exe |
| Full analysis: | https://app.any.run/tasks/3b9856eb-19f0-42d1-923b-2560781e5814 |
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | December 23, 2023, 01:09:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | C5A7A4C2459F958194A6D3D28956BADD |
| SHA1: | 56EFF1043F263F08391CC6D37110B0149153782E |
| SHA256: | C3924870A9317FE091D8306B83CF837C7B0EDA7107FB187DE2C5DA05E9480609 |
| SSDEEP: | 24576:2yJi4OiUtgNaZvkXNYhdbN5HLMDtMYnJ:2yJi4OiUtgNalkXNYhdbN5HwDtMYn |
MALICIOUS
REDLINE has been detected (SURICATA)
- RegAsm.exe (PID: 1308)
- RegAsm.exe (PID: 1544)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 1308)
- RegAsm.exe (PID: 1544)
Create files in the Startup directory
- RegAsm.exe (PID: 1308)
Steals credentials from Web Browsers
- RegAsm.exe (PID: 1308)
- RegAsm.exe (PID: 1544)
SUSPICIOUS
Reads the Internet Settings
- RegAsm.exe (PID: 1308)
Connects to unusual port
- RegAsm.exe (PID: 1308)
- RegAsm.exe (PID: 1544)
Searches for installed software
- RegAsm.exe (PID: 1544)
- RegAsm.exe (PID: 1308)
Reads browser cookies
- RegAsm.exe (PID: 1544)
- RegAsm.exe (PID: 1308)
INFO
Drops the executable file immediately after the start
- OnlyfansLeak.exe (PID: 120)
- RegAsm.exe (PID: 1308)
Reads the computer name
- RegAsm.exe (PID: 1308)
- qemu-ga.exe (PID: 1972)
- RegAsm.exe (PID: 1544)
- OnlyfansLeak.exe (PID: 1792)
- OnlyfansLeak.exe (PID: 120)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 1308)
- RegAsm.exe (PID: 1544)
Reads product name
- RegAsm.exe (PID: 1308)
- RegAsm.exe (PID: 1544)
Reads Environment values
- RegAsm.exe (PID: 1308)
- RegAsm.exe (PID: 1544)
Checks supported languages
- OnlyfansLeak.exe (PID: 1792)
- RegAsm.exe (PID: 1544)
- OnlyfansLeak.exe (PID: 120)
- RegAsm.exe (PID: 1308)
- qemu-ga.exe (PID: 1972)
Manual execution by a user
- OnlyfansLeak.exe (PID: 1792)
Creates files or folders in the user directory
- RegAsm.exe (PID: 1308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:21 17:27:32+01:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 569856 |
| InitializedDataSize: | 14336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8d12e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | Momento |
| FileVersion: | 1.0.0.0 |
| InternalName: | MSG_NET.exe |
| LegalCopyright: | Copyright © 2023 |
| OriginalFileName: | MSG_NET.exe |
| ProductName: | Momento |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
44
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Users\admin\Desktop\OnlyfansLeak.exe" | C:\Users\admin\Desktop\OnlyfansLeak.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Momento Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1308 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | OnlyfansLeak.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 1544 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | OnlyfansLeak.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 1792 | "C:\Users\admin\Desktop\OnlyfansLeak.exe" | C:\Users\admin\Desktop\OnlyfansLeak.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Momento Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1972 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\qemu-ga.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\qemu-ga.exe | — | RegAsm.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: qemu-ga Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
6 179
Read events
6 171
Write events
8
Delete events
0
Modification events
| (PID) Process: | (1308) RegAsm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1308) RegAsm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1308) RegAsm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1308) RegAsm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1308 | RegAsm.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\qemu-ga.exe | executable | |
MD5:D4910F56121AE1E3049EE0ED506ED5DC | SHA256:AC70C1847BDF903A698DE1BADB72B9F9539AE9CC75CB3ACC3062E4622977EE95 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
0
Threats
8
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1308 | RegAsm.exe | 51.178.148.147:33696 | — | OVH SAS | FR | unknown |
1544 | RegAsm.exe | 51.178.148.147:33696 | — | OVH SAS | FR | unknown |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
1308 | RegAsm.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
1308 | RegAsm.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] RedLine Stealer Family Related (MC-NMF Authorization) |
1308 | RegAsm.exe | A Network Trojan was detected | ET MALWARE Redline Stealer Family Activity (Response) |
1308 | RegAsm.exe | Successful Credential Theft Detected | SUSPICIOUS [ANY.RUN] Clear Text Password Exfiltration Atempt |
1308 | RegAsm.exe | Successful Credential Theft Detected | SUSPICIOUS [ANY.RUN] Clear Text Password Exfiltration Atempt |
1544 | RegAsm.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
1544 | RegAsm.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] RedLine Stealer Family Related (MC-NMF Authorization) |
1544 | RegAsm.exe | A Network Trojan was detected | ET MALWARE Redline Stealer Family Activity (Response) |