| File name: | Recovery_Setup.exe |
| Full analysis: | https://app.any.run/tasks/841876b7-7e3b-4ba4-a8fa-5da26642bdeb |
| Verdict: | Malicious activity |
| Threats: | GCleaner is a type of malware loader that has the capability to deliver numerous malicious software programs, which differ based on the location of the targeted victim. This malware is commonly spread through fraudulent websites that advertise free PC optimization tools |
| Analysis date: | May 22, 2025, 01:43:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InnoSetup self-extracting archive, 8 sections |
| MD5: | 9E571DCA867C875C920F5B9E75181BC3 |
| SHA1: | A3982289E746AEDFC04FF3F96FAC3021669D9007 |
| SHA256: | C34601C5DA3501F6EE0EFCE18DE7E6145153ECFAC2CE2019EC52E1535A4B3193 |
| SSDEEP: | 49152:iiWAHfYiKeoyopaRCSgQU9b0chuziYpRFeKOCs8wu8:iiZwiR+pzCUCchwNsKSd |
MALICIOUS
GCLEANER has been detected (YARA)
- Rec528.exe (PID: 1532)
SUSPICIOUS
Process drops legitimate windows executable
- is-D63CI.tmp (PID: 2140)
Executable content was dropped or overwritten
- Recovery_Setup.exe (PID: 6668)
- Rec528.exe (PID: 1532)
- is-D63CI.tmp (PID: 2140)
Reads security settings of Internet Explorer
- Rec528.exe (PID: 1532)
INFO
The sample compiled with english language support
- is-D63CI.tmp (PID: 2140)
- Recovery_Setup.exe (PID: 6668)
Checks supported languages
- Recovery_Setup.exe (PID: 6668)
- is-D63CI.tmp (PID: 2140)
- Rec528.exe (PID: 1532)
- 4rHovyan0J.exe (PID: 5008)
Create files in a temporary directory
- Recovery_Setup.exe (PID: 6668)
- is-D63CI.tmp (PID: 2140)
Reads the computer name
- is-D63CI.tmp (PID: 2140)
- Rec528.exe (PID: 1532)
Checks proxy server information
- Rec528.exe (PID: 1532)
Creates files or folders in the user directory
- Rec528.exe (PID: 1532)
Detects InnoSetup installer (YARA)
- Recovery_Setup.exe (PID: 6668)
- is-D63CI.tmp (PID: 2140)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 5984)
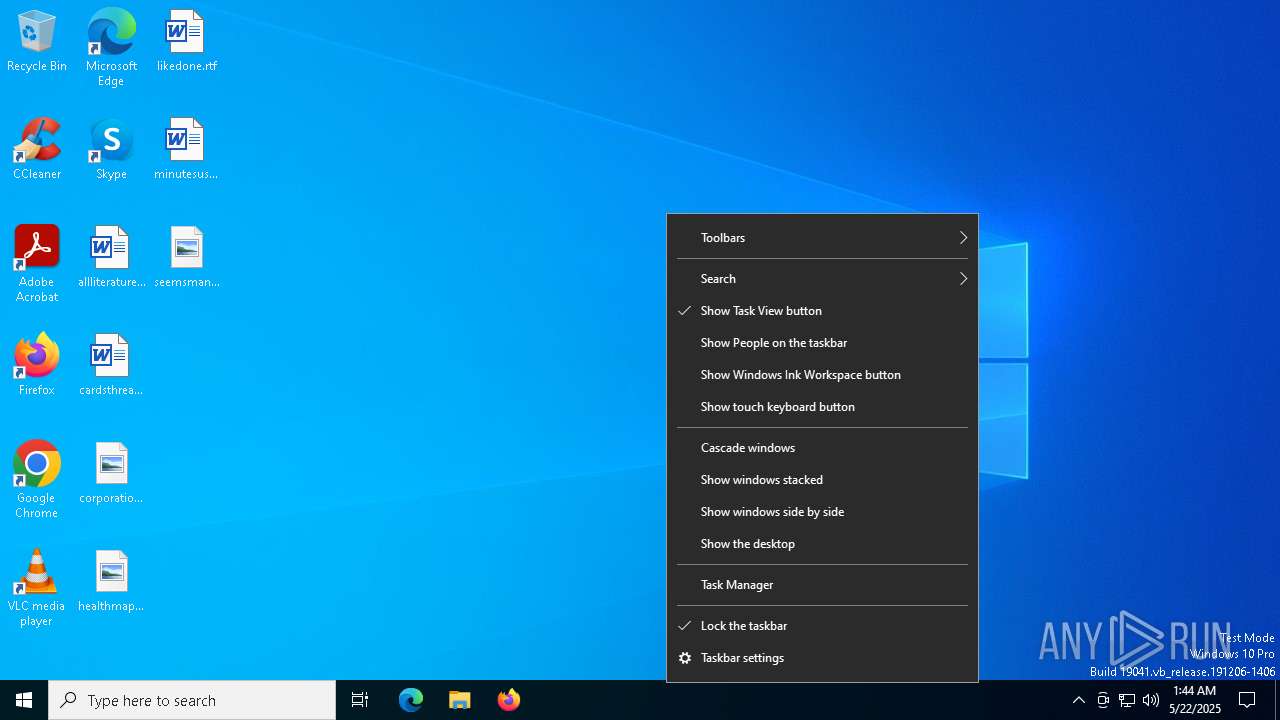
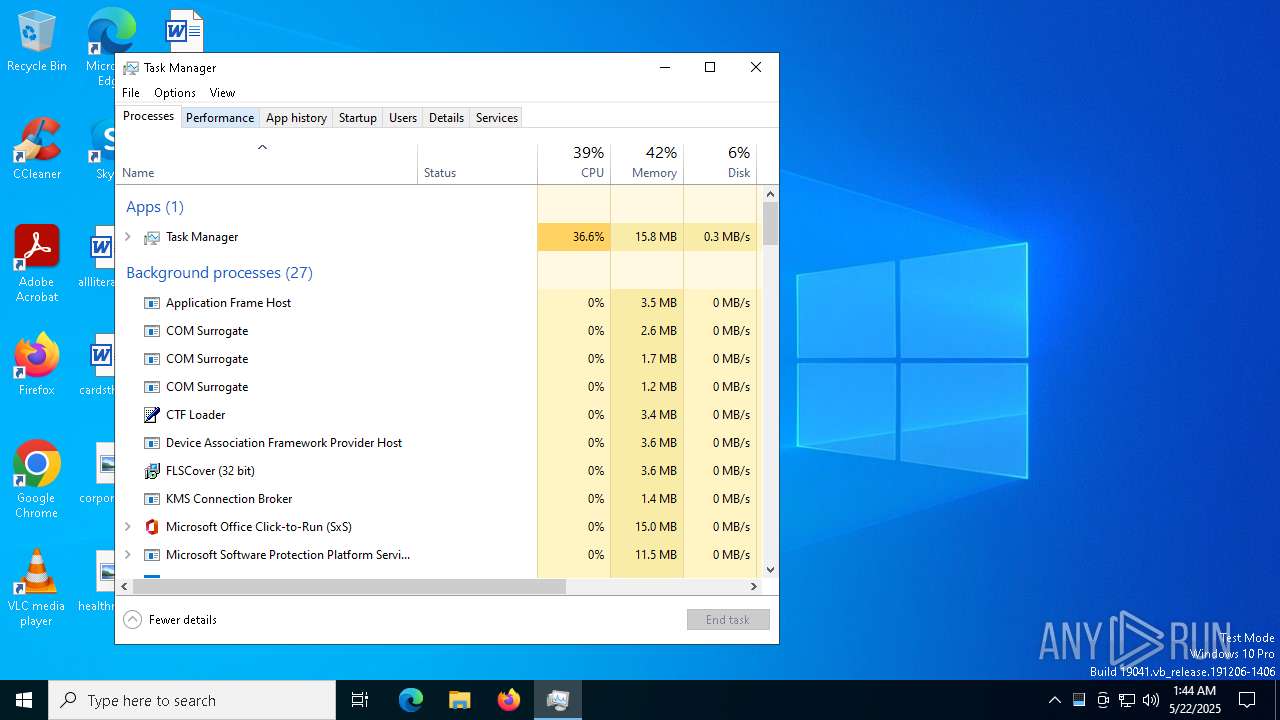
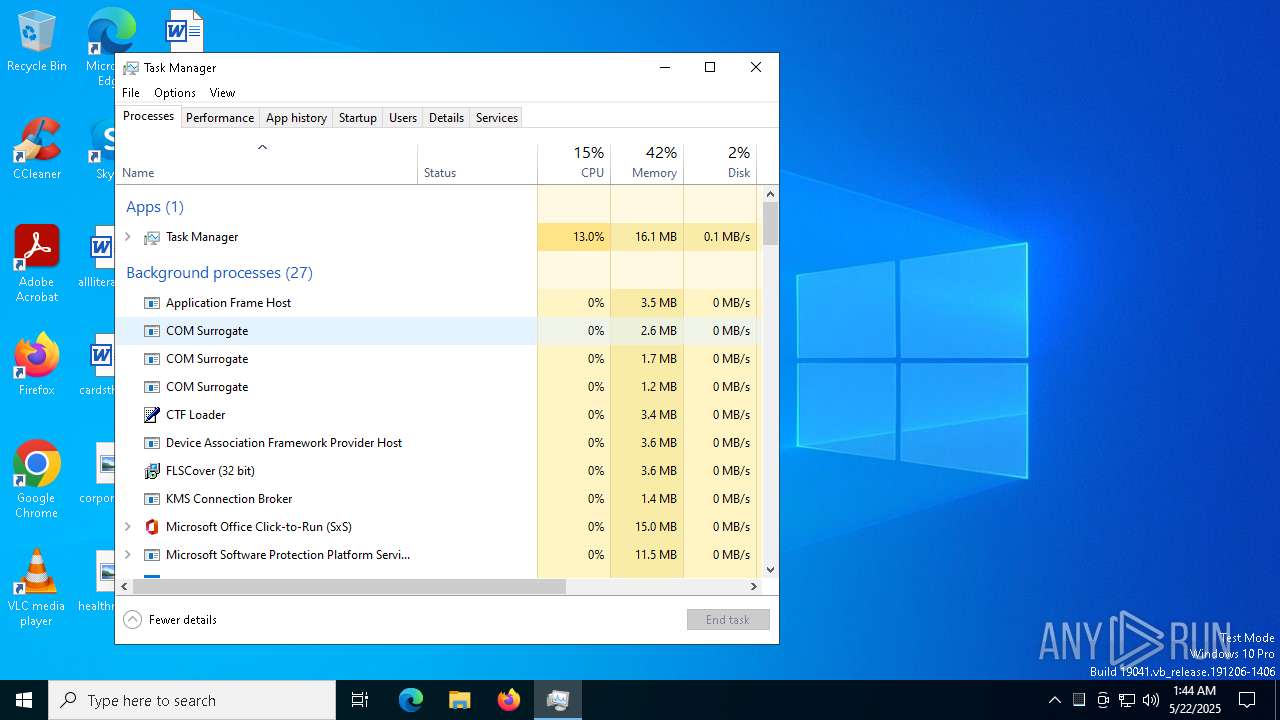
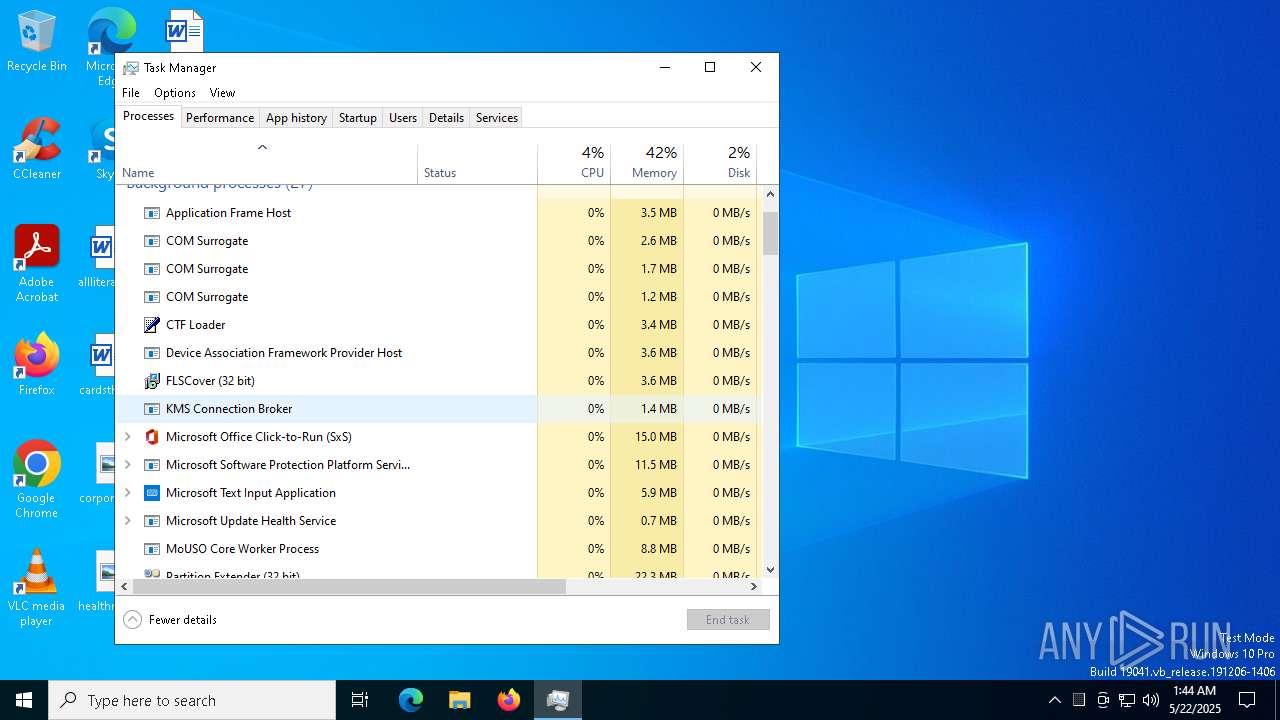
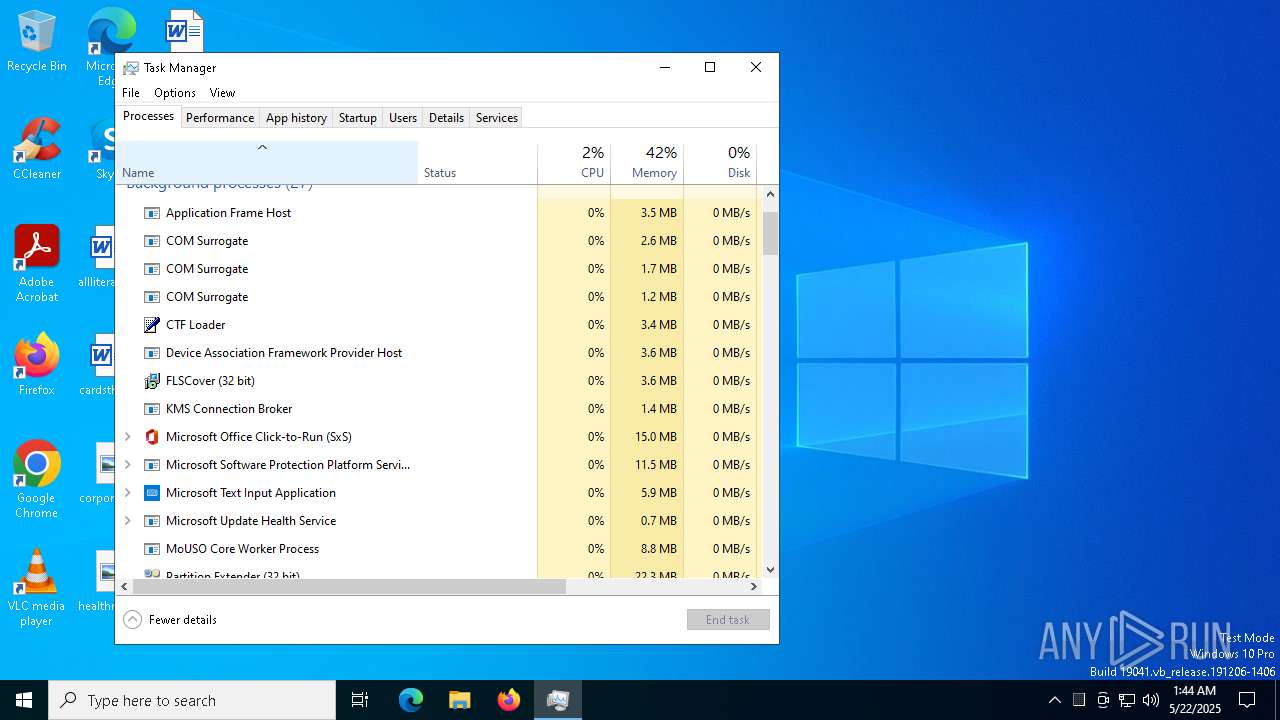
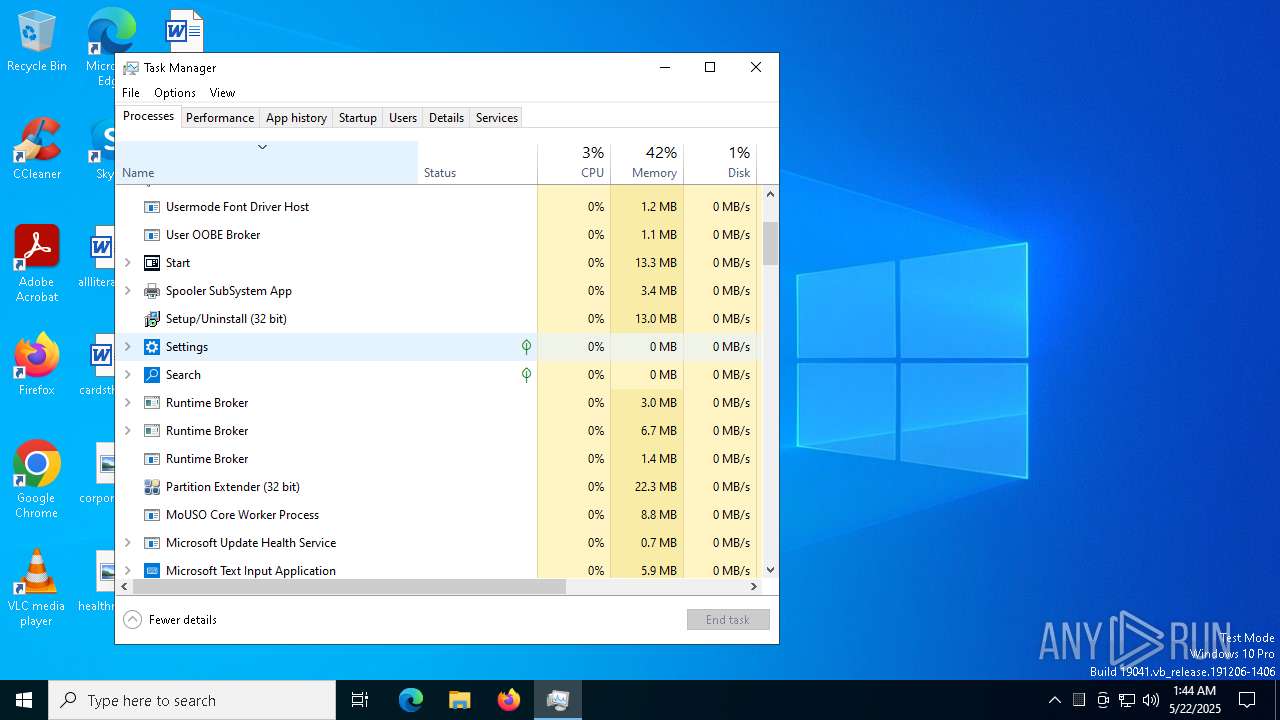
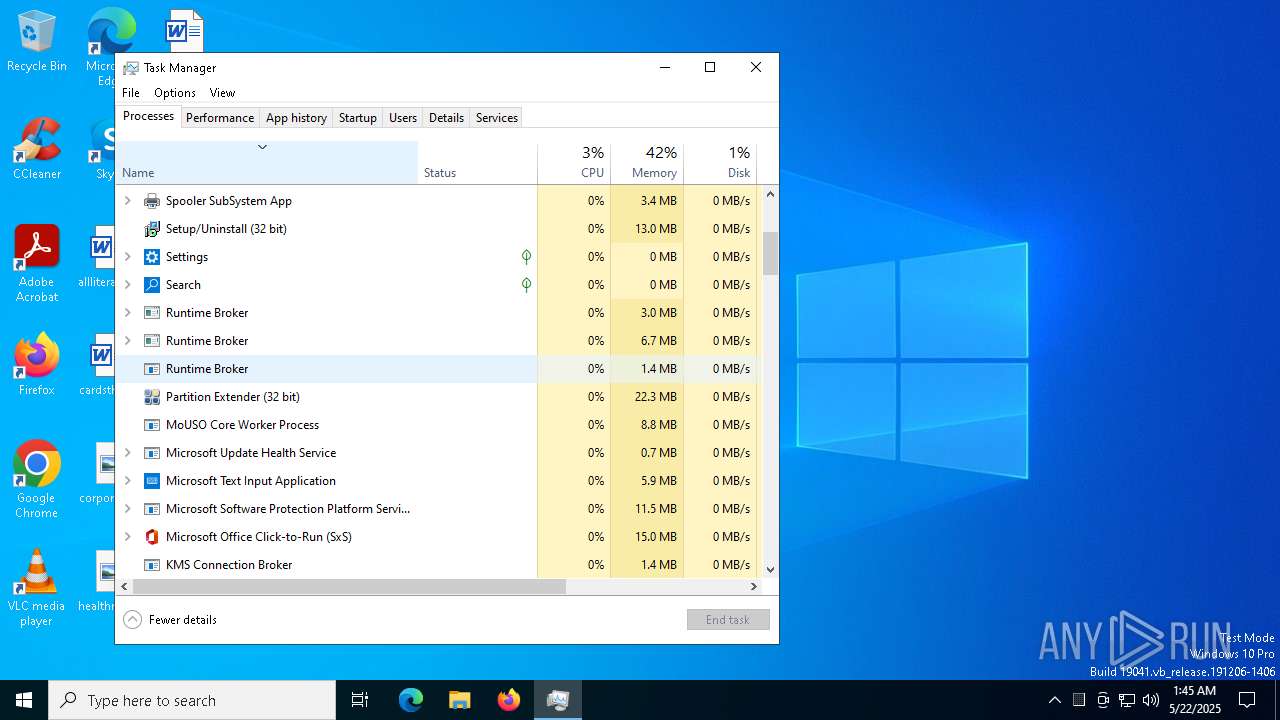
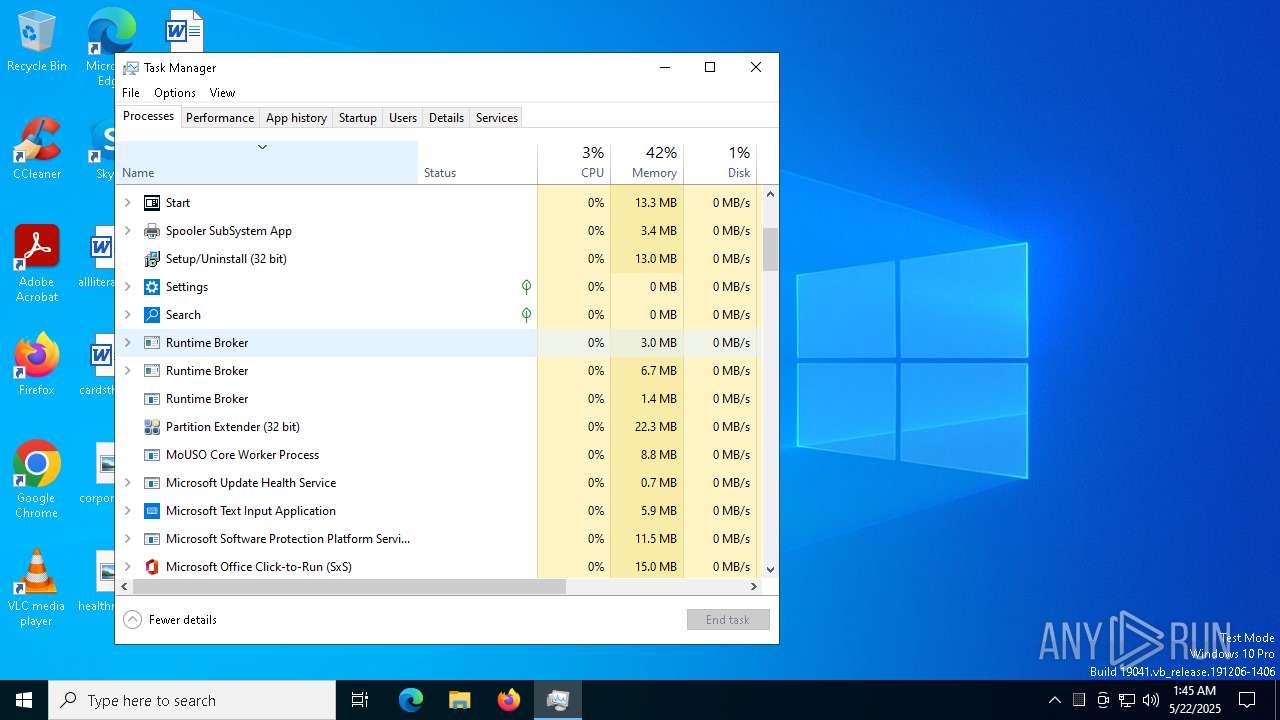
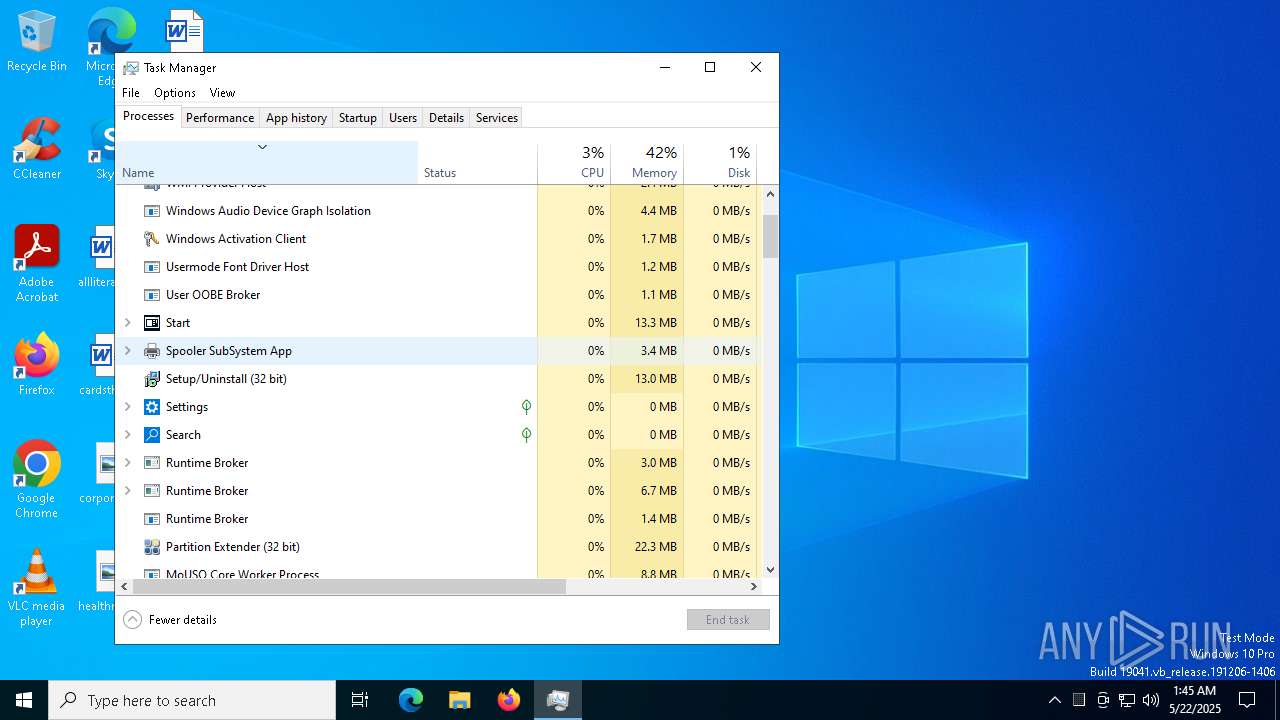
Manual execution by a user
- Taskmgr.exe (PID: 6036)
- Taskmgr.exe (PID: 5984)
Compiled with Borland Delphi (YARA)
- is-D63CI.tmp (PID: 2140)
Creates files in the program directory
- is-D63CI.tmp (PID: 2140)
The sample compiled with chinese language support
- is-D63CI.tmp (PID: 2140)
Creates a software uninstall entry
- is-D63CI.tmp (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (82.8) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.7) |
| .exe | | | Win32 Executable (generic) (3.4) |
| .exe | | | Generic Win/DOS Executable (1.5) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 36864 |
| InitializedDataSize: | 16896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9820 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.5.28 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | This installation was built with Inno Setup: http://www.innosetup.com |
| CompanyName: | |
| FileDescription: | FLSCover |
| FileVersion: | 1.0.5.28 |
| InternalName: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | - |
Total processes
139
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1532 | "C:\Program Files (x86)\FLSCover\Rec528\Rec528.exe" | C:\Program Files (x86)\FLSCover\Rec528\Rec528.exe | is-D63CI.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: Partition Extender Version: 1.4.5.28 Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\AppData\Local\Temp\is-CRE6H.tmp\is-D63CI.tmp" /SL4 $8030C "C:\Users\admin\AppData\Local\Temp\Recovery_Setup.exe" 1937767 52224 | C:\Users\admin\AppData\Local\Temp\is-CRE6H.tmp\is-D63CI.tmp | Recovery_Setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Version: 51.42.0.0 Modules
| |||||||||||||||
| 2316 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5008 | C:\Users\admin\AppData\Roaming\{65b178c1-239c-11ed-b4aa-806e6f6e6963}\4rHovyan0J.exe | — | Rec528.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 5556 | "C:\Users\admin\AppData\Local\Temp\Recovery_Setup.exe" | C:\Users\admin\AppData\Local\Temp\Recovery_Setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: FLSCover Exit code: 3221226540 Version: 1.0.5.28 Modules
| |||||||||||||||
| 5984 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6036 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6668 | "C:\Users\admin\AppData\Local\Temp\Recovery_Setup.exe" | C:\Users\admin\AppData\Local\Temp\Recovery_Setup.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: FLSCover Version: 1.0.5.28 Modules
| |||||||||||||||
| 6800 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 482
Read events
2 470
Write events
11
Delete events
1
Modification events
| (PID) Process: | (2140) is-D63CI.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Rec528_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.1.3-beta | |||
| (PID) Process: | (2140) is-D63CI.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Rec528_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\FLSCover\Rec528 | |||
| (PID) Process: | (2140) is-D63CI.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Rec528_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\FLSCover\Rec528\ | |||
| (PID) Process: | (2140) is-D63CI.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Rec528_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: FLSCover\Rec528 | |||
| (PID) Process: | (2140) is-D63CI.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Rec528_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (2140) is-D63CI.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Rec528_is1 |
| Operation: | write | Name: | DisplayName |
Value: Cov 1.0.5.28 | |||
| (PID) Process: | (2140) is-D63CI.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Rec528_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files (x86)\FLSCover\Rec528\unins000.exe" | |||
| (PID) Process: | (2140) is-D63CI.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Rec528_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files (x86)\FLSCover\Rec528\unins000.exe" /SILENT | |||
| (PID) Process: | (2140) is-D63CI.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Rec528_is1 |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (2140) is-D63CI.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Rec528_is1 |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
Executable files
9
Suspicious files
5
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | is-D63CI.tmp | C:\Users\admin\AppData\Local\Temp\is-OMEHH.tmp\_iscrypt.dll | executable | |
MD5:A69559718AB506675E907FE49DEB71E9 | SHA256:2F6294F9AA09F59A574B5DCD33BE54E16B39377984F3D5658CDA44950FA0F8FC | |||
| 6668 | Recovery_Setup.exe | C:\Users\admin\AppData\Local\Temp\is-CRE6H.tmp\is-D63CI.tmp | executable | |
MD5:1F2BC482C99F55A713CF6CA3C1FF04F8 | SHA256:0A0D0B1916549CF997E2110A768D5BD088F5D1390960C22CB9609FE722779DCF | |||
| 2140 | is-D63CI.tmp | C:\Program Files (x86)\FLSCover\Rec528\Rec528.exe | binary | |
MD5:2547449C3AD1973E8DA4C2813C5DE0B4 | SHA256:5D71A400E4736189C42A38FE325EDB3547E486C1614C88F53924E0124D4300D0 | |||
| 2140 | is-D63CI.tmp | C:\Program Files (x86)\FLSCover\Rec528\Readme.txt | text | |
MD5:C0AE85DB30FE9027DBBF3BA758FA78BE | SHA256:CF63BBFD735C18757AC2AA6CB8A14C82745B6158F9FD299BD189D9CA3E7A2DE7 | |||
| 2140 | is-D63CI.tmp | C:\Program Files (x86)\FLSCover\Rec528\finalrecovery.chm | binary | |
MD5:37E6EEA8C4E469F6439F3790166815DD | SHA256:606D66026DA226D1AA1C1A4CA6416F3B9F6C66791F4116EB3FFF9E8E28E6B113 | |||
| 2140 | is-D63CI.tmp | C:\Program Files (x86)\FLSCover\Rec528\is-ME4FG.tmp | binary | |
MD5:2547449C3AD1973E8DA4C2813C5DE0B4 | SHA256:5D71A400E4736189C42A38FE325EDB3547E486C1614C88F53924E0124D4300D0 | |||
| 2140 | is-D63CI.tmp | C:\Program Files (x86)\FLSCover\Rec528\unins000.exe | executable | |
MD5:9ED3858F4C066125A0A6B9FADCD95DCE | SHA256:8EFE36858B9E1CDF3B5D901A4EC17E4EEC148707F526264F35A2BCDA5E139A13 | |||
| 2140 | is-D63CI.tmp | C:\Program Files (x86)\FLSCover\Rec528\Preview.exe | executable | |
MD5:5C2FE7D4DDE65810152054F3C93C1815 | SHA256:233D846FEB73A38141BDF6C813C7476FA3F66DCD3548338607F3B7CB61CAC730 | |||
| 2140 | is-D63CI.tmp | C:\Program Files (x86)\FLSCover\Rec528\is-H0FAN.tmp | binary | |
MD5:37E6EEA8C4E469F6439F3790166815DD | SHA256:606D66026DA226D1AA1C1A4CA6416F3B9F6C66791F4116EB3FFF9E8E28E6B113 | |||
| 2140 | is-D63CI.tmp | C:\Program Files (x86)\FLSCover\Rec528\data\is-O1PNG.tmp | xml | |
MD5:247D3A0C3B0C53CA33D032A561619495 | SHA256:783AC8FBA1DD88291A4F331EC2459DDE4005CF70FAFB4F19F9061713FFD580EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5404 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | CL | binary | 407 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5404 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | CL | binary | 419 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1532 | Rec528.exe | 45.12.253.56:80 | — | VNET a.s. | BG | malicious |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5404 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |