| File name: | file |
| Full analysis: | https://app.any.run/tasks/94894b55-e705-4a43-b93c-e4d9f505ee46 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | December 21, 2024, 06:33:33 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | CAE8A411CF8F2223C645DAE80819489B |
| SHA1: | E8A4D2C9A8ED23BB0525A609877C8BA99B4A4CA8 |
| SHA256: | C3269A1D5644EFFDF2071A8437D4DEF5644074BCAC0B73715CA891F6B10F5274 |
| SSDEEP: | 98304:bvINkY6lDAZrnTnLznCzrjPPXwNPER/soIo+8w6H1rzqdORqgLMOzJSWVL8je1dv:rA |
MALICIOUS
AMADEY mutex has been found
- skotes.exe (PID: 6228)
- file.exe (PID: 7024)
- file.exe (PID: 7164)
- file.exe (PID: 3696)
- file.exe (PID: 2144)
- skotes.exe (PID: 6180)
- file.exe (PID: 7036)
- file.exe (PID: 1476)
Connects to the CnC server
- skotes.exe (PID: 6228)
AMADEY has been detected (SURICATA)
- skotes.exe (PID: 6228)
AMADEY has been detected (YARA)
- skotes.exe (PID: 6228)
SUSPICIOUS
Reads the BIOS version
- file.exe (PID: 1476)
- skotes.exe (PID: 6228)
- file.exe (PID: 7024)
- file.exe (PID: 7164)
- file.exe (PID: 3696)
- skotes.exe (PID: 6180)
- file.exe (PID: 2144)
- file.exe (PID: 7036)
Reads security settings of Internet Explorer
- skotes.exe (PID: 6228)
- file.exe (PID: 1476)
Starts itself from another location
- file.exe (PID: 1476)
Contacting a server suspected of hosting an CnC
- skotes.exe (PID: 6228)
Connects to the server without a host name
- skotes.exe (PID: 6228)
The process executes via Task Scheduler
- skotes.exe (PID: 6180)
Executable content was dropped or overwritten
- file.exe (PID: 1476)
INFO
Checks supported languages
- file.exe (PID: 1476)
- skotes.exe (PID: 6228)
- file.exe (PID: 7164)
- file.exe (PID: 7024)
- skotes.exe (PID: 6180)
- file.exe (PID: 3696)
- file.exe (PID: 2144)
- file.exe (PID: 7036)
Reads the computer name
- file.exe (PID: 1476)
- skotes.exe (PID: 6228)
Sends debugging messages
- skotes.exe (PID: 6228)
- file.exe (PID: 7024)
- file.exe (PID: 7164)
- skotes.exe (PID: 6180)
- file.exe (PID: 3696)
- file.exe (PID: 2144)
- file.exe (PID: 7036)
- file.exe (PID: 1476)
Checks proxy server information
- skotes.exe (PID: 6228)
Process checks computer location settings
- file.exe (PID: 1476)
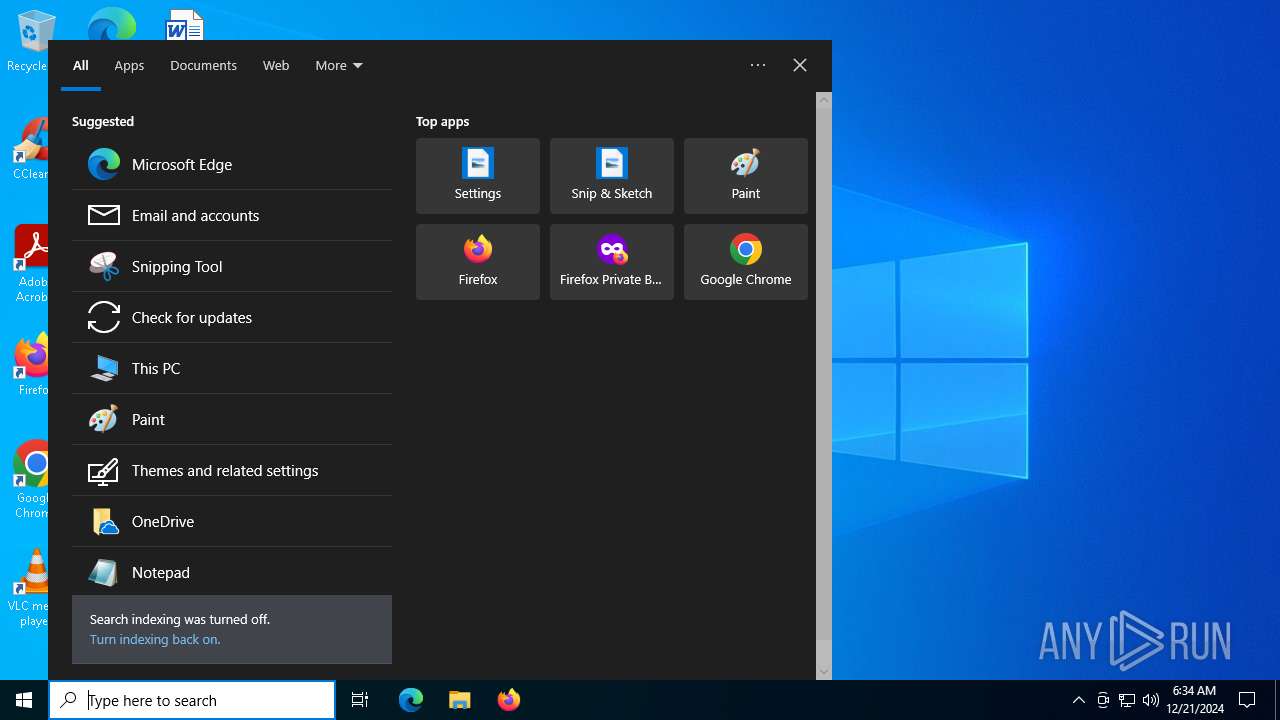
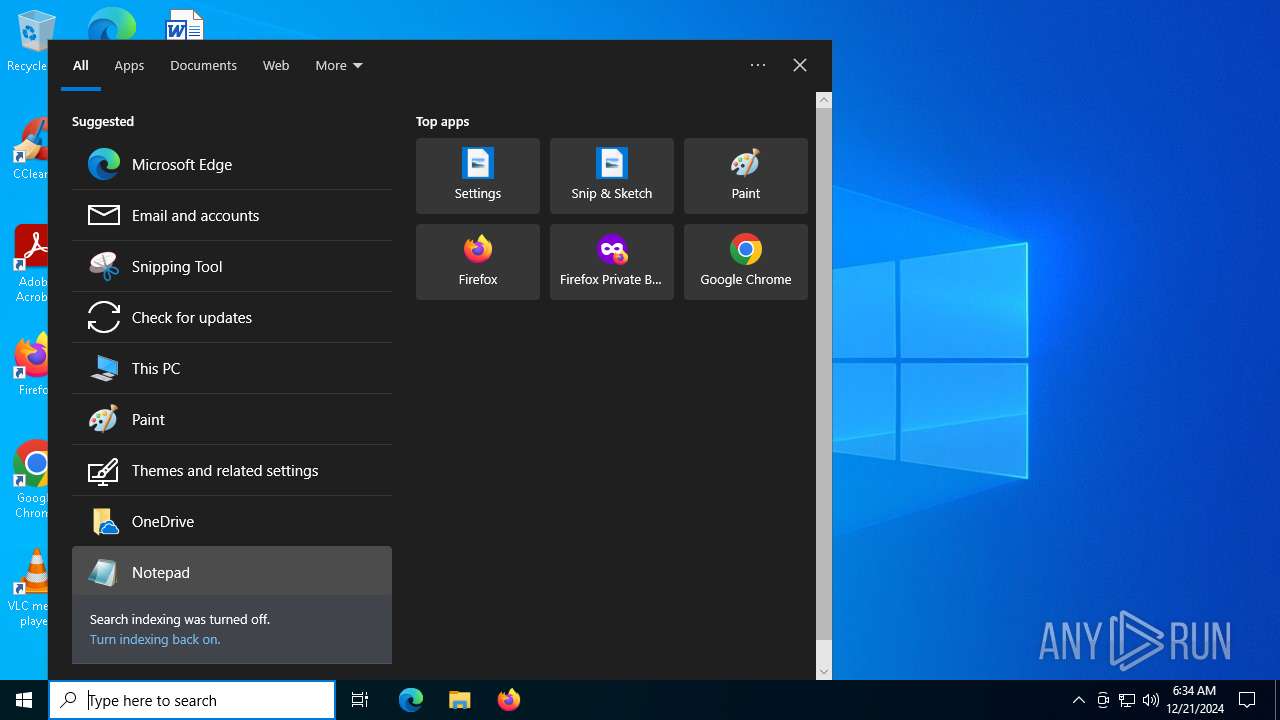
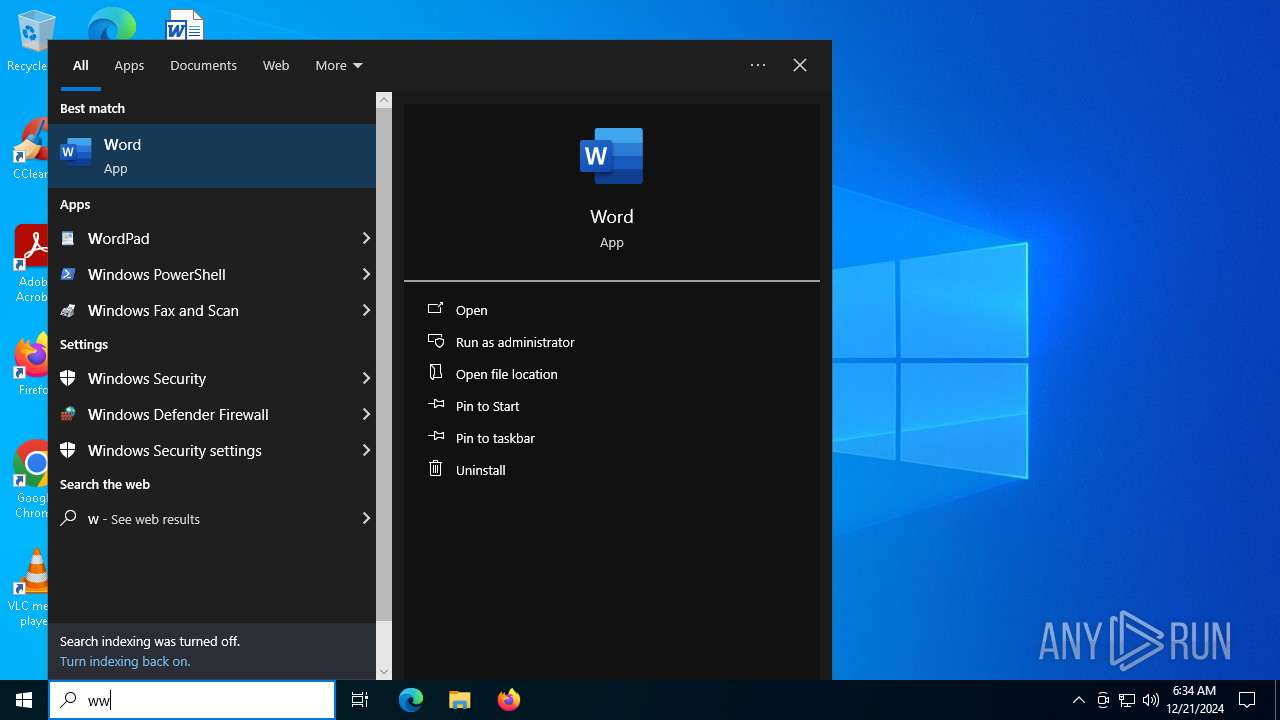
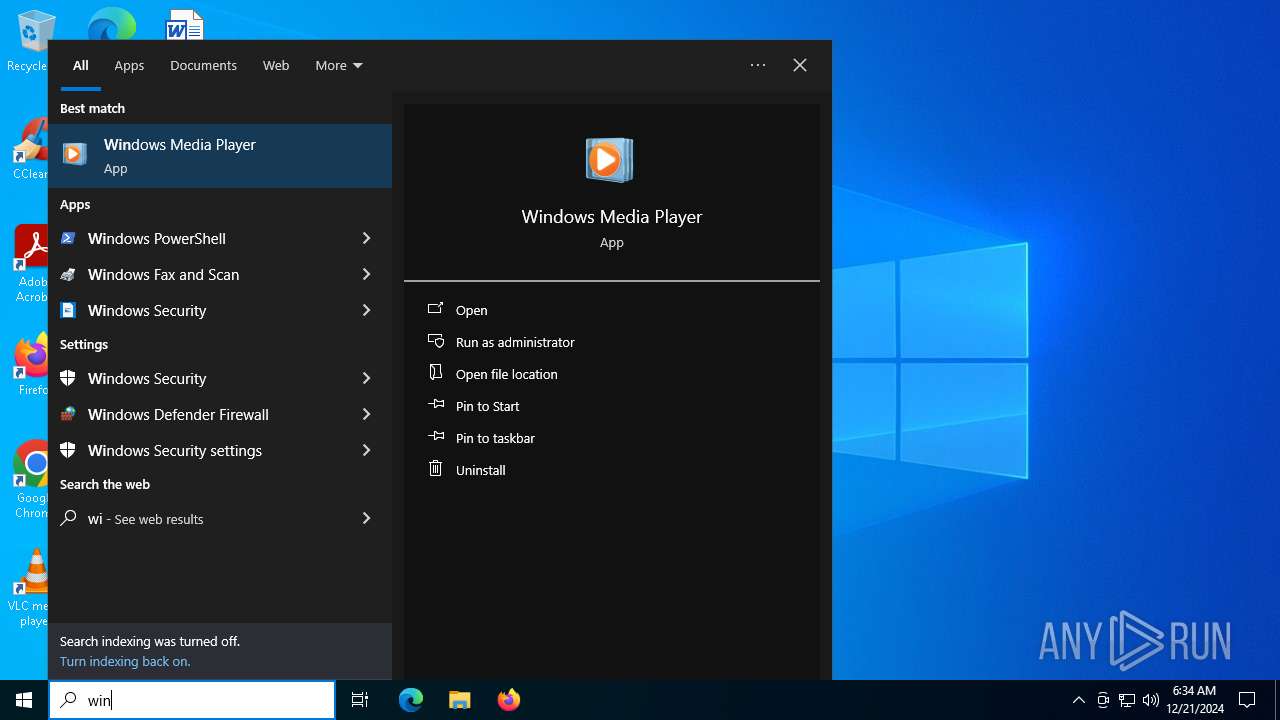
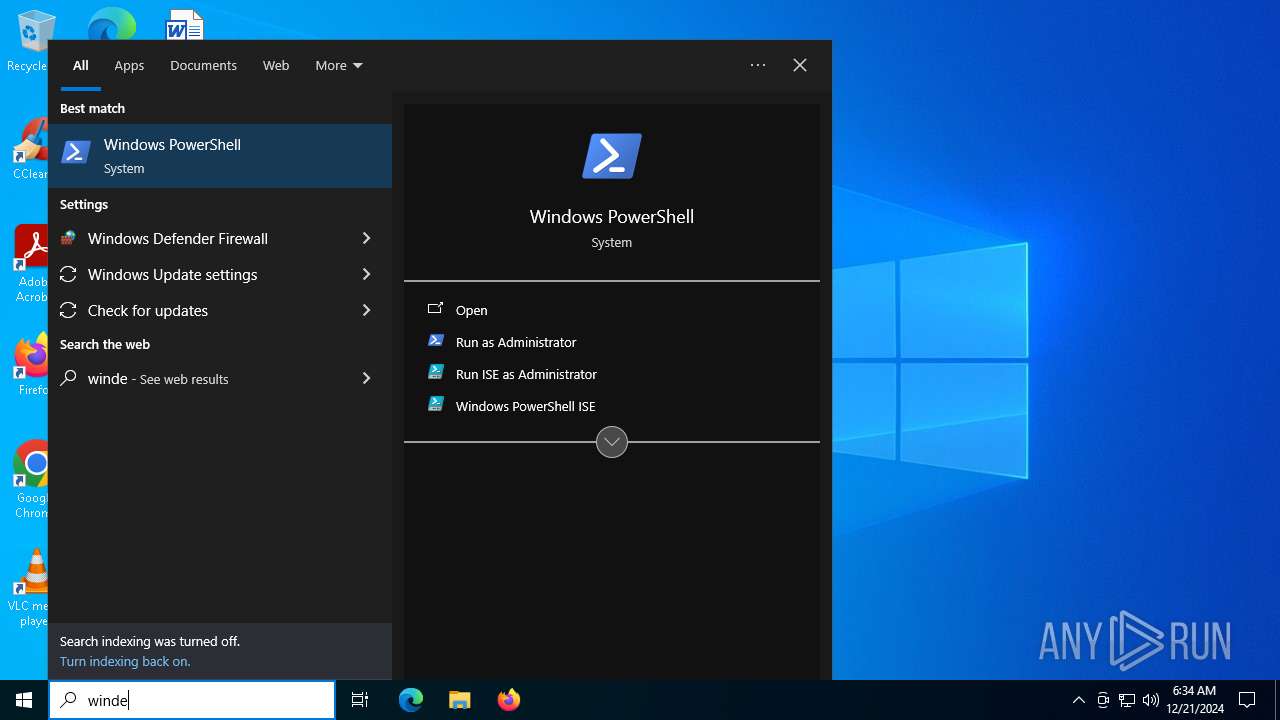
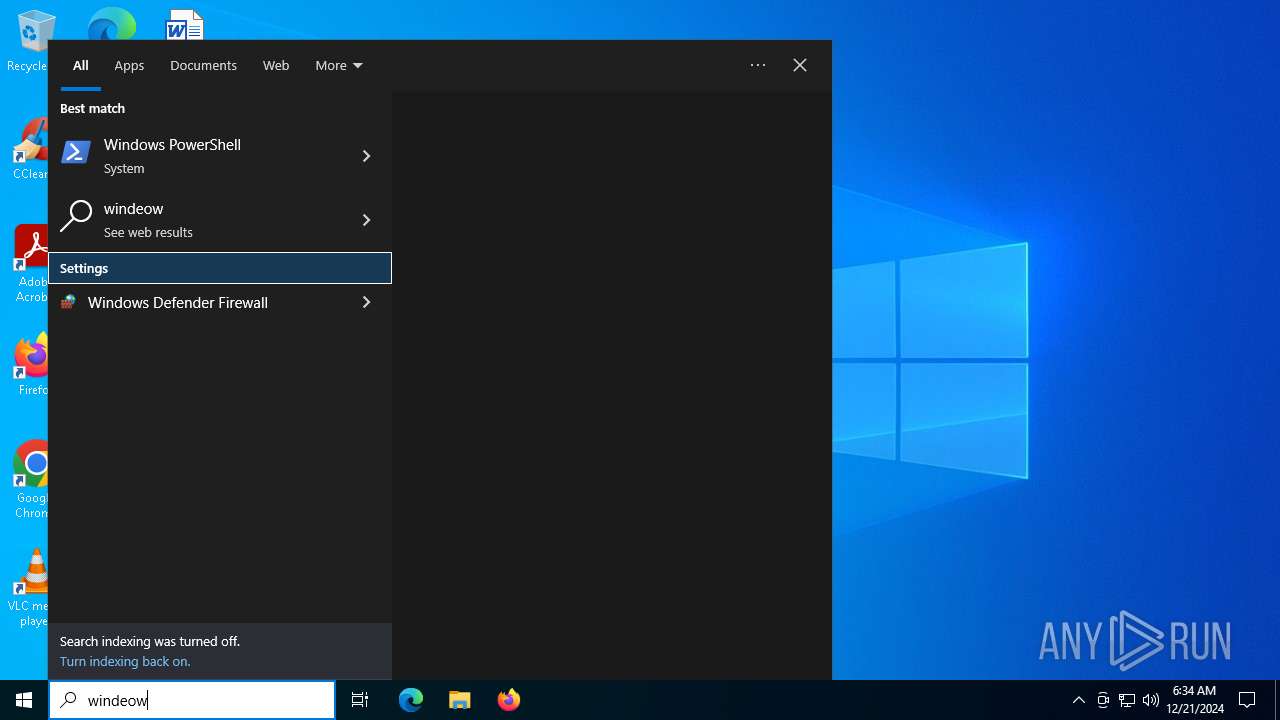
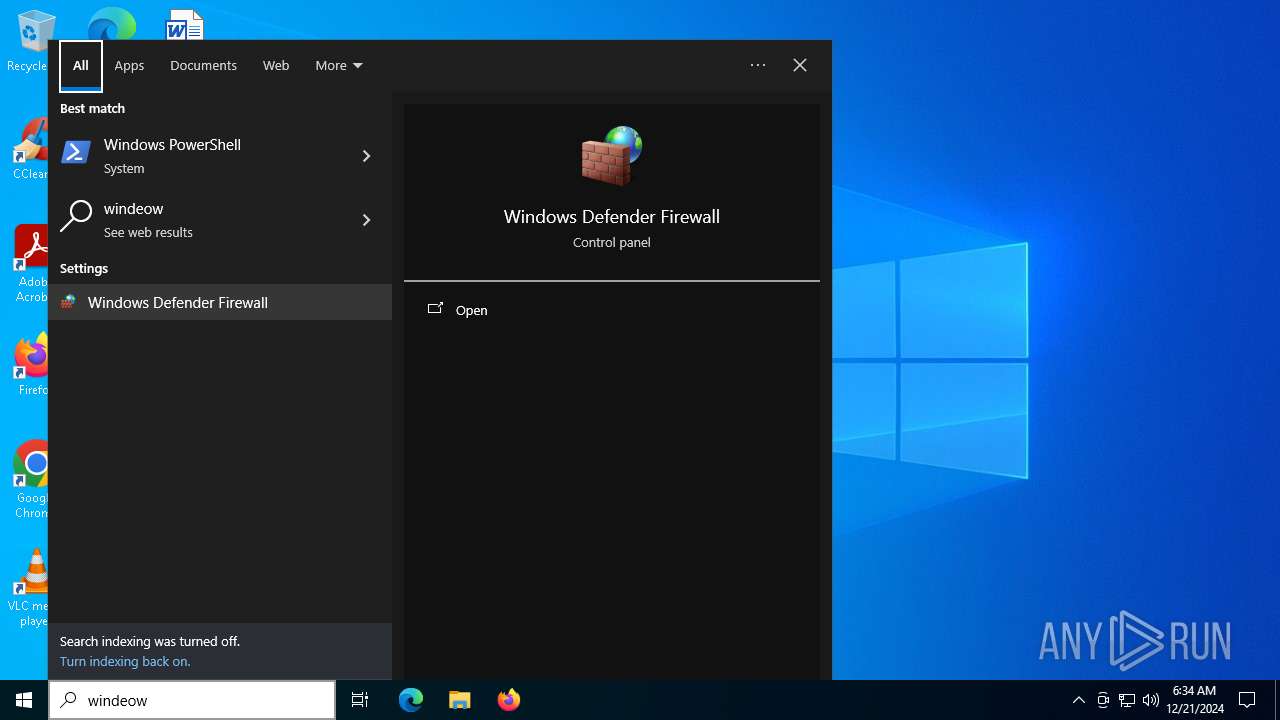
Manual execution by a user
- file.exe (PID: 7164)
- file.exe (PID: 7024)
- file.exe (PID: 3696)
- file.exe (PID: 2144)
- file.exe (PID: 7036)
Themida protector has been detected
- skotes.exe (PID: 6228)
Reads security settings of Internet Explorer
- explorer.exe (PID: 624)
Checks transactions between databases Windows and Oracle
- explorer.exe (PID: 624)
Create files in a temporary directory
- file.exe (PID: 1476)
The process uses the downloaded file
- file.exe (PID: 1476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(6228) skotes.exe
C2185.215.113.43
URLhttp://185.215.113.43/Zu7JuNko/index.php
Version4.42
Options
Drop directoryabc3bc1985
Drop nameskotes.exe
Strings (120)2016
cmd /C RMDIR /s/q
Comodo
st=s
=
skotes.exe
\App
Norton
e1
AVG
" && timeout 1 && del
exe
2019
--
wb
DefaultSettings.YResolution
ProgramData\
:::
VideoID
Rem
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
http://
<d>
2022
Sophos
Programs
lv:
&unit=
------
POST
%-lu
<c>
Content-Type: application/x-www-form-urlencoded
185.215.113.43
Doctor Web
\
id:
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
360TotalSecurity
Startup
clip.dll
"
Content-Type: application/octet-stream
Content-Type: multipart/form-data; boundary=----
cred.dll|clip.dll|
S-%lu-
rb
rundll32.exe
0123456789
GetNativeSystemInfo
abc3bc1985
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
" && ren
d1
ESET
vs:
"
------
sd:
WinDefender
dll
e0
%USERPROFILE%
Panda Security
SOFTWARE\Microsoft\Windows NT\CurrentVersion
zip
cmd
-unicode-
cred.dll
shell32.dll
ProductName
&&
shutdown -s -t 0
|
/Plugins/
Bitdefender
\0000
Content-Disposition: form-data; name="data"; filename="
/Zu7JuNko/index.php
os:
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
av:
4.42
-%lu
Avira
GET
e2
/quiet
Kaspersky Lab
#
ps1
-executionpolicy remotesigned -File "
DefaultSettings.XResolution
Powershell.exe
bi:
msi
https://
random
pc:
un:
abcdefghijklmnopqrstuvwxyz0123456789-_
ar:
Main
"taskkill /f /im "
ComputerName
2025
AVAST Software
SYSTEM\ControlSet001\Services\BasicDisplay\Video
r=
.jpg
CurrentBuild
og:
dm:
?scr=1
kernel32.dll
/k
&& Exit"
+++
rundll32
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:09:22 17:40:44+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.24 |
| CodeSize: | 322048 |
| InitializedDataSize: | 104960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x32a000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
142
Monitored processes
11
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | C:\WINDOWS\explorer.exe /factory,{5BD95610-9434-43C2-886C-57852CC8A120} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1476 | "C:\Users\admin\Desktop\file.exe" | C:\Users\admin\Desktop\file.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2144 | "C:\Users\admin\Desktop\file.exe" | C:\Users\admin\Desktop\file.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3696 | "C:\Users\admin\Desktop\file.exe" | C:\Users\admin\Desktop\file.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4500 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{06622D85-6856-4460-8DE1-A81921B41C4B} | C:\Windows\SysWOW64\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5092 | C:\WINDOWS\system32\DllHost.exe /Processid:{A4B07E49-6567-4FB8-8D39-01920E3B2357} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6180 | "C:\Users\admin\AppData\Local\Temp\abc3bc1985\skotes.exe" | C:\Users\admin\AppData\Local\Temp\abc3bc1985\skotes.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6228 | "C:\Users\admin\AppData\Local\Temp\abc3bc1985\skotes.exe" | C:\Users\admin\AppData\Local\Temp\abc3bc1985\skotes.exe | file.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
Amadey(PID) Process(6228) skotes.exe C2185.215.113.43 URLhttp://185.215.113.43/Zu7JuNko/index.php Version4.42 Options Drop directoryabc3bc1985 Drop nameskotes.exe Strings (120)2016 cmd /C RMDIR /s/q Comodo st=s = skotes.exe \App Norton e1 AVG " && timeout 1 && del exe 2019 -- wb DefaultSettings.YResolution ProgramData\ ::: VideoID Rem SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce SOFTWARE\Microsoft\Windows\CurrentVersion\Run http:// <d> 2022 Sophos Programs lv: &unit= ------ POST %-lu <c> Content-Type: application/x-www-form-urlencoded 185.215.113.43 Doctor Web \ id: SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders 360TotalSecurity Startup clip.dll "
Content-Type: application/octet-stream Content-Type: multipart/form-data; boundary=---- cred.dll|clip.dll| S-%lu- rb rundll32.exe 0123456789 GetNativeSystemInfo abc3bc1985 SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\ " && ren d1 ESET vs: " ------ sd: WinDefender dll e0 %USERPROFILE% Panda Security SOFTWARE\Microsoft\Windows NT\CurrentVersion zip cmd -unicode- cred.dll shell32.dll ProductName && shutdown -s -t 0 | /Plugins/ Bitdefender \0000 Content-Disposition: form-data; name="data"; filename=" /Zu7JuNko/index.php os: SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders av: 4.42 -%lu Avira GET e2 /quiet Kaspersky Lab # ps1 -executionpolicy remotesigned -File " DefaultSettings.XResolution Powershell.exe bi: msi https:// random pc: un: abcdefghijklmnopqrstuvwxyz0123456789-_ ar: Main "taskkill /f /im " ComputerName 2025 AVAST Software SYSTEM\ControlSet001\Services\BasicDisplay\Video r= .jpg CurrentBuild og: dm: ?scr=1 kernel32.dll /k && Exit" +++ rundll32 | |||||||||||||||
| 7024 | "C:\Users\admin\Desktop\file.exe" | C:\Users\admin\Desktop\file.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7036 | "C:\Users\admin\Desktop\file.exe" | C:\Users\admin\Desktop\file.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
7 747
Read events
7 678
Write events
66
Delete events
3
Modification events
| (PID) Process: | (6228) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6228) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6228) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (624) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (624) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 00000000040000000E00000003000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (624) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (624) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\5\Shell\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Rev |
Value: 0 | |||
| (PID) Process: | (624) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\5\Shell\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | FFlags |
Value: 18874369 | |||
| (PID) Process: | (624) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\5\Shell\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Vid |
Value: {65F125E5-7BE1-4810-BA9D-D271C8432CE3} | |||
| (PID) Process: | (624) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\5\Shell\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Mode |
Value: 6 | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1476 | file.exe | C:\Windows\Tasks\skotes.job | binary | |
MD5:5C1248037C7AD7B03CC65510DC854FE4 | SHA256:346EAADFAA7909414462FD712CF686034B7EB99C83B05A46DF9FCA4FC82D4290 | |||
| 1476 | file.exe | C:\Users\admin\AppData\Local\Temp\abc3bc1985\skotes.exe | executable | |
MD5:CAE8A411CF8F2223C645DAE80819489B | SHA256:C3269A1D5644EFFDF2071A8437D4DEF5644074BCAC0B73715CA891F6B10F5274 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
50
DNS requests
23
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6228 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
6228 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
7108 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7108 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6288 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5892 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.25:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 23.212.110.178:443 | www.bing.com | Akamai International B.V. | CZ | whitelisted |
1176 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6228 | skotes.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
file.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
file.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
file.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
file.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
file.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
file.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|