| download: | sureboy.exe |
| Full analysis: | https://app.any.run/tasks/9865e8ea-5d82-4310-9287-fdb813956374 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | April 15, 2019, 01:54:48 |
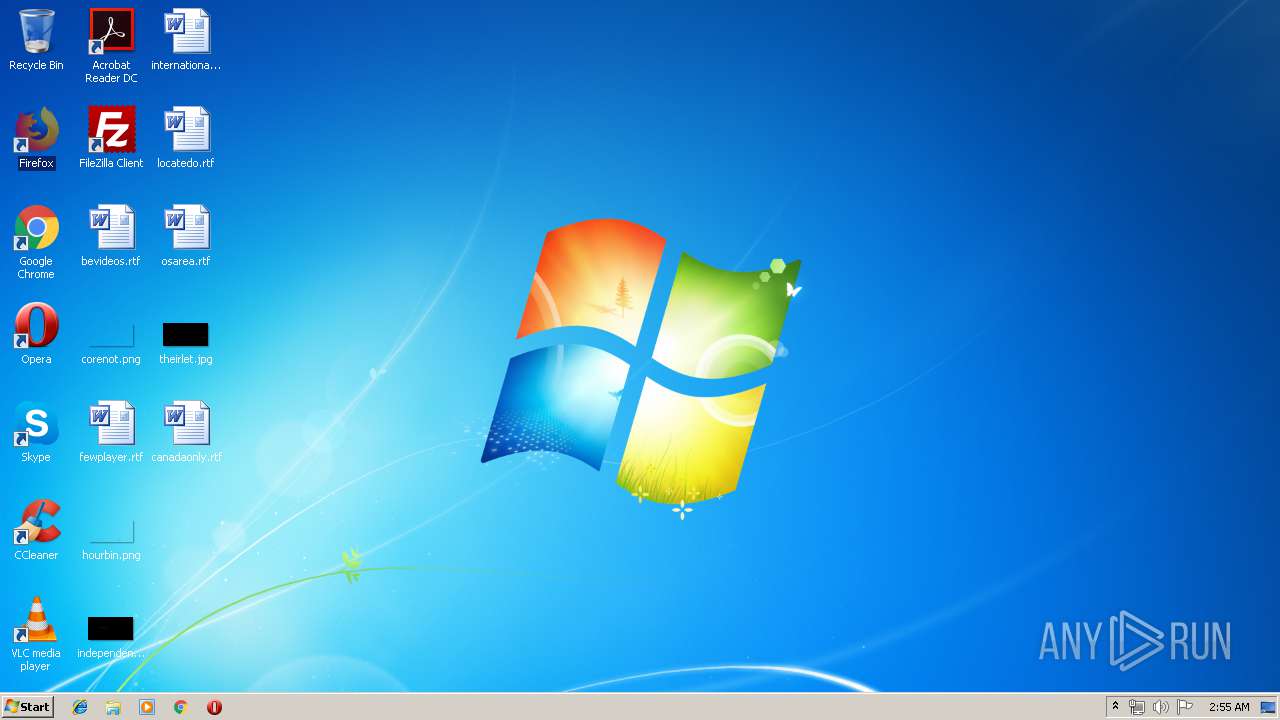
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 765DA31F20FE265BFAAD52A8B7783428 |
| SHA1: | 0D0407DB35F95D14428F4CF90003809A1A191CE1 |
| SHA256: | C2A178F24669726FB79E35B68E57F9511D10D616A9C3E27B359347A7442FB2C0 |
| SSDEEP: | 3072:xkrmco325w3UQCtcN//WhvYuz0arRbGqQFixQlE5p2:8g3fnEcN3WDz0aaVl3 |
MALICIOUS
FORMBOOK was detected
- explorer.exe (PID: 2036)
Changes the autorun value in the registry
- colorcpl.exe (PID: 2792)
Formbook was detected
- colorcpl.exe (PID: 2792)
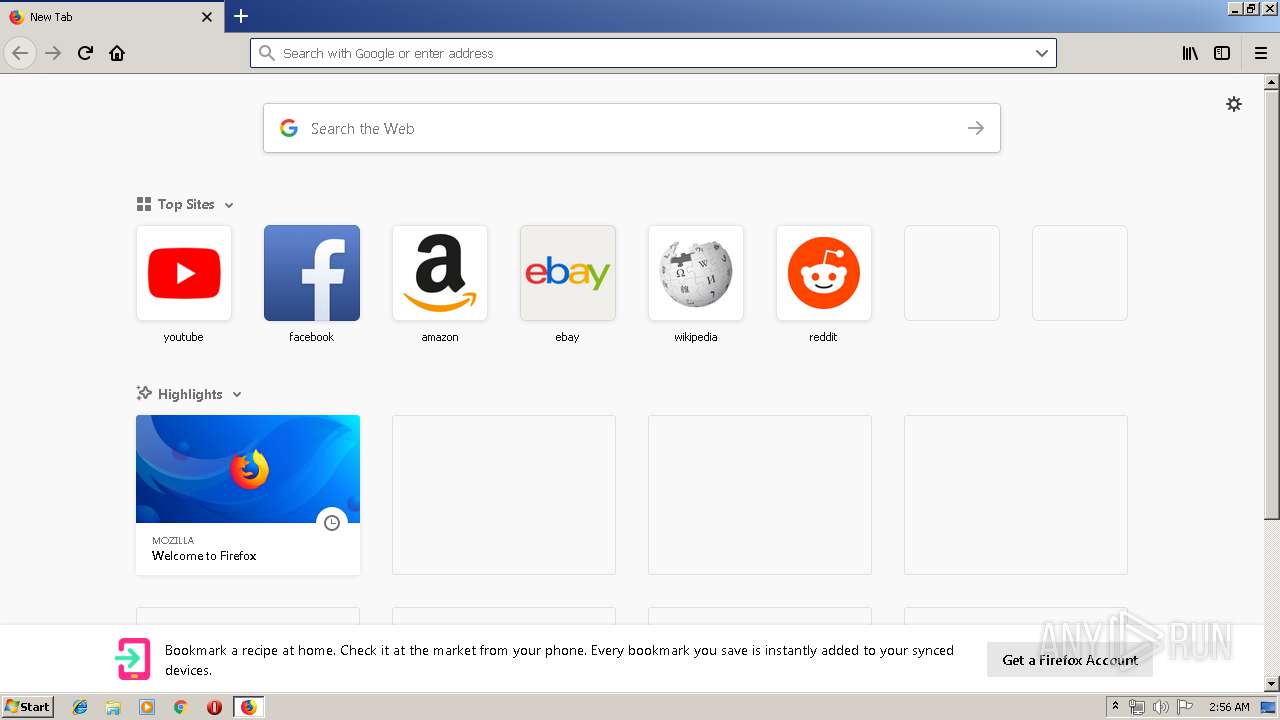
- Firefox.exe (PID: 2900)
Actions looks like stealing of personal data
- colorcpl.exe (PID: 2792)
Stealing of credential data
- colorcpl.exe (PID: 2792)
Connects to CnC server
- explorer.exe (PID: 2036)
SUSPICIOUS
Starts CMD.EXE for commands execution
- colorcpl.exe (PID: 2792)
Executable content was dropped or overwritten
- explorer.exe (PID: 2036)
- DllHost.exe (PID: 2944)
Creates files in the program directory
- DllHost.exe (PID: 2944)
Creates files in the user directory
- colorcpl.exe (PID: 2792)
Loads DLL from Mozilla Firefox
- colorcpl.exe (PID: 2792)
INFO
Adds / modifies Windows certificates
- pingsender.exe (PID: 2988)
- pingsender.exe (PID: 2572)
Creates files in the user directory
- Firefox.exe (PID: 2900)
- firefox.exe (PID: 2284)
Changes settings of System certificates
- pingsender.exe (PID: 2988)
- pingsender.exe (PID: 2572)
Reads CPU info
- firefox.exe (PID: 2284)
Application launched itself
- firefox.exe (PID: 2284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | DOS Executable Generic (100) |
|---|
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:10:23 05:49:35+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 166912 |
| InitializedDataSize: | - |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1b600 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Oct-2012 03:49:35 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x5245 |
| Pages in file: | 0x00E8 |
| Relocations: | 0x0000 |
| Size of header: | 0x5800 |
| Min extra paragraphs: | 0xE883 |
| Max extra paragraphs: | 0x8B09 |
| Initial SS value: | 0x83C8 |
| Initial SP value: | 0x3CC0 |
| Checksum: | 0x008B |
| Initial IP value: | 0xC103 |
| Initial CS value: | 0xC083 |
| Overlay number: | 0xFF08 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 1 |
| Time date stamp: | 23-Oct-2012 03:49:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00028B2C | 0x00028C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.4215 |
Total processes
51
Monitored processes
16
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 948 | "C:\Windows\System32\autofmt.exe" | C:\Windows\System32\autofmt.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Auto File System Format Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2284.13.4268121\1795805723" -childID 2 -isForBrowser -prefsHandle 2492 -prefMapHandle 2500 -prefsLen 216 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2284 "\\.\pipe\gecko-crash-server-pipe.2284" 2556 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 1208 | "C:\Windows\System32\wuapp.exe" | C:\Windows\System32\wuapp.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Application Launcher Exit code: 0 Version: 7.5.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1928 | "C:\Users\admin\AppData\Local\Temp\sureboy.exe" | C:\Users\admin\AppData\Local\Temp\sureboy.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2036 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/6d7d0121-3a61-40be-b0c0-b3dc041fc7e7/main/Firefox/65.0.2/release/20190225143501?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\6d7d0121-3a61-40be-b0c0-b3dc041fc7e7 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2792 | "C:\Windows\System32\colorcpl.exe" | C:\Windows\System32\colorcpl.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Color Control Panel Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2900 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | colorcpl.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2944 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
462
Read events
413
Write events
45
Delete events
4
Modification events
| (PID) Process: | (2792) colorcpl.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | E2XLGT2XCHL |
Value: C:\Program Files\Isxlttx\systraysx44an.exe | |||
| (PID) Process: | (2036) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | 308046O0NS4N39PO |
Value: 000000000200000001000000E3160000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF00AF0B6B2EF3D40100000000 | |||
| (PID) Process: | (2036) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000500000003000000838100000200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F020200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F020200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F02 | |||
| (PID) Process: | (2036) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | P:\Hfref\Choyvp\Qrfxgbc\Sversbk.yax |
Value: 00000000020000000000000001000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF00AF0B6B2EF3D40100000000 | |||
| (PID) Process: | (2036) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000400000000000000030000000200000000000000020000007B00300031003300390044003400340045002D0036004100460045002D0034003900460032002D0038003600390030002D003300440041004600430041004500360046004600420038007D005C004100630063006500730073006F0072006900650073005C00530079007300740065006D00200054006F006F006C0073005C005400610073006B0020005300630068006500640075006C00650072002E006C006E006B0000006C006E006B0000008006EDE0177749713800FEFFFFFFE72F1B77822E1B77B8F944763302000086000000B5B9A3710000000008E1F00520661400F8671400D891FE05987D1400AC3600378CD6800648DE800654F98006EDE01777497138000000000030D78006399C26762062D802800200008000000031000000A064D8022062D80254D78006DE9C26762062D80200000000B102000008000000B90200005CD78006330200001862D80284D78006431945764B64D802489F1D00860000001862D8022094FE0533020000B8F94476541E0000C8B0D102A0D7800633AB1B77C880C7C6000C00001027000012000000AC540200D4D78006F8AA1B77AC540200C8B0D102F4D78006B0B7DE0274D8800600000000A301000034D8000036B9AABFE4D780068291457634D88006E8D7800627954576000000003CBCDE0210D88006CD9445763CBCDE02BCD88006B0B7DE02E194457600000000B0B7DE02BCD8800618D880060200000000000000020000007B00300031003300390044003400340045002D0036004100460045002D0034003900460032002D0038003600390030002D003300440041004600430041004500360046004600420038007D005C004100630063006500730073006F0072006900650073005C00530079007300740065006D00200054006F006F006C0073005C005400610073006B0020005300630068006500640075006C00650072002E006C006E006B0000006C006E006B0000008006EDE0177749713800FEFFFFFFE72F1B77822E1B77B8F944763302000086000000B5B9A3710000000008E1F00520661400F8671400D891FE05987D1400AC3600378CD6800648DE800654F98006EDE01777497138000000000030D78006399C26762062D802800200008000000031000000A064D8022062D80254D78006DE9C26762062D80200000000B102000008000000B90200005CD78006330200001862D80284D78006431945764B64D802489F1D00860000001862D8022094FE0533020000B8F94476541E0000C8B0D102A0D7800633AB1B77C880C7C6000C00001027000012000000AC540200D4D78006F8AA1B77AC540200C8B0D102F4D78006B0B7DE0274D8800600000000A301000034D8000036B9AABFE4D780068291457634D88006E8D7800627954576000000003CBCDE0210D88006CD9445763CBCDE02BCD88006B0B7DE02E194457600000000B0B7DE02BCD8800618D880060200000000000000020000007B00300031003300390044003400340045002D0036004100460045002D0034003900460032002D0038003600390030002D003300440041004600430041004500360046004600420038007D005C004100630063006500730073006F0072006900650073005C00530079007300740065006D00200054006F006F006C0073005C005400610073006B0020005300630068006500640075006C00650072002E006C006E006B0000006C006E006B0000008006EDE0177749713800FEFFFFFFE72F1B77822E1B77B8F944763302000086000000B5B9A3710000000008E1F00520661400F8671400D891FE05987D1400AC3600378CD6800648DE800654F98006EDE01777497138000000000030D78006399C26762062D802800200008000000031000000A064D8022062D80254D78006DE9C26762062D80200000000B102000008000000B90200005CD78006330200001862D80284D78006431945764B64D802489F1D00860000001862D8022094FE0533020000B8F94476541E0000C8B0D102A0D7800633AB1B77C880C7C6000C00001027000012000000AC540200D4D78006F8AA1B77AC540200C8B0D102F4D78006B0B7DE0274D8800600000000A301000034D8000036B9AABFE4D780068291457634D88006E8D7800627954576000000003CBCDE0210D88006CD9445763CBCDE02BCD88006B0B7DE02E194457600000000B0B7DE02BCD8800618D88006 | |||
| (PID) Process: | (2036) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | P:\Hfref\Choyvp\Qrfxgbc\Sversbk.yax |
Value: 00000000020000000000000002000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF00AF0B6B2EF3D40100000000 | |||
| (PID) Process: | (2036) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000400000000000000040000000200000000000000020000007B00300031003300390044003400340045002D0036004100460045002D0034003900460032002D0038003600390030002D003300440041004600430041004500360046004600420038007D005C004100630063006500730073006F0072006900650073005C00530079007300740065006D00200054006F006F006C0073005C005400610073006B0020005300630068006500640075006C00650072002E006C006E006B0000006C006E006B0000008006EDE0177749713800FEFFFFFFE72F1B77822E1B77B8F944763302000086000000B5B9A3710000000008E1F00520661400F8671400D891FE05987D1400AC3600378CD6800648DE800654F98006EDE01777497138000000000030D78006399C26762062D802800200008000000031000000A064D8022062D80254D78006DE9C26762062D80200000000B102000008000000B90200005CD78006330200001862D80284D78006431945764B64D802489F1D00860000001862D8022094FE0533020000B8F94476541E0000C8B0D102A0D7800633AB1B77C880C7C6000C00001027000012000000AC540200D4D78006F8AA1B77AC540200C8B0D102F4D78006B0B7DE0274D8800600000000A301000034D8000036B9AABFE4D780068291457634D88006E8D7800627954576000000003CBCDE0210D88006CD9445763CBCDE02BCD88006B0B7DE02E194457600000000B0B7DE02BCD8800618D880060200000000000000020000007B00300031003300390044003400340045002D0036004100460045002D0034003900460032002D0038003600390030002D003300440041004600430041004500360046004600420038007D005C004100630063006500730073006F0072006900650073005C00530079007300740065006D00200054006F006F006C0073005C005400610073006B0020005300630068006500640075006C00650072002E006C006E006B0000006C006E006B0000008006EDE0177749713800FEFFFFFFE72F1B77822E1B77B8F944763302000086000000B5B9A3710000000008E1F00520661400F8671400D891FE05987D1400AC3600378CD6800648DE800654F98006EDE01777497138000000000030D78006399C26762062D802800200008000000031000000A064D8022062D80254D78006DE9C26762062D80200000000B102000008000000B90200005CD78006330200001862D80284D78006431945764B64D802489F1D00860000001862D8022094FE0533020000B8F94476541E0000C8B0D102A0D7800633AB1B77C880C7C6000C00001027000012000000AC540200D4D78006F8AA1B77AC540200C8B0D102F4D78006B0B7DE0274D8800600000000A301000034D8000036B9AABFE4D780068291457634D88006E8D7800627954576000000003CBCDE0210D88006CD9445763CBCDE02BCD88006B0B7DE02E194457600000000B0B7DE02BCD8800618D880060200000000000000020000007B00300031003300390044003400340045002D0036004100460045002D0034003900460032002D0038003600390030002D003300440041004600430041004500360046004600420038007D005C004100630063006500730073006F0072006900650073005C00530079007300740065006D00200054006F006F006C0073005C005400610073006B0020005300630068006500640075006C00650072002E006C006E006B0000006C006E006B0000008006EDE0177749713800FEFFFFFFE72F1B77822E1B77B8F944763302000086000000B5B9A3710000000008E1F00520661400F8671400D891FE05987D1400AC3600378CD6800648DE800654F98006EDE01777497138000000000030D78006399C26762062D802800200008000000031000000A064D8022062D80254D78006DE9C26762062D80200000000B102000008000000B90200005CD78006330200001862D80284D78006431945764B64D802489F1D00860000001862D8022094FE0533020000B8F94476541E0000C8B0D102A0D7800633AB1B77C880C7C6000C00001027000012000000AC540200D4D78006F8AA1B77AC540200C8B0D102F4D78006B0B7DE0274D8800600000000A301000034D8000036B9AABFE4D780068291457634D88006E8D7800627954576000000003CBCDE0210D88006CD9445763CBCDE02BCD88006B0B7DE02E194457600000000B0B7DE02BCD8800618D88006 | |||
| (PID) Process: | (2036) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | 308046O0NS4N39PO |
Value: 000000000200000002000000E3160000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF00AF0B6B2EF3D40100000000 | |||
| (PID) Process: | (2036) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000500000004000000838100000200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F020200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F020200000002000000724300004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000120200000000CC0B120200000000CC0B12020400050005001F02280C12020800050005001F026CE71F020100000154001F0200000100B8139D75444812020C0003000300000000000500280C12020000000005000000CC0B120201000000C8E91F02C0E91F0200000000C8FDDE02C0FCDE0244E71F023DA9457600000000FBFFFF7F68E71F02987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF00000000000000000000000035EE190651EE190635EE1906000000000000000000000000080000002E006C006E006B0000005300630068006500640075006C00650072002E006C006E006B00000014000000140050000000070000000200060026030200A5863C750800000064021400E72F1B77B5863C753F030000CC04140000001400A86D150011000000B8451700B045170005000000F8F3DD0270E80000F28635BB20E81F028291457670E81F0224E81F022795457600000000ECD2DD024CE81F02CD944576ECD2DD02F8E81F0260CEDD02E19445760000000060CEDD02F8E81F0254E81F02 | |||
| (PID) Process: | (2284) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
2
Suspicious files
116
Text files
24
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2284 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2284 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2284 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2284 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 2284 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 2284 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flash-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 2284 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flash-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 2284 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flashsubdoc-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 2284 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flashsubdoc-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 2284 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flash-digest256.pset | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
18
DNS requests
53
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2036 | explorer.exe | GET | 404 | 157.7.172.129:80 | http://www.tangesuzuki.com/h338/?lz=QkRVqT/f603FcOqBOMynXcNm+Z5deFoFTE1WWyCIeTylq53GCj1A/P5y1Dls8uY9czNXfQ==&Ul=Yv_0&sql=1 | JP | html | 322 b | malicious |
2036 | explorer.exe | POST | — | 157.7.172.129:80 | http://www.tangesuzuki.com/h338/ | JP | — | — | malicious |
2036 | explorer.exe | POST | — | 157.7.172.129:80 | http://www.tangesuzuki.com/h338/ | JP | — | — | malicious |
2036 | explorer.exe | POST | — | 157.7.172.129:80 | http://www.tangesuzuki.com/h338/ | JP | — | — | malicious |
2036 | explorer.exe | GET | 301 | 162.255.118.194:80 | http://www.polyfecta.com/h338/?lz=NGImbPPZXY+1hEuWhckrCR/Qy3CwNoy82plQduu6vXFRZbbygSyabxi6unfOfT2vVjgWLQ==&Ul=Yv_0 | US | html | 182 b | malicious |
2284 | firefox.exe | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2284 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2284 | firefox.exe | POST | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2284 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2036 | explorer.exe | 162.255.118.194:80 | www.polyfecta.com | Namecheap, Inc. | US | malicious |
2284 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
2036 | explorer.exe | 157.7.172.129:80 | www.tangesuzuki.com | GMO Internet,Inc | JP | malicious |
2284 | firefox.exe | 34.213.175.109:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2284 | firefox.exe | 52.35.250.5:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2284 | firefox.exe | 13.32.159.2:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
2284 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2284 | firefox.exe | 172.217.21.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2284 | firefox.exe | 52.24.56.107:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2572 | pingsender.exe | 54.68.141.132:443 | incoming.telemetry.mozilla.org | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.polyfecta.com |
| malicious |
www.allinonekitchenforyou.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
www.tangesuzuki.com |
| malicious |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2036 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
2036 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
2036 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
2036 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
4 ETPRO signatures available at the full report