| download: | /lordsasta/krnl-executor/releases/download/krnl/Release.rar |
| Full analysis: | https://app.any.run/tasks/d904daac-9b7f-421f-ab06-8765c8396428 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | December 13, 2024, 21:14:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
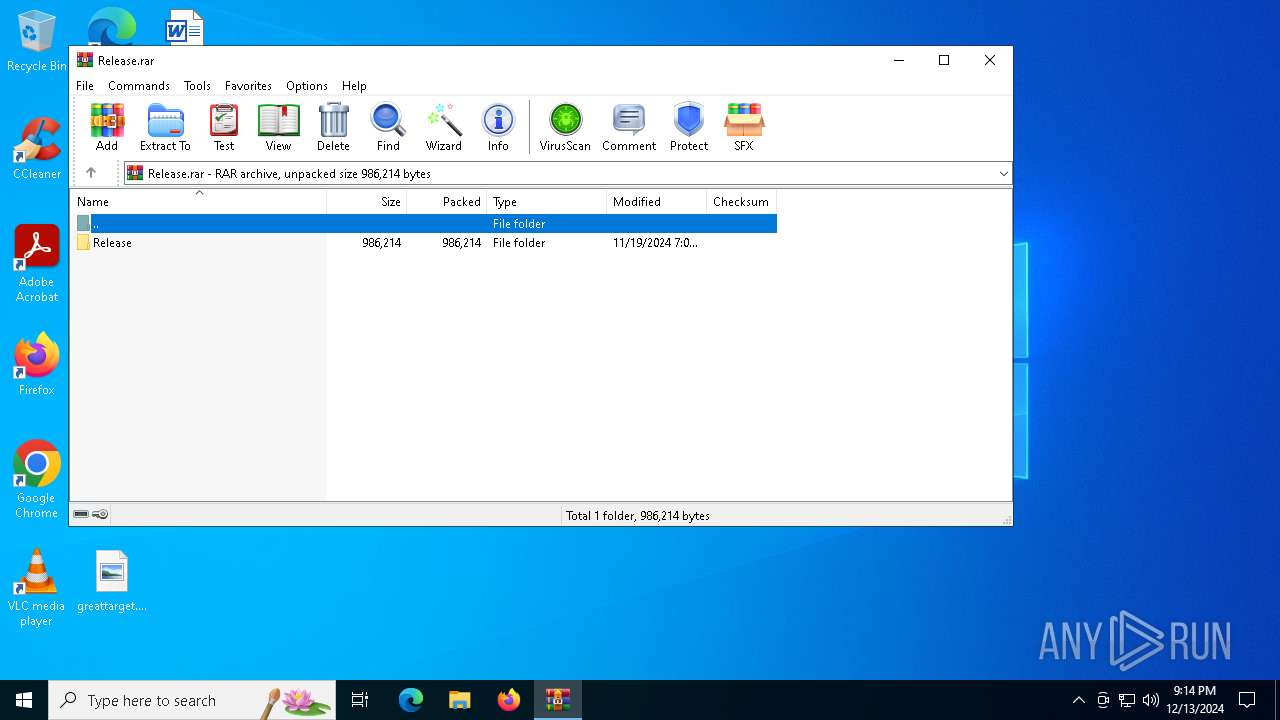
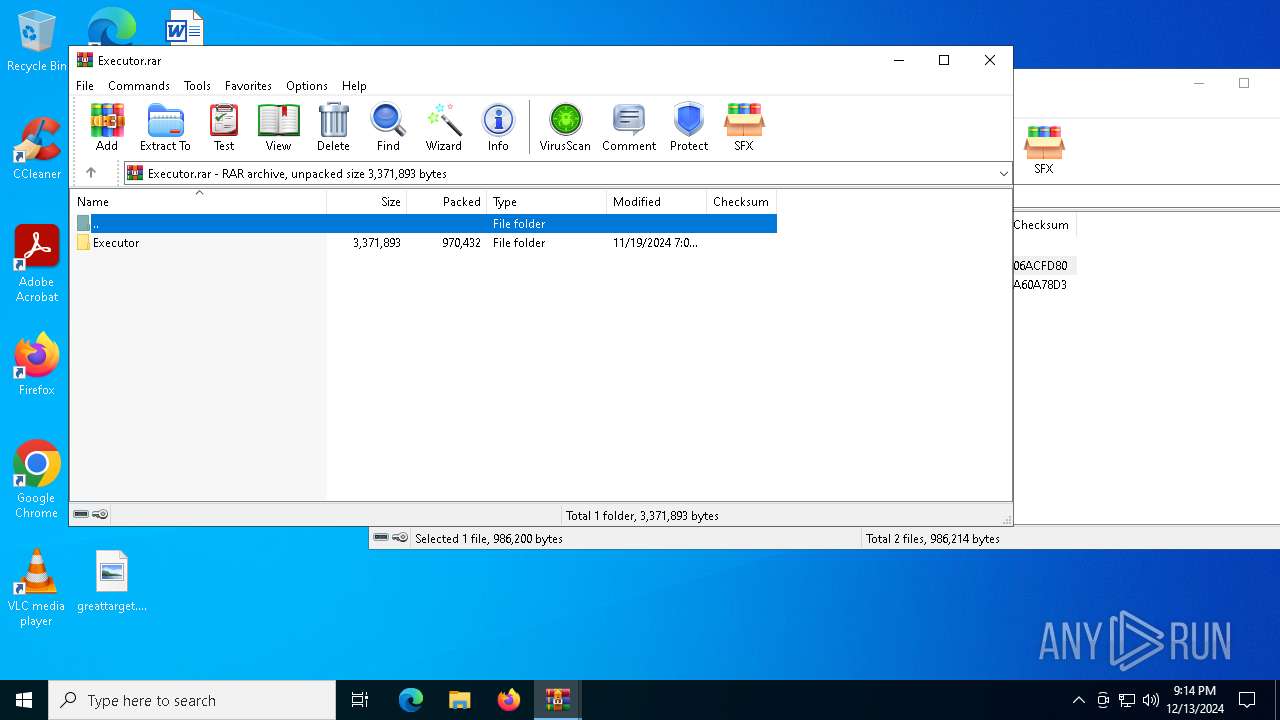
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | BC3158F149F55405909D1FA8BD94C006 |
| SHA1: | 25A016E4D45C5F402EB18A329B8DF45D09D81104 |
| SHA256: | C28E177F4A96A97F256B5919631A3AA1C2BD64E1EE193F9A47A8FA70DBB5FD8D |
| SSDEEP: | 49152:jlXiISg4XNIs4nM5MW4ik2Mk4/nkV8NKt74KSMrRr1QbWLSCzS4XKvEhKu6EAg9V:RXiN6dM5w8Mk4/na7u9yQKmCzqvEhKIp |
MALICIOUS
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
Connects to the CnC server
- svchost.exe (PID: 2192)
SUSPICIOUS
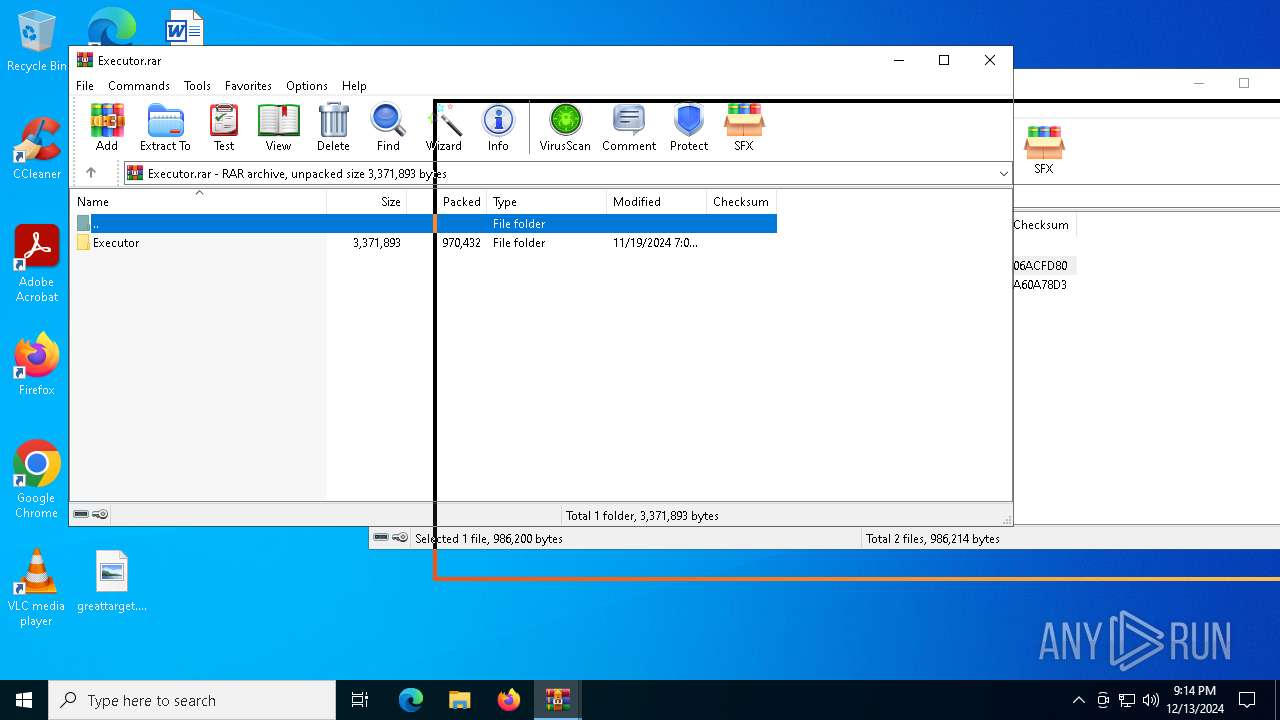
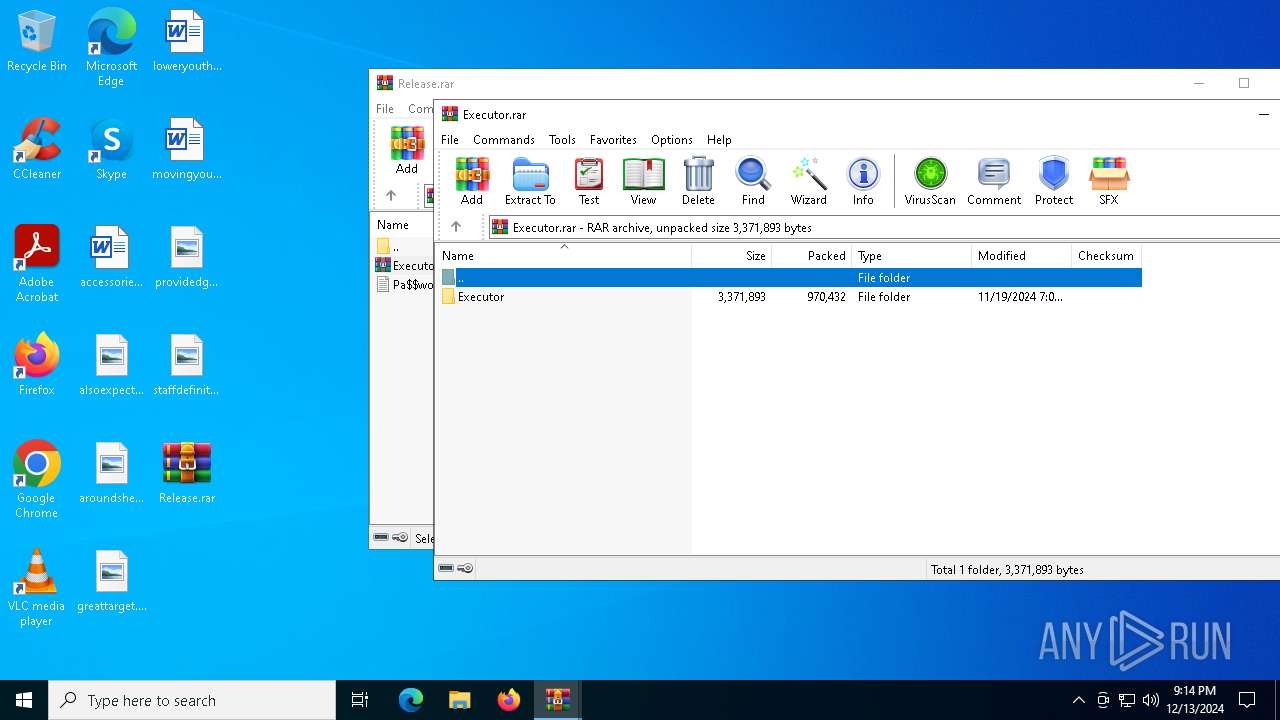
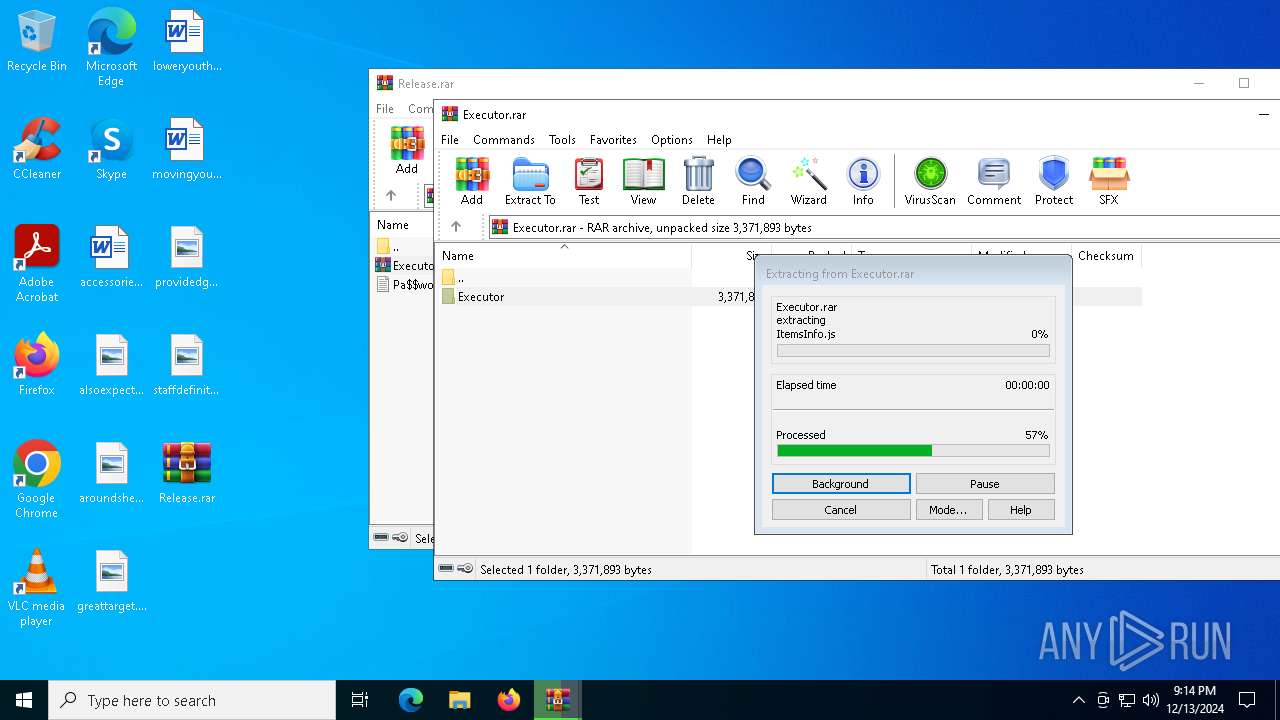
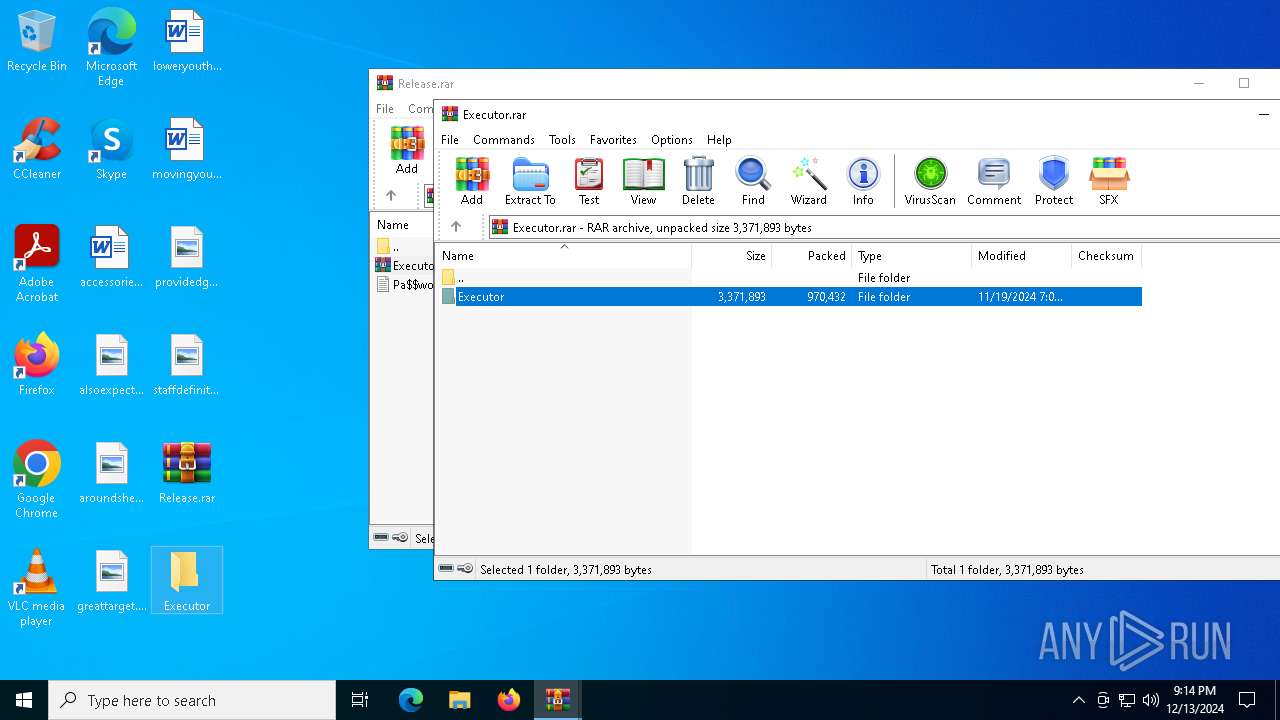
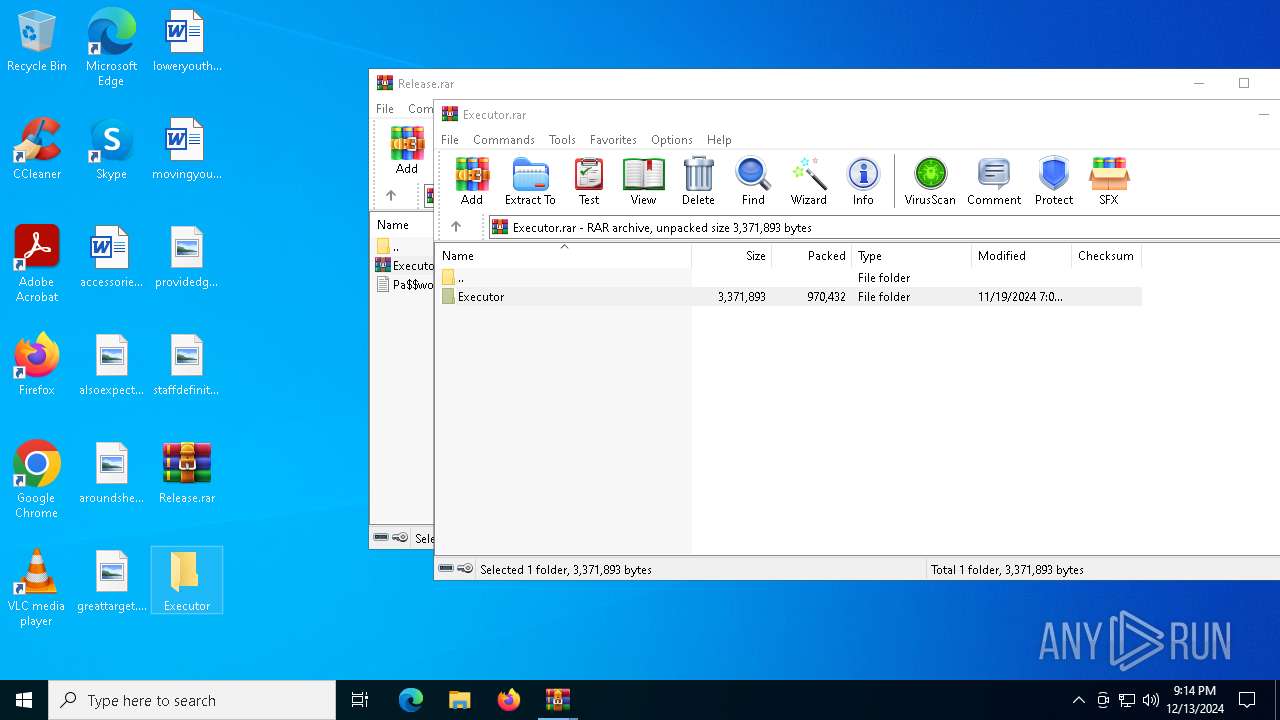
Generic archive extractor
- WinRAR.exe (PID: 5712)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5712)
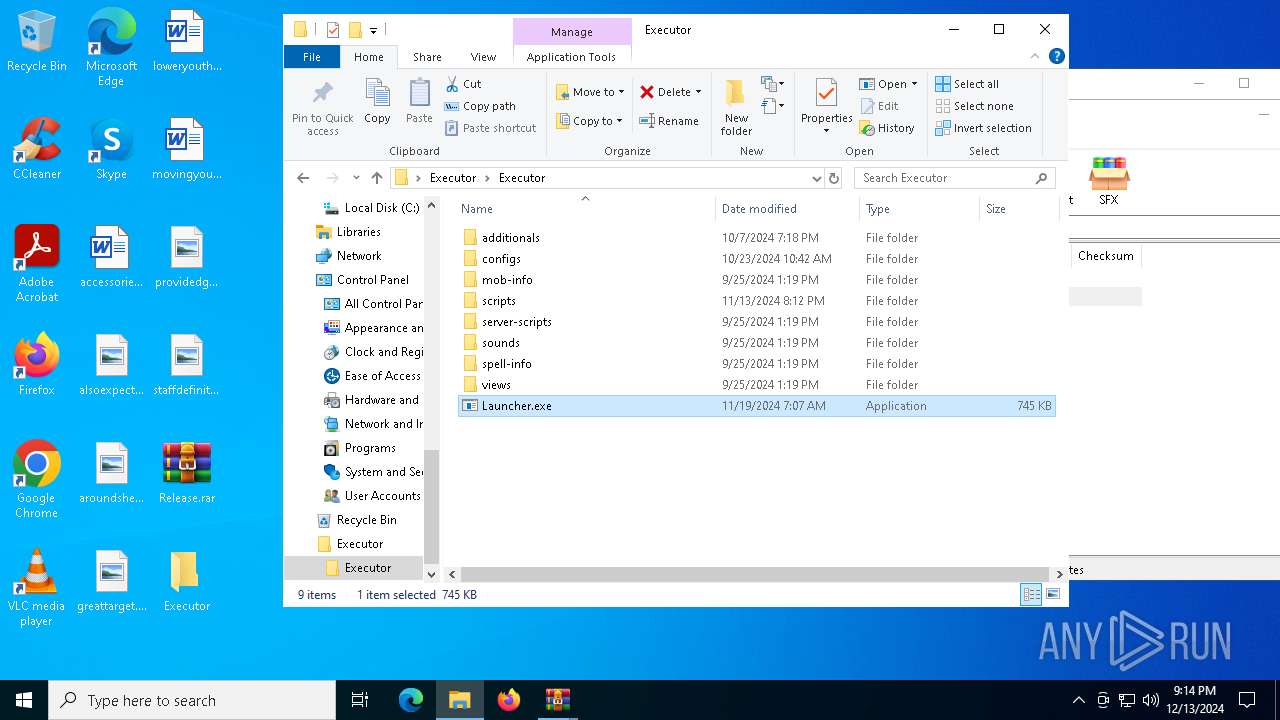
Application launched itself
- WinRAR.exe (PID: 5712)
- Launcher.exe (PID: 5300)
Executes application which crashes
- Launcher.exe (PID: 5300)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2192)
INFO
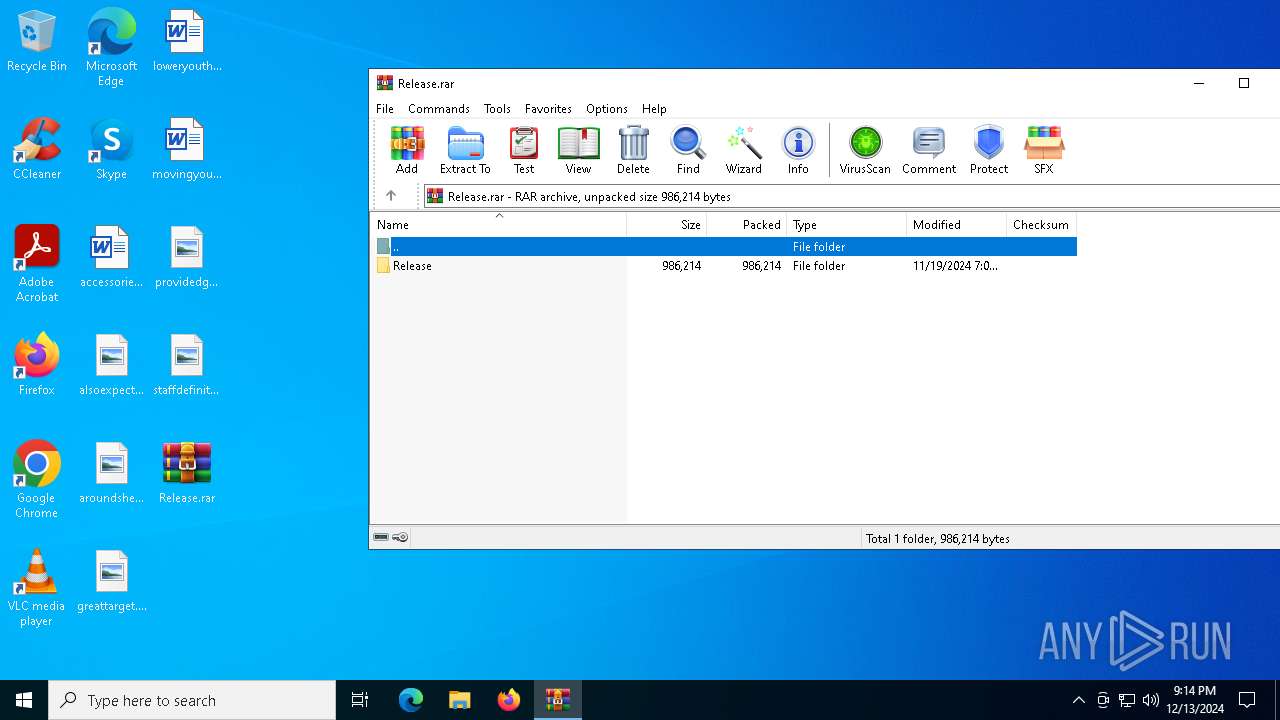
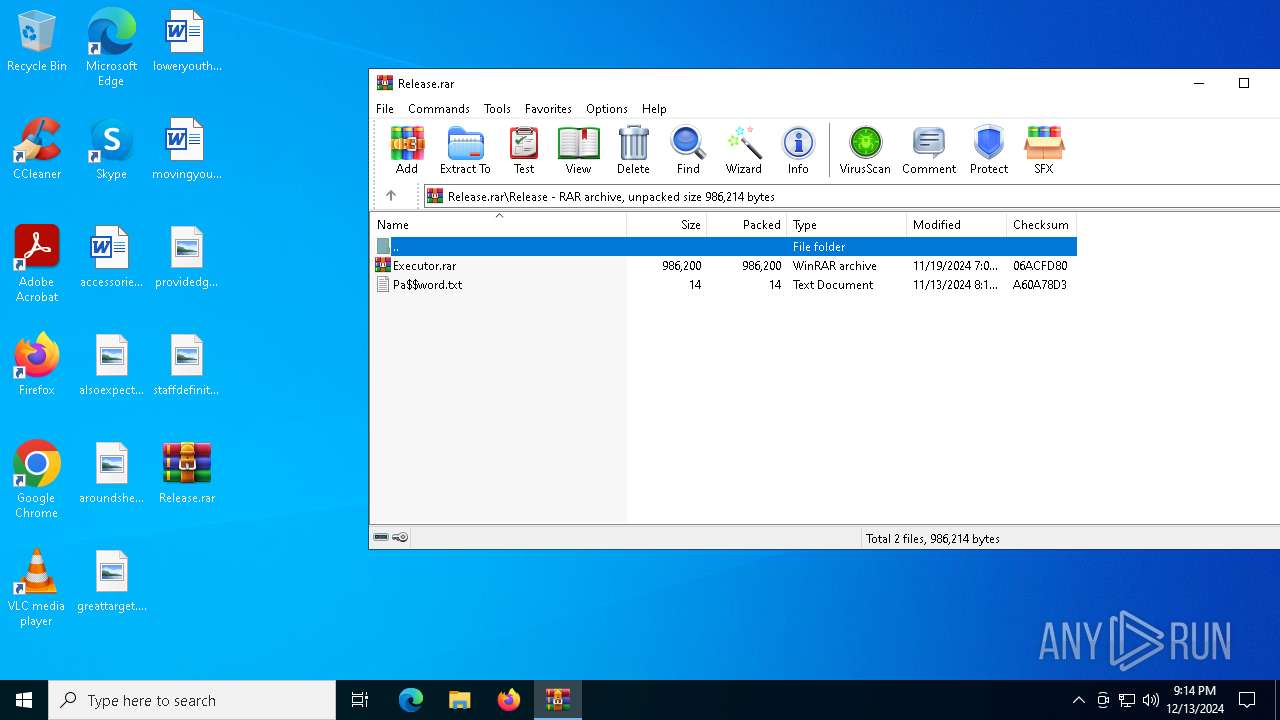
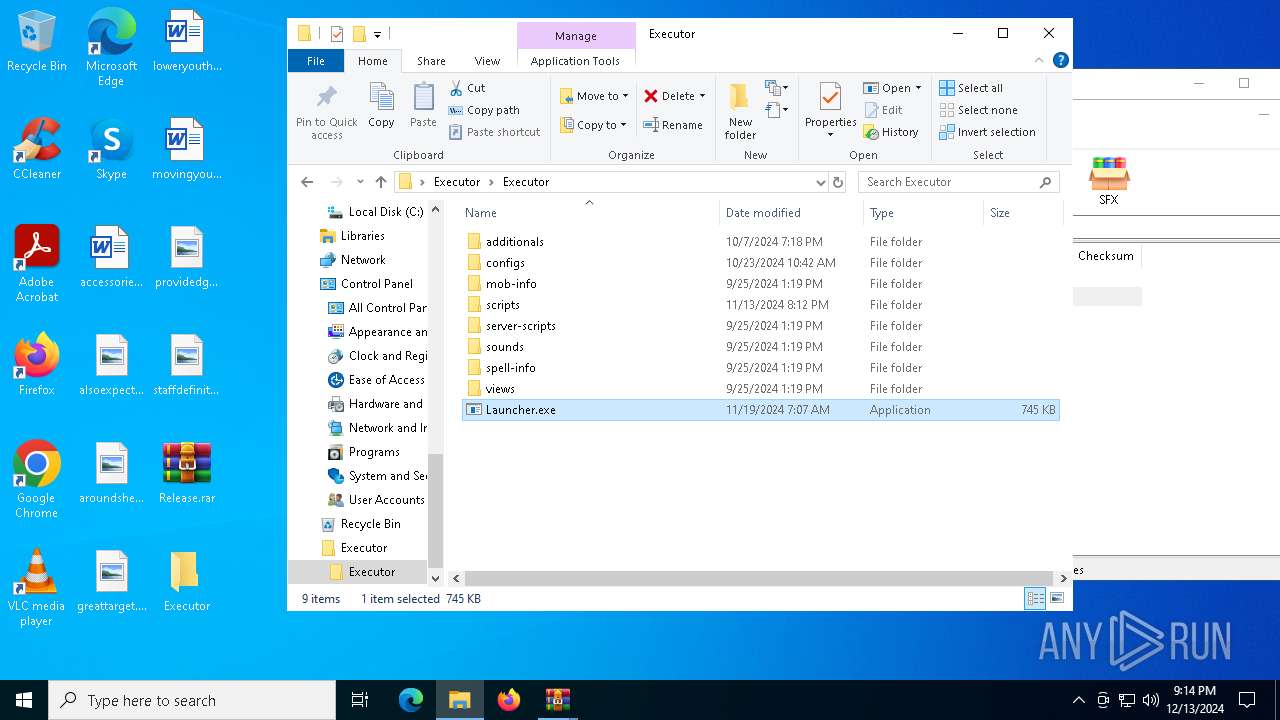
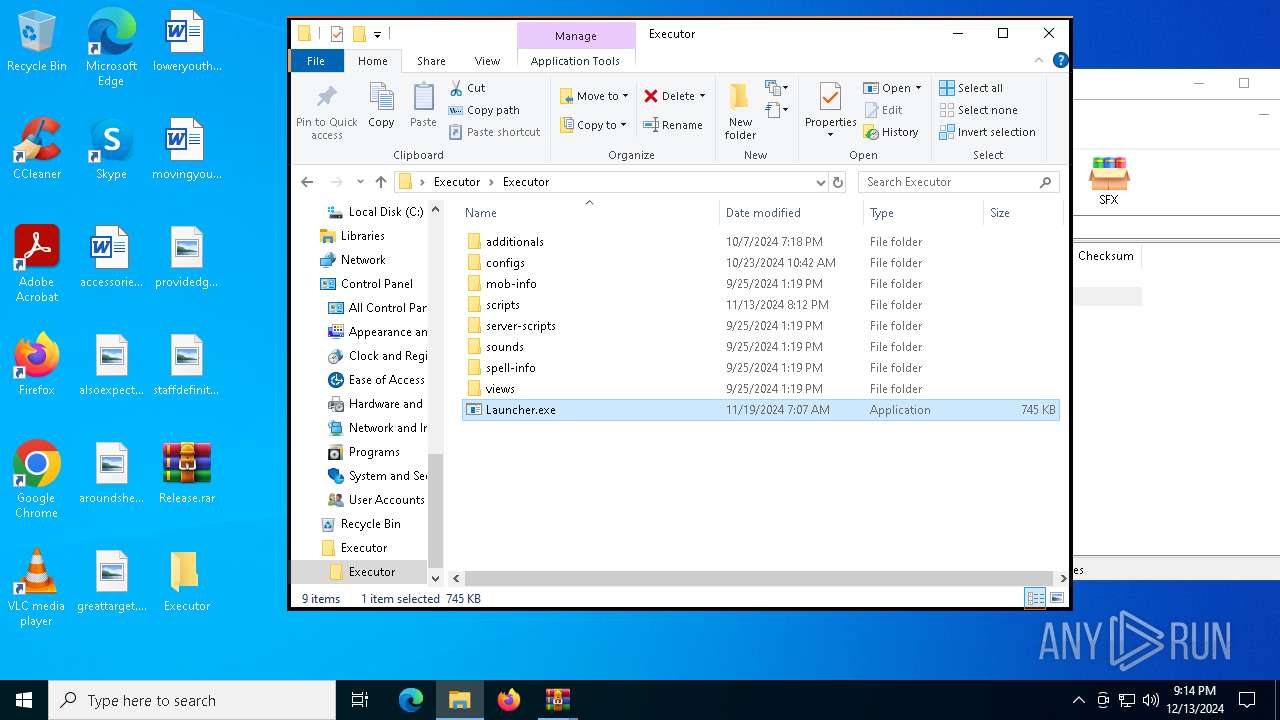
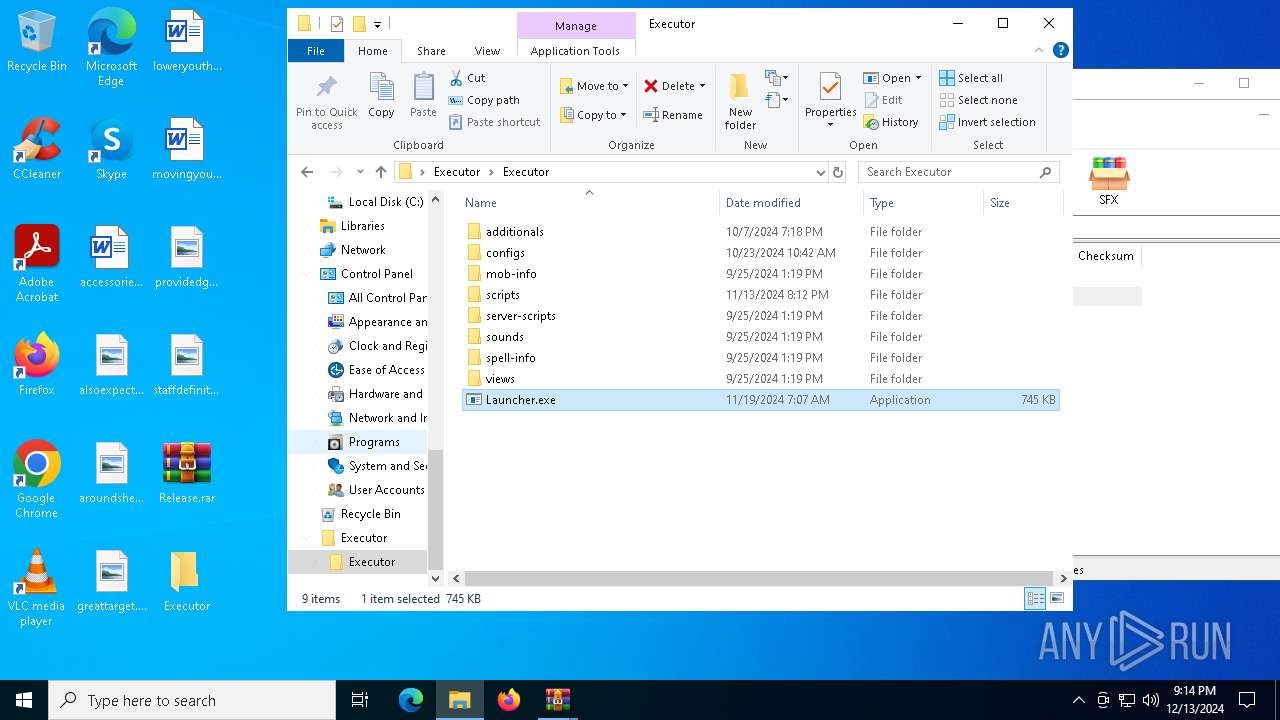
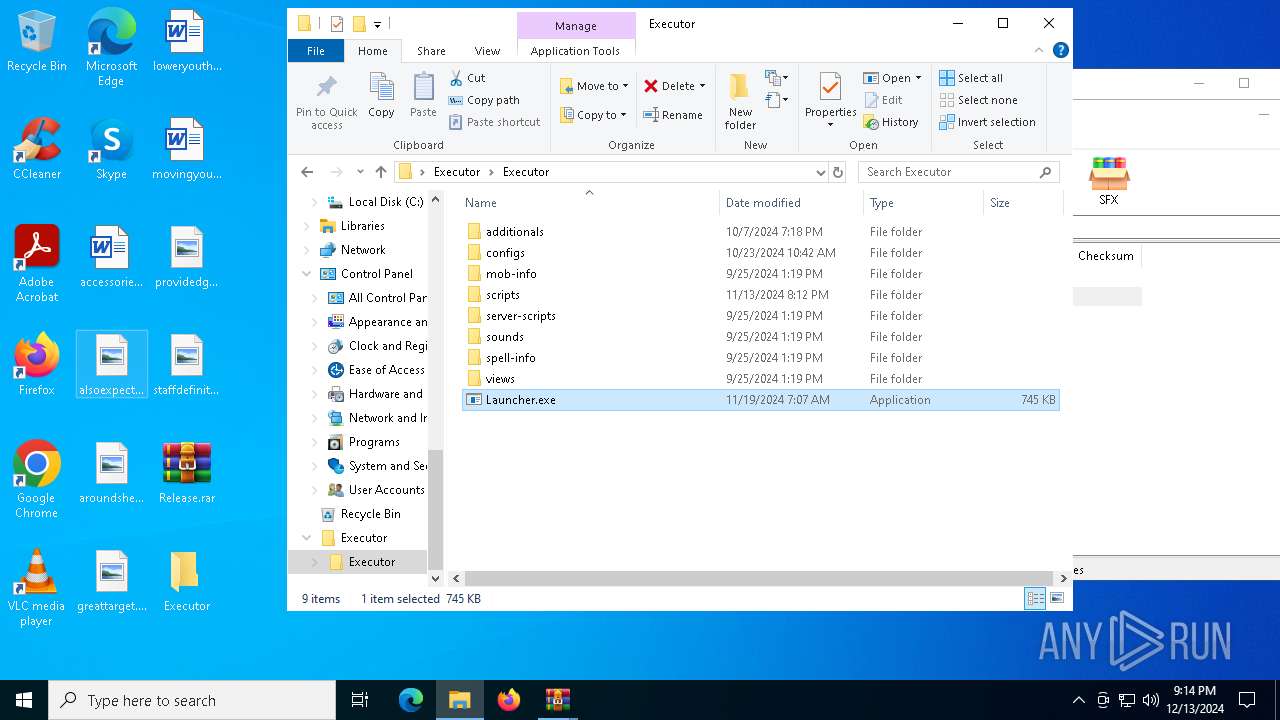
The process uses the downloaded file
- WinRAR.exe (PID: 6724)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6724)
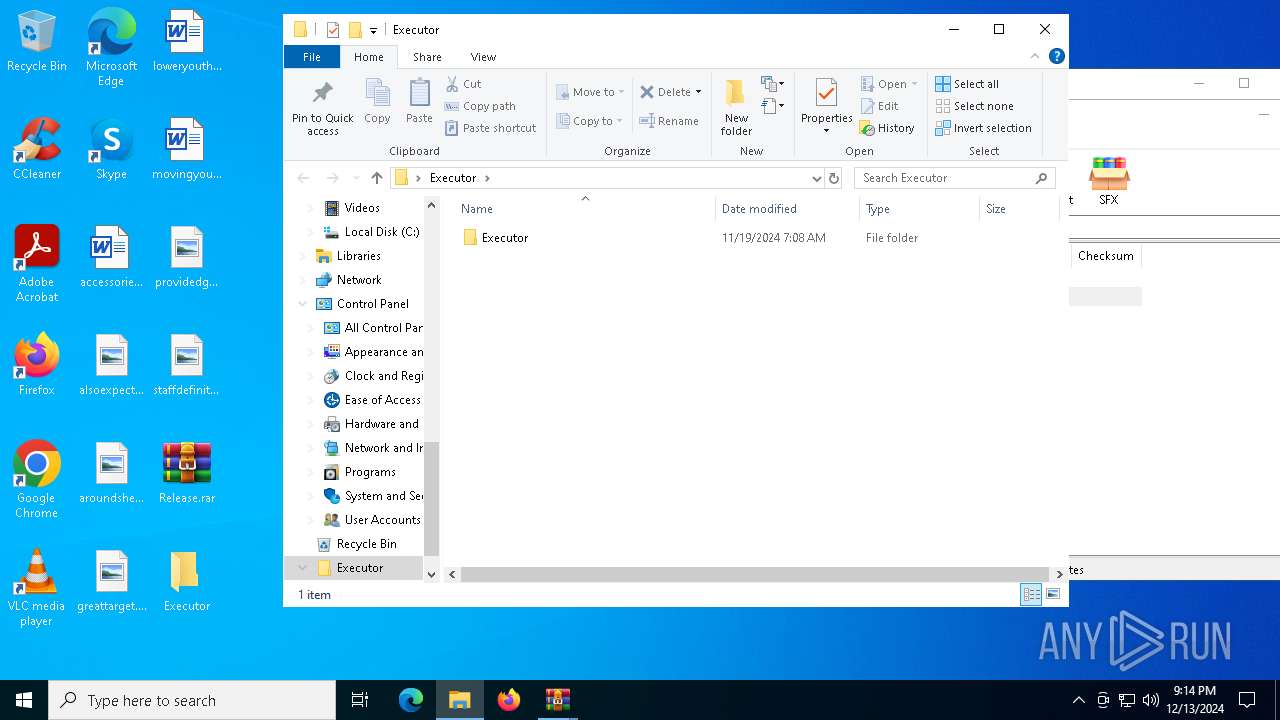
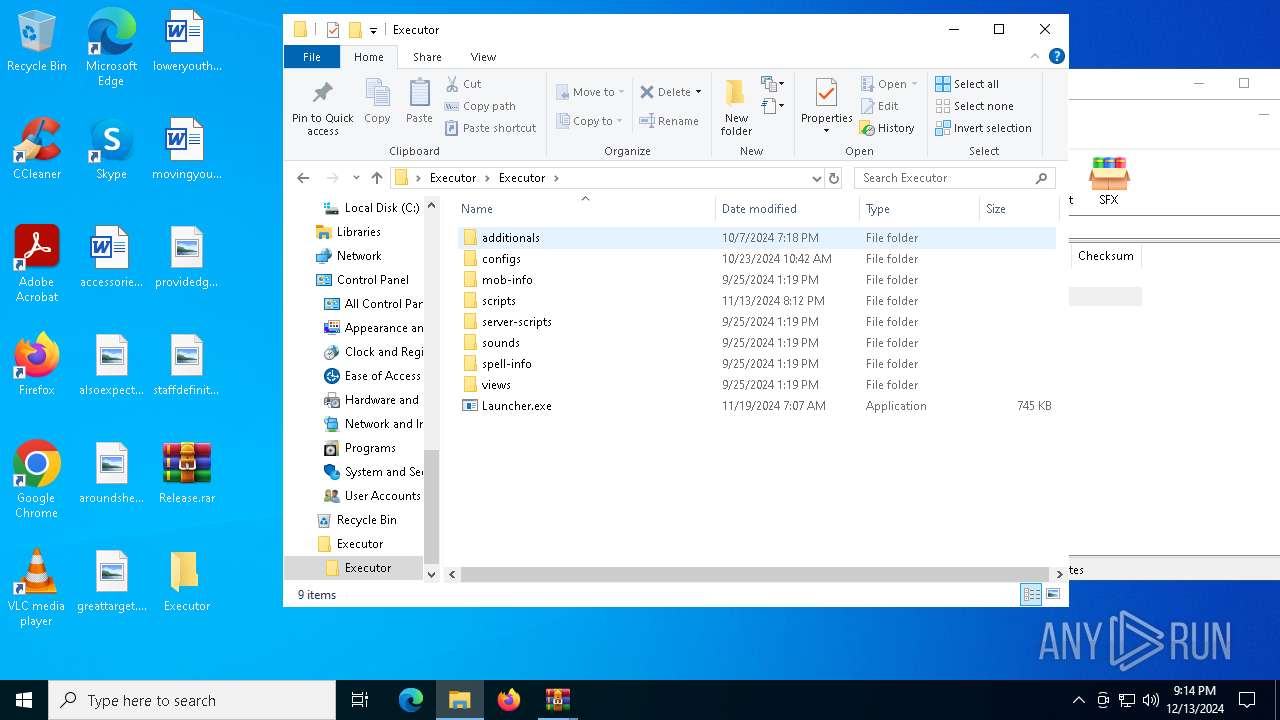
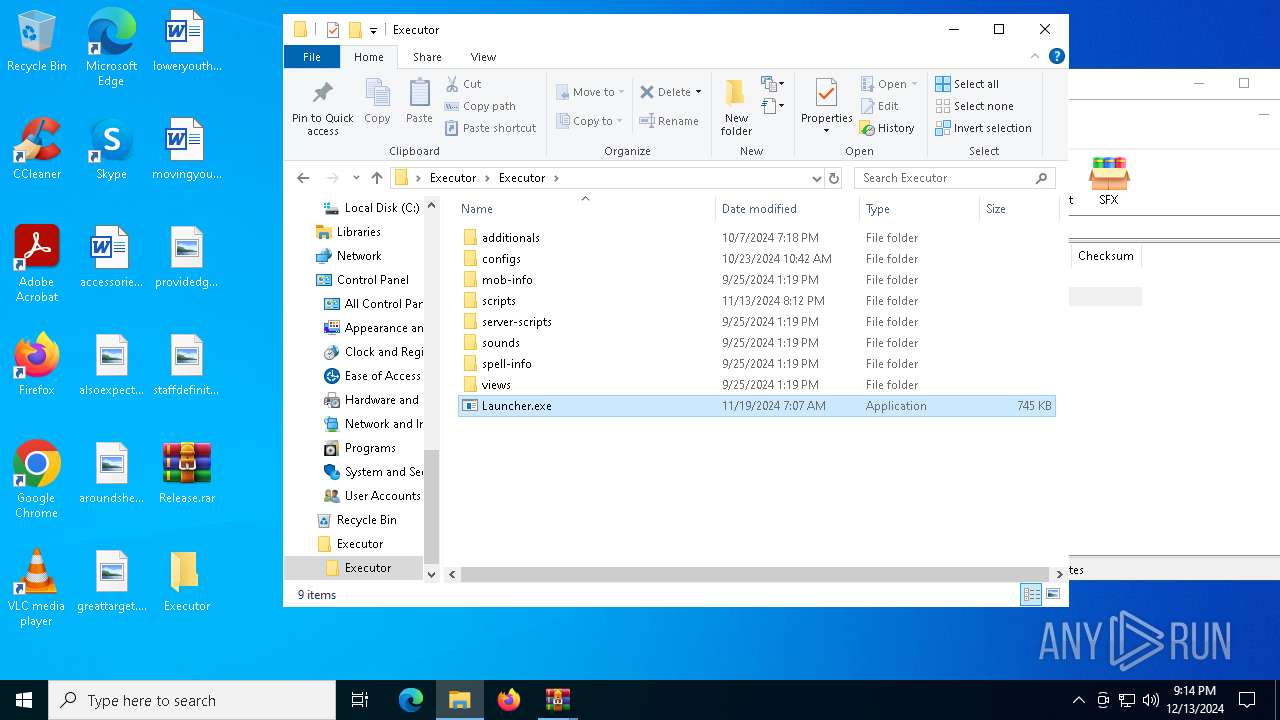
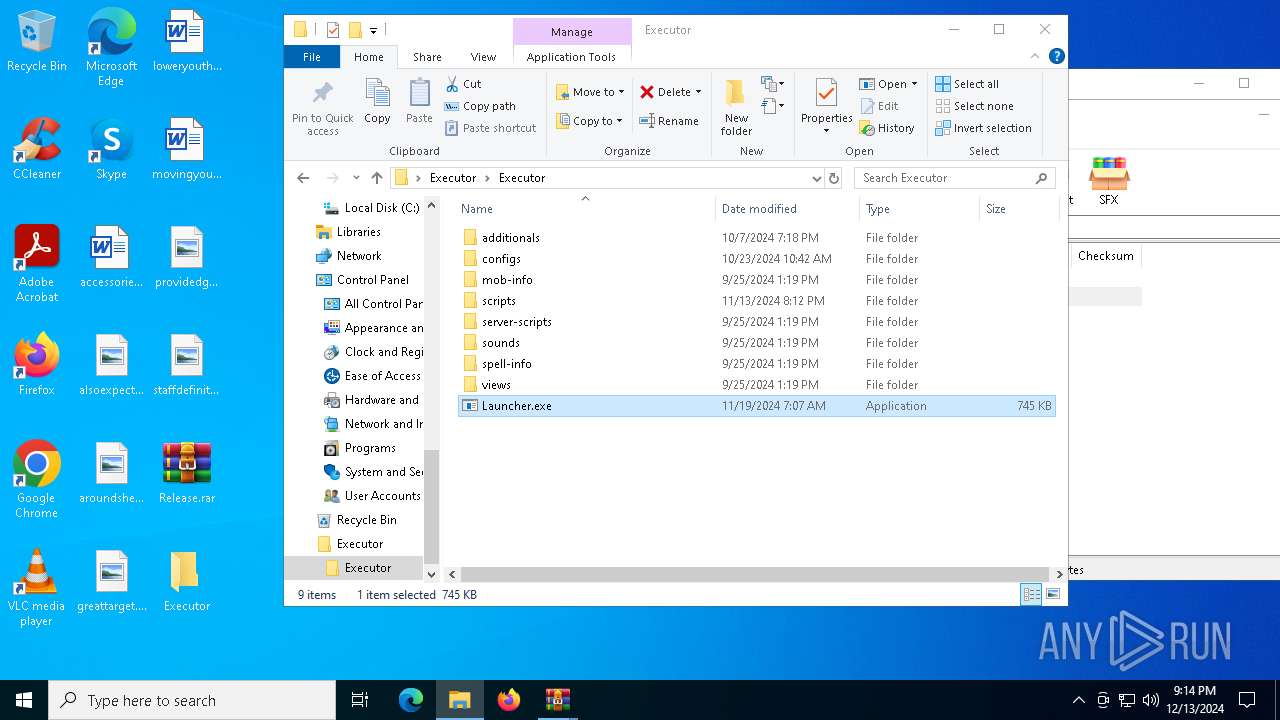
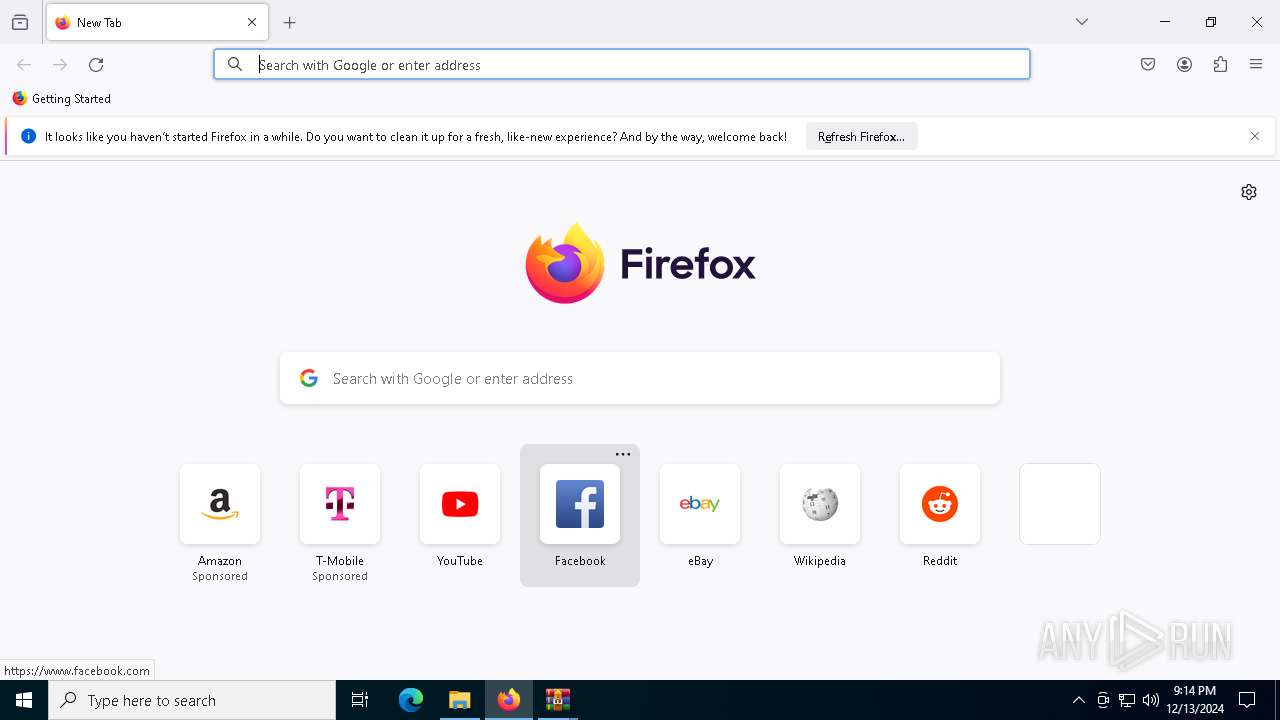
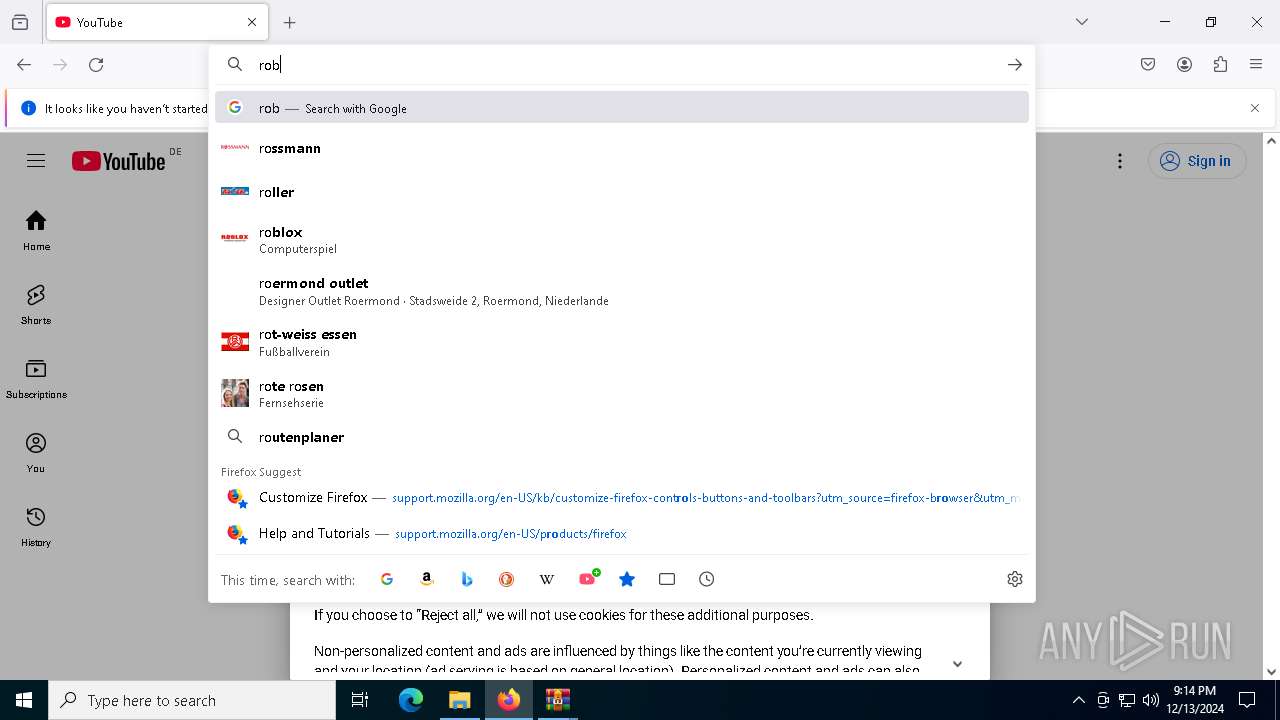
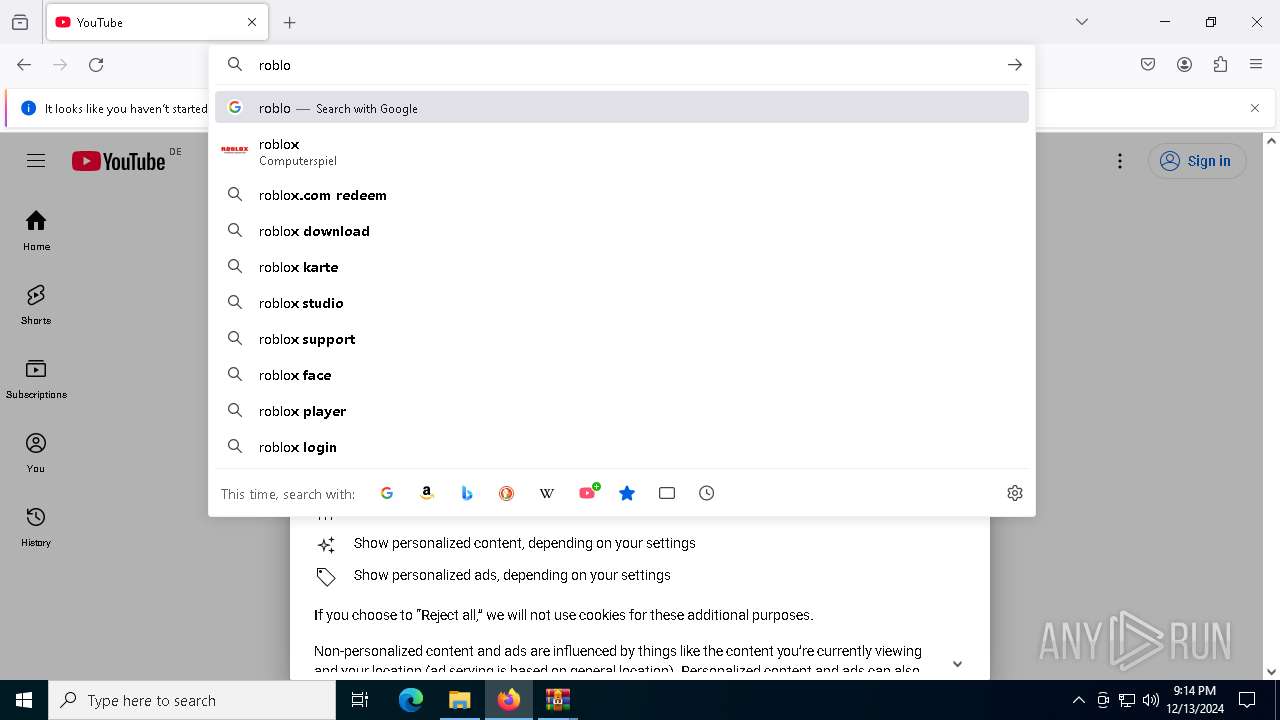
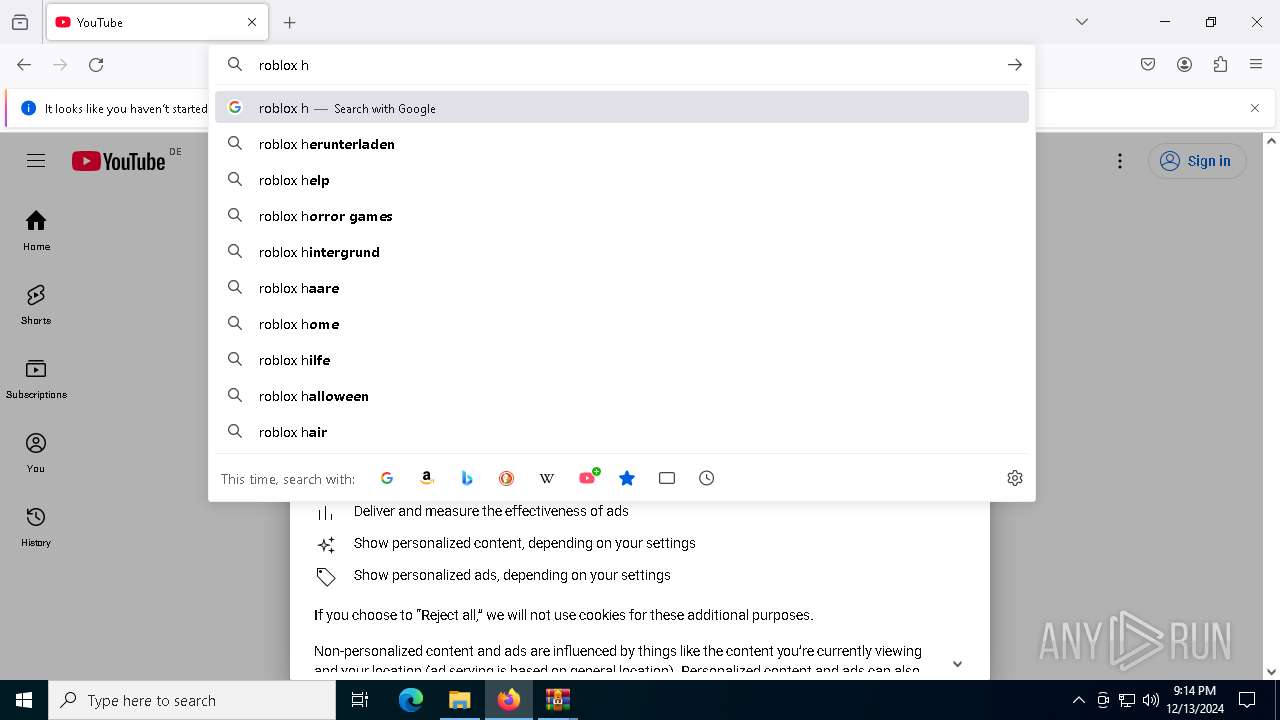
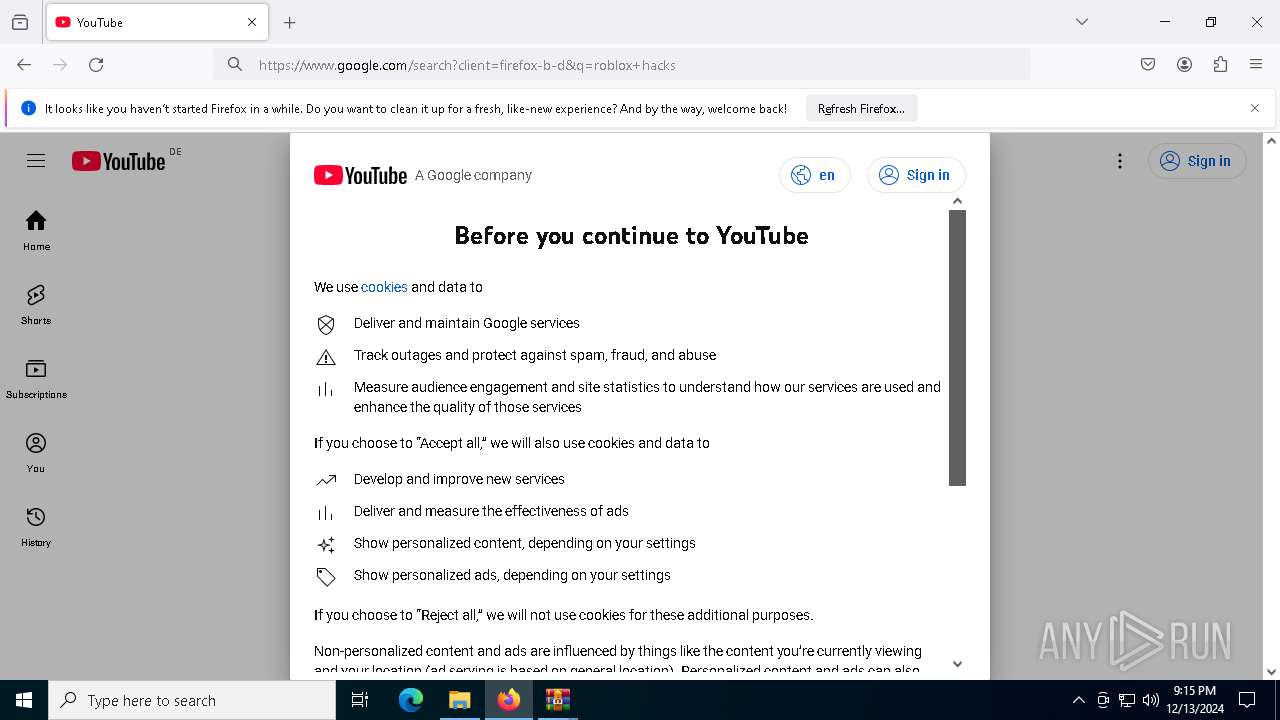
Manual execution by a user
- Launcher.exe (PID: 5300)
- firefox.exe (PID: 6664)
Checks supported languages
- Launcher.exe (PID: 4724)
- Launcher.exe (PID: 5300)
Reads the software policy settings
- Launcher.exe (PID: 4724)
- WerFault.exe (PID: 5740)
Checks proxy server information
- WerFault.exe (PID: 5740)
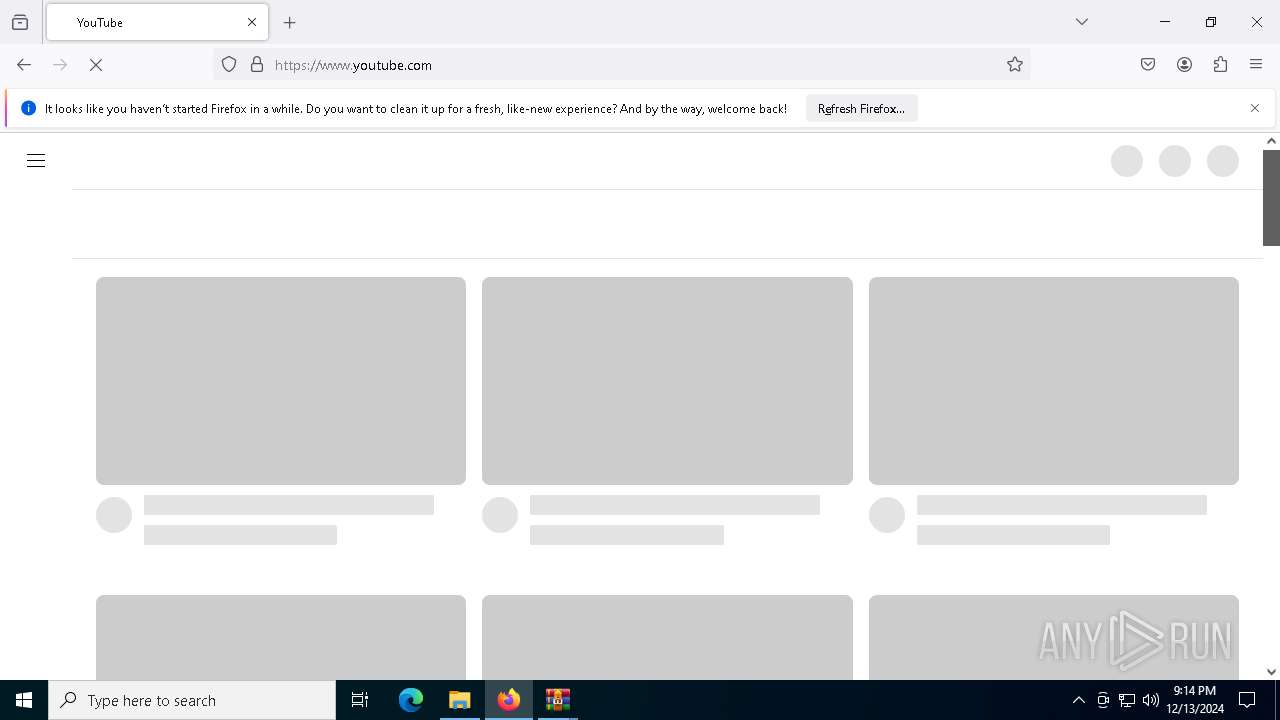
Application launched itself
- firefox.exe (PID: 6664)
- firefox.exe (PID: 6440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 986200 |
| UncompressedSize: | 986200 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | Release/Executor.rar |
Total processes
152
Monitored processes
24
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1912 -parentBuildID 20240213221259 -prefsHandle 1840 -prefMapHandle 1832 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {f8b71ba5-ae61-402e-b116-73f3eaf18c81} 6440 "\\.\pipe\gecko-crash-server-pipe.6440" 1becc7ec310 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3140 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
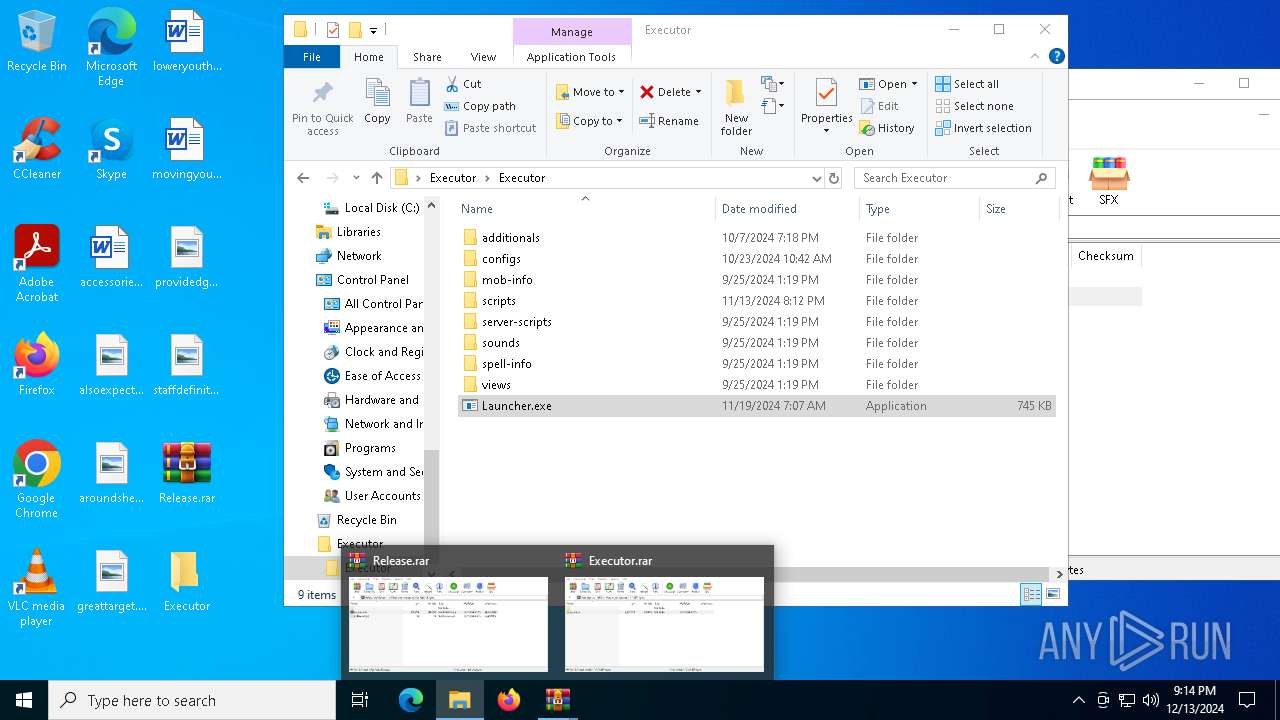
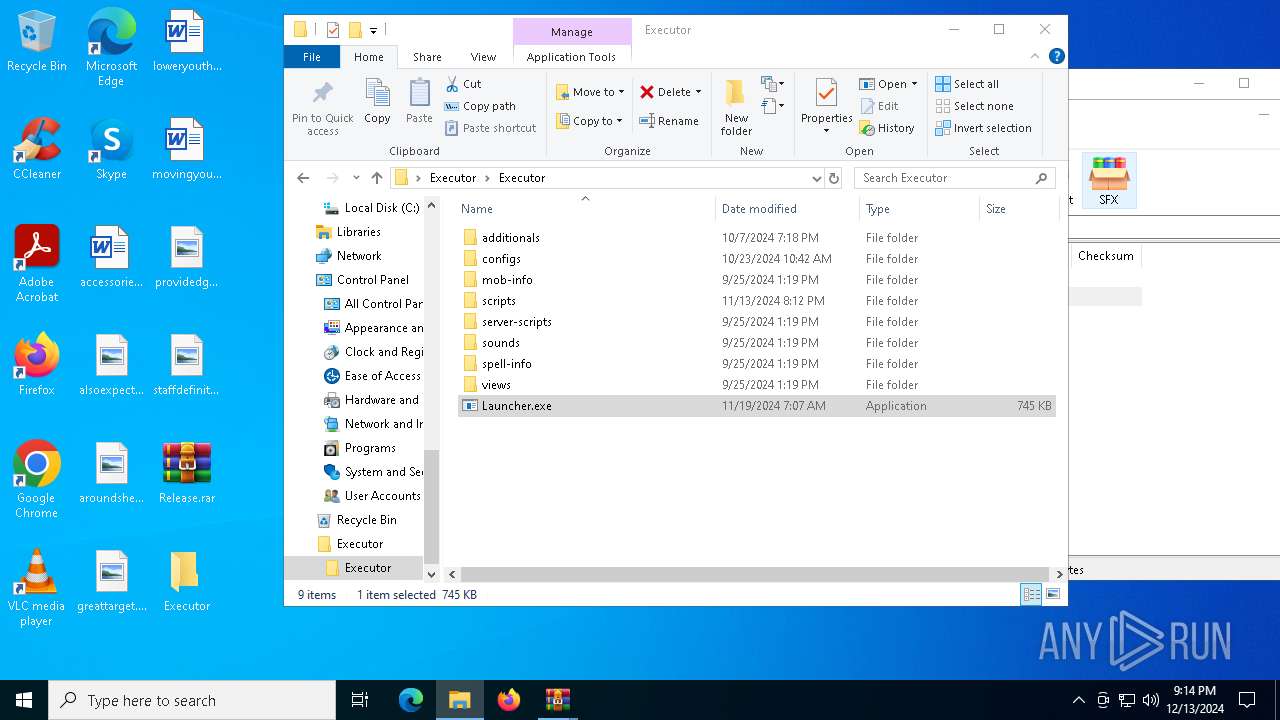
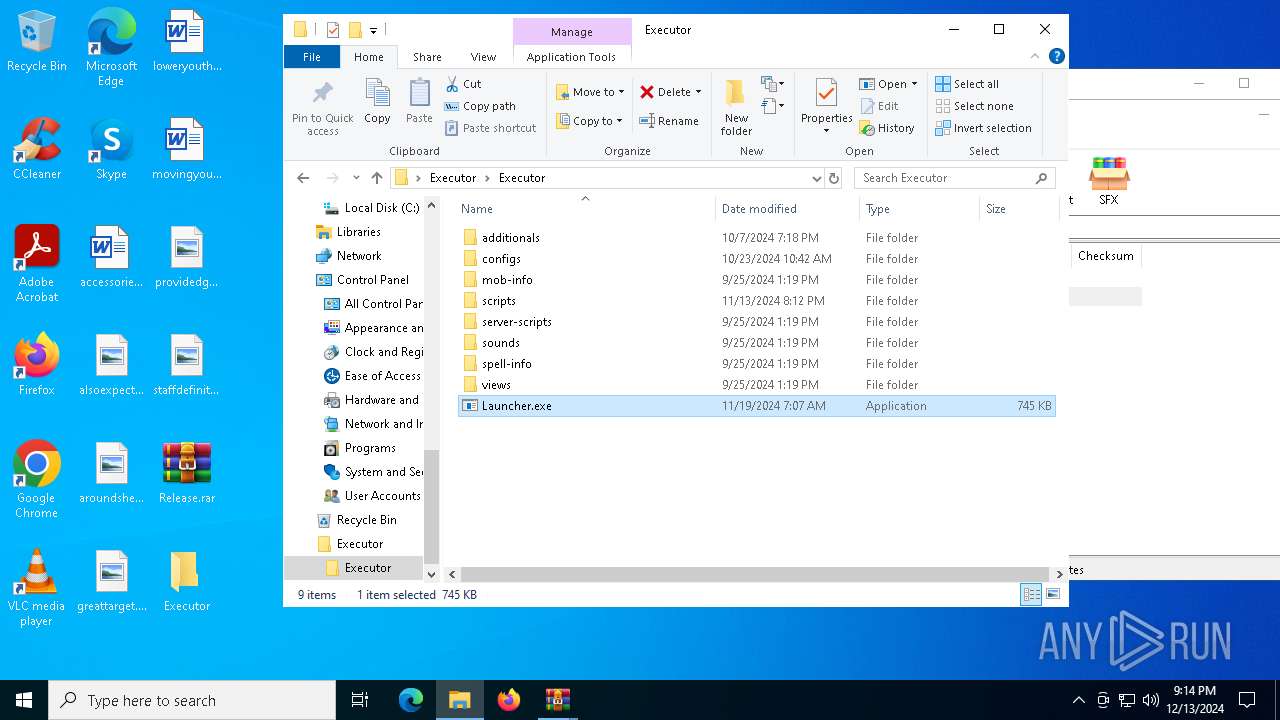
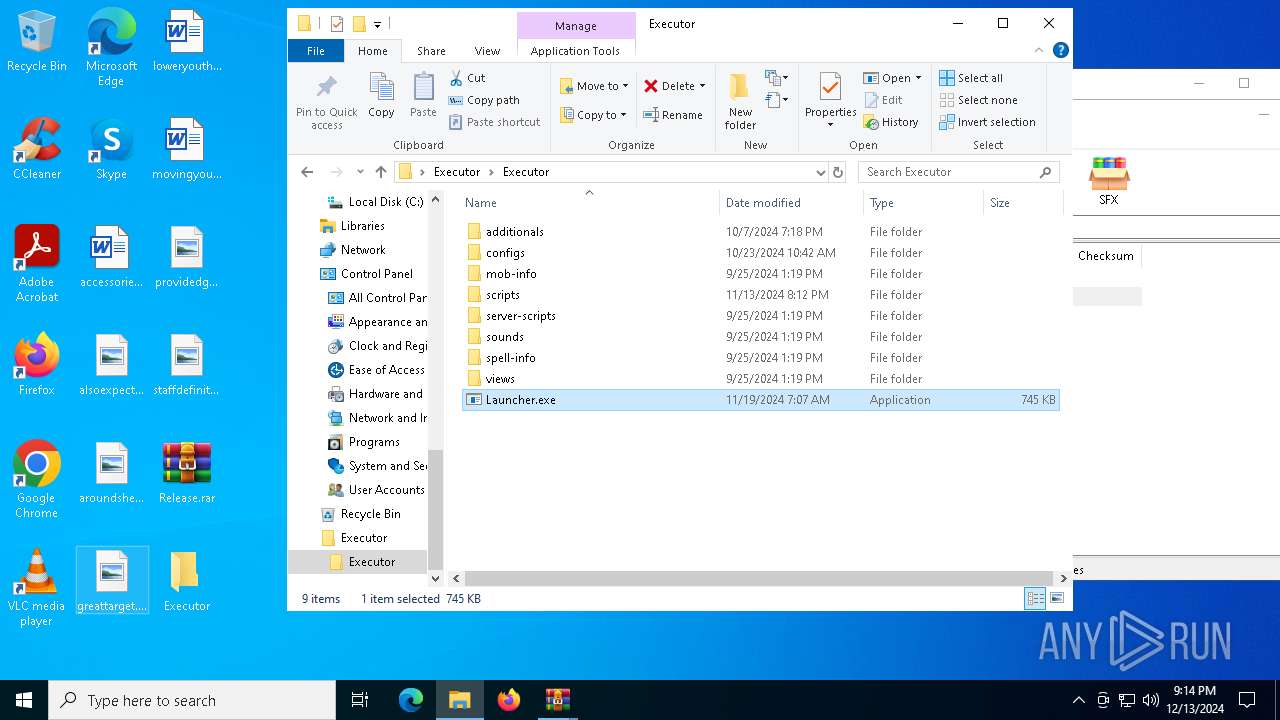
| 4724 | "C:\Users\admin\Desktop\Executor\Executor\Launcher.exe" | C:\Users\admin\Desktop\Executor\Executor\Launcher.exe | Launcher.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5236 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4856 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 4864 -prefMapHandle 4652 -prefsLen 36588 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {17b81dcb-5c29-4cb6-8093-72a1415ba61f} 6440 "\\.\pipe\gecko-crash-server-pipe.6440" 1bed4bb0310 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5300 | "C:\Users\admin\Desktop\Executor\Executor\Launcher.exe" | C:\Users\admin\Desktop\Executor\Executor\Launcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 5316 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2152 -parentBuildID 20240213221259 -prefsHandle 2144 -prefMapHandle 2132 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {92f15833-a122-48af-88c5-a4701c2395b9} 6440 "\\.\pipe\gecko-crash-server-pipe.6440" 1bebf880310 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5540 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5688 -childID 7 -isForBrowser -prefsHandle 5436 -prefMapHandle 5560 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1532 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {b4741205-f86e-428b-ad9f-ba5d1d1ac680} 6440 "\\.\pipe\gecko-crash-server-pipe.6440" 1bed7e93850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5568 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4260 -childID 2 -isForBrowser -prefsHandle 4252 -prefMapHandle 2788 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1532 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {860b3d9a-b363-491d-b4af-d978507a6999} 6440 "\\.\pipe\gecko-crash-server-pipe.6440" 1bed3048690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5604 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5036 -childID 3 -isForBrowser -prefsHandle 5116 -prefMapHandle 5112 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1532 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {4285f1fe-b108-4d32-a9b8-403e8abb4403} 6440 "\\.\pipe\gecko-crash-server-pipe.6440" 1bed62fed90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
Total events
23 229
Read events
23 211
Write events
18
Delete events
0
Modification events
| (PID) Process: | (5712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Release.rar | |||
| (PID) Process: | (5712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
1
Suspicious files
398
Text files
52
Unknown types
52
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
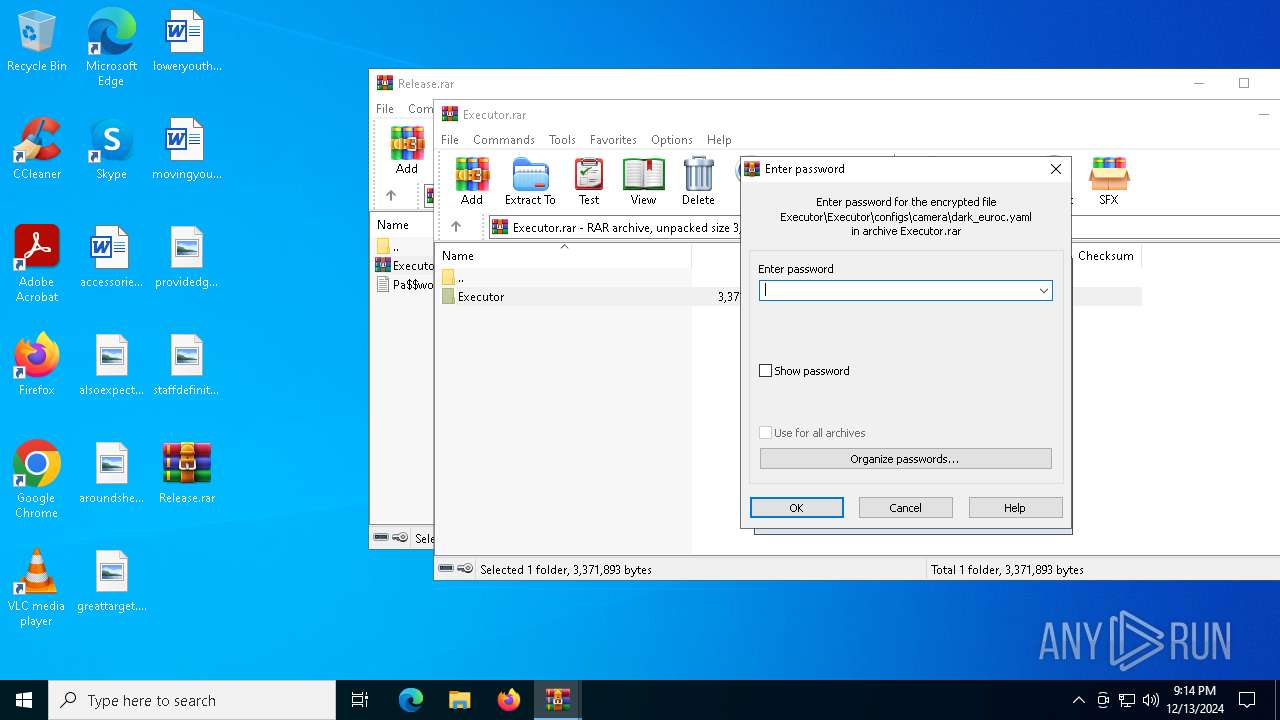
| 5712 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa5712.26302\Executor.rar | compressed | |
MD5:6AB0ABD018BF5687F0637537820CBCF6 | SHA256:DD9DBD0484C88E111103FA990789CA3ED01AD40D569D3D5C35BAF34C2532E7F7 | |||
| 6724 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6724.26817\Executor\Executor\configs\camera\realsense_848_480.yaml | text | |
MD5:0A3A9C6D6B8EDBE68C9E23B03443A7E2 | SHA256:B294EA0ECA78C1F5516BEF1F3F81EF58FE26C5D3D1506CEEAFB8CA63C84D5735 | |||
| 6724 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6724.26817\Executor\Executor\configs\map_refinement\mr_oivio.yaml | text | |
MD5:780FFF3221B3D35FC1A1460B99A700A6 | SHA256:3727DDE7A3E8EEF74076FF068CCD7C364CB9A8640488BC068CD3705B4476EF7C | |||
| 6724 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6724.26817\Executor\Executor\configs\camera\oivio.yaml | text | |
MD5:F6F7DD3DE4538A71757E3EEEDE31DB52 | SHA256:F839763D3EAC65F98DEE1433E5609825017FF247FC6DF4307A49787799AAC667 | |||
| 6724 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6724.26817\Executor\Executor\configs\camera\euroc.yaml | text | |
MD5:62B31102071B36BA67A8AF5AC15275A0 | SHA256:9389B5D73F436DF8387217B34105F12B48687AE6FFBBD9FB02A701A65F7B0E35 | |||
| 6724 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6724.26817\Executor\Executor\configs\visual_odometry\vo_oivio.yaml | text | |
MD5:C45C6FDA25CEB5FCDF5D9261346BD23C | SHA256:0F7B9D2956A42B35E219EA091107498EA707BB83FDF82EFF10A8A45AC72B76A6 | |||
| 6724 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6724.26817\Executor\Executor\configs\visual_odometry\vo_euroc_dark.yaml | text | |
MD5:C2183C839D09BF5FFC08FE6355413AD1 | SHA256:4566F337954D983AAA5A783927CB163EC9E4E8A8B1F67C7882947B4E0713DB23 | |||
| 6724 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6724.26817\Executor\Executor\configs\visual_odometry\vo_euroc.yaml | text | |
MD5:4AACBE6B96A9D82191B27788AEEFE565 | SHA256:CD3903A45ED897987292A137DBE64D993D671E0AB04FD6802DA519B300BFDB80 | |||
| 6724 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6724.26817\Executor\Executor\configs\camera\uma_bumblebee.yaml | text | |
MD5:3DA07A92A0542217DAB0FBADCEF14F7A | SHA256:8405E9AB2ABBFDD817812CD972747CA13990E89277CA45ED00DE17674A5F70C2 | |||
| 6724 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6724.26817\Executor\Executor\configs\camera\tartanair.yaml | text | |
MD5:2E04EB504DBE739471278363665D4B19 | SHA256:3FE6C7CF262718E6DEAFBB8BD30E5C39E36B8975016D1CA83F82BF67CCA62880 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
129
DNS requests
137
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6248 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5540 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5540 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5740 | WerFault.exe | GET | 200 | 23.48.23.169:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5740 | WerFault.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6440 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
640 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.189:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (processhol .sbs) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (3xp3cts1aim .sbs) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (p10tgrace .sbs) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (librari-night .sbs) |
2192 | svchost.exe | A Network Trojan was detected | ET MALWARE Observed DNS Query to Lumma Stealer Domain (processhol .sbs) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (befall-sm0ker .sbs) |
2192 | svchost.exe | A Network Trojan was detected | ET MALWARE Observed DNS Query to Lumma Stealer Domain (3xp3cts1aim .sbs) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (owner-vacat10n .sbs) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (cook-rain .sbs) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (peepburry828 .sbs) |