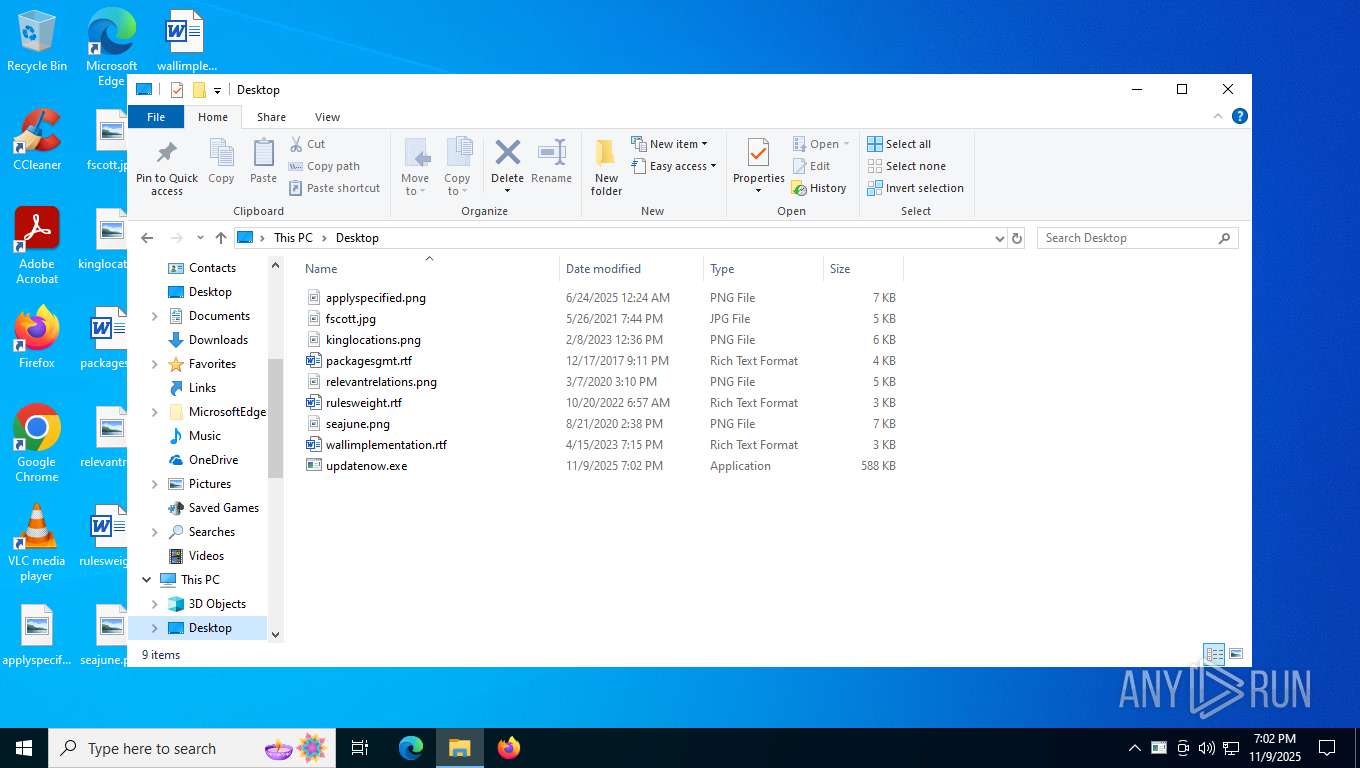
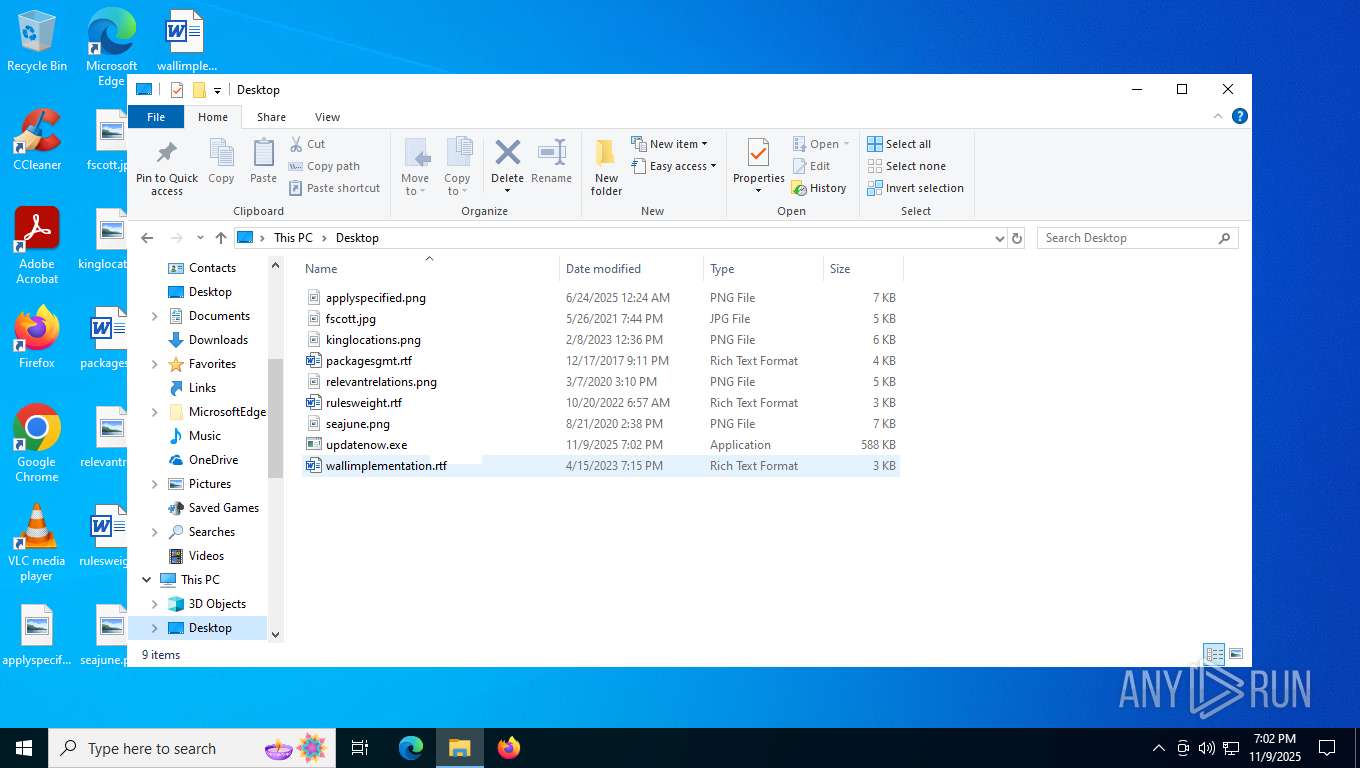
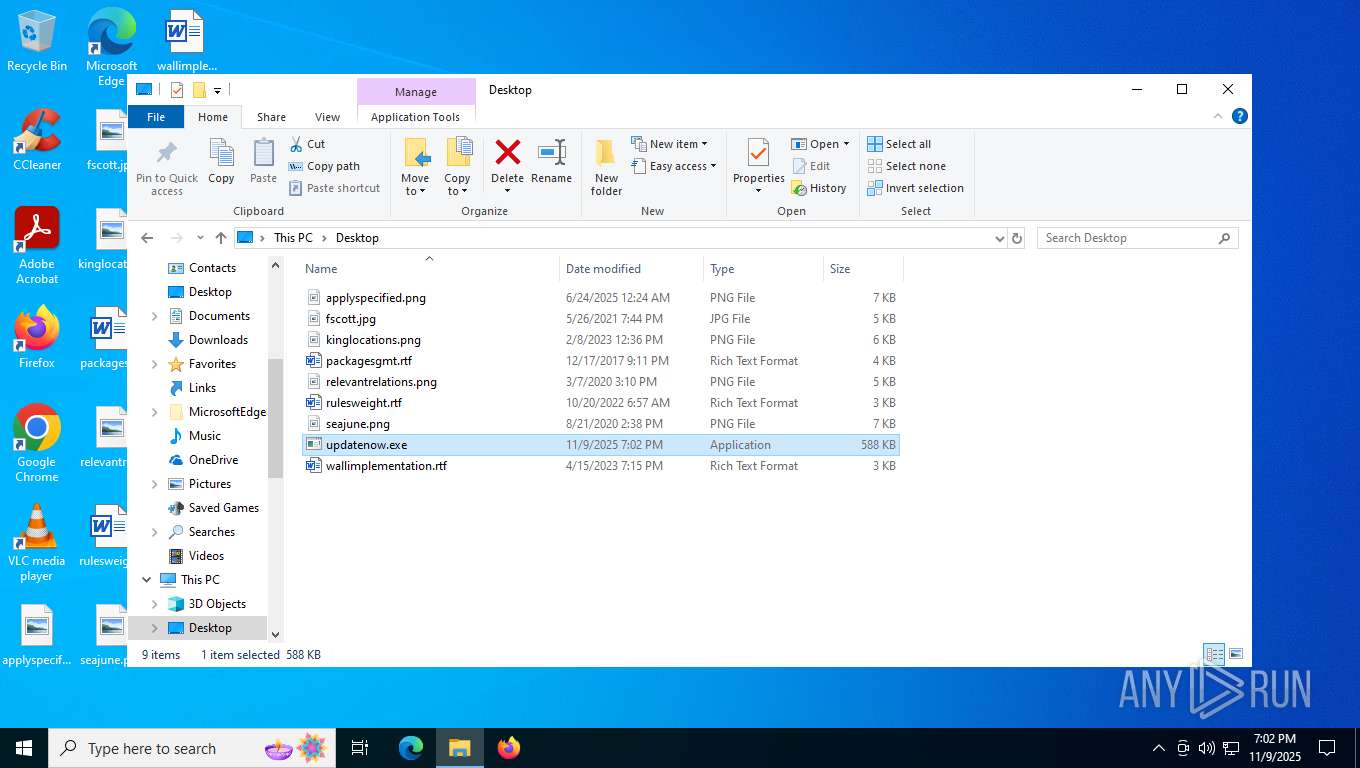
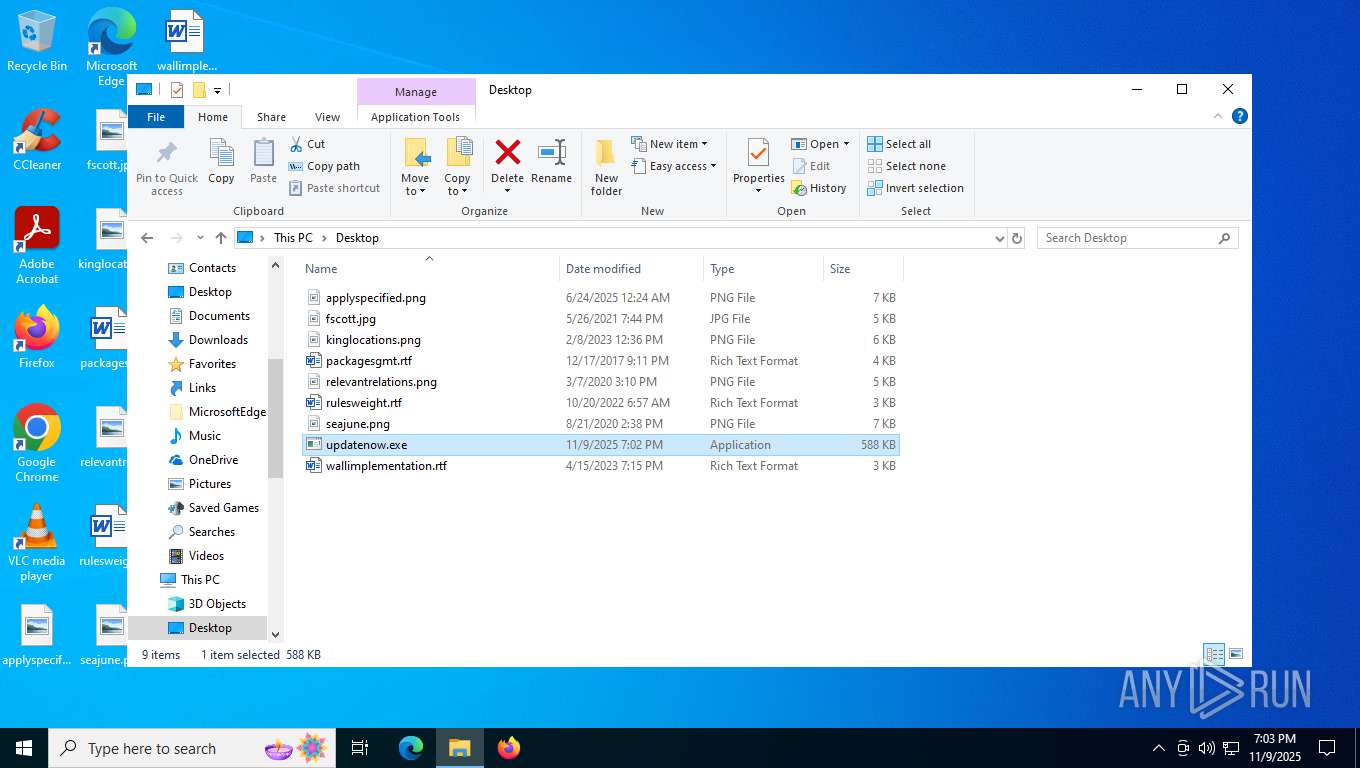
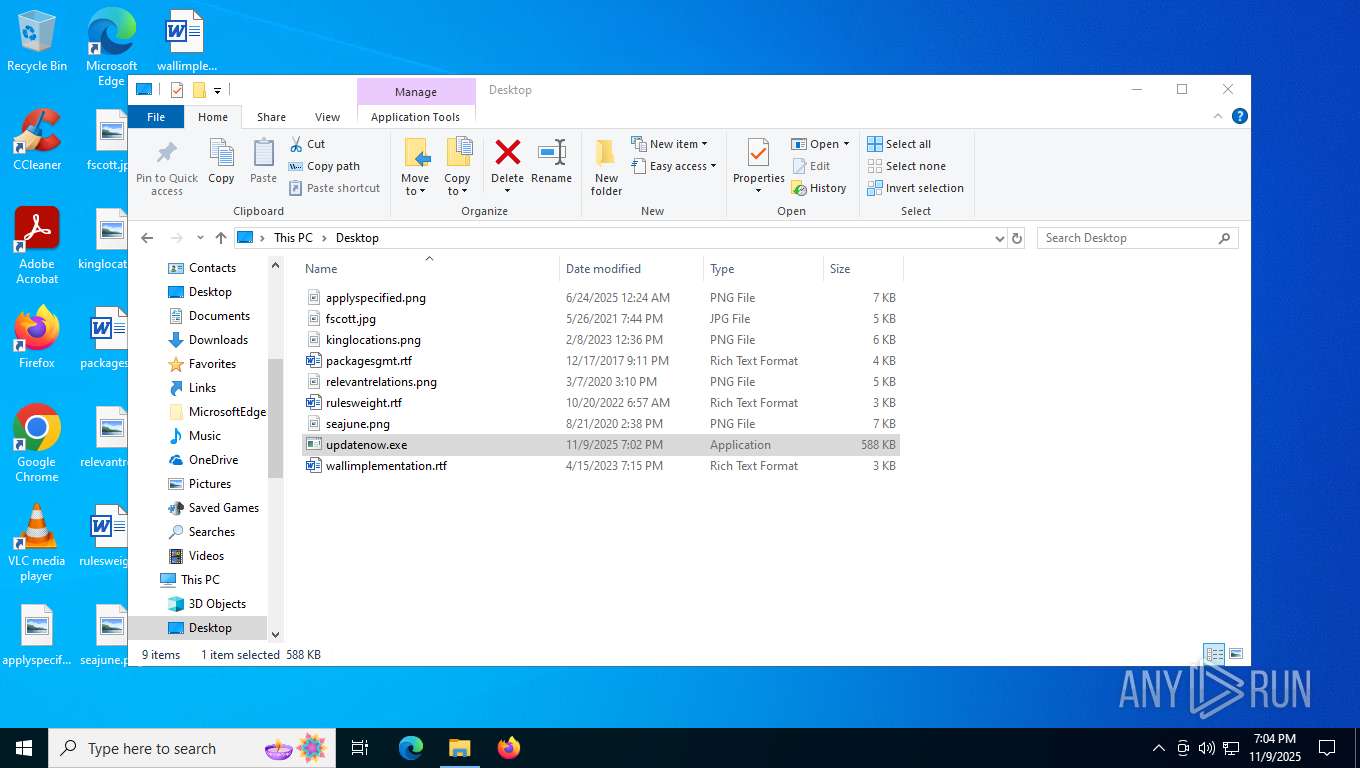
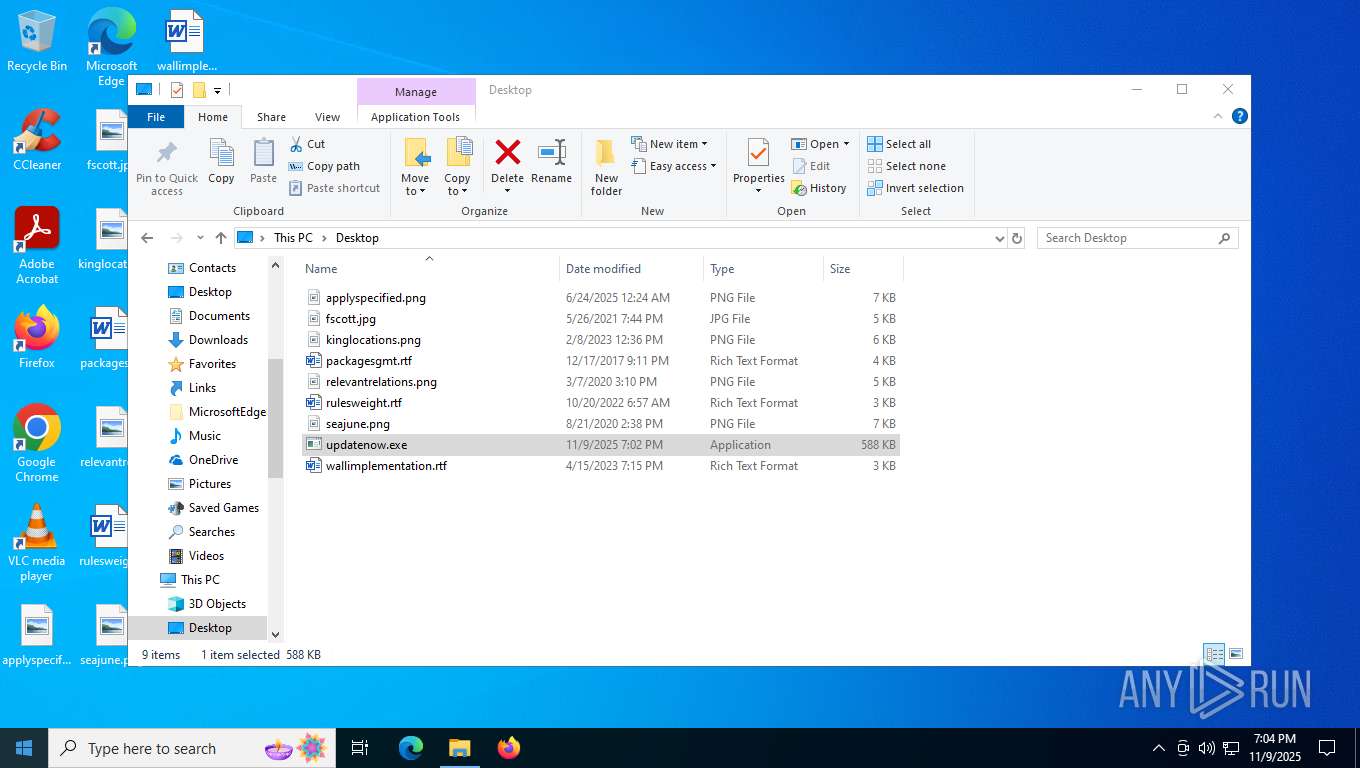
| File name: | updatenow.exe |
| Full analysis: | https://app.any.run/tasks/b98396e1-845e-4aa9-939e-52db411dfee7 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | November 09, 2025, 19:01:32 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | D797600296DDBED4497725579D814B7E |
| SHA1: | 54B22078651DCEE13472858D706F886A34678B2E |
| SHA256: | C25A6673A24D169DE1BB399D226C12CDC666E0FA534149FC9FA7896EE61D406F |
| SSDEEP: | 24576:gs8uCqXG8K70lrfYW5VkP3dRbZS59kJ3y0emLz4d+c6:UuCqXG8KCrfYW5VkvdRbZS59kJ3y0emm |
MALICIOUS
Steals credentials from Web Browsers
- RegSvcs.exe (PID: 6252)
- RegSvcs.exe (PID: 1784)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 6252)
- RegSvcs.exe (PID: 1784)
AGENTTESLA has been detected (YARA)
- RegSvcs.exe (PID: 6252)
- RegSvcs.exe (PID: 1784)
SUSPICIOUS
Connects to SMTP port
- RegSvcs.exe (PID: 6252)
- RegSvcs.exe (PID: 1784)
INFO
The sample compiled with english language support
- updatenow.exe (PID: 5392)
Checks supported languages
- updatenow.exe (PID: 5392)
- RegSvcs.exe (PID: 6252)
- updatenow.exe (PID: 5972)
- RegSvcs.exe (PID: 1784)
Reads mouse settings
- updatenow.exe (PID: 5392)
- updatenow.exe (PID: 5972)
Reads the computer name
- updatenow.exe (PID: 5392)
- RegSvcs.exe (PID: 6252)
- updatenow.exe (PID: 5972)
- RegSvcs.exe (PID: 1784)
Reads the machine GUID from the registry
- RegSvcs.exe (PID: 6252)
- RegSvcs.exe (PID: 1784)
Reads Environment values
- RegSvcs.exe (PID: 6252)
Create files in a temporary directory
- updatenow.exe (PID: 5392)
- updatenow.exe (PID: 5972)
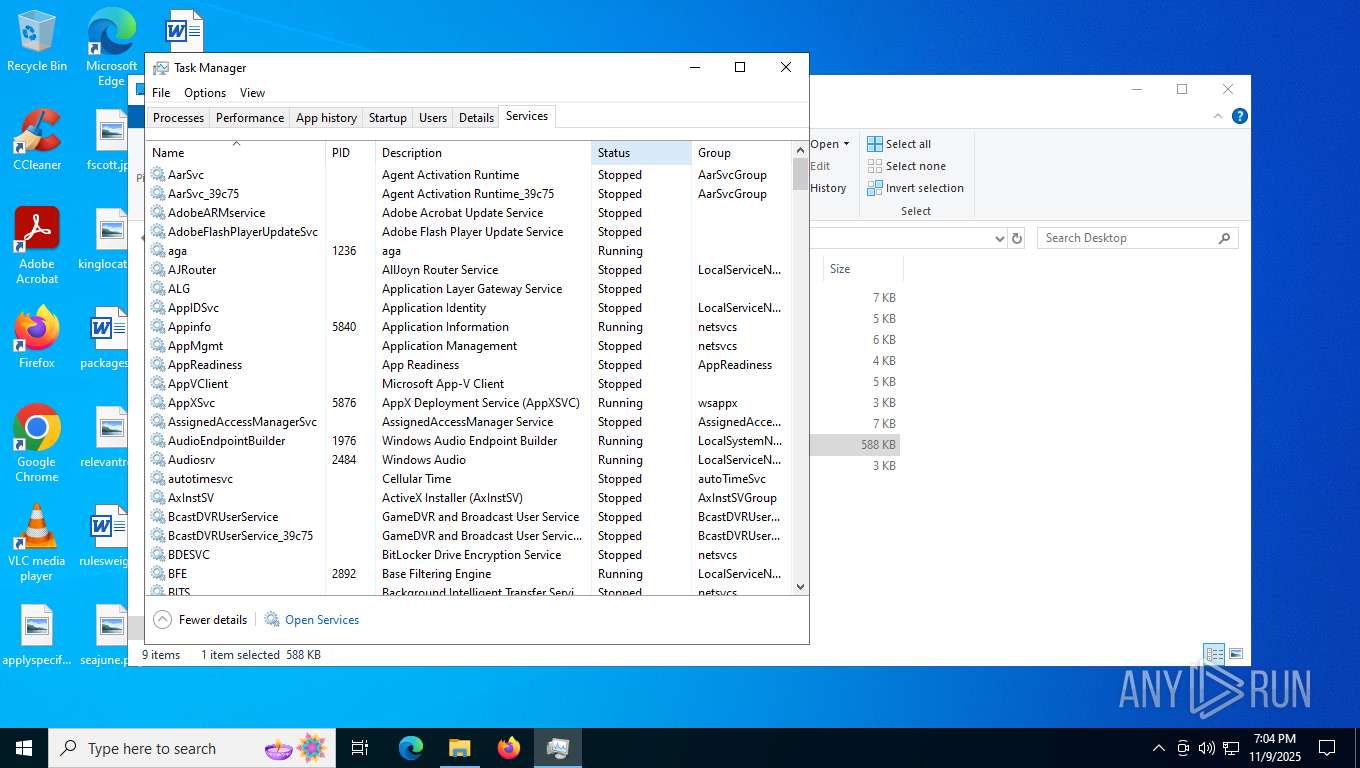
ULTRAVNC has been detected
- RegSvcs.exe (PID: 6252)
- RegSvcs.exe (PID: 1784)
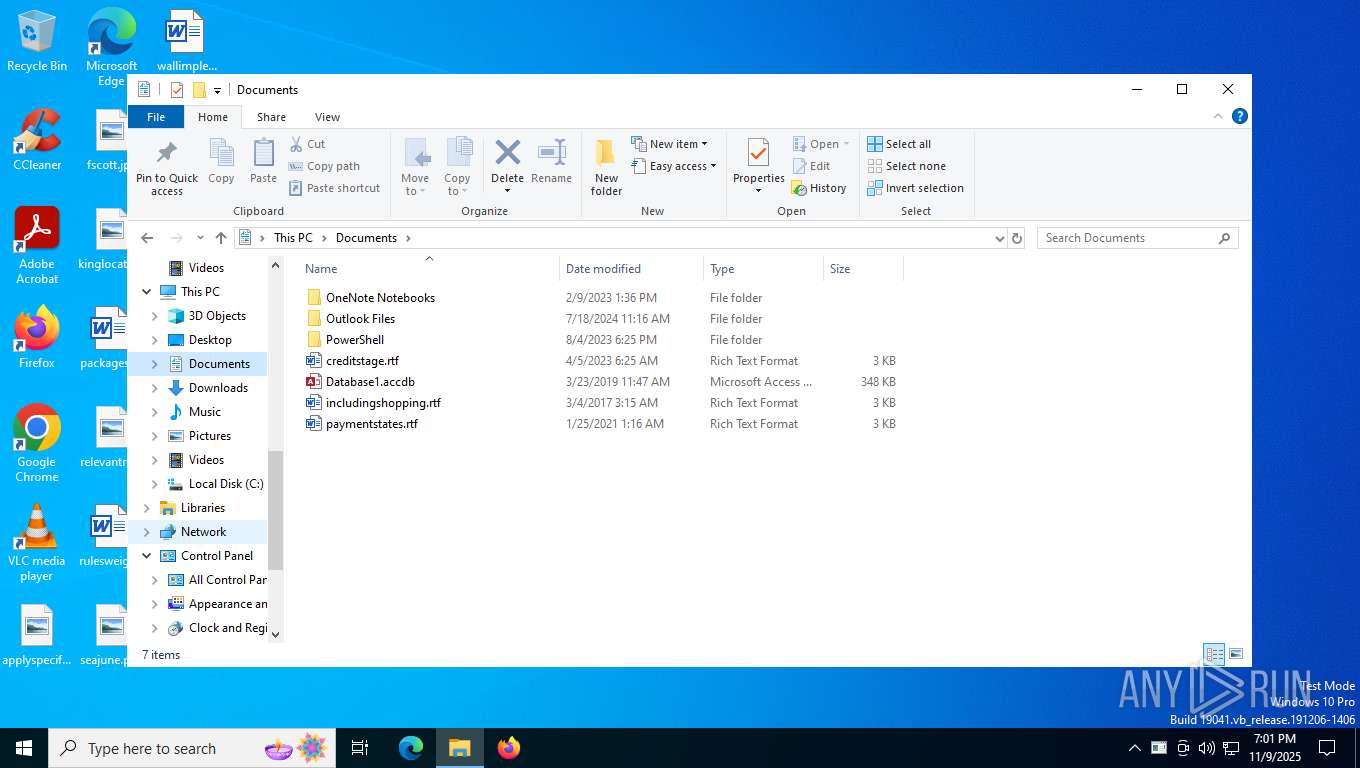
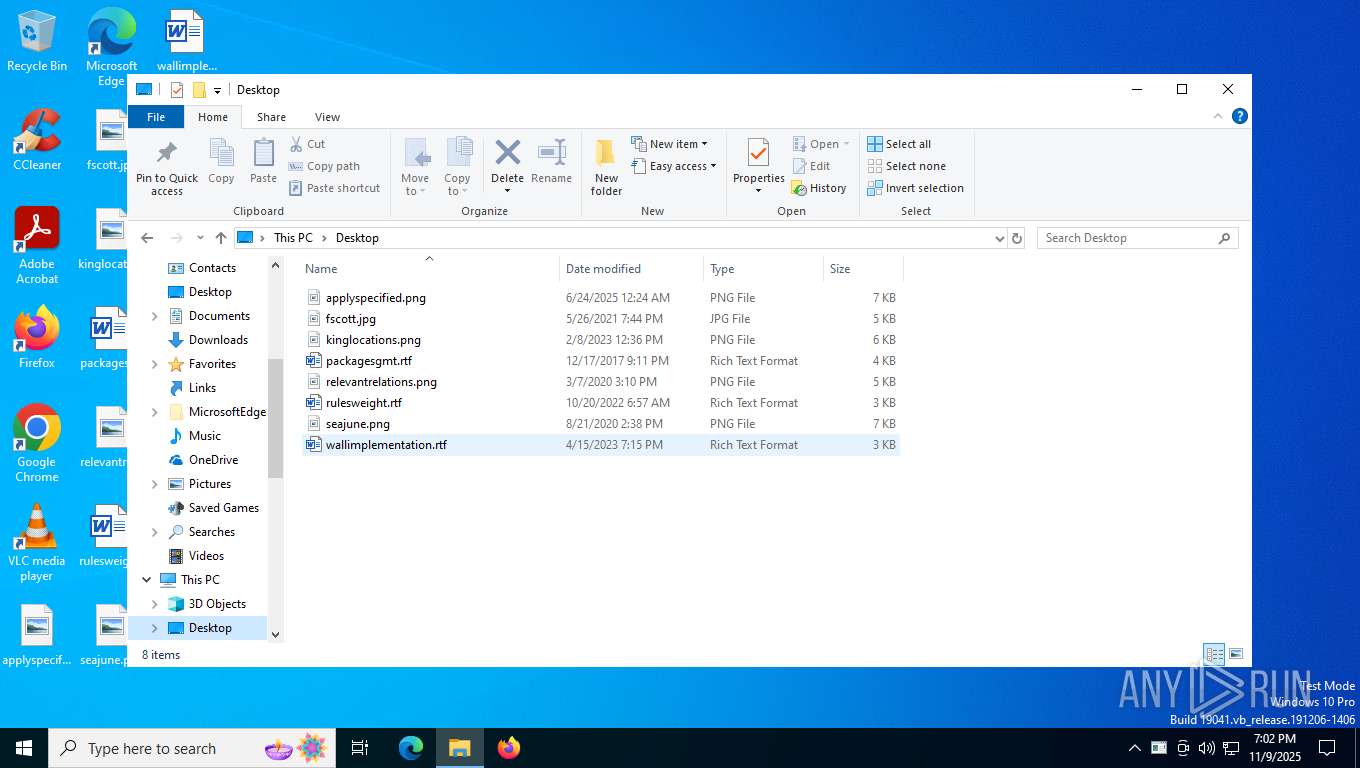
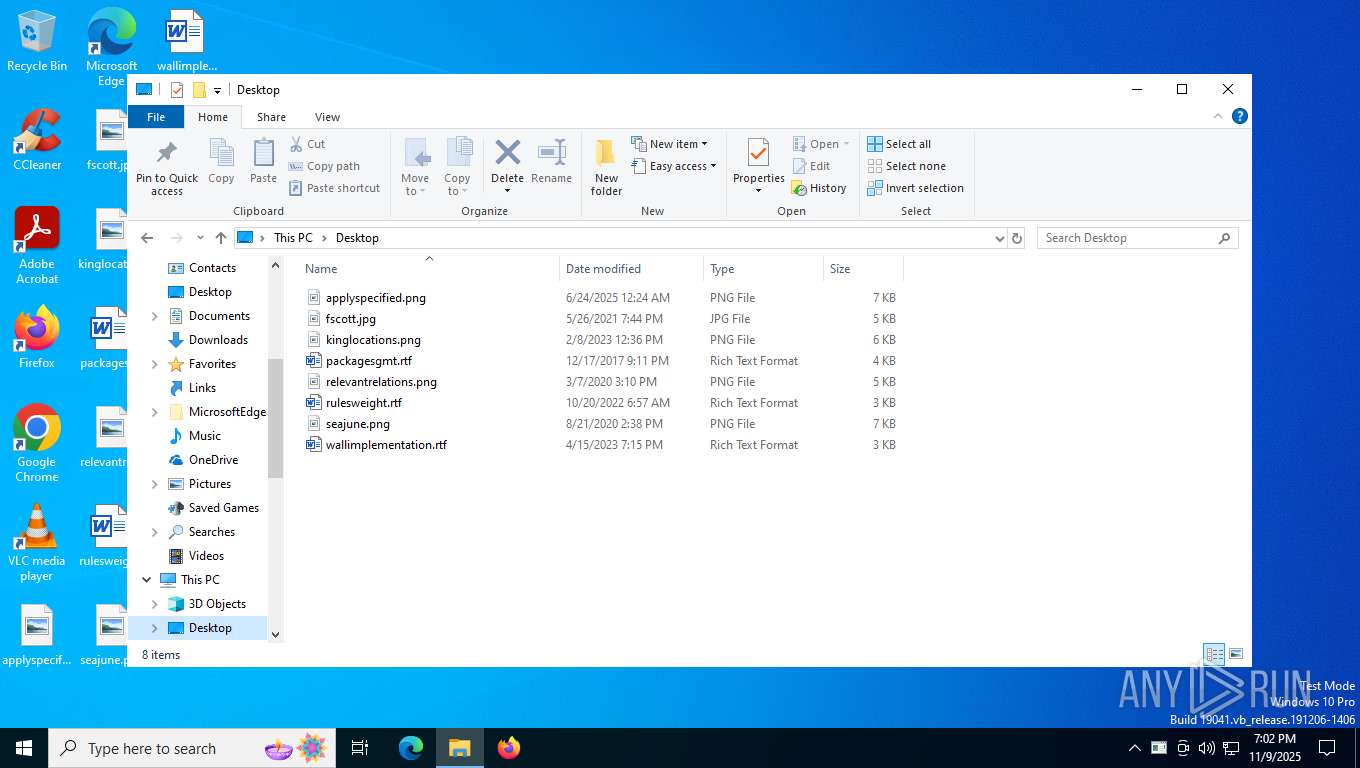
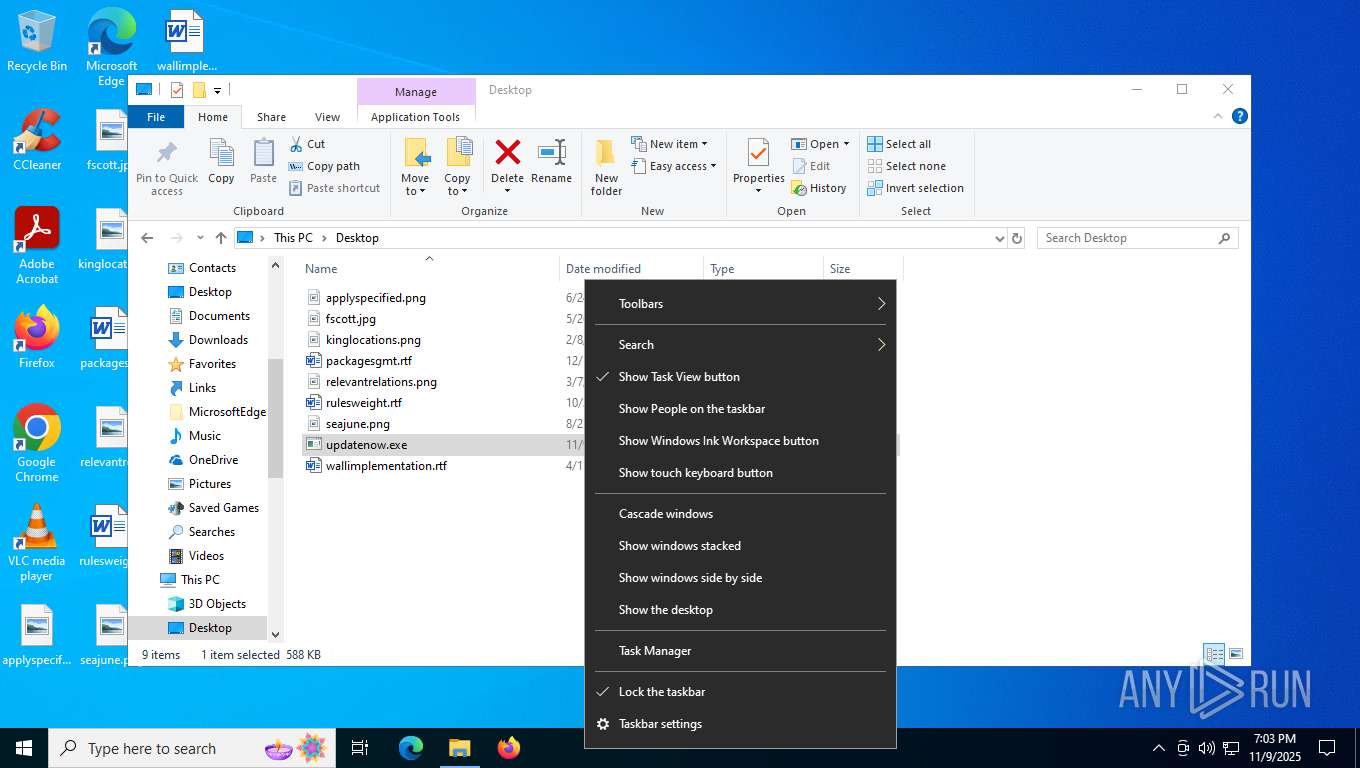
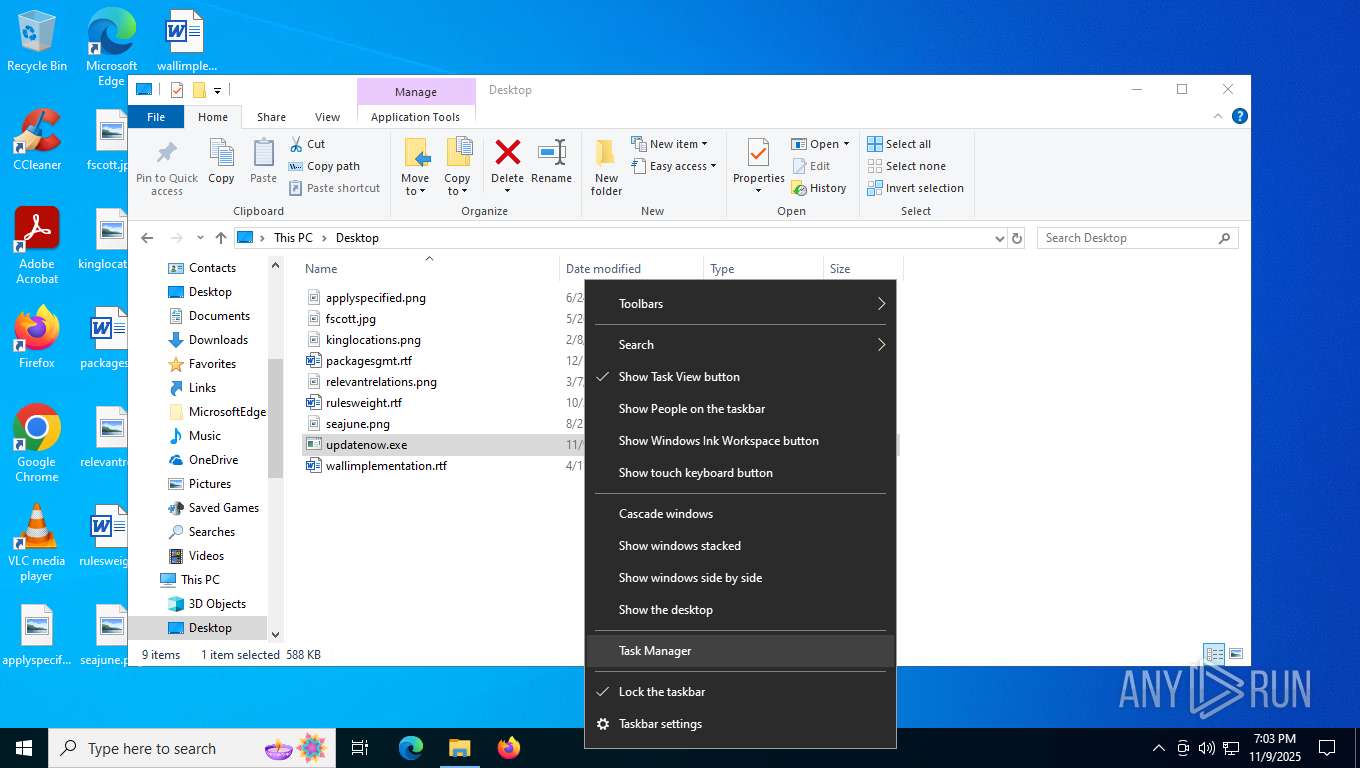
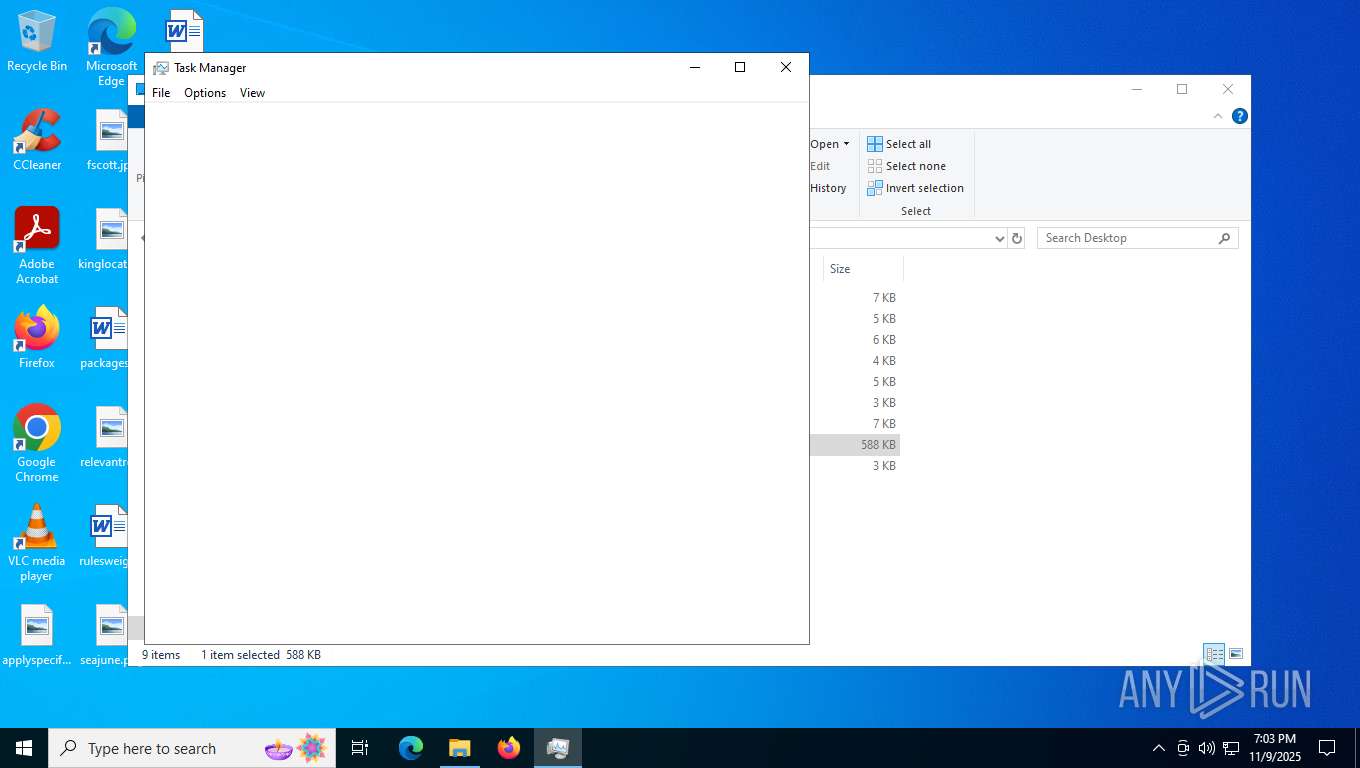
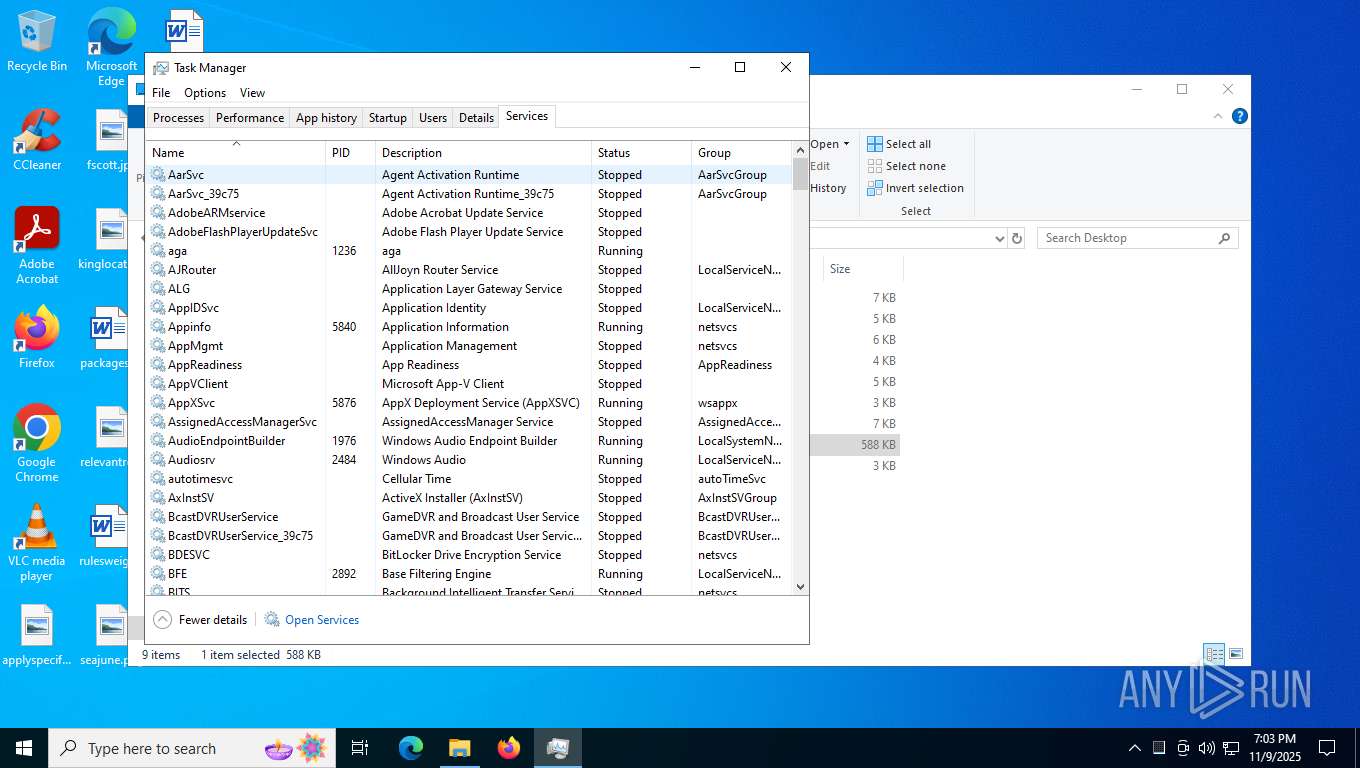
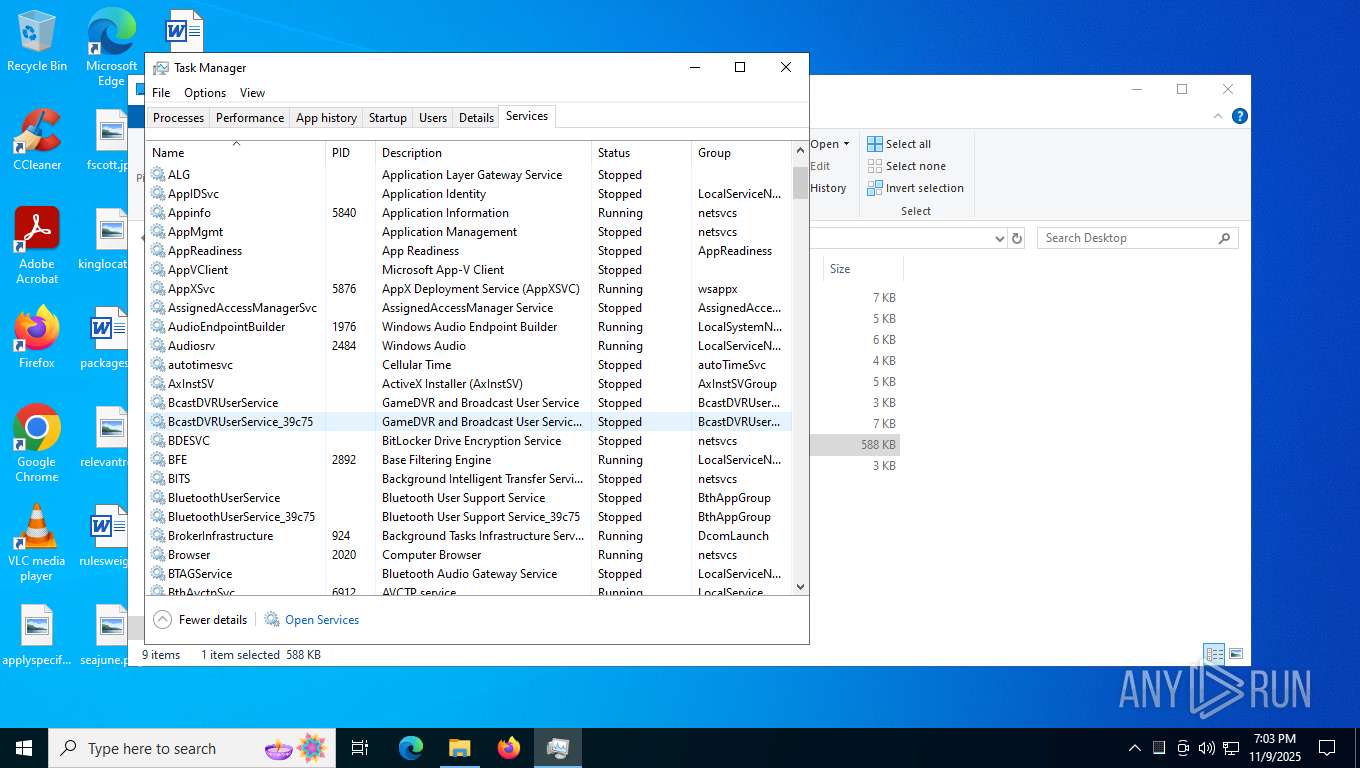
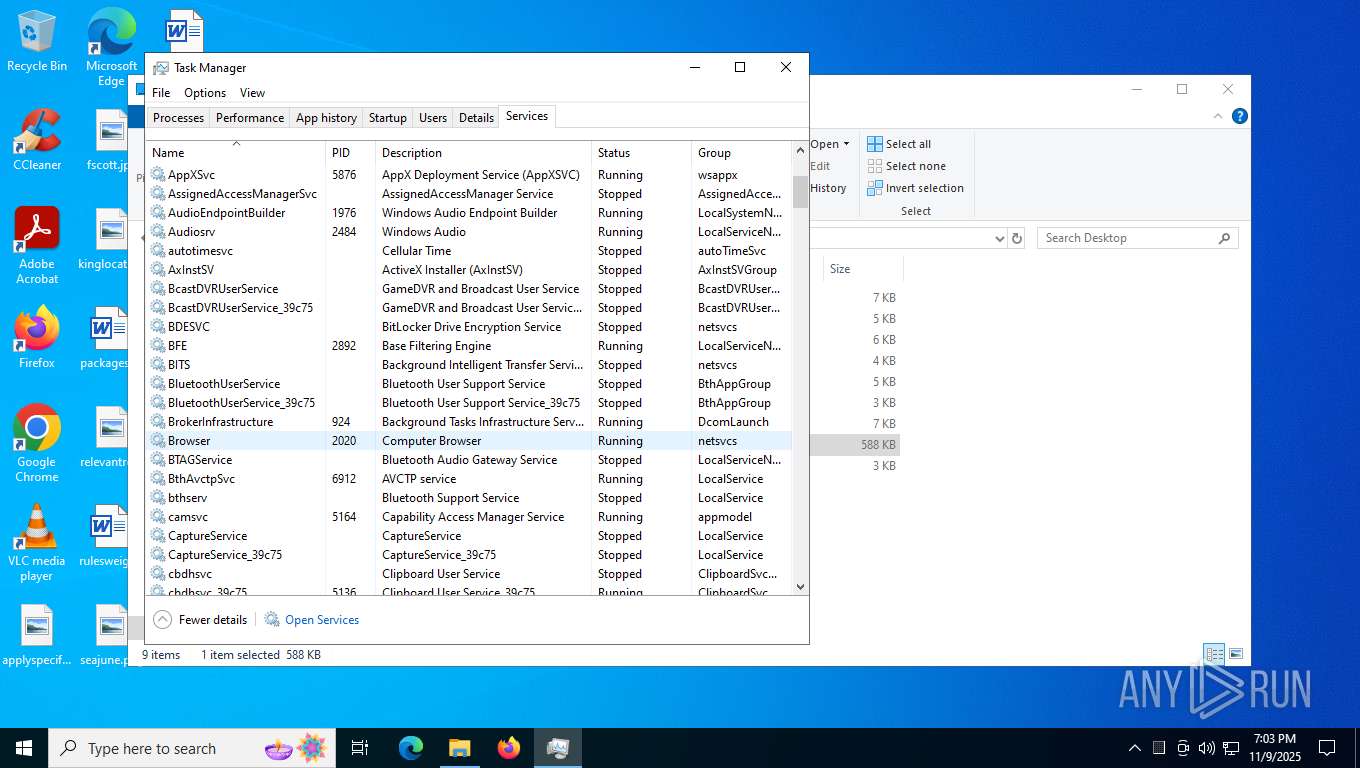
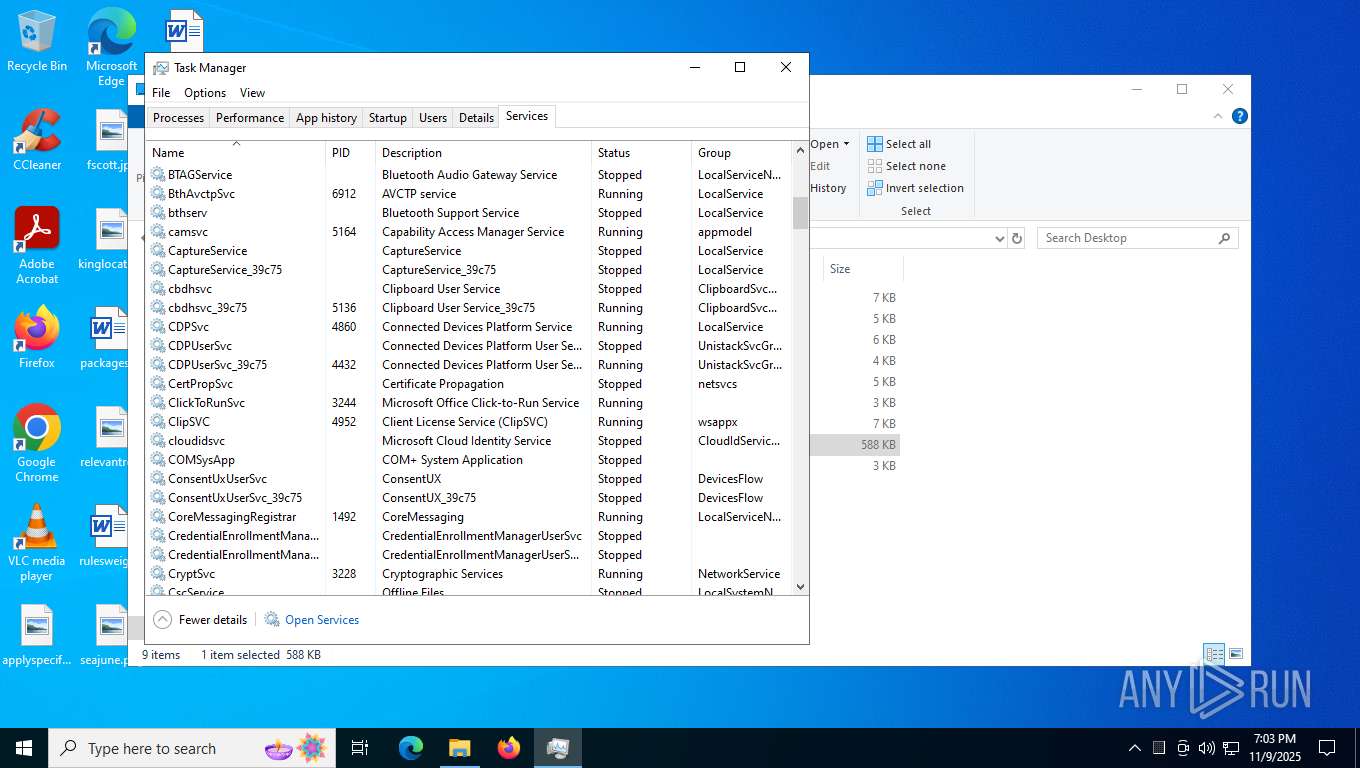
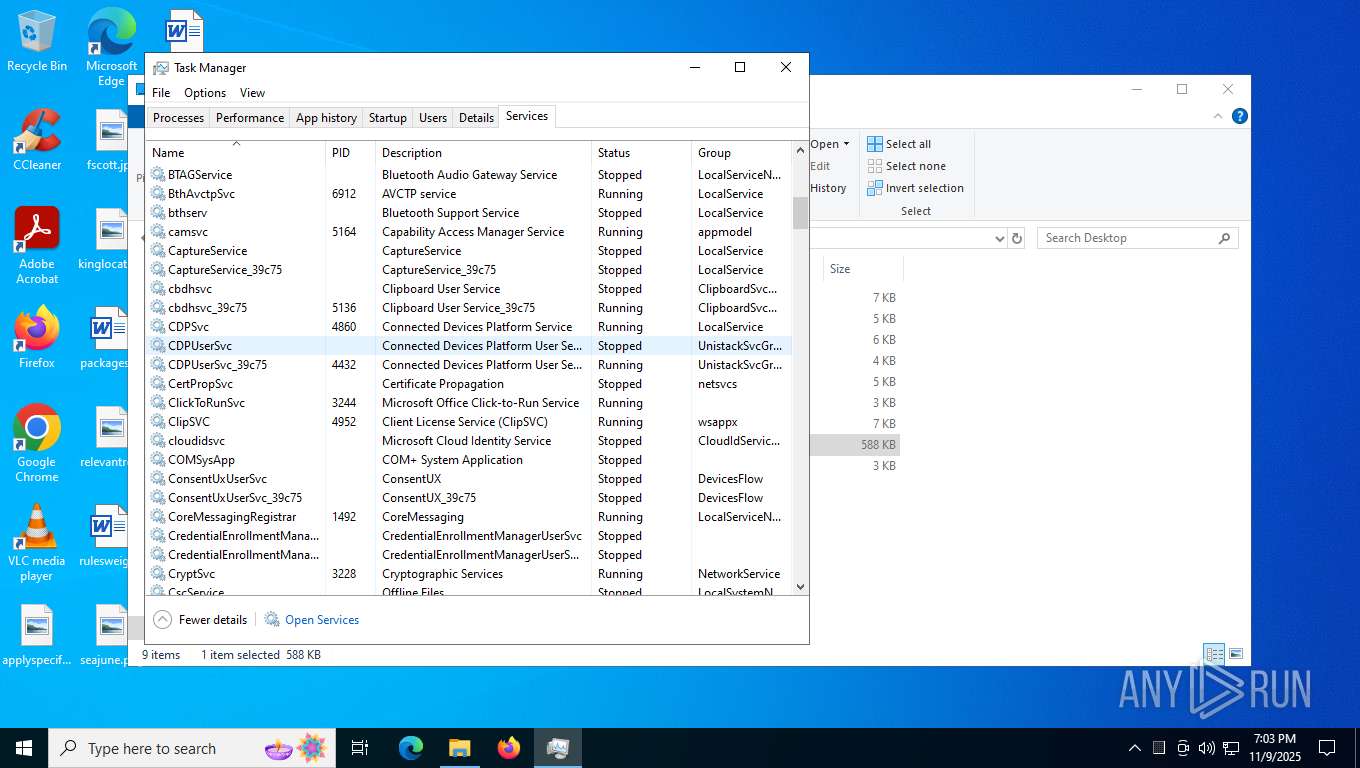
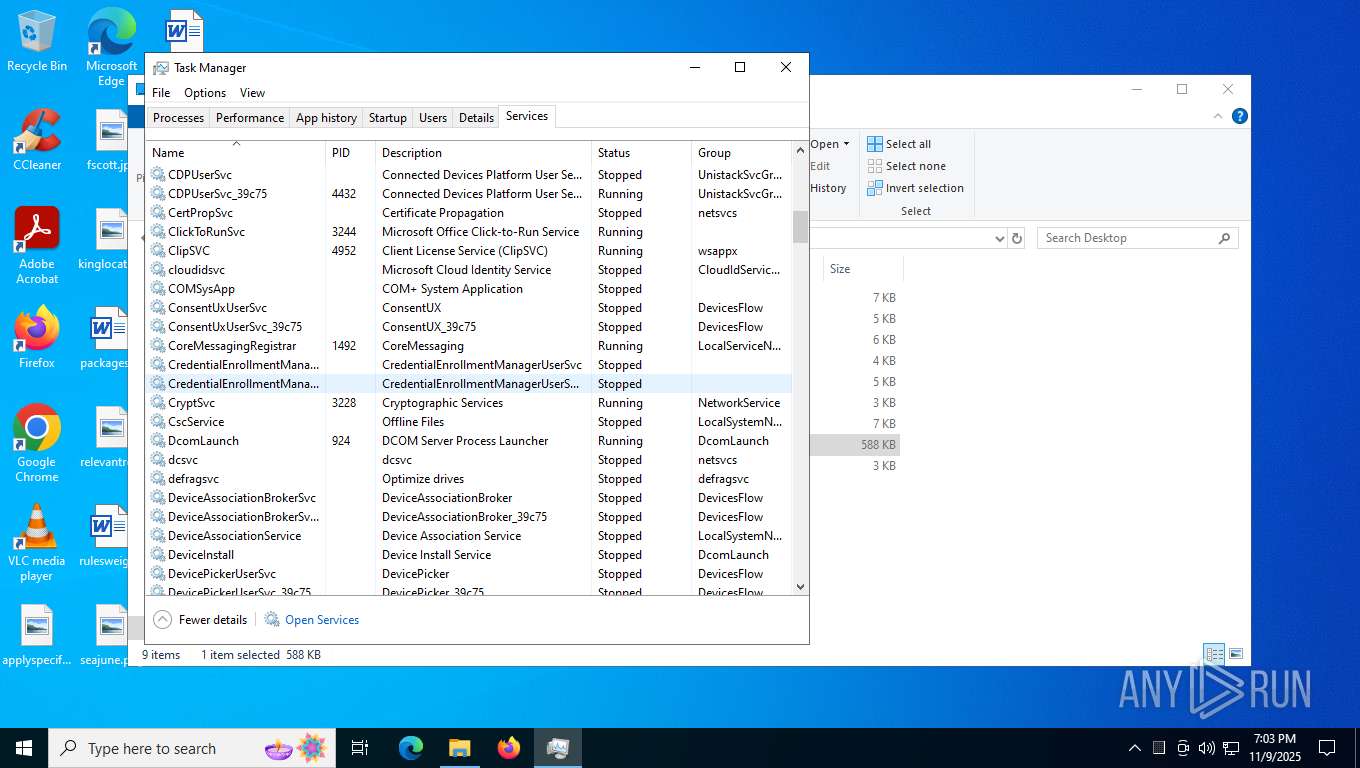
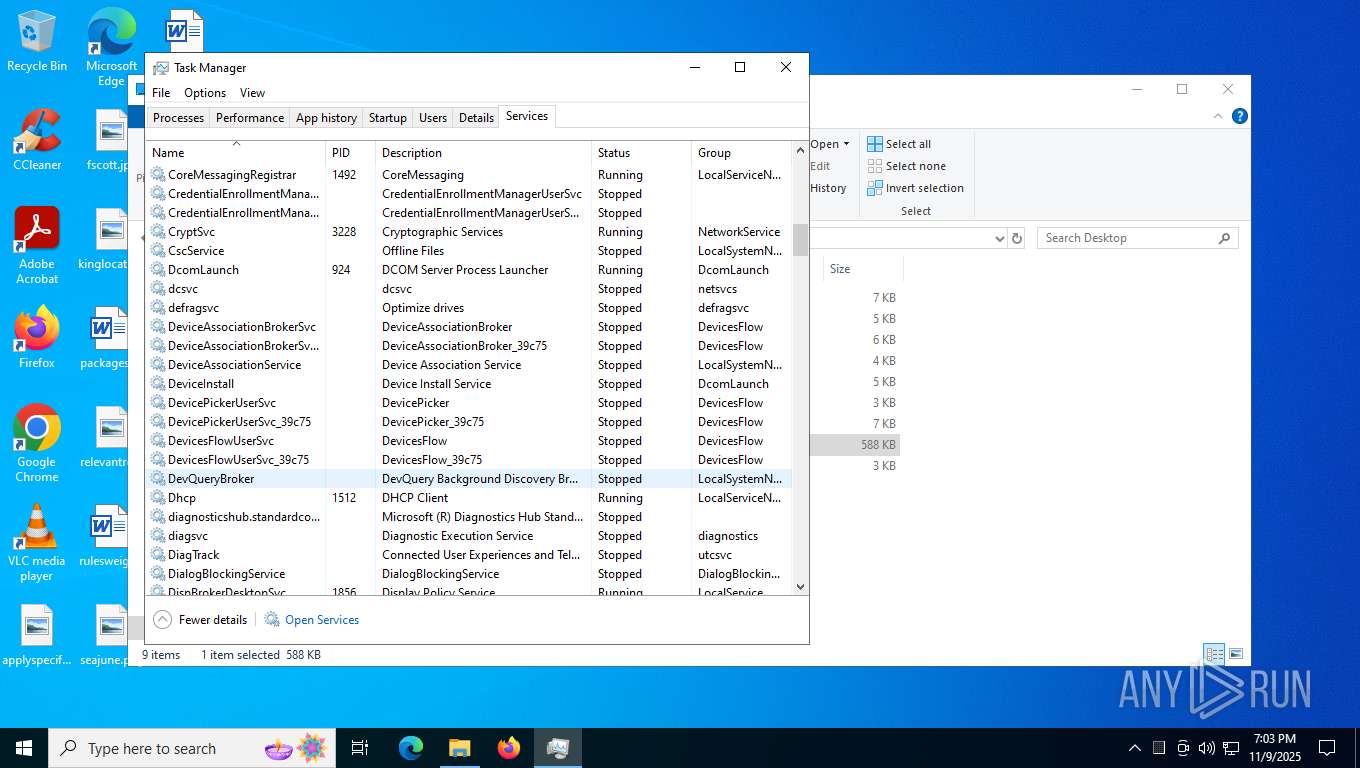
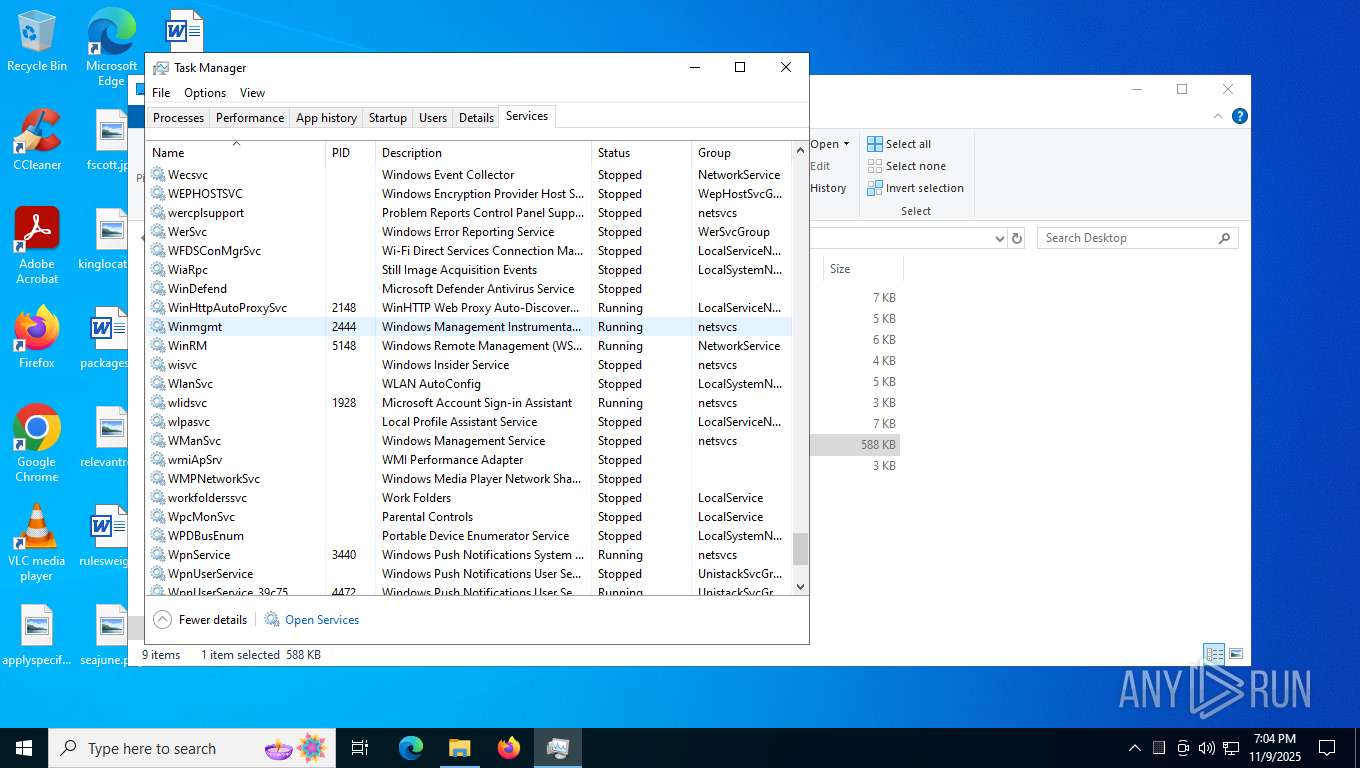
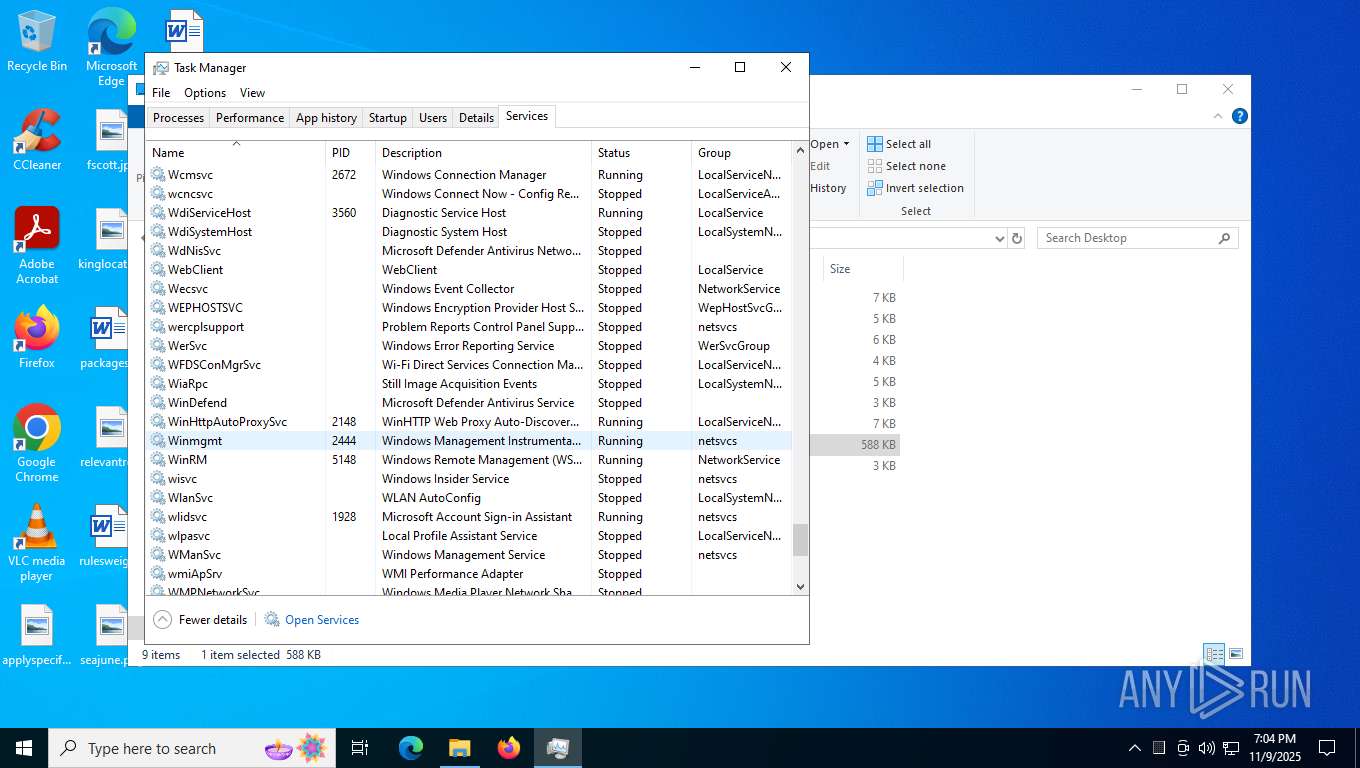
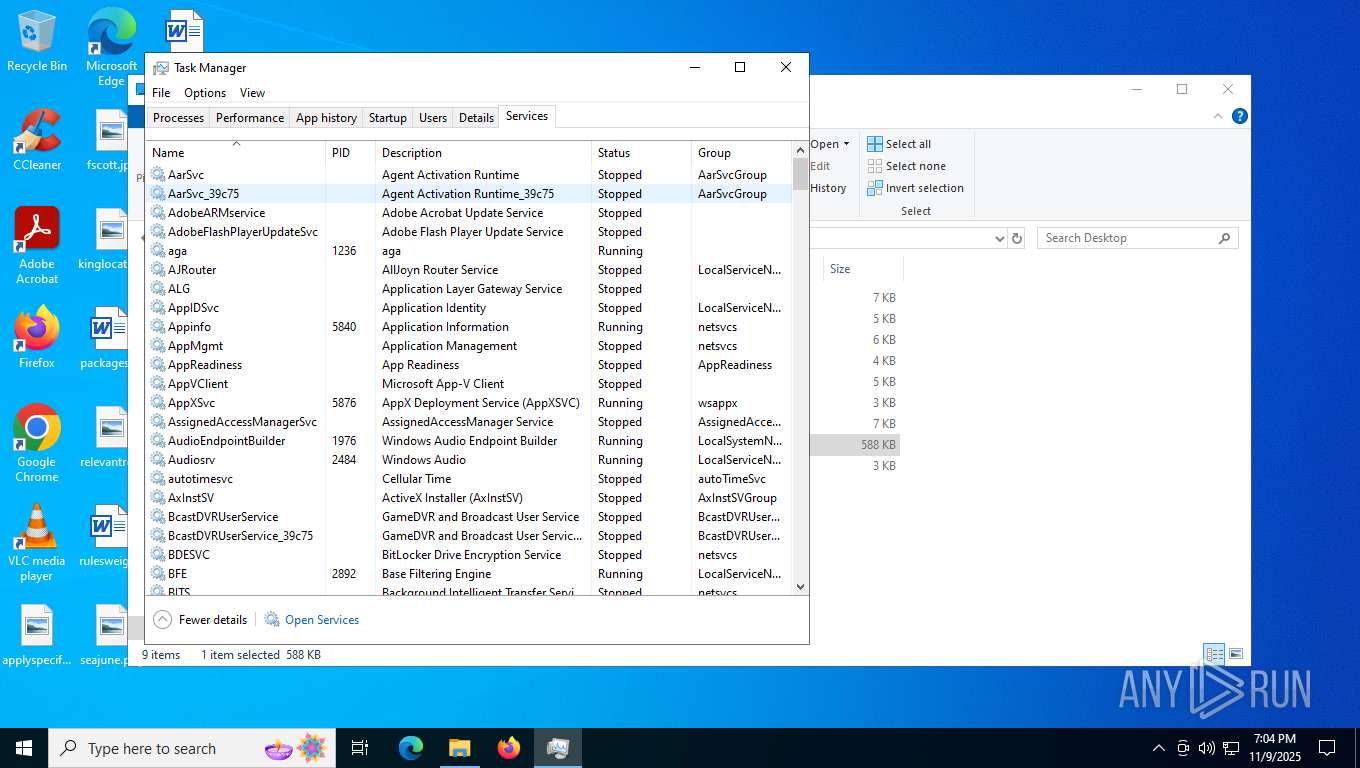
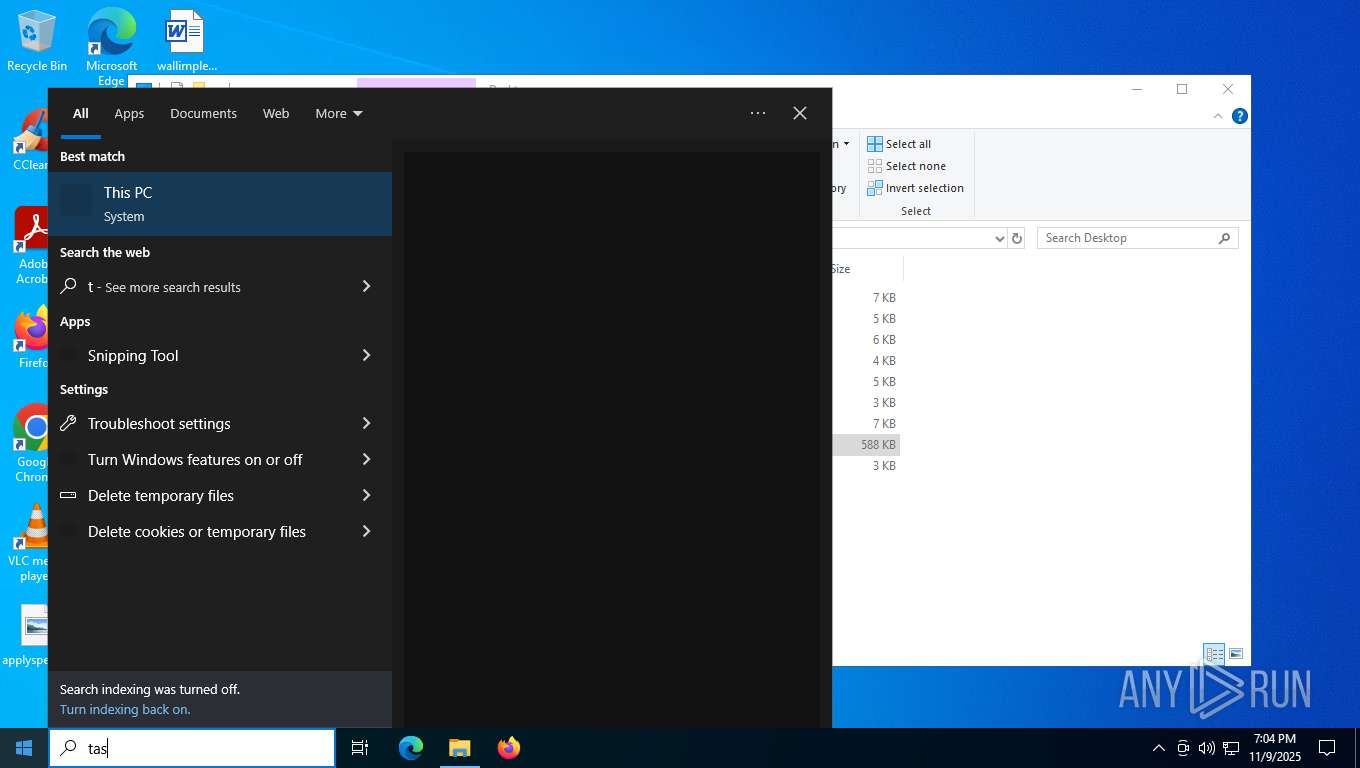
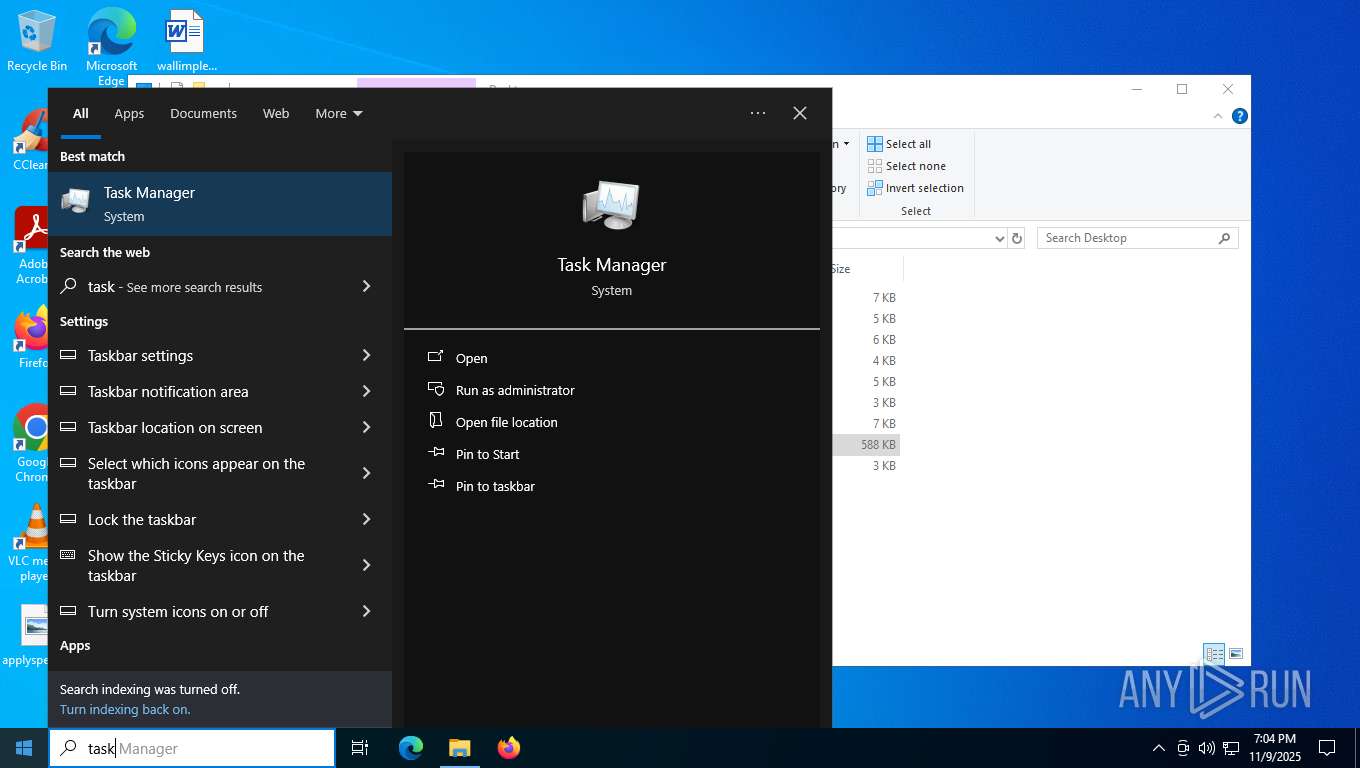
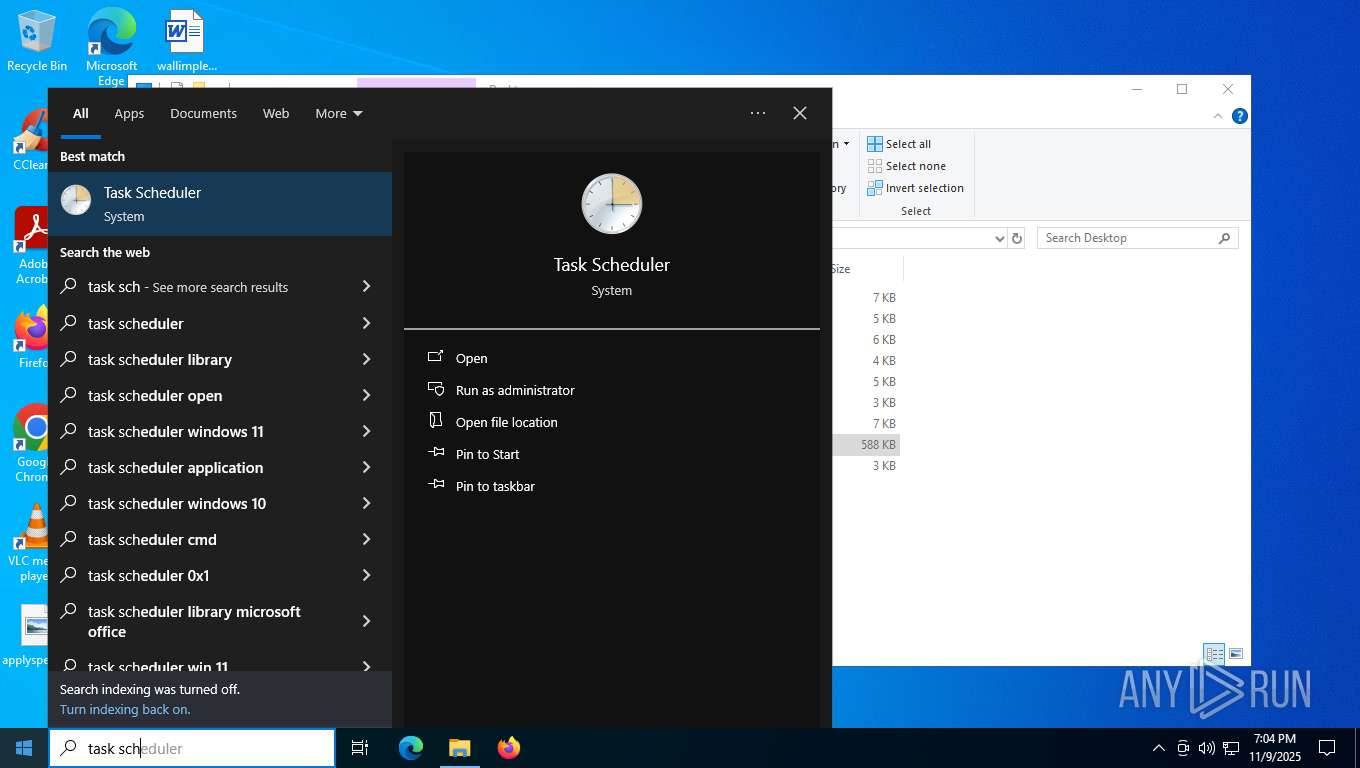
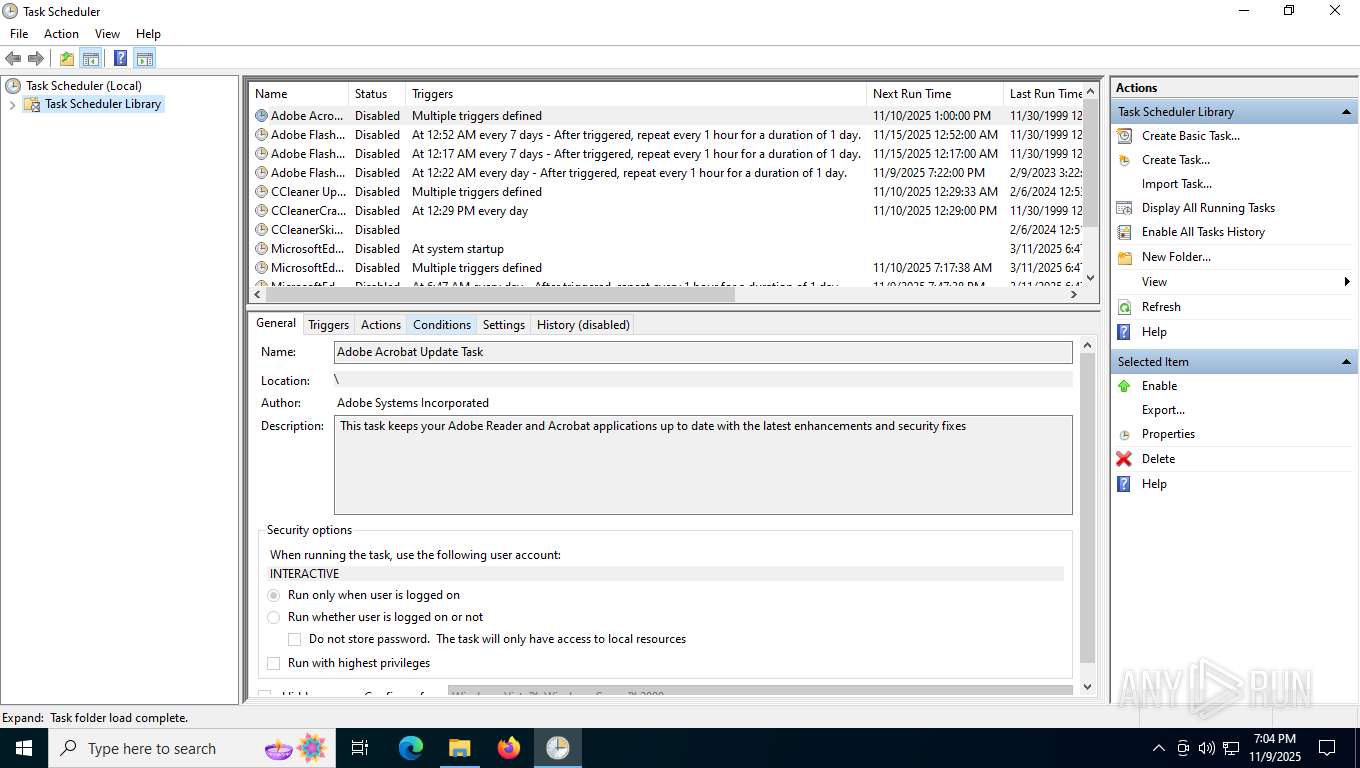
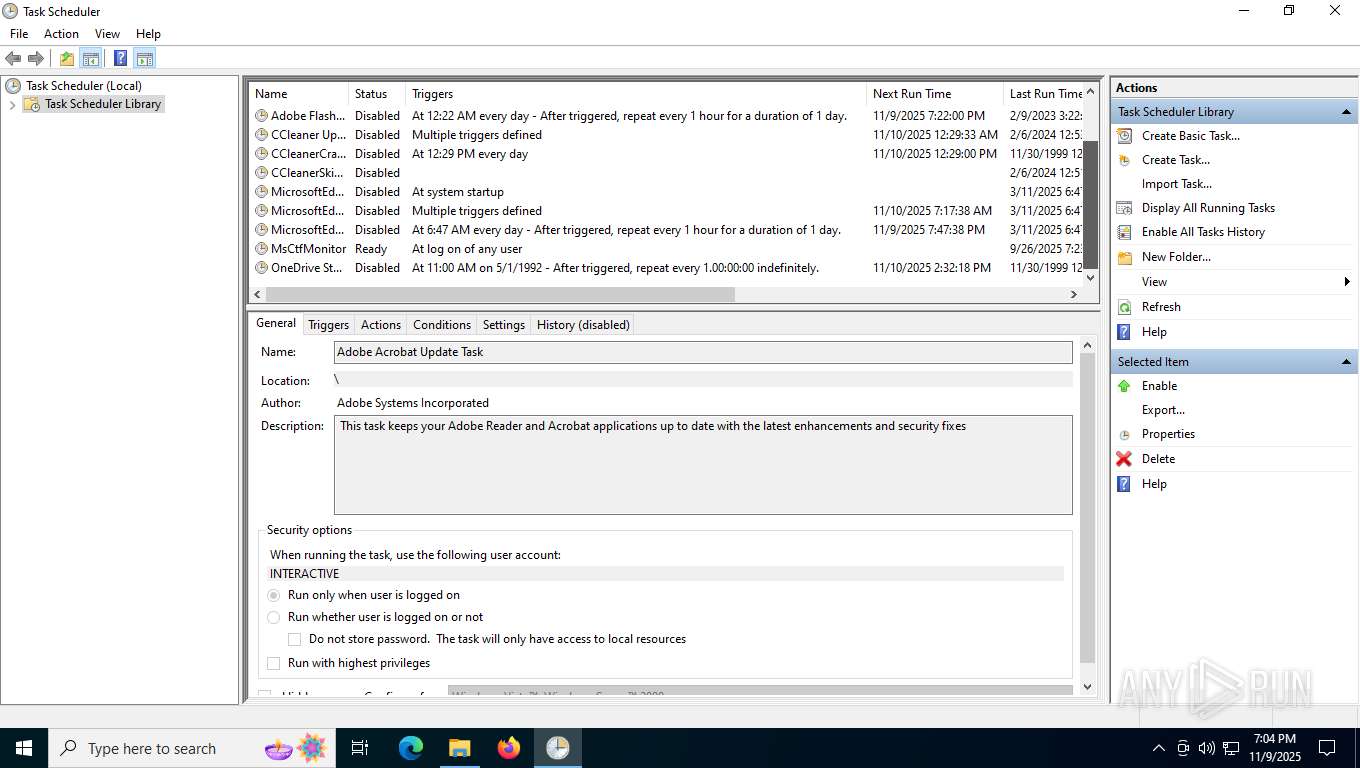
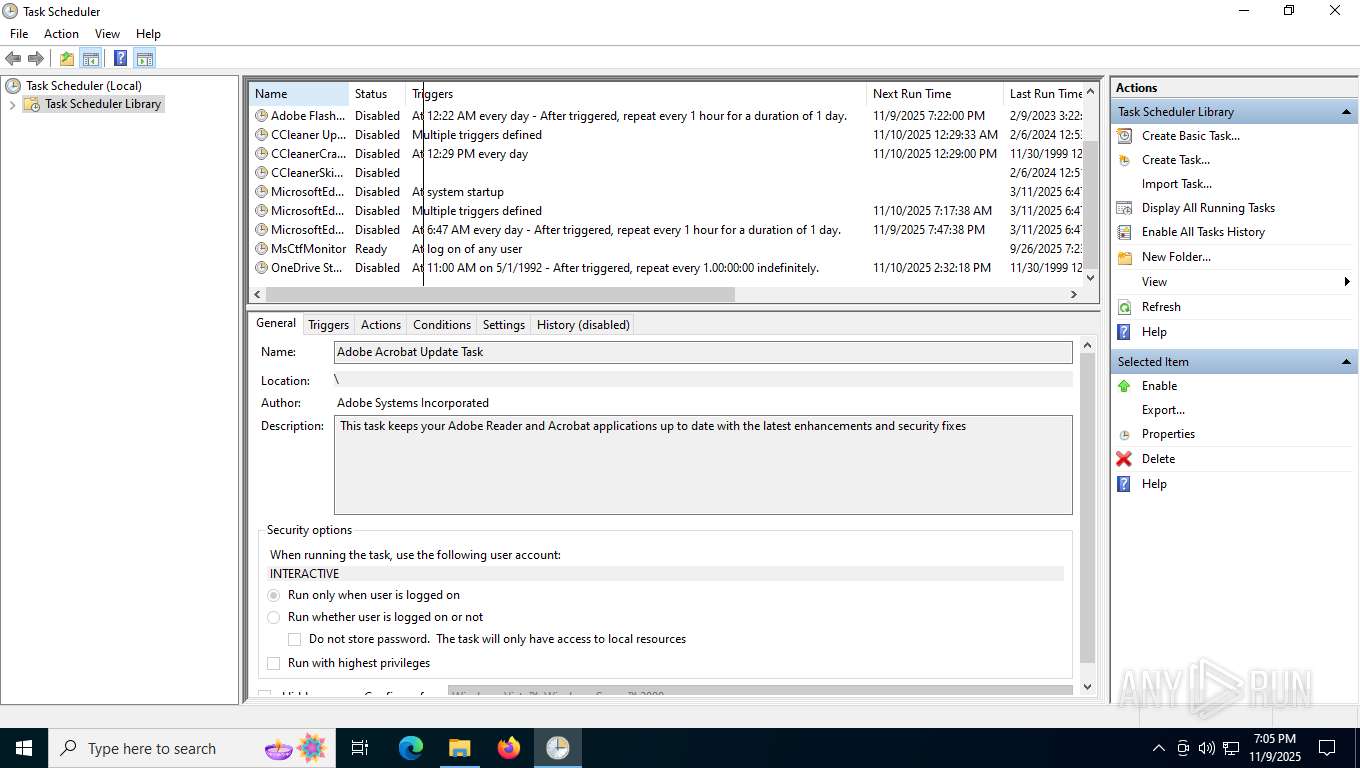
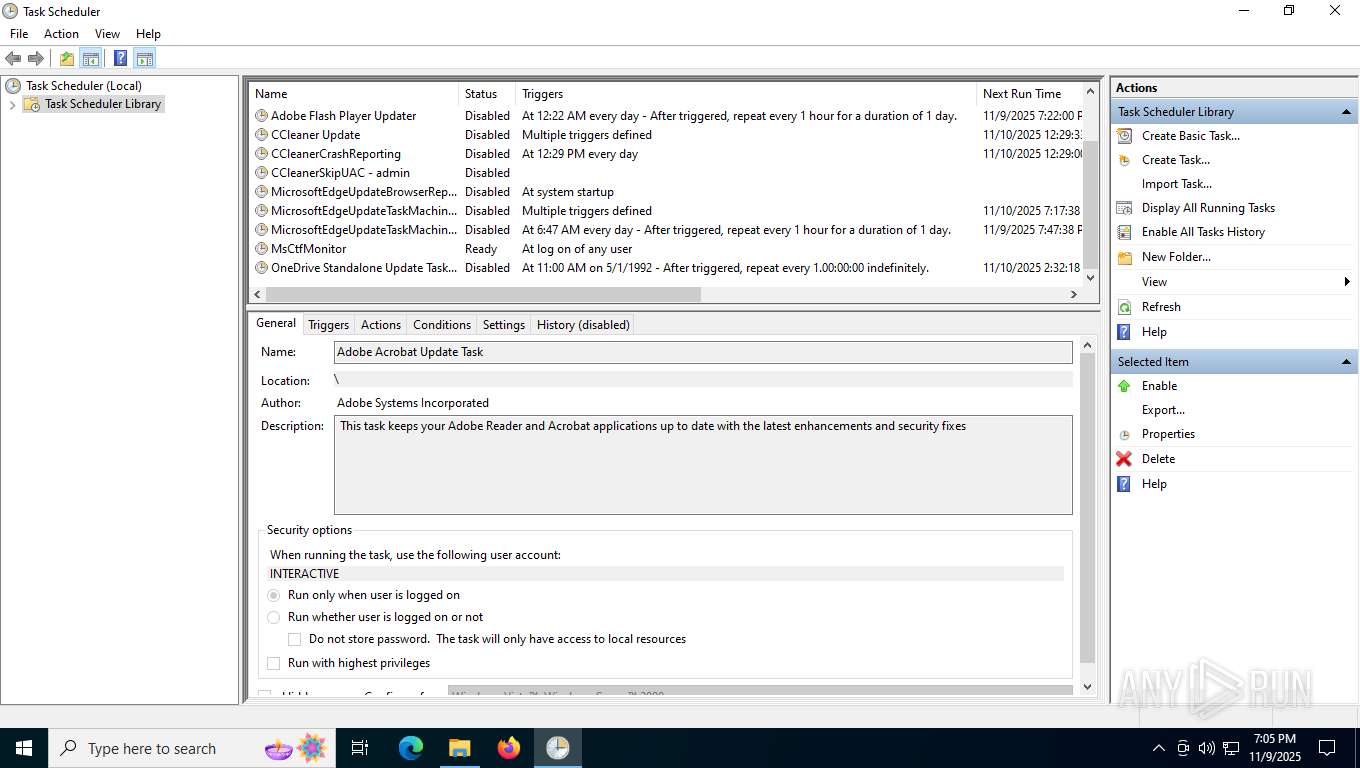
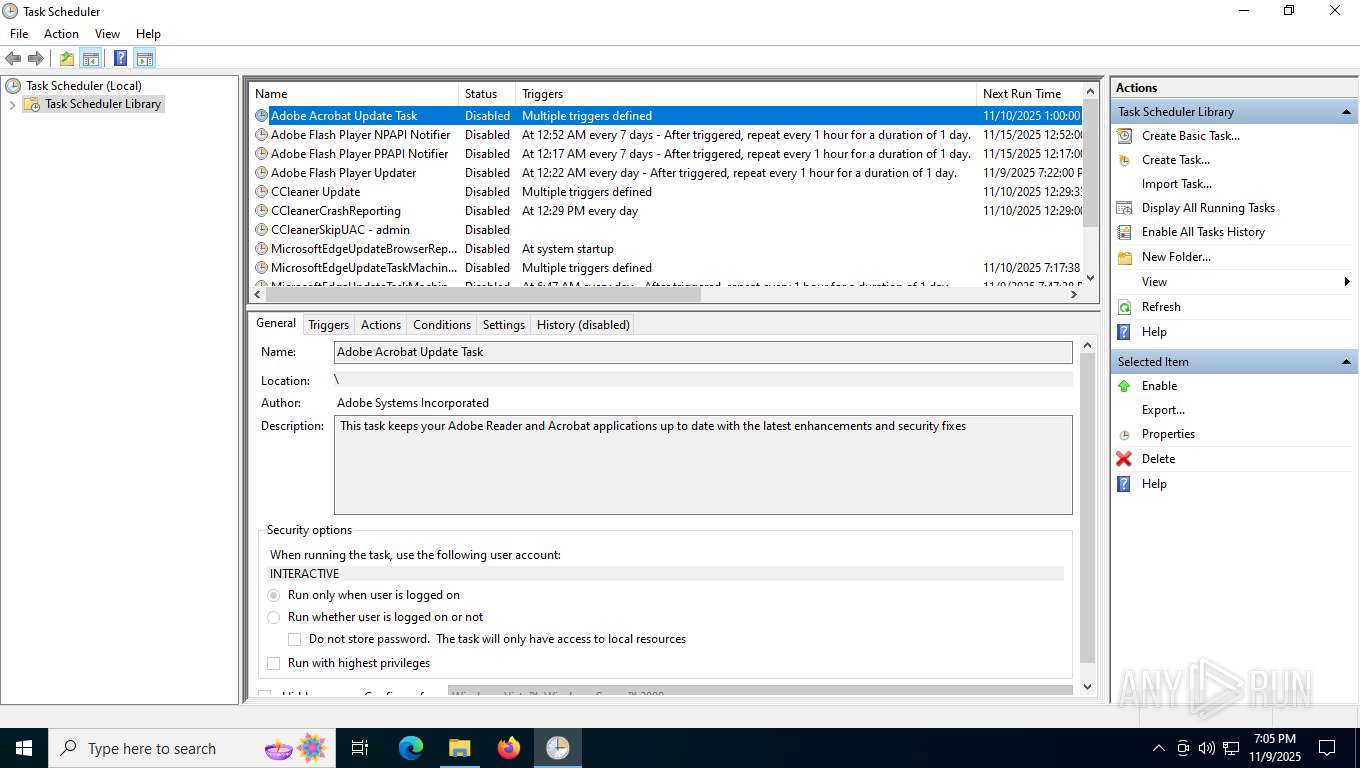
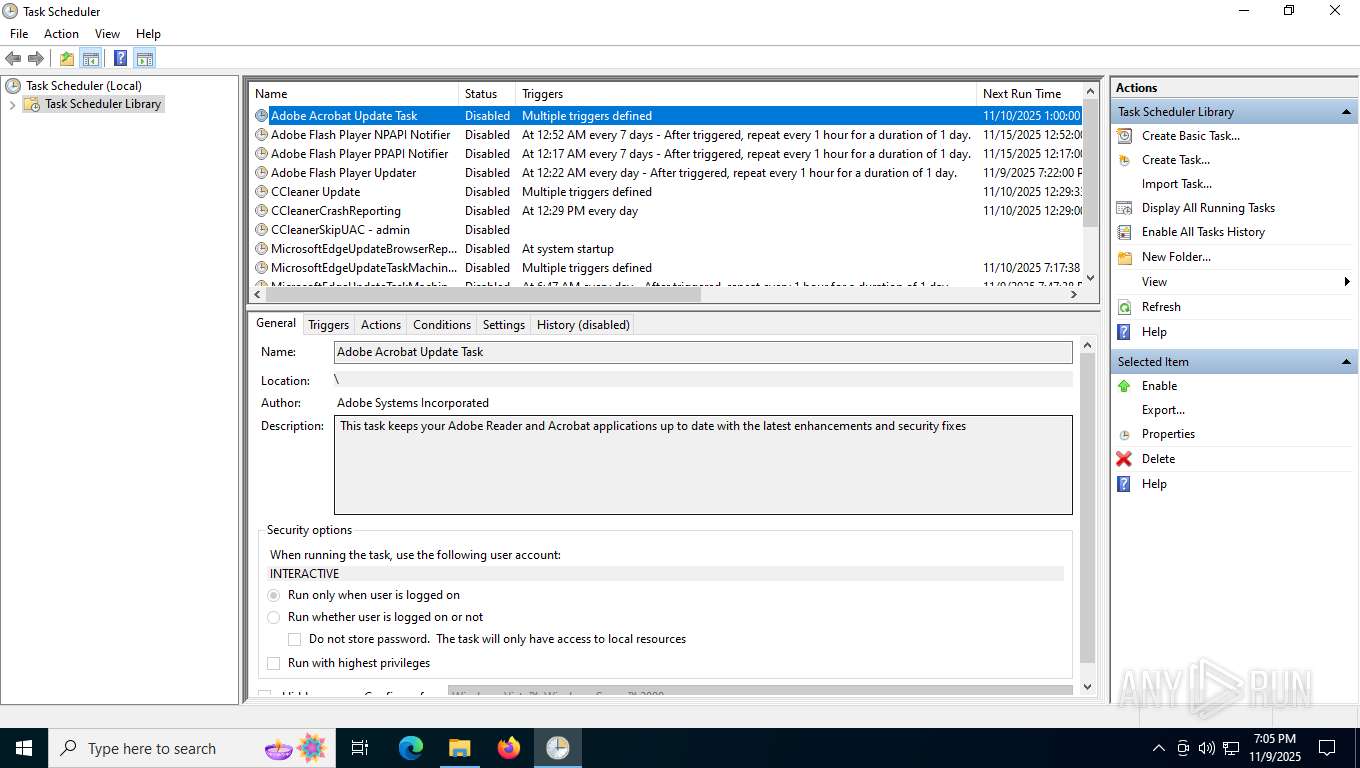
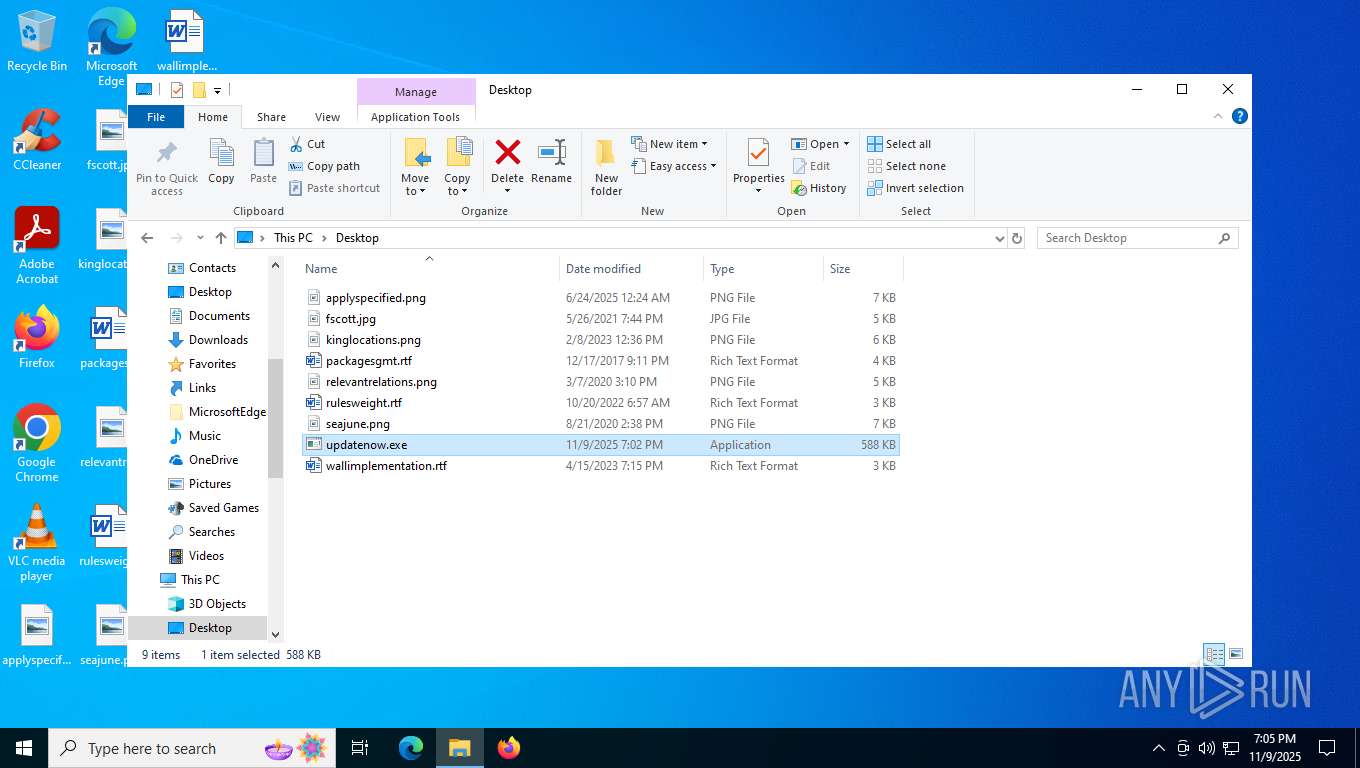
Manual execution by a user
- updatenow.exe (PID: 5972)
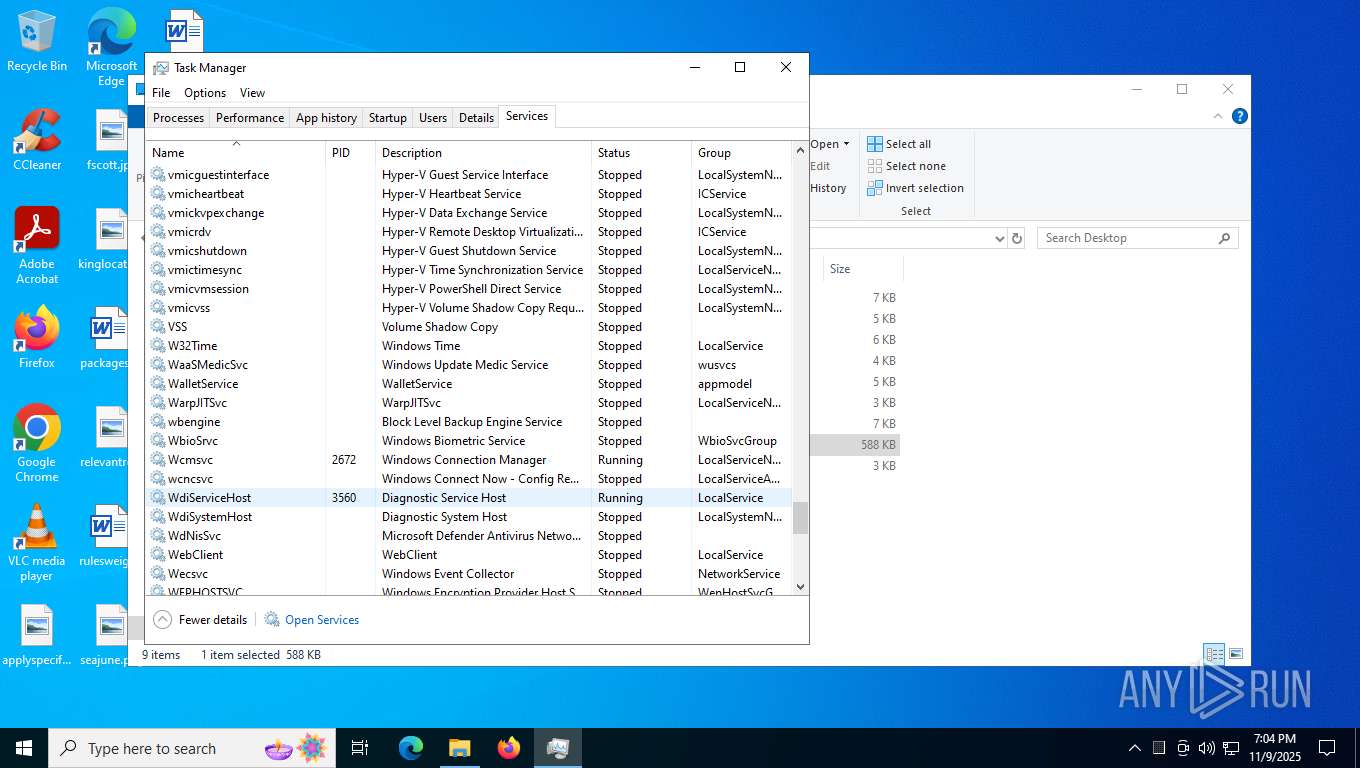
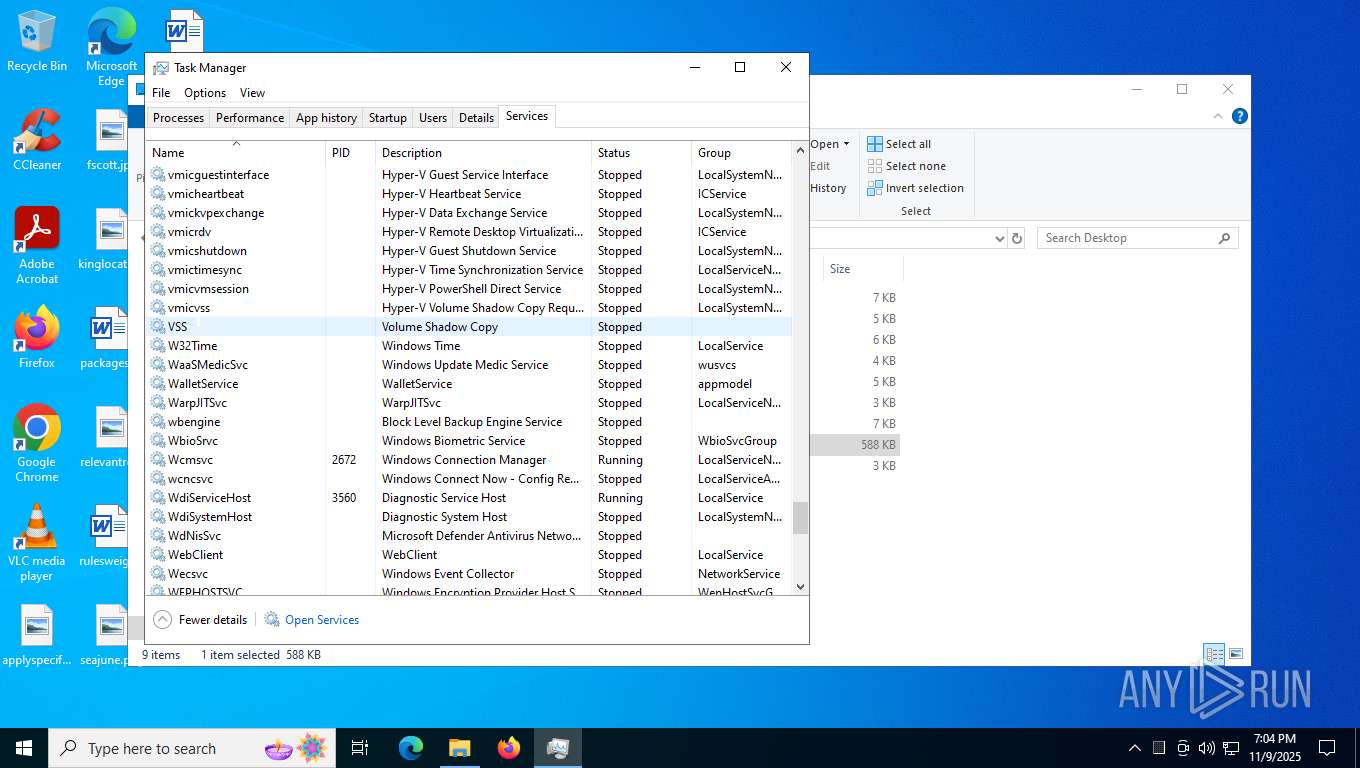
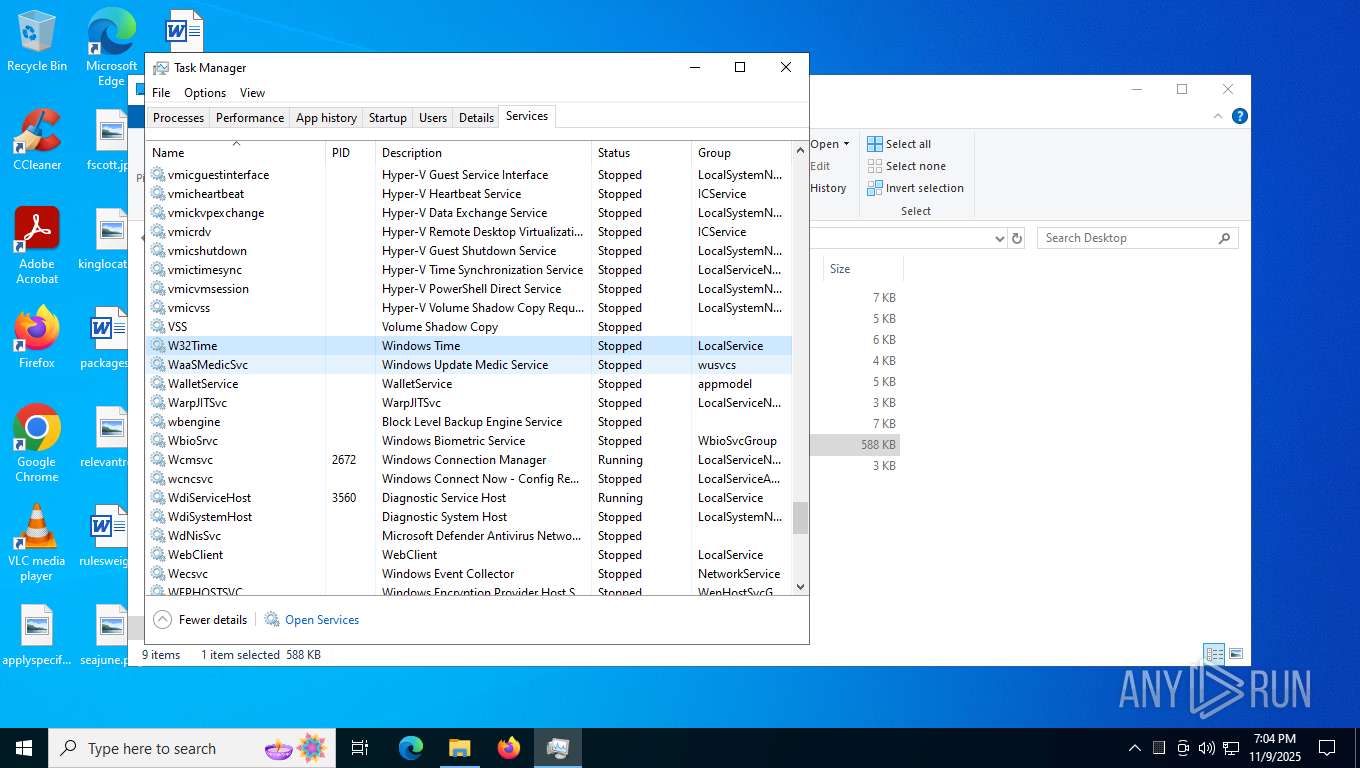
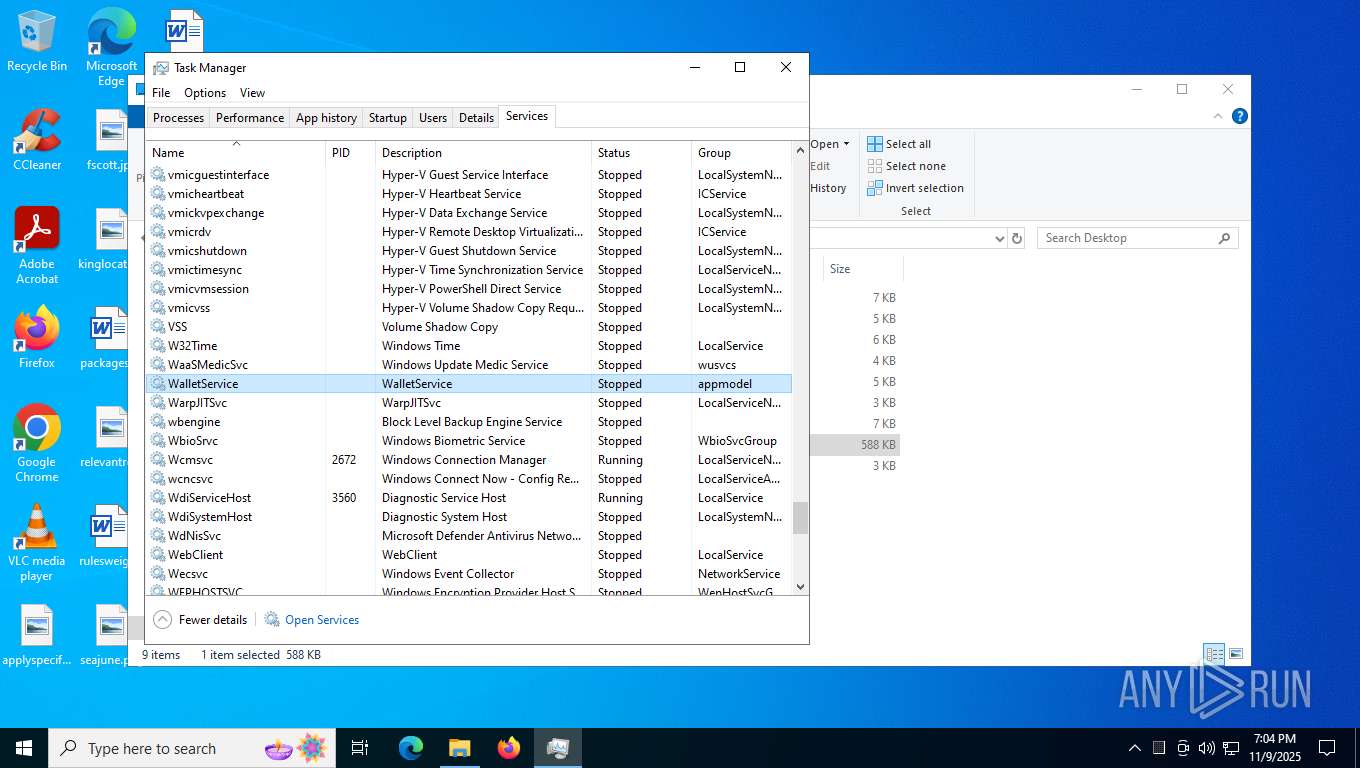
- Taskmgr.exe (PID: 3420)
- Taskmgr.exe (PID: 3696)
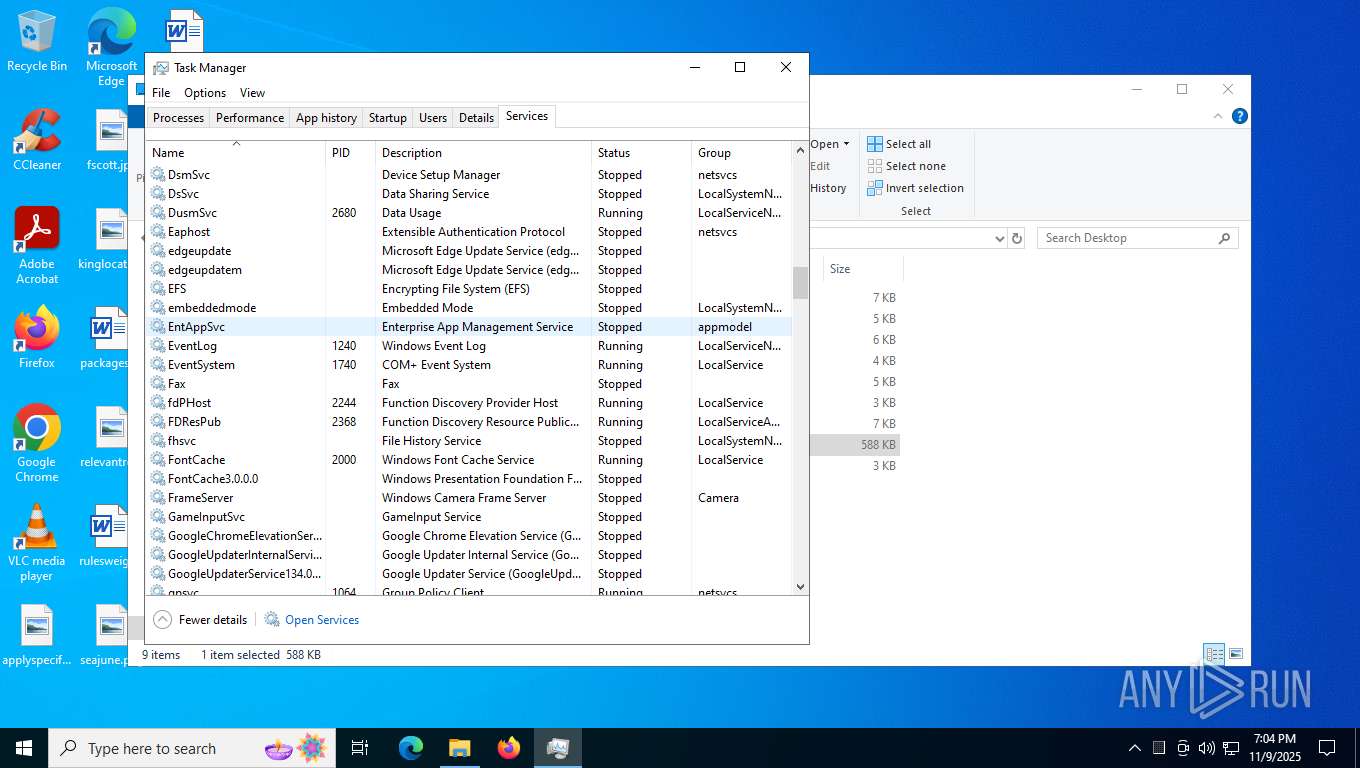
- mmc.exe (PID: 6776)
- mmc.exe (PID: 6264)
Checks proxy server information
- slui.exe (PID: 2820)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 3696)
- mmc.exe (PID: 6264)
Reads the software policy settings
- slui.exe (PID: 2820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(6252) RegSvcs.exe
Hosts (1)cp8nl.hyperhost.ua
Ports (1)587
Protocolsmtp
Usernameblessed4ever@genesio.top
Passwordcy+G_(979n9N
(PID) Process(1784) RegSvcs.exe
Hosts (1)cp8nl.hyperhost.ua
Ports (1)587
Protocolsmtp
Usernameblessed4ever@genesio.top
Passwordcy+G_(979n9N
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:08:30 11:16:49+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 356352 |
| InitializedDataSize: | 249856 |
| UninitializedDataSize: | 778240 |
| EntryPoint: | 0x115060 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
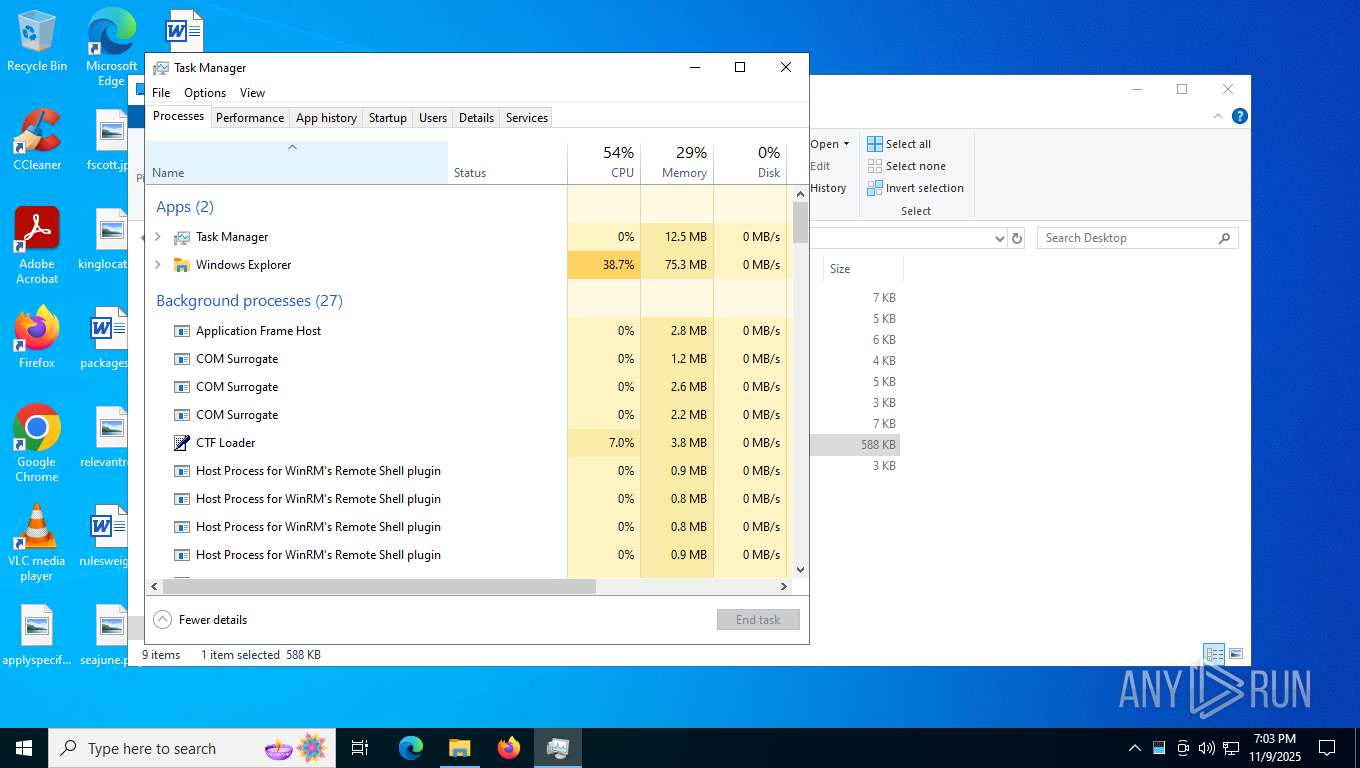
Total processes
157
Monitored processes
10
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1784 | "C:\Users\admin\Desktop\updatenow.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | updatenow.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
AgentTesla(PID) Process(1784) RegSvcs.exe Hosts (1)cp8nl.hyperhost.ua Ports (1)587 Protocolsmtp Usernameblessed4ever@genesio.top Passwordcy+G_(979n9N | |||||||||||||||
| 2276 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2820 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3420 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3696 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5392 | "C:\Users\admin\AppData\Local\Temp\updatenow.exe" | C:\Users\admin\AppData\Local\Temp\updatenow.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5972 | "C:\Users\admin\Desktop\updatenow.exe" | C:\Users\admin\Desktop\updatenow.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6252 | "C:\Users\admin\AppData\Local\Temp\updatenow.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | updatenow.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
AgentTesla(PID) Process(6252) RegSvcs.exe Hosts (1)cp8nl.hyperhost.ua Ports (1)587 Protocolsmtp Usernameblessed4ever@genesio.top Passwordcy+G_(979n9N | |||||||||||||||
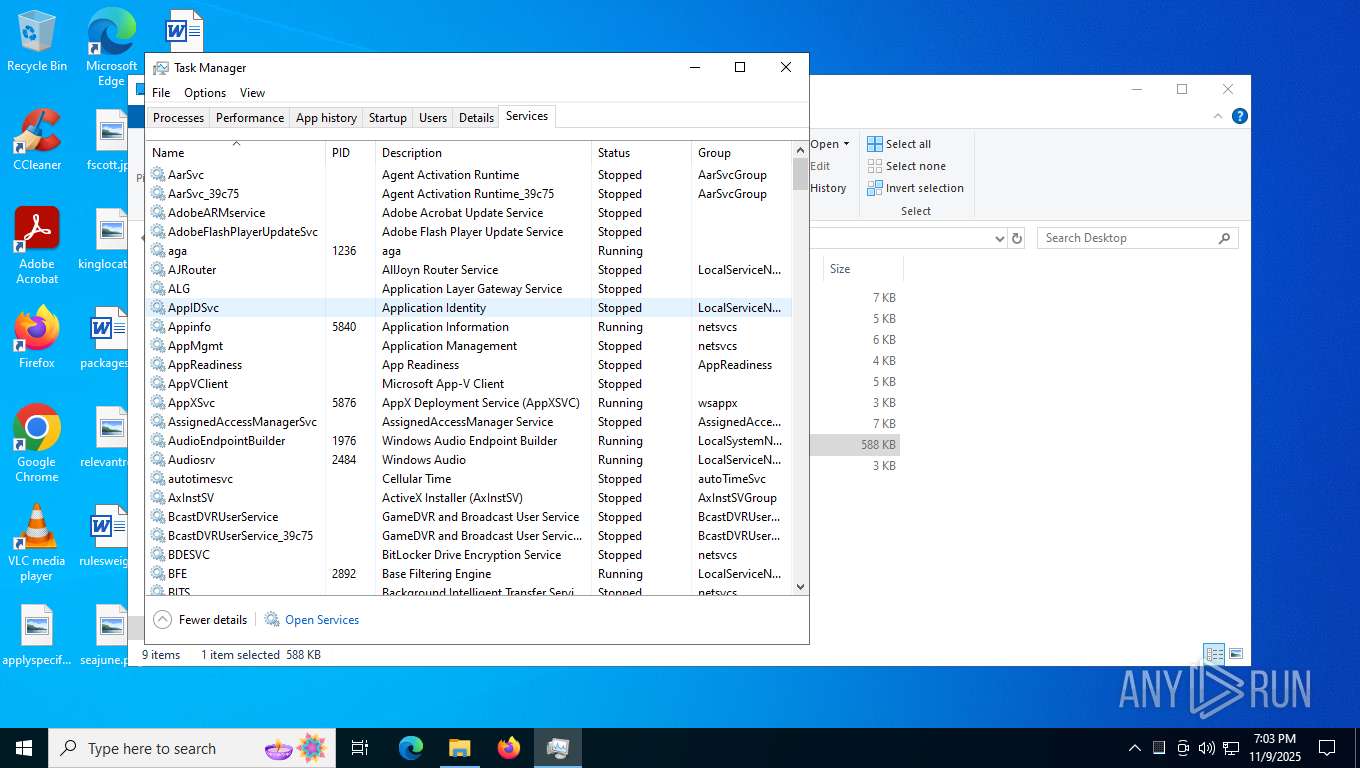
| 6264 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6776 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 156
Read events
8 146
Write events
8
Delete events
2
Modification events
| (PID) Process: | (3696) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
| (PID) Process: | (3696) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 0D00000060000000600000006800000068000000E3010000DC010000000001000000008000000080D8010080DF010080000100018900000034000000310300008C020000E80300000000000000000000000000000F000000010000000000000058AA2910F67F00000000000000000000000000002E0100001E0000008990000000000000FF00000001015002000000000D0000000000000098AA2910F67F00000000000000000000FFFFFFFF960000001E0000008B900000010000000000000000101001000000000300000000000000B0AA2910F67F00000000000000000000FFFFFFFF780000001E0000008C900000020000000000000001021200000000000400000000000000C8AA2910F67F00000000000000000000FFFFFFFF960000001E0000008D900000030000000000000000011001000000000200000000000000E8AA2910F67F00000000000000000000FFFFFFFF320000001E0000008A90000004000000000000000008200100000000050000000000000000AB2910F67F00000000000000000000FFFFFFFFC80000001E0000008E90000005000000000000000001100100000000060000000000000028AB2910F67F00000000000000000000FFFFFFFF040100001E0000008F90000006000000000000000001100100000000070000000000000050AB2910F67F00000000000000000000FFFFFFFF49000000490000009090000007000000000000000004250000000000080000000000000080AA2910F67F00000000000000000000FFFFFFFF49000000490000009190000008000000000000000004250000000000090000000000000070AB2910F67F00000000000000000000FFFFFFFF490000004900000092900000090000000000000000042508000000000A0000000000000088AB2910F67F00000000000000000000FFFFFFFF4900000049000000939000000A0000000000000000042508000000000B00000000000000A8AB2910F67F00000000000000000000FFFFFFFF490000004900000039A000000B0000000000000000042509000000001C00000000000000C8AB2910F67F00000000000000000000FFFFFFFFC8000000490000003AA000000C0000000000000000011009000000001D00000000000000F0AB2910F67F00000000000000000000FFFFFFFF64000000490000004CA000000D0000000000000000021508000000001E0000000000000010AC2910F67F00000000000000000000FFFFFFFF64000000490000004DA000000E000000000000000002150800000000030000000A000000010000000000000058AA2910F67F0000000000000000000000000000D70000001E0000008990000000000000FF00000001015002000000000400000000000000C8AA2910F67F0000000000000000000001000000960000001E0000008D900000010000000000000001011000000000000300000000000000B0AA2910F67F00000000000000000000FFFFFFFF640000001E0000008C900000020000000000000000021000000000000C0000000000000040AC2910F67F0000000000000000000003000000640000001E00000094900000030000000000000001021000000000000D0000000000000068AC2910F67F00000000000000000000FFFFFFFF640000001E00000095900000040000000000000000011001000000000E0000000000000090AC2910F67F0000000000000000000005000000320000001E00000096900000050000000000000001042001000000000F00000000000000B8AC2910F67F0000000000000000000006000000320000001E00000097900000060000000000000001042001000000001000000000000000D8AC2910F67F0000000000000000000007000000460000001E00000098900000070000000000000001011001000000001100000000000000F8AC2910F67F00000000000000000000FFFFFFFF640000001E0000009990000008000000000000000001100100000000060000000000000028AB2910F67F0000000000000000000009000000040100001E0000008F9000000900000000000000010110010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000040000000B000000010000000000000058AA2910F67F0000000000000000000000000000D70000001E0000009E90000000000000FF0000000101500200000000120000000000000020AD2910F67F00000000000000000000FFFFFFFF2D0000001E0000009B90000001000000000000000004200100000000140000000000000040AD2910F67F00000000000000000000FFFFFFFF640000001E0000009D90000002000000000000000001100100000000130000000000000068AD2910F67F00000000000000000000FFFFFFFF640000001E0000009C900000030000000000000000011001000000000300000000000000B0AA2910F67F00000000000000000000FFFFFFFF640000001E0000008C90000004000000000000000102100000000000070000000000000050AB2910F67F000000000000000000000500000049000000490000009090000005000000000000000104210000000000080000000000000080AA2910F67F000000000000000000000600000049000000490000009190000006000000000000000104210000000000090000000000000070AB2910F67F0000000000000000000007000000490000004900000092900000070000000000000001042108000000000A0000000000000088AB2910F67F0000000000000000000008000000490000004900000093900000080000000000000001042108000000000B00000000000000A8AB2910F67F0000000000000000000009000000490000004900000039A00000090000000000000001042109000000001C00000000000000C8AB2910F67F000000000000000000000A00000064000000490000003AA000000A00000000000000000110090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000008000000010000000000000058AA2910F67F0000000000000000000000000000C60000001E000000B090000000000000FF0000000101500200000000150000000000000088AD2910F67F00000000000000000000FFFFFFFF6B0000001E000000B1900000010000000000000000042500000000001600000000000000B8AD2910F67F00000000000000000000FFFFFFFF6B0000001E000000B2900000020000000000000000042500000000001800000000000000E0AD2910F67F00000000000000000000FFFFFFFF6B0000001E000000B490000003000000000000000004250000000000170000000000000008AE2910F67F00000000000000000000FFFFFFFF6B0000001E000000B390000004000000000000000004250000000000190000000000000040AE2910F67F00000000000000000000FFFFFFFFA00000001E000000B5900000050000000000000000042001000000001A0000000000000070AE2910F67F00000000000000000000FFFFFFFF7D0000001E000000B6900000060000000000000000042001000000001B00000000000000A0AE2910F67F00000000000000000000FFFFFFFF7D0000001E000000B790000007000000000000000004200100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA00000000000000000000000000000000000000000000009D200000200000009100000064000000320000006400000050000000320000003200000028000000500000003C0000005000000050000000320000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C00000050000000500000009700000032000000780000003200000050000000500000005000000050000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA000000000000000000000000000000000000009D200000200000009100000064000000320000009700000050000000320000003200000028000000500000003C000000500000005000000032000000500000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C0000005000000064000000780000003200000078000000780000003200000050000000500000005000000050000000C8000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C0000002D0000002E0000002F00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000002000000030000000400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001000000000000000000000000000000 | |||
| (PID) Process: | (6264) mmc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\MMC\SnapIns\FX:{c7b8fb06-bfe1-4c2e-9217-7a69a95bbac4} |
| Operation: | write | Name: | HelpTopic |
Value: C:\WINDOWS\Help\taskscheduler.chm | |||
| (PID) Process: | (6264) mmc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\MMC\SnapIns\FX:{c7b8fb06-bfe1-4c2e-9217-7a69a95bbac4} |
| Operation: | write | Name: | LinkedHelpTopics |
Value: C:\WINDOWS\Help\taskscheduler.chm | |||
| (PID) Process: | (6264) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6264) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File1 |
Value: C:\WINDOWS\system32\taskschd.msc | |||
| (PID) Process: | (6264) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File2 |
Value: C:\WINDOWS\system32\devmgmt.msc | |||
| (PID) Process: | (6264) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File3 |
Value: C:\WINDOWS\system32\gpedit.msc | |||
| (PID) Process: | (6264) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File4 |
Value: C:\WINDOWS\System32\services.msc | |||
Executable files
0
Suspicious files
5
Text files
3
Unknown types
0
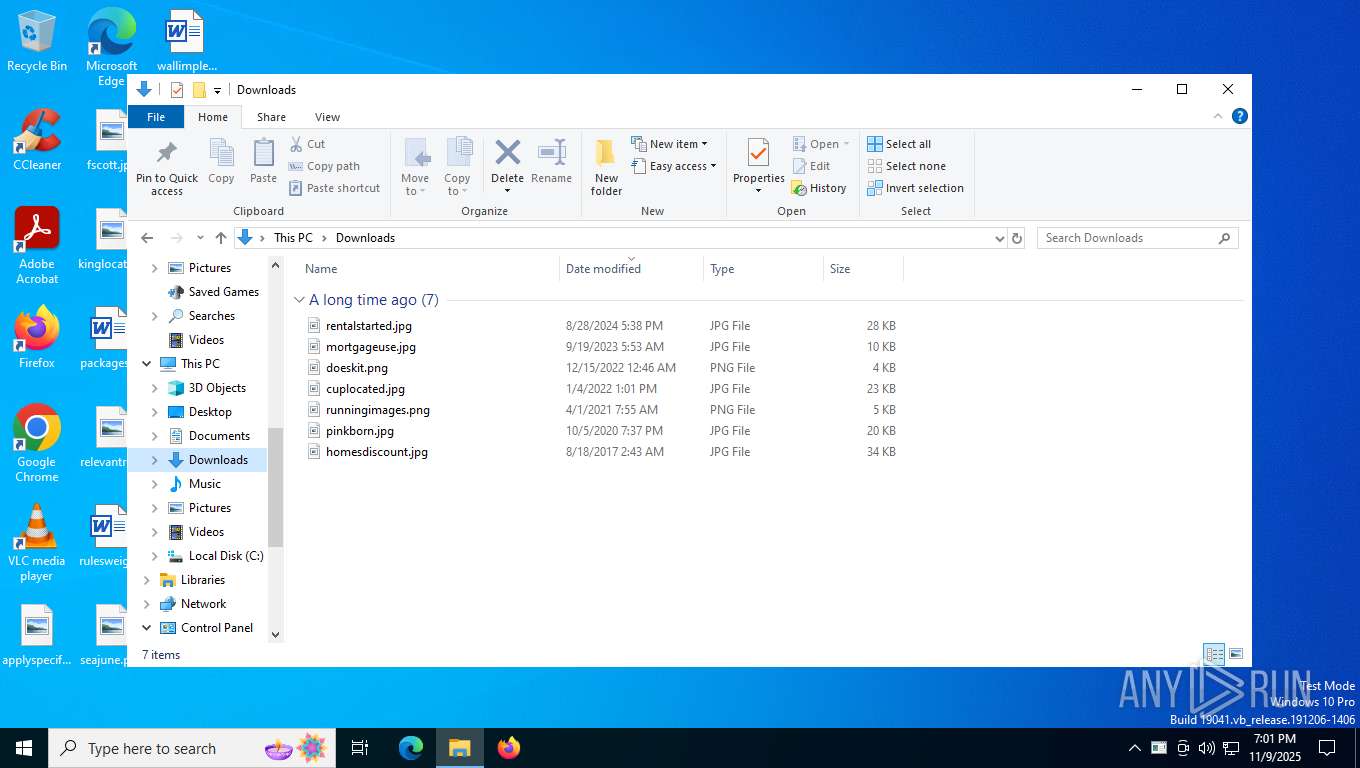
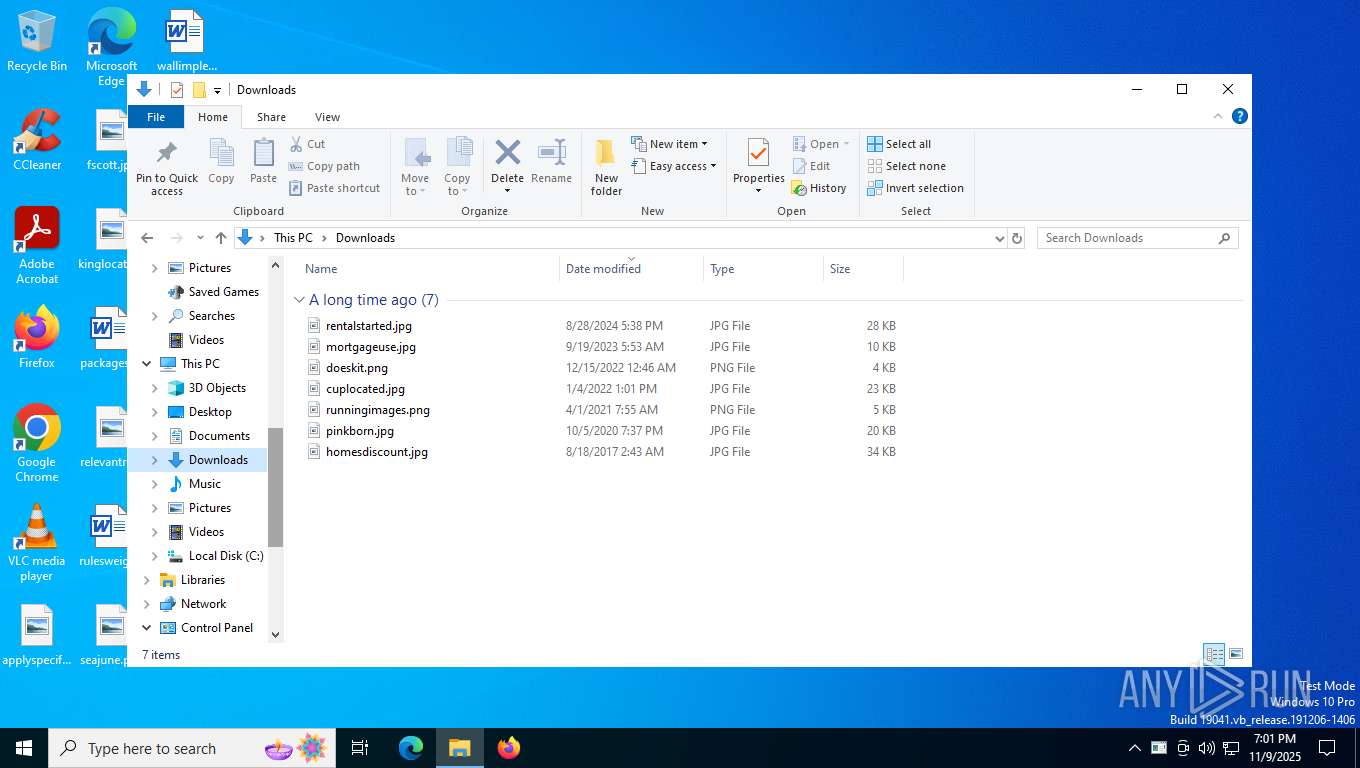
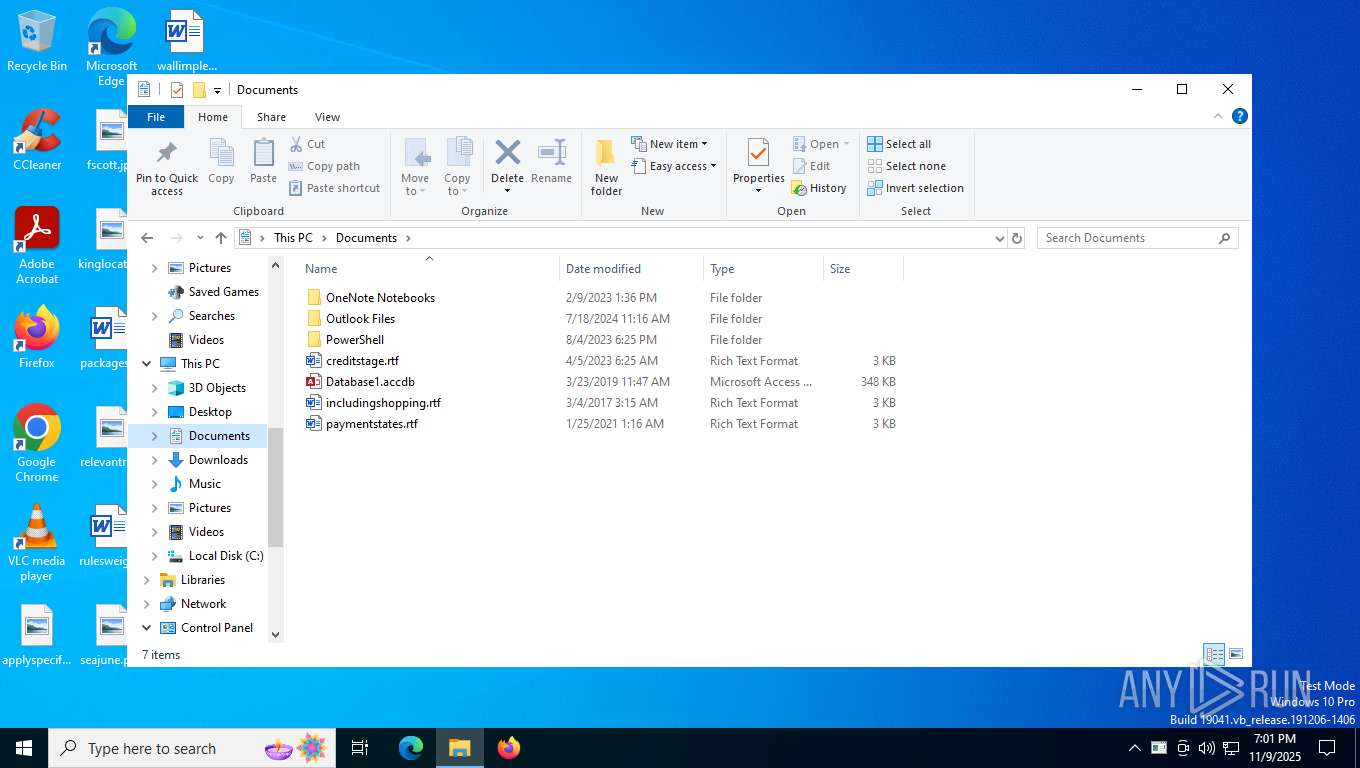
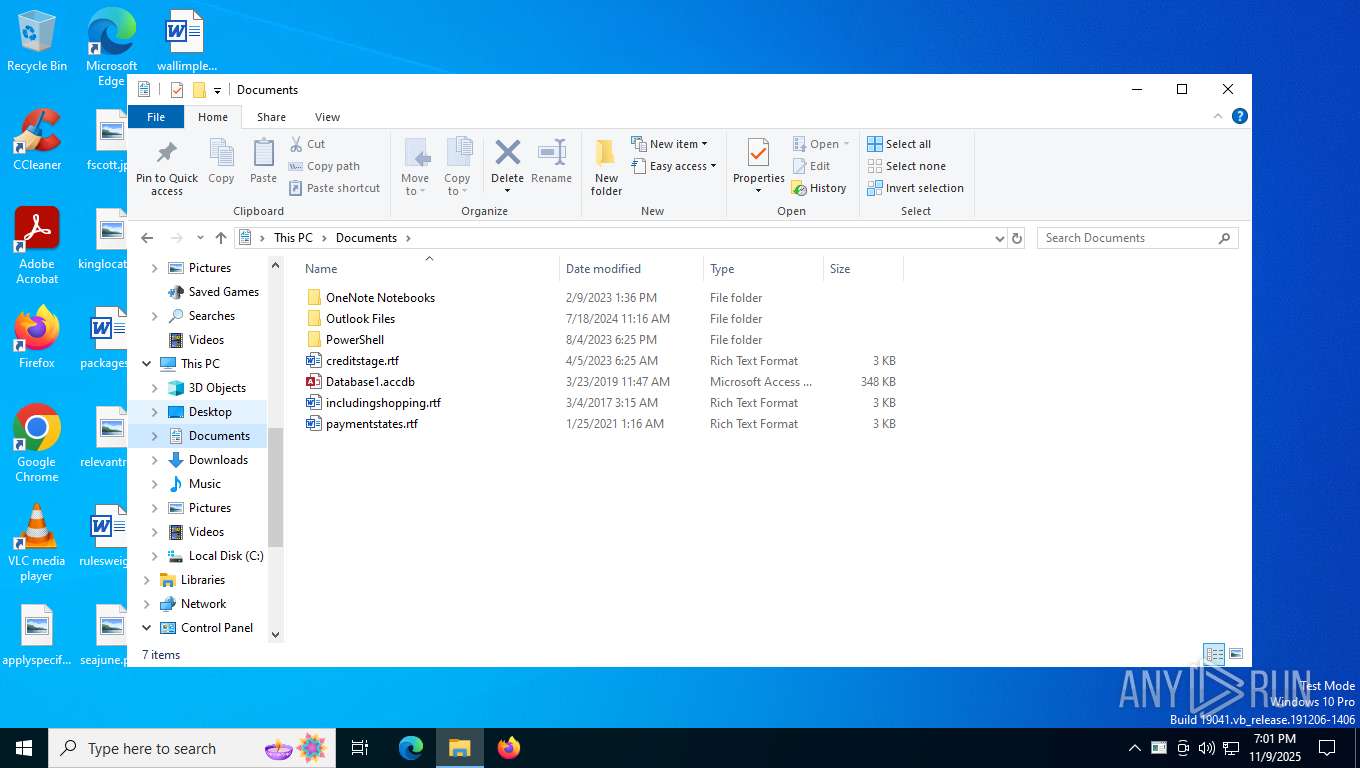
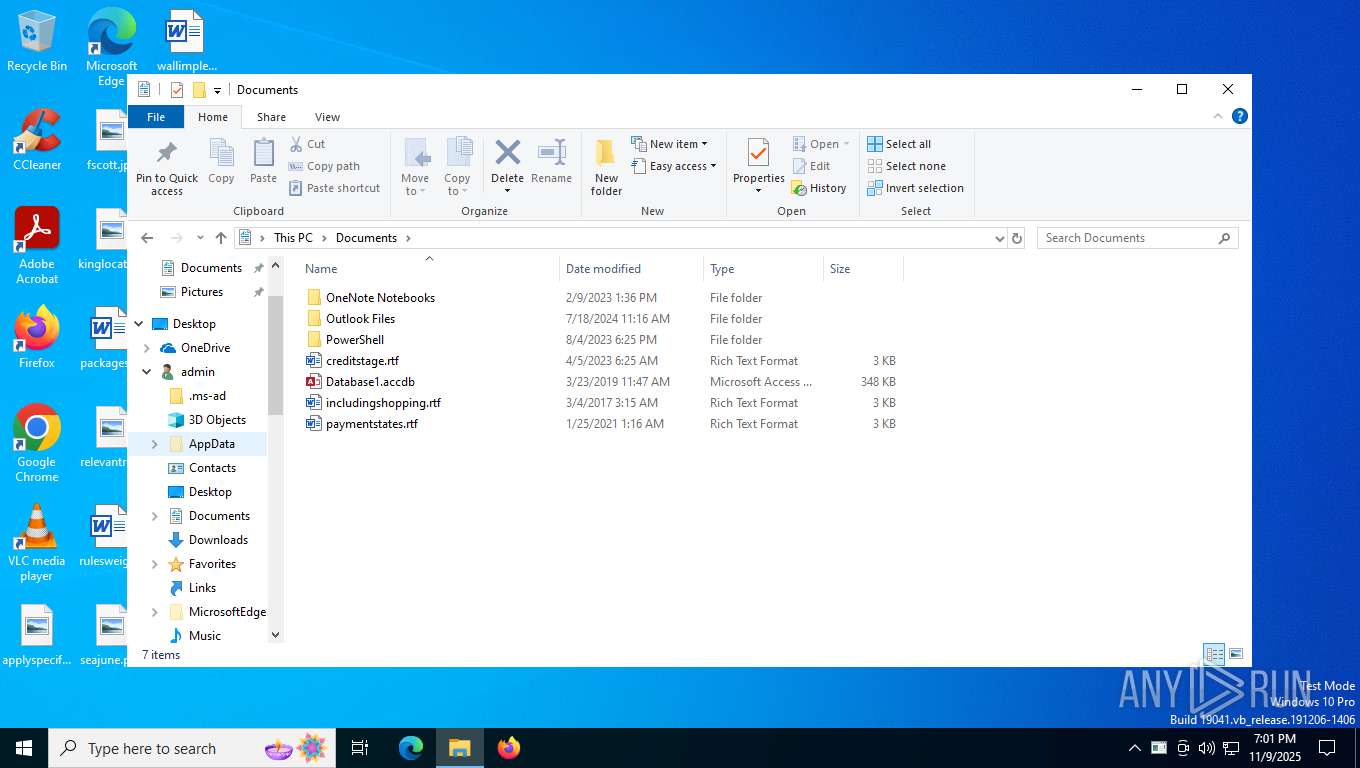
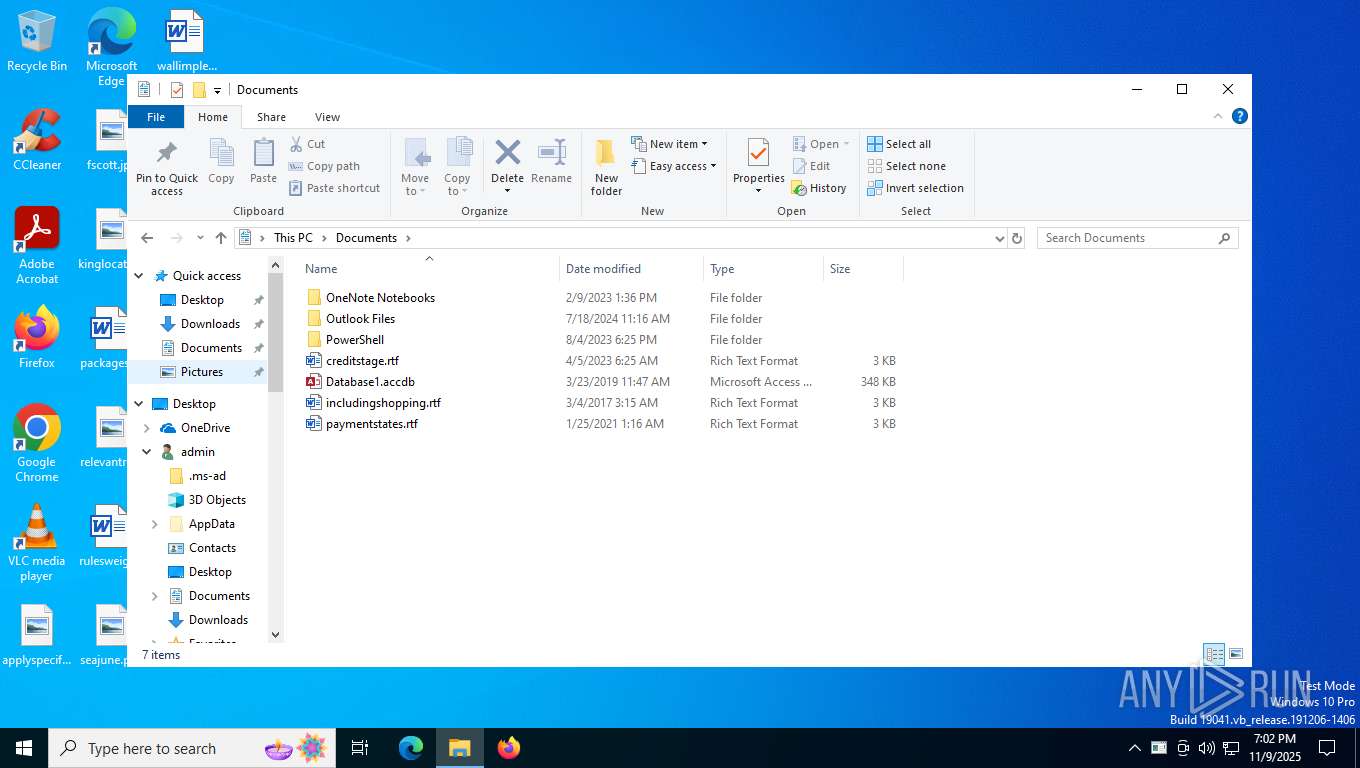
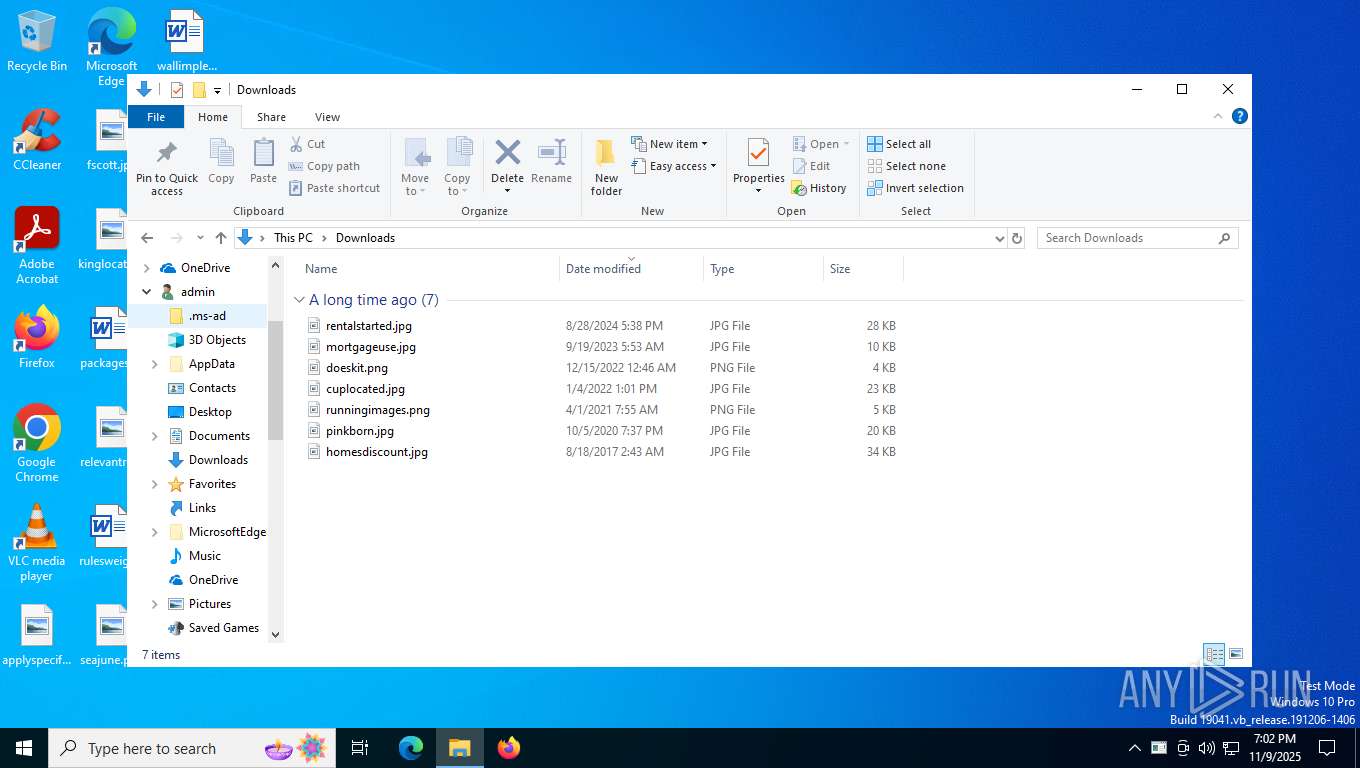
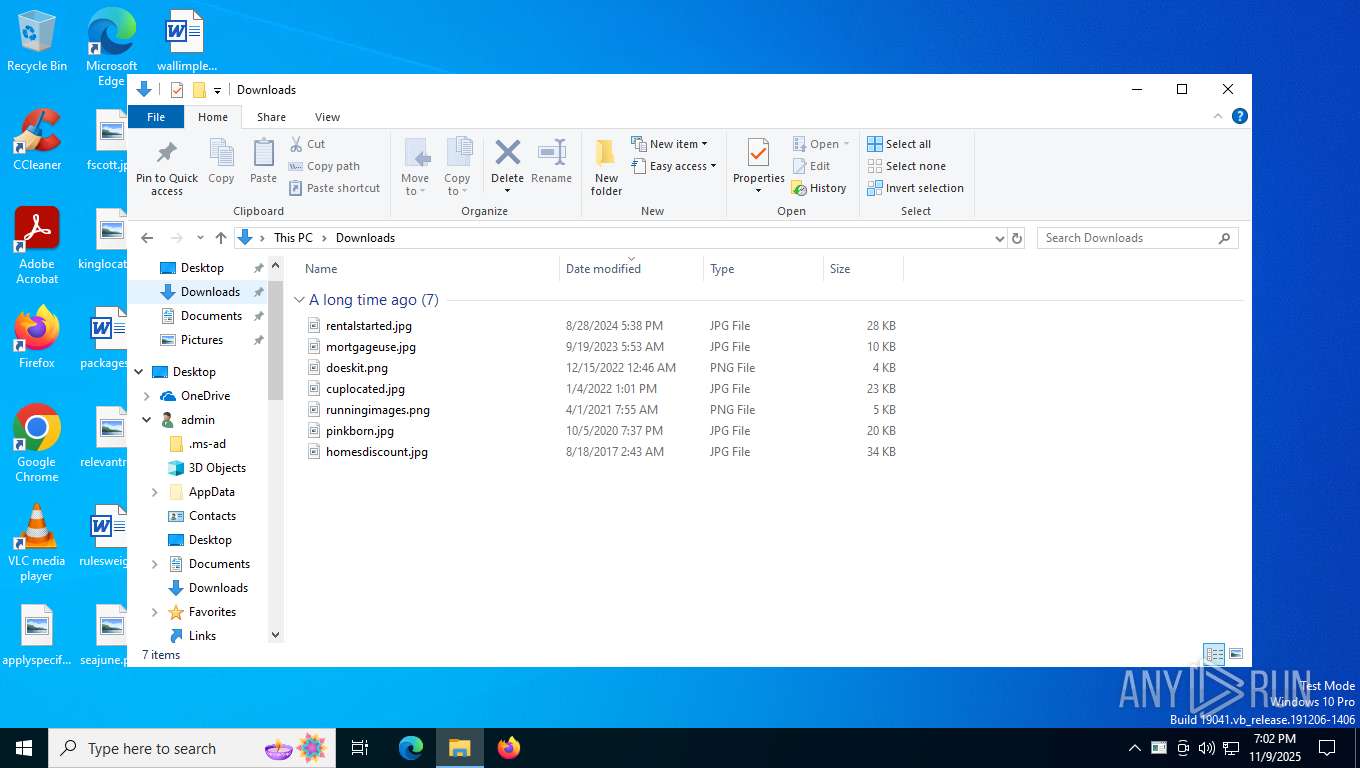
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5392 | updatenow.exe | C:\Users\admin\AppData\Local\Temp\aut203F.tmp | binary | |
MD5:0819CEF99899BB813BA1C0BC781AE3C1 | SHA256:3968F03FD487A9DB3B65C92734FD60ABD37C444FFB9CBD7773558F89F618DC0E | |||
| 5392 | updatenow.exe | C:\Users\admin\AppData\Local\Temp\aut202F.tmp | binary | |
MD5:1496D7E9B9A3C19F865A4CC7F48A2829 | SHA256:35A3884BEF5792F25EB48EF4AF6DD03CE079D0452A8558DDC0B229C8E865C47F | |||
| 5392 | updatenow.exe | C:\Users\admin\AppData\Local\Temp\Glagolitic | binary | |
MD5:B263C4D880A9125F712A36FD5607B58B | SHA256:CE9E4D62E6CEA290AA446BE1F4D25D64B54FE60A9911E25524525F2936DF4012 | |||
| 5392 | updatenow.exe | C:\Users\admin\AppData\Local\Temp\snaith | text | |
MD5:E0C174FA47E17E2F84249A0749F98569 | SHA256:03C54F7BA107E5B75523099068F0B4395743D5A27ADA9FC250120874692F58BC | |||
| 5972 | updatenow.exe | C:\Users\admin\AppData\Local\Temp\autDF49.tmp | binary | |
MD5:1496D7E9B9A3C19F865A4CC7F48A2829 | SHA256:35A3884BEF5792F25EB48EF4AF6DD03CE079D0452A8558DDC0B229C8E865C47F | |||
| 5972 | updatenow.exe | C:\Users\admin\AppData\Local\Temp\autDF59.tmp | binary | |
MD5:0819CEF99899BB813BA1C0BC781AE3C1 | SHA256:3968F03FD487A9DB3B65C92734FD60ABD37C444FFB9CBD7773558F89F618DC0E | |||
| 3696 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\3534848bb9f4cb71\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
| 6264 | mmc.exe | C:\Users\admin\AppData\Roaming\Microsoft\MMC\taskschd | xml | |
MD5:FC232DB7013AD5B2C4C2F015587BF285 | SHA256:E09D41F50E87CEFE485232FA2B5ED83CCD84364FA0E9BBD0B85762D9767D003C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
41
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1928 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5596 | MoUsoCoreWorker.exe | GET | 200 | 2.16.238.152:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6188 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | DE | binary | 401 b | whitelisted |
6188 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | DE | binary | 814 b | whitelisted |
6188 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | DE | binary | 402 b | whitelisted |
6188 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | DE | binary | 813 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5656 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1928 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6252 | RegSvcs.exe | 185.174.175.187:587 | cp8nl.hyperhost.ua | ITL LLC | UA | malicious |
1928 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1928 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5596 | MoUsoCoreWorker.exe | 2.16.238.152:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5524 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
cp8nl.hyperhost.ua |
| malicious |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
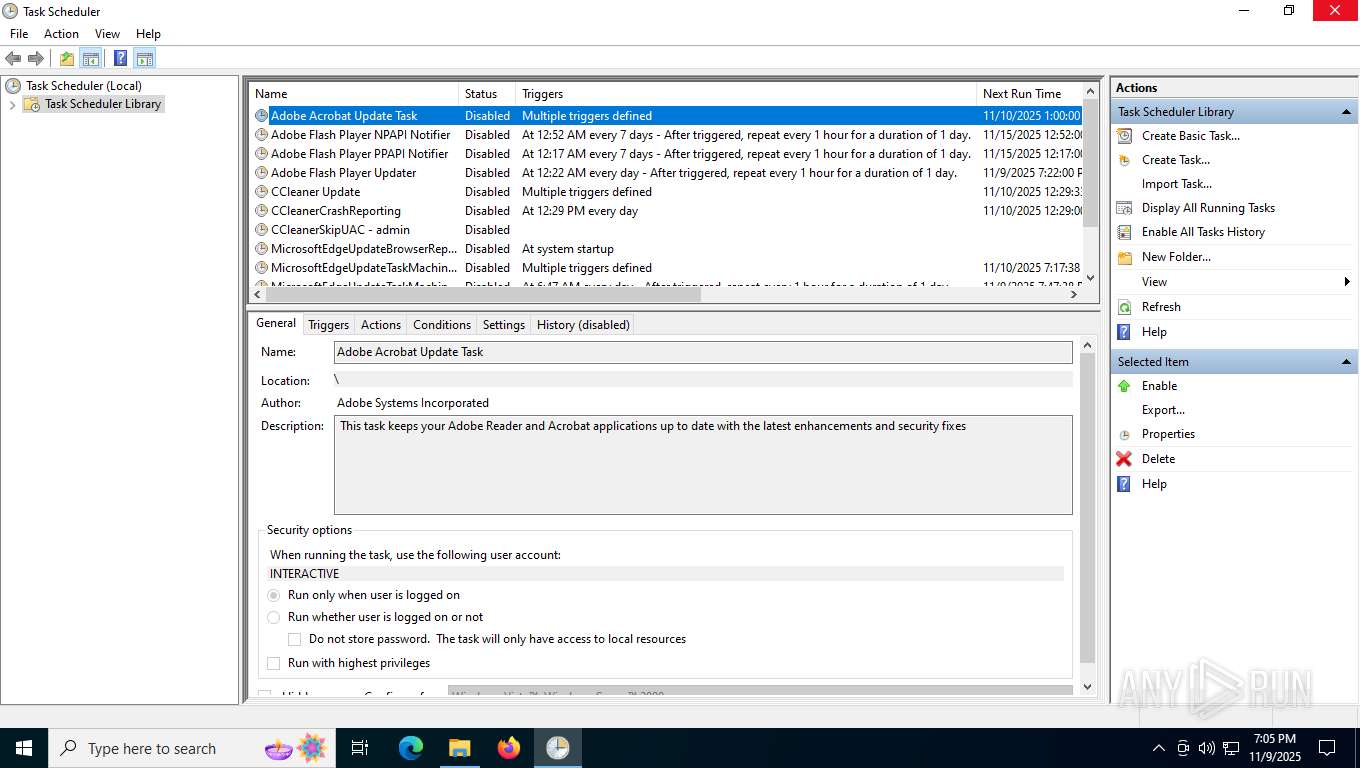
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|