| File name: | QuantumHacksv2.exe |
| Full analysis: | https://app.any.run/tasks/9a97c048-911f-4d30-8fa3-cc5b0cfc47cd |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 29, 2025, 01:59:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | AC2040D78A083A189723E1392A3428EE |
| SHA1: | AA8FE9D0108323673F8BA5D6043B3FA324A264CB |
| SHA256: | C1D24472DC3C469D7DBDA5CB07D46D22307C8D4F1118E498524E579F15EA9C35 |
| SSDEEP: | 98304:CbnKllghKmvuBPLIp0/o5Wt8COrAJEYk4ytWxuvQQWfgMnIhg4d25/aRh8WbsmvD:iPLXgQ |
MALICIOUS
LUMMA mutex has been found
- calc.exe (PID: 960)
- calc.exe (PID: 616)
Actions looks like stealing of personal data
- calc.exe (PID: 960)
- calc.exe (PID: 616)
LUMMA has been detected (YARA)
- calc.exe (PID: 960)
- calc.exe (PID: 616)
SUSPICIOUS
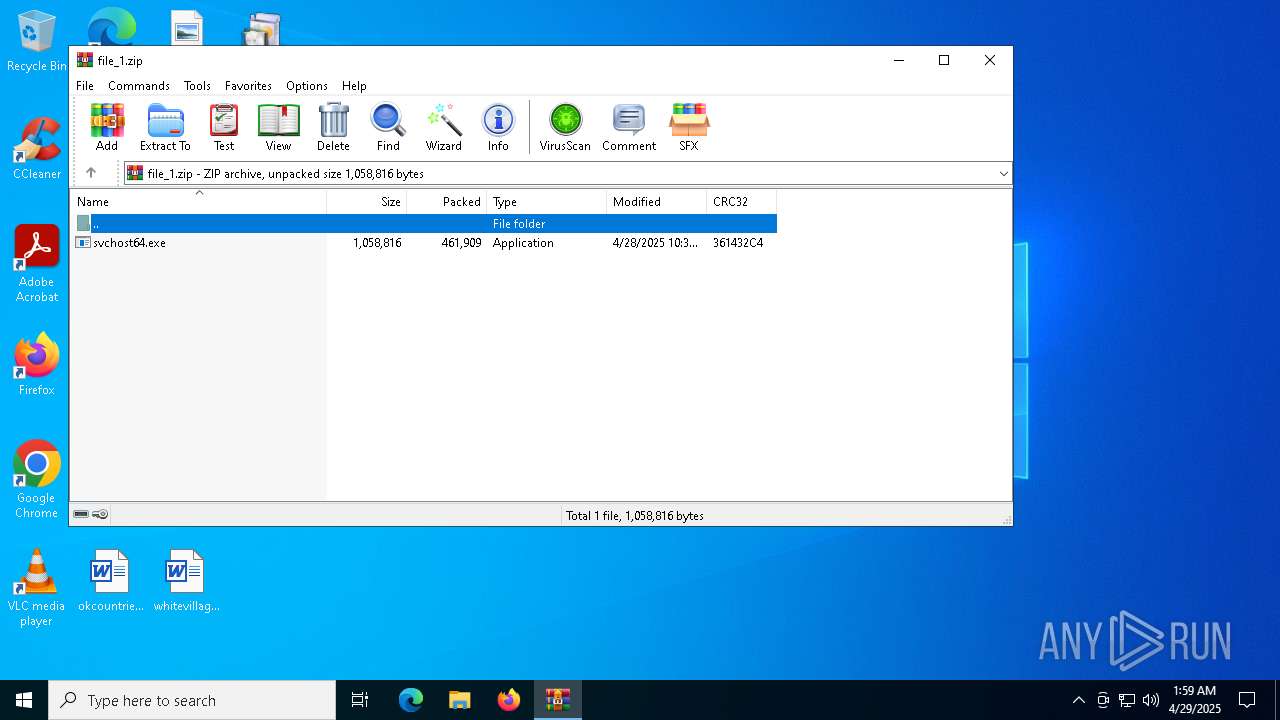
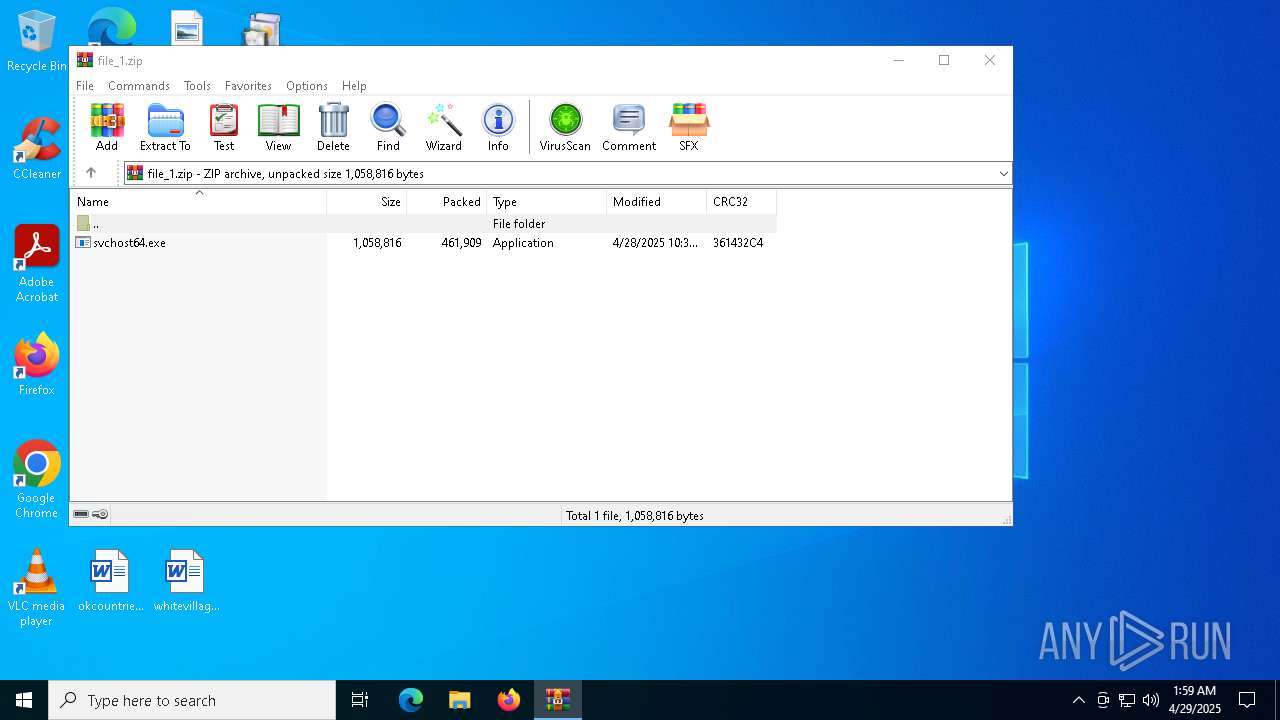
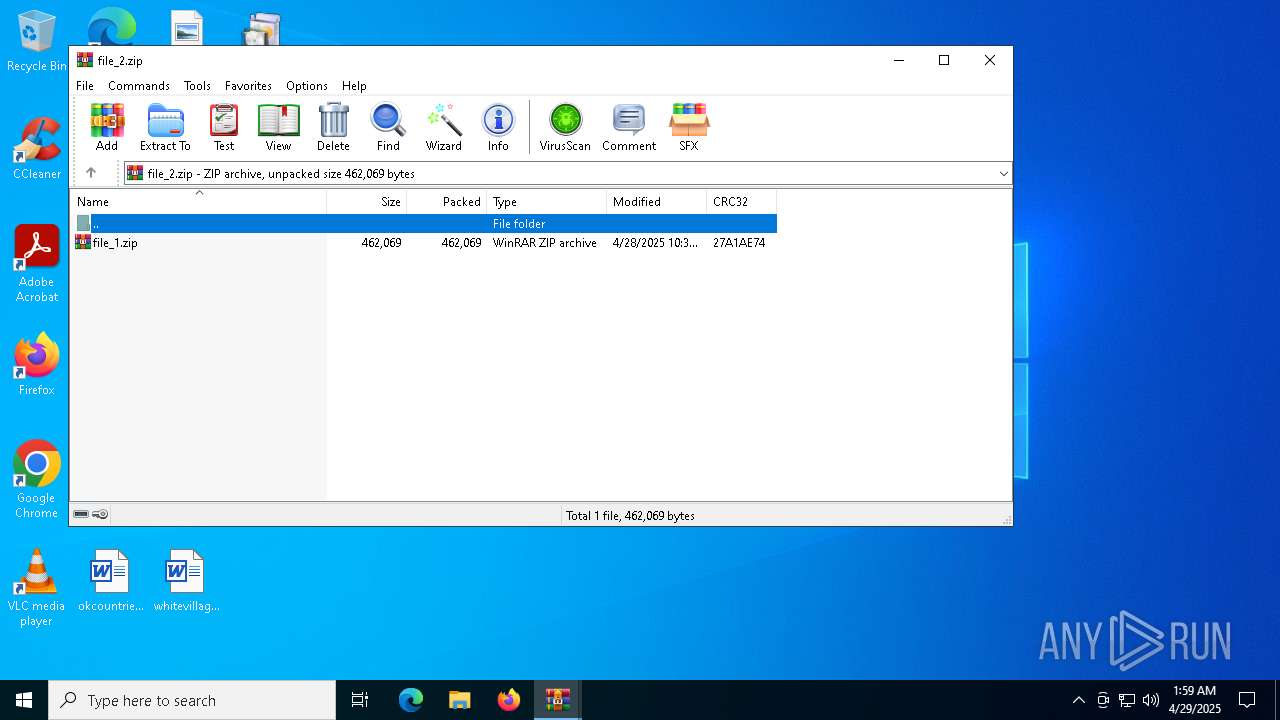
Drops 7-zip archiver for unpacking
- QuantumHacksv2.exe (PID: 2088)
Executing commands from a ".bat" file
- QuantumHacksv2.exe (PID: 2088)
Reads security settings of Internet Explorer
- QuantumHacksv2.exe (PID: 2088)
- WinRAR.exe (PID: 1616)
Starts CMD.EXE for commands execution
- QuantumHacksv2.exe (PID: 2088)
Executable content was dropped or overwritten
- QuantumHacksv2.exe (PID: 2088)
- 7z.exe (PID: 4008)
- cmd.exe (PID: 6540)
The executable file from the user directory is run by the CMD process
- 7z.exe (PID: 1056)
- 7z.exe (PID: 2136)
- 7z.exe (PID: 4008)
- svchost64.exe (PID: 5176)
- 7z.exe (PID: 5868)
There is functionality for taking screenshot (YARA)
- QuantumHacksv2.exe (PID: 2088)
- calc.exe (PID: 616)
- calc.exe (PID: 960)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 6540)
Searches for installed software
- calc.exe (PID: 616)
- calc.exe (PID: 960)
INFO
Create files in a temporary directory
- QuantumHacksv2.exe (PID: 2088)
- 7z.exe (PID: 2136)
- 7z.exe (PID: 4008)
- 7z.exe (PID: 5868)
- 7z.exe (PID: 1056)
Checks supported languages
- QuantumHacksv2.exe (PID: 2088)
- mode.com (PID: 4892)
- 7z.exe (PID: 1056)
- 7z.exe (PID: 2136)
- 7z.exe (PID: 4008)
- svchost64.exe (PID: 5176)
- svchost64.exe (PID: 3768)
- 7z.exe (PID: 5868)
The sample compiled with english language support
- QuantumHacksv2.exe (PID: 2088)
Reads the computer name
- QuantumHacksv2.exe (PID: 2088)
- 7z.exe (PID: 1056)
- 7z.exe (PID: 2136)
- 7z.exe (PID: 4008)
- 7z.exe (PID: 5868)
Process checks computer location settings
- QuantumHacksv2.exe (PID: 2088)
Reads the software policy settings
- calc.exe (PID: 960)
- calc.exe (PID: 616)
- slui.exe (PID: 4188)
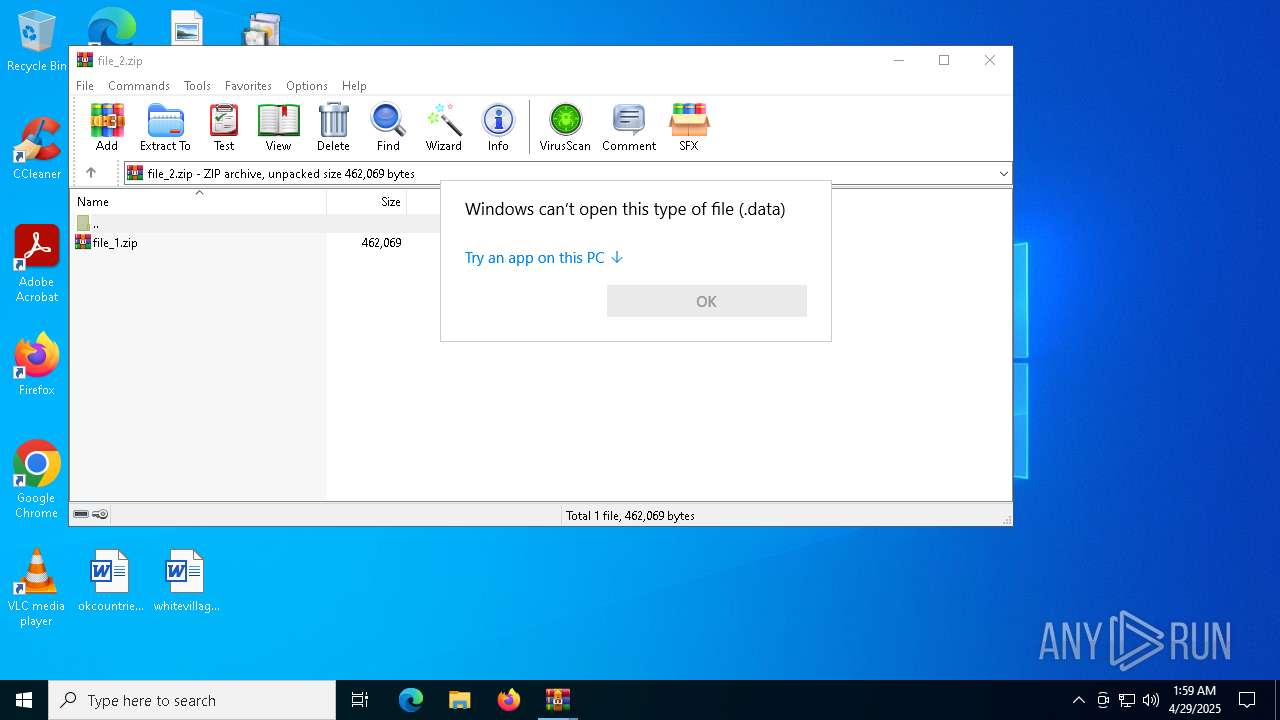
Manual execution by a user
- svchost64.exe (PID: 3768)
- WinRAR.exe (PID: 4688)
- WinRAR.exe (PID: 1616)
- OpenWith.exe (PID: 2692)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 2692)
Checks proxy server information
- slui.exe (PID: 4188)
Starts MODE.COM to configure console settings
- mode.com (PID: 4892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(960) calc.exe
C2 (9)mobitront.run/dsiu
parakehjet.run/kewk
buzzarddf.live/ktnt
zenithcorde.top/auid
bearjk.live/benj
techguidet.digital/apdo
techsyncq.run/riid
btcgeared.live/lbak
fishgh.digital/tequ
(PID) Process(616) calc.exe
C2 (9)mobitront.run/dsiu
parakehjet.run/kewk
buzzarddf.live/ktnt
zenithcorde.top/auid
bearjk.live/benj
techguidet.digital/apdo
techsyncq.run/riid
btcgeared.live/lbak
fishgh.digital/tequ
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:05:28 09:05:18+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 102400 |
| InitializedDataSize: | 38400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1945f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.67.1.0 |
| ProductVersionNumber: | 3.67.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | FileZilla Project |
| LegalCopyright: | Copyright (C) 2006-2024 |
| OriginalFileName: | filezilla.exe |
| Comments: | Version 3.67.1 |
| FileVersion: | 3.67.1.0 |
| ProductName: | FileZilla |
| ProductVersion: | 3.67.1.0 |
| InternalName: | FileZilla 3 |
| FileDescription: | FileZilla FTP Client |
| Created: | 7z SFX Constructor v4.6.0.0 (http://usbtor.ru/viewtopic.php?t=798) |
| Builder: | ahileeeeeess 00:40:20 29/04/2025 |
Total processes
137
Monitored processes
18
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\windows\syswow64\calc.exe" | C:\Windows\SysWOW64\calc.exe | svchost64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Calculator Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
Lumma(PID) Process(616) calc.exe C2 (9)mobitront.run/dsiu parakehjet.run/kewk buzzarddf.live/ktnt zenithcorde.top/auid bearjk.live/benj techguidet.digital/apdo techsyncq.run/riid btcgeared.live/lbak fishgh.digital/tequ | |||||||||||||||
| 960 | "C:\windows\syswow64\calc.exe" | C:\Windows\SysWOW64\calc.exe | svchost64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Calculator Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
Lumma(PID) Process(960) calc.exe C2 (9)mobitront.run/dsiu parakehjet.run/kewk buzzarddf.live/ktnt zenithcorde.top/auid bearjk.live/benj techguidet.digital/apdo techsyncq.run/riid btcgeared.live/lbak fishgh.digital/tequ | |||||||||||||||
| 1056 | 7z.exe e extracted/file_3.zip -oextracted | C:\Users\admin\AppData\Local\Temp\main\7z.exe | — | cmd.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
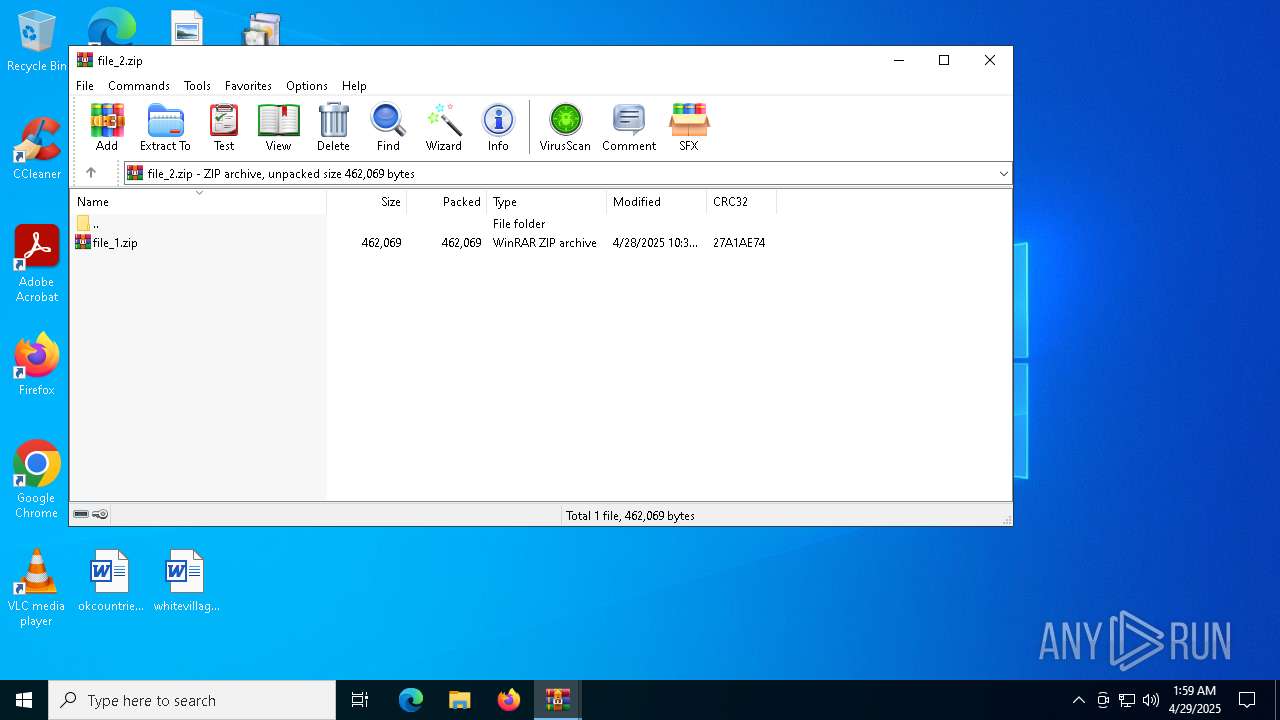
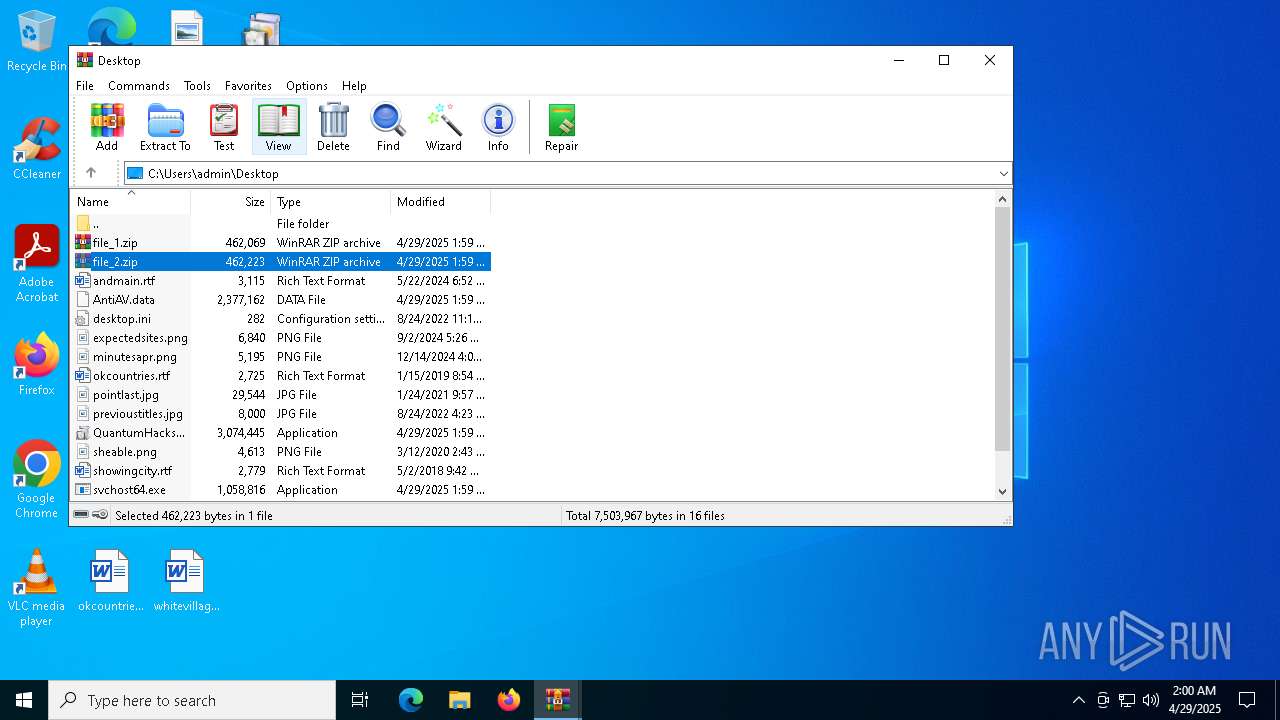
| 1616 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\file_2.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2088 | "C:\Users\admin\Desktop\QuantumHacksv2.exe" | C:\Users\admin\Desktop\QuantumHacksv2.exe | explorer.exe | ||||||||||||
User: admin Company: FileZilla Project Integrity Level: MEDIUM Description: FileZilla FTP Client Version: 3.67.1.0 Modules
| |||||||||||||||
| 2136 | 7z.exe e extracted/file_2.zip -oextracted | C:\Users\admin\AppData\Local\Temp\main\7z.exe | — | cmd.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Desktop\AntiAV.data | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3768 | "C:\Users\admin\Desktop\svchost64.exe" | C:\Users\admin\Desktop\svchost64.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4008 | 7z.exe e extracted/file_1.zip -oextracted | C:\Users\admin\AppData\Local\Temp\main\7z.exe | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
Total events
14 189
Read events
14 164
Write events
25
Delete events
0
Modification events
| (PID) Process: | (4688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\file_1.zip | |||
| (PID) Process: | (4688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4688) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
4
Suspicious files
6
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6540 | cmd.exe | C:\Users\admin\AppData\Local\Temp\main\file.bin | compressed | |
MD5:94E17ACF936E453C0CFE3B76420D7FCF | SHA256:6D501C1F888870561B450B6CEAC0ADF18050F52D012CEA1C4FE036916BACE9E3 | |||
| 6540 | cmd.exe | C:\Users\admin\AppData\Local\Temp\main\file.zip | compressed | |
MD5:94E17ACF936E453C0CFE3B76420D7FCF | SHA256:6D501C1F888870561B450B6CEAC0ADF18050F52D012CEA1C4FE036916BACE9E3 | |||
| 5868 | 7z.exe | C:\Users\admin\AppData\Local\Temp\main\extracted\file_3.zip | compressed | |
MD5:8AA480752BB572C28DD981096D85C8C8 | SHA256:6E706719F1472F6D96A8C675064E82AC75300940151ECE70E774734C0DCAED17 | |||
| 2088 | QuantumHacksv2.exe | C:\Users\admin\AppData\Local\Temp\main\7z.exe | executable | |
MD5:619F7135621B50FD1900FF24AADE1524 | SHA256:344F076BB1211CB02ECA9E5ED2C0CE59BCF74CCBC749EC611538FA14ECB9AAD2 | |||
| 2136 | 7z.exe | C:\Users\admin\AppData\Local\Temp\main\extracted\file_1.zip | compressed | |
MD5:CEA188BAA09A3AAEBD7A921F6632AD80 | SHA256:16B98F523CDF8A6AD515437329662E010AEB1807B86850D5B3BB4DAD32750DDB | |||
| 1056 | 7z.exe | C:\Users\admin\AppData\Local\Temp\main\extracted\AntiAV.data | text | |
MD5:91281AB5814EDD87B7A77F3E754389AD | SHA256:51559F5FB63803D8D4FF81519FAD1E4BA4EAE18AC57976A1FD922702F879F040 | |||
| 2088 | QuantumHacksv2.exe | C:\Users\admin\AppData\Local\Temp\main\main.bat | text | |
MD5:AD15EC748259F4BD9686ABBBA5B29307 | SHA256:20D797B8D9D9F6C14C53DAE00B16397885E3DA8A9A95FA1CA5B34B79414C8944 | |||
| 6540 | cmd.exe | C:\Users\admin\AppData\Local\Temp\main\svchost64.exe | executable | |
MD5:5E36978CE37CD85EE2DCFF0E330685EC | SHA256:7E5DD8554E22DCB9FEC7ACA7AAA6B5A61DC8B2A8C1E66B6A95CE99FC723F1CE1 | |||
| 2088 | QuantumHacksv2.exe | C:\Users\admin\AppData\Local\Temp\main\KillDuplicate.cmd | text | |
MD5:68CECDF24AA2FD011ECE466F00EF8450 | SHA256:64929489DC8A0D66EA95113D4E676368EDB576EA85D23564D53346B21C202770 | |||
| 2088 | QuantumHacksv2.exe | C:\Users\admin\AppData\Local\Temp\main\7z.dll | executable | |
MD5:72491C7B87A7C2DD350B727444F13BB4 | SHA256:34AD9BB80FE8BF28171E671228EB5B64A55CAA388C31CB8C0DF77C0136735891 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
36
DNS requests
6
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 104.21.51.232:443 | https://zenithcorde.top/auid | US | binary | 10.7 Kb | unknown |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
— | — | POST | 522 | 188.114.97.3:443 | https://mobitront.run/dsiu | US | — | — | malicious |
— | — | POST | 200 | 172.67.190.162:443 | https://zenithcorde.top/auid | US | binary | 32.7 Kb | unknown |
— | — | POST | 200 | 172.67.190.162:443 | https://zenithcorde.top/auid | US | binary | 69 b | unknown |
— | — | POST | 200 | 104.21.51.232:443 | https://zenithcorde.top/auid | US | binary | 69 b | unknown |
— | — | POST | 200 | 104.21.51.232:443 | https://zenithcorde.top/auid | US | binary | 69 b | unknown |
— | — | POST | 200 | 104.21.51.232:443 | https://zenithcorde.top/auid | US | binary | 69 b | unknown |
— | — | POST | 522 | 188.114.96.3:443 | https://mobitront.run/dsiu | US | — | — | malicious |
— | — | POST | 200 | 172.67.190.162:443 | https://zenithcorde.top/auid | US | binary | 69 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
960 | calc.exe | 188.114.97.3:443 | mobitront.run | CLOUDFLARENET | NL | malicious |
616 | calc.exe | 188.114.97.3:443 | mobitront.run | CLOUDFLARENET | NL | malicious |
960 | calc.exe | 104.21.51.232:443 | zenithcorde.top | CLOUDFLARENET | — | unknown |
616 | calc.exe | 104.21.51.232:443 | zenithcorde.top | CLOUDFLARENET | — | unknown |
5332 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4188 | slui.exe | 13.77.207.86:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
mobitront.run |
| malicious |
zenithcorde.top |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |