| File name: | xmrig-6.22.2 - Copy.zip |
| Full analysis: | https://app.any.run/tasks/a6bf4a8e-39d4-447c-89d7-c03e46afa7e2 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | December 04, 2024, 14:17:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 419A5CD5844C4F5E8AE63C15DDE769C4 |
| SHA1: | BC918931D8EC683A2E8B9245BB2895586089FA37 |
| SHA256: | C1AFED1D6DA64C791CCA5C44F846DD285D579185807E39AF96AFC9FD805AD0DA |
| SSDEEP: | 98304:sX7GS/jQ7r5gofzPgBPyn+Cusep1aNrpymfGGXm8qrqLlbg214CBGHM2E8Q2Lxer:2gBYbuJN |
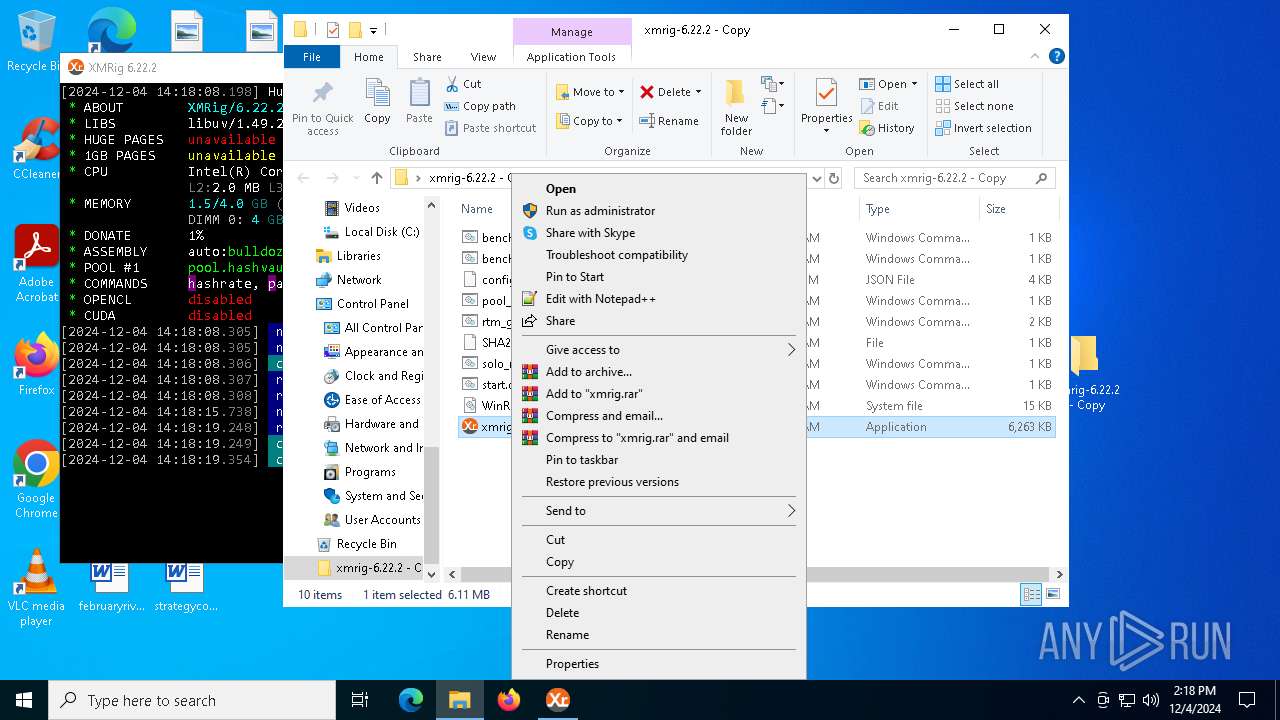
MALICIOUS
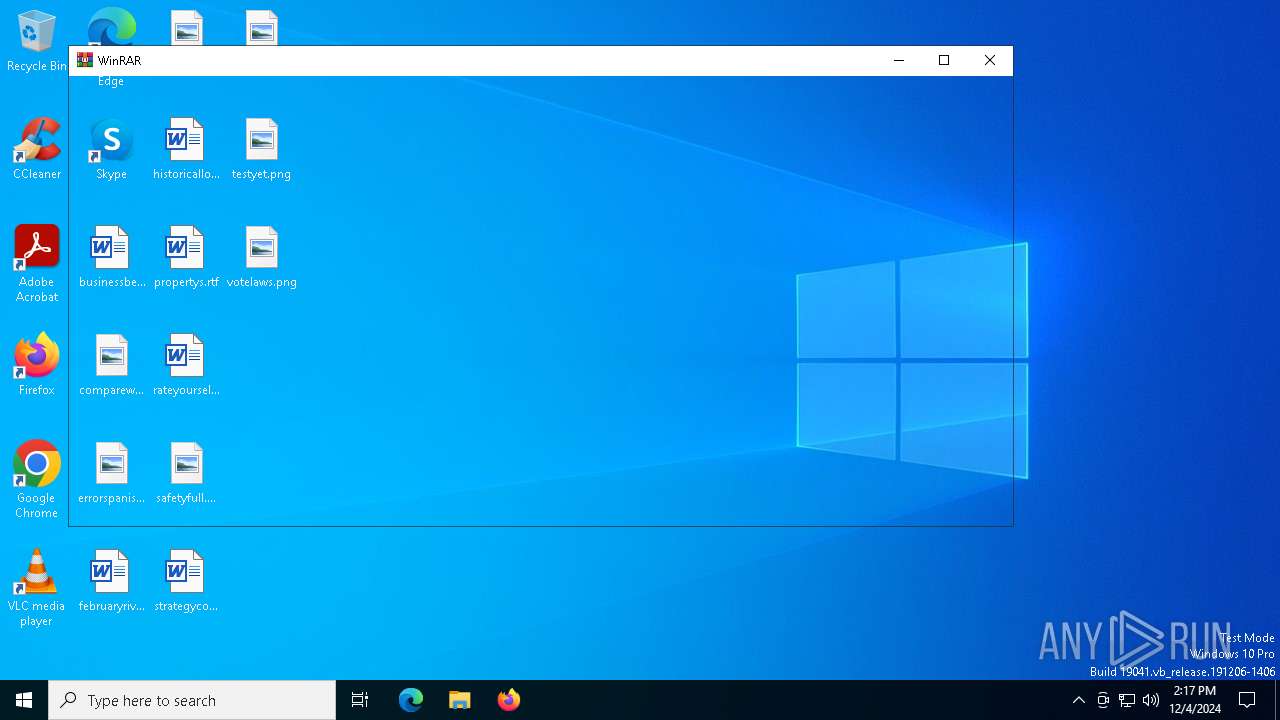
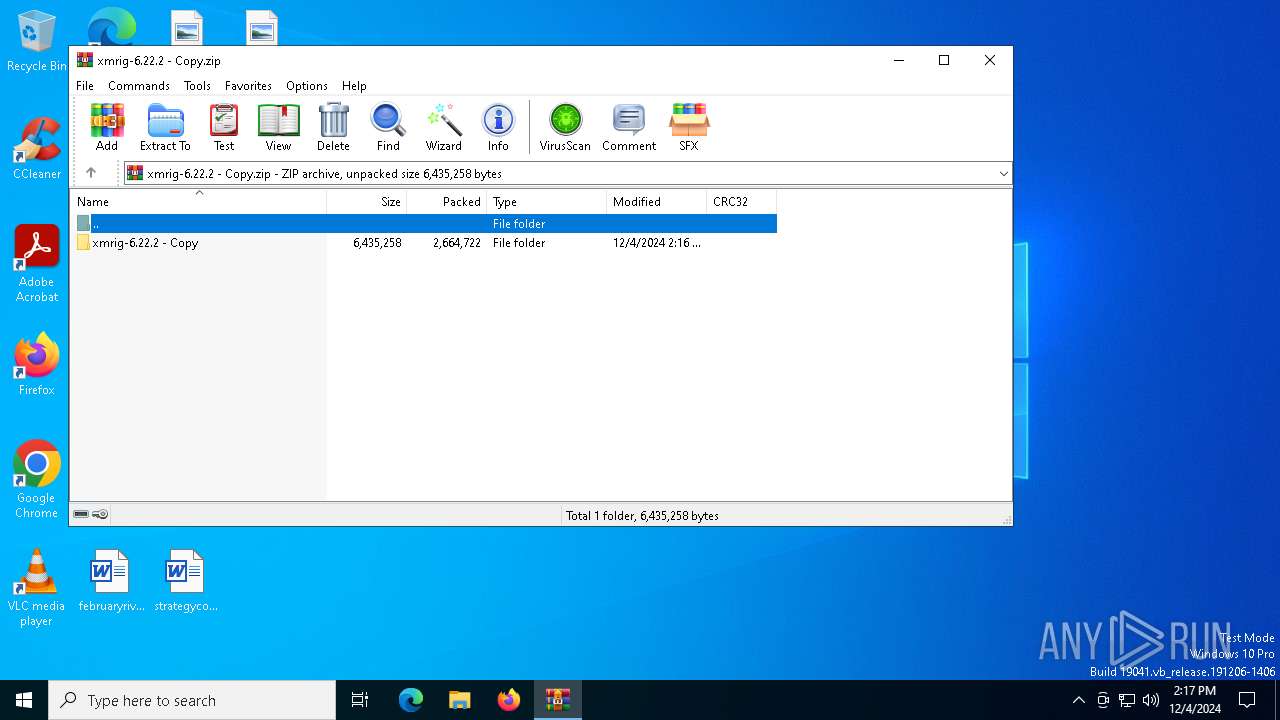
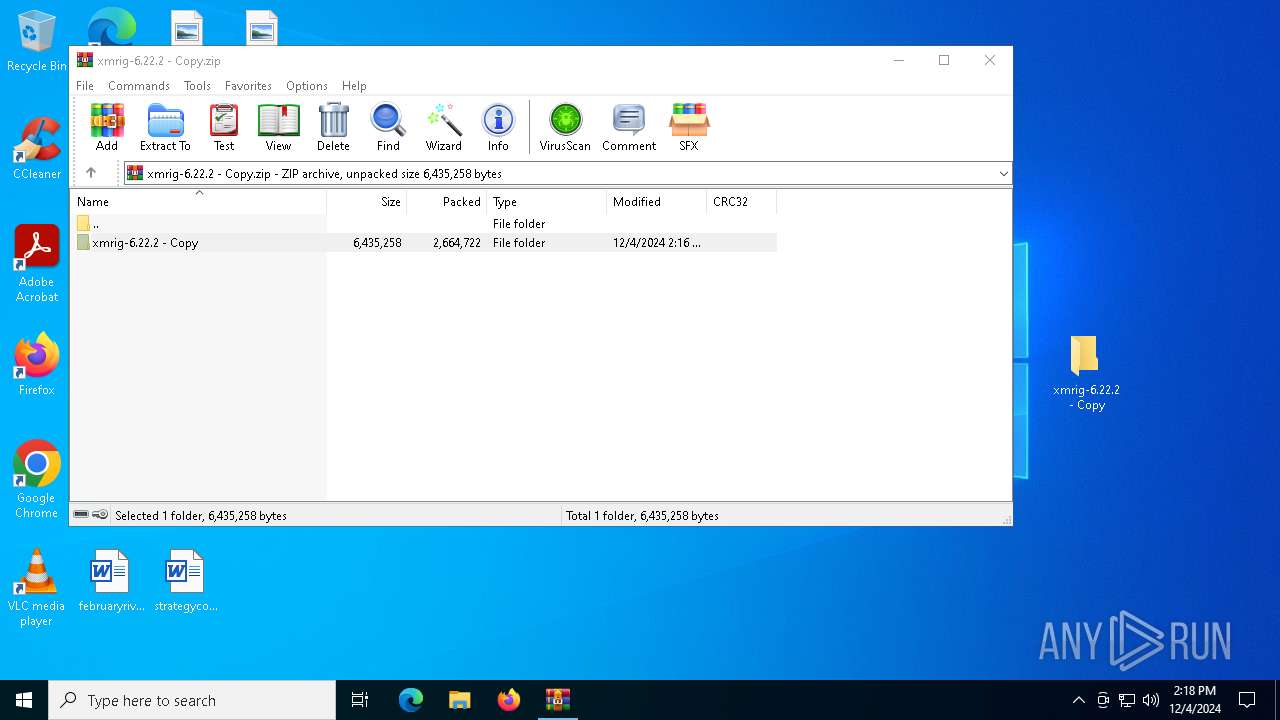
Generic archive extractor
- WinRAR.exe (PID: 6244)
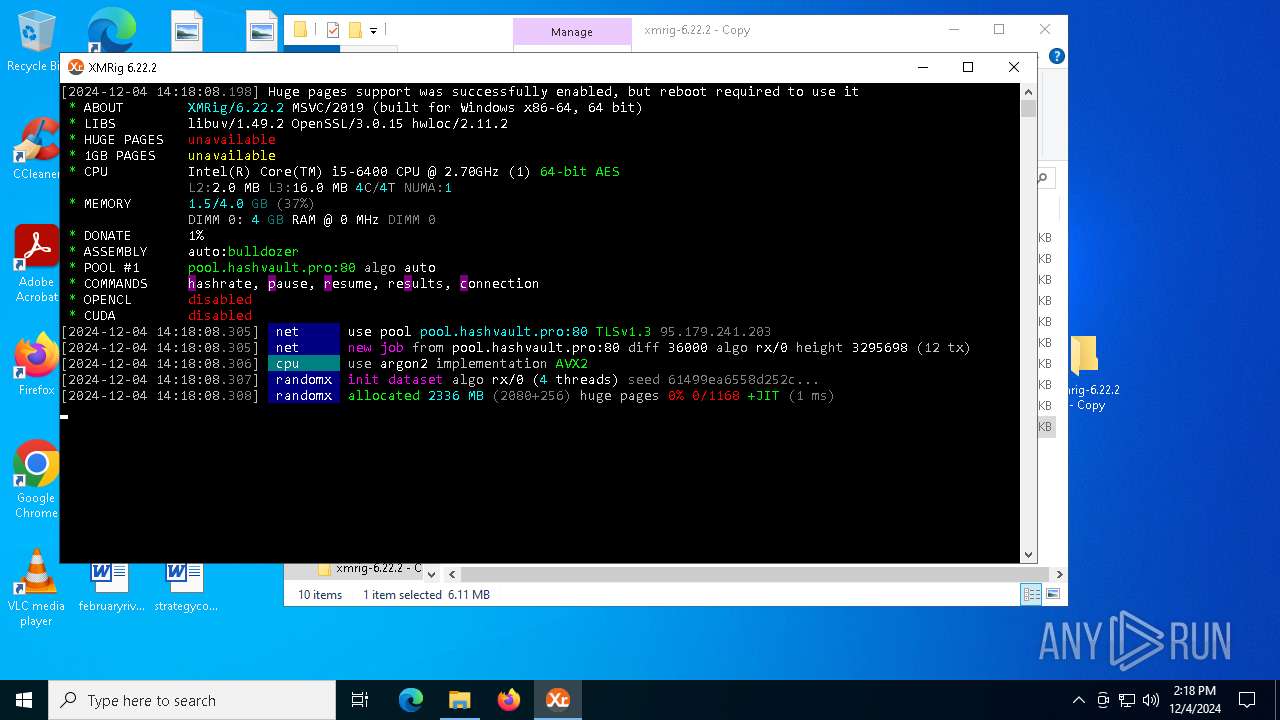
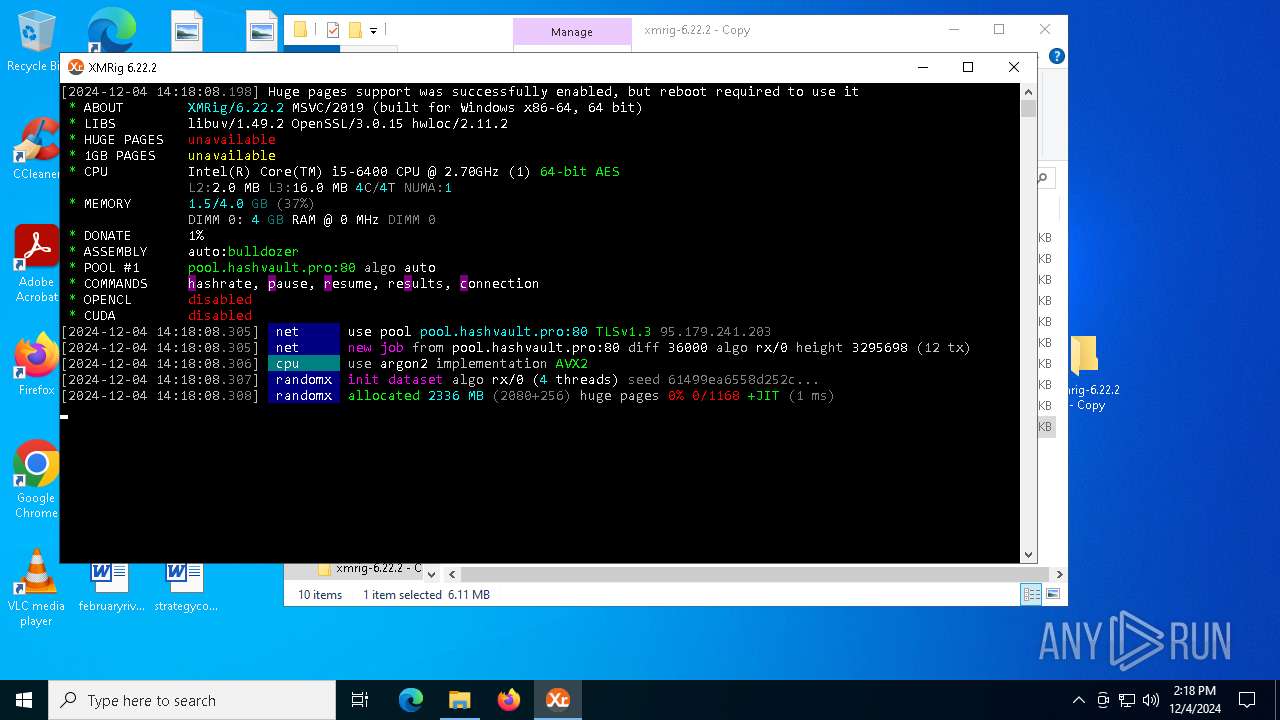
MINER has been detected (SURICATA)
- svchost.exe (PID: 2192)
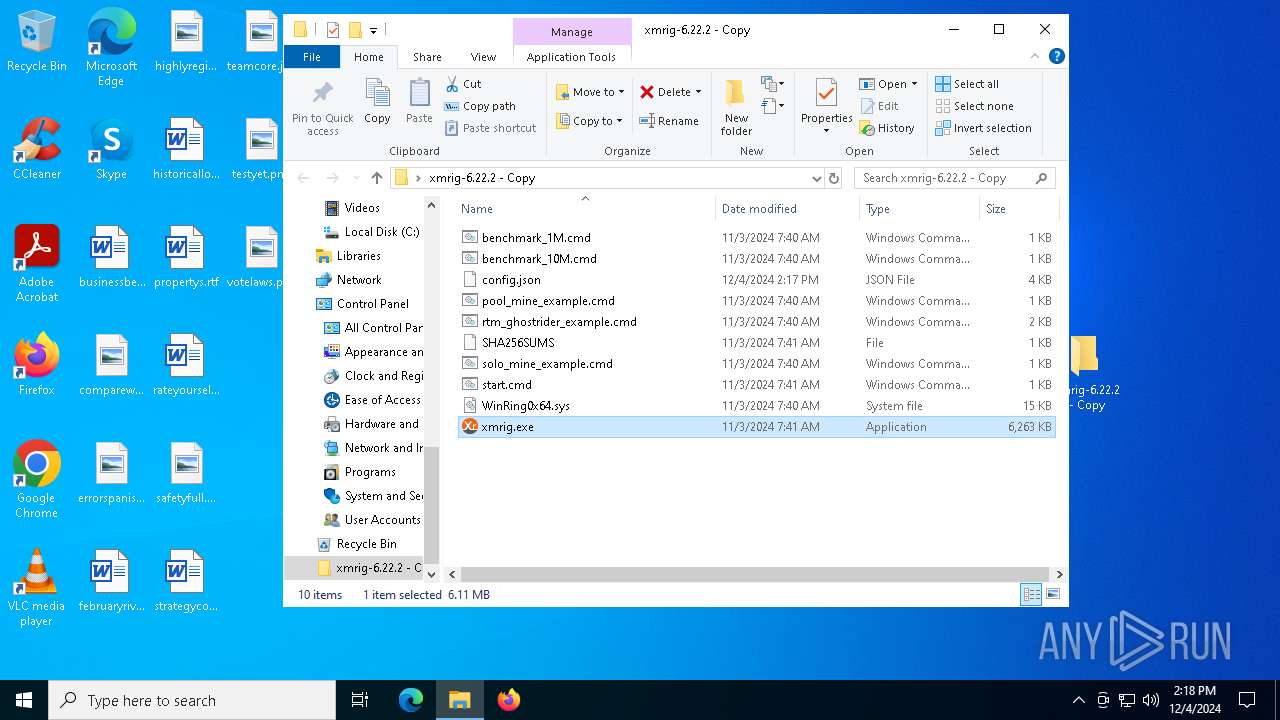
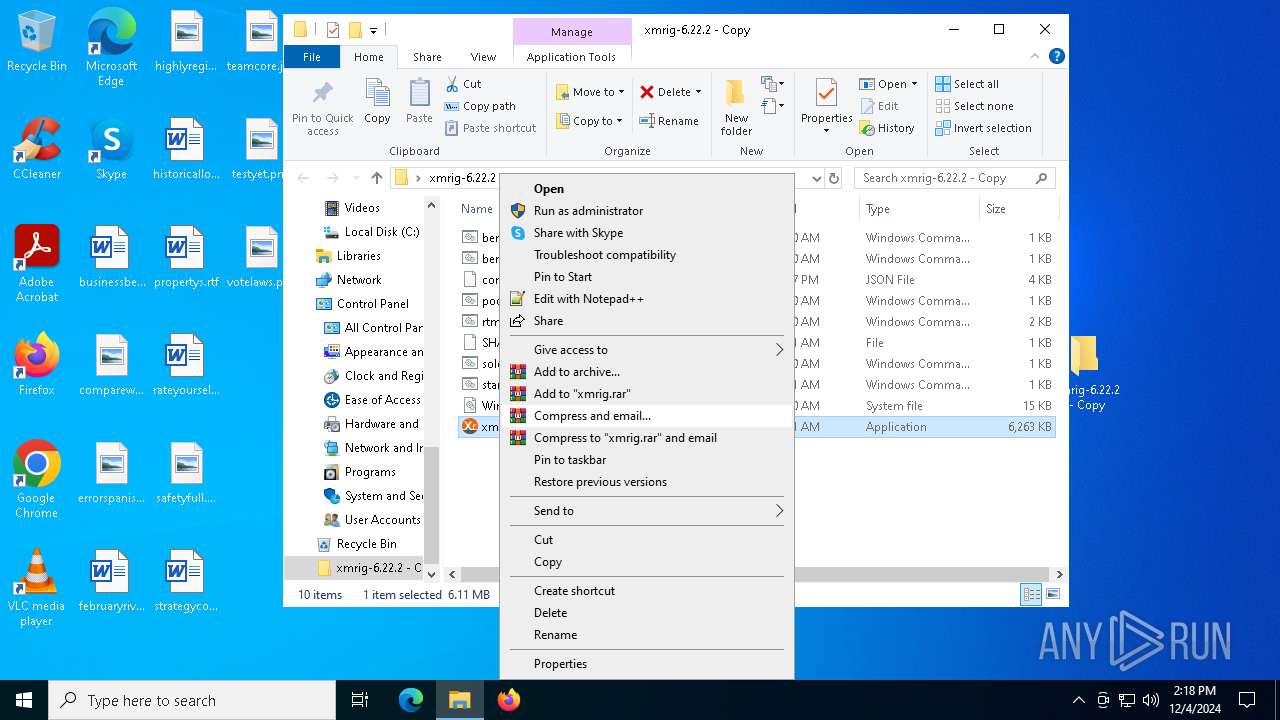
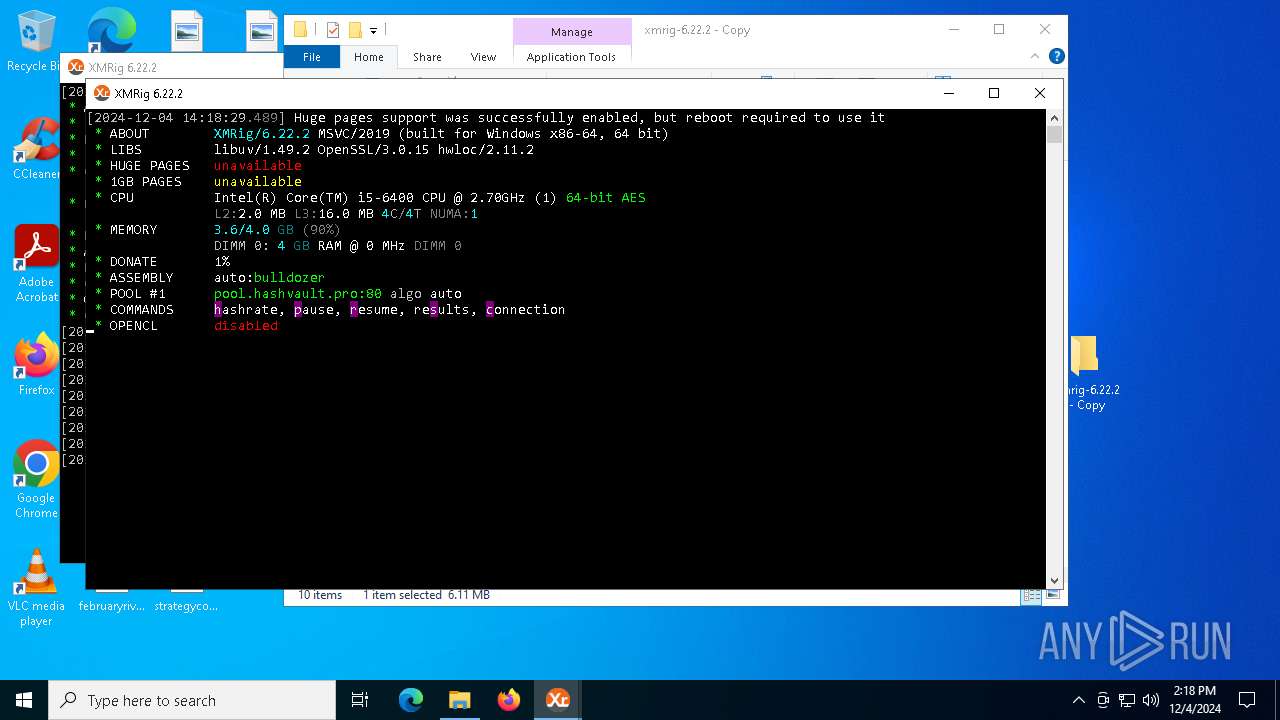
XMRig has been detected
- xmrig.exe (PID: 7032)
- xmrig.exe (PID: 1804)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 6244)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2192)
INFO
The process uses the downloaded file
- WinRAR.exe (PID: 6244)
Checks supported languages
- xmrig.exe (PID: 7032)
- xmrig.exe (PID: 1804)
Reads the computer name
- xmrig.exe (PID: 7032)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6244)
Manual execution by a user
- xmrig.exe (PID: 7032)
- xmrig.exe (PID: 1804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:12:04 06:16:48 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | xmrig-6.22.2 - Copy/ |
Total processes
131
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1804 | "C:\Users\admin\Desktop\xmrig-6.22.2 - Copy\xmrig.exe" | C:\Users\admin\Desktop\xmrig-6.22.2 - Copy\xmrig.exe | explorer.exe | ||||||||||||
User: admin Company: www.xmrig.com Integrity Level: HIGH Description: XMRig miner Version: 6.22.2 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5872 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | xmrig.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6244 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\xmrig-6.22.2 - Copy.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6920 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7032 | "C:\Users\admin\Desktop\xmrig-6.22.2 - Copy\xmrig.exe" | C:\Users\admin\Desktop\xmrig-6.22.2 - Copy\xmrig.exe | explorer.exe | ||||||||||||
User: admin Company: www.xmrig.com Integrity Level: HIGH Description: XMRig miner Version: 6.22.2 Modules
| |||||||||||||||
| 7044 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | xmrig.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 465
Read events
2 447
Write events
18
Delete events
0
Modification events
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\xmrig-6.22.2 - Copy.zip | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
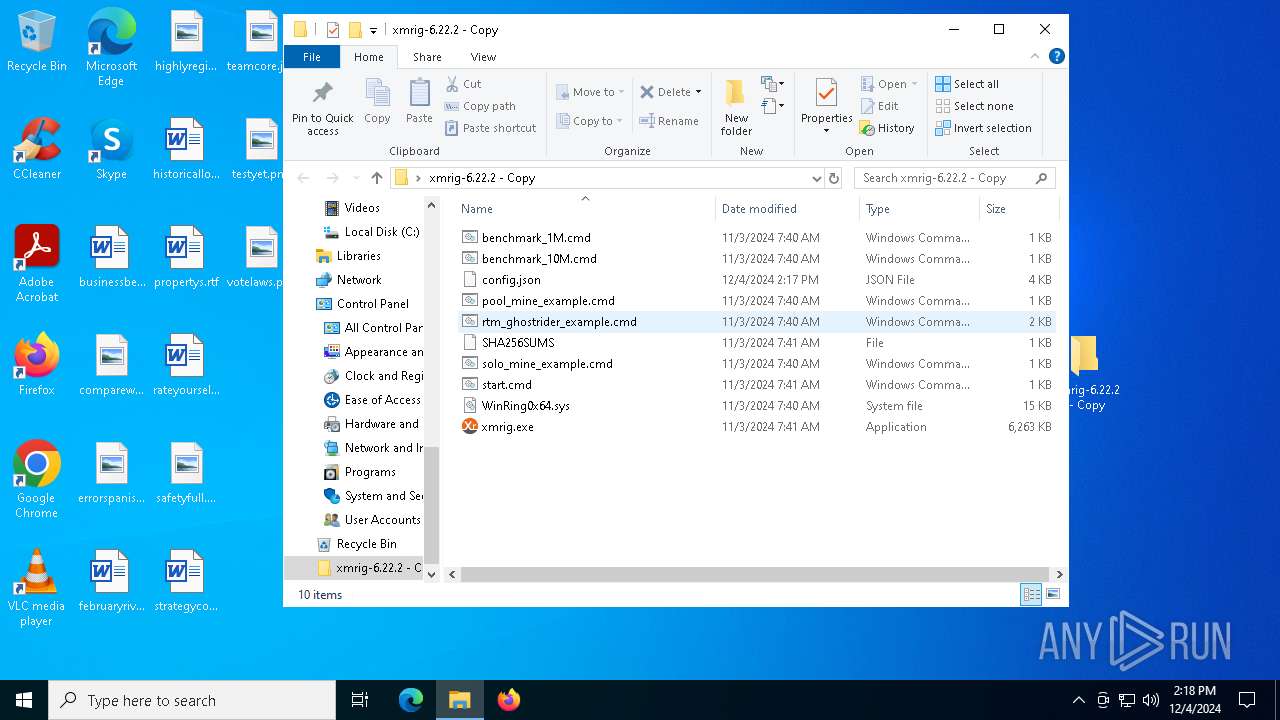
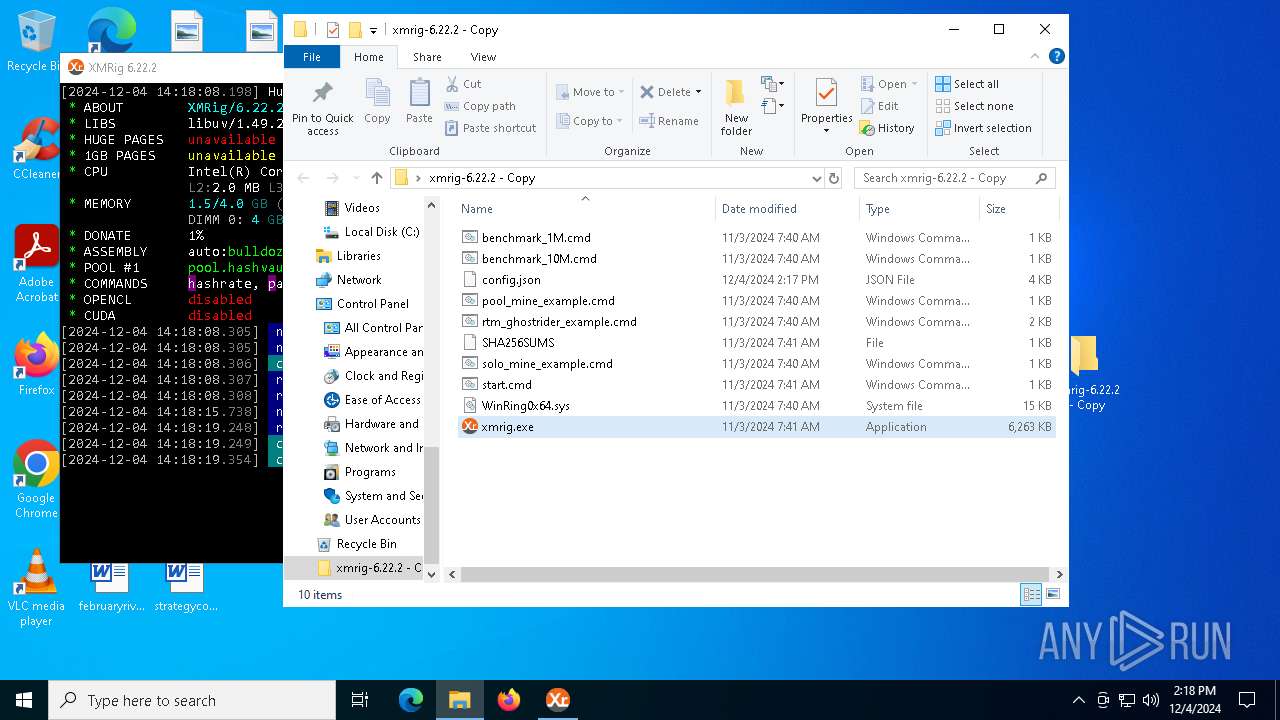
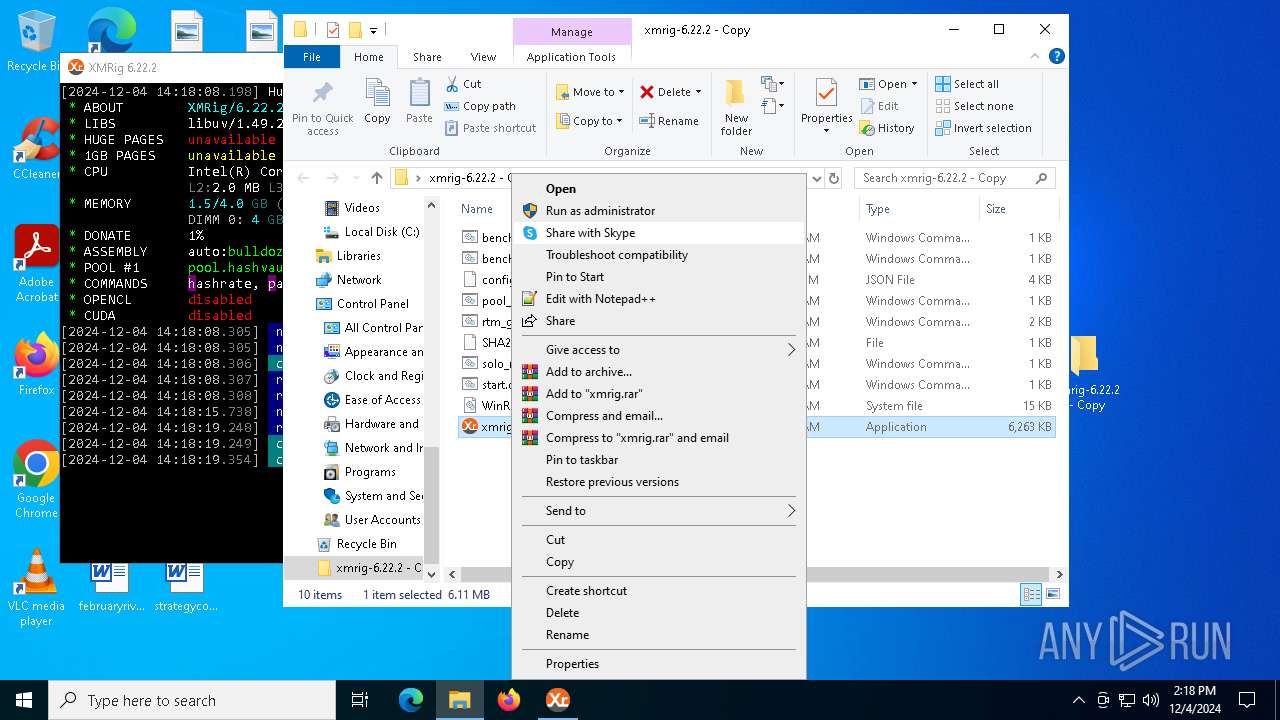
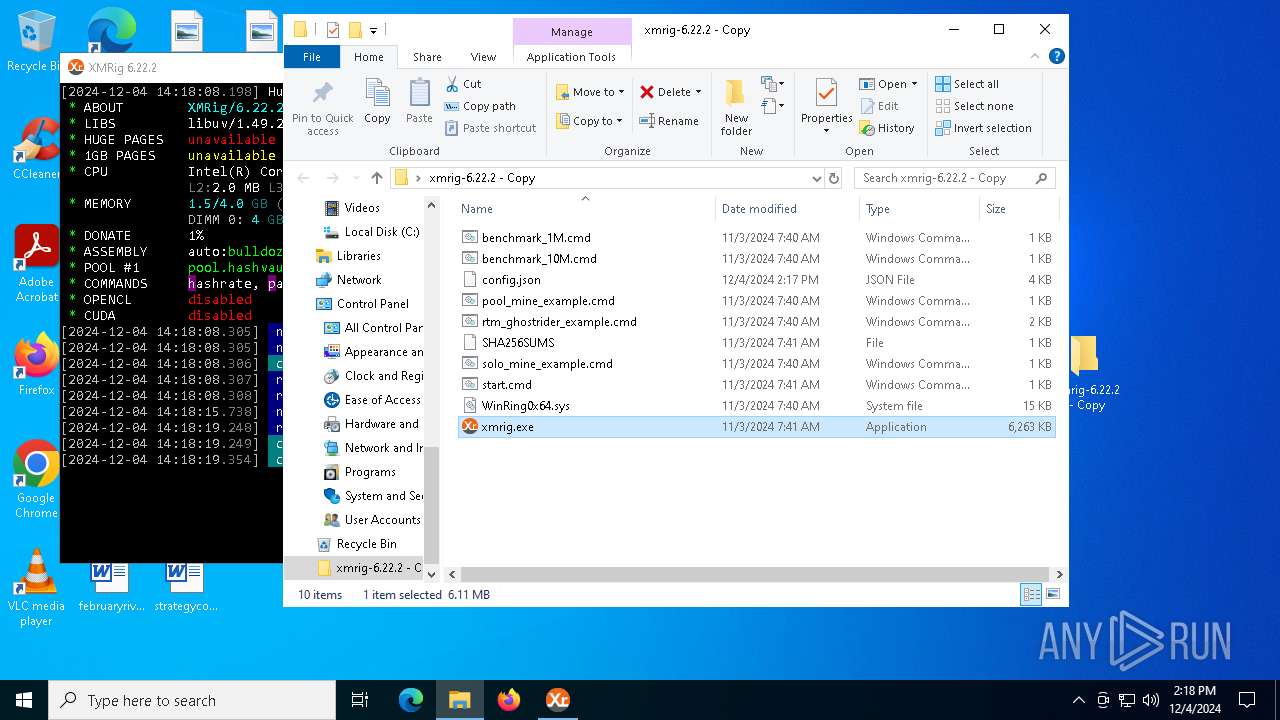
Executable files
2
Suspicious files
1
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6244.19012\xmrig-6.22.2 - Copy\benchmark_10M.cmd | text | |
MD5:5BE1C4CACB5AE37C43527E99A097DC7A | SHA256:235A64E3520B1C2C27763122B303F78AEE8D7C083DFD9F1EB936CD5174383609 | |||
| 6244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6244.19012\xmrig-6.22.2 - Copy\pool_mine_example.cmd | text | |
MD5:2E737F5C3AF9C8AA5216DFDC5BE02CC6 | SHA256:E73491065D86B1AD69229BB5D2019E08B947E11A2A57ADF5C2D9A2B5D8F4ACAD | |||
| 6244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6244.19012\xmrig-6.22.2 - Copy\solo_mine_example.cmd | text | |
MD5:090703E56F46330ED625AC4363C9D25C | SHA256:33497C69C21FA96BBC96F1D7F09608E462F8AB22555364977C0BD35FEF27BC29 | |||
| 6244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6244.19012\xmrig-6.22.2 - Copy\WinRing0x64.sys | executable | |
MD5:0C0195C48B6B8582FA6F6373032118DA | SHA256:11BD2C9F9E2397C9A16E0990E4ED2CF0679498FE0FD418A3DFDAC60B5C160EE5 | |||
| 6244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6244.19012\xmrig-6.22.2 - Copy\config.json | binary | |
MD5:924C9C209C2D5B285D850A88373CD082 | SHA256:60FA3DD90F4F221108E0615CA154F670939A860470F47019CC9F3D9ADE6A8024 | |||
| 6244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6244.19012\xmrig-6.22.2 - Copy\rtm_ghostrider_example.cmd | text | |
MD5:3F0155ABE745BE1F6089EAFC4F517AC8 | SHA256:810614290BDB14D2DDF10F65F8ADC988A8272764F2A9E2C378E52FAD162DA344 | |||
| 6244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6244.19012\xmrig-6.22.2 - Copy\benchmark_1M.cmd | text | |
MD5:CBA1927CF6959DC99ECBD0C553E4DB6F | SHA256:D7747E7A3C782009F4CEB6E9C106115876386853929563B509DA5258E3968D15 | |||
| 6244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6244.19012\xmrig-6.22.2 - Copy\start.cmd | text | |
MD5:EAF3A00CC0465F8AF471B849ADA29843 | SHA256:8E70EF38FE14A2EE2848DF3D6F7E260D1CAF8CFC15DE694D678B8AF151D62333 | |||
| 6244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6244.19012\xmrig-6.22.2 - Copy\SHA256SUMS | text | |
MD5:C7A209DEE0F5D1C6C3DD496BA22F78AB | SHA256:C83B38B121842A02FB910FE260C83CCED6AA90663C2A1626231FF5122850DEE8 | |||
| 6244 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6244.19012\xmrig-6.22.2 - Copy\xmrig.exe | executable | |
MD5:F6D520AE125F03056C4646C508218D16 | SHA256:D2FCF28897DDC2137141D838B734664FF7592E03FCD467A433A51CB4976B4FB1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
30
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
7160 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
7160 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3040 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
5064 | SearchApp.exe | 2.23.209.163:443 | www.bing.com | Akamai International B.V. | GB | unknown |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
1176 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
1076 | svchost.exe | 23.32.186.57:443 | go.microsoft.com | AKAMAI-AS | BR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| unknown |
crl.microsoft.com |
| unknown |
google.com |
| unknown |
www.microsoft.com |
| unknown |
www.bing.com |
| unknown |
ocsp.digicert.com |
| unknown |
login.live.com |
| unknown |
go.microsoft.com |
| unknown |
pool.hashvault.pro |
| unknown |
slscr.update.microsoft.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER CoinMiner Domain in DNS Lookup (pool .hashvault .pro) |