| URL: | https://onedrive.live.com/download?cid=15782FC1157D6AC7&resid=15782FC1157D6AC7%21109&authkey=ADbokiH_3KbVNLI |
| Full analysis: | https://app.any.run/tasks/047dbfb2-189e-488c-999b-5c4ca1813097 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | June 12, 2019, 07:47:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F17146E83131C615E1CFD39E75373E3F |
| SHA1: | 70DBCCD9EC1B1F53E660698E6CE1BF89582DB814 |
| SHA256: | C180566593118C3EA814F091D41DEE3760F6328B0969C53E0E226DCB6DDD750D |
| SSDEEP: | 3:N8Ck3CTwKbl9oCSTPB5QJCST7Apoqjt6WuT9s:2CkST/ZJST04SApoqj6T9s |
MALICIOUS
Application was dropped or rewritten from another process
- Update PO# 3900003328.exe (PID: 2632)
- Update PO# 3900003328.exe (PID: 2852)
- Update PO# 3900003328.exe (PID: 3520)
Detected artifacts of LokiBot
- Update PO# 3900003328.exe (PID: 2852)
Actions looks like stealing of personal data
- Update PO# 3900003328.exe (PID: 2852)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 3316)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 912)
- firefox.exe (PID: 3316)
- Update PO# 3900003328.exe (PID: 2852)
Creates files in the user directory
- Update PO# 3900003328.exe (PID: 2852)
Loads DLL from Mozilla Firefox
- Update PO# 3900003328.exe (PID: 2852)
Application launched itself
- Update PO# 3900003328.exe (PID: 2632)
INFO
Application launched itself
- firefox.exe (PID: 3316)
Reads CPU info
- firefox.exe (PID: 3316)
Creates files in the user directory
- firefox.exe (PID: 3316)
Reads settings of System Certificates
- firefox.exe (PID: 3316)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
9
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
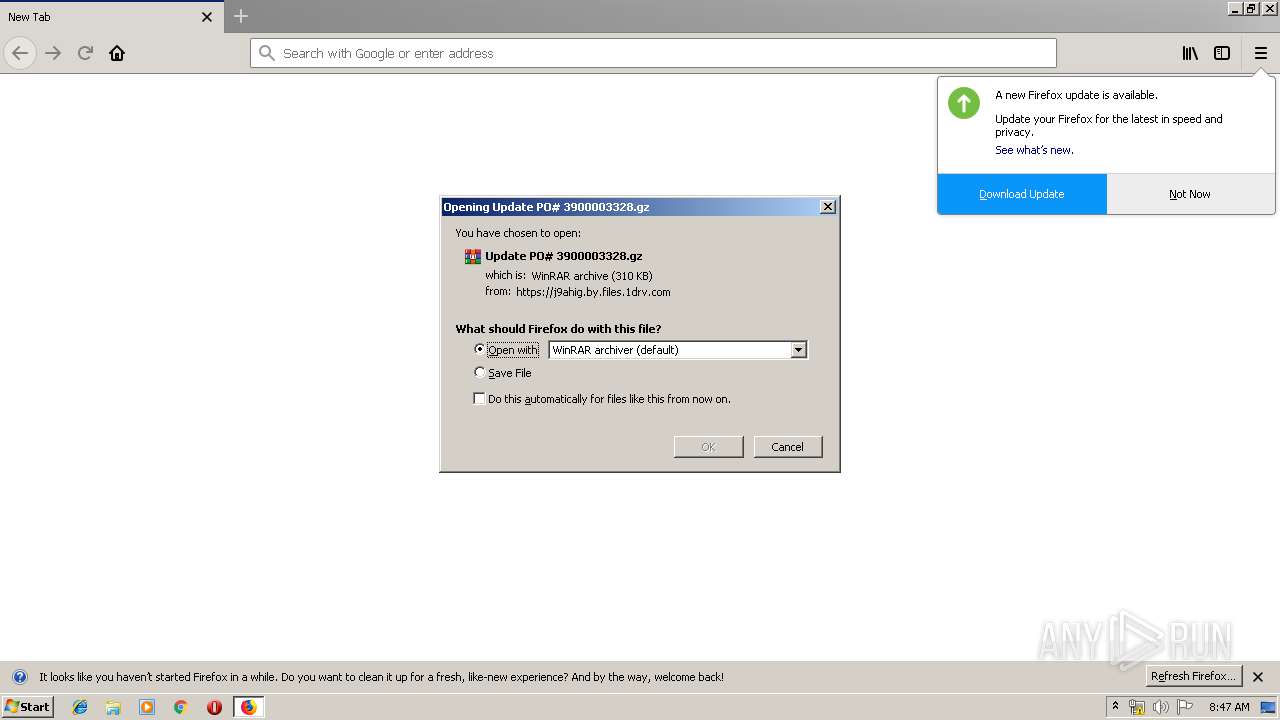
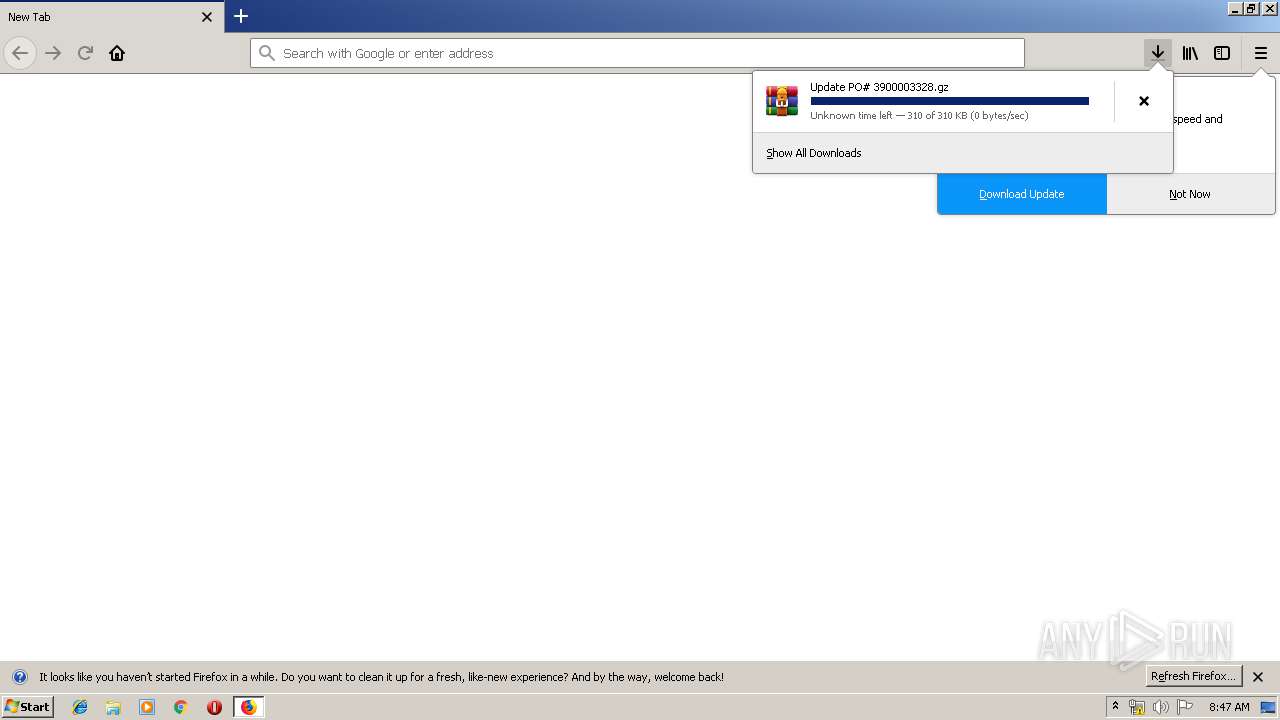
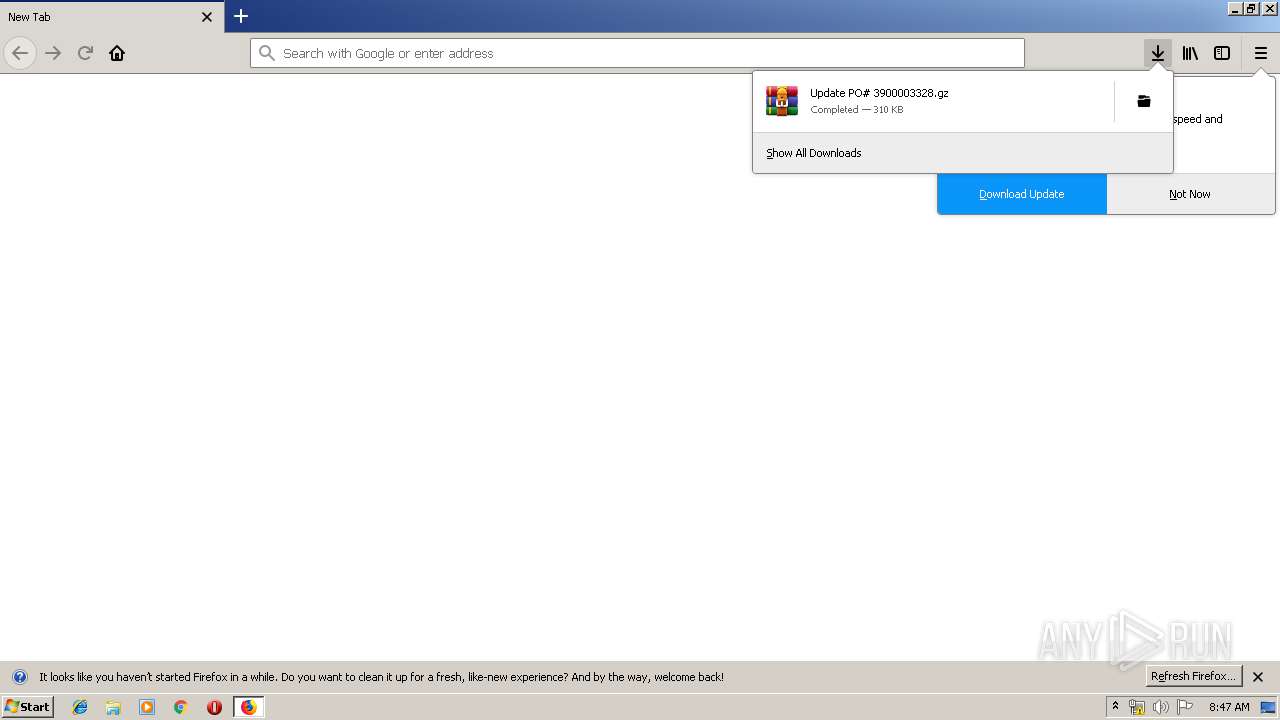
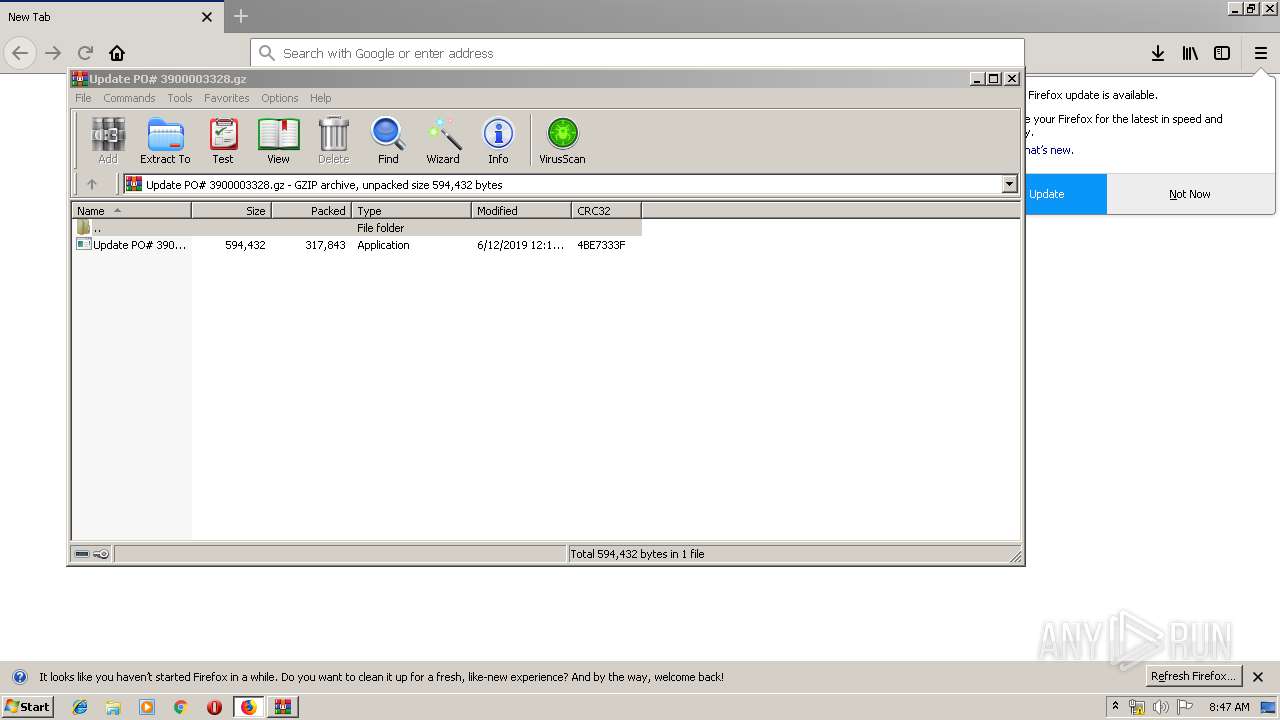
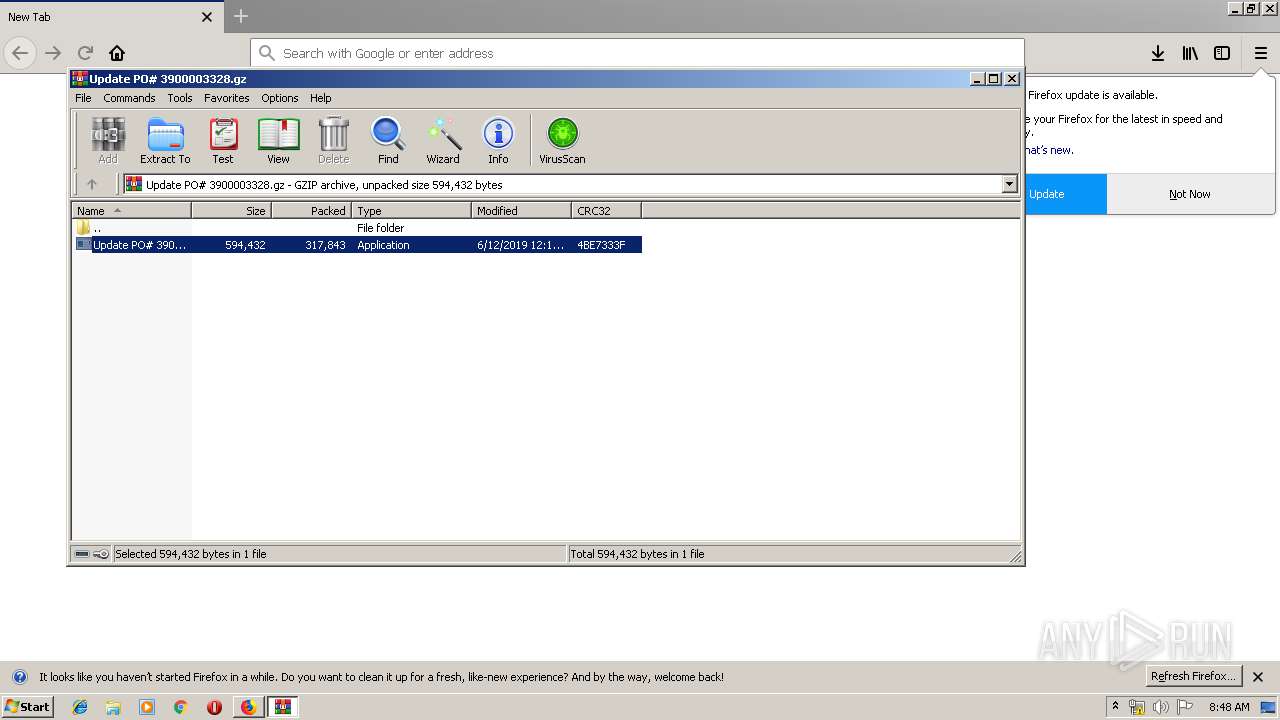
| 912 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Update PO# 3900003328.gz" | C:\Program Files\WinRAR\WinRAR.exe | firefox.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1808 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3316.6.1995306759\233697120" -childID 1 -isForBrowser -prefsHandle 1704 -prefMapHandle 1572 -prefsLen 1 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3316 "\\.\pipe\gecko-crash-server-pipe.3316" 1708 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3316.13.2065260777\1516410196" -childID 2 -isForBrowser -prefsHandle 2644 -prefMapHandle 2648 -prefsLen 216 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3316 "\\.\pipe\gecko-crash-server-pipe.3316" 2660 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2632 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa912.18204\Update PO# 3900003328.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa912.18204\Update PO# 3900003328.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa912.18204\Update PO# 3900003328.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa912.18204\Update PO# 3900003328.exe | Update PO# 3900003328.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3316.0.1491389032\1622747598" -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - "C:\Users\admin\AppData\LocalLow\Mozilla\Temp-{ce348e4c-7d33-445e-89f9-60108c51bcaf}" 3316 "\\.\pipe\gecko-crash-server-pipe.3316" 1112 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
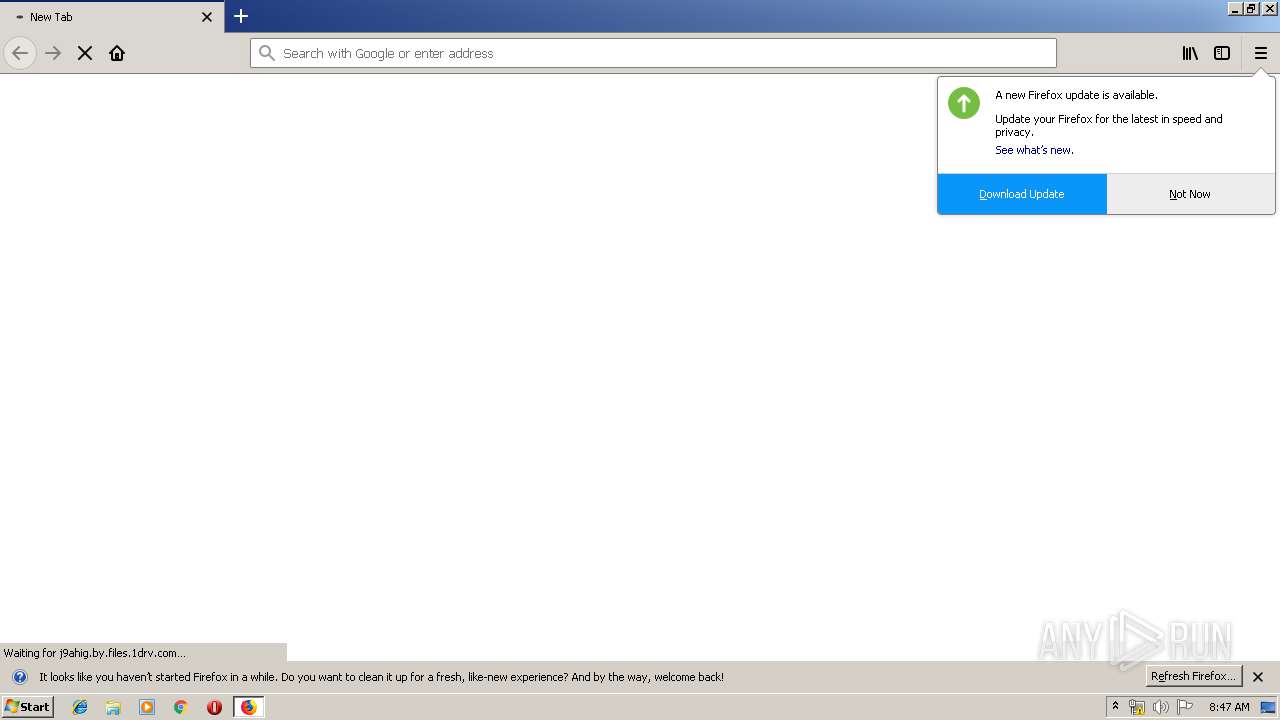
| 3316 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://onedrive.live.com/download?cid=15782FC1157D6AC7&resid=15782FC1157D6AC7%21109&authkey=ADbokiH_3KbVNLI | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 3520 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa912.18204\Update PO# 3900003328.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa912.18204\Update PO# 3900003328.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3588 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3316.20.11603874\292002168" -childID 3 -isForBrowser -prefsHandle 3224 -prefMapHandle 3384 -prefsLen 5824 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3316 "\\.\pipe\gecko-crash-server-pipe.3316" 3396 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
Total events
1 719
Read events
1 690
Write events
29
Delete events
0
Modification events
| (PID) Process: | (3316) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3316) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3316) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3316) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3316) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.gz\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
| (PID) Process: | (912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (912) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Update PO# 3900003328.gz | |||
| (PID) Process: | (912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
Executable files
3
Suspicious files
73
Text files
32
Unknown types
57
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3316 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\trash8319 | — | |
MD5:— | SHA256:— | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cert9.db-journal | — | |
MD5:— | SHA256:— | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\2A7FB49184C162E8391F613817174350B251685D | der | |
MD5:— | SHA256:— | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:— | SHA256:— | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3316 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\EECD53ADA09C1DD3DBE3DDD249D1813D1978DDF3 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
27
DNS requests
119
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3316 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3316 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3316 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3316 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3316 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3316 | firefox.exe | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
3316 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3316 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3316 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3316 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3316 | firefox.exe | 35.164.130.113:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3316 | firefox.exe | 54.190.222.97:443 | search.services.mozilla.com | Amazon.com, Inc. | US | malicious |
3316 | firefox.exe | 54.213.5.202:443 | aus5.mozilla.org | Amazon.com, Inc. | US | unknown |
3316 | firefox.exe | 172.217.22.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3316 | firefox.exe | 13.107.42.12:443 | j9ahig.by.files.1drv.com | Microsoft Corporation | US | suspicious |
3316 | firefox.exe | 172.217.22.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3316 | firefox.exe | 172.217.21.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3316 | firefox.exe | 13.32.166.103:443 | tracking-protection.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
3316 | firefox.exe | 54.186.120.41:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3316 | firefox.exe | 13.32.166.225:443 | content-signature.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
onedrive.live.com |
| shared |
aus5.mozilla.org |
| whitelisted |
balrog-aus5.r53-2.services.mozilla.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
l-0004.l-msedge.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |