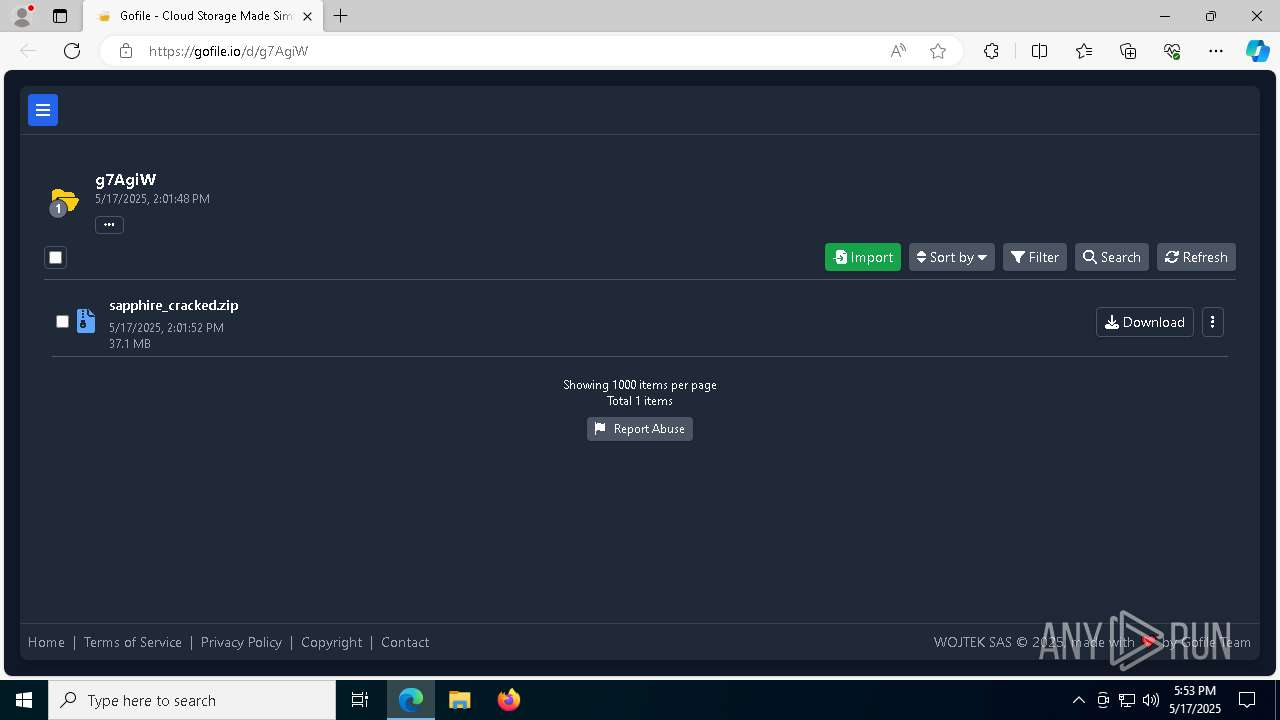
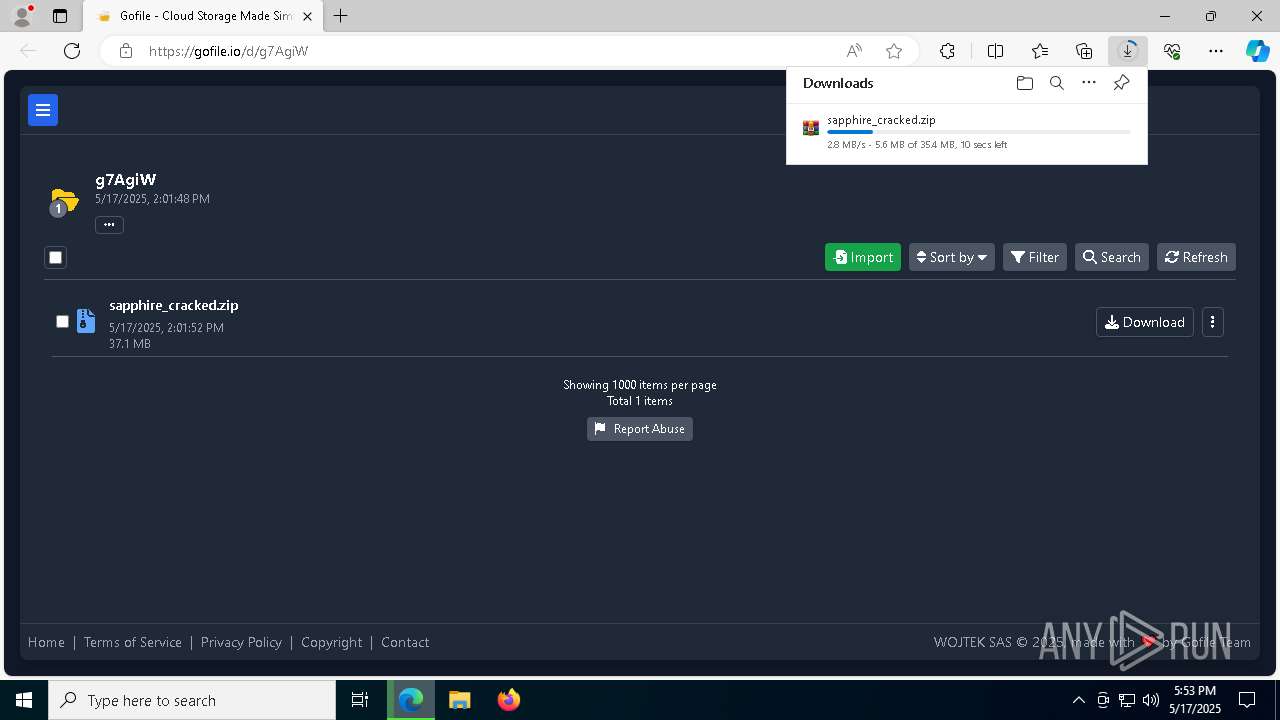
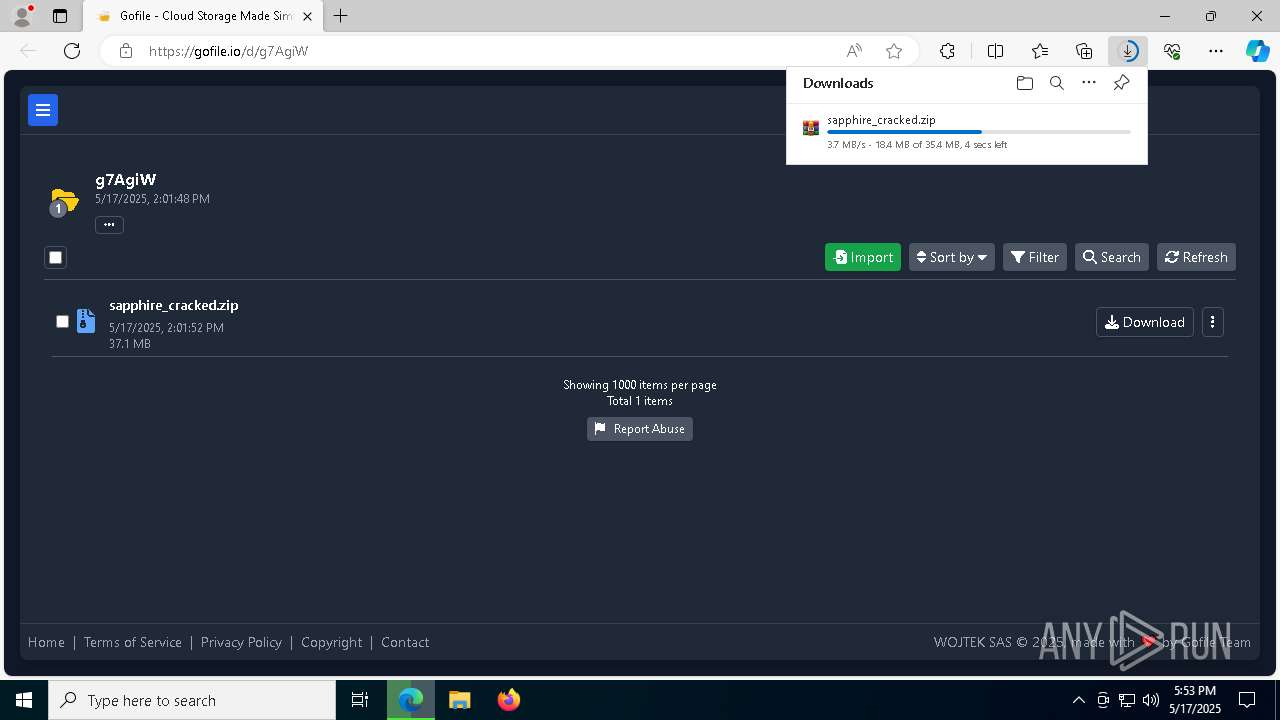
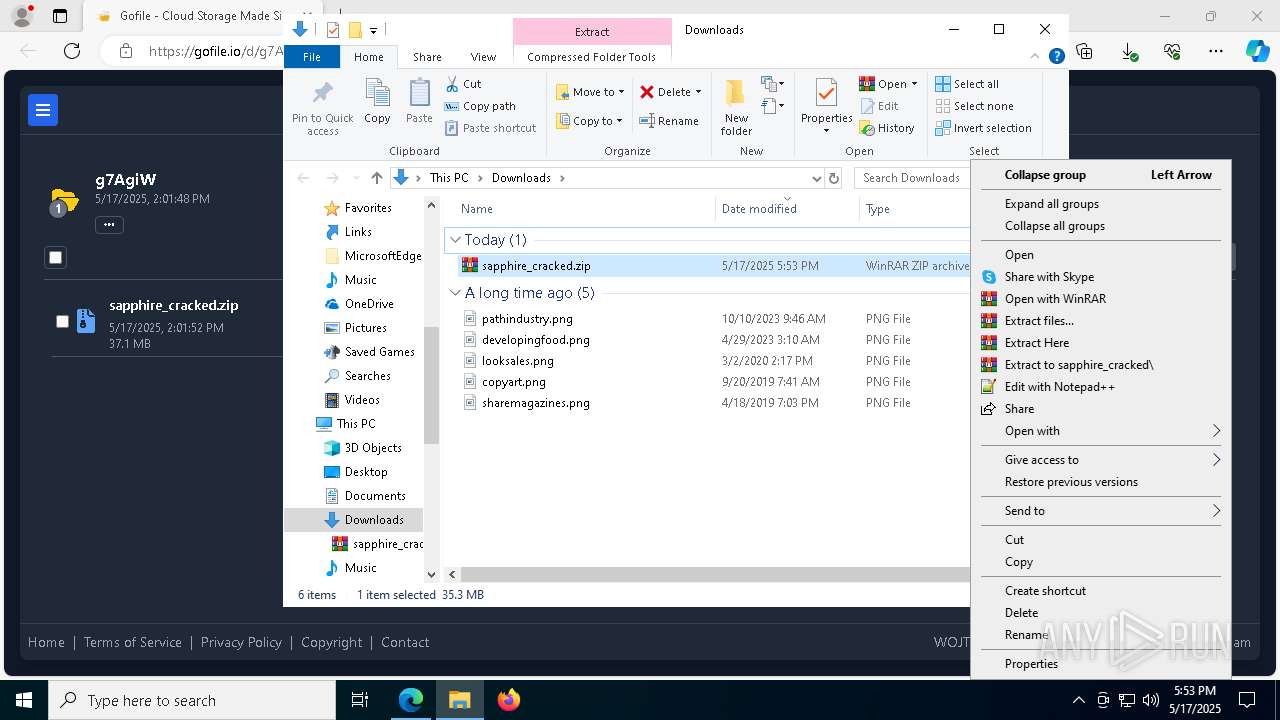
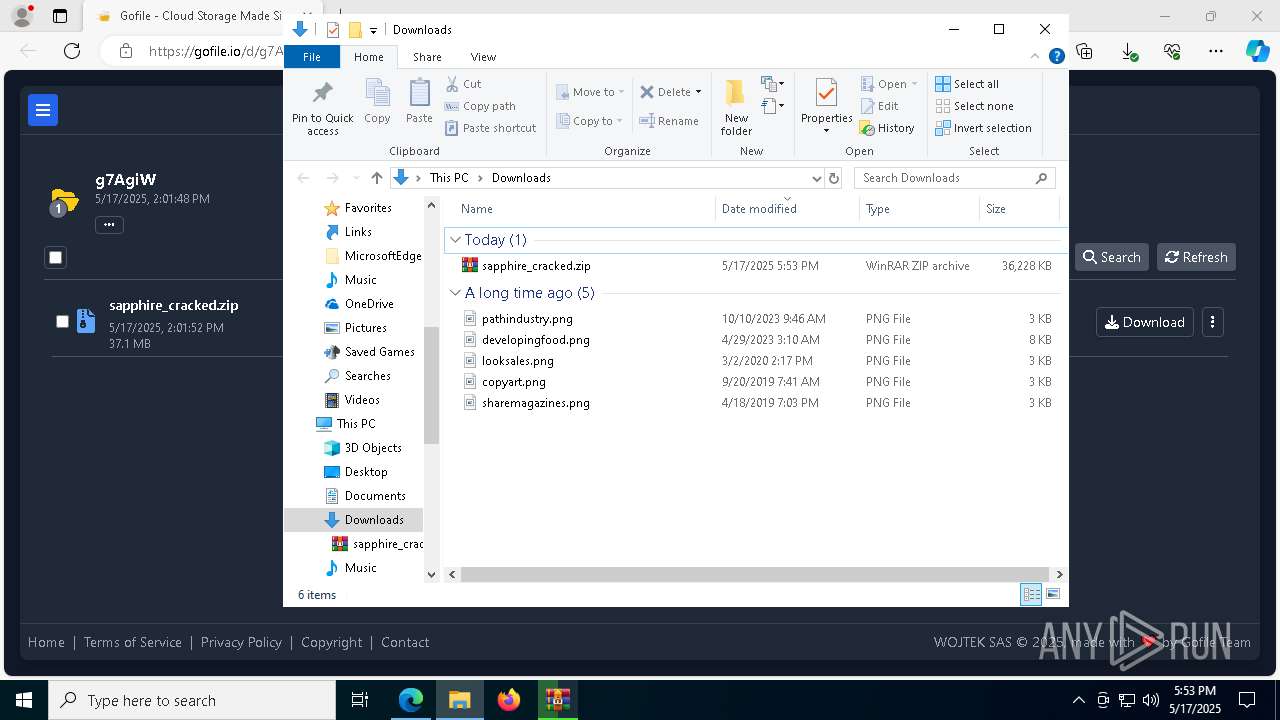
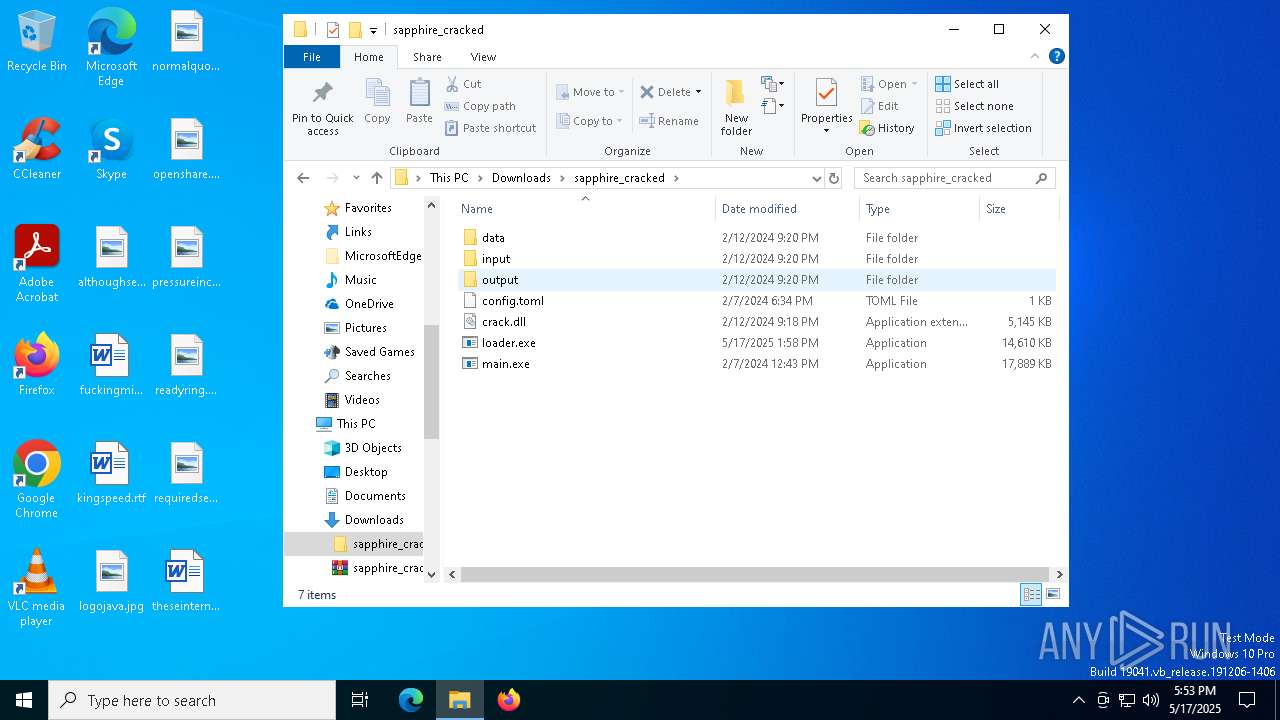
| URL: | https://gofile.io/d/g7AgiW |
| Full analysis: | https://app.any.run/tasks/df907503-abd8-4891-b64d-e13d13a601a1 |
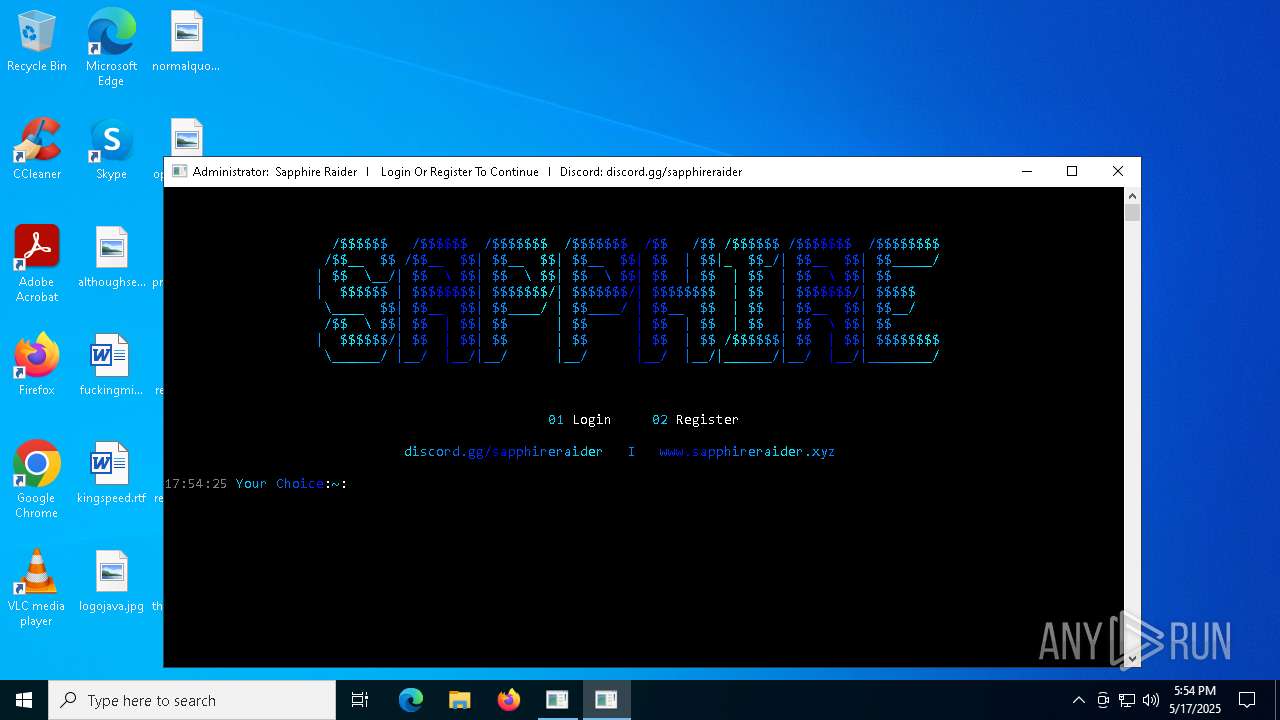
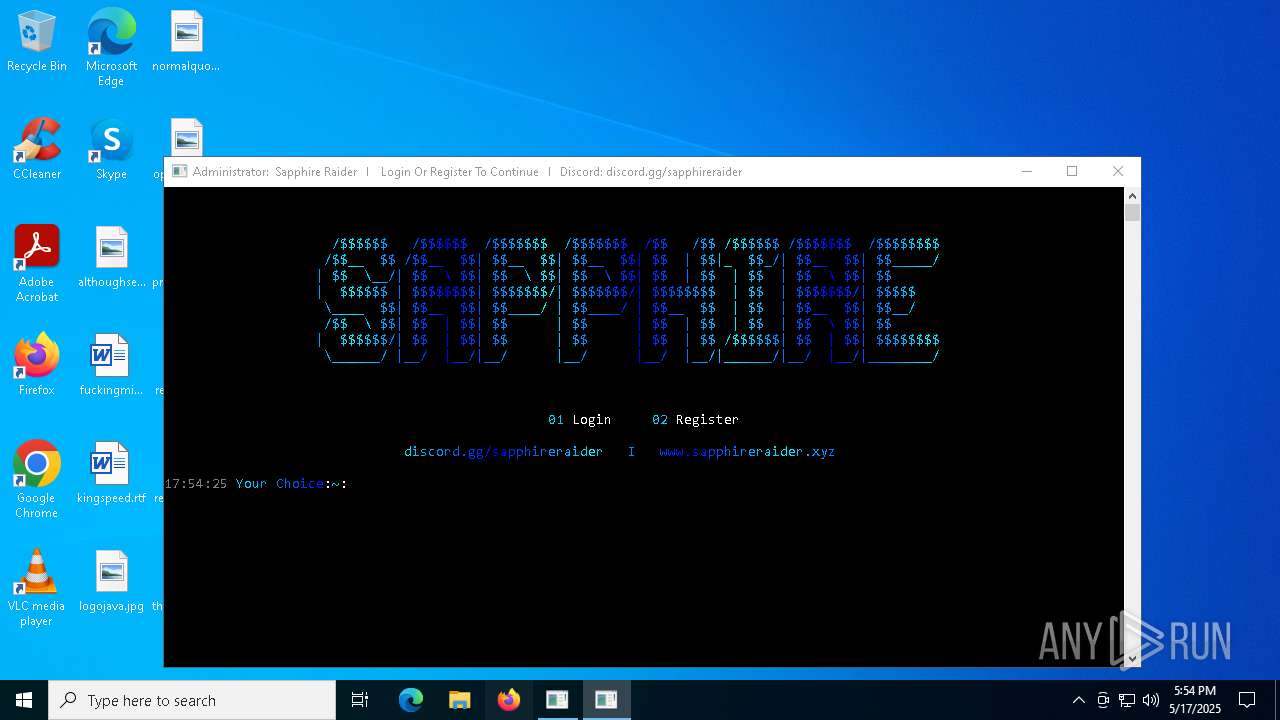
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | May 17, 2025, 17:52:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 209A7B0FAF516D74E1FAF1DADA066D9A |
| SHA1: | E5F178E72A284753F228D82AA92B78D4E73C9AAB |
| SHA256: | C1274945325BA1EAACC47951D5082F1F39A622A219061D2D4605DDCE29E761FC |
| SSDEEP: | 3:N8rxL16yn:2ZX |
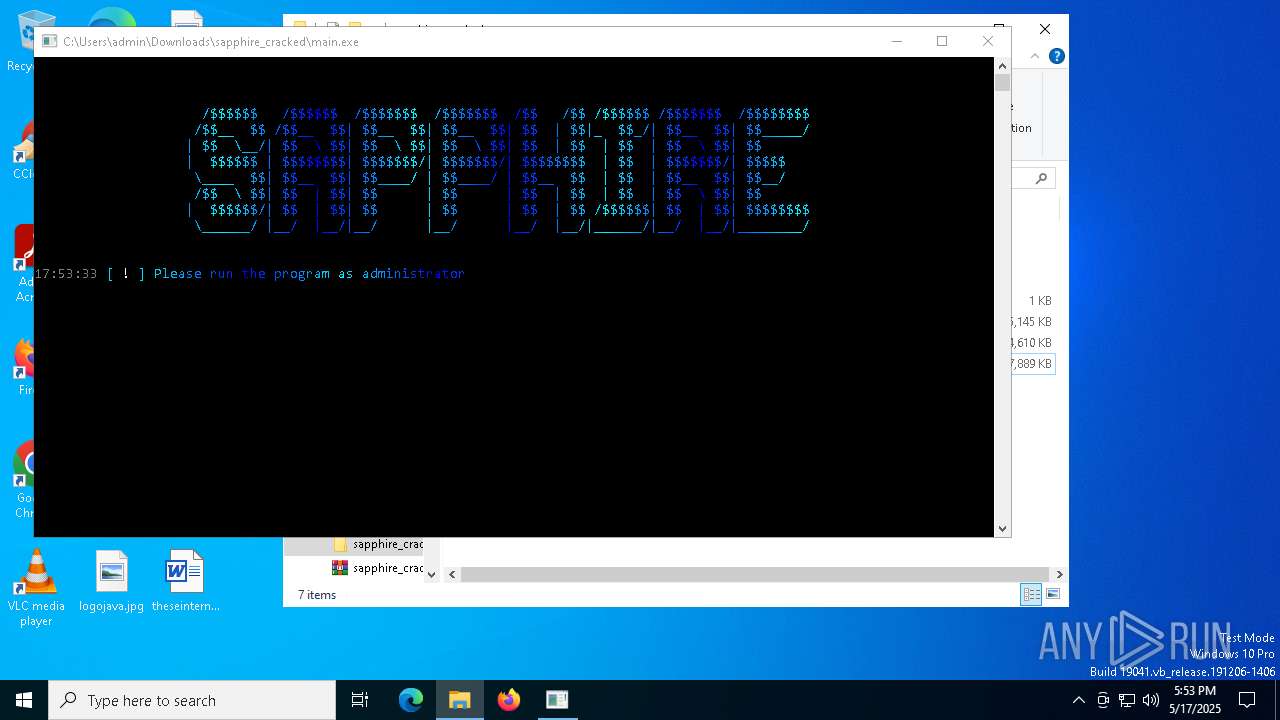
MALICIOUS
TROX has been detected
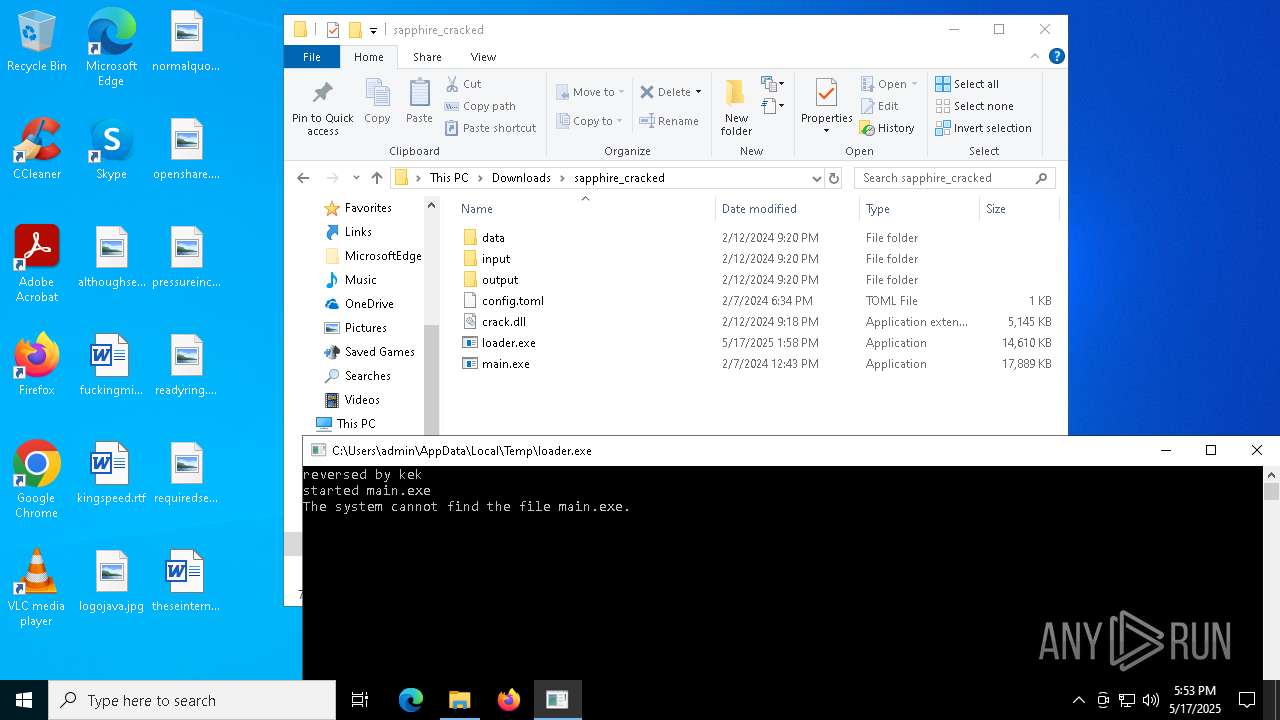
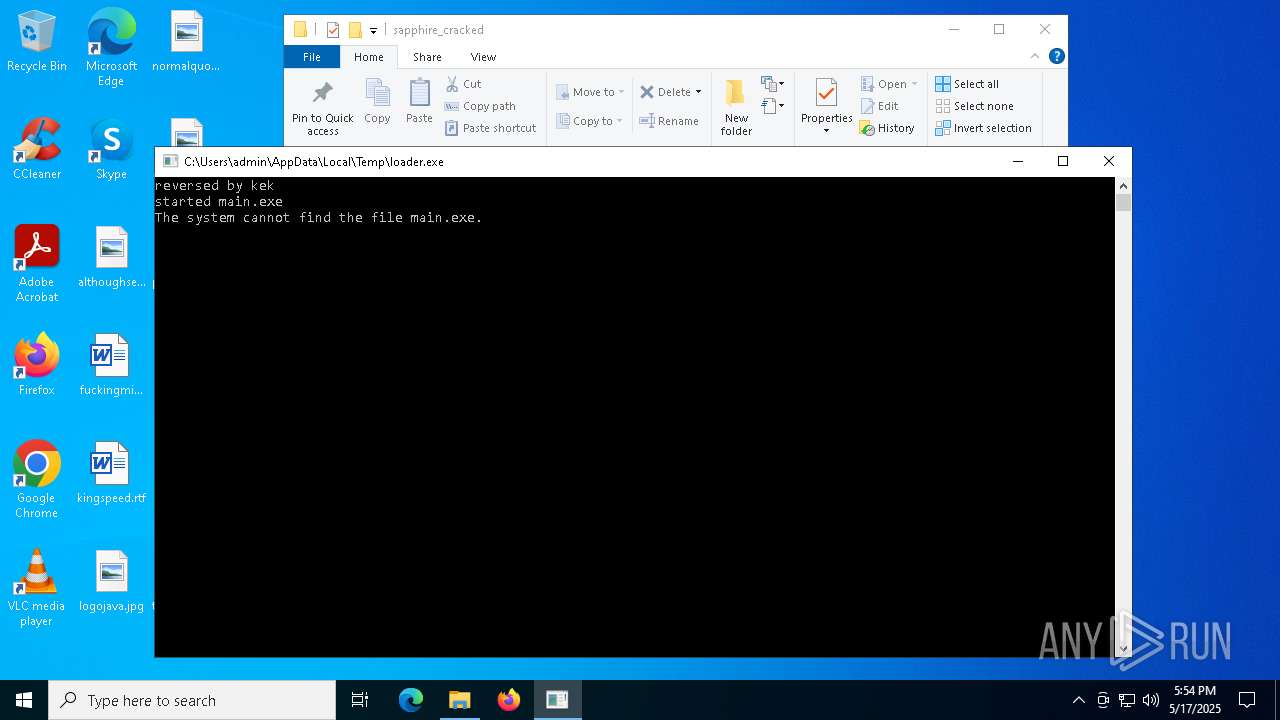
- main.exe (PID: 7420)
- loader.exe (PID: 7788)
- main.exe (PID: 8360)
- loader.exe (PID: 4932)
- main.exe (PID: 4000)
Known privilege escalation attack
- dllhost.exe (PID: 6300)
Adds path to the Windows Defender exclusion list
- Built.exe (PID: 7556)
- cmd.exe (PID: 7196)
- cmd.exe (PID: 7416)
- Built.exe (PID: 7436)
- cmd.exe (PID: 744)
- cmd.exe (PID: 7300)
Executing a file with an untrusted certificate
- Built.exe (PID: 7556)
- Built.exe (PID: 7464)
- Built.exe (PID: 7760)
- Built.exe (PID: 7436)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 4448)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 7504)
- powershell.exe (PID: 8840)
Changes Windows Defender settings
- cmd.exe (PID: 7196)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 744)
- cmd.exe (PID: 4448)
- cmd.exe (PID: 7300)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 7504)
- powershell.exe (PID: 8840)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 7504)
- powershell.exe (PID: 8840)
Changes settings for real-time protection
- powershell.exe (PID: 7504)
- powershell.exe (PID: 8840)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 7504)
- powershell.exe (PID: 8840)
Changes Controlled Folder Access settings
- powershell.exe (PID: 7504)
- powershell.exe (PID: 8840)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 7504)
- powershell.exe (PID: 8840)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 6112)
- cmd.exe (PID: 1324)
Bypass execution policy to execute commands
- powershell.exe (PID: 6264)
- powershell.exe (PID: 7228)
GROWTOPIA has been detected (YARA)
- Built.exe (PID: 7556)
DISCORDGRABBER has been detected (YARA)
- Built.exe (PID: 7556)
BLANKGRABBER has been detected (SURICATA)
- Built.exe (PID: 7556)
- Built.exe (PID: 7436)
UMBRALSTEALER has been detected (YARA)
- Built.exe (PID: 7556)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 1228)
- MpCmdRun.exe (PID: 8700)
SUSPICIOUS
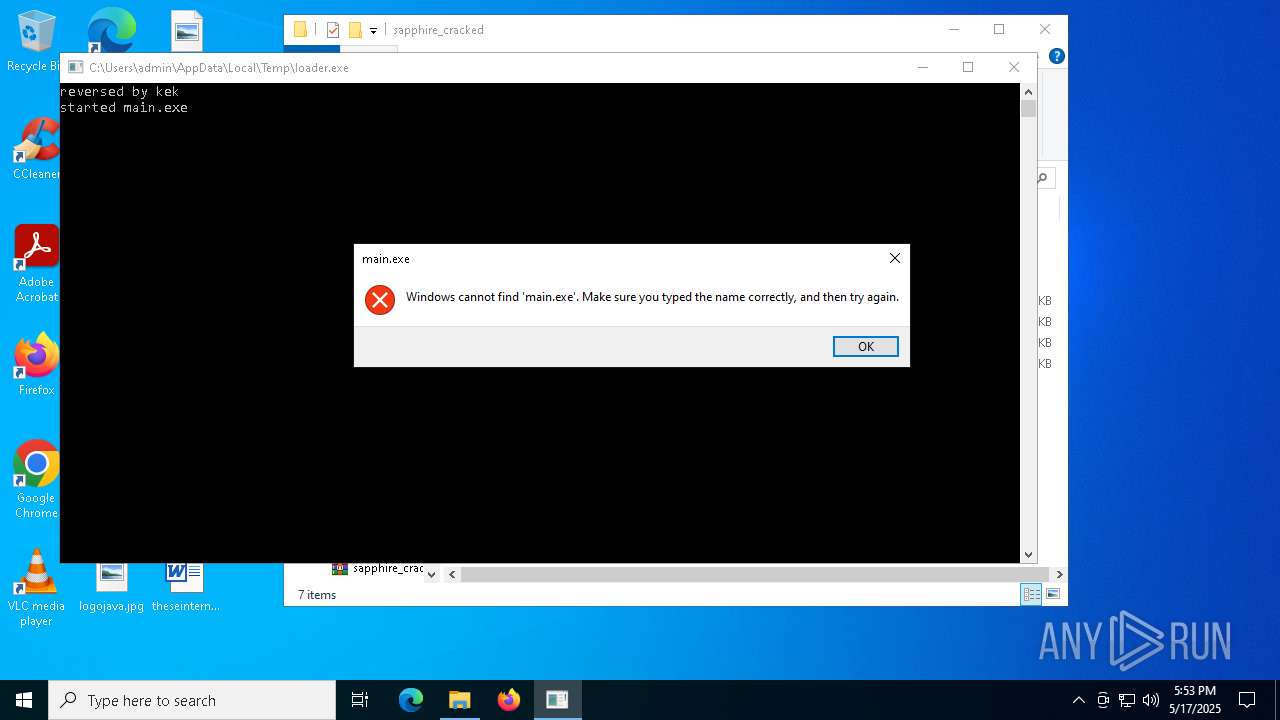
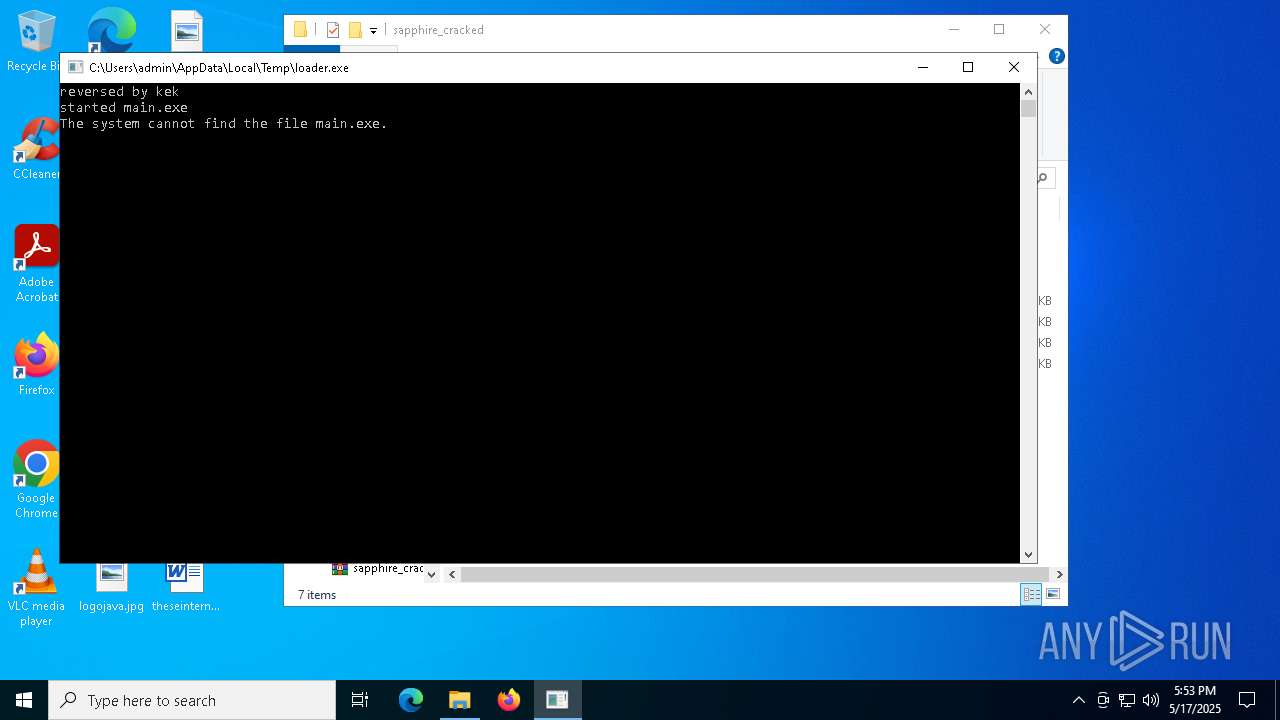
Process drops legitimate windows executable
- main.exe (PID: 7420)
- loader.exe (PID: 7788)
- dwm.exe (PID: 7600)
- Built.exe (PID: 7464)
- Built.exe (PID: 7556)
- main.exe (PID: 8360)
- loader.exe (PID: 4932)
- Built.exe (PID: 7760)
- Built.exe (PID: 7436)
- main.exe (PID: 4000)
Process drops python dynamic module
- main.exe (PID: 7420)
- loader.exe (PID: 7788)
- Built.exe (PID: 7464)
- main.exe (PID: 8360)
- loader.exe (PID: 4932)
- Built.exe (PID: 7760)
- main.exe (PID: 4000)
Executable content was dropped or overwritten
- main.exe (PID: 7420)
- loader.exe (PID: 7788)
- dwm.exe (PID: 7600)
- Built.exe (PID: 7464)
- Built.exe (PID: 7556)
- loader.exe (PID: 2092)
- csc.exe (PID: 6760)
- main.exe (PID: 8360)
- loader.exe (PID: 4932)
- Built.exe (PID: 7760)
- Built.exe (PID: 7436)
- csc.exe (PID: 8640)
- main.exe (PID: 4000)
The process drops C-runtime libraries
- main.exe (PID: 7420)
- loader.exe (PID: 7788)
- Built.exe (PID: 7464)
- main.exe (PID: 8360)
- loader.exe (PID: 4932)
- Built.exe (PID: 7760)
- main.exe (PID: 4000)
Loads Python modules
- main.exe (PID: 7212)
Reads security settings of Internet Explorer
- main.exe (PID: 7420)
Probably UAC bypass using CMSTP.exe (Connection Manager service profile)
- loader.exe (PID: 7352)
- loader.exe (PID: 9128)
Uses TASKKILL.EXE to kill process
- mshta.exe (PID: 7880)
- cmd.exe (PID: 8384)
- cmd.exe (PID: 8684)
- cmd.exe (PID: 8988)
- cmd.exe (PID: 7444)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 8500)
- mshta.exe (PID: 7900)
Starts CMD.EXE for commands execution
- loader.exe (PID: 6940)
- Built.exe (PID: 7556)
- main.exe (PID: 7212)
- main.exe (PID: 8648)
- loader.exe (PID: 472)
- Built.exe (PID: 7436)
- main.exe (PID: 4944)
Starts a Microsoft application from unusual location
- Built.exe (PID: 7464)
- Built.exe (PID: 7556)
- Built.exe (PID: 7760)
- Built.exe (PID: 7436)
Application launched itself
- Built.exe (PID: 7464)
- Built.exe (PID: 7760)
Found strings related to reading or modifying Windows Defender settings
- Built.exe (PID: 7556)
- Built.exe (PID: 7436)
Get information on the list of running processes
- Built.exe (PID: 7556)
- cmd.exe (PID: 616)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 7900)
- cmd.exe (PID: 7600)
- Built.exe (PID: 7436)
- cmd.exe (PID: 7940)
- cmd.exe (PID: 4428)
- cmd.exe (PID: 5416)
- cmd.exe (PID: 4896)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7196)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 7320)
- cmd.exe (PID: 6112)
- cmd.exe (PID: 7580)
- cmd.exe (PID: 8984)
- cmd.exe (PID: 744)
- cmd.exe (PID: 4448)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 7300)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 8540)
- cmd.exe (PID: 9008)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 7012)
- cmd.exe (PID: 7232)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7196)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 744)
- cmd.exe (PID: 7300)
Script disables Windows Defender's IPS
- cmd.exe (PID: 7232)
- cmd.exe (PID: 4448)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 7232)
- cmd.exe (PID: 4448)
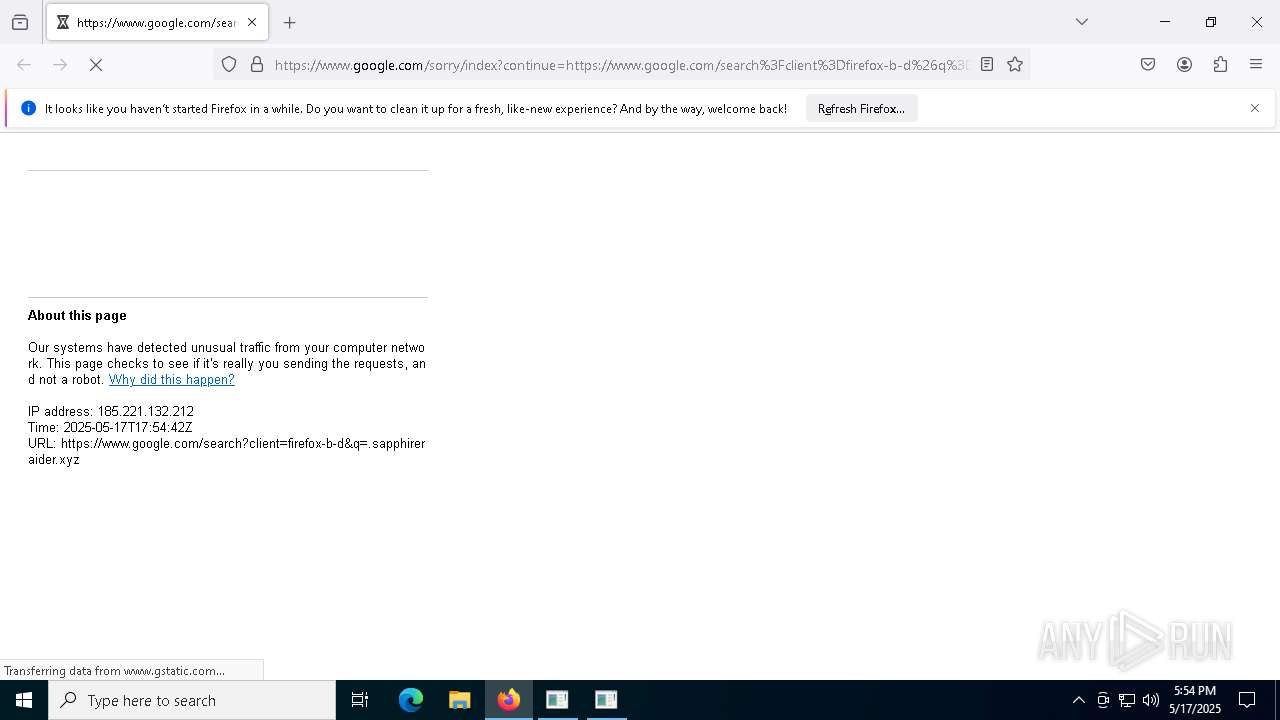
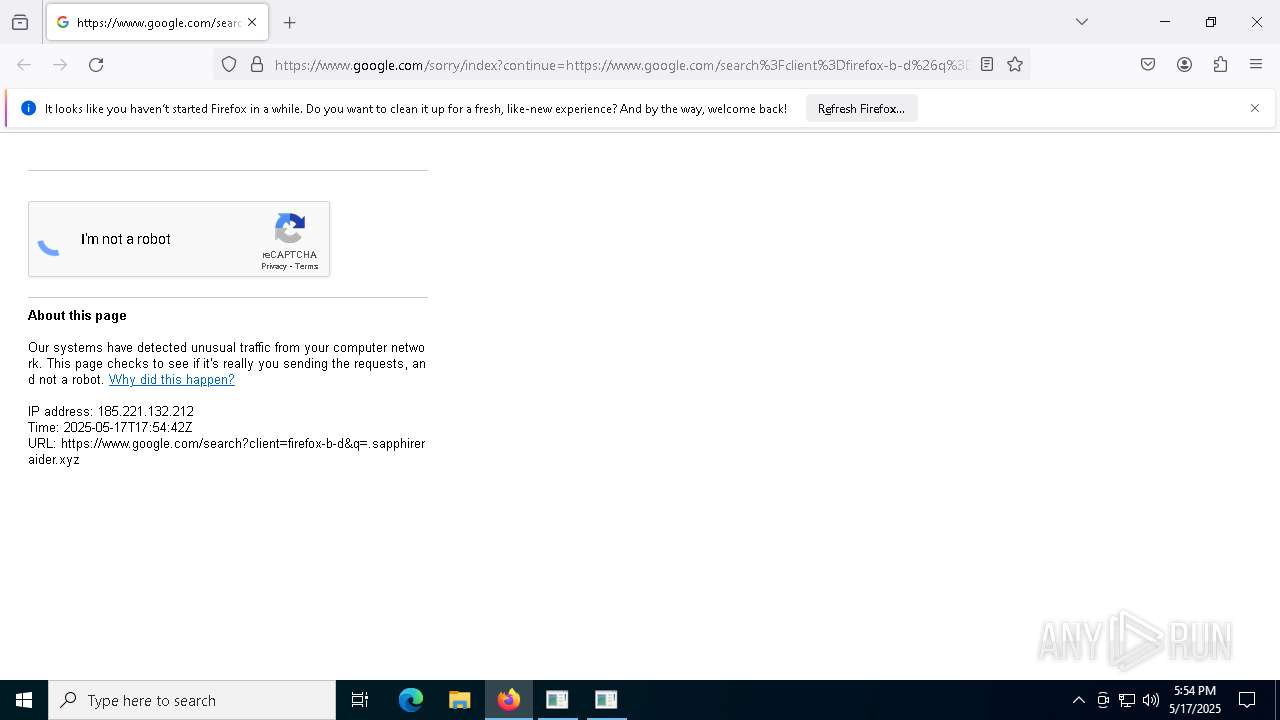
Checks for external IP
- svchost.exe (PID: 2196)
- Built.exe (PID: 7556)
- Built.exe (PID: 7436)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6668)
- cmd.exe (PID: 1748)
- cmd.exe (PID: 8240)
- cmd.exe (PID: 7448)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 4892)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 6272)
- cmd.exe (PID: 7856)
- cmd.exe (PID: 8584)
- cmd.exe (PID: 9024)
- cmd.exe (PID: 9052)
- cmd.exe (PID: 2148)
Starts application with an unusual extension
- cmd.exe (PID: 7388)
- cmd.exe (PID: 8220)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 8748)
- cmd.exe (PID: 8956)
- cmd.exe (PID: 9172)
- cmd.exe (PID: 2140)
- cmd.exe (PID: 8852)
- cmd.exe (PID: 728)
- cmd.exe (PID: 6816)
- cmd.exe (PID: 7952)
- cmd.exe (PID: 2908)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 3768)
- cmd.exe (PID: 7548)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 7732)
- cmd.exe (PID: 7580)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 6112)
- cmd.exe (PID: 1324)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 6112)
- cmd.exe (PID: 1324)
Base64-obfuscated command line is found
- cmd.exe (PID: 6112)
- cmd.exe (PID: 1324)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6760)
- csc.exe (PID: 8640)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 8672)
- cmd.exe (PID: 7144)
Possible usage of Discord/Telegram API has been detected (YARA)
- Built.exe (PID: 7556)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 7736)
- cmd.exe (PID: 8440)
The executable file from the user directory is run by the CMD process
- rar.exe (PID: 8216)
- rar.exe (PID: 5972)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Built.exe (PID: 7556)
- Built.exe (PID: 7436)
INFO
Application launched itself
- msedge.exe (PID: 864)
- msedge.exe (PID: 6032)
- firefox.exe (PID: 6964)
- firefox.exe (PID: 4696)
Checks supported languages
- identity_helper.exe (PID: 7676)
- identity_helper.exe (PID: 5968)
- main.exe (PID: 7212)
- main.exe (PID: 7420)
Create files in a temporary directory
- main.exe (PID: 7420)
Reads the computer name
- identity_helper.exe (PID: 5968)
- identity_helper.exe (PID: 7676)
- main.exe (PID: 7420)
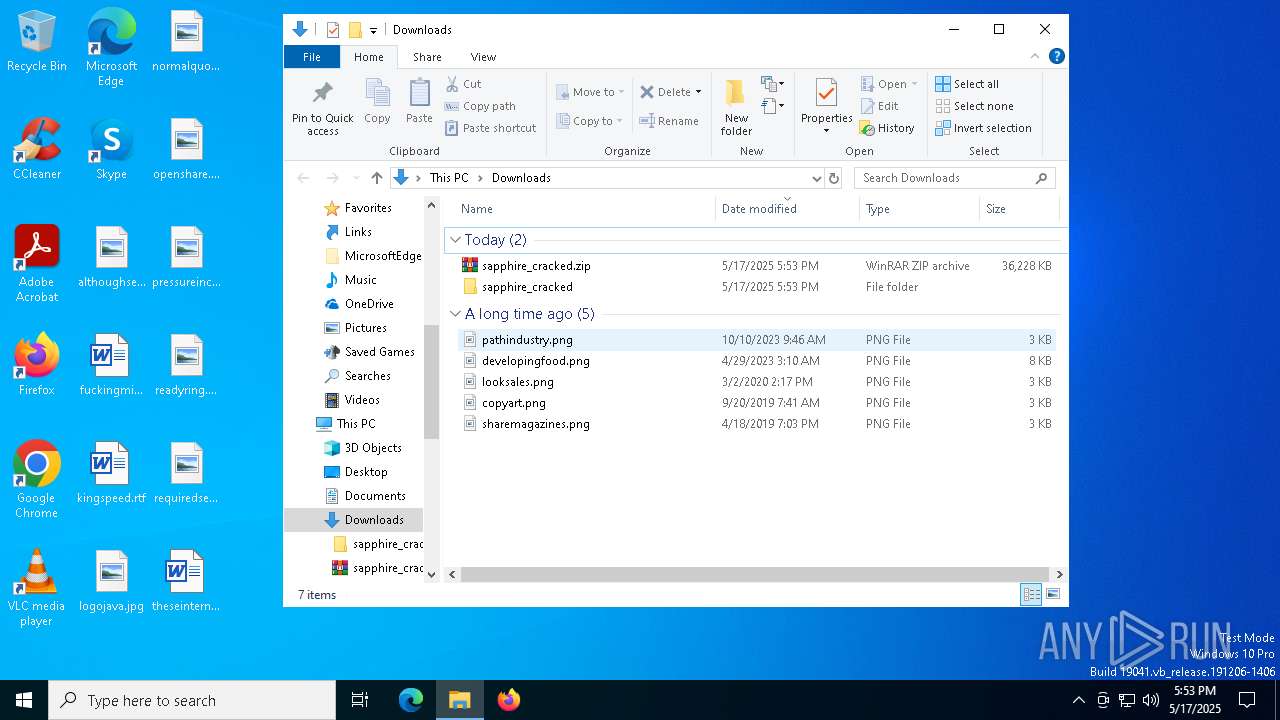
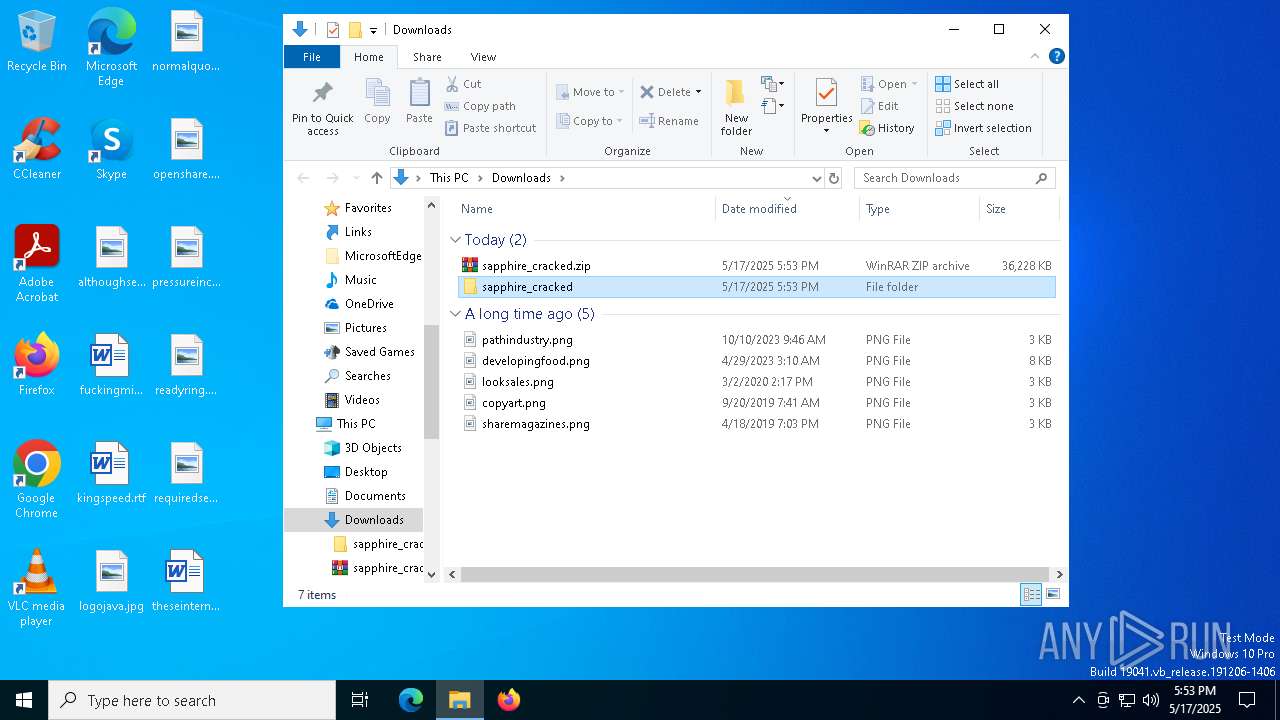
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6272)
Reads Environment values
- identity_helper.exe (PID: 5968)
- identity_helper.exe (PID: 7676)
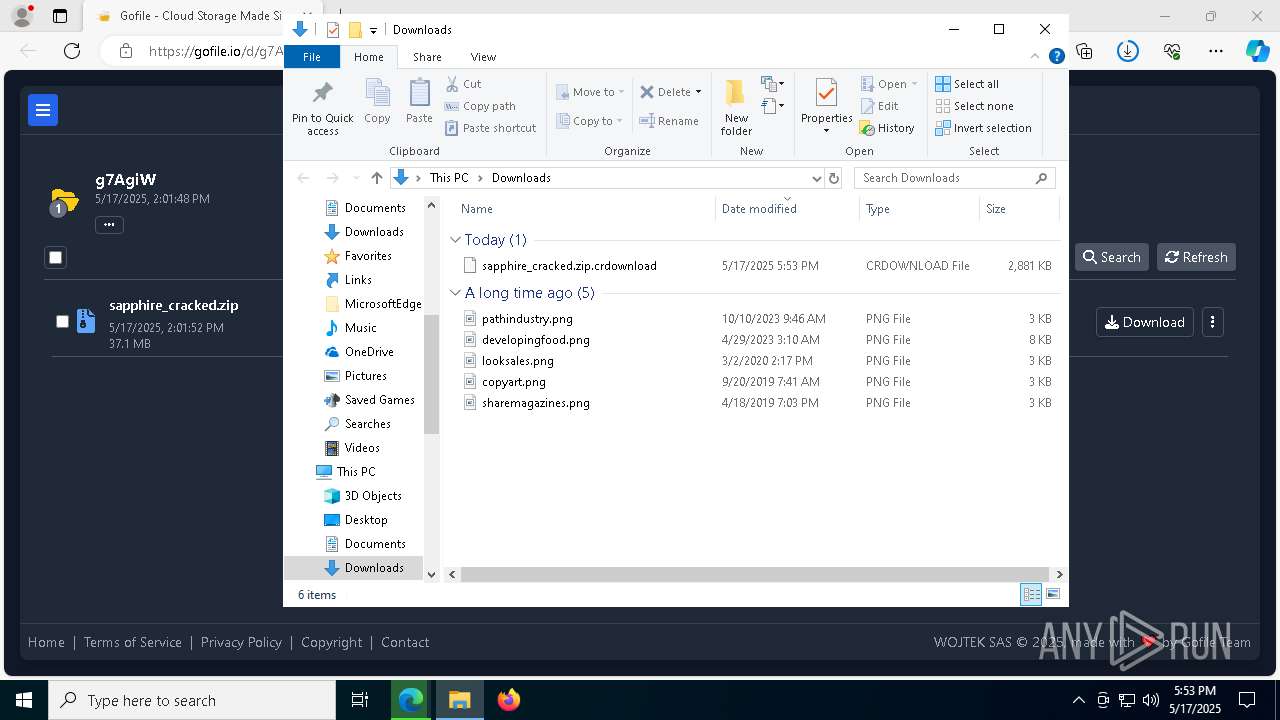
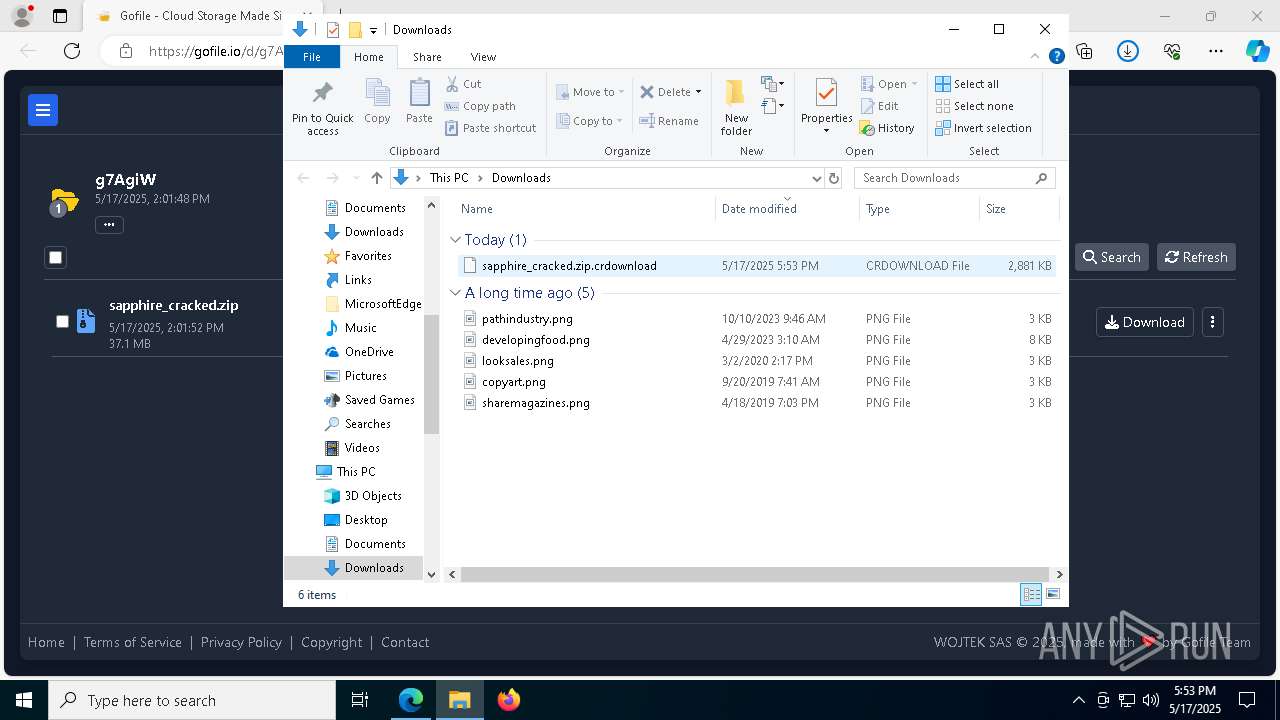
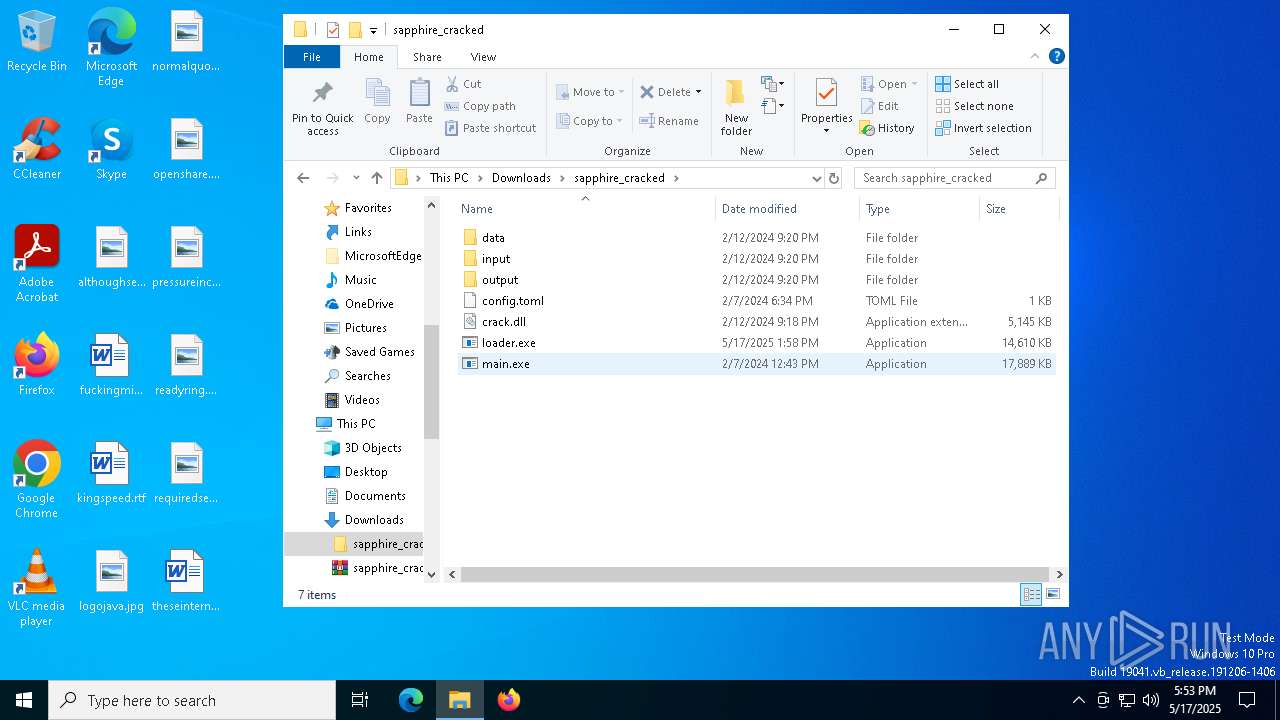
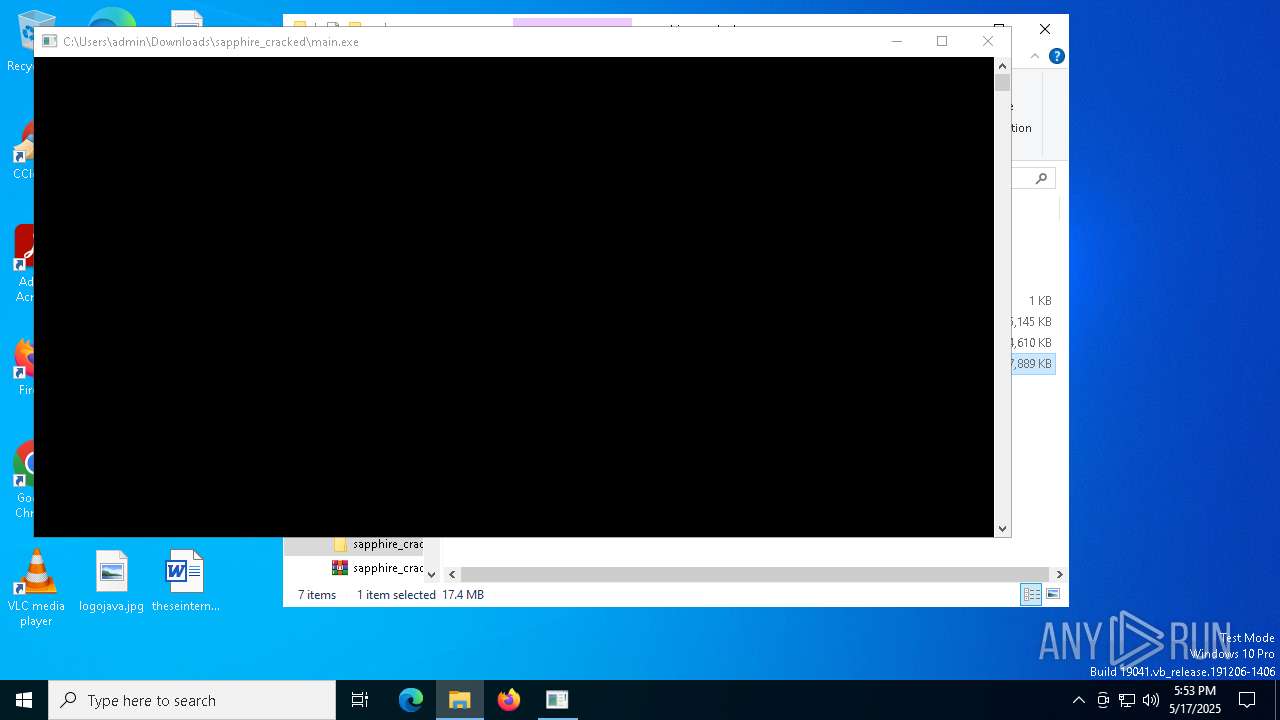
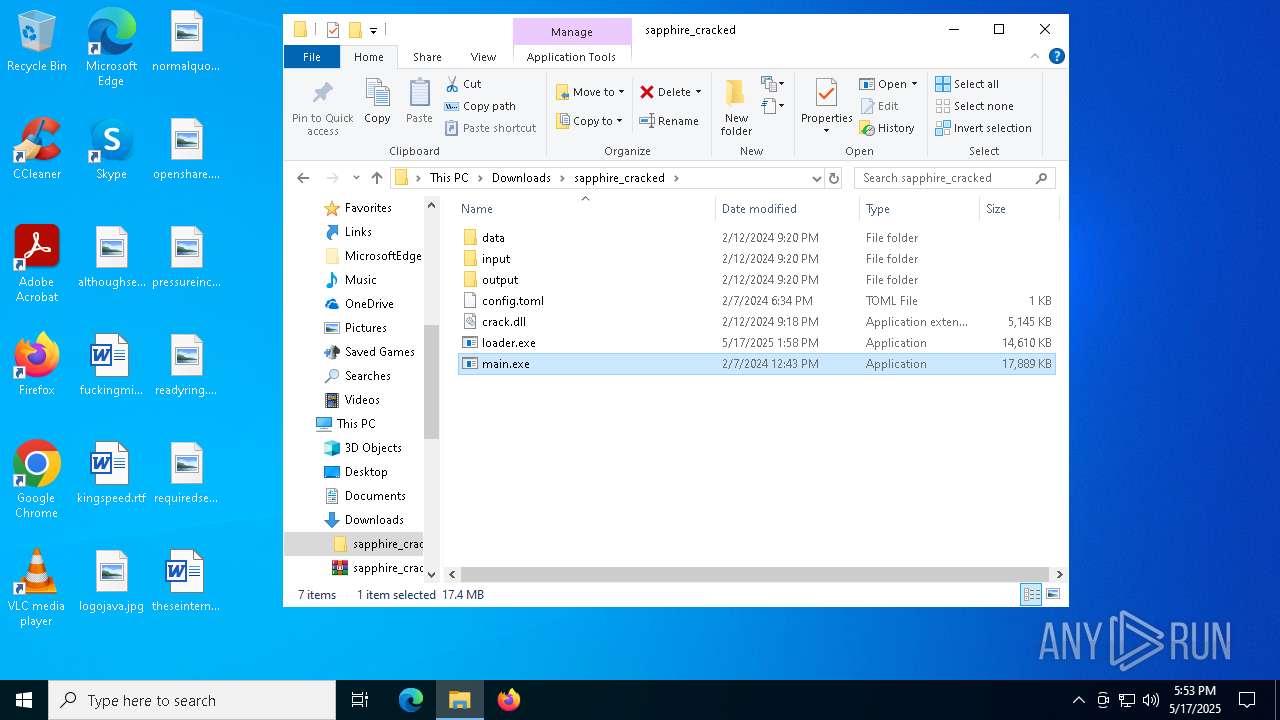
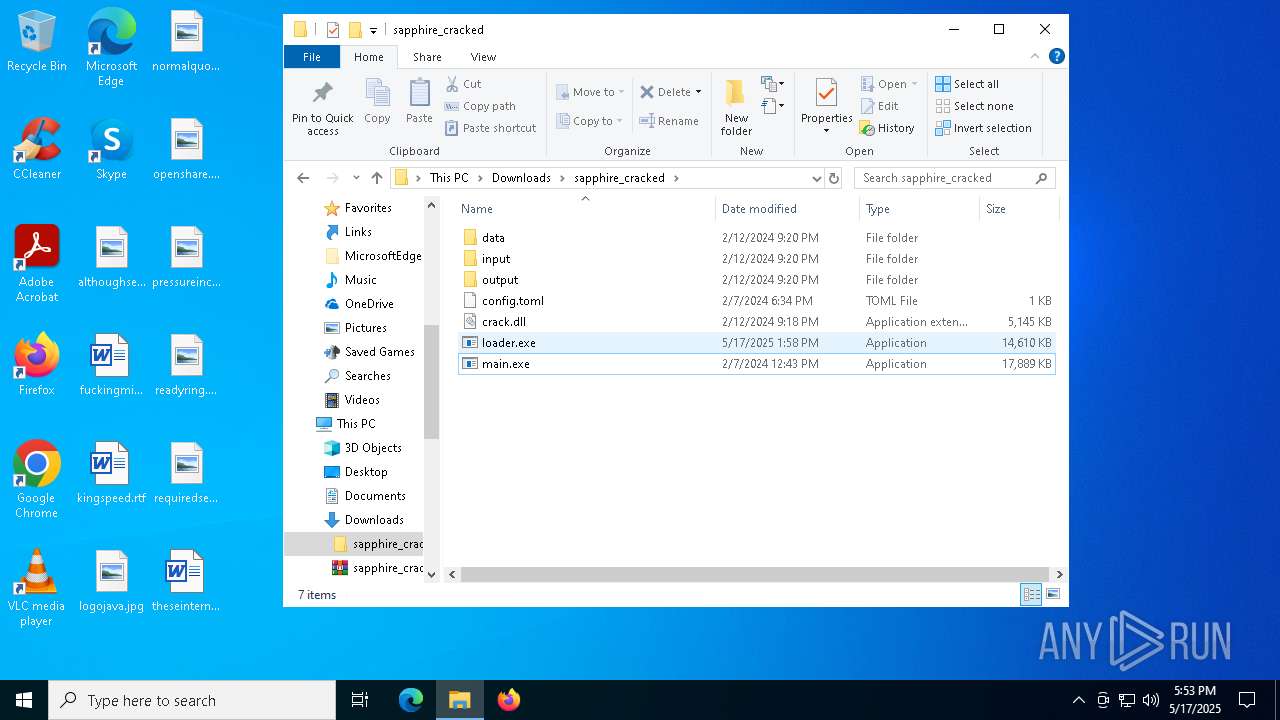
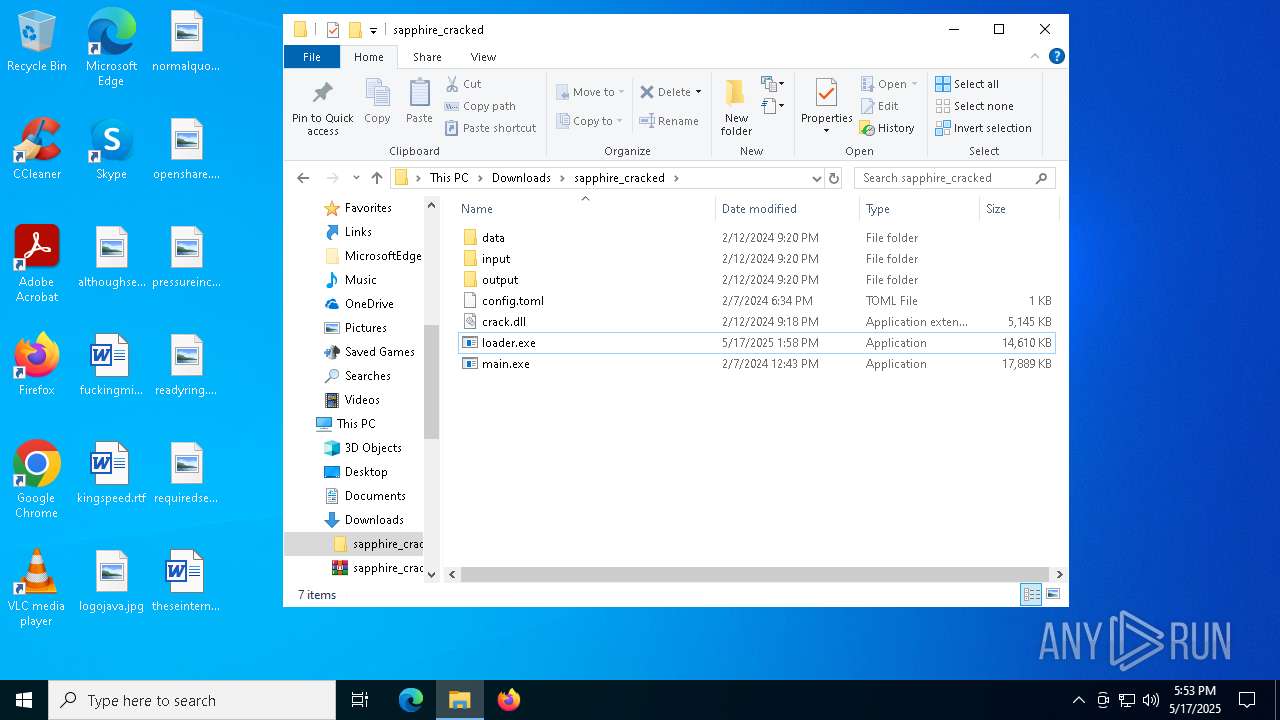
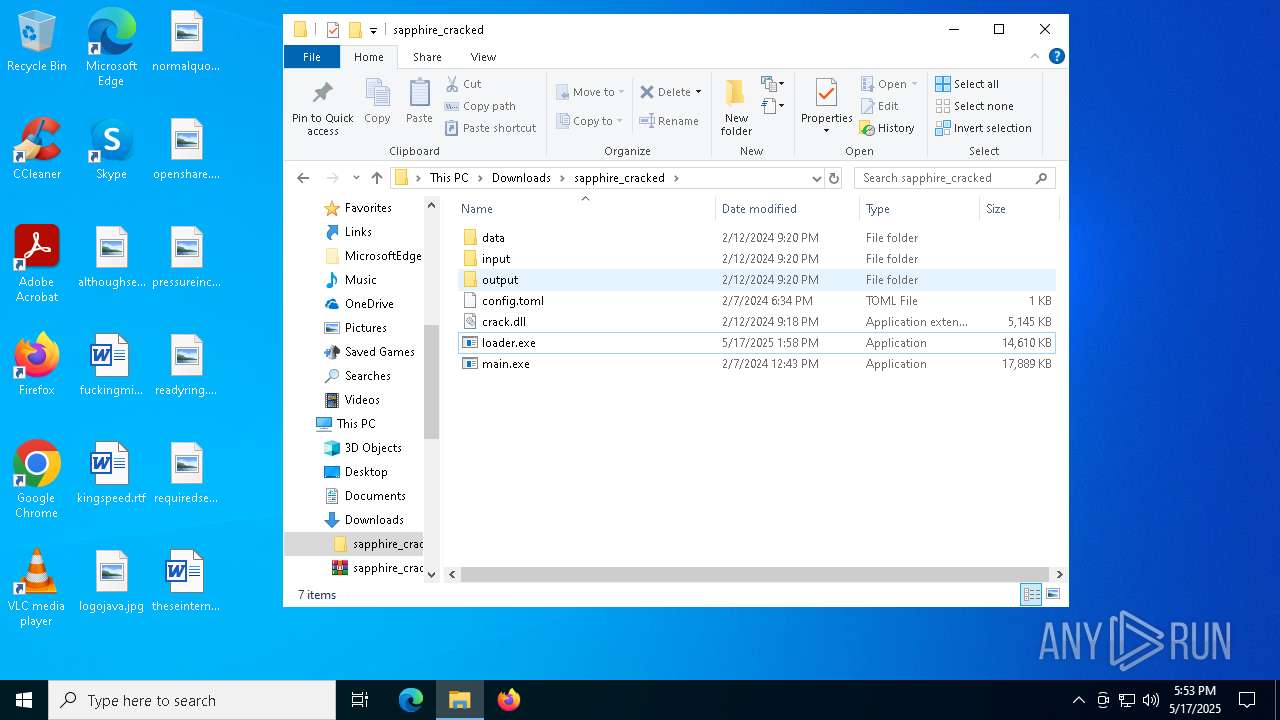
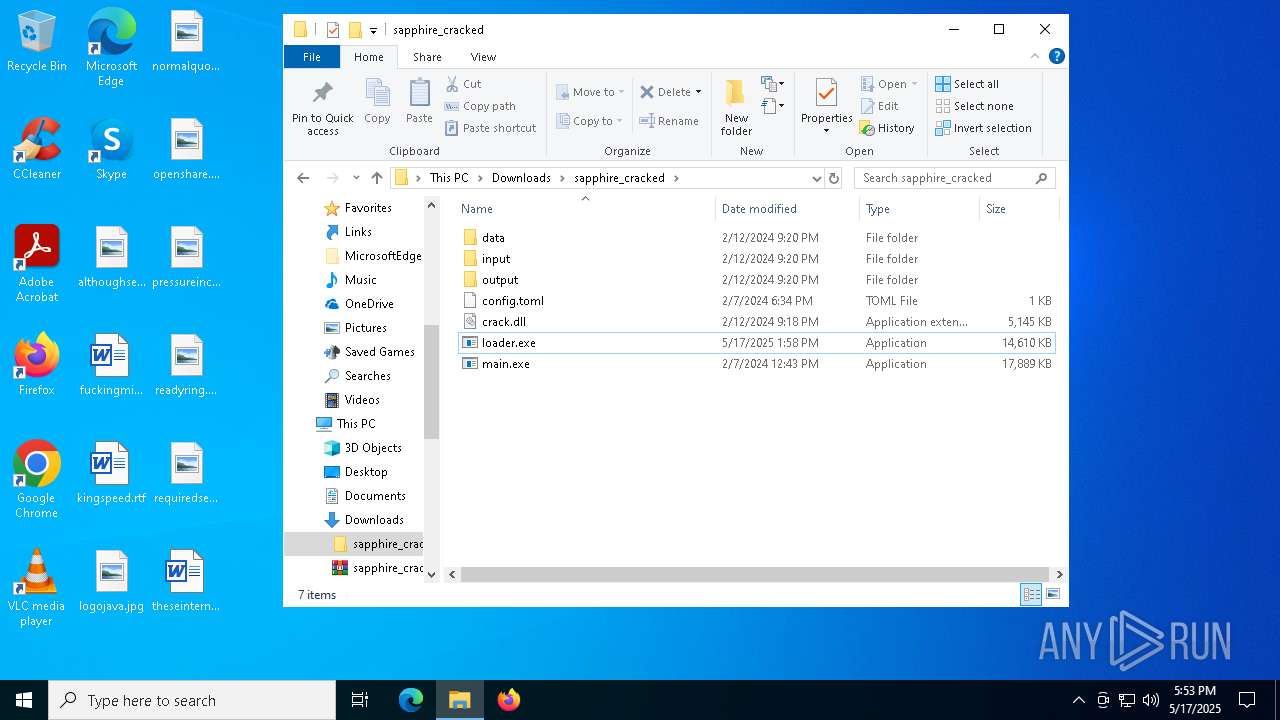
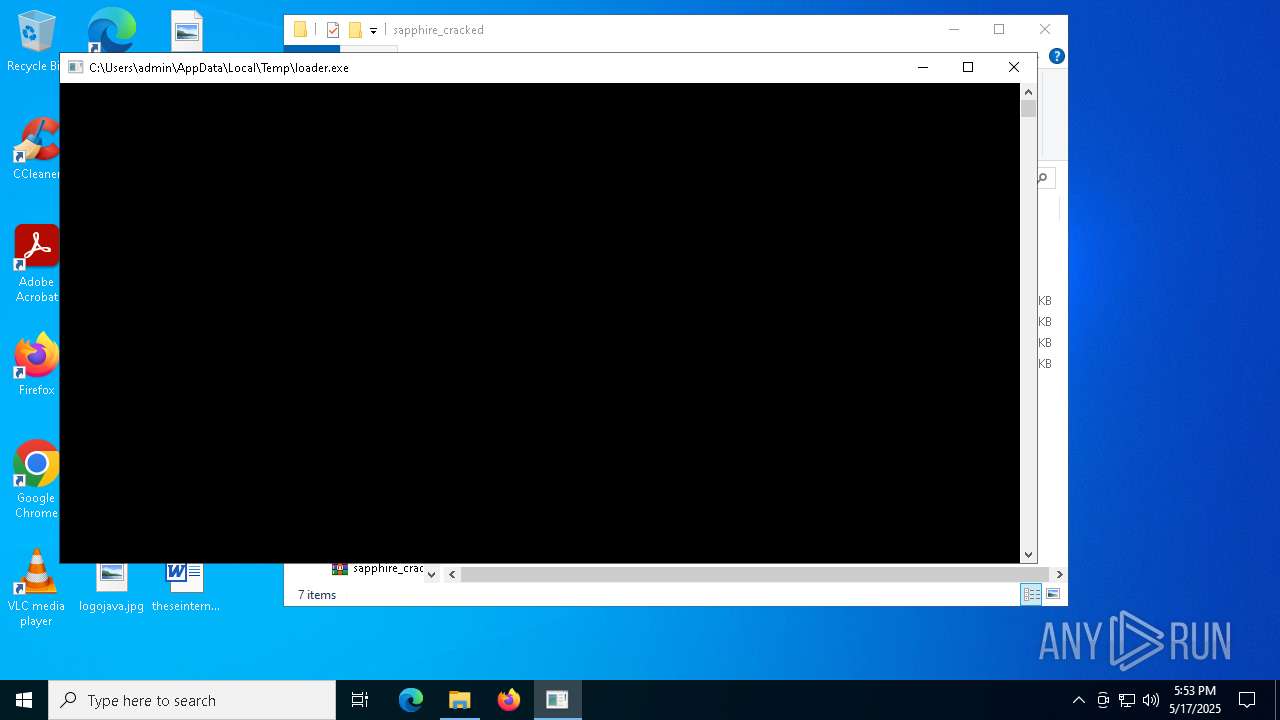
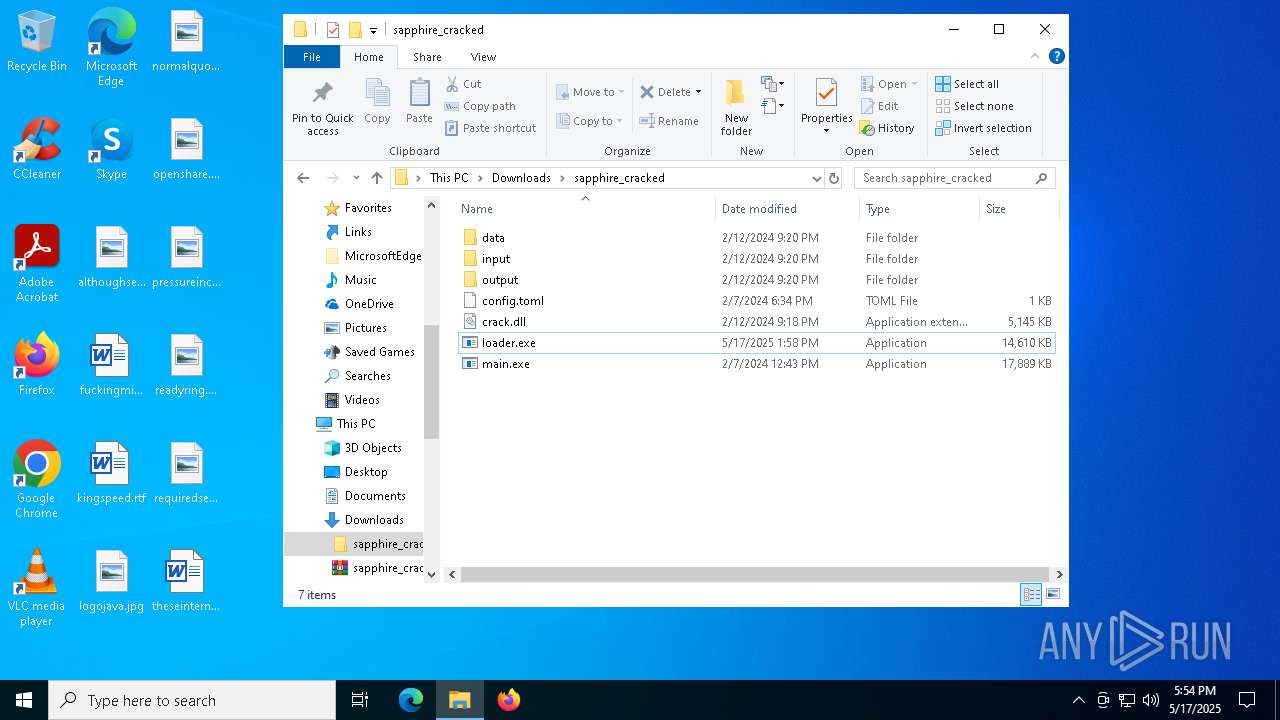
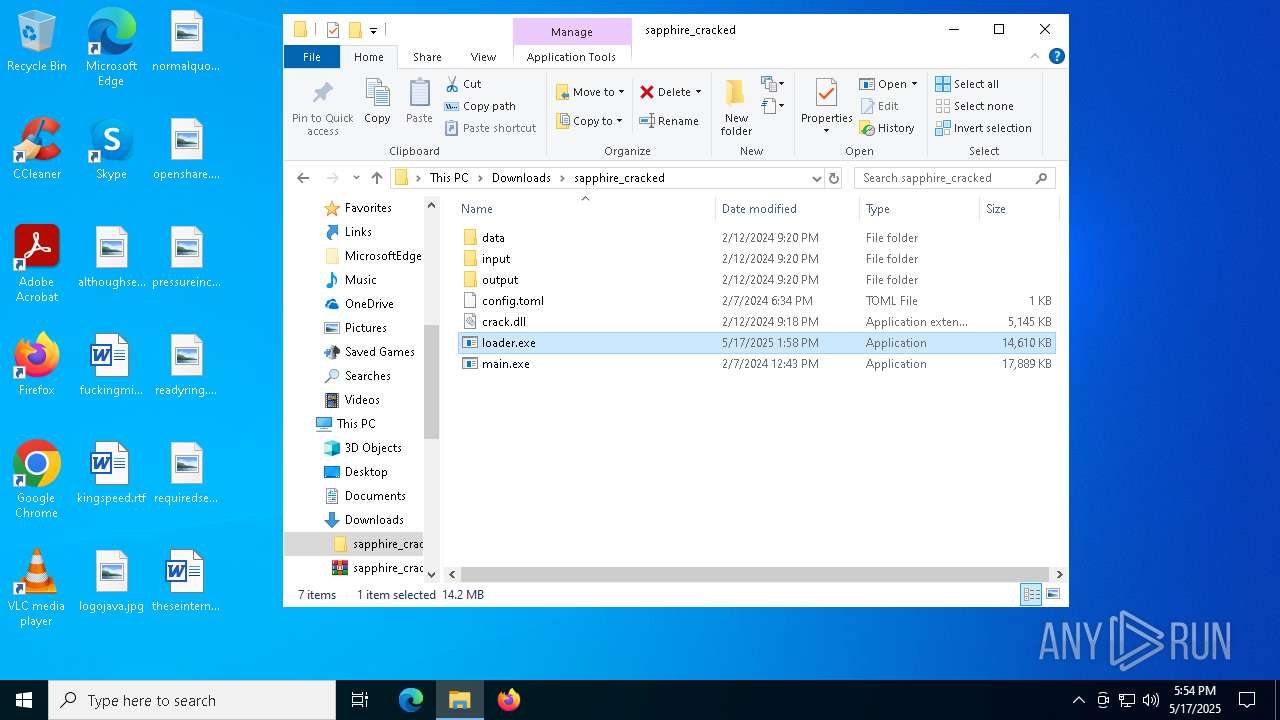
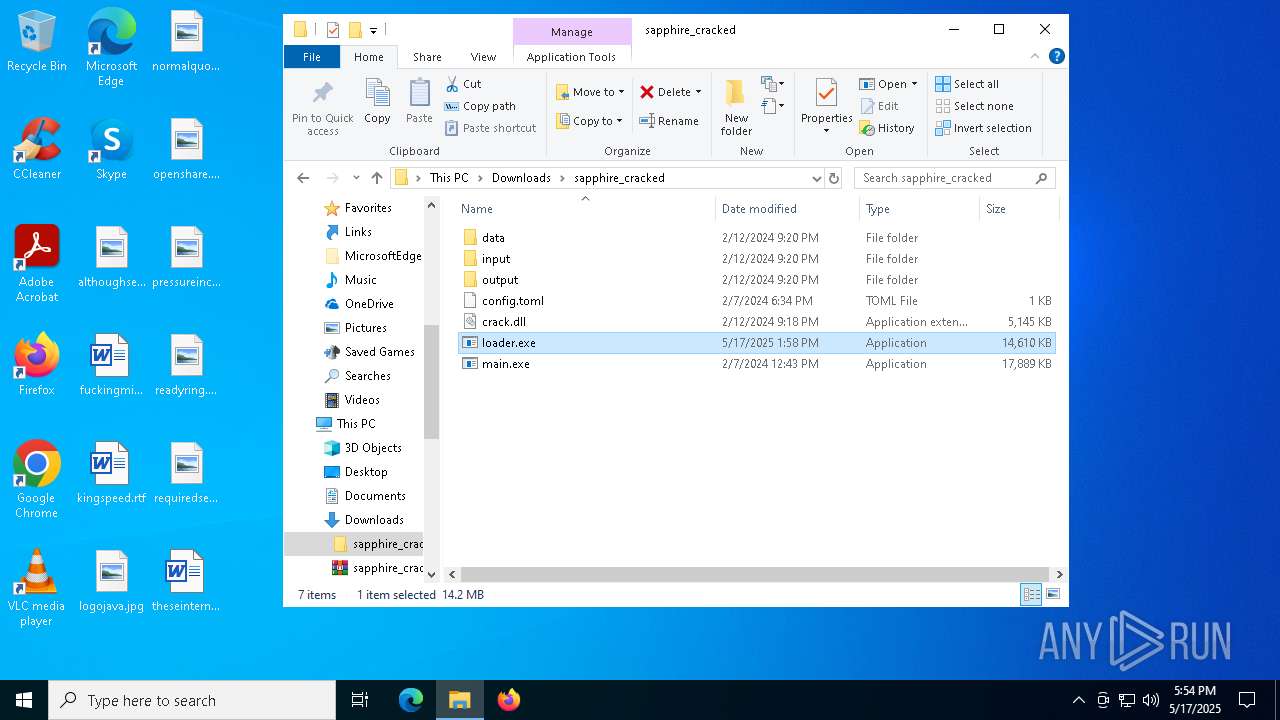
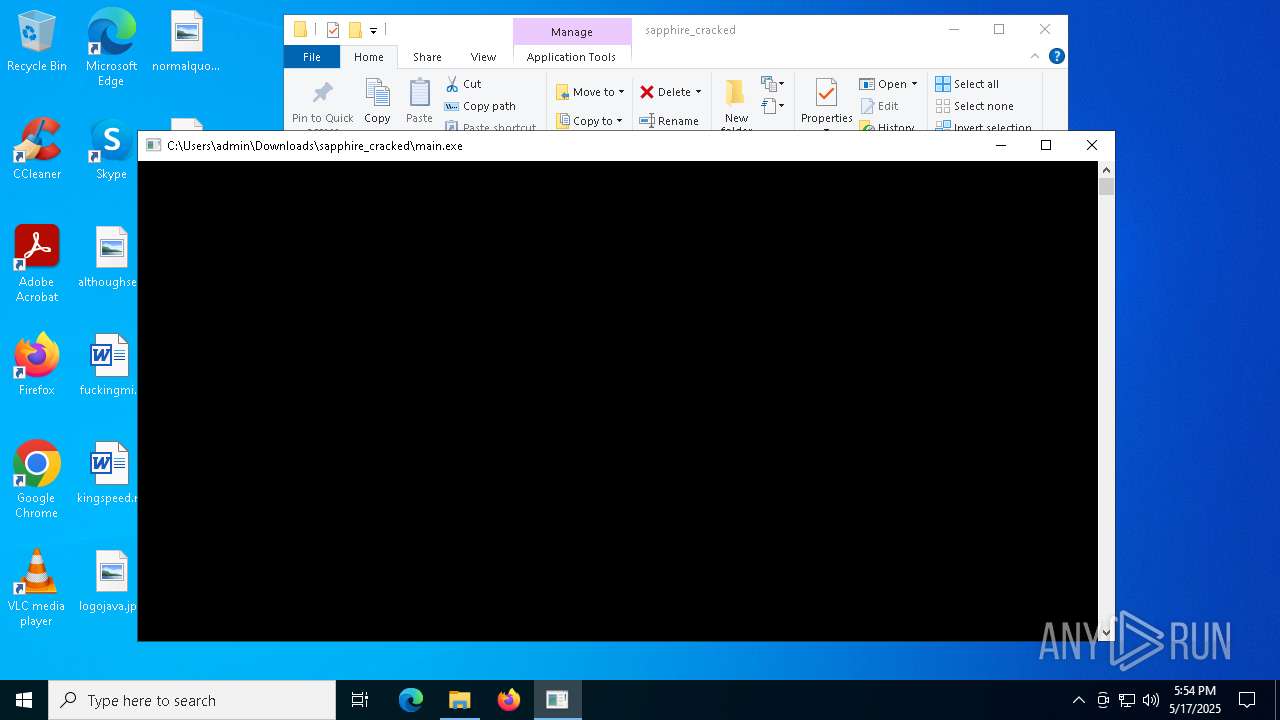
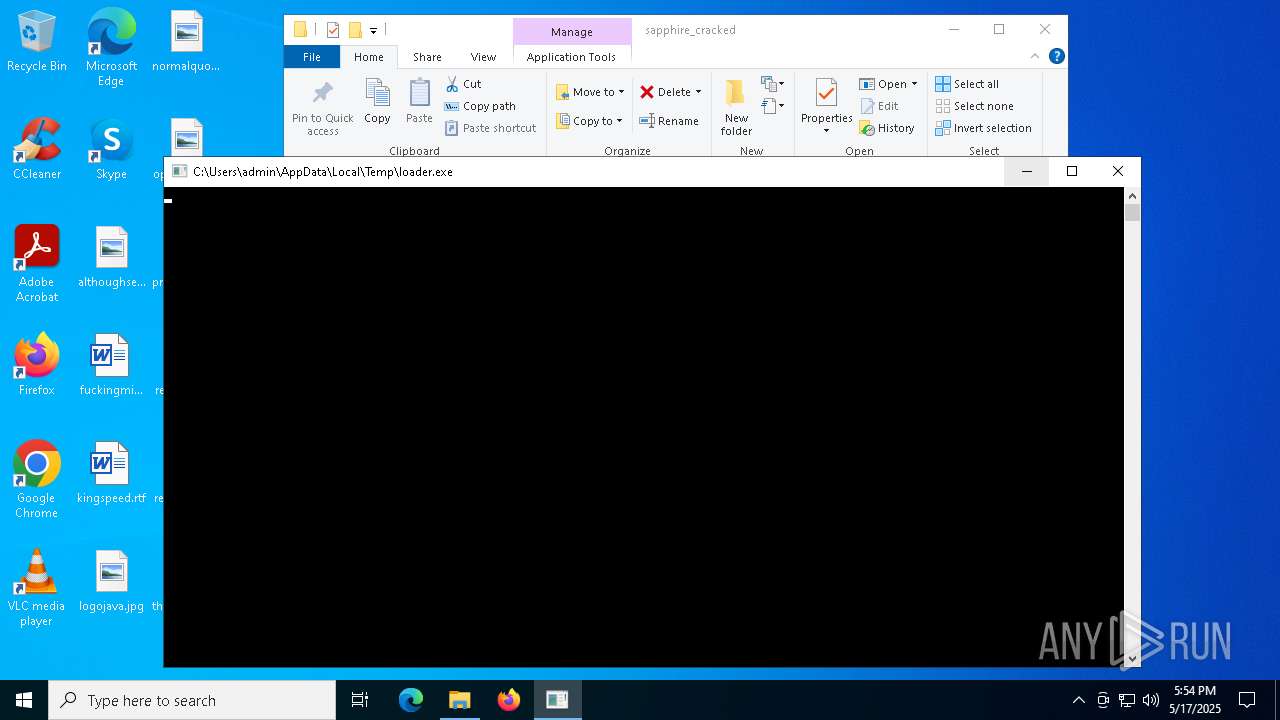
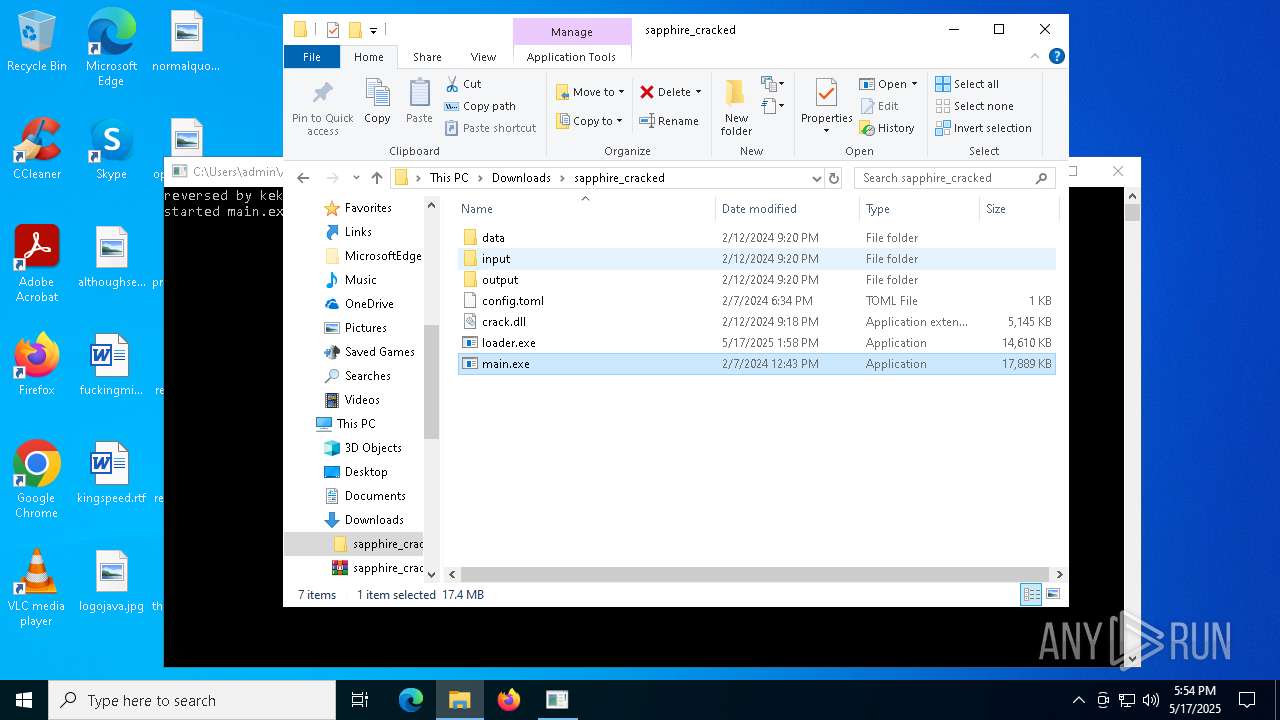
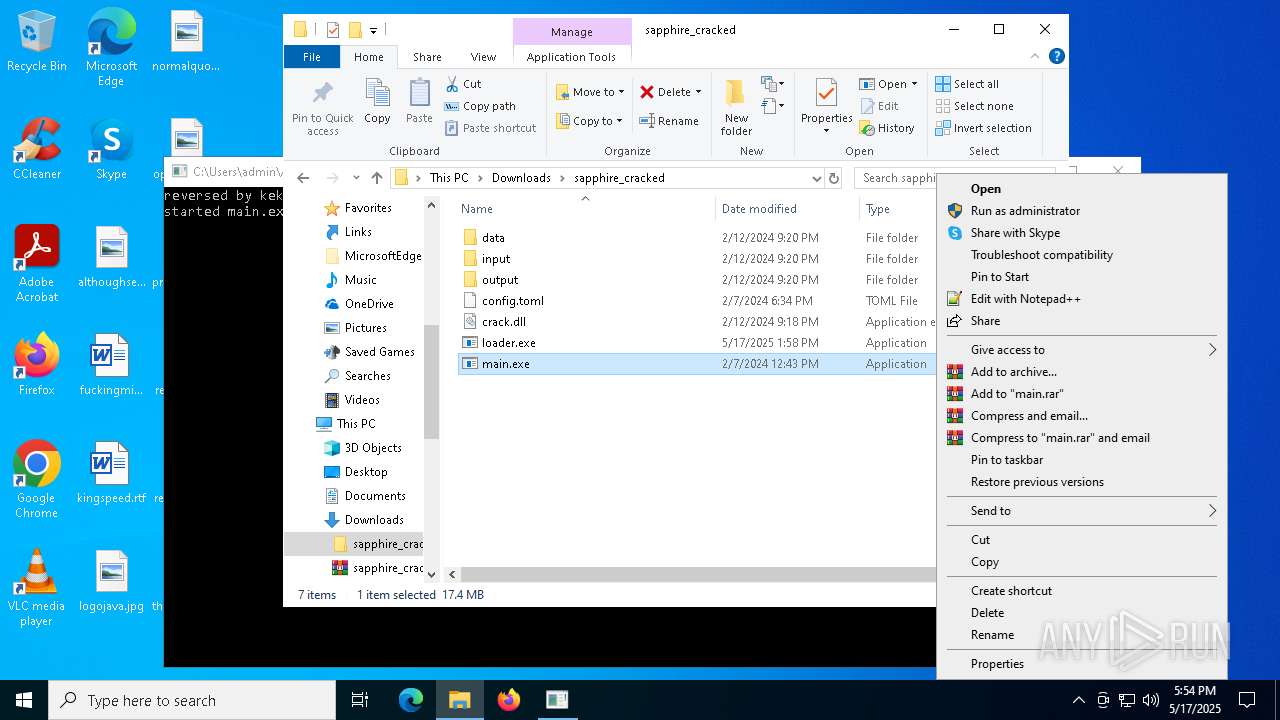
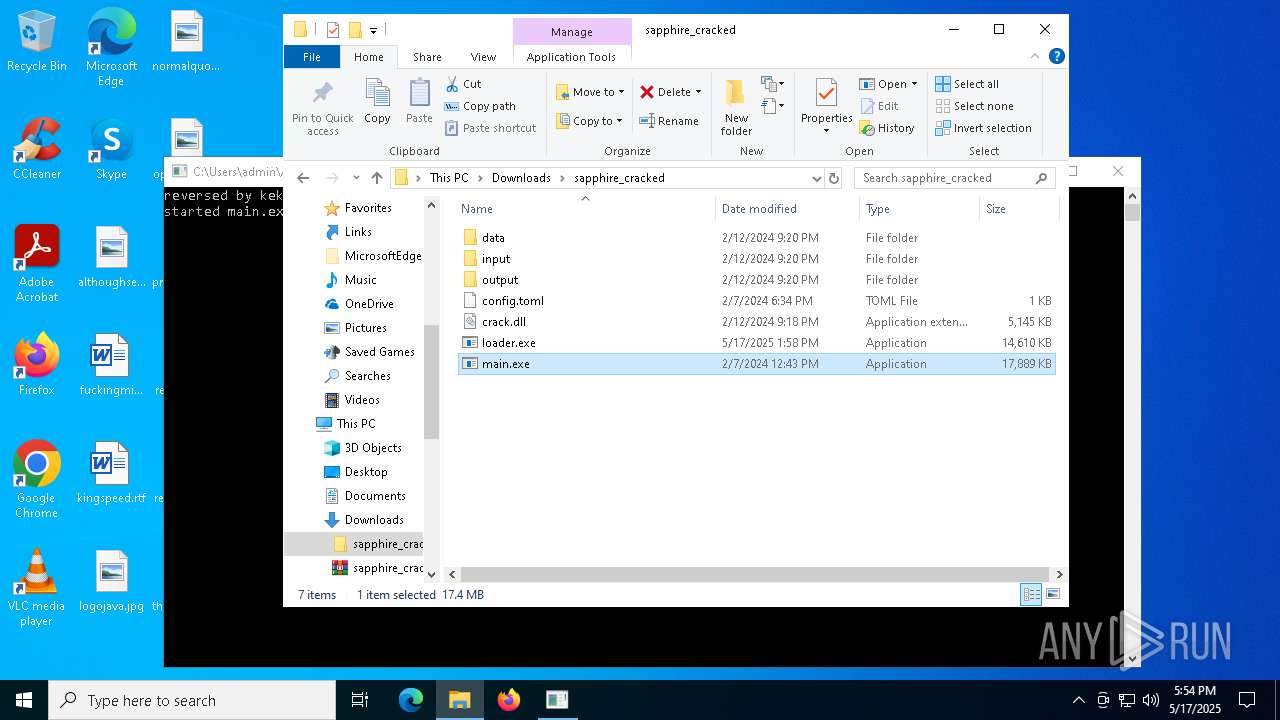
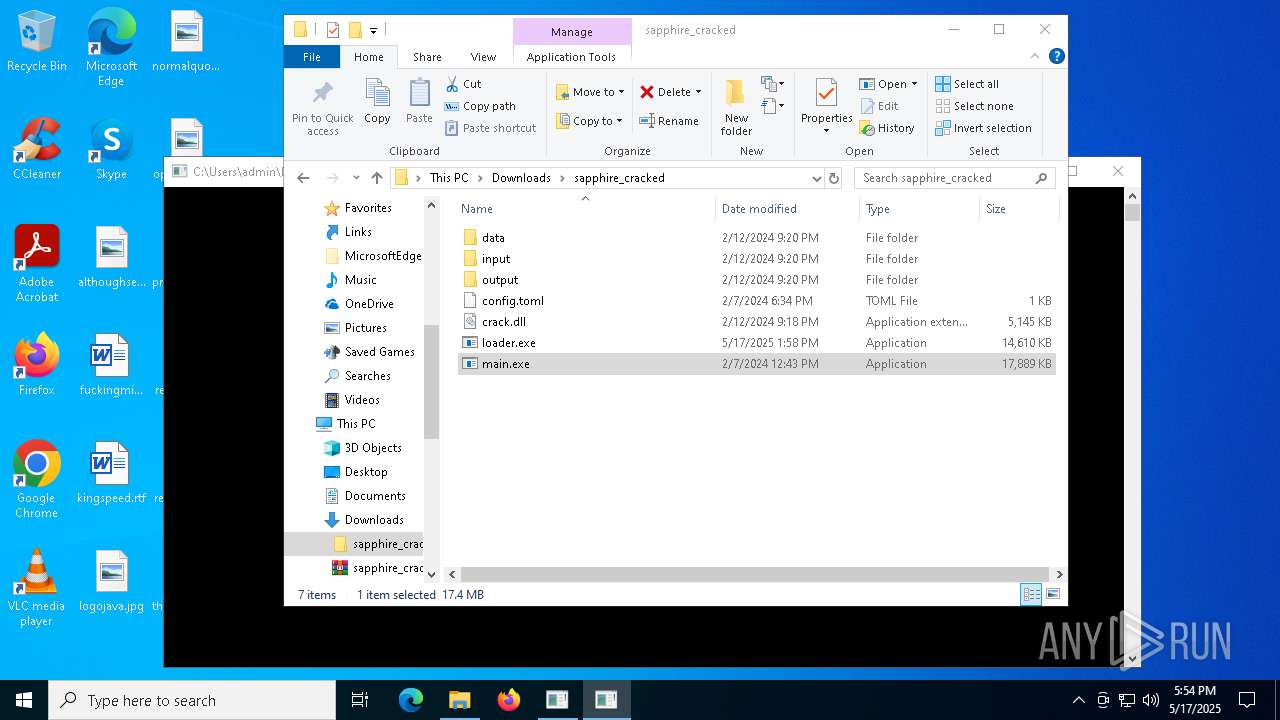
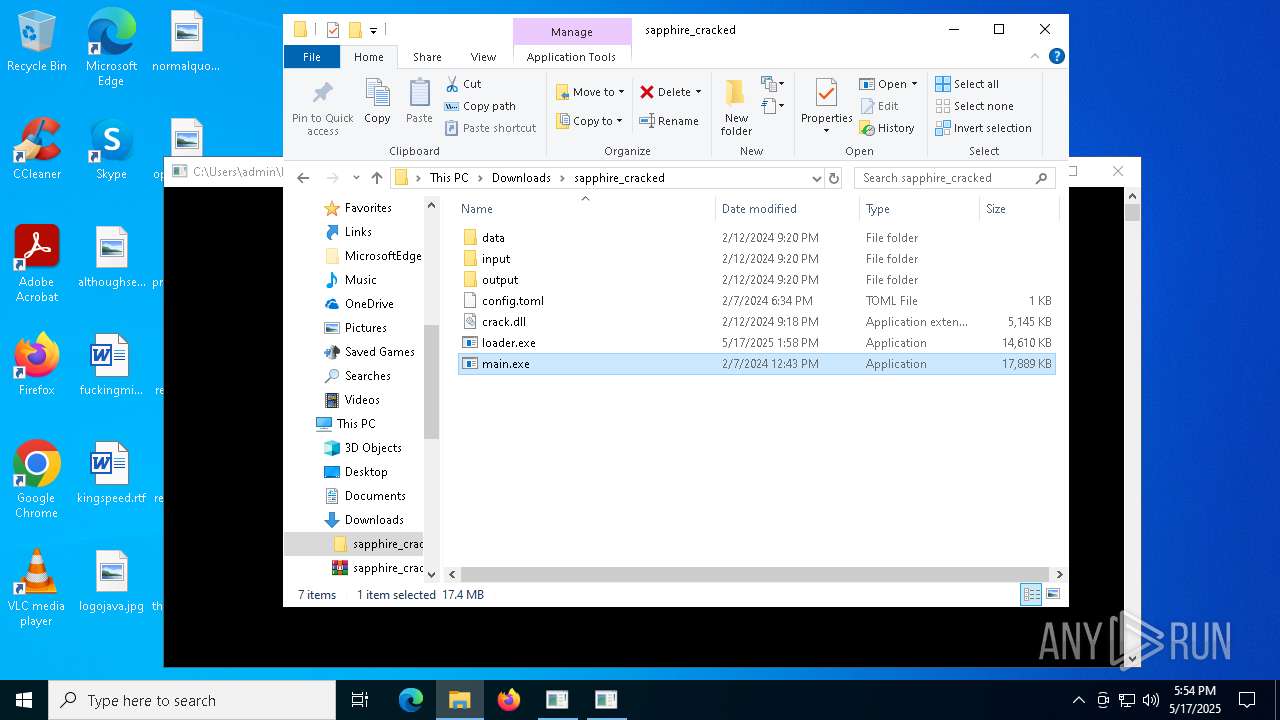
Manual execution by a user
- WinRAR.exe (PID: 6272)
- main.exe (PID: 7420)
- loader.exe (PID: 7352)
- loader.exe (PID: 9128)
- main.exe (PID: 8360)
- loader.exe (PID: 6964)
- main.exe (PID: 4000)
- firefox.exe (PID: 4696)
The sample compiled with english language support
- main.exe (PID: 7420)
- loader.exe (PID: 7788)
- Built.exe (PID: 7464)
- Built.exe (PID: 7556)
- main.exe (PID: 8360)
- loader.exe (PID: 4932)
- Built.exe (PID: 7760)
- dwm.exe (PID: 7600)
- Built.exe (PID: 7436)
- main.exe (PID: 4000)
Checks the directory tree
- tree.com (PID: 7772)
- tree.com (PID: 8496)
- tree.com (PID: 9116)
- tree.com (PID: 8660)
- tree.com (PID: 8860)
- tree.com (PID: 8252)
- tree.com (PID: 8812)
- tree.com (PID: 904)
- tree.com (PID: 6112)
- tree.com (PID: 1328)
- tree.com (PID: 6980)
- tree.com (PID: 8688)
The Powershell gets current clipboard
- powershell.exe (PID: 7812)
- powershell.exe (PID: 7880)
Themida protector has been detected
- loader.exe (PID: 7788)
PyInstaller has been detected (YARA)
- Built.exe (PID: 7464)
Found Base64 encoded reflection usage via PowerShell (YARA)
- Built.exe (PID: 7556)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 8832)
- getmac.exe (PID: 8248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(7556) Built.exe
Telegram-Tokens (1)7988457437:AAEb_TIWN7NuYIwbRK-TZQ6YU6jhqnYbxRg
Telegram-Info-Links
7988457437:AAEb_TIWN7NuYIwbRK-TZQ6YU6jhqnYbxRg
Get info about bothttps://api.telegram.org/bot7988457437:AAEb_TIWN7NuYIwbRK-TZQ6YU6jhqnYbxRg/getMe
Get incoming updateshttps://api.telegram.org/bot7988457437:AAEb_TIWN7NuYIwbRK-TZQ6YU6jhqnYbxRg/getUpdates
Get webhookhttps://api.telegram.org/bot7988457437:AAEb_TIWN7NuYIwbRK-TZQ6YU6jhqnYbxRg/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7988457437:AAEb_TIWN7NuYIwbRK-TZQ6YU6jhqnYbxRg/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7988457437:AAEb_TIWN7NuYIwbRK-TZQ6YU6jhqnYbxRg/deleteWebhook?drop_pending_updates=true
Total processes
473
Monitored processes
333
Malicious processes
21
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | "C:\Users\admin\AppData\Local\Temp\loader.exe" | C:\Users\admin\AppData\Local\Temp\onefile_4932_133919780546420474\loader.exe | — | loader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 616 | C:\WINDOWS\system32\cmd.exe /c "tasklist /FO LIST" | C:\Windows\System32\cmd.exe | — | Built.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | wmic csproduct get uuid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | C:\WINDOWS\system32\cmd.exe /c "tree /A /F" | C:\Windows\System32\cmd.exe | — | Built.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | C:\WINDOWS\system32\cmd.exe /c "powershell -Command Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Temp\Built.exe'" | C:\Windows\System32\cmd.exe | — | Built.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 896 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | tree /A /F | C:\Windows\System32\tree.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Tree Walk Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
150 612
Read events
150 557
Write events
55
Delete events
0
Modification events
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 53C37ADAEE932F00 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 518B84DAEE932F00 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {70EB4543-4955-4589-965A-13048A497F76} | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6825DC06-D91C-49B0-B533-7AE652A41EA5} | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A97766A5-9A25-4395-A33B-33EB37E3091B} | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7CD5147B-E92A-4C3E-949A-68B2A3F5218A} | |||
Executable files
247
Suspicious files
359
Text files
164
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b3c1.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b3e1.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b400.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b41f.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b42f.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
115
DNS requests
159
Threats
35
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 304 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7392 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7556 | Built.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
7392 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7556 | Built.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=225545 | unknown | — | — | whitelisted |
7436 | Built.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=225545 | unknown | — | — | whitelisted |
6964 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6964 | firefox.exe | POST | 200 | 184.24.77.53:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4164 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7312 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6032 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7312 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
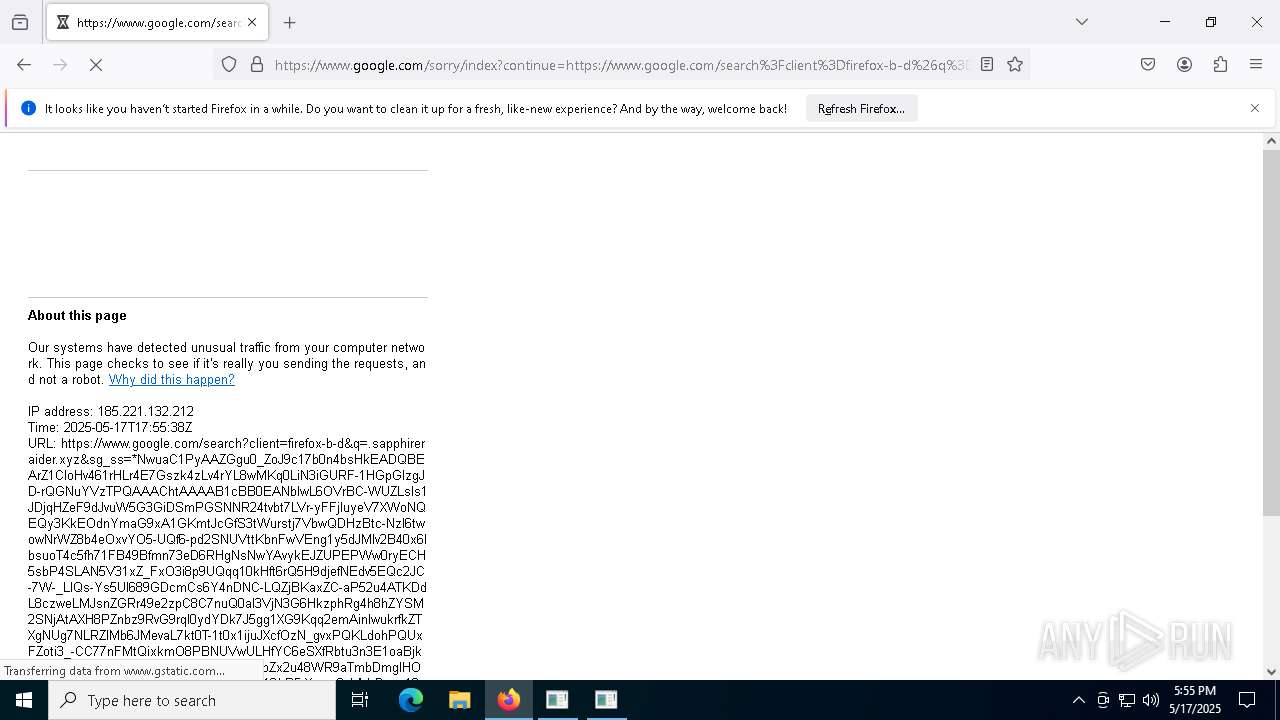
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
gofile.io |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7312 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7312 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7312 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7312 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7312 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7312 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7312 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7312 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7312 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7312 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |