| File name: | c23e76387cb8886166ed1a5a9f70ade6648b5527.exe |
| Full analysis: | https://app.any.run/tasks/3926944a-217b-42fb-9787-f0793c8c8684 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | November 04, 2020, 11:14:44 |
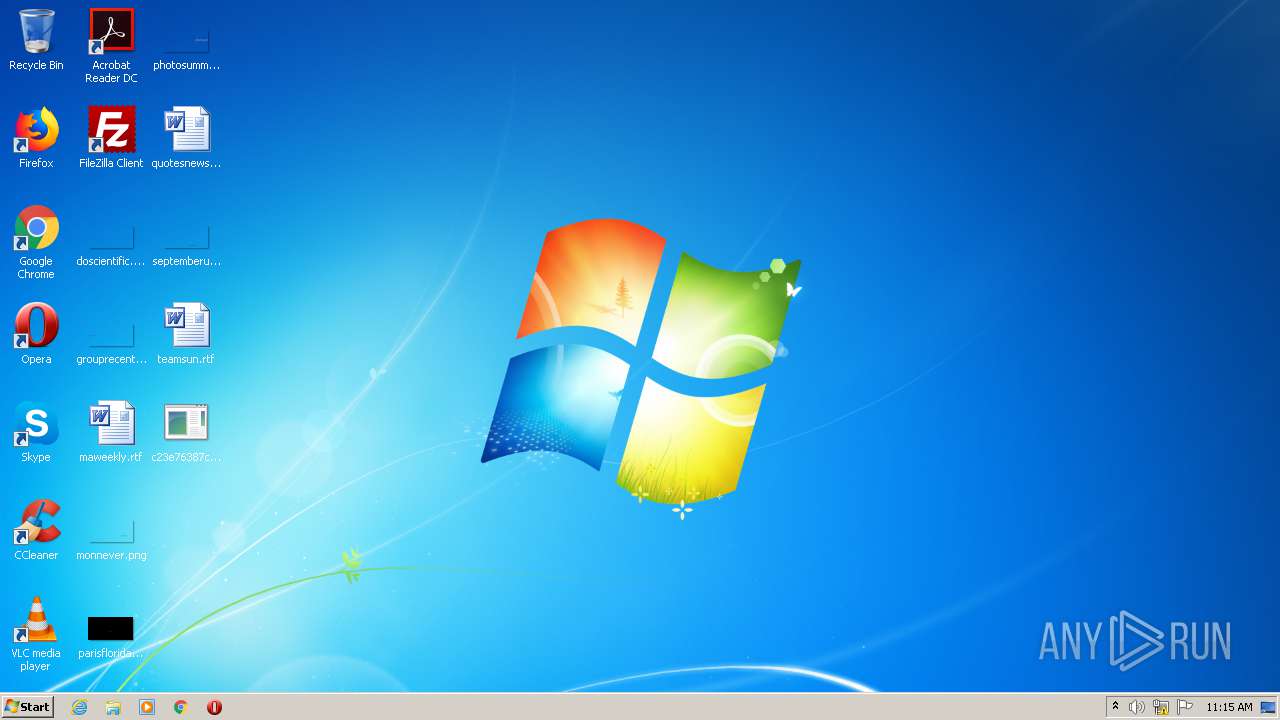
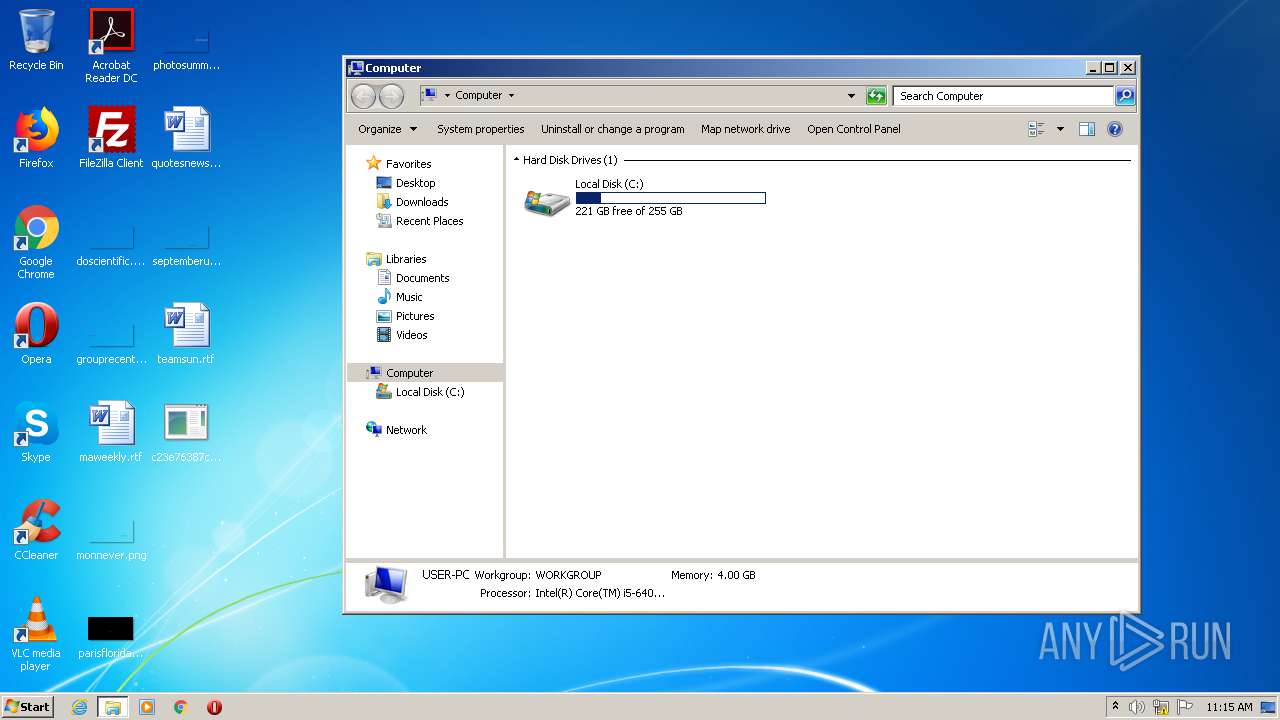
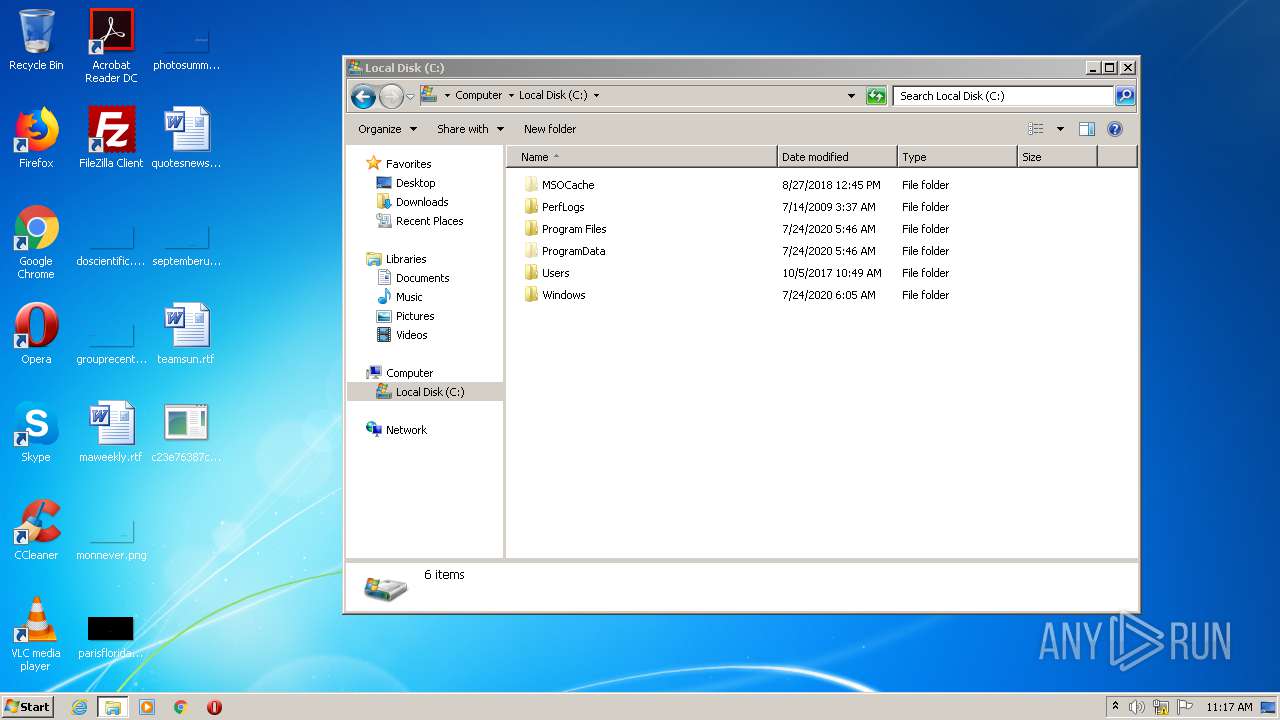
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | B5667C0D2195F03843A850C67F08F47B |
| SHA1: | C23E76387CB8886166ED1A5A9F70ADE6648B5527 |
| SHA256: | C0F5830BA5B9D5488F613F696AE00591321801FE71CA1BBFE6CB2A270EF96637 |
| SSDEEP: | 24576:8Wysf//jWGtt5Za87BvEI4k67kVpeyV6iJU:Mw6mZa8FMxrIVjwiJU |
MALICIOUS
FORMBOOK was detected
- explorer.exe (PID: 352)
Connects to CnC server
- explorer.exe (PID: 352)
SUSPICIOUS
Starts CMD.EXE for commands execution
- wuauclt.exe (PID: 1084)
INFO
Manual execution by user
- wuauclt.exe (PID: 1084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2046:08:25 06:27:55+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 873472 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd7332 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | GamePacman |
| FileVersion: | 1.0.0.0 |
| InternalName: | 物B.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | 物B.exe |
| ProductName: | GamePacman |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jul-1910 21:59:39 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | GamePacman |
| FileVersion: | 1.0.0.0 |
| InternalName: | 物B.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFilename: | 物B.exe |
| ProductName: | GamePacman |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 19-Jul-1910 21:59:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000D5348 | 0x000D5400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.66405 |
.rsrc | 0x000D8000 | 0x0000059C | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.04749 |
.reloc | 0x000DA000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
40
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1084 | "C:\Windows\System32\wuauclt.exe" | C:\Windows\System32\wuauclt.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Exit code: 0 Version: 7.5.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2512 | /c del "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\System32\cmd.exe | — | wuauclt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2620 | "C:\Users\admin\Desktop\c23e76387cb8886166ed1a5a9f70ade6648b5527.exe" | C:\Users\admin\Desktop\c23e76387cb8886166ed1a5a9f70ade6648b5527.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: GamePacman Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3884 | "{path}" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | — | c23e76387cb8886166ed1a5a9f70ade6648b5527.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
Total events
1 095
Read events
1 045
Write events
50
Delete events
0
Modification events
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ApplicationDestinations |
| Operation: | write | Name: | MaxEntries |
Value: 15 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000020000000B000000070000000A000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\BdeUnlockWizard.exe,-100 |
Value: &Unlock Drive... | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\27\Shell\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Rev |
Value: 0 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\27\Shell\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | FFlags |
Value: 1092616193 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\27\Shell\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Vid |
Value: {65F125E5-7BE1-4810-BA9D-D271C8432CE3} | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\27\Shell\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Mode |
Value: 6 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
12
DNS requests
13
Threats
36
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
352 | explorer.exe | GET | 404 | 34.102.136.180:80 | http://www.legend-producer.com/nko/?N2f=OpEUvkZGtSCmLLG+8K9o/QUFjmYuShmLDlMwEFV53ErDUkwOqND4gHQkIBvLq5lmcGpLnQ==&Up8h=cz7tThZp90h4oD | US | xml | 341 b | whitelisted |
352 | explorer.exe | GET | 404 | 151.101.0.119:80 | http://www.matheusoliveiradesign.com/nko/?N2f=AvV2DxiZYCKVgGHDcGYcx11fpeDFzVc/JTDr/siBplHG1AVOZarp3YqLBTmSHGSVYMuCag==&Up8h=cz7tThZp90h4oD | US | xml | 341 b | malicious |
352 | explorer.exe | GET | 404 | 51.38.53.69:80 | http://www.premium-vitality.com/nko/?N2f=+ATwUOajsRI8/ATy7UZF+pf4lKza1K/ikJNlCazsqsPRaGk4oVHwvOYmMizsV8QX10WSrg==&Up8h=cz7tThZp90h4oD | GB | xml | 341 b | malicious |
352 | explorer.exe | GET | 404 | 23.227.38.64:80 | http://www.cleanoralbr.com/nko/?N2f=0jcaAJW8qxSn7ZNheFHV9ordmMyMu3tmSqVAGJ3Pju14AHxO59JdvYGn9nQyzucpsqajsA==&Up8h=cz7tThZp90h4oD | CA | xml | 341 b | malicious |
352 | explorer.exe | GET | 404 | 154.220.195.87:80 | http://www.jiazhoulighting.net/nko/?N2f=yXHZfFovXBT3zffvFBmPzk9cKUGdAj0sxYr7hwnwn6HiTIWZsC0UR+Gr1nWvOCYJnaQxyg==&Up8h=cz7tThZp90h4oD | US | xml | 341 b | malicious |
352 | explorer.exe | GET | 404 | 104.19.253.28:80 | http://www.corinthia.media/nko/?N2f=4Fy2aRaCpFcv+kD53R+EV69RJ3AcoMbeG9eIYXUeBiGoKcU06BzT4ifPwtk5kJ6ZvO+Mqw==&Up8h=cz7tThZp90h4oD | US | xml | 341 b | malicious |
352 | explorer.exe | GET | 404 | 198.54.117.215:80 | http://www.comeongetreal.com/nko/?N2f=AYwVFN7lOkqKd8/MD3muAiH8Ur06JIpN6t+l/084v/oNwKnyVH/YlGT28flUQGuiUpeftg==&Up8h=cz7tThZp90h4oD | US | xml | 341 b | malicious |
352 | explorer.exe | GET | 404 | 34.102.136.180:80 | http://www.will-legend.com/nko/?N2f=HbtYDw6bf5Emtw9lskT4zx0f4HTCOw+/B32yNRe2NBDzddGm6A65g768E3m/Fi/LN8+5lw==&Up8h=cz7tThZp90h4oD | US | xml | 341 b | whitelisted |
352 | explorer.exe | GET | 404 | 156.67.213.64:80 | http://www.worldstream.online/nko/?N2f=6EqZr3Psyz9S0KVaNjD0mqnRGfXtauDOcAYLBMrkRcmUH4B9UQF5icpfglGMWsIGI8AcoQ==&Up8h=cz7tThZp90h4oD | SG | xml | 341 b | malicious |
352 | explorer.exe | GET | 404 | 108.62.244.153:80 | http://www.apartfriendlyneocondopyx.com/nko/?N2f=36ciWhkqfba5SZqB/I7KfOudwMynDCH3PEedLkSesWU87SyChBuxU5wtu0wGY+dZN5SyDg==&Up8h=cz7tThZp90h4oD | US | xml | 341 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
352 | explorer.exe | 23.227.38.64:80 | www.cleanoralbr.com | Shopify, Inc. | CA | malicious |
352 | explorer.exe | 104.19.253.28:80 | www.corinthia.media | Cloudflare Inc | US | malicious |
352 | explorer.exe | 88.99.167.187:80 | www.mari-house.com | Hetzner Online GmbH | DE | malicious |
352 | explorer.exe | 108.62.244.153:80 | www.apartfriendlyneocondopyx.com | Nobis Technology Group, LLC | US | malicious |
352 | explorer.exe | 151.101.0.119:80 | www.matheusoliveiradesign.com | Fastly | US | malicious |
— | — | 81.17.18.195:80 | www.jowdykanefuneralhome.net | Private Layer INC | CH | malicious |
352 | explorer.exe | 51.38.53.69:80 | www.premium-vitality.com | — | GB | malicious |
352 | explorer.exe | 34.102.136.180:80 | www.legend-producer.com | — | US | whitelisted |
352 | explorer.exe | 154.220.195.87:80 | www.jiazhoulighting.net | MULTACOM CORPORATION | US | malicious |
— | — | 198.54.117.215:80 | www.comeongetreal.com | Namecheap, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cleanoralbr.com |
| malicious |
www.corinthia.media |
| malicious |
www.mari-house.com |
| unknown |
www.apartfriendlyneocondopyx.com |
| malicious |
www.matheusoliveiradesign.com |
| malicious |
www.jowdykanefuneralhome.net |
| malicious |
www.premium-vitality.com |
| malicious |
www.legend-producer.com |
| whitelisted |
www.jiazhoulighting.net |
| malicious |
www.comeongetreal.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
352 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
352 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
352 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
352 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
352 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
12 ETPRO signatures available at the full report