| File name: | Wire_Slip_pdf.exe.bz2 |
| Full analysis: | https://app.any.run/tasks/2e49ea5f-1e86-4de6-9c5c-f9e5e2d10c08 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | May 27, 2020, 17:50:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
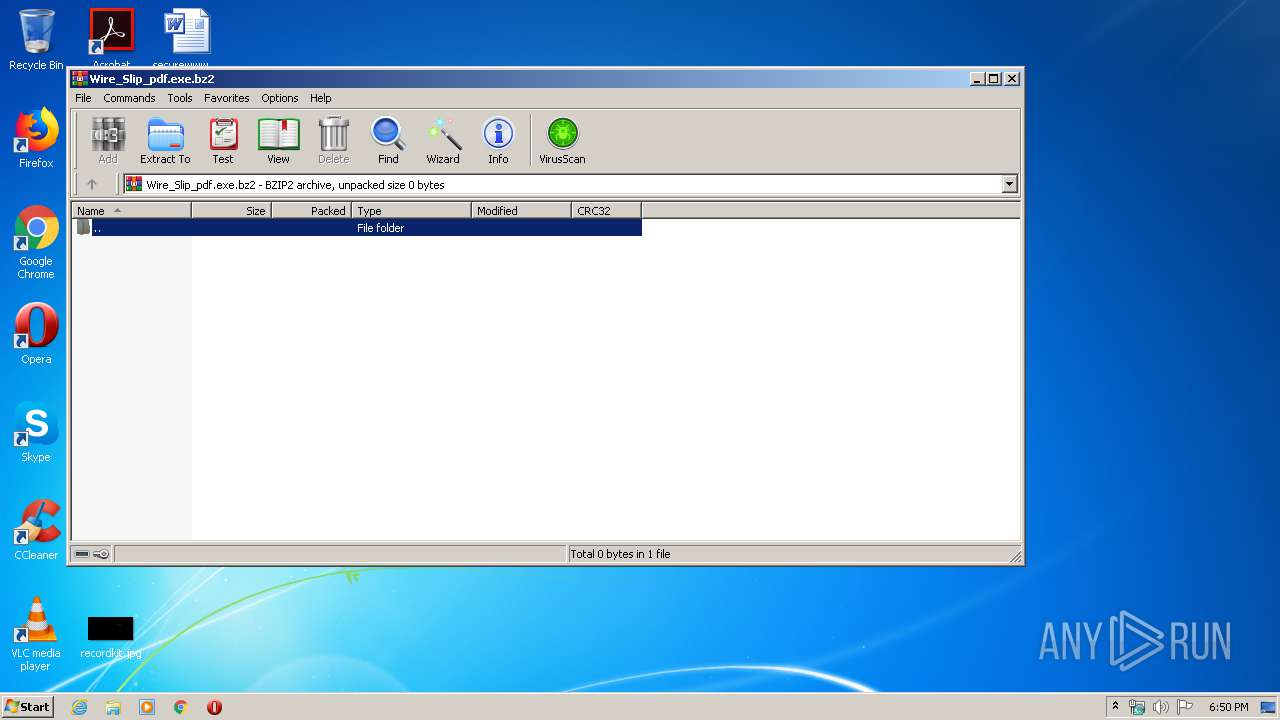
| MIME: | application/x-bzip2 |
| File info: | bzip2 compressed data, block size = 900k |
| MD5: | 738B83ABDCDB6462DBCF3B6B17E743DE |
| SHA1: | E203B4F05EBFB4B1A97573353D48464D7626BE19 |
| SHA256: | C0D3574A4C99D94A21FDCE3FF06F1186EF8980372320FA45603FC10F2DD496A5 |
| SSDEEP: | 6144:TzkSADm20B8DLItJffd6bePfii59nWYvRfe8J:TzkSADFrDLCV6yPfZbWAfr |
MALICIOUS
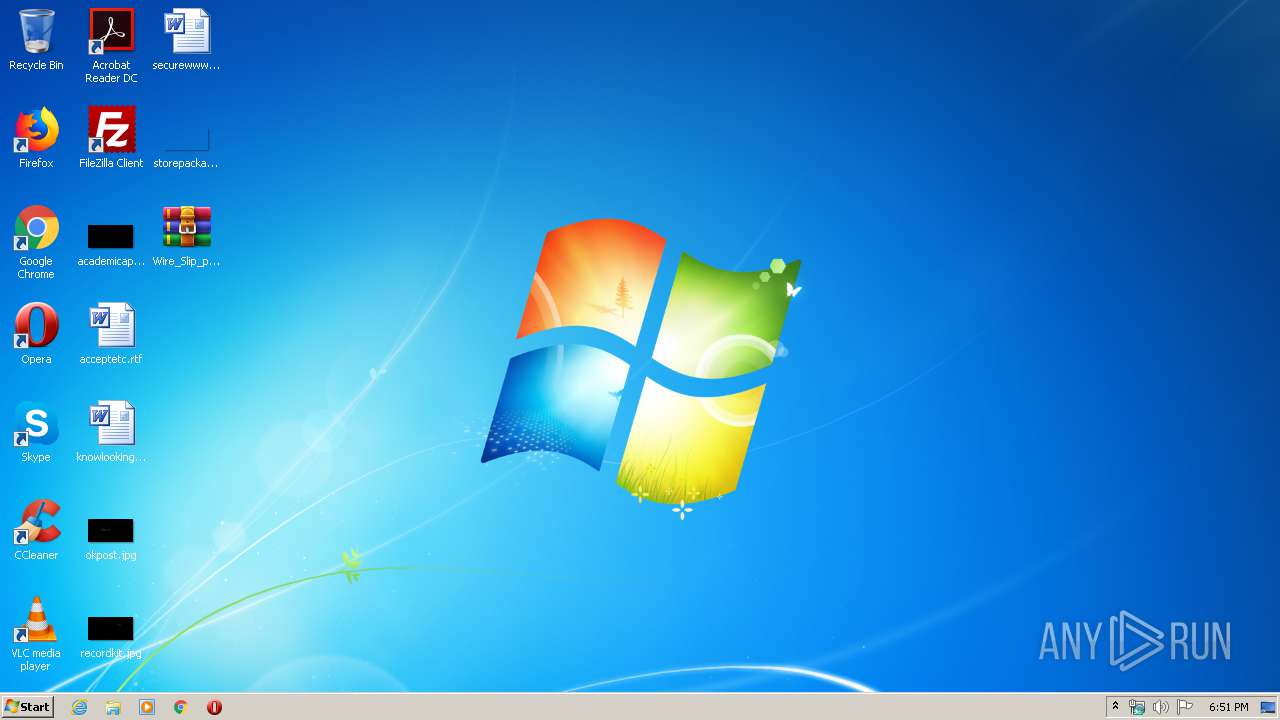
Application was dropped or rewritten from another process
- Wire_Slip_pdf.exe (PID: 3072)
- regsvchtg8in.exe (PID: 1668)
FORMBOOK was detected
- lsm.exe (PID: 2580)
- explorer.exe (PID: 312)
- Firefox.exe (PID: 1628)
Changes the autorun value in the registry
- lsm.exe (PID: 2580)
Actions looks like stealing of personal data
- lsm.exe (PID: 2580)
Connects to CnC server
- explorer.exe (PID: 312)
Stealing of credential data
- lsm.exe (PID: 2580)
SUSPICIOUS
Creates files in the user directory
- explorer.exe (PID: 312)
- lsm.exe (PID: 2580)
Starts CMD.EXE for commands execution
- lsm.exe (PID: 2580)
Loads DLL from Mozilla Firefox
- lsm.exe (PID: 2580)
Executable content was dropped or overwritten
- explorer.exe (PID: 312)
- DllHost.exe (PID: 2652)
Creates files in the program directory
- DllHost.exe (PID: 2652)
Executed via COM
- DllHost.exe (PID: 2652)
INFO
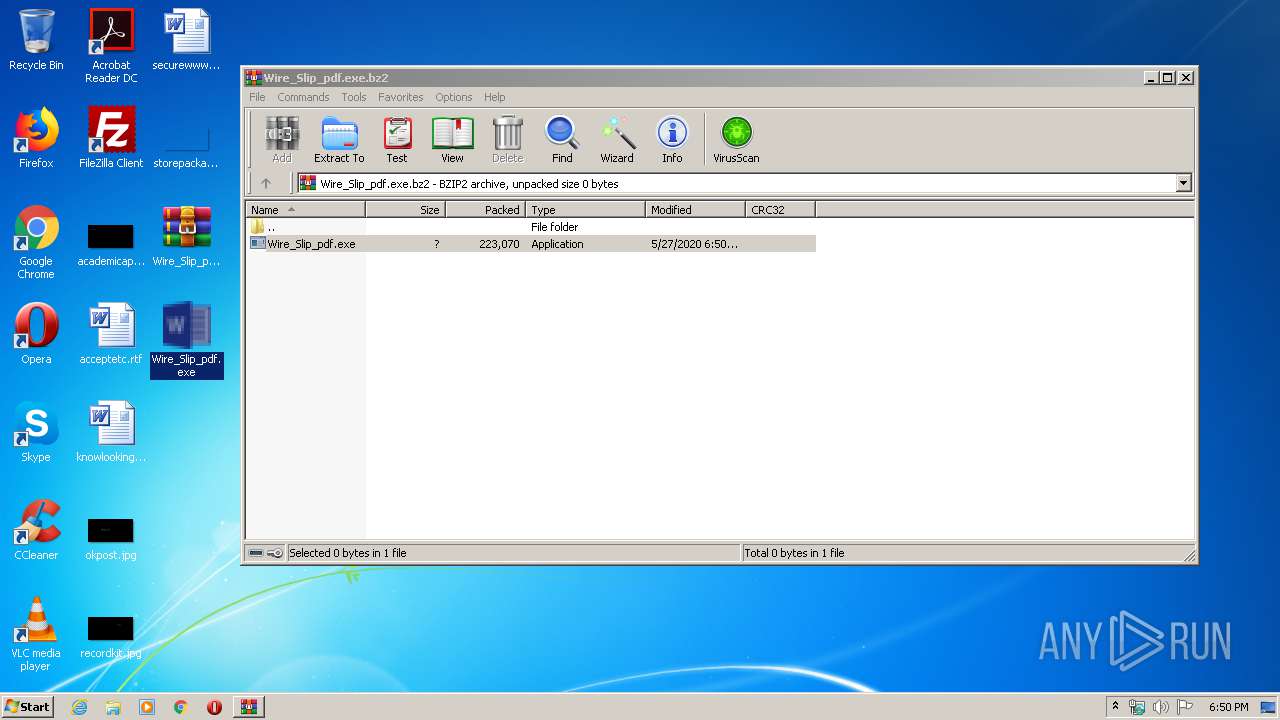
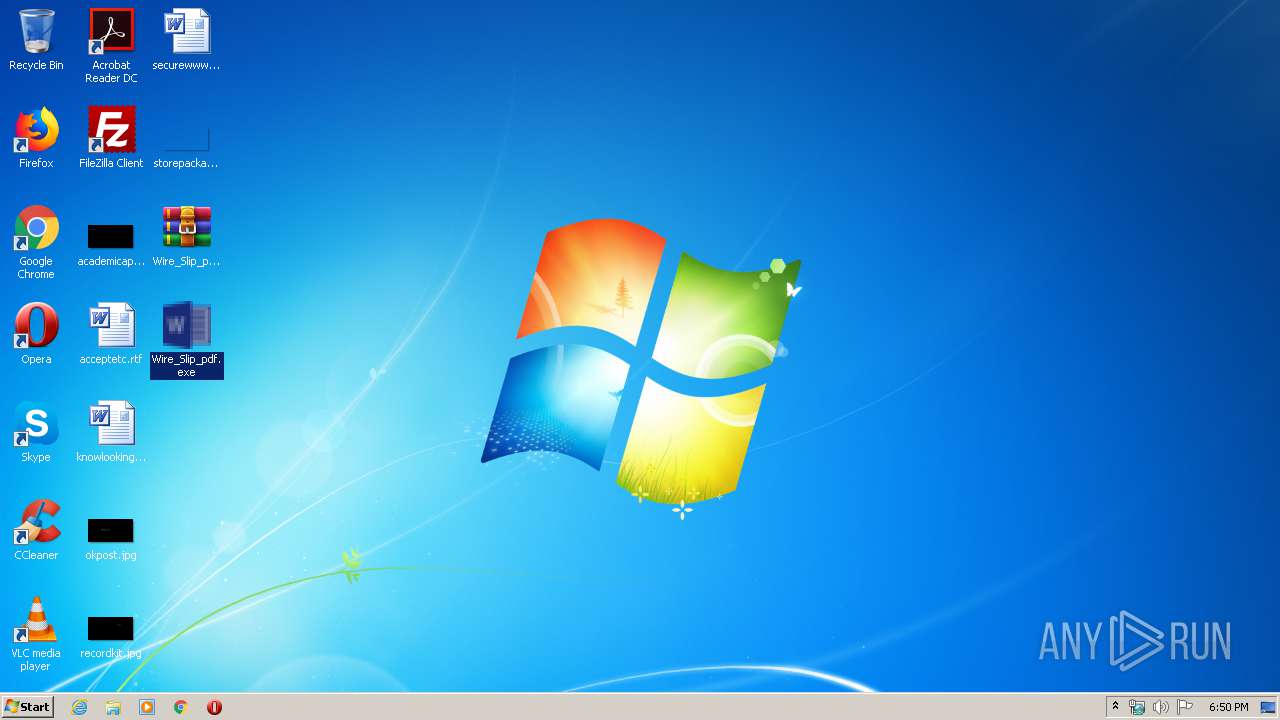
Manual execution by user
- lsm.exe (PID: 2580)
- Wire_Slip_pdf.exe (PID: 3072)
Reads the hosts file
- lsm.exe (PID: 2580)
Creates files in the user directory
- Firefox.exe (PID: 1628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .bz2/bzip2 | | | bzip2 compressed archive (100) |
|---|
Total processes
47
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1628 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | lsm.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Opr2pln\regsvchtg8in.exe" | C:\Program Files\Opr2pln\regsvchtg8in.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
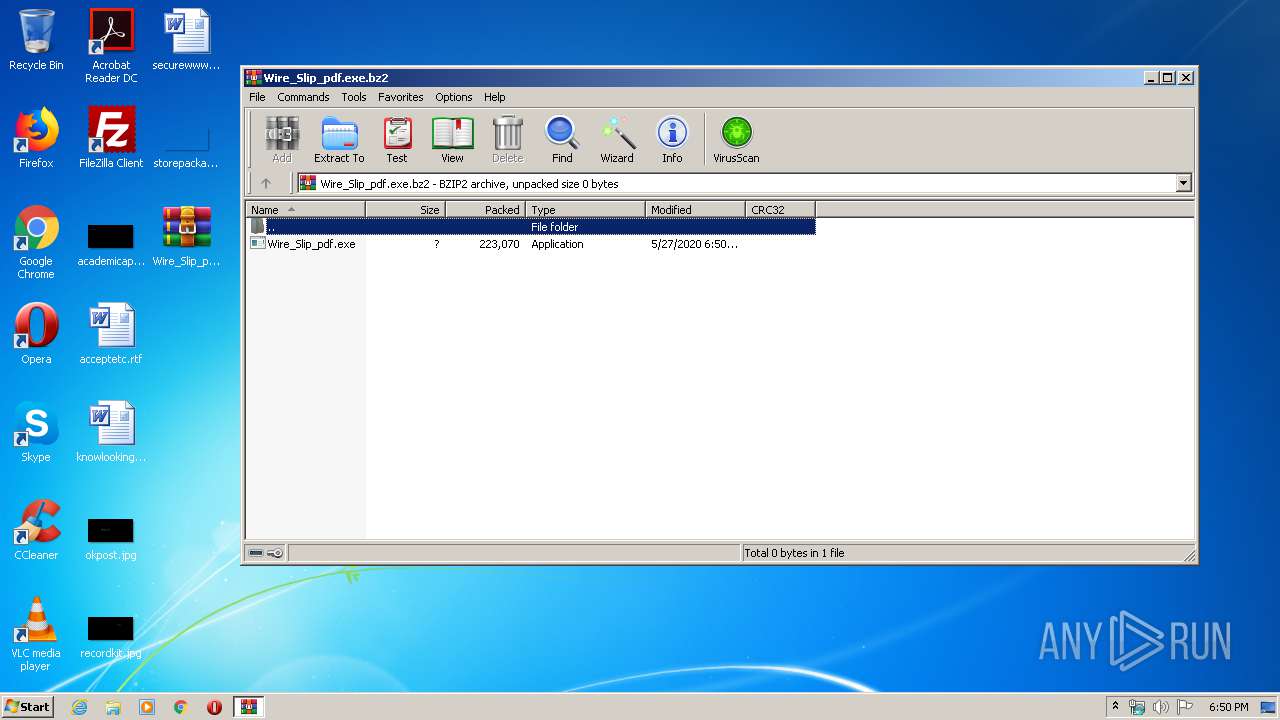
| 2412 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Wire_Slip_pdf.exe.bz2" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2580 | "C:\Windows\System32\lsm.exe" | C:\Windows\System32\lsm.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Local Session Manager Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2652 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2884 | /c del "C:\Users\admin\Desktop\Wire_Slip_pdf.exe" | C:\Windows\System32\cmd.exe | — | lsm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3072 | "C:\Users\admin\Desktop\Wire_Slip_pdf.exe" | C:\Users\admin\Desktop\Wire_Slip_pdf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 062
Read events
3 013
Write events
49
Delete events
0
Modification events
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Wire_Slip_pdf.exe.bz2 | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2412) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (312) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.bz2\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
Executable files
3
Suspicious files
73
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2412.17366\Wire_Slip_pdf.exe | — | |
MD5:— | SHA256:— | |||
| 312 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\290532160612e071.automaticDestinations-ms | automaticdestinations-ms | |
MD5:331C63F43B123BBFA883F38834A39C40 | SHA256:4CDCB2EAC34611745906FFA9D43C3CBDD7BFEFC7A10B8D2C4B08635C23C2635A | |||
| 2580 | lsm.exe | C:\Users\admin\AppData\Roaming\651AO9PC\651logim.jpeg | image | |
MD5:32221A14176E80FF7227A804509B72AA | SHA256:A1706ABEFC4A1B9F9C274A3077926CF3966C2ED4831481A4B19B9183A3B99C96 | |||
| 312 | explorer.exe | C:\Users\admin\AppData\Local\Temp\Opr2pln\regsvchtg8in.exe | executable | |
MD5:4E27900568769C906D602CAAB43A6045 | SHA256:A4D34995DBE67A24B6BCC4DD52845DE151673EA8CB24640240906518707E99C6 | |||
| 1628 | Firefox.exe | C:\Users\admin\AppData\Roaming\651AO9PC\651logrf.ini | binary | |
MD5:53028481B5B5795F1501241CCC7ABFF6 | SHA256:75B5F3045E20C80F264568707E2D444DC7498DB119D9661AE51A91575960FC5A | |||
| 312 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:39BD070E1C9C7677EBDA03A00C2A0DE4 | SHA256:3232C28F27D1002DB447F02AA72B05EA2DF8BC05D21A9BADF1DD548F4C18643E | |||
| 312 | explorer.exe | C:\Users\admin\Desktop\Wire_Slip_pdf.exe | executable | |
MD5:4E27900568769C906D602CAAB43A6045 | SHA256:A4D34995DBE67A24B6BCC4DD52845DE151673EA8CB24640240906518707E99C6 | |||
| 2580 | lsm.exe | C:\Users\admin\AppData\Roaming\651AO9PC\651logrc.ini | binary | |
MD5:2855A82ECDD565B4D957EC2EE05AED26 | SHA256:88E38DA5B12DD96AFD9DC90C79929EC31D8604B1AFDEBDD5A02B19249C08C939 | |||
| 312 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\Wire_Slip_pdf.exe.bz2.lnk | lnk | |
MD5:DEE187D7F1DAB405DD2BF40D92412FA0 | SHA256:A7F4B45257084E9FCDA5BCDD565EF8F401BF2C3B5296129A03F996DC6109DE1B | |||
| 2580 | lsm.exe | C:\Users\admin\AppData\Roaming\651AO9PC\651logri.ini | binary | |
MD5:D63A82E5D81E02E399090AF26DB0B9CB | SHA256:EAECE2EBA6310253249603033C744DD5914089B0BB26BDE6685EC9813611BAAE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
17
DNS requests
15
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
312 | explorer.exe | POST | — | 184.168.221.63:80 | http://www.pixelcinematography.com/ssr/ | US | — | — | malicious |
312 | explorer.exe | POST | — | 63.250.47.83:80 | http://www.glamotd.com/ssr/ | US | — | — | malicious |
312 | explorer.exe | POST | — | 63.250.47.83:80 | http://www.glamotd.com/ssr/ | US | — | — | malicious |
312 | explorer.exe | GET | 404 | 35.214.191.38:80 | http://www.segurosemporda.cat/ssr/?uzpD=1qy98zdMVXYzQ11pe3iG91SDK29Z9OCsRQbZiTKKG1PP2XH0gGHpFR5g07KrTm0qkxrEXw==&4h=W6QlrtLh5B2LXLvP | US | html | 459 b | malicious |
312 | explorer.exe | POST | — | 35.214.191.38:80 | http://www.segurosemporda.cat/ssr/ | US | — | — | malicious |
312 | explorer.exe | POST | — | 35.214.191.38:80 | http://www.segurosemporda.cat/ssr/ | US | — | — | malicious |
312 | explorer.exe | POST | — | 35.214.191.38:80 | http://www.segurosemporda.cat/ssr/ | US | — | — | malicious |
312 | explorer.exe | GET | 301 | 35.242.251.130:80 | http://www.mcarselloteachingportfolio.com/ssr/?uzpD=M9DeyV41VEVME5TZQcIYacosWApjjzBtEVOj9nq26s2n2p1N1EKwJ81DAsjdy/mDduwe3A==&4h=W6QlrtLh5B2LXLvP&sql=1 | US | — | — | malicious |
312 | explorer.exe | POST | — | 35.242.251.130:80 | http://www.mcarselloteachingportfolio.com/ssr/ | US | — | — | malicious |
312 | explorer.exe | POST | — | 35.242.251.130:80 | http://www.mcarselloteachingportfolio.com/ssr/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
312 | explorer.exe | 35.242.251.130:80 | www.mcarselloteachingportfolio.com | — | US | malicious |
312 | explorer.exe | 23.20.239.12:80 | www.yohogame.com | Amazon.com, Inc. | US | shared |
312 | explorer.exe | 184.168.221.63:80 | www.pixelcinematography.com | GoDaddy.com, LLC | US | malicious |
312 | explorer.exe | 63.250.47.83:80 | www.glamotd.com | Frontline Data Services, Inc | US | malicious |
312 | explorer.exe | 35.214.191.38:80 | www.segurosemporda.cat | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cnnenterprisesinc.com |
| unknown |
www.alkgh.link |
| unknown |
www.h93gybwhr5.biz |
| unknown |
www.yohogame.com |
| shared |
www.zhongkewy.com |
| unknown |
www.mcarselloteachingportfolio.com |
| malicious |
www.benefitfocusonline.com |
| unknown |
www.pixelcinematography.com |
| malicious |
www.seronreserve.com |
| unknown |
www.glamotd.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
312 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
312 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
312 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
312 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
312 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
312 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
312 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
312 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
312 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
13 ETPRO signatures available at the full report