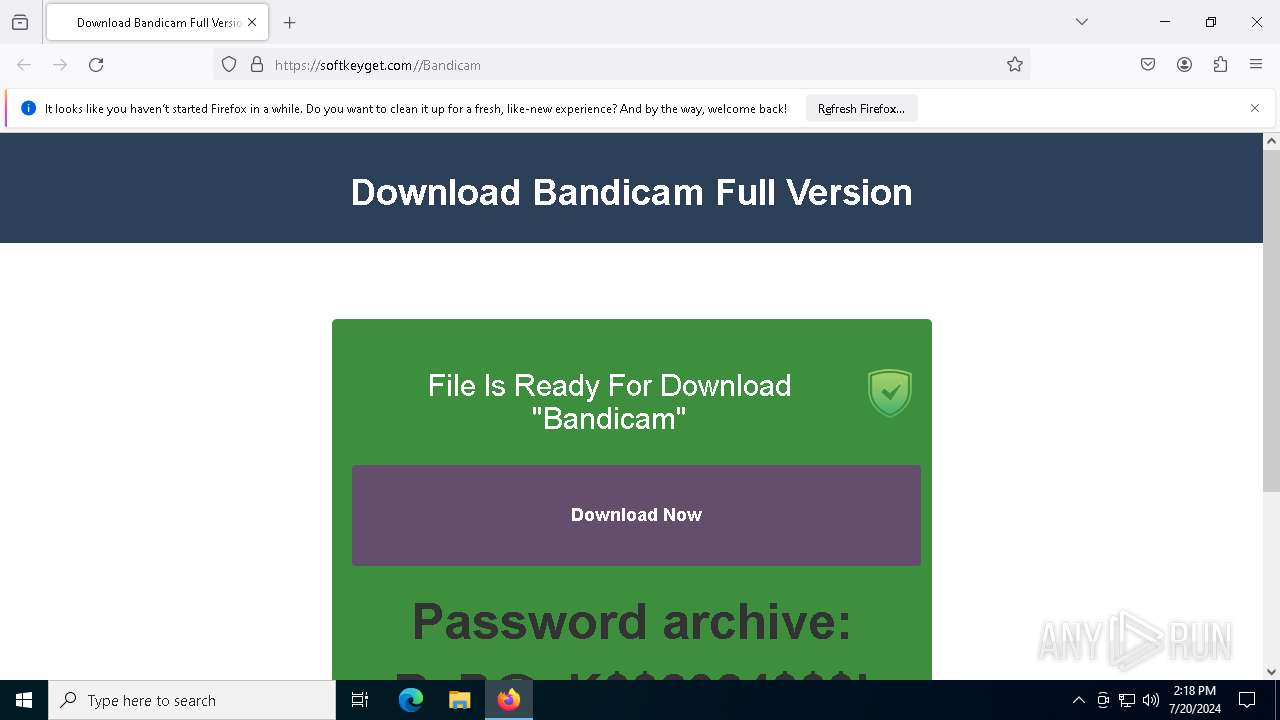
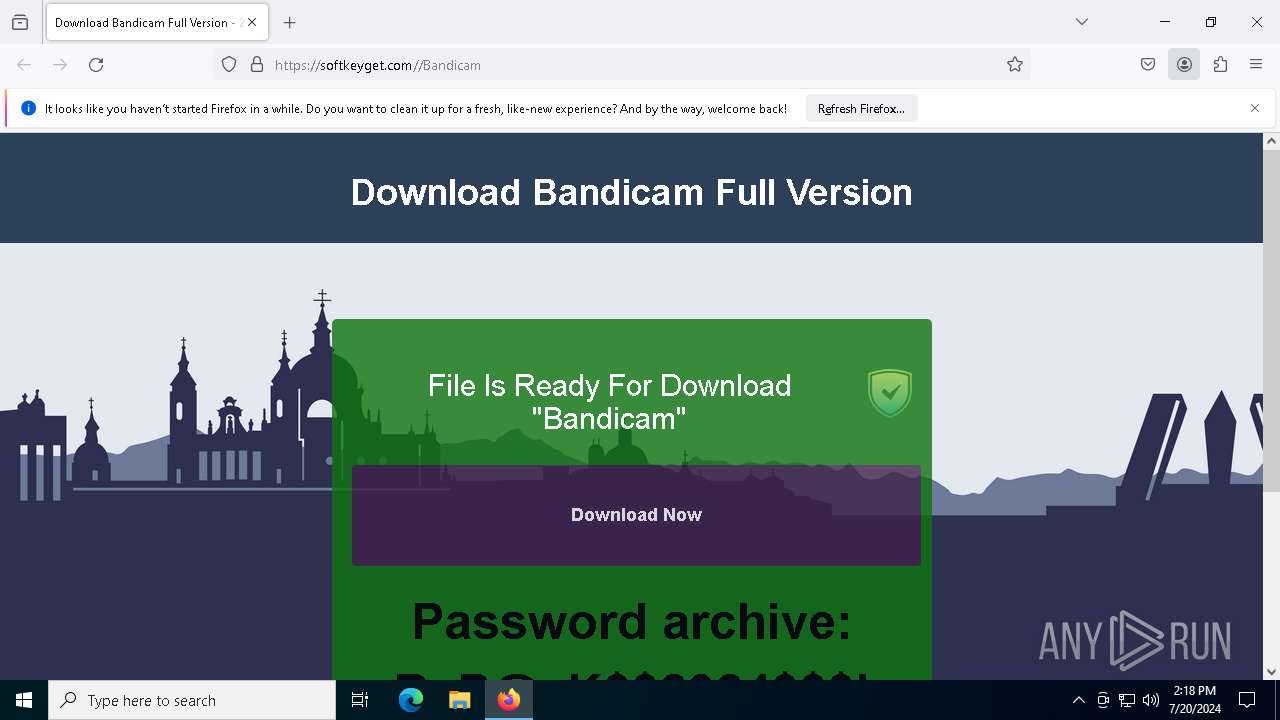
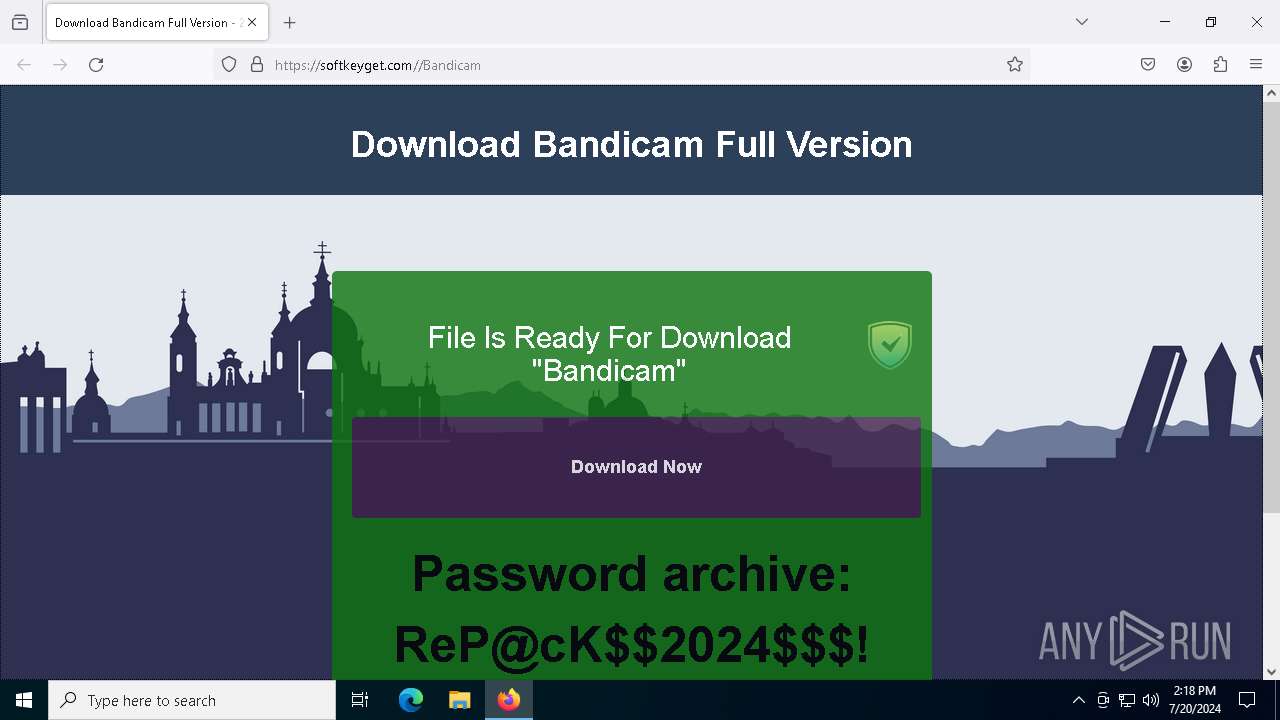
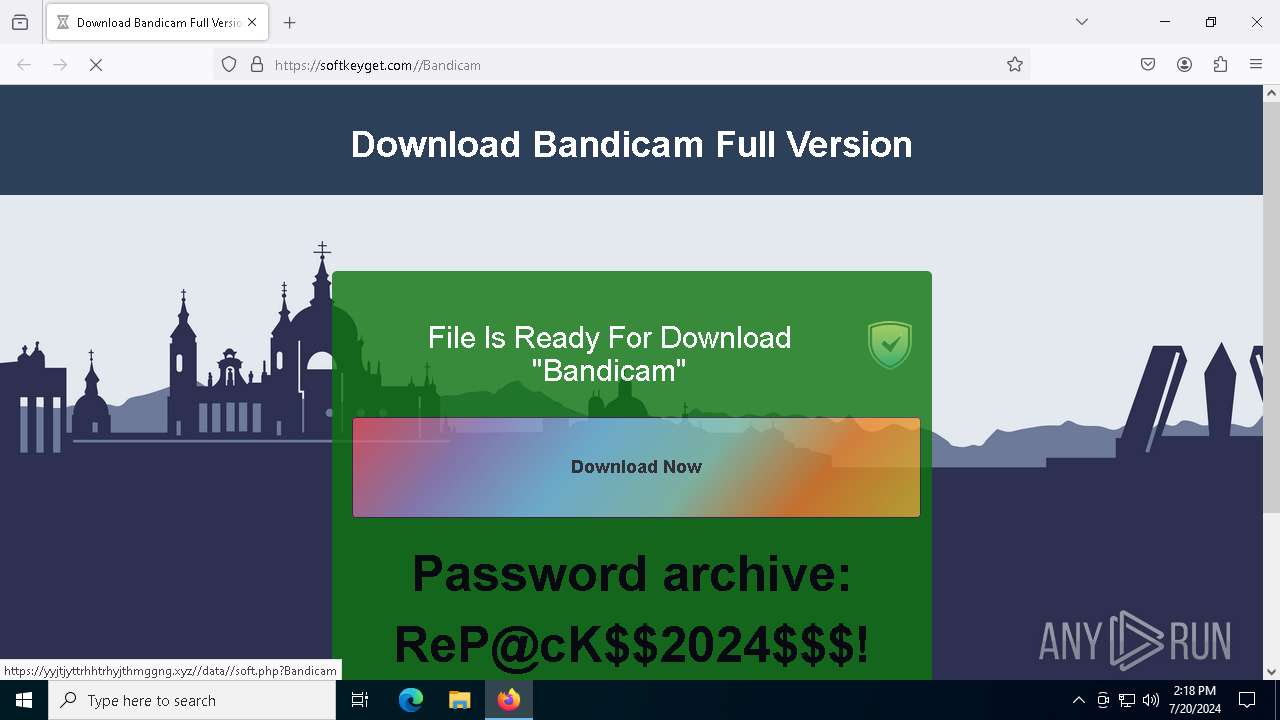
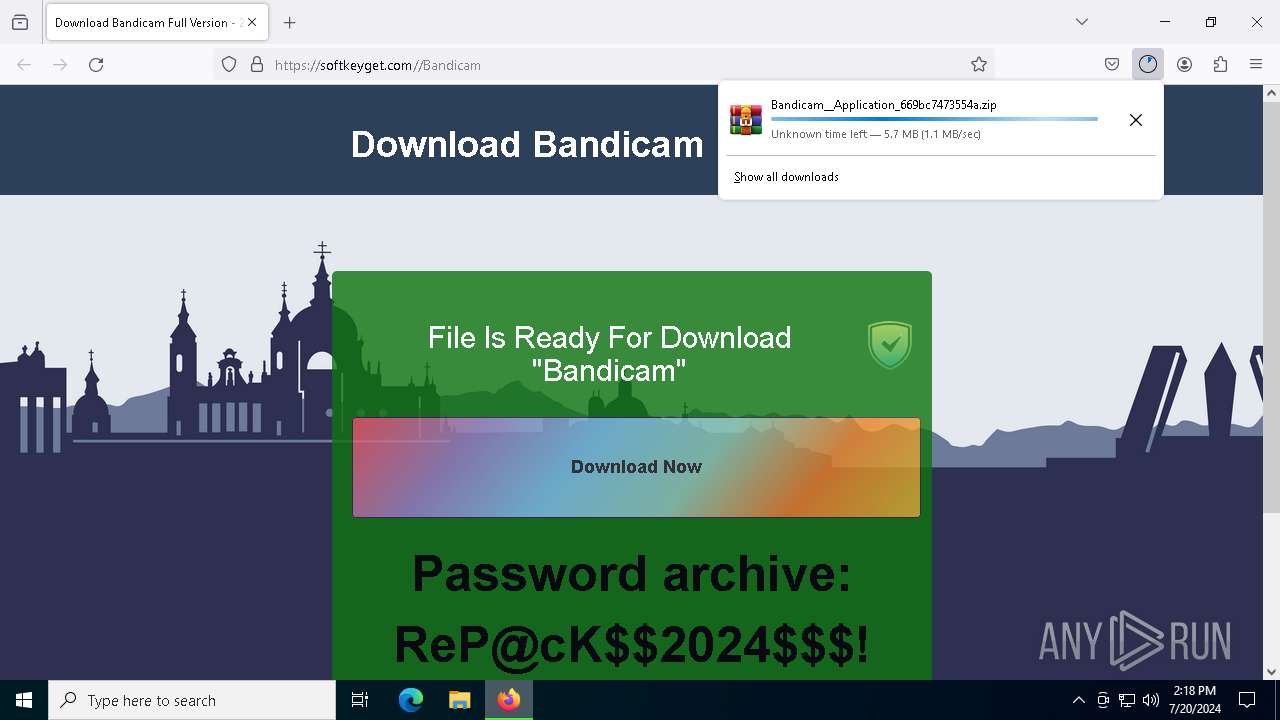
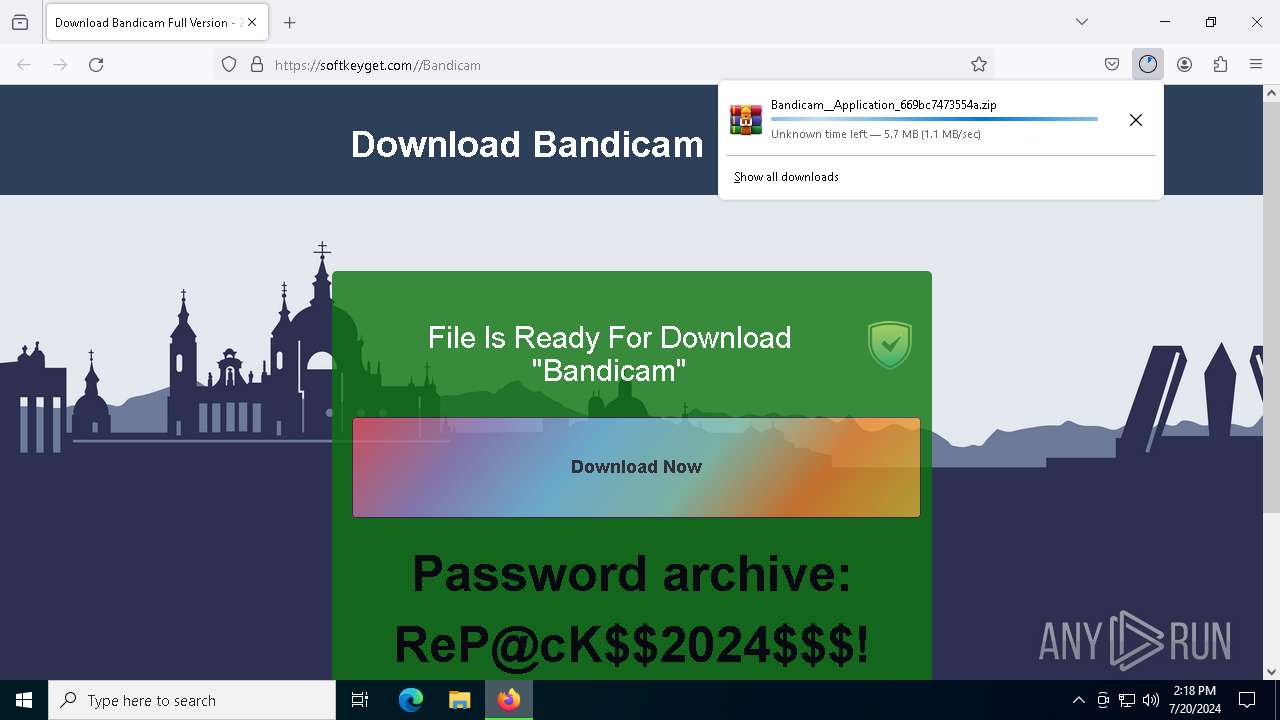
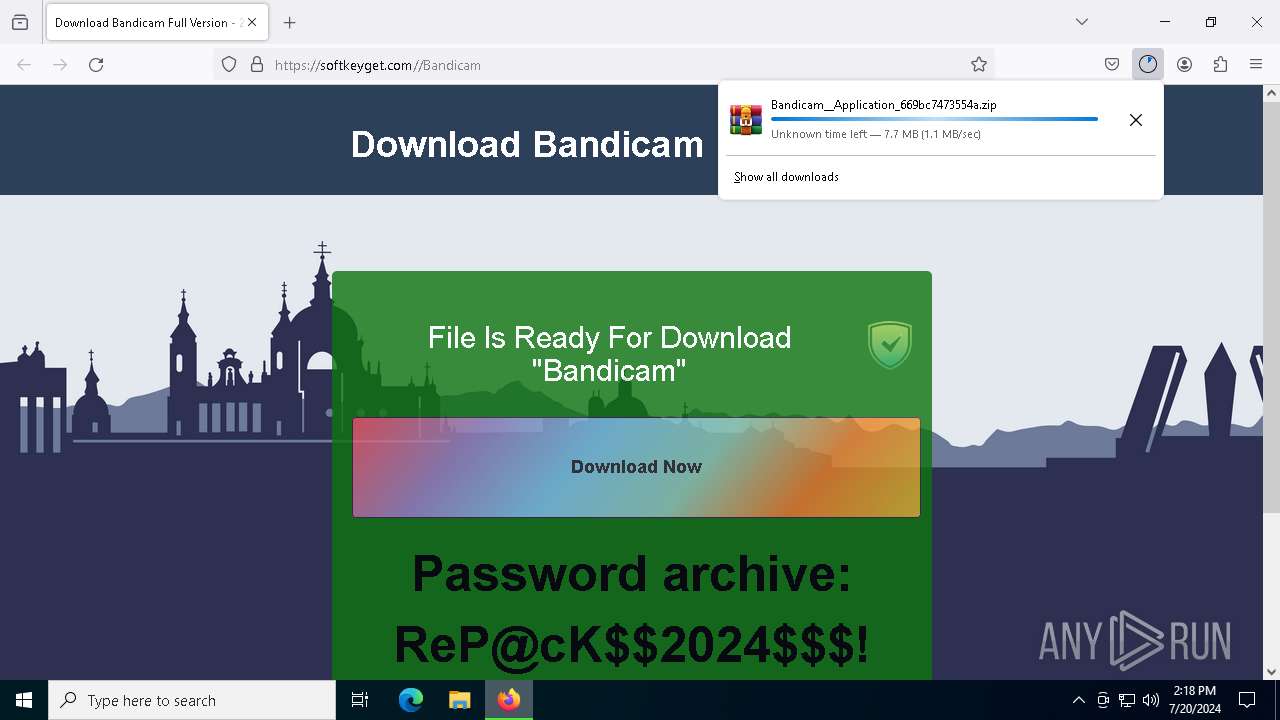
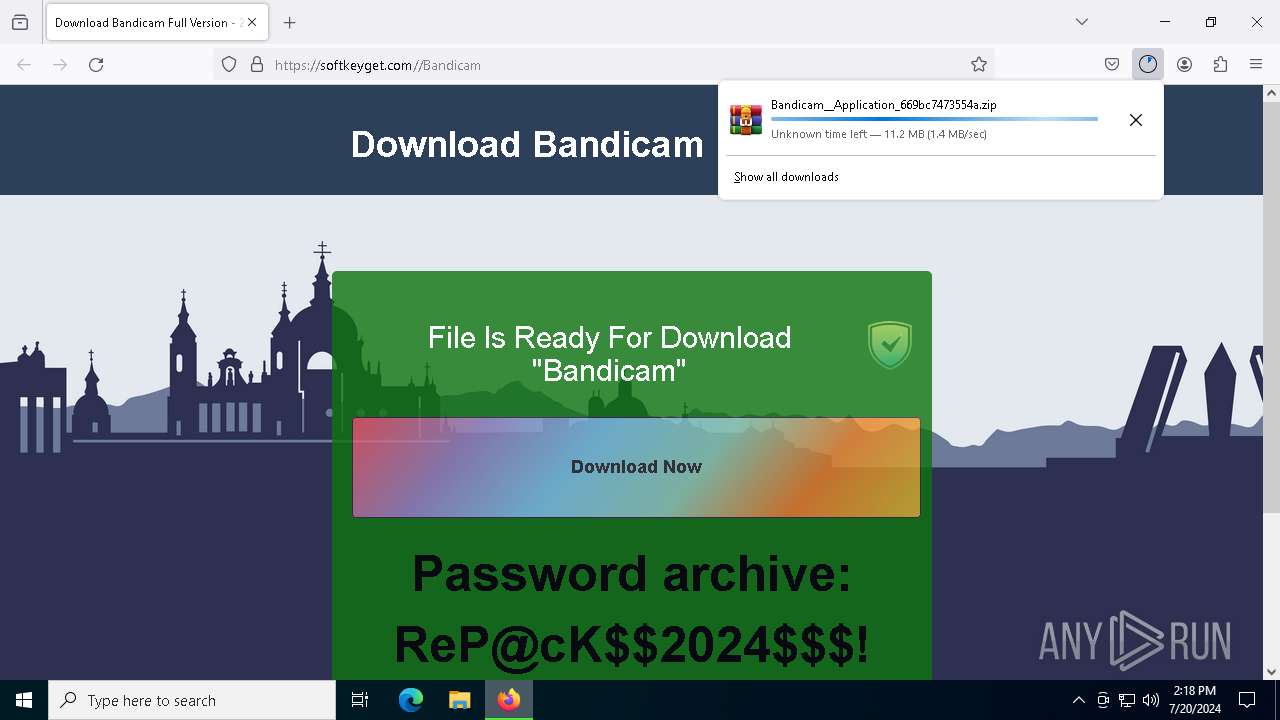
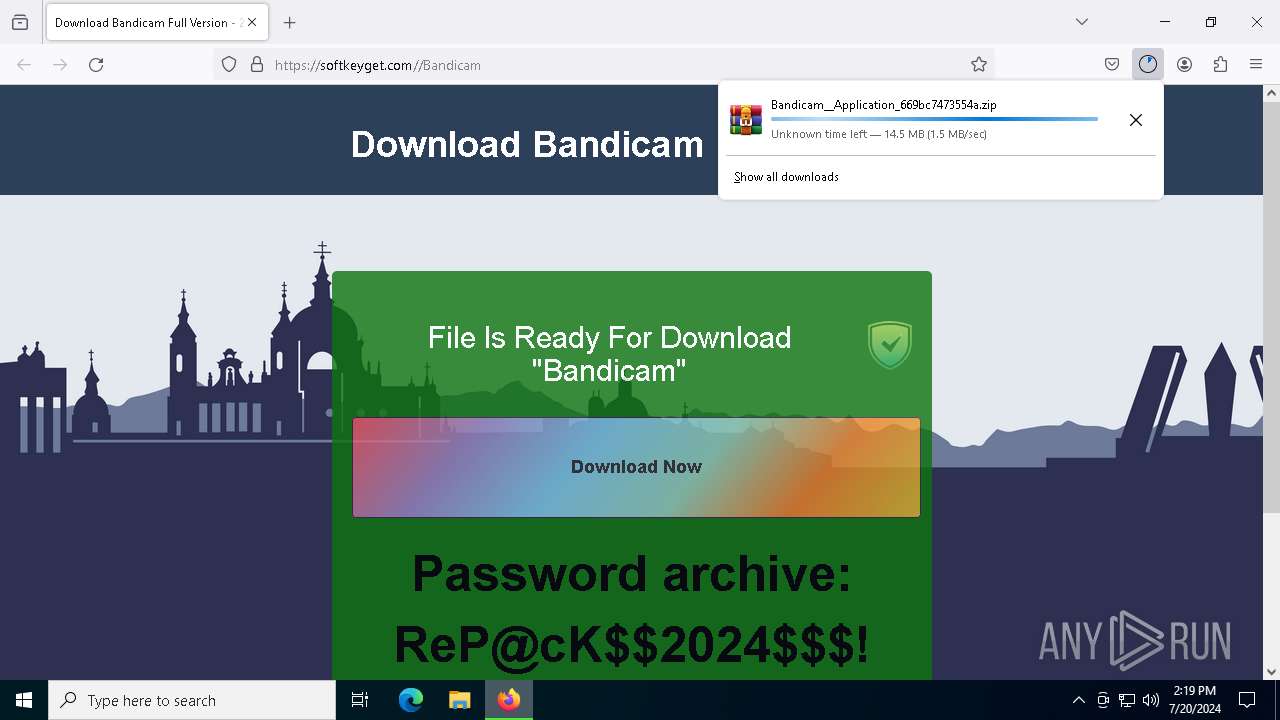
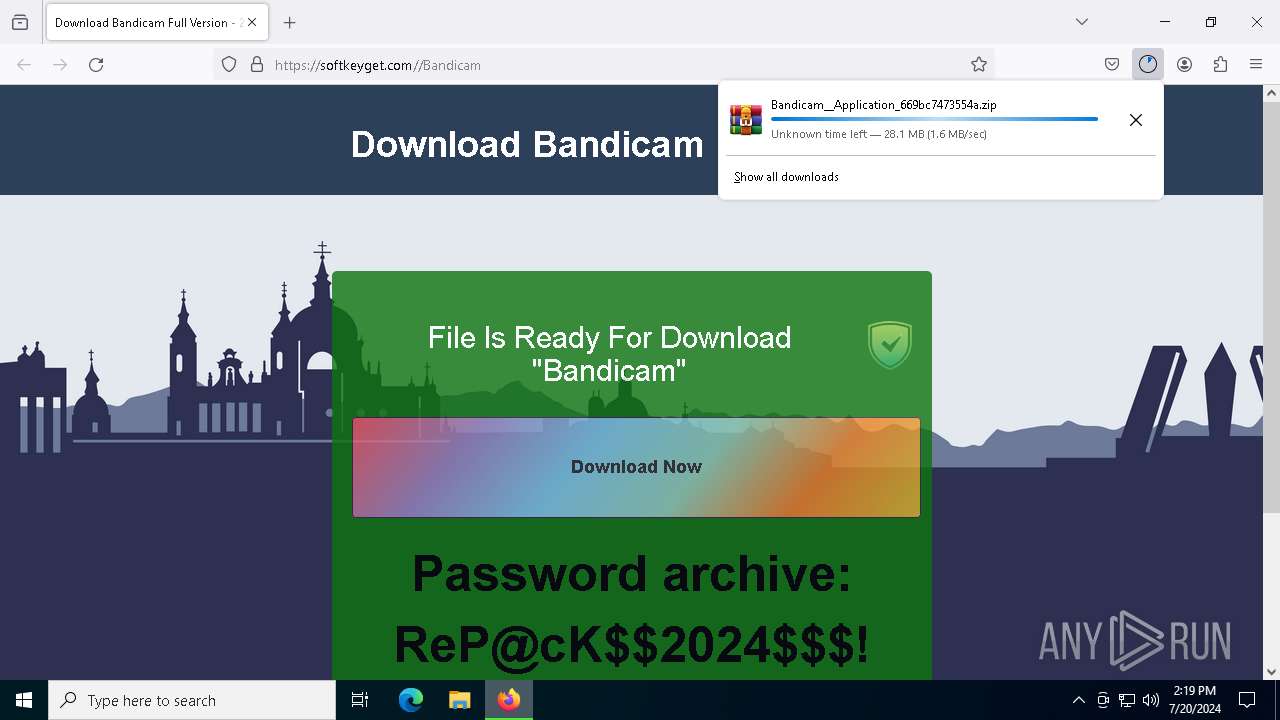
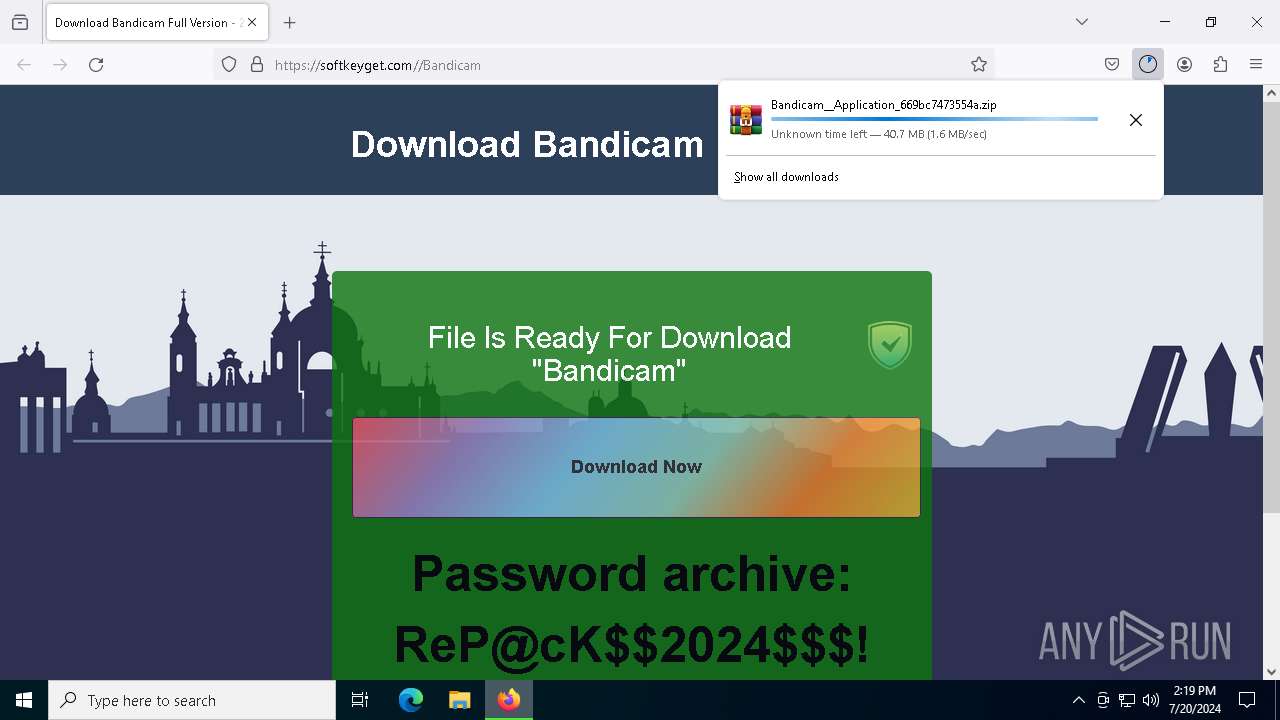
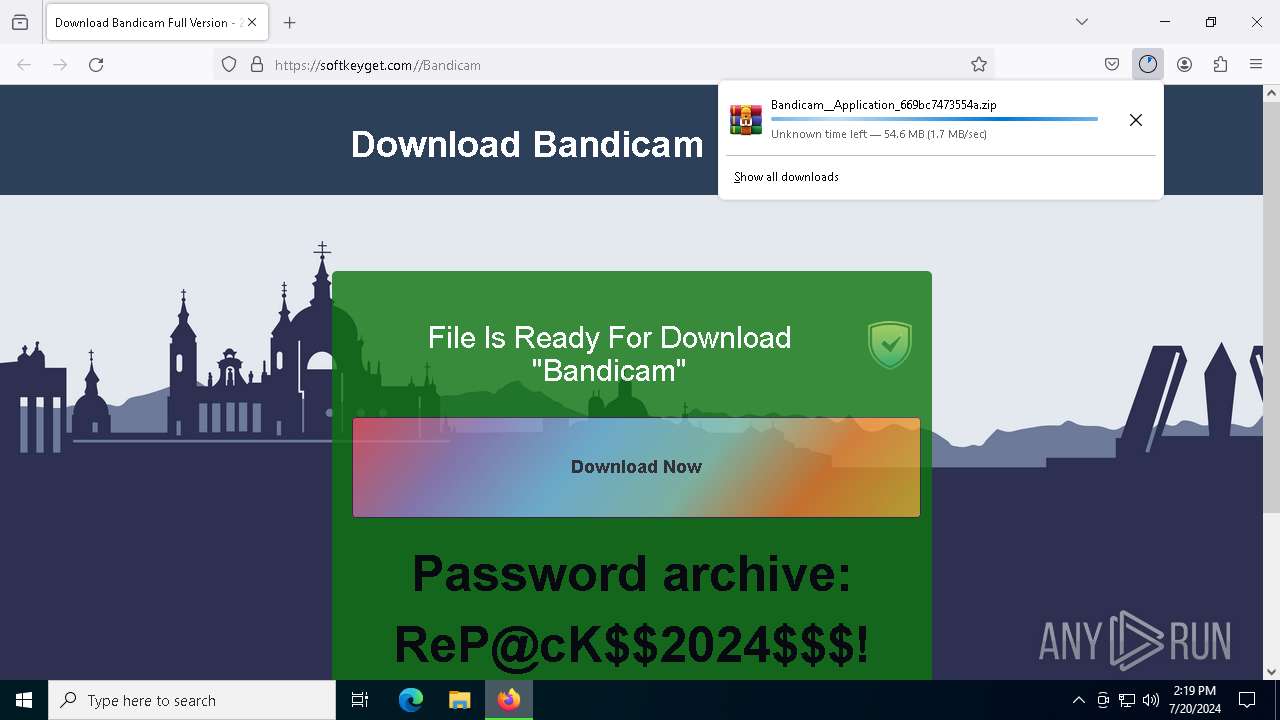
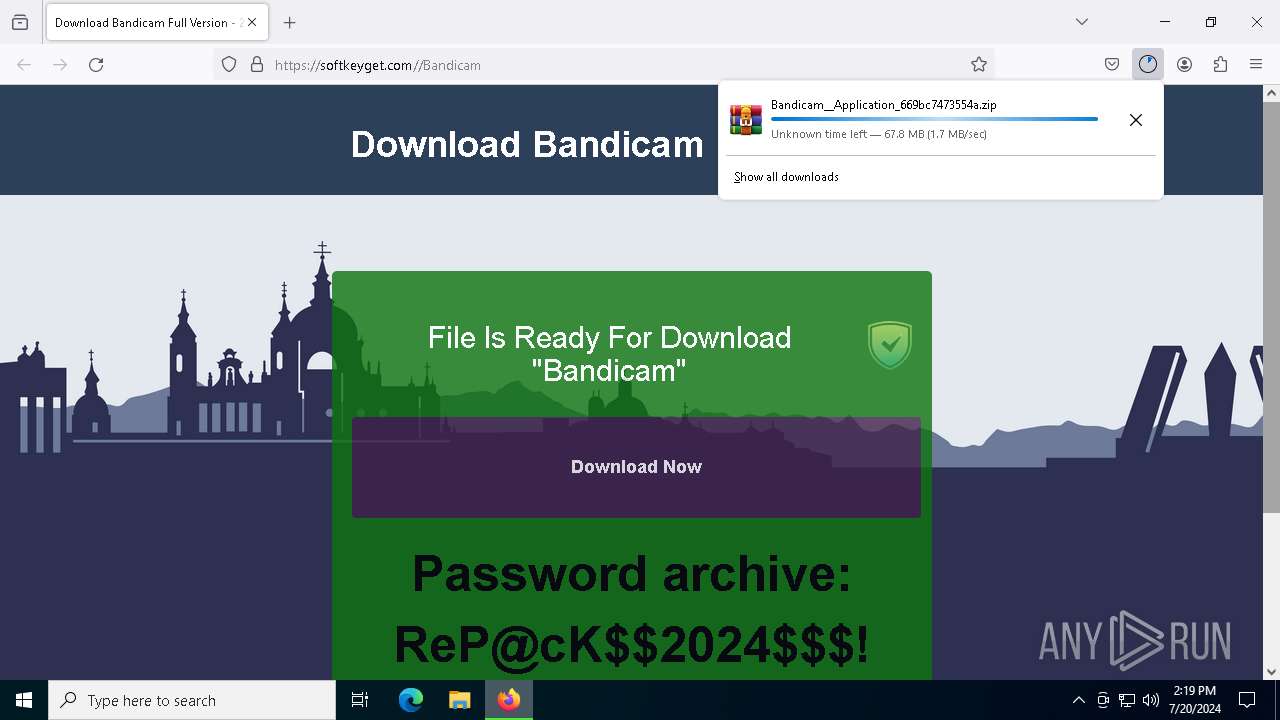
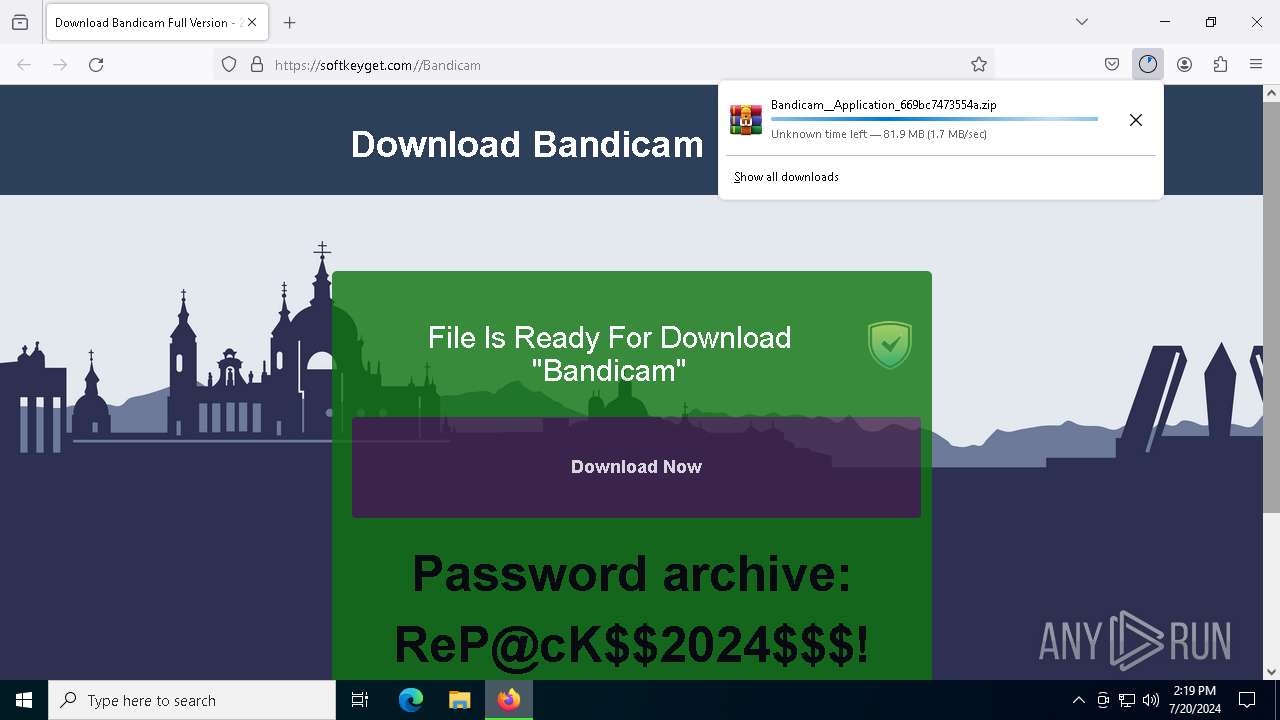
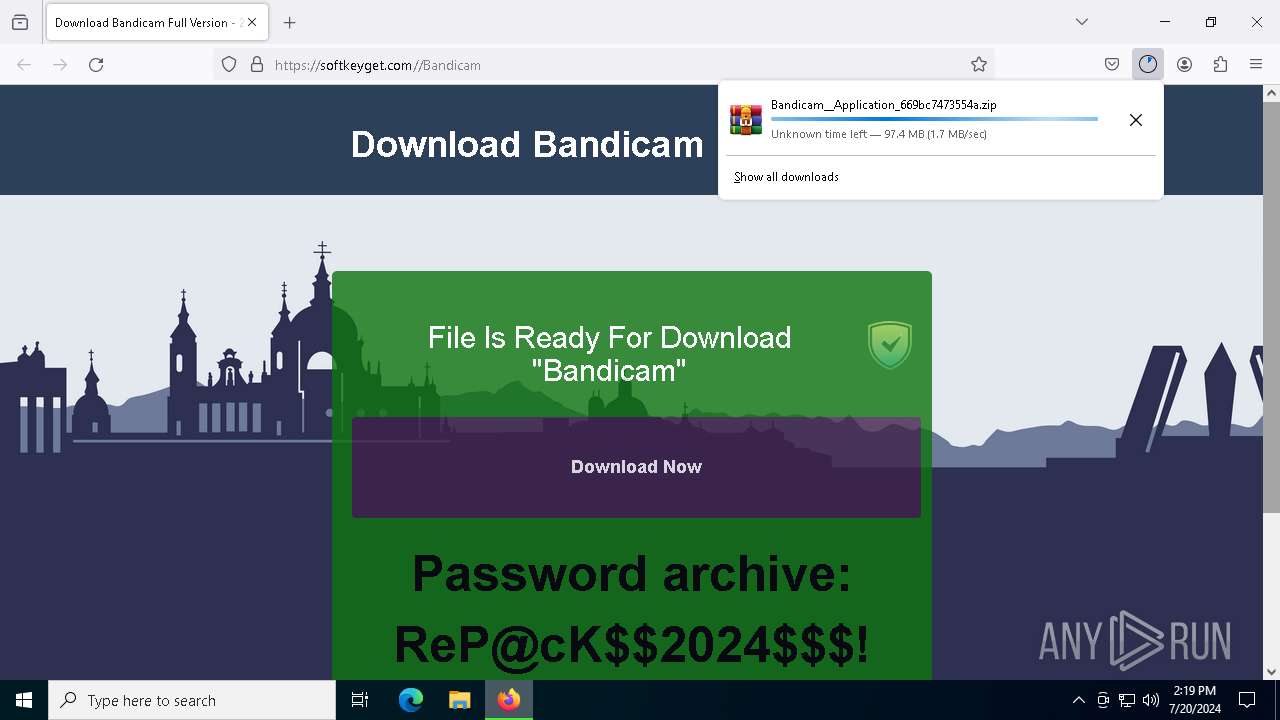
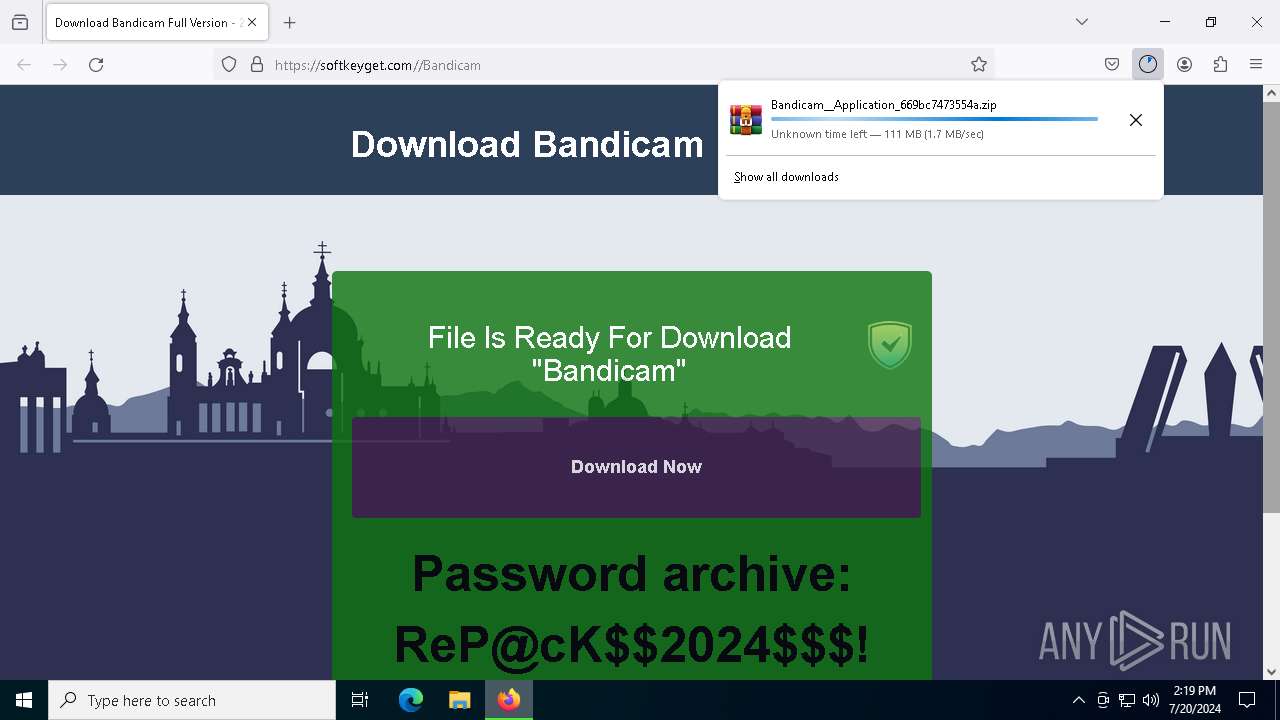
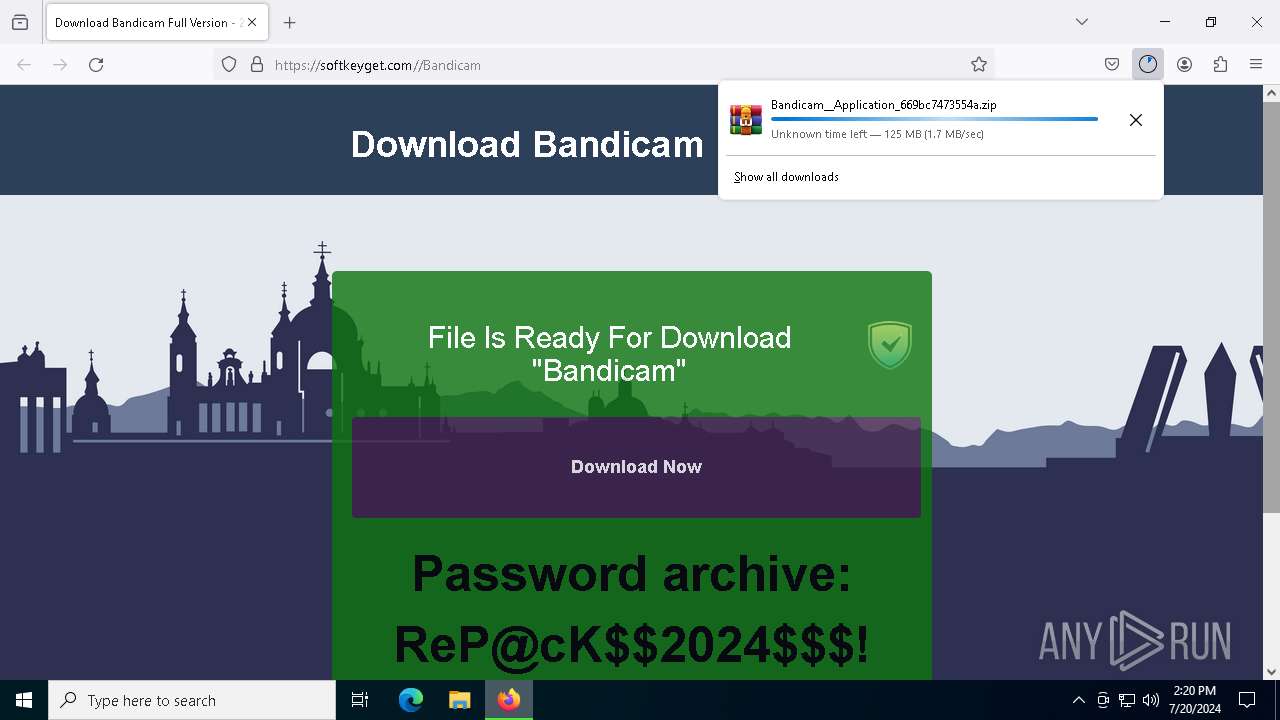
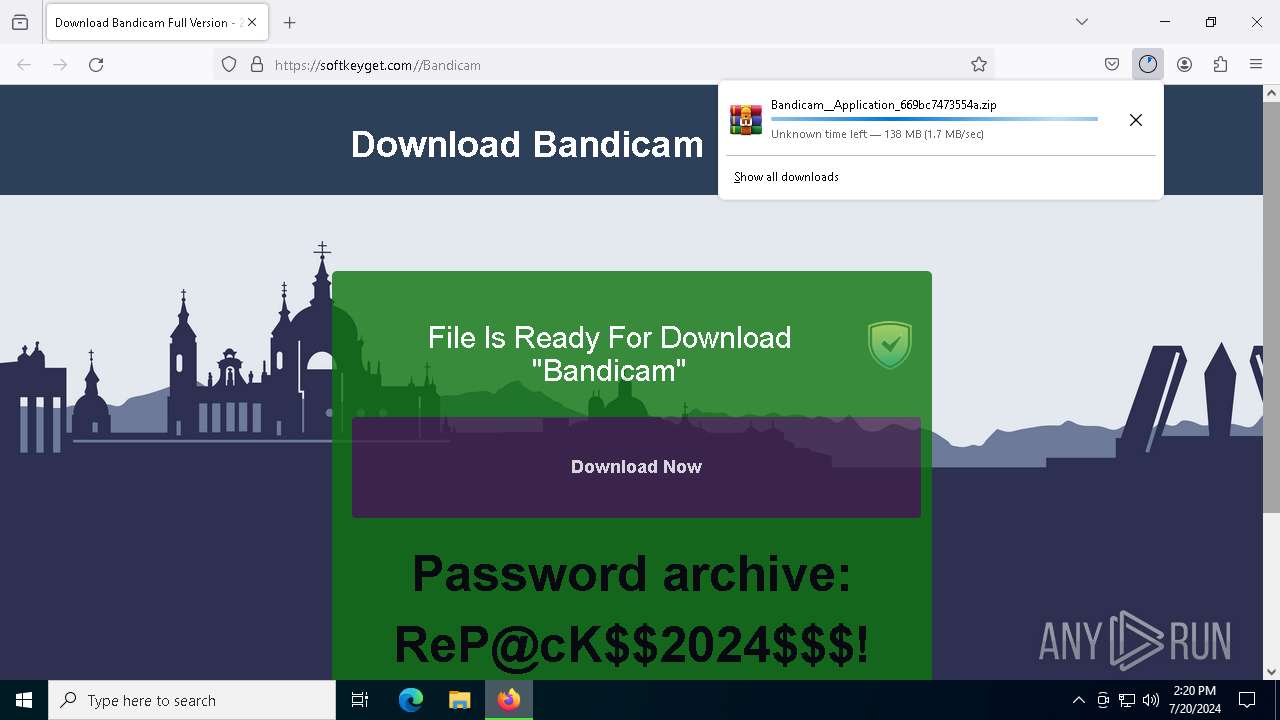
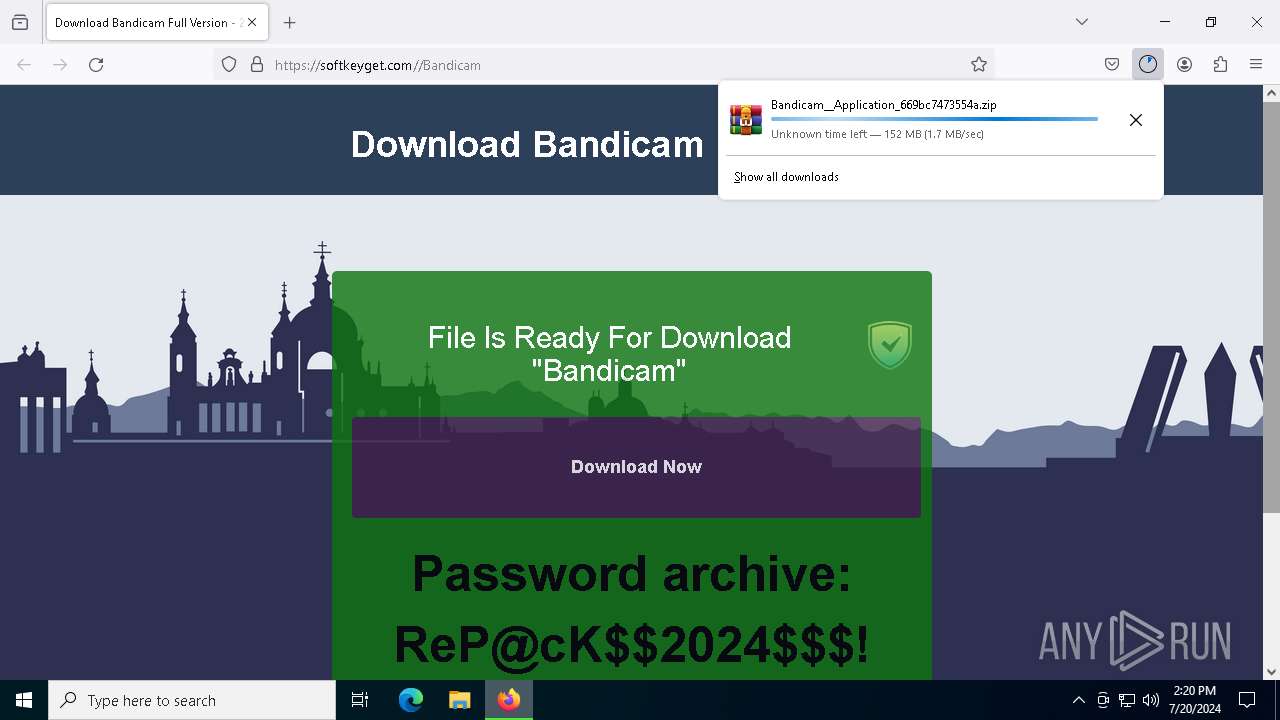
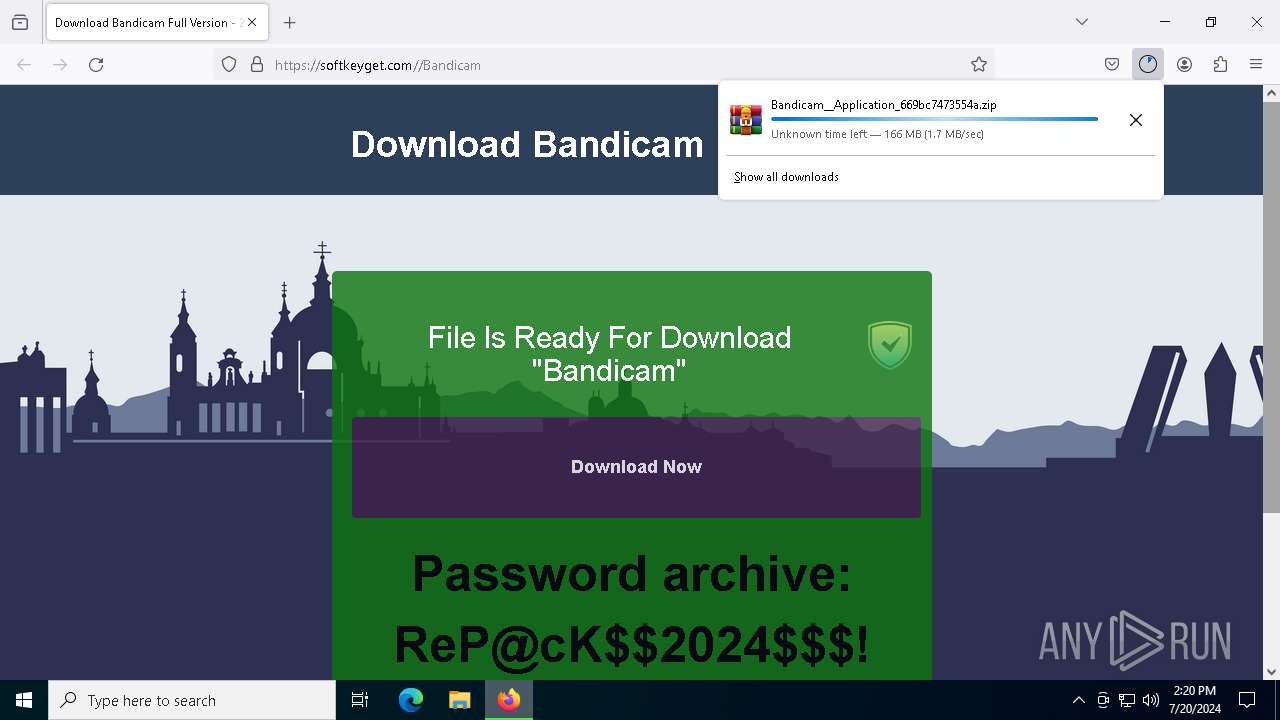
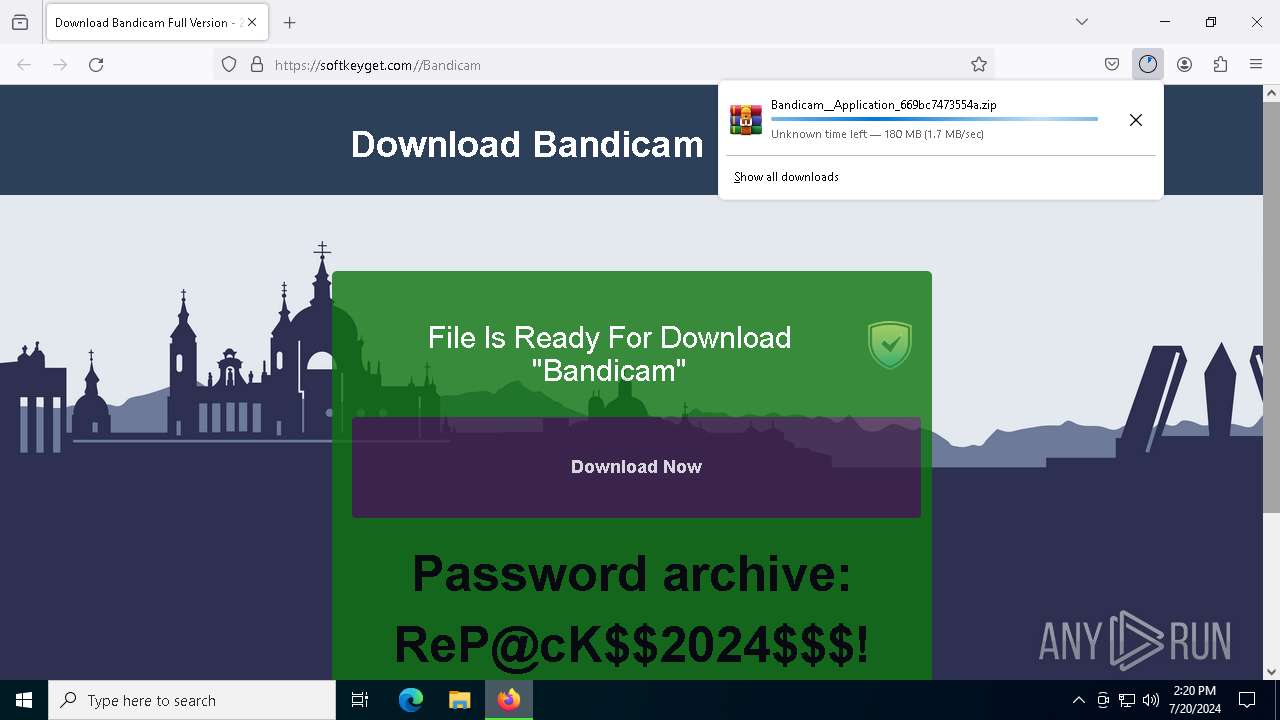
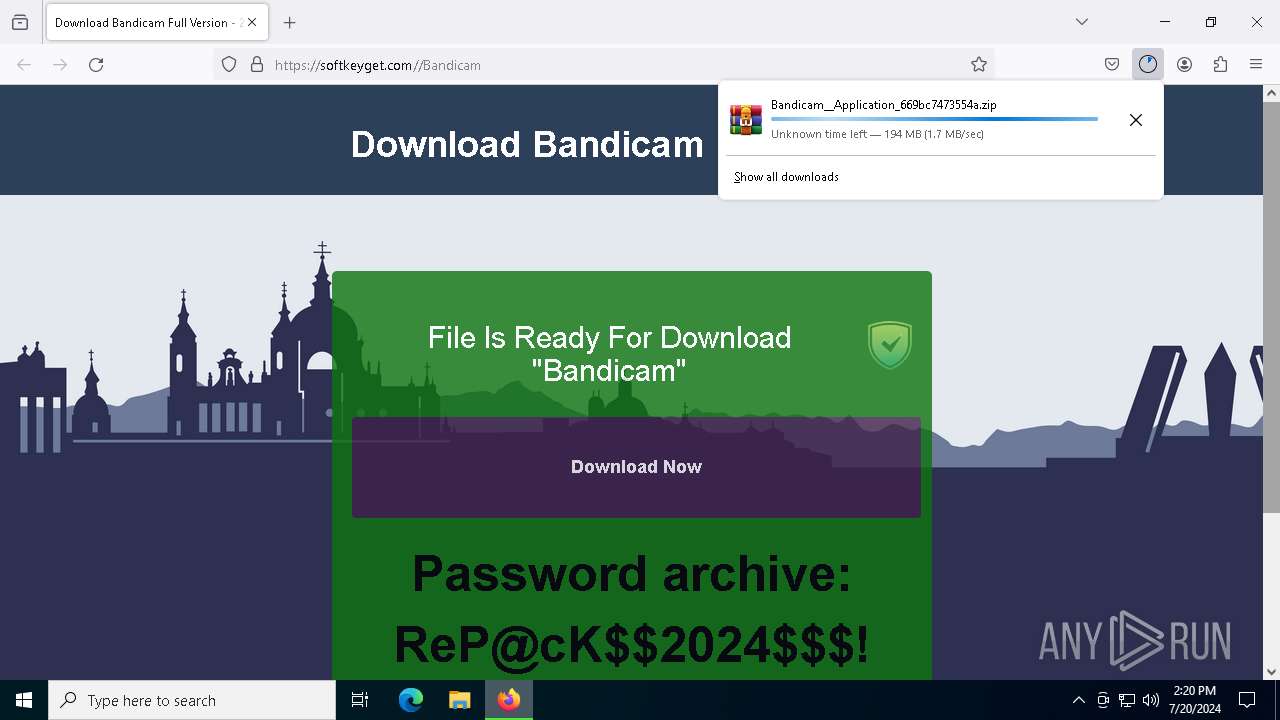
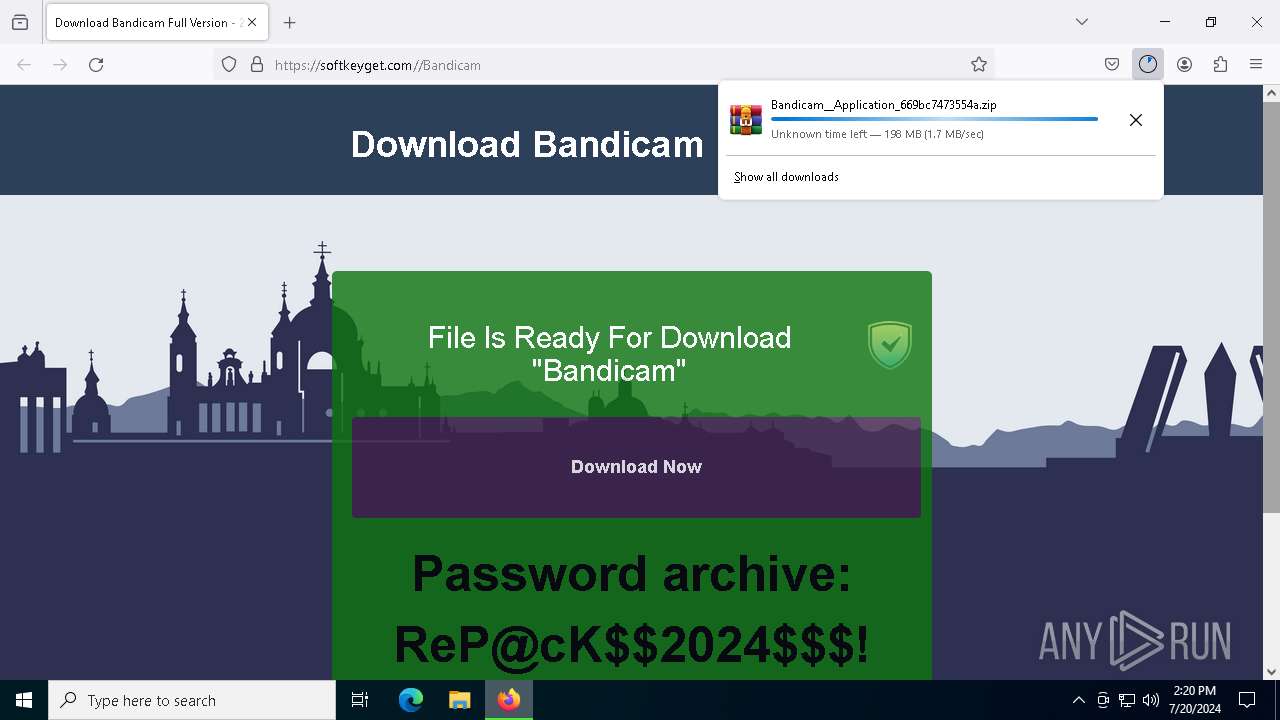
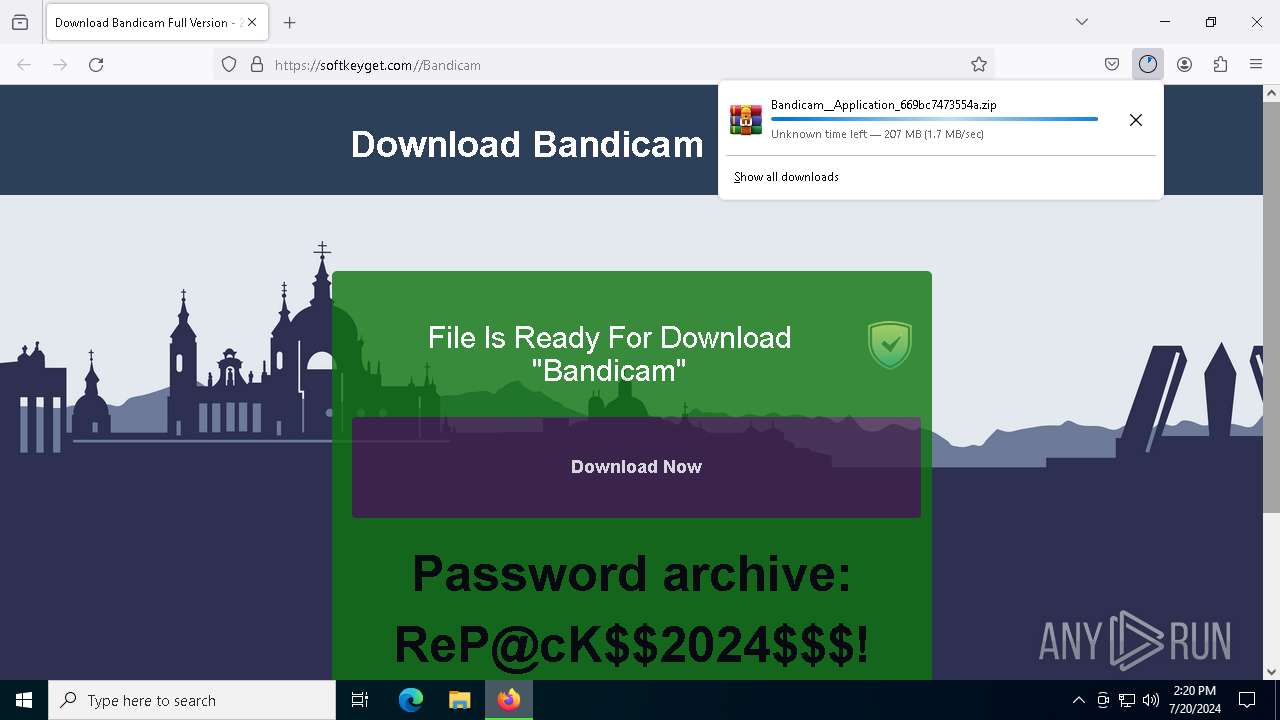
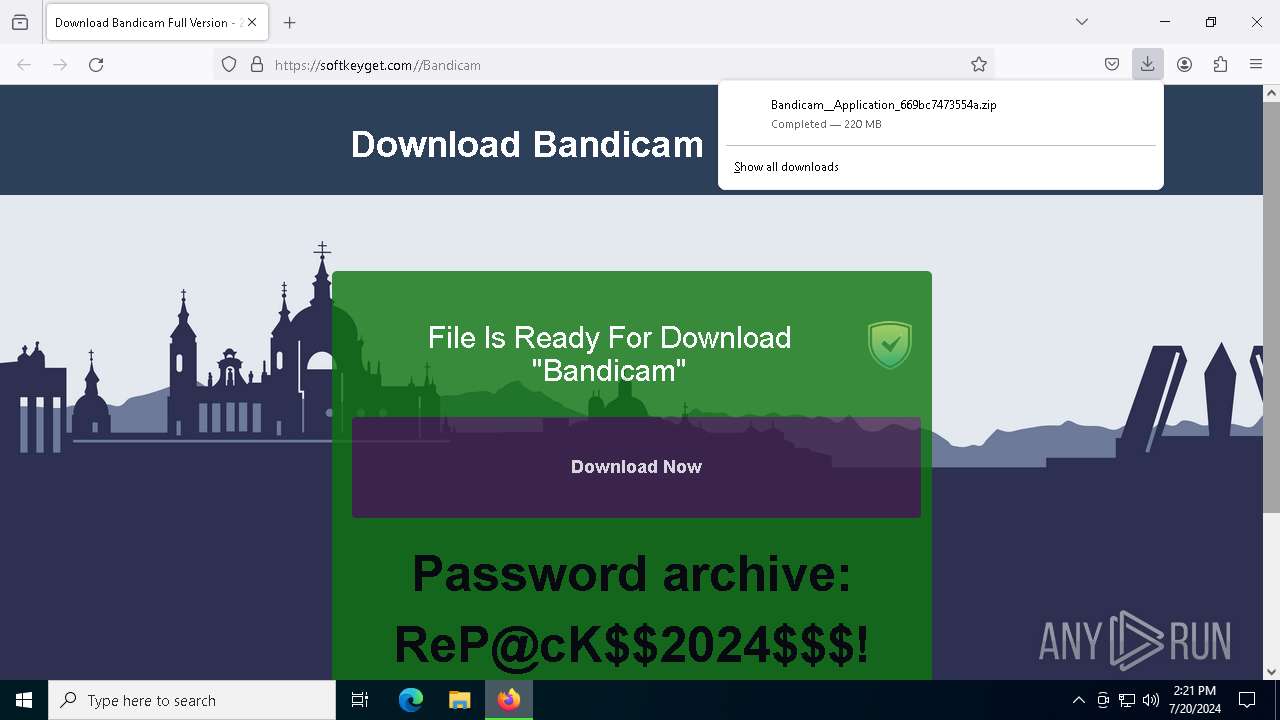
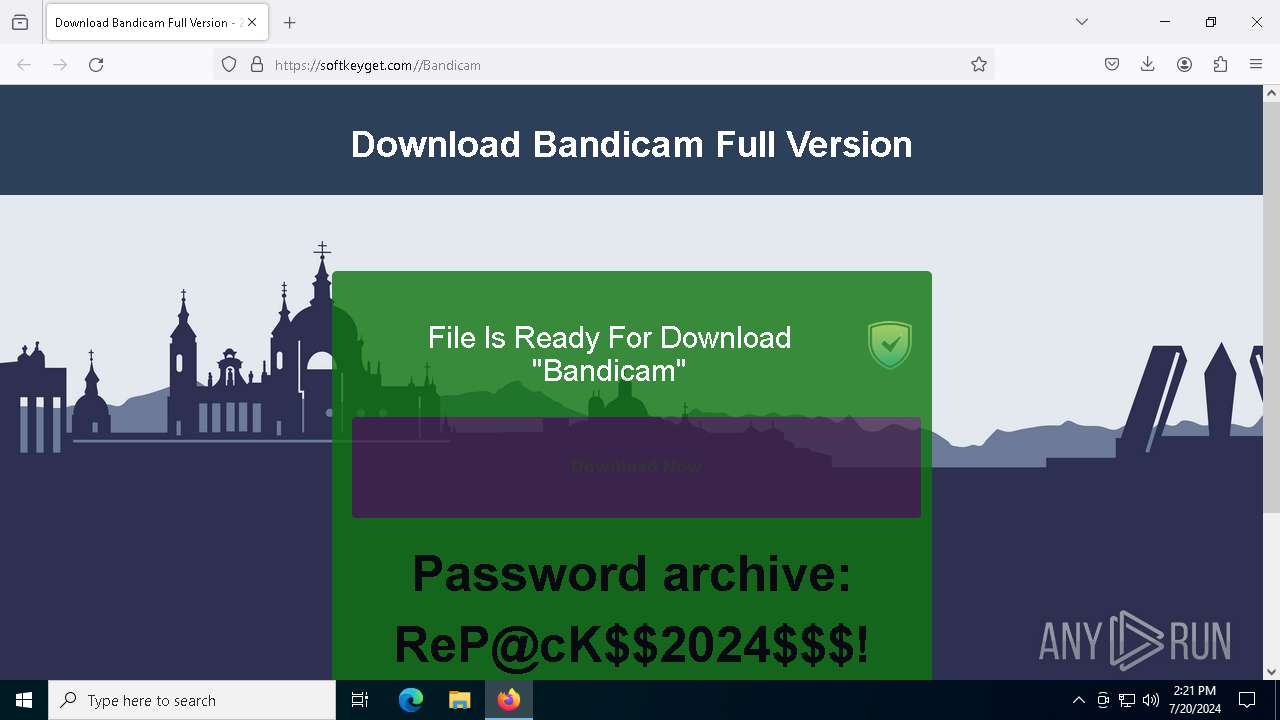
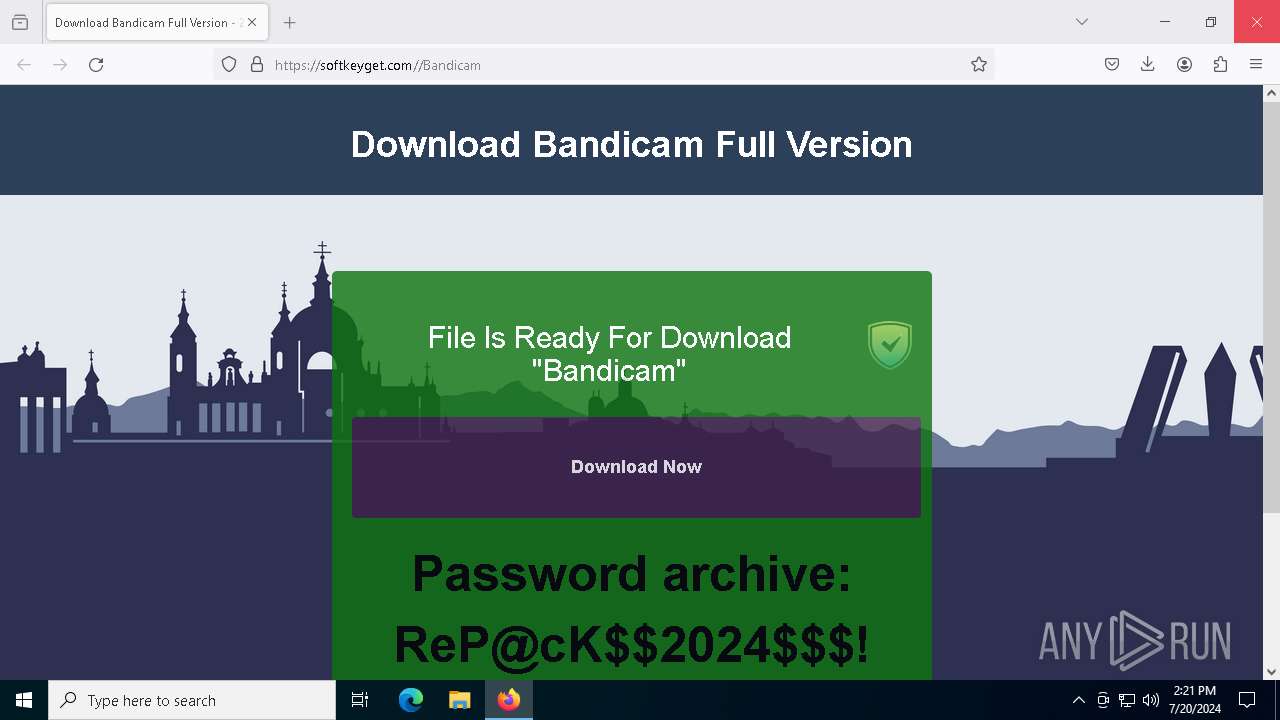
| URL: | https://softkeyget.com//Bandicam |
| Full analysis: | https://app.any.run/tasks/35a4f692-f54e-4ce6-9f2f-638b483c8370 |
| Verdict: | Malicious activity |
| Threats: | Stealc is a stealer malware that targets victims’ sensitive data, which it exfiltrates from browsers, messaging apps, and other software. The malware is equipped with advanced features, including fingerprinting, control panel, evasion mechanisms, string obfuscation, etc. Stealc establishes persistence and communicates with its C2 server through HTTP POST requests. |
| Analysis date: | July 20, 2024, 14:18:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E4B022D5F04E02FDF6B7081E7C4E6602 |
| SHA1: | 551D042A96C2D304A83739F0EA234E21E56C0267 |
| SHA256: | C04D3EFFE572EDB51B53B4B76CAECD744BDE0B977C4B2669FEB7AE7338D63FCE |
| SSDEEP: | 3:N8H0KRiB:2rRiB |
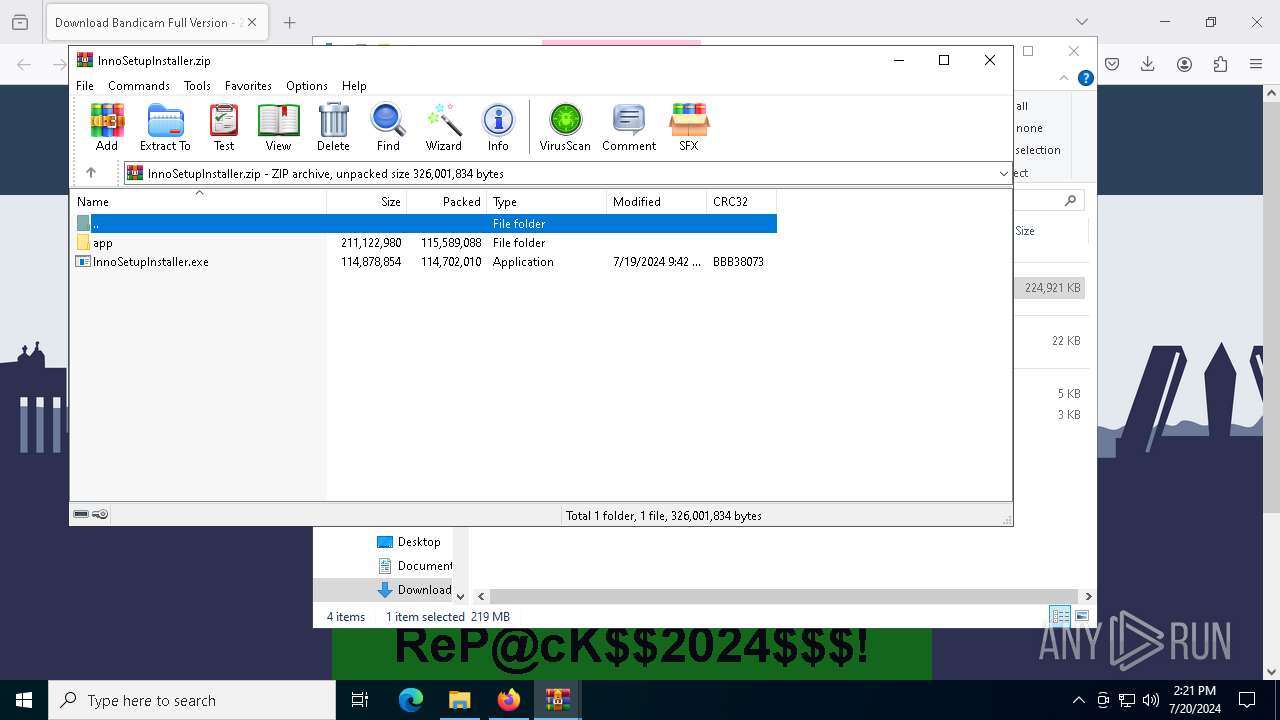
MALICIOUS
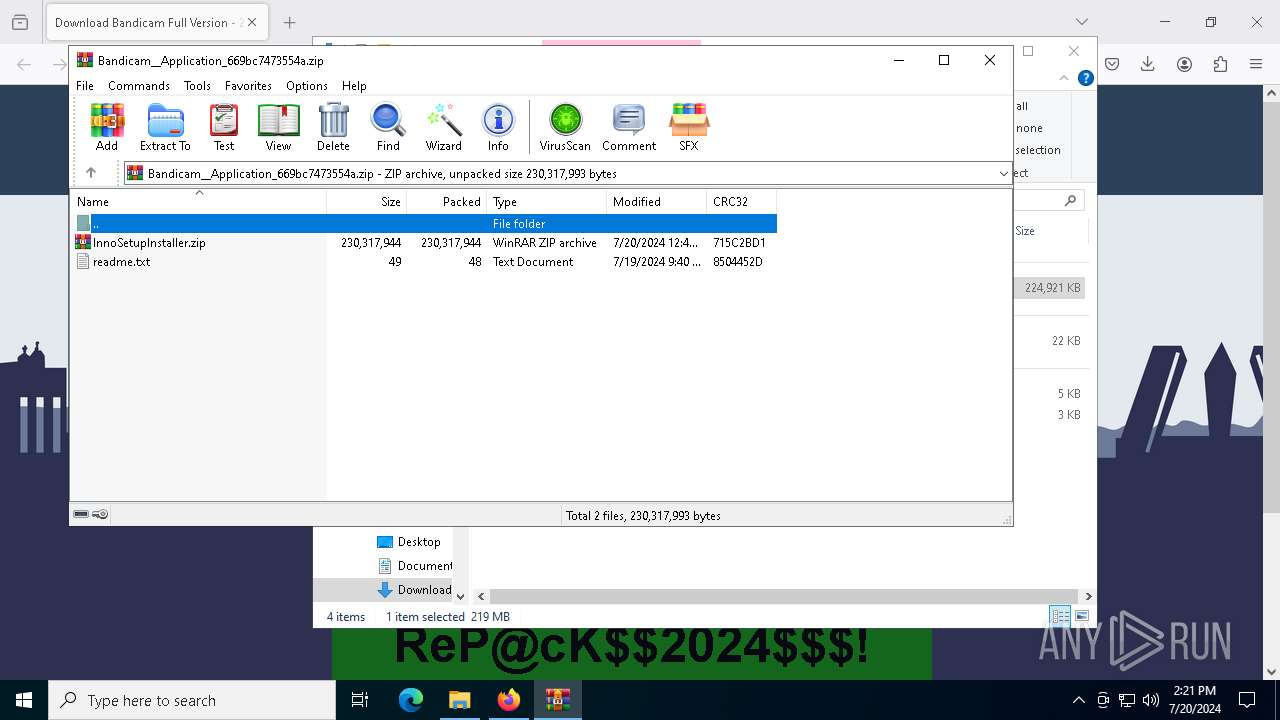
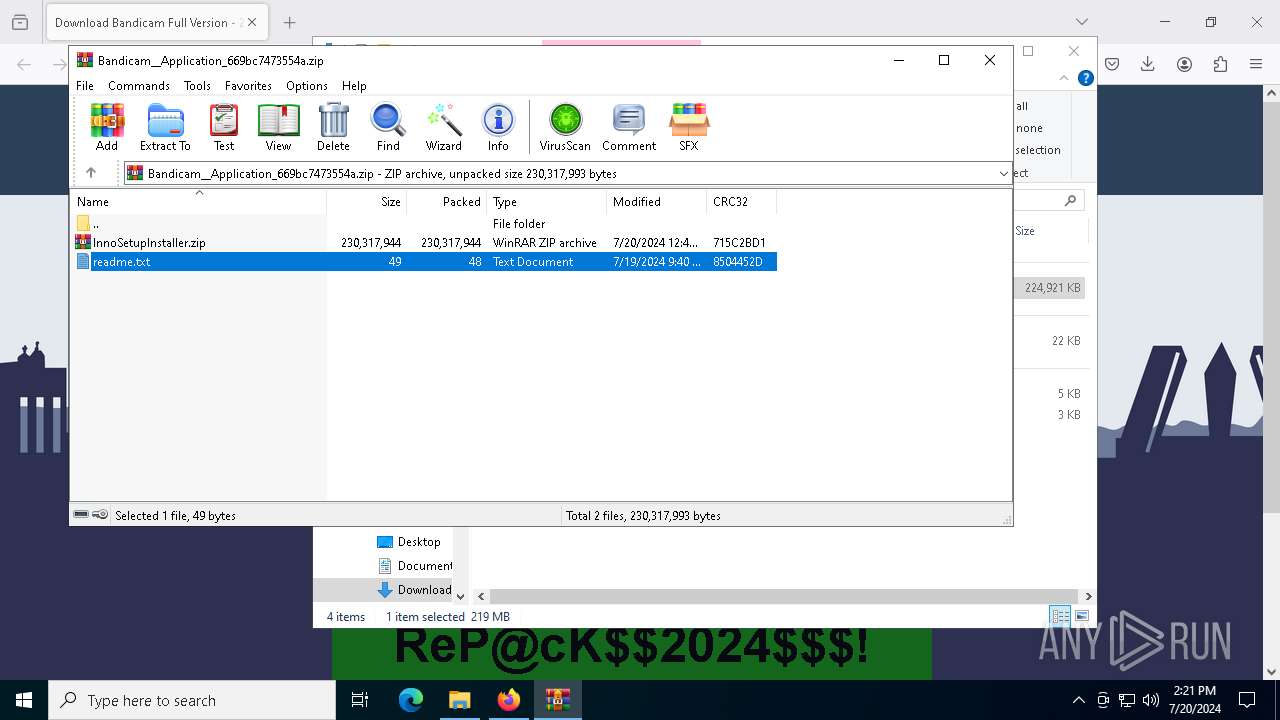
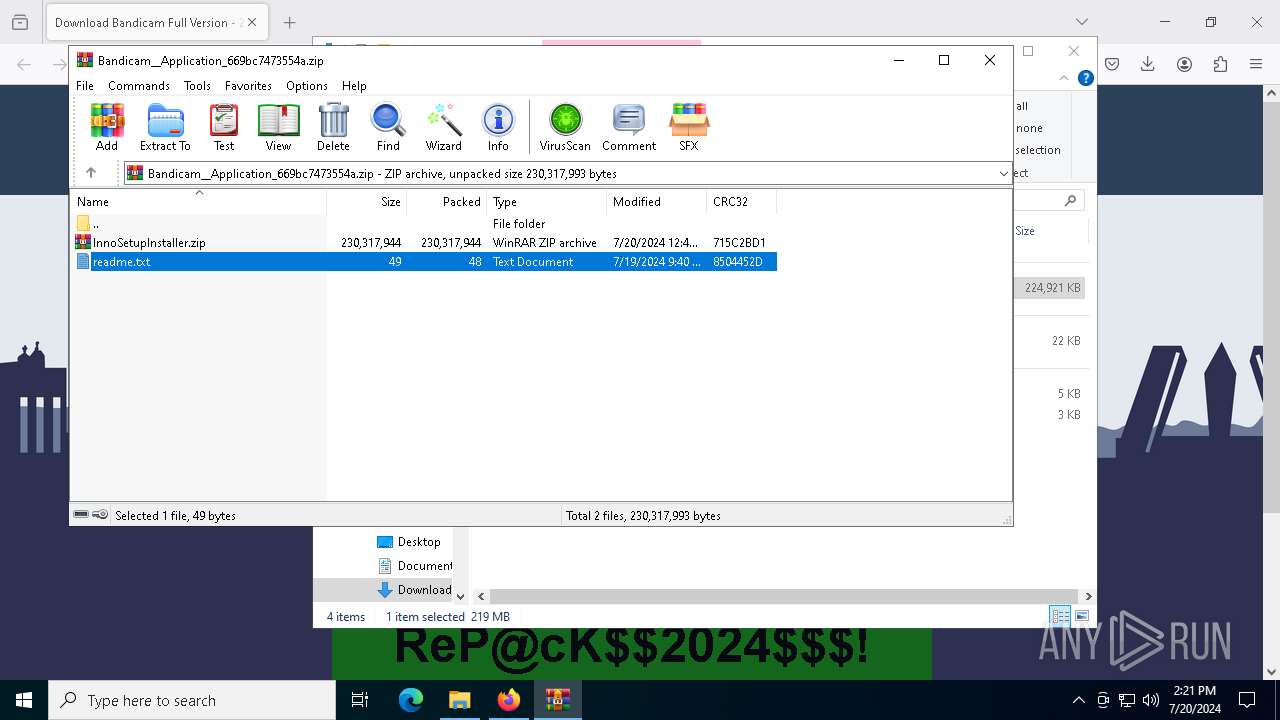
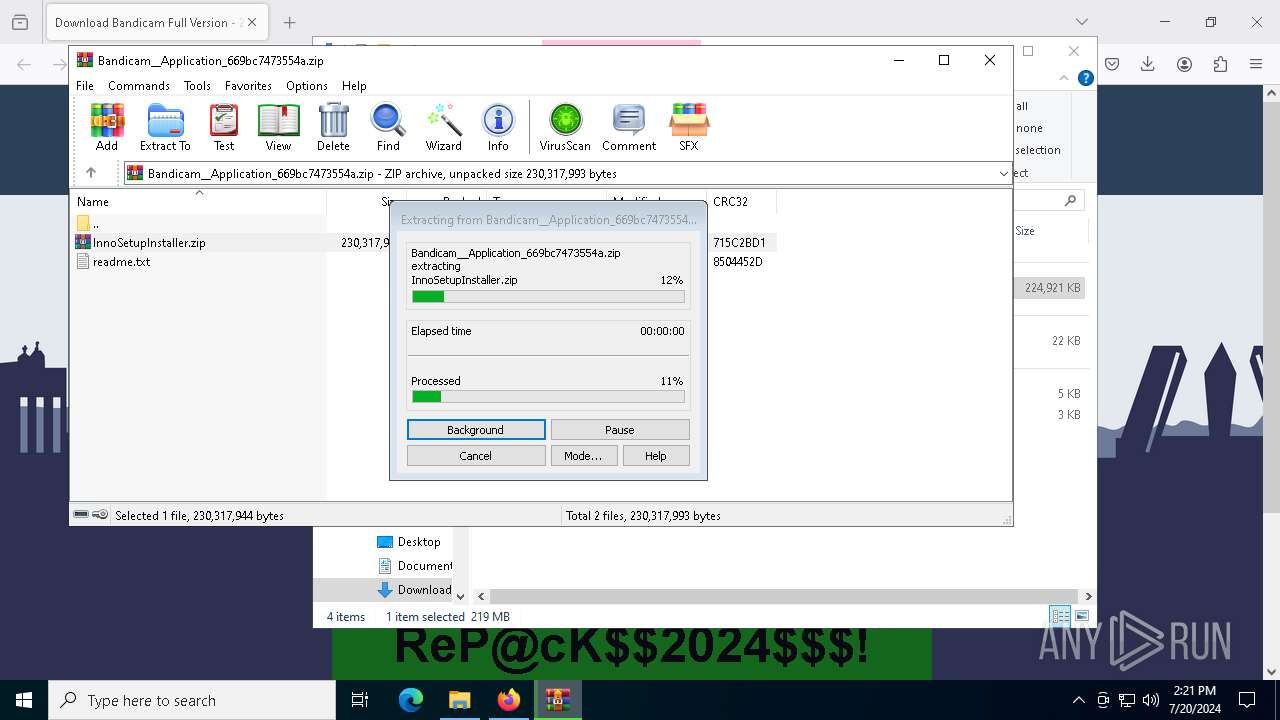
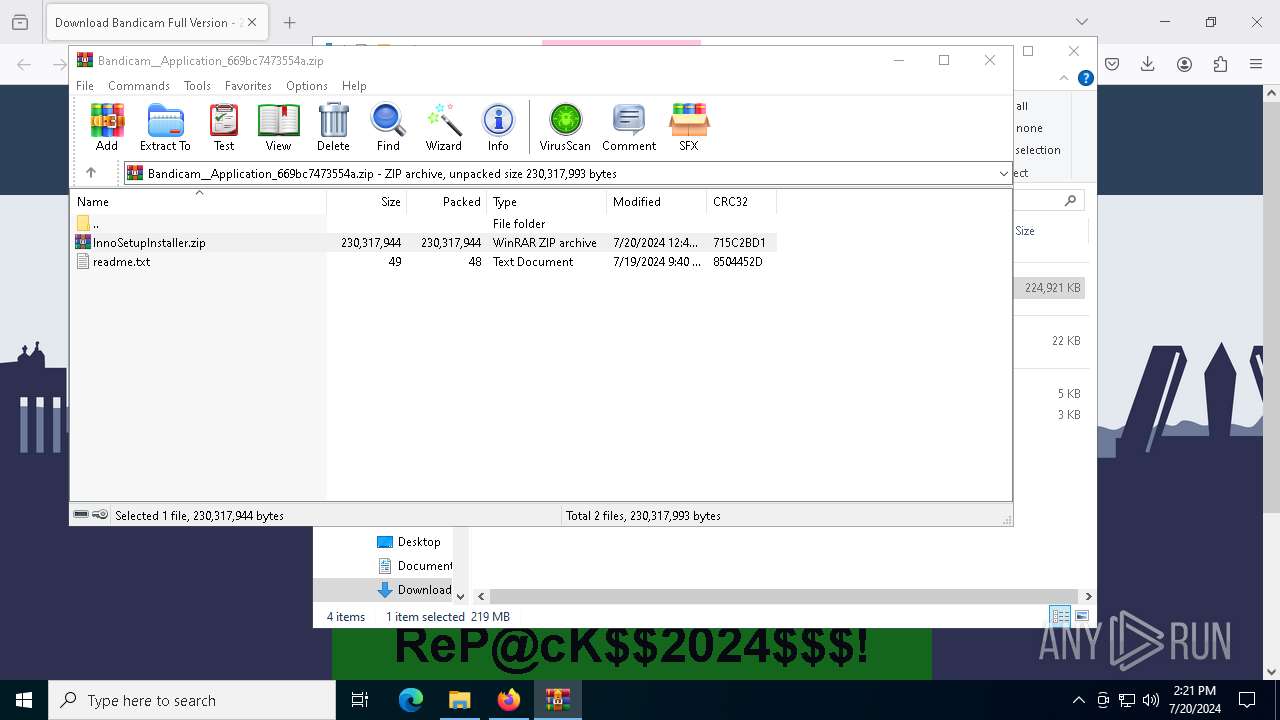
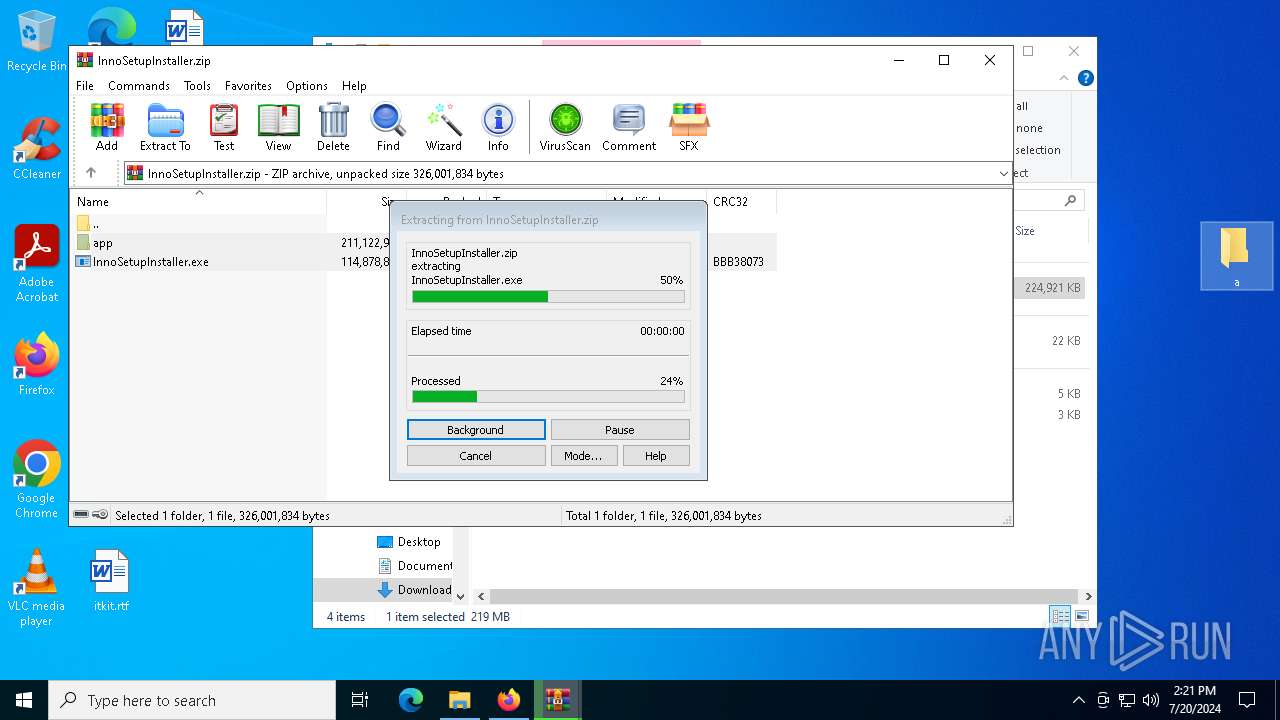
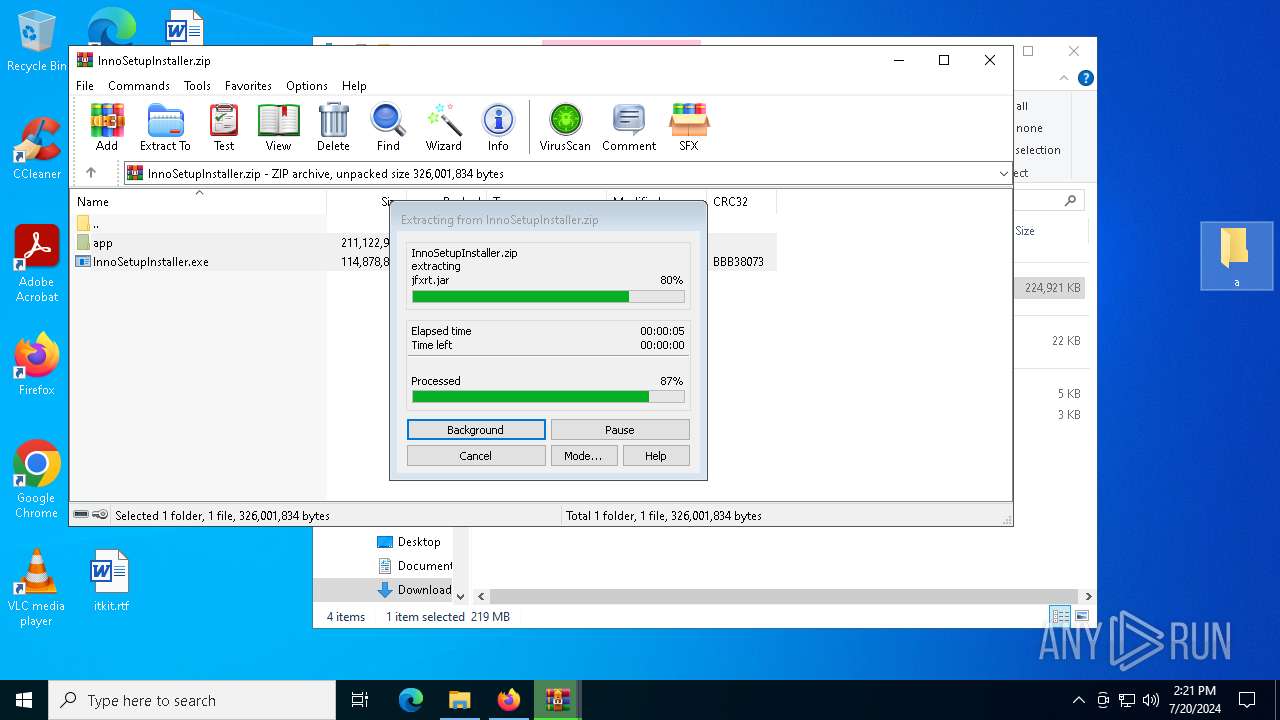
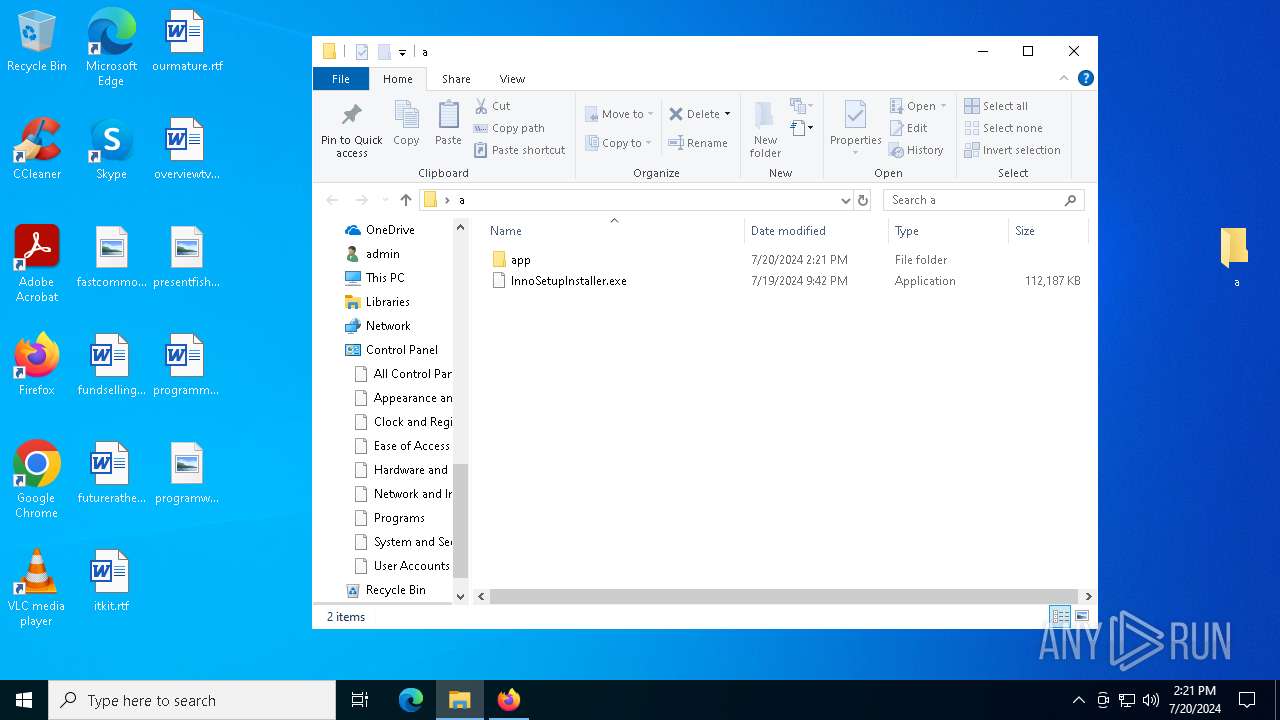
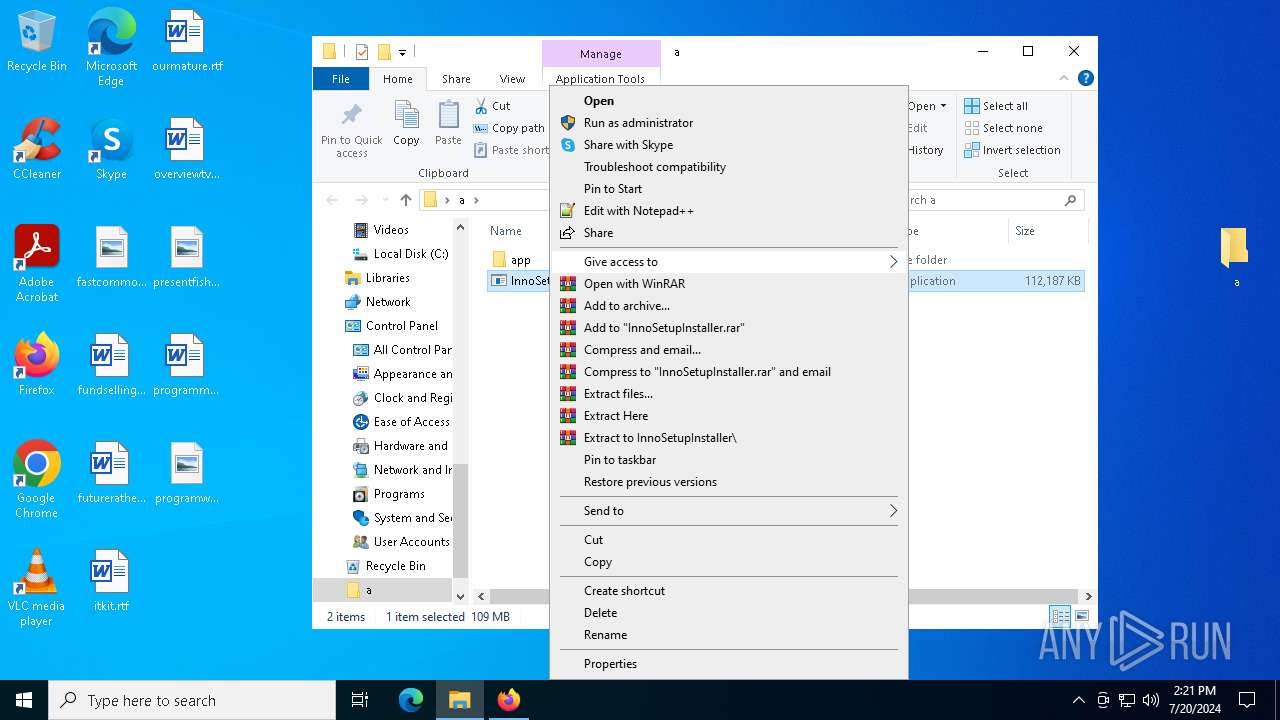
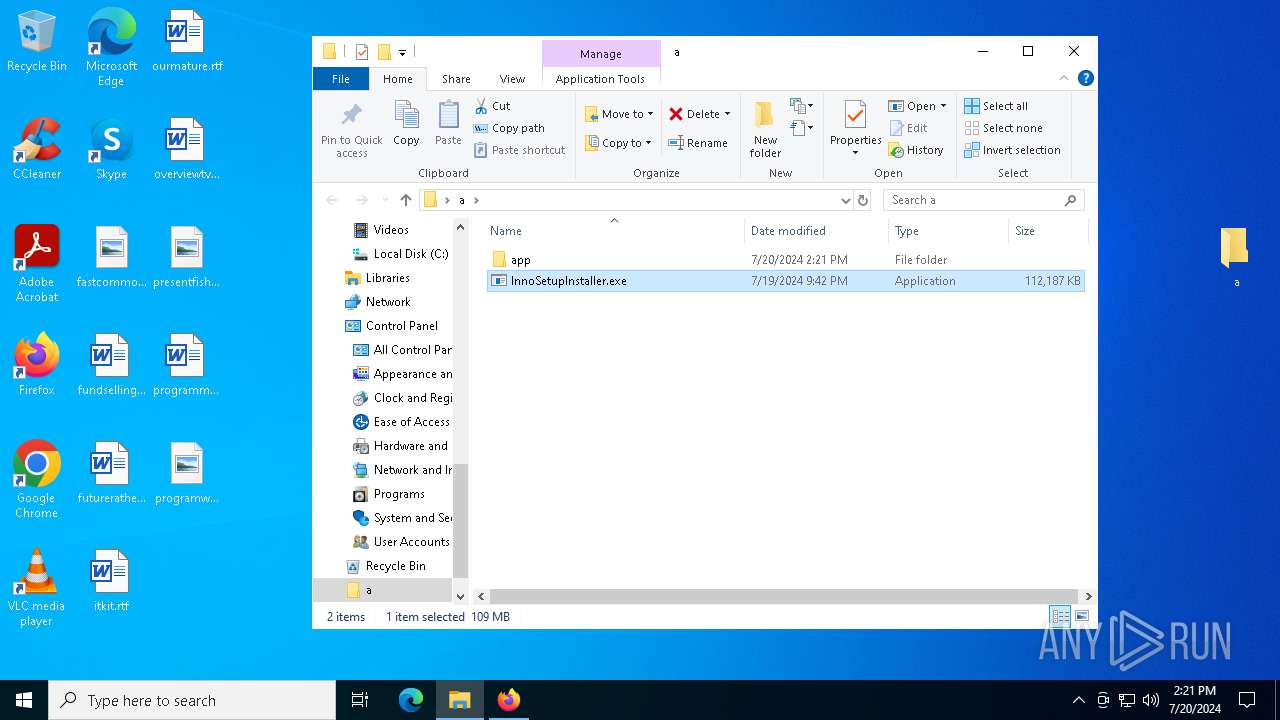
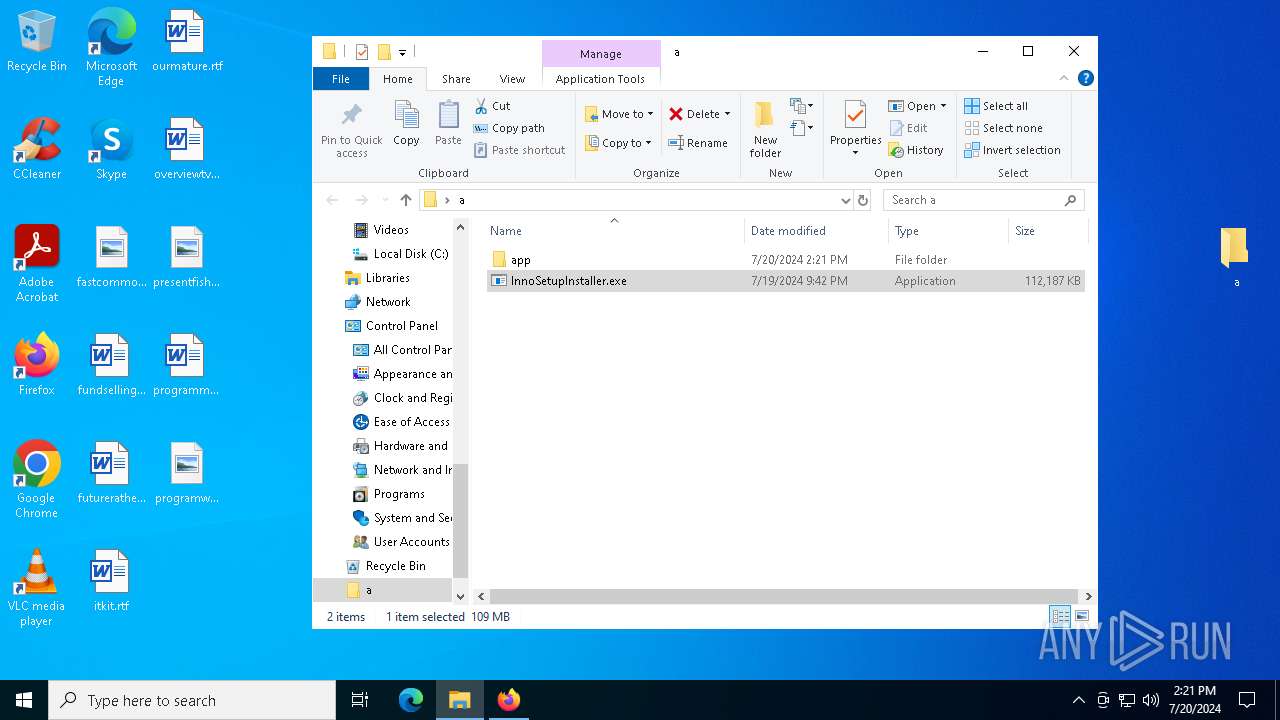
Drops the executable file immediately after the start
- InnoSetupInstaller.exe (PID: 6700)
Stealers network behavior
- RegAsm.exe (PID: 7872)
STEALC has been detected (SURICATA)
- RegAsm.exe (PID: 7872)
Connects to the CnC server
- RegAsm.exe (PID: 7872)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1320)
- RegAsm.exe (PID: 7872)
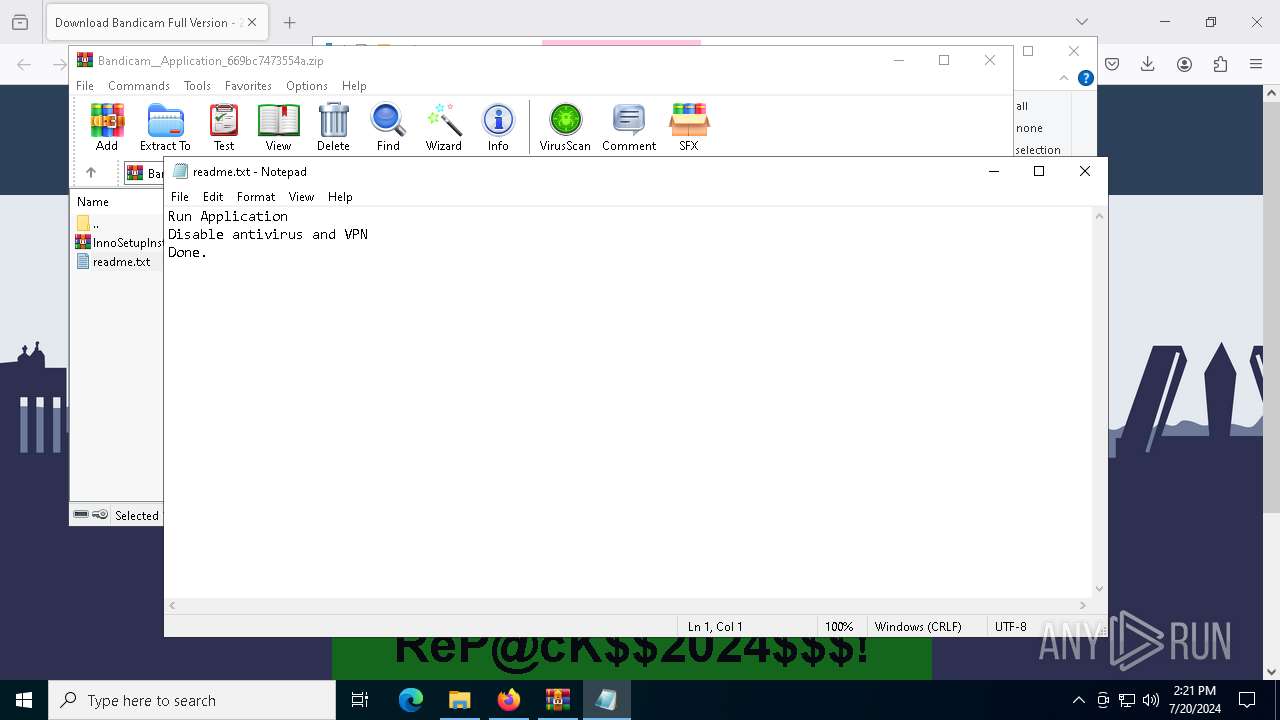
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 1320)
Application launched itself
- WinRAR.exe (PID: 1320)
Process drops legitimate windows executable
- WinRAR.exe (PID: 7216)
Starts POWERSHELL.EXE for commands execution
- InnoSetupInstaller.exe (PID: 6700)
Executable content was dropped or overwritten
- InnoSetupInstaller.exe (PID: 6700)
Powershell scripting: start process
- InnoSetupInstaller.exe (PID: 6700)
Windows Defender mutex has been found
- RegAsm.exe (PID: 7872)
Contacting a server suspected of hosting an CnC
- RegAsm.exe (PID: 7872)
INFO
Application launched itself
- firefox.exe (PID: 1456)
- firefox.exe (PID: 2116)
Executable content was dropped or overwritten
- firefox.exe (PID: 1456)
- WinRAR.exe (PID: 7216)
Reads Microsoft Office registry keys
- firefox.exe (PID: 1456)
- WinRAR.exe (PID: 1320)
Drops the executable file immediately after the start
- firefox.exe (PID: 1456)
- WinRAR.exe (PID: 7216)
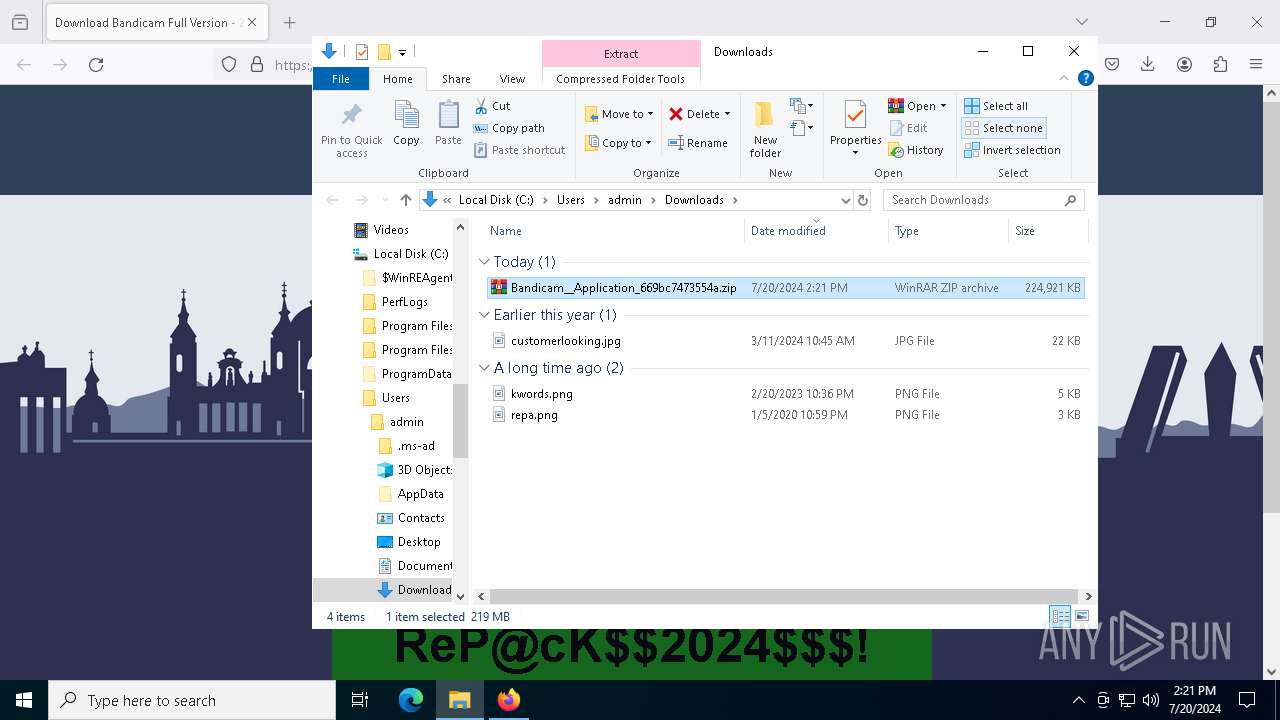
The process uses the downloaded file
- firefox.exe (PID: 1456)
- WinRAR.exe (PID: 1320)
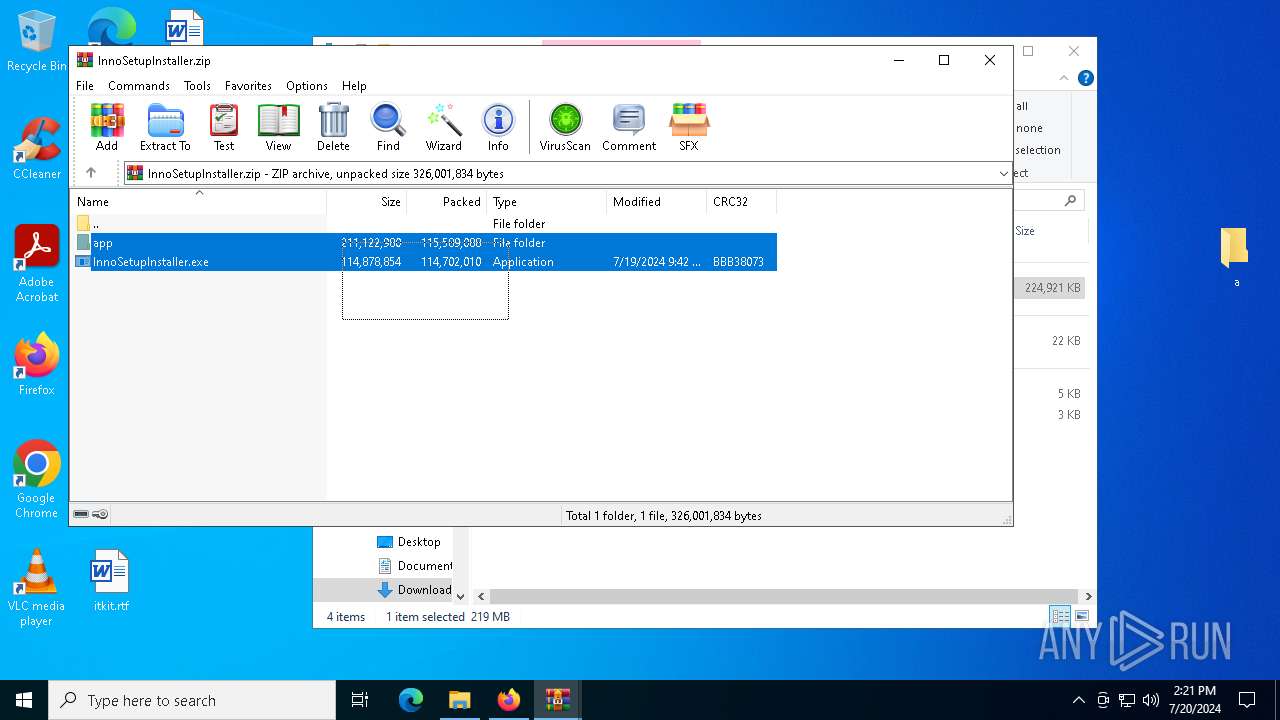
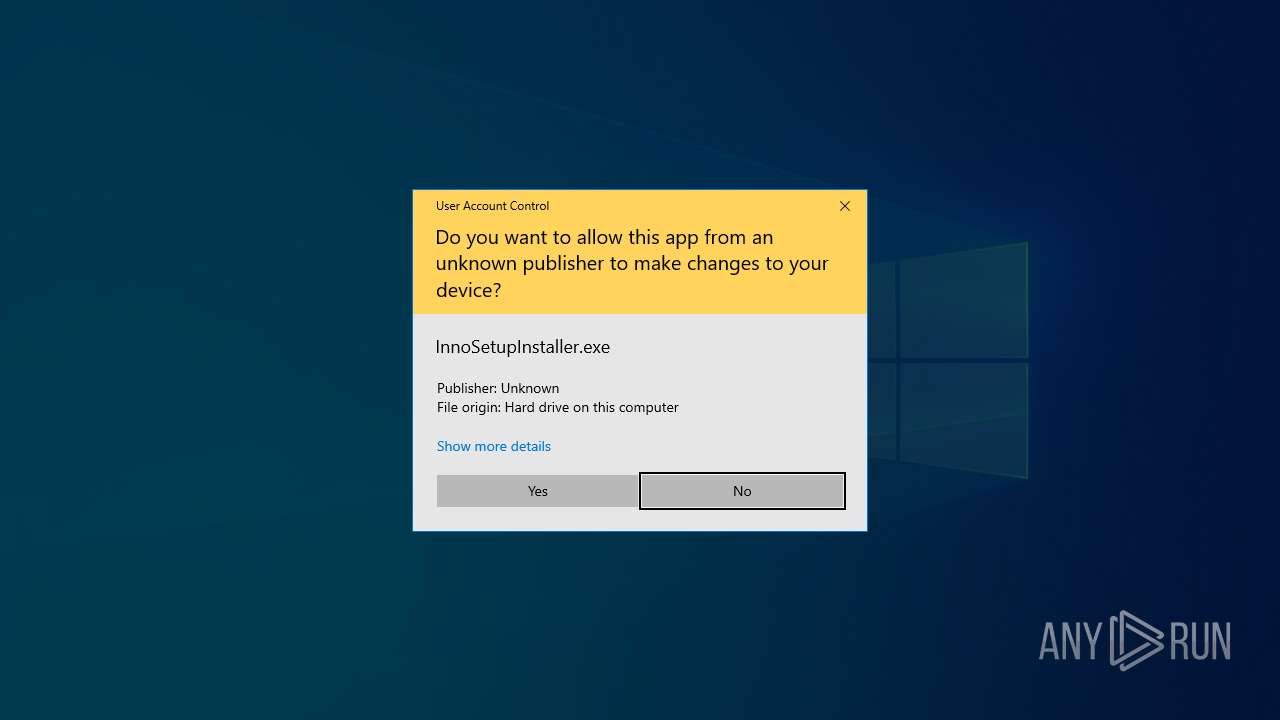
Manual execution by a user
- WinRAR.exe (PID: 1320)
- InnoSetupInstaller.exe (PID: 6700)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6920)
Reads the computer name
- InnoSetupInstaller.exe (PID: 6700)
- RegAsm.exe (PID: 7872)
Checks supported languages
- InnoSetupInstaller.exe (PID: 6700)
- EEV7NMEX.exe (PID: 7288)
- RegAsm.exe (PID: 7872)
Checks current location (POWERSHELL)
- powershell.exe (PID: 3444)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3444)
Reads the machine GUID from the registry
- InnoSetupInstaller.exe (PID: 6700)
Reads Environment values
- InnoSetupInstaller.exe (PID: 6700)
Disables trace logs
- InnoSetupInstaller.exe (PID: 6700)
Checks proxy server information
- InnoSetupInstaller.exe (PID: 6700)
- RegAsm.exe (PID: 7872)
Reads the software policy settings
- InnoSetupInstaller.exe (PID: 6700)
Creates files or folders in the user directory
- InnoSetupInstaller.exe (PID: 6700)
The executable file from the user directory is run by the Powershell process
- EEV7NMEX.exe (PID: 7288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
167
Monitored processes
24
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 844 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4920 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 5140 -prefMapHandle 5196 -prefsLen 34713 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {53e5cc9e-db8e-4180-9366-c46bc350dc4b} 1456 "\\.\pipe\gecko-crash-server-pipe.1456" 273fa62f910 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4548 -childID 2 -isForBrowser -prefsHandle 3512 -prefMapHandle 3388 -prefsLen 36263 -prefMapSize 244343 -jsInitHandle 1308 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {1cf733eb-ad0e-4465-9951-4ef1efdfed2e} 1456 "\\.\pipe\gecko-crash-server-pipe.1456" 273f89a2d90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
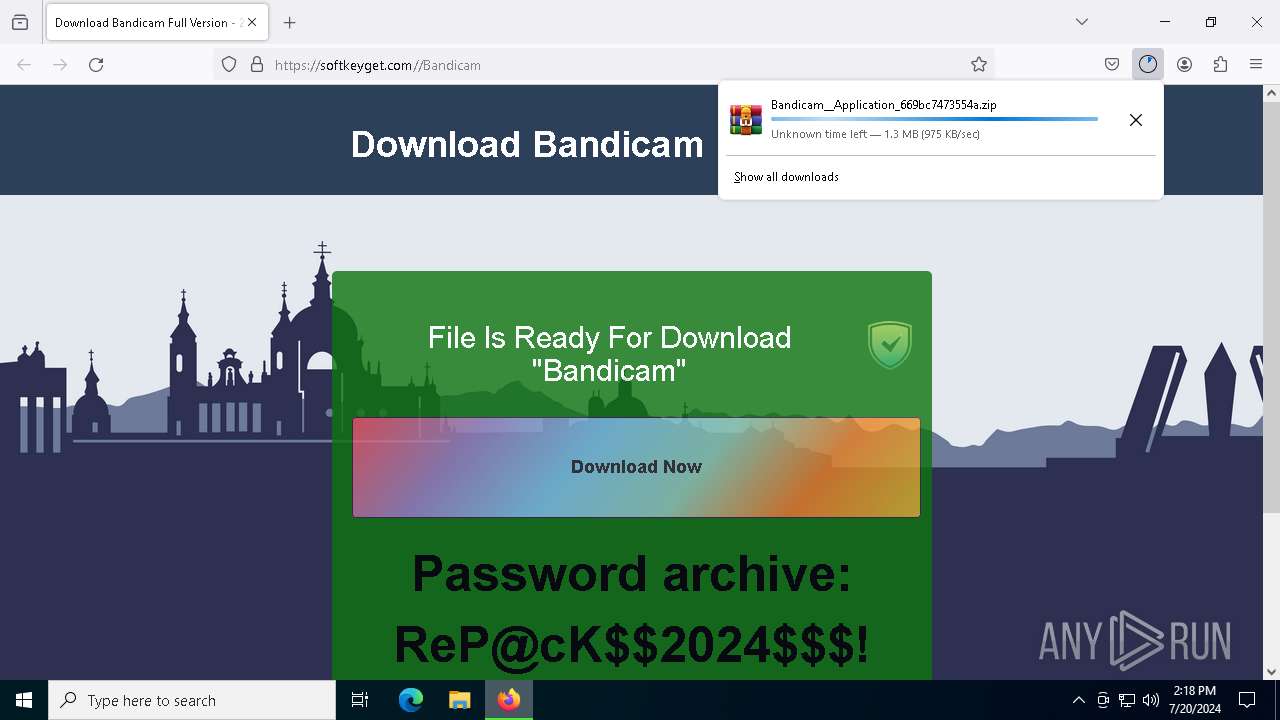
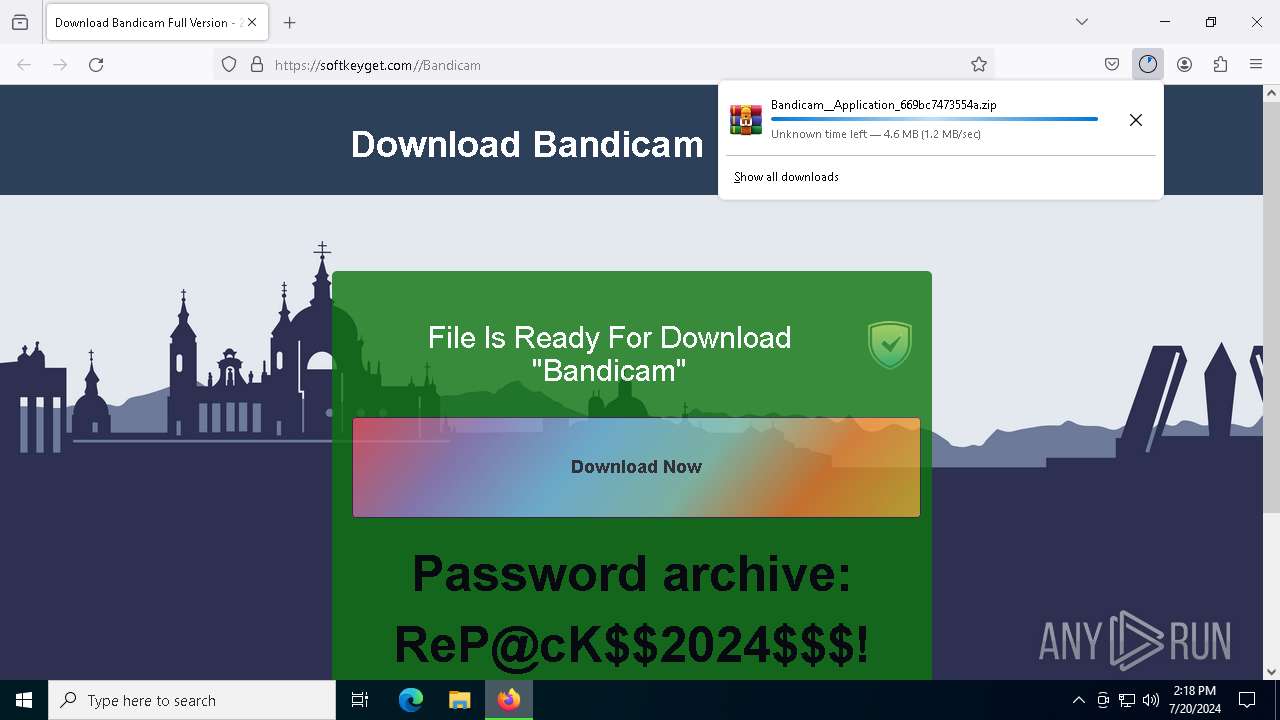
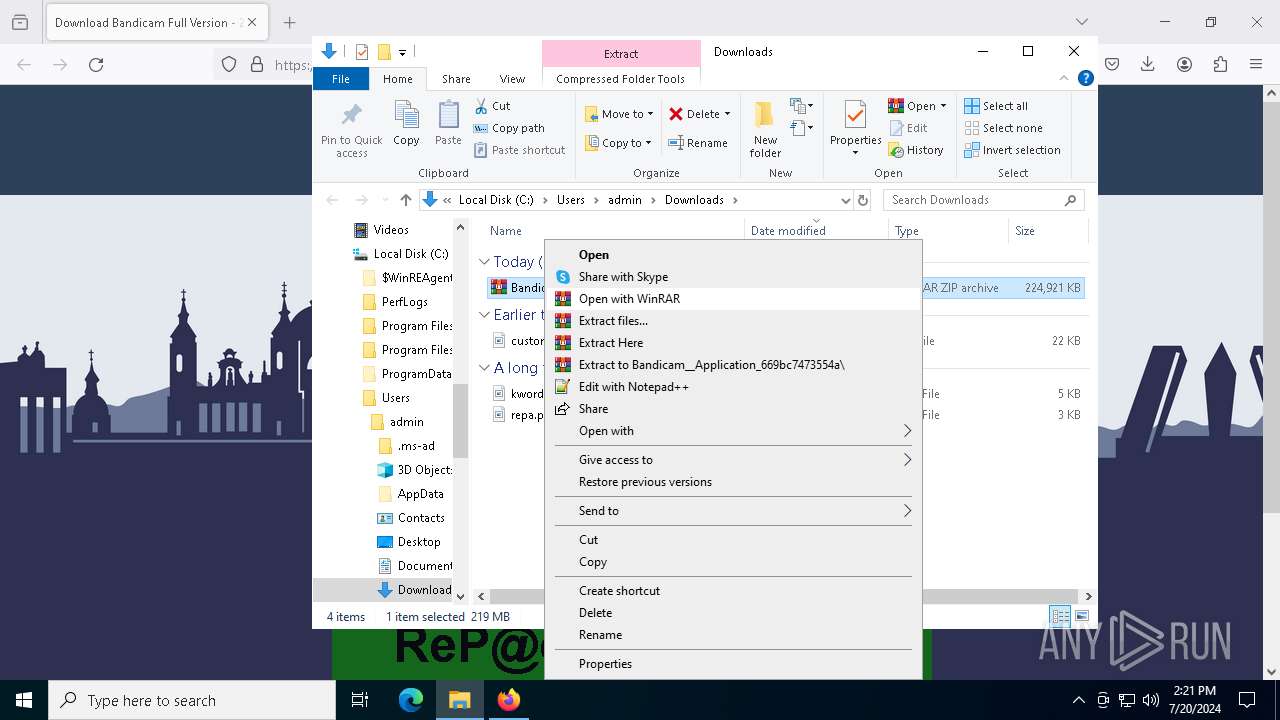
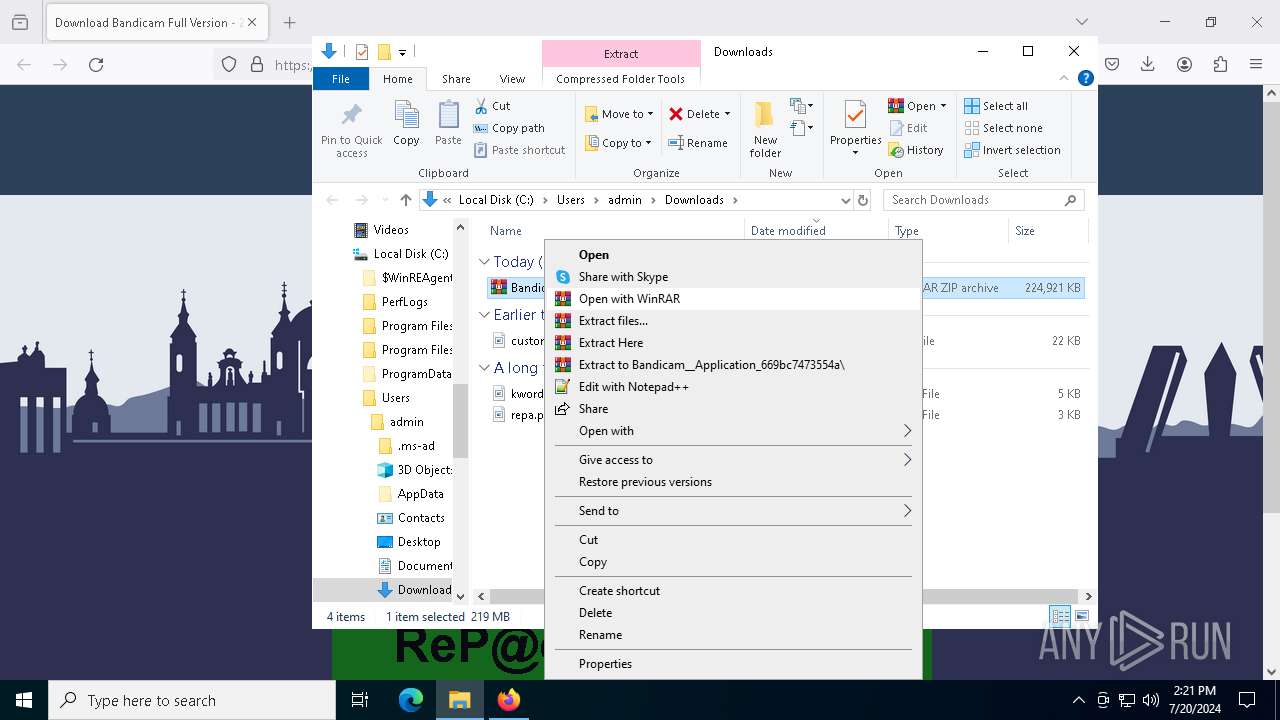
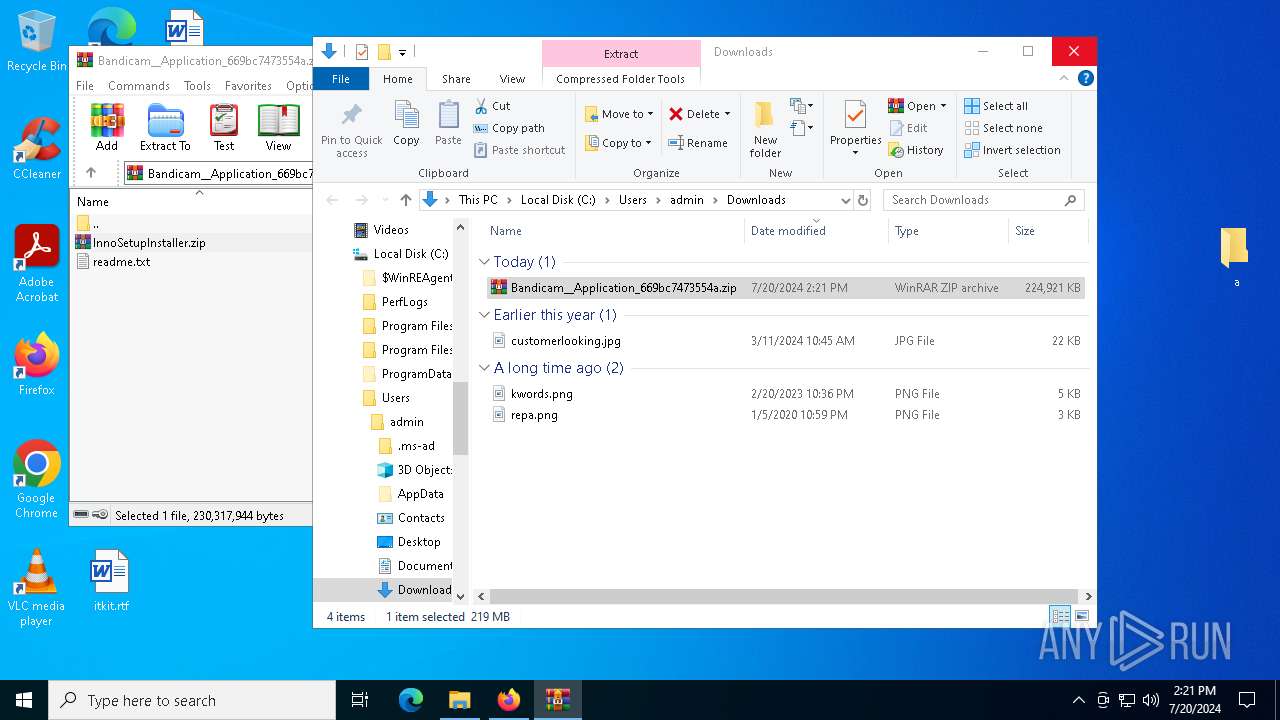
| 1320 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Bandicam__Application_669bc7473554a.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://softkeyget.com//Bandicam | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://softkeyget.com//Bandicam" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3384 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | EEV7NMEX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 3444 | "powershell.exe" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | InnoSetupInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4732 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5464 -childID 4 -isForBrowser -prefsHandle 5552 -prefMapHandle 5460 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1308 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {99b08026-0bef-4ad8-b57d-40ce2c15b66c} 1456 "\\.\pipe\gecko-crash-server-pipe.1456" 273f4af8310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5124 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5528 -childID 6 -isForBrowser -prefsHandle 5680 -prefMapHandle 5676 -prefsLen 34713 -prefMapSize 244343 -jsInitHandle 1308 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {44baa211-b80f-4be3-83bc-91e769cc8dec} 1456 "\\.\pipe\gecko-crash-server-pipe.1456" 273f4af8f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
41 928
Read events
41 798
Write events
129
Delete events
1
Modification events
| (PID) Process: | (2116) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: E3A0B6A303000000 | |||
| (PID) Process: | (1456) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 08F0B7A303000000 | |||
| (PID) Process: | (1456) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 0 | |||
| (PID) Process: | (1456) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 1 | |||
| (PID) Process: | (1456) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Installer\308046B0AF4A39CB |
| Operation: | delete value | Name: | installer.taskbarpin.win10.enabled |
Value: | |||
| (PID) Process: | (1456) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (1456) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (1456) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Theme |
Value: 1 | |||
| (PID) Process: | (1456) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (1456) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
Executable files
114
Suspicious files
198
Text files
107
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1456 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 1456 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 1456 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 1456 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1456 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1456 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1456 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1456 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1456 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | sqlite | |
MD5:B6171020B6B4E4BBC18E5F9DF442859C | SHA256:BC7AE98155D9F632302C308D11A77D85C1B5136506DFD1CABE2BCCC5CAE522E7 | |||
| 1456 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
99
DNS requests
129
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1456 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
1456 | firefox.exe | POST | 200 | 184.24.77.75:80 | http://r3.o.lencr.org/ | unknown | — | — | unknown |
1456 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
1456 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
1456 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
1456 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
1456 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
1456 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
1456 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
1456 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4716 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5620 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 4.209.32.198:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
8108 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2760 | svchost.exe | 40.115.3.253:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1456 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
1456 | firefox.exe | 172.67.182.131:443 | softkeyget.com | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
softkeyget.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2168 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
7872 | RegAsm.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
7872 | RegAsm.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Stealc HTTP POST Request |
7872 | RegAsm.exe | Malware Command and Control Activity Detected | ET MALWARE [SEKOIA.IO] Win32/Stealc C2 Check-in |