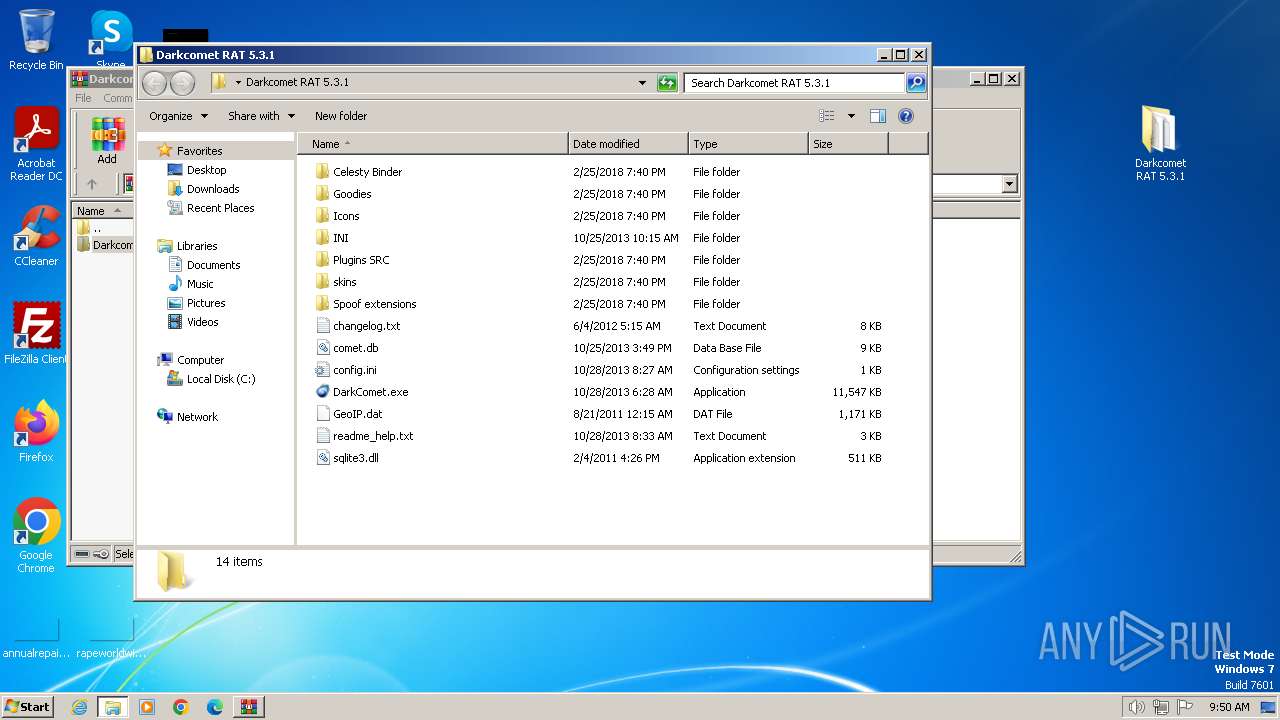
| File name: | Darkcomet RAT 5.3.1.zip |
| Full analysis: | https://app.any.run/tasks/a8b191d7-127f-4885-a24c-f20600650fce |
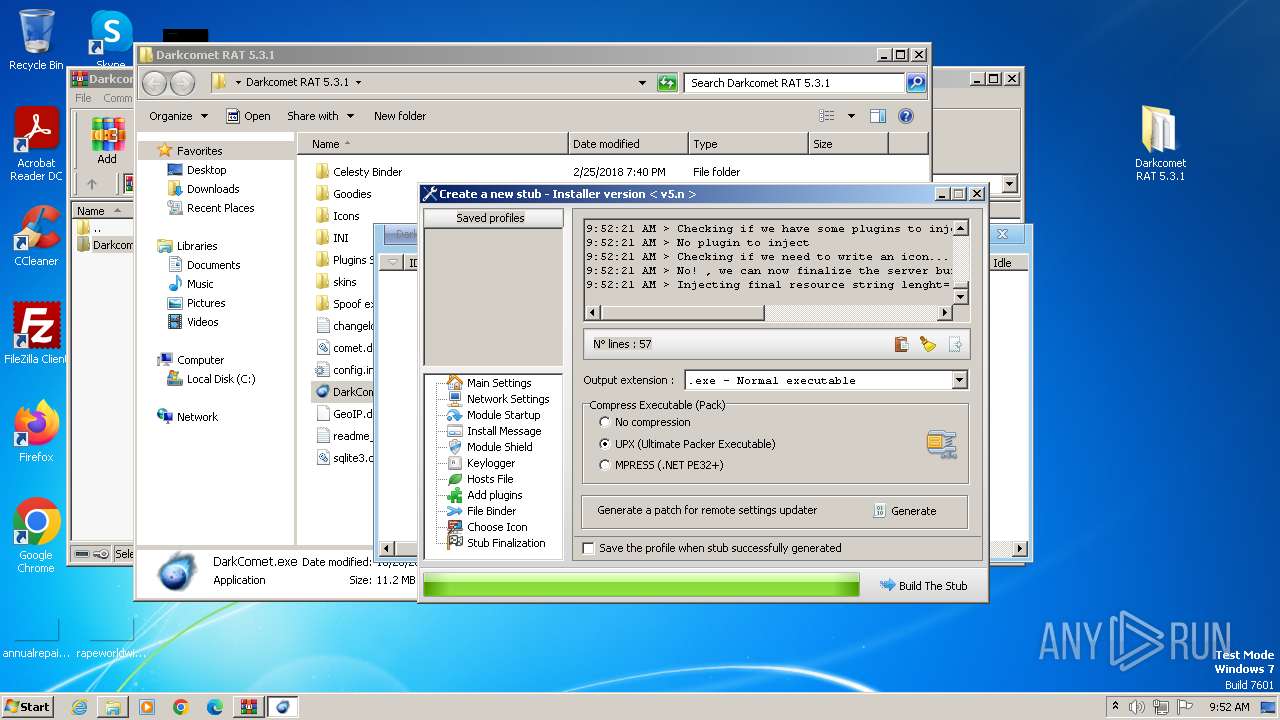
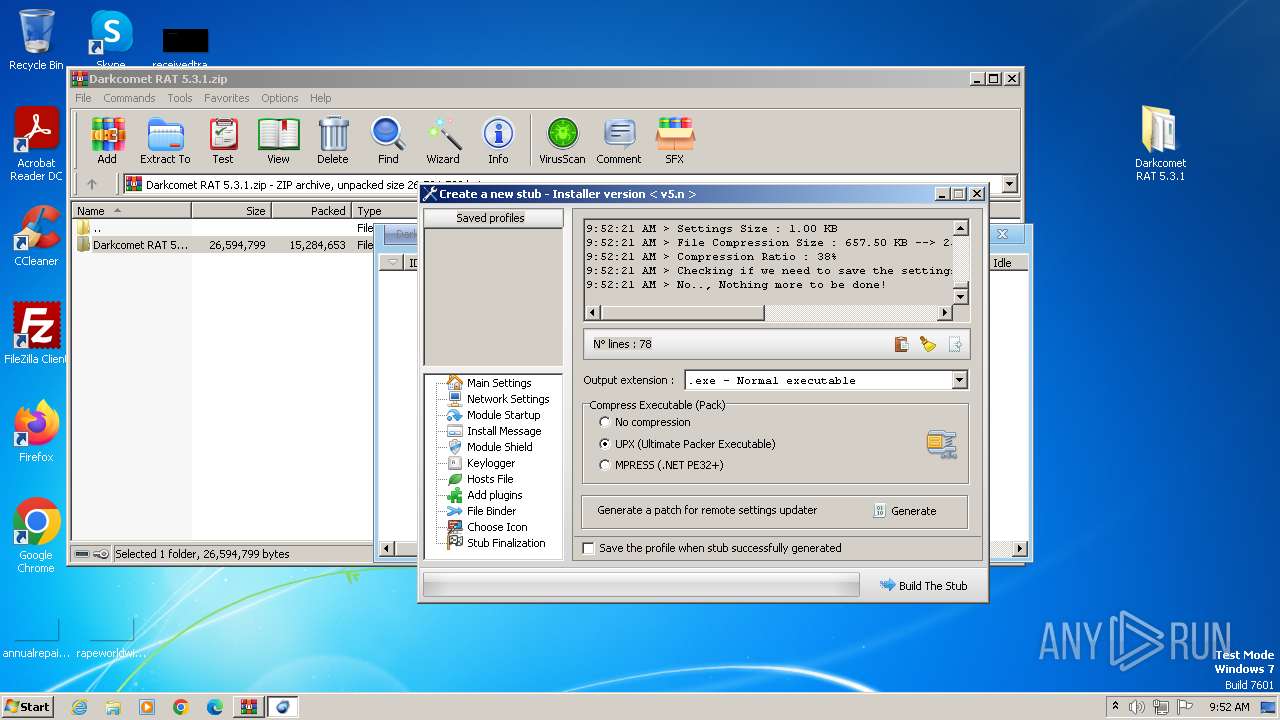
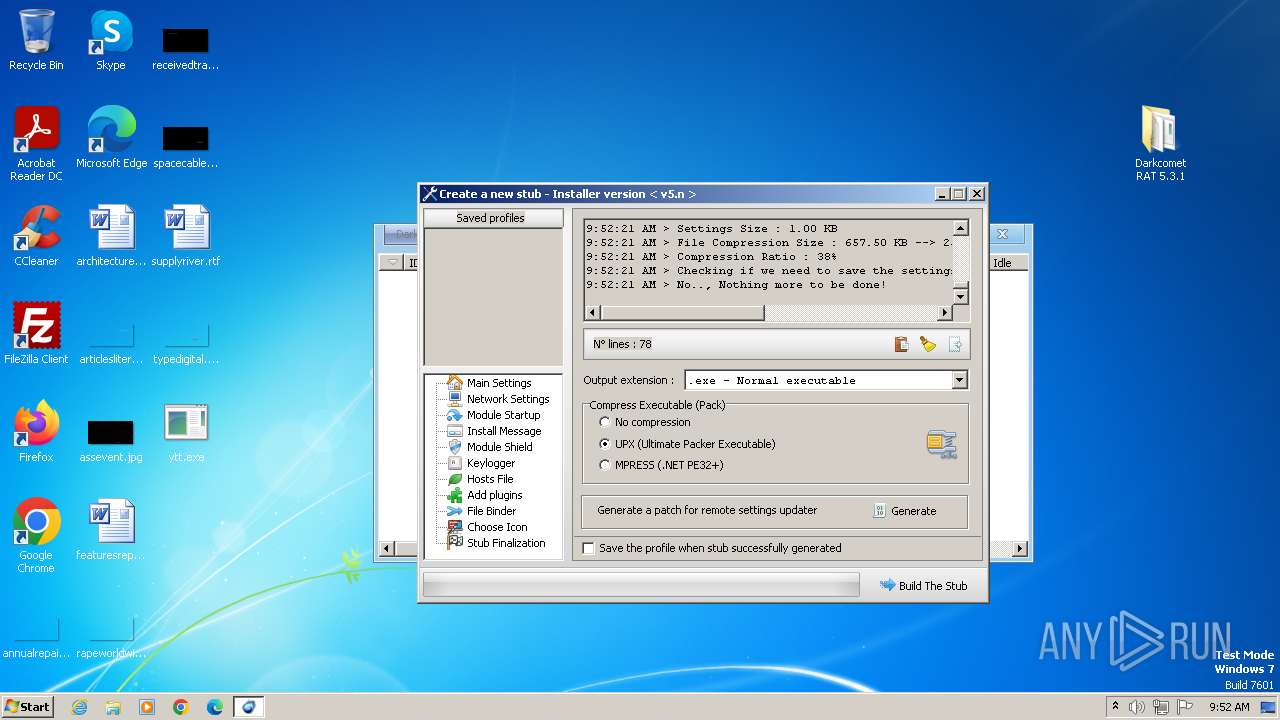
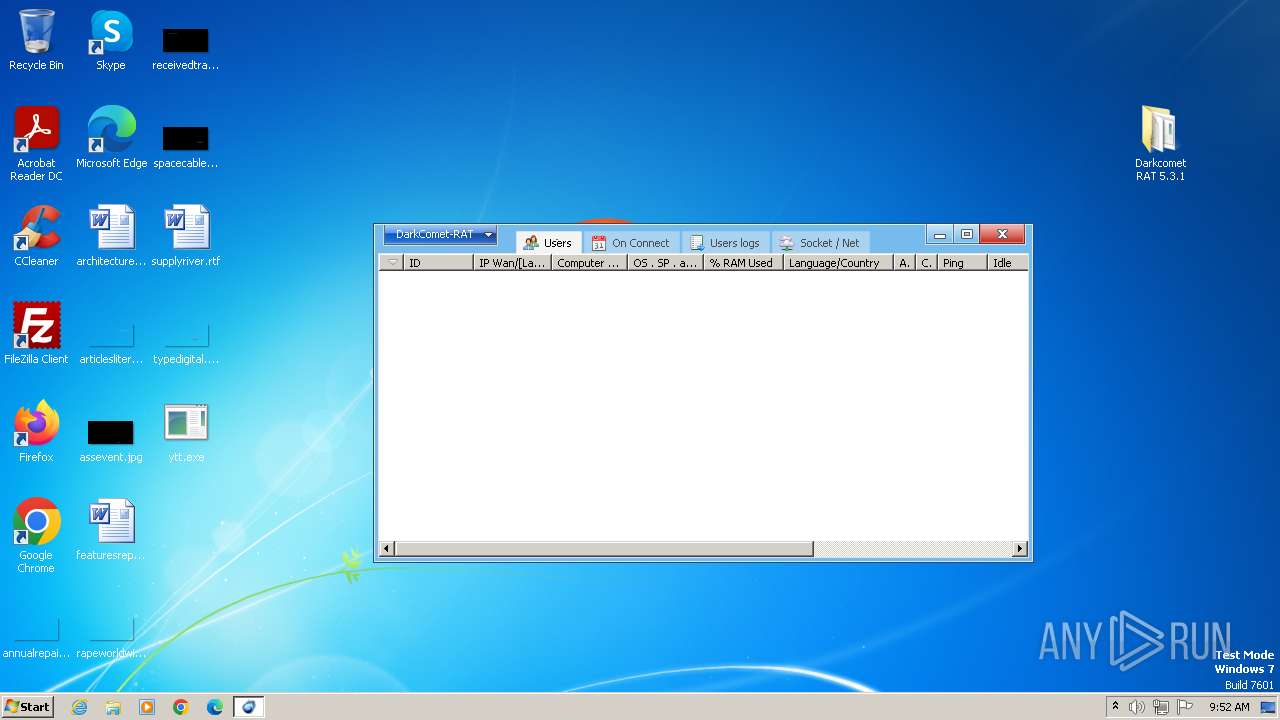
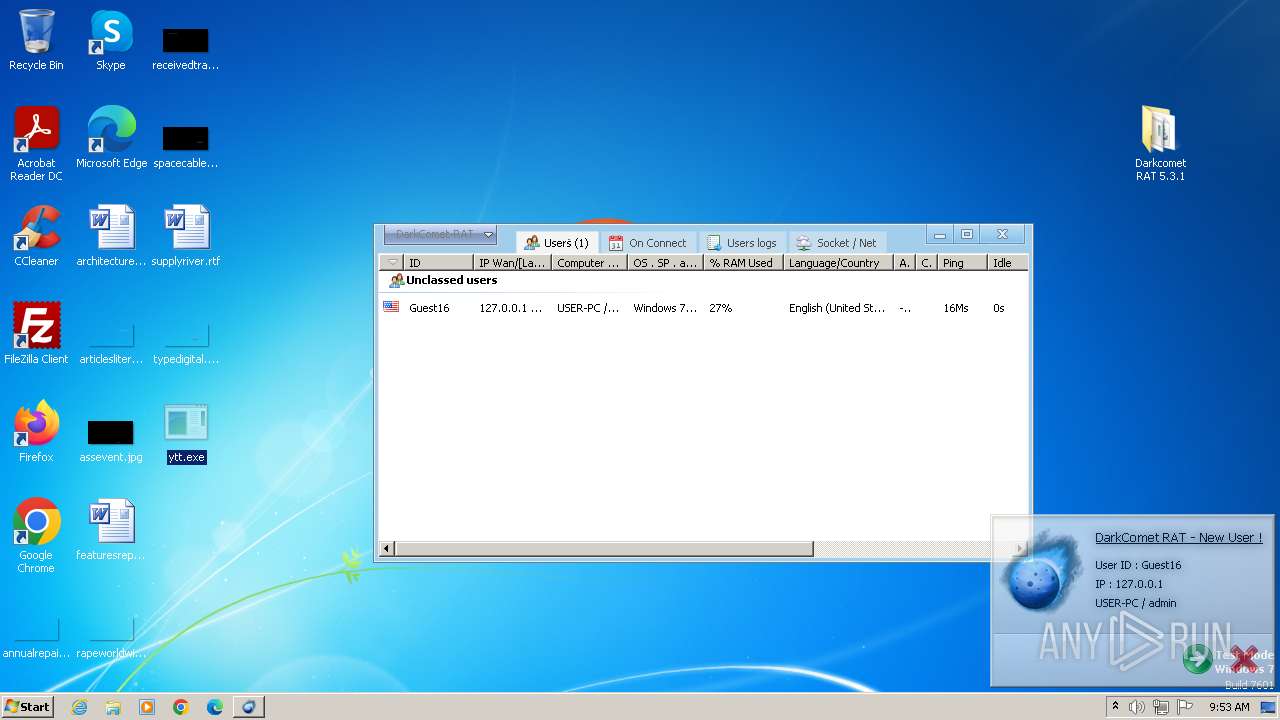
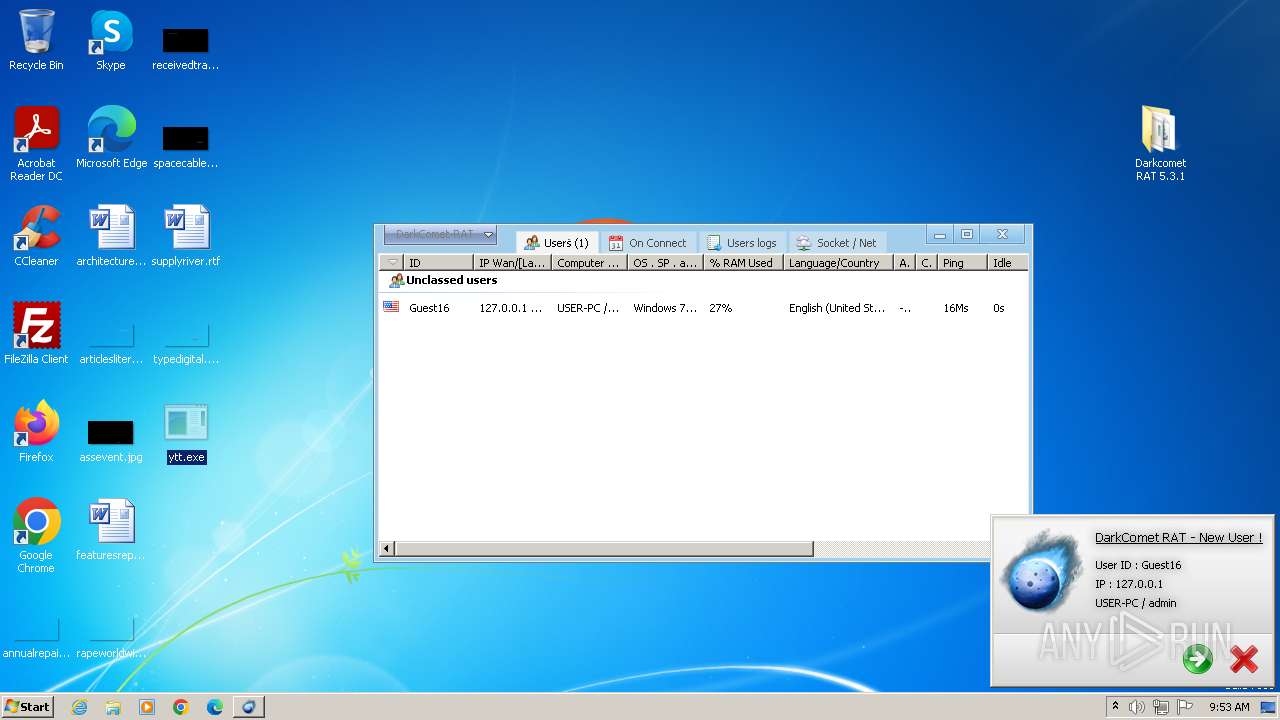
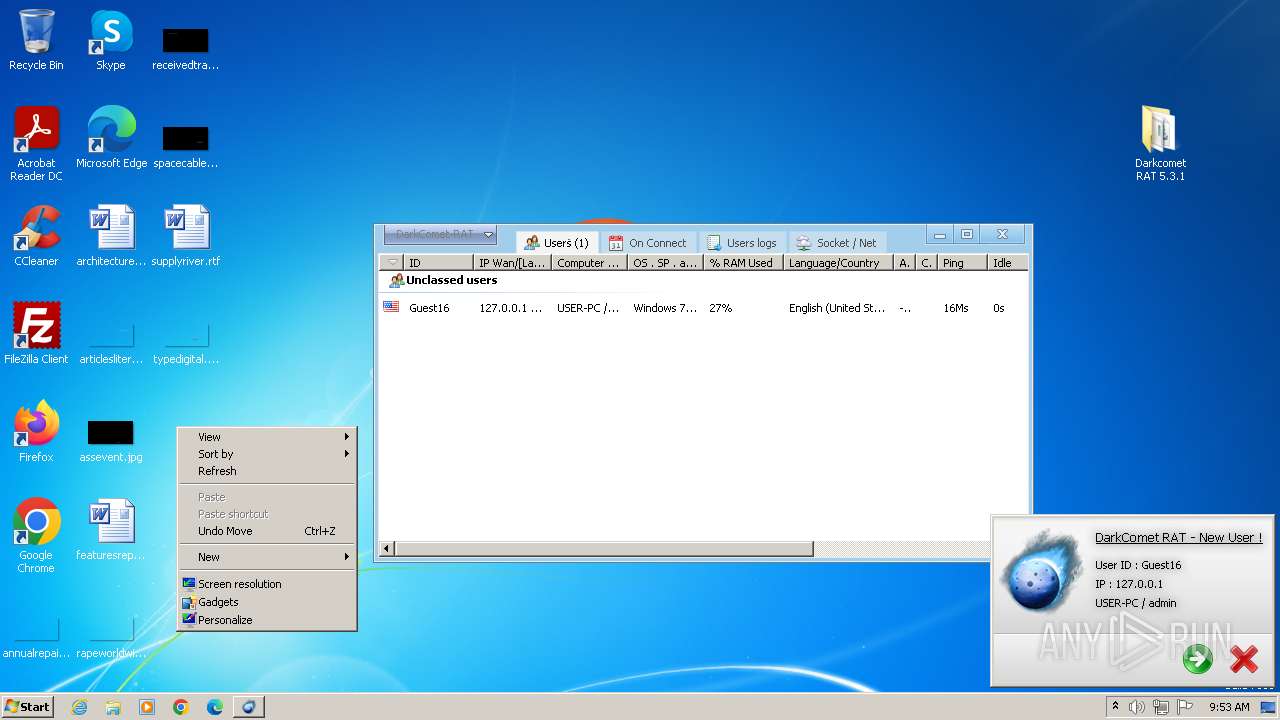
| Verdict: | Malicious activity |
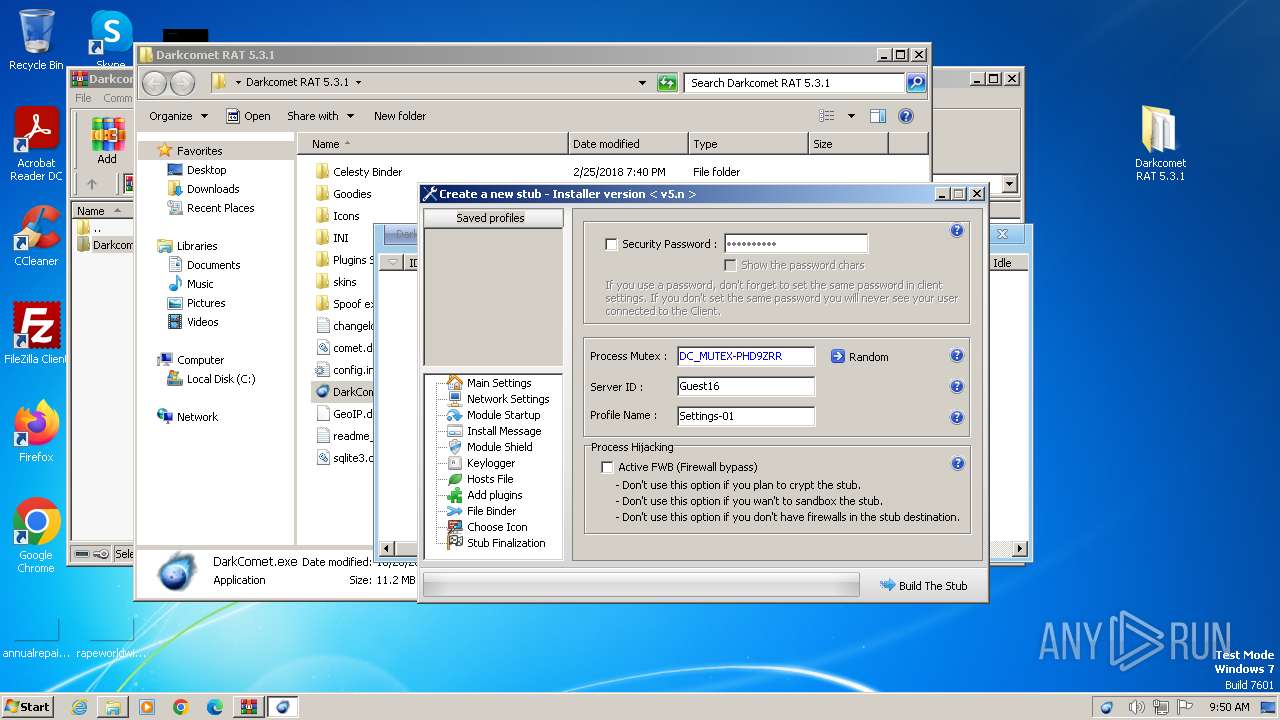
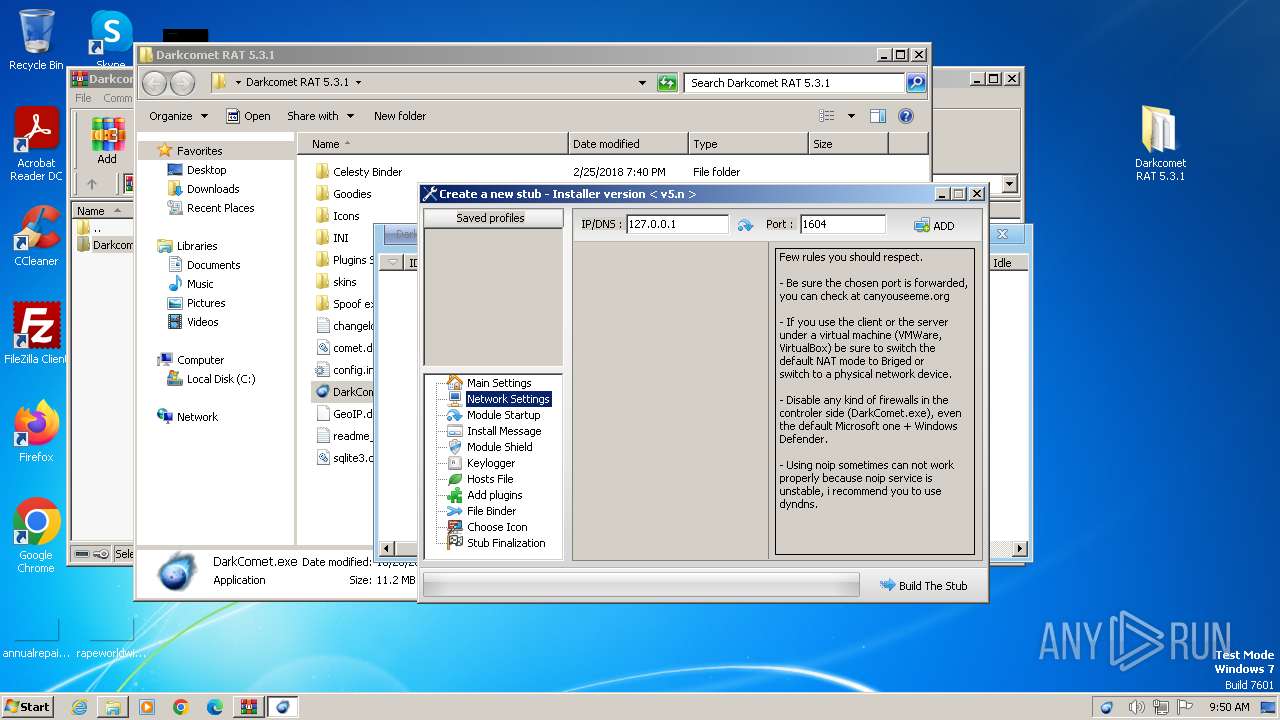
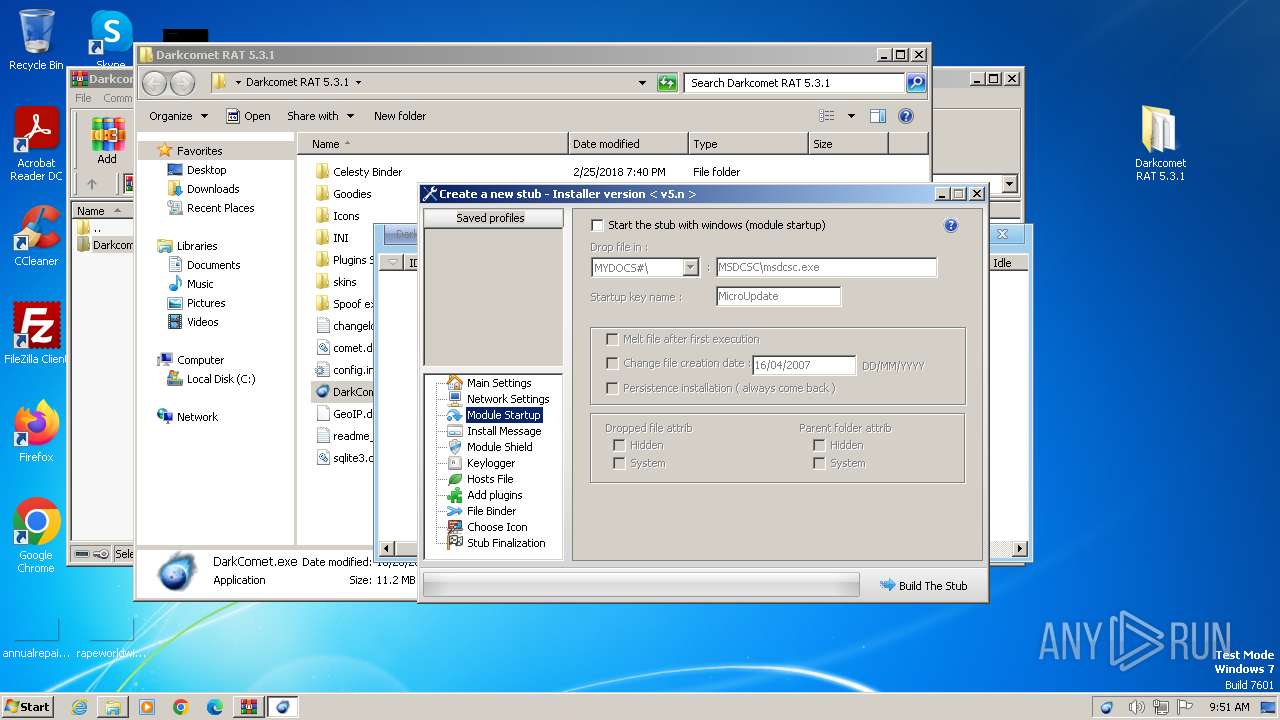
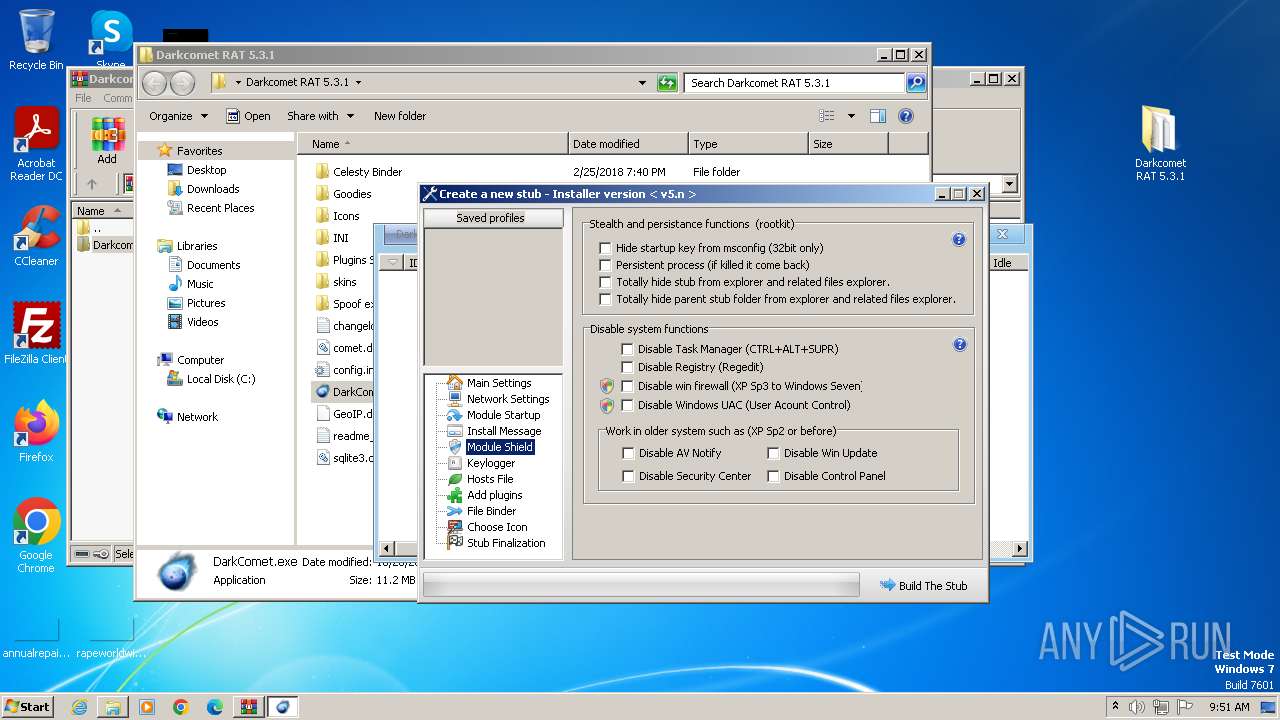
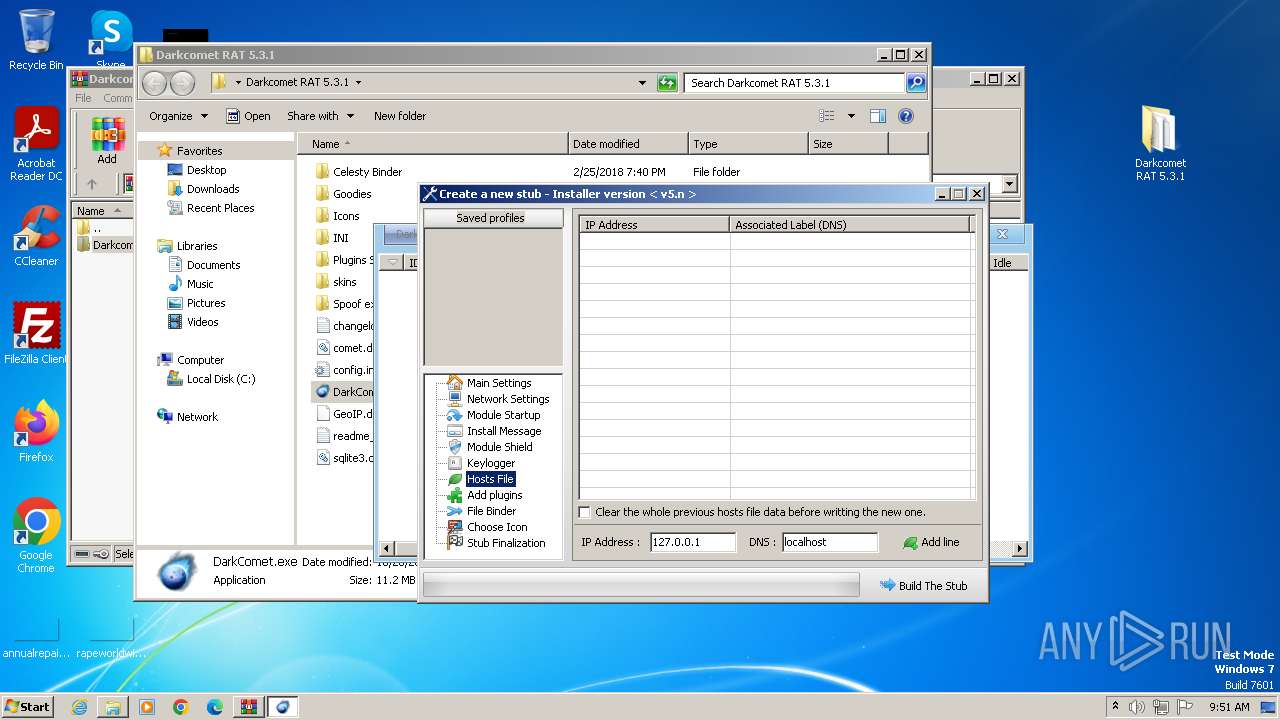
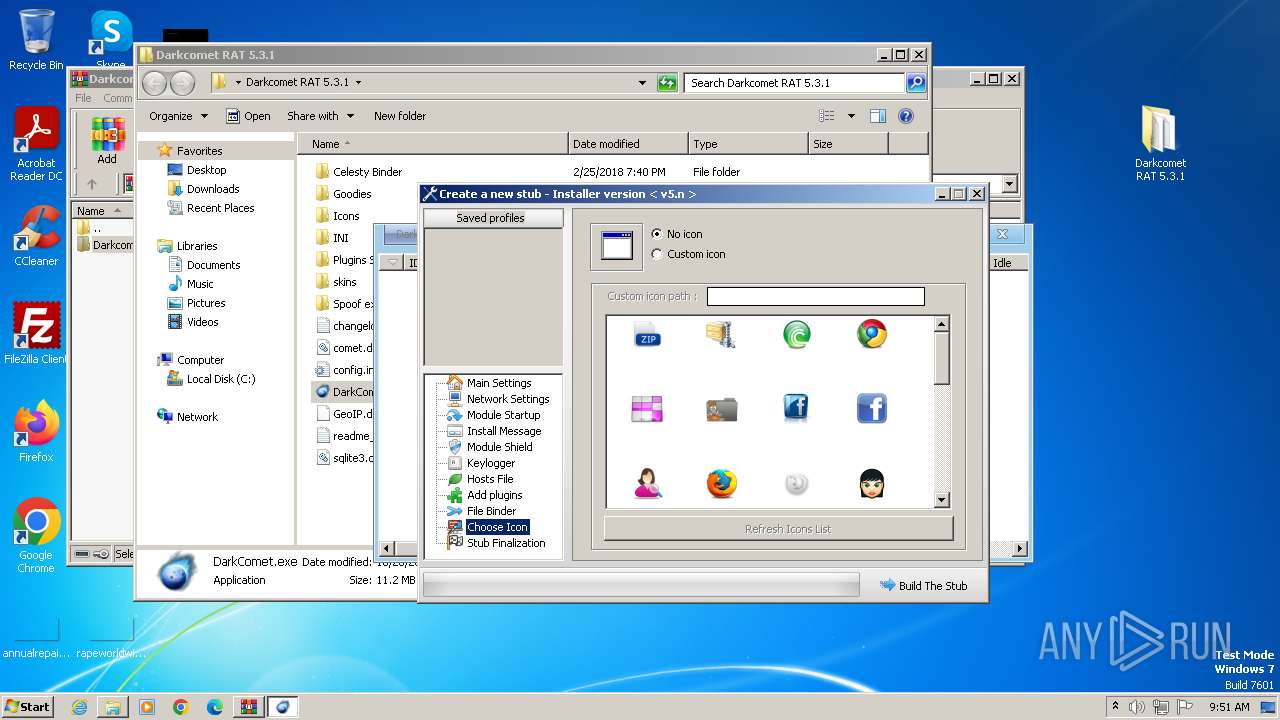
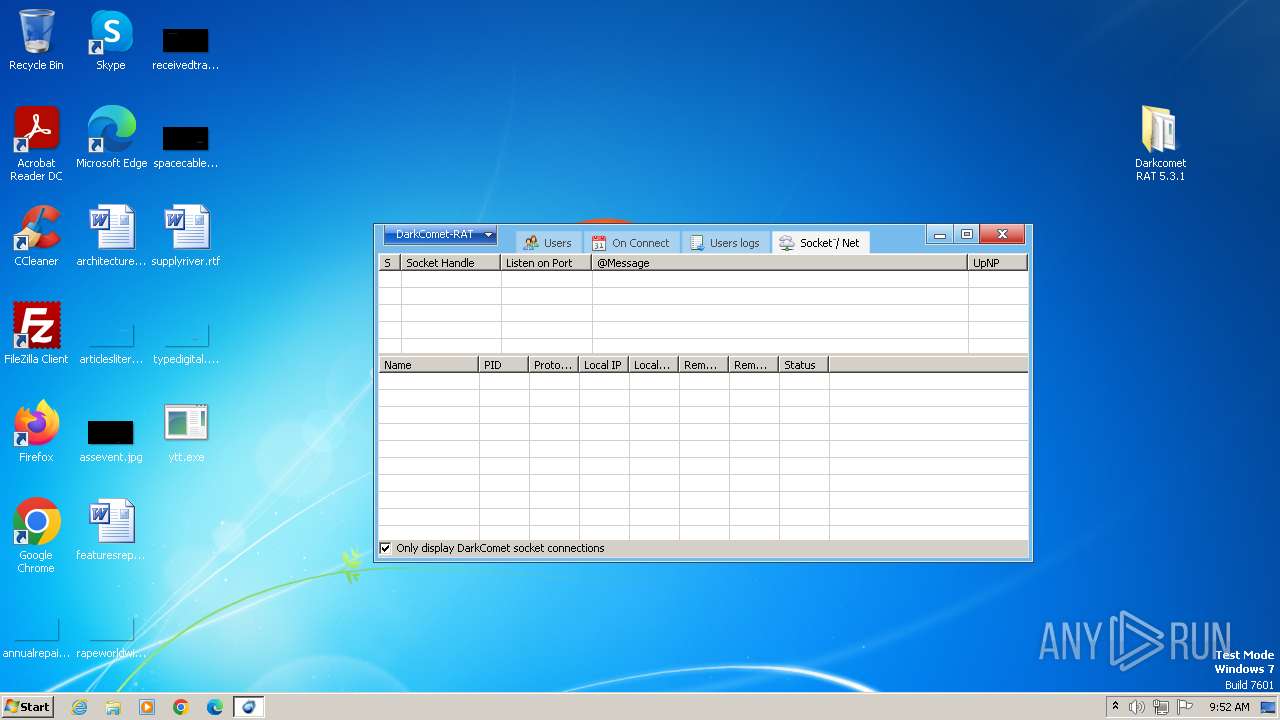
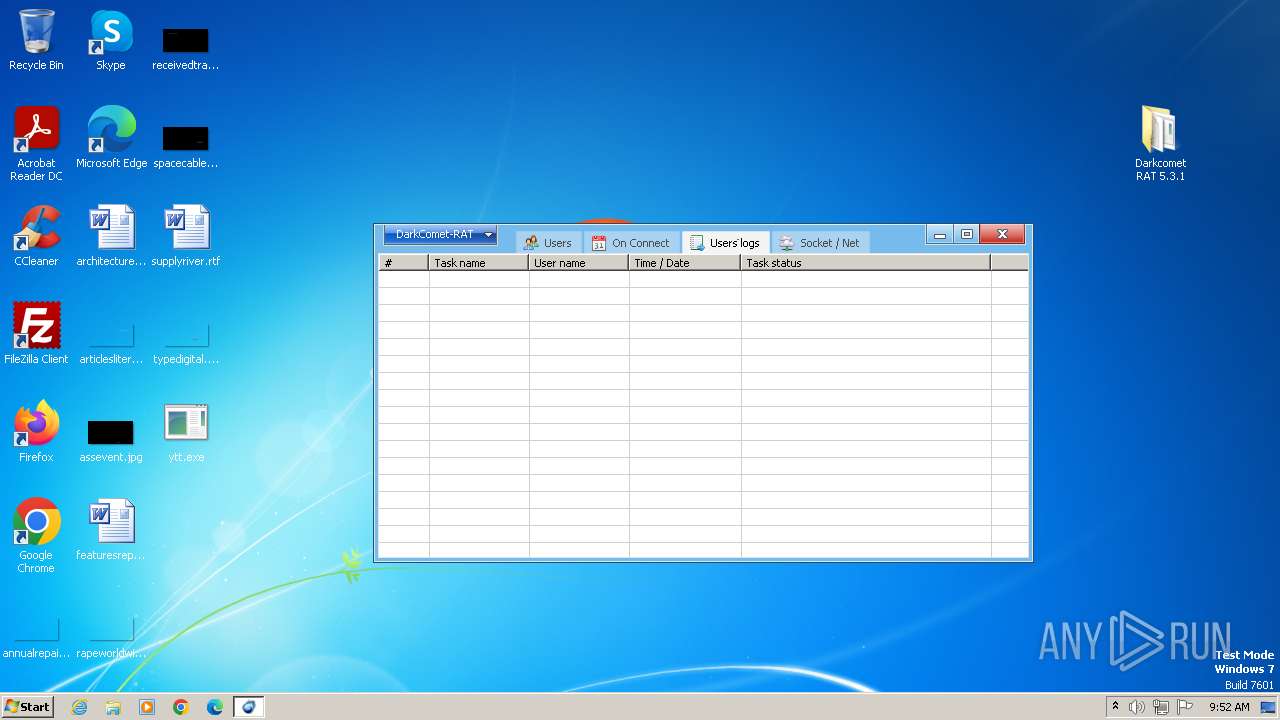
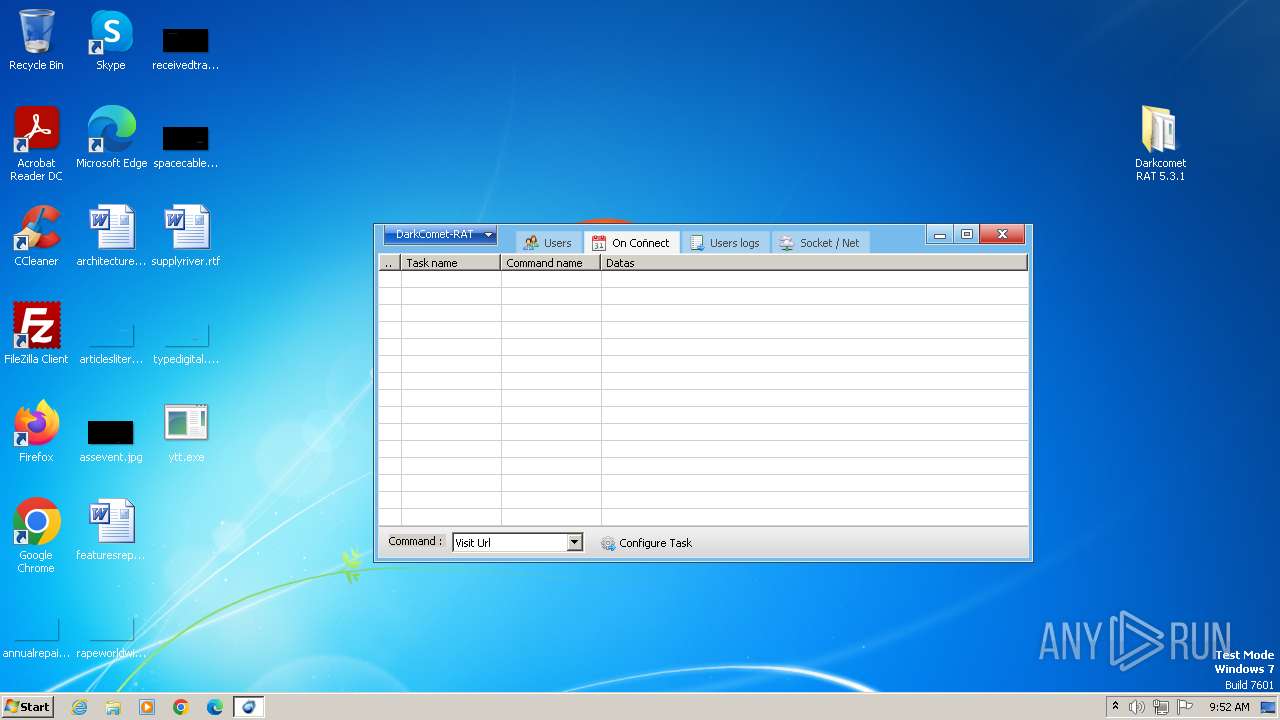
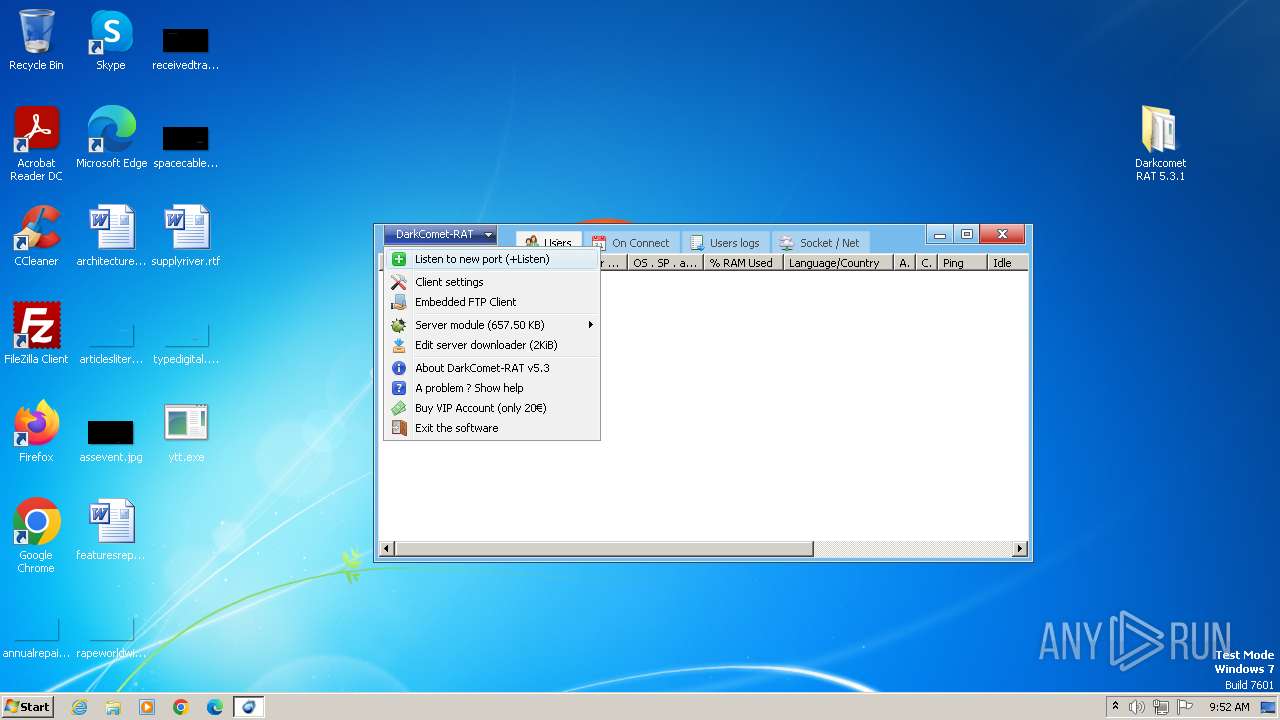
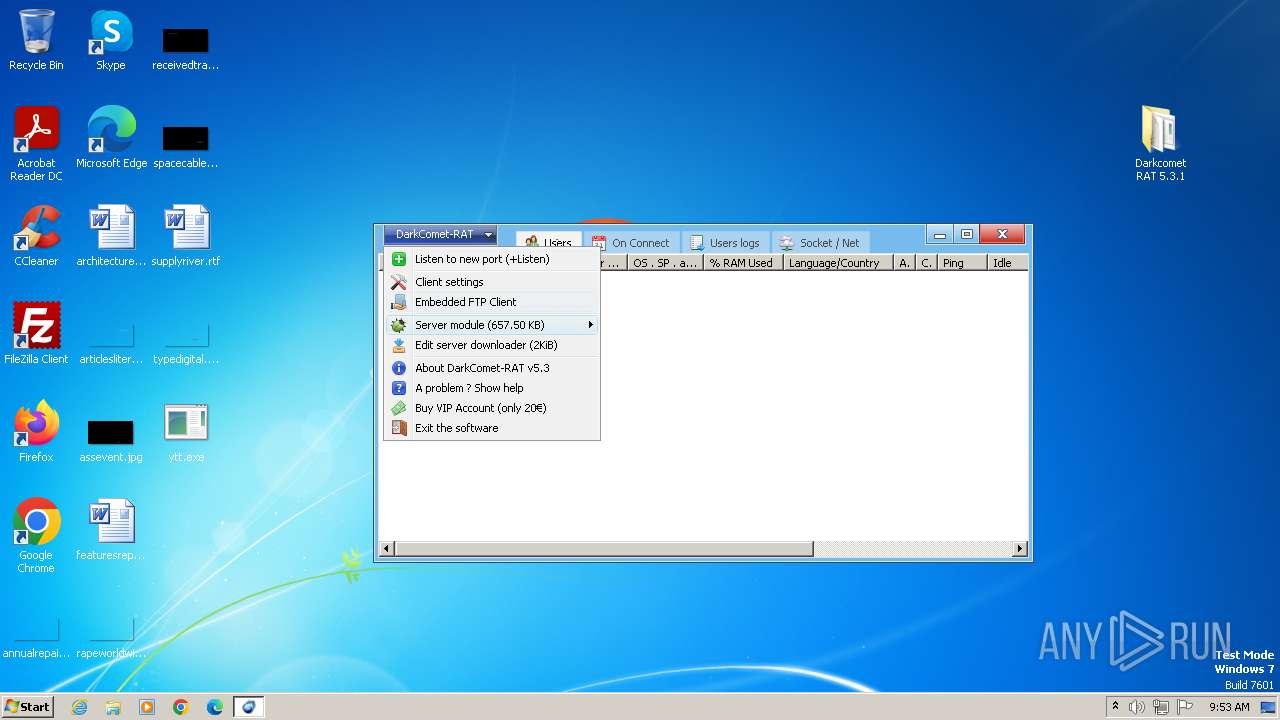
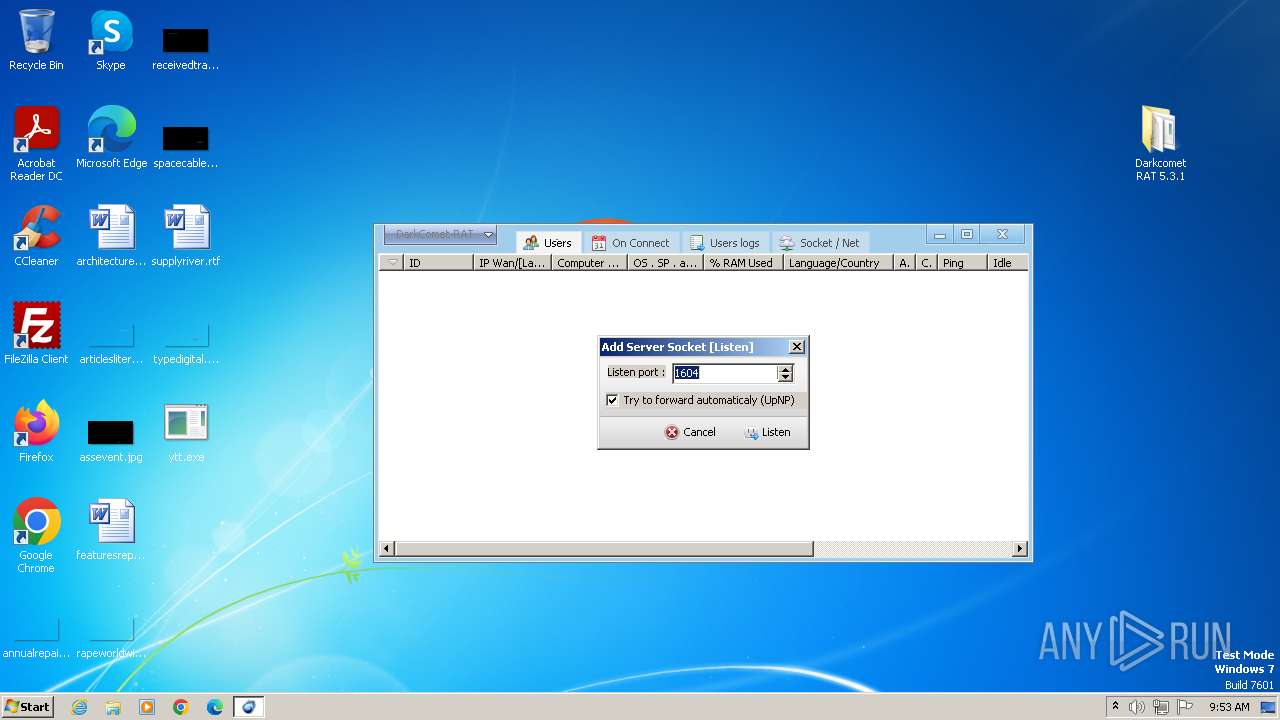
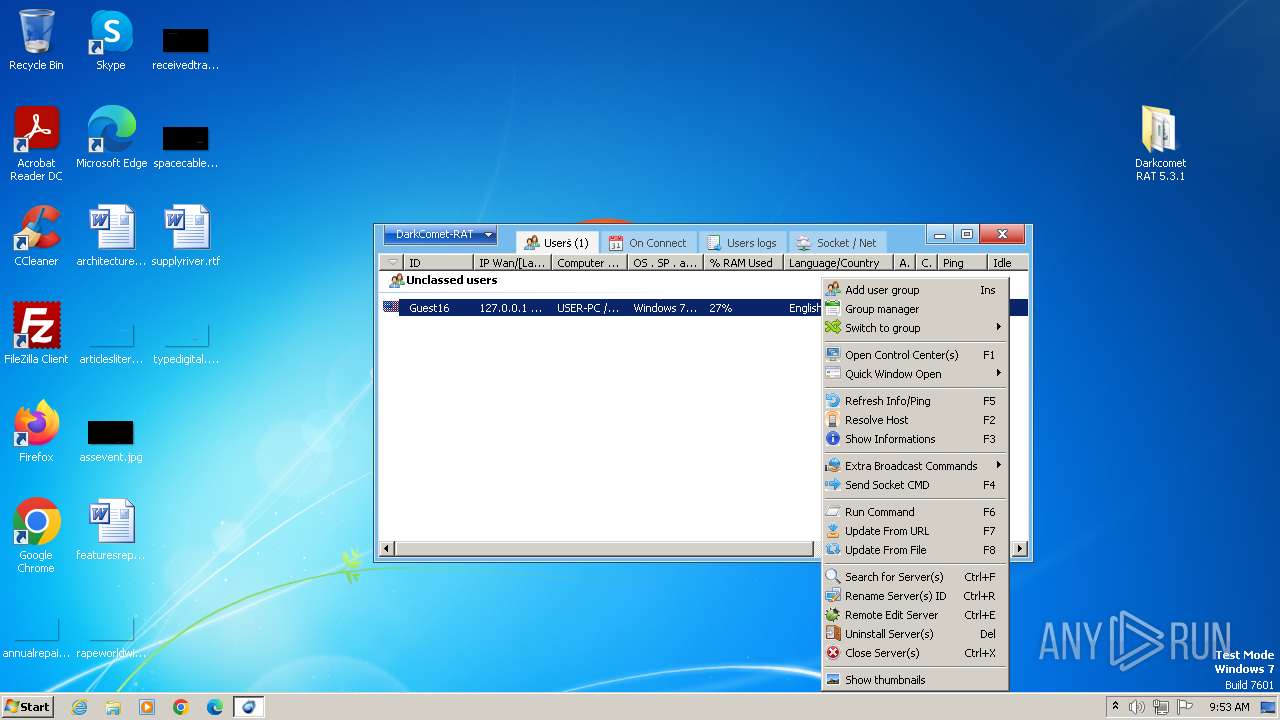
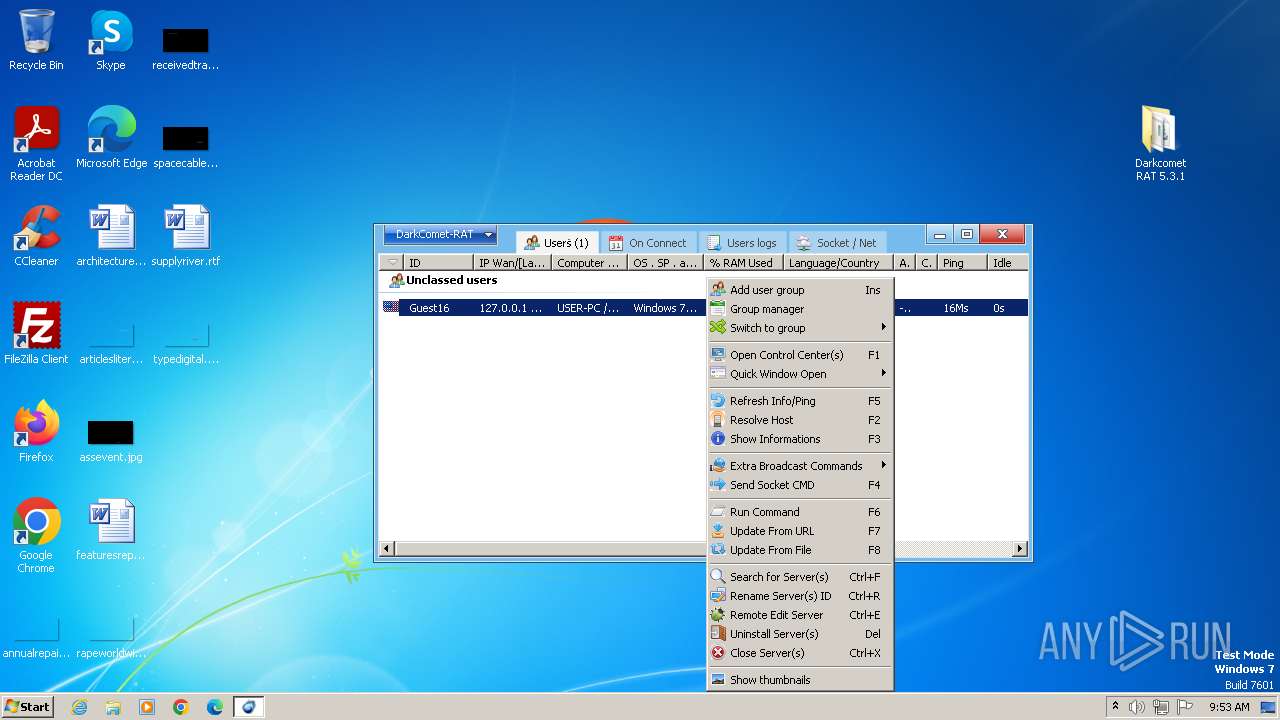
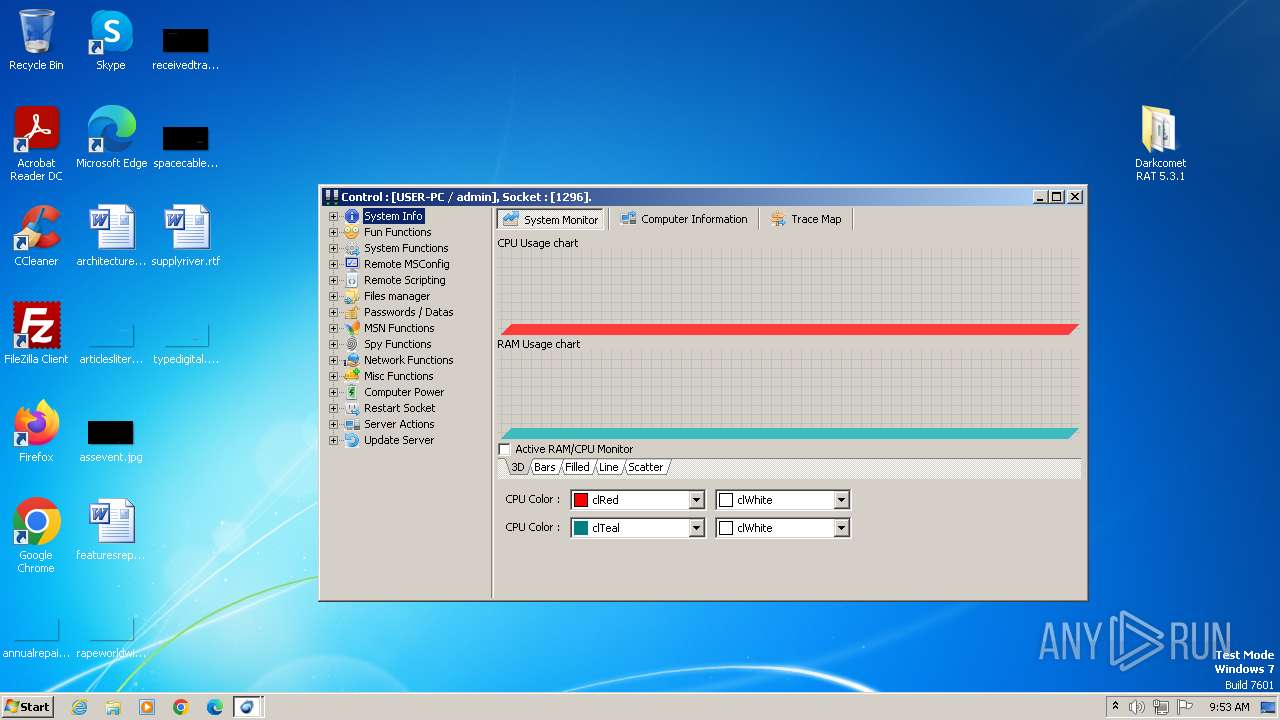
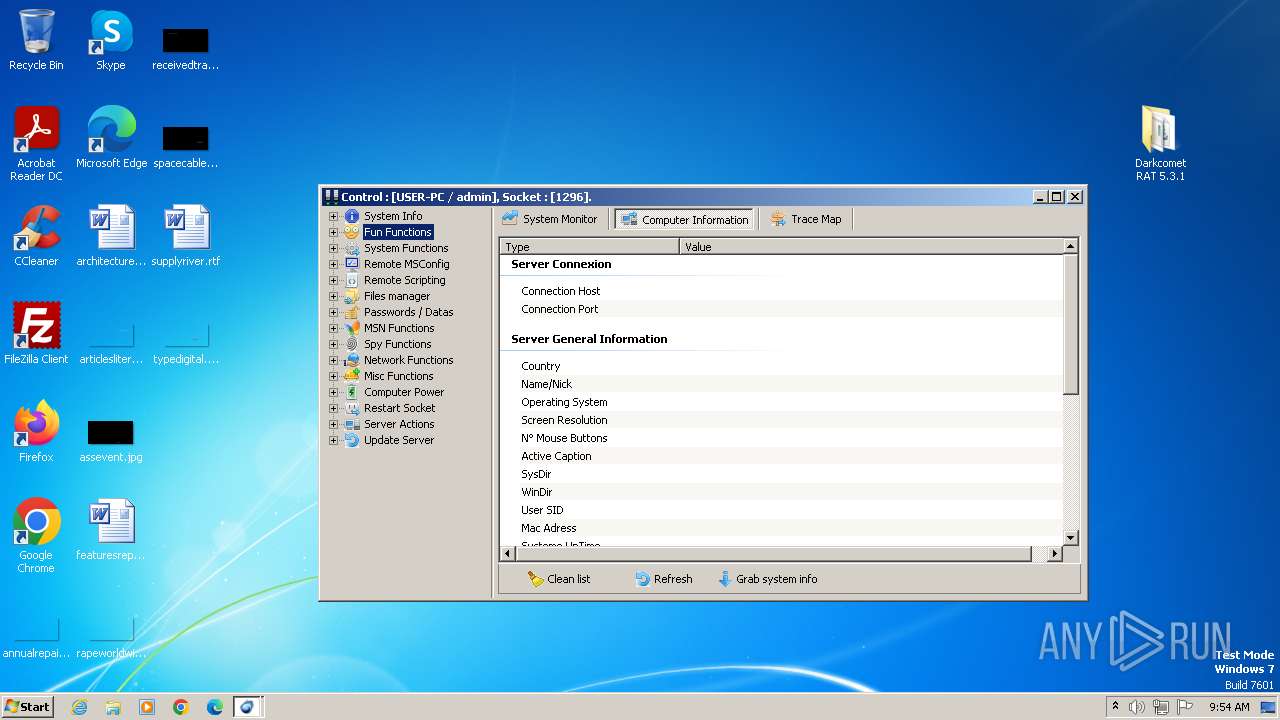
| Threats: | DarkComet RAT is a malicious program designed to remotely control or administer a victim's computer, steal private data and spy on the victim. |
| Analysis date: | June 21, 2024, 08:49:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 9F9347ECF2CC6541FB64ACD6FC0A5749 |
| SHA1: | 6C0D454EC2068D1C7D502A167CA02C8DAFD0B244 |
| SHA256: | BFE9A76229E6E502B7C542007CD976DD3B5E0D26190CDF7CC8A5E5AAB0A63F7D |
| SSDEEP: | 393216:Yia1rsEqp8mxBktqBEH3JM/qbxhbRLEJt5RXtW3hg:Yl1rsEqJxChH3coxhbePK3hg |
MALICIOUS
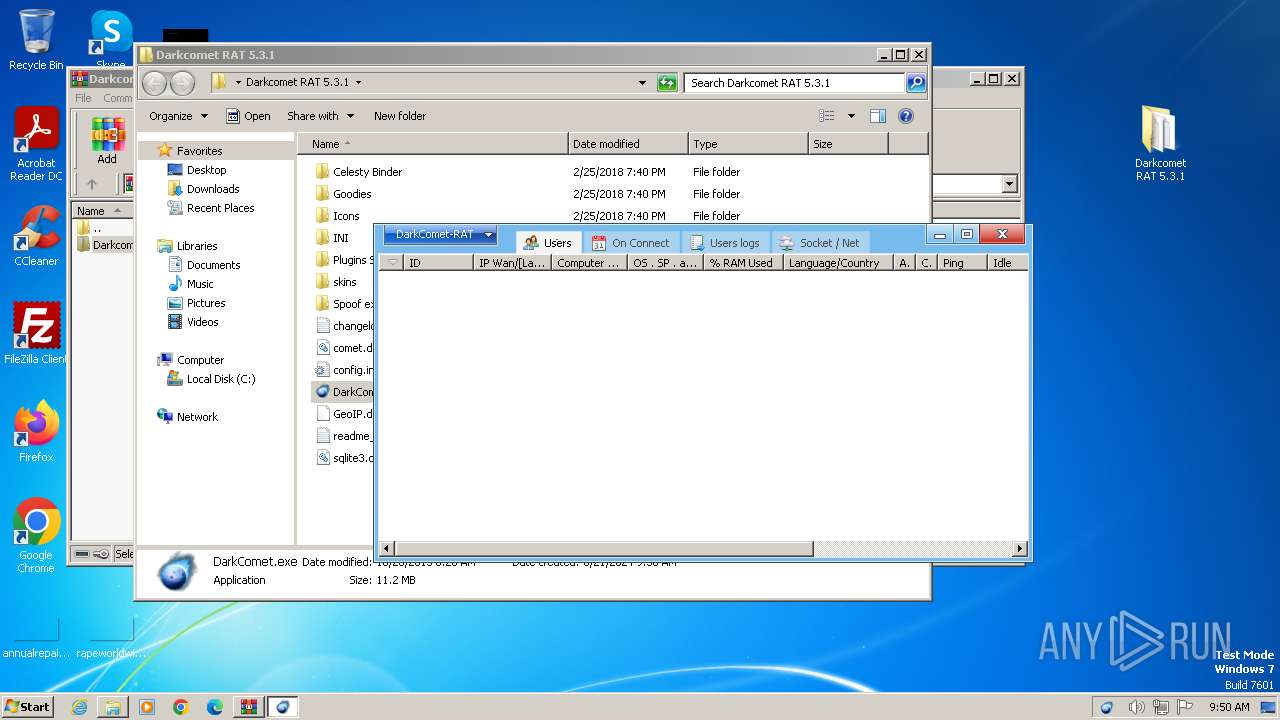
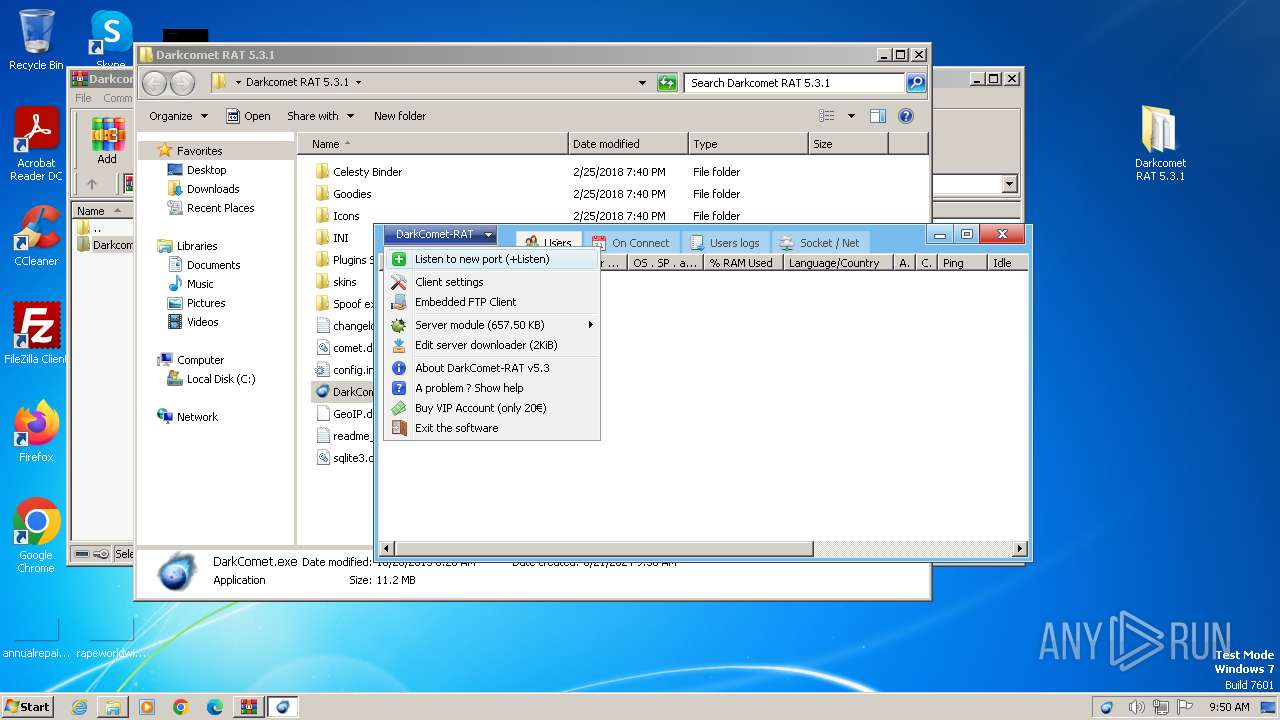
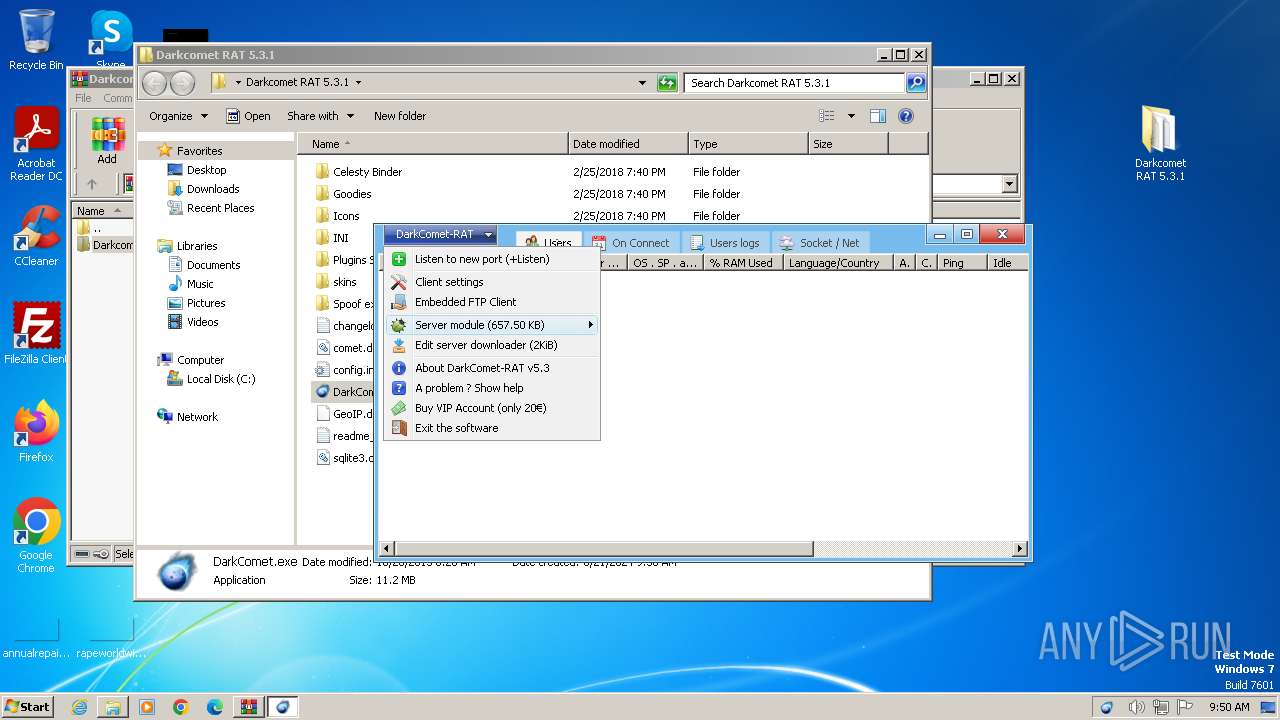
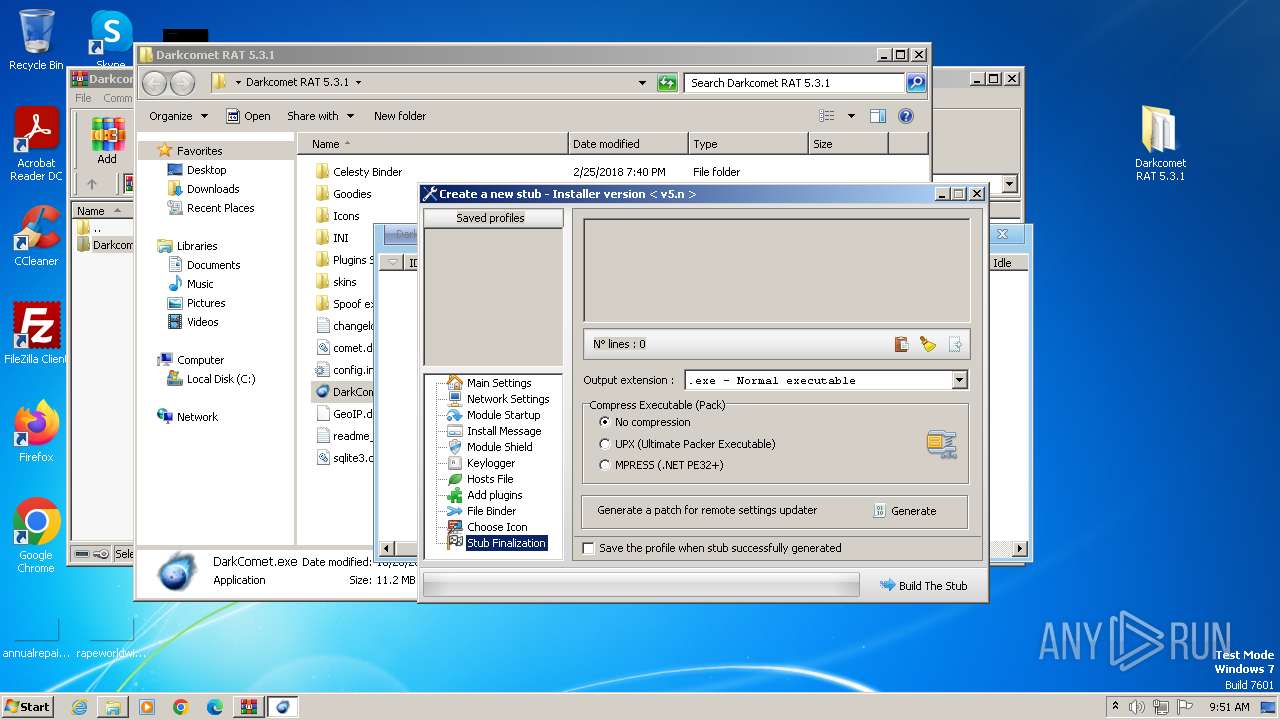
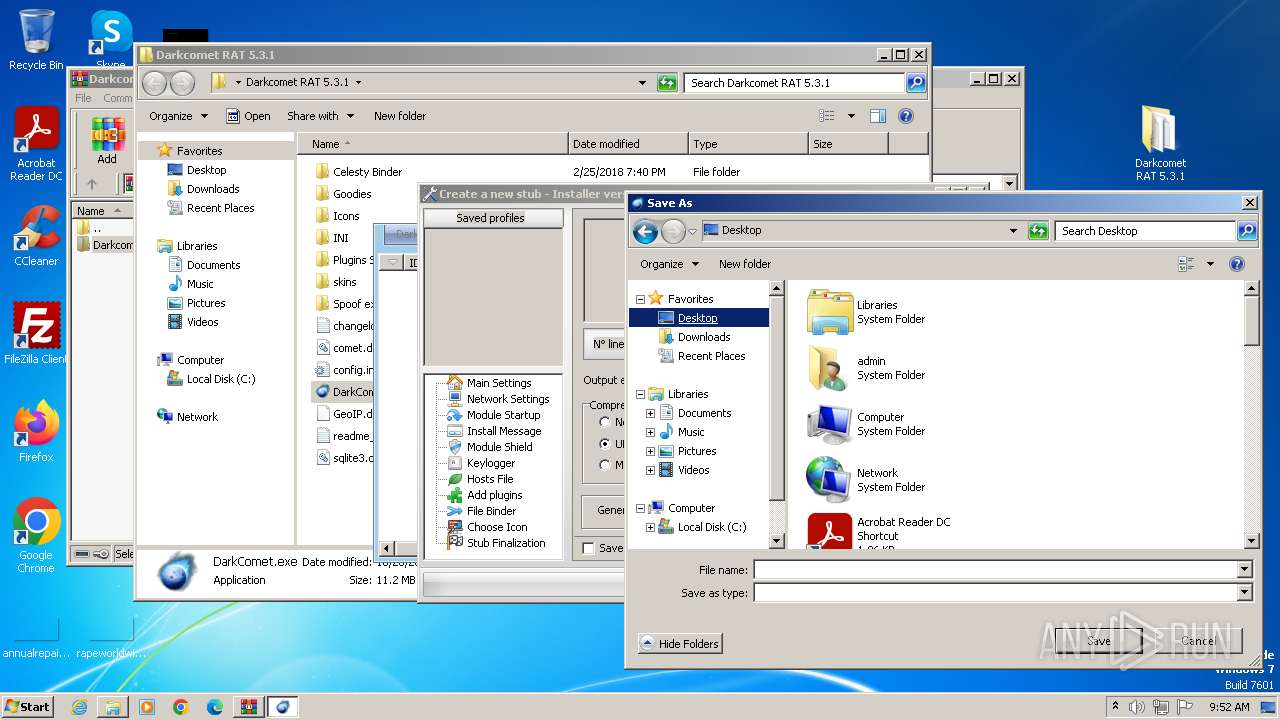
DARKCOMET has been detected (YARA)
- DarkComet.exe (PID: 3124)
- msdcsc.exe (PID: 3320)
Drops the executable file immediately after the start
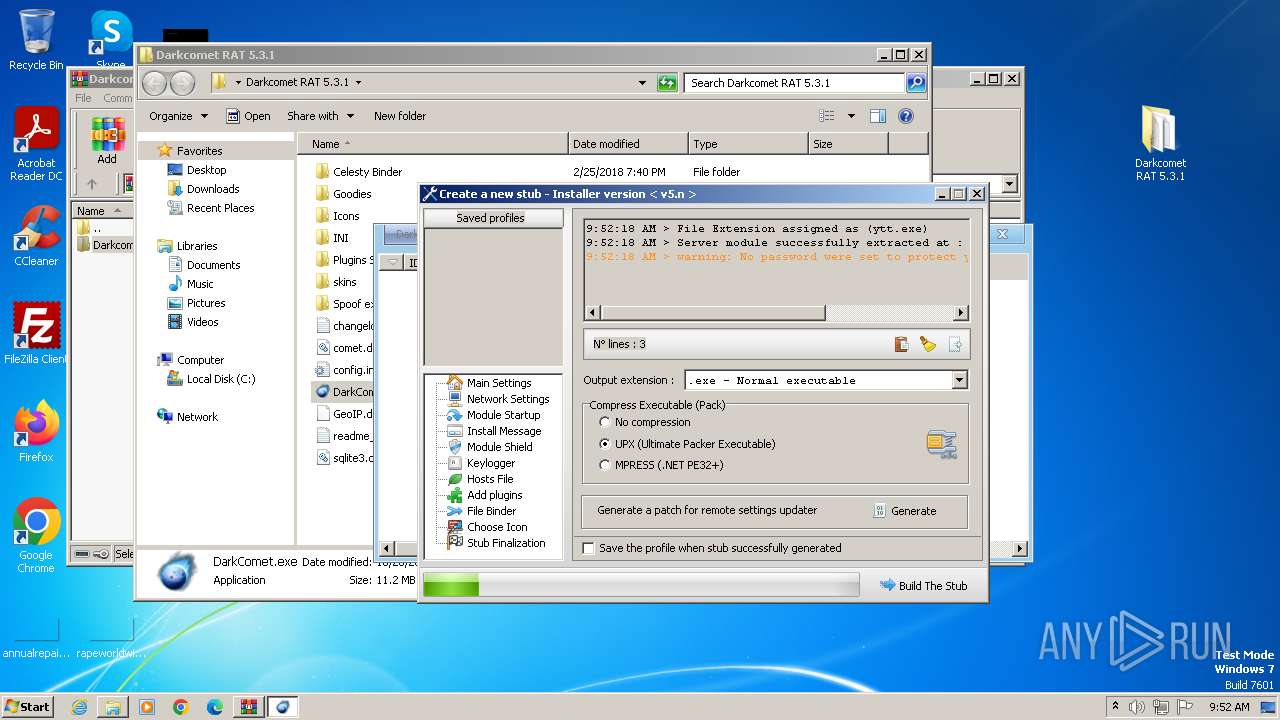
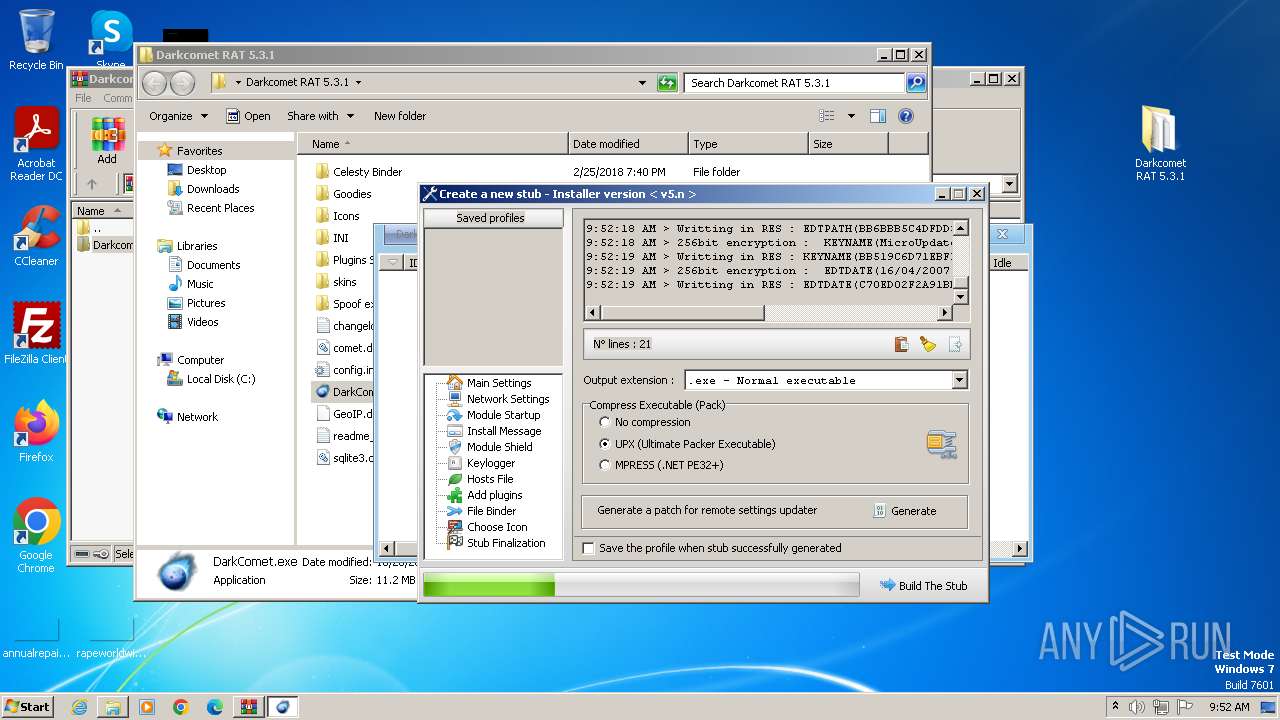
- UPX.exe (PID: 656)
- DarkComet.exe (PID: 3124)
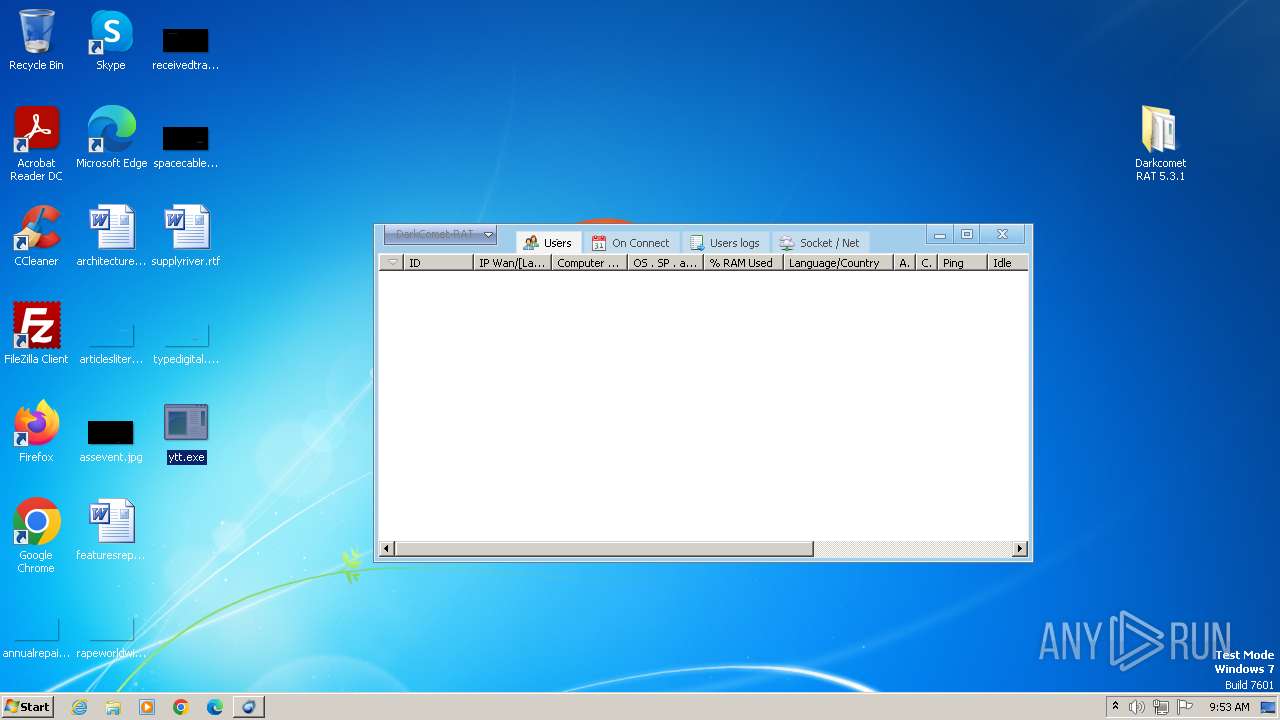
- ytt.exe (PID: 1828)
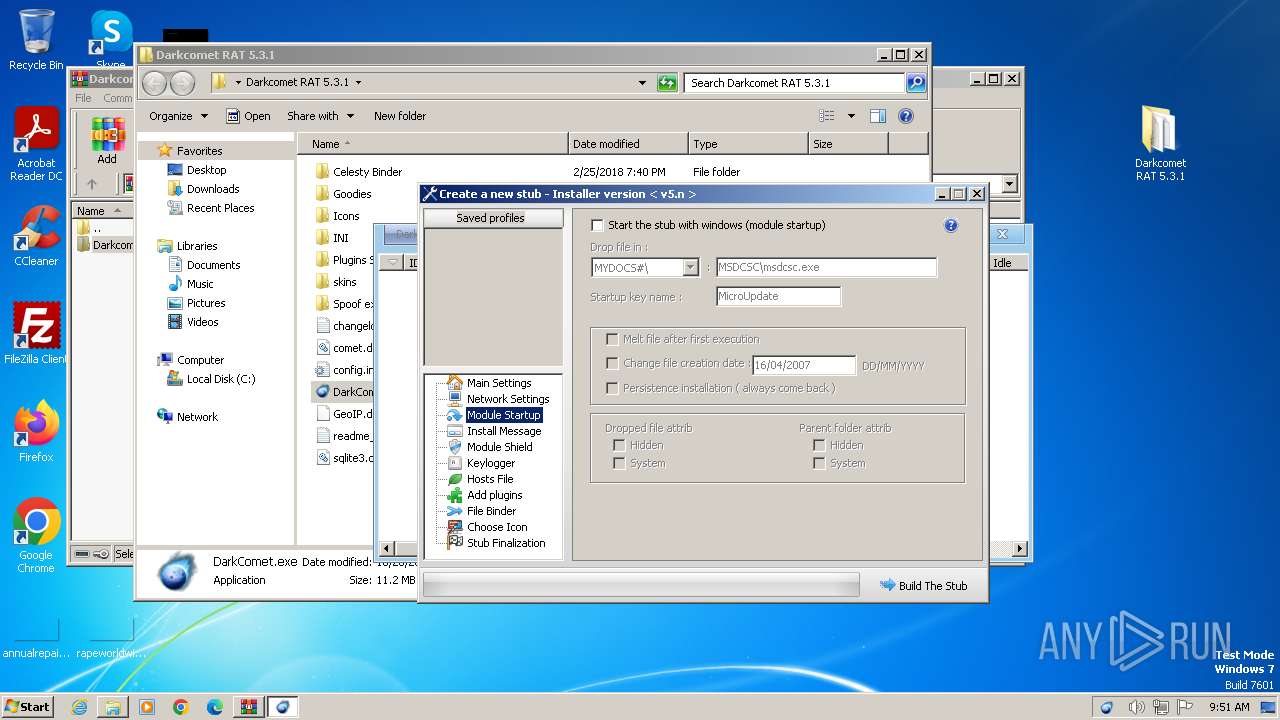
Changes the login/logoff helper path in the registry
- ytt.exe (PID: 1828)
Changes the autorun value in the registry
- ytt.exe (PID: 1828)
- msdcsc.exe (PID: 3320)
Changes Security Center notification settings
- msdcsc.exe (PID: 3320)
SUSPICIOUS
Executable content was dropped or overwritten
- UPX.exe (PID: 656)
- DarkComet.exe (PID: 3124)
- ytt.exe (PID: 1828)
Reads the Internet Settings
- DarkComet.exe (PID: 3124)
- ytt.exe (PID: 1828)
Reads security settings of Internet Explorer
- DarkComet.exe (PID: 3124)
- ytt.exe (PID: 1828)
Starts itself from another location
- ytt.exe (PID: 1828)
Starts CMD.EXE for commands execution
- ytt.exe (PID: 1828)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 4012)
- cmd.exe (PID: 1172)
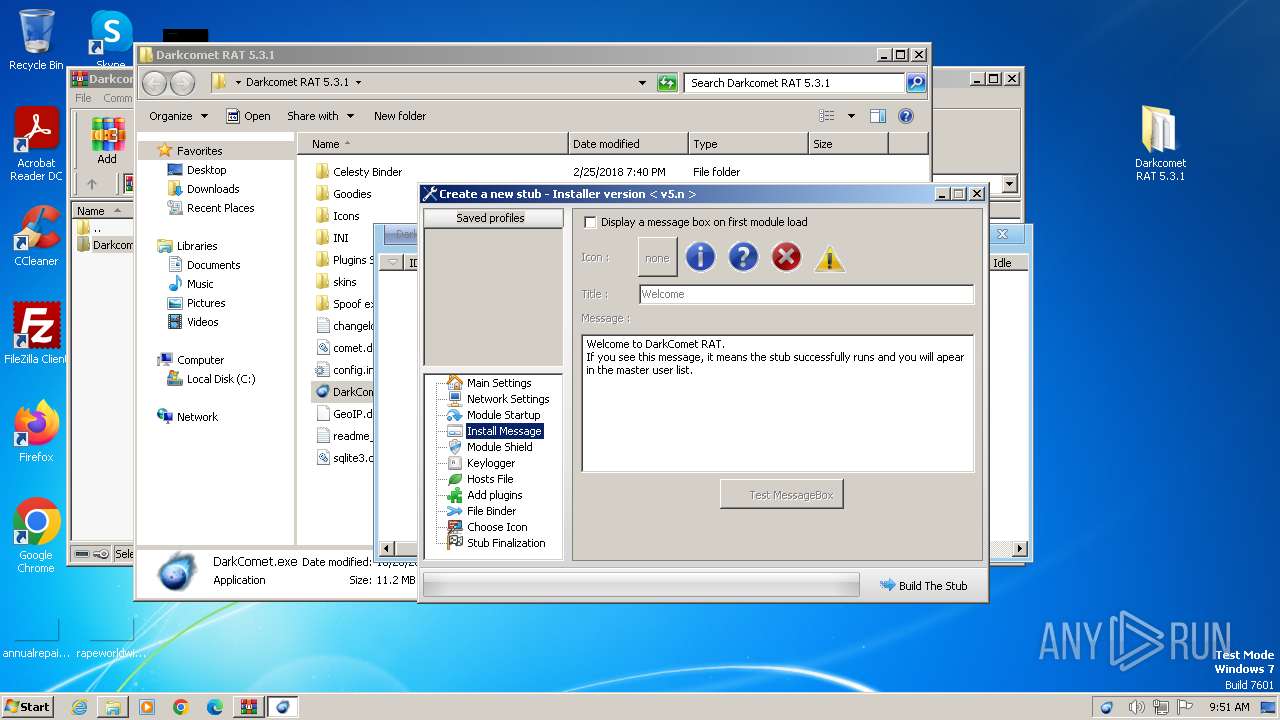
Start notepad (likely ransomware note)
- ytt.exe (PID: 1828)
- msdcsc.exe (PID: 3320)
Reads the date of Windows installation
- ytt.exe (PID: 1828)
INFO
Executable content was dropped or overwritten
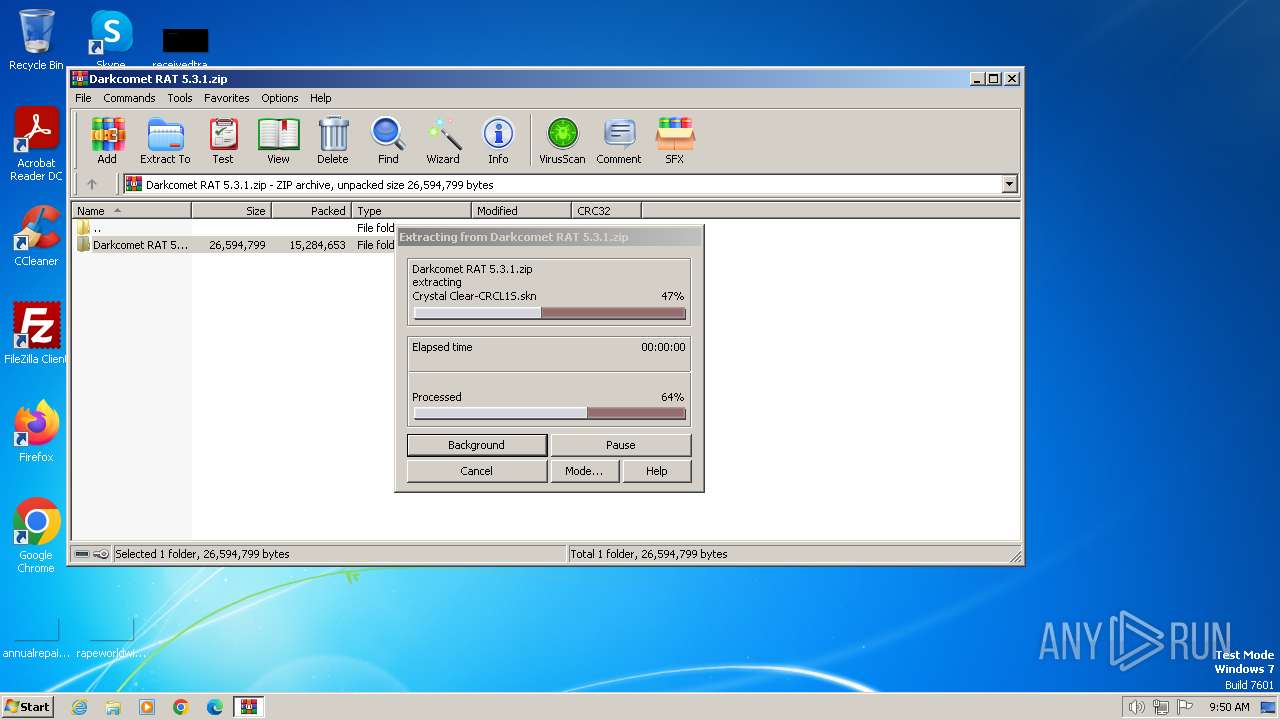
- WinRAR.exe (PID: 3416)
Checks supported languages
- DarkComet.exe (PID: 3124)
- UPX.exe (PID: 656)
- upnp.exe (PID: 2556)
- ytt.exe (PID: 1828)
- msdcsc.exe (PID: 3320)
Drops a (possible) Coronavirus decoy
- WinRAR.exe (PID: 3416)
Reads the computer name
- DarkComet.exe (PID: 3124)
- upnp.exe (PID: 2556)
- ytt.exe (PID: 1828)
- msdcsc.exe (PID: 3320)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3416)
Manual execution by a user
- DarkComet.exe (PID: 3124)
- ytt.exe (PID: 1828)
UPX packer has been detected
- DarkComet.exe (PID: 3124)
- msdcsc.exe (PID: 3320)
Reads the machine GUID from the registry
- DarkComet.exe (PID: 3124)
- ytt.exe (PID: 1828)
Create files in a temporary directory
- DarkComet.exe (PID: 3124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
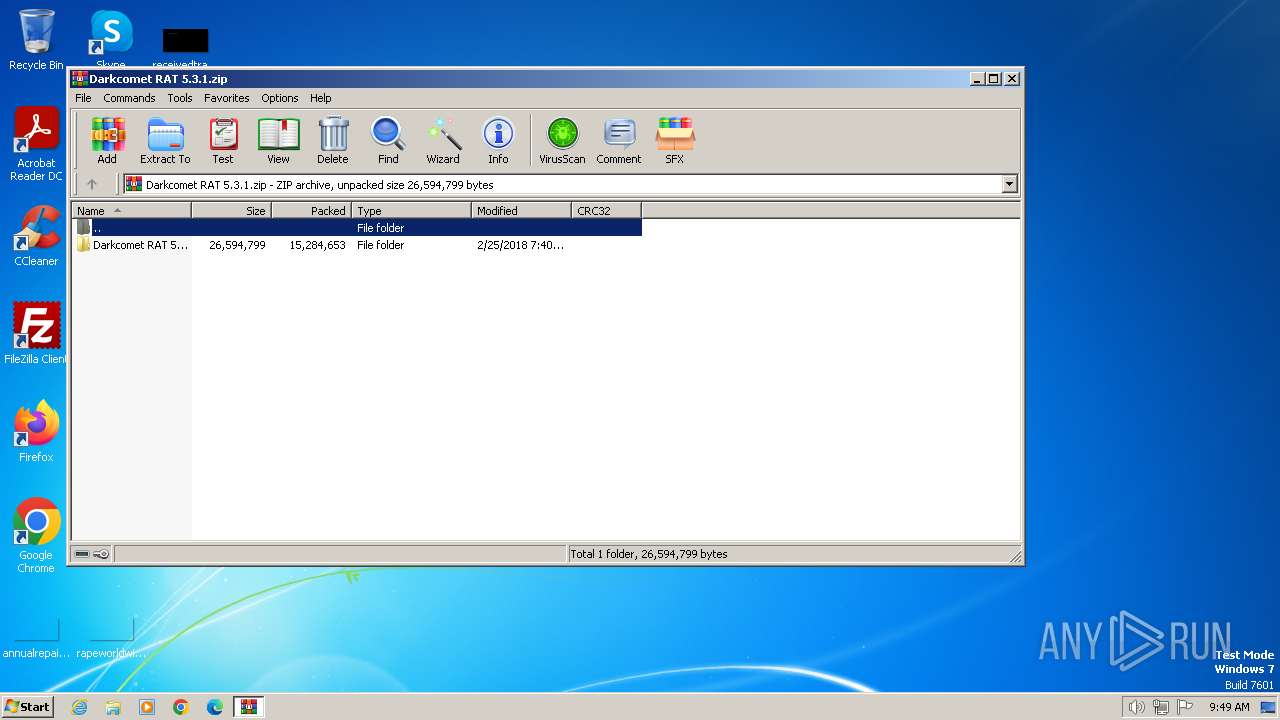
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:02:25 11:40:32 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Darkcomet RAT 5.3.1/ |
Total processes
59
Monitored processes
12
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | notepad | C:\Windows\System32\notepad.exe | — | ytt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 656 | "C:\Users\admin\Desktop\Darkcomet RAT 5.3.1\UPX.exe" -9 "C:\Users\admin\Desktop\ytt.exe" | C:\Users\admin\Desktop\Darkcomet RAT 5.3.1\UPX.exe | DarkComet.exe | ||||||||||||
User: admin Company: The UPX Team http://upx.sf.net Integrity Level: MEDIUM Description: UPX executable packer Exit code: 0 Version: 3.07 (2010-09-08) Modules
| |||||||||||||||
| 1172 | "C:\Windows\System32\cmd.exe" /k attrib "C:\Users\admin\Desktop\ytt.exe" +s +h | C:\Windows\System32\cmd.exe | — | ytt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1524 | notepad | C:\Windows\System32\notepad.exe | — | msdcsc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1828 | "C:\Users\admin\Desktop\ytt.exe" | C:\Users\admin\Desktop\ytt.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Remote Service Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2556 | "C:\Users\admin\AppData\Local\Temp\upnp.exe" -a 192.168.100.234 1604 1604 TCP | C:\Users\admin\AppData\Local\Temp\upnp.exe | DarkComet.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3124 | "C:\Users\admin\Desktop\Darkcomet RAT 5.3.1\DarkComet.exe" | C:\Users\admin\Desktop\Darkcomet RAT 5.3.1\DarkComet.exe | explorer.exe | ||||||||||||
User: admin Company: Unremote.org Integrity Level: MEDIUM Description: A remote administration tool from the cosmos Version: 4.2.0.28 Modules
| |||||||||||||||
| 3320 | "C:\Users\admin\Documents\MSDCSC\msdcsc.exe" | C:\Users\admin\Documents\MSDCSC\msdcsc.exe | ytt.exe | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Remote Service Application Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3324 | attrib "C:\Users\admin\Desktop" +s +h | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3404 | attrib "C:\Users\admin\Desktop\ytt.exe" +s +h | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
14 360
Read events
14 184
Write events
173
Delete events
3
Modification events
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Darkcomet RAT 5.3.1.zip | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
12
Suspicious files
134
Text files
49
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3416.12952\Darkcomet RAT 5.3.1\Celesty Binder\Celesty.exe | executable | |
MD5:C3009EE63BC661D9EA75EAEB256448CA | SHA256:0BB88564A22BFD6D9AD6E4D8EFA9077792A7B6094C2A0F865D70C43E11507352 | |||
| 3416 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3416.12952\Darkcomet RAT 5.3.1\Celesty Binder\Lang\EN.ini | text | |
MD5:D5B95D8DBCDCC5BE0290067BE9043009 | SHA256:48A43817F513A7DE5F033F842EA71DCEC7CFE45E2EDC87BE844E461D99E2572E | |||
| 3416 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3416.12952\Darkcomet RAT 5.3.1\Celesty Binder\Lang\AR.ini | text | |
MD5:4276808F92D3EFE8359CB03F9C45C9E1 | SHA256:C4E0CD4D29594C9CB188DEAB7BB5F73FC6B3ED832468322ABC05B4E981C306C4 | |||
| 3416 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3416.12952\Darkcomet RAT 5.3.1\Celesty Binder\Lang\FR.ini | text | |
MD5:A8568B41DF3F0A47F875964E8FEEFA70 | SHA256:F515EE7D43CF301FE771599C60E2771DB6F27E614AF6A4403771A0D99CB19BC7 | |||
| 3416 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3416.12952\Darkcomet RAT 5.3.1\Celesty Binder\Lang\IT.ini | binary | |
MD5:1CB447996787264785C83D110C67AB13 | SHA256:840DB2223BC47B37C44393BCE4CA8583D373EF6D70B6BC9143561190AA16CDCB | |||
| 3416 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3416.12952\Darkcomet RAT 5.3.1\Celesty Binder\Lang\GR.ini | text | |
MD5:8B35CDF90F3D89D2502E1F61B2BBF631 | SHA256:FCA01673CB23ABD479B6D54D19A40A87E9D72B90ECC7F5D59AF14D192CC07C7C | |||
| 3416 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3416.12952\Darkcomet RAT 5.3.1\Celesty Binder\config.ini | ini | |
MD5:FACE4F2A1F63AB5DAF4456E3A46F62DC | SHA256:E529BCDCCA95735AEE7020A3B26312560584B78394CE971B3A729823DD148AAA | |||
| 3416 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3416.12952\Darkcomet RAT 5.3.1\config.ini | ini | |
MD5:0A5BACCB60DDF613C9EF2B18E0B1863F | SHA256:21A222E00EA35F663DC6C397C0A0AA6D80E52187644B170CEE9E186892A22F4E | |||
| 3416 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3416.12952\Darkcomet RAT 5.3.1\Celesty Binder\readme.txt | text | |
MD5:EC0EB4AD970DC1D264BC6C6E7471428D | SHA256:BEC0F54669D35669D4E90E4AA588B96002B8A4E85048CE1CBF707F7F86AC250D | |||
| 3416 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3416.12952\Darkcomet RAT 5.3.1\changelog.txt | text | |
MD5:7A23E5B811DD52E99CBDB72A7FE4CE12 | SHA256:7CF268D2FBBC3BB3E1CE2019D53F7C88B42F3BBCD4833AC69798D34FBD809DFE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
11
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.40.113.217:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.199.47.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1372 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1372 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1372 | svchost.exe | 23.199.47.143:80 | crl.microsoft.com | Akamai International B.V. | US | unknown |
1372 | svchost.exe | 23.40.113.217:80 | www.microsoft.com | AKAMAI-AS | FR | unknown |
1060 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2556 | upnp.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |