| File name: | win.exe |
| Full analysis: | https://app.any.run/tasks/016a93c2-91fd-46ba-a029-cc540d4c1a41 |
| Verdict: | Malicious activity |
| Threats: | Akira Ransomware emerged in March 2023 and compromised over 250 organizations by January 2024 with approximately $42 million in ransom payments. It employs double extortion tactics exfiltrating data before encryption and threatening to publish it on a dedicated website. |
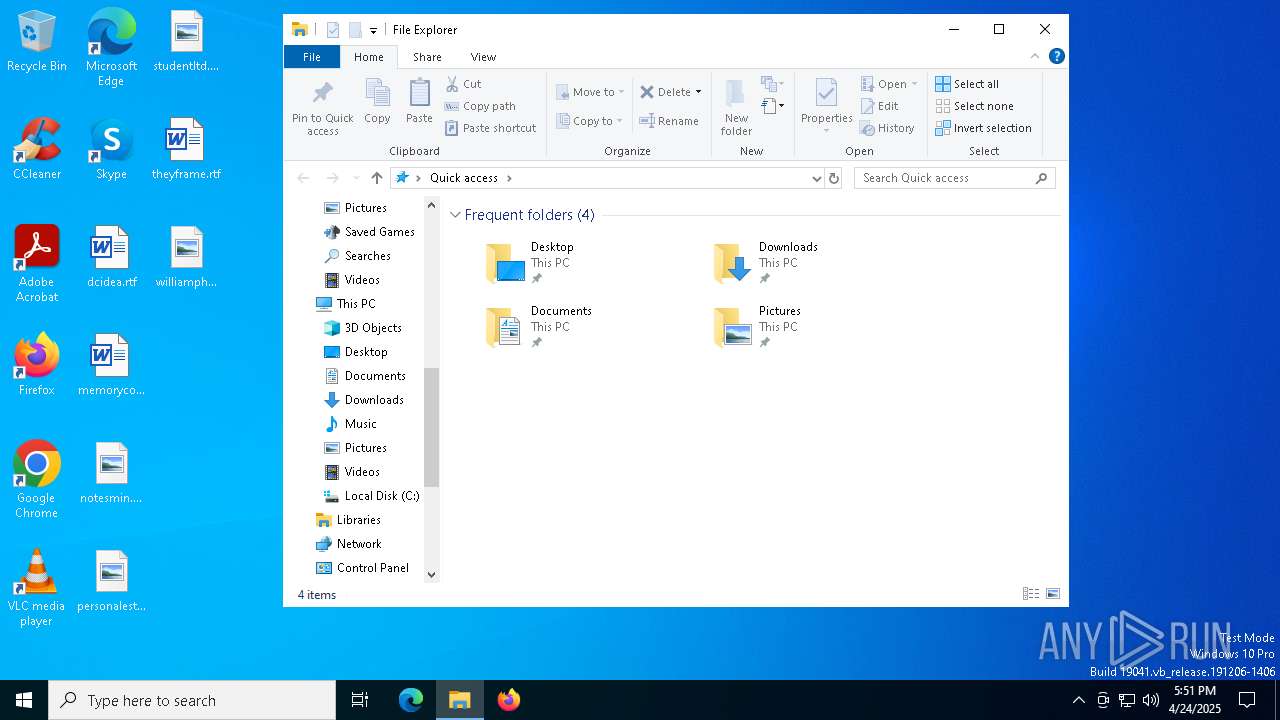
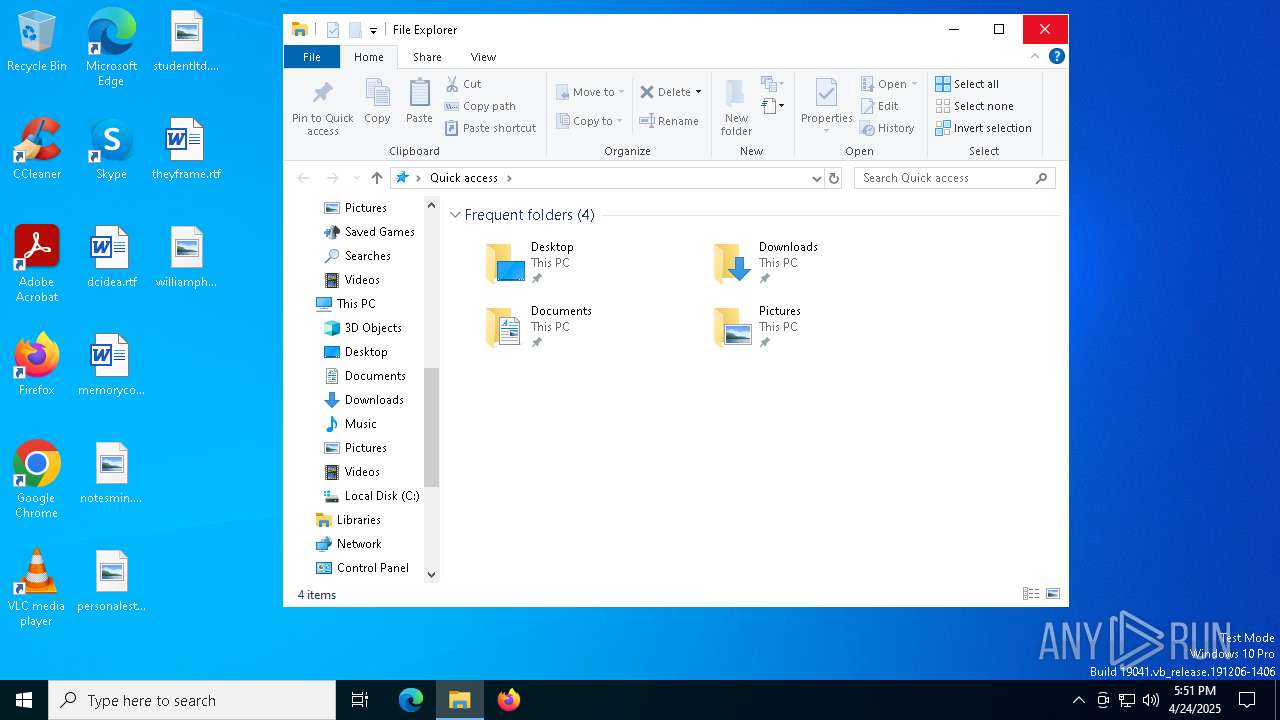
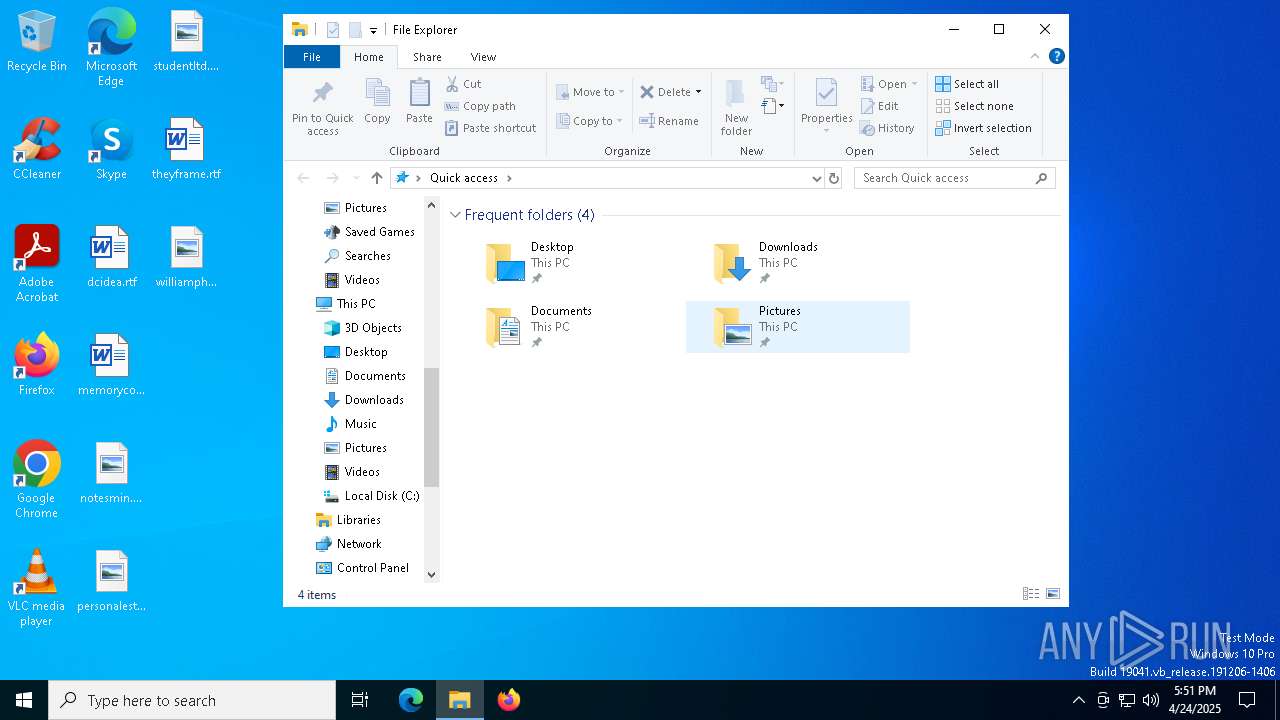
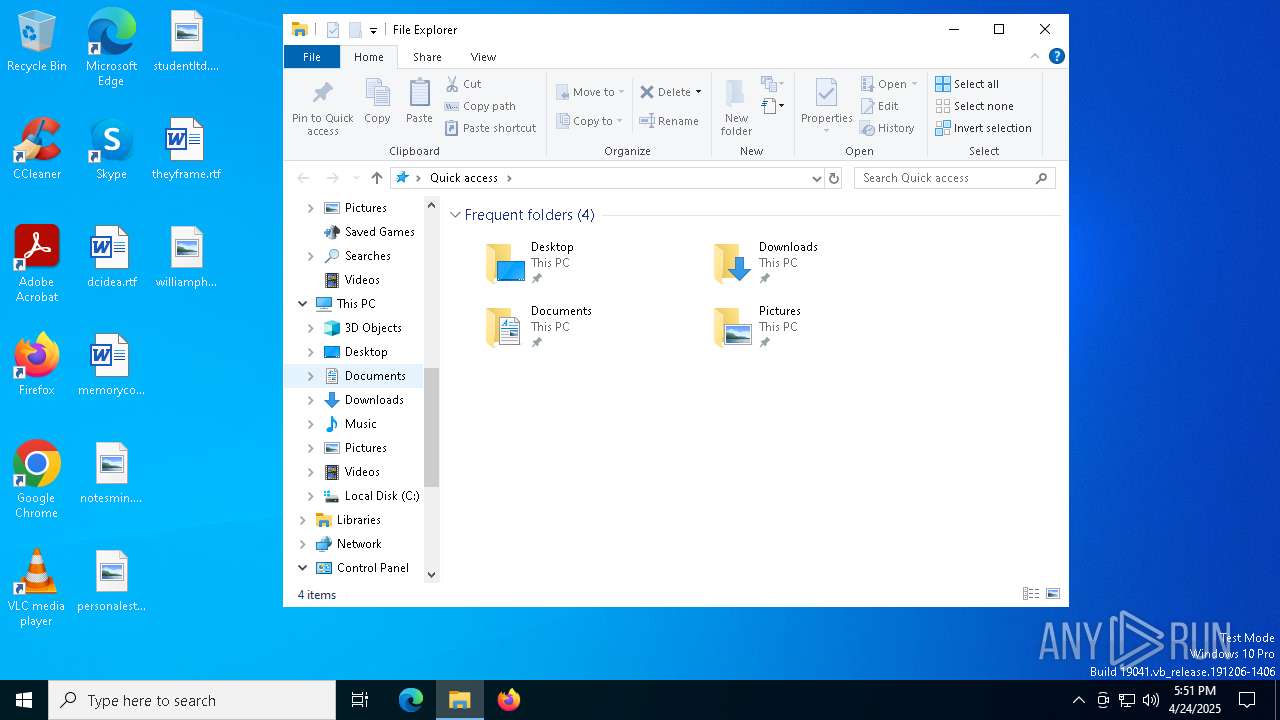
| Analysis date: | April 24, 2025, 17:51:12 |
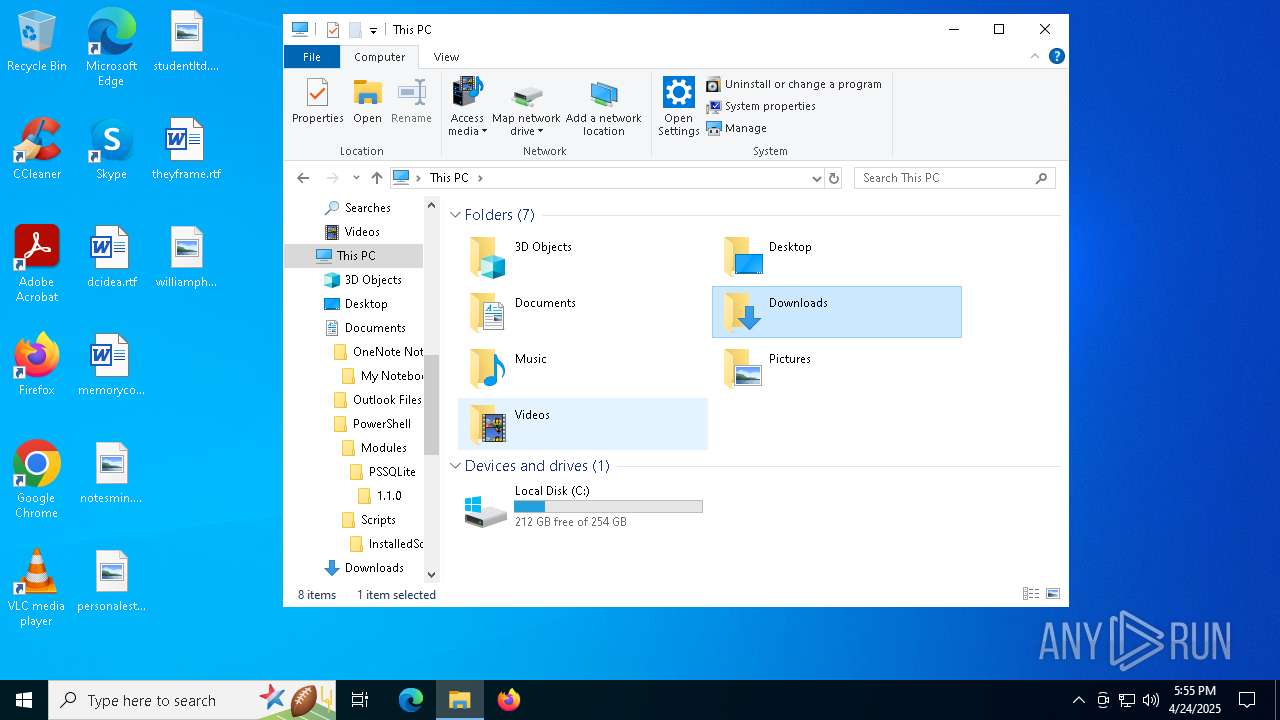
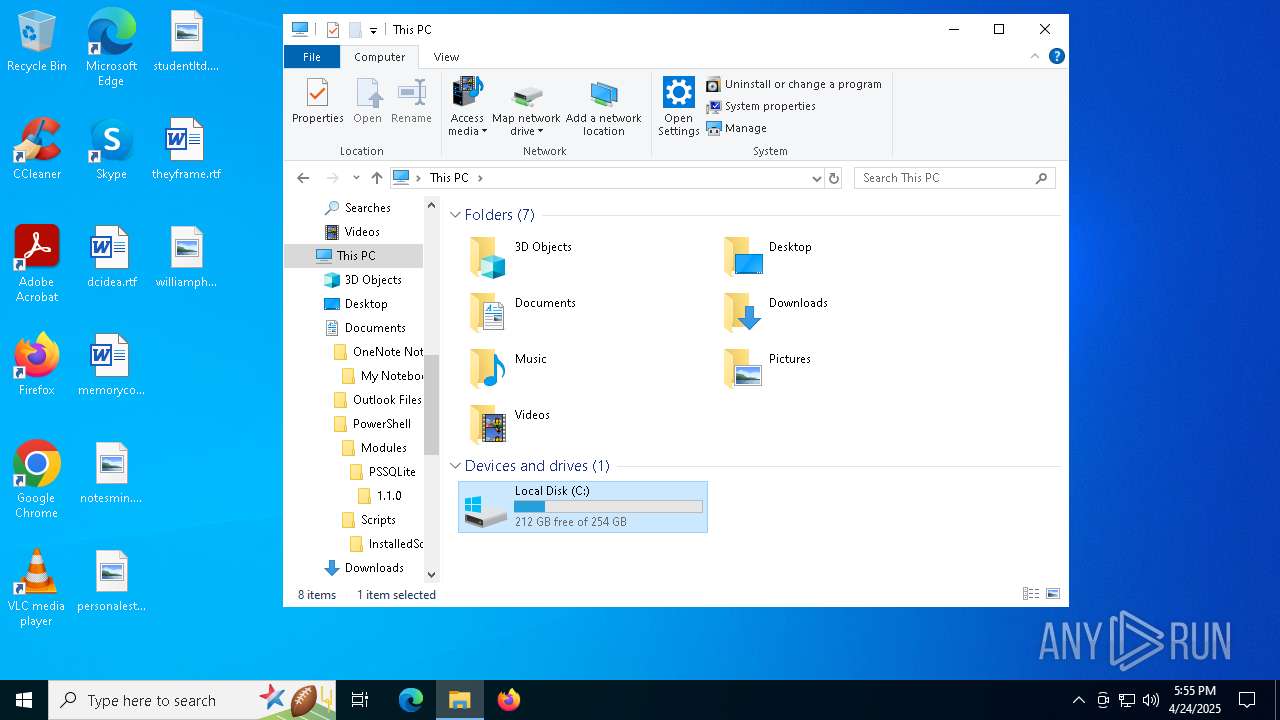
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | C387B2EB96BB137CDD54220D920EDCE9 |
| SHA1: | 57709DBC3B8F78D3197E75F8F568E5632E768482 |
| SHA256: | BFDB075AA514CB43B711BAB06E775C081671863BC89C8E84763864E0AA35DD2C |
| SSDEEP: | 24576:i4/HJQfGMrq1nkF2az/SWIGd0pS4ZvS7H63:i4JQfTr2nkF2az/jIGd0pS4ZvS7H63 |
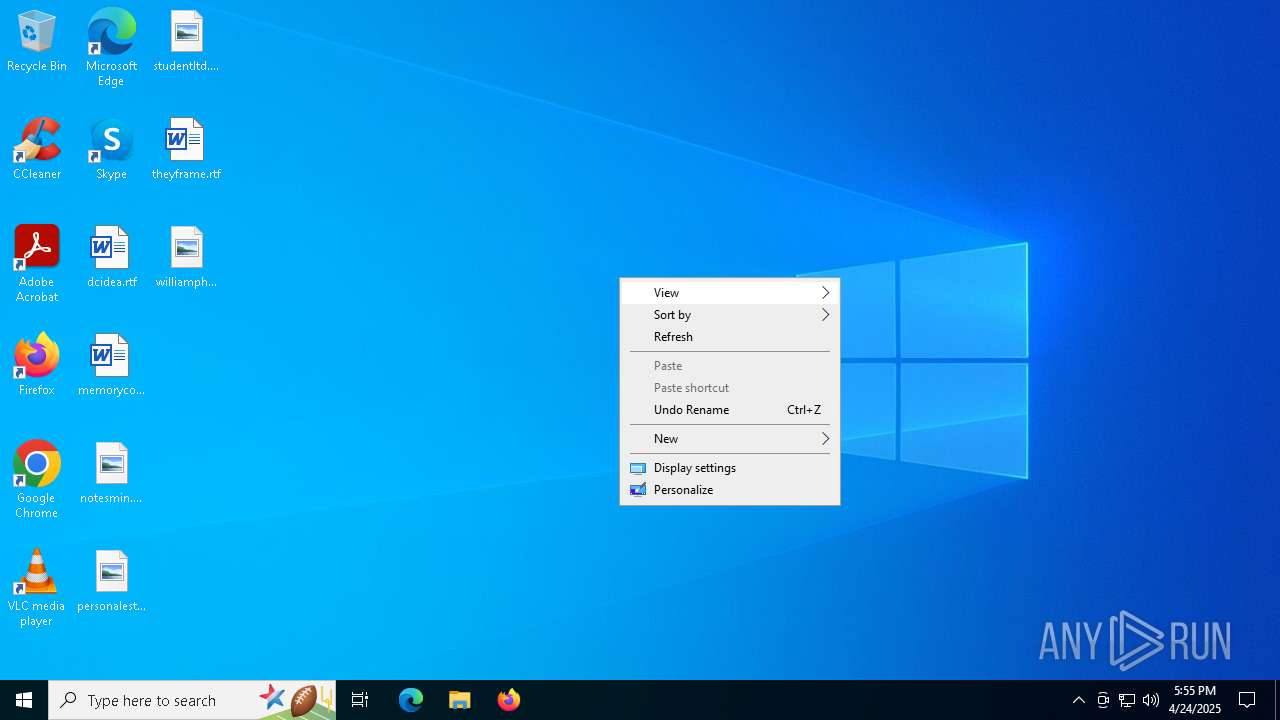
MALICIOUS
AKIRA has been detected
- win.exe (PID: 7264)
RANSOMWARE has been detected
- win.exe (PID: 7264)
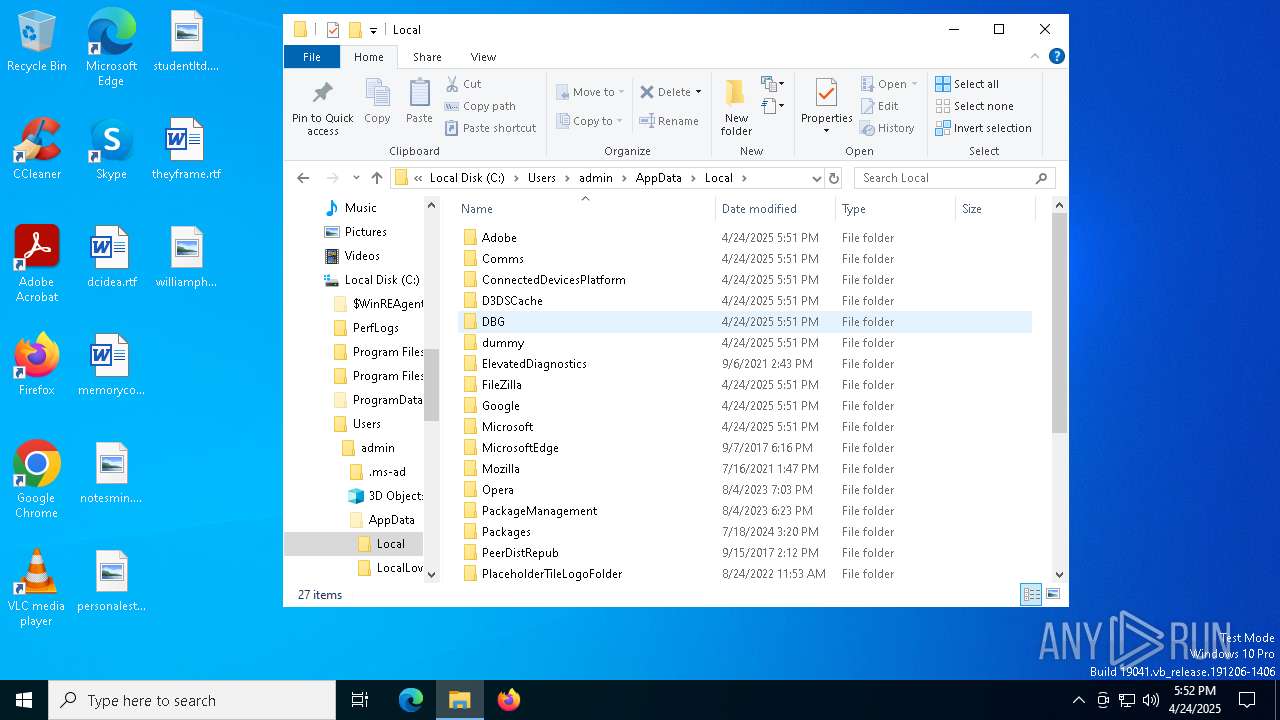
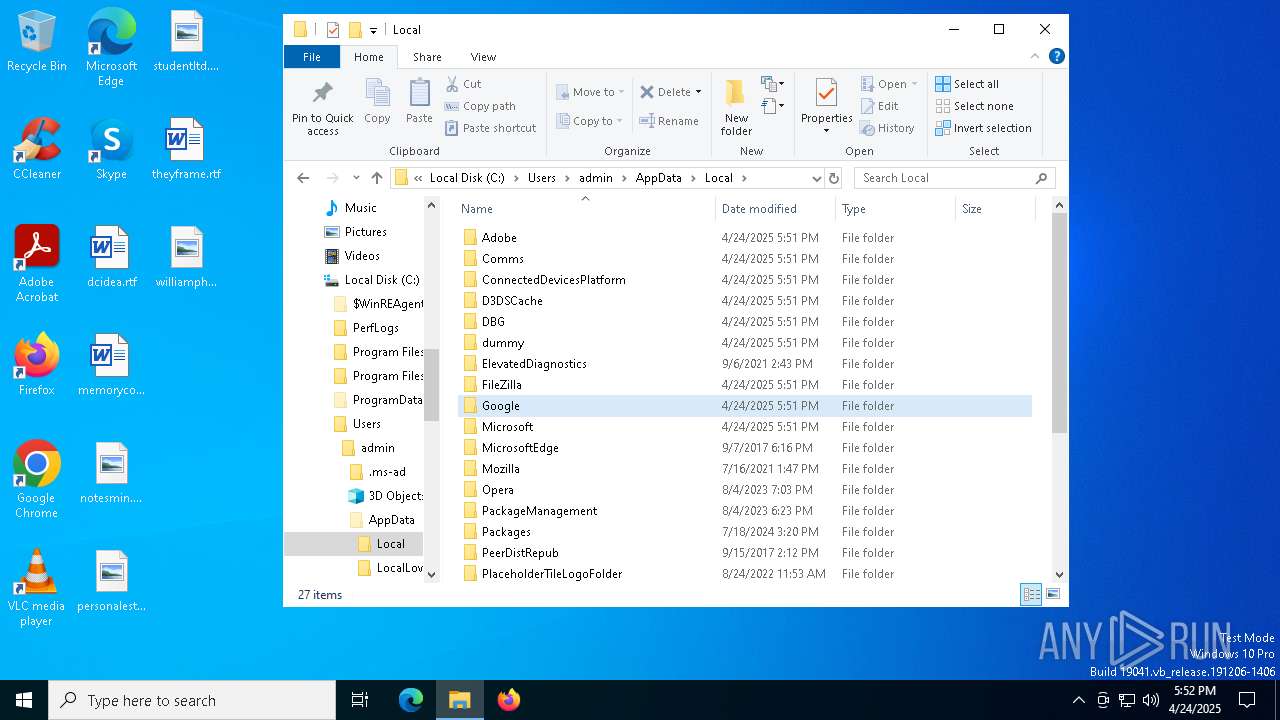
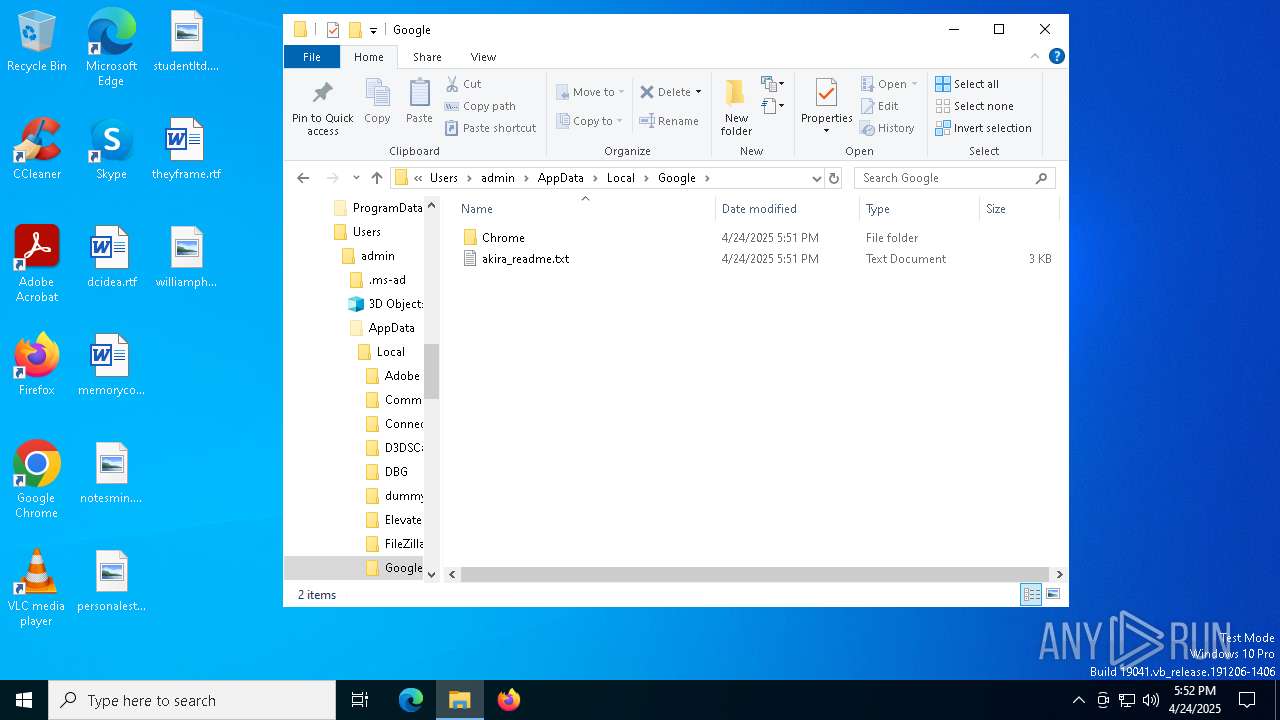
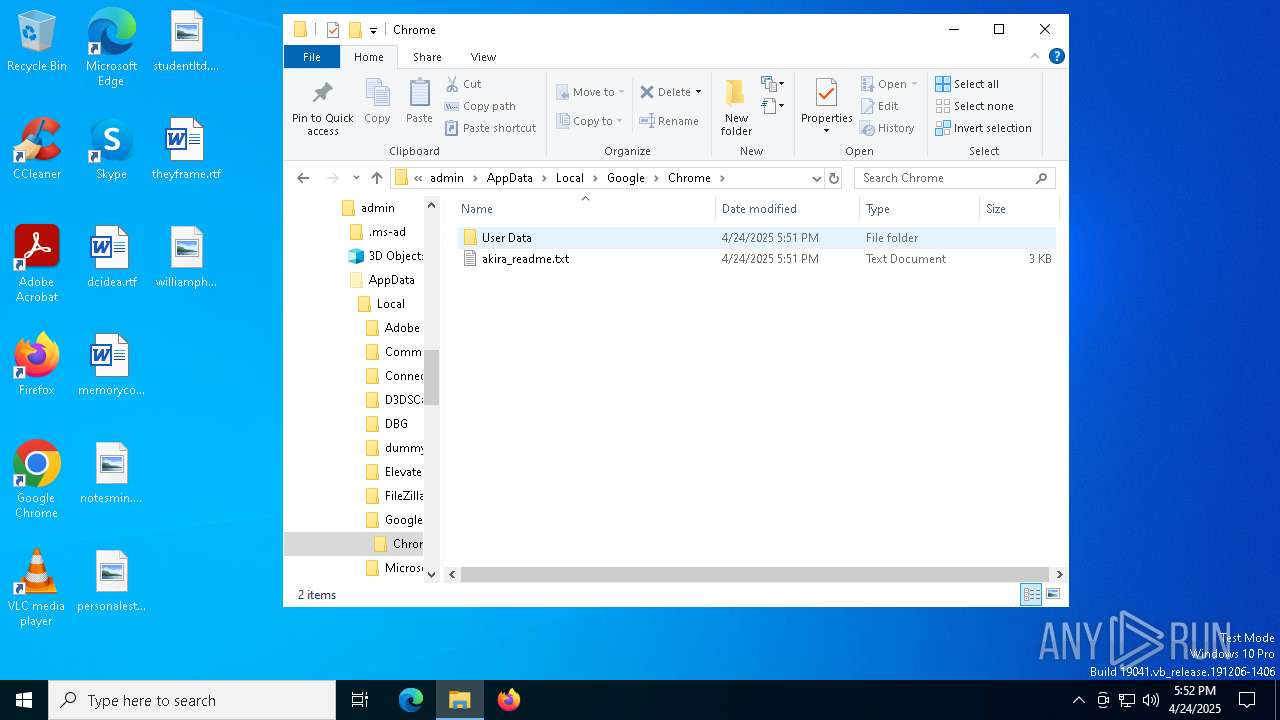
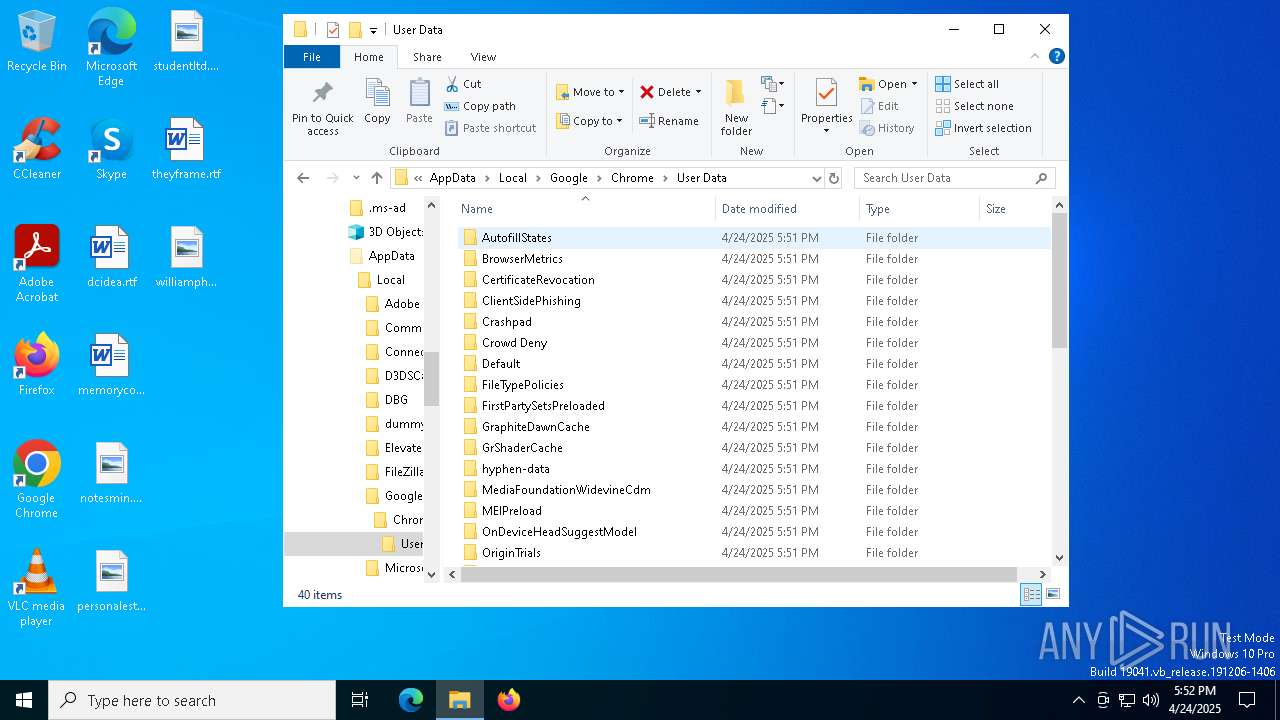
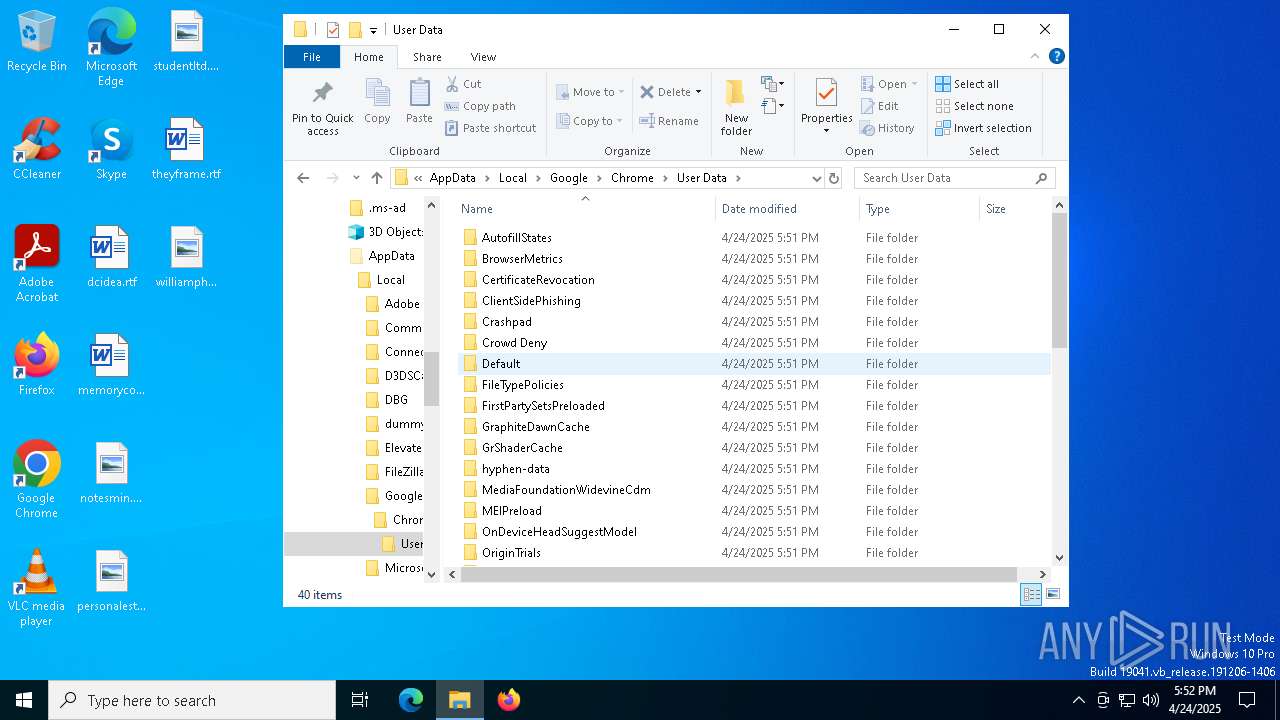
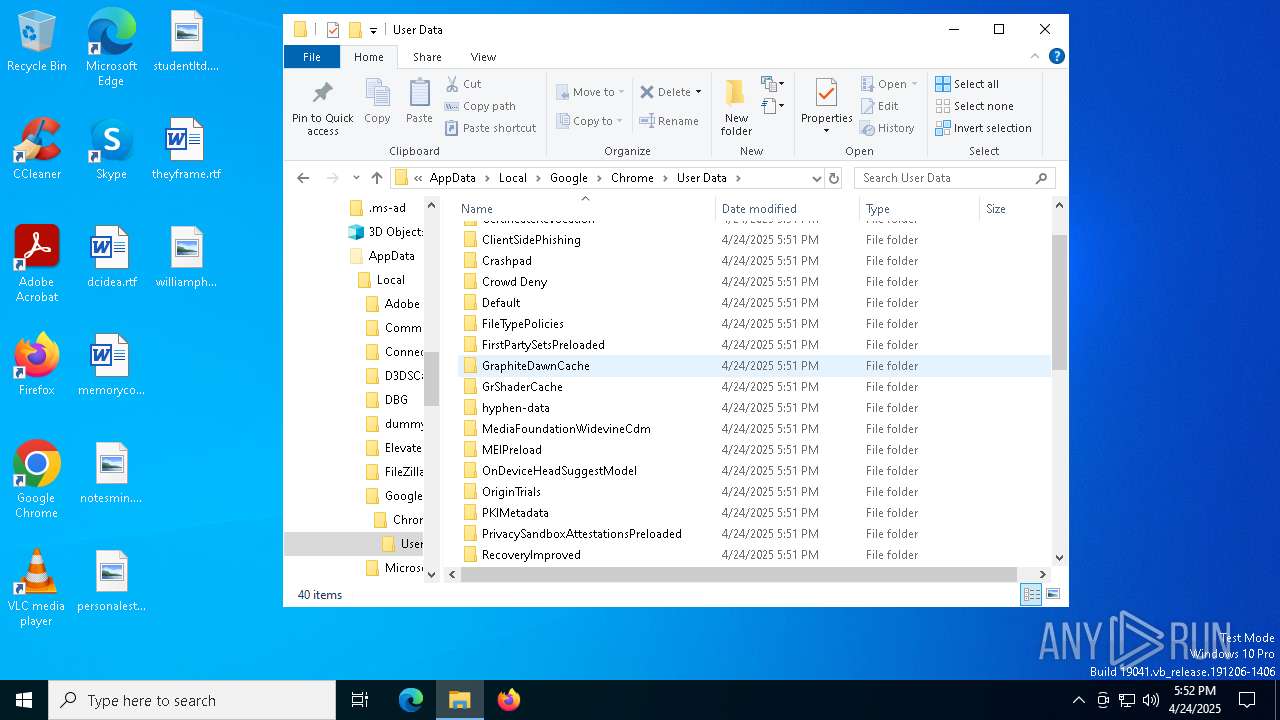
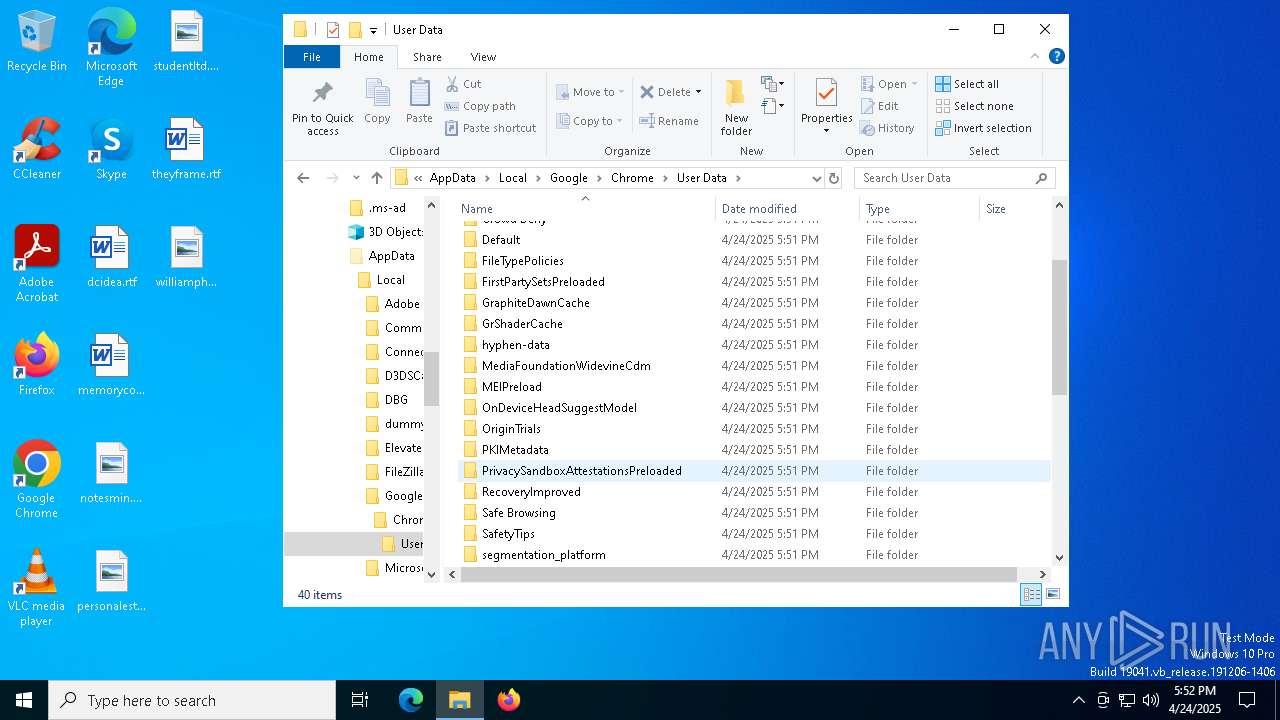
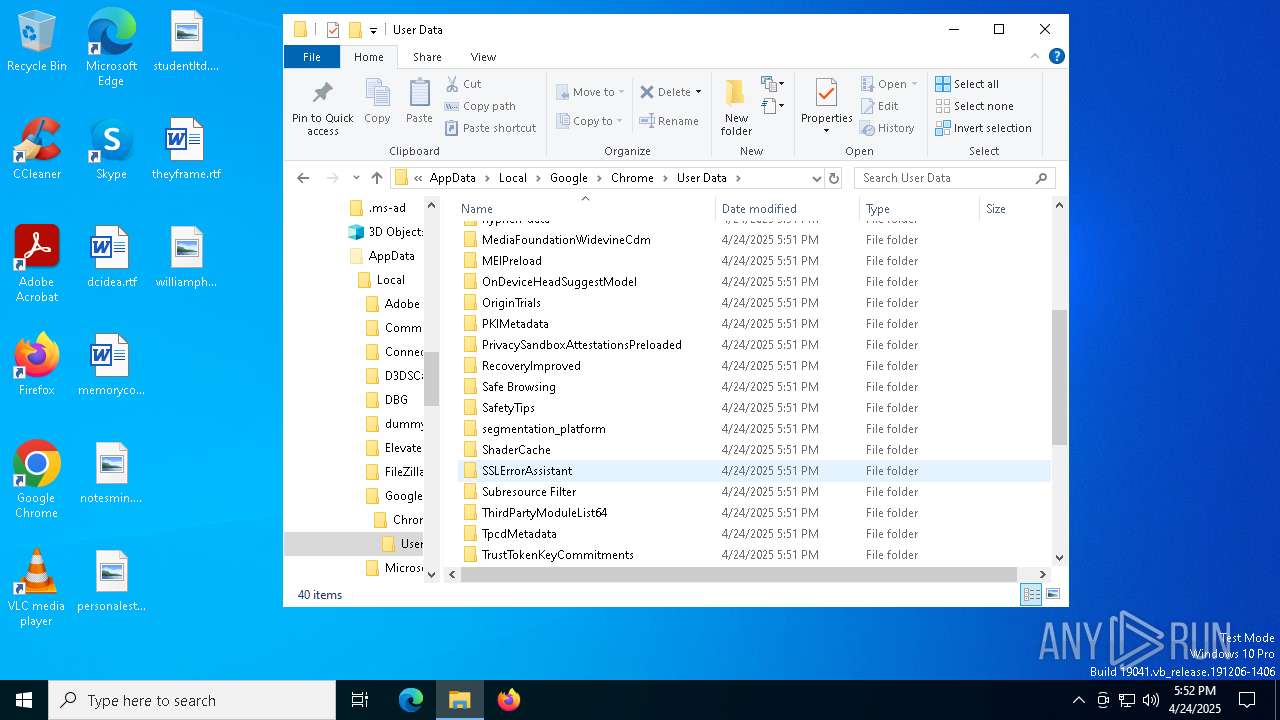
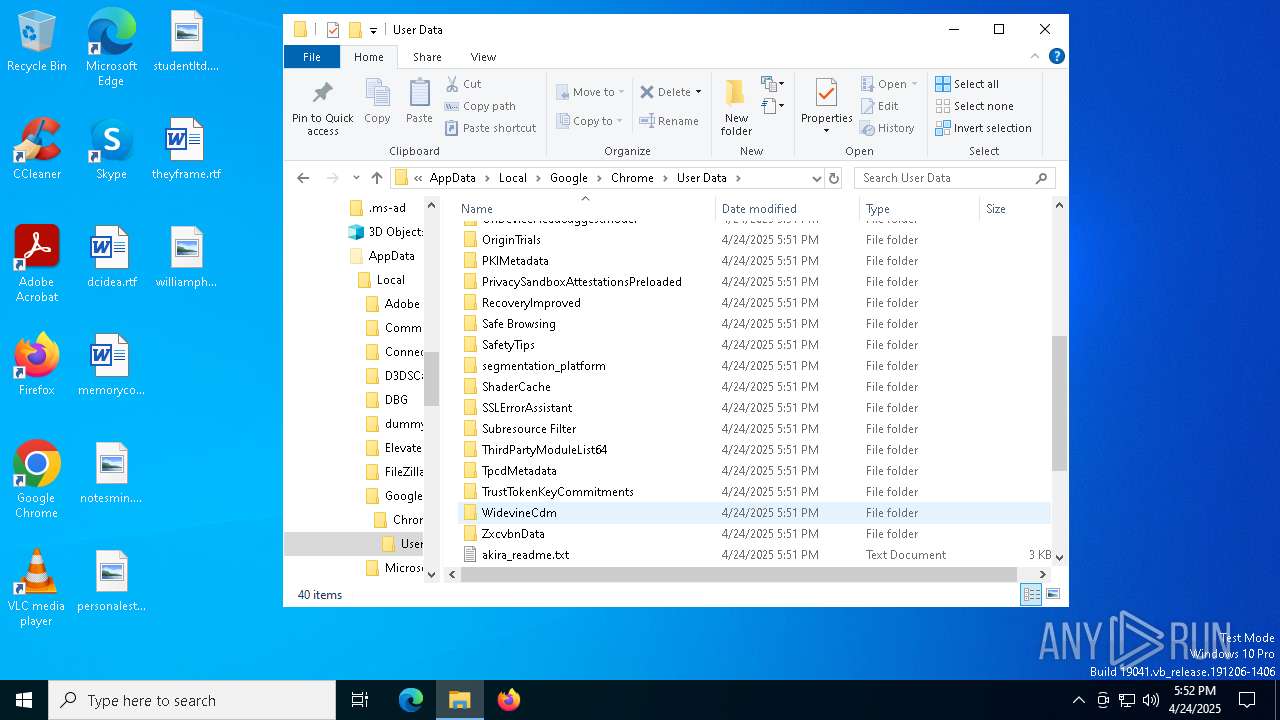
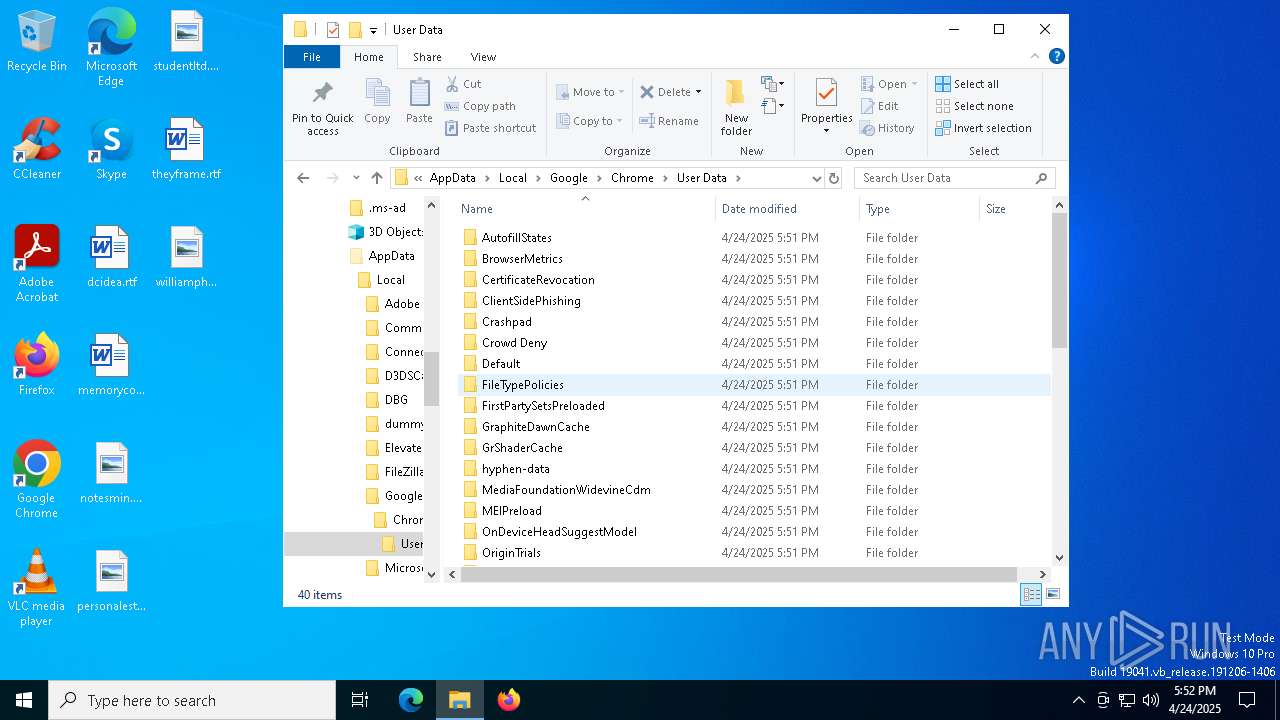
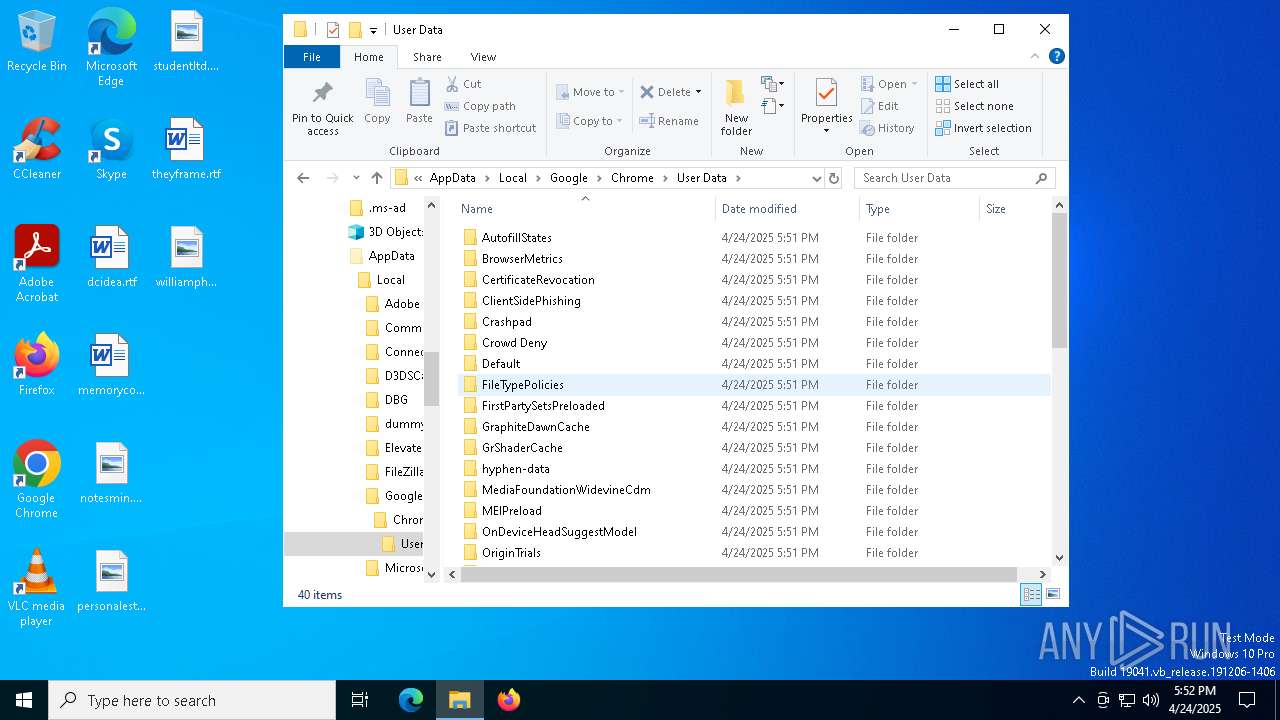
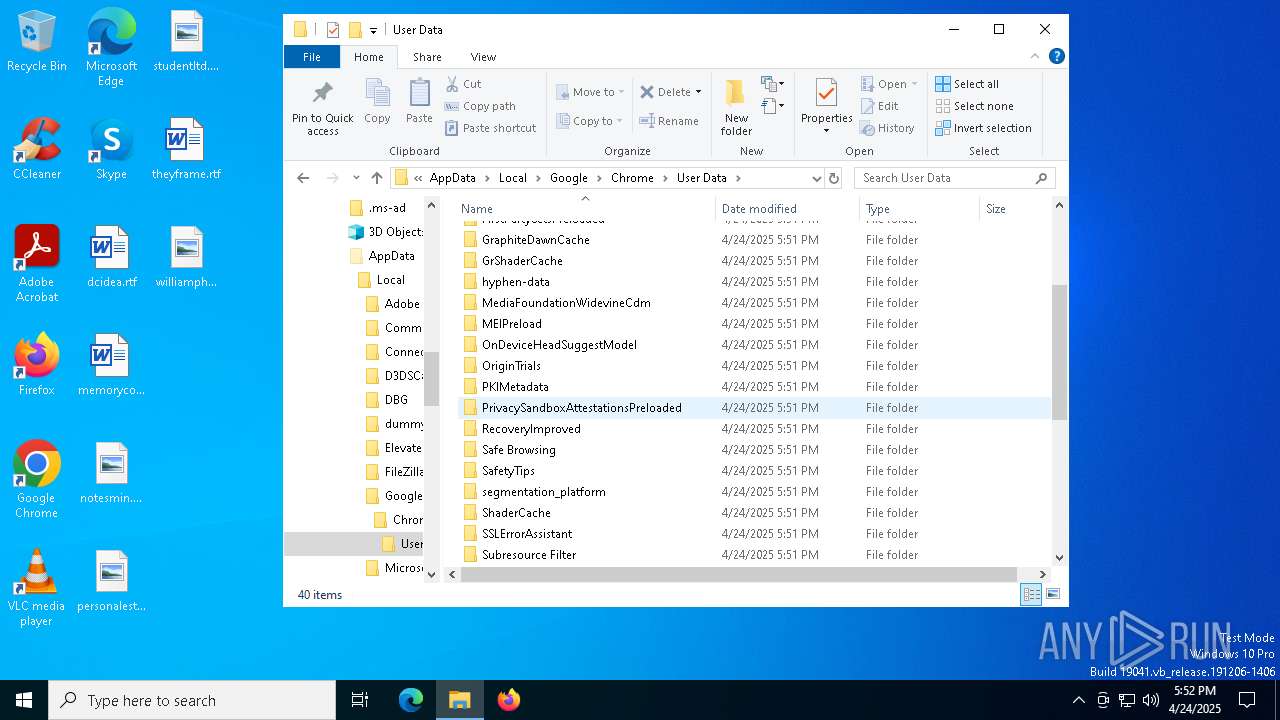
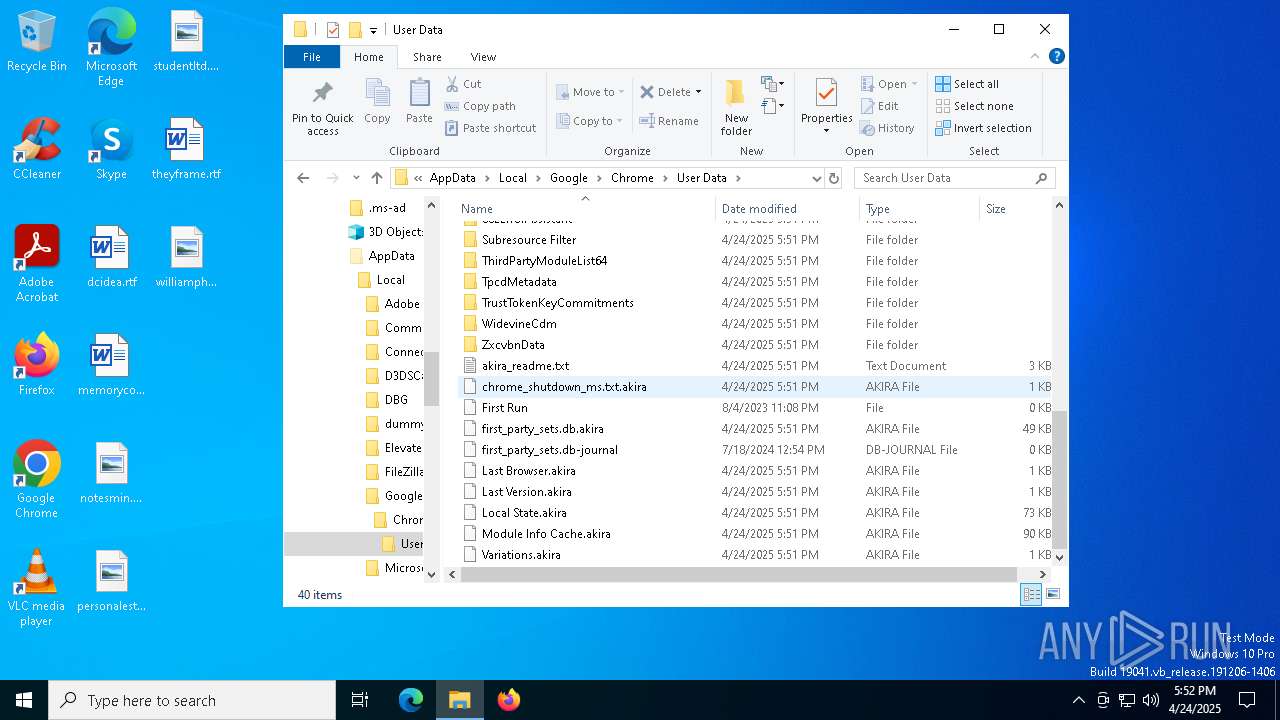
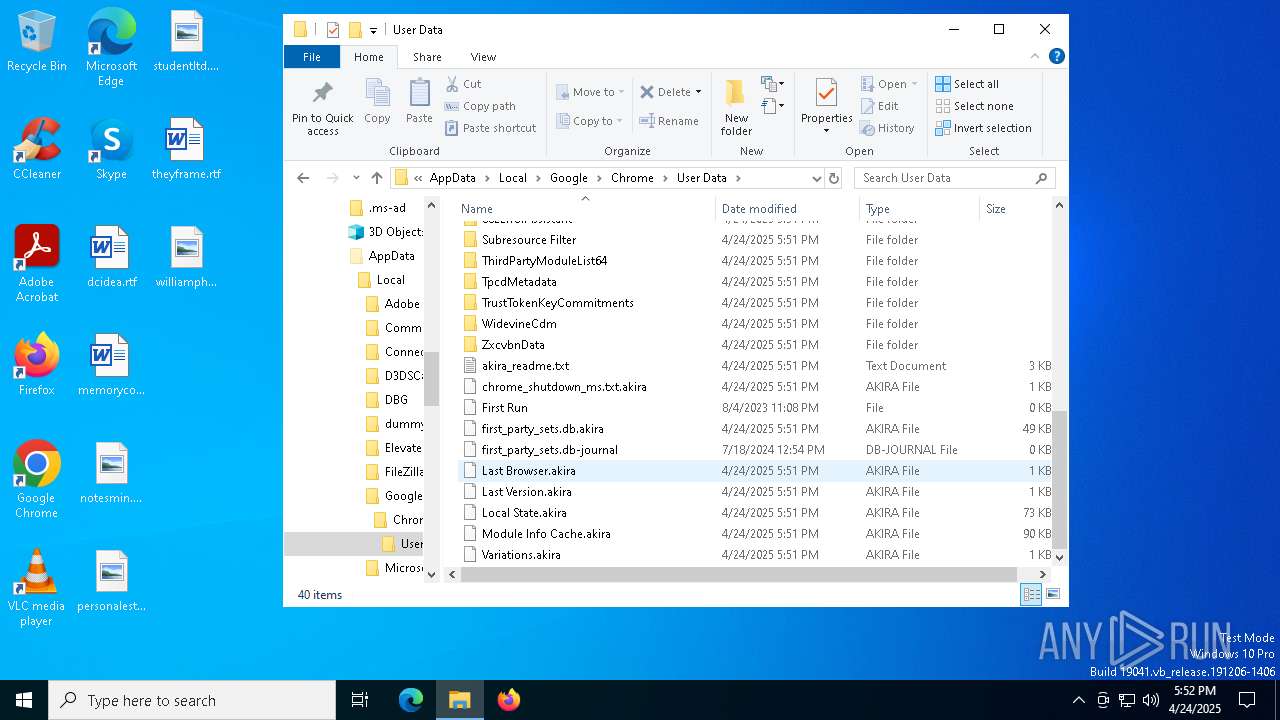
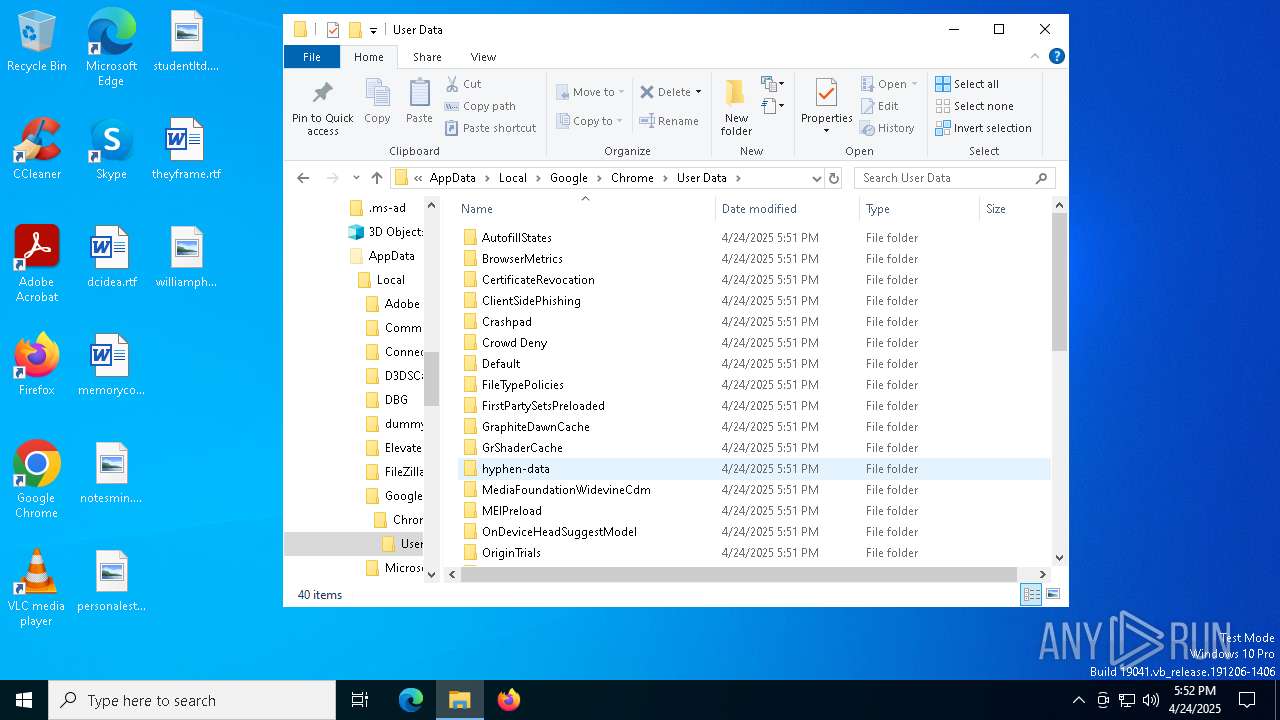
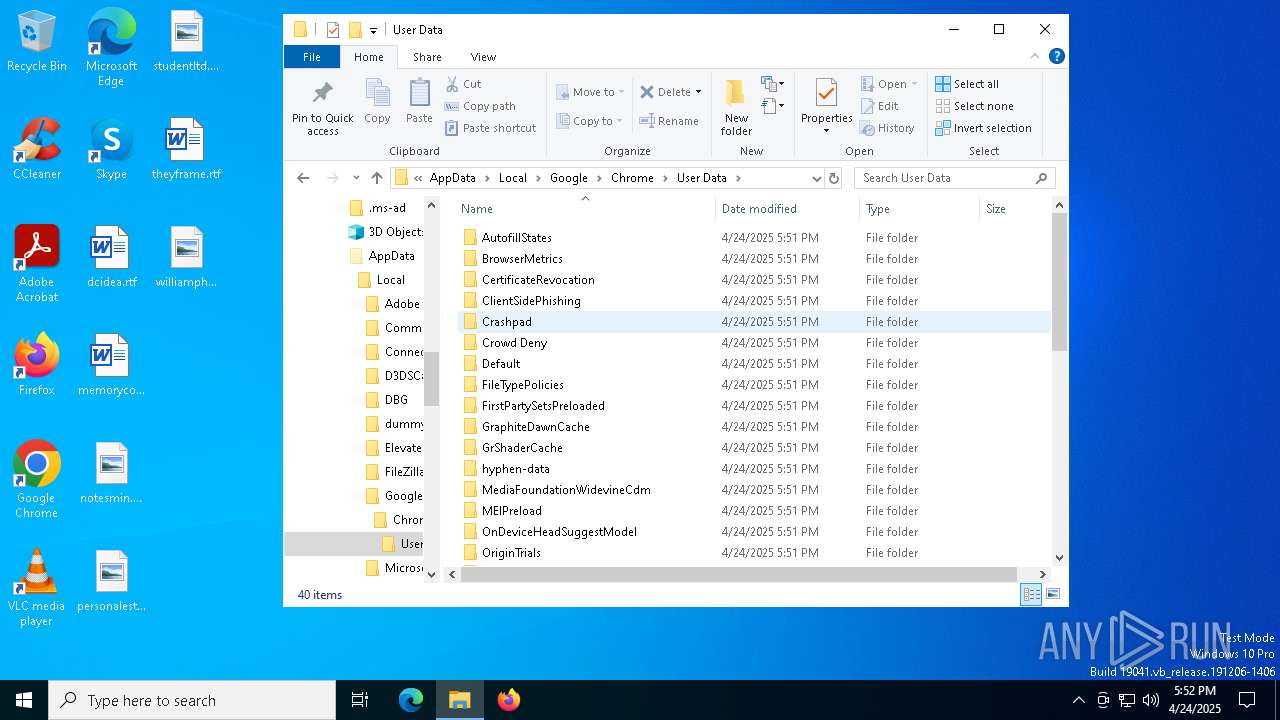
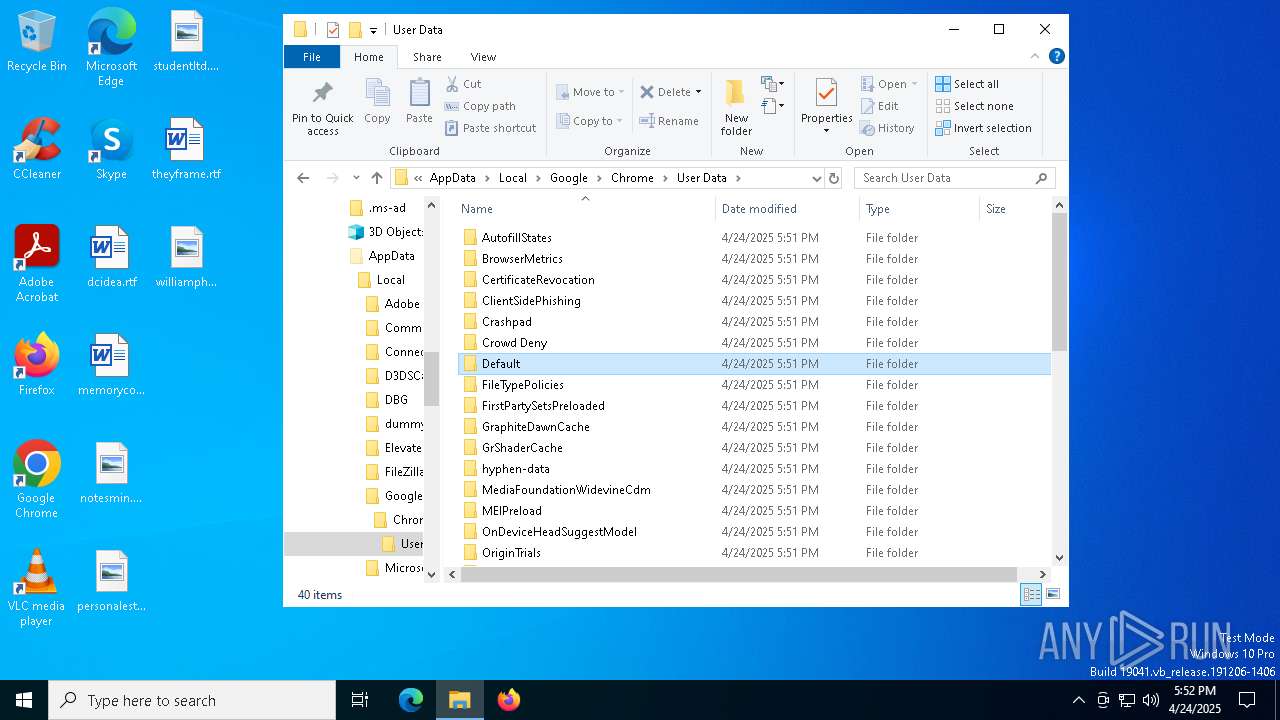
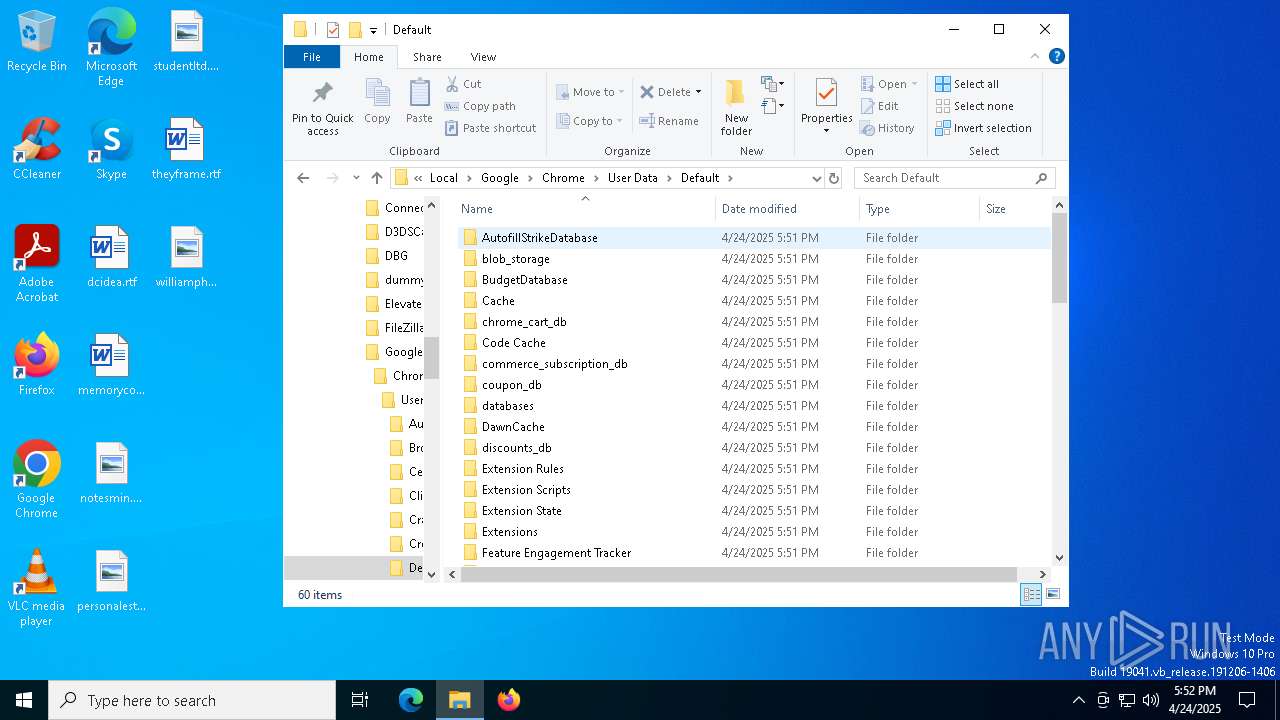
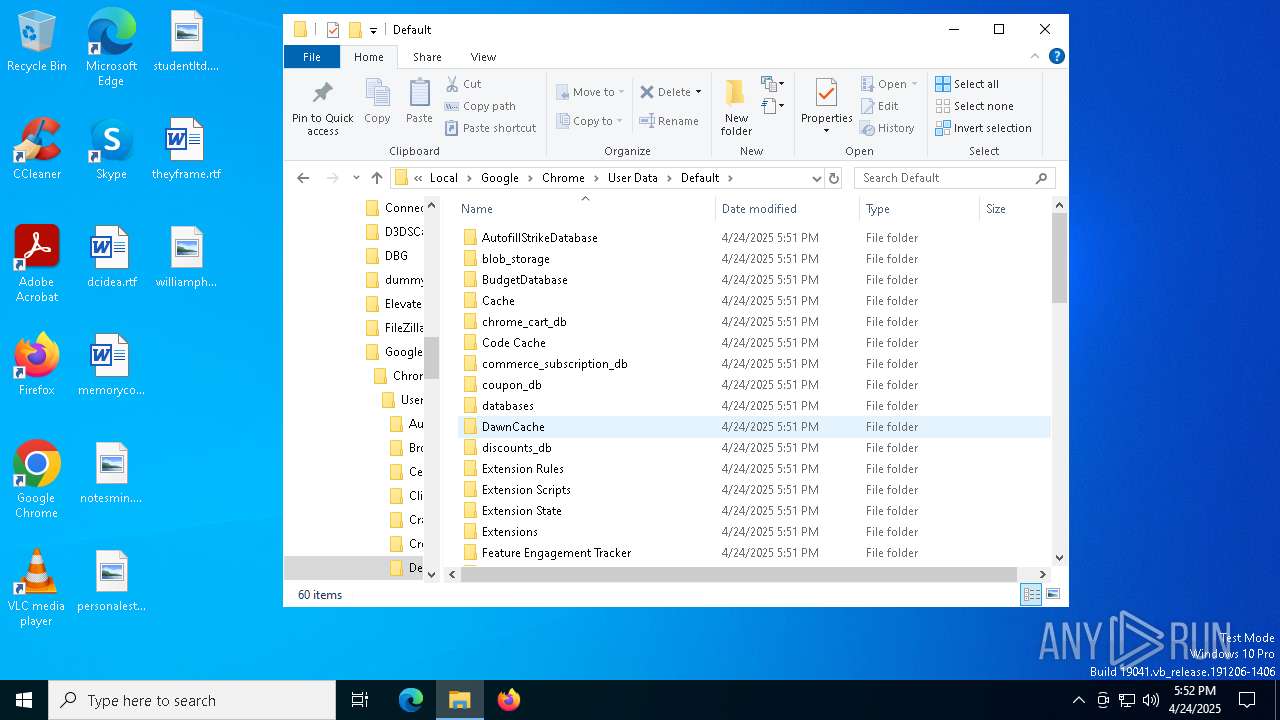
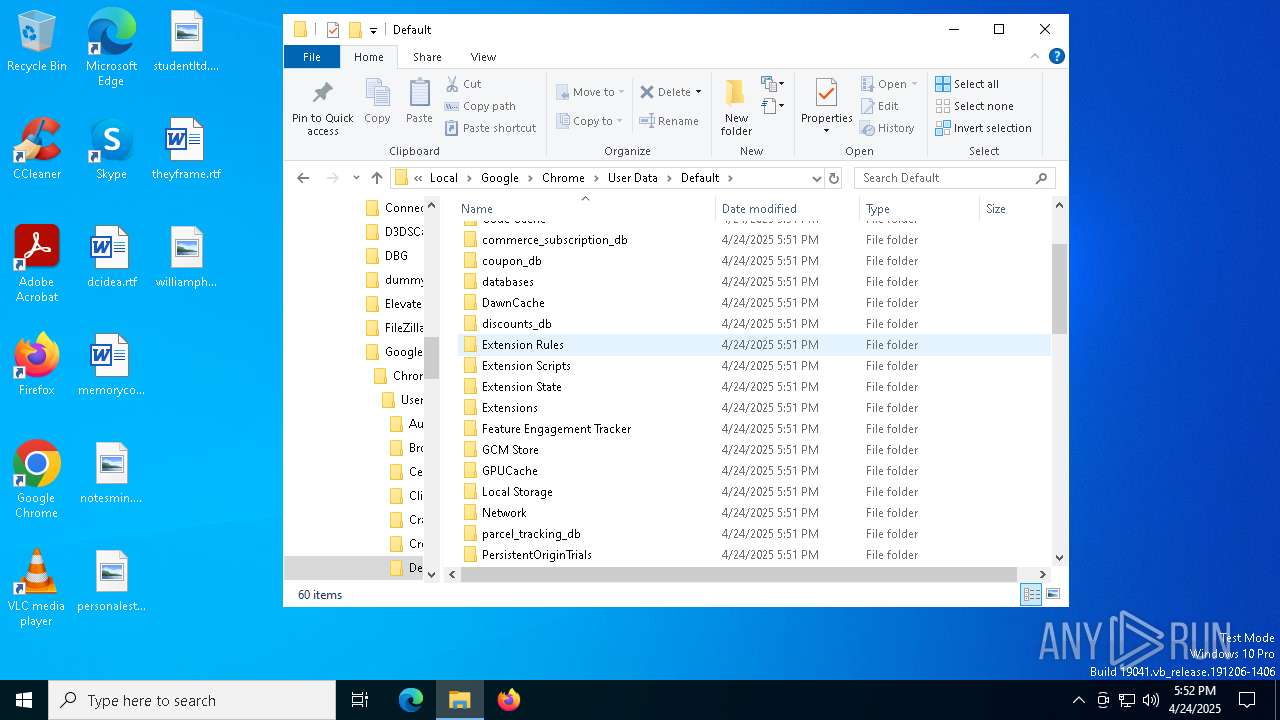
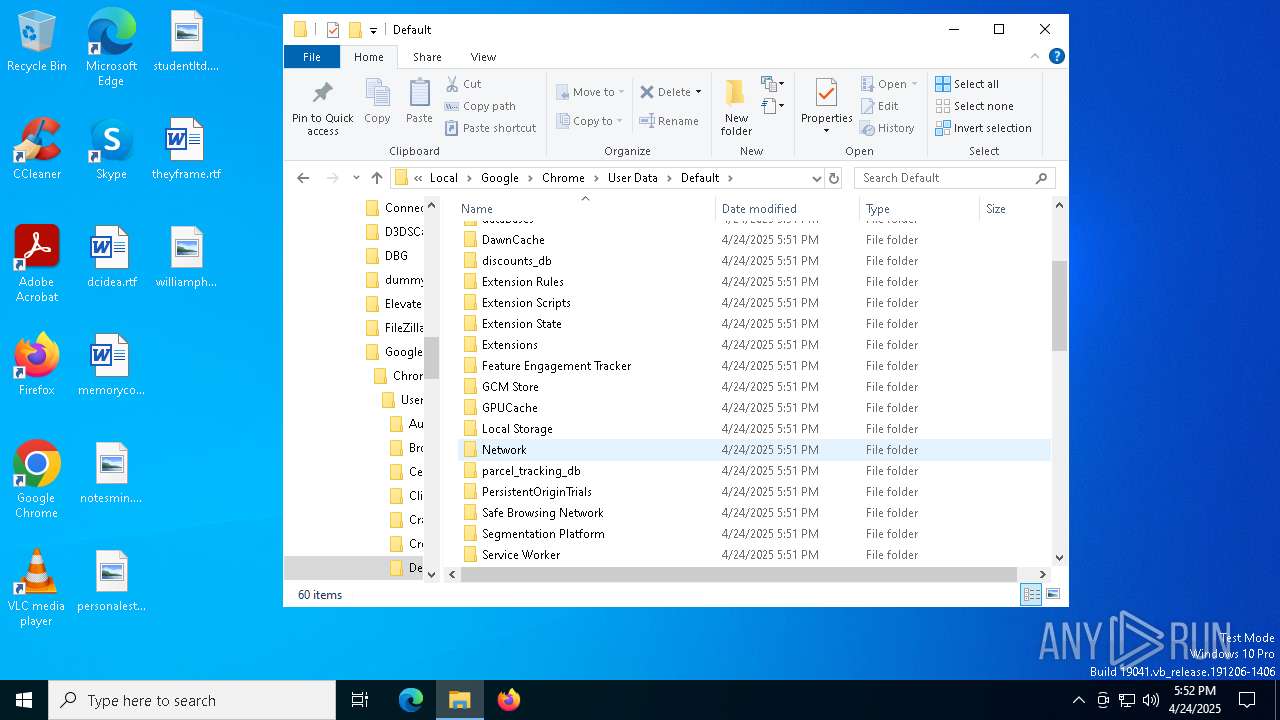
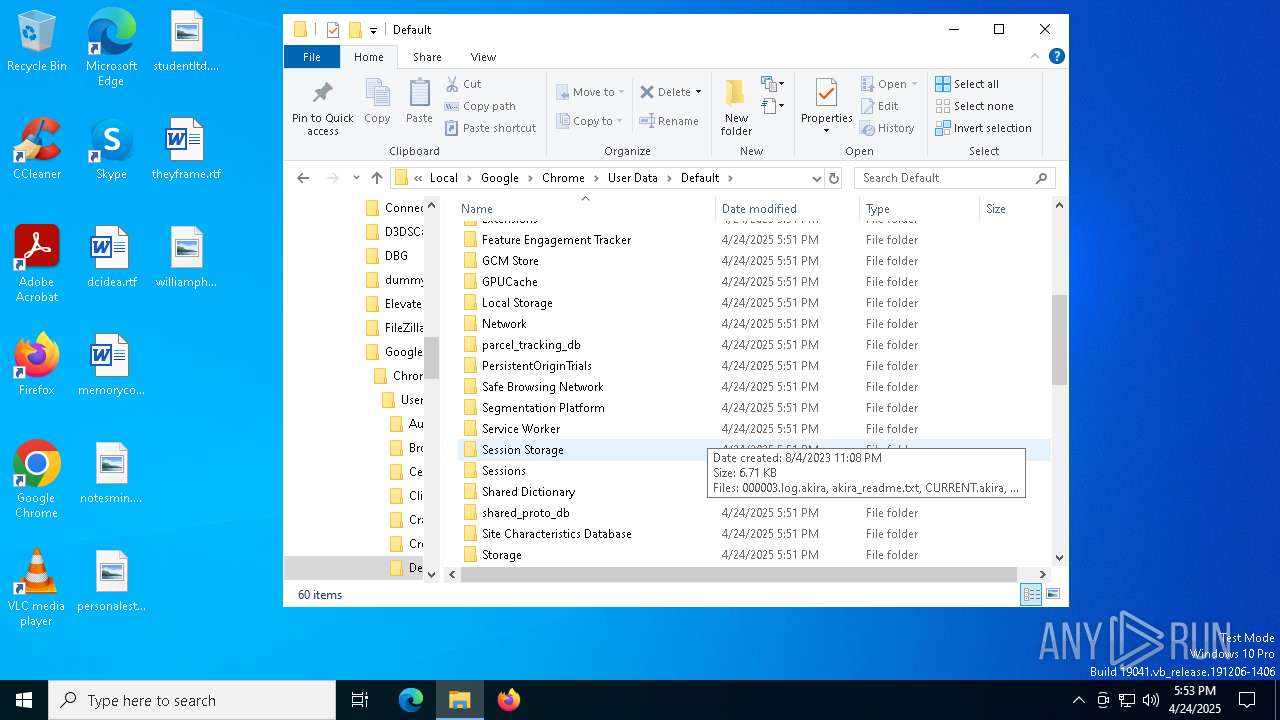
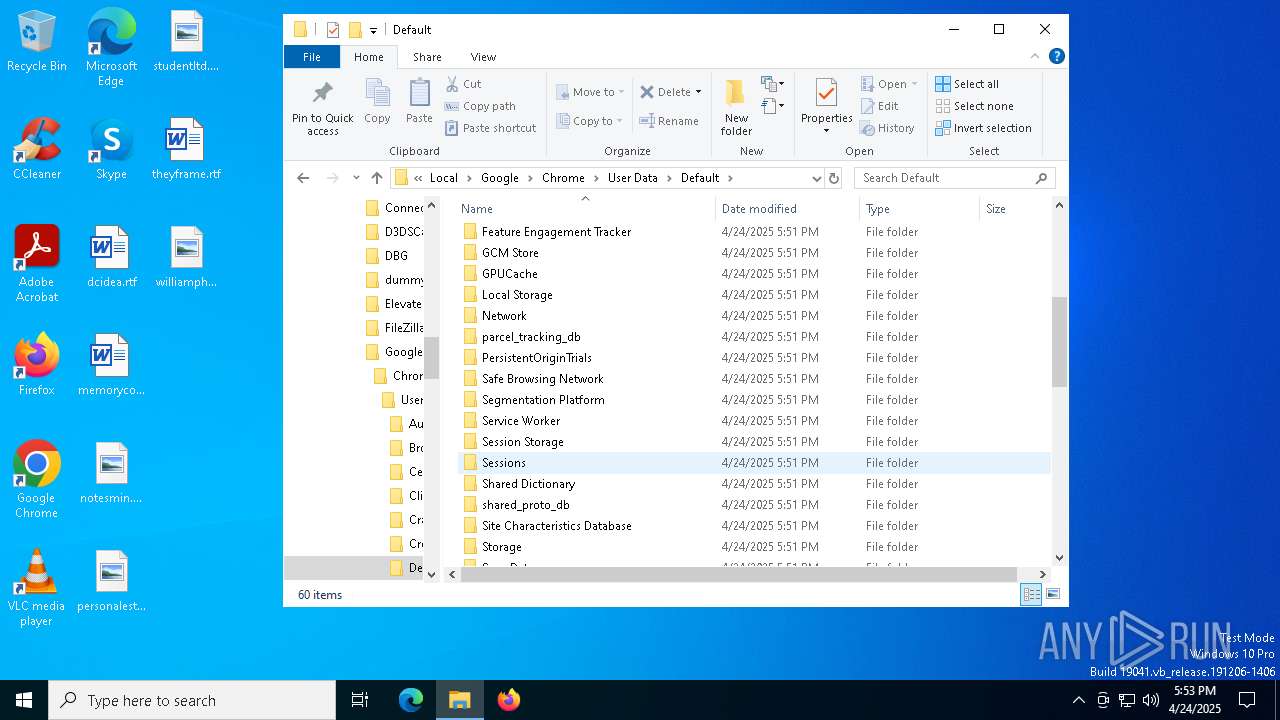
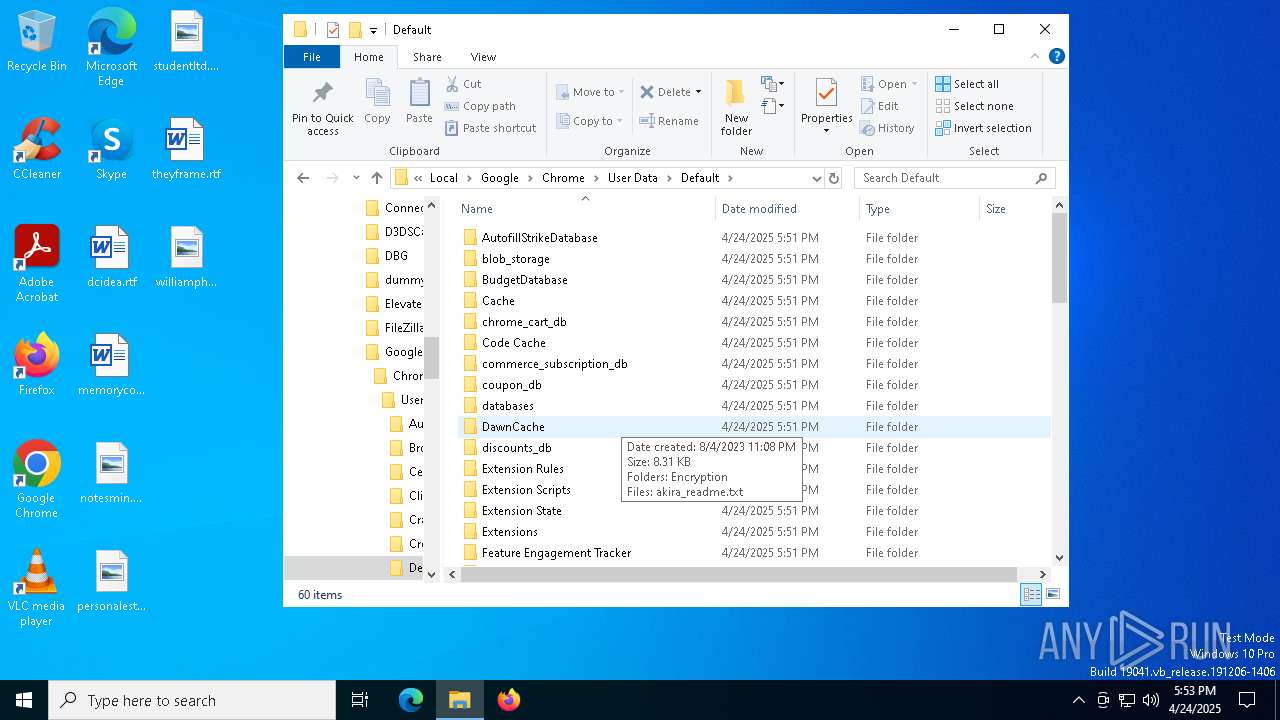
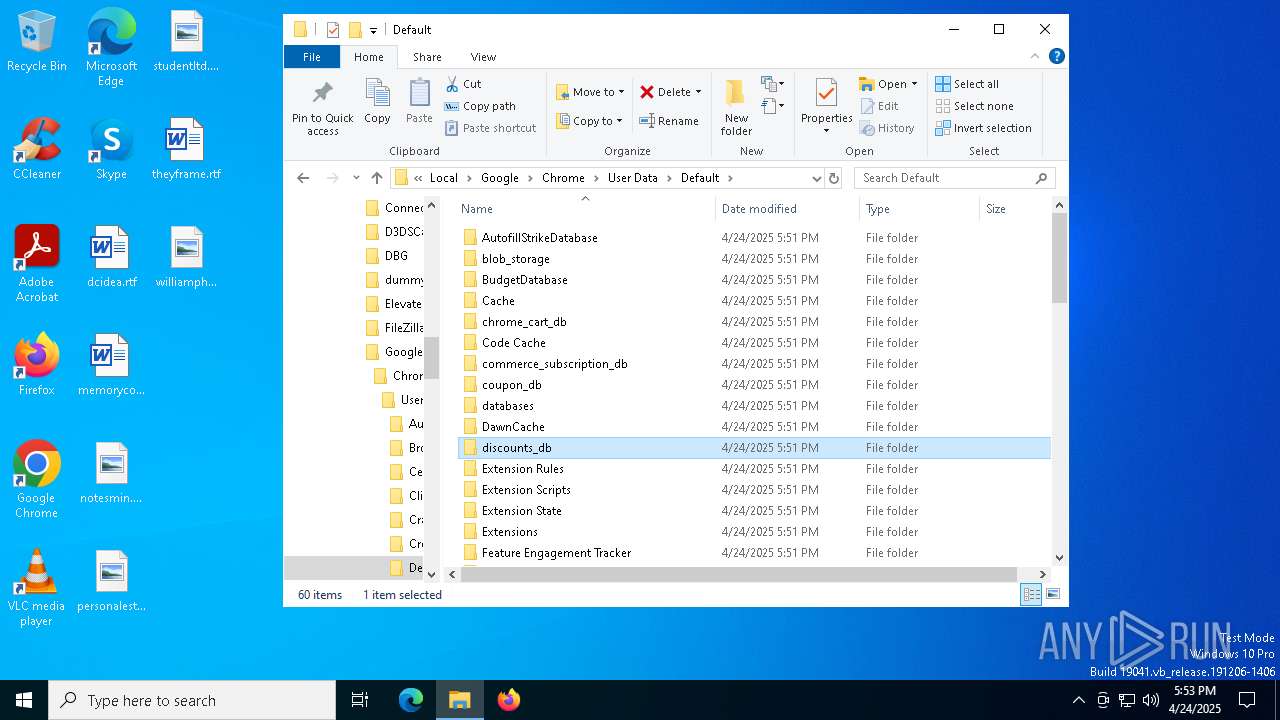
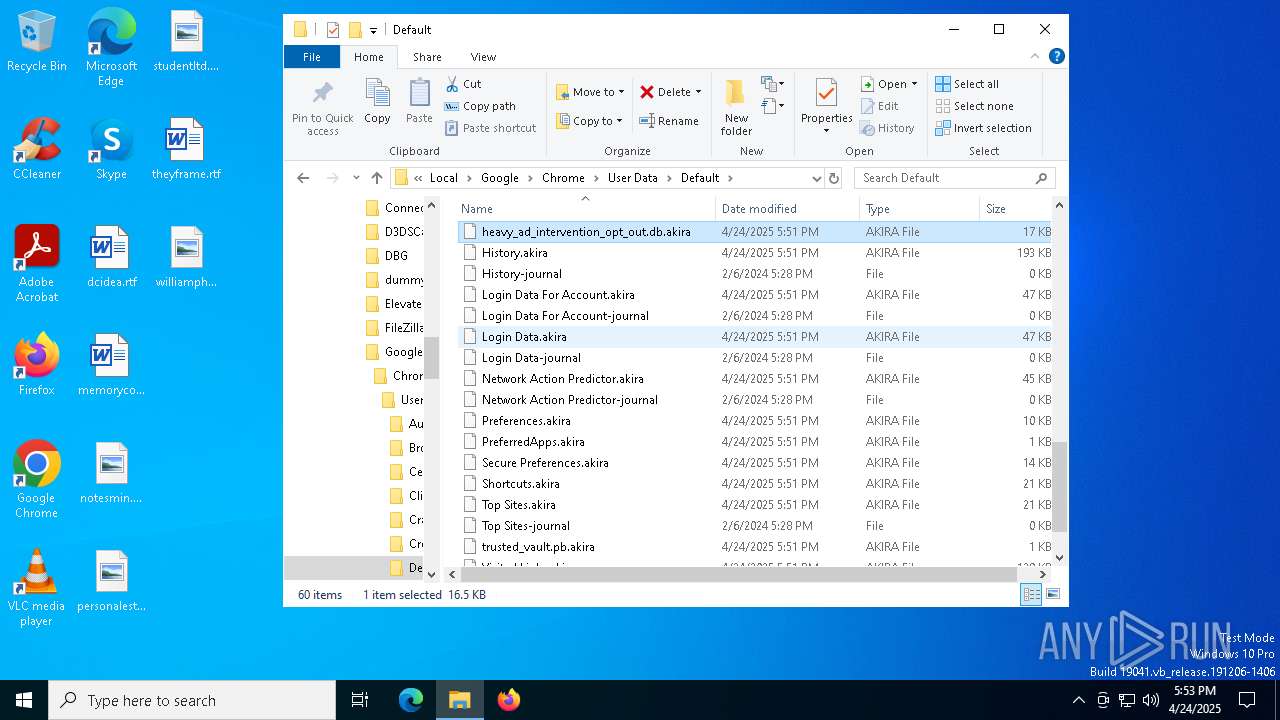
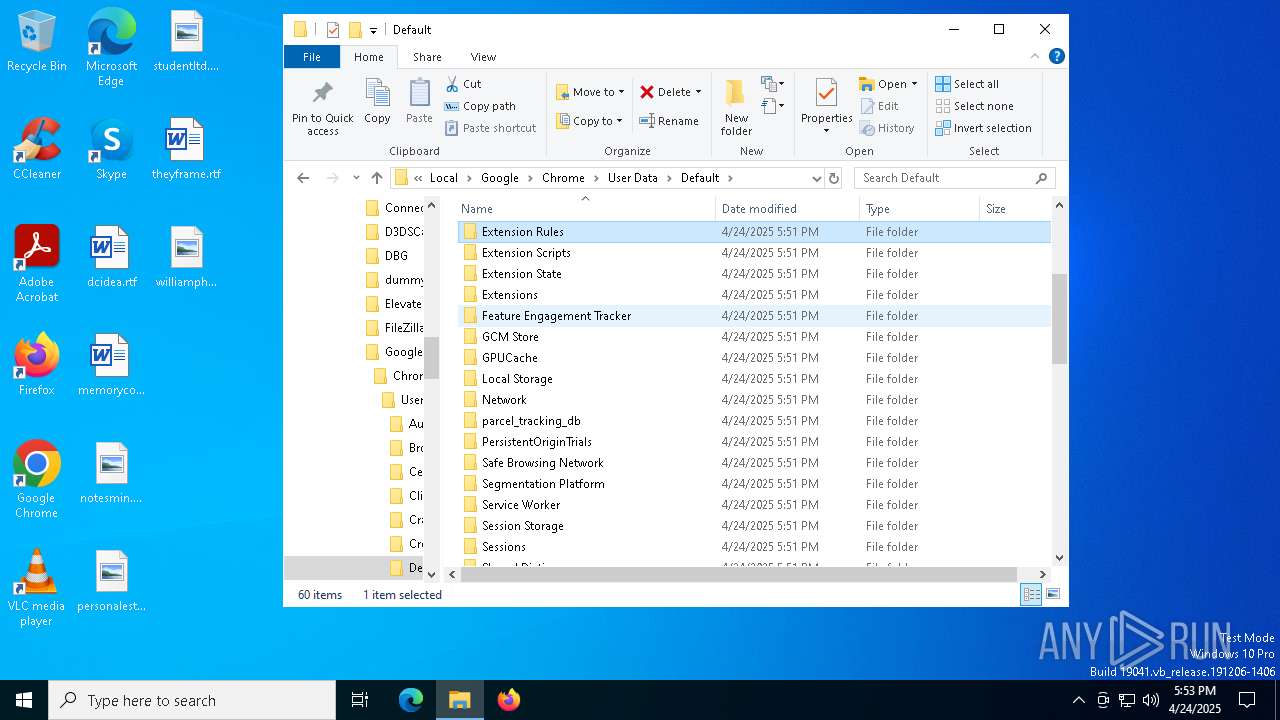
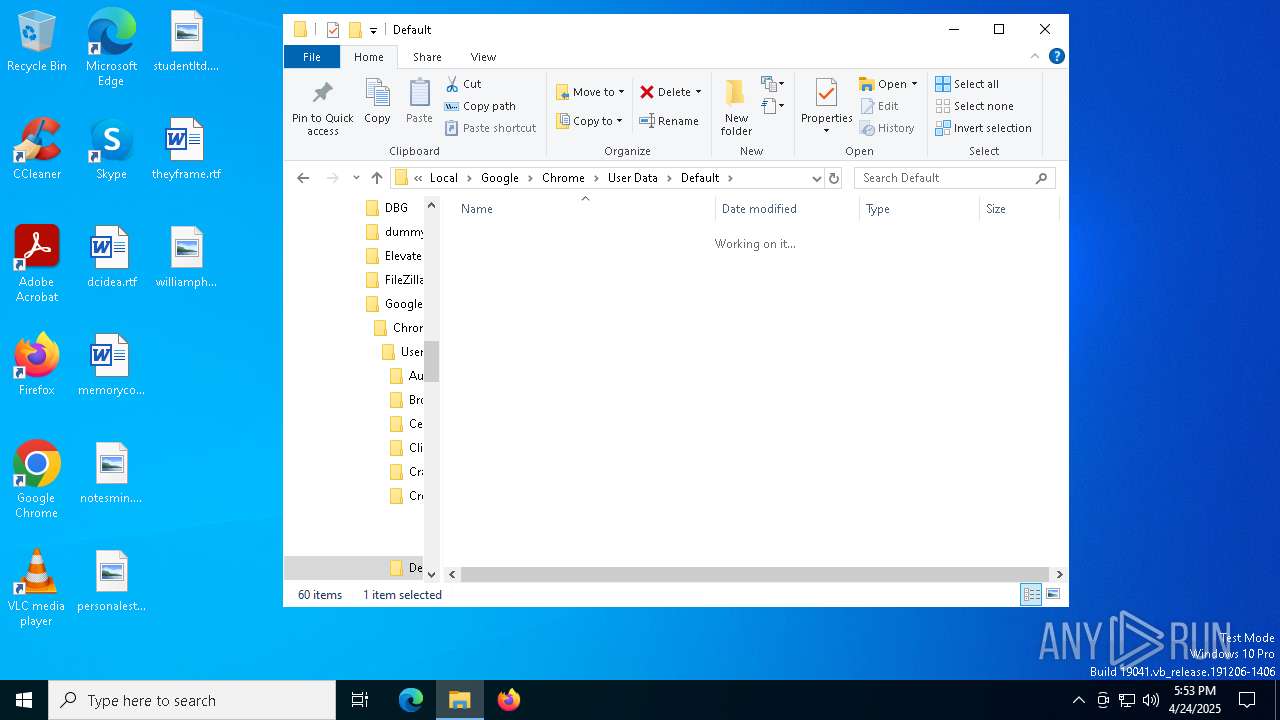
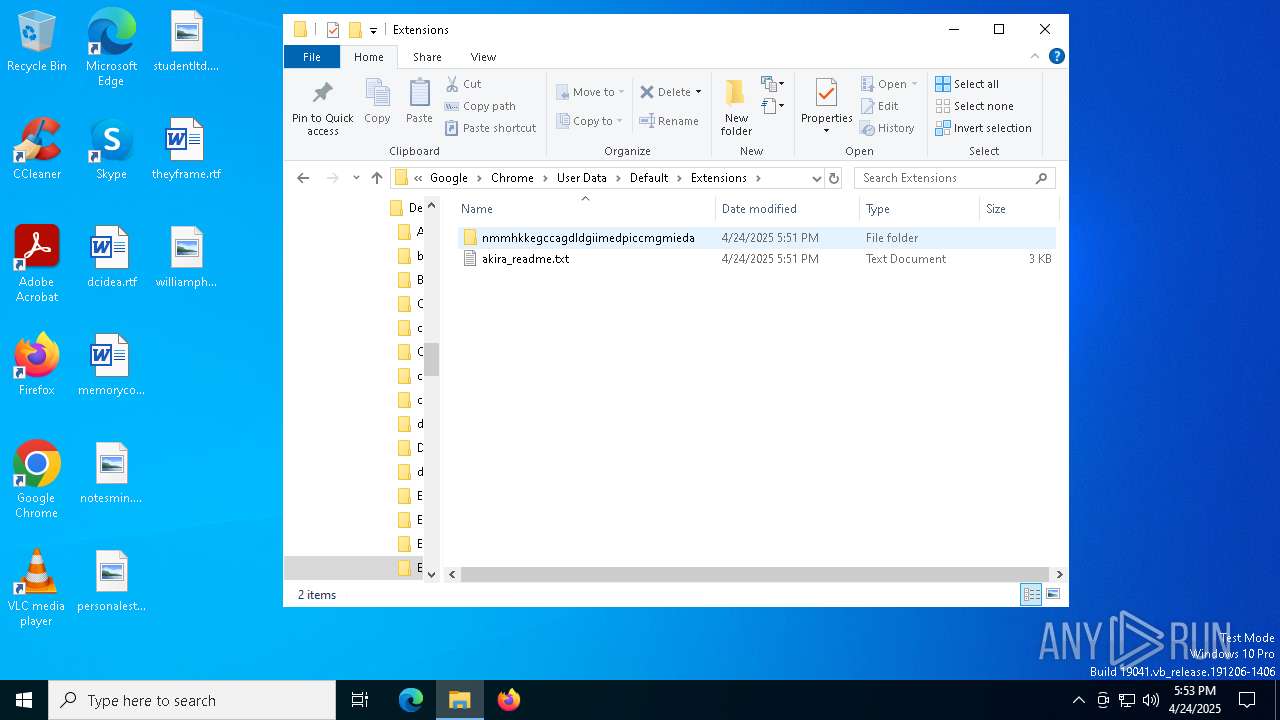
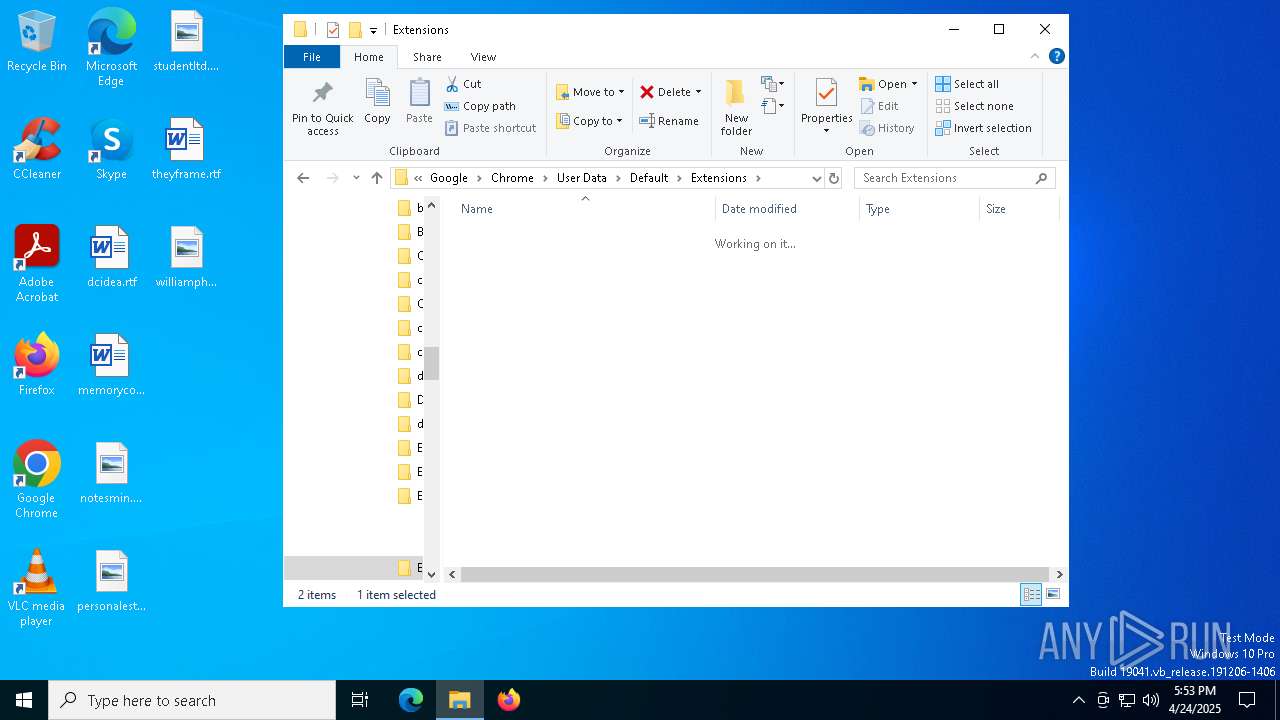
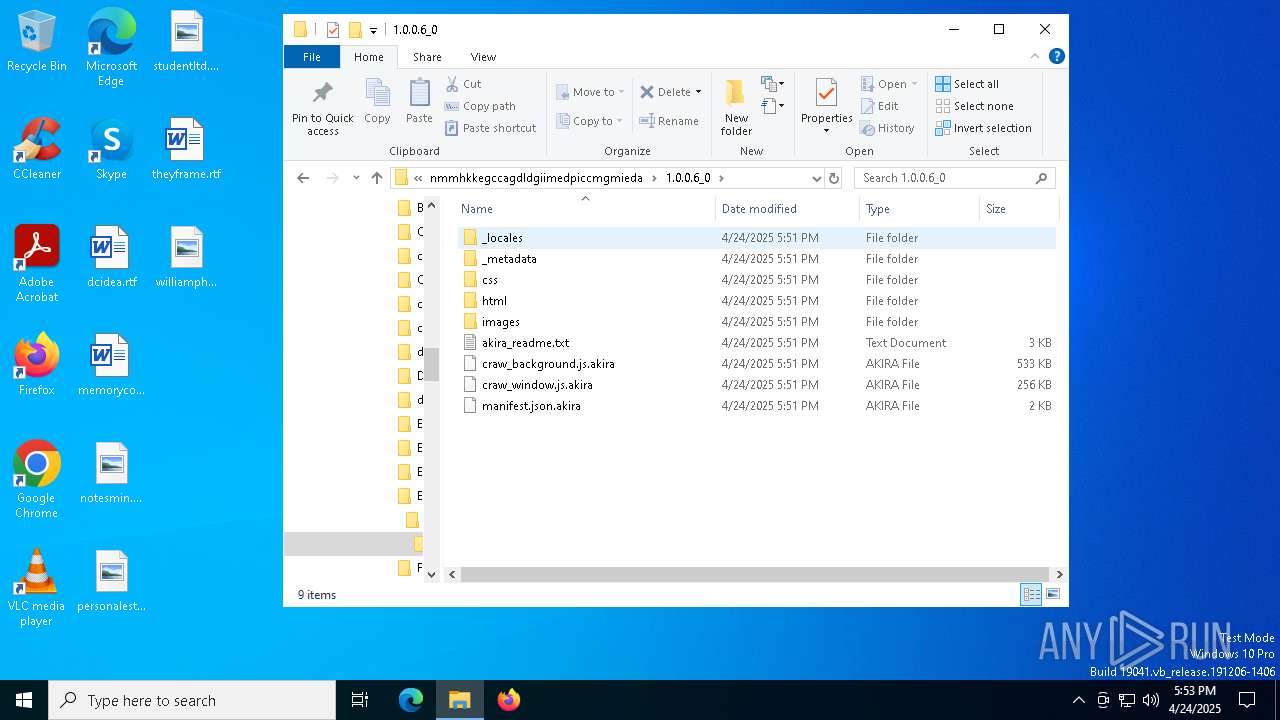
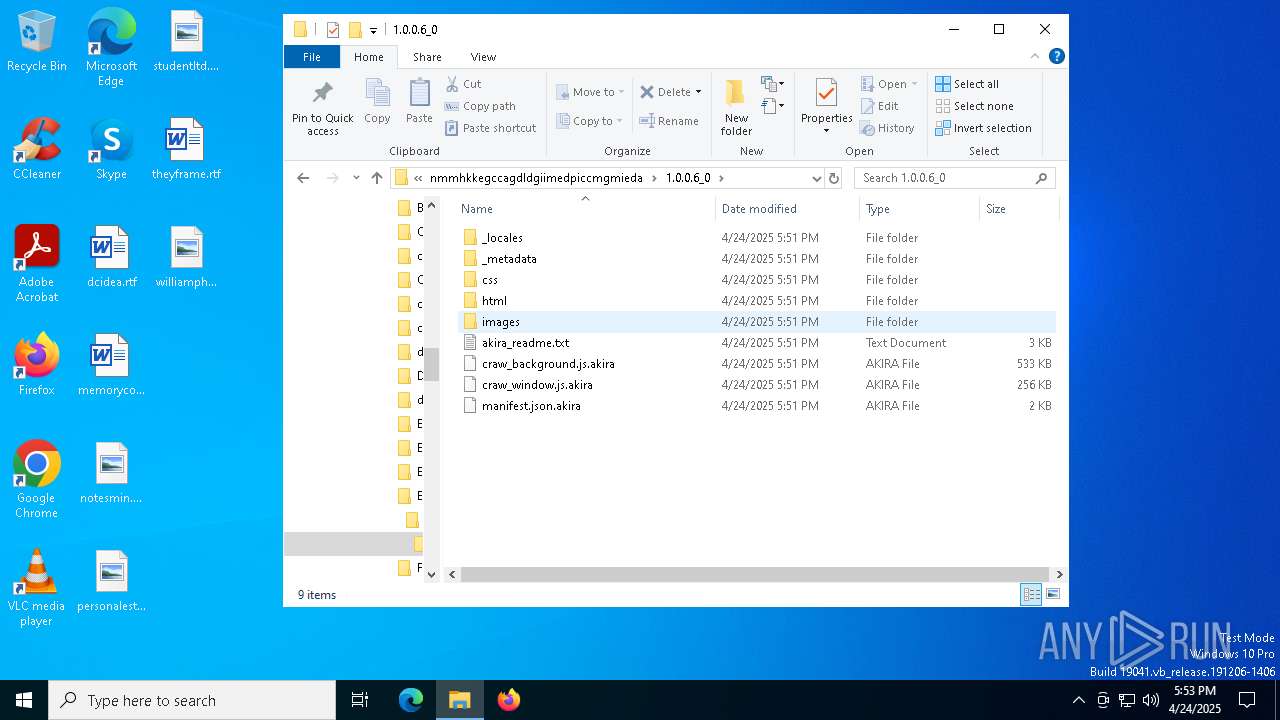
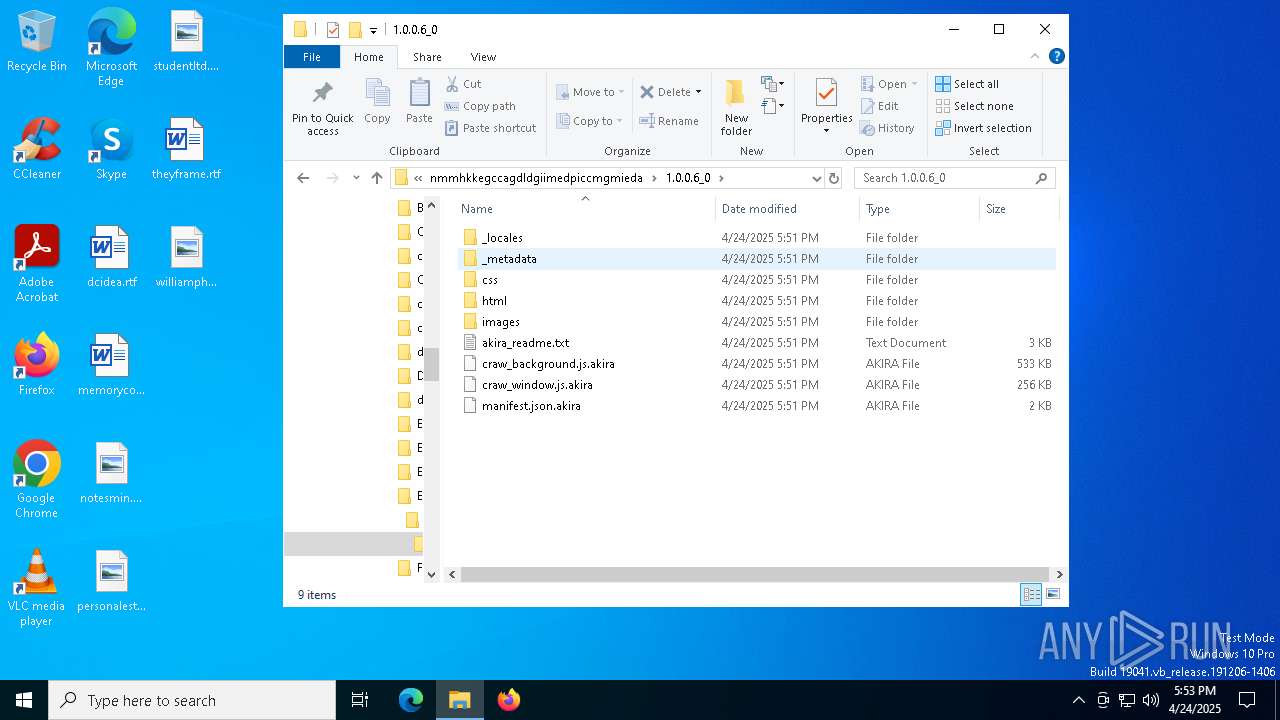
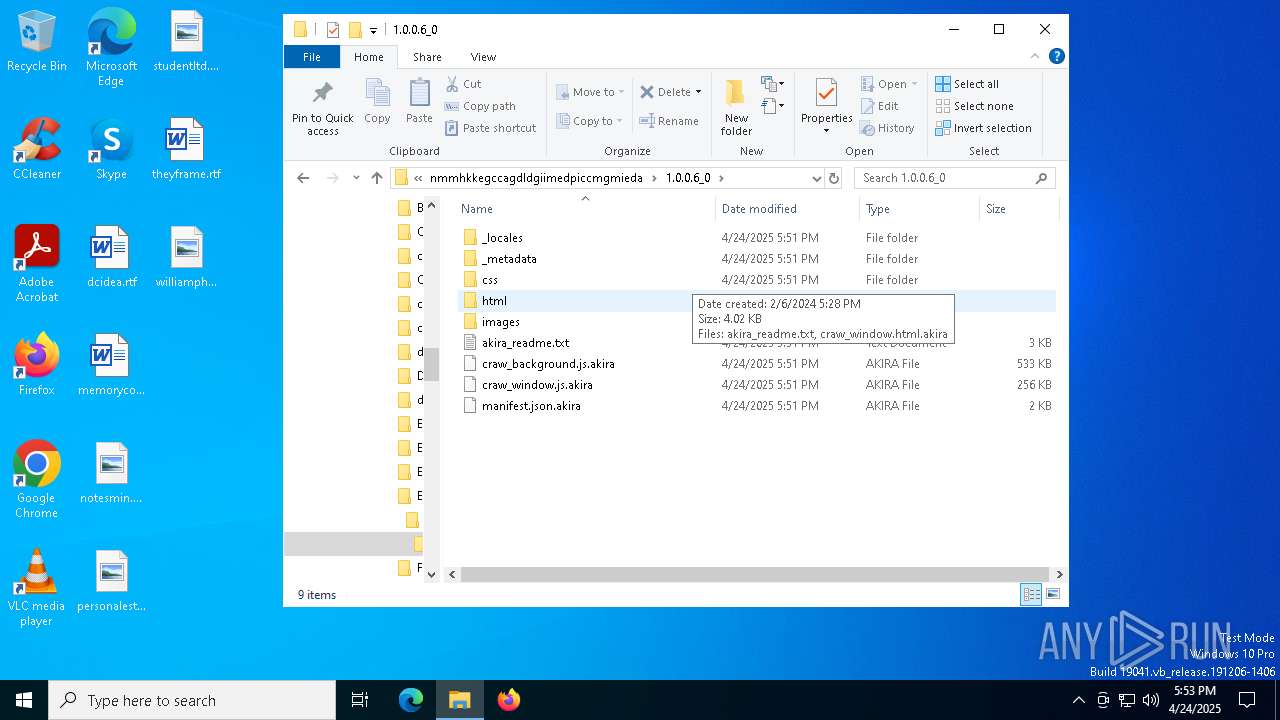
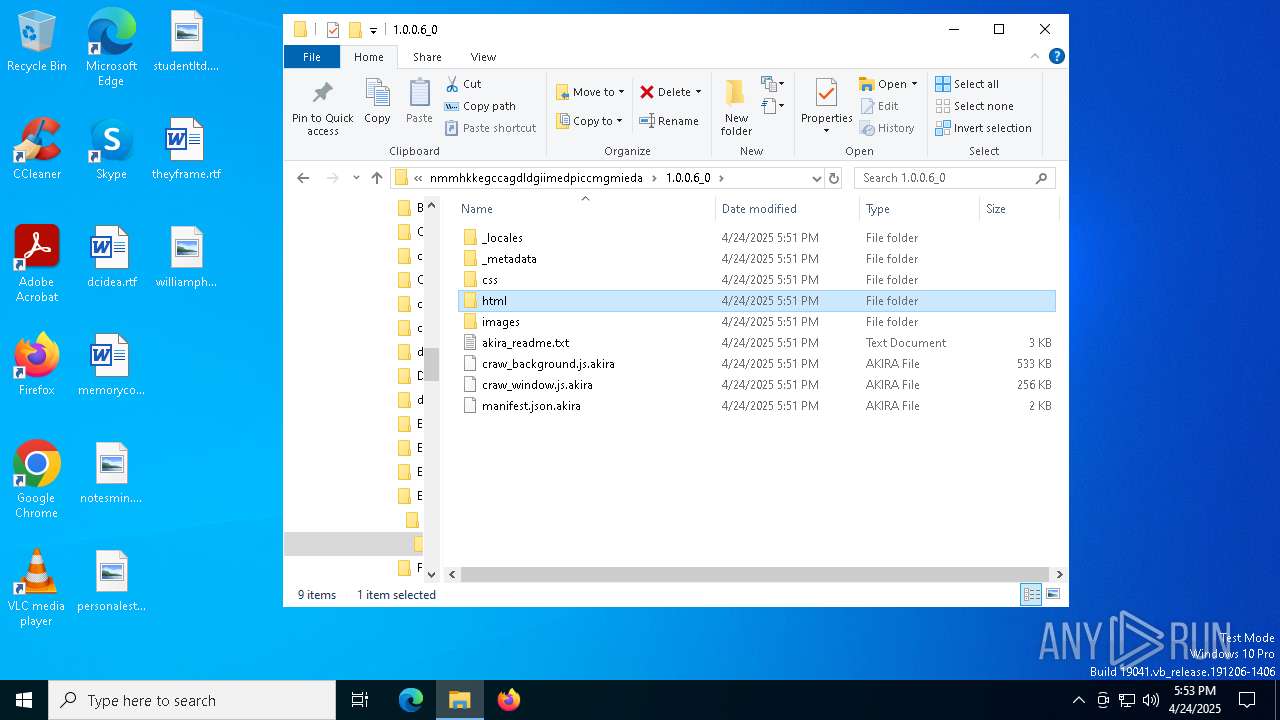
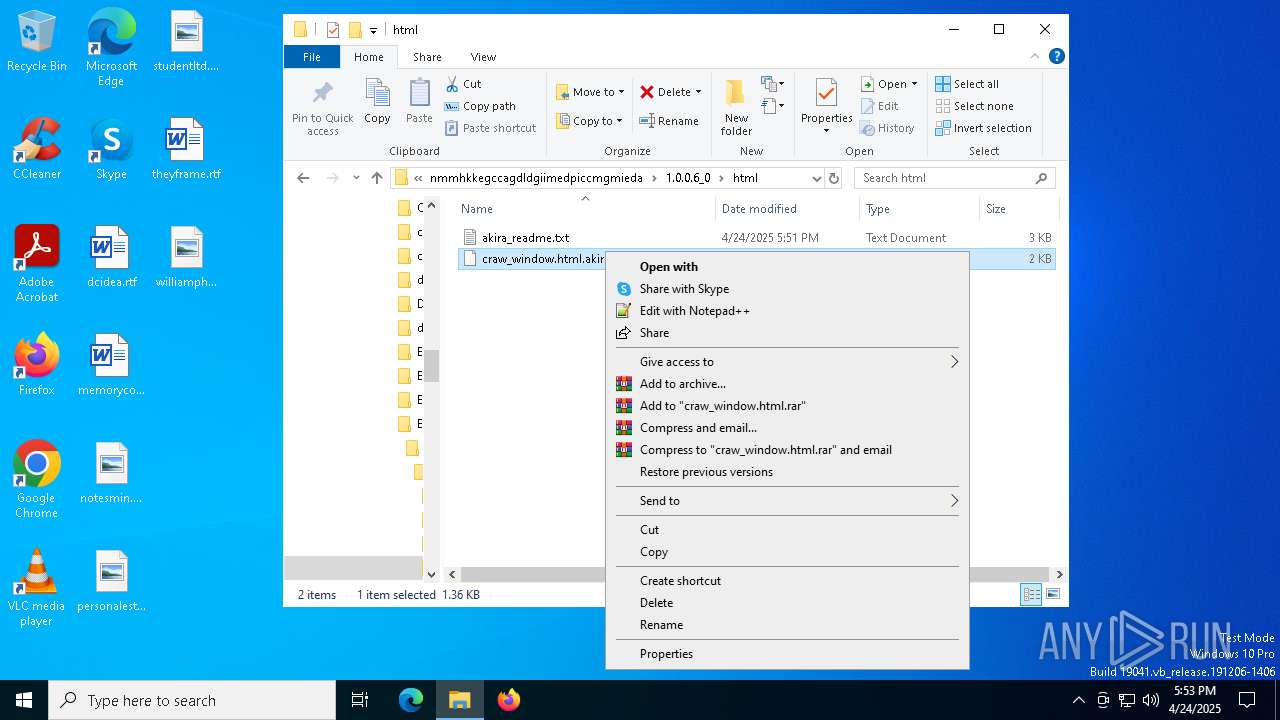
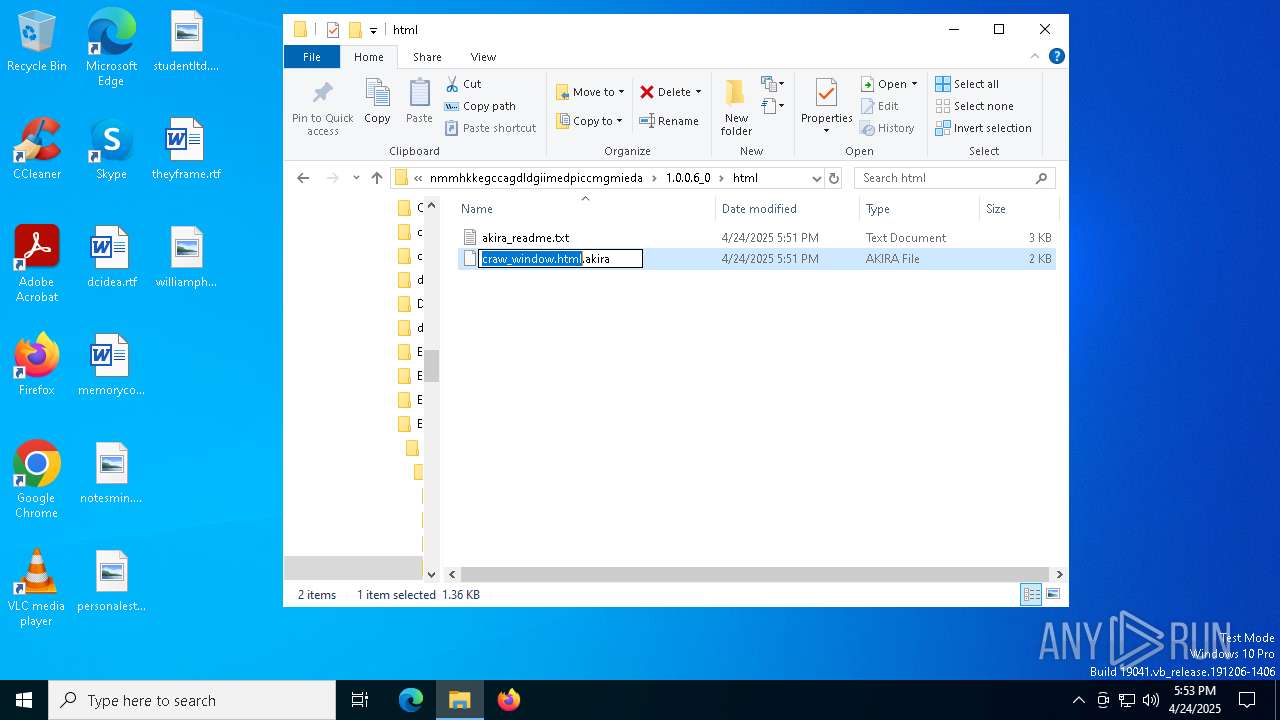
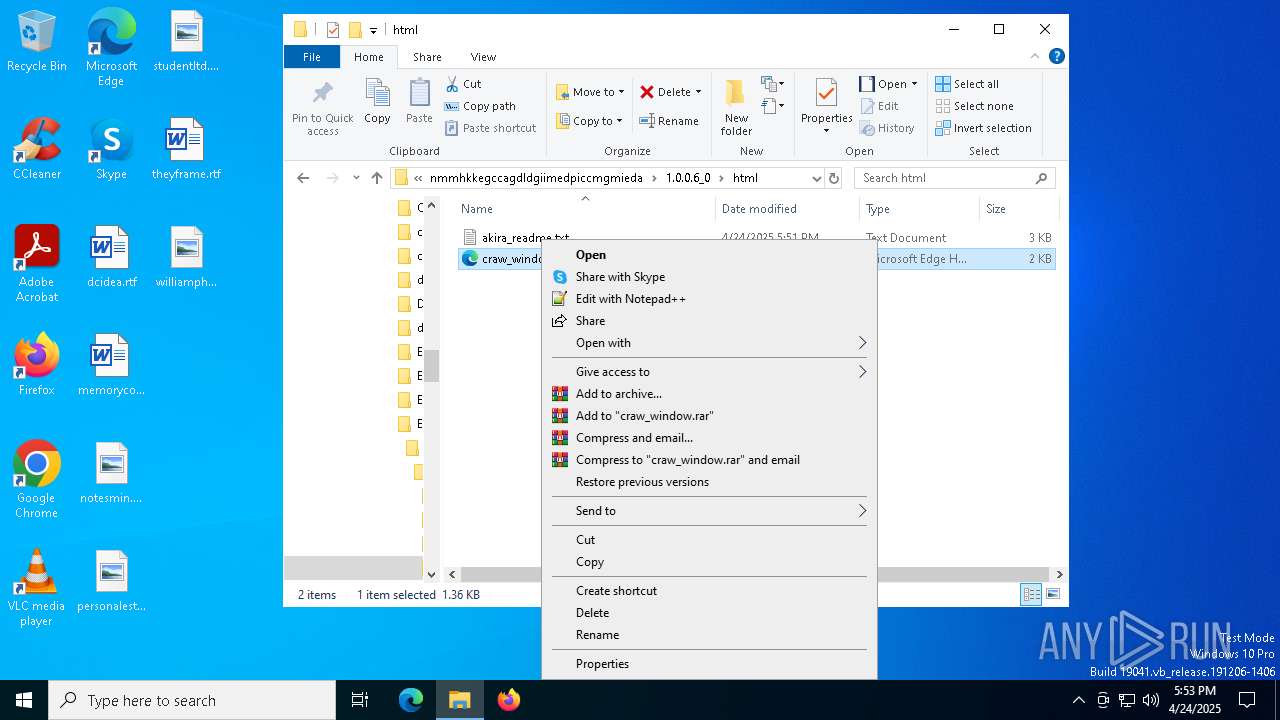
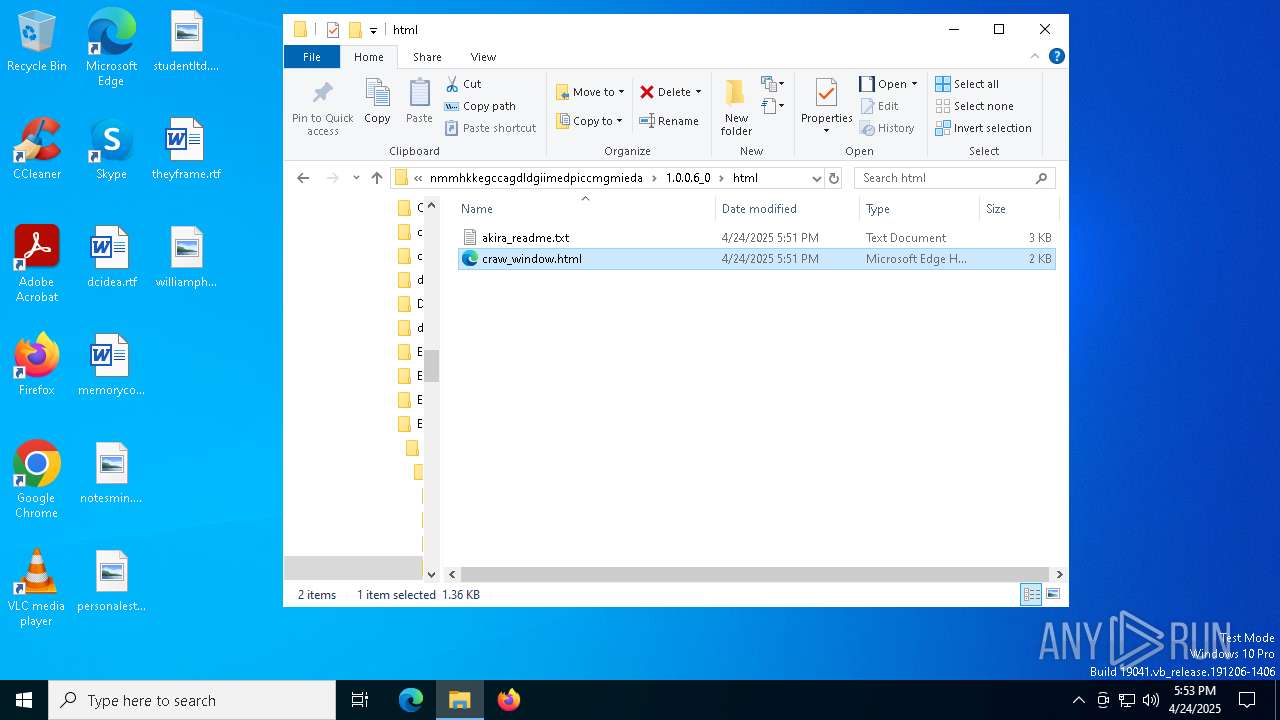
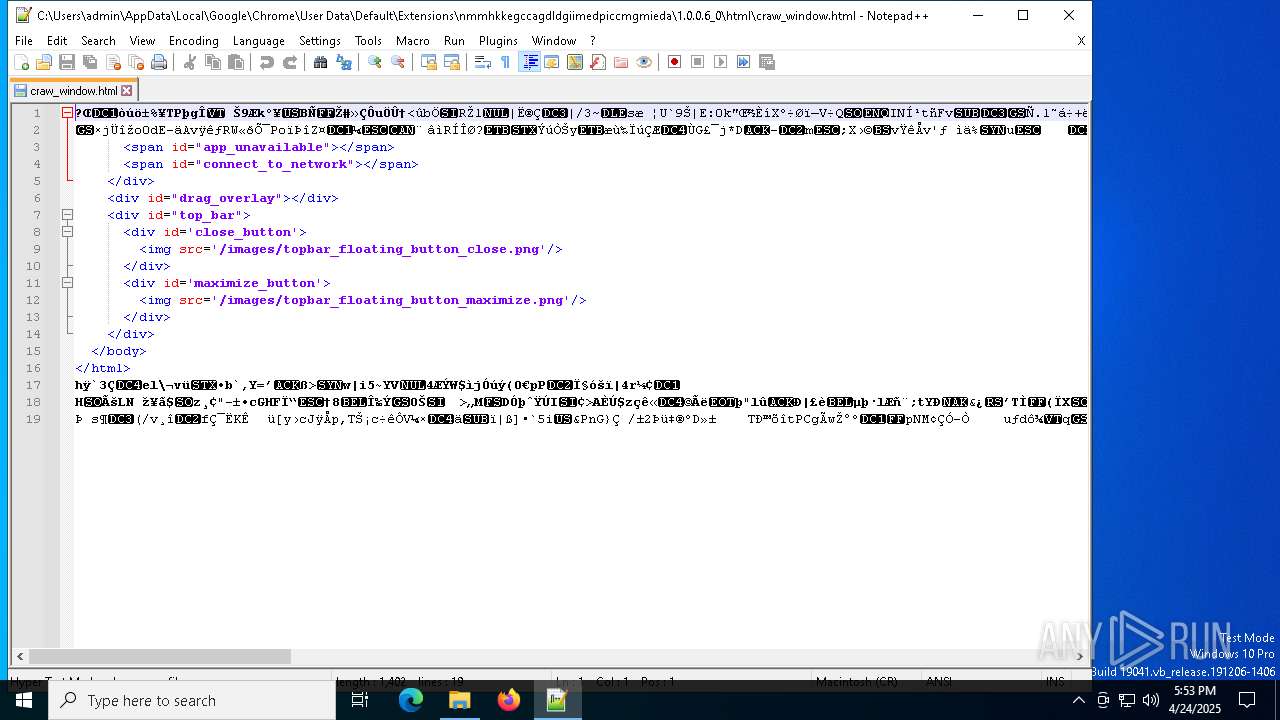
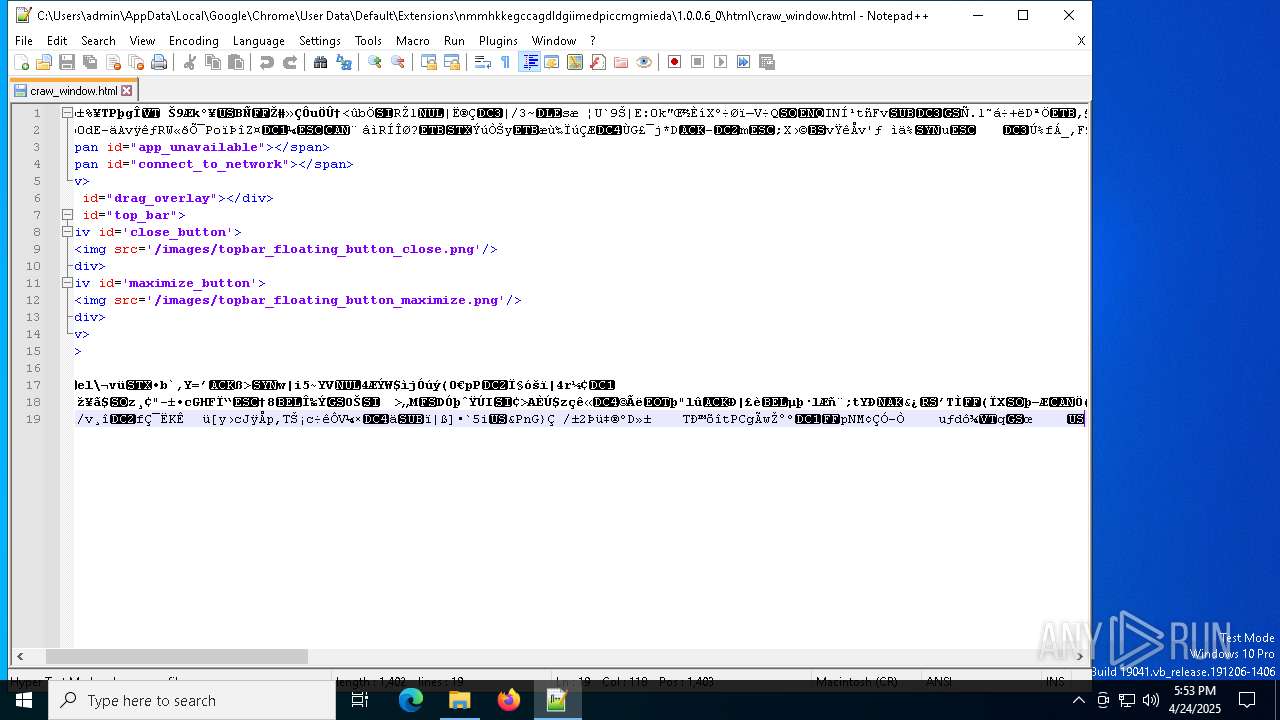
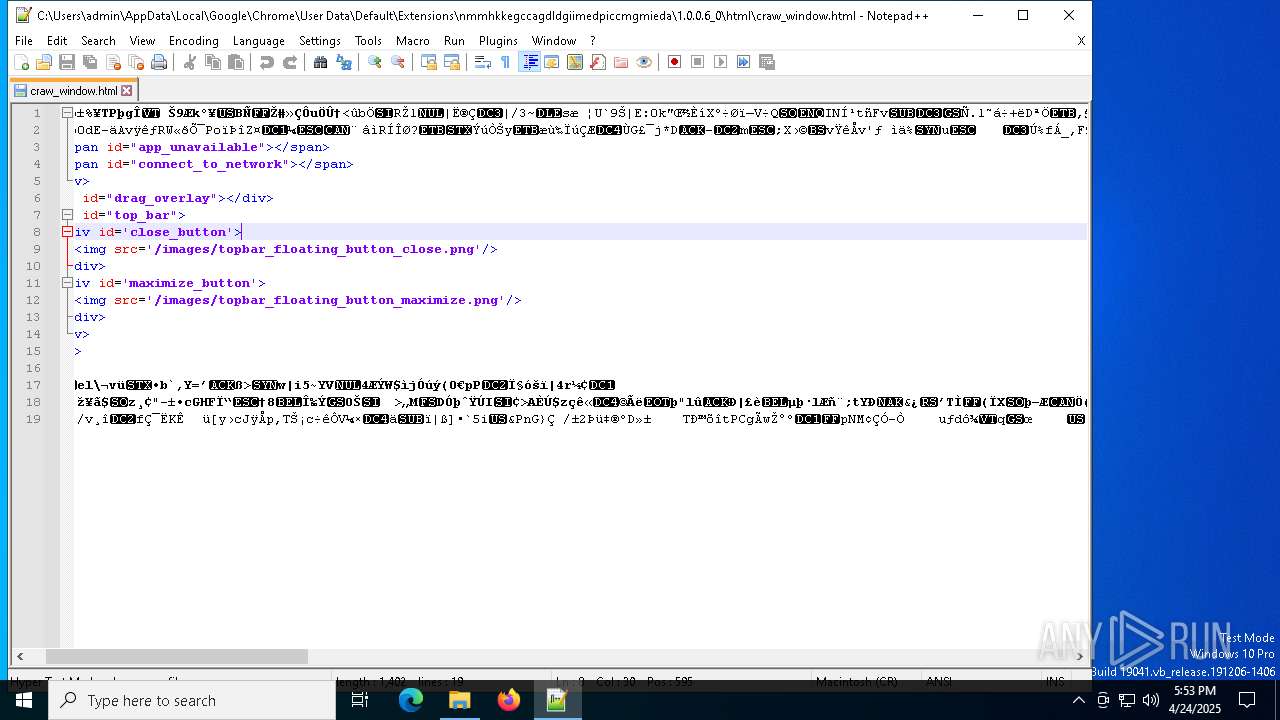
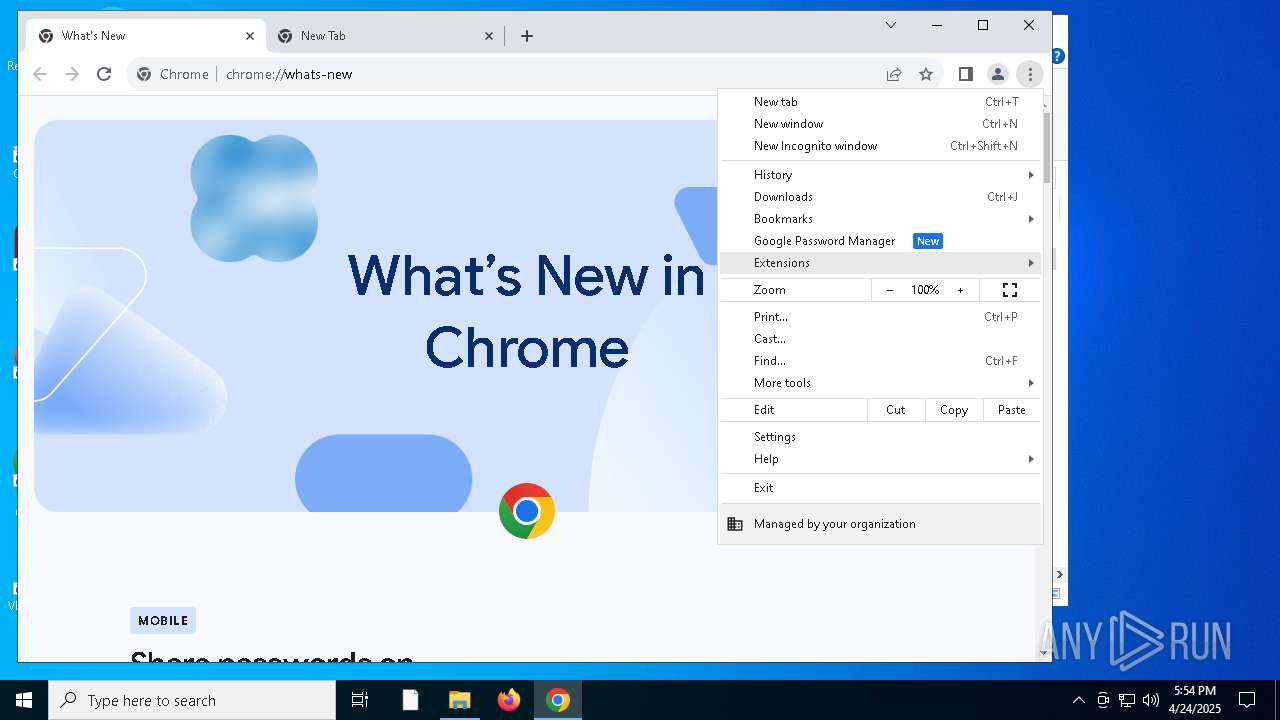
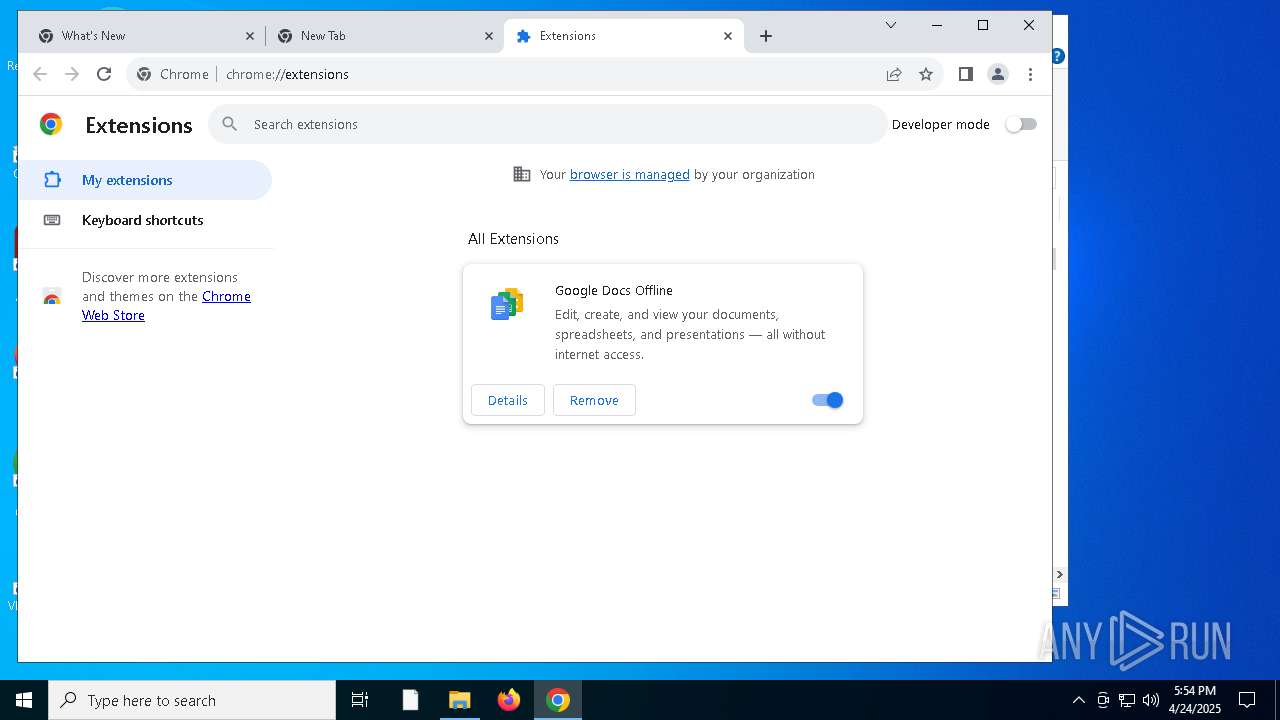
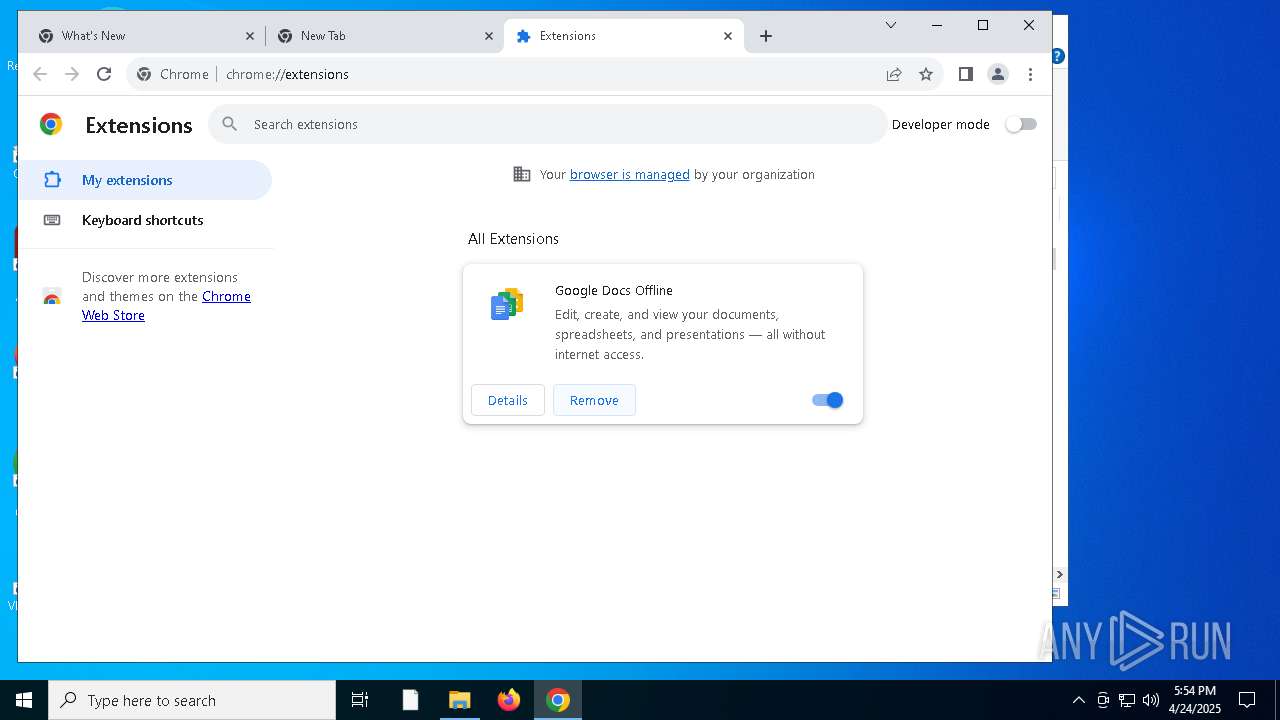
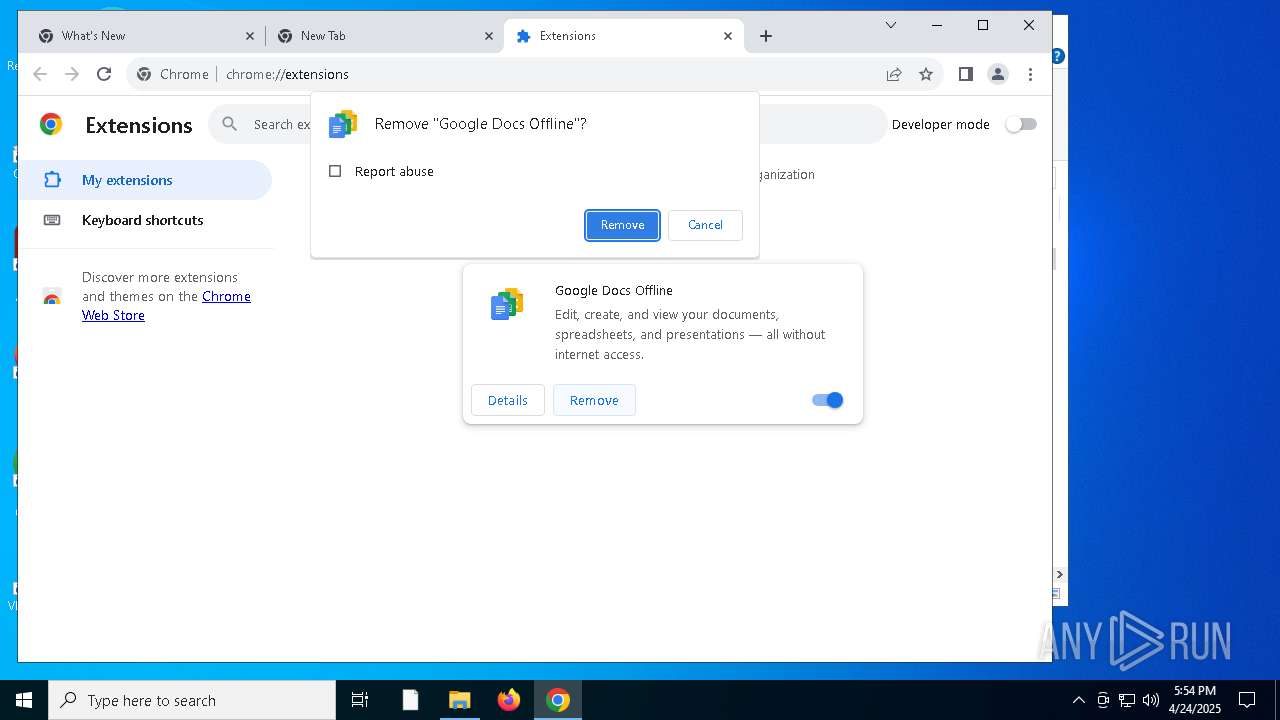
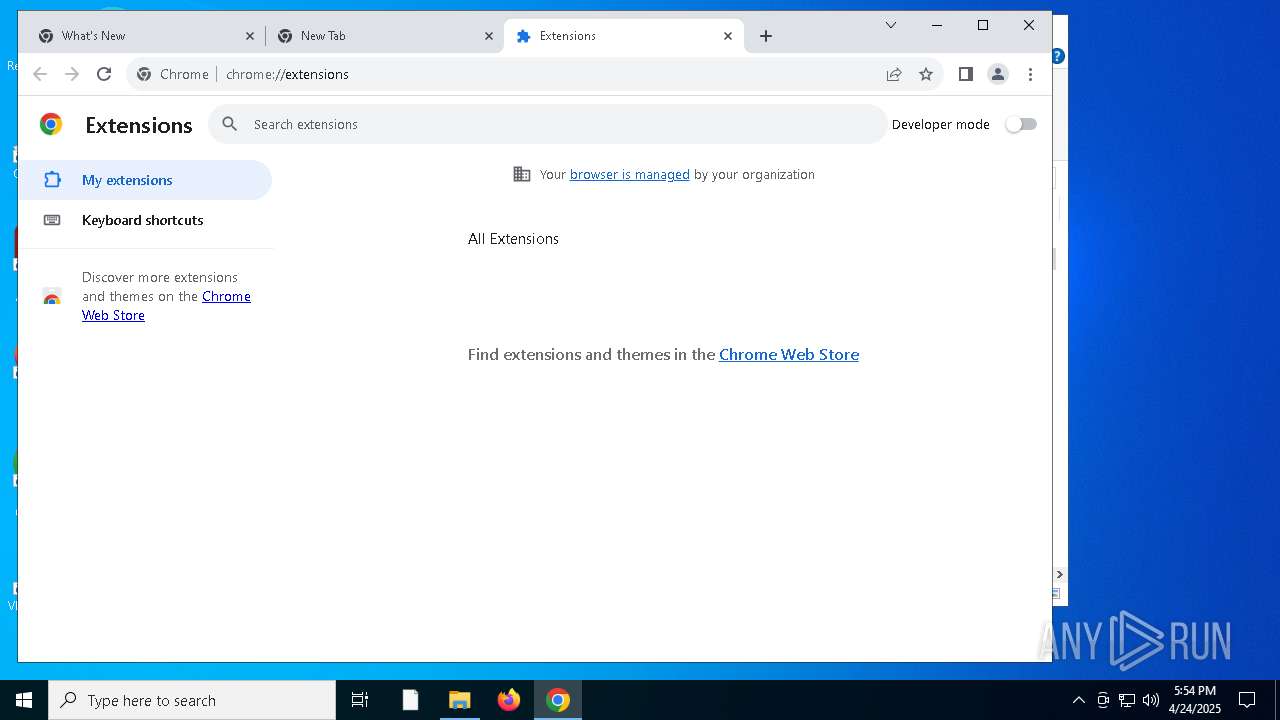
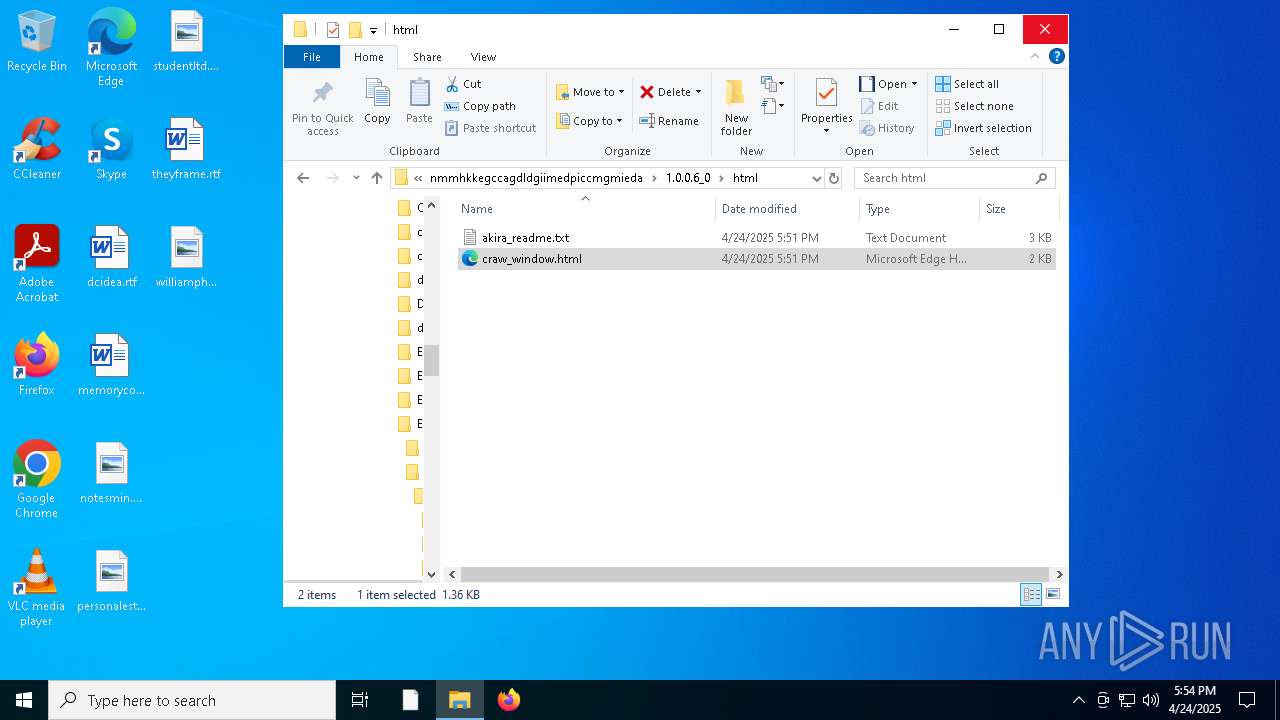
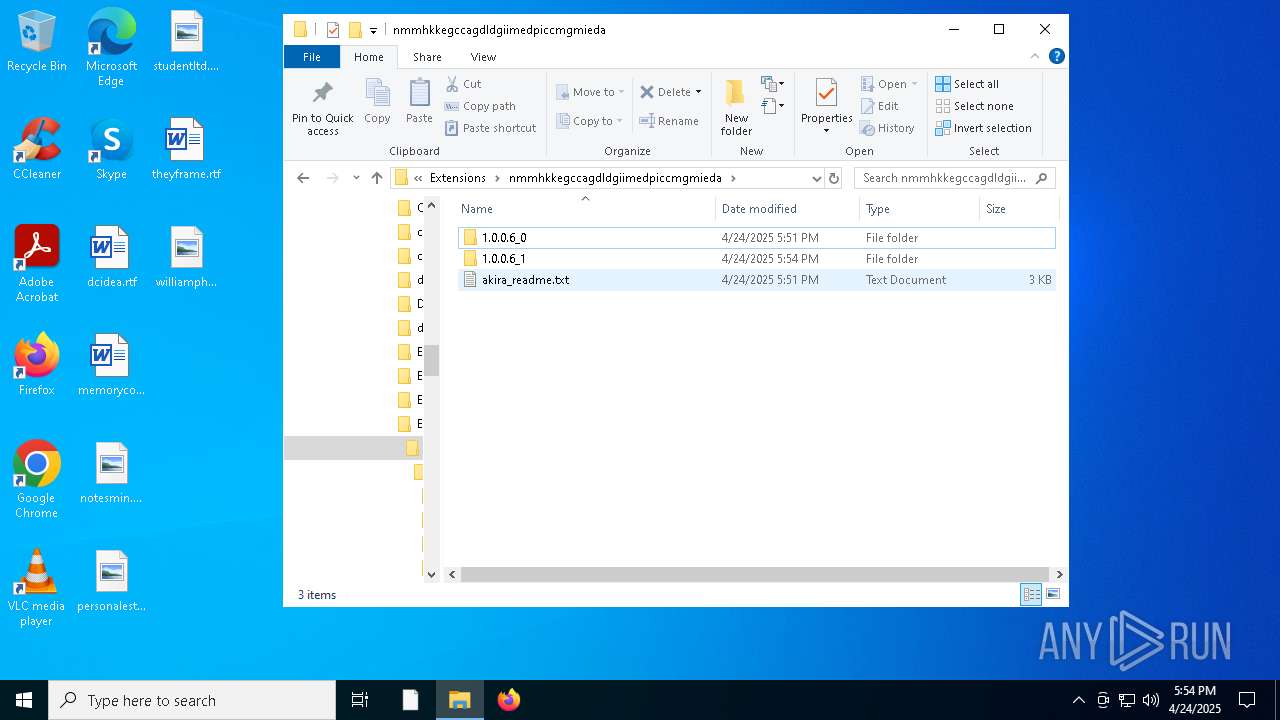
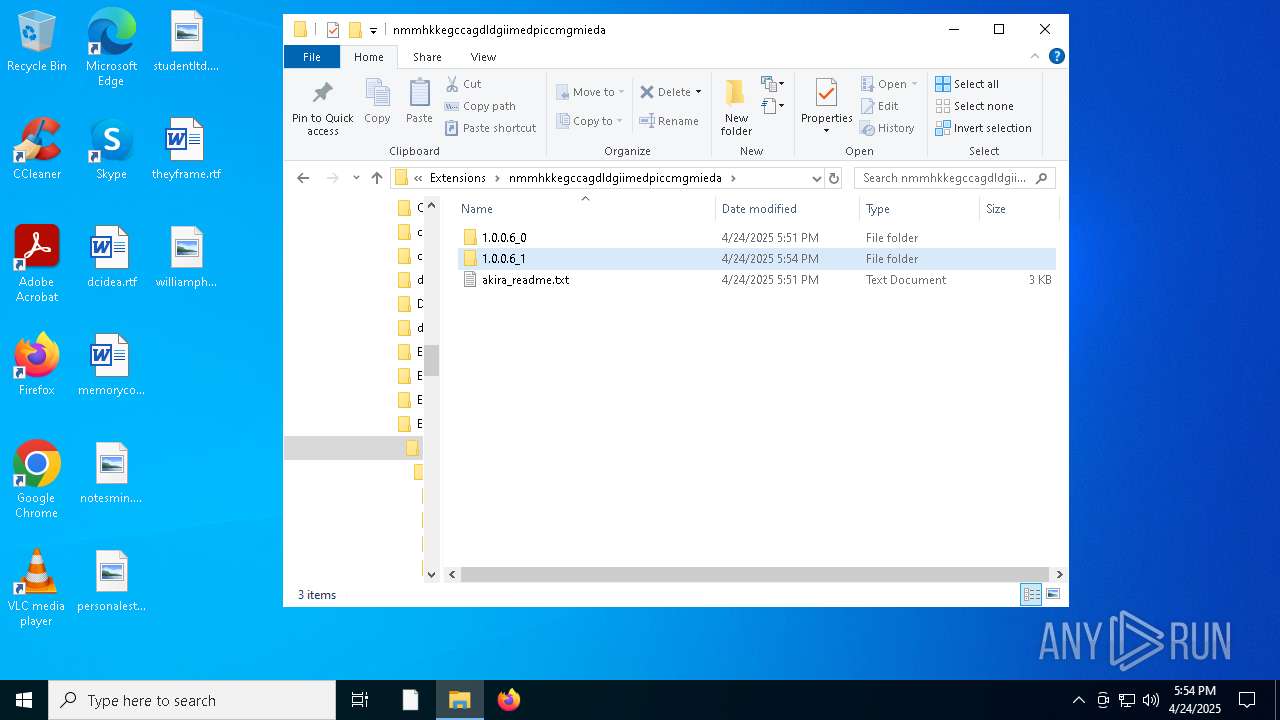
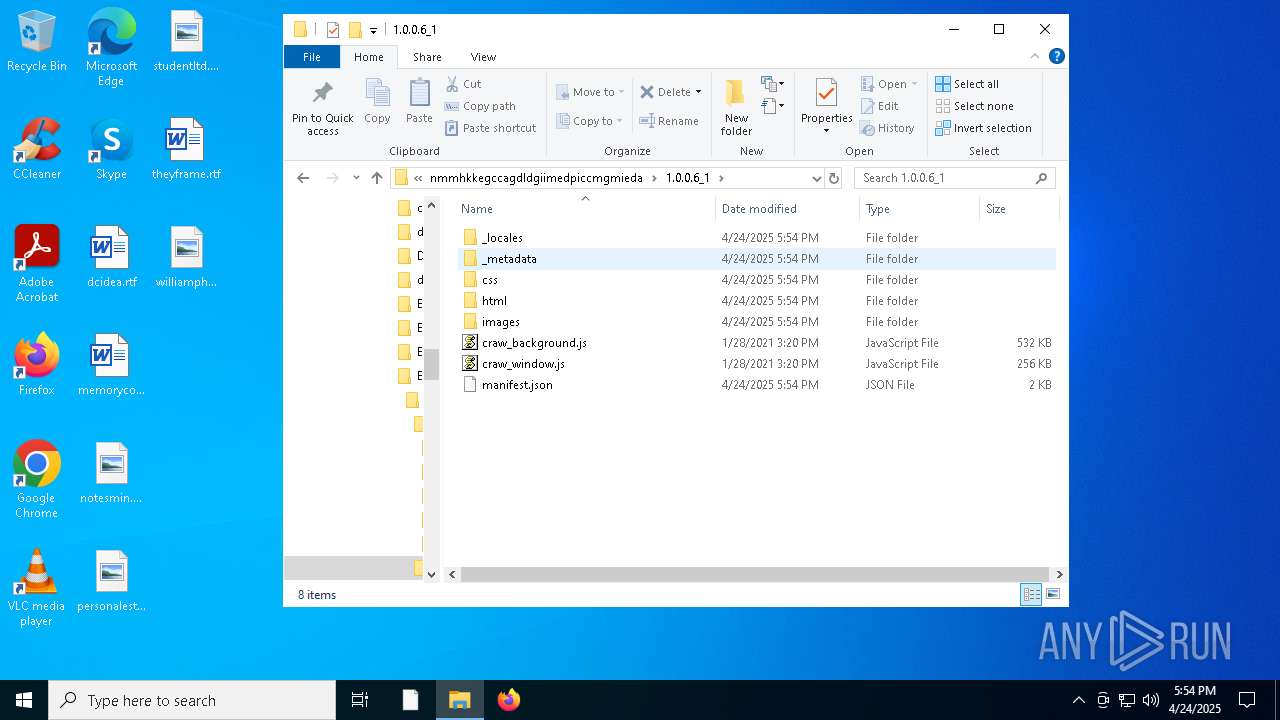
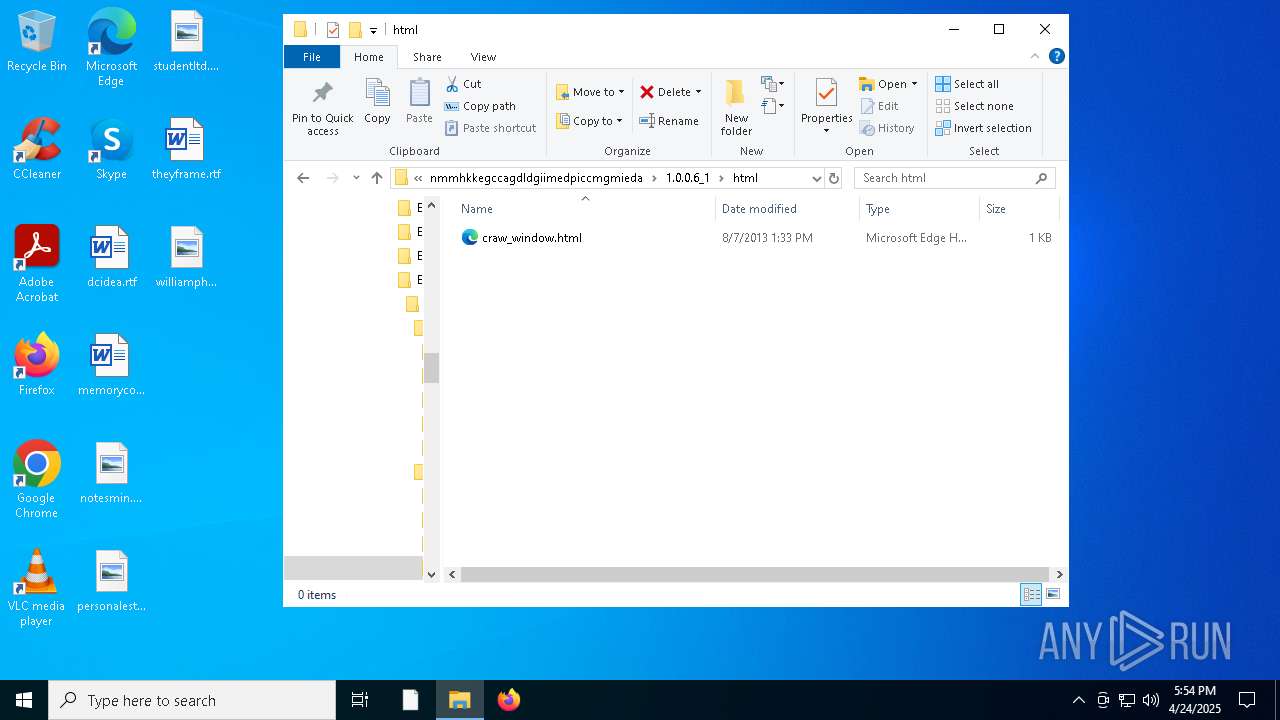
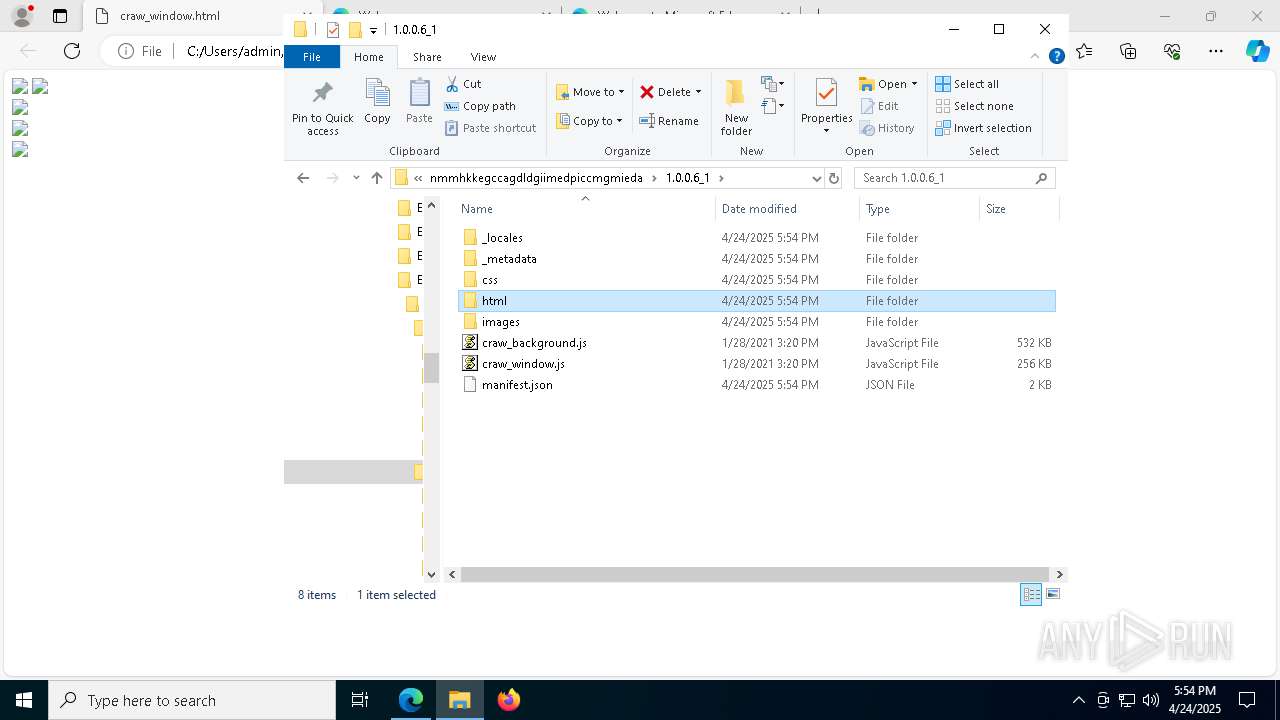
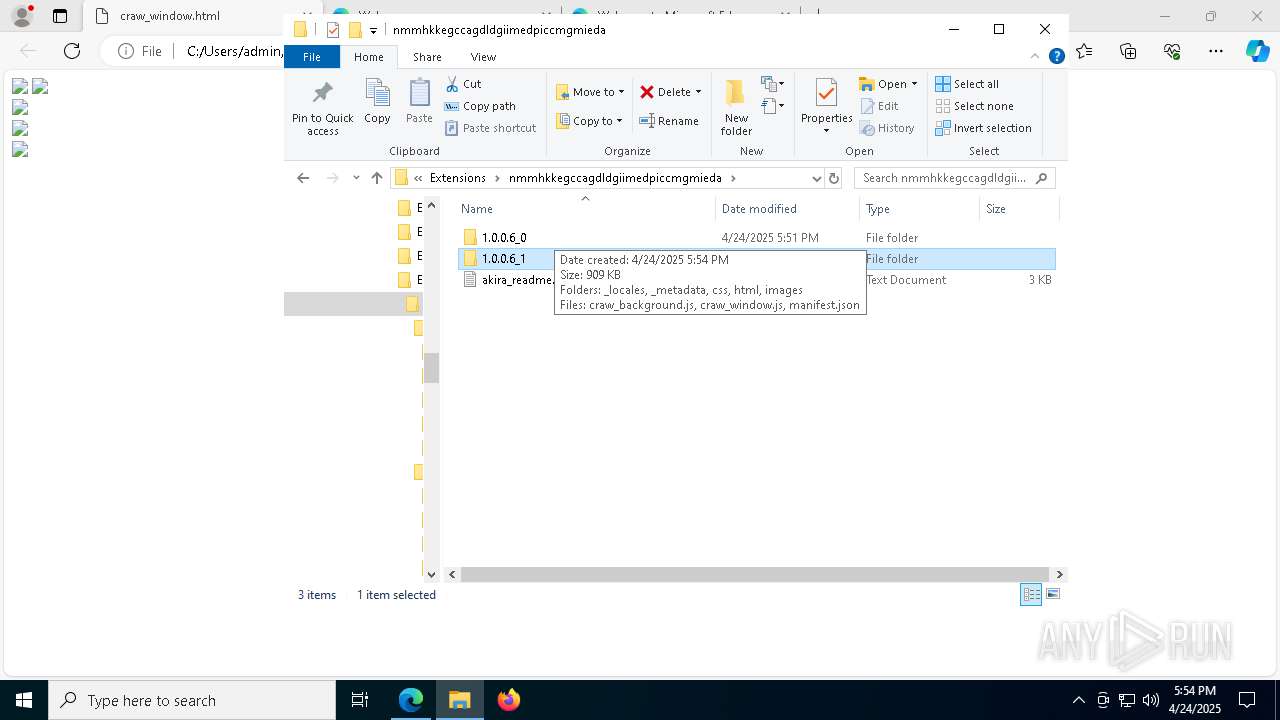
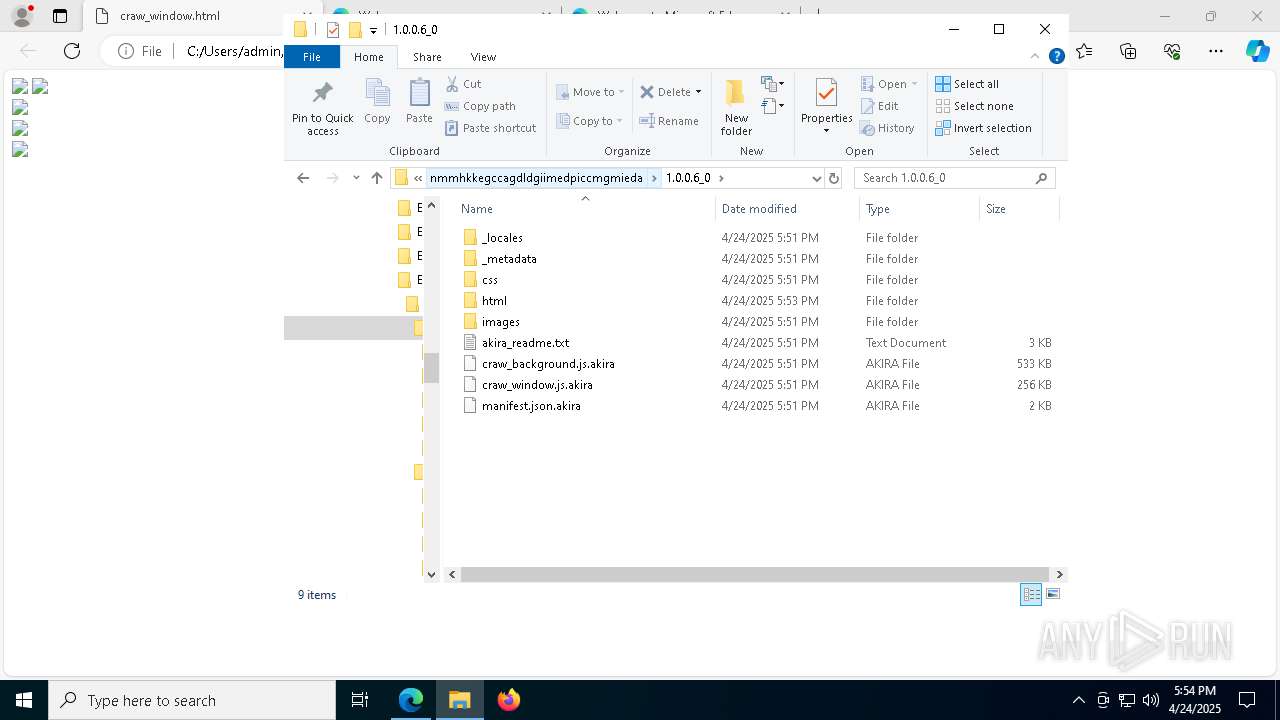
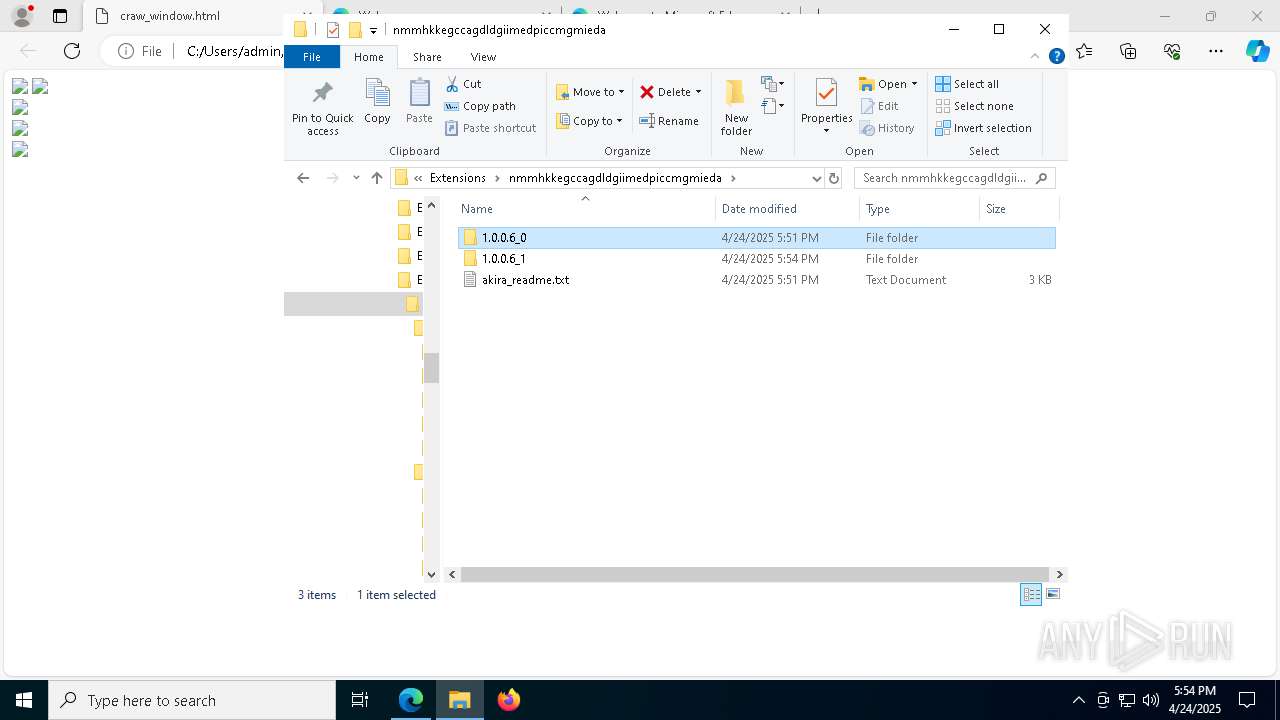
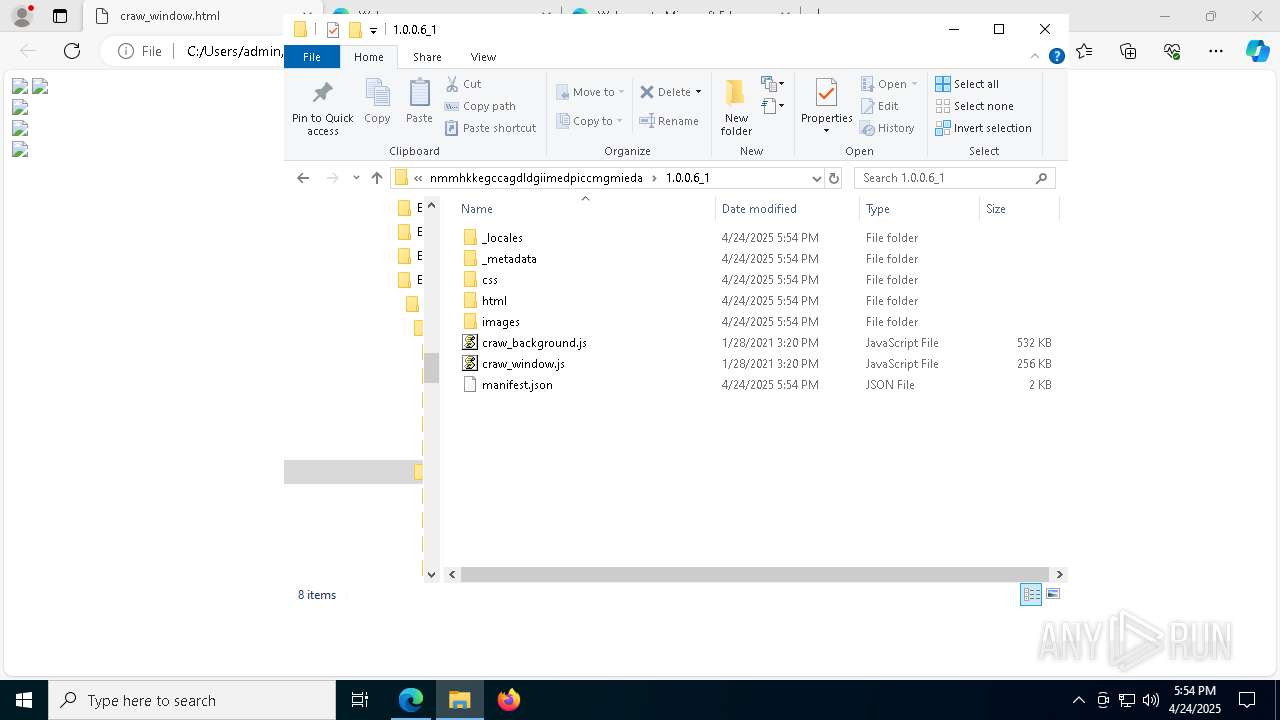
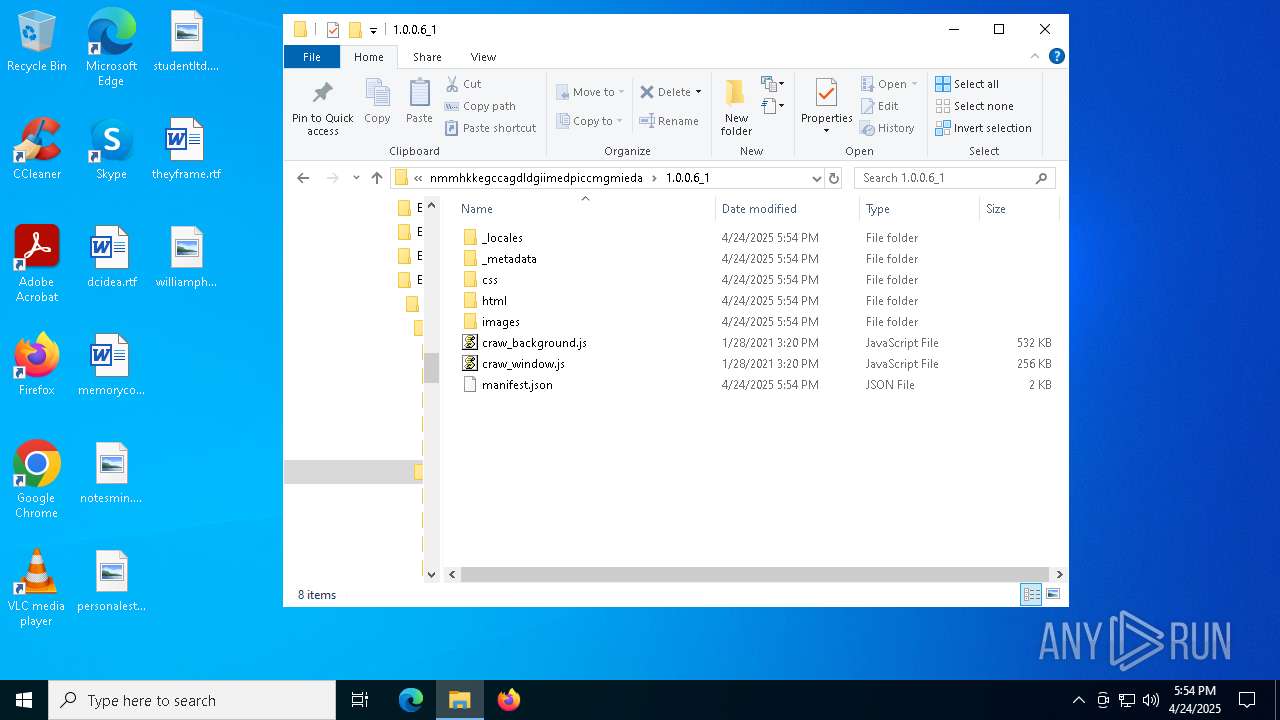
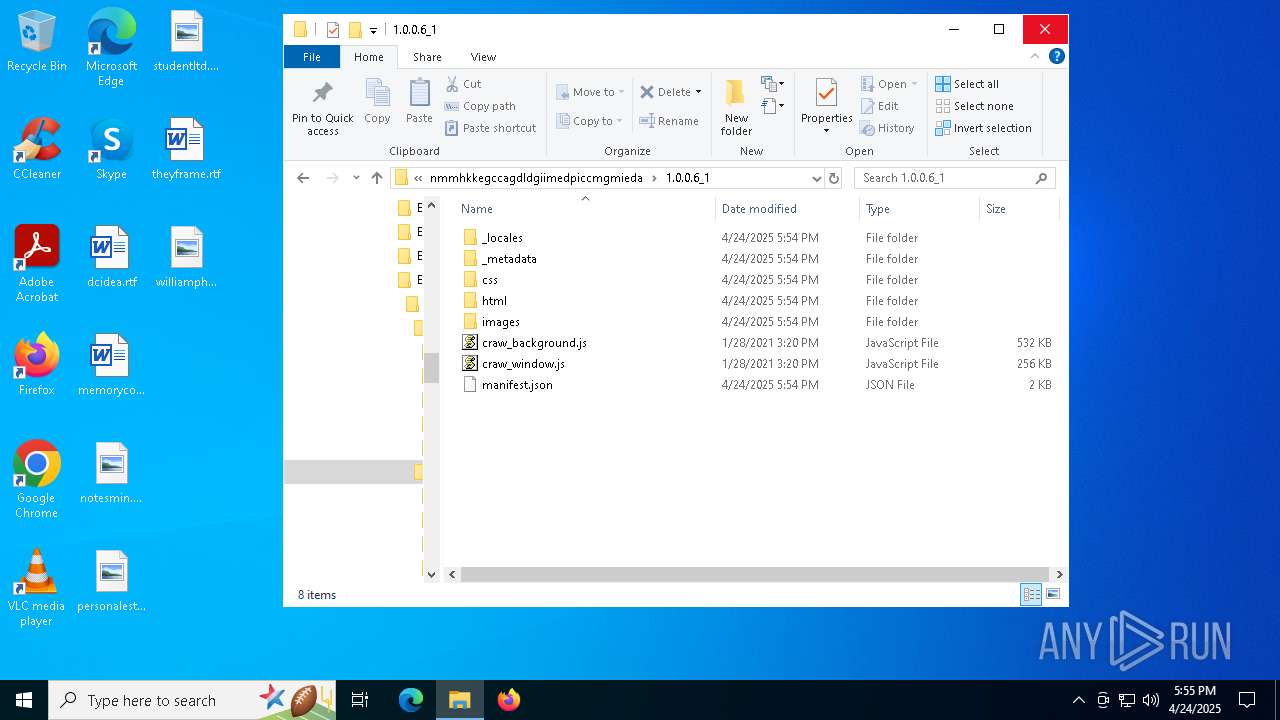
Modifies files in the Chrome extension folder
- win.exe (PID: 7264)
AKIRA has been detected (YARA)
- win.exe (PID: 7264)
SUSPICIOUS
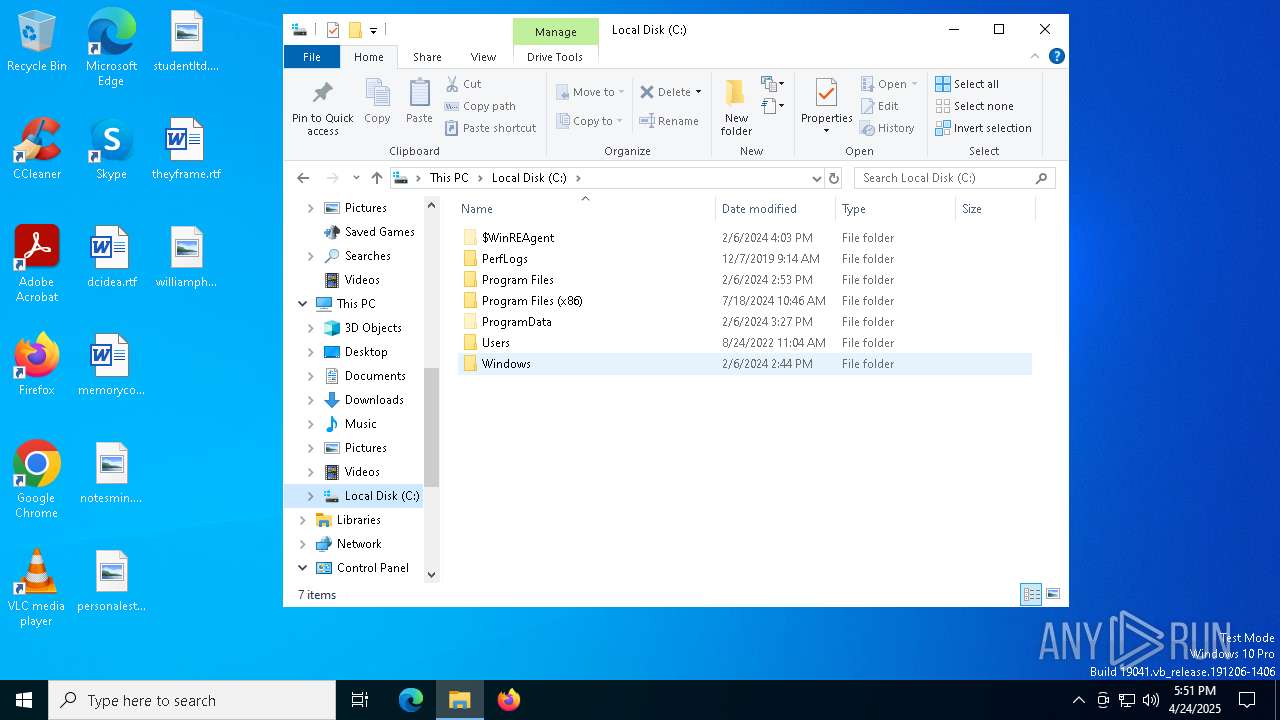
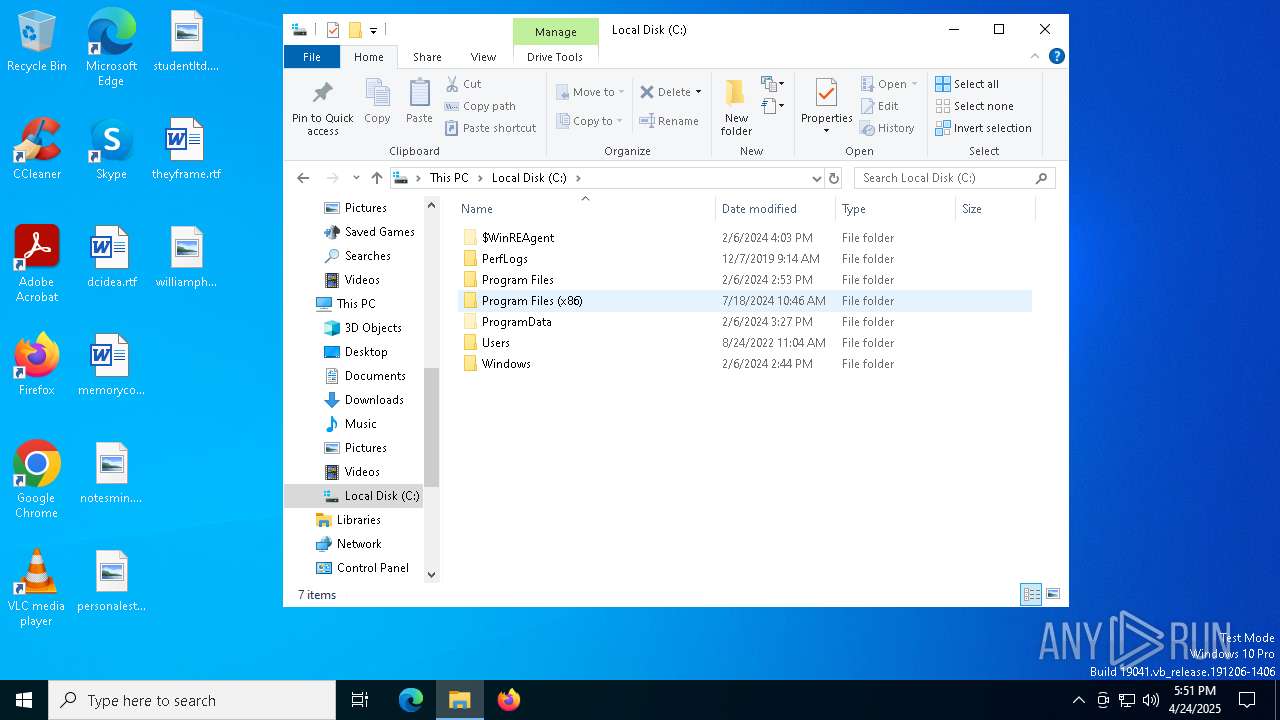
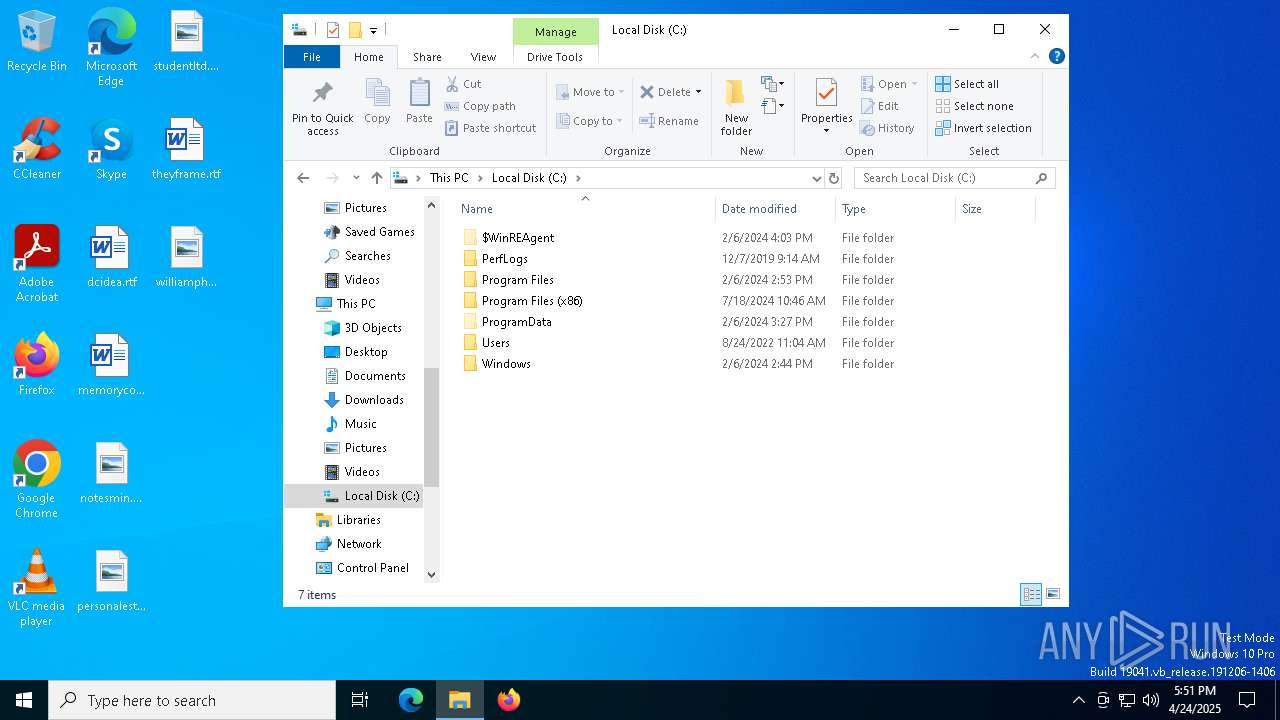
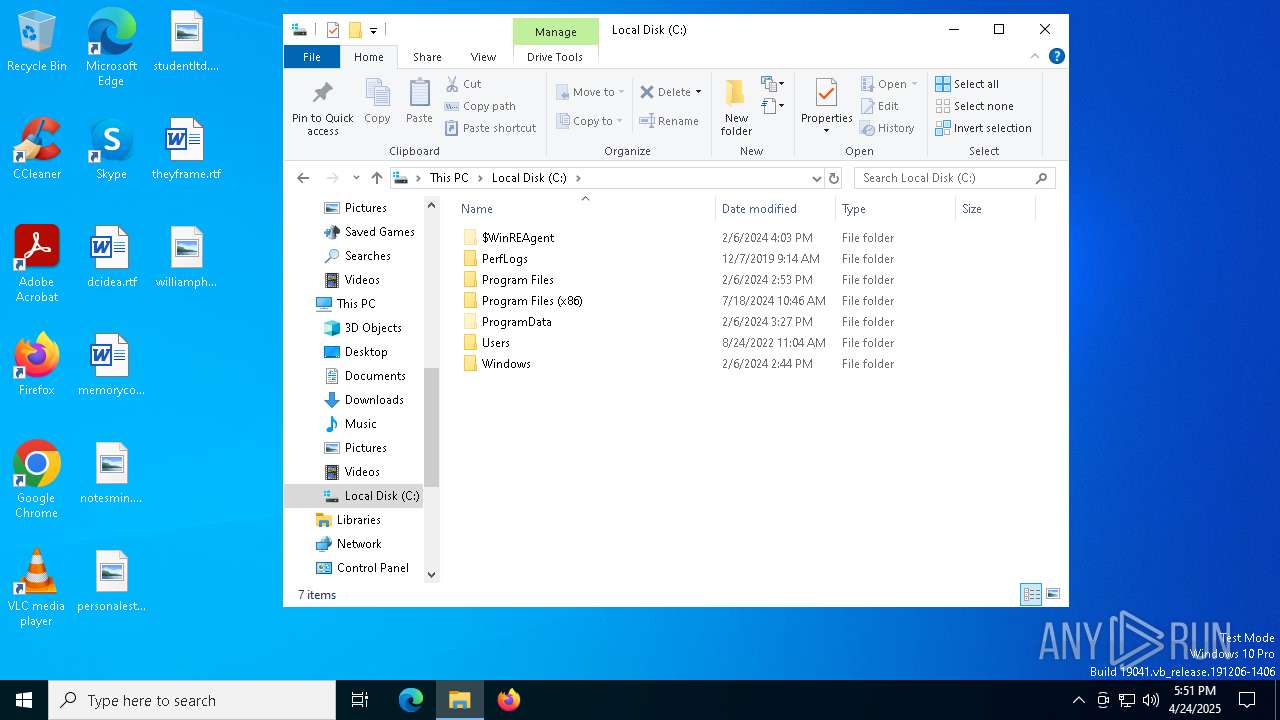
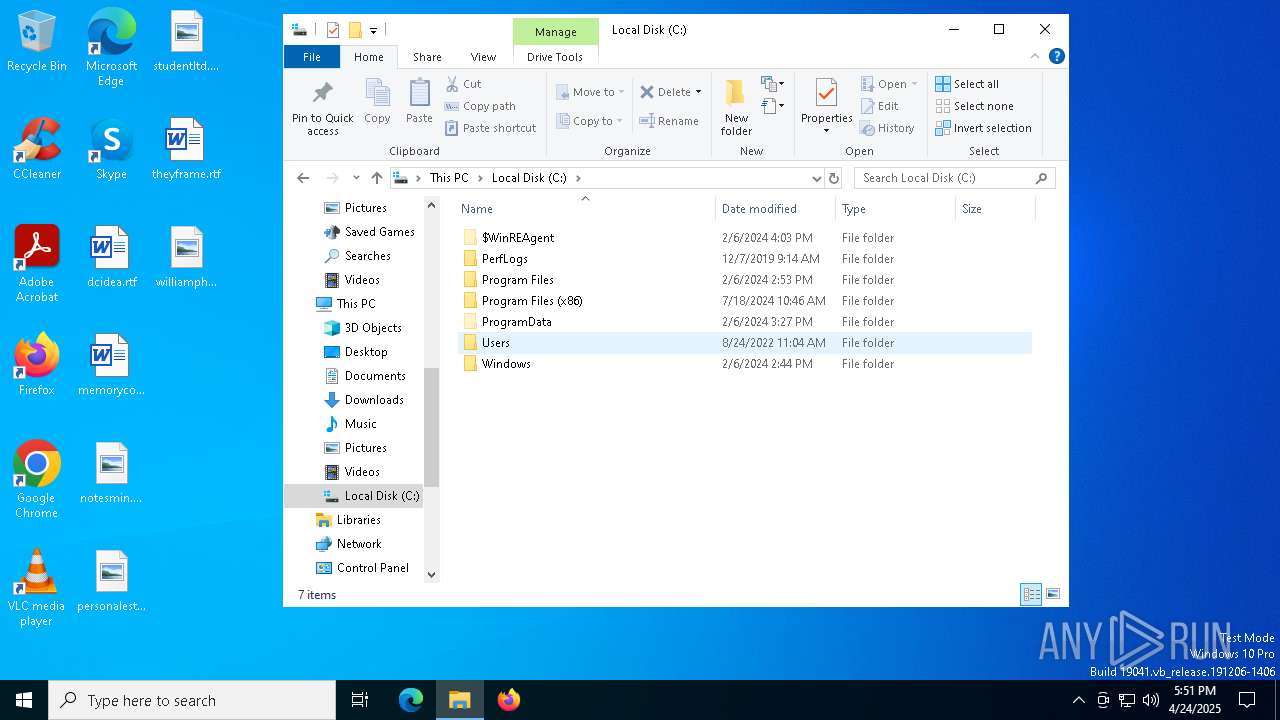
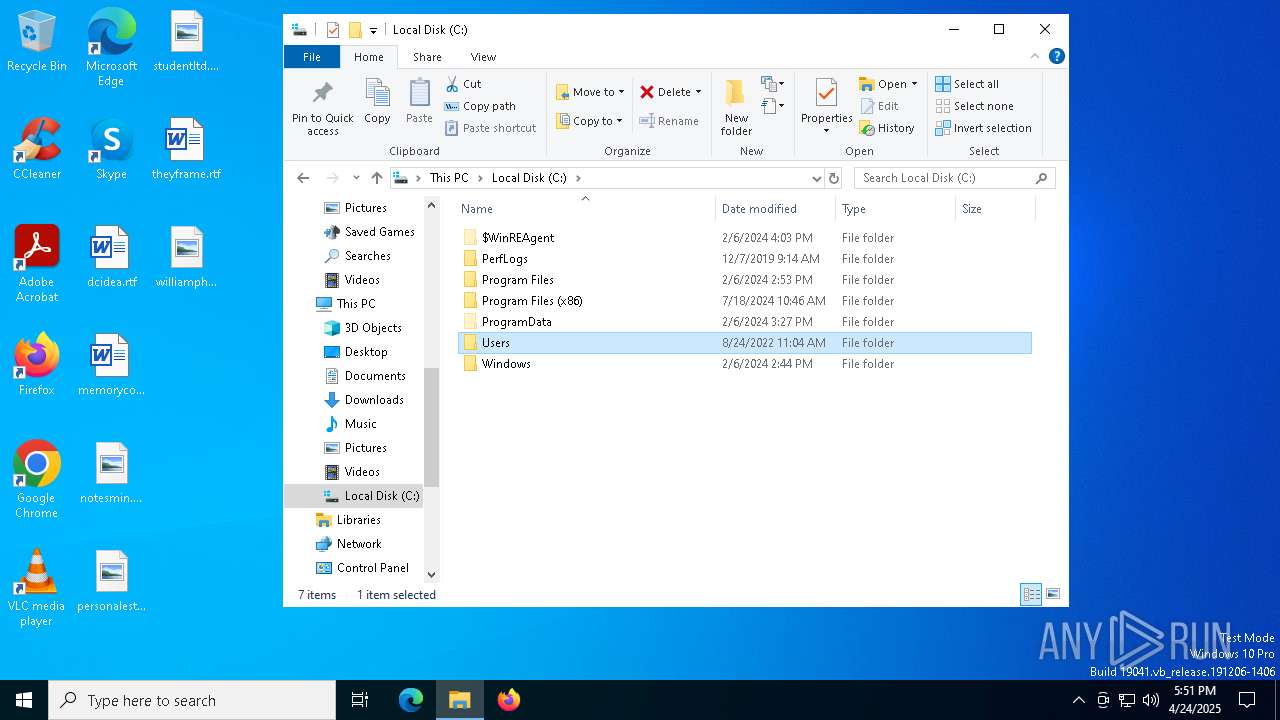
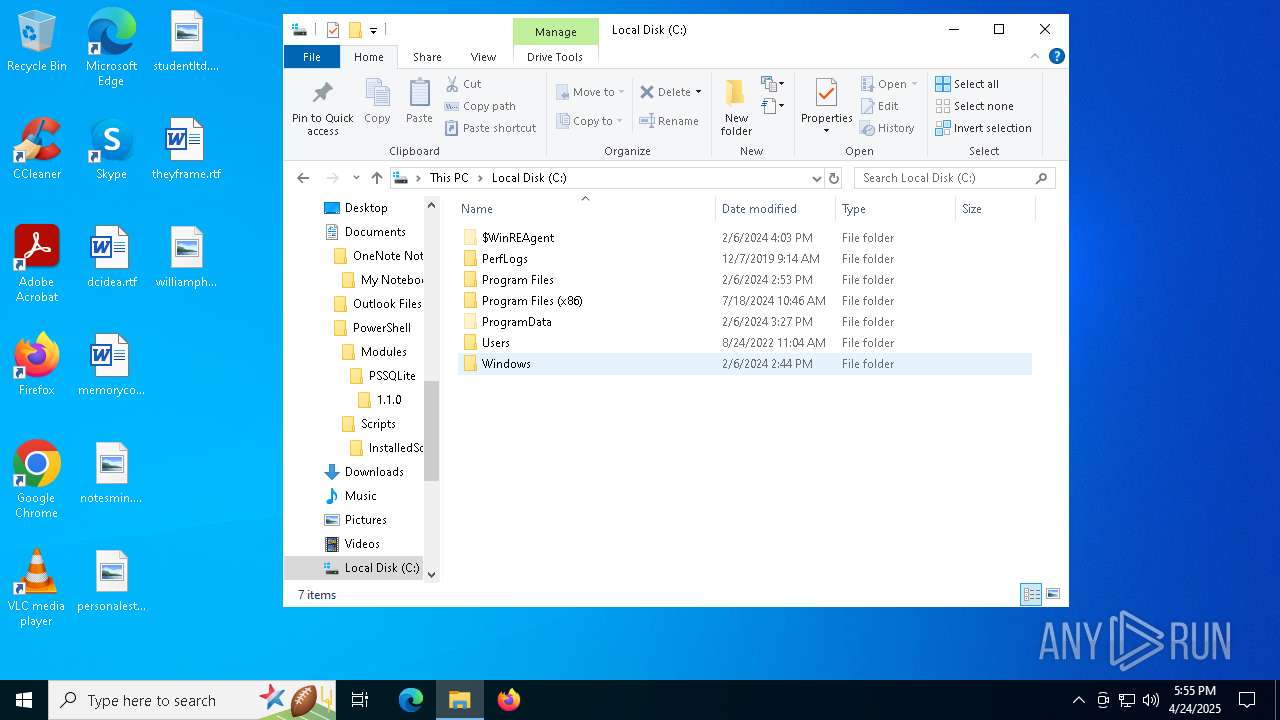
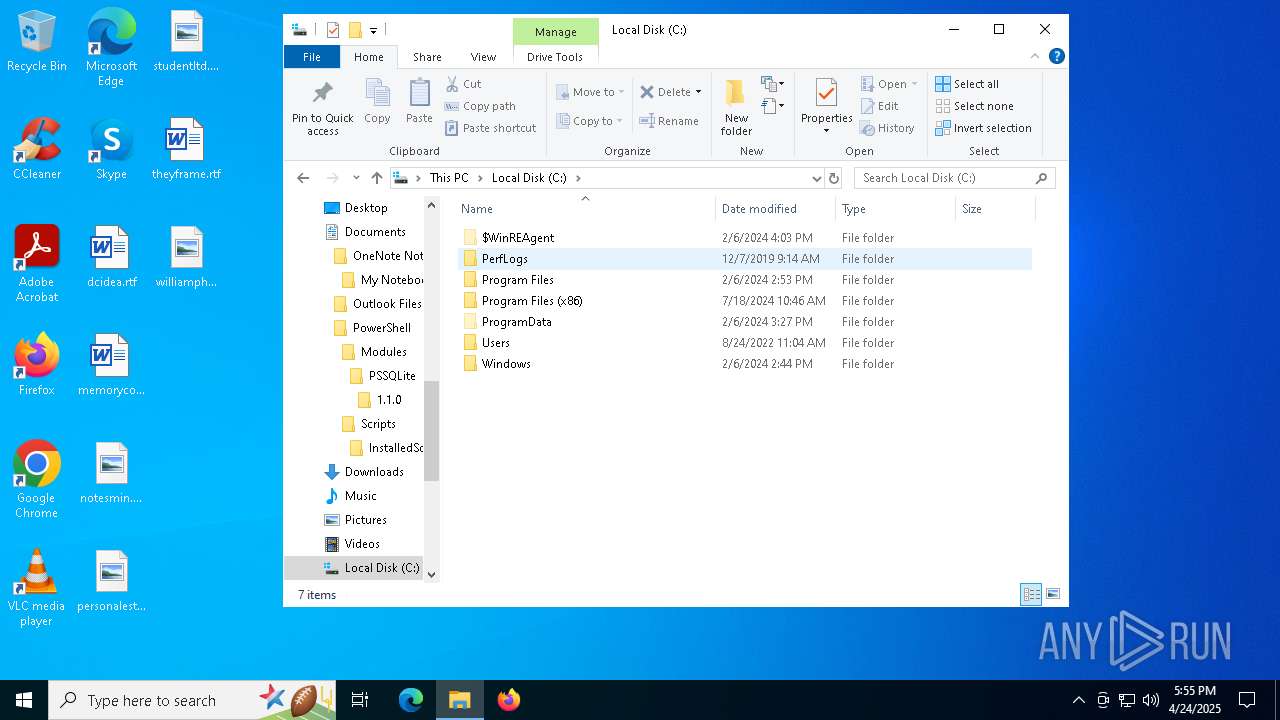
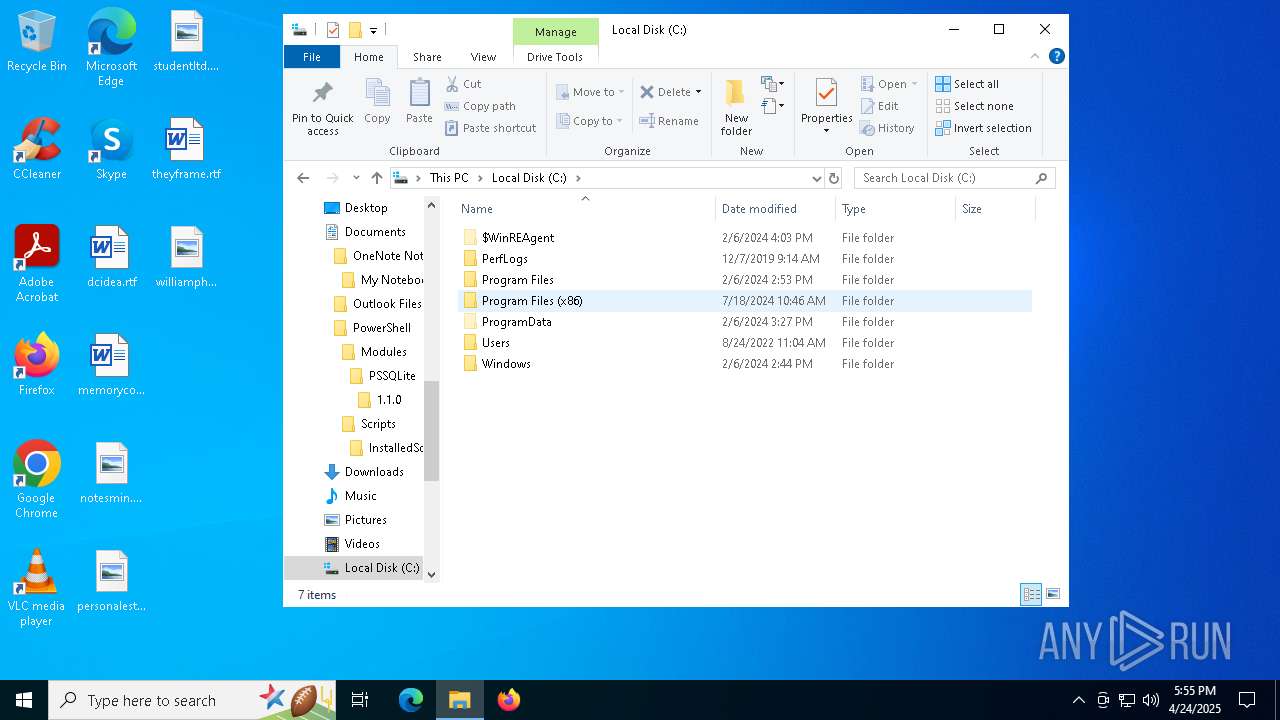
Creates file in the systems drive root
- win.exe (PID: 7264)
Write to the desktop.ini file (may be used to cloak folders)
- win.exe (PID: 7264)
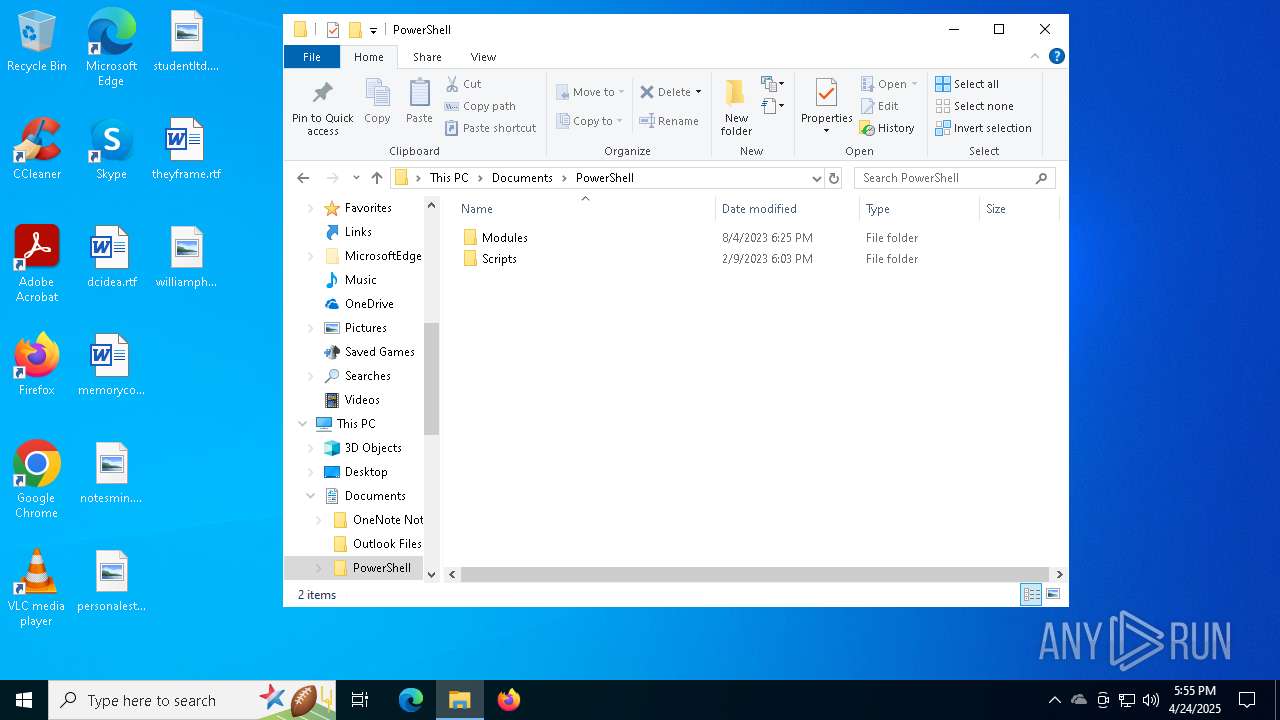
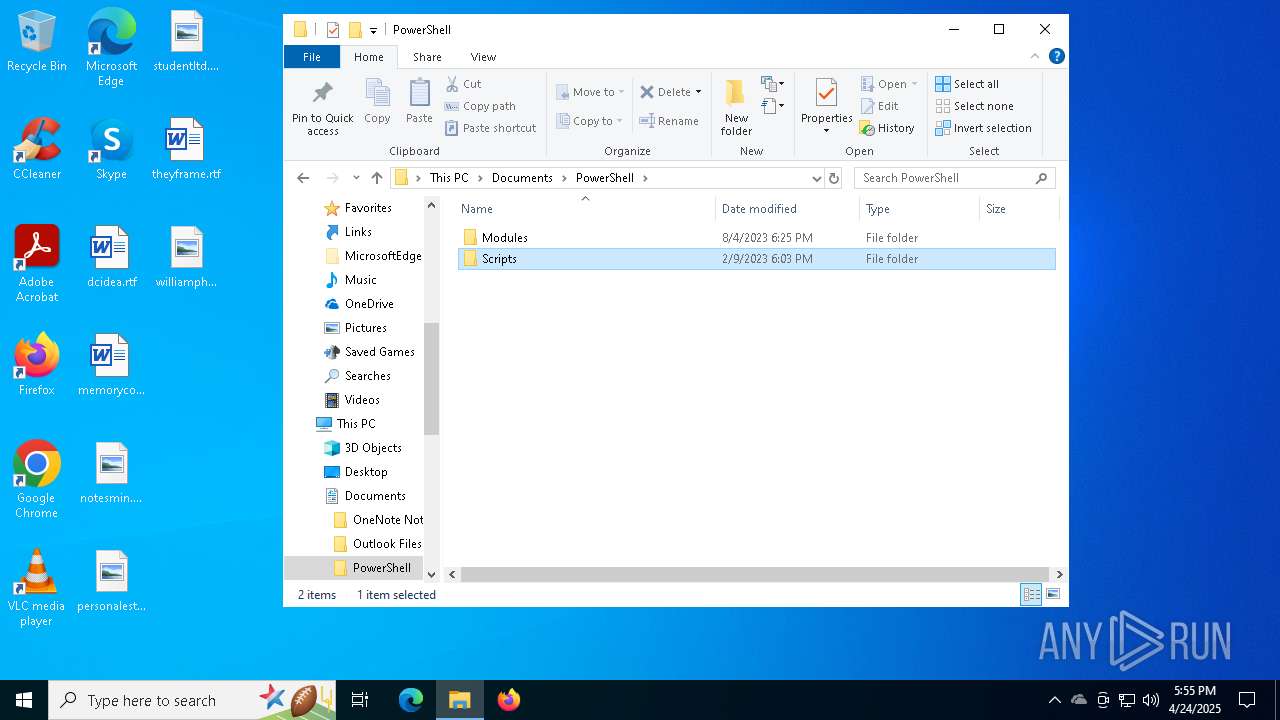
Executed via WMI
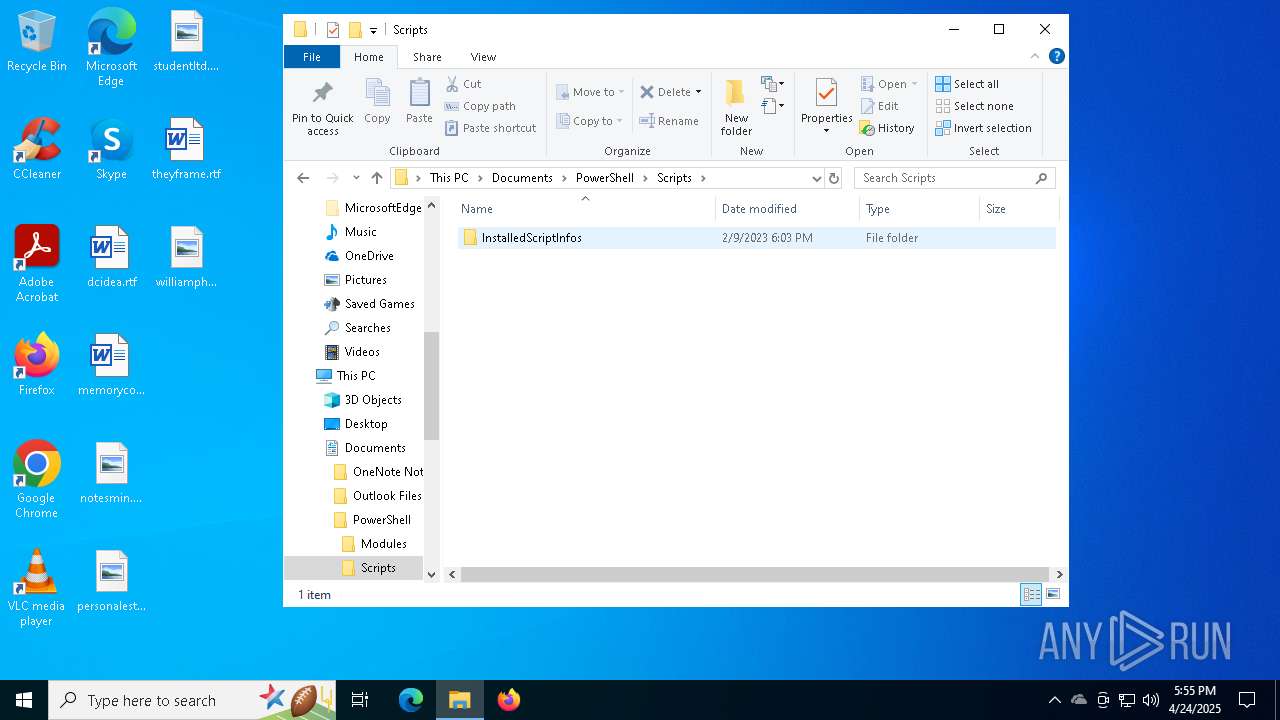
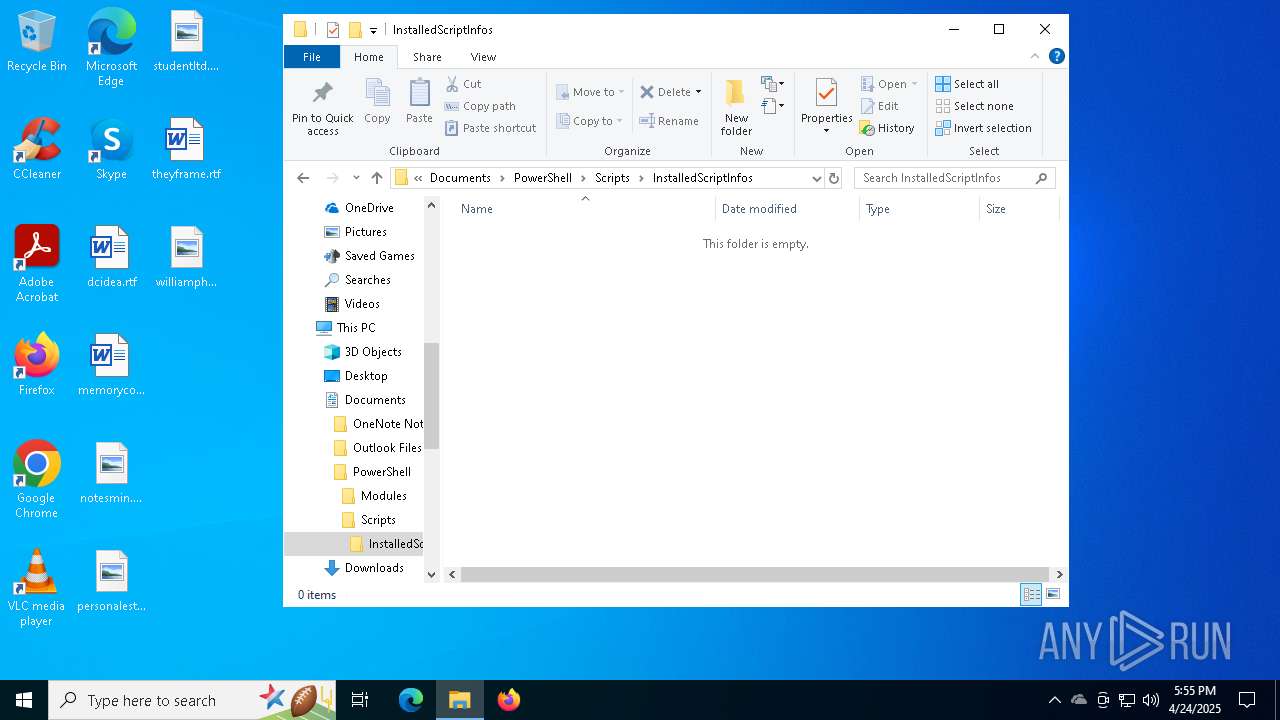
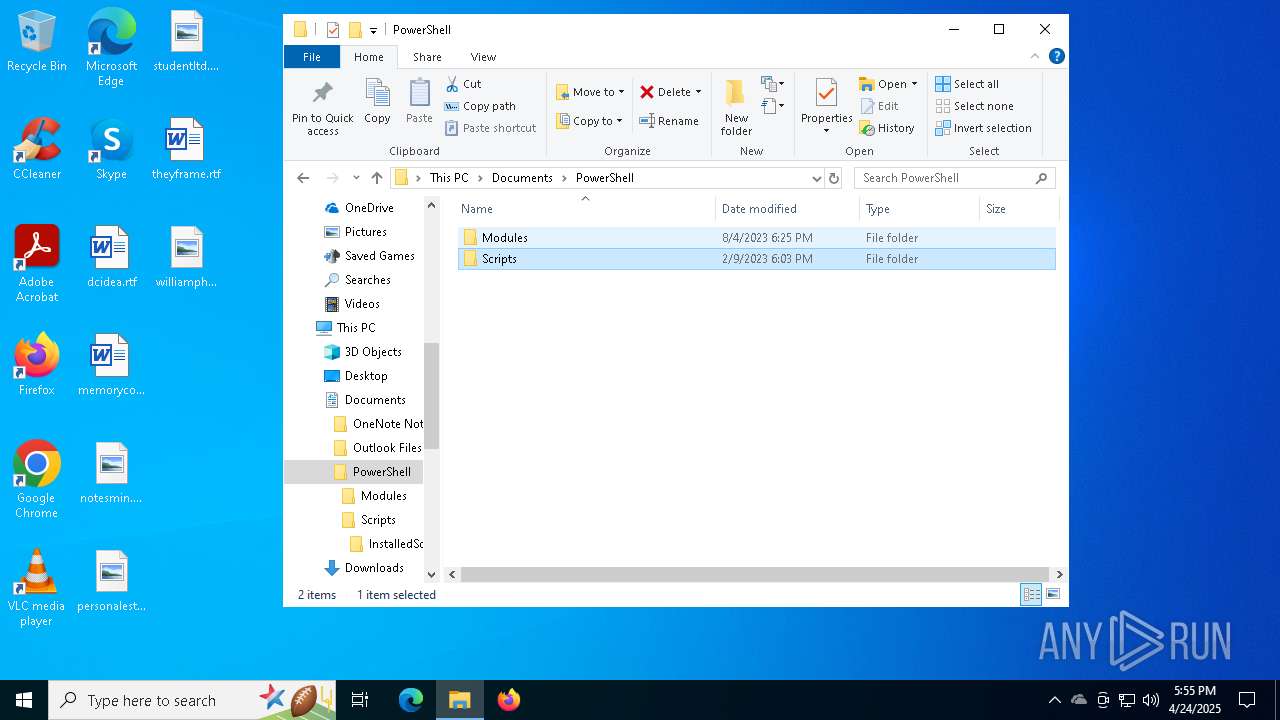
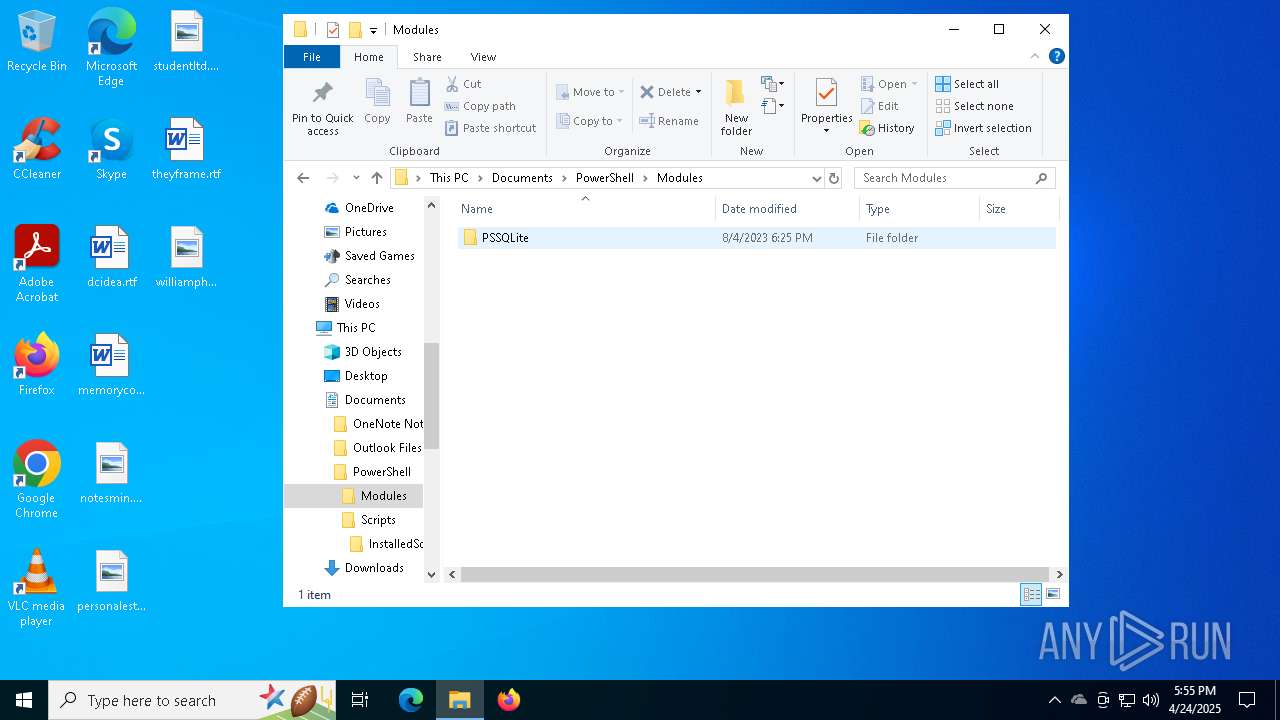
- powershell.exe (PID: 7412)
Application launched itself
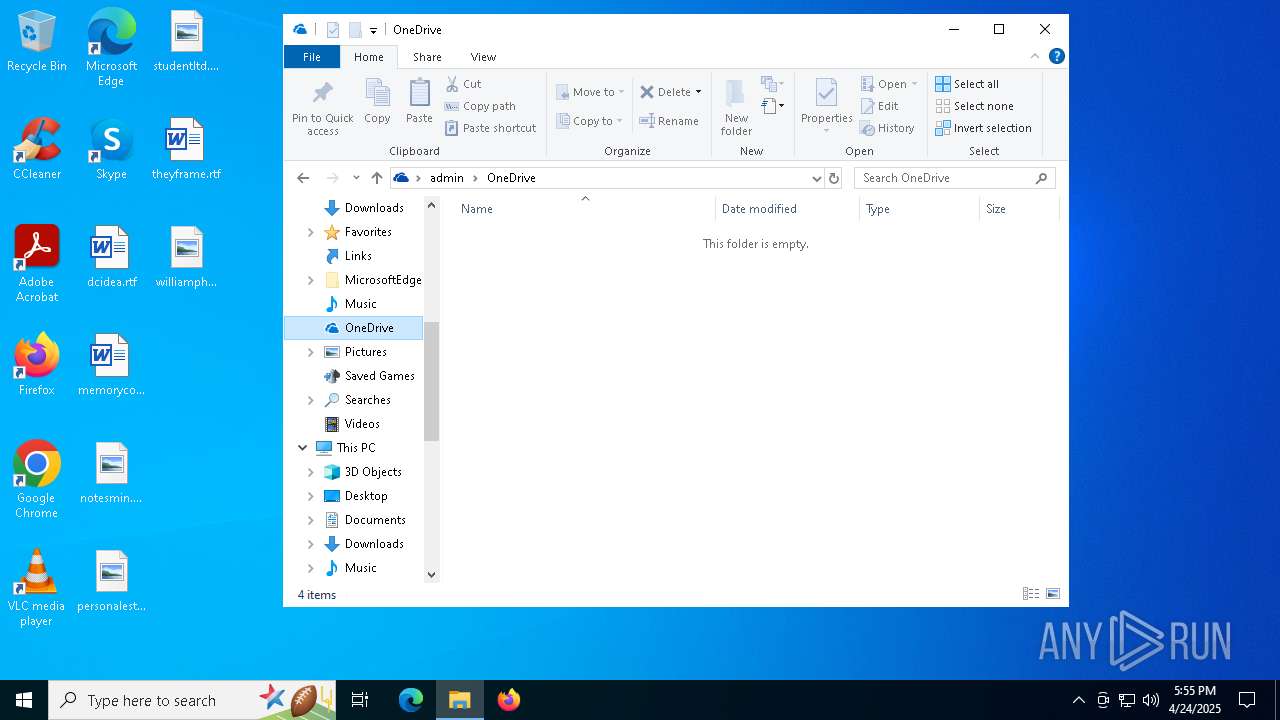
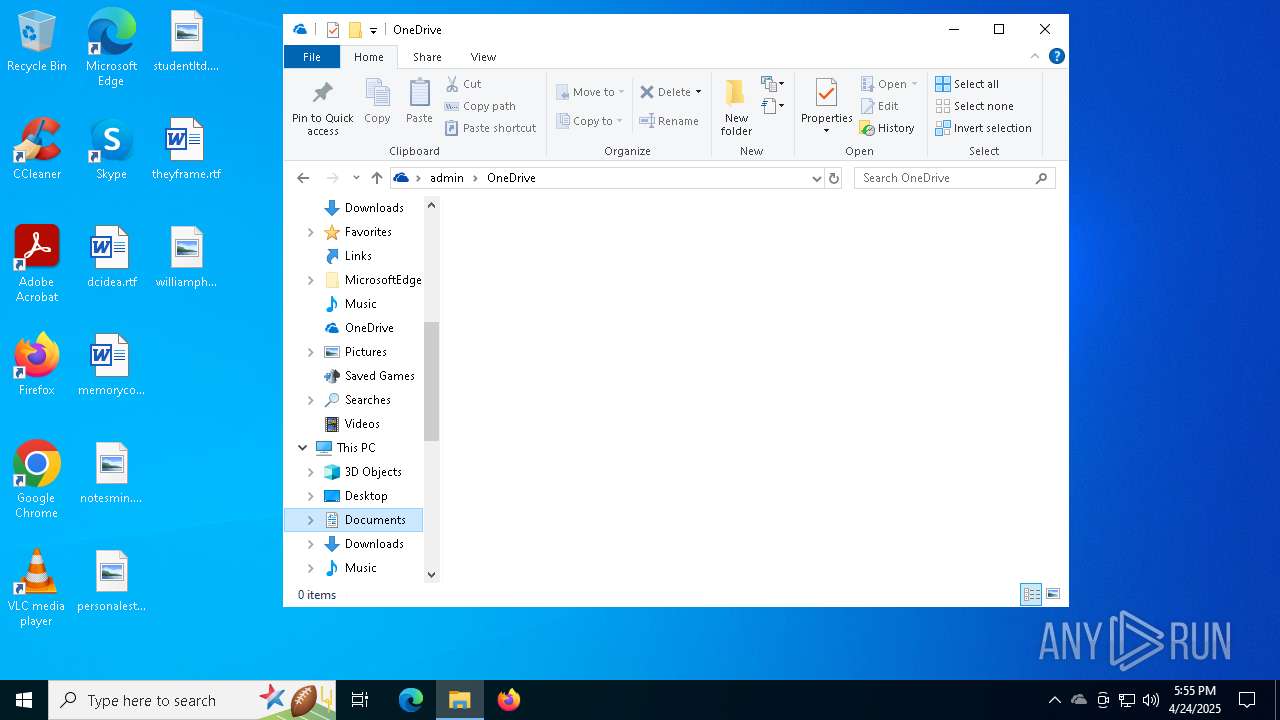
- OneDriveSetup.exe (PID: 5436)
Executable content was dropped or overwritten
- OneDriveSetup.exe (PID: 1348)
Process drops legitimate windows executable
- OneDriveSetup.exe (PID: 1348)
The process drops C-runtime libraries
- OneDriveSetup.exe (PID: 1348)
INFO
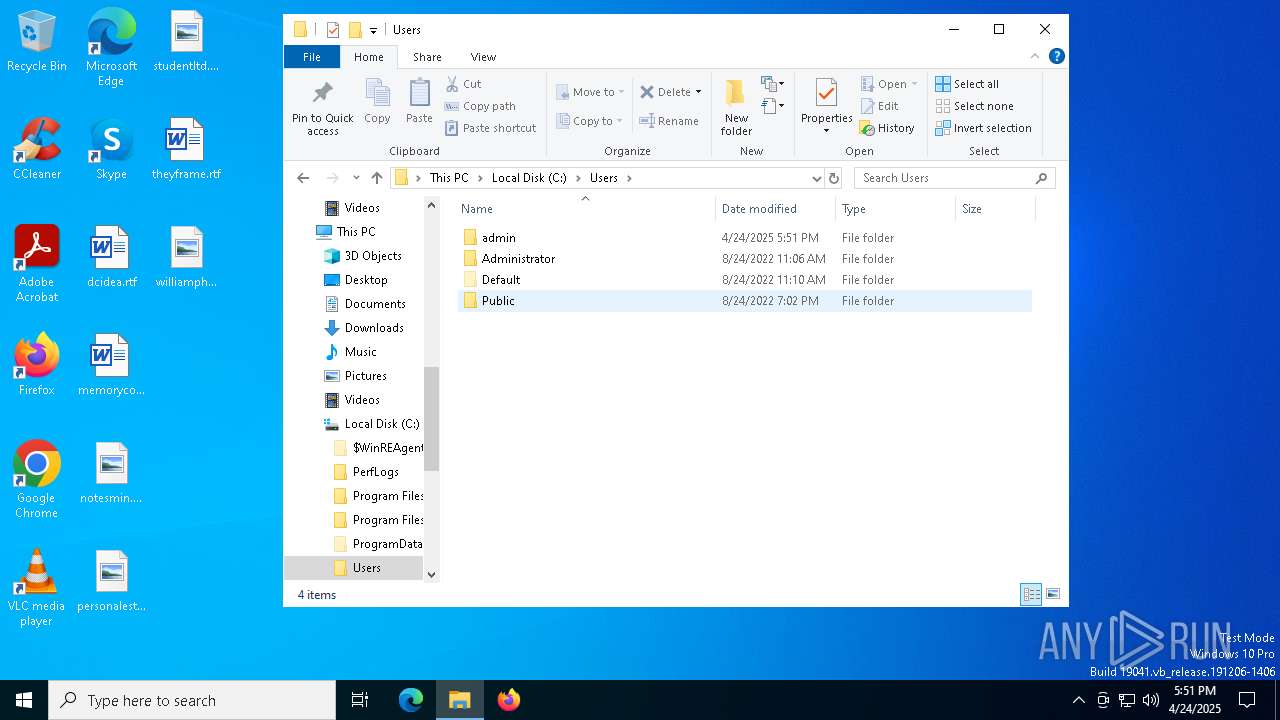
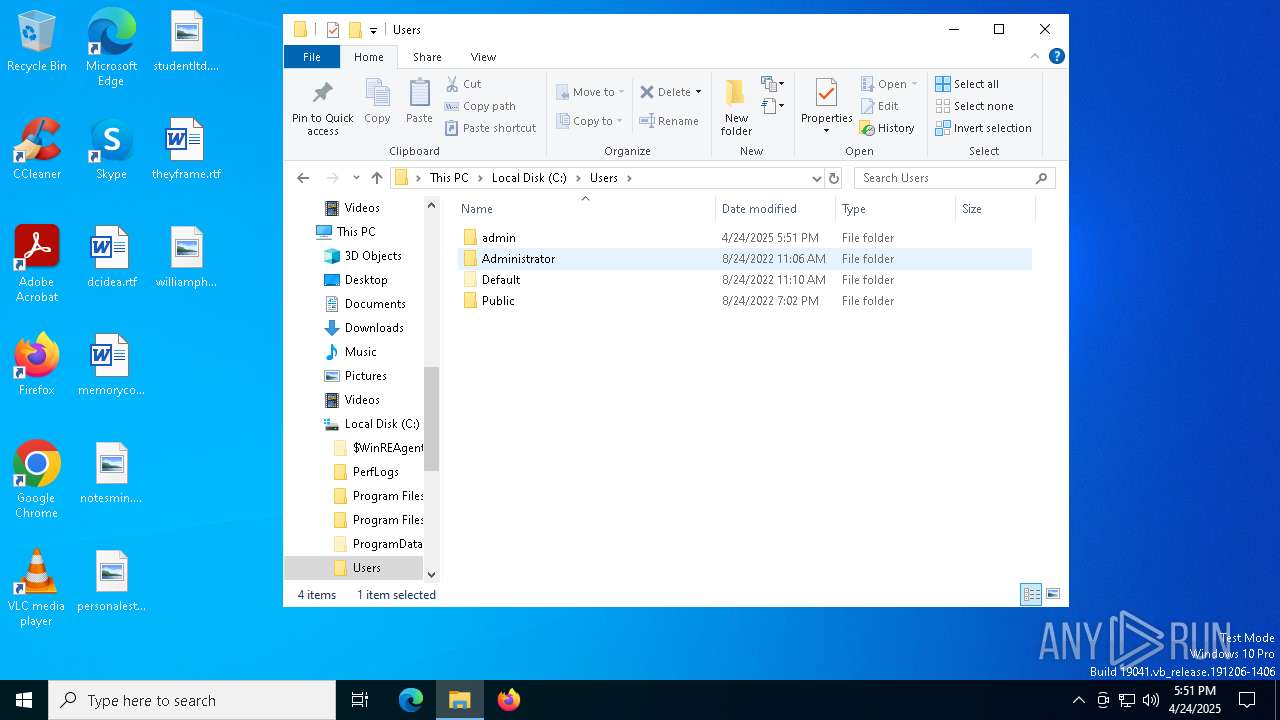
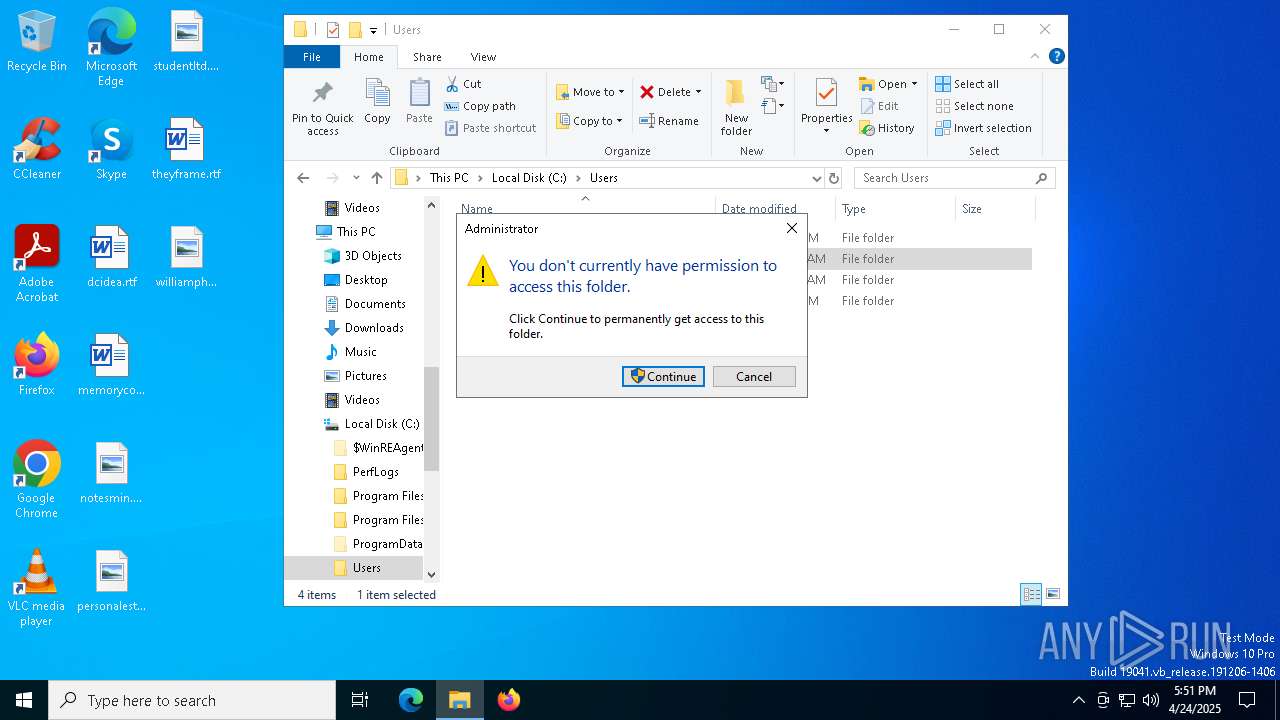
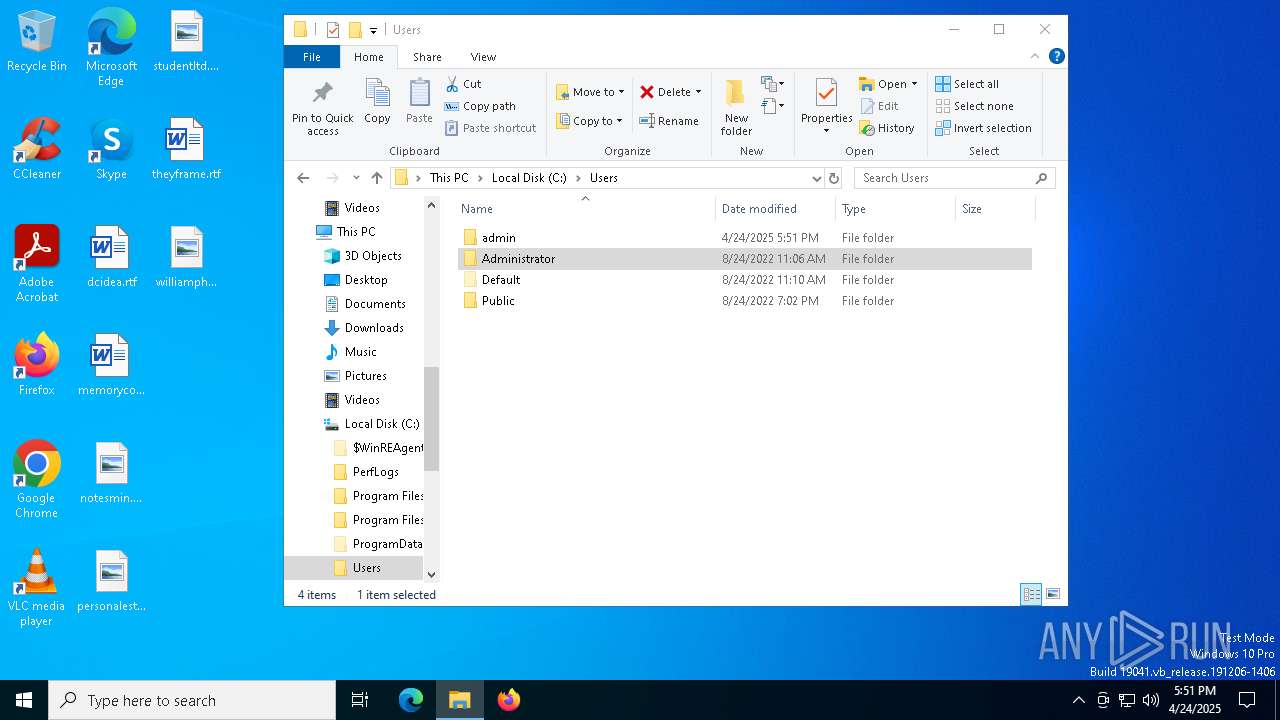
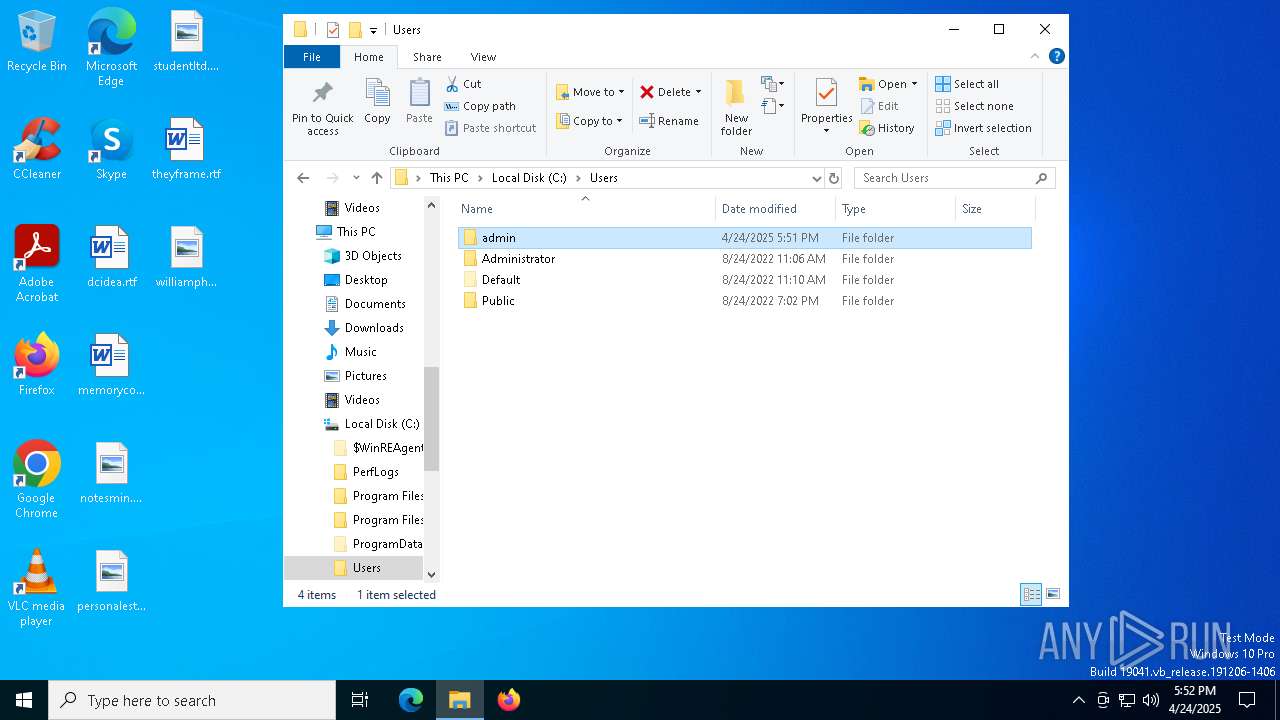
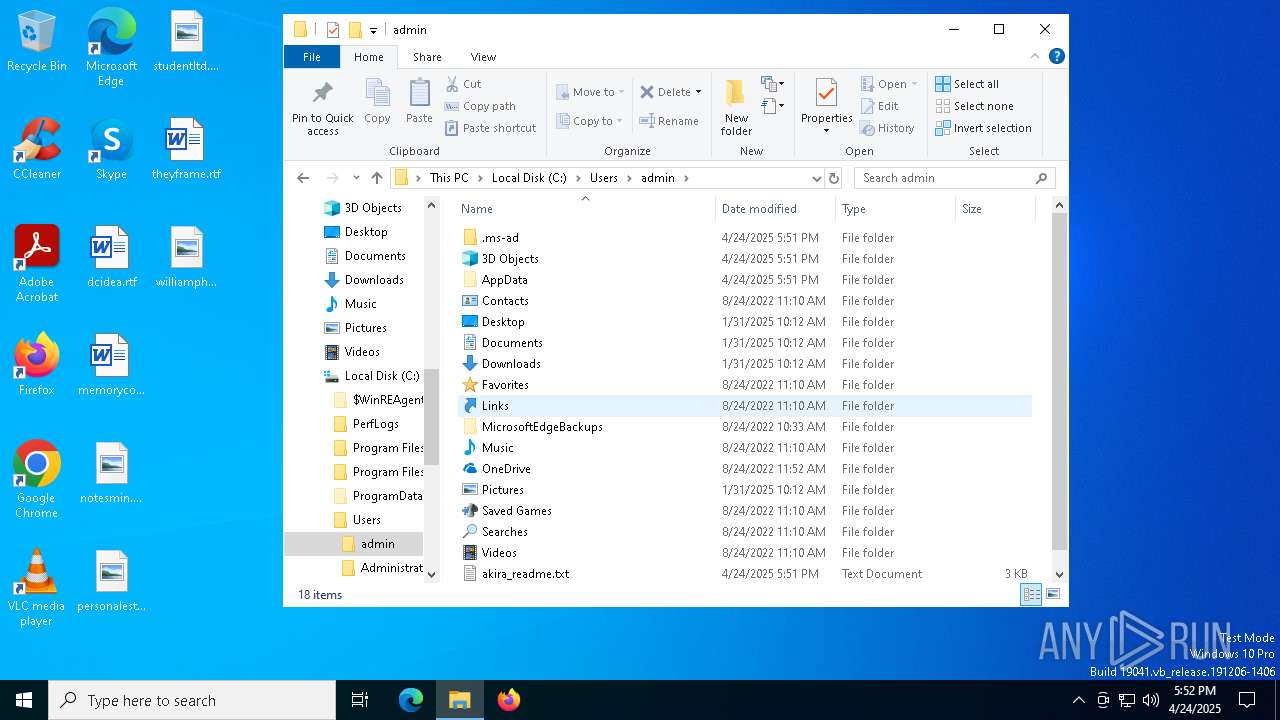
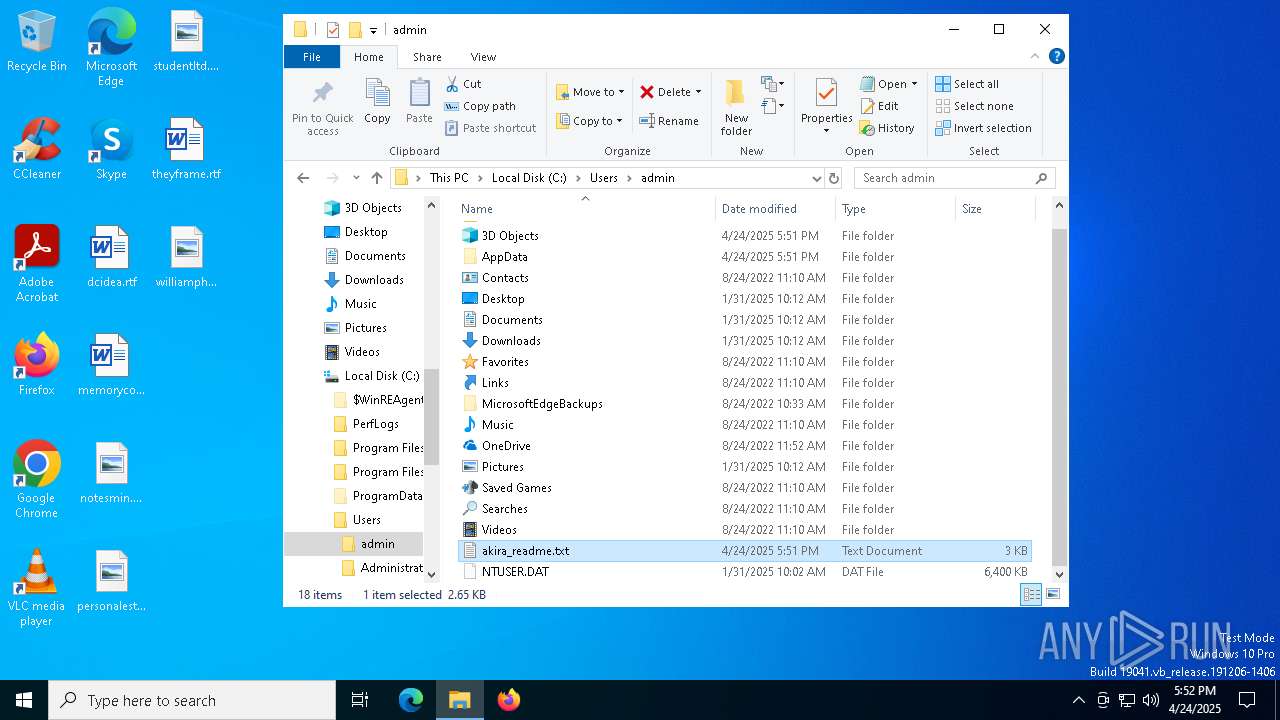
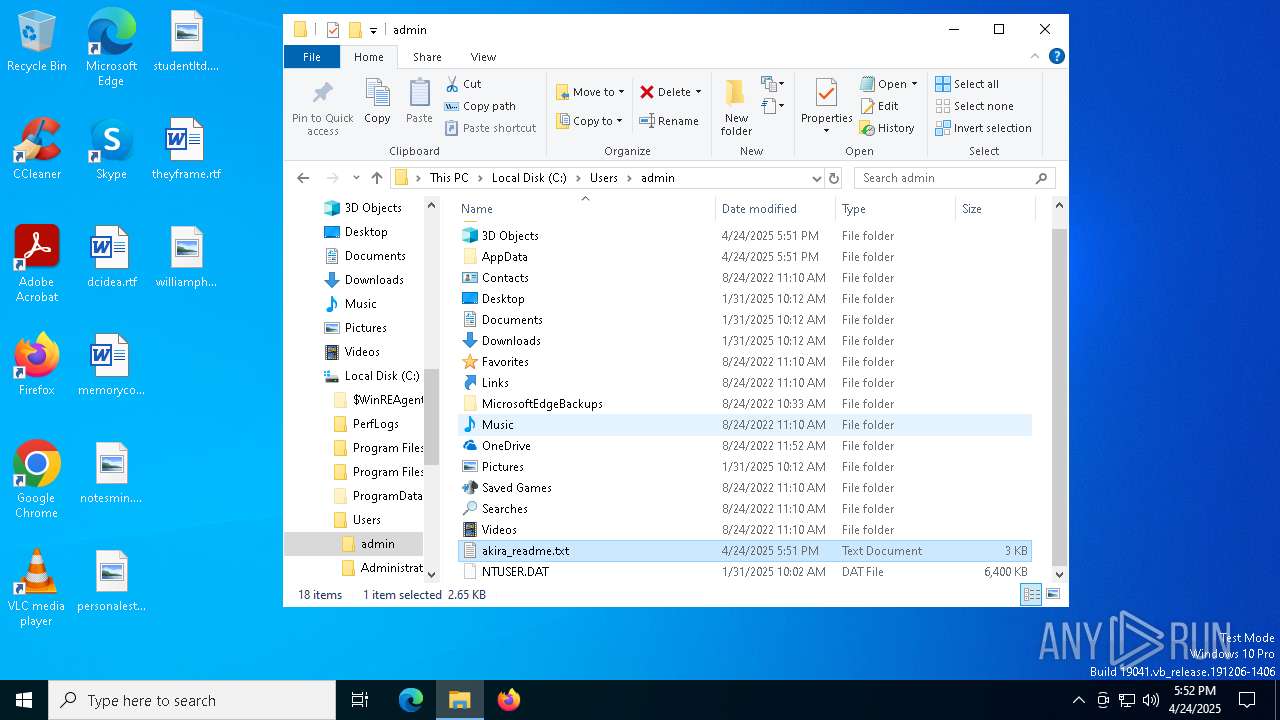
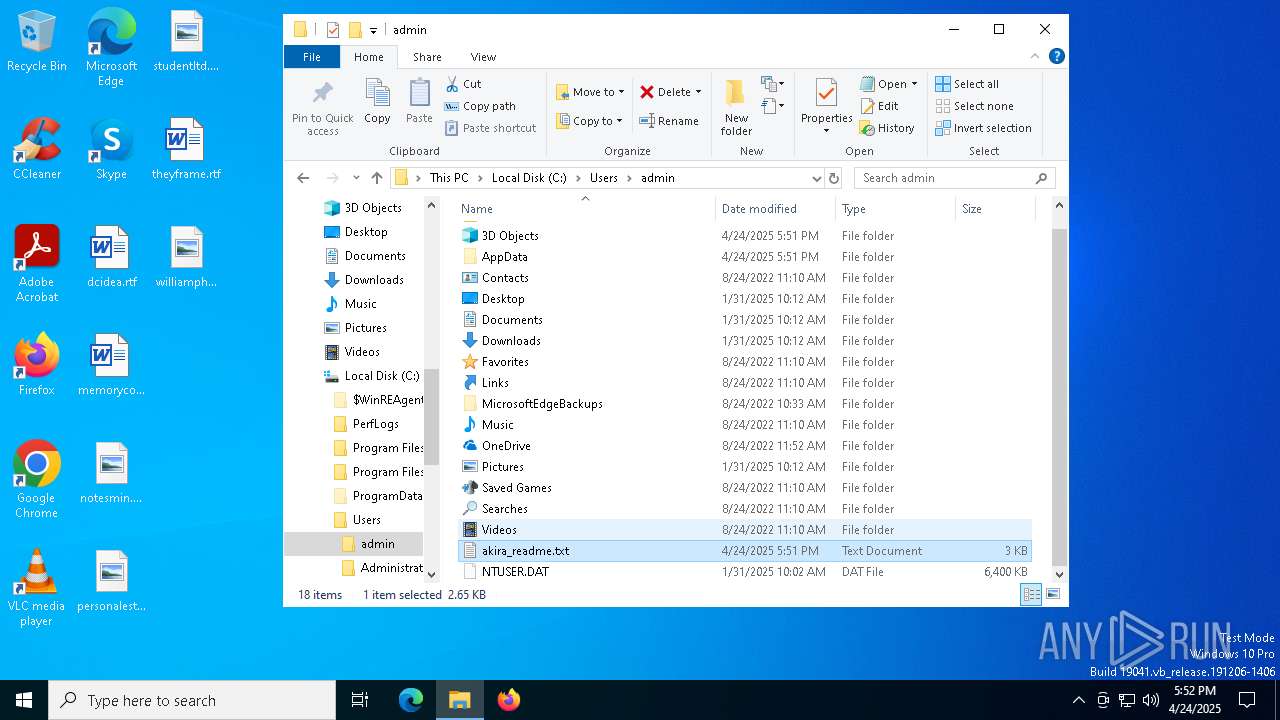
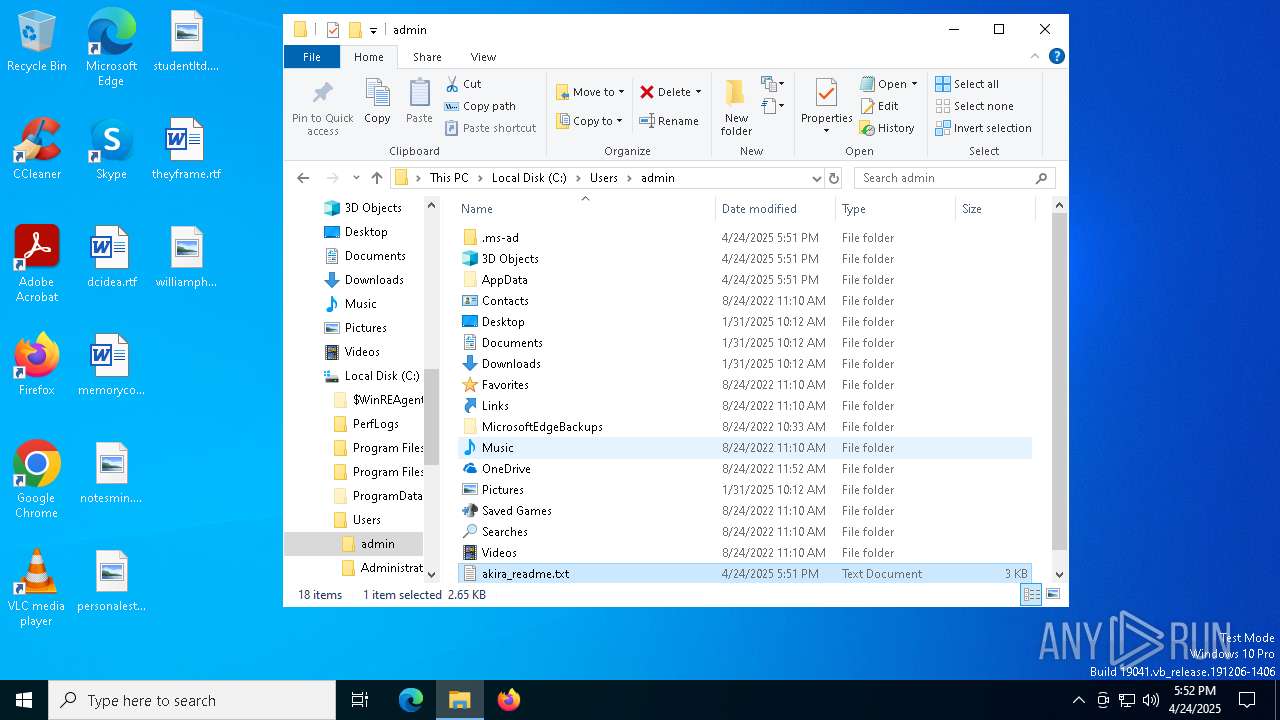
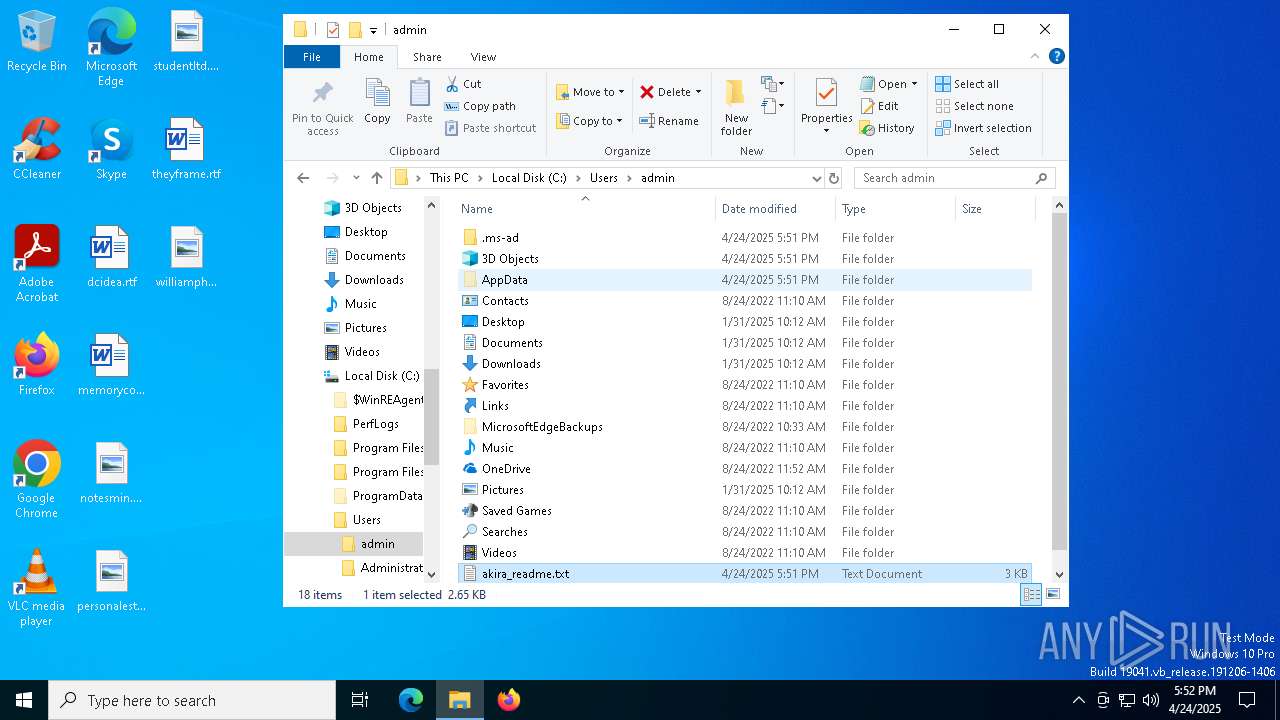
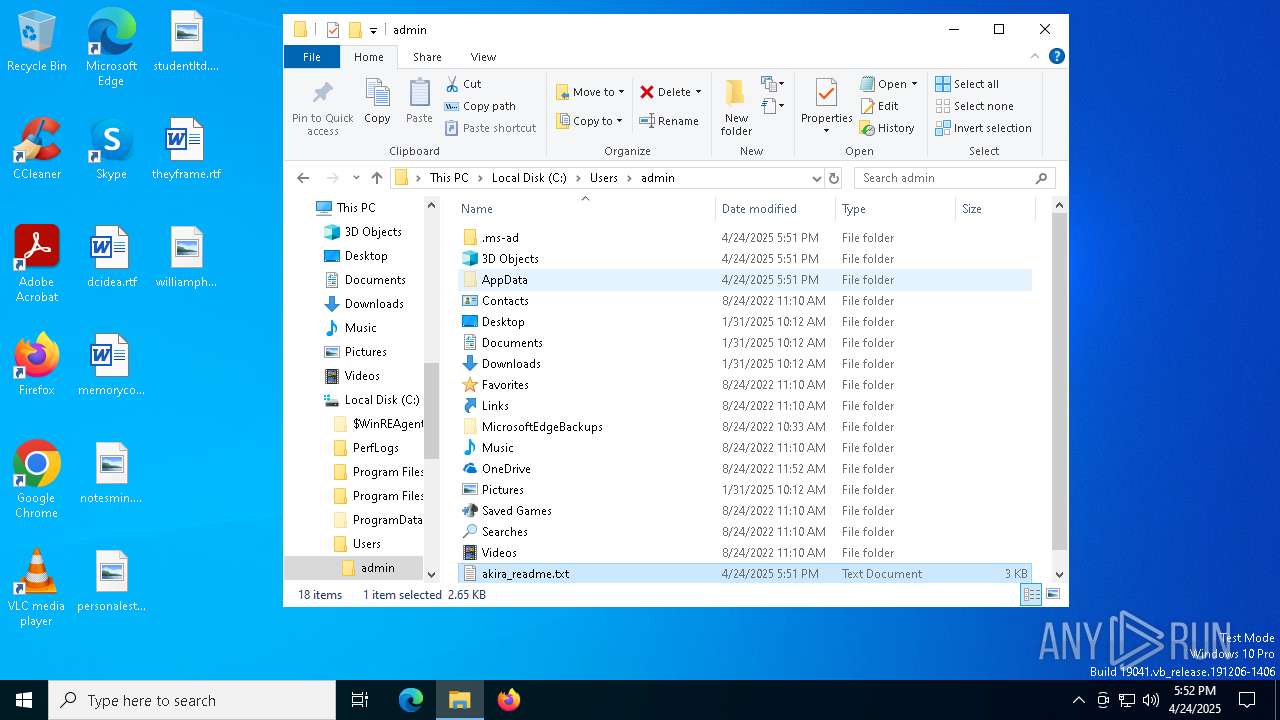
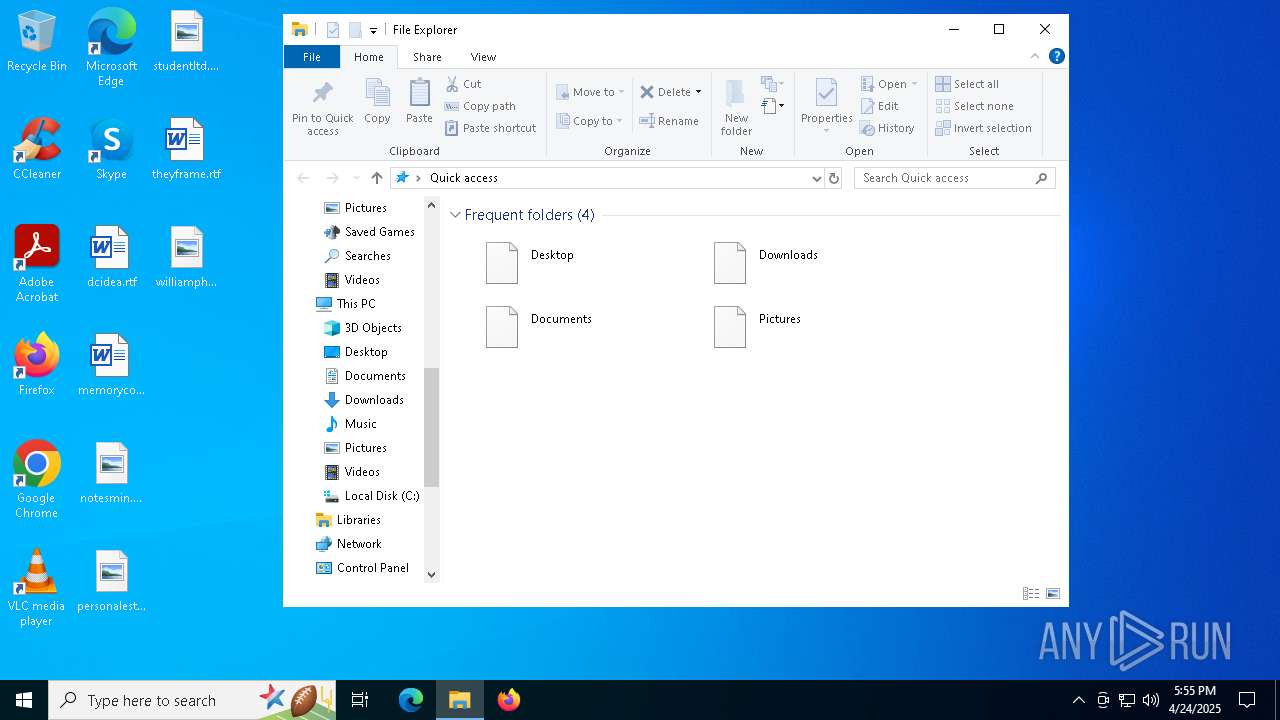
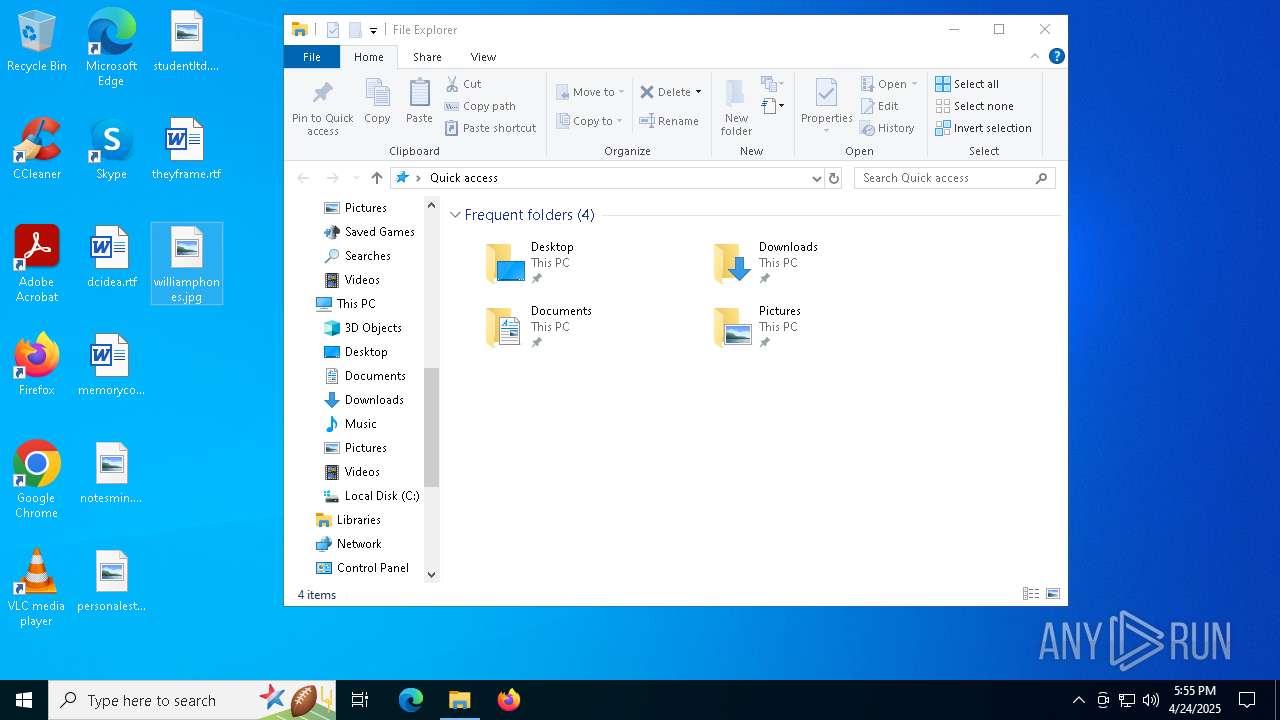
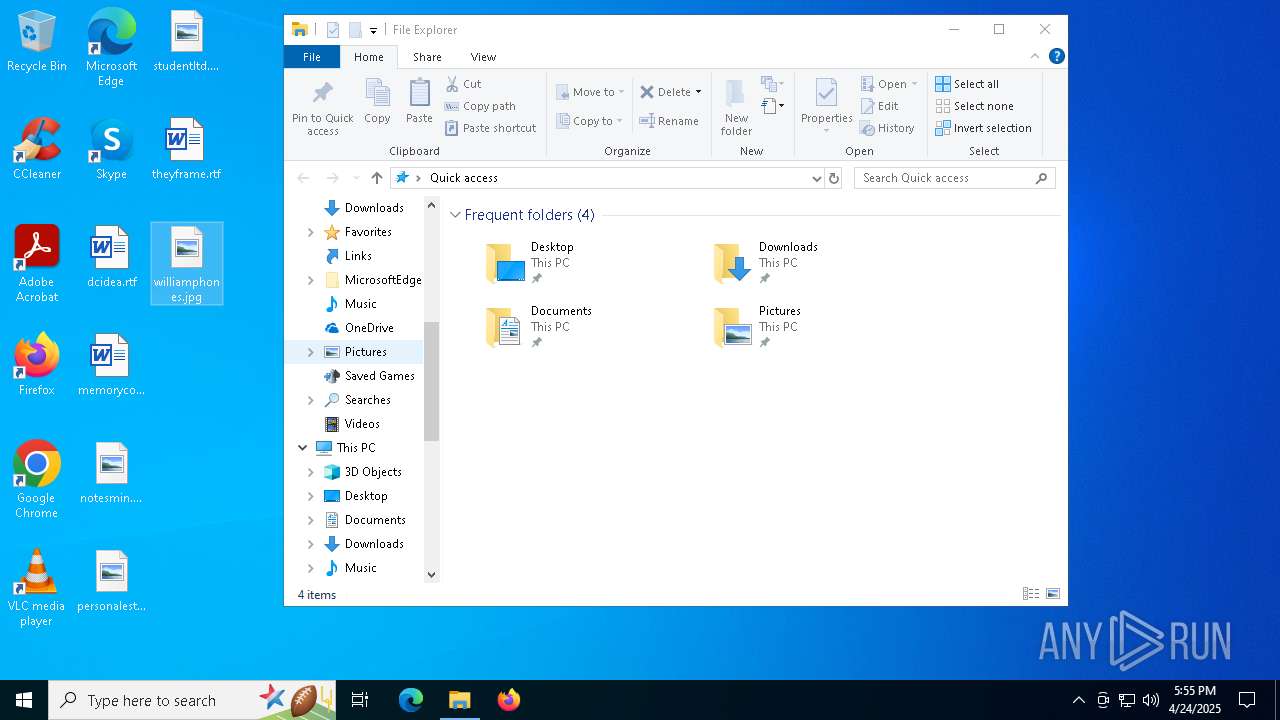
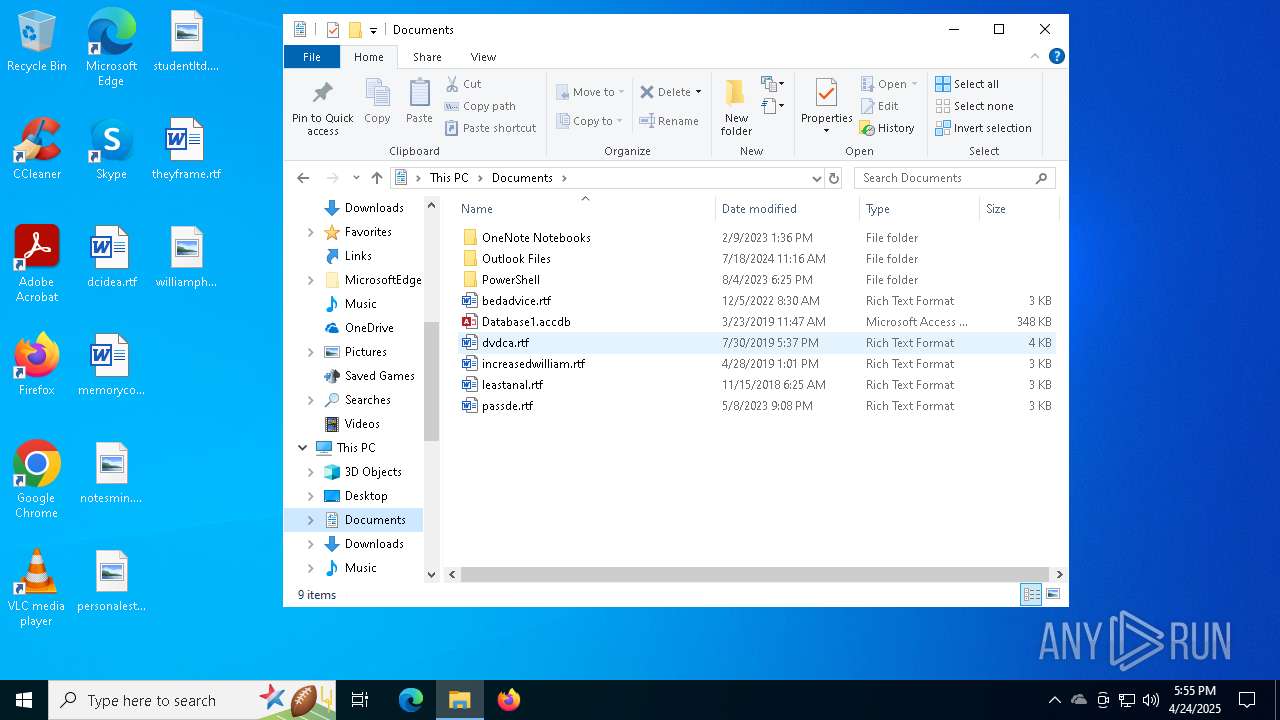
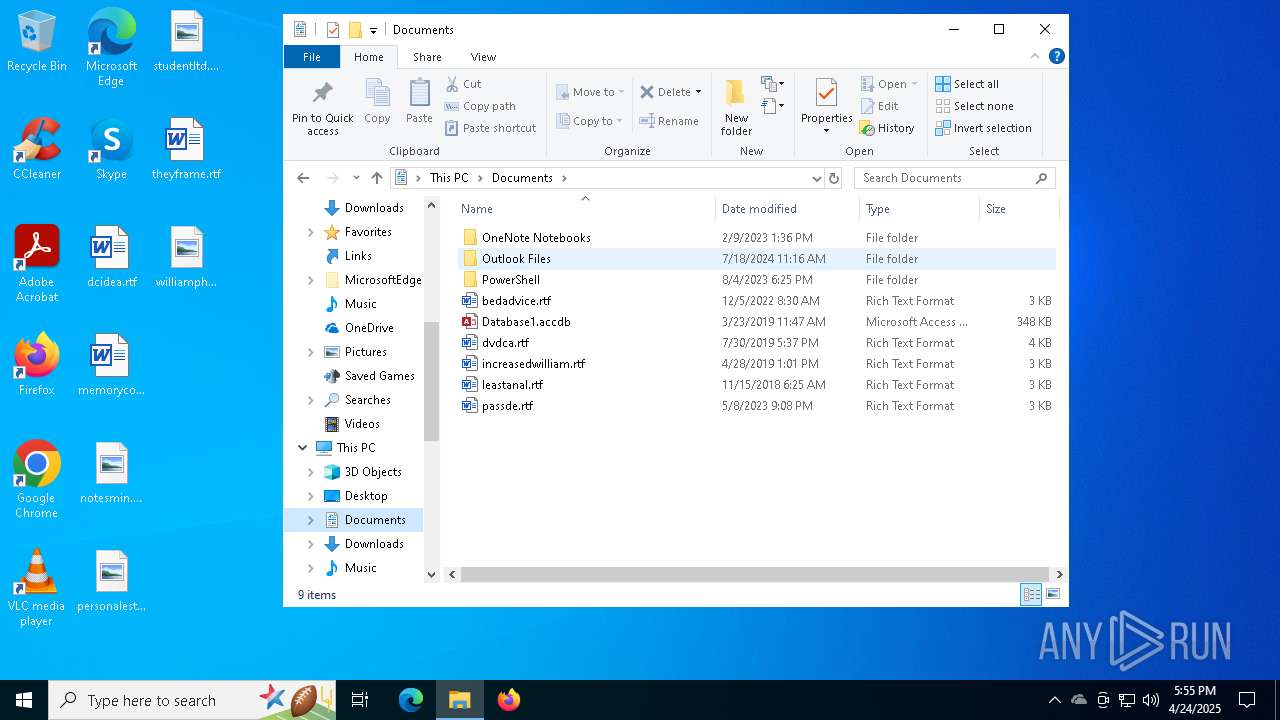
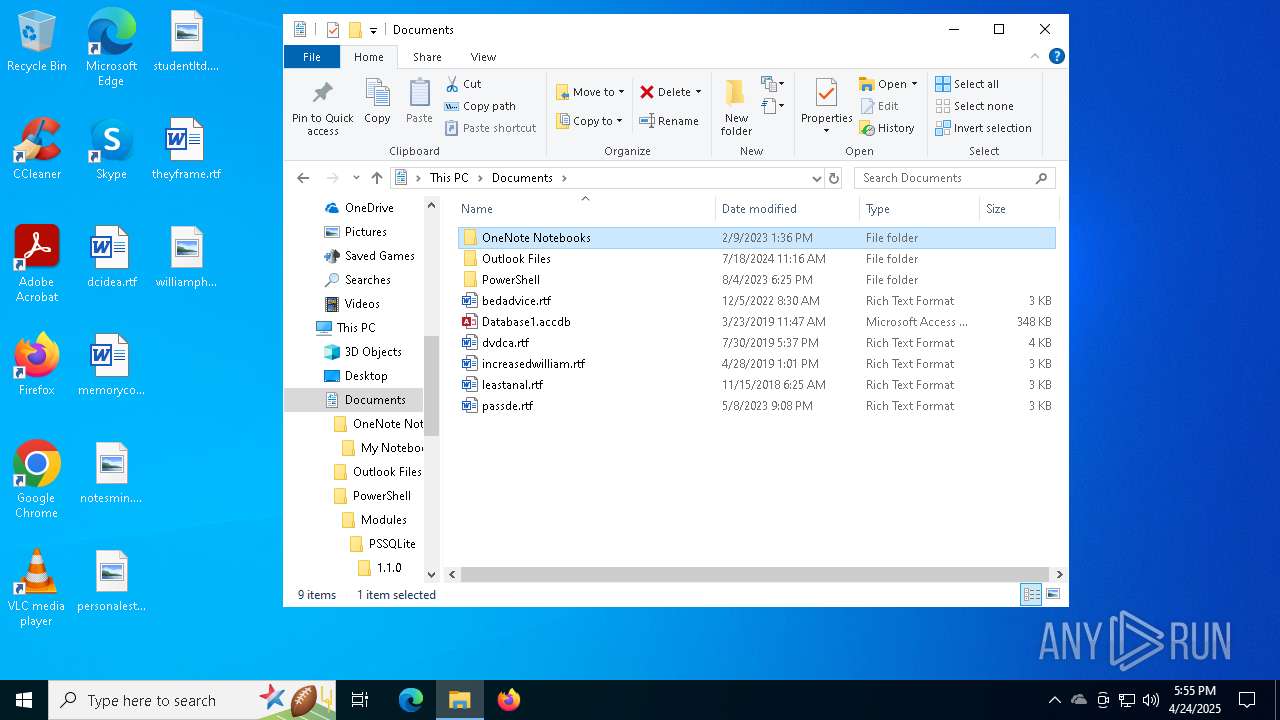
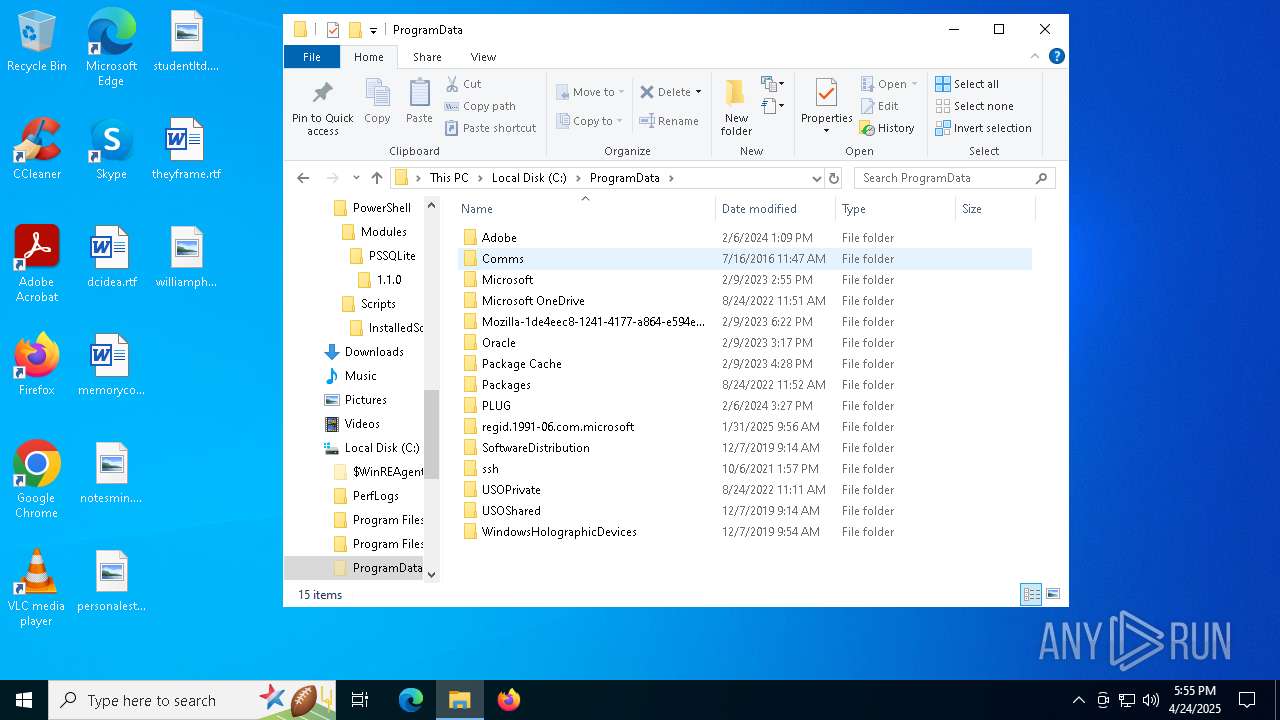
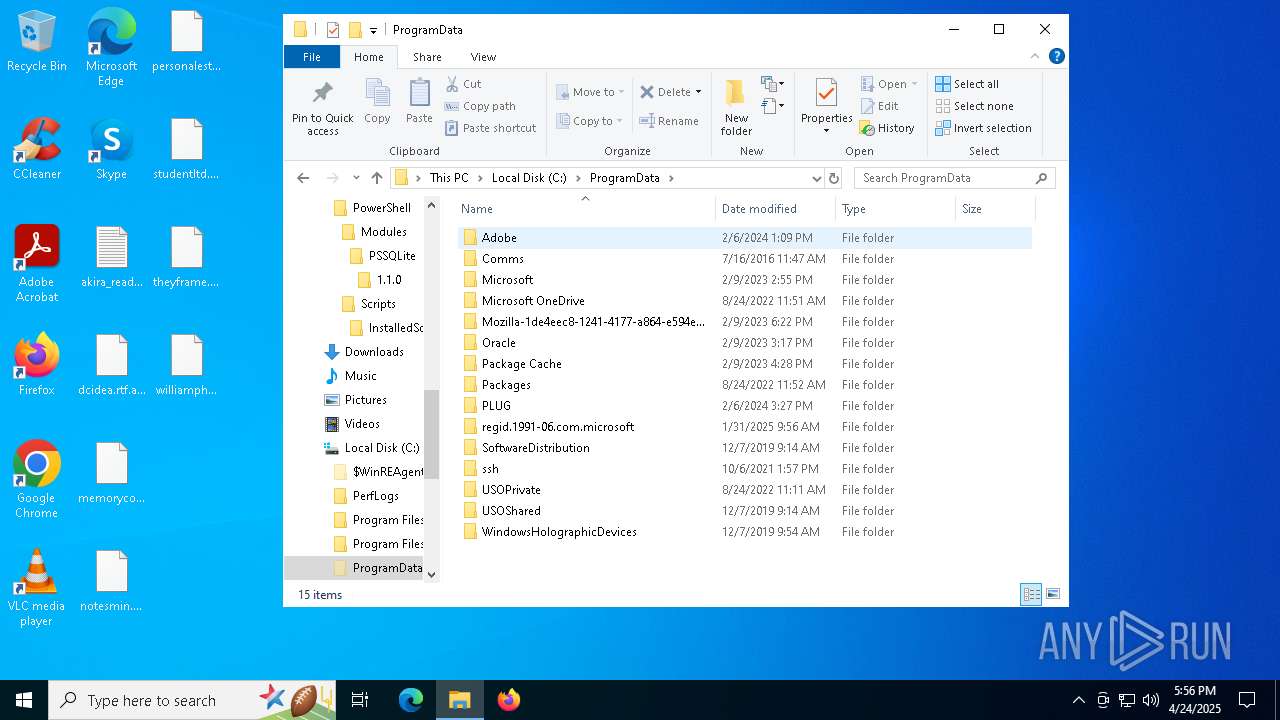
Creates files or folders in the user directory
- win.exe (PID: 7264)
Checks supported languages
- win.exe (PID: 7264)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7412)
Reads the computer name
- win.exe (PID: 7264)
Manual execution by a user
- notepad.exe (PID: 7404)
- OneDrive.exe (PID: 5272)
- msedge.exe (PID: 4120)
- chrome.exe (PID: 7540)
- notepad++.exe (PID: 6036)
Application launched itself
- chrome.exe (PID: 7540)
- msedge.exe (PID: 4120)
- msedge.exe (PID: 7176)
The sample compiled with english language support
- OneDriveSetup.exe (PID: 1348)
The sample compiled with portuguese language support
- OneDriveSetup.exe (PID: 1348)
The sample compiled with chinese language support
- OneDriveSetup.exe (PID: 1348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:03:19 17:53:17+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.37 |
| CodeSize: | 837632 |
| InitializedDataSize: | 251392 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8dd38 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
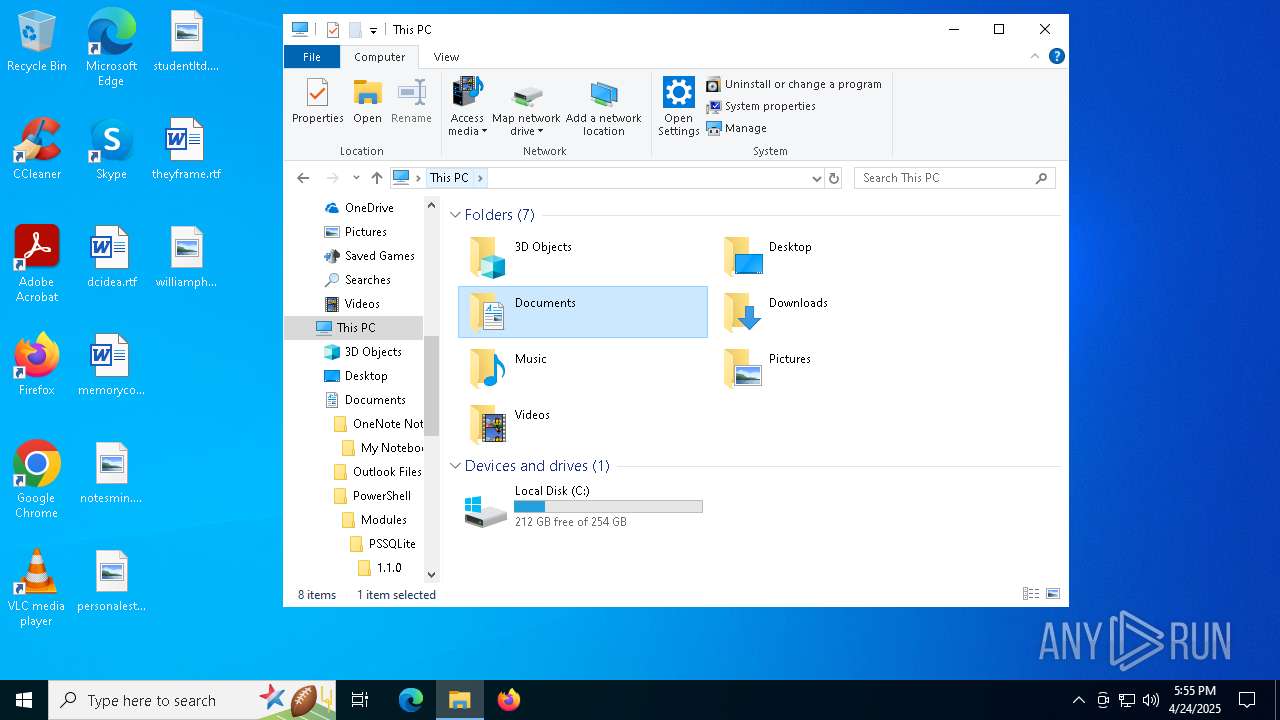
Total processes
270
Monitored processes
122
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7504 --field-trial-handle=1924,i,3356028137122209941,6130102327857804493,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5364 --field-trial-handle=1924,i,3356028137122209941,6130102327857804493,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2356 --field-trial-handle=2312,i,16136929892775610022,11591041406869660376,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --mojo-platform-channel-handle=5756 --field-trial-handle=1924,i,3356028137122209941,6130102327857804493,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --mojo-platform-channel-handle=4648 --field-trial-handle=1924,i,3356028137122209941,6130102327857804493,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 744 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7460 --field-trial-handle=2296,i,4125081003201192219,3596134351255734137,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 872 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3492 --field-trial-handle=2296,i,4125081003201192219,3596134351255734137,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --mojo-platform-channel-handle=5744 --field-trial-handle=1924,i,3356028137122209941,6130102327857804493,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7916 --field-trial-handle=2296,i,4125081003201192219,3596134351255734137,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
47 546
Read events
46 269
Write events
622
Delete events
655
Modification events
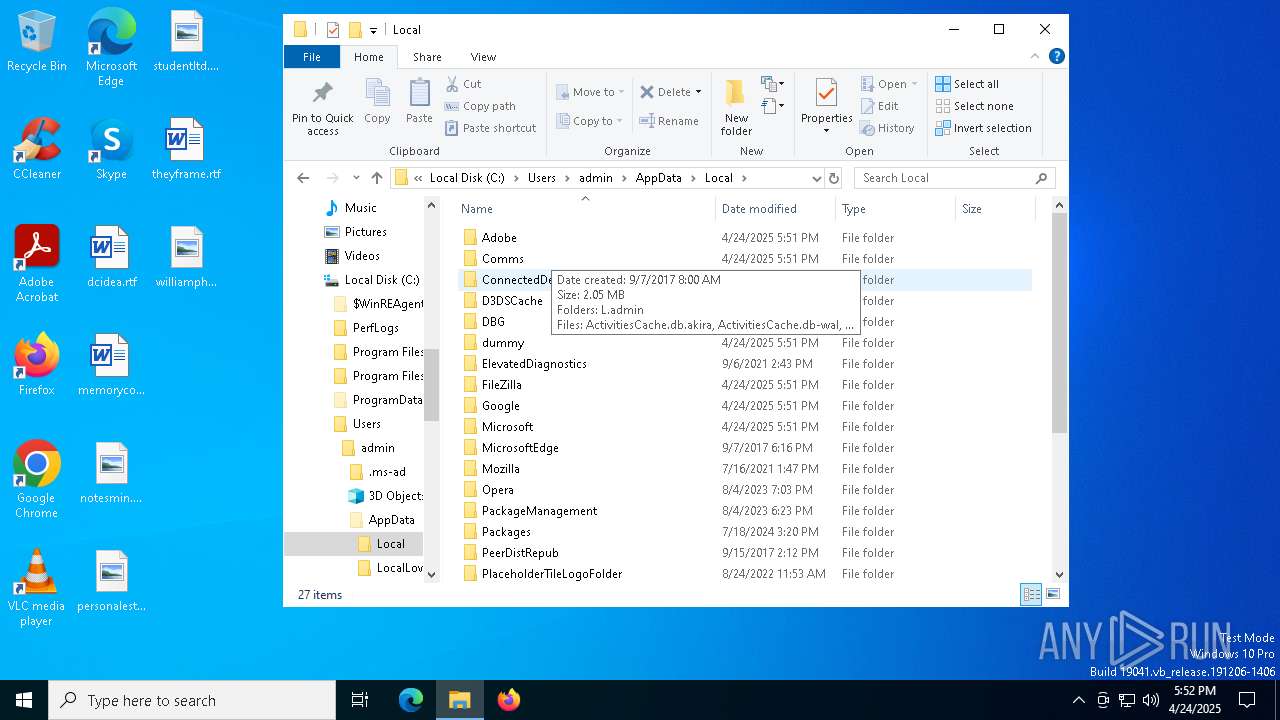
| (PID) Process: | (7264) win.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0002 |
| Operation: | write | Name: | Sequence |
Value: 2 | |||
| (PID) Process: | (7264) win.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Owner |
Value: 601C00000DB1BA7A41B5DB01 | |||
| (PID) Process: | (7264) win.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | SessionHash |
Value: 08C94BBA3441880F40BD5A4ADADEE44B062B67F1F096761363D68922896783ED | |||
| (PID) Process: | (7264) win.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (7264) win.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\ConnectedDevicesPlatform\L.admin\ActivitiesCache.db-shm | |||
| (PID) Process: | (7264) win.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFilesHash |
Value: 1D9BD79D65CF4766E56DC9FCD820CDD634CBAC2E82C446318C6F82DF392F4867 | |||
| (PID) Process: | (7264) win.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Sequence |
Value: 2 | |||
| (PID) Process: | (7264) win.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0002 |
| Operation: | write | Name: | Owner |
Value: 601C00000DB1BA7A41B5DB01 | |||
| (PID) Process: | (7264) win.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0002 |
| Operation: | write | Name: | SessionHash |
Value: FEF7D6640665FBF17E095DA7B95383D6D8F7B62406340806DA08F115F498C86D | |||
| (PID) Process: | (7264) win.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0002 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
Executable files
264
Suspicious files
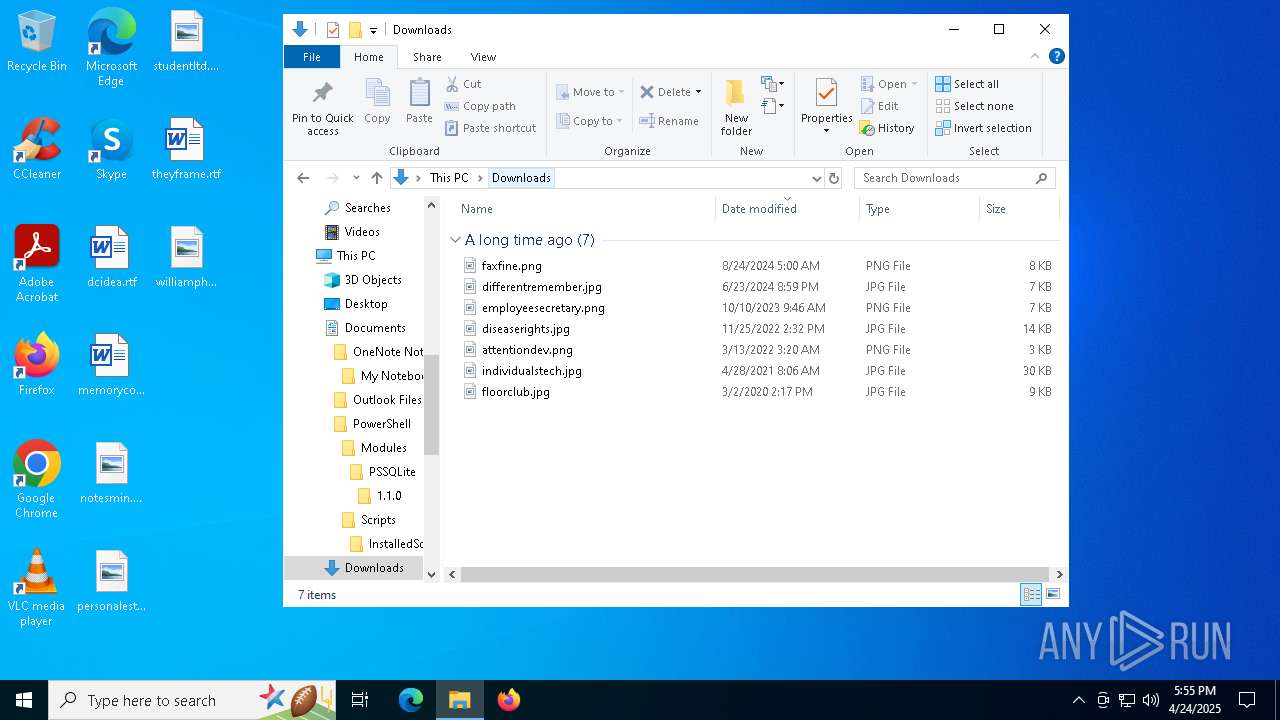
7 525
Text files
3 286
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7412 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:AFF88F6B85745502FCC8A2BA576CAA60 | SHA256:42B1CE8C922CB4C67B98832A2BBCD2EA2B9E5F539692F54C45675A9A752A61D6 | |||
| 7412 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_z33gpcu3.04h.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
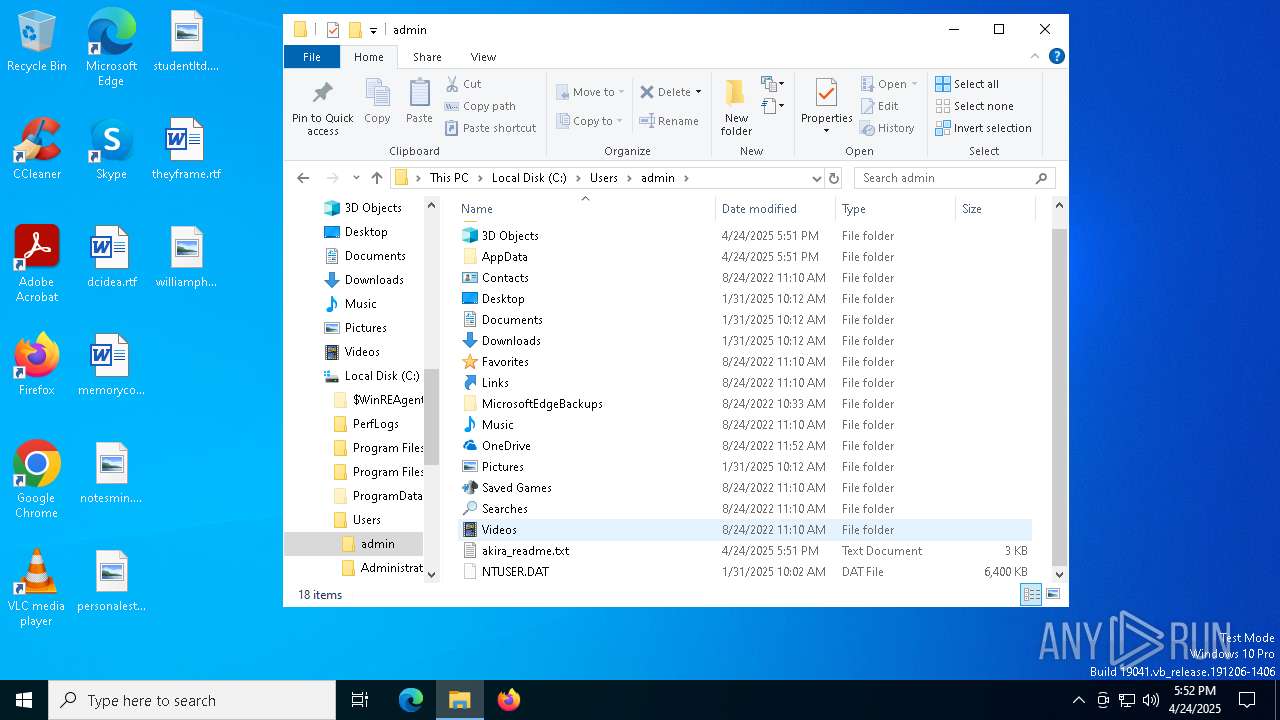
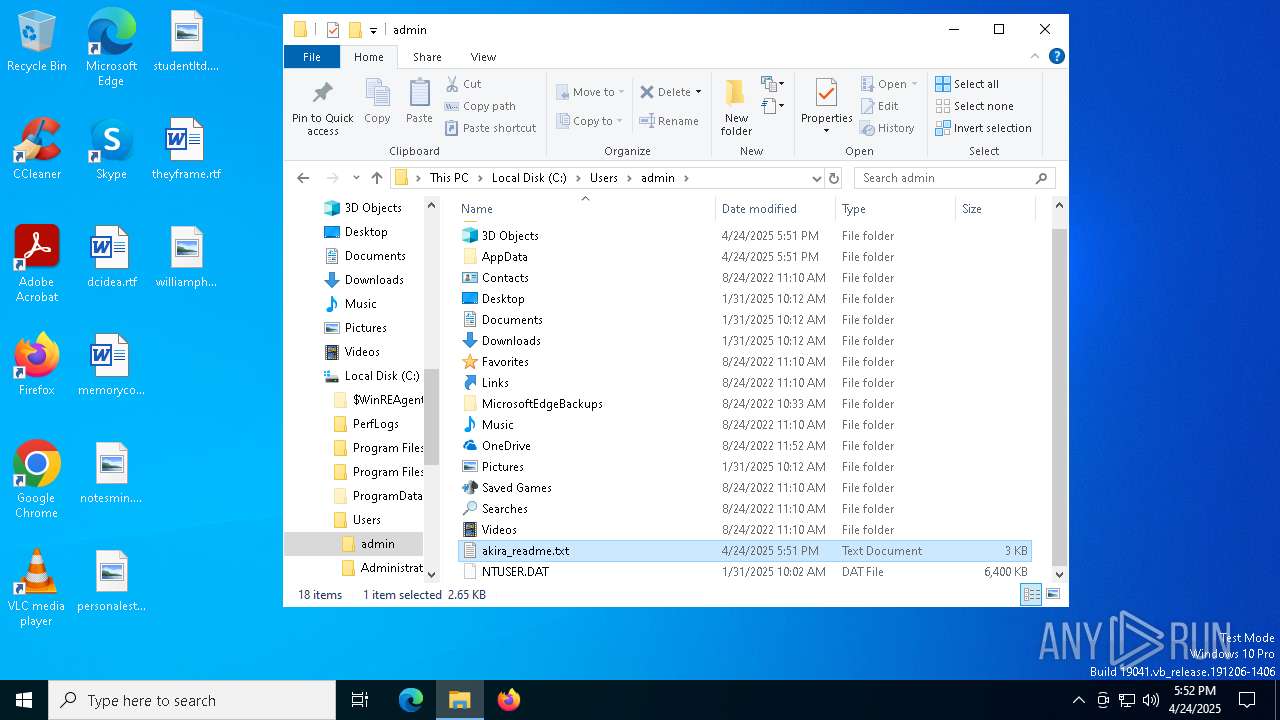
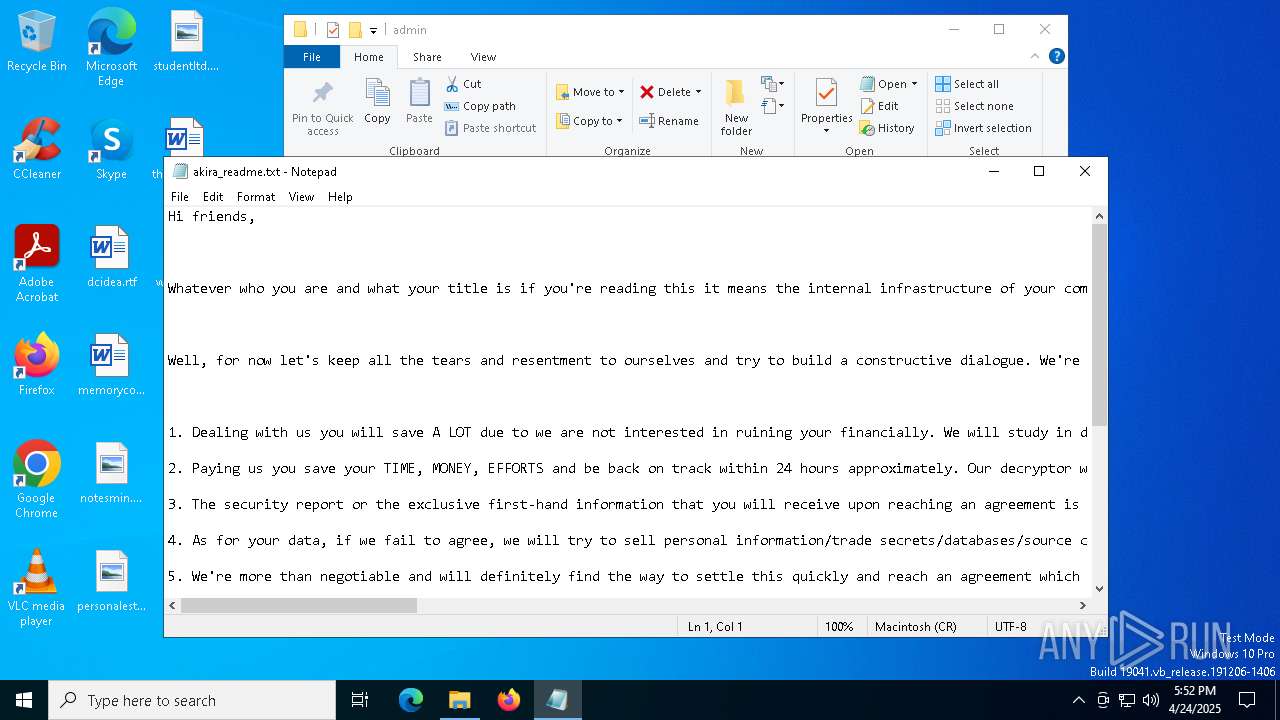
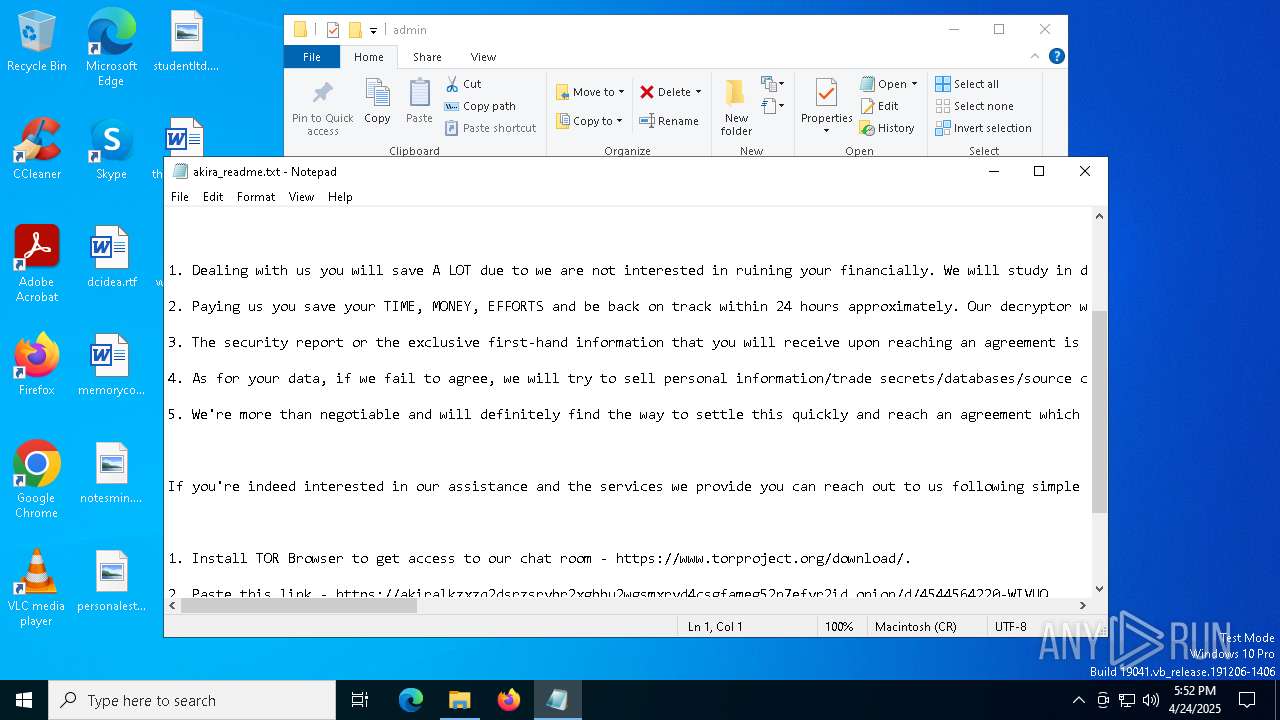
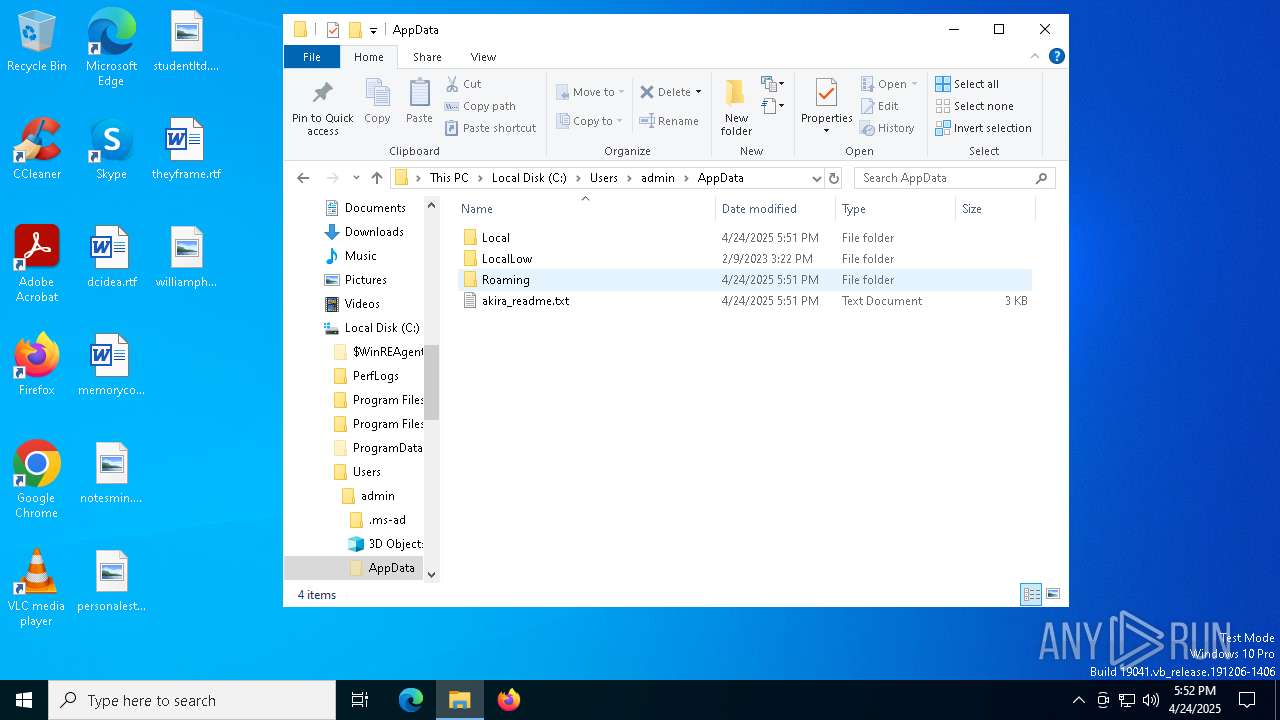
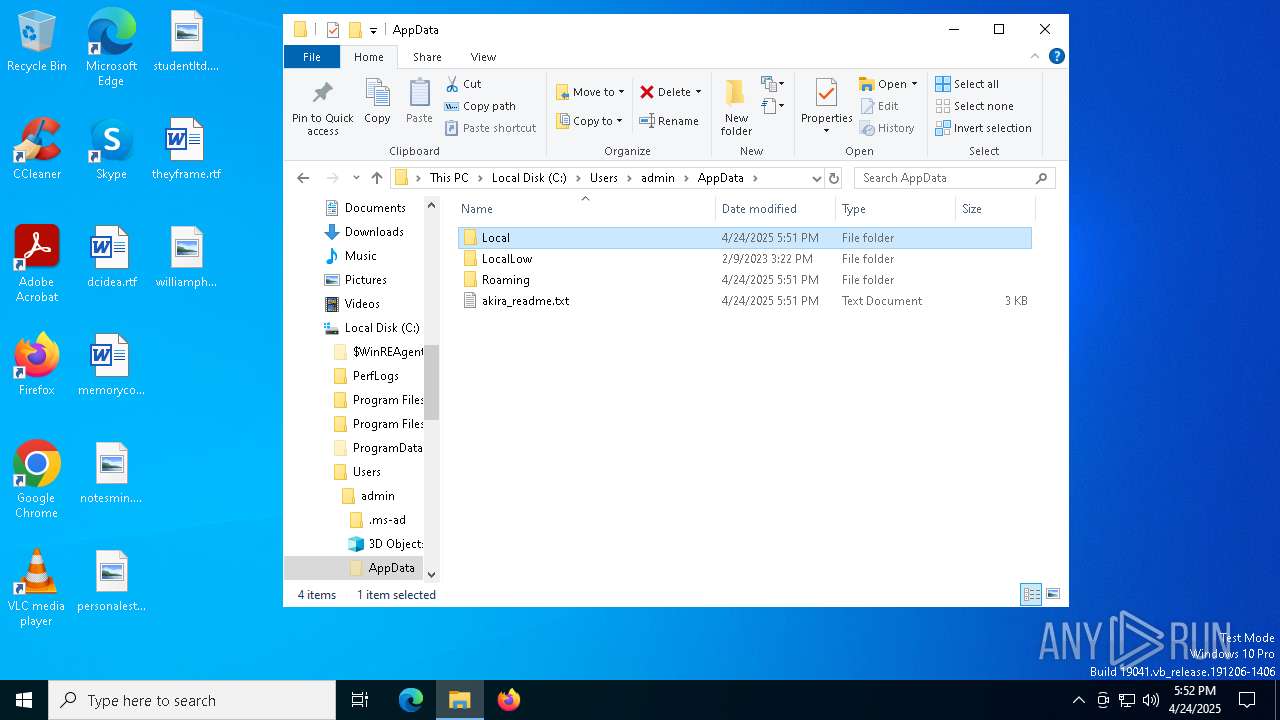
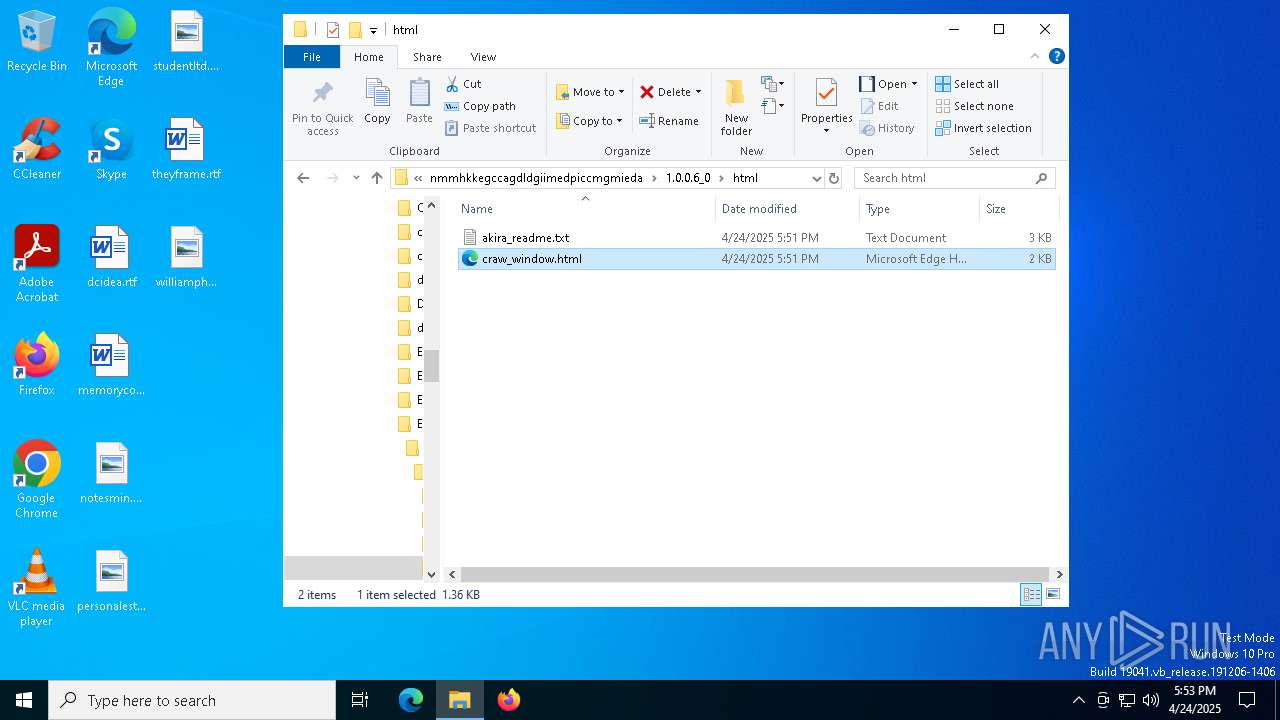
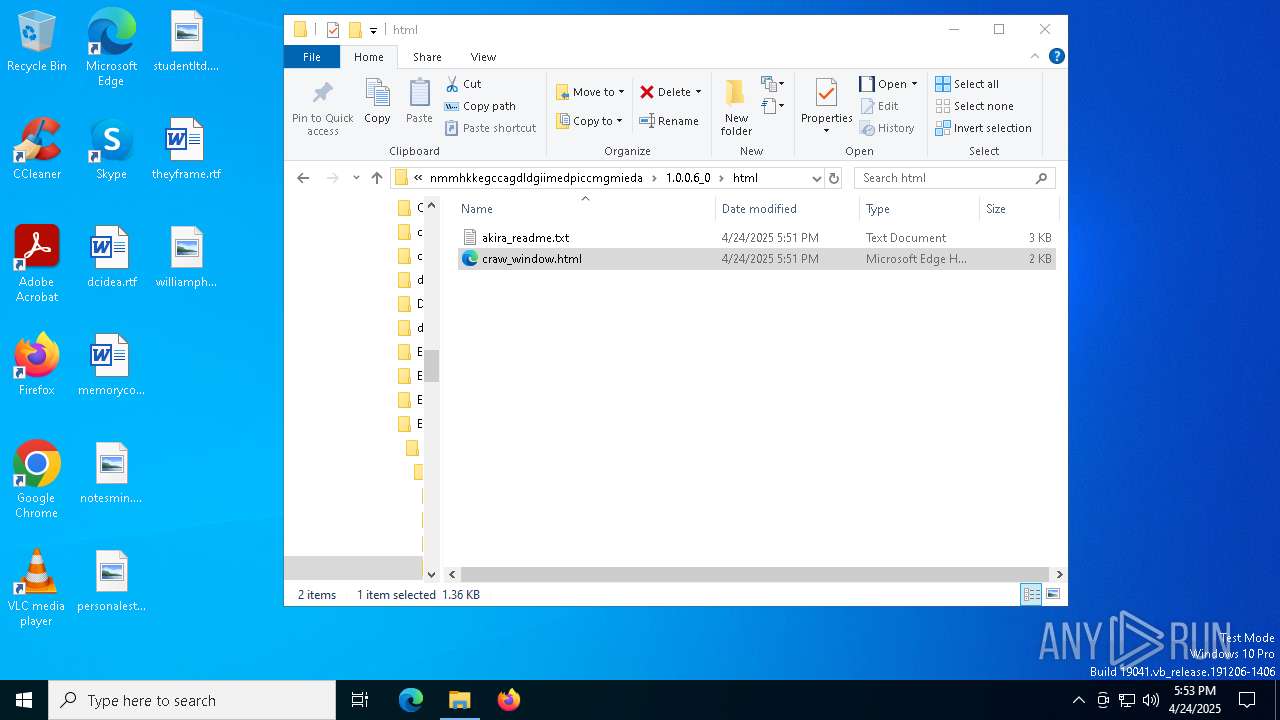
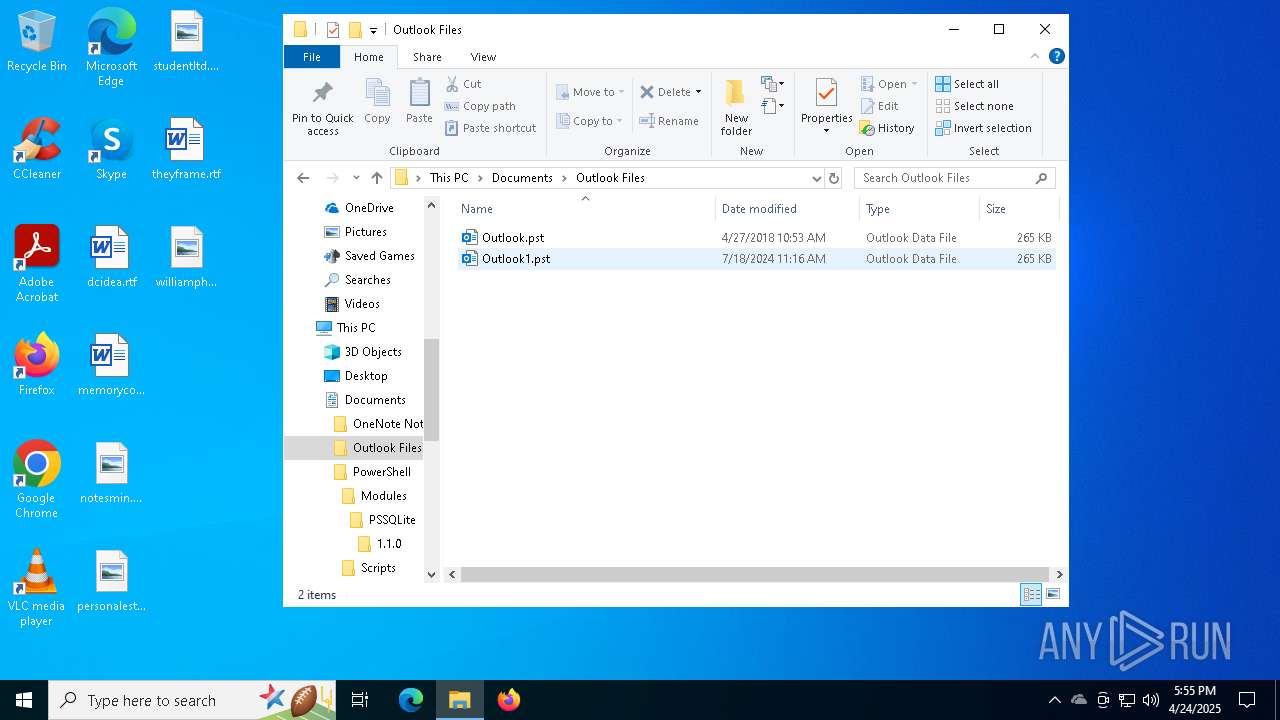
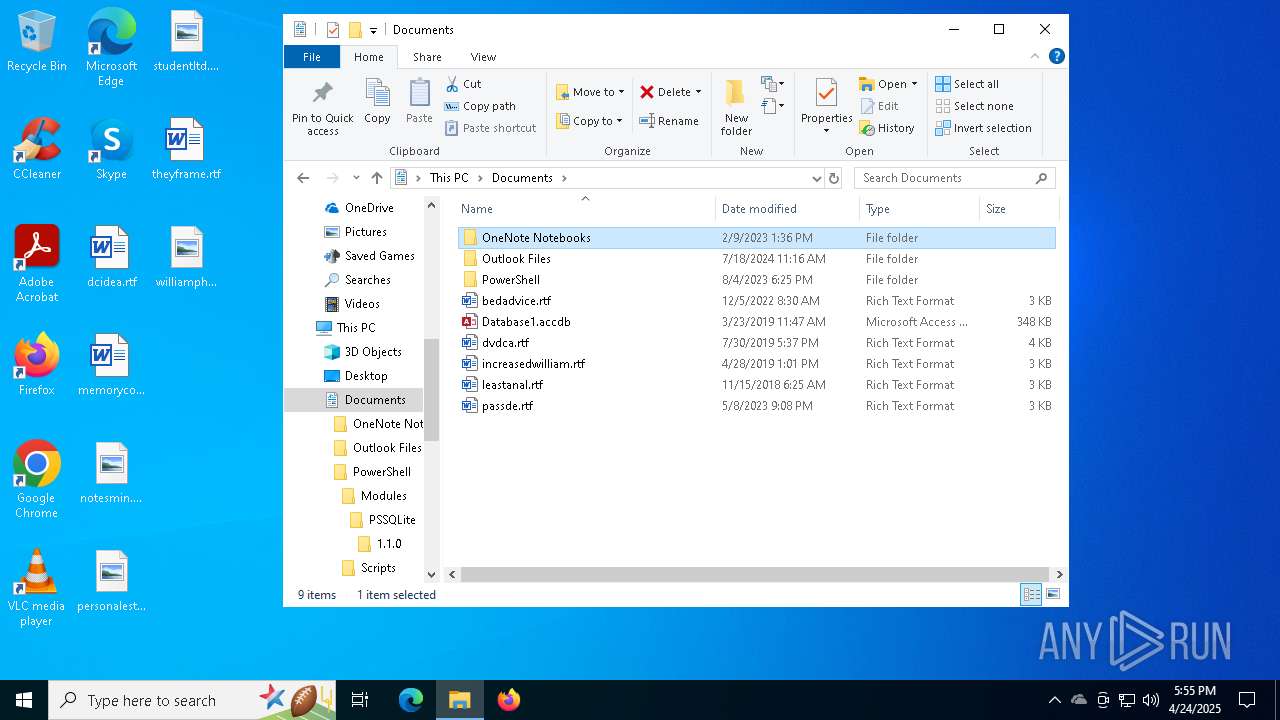
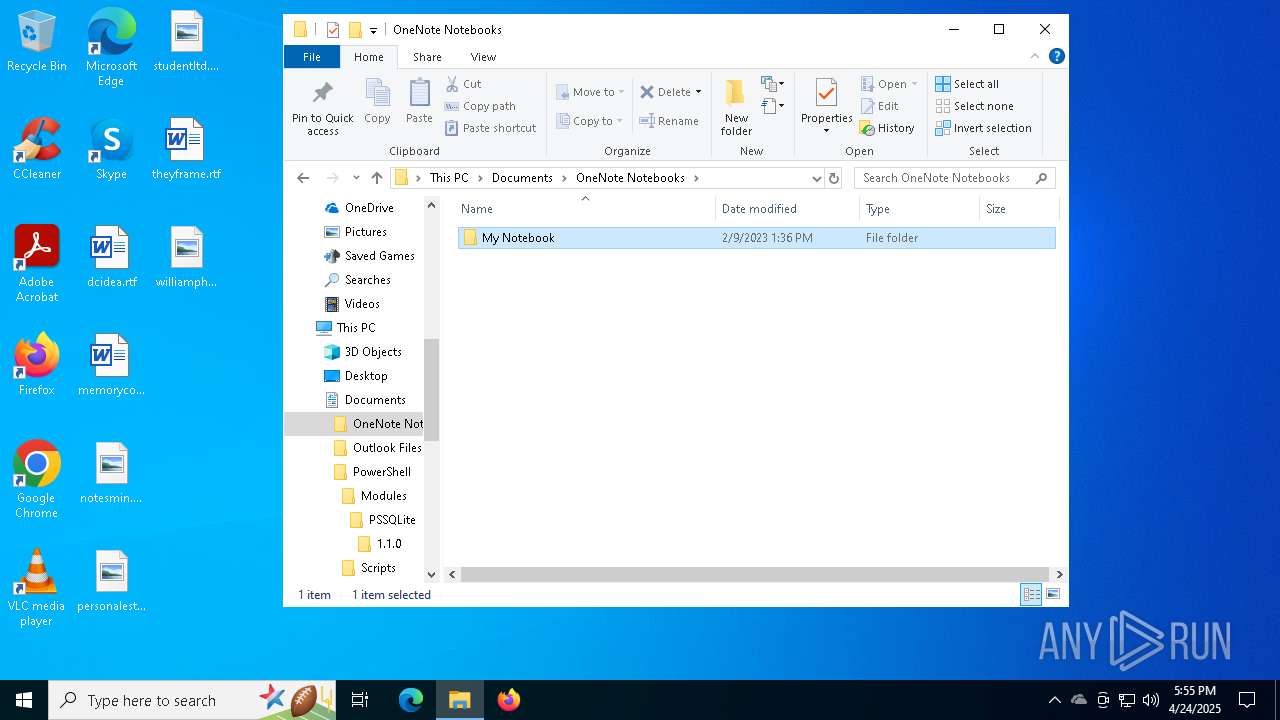
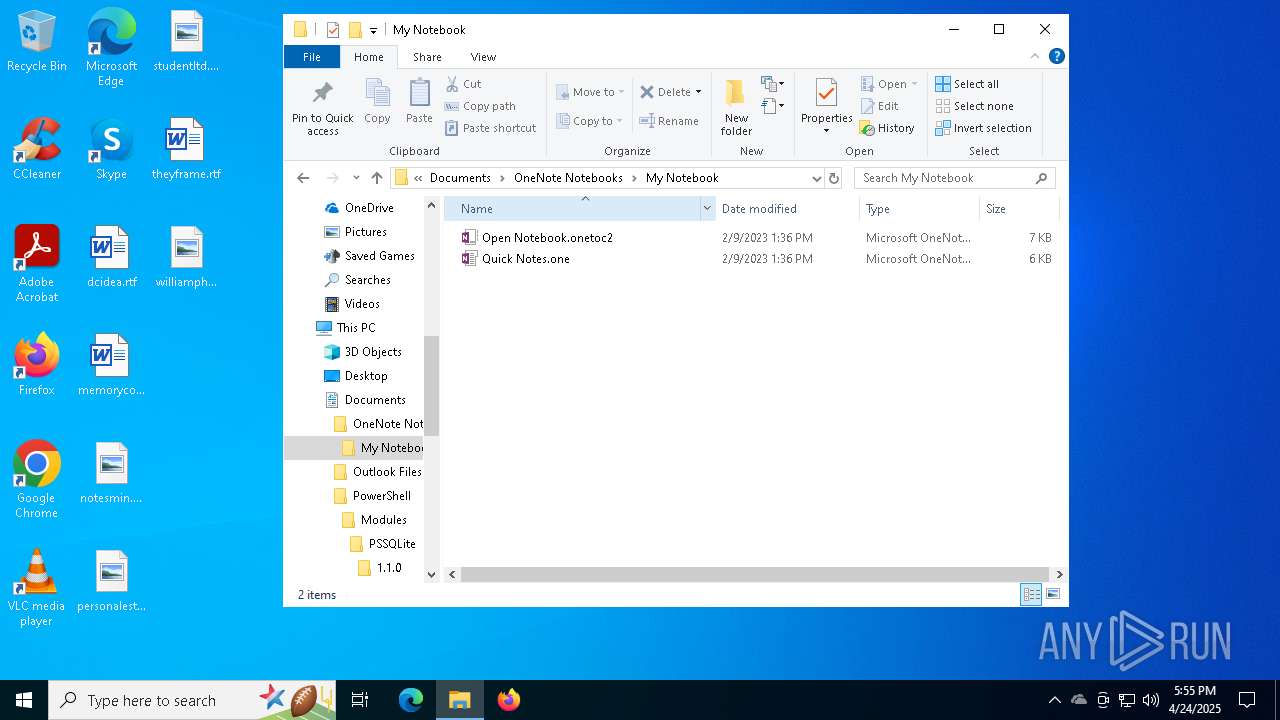
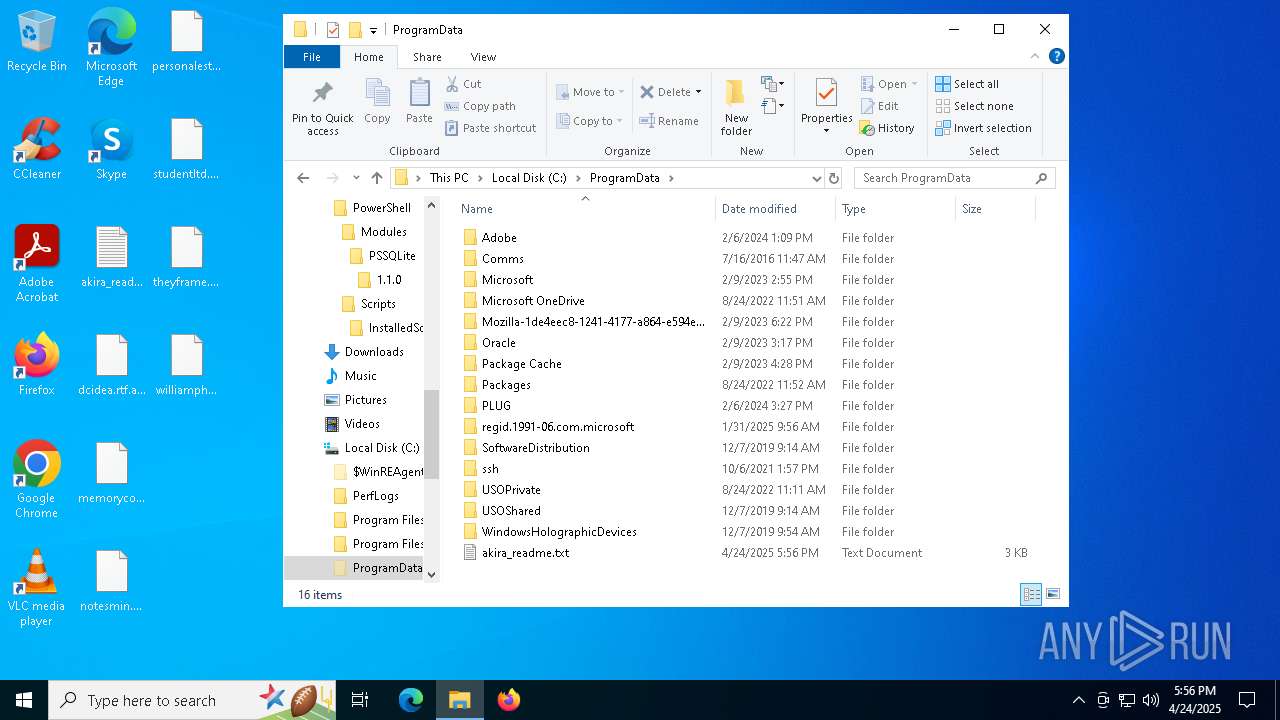
| 7264 | win.exe | C:\Users\admin\AppData\Local\akira_readme.txt | text | |
MD5:7E1774A51F33B59AEB9919CBC37875D6 | SHA256:7C47CDDF82409AFA1427F592138CD10F37EE8E8F7AFBE4320881825E48034456 | |||
| 7264 | win.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\Files\akira_readme.txt | text | |
MD5:7E1774A51F33B59AEB9919CBC37875D6 | SHA256:7C47CDDF82409AFA1427F592138CD10F37EE8E8F7AFBE4320881825E48034456 | |||
| 7264 | win.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\akira_readme.txt | text | |
MD5:7E1774A51F33B59AEB9919CBC37875D6 | SHA256:7C47CDDF82409AFA1427F592138CD10F37EE8E8F7AFBE4320881825E48034456 | |||
| 7412 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_oafpfrct.tfv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7264 | win.exe | C:\bootTel.dat | binary | |
MD5:D8AAB76C4F564BC05F8BF9F66013CDA1 | SHA256:18E185BF37E6E8BB5A3FD039A7AEED7F6D31DE7F219FD630F930F2B2466C268E | |||
| 7264 | win.exe | C:\Users\admin\akira_readme.txt | text | |
MD5:7E1774A51F33B59AEB9919CBC37875D6 | SHA256:7C47CDDF82409AFA1427F592138CD10F37EE8E8F7AFBE4320881825E48034456 | |||
| 7264 | win.exe | C:\Users\admin\3D Objects\akira_readme.txt | text | |
MD5:7E1774A51F33B59AEB9919CBC37875D6 | SHA256:7C47CDDF82409AFA1427F592138CD10F37EE8E8F7AFBE4320881825E48034456 | |||
| 7264 | win.exe | C:\Users\admin\AppData\akira_readme.txt | text | |
MD5:7E1774A51F33B59AEB9919CBC37875D6 | SHA256:7C47CDDF82409AFA1427F592138CD10F37EE8E8F7AFBE4320881825E48034456 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
153
DNS requests
189
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 2.17.251.99:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.21.189.233:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.21.189.233:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2852 | SIHClient.exe | GET | 200 | 2.21.189.233:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2852 | SIHClient.exe | GET | 200 | 2.21.189.233:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.210.252.238:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
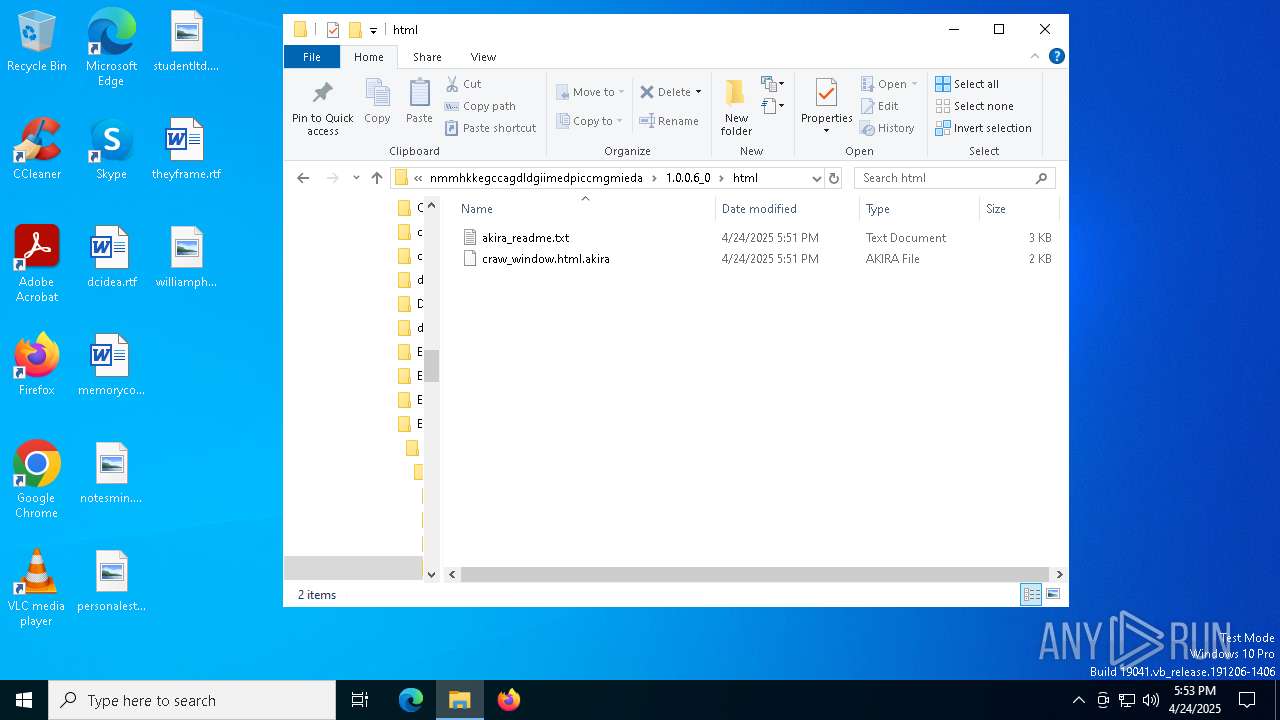
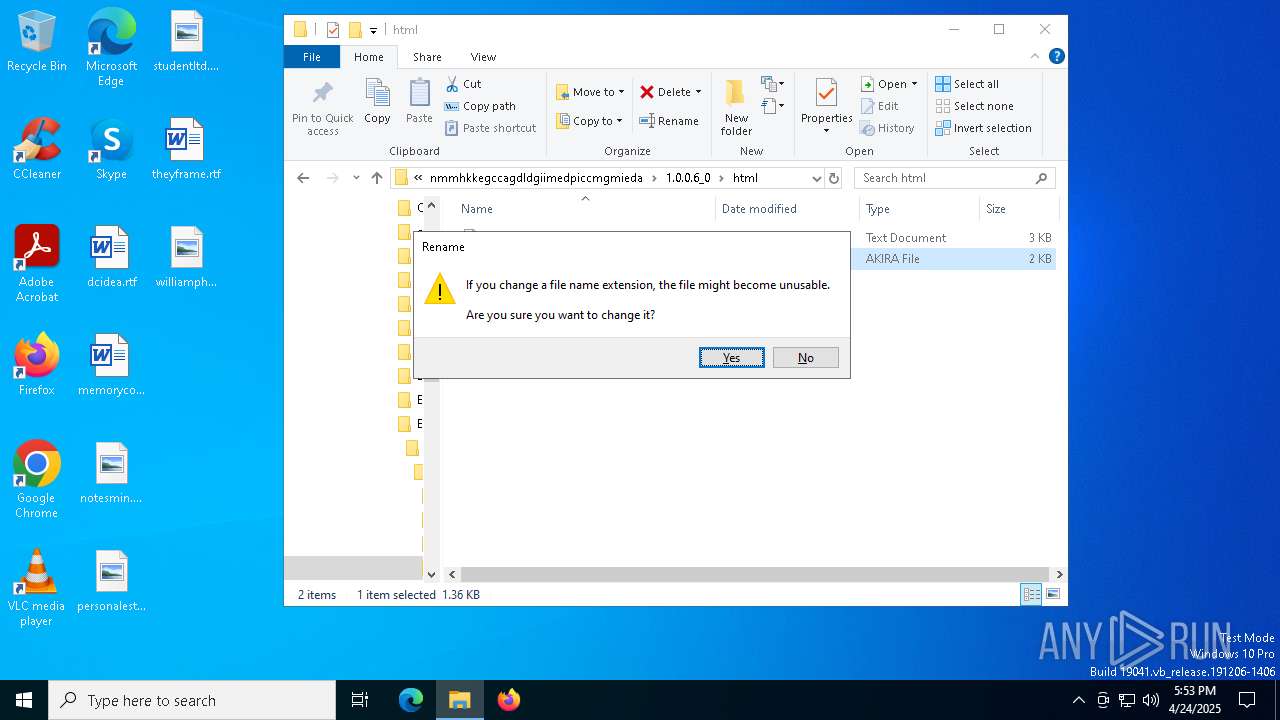
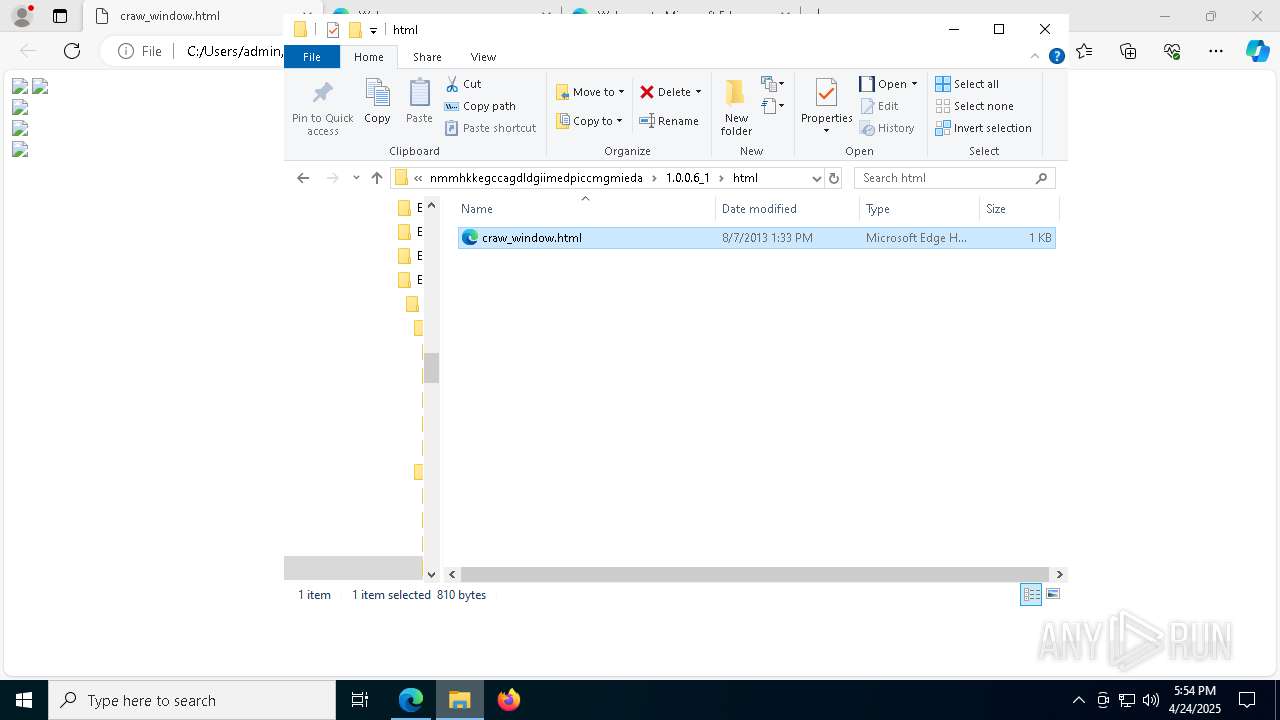
7612 | chrome.exe | GET | 302 | 216.58.207.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | unknown | — | — | whitelisted |
7612 | chrome.exe | GET | 200 | 173.194.15.10:80 | http://r5---sn-f5f7lnld.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&met=1745517238,&mh=e_&mip=185.241.208.71&mm=28&mn=sn-f5f7lnld&ms=nvh&mt=1745516901&mv=m&mvi=5&pl=24&rmhost=r2---sn-f5f7lnld.gvt1.com&rms=nvh,nvh&shardbypass=sd | unknown | — | — | unknown |
4824 | backgroundTaskHost.exe | GET | 200 | 23.210.252.238:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5416 | SearchApp.exe | GET | 200 | 23.210.252.238:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 2.17.251.99:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 2.21.189.233:80 | www.microsoft.com | Akamai International B.V. | GB | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.21.189.233:80 | www.microsoft.com | Akamai International B.V. | GB | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 4.207.247.137:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | svchost.exe | 20.190.147.9:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 23.210.252.238:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5136 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
5136 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
5136 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
5136 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |