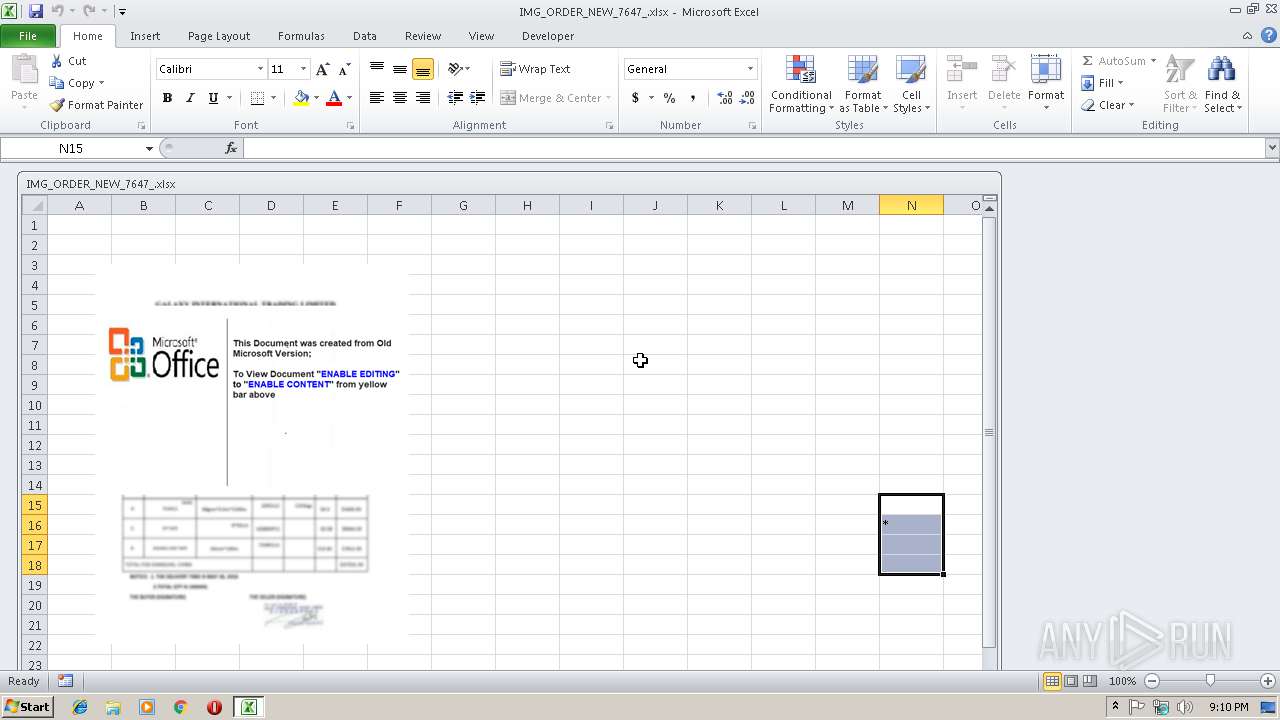
| File name: | IMG_ORDER_NEW_7647_.xlsx |
| Full analysis: | https://app.any.run/tasks/f2b1c013-6542-48ec-b998-237067c5a5fd |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | January 22, 2019, 21:10:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/encrypted |
| File info: | CDFV2 Encrypted |
| MD5: | A2CD8D4D640604CC7A47A7B5B480C321 |
| SHA1: | 43B3DED1BC24F843CFBEA9A54F933F41A1612F51 |
| SHA256: | BFAEBEB4A8B10DE53D5D31EC919140E4C5741885A4FE629DE6542F574CA6B2F7 |
| SSDEEP: | 3072:5Icg/zDGgRQ49QRItHLrFG5tk9TD6c0H0cA/ejoK6WcMoEiKhA9hnmB1Ekko8oy:CxNoufFKk9T2c0H+/ejofQxCszEfAy |
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 2564)
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 2564)
FORMBOOK was detected
- explorer.exe (PID: 284)
Application was dropped or rewritten from another process
- vbc.exe (PID: 2364)
- regsvcbzd0yr.exe (PID: 3380)
Downloads executable files from the Internet
- EQNEDT32.EXE (PID: 2564)
Downloads executable files from IP
- EQNEDT32.EXE (PID: 2564)
Connects to CnC server
- explorer.exe (PID: 284)
Changes the autorun value in the registry
- spoolsv.exe (PID: 3416)
Formbook was detected
- spoolsv.exe (PID: 3416)
- Firefox.exe (PID: 2936)
Actions looks like stealing of personal data
- spoolsv.exe (PID: 3416)
Stealing of credential data
- spoolsv.exe (PID: 3416)
SUSPICIOUS
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 2564)
- explorer.exe (PID: 284)
- DllHost.exe (PID: 2864)
Starts CMD.EXE for commands execution
- spoolsv.exe (PID: 3416)
Creates files in the user directory
- spoolsv.exe (PID: 3416)
Loads DLL from Mozilla Firefox
- spoolsv.exe (PID: 3416)
Creates files in the program directory
- DllHost.exe (PID: 2864)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2852)
Starts Microsoft Office Application
- explorer.exe (PID: 284)
Creates files in the user directory
- Firefox.exe (PID: 2936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
10
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1760 | /c del "C:\Users\Public\vbc.exe" | C:\Windows\System32\cmd.exe | — | spoolsv.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2364 | "C:\Users\Public\vbc.exe" | C:\Users\Public\vbc.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: cAnNoN Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2852 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2864 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | spoolsv.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3036 | "C:\Windows\System32\systray.exe" | C:\Windows\System32\systray.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Systray .exe stub Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3380 | "C:\Program Files\H3f3du\regsvcbzd0yr.exe" | C:\Program Files\H3f3du\regsvcbzd0yr.exe | — | explorer.exe | |||||||||||
User: admin Company: cAnNoN Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3416 | "C:\Windows\System32\spoolsv.exe" | C:\Windows\System32\spoolsv.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
772
Read events
713
Write events
47
Delete events
12
Modification events
| (PID) Process: | (2852) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 32, |
Value: 33322C00240B0000010000000000000000000000 | |||
| (PID) Process: | (2852) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2852) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2852) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 240B000006EE04F696B2D40100000000 | |||
| (PID) Process: | (2852) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | 32, |
Value: 33322C00240B0000010000000000000000000000 | |||
| (PID) Process: | (2852) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2852) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2852) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2852) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2852) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\20EECA |
| Operation: | write | Name: | 20EECA |
Value: 04000000240B00003A00000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0049004D0047005F004F0052004400450052005F004E00450057005F0037003600340037005F002E0078006C0073007800000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000100000000000000B01217F796B2D401CAEE2000CAEE200000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
4
Suspicious files
73
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2852 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVREA83.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2364 | vbc.exe | C:\Users\admin\AppData\Local\Temp\~DF1D6F24AC6D6292EB.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4BFE3FBE.png | — | |
MD5:— | SHA256:— | |||
| 2852 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFEFECA6A9BF18DA00.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~$IMG_ORDER_NEW_7647_.xlsx | — | |
MD5:— | SHA256:— | |||
| 3416 | spoolsv.exe | C:\Users\admin\AppData\Roaming\N05-24-S\N05logrc.ini | binary | |
MD5:— | SHA256:— | |||
| 2564 | EQNEDT32.EXE | C:\Users\Public\vbc.exe | executable | |
MD5:— | SHA256:— | |||
| 2564 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\vbc[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2864 | DllHost.exe | C:\Program Files\H3f3du\regsvcbzd0yr.exe | executable | |
MD5:— | SHA256:— | |||
| 3416 | spoolsv.exe | C:\Users\admin\AppData\Roaming\N05-24-S\N05logim.jpeg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2564 | EQNEDT32.EXE | GET | 200 | 23.249.161.100:80 | http://23.249.161.100/jhn/vbc.exe | US | executable | 548 Kb | malicious |
284 | explorer.exe | GET | 404 | 91.215.217.222:80 | http://www.facebookconference.com/j01/?t8LTihM=ILzlljN6ynM8ROxU2NWywNDYmIcwAC92pmMqTCwgByQJCV1UCUleNmdHOiYv3OxMh2qDbg==&3f6=ll1DUf | BG | html | 321 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2564 | EQNEDT32.EXE | 23.249.161.100:80 | — | ColoCrossing | US | malicious |
284 | explorer.exe | 91.215.217.222:80 | www.facebookconference.com | Internet Corporated Networks Ltd. | BG | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.facebookconference.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2564 | EQNEDT32.EXE | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2564 | EQNEDT32.EXE | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2564 | EQNEDT32.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M1 |
2564 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2564 | EQNEDT32.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M2 |
2564 | EQNEDT32.EXE | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
284 | explorer.exe | A Network Trojan was detected | SC SPYWARE Trojan-Spy.Win32.Noon |
284 | explorer.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious HTTP-GET request with body and minimal header |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1 ETPRO signatures available at the full report