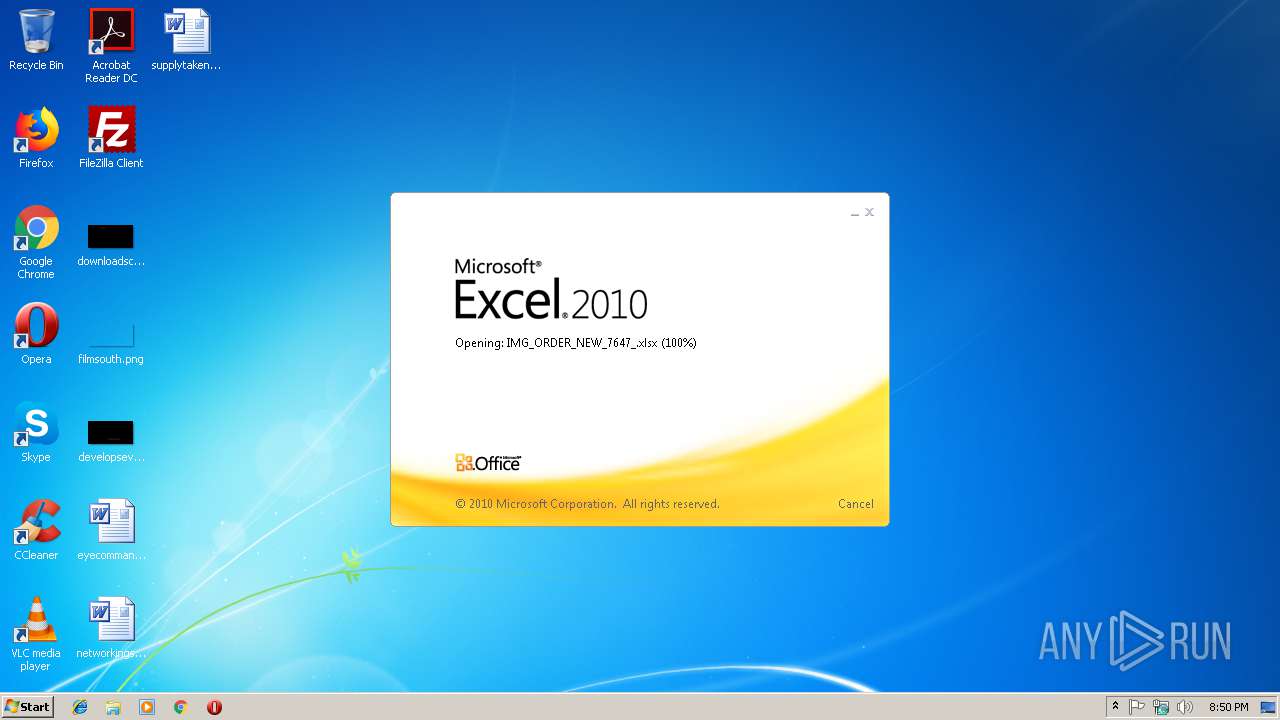
| File name: | IMG_ORDER_NEW_7647_.xlsx |
| Full analysis: | https://app.any.run/tasks/a94679ce-bf21-4923-9d7e-0089e92d1736 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | January 22, 2019, 20:50:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/encrypted |
| File info: | CDFV2 Encrypted |
| MD5: | A2CD8D4D640604CC7A47A7B5B480C321 |
| SHA1: | 43B3DED1BC24F843CFBEA9A54F933F41A1612F51 |
| SHA256: | BFAEBEB4A8B10DE53D5D31EC919140E4C5741885A4FE629DE6542F574CA6B2F7 |
| SSDEEP: | 3072:5Icg/zDGgRQ49QRItHLrFG5tk9TD6c0H0cA/ejoK6WcMoEiKhA9hnmB1Ekko8oy:CxNoufFKk9T2c0H+/ejofQxCszEfAy |
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3024)
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 3024)
Application was dropped or rewritten from another process
- vbc.exe (PID: 2816)
Downloads executable files from IP
- EQNEDT32.EXE (PID: 3024)
Downloads executable files from the Internet
- EQNEDT32.EXE (PID: 3024)
Uses SVCHOST.EXE for hidden code execution
- explorer.exe (PID: 116)
FORMBOOK was detected
- explorer.exe (PID: 116)
Changes the autorun value in the registry
- svchost.exe (PID: 2924)
Connects to CnC server
- explorer.exe (PID: 116)
Formbook was detected
- svchost.exe (PID: 2924)
- Firefox.exe (PID: 3984)
Actions looks like stealing of personal data
- svchost.exe (PID: 2924)
Stealing of credential data
- svchost.exe (PID: 2924)
SUSPICIOUS
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 3024)
Creates files in the user directory
- explorer.exe (PID: 116)
- svchost.exe (PID: 2924)
Reads Internet Cache Settings
- explorer.exe (PID: 116)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 2924)
Loads DLL from Mozilla Firefox
- svchost.exe (PID: 2924)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2876)
Starts Microsoft Office Application
- explorer.exe (PID: 116)
Creates files in the user directory
- EXCEL.EXE (PID: 2876)
- Firefox.exe (PID: 3984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2816 | "C:\Users\Public\vbc.exe" | C:\Users\Public\vbc.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: cAnNoN Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2924 | "C:\Windows\System32\svchost.exe" | C:\Windows\System32\svchost.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3024 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3484 | /c del "C:\Users\Public\vbc.exe" | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3984 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | svchost.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
Total events
722
Read events
655
Write events
58
Delete events
9
Modification events
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000AF35259D31591640B37B8C26D82B0E0D000000000200000000001066000000010000200000002DB5B1B5E8BE56D28C8606851CEBDA8CC24797AEBE4A2C1CBC3C2680CD832122000000000E8000000002000020000000513932600BB2026BC92BD1E805CBE6444E55F2266B9B13E8D2CE48490ED73513300000009997EF3106787ECE301FE1006EA828804FBA0B25AF8650F07B7DDBF4D65BDF961F32910F73F267AC6A357C5E1DA87C74400000003BC9C4FE7FEABDADB5964ECC413BEC393E521976770A69E367D76EA3422B5944FA22C57CAF1CB7282EE11E9DA01DC2F7694E4C15DE8E91AC7E9736AE9AD01AB2 | |||
| (PID) Process: | (2876) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 7q$ |
Value: 377124003C0B0000010000000000000000000000 | |||
| (PID) Process: | (2876) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2876) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2876) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 3C0B000016B3722994B2D40100000000 | |||
| (PID) Process: | (2876) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | 7q$ |
Value: 377124003C0B0000010000000000000000000000 | |||
| (PID) Process: | (2876) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2876) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2876) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2876) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
73
Text files
3
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2876 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR9197.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2816 | vbc.exe | C:\Users\admin\AppData\Local\Temp\~DF143D78B4BAE1CBEB.TMP | — | |
MD5:— | SHA256:— | |||
| 3024 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\vbc[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2876 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3024 | EQNEDT32.EXE | C:\Users\Public\vbc.exe | executable | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\9839aec31243a928.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 2924 | svchost.exe | C:\Users\admin\AppData\Roaming\N05-24-S\N05logim.jpeg | image | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 2876 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\IMG_ORDER_NEW_7647_.xlsx.LNK | lnk | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019012220190123\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3024 | EQNEDT32.EXE | GET | 200 | 23.249.161.100:80 | http://23.249.161.100/jhn/vbc.exe | US | executable | 548 Kb | malicious |
116 | explorer.exe | GET | 301 | 217.160.0.160:80 | http://www.libertyfallen.site/j01/?otJHZlY=AL0CkUwz6NK+2YVCnyC4od7xS/t1Z41i3c4vsXS+lnaDa4Wiw+nPJV9LyI+dyeBwoimfKA==&Mv18=cBUdRzC8V6Ut-P | DE | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3024 | EQNEDT32.EXE | 23.249.161.100:80 | — | ColoCrossing | US | malicious |
116 | explorer.exe | 217.160.0.160:80 | www.libertyfallen.site | 1&1 Internet SE | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.libertyfallen.site |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3024 | EQNEDT32.EXE | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3024 | EQNEDT32.EXE | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
3024 | EQNEDT32.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M1 |
3024 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3024 | EQNEDT32.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M2 |
3024 | EQNEDT32.EXE | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
116 | explorer.exe | A Network Trojan was detected | SC SPYWARE Trojan-Spy.Win32.Noon |
116 | explorer.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious HTTP-GET request with body and minimal header |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
1 ETPRO signatures available at the full report