| File name: | NEW_ORDER.xlsx |
| Full analysis: | https://app.any.run/tasks/7ec496bb-c127-4c51-85df-67da5624a83a |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | January 17, 2019, 17:19:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 5D3F544ADA90846FF608C20C84C9AF76 |
| SHA1: | 2B172C1DFF42D0A9B08AF2A9D2AD7F9E4AD9CD41 |
| SHA256: | BF8E43A69DE5589D719BBF99086A86B049C08DD6F8A9664FCA705398156CBA22 |
| SSDEEP: | 192:JC/1fOV8vdQjmDiU7k+vxZa/4wLiSXiOv5qhEl/JqPJcta:Ide8qmDiyJZa/HiSXPv5xpJqh |
MALICIOUS
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 2880)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 2880)
Application was dropped or rewritten from another process
- namehftgb.exe (PID: 2344)
- namehftgb.exe (PID: 380)
Downloads executable files from the Internet
- EQNEDT32.EXE (PID: 2880)
Detected Hawkeye Keylogger
- namehftgb.exe (PID: 380)
Actions looks like stealing of personal data
- vbc.exe (PID: 1996)
- vbc.exe (PID: 1852)
Stealing of credential data
- vbc.exe (PID: 1996)
- vbc.exe (PID: 1852)
SUSPICIOUS
Creates files in the user directory
- EQNEDT32.EXE (PID: 2880)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 2880)
Application launched itself
- namehftgb.exe (PID: 2344)
Executes scripts
- namehftgb.exe (PID: 380)
Connects to SMTP port
- namehftgb.exe (PID: 380)
INFO
Creates files in the user directory
- EXCEL.EXE (PID: 2772)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2772)
Reads the machine GUID from the registry
- EXCEL.EXE (PID: 2772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:01:17 05:03:24 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | docProps/ |
XML
| Application: | Microsoft Excel |
|---|---|
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| Company: | - |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 12 |
| CreateDate: | 2006:09:16 00:00:00Z |
| ModifyDate: | 2006:09:16 00:00:00Z |
XMP
| Creator: | POLOLOCO |
|---|
Total processes
40
Monitored processes
6
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 380 | "C:\Users\admin\AppData\Roaming\namehftgb.exe" | C:\Users\admin\AppData\Roaming\namehftgb.exe | namehftgb.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1852 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmpA1C4.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | namehftgb.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 Modules
| |||||||||||||||
| 1996 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp7583.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | namehftgb.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 Modules
| |||||||||||||||
| 2344 | "C:\Users\admin\AppData\Roaming\namehftgb.exe" | C:\Users\admin\AppData\Roaming\namehftgb.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.4756.1000 Modules
| |||||||||||||||
| 2880 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
Total events
551
Read events
488
Write events
56
Delete events
7
Modification events
| (PID) Process: | (2772) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | s)? |
Value: 73293F00D40A0000010000000000000000000000 | |||
| (PID) Process: | (2772) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2772) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2772) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: D40A0000F2E073DD88AED40100000000 | |||
| (PID) Process: | (2772) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | s)? |
Value: 73293F00D40A0000010000000000000000000000 | |||
| (PID) Process: | (2772) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2772) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2772) EXCEL.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | EXCELFiles |
Value: 1311834135 | |||
| (PID) Process: | (2772) EXCEL.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000100000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311834238 | |||
| (PID) Process: | (2772) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
2
Suspicious files
0
Text files
5
Unknown types
2
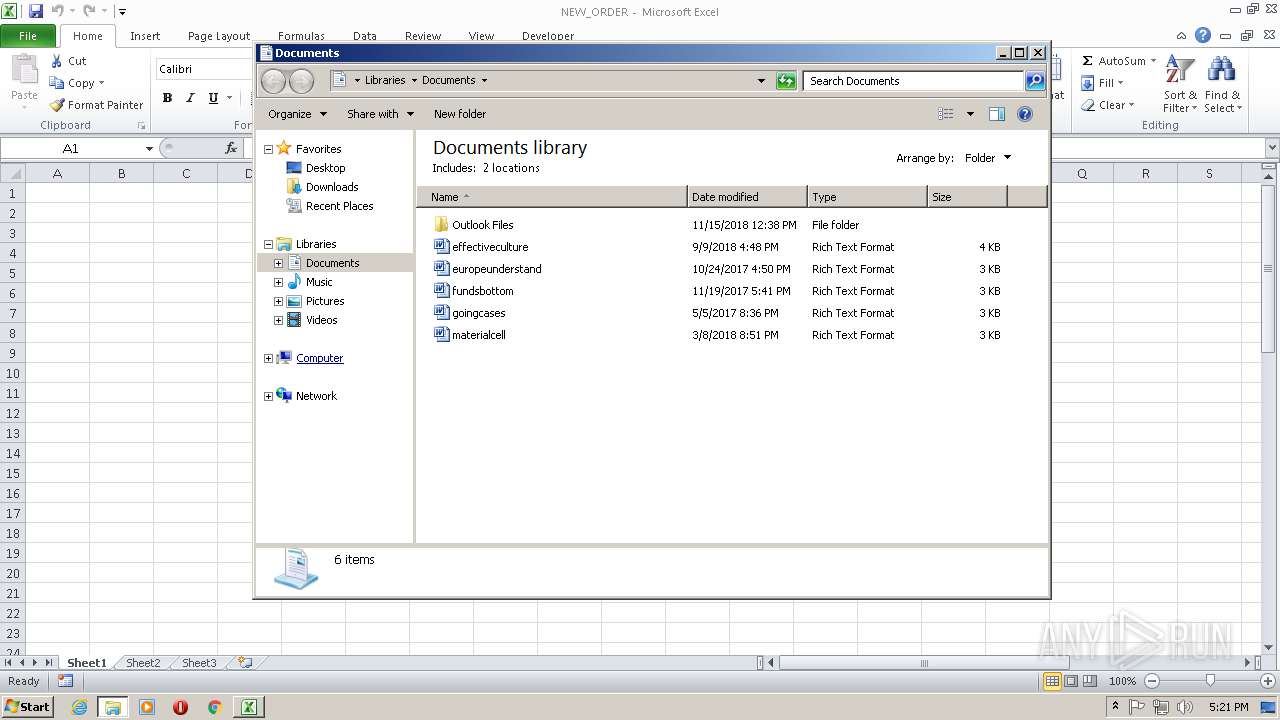
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2772 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR69D4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1996 | vbc.exe | C:\Users\admin\AppData\Local\Temp\bhv763E.tmp | — | |
MD5:— | SHA256:— | |||
| 2772 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2772 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\NEW_ORDER.LNK | lnk | |
MD5:— | SHA256:— | |||
| 1996 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmp7583.tmp | text | |
MD5:— | SHA256:— | |||
| 2880 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\namehftgb.exe | executable | |
MD5:— | SHA256:— | |||
| 380 | namehftgb.exe | C:\Users\admin\AppData\Local\Temp\42629f46-7f45-27b3-2ec8-5af31eecdb5f | text | |
MD5:— | SHA256:— | |||
| 2880 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\vva[1].exe | executable | |
MD5:— | SHA256:— | |||
| 1852 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmpA1C4.tmp | text | |
MD5:7FB9A9AD0FD9B1E0108ED71FBB276048 | SHA256:7D63C301317E144B0133A72250AE2D8E09AF65A92E6A807EC58A71939FE530A9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
3
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2880 | EQNEDT32.EXE | GET | 200 | 50.87.7.134:80 | http://rogamaquinaria.com/zpoo/vva.exe | US | executable | 1.02 Mb | malicious |
380 | namehftgb.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 13 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
380 | namehftgb.exe | 66.171.248.178:80 | bot.whatismyipaddress.com | Alchemy Communications, Inc. | US | malicious |
380 | namehftgb.exe | 185.20.209.34:587 | smtp.zoho.eu | Computerline GmbH | CH | malicious |
2880 | EQNEDT32.EXE | 50.87.7.134:80 | rogamaquinaria.com | Unified Layer | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rogamaquinaria.com |
| malicious |
bot.whatismyipaddress.com |
| shared |
smtp.zoho.eu |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2880 | EQNEDT32.EXE | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2880 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
380 | namehftgb.exe | Misc activity | SUSPICIOUS [PTsecurity] External IP Request (HawkEye) |
2 ETPRO signatures available at the full report