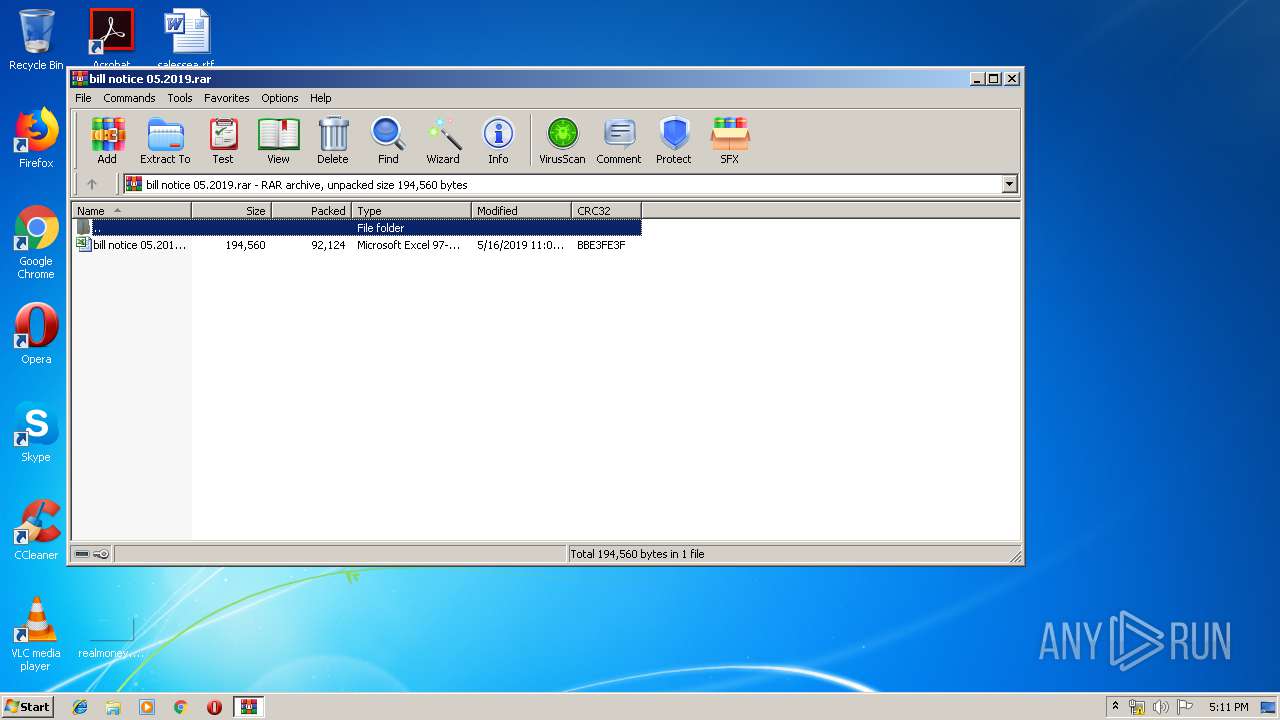
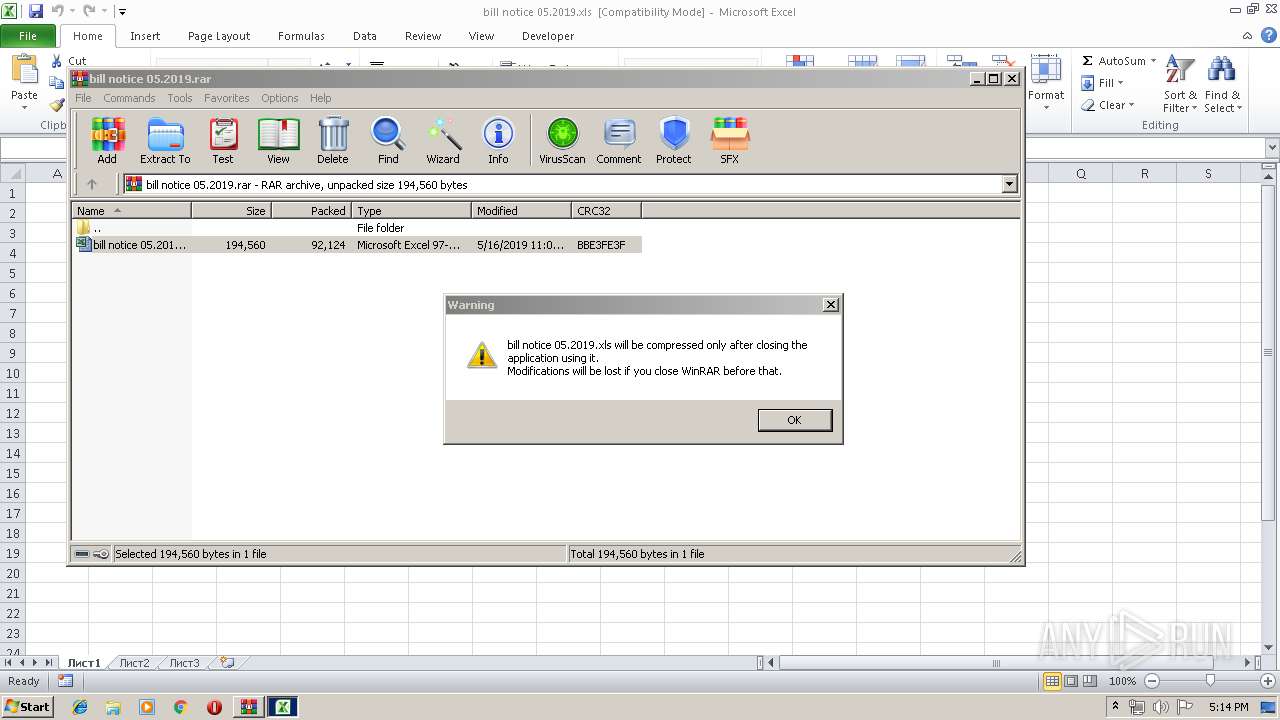
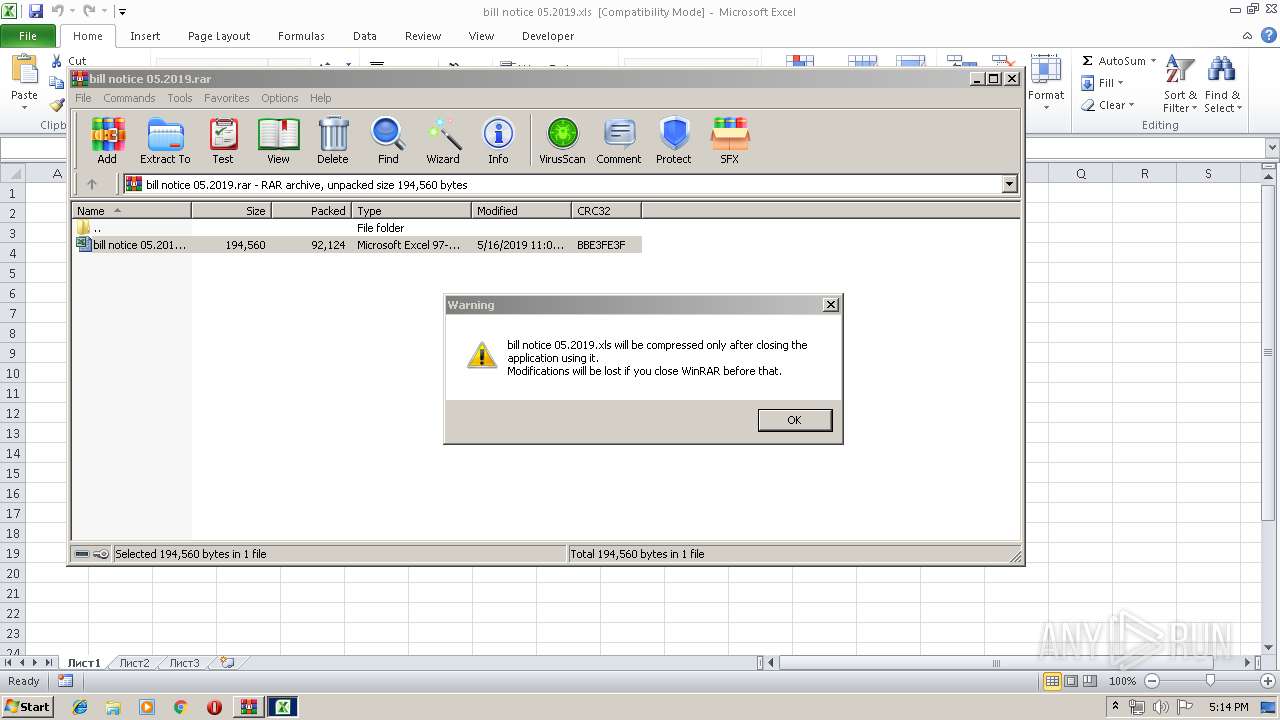
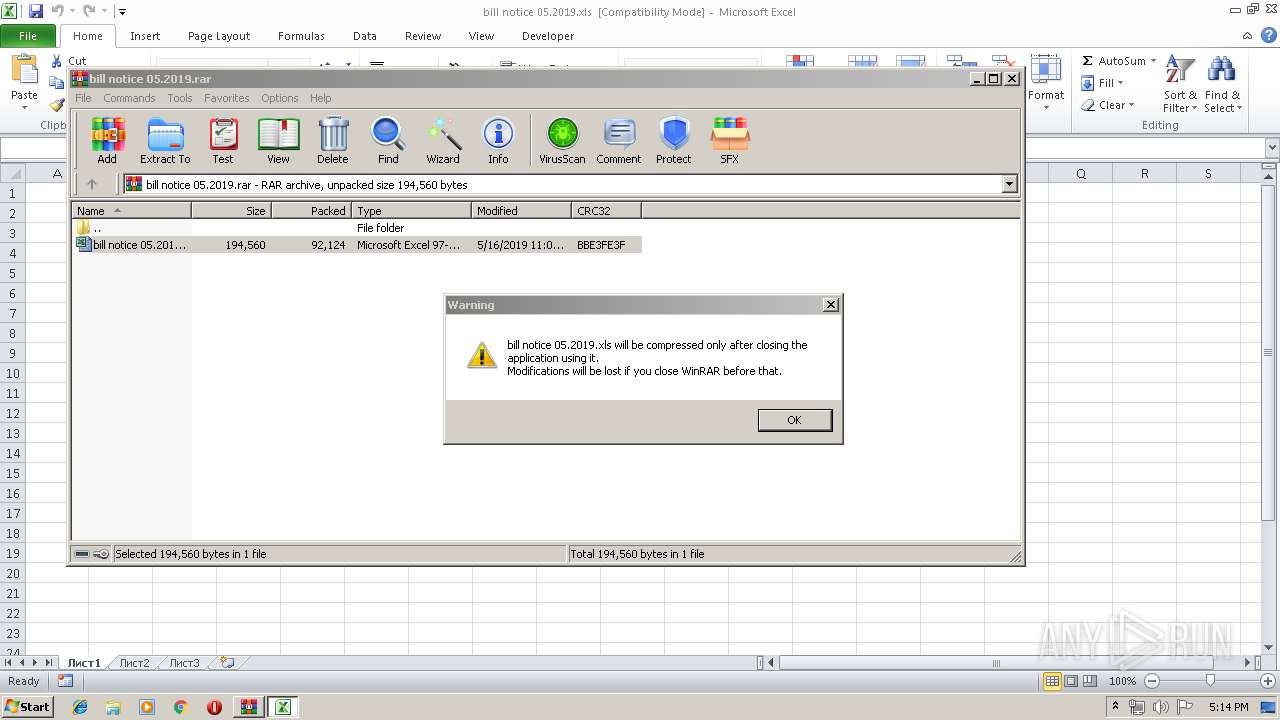
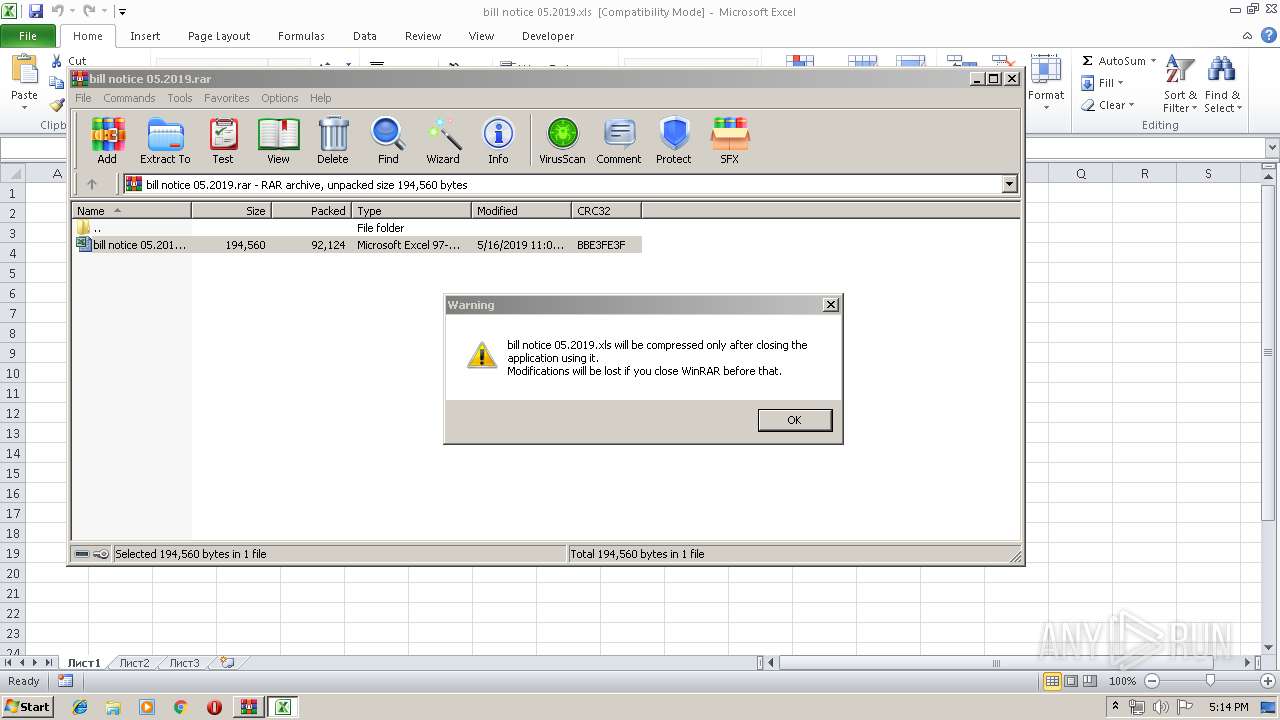
| File name: | bill notice 05.2019.rar |
| Full analysis: | https://app.any.run/tasks/6e30f5f4-b598-45bc-a850-157744ef8044 |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | May 20, 2019, 16:11:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 0569CA387F8B950E00B99E9ACB612BE9 |
| SHA1: | 33D0CDACED6249AA93B4B1B54D2005A907EE563F |
| SHA256: | BF5E00FA491B76FCCEEA0B8DE133F5C28E20C556FACCE6652E6BCA60FA946746 |
| SSDEEP: | 1536:Tr99BZ4Hi14xpjaCvCl7fnrZ0L/gCwKzDQV+o5p5t/1MxxJZ/dd6mEpjKCqvDawE:d9BZ4Hddsl50LpwKzcV+CqxrZWFsawE |
MALICIOUS
Loads the Task Scheduler COM API
- OSPPSVC.EXE (PID: 1808)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2156)
Application was dropped or rewritten from another process
- wprgxyeqd79.exe (PID: 1152)
- uninstall.exe (PID: 344)
- exit.exe (PID: 1812)
- rtegre.exe (PID: 3448)
- veter1605_MAPS_10cr0.exe (PID: 1404)
- exit.exe (PID: 900)
- winserv.exe (PID: 3324)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 2156)
Loads dropped or rewritten executable
- cmd.exe (PID: 3064)
- taskkill.exe (PID: 2468)
- taskkill.exe (PID: 332)
- taskkill.exe (PID: 2844)
- exit.exe (PID: 1812)
- taskkill.exe (PID: 1520)
- taskkill.exe (PID: 2576)
- taskkill.exe (PID: 2512)
- svchost.exe (PID: 1004)
- taskkill.exe (PID: 4056)
- taskkill.exe (PID: 3176)
- OSPPSVC.EXE (PID: 1808)
- wmiprvse.exe (PID: 3644)
- PING.EXE (PID: 3832)
- taskkill.exe (PID: 1908)
- WinRAR.exe (PID: 3288)
- taskkill.exe (PID: 2384)
- taskkill.exe (PID: 1040)
- taskkill.exe (PID: 3536)
- taskkill.exe (PID: 856)
- taskkill.exe (PID: 3864)
- taskkill.exe (PID: 864)
- taskkill.exe (PID: 456)
- taskkill.exe (PID: 928)
- taskkill.exe (PID: 2388)
- taskkill.exe (PID: 1532)
- taskkill.exe (PID: 2660)
- conhost.exe (PID: 3540)
- PING.EXE (PID: 3628)
- uninstall.exe (PID: 344)
- veter1605_MAPS_10cr0.exe (PID: 1404)
- taskkill.exe (PID: 3772)
- taskkill.exe (PID: 2504)
- cmd.exe (PID: 772)
- taskkill.exe (PID: 904)
- EXCEL.EXE (PID: 2156)
- taskkill.exe (PID: 3720)
- wprgxyeqd79.exe (PID: 1152)
- taskkill.exe (PID: 1828)
- rtegre.exe (PID: 3448)
- reg.exe (PID: 1496)
- taskkill.exe (PID: 3196)
- taskkill.exe (PID: 3640)
- taskkill.exe (PID: 2900)
- taskkill.exe (PID: 2940)
- taskkill.exe (PID: 3048)
- taskkill.exe (PID: 2760)
- taskkill.exe (PID: 536)
- conhost.exe (PID: 3512)
- exit.exe (PID: 900)
- taskkill.exe (PID: 2936)
- winserv.exe (PID: 3324)
- taskkill.exe (PID: 3904)
- taskkill.exe (PID: 284)
- taskkill.exe (PID: 3436)
- taskkill.exe (PID: 2528)
- taskkill.exe (PID: 2556)
- taskkill.exe (PID: 1784)
- taskkill.exe (PID: 2536)
- taskkill.exe (PID: 3164)
- taskkill.exe (PID: 3688)
- taskkill.exe (PID: 3428)
- taskkill.exe (PID: 3912)
- taskkill.exe (PID: 2840)
- taskkill.exe (PID: 992)
- taskkill.exe (PID: 2836)
- taskkill.exe (PID: 3128)
- taskkill.exe (PID: 3436)
- taskkill.exe (PID: 3920)
- taskkill.exe (PID: 1928)
- taskkill.exe (PID: 1040)
- taskkill.exe (PID: 1664)
- taskkill.exe (PID: 332)
- taskkill.exe (PID: 992)
- taskkill.exe (PID: 2120)
- taskkill.exe (PID: 3204)
- taskkill.exe (PID: 3516)
- taskkill.exe (PID: 3748)
- taskkill.exe (PID: 2456)
- taskkill.exe (PID: 2388)
- taskkill.exe (PID: 3576)
- taskkill.exe (PID: 856)
- taskkill.exe (PID: 1656)
- taskkill.exe (PID: 2548)
- taskkill.exe (PID: 3824)
- taskkill.exe (PID: 276)
- taskkill.exe (PID: 2636)
- taskkill.exe (PID: 2380)
- taskkill.exe (PID: 2312)
- taskkill.exe (PID: 3264)
- taskkill.exe (PID: 2244)
- taskkill.exe (PID: 2244)
- taskkill.exe (PID: 584)
- taskkill.exe (PID: 3812)
- taskkill.exe (PID: 3988)
- taskkill.exe (PID: 2536)
- taskkill.exe (PID: 3296)
- taskkill.exe (PID: 2336)
- taskkill.exe (PID: 3820)
- taskkill.exe (PID: 2996)
- taskkill.exe (PID: 2548)
- taskkill.exe (PID: 3632)
- taskkill.exe (PID: 868)
- taskkill.exe (PID: 2360)
- taskkill.exe (PID: 128)
- taskkill.exe (PID: 3004)
- taskkill.exe (PID: 1232)
- taskkill.exe (PID: 1000)
- taskkill.exe (PID: 3240)
- taskkill.exe (PID: 2704)
- taskkill.exe (PID: 3872)
- taskkill.exe (PID: 2836)
- taskkill.exe (PID: 3536)
- taskkill.exe (PID: 2652)
- taskkill.exe (PID: 3816)
- taskkill.exe (PID: 2380)
- taskkill.exe (PID: 2296)
- taskkill.exe (PID: 2728)
- taskkill.exe (PID: 2568)
- taskkill.exe (PID: 2644)
- taskkill.exe (PID: 3152)
- taskkill.exe (PID: 3104)
- taskkill.exe (PID: 4064)
- taskkill.exe (PID: 3368)
- taskkill.exe (PID: 1760)
- taskkill.exe (PID: 3648)
- taskkill.exe (PID: 1008)
- taskkill.exe (PID: 3168)
- taskkill.exe (PID: 2964)
- taskkill.exe (PID: 3736)
- taskkill.exe (PID: 2064)
- taskkill.exe (PID: 1564)
- taskkill.exe (PID: 3116)
- taskkill.exe (PID: 3972)
- taskkill.exe (PID: 2400)
- taskkill.exe (PID: 2984)
- taskkill.exe (PID: 3300)
- taskkill.exe (PID: 2364)
- taskkill.exe (PID: 2112)
- taskkill.exe (PID: 1760)
- taskkill.exe (PID: 1860)
- taskkill.exe (PID: 276)
- taskkill.exe (PID: 1540)
- taskkill.exe (PID: 1828)
- taskkill.exe (PID: 4044)
- taskkill.exe (PID: 2640)
- taskkill.exe (PID: 2452)
- taskkill.exe (PID: 1532)
- taskkill.exe (PID: 2700)
- taskkill.exe (PID: 2592)
- taskkill.exe (PID: 3444)
- taskkill.exe (PID: 2532)
- taskkill.exe (PID: 2972)
- taskkill.exe (PID: 2756)
- taskkill.exe (PID: 3688)
- taskkill.exe (PID: 1940)
- taskkill.exe (PID: 3392)
- taskkill.exe (PID: 3548)
- taskkill.exe (PID: 3176)
- taskkill.exe (PID: 2936)
- taskkill.exe (PID: 3032)
- taskkill.exe (PID: 3940)
- taskkill.exe (PID: 3660)
- taskkill.exe (PID: 3884)
- taskkill.exe (PID: 4064)
- taskkill.exe (PID: 636)
- taskkill.exe (PID: 3476)
- taskkill.exe (PID: 1412)
- taskkill.exe (PID: 3784)
- taskkill.exe (PID: 996)
- taskkill.exe (PID: 3028)
- taskkill.exe (PID: 2132)
- taskkill.exe (PID: 3124)
- taskkill.exe (PID: 3356)
- taskkill.exe (PID: 2636)
- taskkill.exe (PID: 3220)
- taskkill.exe (PID: 2728)
- taskkill.exe (PID: 2336)
- taskkill.exe (PID: 1888)
- taskkill.exe (PID: 788)
- taskkill.exe (PID: 2500)
- taskkill.exe (PID: 2948)
- taskkill.exe (PID: 1864)
- taskkill.exe (PID: 2756)
- taskkill.exe (PID: 2096)
- taskkill.exe (PID: 3296)
- taskkill.exe (PID: 3116)
- taskkill.exe (PID: 3428)
- taskkill.exe (PID: 1232)
- taskkill.exe (PID: 1928)
- taskkill.exe (PID: 1472)
- taskkill.exe (PID: 3516)
- taskkill.exe (PID: 3920)
- taskkill.exe (PID: 2716)
- taskkill.exe (PID: 2140)
- taskkill.exe (PID: 3572)
- taskkill.exe (PID: 3172)
- taskkill.exe (PID: 2576)
- taskkill.exe (PID: 3244)
- taskkill.exe (PID: 3504)
- taskkill.exe (PID: 864)
- taskkill.exe (PID: 4088)
- taskkill.exe (PID: 2132)
- taskkill.exe (PID: 2300)
- taskkill.exe (PID: 2176)
- taskkill.exe (PID: 3008)
- taskkill.exe (PID: 1356)
- taskkill.exe (PID: 1700)
- taskkill.exe (PID: 3812)
- taskkill.exe (PID: 3788)
- taskkill.exe (PID: 612)
- taskkill.exe (PID: 636)
- taskkill.exe (PID: 3680)
- taskkill.exe (PID: 2560)
- taskkill.exe (PID: 2568)
- taskkill.exe (PID: 2288)
- taskkill.exe (PID: 3916)
- taskkill.exe (PID: 3072)
- taskkill.exe (PID: 2684)
- taskkill.exe (PID: 3500)
- taskkill.exe (PID: 1872)
- taskkill.exe (PID: 2120)
- taskkill.exe (PID: 3504)
- taskkill.exe (PID: 900)
- taskkill.exe (PID: 3048)
- taskkill.exe (PID: 3668)
- taskkill.exe (PID: 3964)
- taskkill.exe (PID: 2292)
- taskkill.exe (PID: 2188)
- taskkill.exe (PID: 1896)
- taskkill.exe (PID: 2212)
- taskkill.exe (PID: 2660)
- taskkill.exe (PID: 1412)
- taskkill.exe (PID: 2152)
- taskkill.exe (PID: 1680)
- taskkill.exe (PID: 3804)
- taskkill.exe (PID: 1700)
- taskkill.exe (PID: 952)
- taskkill.exe (PID: 3684)
- taskkill.exe (PID: 2084)
- taskkill.exe (PID: 1872)
- taskkill.exe (PID: 2884)
- taskkill.exe (PID: 2684)
- taskkill.exe (PID: 1860)
- taskkill.exe (PID: 912)
- taskkill.exe (PID: 2768)
- taskkill.exe (PID: 3584)
- taskkill.exe (PID: 2652)
- taskkill.exe (PID: 1724)
- taskkill.exe (PID: 2420)
- taskkill.exe (PID: 2768)
- taskkill.exe (PID: 2908)
- taskkill.exe (PID: 3716)
- taskkill.exe (PID: 2532)
- taskkill.exe (PID: 2432)
- taskkill.exe (PID: 2664)
- taskkill.exe (PID: 3532)
- taskkill.exe (PID: 2144)
- taskkill.exe (PID: 3720)
- taskkill.exe (PID: 3816)
- taskkill.exe (PID: 1672)
- taskkill.exe (PID: 928)
- taskkill.exe (PID: 1516)
- taskkill.exe (PID: 3912)
- taskkill.exe (PID: 2708)
- taskkill.exe (PID: 2240)
- taskkill.exe (PID: 3840)
- taskkill.exe (PID: 3904)
- taskkill.exe (PID: 128)
- taskkill.exe (PID: 3304)
- taskkill.exe (PID: 2164)
- taskkill.exe (PID: 320)
- taskkill.exe (PID: 1864)
- taskkill.exe (PID: 1936)
- taskkill.exe (PID: 2240)
- taskkill.exe (PID: 3148)
- taskkill.exe (PID: 3728)
- taskkill.exe (PID: 2480)
- taskkill.exe (PID: 3896)
- taskkill.exe (PID: 2064)
- taskkill.exe (PID: 1336)
- taskkill.exe (PID: 2608)
- taskkill.exe (PID: 3756)
- taskkill.exe (PID: 3252)
- taskkill.exe (PID: 408)
- taskkill.exe (PID: 2780)
- taskkill.exe (PID: 2900)
- taskkill.exe (PID: 3268)
- taskkill.exe (PID: 2328)
- taskkill.exe (PID: 3940)
- taskkill.exe (PID: 2584)
- taskkill.exe (PID: 3928)
- taskkill.exe (PID: 3652)
- taskkill.exe (PID: 3648)
- taskkill.exe (PID: 3564)
- taskkill.exe (PID: 3388)
- taskkill.exe (PID: 2528)
- taskkill.exe (PID: 3416)
- taskkill.exe (PID: 2696)
- taskkill.exe (PID: 2428)
- taskkill.exe (PID: 3580)
- taskkill.exe (PID: 4028)
- taskkill.exe (PID: 4008)
- taskkill.exe (PID: 952)
- taskkill.exe (PID: 3756)
- taskkill.exe (PID: 2152)
- taskkill.exe (PID: 3112)
- taskkill.exe (PID: 2948)
- taskkill.exe (PID: 2212)
- taskkill.exe (PID: 3804)
- taskkill.exe (PID: 3552)
- taskkill.exe (PID: 2340)
- taskkill.exe (PID: 1848)
- taskkill.exe (PID: 2888)
- taskkill.exe (PID: 3144)
- taskkill.exe (PID: 3728)
- taskkill.exe (PID: 768)
- taskkill.exe (PID: 236)
- taskkill.exe (PID: 2944)
- taskkill.exe (PID: 3212)
- taskkill.exe (PID: 4028)
- taskkill.exe (PID: 2088)
- taskkill.exe (PID: 2716)
- taskkill.exe (PID: 1140)
- taskkill.exe (PID: 2420)
- taskkill.exe (PID: 324)
- taskkill.exe (PID: 2108)
Changes the autorun value in the registry
- reg.exe (PID: 1496)
RMS RAT was detected
- winserv.exe (PID: 3324)
SUSPICIOUS
Starts Microsoft Office Application
- WinRAR.exe (PID: 3288)
Executable content was dropped or overwritten
- wprgxyeqd79.exe (PID: 1152)
- cmd.exe (PID: 3064)
- uninstall.exe (PID: 344)
- veter1605_MAPS_10cr0.exe (PID: 1404)
Reads Internet Cache Settings
- EXCEL.EXE (PID: 2156)
Starts CMD.EXE for commands execution
- exit.exe (PID: 1812)
- exit.exe (PID: 900)
Creates files in the program directory
- uninstall.exe (PID: 344)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 772)
Reads Windows Product ID
- winserv.exe (PID: 3324)
Reads Environment values
- winserv.exe (PID: 3324)
Reads the machine GUID from the registry
- winserv.exe (PID: 3324)
Creates files in the user directory
- winserv.exe (PID: 3324)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 772)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2156)
Creates files in the user directory
- EXCEL.EXE (PID: 2156)
Dropped object may contain Bitcoin addresses
- wprgxyeqd79.exe (PID: 1152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
360
Monitored processes
329
Malicious processes
9
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | taskkill /f /im "rundll32.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 128 | taskkill /f /im "rundll32.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 236 | taskkill /f /im "rundll32.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 276 | taskkill /f /im "rundll32.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 276 | taskkill /f /im "rundll32.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 284 | taskkill /f /im "rundll32.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 320 | taskkill /f /im "rundll32.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 324 | taskkill /f /im "rundll32.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 332 | taskkill /f /im "rundll32.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 332 | taskkill /f /im "rundll32.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 461
Read events
2 386
Write events
68
Delete events
7
Modification events
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\bill notice 05.2019.rar | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | h<; |
Value: 683C3B006C080000010000000000000000000000 | |||
| (PID) Process: | (2156) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
Executable files
11
Suspicious files
2
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR14C8.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1152 | wprgxyeqd79.exe | C:\Users\admin\AppData\Local\Temp\i.cmd | text | |
MD5:— | SHA256:— | |||
| 1152 | wprgxyeqd79.exe | C:\Users\admin\AppData\Local\Temp\exit.exe | executable | |
MD5:— | SHA256:— | |||
| 2156 | EXCEL.EXE | C:\Users\Public\wprgxyeqd79.exe | executable | |
MD5:— | SHA256:— | |||
| 1152 | wprgxyeqd79.exe | C:\Users\admin\AppData\Local\Temp\kernel.dll | executable | |
MD5:— | SHA256:— | |||
| 2156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\pasmmm[1].exe | executable | |
MD5:— | SHA256:— | |||
| 3064 | cmd.exe | C:\Users\admin\AppData\Local\Temp\uninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 2156 | EXCEL.EXE | C:\Users\Public\rtegre.exe | executable | |
MD5:— | SHA256:— | |||
| 2156 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\ananas[1].exe | executable | |
MD5:— | SHA256:— | |||
| 344 | uninstall.exe | C:\ProgramData\Windows Anytime Upgrade\settings.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
21
DNS requests
7
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3448 | rtegre.exe | GET | — | 66.111.2.131:9030 | http://66.111.2.131:9030/tor/status-vote/current/consensus | US | — | — | suspicious |
3448 | rtegre.exe | GET | — | 162.247.74.201:80 | http://162.247.74.201/tor/server/fp/00cce6a84e6d63a1a42e105839bc8ed5d4b16669 | US | — | — | suspicious |
3448 | rtegre.exe | GET | — | 162.247.74.201:80 | http://162.247.74.201/tor/server/fp/00b87ecf94c71dbf56805eb4469baf3924a13ad7 | US | — | — | suspicious |
3448 | rtegre.exe | GET | — | 162.247.74.201:80 | http://162.247.74.201/tor/server/fp/00dc112f7d4606d7e0e4b378d050490811bb20e5 | US | — | — | suspicious |
3448 | rtegre.exe | GET | — | 104.218.63.73:80 | http://104.218.63.73/tor/server/fp/003d78825e0b9609eecff5e4e0529717772e53c7 | CA | — | — | suspicious |
3448 | rtegre.exe | GET | — | 162.247.74.201:80 | http://162.247.74.201/tor/server/fp/000cfdec3727b4cb82a48d4ebc493103bf3a934e | US | — | — | suspicious |
3448 | rtegre.exe | GET | — | 162.247.74.201:80 | http://162.247.74.201/tor/server/fp/0077bcba7244db3e6a5ed2746e86170066684887 | US | — | — | suspicious |
3448 | rtegre.exe | GET | — | 185.13.39.197:80 | http://185.13.39.197/tor/server/fp/0011bd2485ad45d984ec4159c88fc066e5e3300e | FR | — | — | suspicious |
3448 | rtegre.exe | GET | — | 104.218.63.73:80 | http://104.218.63.73/tor/server/fp/0041e0150b0a307506c2863efc9f2b7e3a523b36 | CA | — | — | suspicious |
3448 | rtegre.exe | GET | — | 162.247.74.201:80 | http://162.247.74.201/tor/server/fp/001524dd403d729f08f7e5d77813ef12756cfa8d | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3448 | rtegre.exe | 162.247.74.201:443 | — | The Calyx Institute | US | suspicious |
2156 | EXCEL.EXE | 47.245.58.124:443 | kentona.su | — | US | suspicious |
3324 | winserv.exe | 217.12.201.159:5655 | — | ITL Company | NL | suspicious |
— | — | 66.111.2.131:9030 | — | The New York Internet Company | US | suspicious |
3448 | rtegre.exe | 54.243.198.12:443 | api.ipify.org | Amazon.com, Inc. | US | malicious |
3448 | rtegre.exe | 199.249.230.103:80 | — | Quintex Alliance Consulting | US | suspicious |
3448 | rtegre.exe | 162.247.74.201:80 | — | The Calyx Institute | US | suspicious |
3448 | rtegre.exe | 89.236.112.100:443 | — | TNNet Oy | FI | suspicious |
— | — | 129.6.15.28:13 | time-a.nist.gov | National Bureau of Standards | US | unknown |
3448 | rtegre.exe | 104.218.63.73:80 | — | Tech Futures Interactive Inc. | CA | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kentona.su |
| malicious |
www.cloudflare.com |
| whitelisted |
api.ipify.org |
| shared |
time-a.nist.gov |
| whitelisted |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
3448 | rtegre.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 550 |
3448 | rtegre.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
3448 | rtegre.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
3448 | rtegre.exe | Misc Attack | ET TOR Known Tor Exit Node Traffic group 12 |
3448 | rtegre.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 12 |
3448 | rtegre.exe | Potential Corporate Privacy Violation | ET P2P Tor Get Server Request |
3448 | rtegre.exe | Misc Attack | ET TOR Known Tor Exit Node Traffic group 85 |
3448 | rtegre.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 85 |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
winserv.exe | Error WTSQueryUserToken #1314 |
winserv.exe | 20-05-2019_17:12:35:839#T:Error #20 @2 |
winserv.exe | 20-05-2019_17:13:04:714#T:Msg Size: 104 |
winserv.exe | 20-05-2019_17:13:04:714#T:Msg code: 3 |
winserv.exe | MSG_KEEP_ALIVE |
winserv.exe | MSG_KEEP_ALIVE |