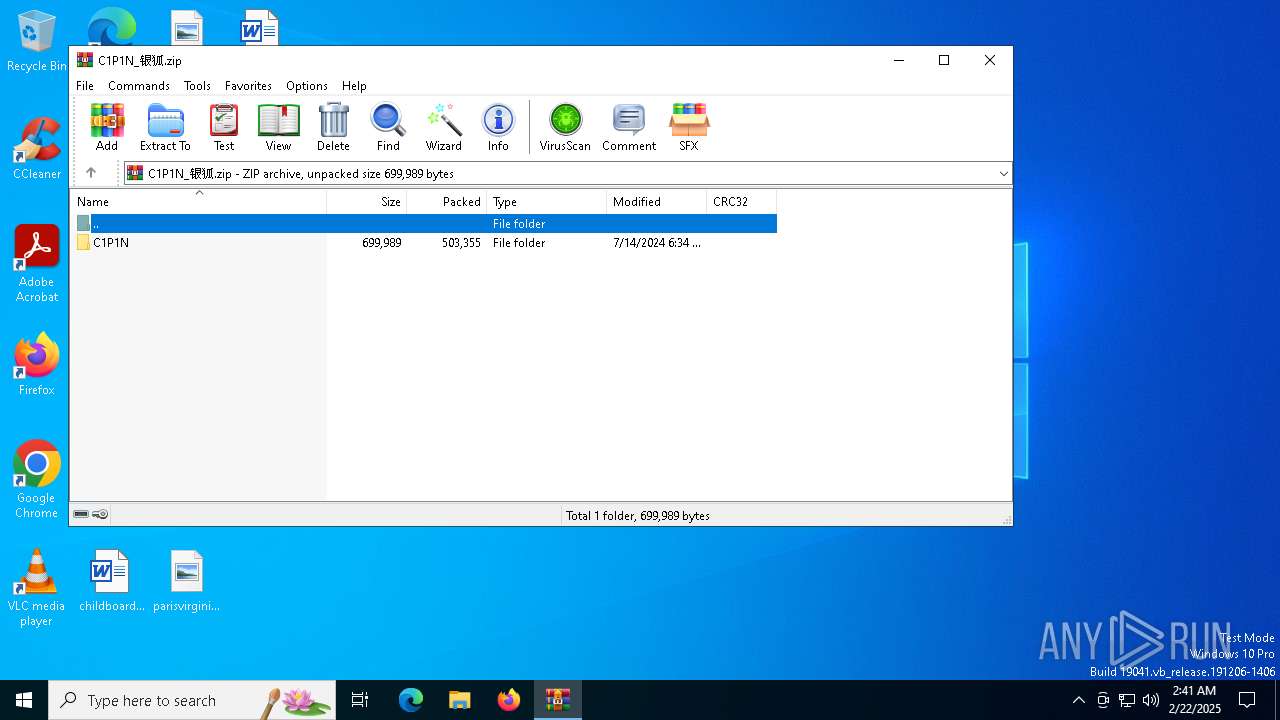
| File name: | C1P1N_银狐.zip |
| Full analysis: | https://app.any.run/tasks/83624a2b-e949-493a-8143-3f19282462c2 |
| Verdict: | Malicious activity |
| Threats: | Gh0st RAT is a malware with advanced trojan functionality that enables attackers to establish full control over the victim’s system. The spying capabilities of Gh0st RAT made it a go-to tool for numerous criminal groups in high-profile attacks against government and corporate organizations. The most common vector of attack involving this malware begins with spam and phishing emails. |
| Analysis date: | February 22, 2025, 02:41:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 144FE0BA23D361A2E7294616893B6235 |
| SHA1: | BD61596EA5E5CF030C3FDC8EAB8206C376260F01 |
| SHA256: | BF379C59777681697A8963950498FBCC236CD3142EAC90A384FD764B3A69AF61 |
| SSDEEP: | 12288:rHNbi2fscbkooTblJq9pqp3iG5nhBCMe7L1gAY3K05ou:rNbi2kcbJoTv+pqp3iG5hBfsL1gAYP5V |
MALICIOUS
Gh0st has been detected
- UEc.exe (PID: 6916)
SUSPICIOUS
Creates file in the systems drive root
- UEc.exe (PID: 6916)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 7092)
- cmd.exe (PID: 7024)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 5892)
- cmd.exe (PID: 1792)
- cmd.exe (PID: 5460)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 5028)
- cmd.exe (PID: 512)
- cmd.exe (PID: 6724)
- cmd.exe (PID: 6668)
- cmd.exe (PID: 4804)
- cmd.exe (PID: 6760)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 2456)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 5320)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 5460)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 3664)
- cmd.exe (PID: 5876)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 4972)
- cmd.exe (PID: 6780)
- cmd.exe (PID: 6096)
- cmd.exe (PID: 6084)
- cmd.exe (PID: 6936)
- cmd.exe (PID: 7036)
- cmd.exe (PID: 732)
- cmd.exe (PID: 5432)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 1876)
- cmd.exe (PID: 3984)
- cmd.exe (PID: 3840)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 6444)
- cmd.exe (PID: 6716)
- cmd.exe (PID: 6696)
- cmd.exe (PID: 5004)
- cmd.exe (PID: 6996)
- cmd.exe (PID: 3052)
- cmd.exe (PID: 6800)
- cmd.exe (PID: 4872)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 6984)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 1760)
- cmd.exe (PID: 7096)
- cmd.exe (PID: 6212)
- cmd.exe (PID: 3732)
- cmd.exe (PID: 6304)
- cmd.exe (PID: 1512)
- cmd.exe (PID: 5256)
- cmd.exe (PID: 4980)
- cmd.exe (PID: 4704)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 6704)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 6812)
- cmd.exe (PID: 2632)
- cmd.exe (PID: 6988)
- cmd.exe (PID: 3792)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 7040)
- cmd.exe (PID: 2792)
- cmd.exe (PID: 6284)
- cmd.exe (PID: 7096)
- cmd.exe (PID: 7140)
- cmd.exe (PID: 7124)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 4548)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 3552)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 4908)
- cmd.exe (PID: 6756)
- cmd.exe (PID: 6356)
- cmd.exe (PID: 6664)
- cmd.exe (PID: 4864)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 2680)
- cmd.exe (PID: 4804)
- cmd.exe (PID: 6828)
- cmd.exe (PID: 3656)
- cmd.exe (PID: 2012)
- cmd.exe (PID: 3364)
- cmd.exe (PID: 1220)
- cmd.exe (PID: 1076)
- cmd.exe (PID: 1080)
- cmd.exe (PID: 7120)
- cmd.exe (PID: 7140)
- cmd.exe (PID: 6232)
- cmd.exe (PID: 3732)
- cmd.exe (PID: 2632)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 5028)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 2260)
- cmd.exe (PID: 6760)
- cmd.exe (PID: 1864)
- cmd.exe (PID: 6856)
- cmd.exe (PID: 5652)
- cmd.exe (PID: 1612)
- cmd.exe (PID: 5092)
- cmd.exe (PID: 1448)
- cmd.exe (PID: 6964)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 7028)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 7024)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 2424)
- cmd.exe (PID: 1796)
- cmd.exe (PID: 628)
- cmd.exe (PID: 7132)
- cmd.exe (PID: 3560)
- cmd.exe (PID: 3420)
- cmd.exe (PID: 6740)
- cmd.exe (PID: 5712)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 5912)
- cmd.exe (PID: 4704)
- cmd.exe (PID: 6276)
- cmd.exe (PID: 4360)
- cmd.exe (PID: 6356)
- cmd.exe (PID: 6172)
- cmd.exe (PID: 6664)
- cmd.exe (PID: 6844)
- cmd.exe (PID: 6804)
- cmd.exe (PID: 6888)
- cmd.exe (PID: 7008)
- cmd.exe (PID: 6984)
- cmd.exe (PID: 7044)
- cmd.exe (PID: 7048)
- cmd.exe (PID: 2976)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 6428)
- cmd.exe (PID: 6220)
- cmd.exe (PID: 3664)
- cmd.exe (PID: 2072)
- cmd.exe (PID: 4024)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 3608)
- cmd.exe (PID: 4320)
- cmd.exe (PID: 2088)
- cmd.exe (PID: 1512)
- cmd.exe (PID: 6092)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 5320)
- cmd.exe (PID: 6304)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 3640)
- cmd.exe (PID: 4708)
- cmd.exe (PID: 6664)
- cmd.exe (PID: 3436)
- cmd.exe (PID: 6548)
- cmd.exe (PID: 6880)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 2216)
- cmd.exe (PID: 7108)
- cmd.exe (PID: 6936)
- cmd.exe (PID: 648)
- cmd.exe (PID: 4384)
- cmd.exe (PID: 6332)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 6648)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 6388)
- cmd.exe (PID: 2512)
- cmd.exe (PID: 6292)
- cmd.exe (PID: 5604)
- cmd.exe (PID: 4308)
- cmd.exe (PID: 6076)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 5776)
- cmd.exe (PID: 4704)
- cmd.exe (PID: 3824)
- cmd.exe (PID: 6756)
- cmd.exe (PID: 6844)
- cmd.exe (PID: 6696)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 1612)
- cmd.exe (PID: 6424)
- cmd.exe (PID: 6856)
- cmd.exe (PID: 7072)
- cmd.exe (PID: 4228)
- cmd.exe (PID: 6204)
- cmd.exe (PID: 4136)
- cmd.exe (PID: 6644)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 6276)
- cmd.exe (PID: 6356)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 5076)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 5320)
- cmd.exe (PID: 5000)
- cmd.exe (PID: 1704)
- cmd.exe (PID: 6472)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 244)
- cmd.exe (PID: 3812)
- cmd.exe (PID: 3080)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 6744)
- cmd.exe (PID: 3824)
- cmd.exe (PID: 6748)
- cmd.exe (PID: 6756)
- cmd.exe (PID: 7120)
- cmd.exe (PID: 6416)
- cmd.exe (PID: 5388)
- cmd.exe (PID: 6844)
- cmd.exe (PID: 6856)
- cmd.exe (PID: 5076)
- cmd.exe (PID: 1192)
- cmd.exe (PID: 7068)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 6464)
- cmd.exe (PID: 5696)
- cmd.exe (PID: 5432)
- cmd.exe (PID: 6496)
- cmd.exe (PID: 3612)
- cmd.exe (PID: 5192)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 4976)
- cmd.exe (PID: 5004)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 1612)
- cmd.exe (PID: 1944)
- cmd.exe (PID: 3220)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 6304)
- cmd.exe (PID: 372)
- cmd.exe (PID: 3864)
- cmd.exe (PID: 3640)
- cmd.exe (PID: 6288)
- cmd.exe (PID: 1412)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 6056)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 1792)
- cmd.exe (PID: 1684)
- cmd.exe (PID: 5572)
- cmd.exe (PID: 4708)
- cmd.exe (PID: 556)
- cmd.exe (PID: 6900)
- cmd.exe (PID: 5788)
- cmd.exe (PID: 3364)
- cmd.exe (PID: 1192)
- cmd.exe (PID: 5300)
- cmd.exe (PID: 5252)
- cmd.exe (PID: 6572)
- cmd.exe (PID: 6420)
- cmd.exe (PID: 4444)
- cmd.exe (PID: 6372)
- cmd.exe (PID: 6476)
- cmd.exe (PID: 1472)
- cmd.exe (PID: 4592)
- cmd.exe (PID: 3792)
- cmd.exe (PID: 6964)
- cmd.exe (PID: 5432)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 4360)
- cmd.exe (PID: 5388)
- cmd.exe (PID: 3824)
- cmd.exe (PID: 5004)
- cmd.exe (PID: 6664)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 3952)
- cmd.exe (PID: 7016)
- cmd.exe (PID: 7068)
- cmd.exe (PID: 4980)
- cmd.exe (PID: 3876)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 5236)
- cmd.exe (PID: 6748)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 6496)
- cmd.exe (PID: 4668)
- cmd.exe (PID: 6516)
- cmd.exe (PID: 6856)
- cmd.exe (PID: 5076)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 6464)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 7040)
- cmd.exe (PID: 6332)
- cmd.exe (PID: 3620)
Connects to unusual port
- UEc.exe (PID: 6916)
There is functionality for taking screenshot (YARA)
- UEc.exe (PID: 6916)
Starts CMD.EXE for commands execution
- UEc.exe (PID: 6916)
INFO
Reads the computer name
- UEc.exe (PID: 6916)
Manual execution by a user
- UEc.exe (PID: 6916)
Checks supported languages
- UEc.exe (PID: 6916)
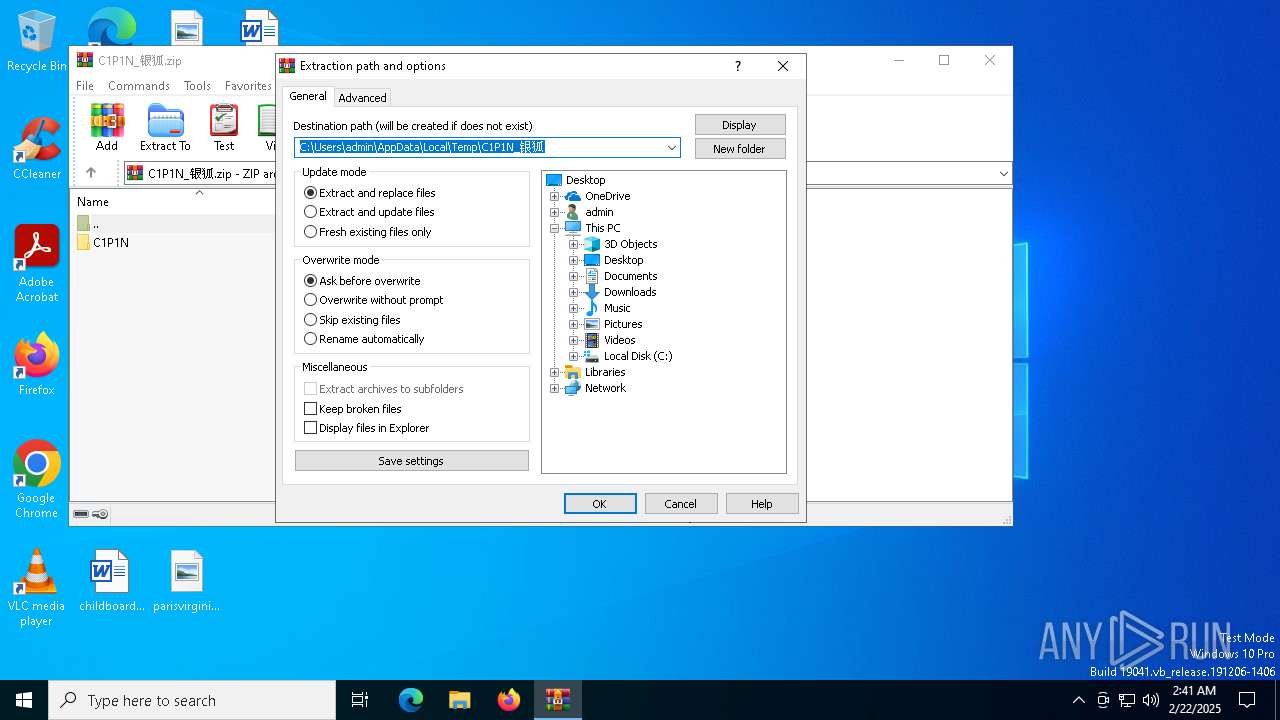
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3680)
The sample compiled with russian language support
- WinRAR.exe (PID: 3680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:07:15 02:34:14 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | C1P1N/ |
Total processes
739
Monitored processes
613
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 244 | cmd /c echo.>c:\xxxx.ini | C:\Windows\SysWOW64\cmd.exe | — | UEc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 372 | cmd /c echo.>c:\xxxx.ini | C:\Windows\SysWOW64\cmd.exe | — | UEc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 512 | cmd /c echo.>c:\xxxx.ini | C:\Windows\SysWOW64\cmd.exe | — | UEc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 556 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 556 | cmd /c echo.>c:\xxxx.ini | C:\Windows\SysWOW64\cmd.exe | — | UEc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | cmd /c echo.>c:\xxxx.ini | C:\Windows\SysWOW64\cmd.exe | — | UEc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 648 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 419
Read events
9 382
Write events
24
Delete events
13
Modification events
| (PID) Process: | (3680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\C1P1N_银狐.zip | |||
| (PID) Process: | (3680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (3680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
0
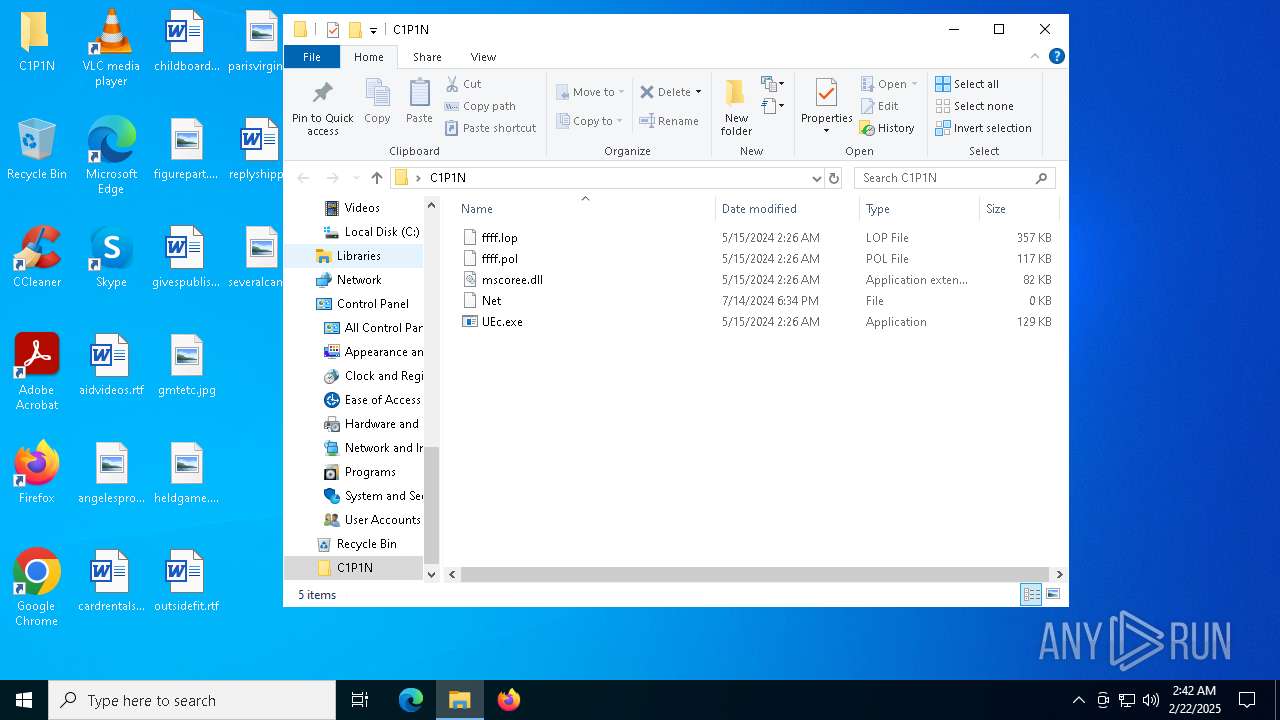
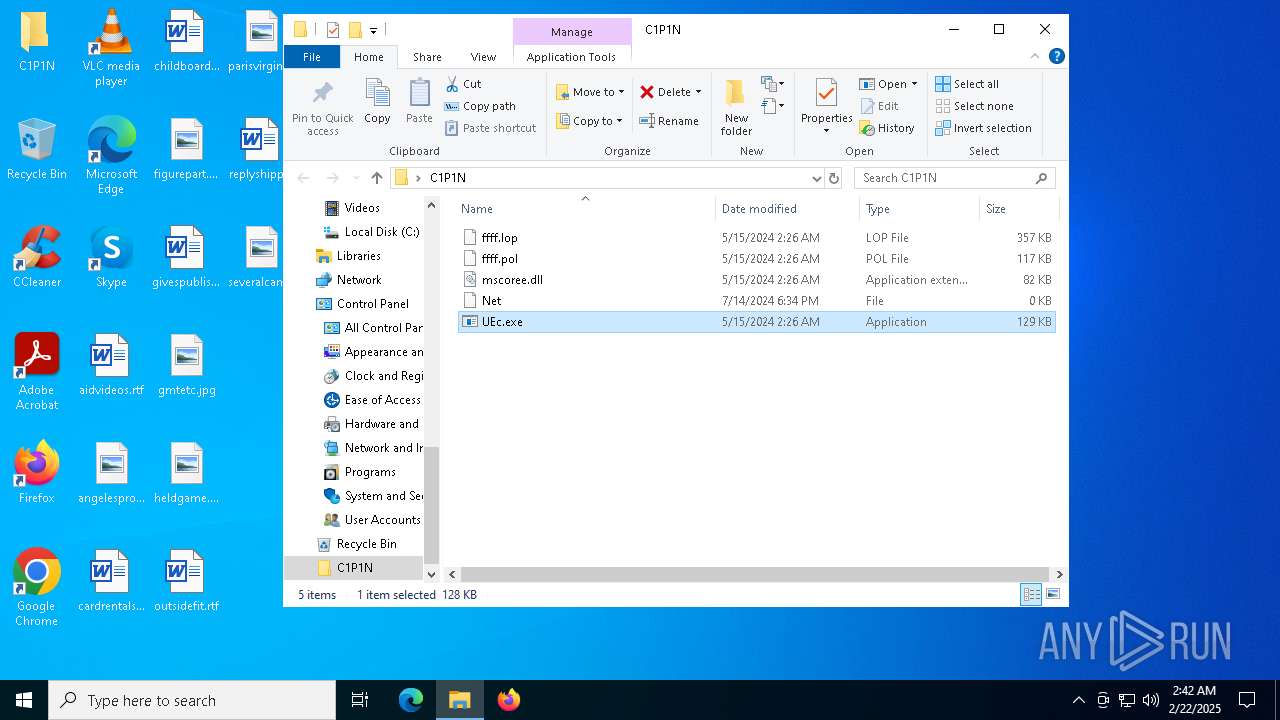
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3680 | WinRAR.exe | C:\Users\admin\Desktop\C1P1N\ffff.pol | binary | |
MD5:8E569559638F23651C0D6084D6DAC05D | SHA256:F9084C7890A139AB1CDE14D389EC05A1C778D5F799D56CFB04EFDB14D5276315 | |||
| 3680 | WinRAR.exe | C:\Users\admin\Desktop\C1P1N\UEc.exe | executable | |
MD5:4EE04272912BC9C6672677A2824FFA03 | SHA256:FEA8CDBF096EAAE458C7C74E7F0DC1EC693944812BD02C27B057EA80CCA6CDEA | |||
| 3680 | WinRAR.exe | C:\Users\admin\Desktop\C1P1N\mscoree.dll | executable | |
MD5:D9B26D2AFDFD587256FBAE5D1B8F3345 | SHA256:C6ABCA24C8545C4D8AF7A57BB220E2BCA4CF895A4C4A8A6EA96D02BCEEB83FD7 | |||
| 3680 | WinRAR.exe | C:\Users\admin\Desktop\C1P1N\ffff.lop | binary | |
MD5:371F549D9B1975D1AF4105DB921D3424 | SHA256:4ADA496416653A0F1C497AF4555A75F44C3E3C6DE4F857B4EBD2D6395179320B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
45
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6380 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3820 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3820 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
440 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3052 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.216.77.30:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 104.126.37.155:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3976 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ynjwec.net |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
UEc.exe | Thread running...
|
UEc.exe | Thread running...
|
UEc.exe | Thread running...
|
UEc.exe | Thread running...
|
UEc.exe | Thread running...
|
UEc.exe | Thread running...
|
UEc.exe | Thread running...
|
UEc.exe | Thread running...
|
UEc.exe | Thread running...
|
UEc.exe | Thread running...
|