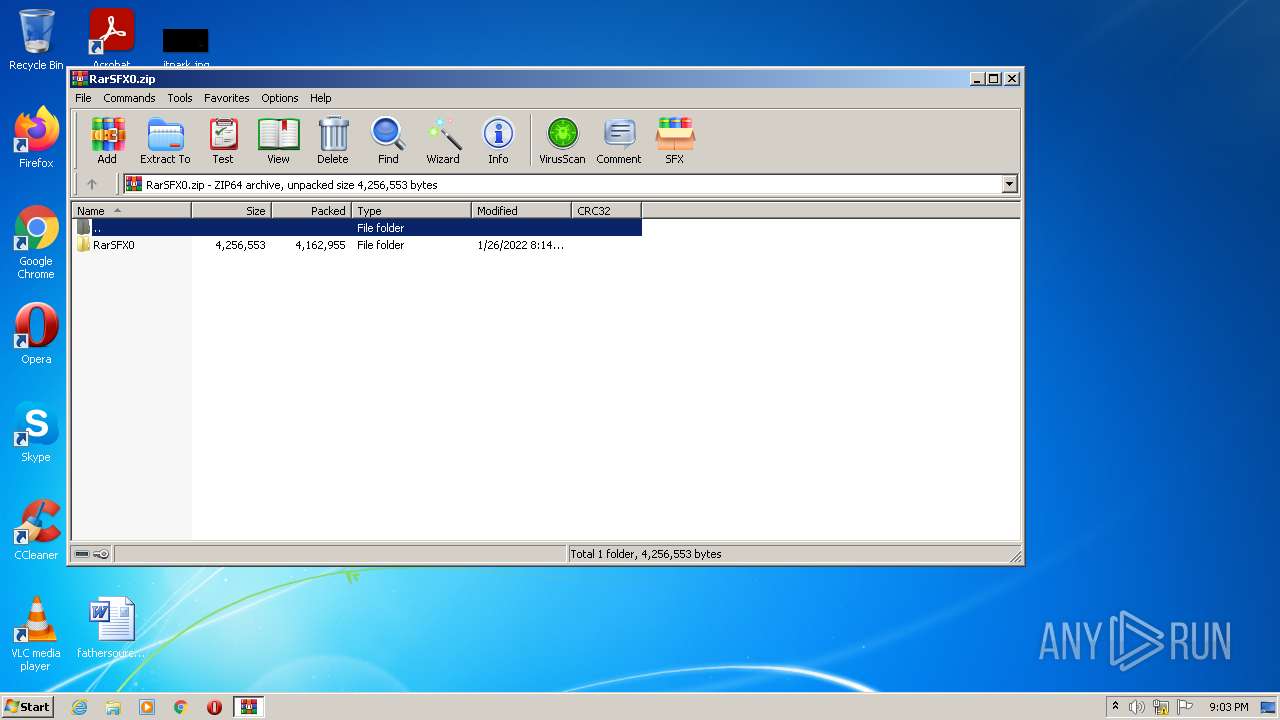
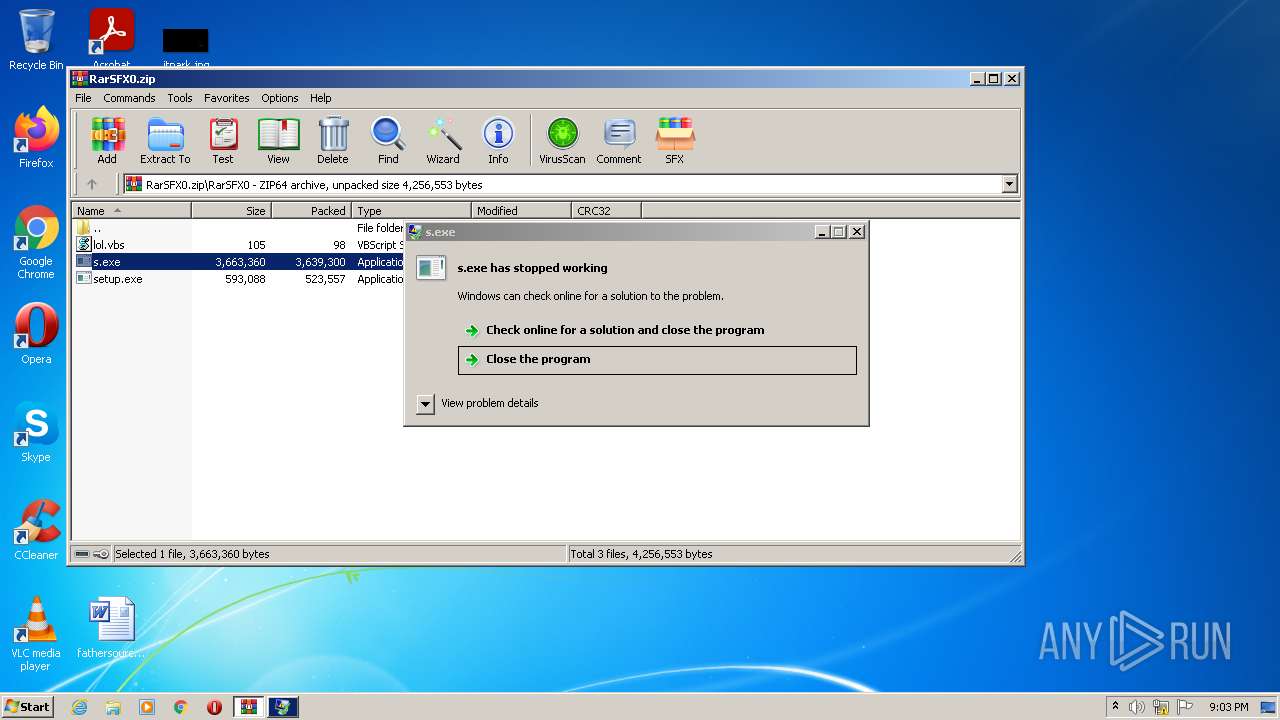
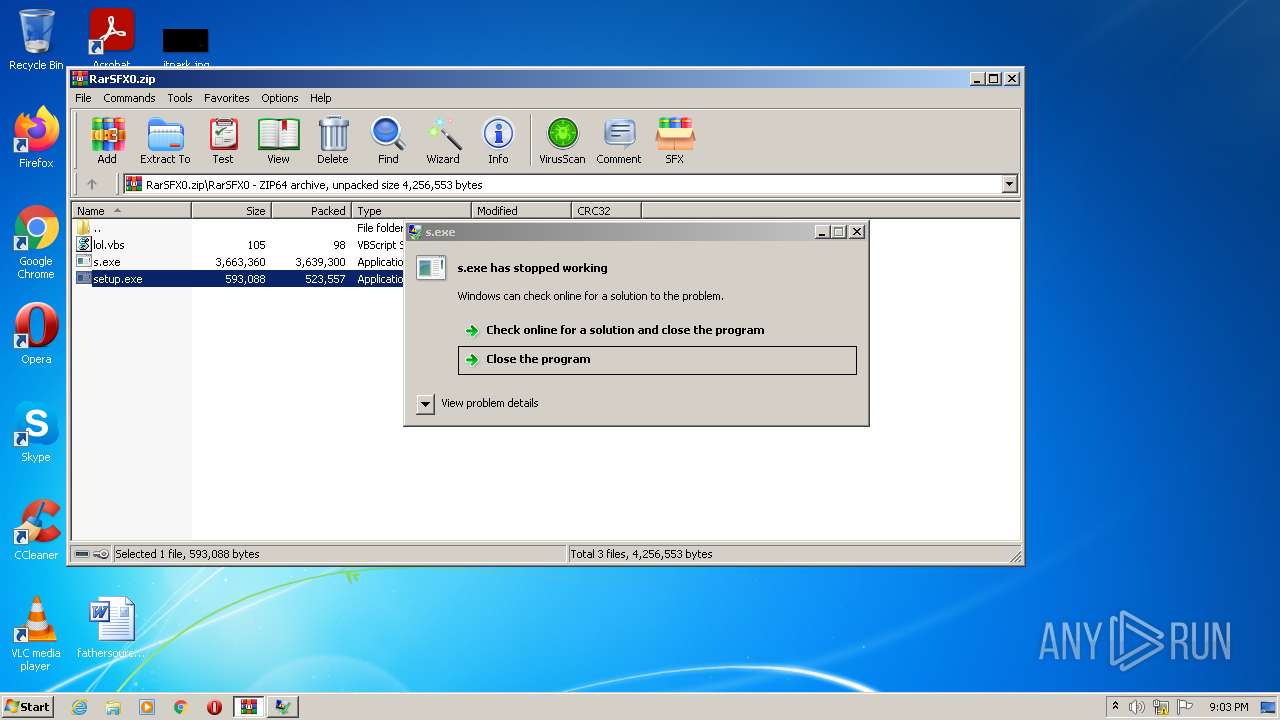
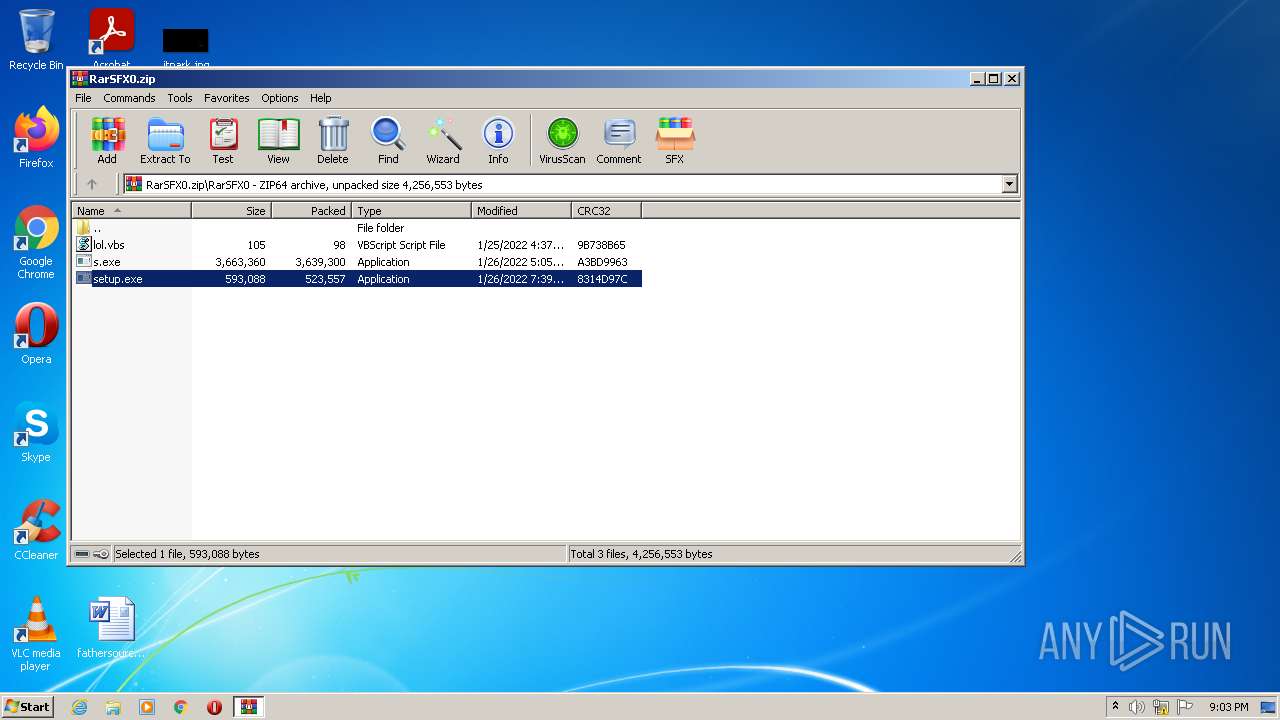
| File name: | RarSFX0.zip |
| Full analysis: | https://app.any.run/tasks/8b4a5c11-d989-4397-b9d8-434b074f5b6d |
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | May 20, 2022, 20:03:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract |
| MD5: | CD5298319E3EF7CB3718332C5DFC1318 |
| SHA1: | 9AD776F24DFEEC31A3B688D0ED07940EC56AB6E4 |
| SHA256: | BEA5A4C01127B0732C8DFF74D3296E1D3E4301BEE14EC3925A3D8FFA59D2C451 |
| SSDEEP: | 98304:CyoB4a4/G09V1ShJNTd/XXTDhGLm+O8Zq9lY/NpkUY+KExoCYt:CyoS/jV1ShJtlTdBeZ6lcAUsEY |
MALICIOUS
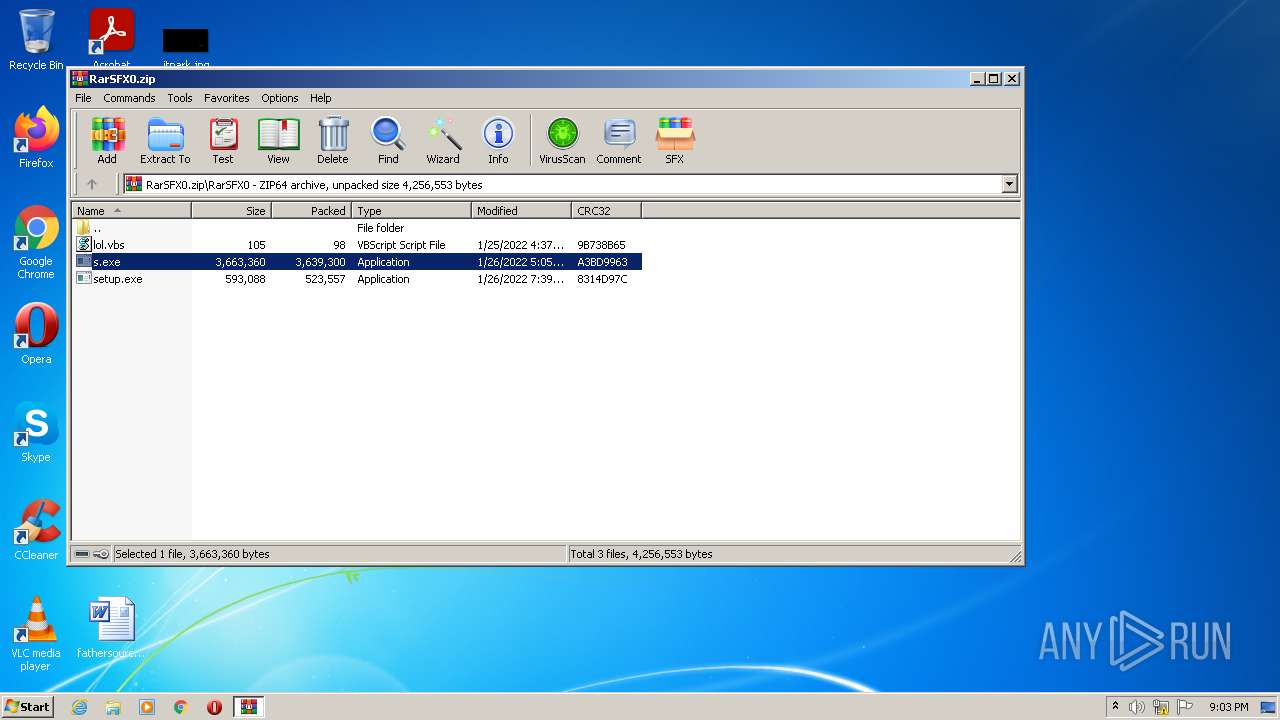
Drops executable file immediately after starts
- WinRAR.exe (PID: 2924)
- setup.exe (PID: 128)
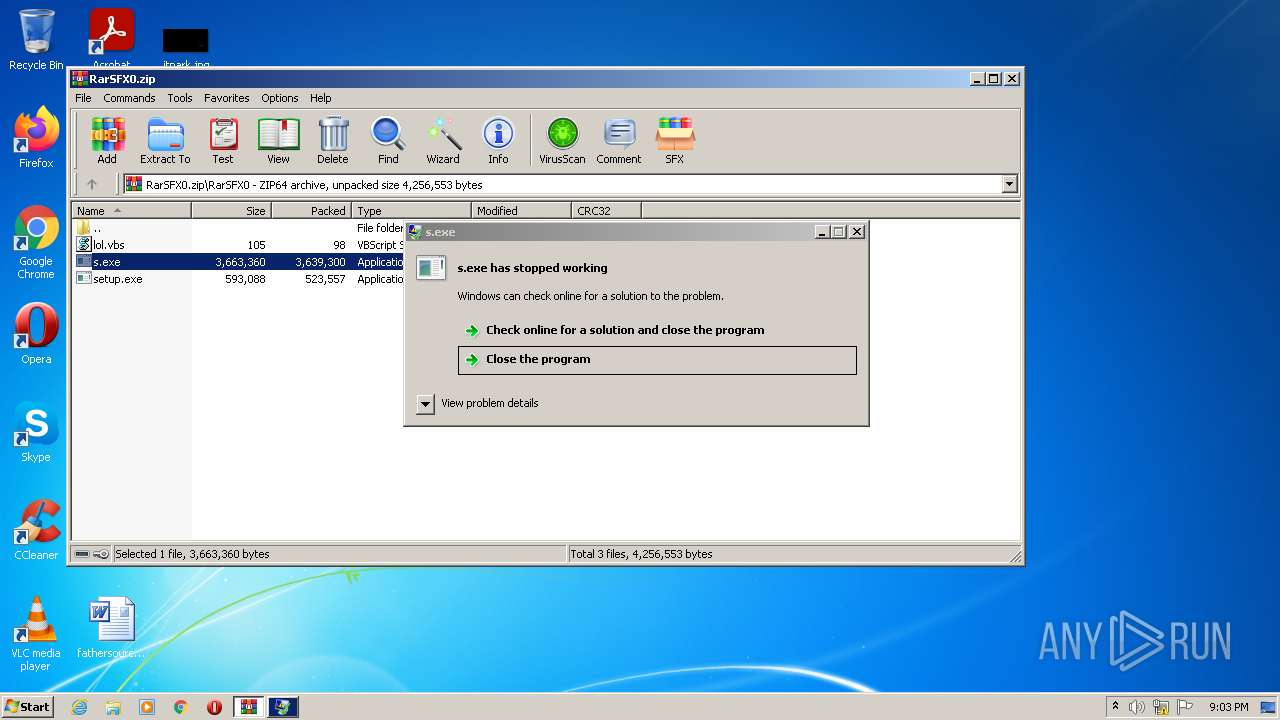
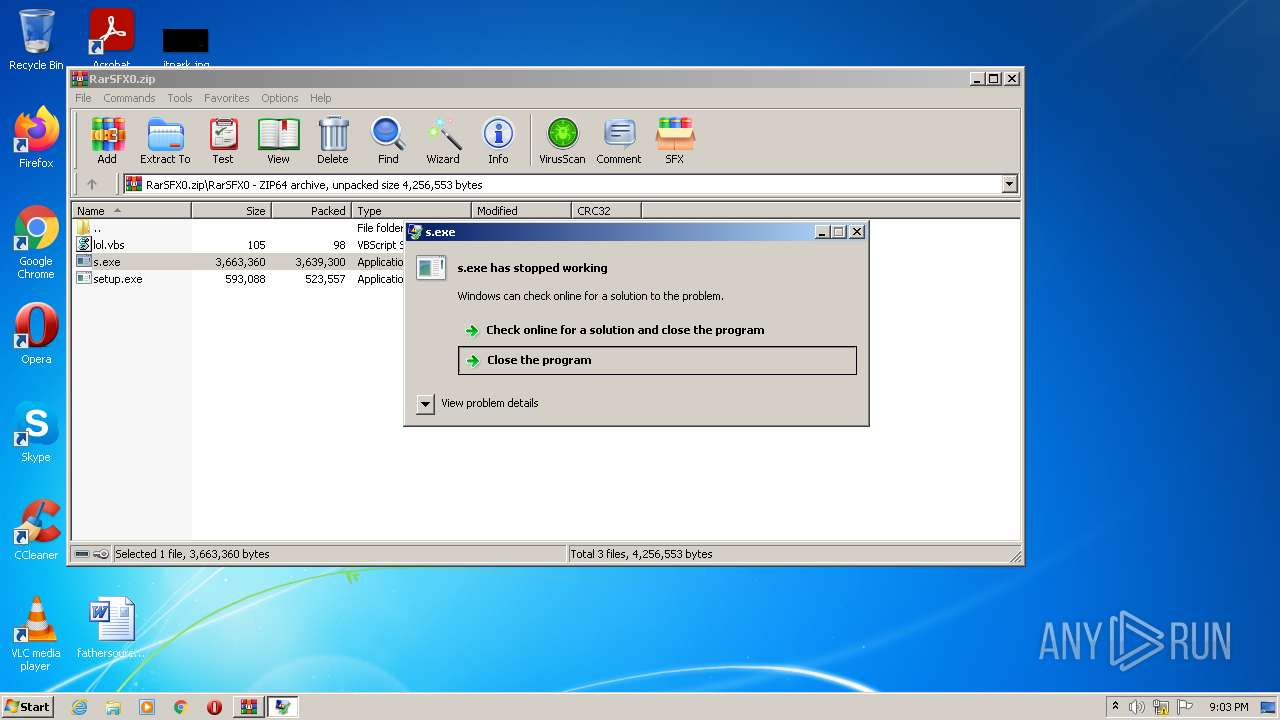
Application was dropped or rewritten from another process
- s.exe (PID: 3724)
- setup.exe (PID: 3516)
- setup.exe (PID: 128)
REDLINE detected by memory dumps
- s.exe (PID: 3724)
- AppLaunch.exe (PID: 928)
Actions looks like stealing of personal data
- WinRAR.exe (PID: 2924)
Uses Task Scheduler to run other applications
- setup.exe (PID: 128)
- setup.exe (PID: 128)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2660)
- schtasks.exe (PID: 2460)
- schtasks.exe (PID: 2248)
SUSPICIOUS
Checks supported languages
- s.exe (PID: 3724)
- AppLaunch.exe (PID: 928)
- WinRAR.exe (PID: 2924)
- setup.exe (PID: 128)
- powershell.exe (PID: 328)
Reads the computer name
- WinRAR.exe (PID: 2924)
- AppLaunch.exe (PID: 928)
- setup.exe (PID: 128)
- powershell.exe (PID: 328)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2924)
- setup.exe (PID: 128)
Reads Windows owner or organization settings
- setup.exe (PID: 128)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2924)
- setup.exe (PID: 128)
Creates files in the user directory
- setup.exe (PID: 128)
Reads Environment values
- setup.exe (PID: 128)
Executes PowerShell scripts
- setup.exe (PID: 128)
INFO
Checks supported languages
- schtasks.exe (PID: 2460)
- schtasks.exe (PID: 2660)
- schtasks.exe (PID: 2248)
Reads the computer name
- schtasks.exe (PID: 2660)
- schtasks.exe (PID: 2248)
- schtasks.exe (PID: 2460)
Reads settings of System Certificates
- powershell.exe (PID: 328)
Checks Windows Trust Settings
- powershell.exe (PID: 328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(3724) s.exe
C2 (1)45.9.20.167:34189
Botnet640639202
Err_msg
Auth_value1cf2ebfb78a2360e657cacea44023218
US (149)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
.
1
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Network\
Host
Port
:
User
Pass
MANGO
eNetworkCredentialxpirNetworkCredentialy
NetworkCredential
%USEWanaLifeRPROFILE%\AppDaWanaLifeta\LWanaLifeocal
WanaLife
Def
Win
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrMemoryStreamyptOpeMemoryStreamnAlgorithmProviMemoryStreamder
MemoryStream
BCrFileStreamyptCloseAlgoritFileStreamhmProvFileStreamider
BCrIOStreamyptDecrIOStreamypt
IOStream
BCrFile.ReadyptDesFile.ReadtroyKFile.Readey
File.Read
BCFile.OpenryptGeFile.OpentPropeFile.Openrty
File.Open
BCFile.CloseryptSFile.CloseetPrFile.CloseoperFile.Closety
File.Close
BCrFile.ReadAllTextyptImFile.ReadAllTextportKFile.ReadAllTextey
File.ReadAllText
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
net.tcp://
/
localhost
1cf2ebfb78a2360e657cacea44023218
Authorization
ns1
UNKNWON
AiUxDCYgWTUsJ00RPQcvVykDOAsiCApZ
640639202
Ladyism
Yandex\YaAddon
ToString
asf
*wallet*
_
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
String
Replace
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
gasdl94ja;sdiasdl94ja;s32
asdl94ja;s
Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds
asdl94jlajsd
Width
Height
CopyFromScreen
https://api.ip.sb/ip
80
81
0.0.0.0
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
Name
NumberOfCores
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
(PID) Process(928) AppLaunch.exe
C2 (1)45.9.20.167:34189
Botnet640639202
Err_msg
Auth_value1cf2ebfb78a2360e657cacea44023218
US (149)
LEnvironmentogiEnvironmentn DatEnvironmenta
Environment
WSystem.Texteb DatSystem.Texta
System.Text
CoCryptographyokieCryptographys
Cryptography
ExtGenericension CooGenerickies
Generic
OFileInfopeFileInfora GFileInfoX StabFileInfole
FileInfo
OpLinqera GLinqX
Linq
ApGenericpDaGenericta\RGenericoamiGenericng\
Network
Extension
UNKNOWN
.
1
cFileStreamredFileStreamit_cFileStreamardFileStreams
FileStream
\
Network\
Host
Port
:
User
Pass
MANGO
eNetworkCredentialxpirNetworkCredentialy
NetworkCredential
%USEWanaLifeRPROFILE%\AppDaWanaLifeta\LWanaLifeocal
WanaLife
Def
Win
String.Replace
String.Remove
bcrFileStream.IOypt.dFileStream.IOll
FileStream.IO
BCrMemoryStreamyptOpeMemoryStreamnAlgorithmProviMemoryStreamder
MemoryStream
BCrFileStreamyptCloseAlgoritFileStreamhmProvFileStreamider
BCrIOStreamyptDecrIOStreamypt
IOStream
BCrFile.ReadyptDesFile.ReadtroyKFile.Readey
File.Read
BCFile.OpenryptGeFile.OpentPropeFile.Openrty
File.Open
BCFile.CloseryptSFile.CloseetPrFile.CloseoperFile.Closety
File.Close
BCrFile.ReadAllTextyptImFile.ReadAllTextportKFile.ReadAllTextey
File.ReadAllText
windows-1251
AES
Microsoft Primitive Provider
ChainingModeGCM
AuthTagLength
ChainingMode
ObjectLength
KeyDataBlob
-
net.tcp://
/
localhost
1cf2ebfb78a2360e657cacea44023218
Authorization
ns1
UNKNWON
AiUxDCYgWTUsJ00RPQcvVykDOAsiCApZ
640639202
Ladyism
Yandex\YaAddon
ToString
asf
*wallet*
_
\TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata
String
Replace
string.Replace
%USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng
File.Write
Handler
npvo*
%USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl
serviceInterface.Extension
ProldCharotonVoldCharPN
oldChar
nSystem.CollectionspvoSystem.Collections*
System.Collections
(
UNIQUE
cstringmstringd
string
/ProcessC Process
Process
|
"
gasdl94ja;sdiasdl94ja;s32
asdl94ja;s
Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds
asdl94jlajsd
Width
Height
CopyFromScreen
https://api.ip.sb/ip
80
81
0.0.0.0
SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor
System.Windows.Forms
Name
NumberOfCores
roSystem.Linqot\CISystem.LinqMV2
System.Linq
SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller
AdapterRAM
SOFTWARE\WOW6432Node\Clients\StartMenuInternet
SOFTWARE\Clients\StartMenuInternet
shell\open\command
Unknown Version
SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente
System.Management
SerialNumber
SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId='
'
FileSystem
SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId='
System.
ExecutablePath
[
]
Concat0 MConcatb oConcatr Concat0
Concat
SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem
Memory
{0}{1}{2}
x32
x64
x86
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
CSDVersion
Unknown
_[
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | RarSFX0/ |
|---|---|
| ZipUncompressedSize: | 4294967295 |
| ZipCompressedSize: | 4294967295 |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2022:01:26 17:14:03 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 45 |
Total processes
52
Monitored processes
9
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.16265\RarSFX0\setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.16265\RarSFX0\setup.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft.Office.Tools.Excel.v4.0.Utilities.dll Exit code: 0 Version: 10.0.30319.1 Modules
| |||||||||||||||
| 328 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Roaming\Windows Folder' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 928 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AppLaunch.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AppLaunch.exe | s.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET ClickOnce Launch Utility Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
RedLine(PID) Process(928) AppLaunch.exe C2 (1)45.9.20.167:34189 Botnet640639202 Err_msg Auth_value1cf2ebfb78a2360e657cacea44023218 US (149) LEnvironmentogiEnvironmentn DatEnvironmenta Environment WSystem.Texteb DatSystem.Texta System.Text CoCryptographyokieCryptographys Cryptography ExtGenericension CooGenerickies Generic OFileInfopeFileInfora GFileInfoX StabFileInfole FileInfo OpLinqera GLinqX Linq ApGenericpDaGenericta\RGenericoamiGenericng\ Network Extension UNKNOWN . 1 cFileStreamredFileStreamit_cFileStreamardFileStreams FileStream \ Network\ Host Port : User Pass MANGO eNetworkCredentialxpirNetworkCredentialy NetworkCredential %USEWanaLifeRPROFILE%\AppDaWanaLifeta\LWanaLifeocal WanaLife Def Win String.Replace String.Remove bcrFileStream.IOypt.dFileStream.IOll FileStream.IO BCrMemoryStreamyptOpeMemoryStreamnAlgorithmProviMemoryStreamder MemoryStream BCrFileStreamyptCloseAlgoritFileStreamhmProvFileStreamider BCrIOStreamyptDecrIOStreamypt IOStream BCrFile.ReadyptDesFile.ReadtroyKFile.Readey File.Read BCFile.OpenryptGeFile.OpentPropeFile.Openrty File.Open BCFile.CloseryptSFile.CloseetPrFile.CloseoperFile.Closety File.Close BCrFile.ReadAllTextyptImFile.ReadAllTextportKFile.ReadAllTextey File.ReadAllText windows-1251 AES Microsoft Primitive Provider ChainingModeGCM AuthTagLength ChainingMode ObjectLength KeyDataBlob - net.tcp:// / localhost 1cf2ebfb78a2360e657cacea44023218 Authorization ns1 UNKNWON AiUxDCYgWTUsJ00RPQcvVykDOAsiCApZ 640639202 Ladyism Yandex\YaAddon ToString asf *wallet* _ \TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata String Replace string.Replace %USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng File.Write Handler npvo* %USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl serviceInterface.Extension ProldCharotonVoldCharPN oldChar nSystem.CollectionspvoSystem.Collections* System.Collections ( UNIQUE cstringmstringd string /ProcessC Process Process | " gasdl94ja;sdiasdl94ja;s32 asdl94ja;s Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds asdl94jlajsd Width Height CopyFromScreen https://api.ip.sb/ip 80 81 0.0.0.0 SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor System.Windows.Forms Name NumberOfCores roSystem.Linqot\CISystem.LinqMV2 System.Linq SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller AdapterRAM SOFTWARE\WOW6432Node\Clients\StartMenuInternet SOFTWARE\Clients\StartMenuInternet shell\open\command Unknown Version SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente System.Management SerialNumber SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId=' ' FileSystem SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId=' System. ExecutablePath [ ] Concat0 MConcatb oConcatr Concat0 Concat SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem Memory {0}{1}{2} x32 x64 x86 SOFTWARE\Microsoft\Windows NT\CurrentVersion ProductName CSDVersion Unknown _[ | |||||||||||||||
| 2248 | "C:\Windows\System32\schtasks.exe" /create /tn WindowsService /tr "C:\Users\admin\AppData\Roaming\Windows Folder\Windows Service.exe" /sc onlogon /rl highest | C:\Windows\System32\schtasks.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2460 | "C:\Windows\System32\schtasks.exe" /delete /tn WindowsService /f | C:\Windows\System32\schtasks.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2660 | "C:\Windows\System32\schtasks.exe" /create /sc MINUTE /mo 1 /tn WindowsServiceUpload /tr "C:\Users\admin\AppData\Roaming\Windows Folder\Windows Service.exe" /f /rl highest | C:\Windows\System32\schtasks.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2924 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\RarSFX0.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3516 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.16265\RarSFX0\setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.16265\RarSFX0\setup.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft.Office.Tools.Excel.v4.0.Utilities.dll Exit code: 3221226540 Version: 10.0.30319.1 Modules
| |||||||||||||||
| 3724 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.15284\RarSFX0\s.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.15284\RarSFX0\s.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225513 Modules
RedLine(PID) Process(3724) s.exe C2 (1)45.9.20.167:34189 Botnet640639202 Err_msg Auth_value1cf2ebfb78a2360e657cacea44023218 US (149) LEnvironmentogiEnvironmentn DatEnvironmenta Environment WSystem.Texteb DatSystem.Texta System.Text CoCryptographyokieCryptographys Cryptography ExtGenericension CooGenerickies Generic OFileInfopeFileInfora GFileInfoX StabFileInfole FileInfo OpLinqera GLinqX Linq ApGenericpDaGenericta\RGenericoamiGenericng\ Network Extension UNKNOWN . 1 cFileStreamredFileStreamit_cFileStreamardFileStreams FileStream \ Network\ Host Port : User Pass MANGO eNetworkCredentialxpirNetworkCredentialy NetworkCredential %USEWanaLifeRPROFILE%\AppDaWanaLifeta\LWanaLifeocal WanaLife Def Win String.Replace String.Remove bcrFileStream.IOypt.dFileStream.IOll FileStream.IO BCrMemoryStreamyptOpeMemoryStreamnAlgorithmProviMemoryStreamder MemoryStream BCrFileStreamyptCloseAlgoritFileStreamhmProvFileStreamider BCrIOStreamyptDecrIOStreamypt IOStream BCrFile.ReadyptDesFile.ReadtroyKFile.Readey File.Read BCFile.OpenryptGeFile.OpentPropeFile.Openrty File.Open BCFile.CloseryptSFile.CloseetPrFile.CloseoperFile.Closety File.Close BCrFile.ReadAllTextyptImFile.ReadAllTextportKFile.ReadAllTextey File.ReadAllText windows-1251 AES Microsoft Primitive Provider ChainingModeGCM AuthTagLength ChainingMode ObjectLength KeyDataBlob - net.tcp:// / localhost 1cf2ebfb78a2360e657cacea44023218 Authorization ns1 UNKNWON AiUxDCYgWTUsJ00RPQcvVykDOAsiCApZ 640639202 Ladyism Yandex\YaAddon ToString asf *wallet* _ \TeEnvironmentlegraEnvironmentm DEnvironmentesktoEnvironmentp\tdEnvironmentata String Replace string.Replace %USERPFile.WriteROFILE%\AppFile.WriteData\RoamiFile.Writeng File.Write Handler npvo* %USERPserviceInterface.ExtensionROFILE%\ApserviceInterface.ExtensionpData\LocaserviceInterface.Extensionl serviceInterface.Extension ProldCharotonVoldCharPN oldChar nSystem.CollectionspvoSystem.Collections* System.Collections ( UNIQUE cstringmstringd string /ProcessC Process Process | " gasdl94ja;sdiasdl94ja;s32 asdl94ja;s Gasdl94jlajsdetDevasdl94jlajsdiceCapasdl94jlajsds asdl94jlajsd Width Height CopyFromScreen https://api.ip.sb/ip 80 81 0.0.0.0 SELSystem.Windows.FormsECT * FRSystem.Windows.FormsOM WinSystem.Windows.Forms32_ProcSystem.Windows.Formsessor System.Windows.Forms Name NumberOfCores roSystem.Linqot\CISystem.LinqMV2 System.Linq SELSystem.LinqECT * FRSystem.LinqOM WinSystem.Linq32_VideoCoSystem.Linqntroller AdapterRAM SOFTWARE\WOW6432Node\Clients\StartMenuInternet SOFTWARE\Clients\StartMenuInternet shell\open\command Unknown Version SELESystem.ManagementCT * FRSystem.ManagementOM WiSystem.Managementn32_DisSystem.ManagementkDrivSystem.Managemente System.Management SerialNumber SELSystem.Text.RegularExpressionsECT * FRSystem.Text.RegularExpressionsOM Win32_PSystem.Text.RegularExpressionsrocess WSystem.Text.RegularExpressionshere SessSystem.Text.RegularExpressionsionId=' ' FileSystem SSystem.ELECT * FRSystem.OM WiSystem.n32_ProcSystem.ess WherSystem.e SessiSystem.onId=' System. ExecutablePath [ ] Concat0 MConcatb oConcatr Concat0 Concat SELEMemoryCT * FMemoryROM WiMemoryn32_OperMemoryatingSMemoryystem Memory {0}{1}{2} x32 x64 x86 SOFTWARE\Microsoft\Windows NT\CurrentVersion ProductName CSDVersion Unknown _[ | |||||||||||||||
Total events
5 454
Read events
5 404
Write events
50
Delete events
0
Modification events
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\RarSFX0.zip | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
5
Suspicious files
2
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2924 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.15284\RarSFX0\lol.vbs | text | |
MD5:— | SHA256:— | |||
| 2924 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.16265\RarSFX0\lol.vbs | text | |
MD5:— | SHA256:— | |||
| 2924 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.15284\RarSFX0\setup.exe | executable | |
MD5:— | SHA256:— | |||
| 128 | setup.exe | C:\Users\admin\AppData\Roaming\Windows Folder\Windows Service.exe | executable | |
MD5:— | SHA256:— | |||
| 2924 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.15284\RarSFX0\s.exe | executable | |
MD5:— | SHA256:— | |||
| 2924 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.16265\RarSFX0\setup.exe | executable | |
MD5:— | SHA256:— | |||
| 2924 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.16265\RarSFX0\s.exe | executable | |
MD5:— | SHA256:— | |||
| 328 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 328 | powershell.exe | C:\Users\admin\AppData\Local\Temp\pwbfrkjq.ehj.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 328 | powershell.exe | C:\Users\admin\AppData\Local\Temp\k34eb4vj.jyd.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
128 | setup.exe | 185.199.110.133:443 | raw.githubusercontent.com | GitHub, Inc. | NL | malicious |
928 | AppLaunch.exe | 45.9.20.167:34189 | — | — | — | malicious |
128 | setup.exe | 185.199.111.133:443 | raw.githubusercontent.com | GitHub, Inc. | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
raw.githubusercontent.com |
| shared |
dns.msftncsi.com |
| shared |