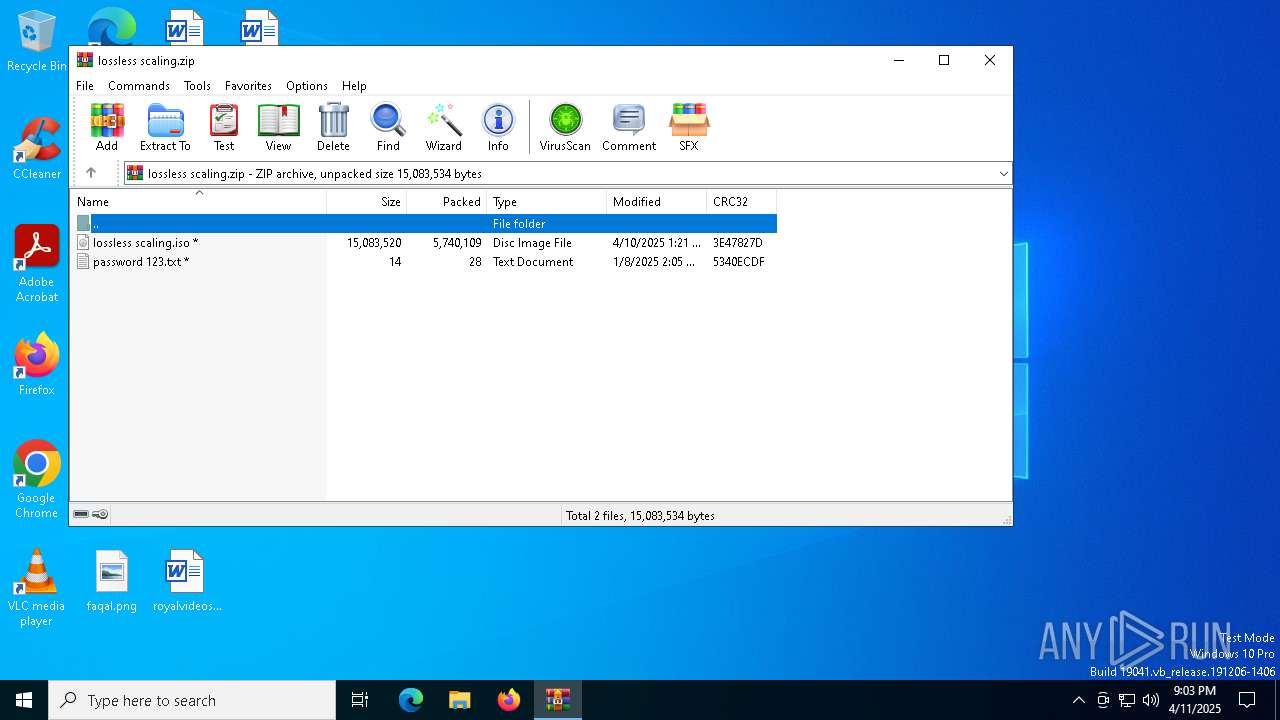
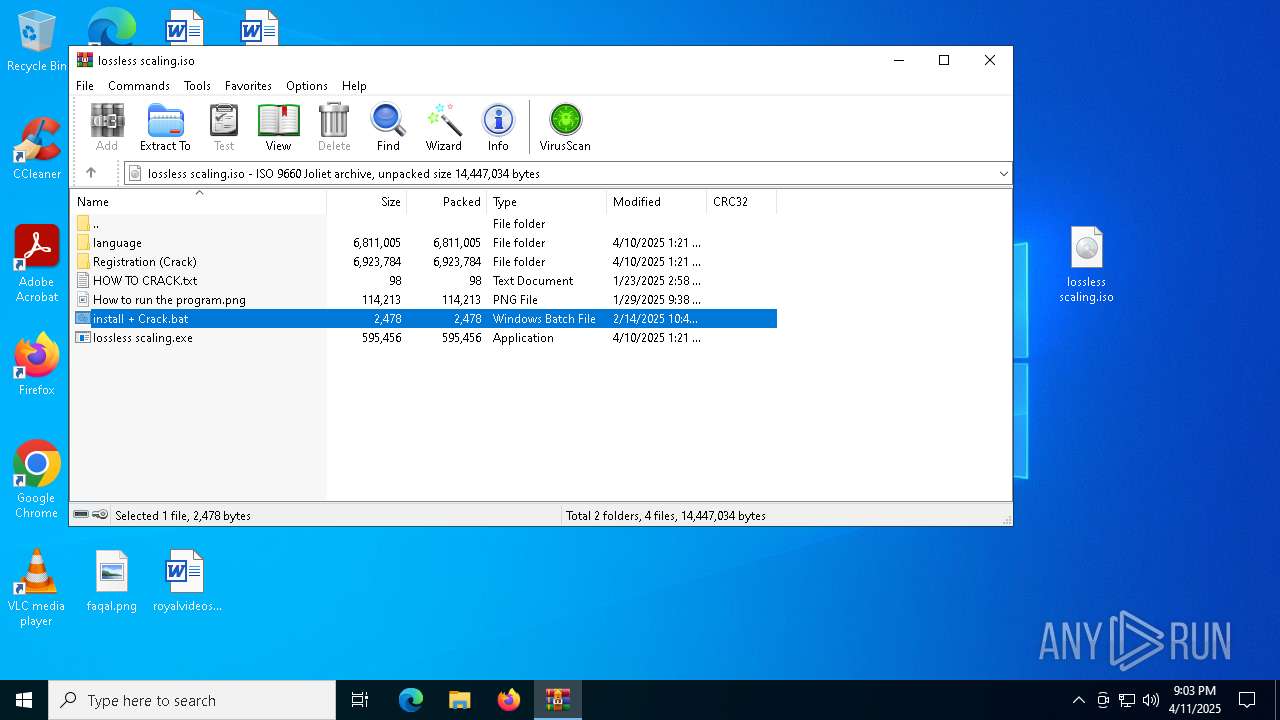
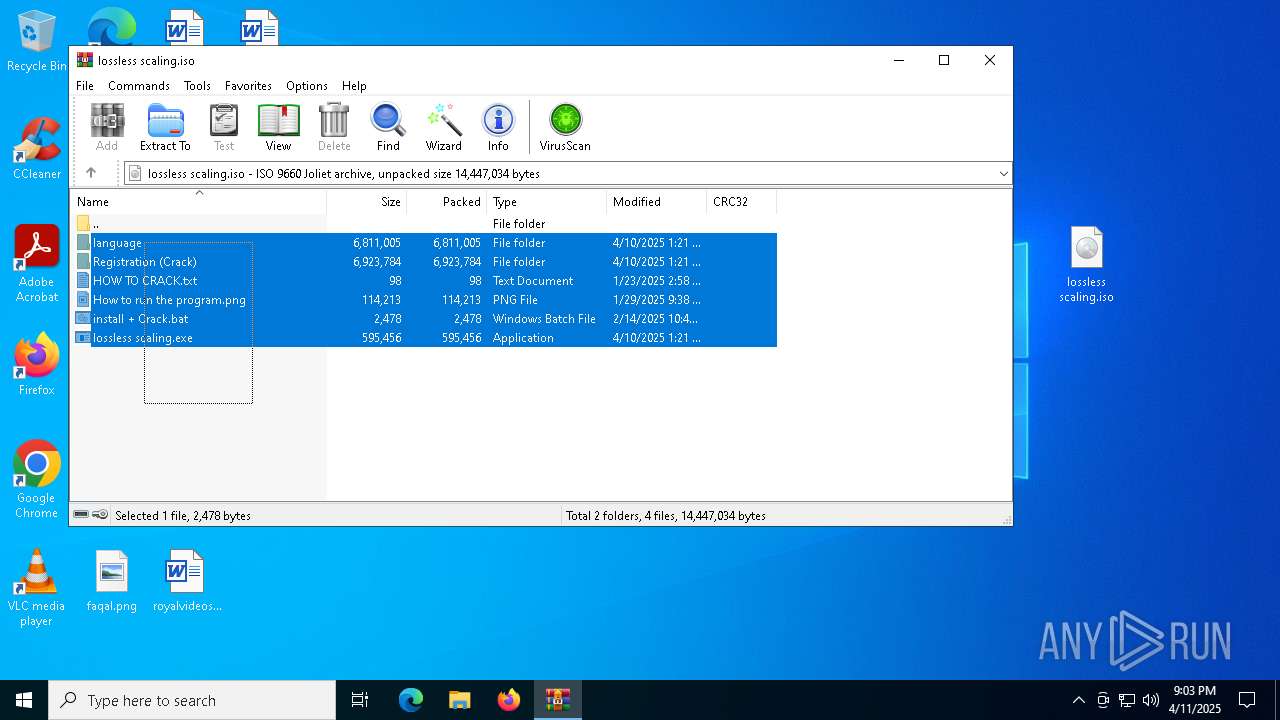
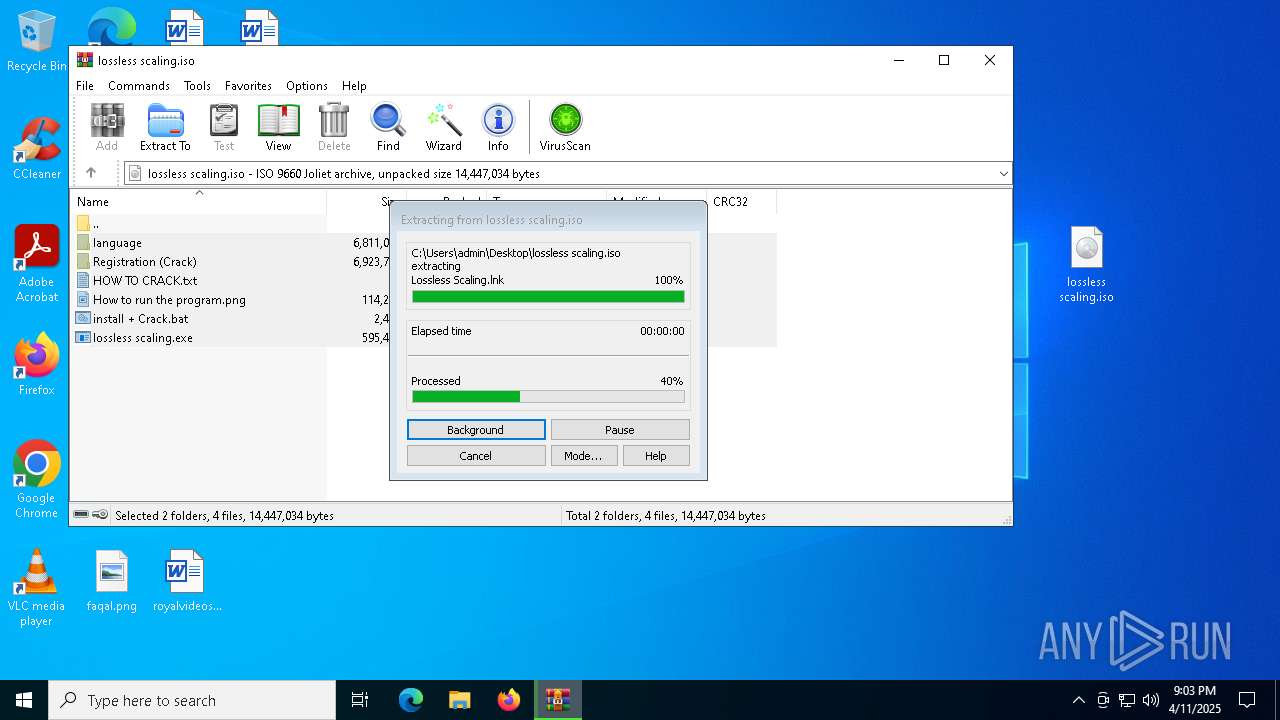
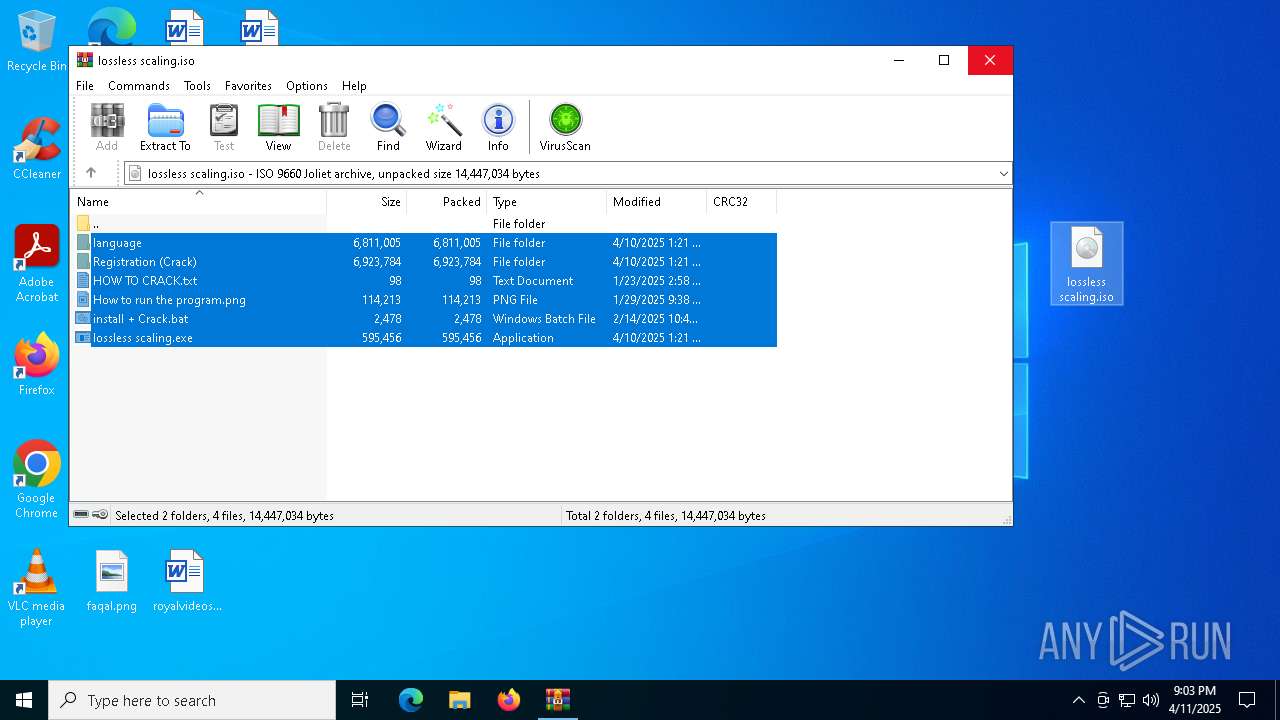
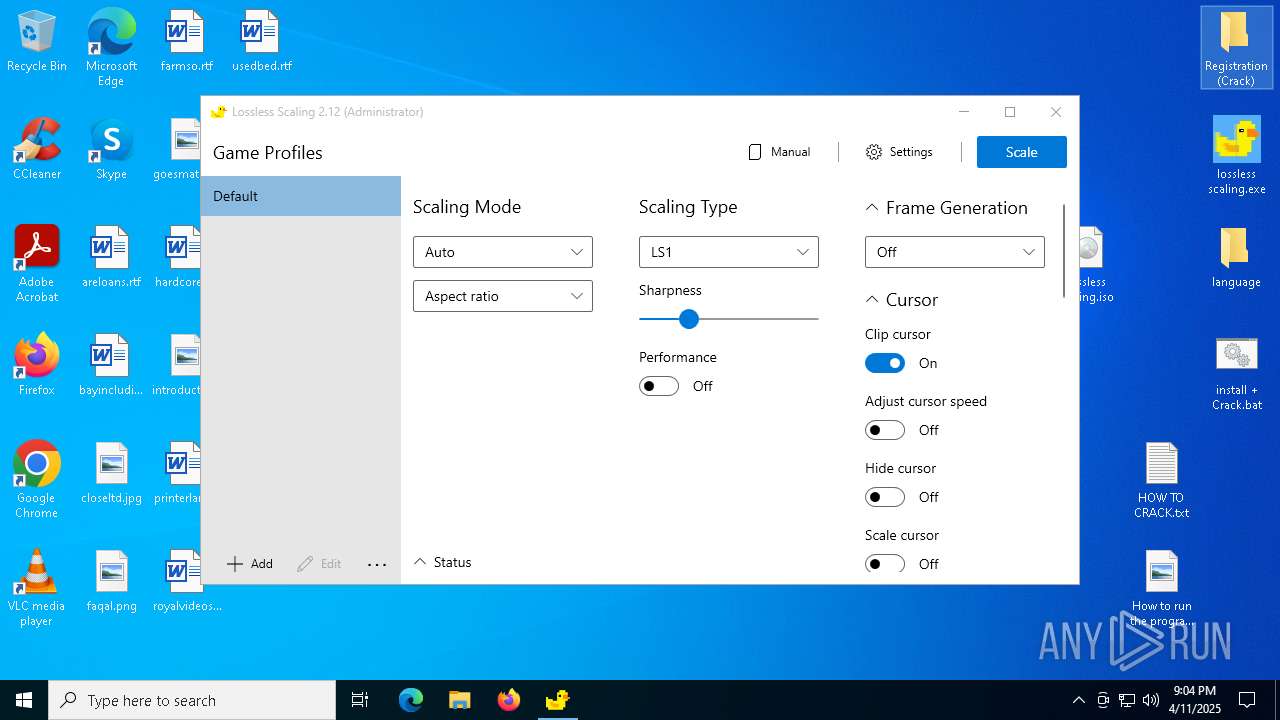
| File name: | lossless scaling.zip |
| Full analysis: | https://app.any.run/tasks/f9637157-5bb1-49fb-a7ab-452e97148969 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 11, 2025, 21:03:32 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 96B477C099ADE32978EEC1B1E605E4DE |
| SHA1: | 2B5A57BEDD9CBC047ABA3B401749BFB137B07640 |
| SHA256: | BE73462D8628400651FD9F5B0DE91CDFB8F33AAA30AACAD8509D97CD45A1DE1F |
| SSDEEP: | 98304:y+mV4phEMr37b6oicekPRHT2e5llp+N79KrHdxxks2LR1SYsb50X/f6As0LHLH8N:y0fR2V/SnlaAidg4+J |
MALICIOUS
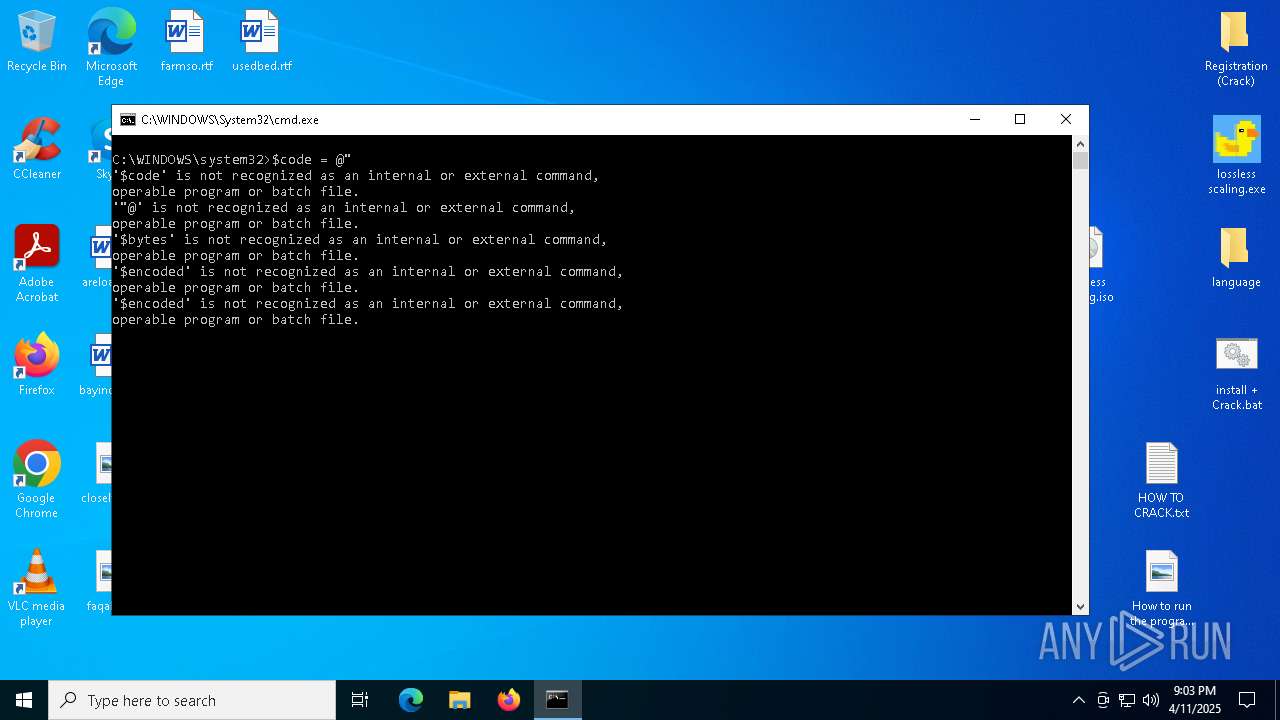
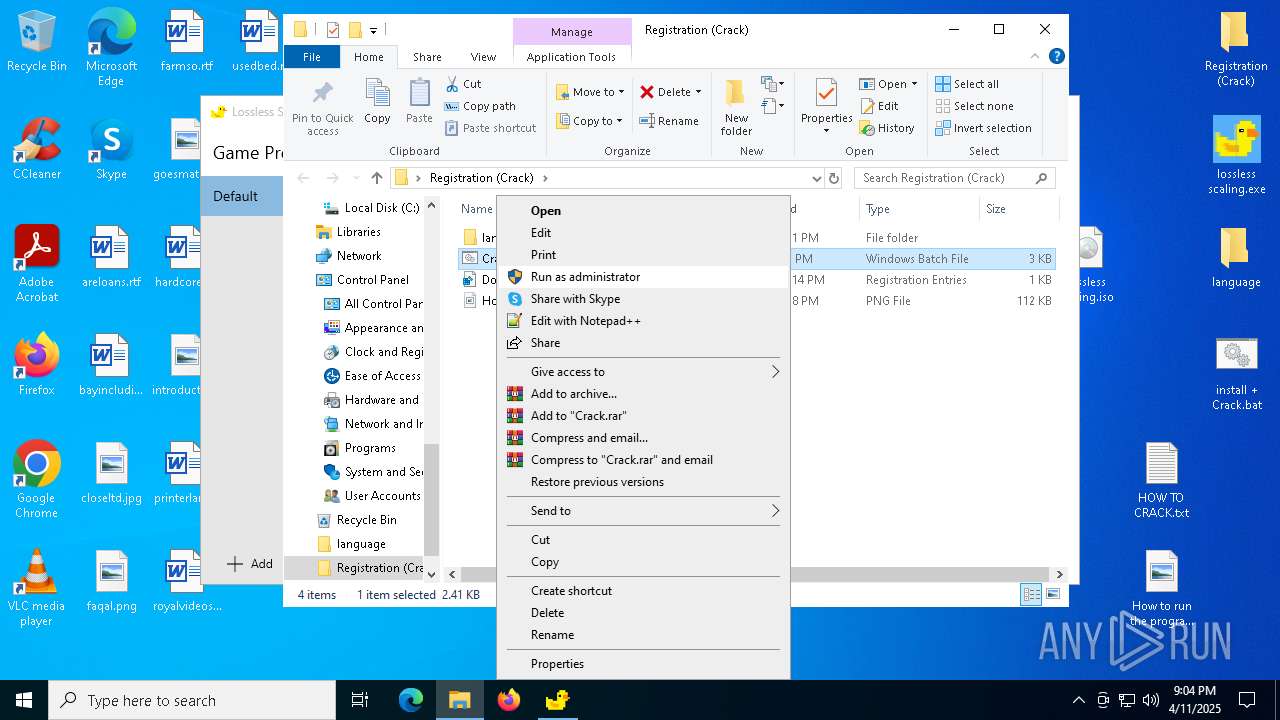
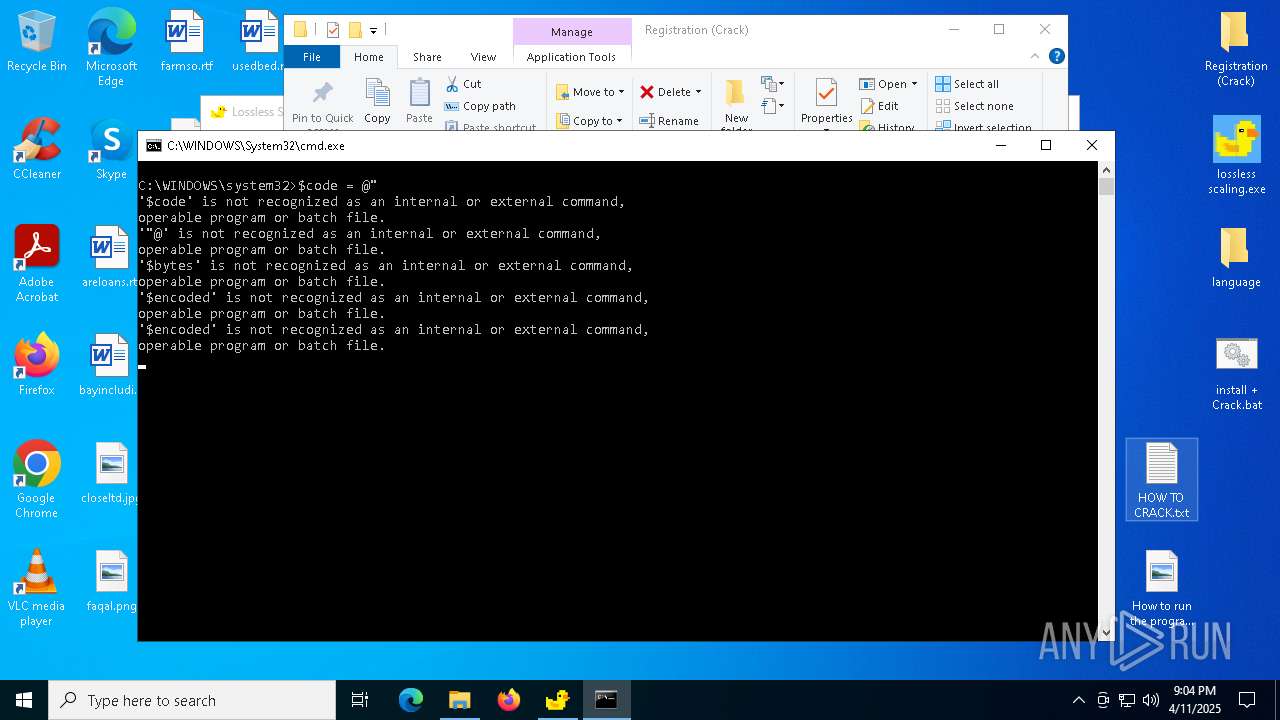
Bypass execution policy to execute commands
- powershell.exe (PID: 8164)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7868)
- powershell.exe (PID: 7808)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 4268)
- powershell.exe (PID: 8428)
- powershell.exe (PID: 8436)
- powershell.exe (PID: 6436)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 5416)
- powershell.exe (PID: 4724)
Run PowerShell with an invisible window
- powershell.exe (PID: 8164)
- powershell.exe (PID: 7728)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 8052)
- powershell.exe (PID: 8164)
- wscript.exe (PID: 7752)
- wscript.exe (PID: 7640)
- cmd.exe (PID: 7464)
- powershell.exe (PID: 7728)
- wscript.exe (PID: 1348)
- wscript.exe (PID: 2432)
- wscript.exe (PID: 9188)
- wscript.exe (PID: 10236)
- wscript.exe (PID: 7920)
- wscript.exe (PID: 8608)
Uses Task Scheduler to run other applications
- powershell.exe (PID: 7204)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7808)
- powershell.exe (PID: 7868)
- powershell.exe (PID: 8436)
- powershell.exe (PID: 8428)
- powershell.exe (PID: 6436)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 5416)
- powershell.exe (PID: 4724)
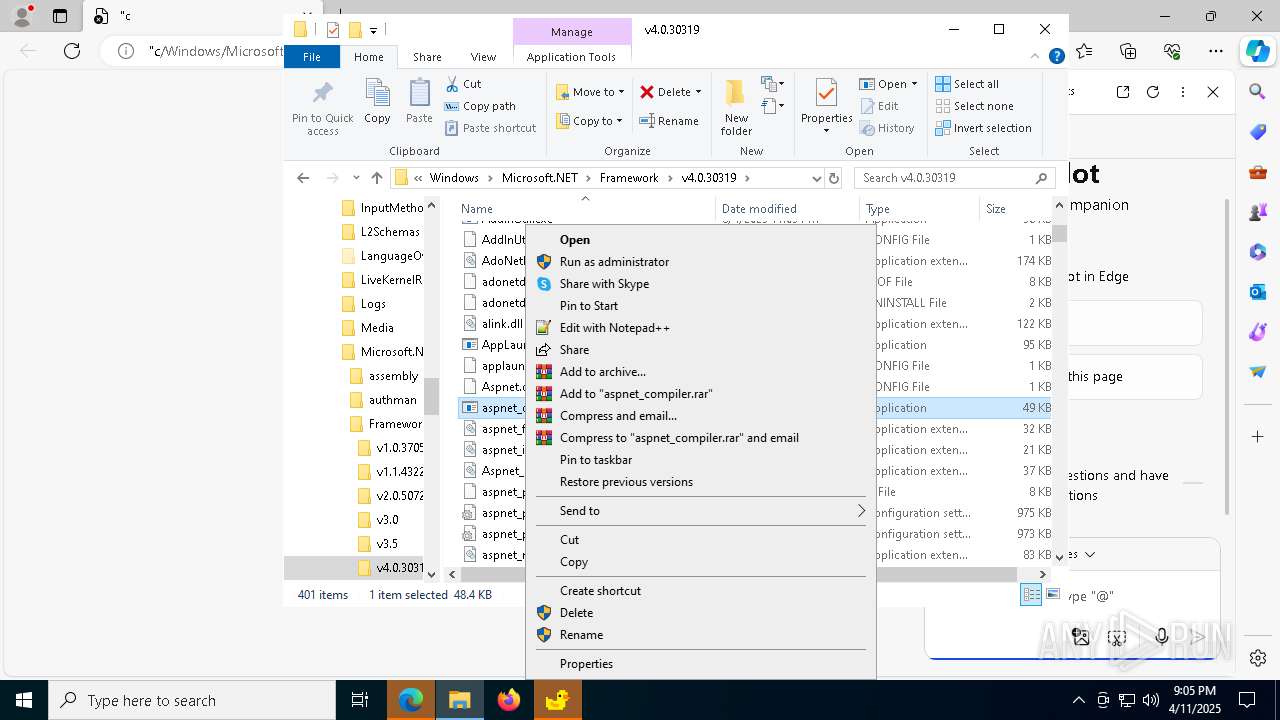
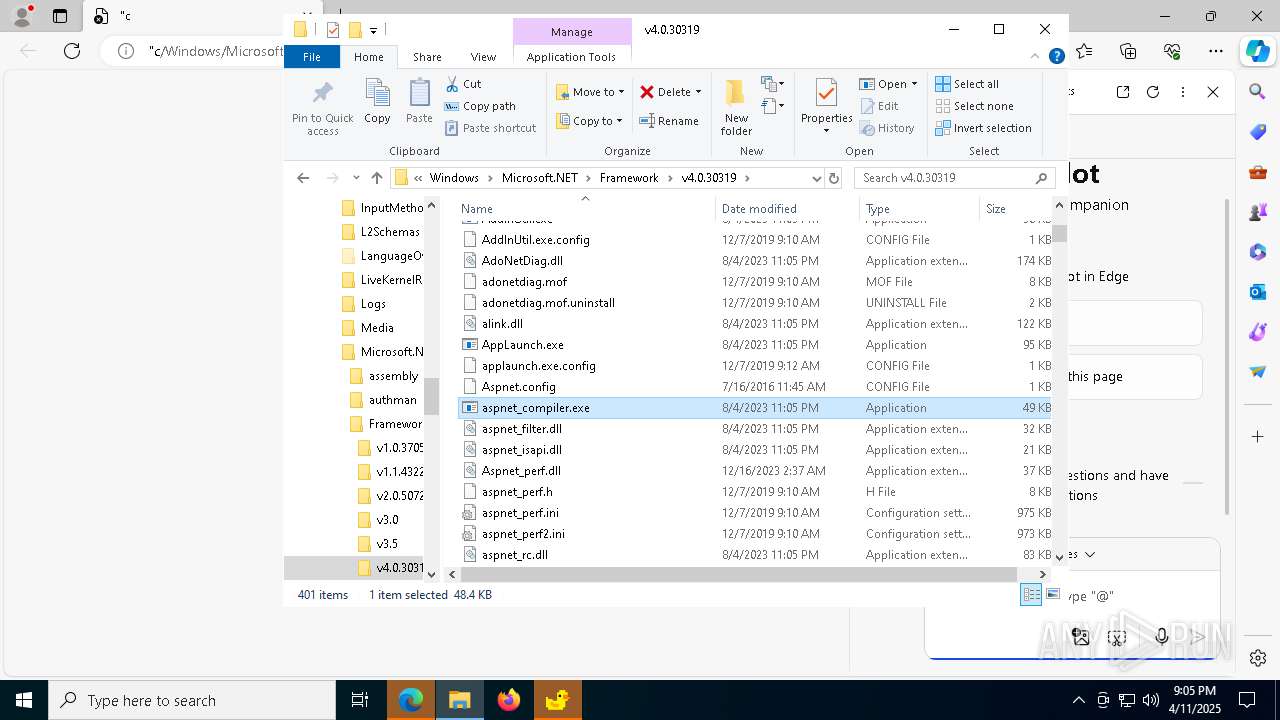
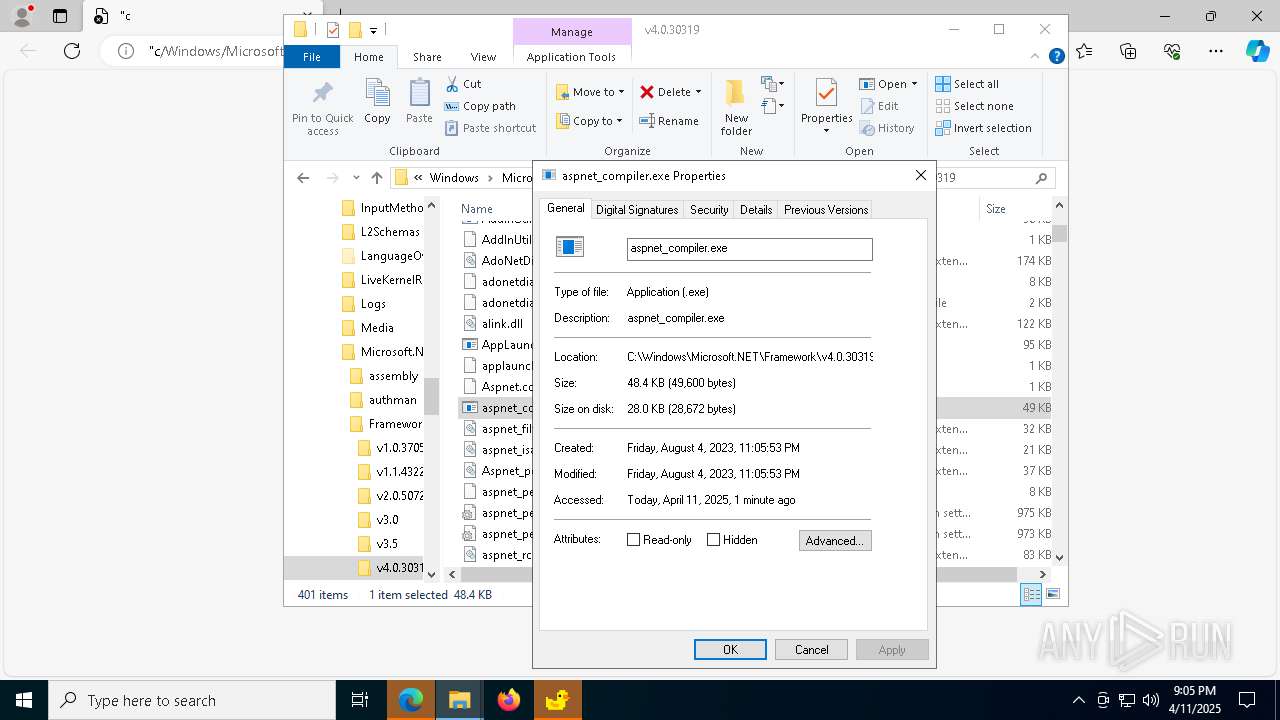
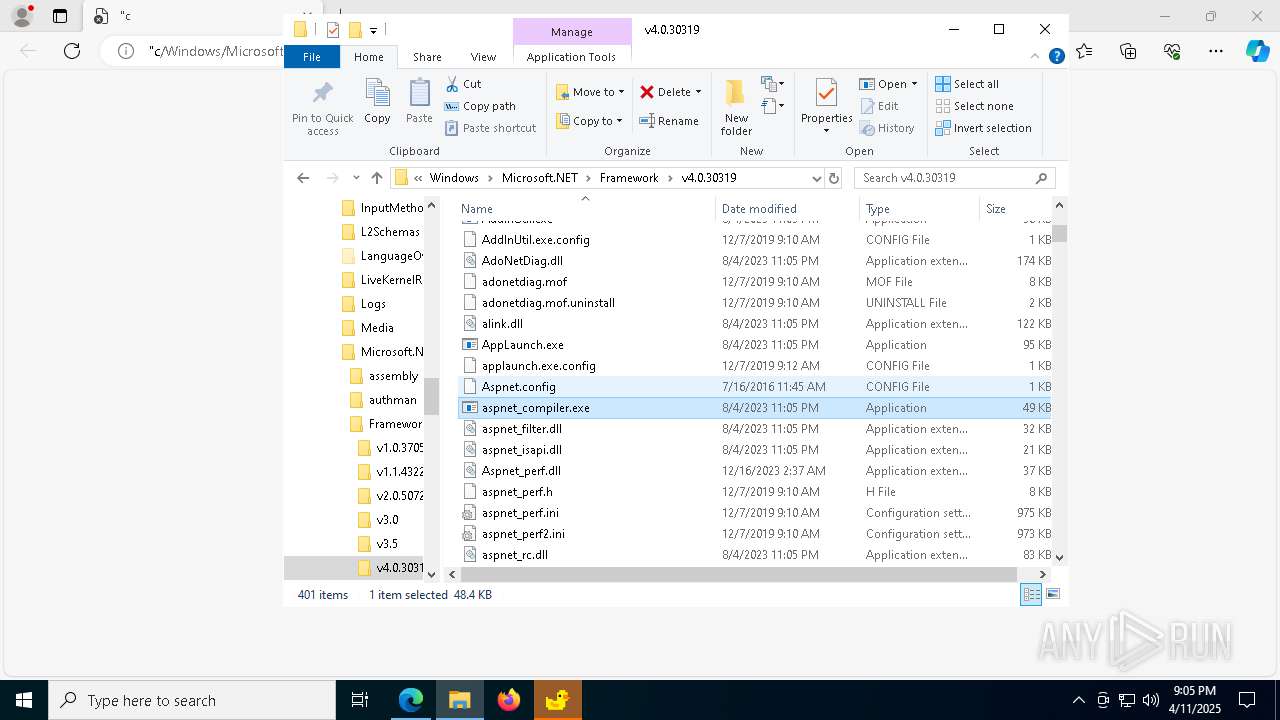
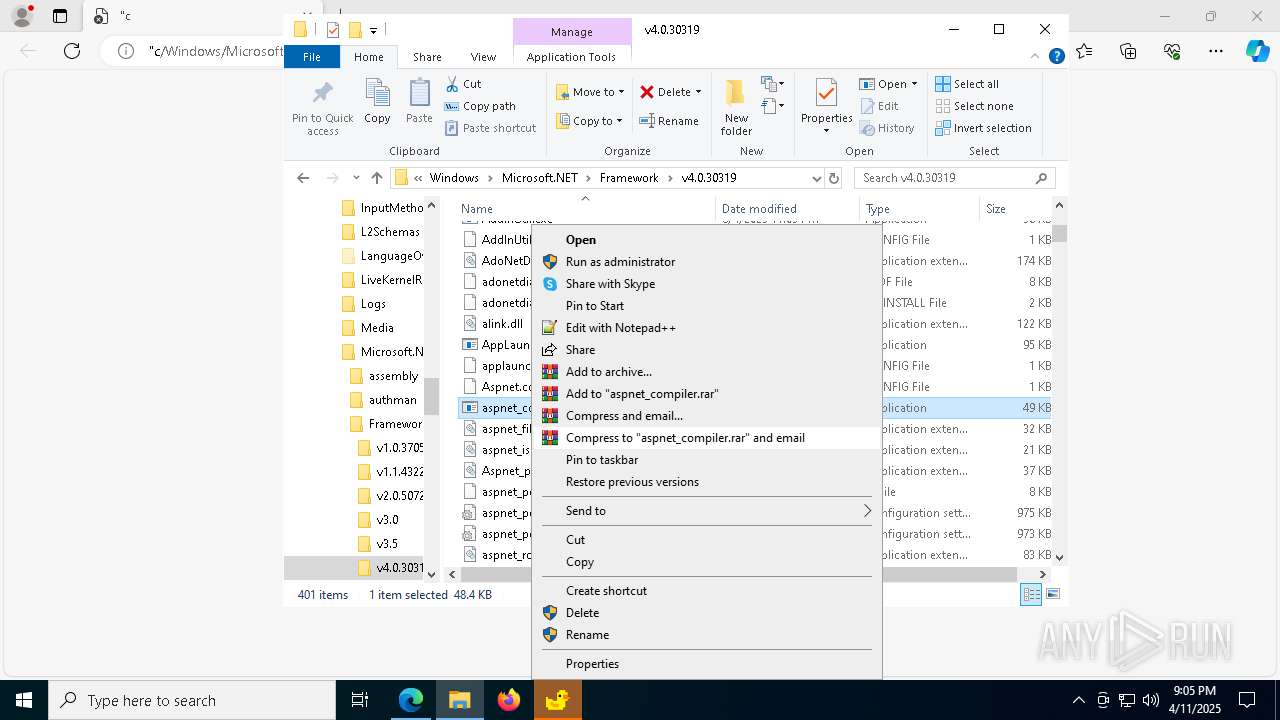
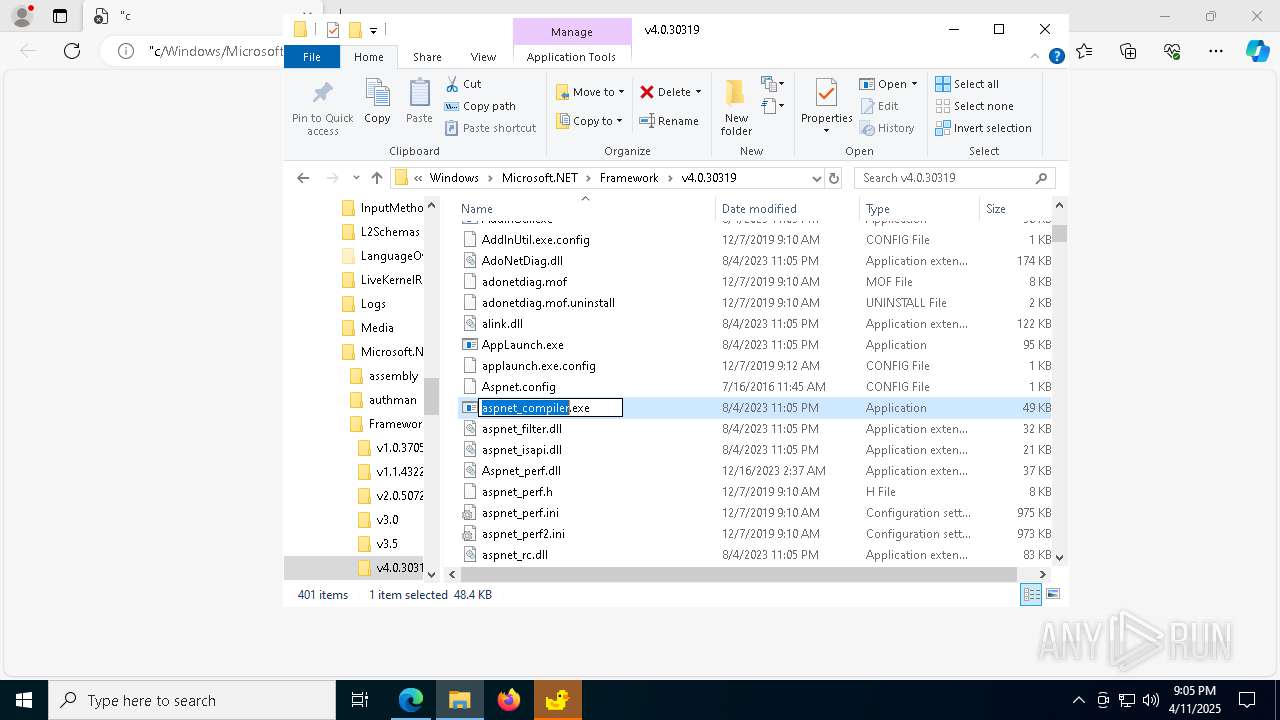
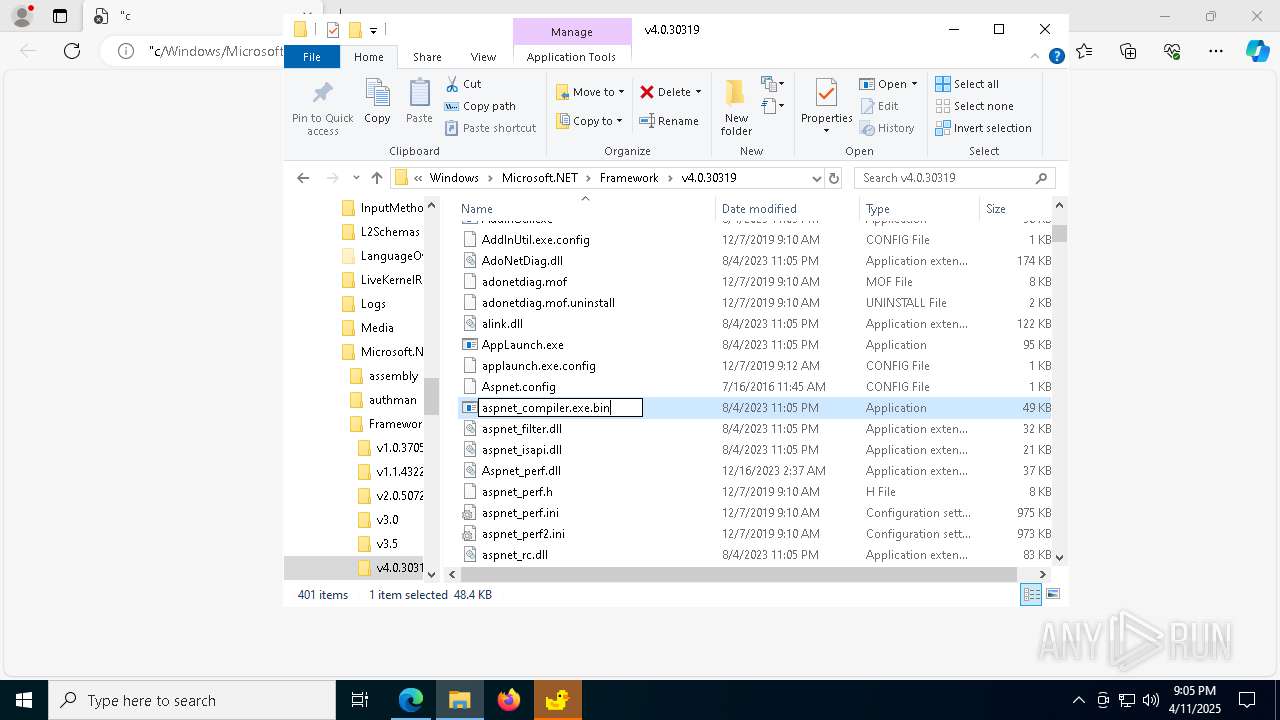
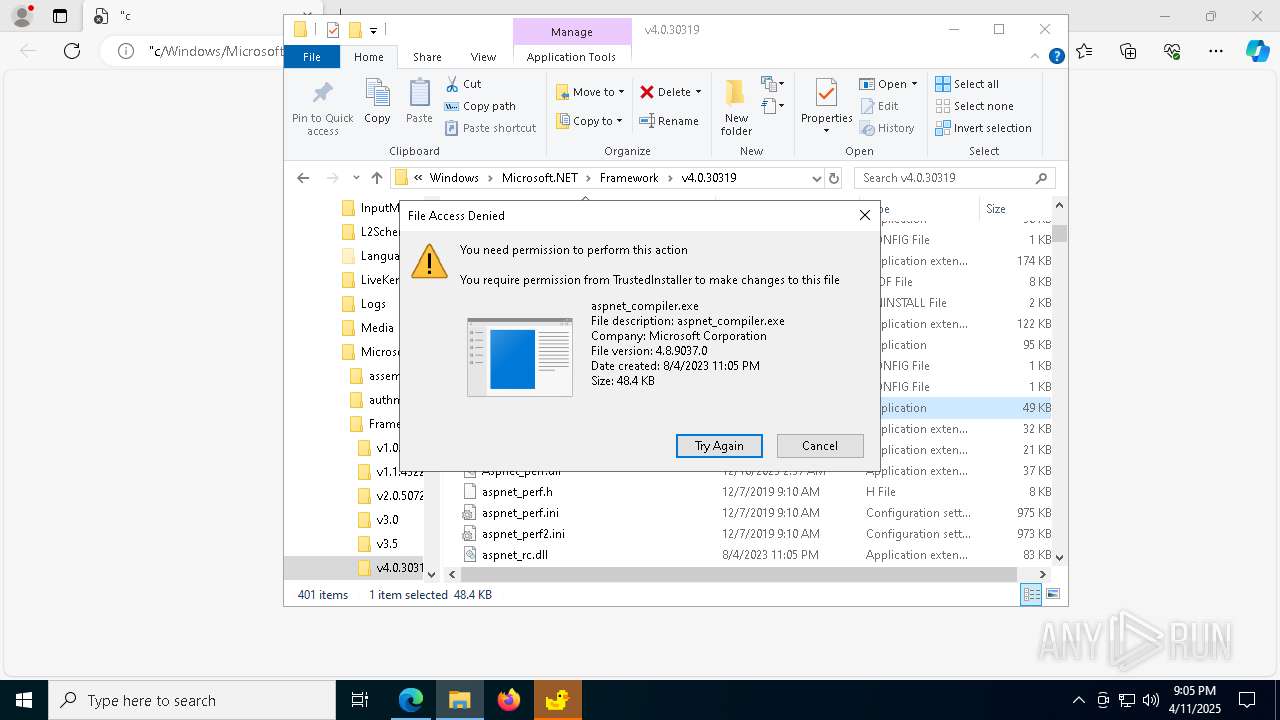
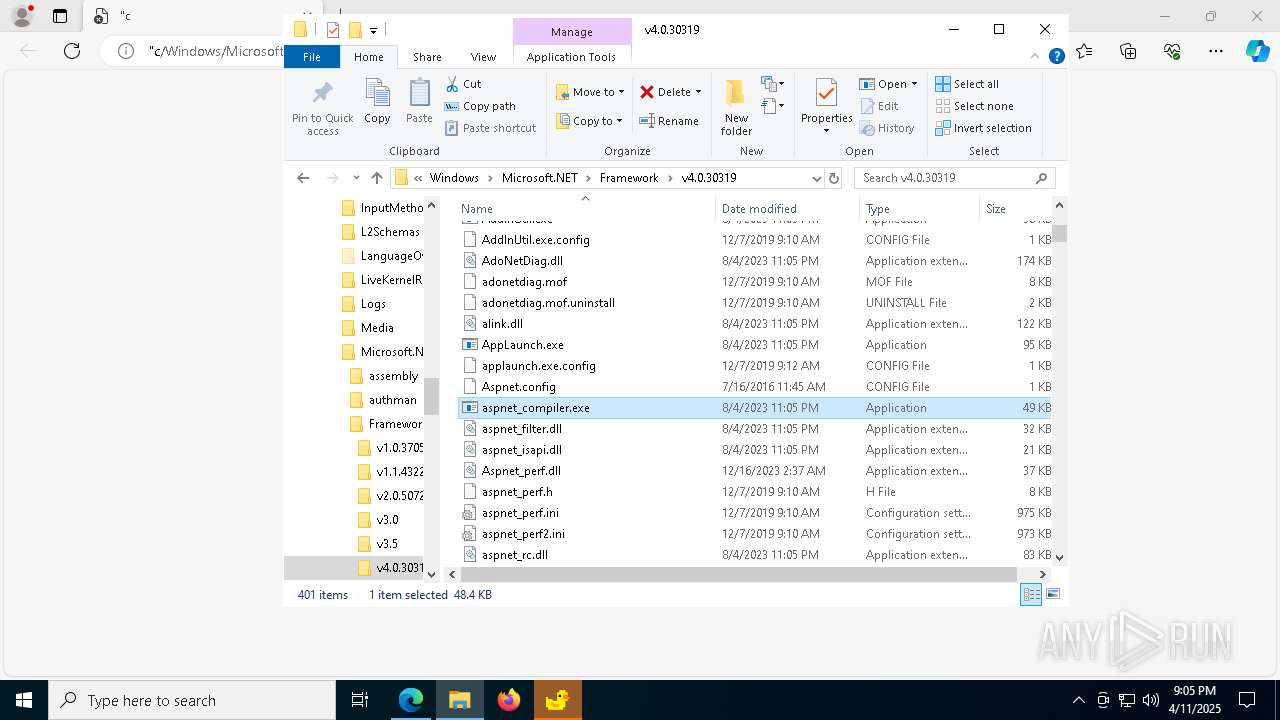
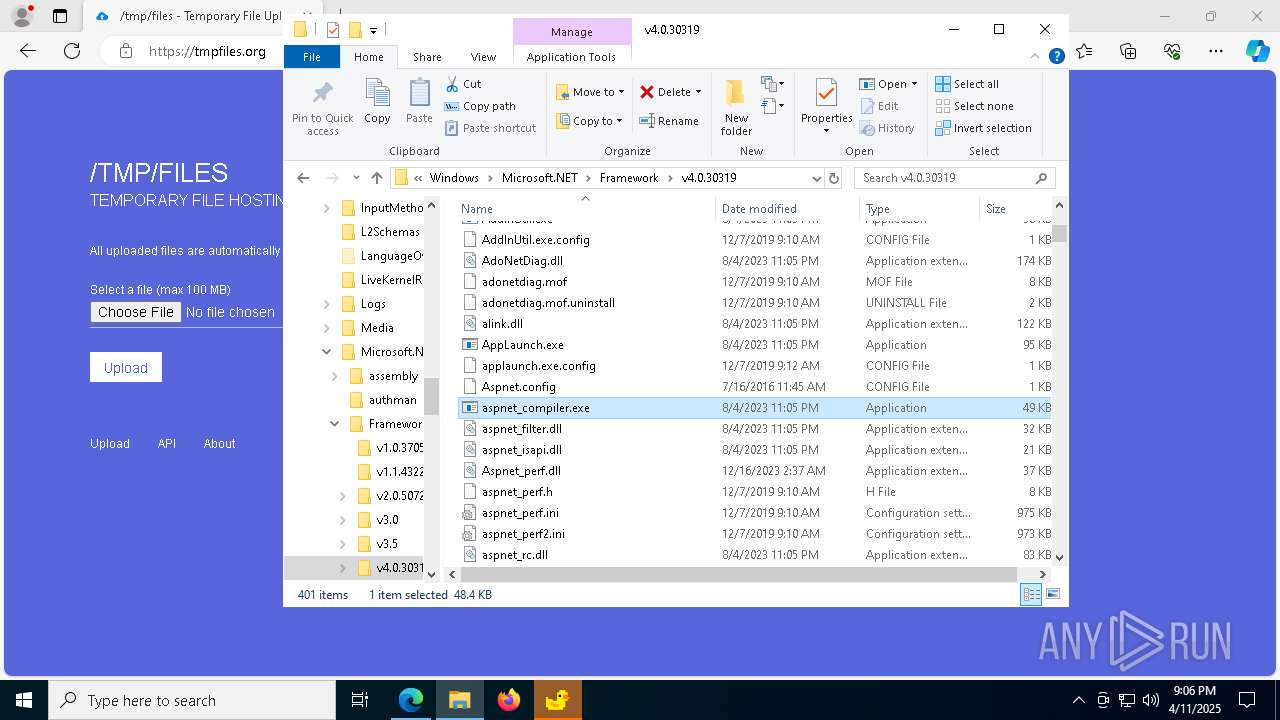
ASYNCRAT has been detected (SURICATA)
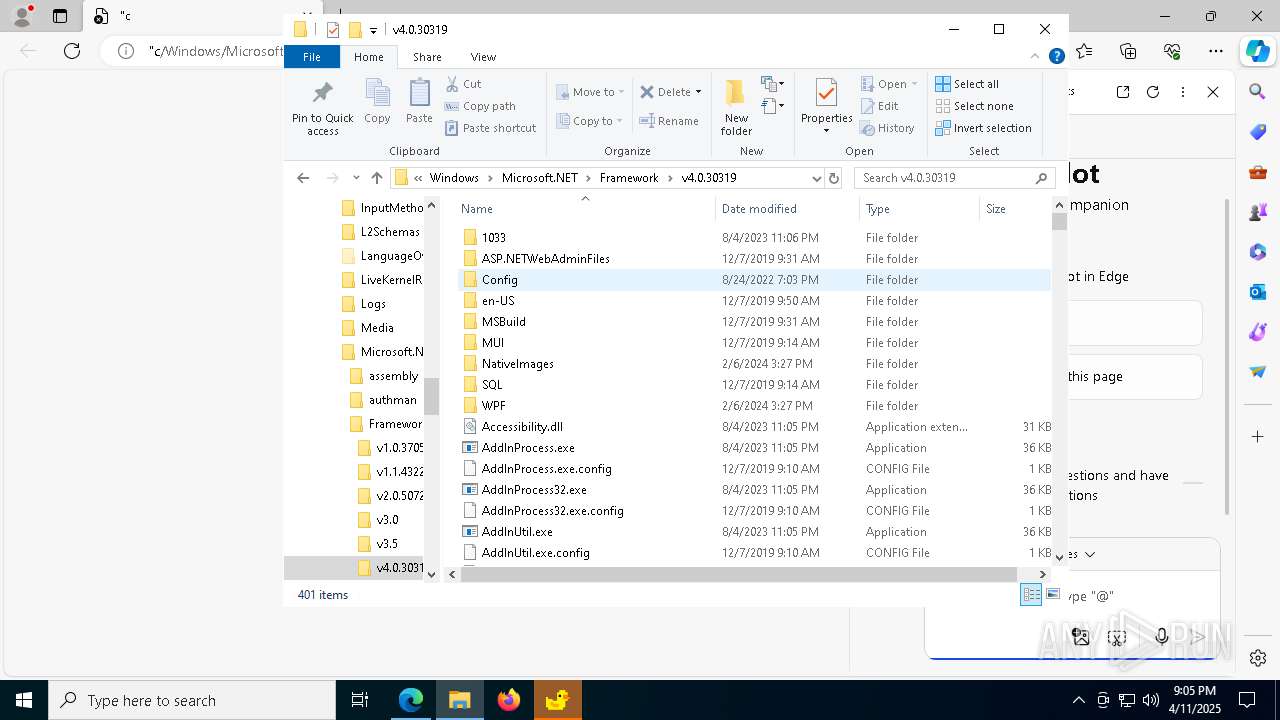
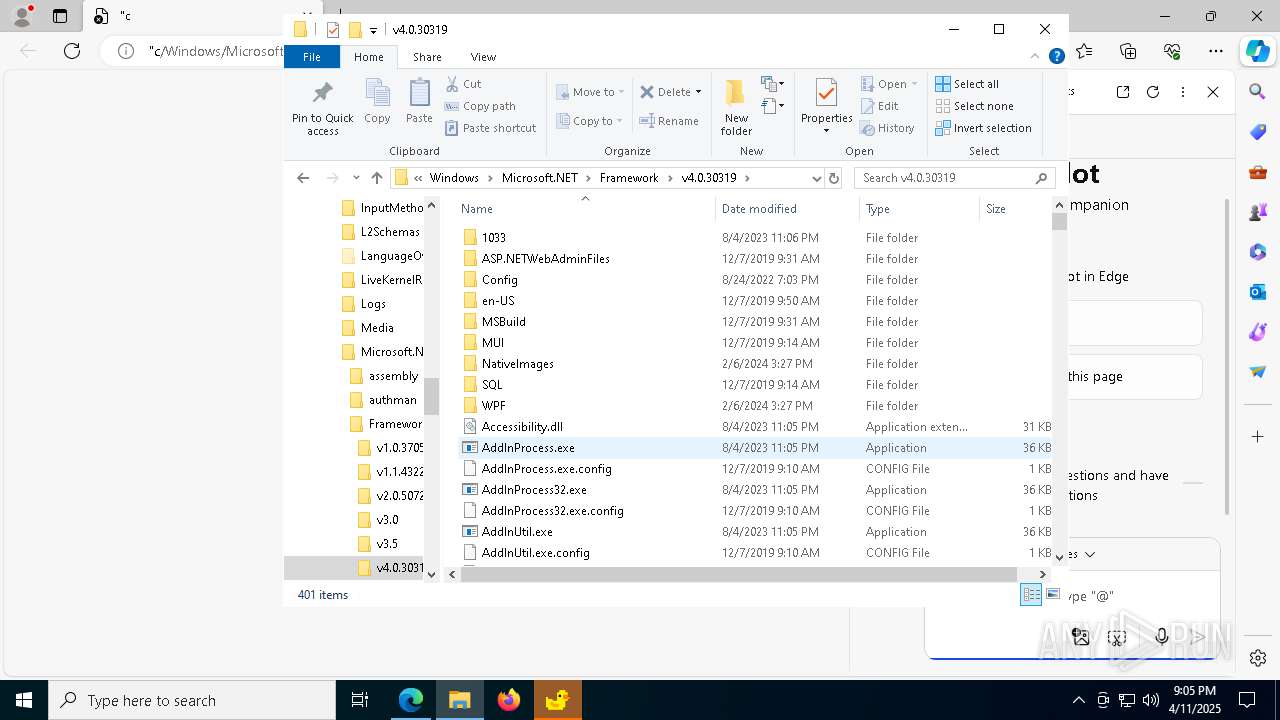
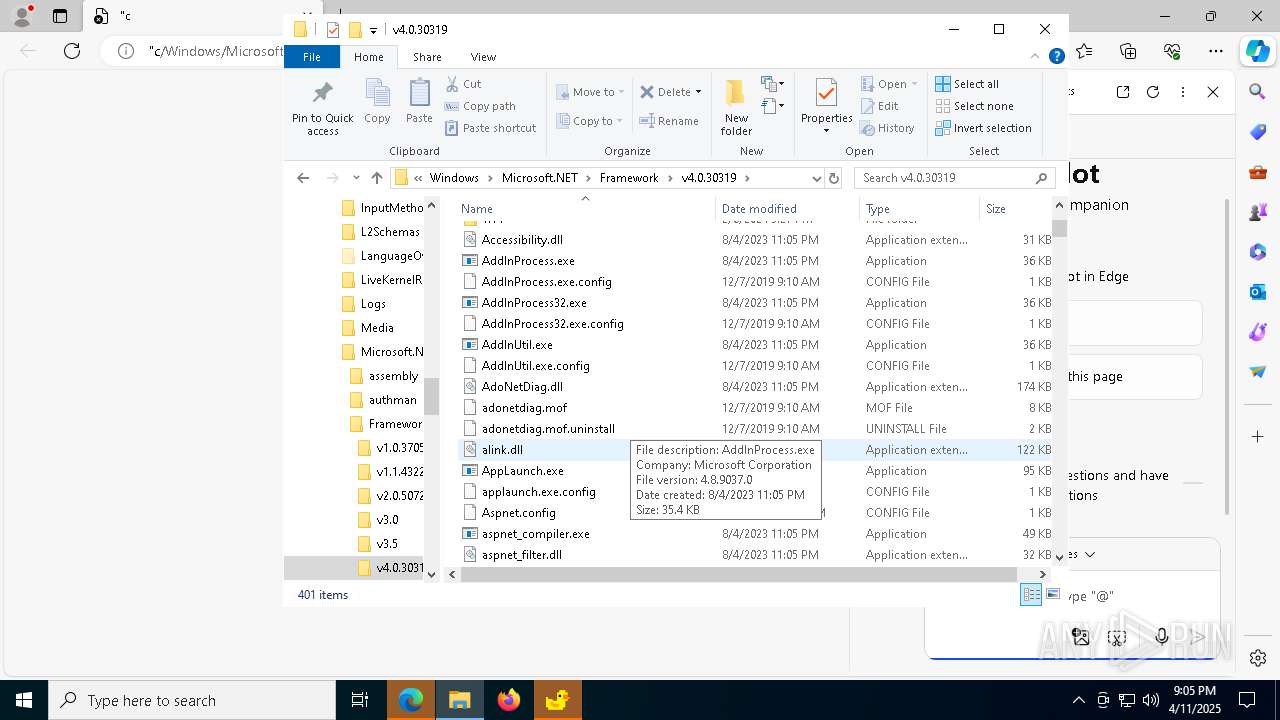
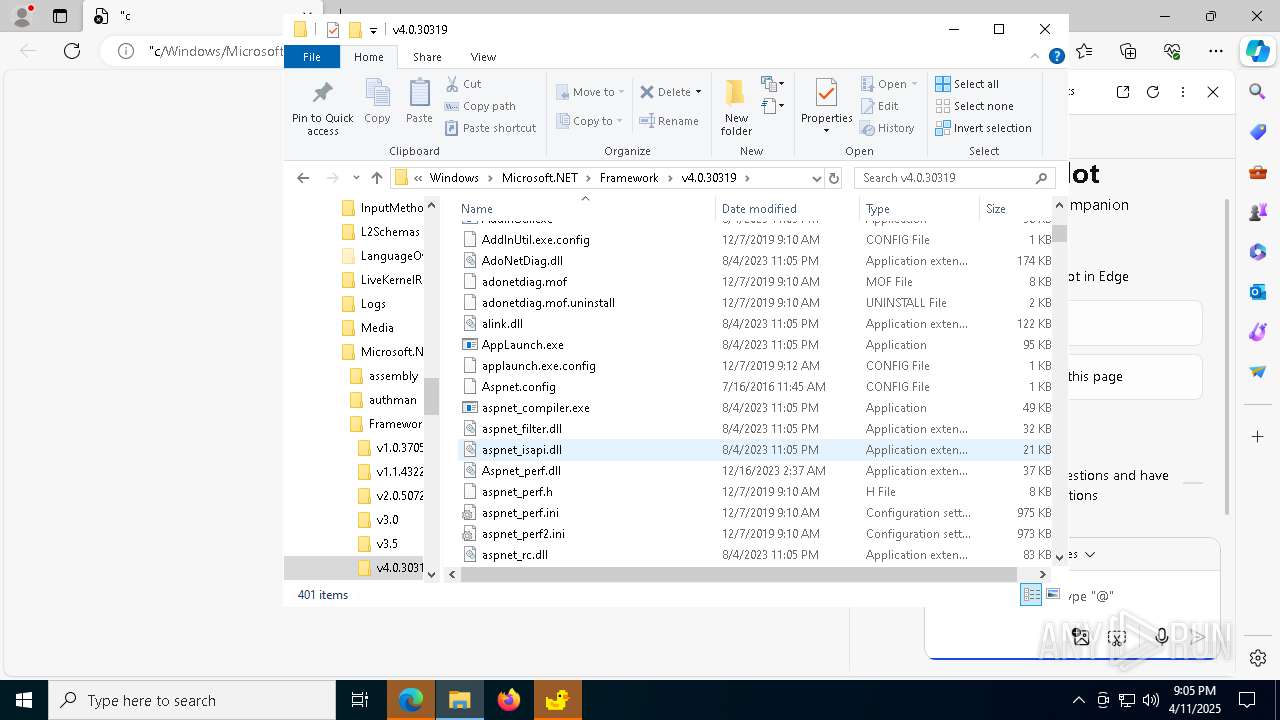
- aspnet_compiler.exe (PID: 6652)
Actions looks like stealing of personal data
- aspnet_compiler.exe (PID: 6652)
SUSPICIOUS
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 8052)
- net.exe (PID: 8116)
- cmd.exe (PID: 7464)
- net.exe (PID: 7688)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 8052)
- wscript.exe (PID: 7752)
- wscript.exe (PID: 7640)
- cmd.exe (PID: 7464)
- wscript.exe (PID: 1348)
- wscript.exe (PID: 2432)
- wscript.exe (PID: 10236)
- wscript.exe (PID: 9188)
- wscript.exe (PID: 7920)
- wscript.exe (PID: 8608)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8052)
- cmd.exe (PID: 7464)
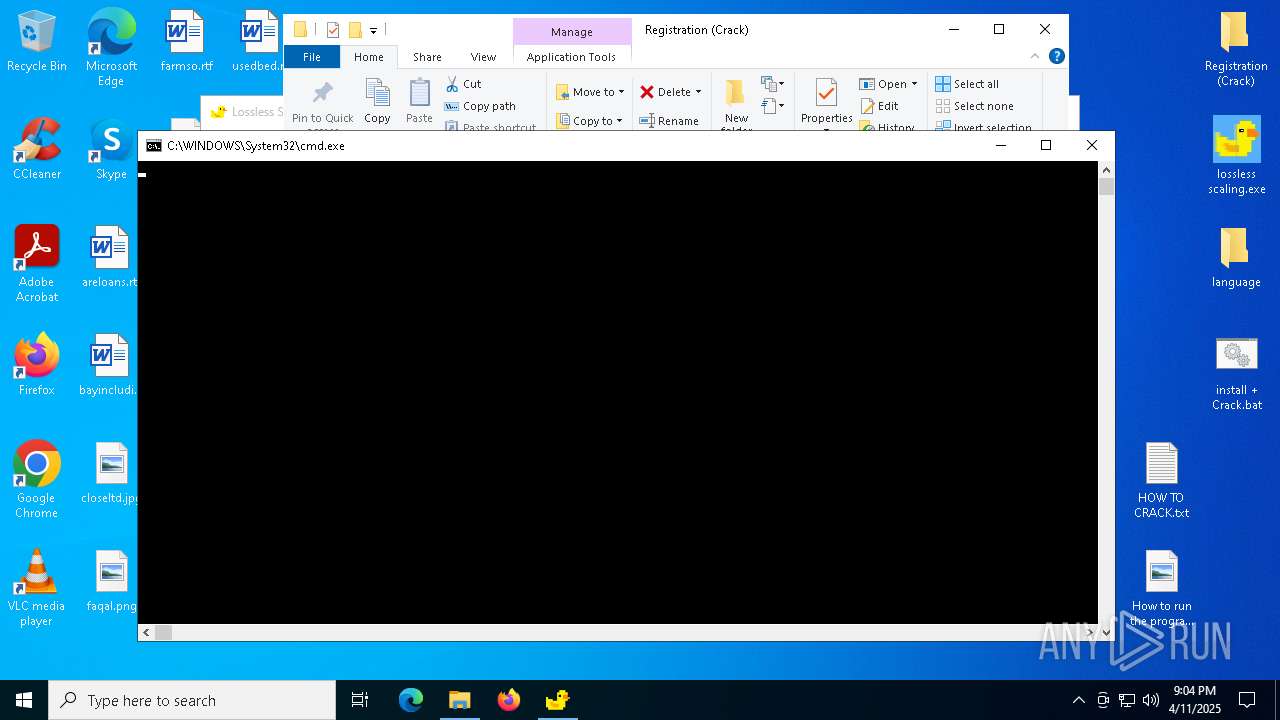
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8052)
- powershell.exe (PID: 8164)
- wscript.exe (PID: 7752)
- wscript.exe (PID: 7640)
- cmd.exe (PID: 7464)
- powershell.exe (PID: 7728)
- wscript.exe (PID: 1348)
- wscript.exe (PID: 2432)
- wscript.exe (PID: 9188)
- wscript.exe (PID: 10236)
- wscript.exe (PID: 7920)
- wscript.exe (PID: 8608)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8164)
- powershell.exe (PID: 7728)
Application launched itself
- powershell.exe (PID: 8164)
- powershell.exe (PID: 7728)
The process executes Powershell scripts
- powershell.exe (PID: 8164)
- wscript.exe (PID: 7752)
- wscript.exe (PID: 7640)
- powershell.exe (PID: 7728)
- wscript.exe (PID: 1348)
- wscript.exe (PID: 2432)
- wscript.exe (PID: 10236)
- wscript.exe (PID: 9188)
- wscript.exe (PID: 7920)
- wscript.exe (PID: 8608)
Executable content was dropped or overwritten
- powershell.exe (PID: 7204)
- Dism.exe (PID: 2852)
- Dism.exe (PID: 8232)
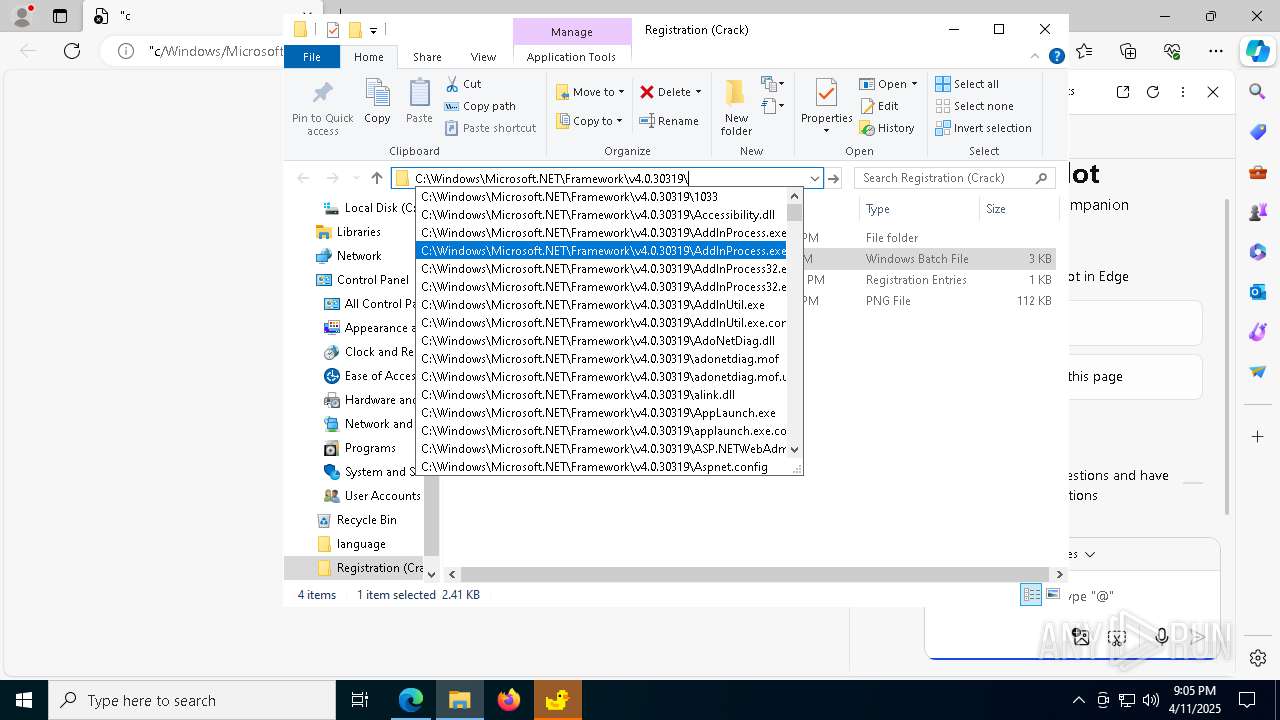
Uses REG/REGEDIT.EXE to modify registry
- powershell.exe (PID: 7204)
- powershell.exe (PID: 4268)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7808)
- powershell.exe (PID: 7868)
- powershell.exe (PID: 4268)
- powershell.exe (PID: 8428)
- powershell.exe (PID: 8436)
- powershell.exe (PID: 6436)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 4724)
- powershell.exe (PID: 5416)
Lists all scheduled tasks
- schtasks.exe (PID: 7464)
- schtasks.exe (PID: 5864)
- schtasks.exe (PID: 7568)
- schtasks.exe (PID: 4740)
- schtasks.exe (PID: 6108)
- schtasks.exe (PID: 4608)
- schtasks.exe (PID: 6404)
- schtasks.exe (PID: 7620)
- schtasks.exe (PID: 1616)
- schtasks.exe (PID: 9200)
- schtasks.exe (PID: 9060)
- schtasks.exe (PID: 10236)
- schtasks.exe (PID: 9004)
- schtasks.exe (PID: 8216)
The process verifies whether the antivirus software is installed
- powershell.exe (PID: 7204)
- powershell.exe (PID: 4268)
Likely accesses (executes) a file from the Public directory
- schtasks.exe (PID: 7412)
- schtasks.exe (PID: 7704)
- wscript.exe (PID: 7640)
- wscript.exe (PID: 7752)
- schtasks.exe (PID: 4268)
- powershell.exe (PID: 7868)
- RAR.exe (PID: 5332)
- powershell.exe (PID: 7808)
- RAR.exe (PID: 7636)
- wscript.exe (PID: 2432)
- wscript.exe (PID: 1348)
- powershell.exe (PID: 8428)
- powershell.exe (PID: 8436)
- wscript.exe (PID: 10236)
- powershell.exe (PID: 6436)
- wscript.exe (PID: 9188)
- powershell.exe (PID: 7632)
- wscript.exe (PID: 7920)
- wscript.exe (PID: 8608)
- powershell.exe (PID: 5416)
- powershell.exe (PID: 4724)
The process executes VB scripts
- powershell.exe (PID: 7204)
- powershell.exe (PID: 4268)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7752)
- wscript.exe (PID: 7640)
- wscript.exe (PID: 1348)
- wscript.exe (PID: 2432)
- wscript.exe (PID: 10236)
- wscript.exe (PID: 9188)
- wscript.exe (PID: 7920)
- wscript.exe (PID: 8608)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7752)
- wscript.exe (PID: 7640)
- wscript.exe (PID: 1348)
- wscript.exe (PID: 2432)
- wscript.exe (PID: 10236)
- wscript.exe (PID: 9188)
- wscript.exe (PID: 7920)
- wscript.exe (PID: 8608)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 2040)
- DismHost.exe (PID: 8928)
The process creates files with name similar to system file names
- Dism.exe (PID: 2852)
- Dism.exe (PID: 8232)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 7808)
- powershell.exe (PID: 7868)
- powershell.exe (PID: 8436)
- powershell.exe (PID: 8428)
- powershell.exe (PID: 6436)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 4724)
- powershell.exe (PID: 5416)
Executes as Windows Service
- VSSVC.exe (PID: 8120)
Connects to unusual port
- aspnet_compiler.exe (PID: 6652)
- aspnet_compiler.exe (PID: 8872)
Contacting a server suspected of hosting an CnC
- aspnet_compiler.exe (PID: 6652)
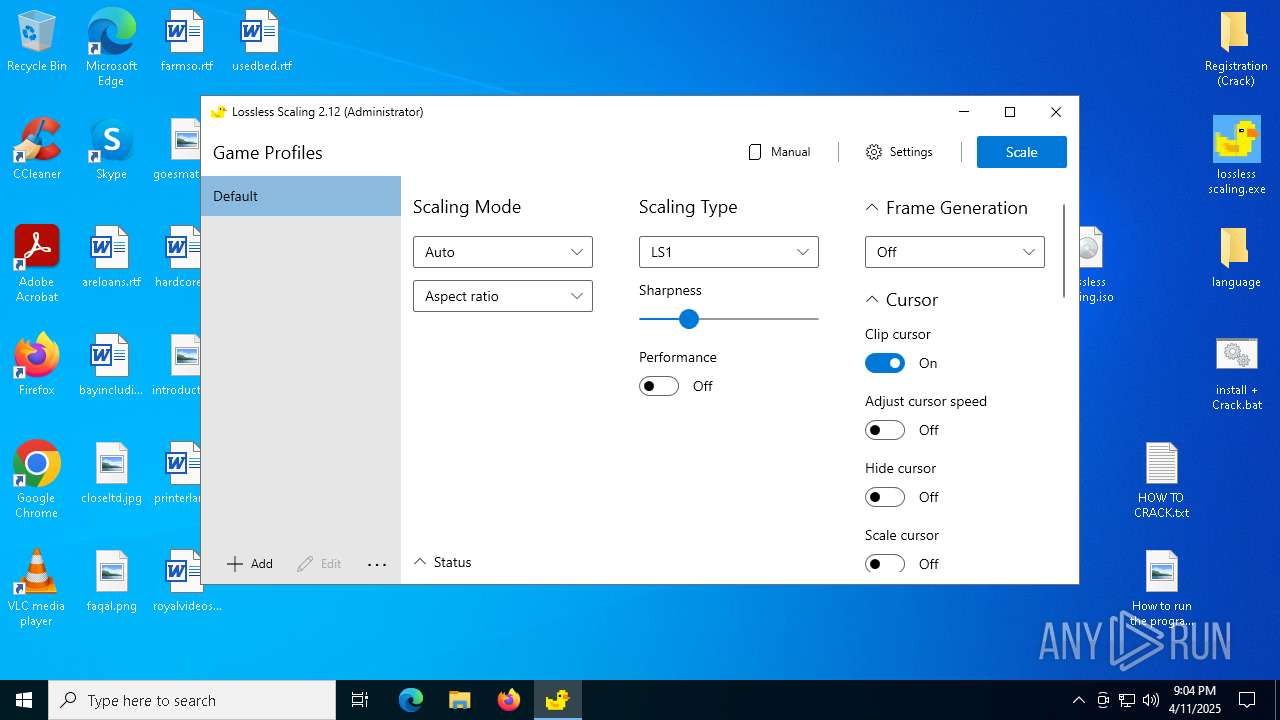
Executes application which crashes
- LosslessScaling.exe (PID: 7844)
There is functionality for taking screenshot (YARA)
- LosslessScaling.exe (PID: 5960)
The process executes via Task Scheduler
- wscript.exe (PID: 10236)
- wscript.exe (PID: 9188)
- wscript.exe (PID: 8608)
- wscript.exe (PID: 7920)
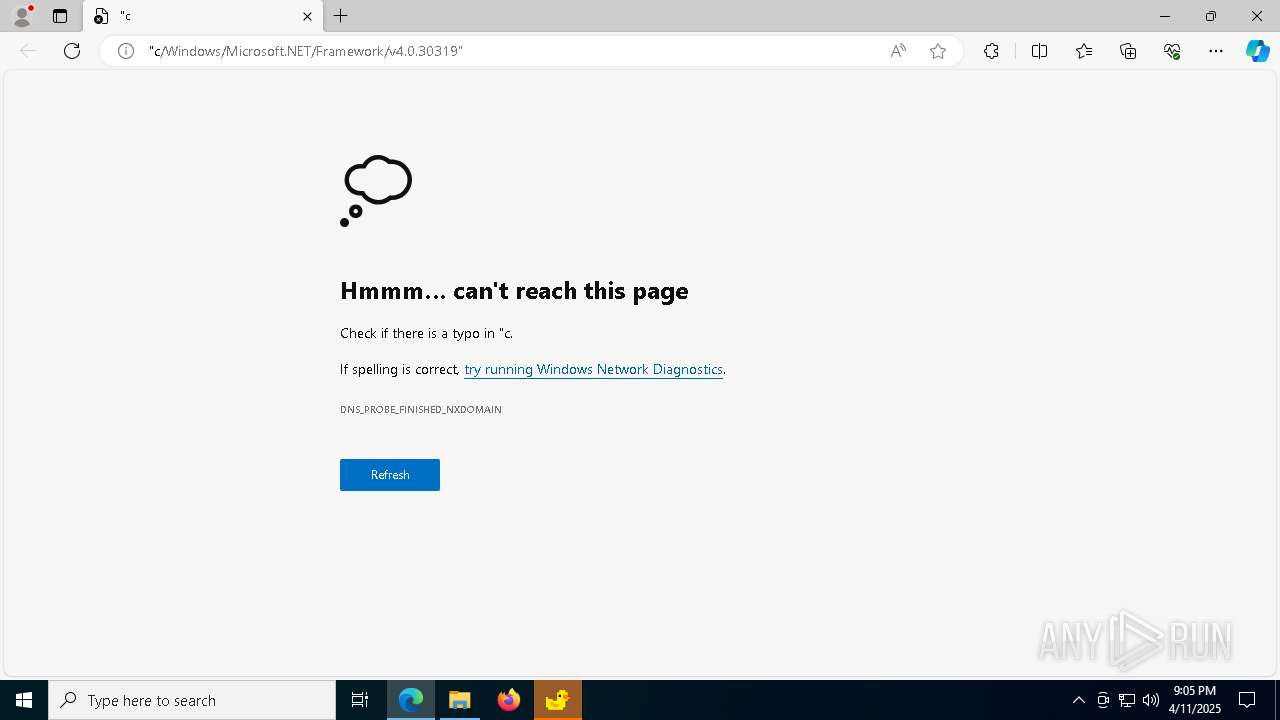
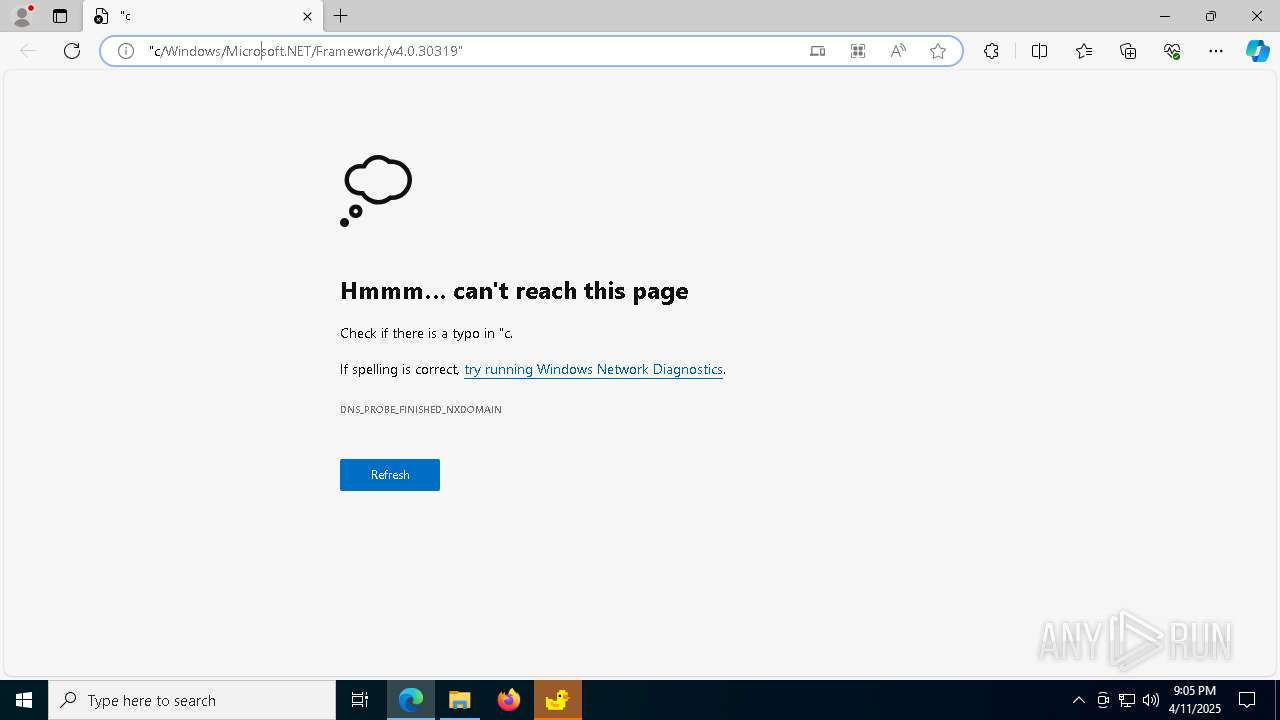
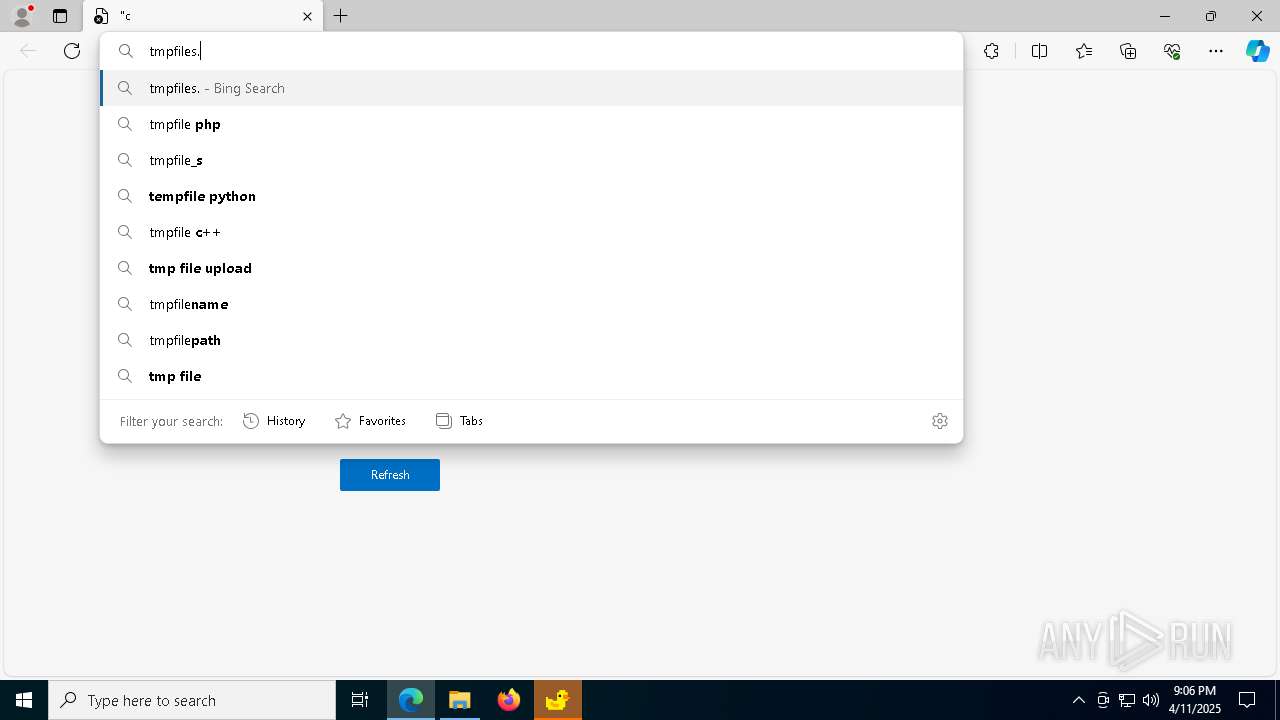
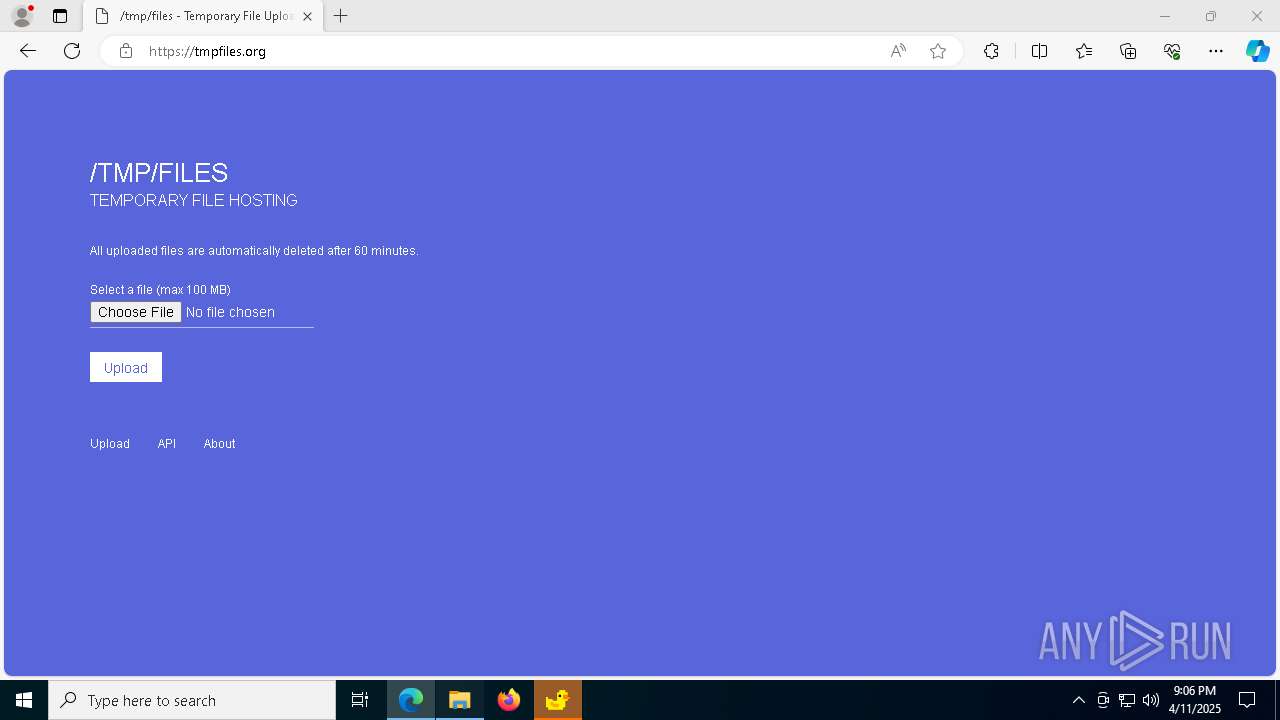
Possible Social Engineering Attempted
- msedge.exe (PID: 840)
Searches for installed software
- TiWorker.exe (PID: 8044)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 7932)
- powershell.exe (PID: 7204)
- Dism.exe (PID: 2852)
- Dism.exe (PID: 8232)
- msedge.exe (PID: 4276)
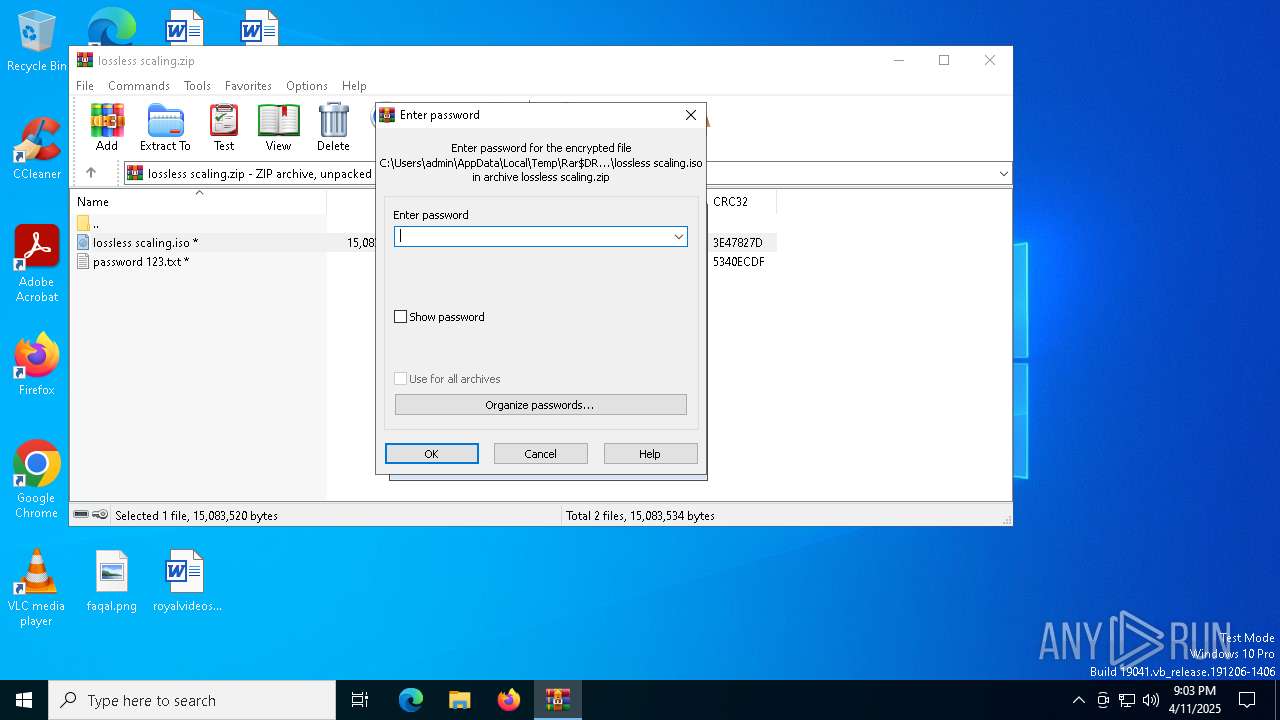
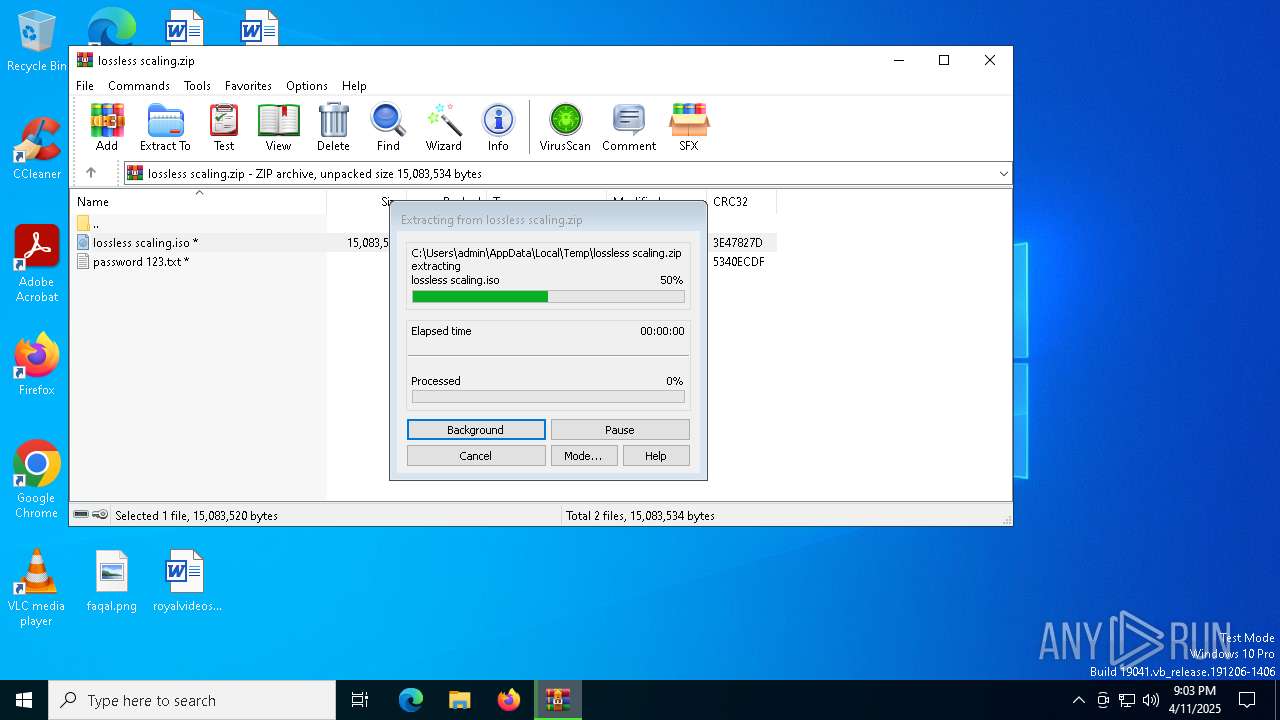
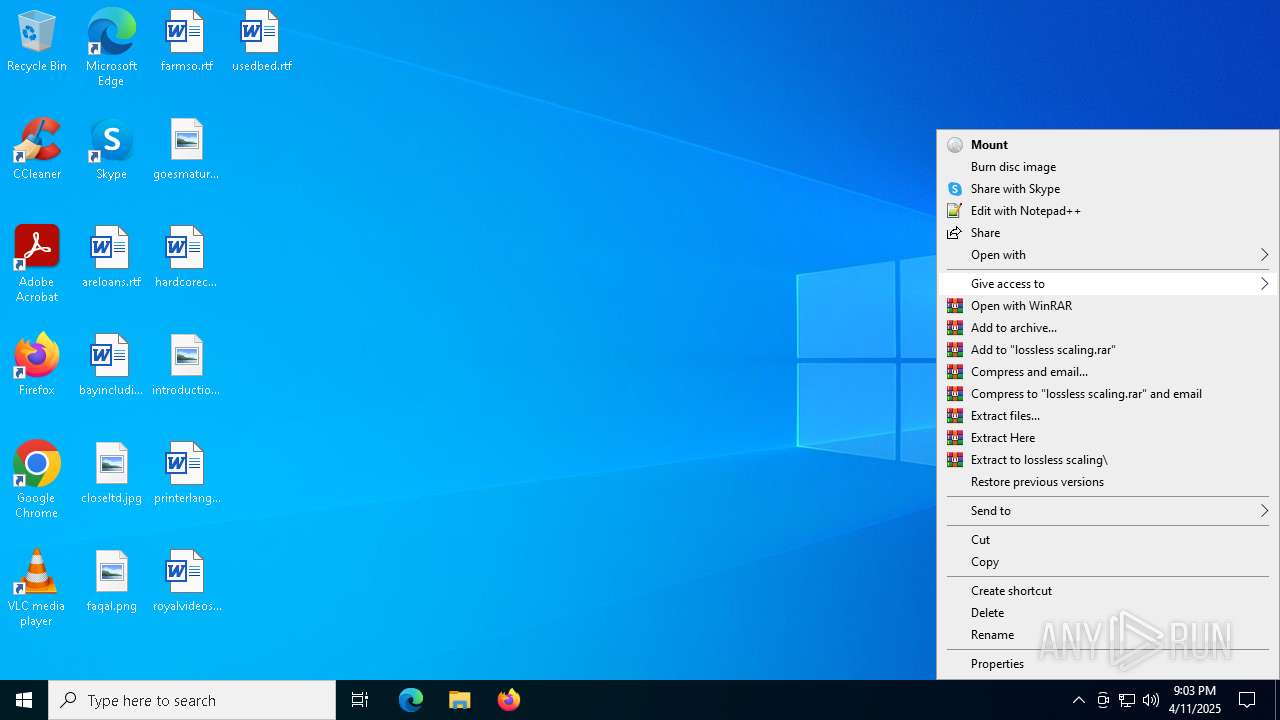
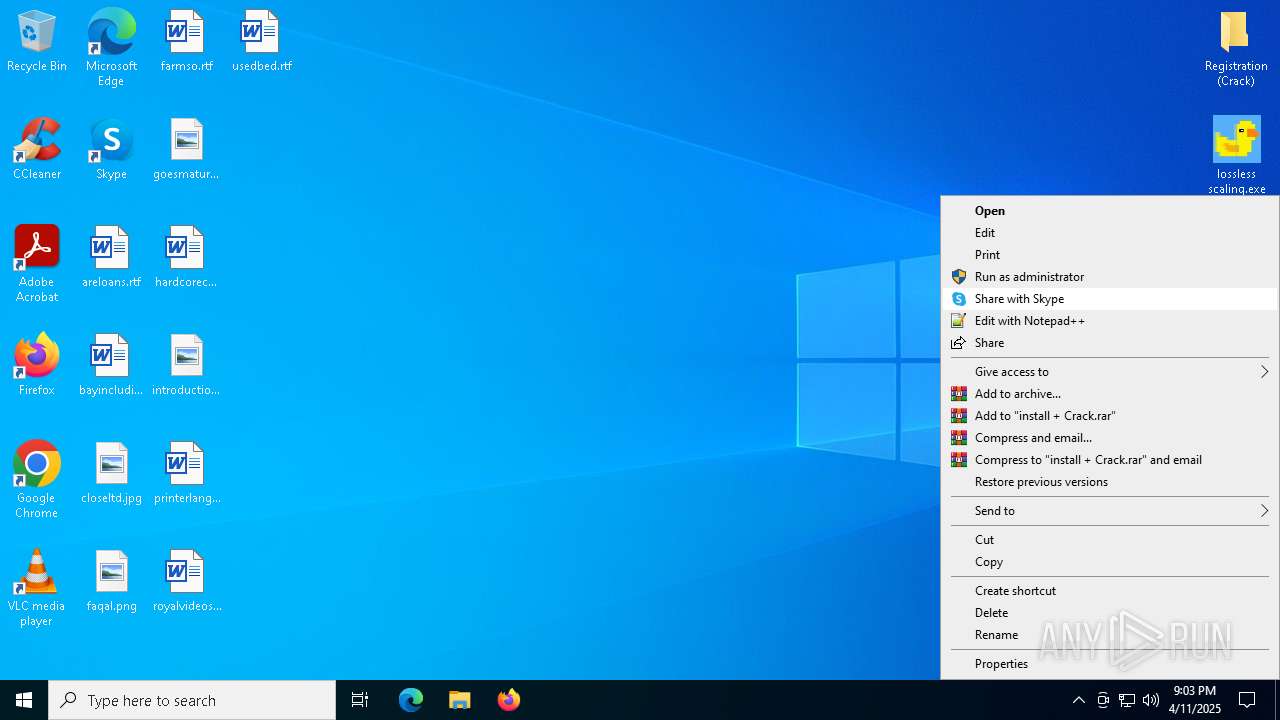
Manual execution by a user
- cmd.exe (PID: 8052)
- WinRAR.exe (PID: 7932)
- cmd.exe (PID: 7464)
- msedge.exe (PID: 4628)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7932)
- msedge.exe (PID: 4276)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7808)
- powershell.exe (PID: 7868)
- powershell.exe (PID: 4268)
- powershell.exe (PID: 8428)
- powershell.exe (PID: 8436)
- powershell.exe (PID: 6436)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 4724)
- powershell.exe (PID: 5416)
Creates files in the program directory
- powershell.exe (PID: 7204)
Reads the computer name
- LosslessScaling.exe (PID: 5960)
- DismHost.exe (PID: 2040)
- aspnet_compiler.exe (PID: 6652)
- aspnet_compiler.exe (PID: 6028)
- LosslessScaling.exe (PID: 7844)
- DismHost.exe (PID: 8928)
- identity_helper.exe (PID: 6136)
- aspnet_compiler.exe (PID: 9164)
- aspnet_compiler.exe (PID: 8872)
- aspnet_compiler.exe (PID: 8904)
- aspnet_compiler.exe (PID: 10156)
- aspnet_compiler.exe (PID: 9496)
- aspnet_compiler.exe (PID: 8348)
Checks supported languages
- LosslessScaling.exe (PID: 5960)
- RAR.exe (PID: 5332)
- DismHost.exe (PID: 2040)
- aspnet_compiler.exe (PID: 6652)
- aspnet_compiler.exe (PID: 6028)
- LosslessScaling.exe (PID: 7844)
- RAR.exe (PID: 7636)
- DismHost.exe (PID: 8928)
- identity_helper.exe (PID: 6136)
- aspnet_compiler.exe (PID: 9164)
- aspnet_compiler.exe (PID: 8872)
- aspnet_compiler.exe (PID: 8904)
- aspnet_compiler.exe (PID: 10156)
- aspnet_compiler.exe (PID: 9496)
- aspnet_compiler.exe (PID: 8348)
Reads the machine GUID from the registry
- LosslessScaling.exe (PID: 5960)
- RAR.exe (PID: 5332)
- aspnet_compiler.exe (PID: 6652)
- aspnet_compiler.exe (PID: 6028)
- LosslessScaling.exe (PID: 7844)
- RAR.exe (PID: 7636)
- aspnet_compiler.exe (PID: 8872)
- aspnet_compiler.exe (PID: 9164)
- aspnet_compiler.exe (PID: 8904)
- aspnet_compiler.exe (PID: 10156)
- aspnet_compiler.exe (PID: 9496)
- aspnet_compiler.exe (PID: 8348)
LOSSLESSSCALING mutex has been found
- LosslessScaling.exe (PID: 5960)
- LosslessScaling.exe (PID: 7844)
Creates files or folders in the user directory
- LosslessScaling.exe (PID: 5960)
- WerFault.exe (PID: 6036)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7808)
- powershell.exe (PID: 7868)
- powershell.exe (PID: 4268)
- powershell.exe (PID: 8428)
- powershell.exe (PID: 8436)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 6436)
- powershell.exe (PID: 4724)
- powershell.exe (PID: 5416)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 4268)
Create files in a temporary directory
- Dism.exe (PID: 2852)
- aspnet_compiler.exe (PID: 6652)
- Dism.exe (PID: 8232)
Reads Environment values
- DismHost.exe (PID: 2040)
- DismHost.exe (PID: 8928)
- identity_helper.exe (PID: 6136)
Reads the software policy settings
- aspnet_compiler.exe (PID: 6652)
- slui.exe (PID: 7504)
- TiWorker.exe (PID: 8044)
- slui.exe (PID: 6068)
Manages system restore points
- SrTasks.exe (PID: 4692)
- SrTasks.exe (PID: 8684)
Application launched itself
- msedge.exe (PID: 4628)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 9964)
Checks proxy server information
- slui.exe (PID: 6068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:10 06:21:54 |
| ZipCRC: | 0x3e47827d |
| ZipCompressedSize: | 5740109 |
| ZipUncompressedSize: | 15083520 |
| ZipFileName: | lossless scaling.iso |
Total processes
310
Monitored processes
162
Malicious processes
20
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 840 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2520 --field-trial-handle=2448,i,15682372079534130007,3237120140411748556,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7980 --field-trial-handle=2448,i,15682372079534130007,3237120140411748556,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7964 --field-trial-handle=2448,i,15682372079534130007,3237120140411748556,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1272 | "C:\WINDOWS\system32\reg.exe" ADD HKCU\SOFTWARE\Valve\Steam\Apps\993090 /v Installed /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\Public\IObitUnlocker\Backup.vbs" | C:\Windows\System32\wscript.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1616 | "C:\WINDOWS\system32\schtasks.exe" /query /tn administrator | C:\Windows\System32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | C:\Users\admin\AppData\Local\Temp\A37D1053-346C-4BF8-8D23-D7CF35EAFC3B\dismhost.exe {8D570661-D755-489F-8BA3-D90910319049} | C:\Users\admin\AppData\Local\Temp\A37D1053-346C-4BF8-8D23-D7CF35EAFC3B\DismHost.exe | — | Dism.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4256 --field-trial-handle=2448,i,15682372079534130007,3237120140411748556,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2444 --field-trial-handle=2448,i,15682372079534130007,3237120140411748556,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2104 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3456 --field-trial-handle=2448,i,15682372079534130007,3237120140411748556,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
156 407
Read events
155 531
Write events
683
Delete events
193
Modification events
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\lossless scaling.zip | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
205
Suspicious files
2 308
Text files
1 805
Unknown types
6
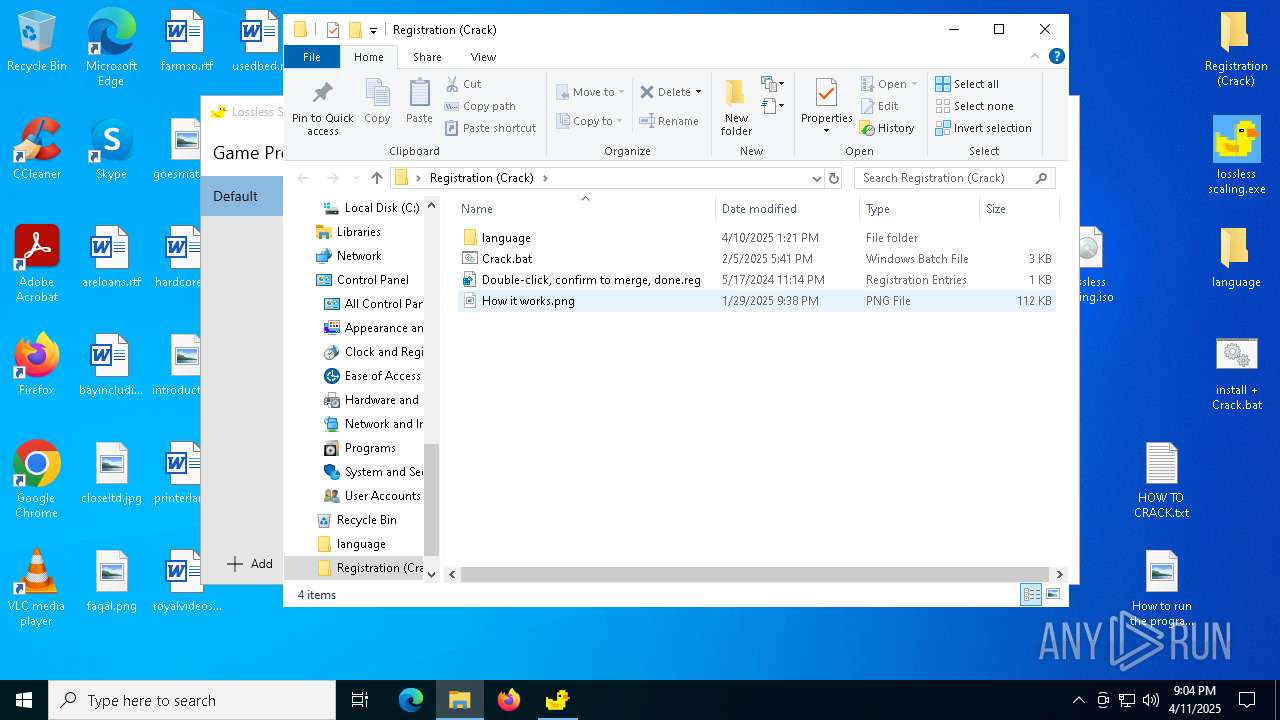
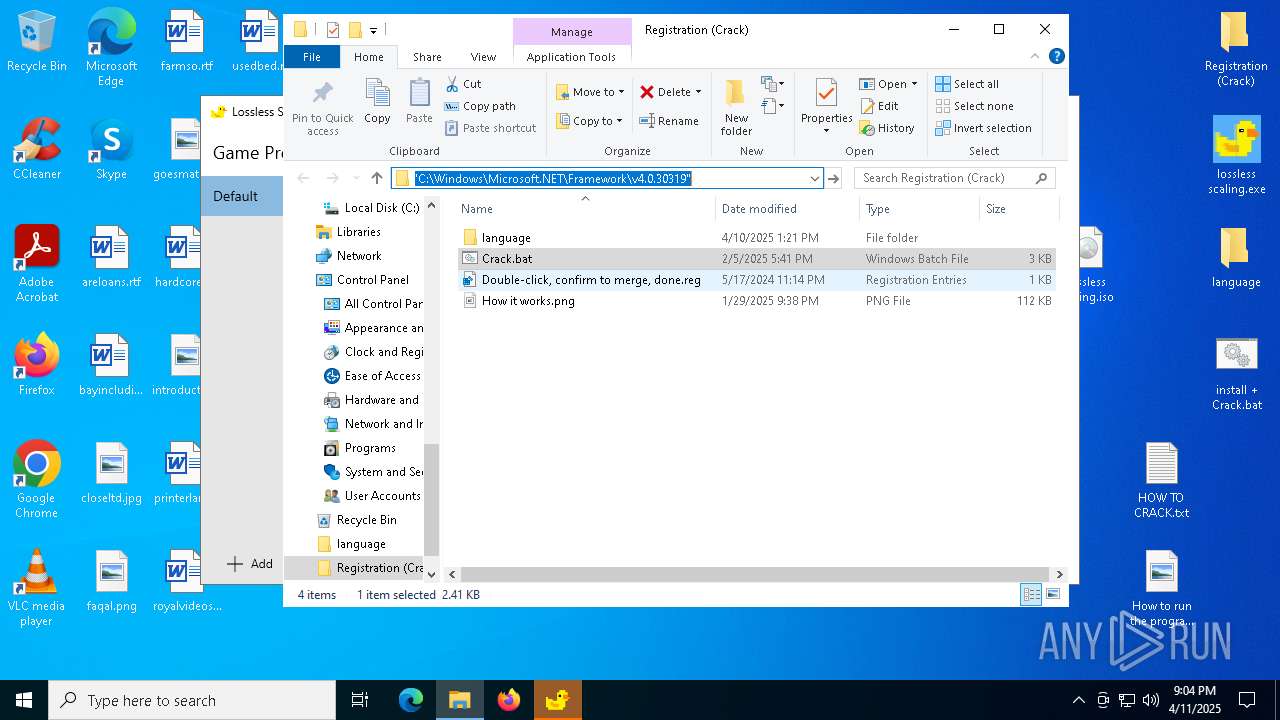
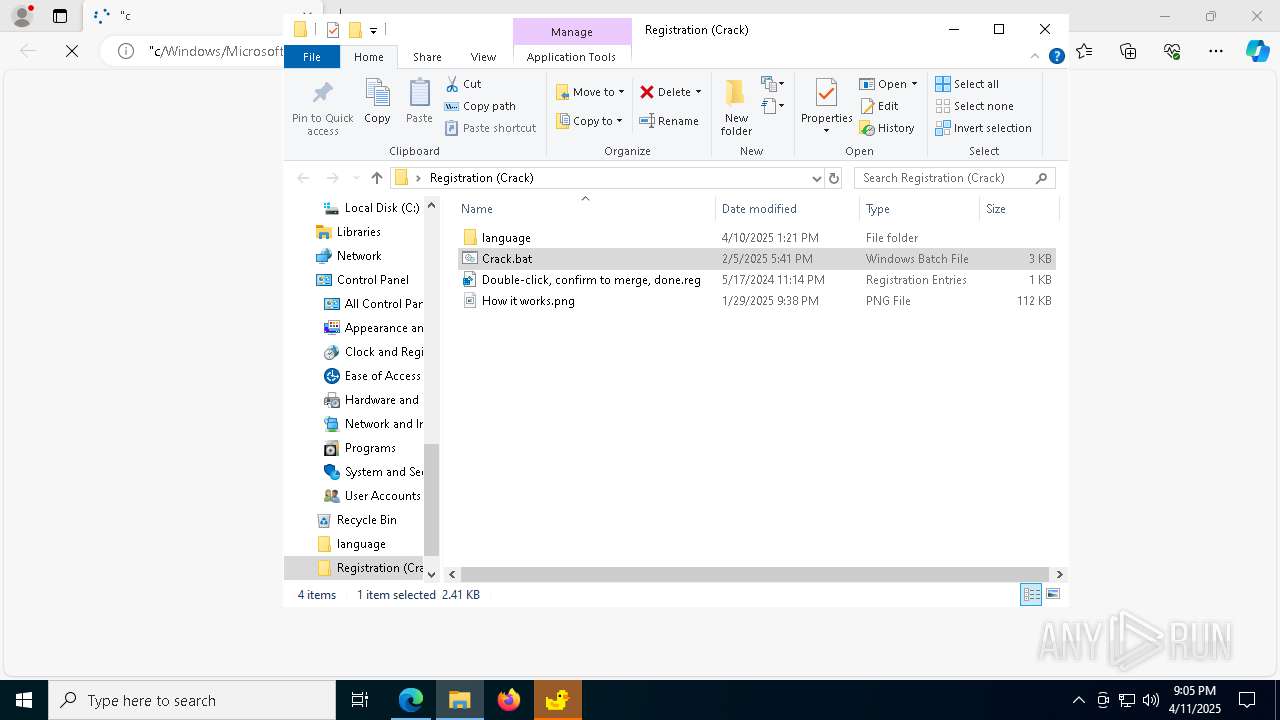
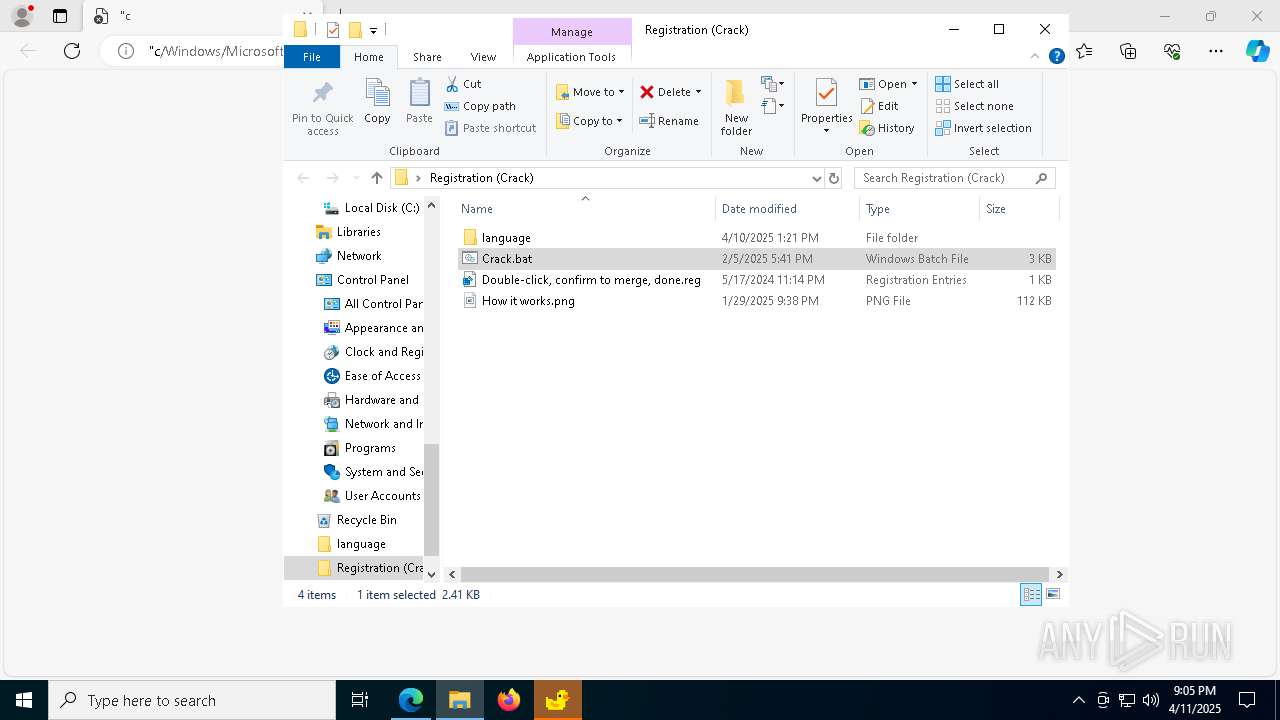
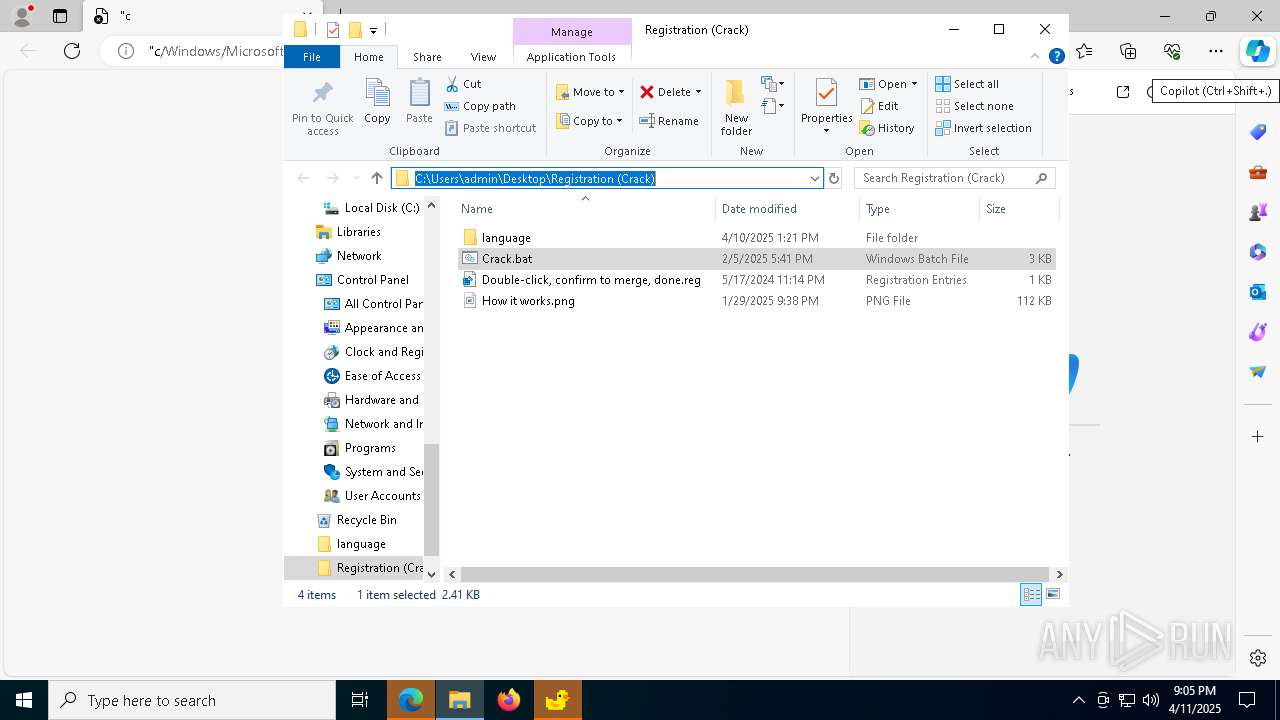
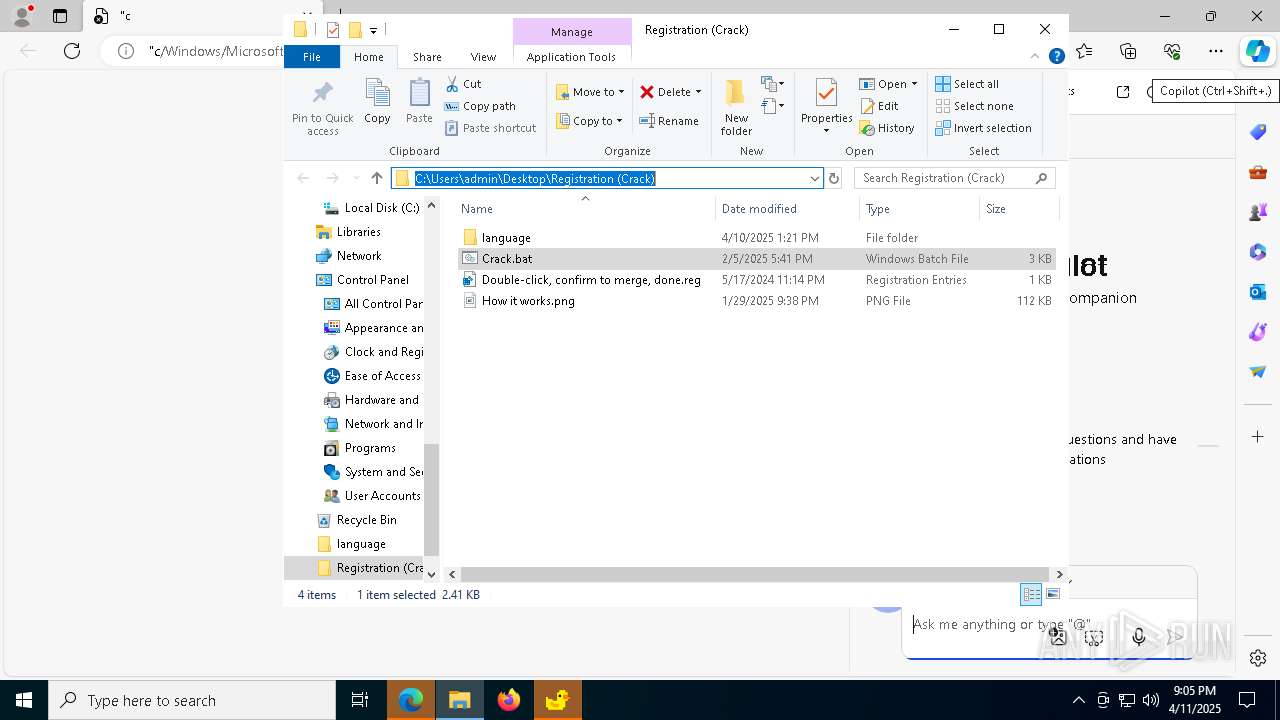
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7324.23205\lossless scaling.iso | — | |
MD5:— | SHA256:— | |||
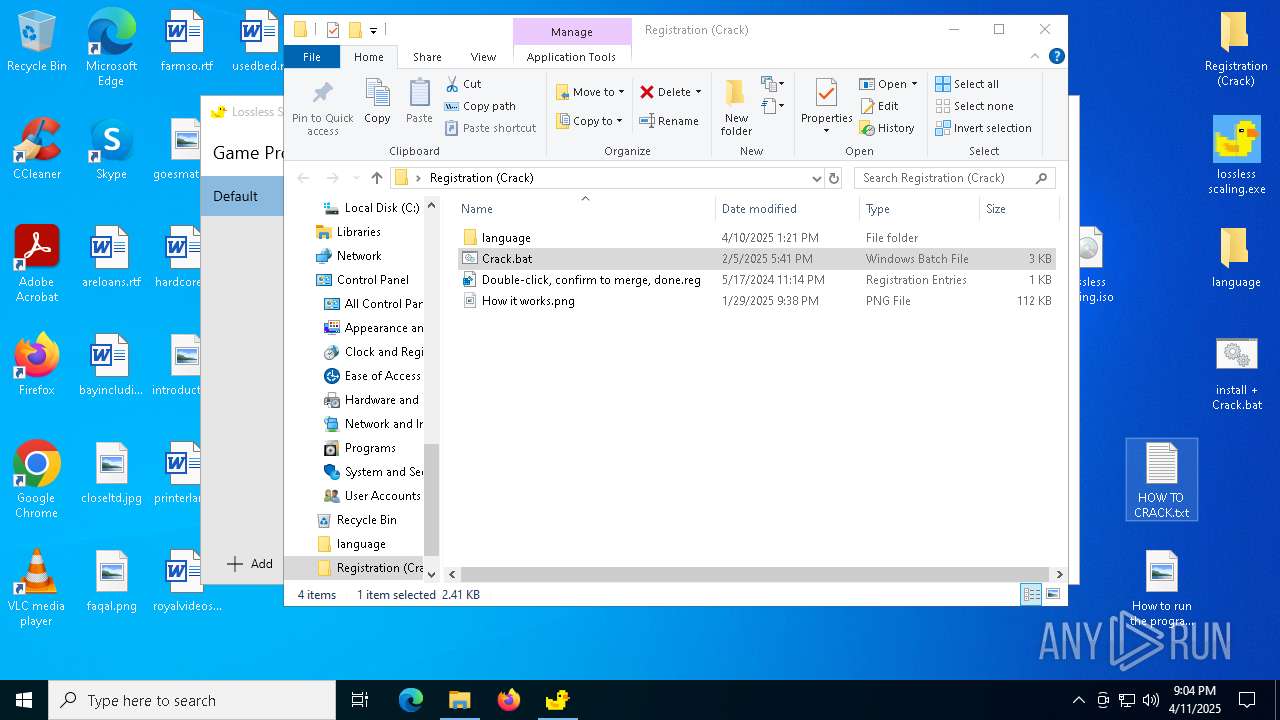
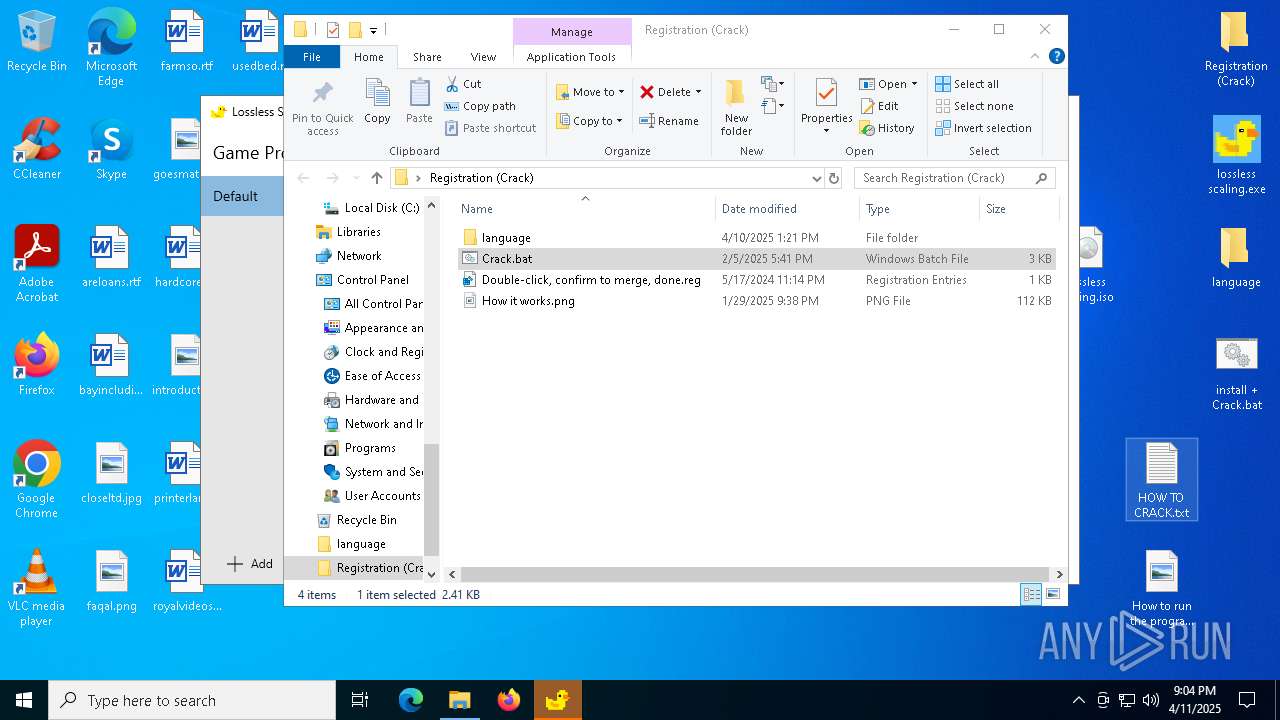
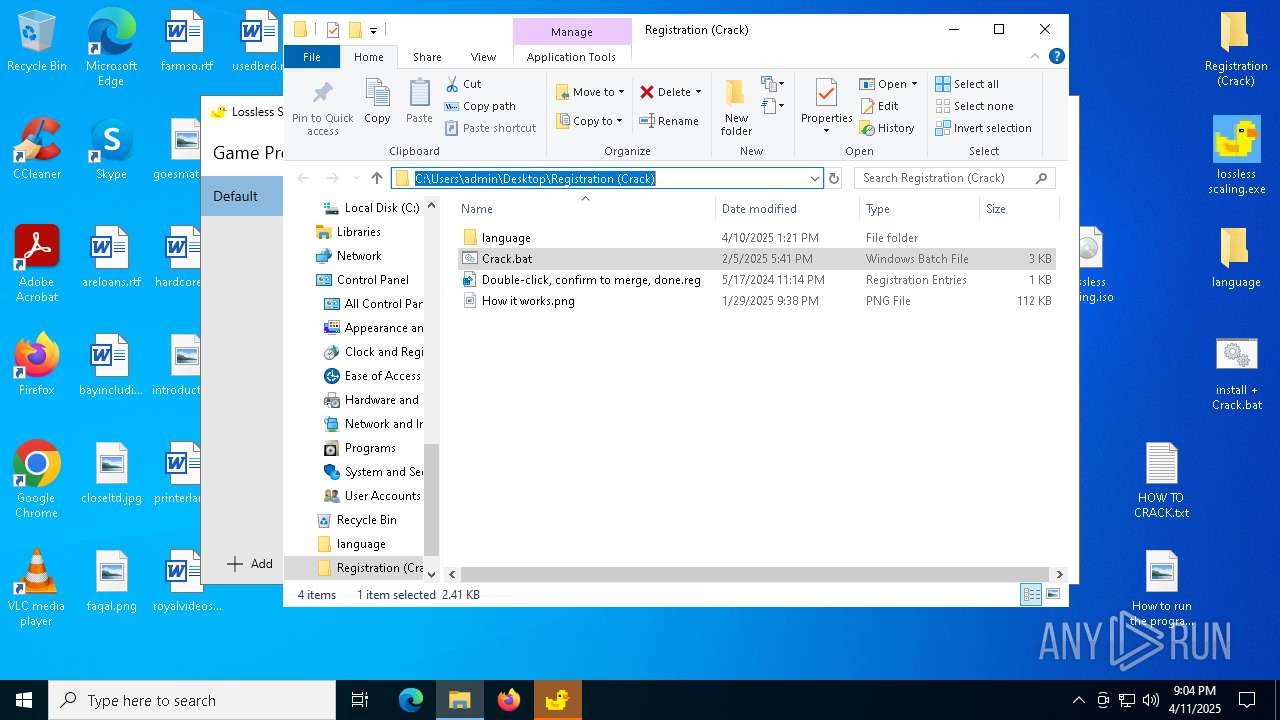
| 7932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7932.23947\install + Crack.bat | text | |
MD5:E90E30E3C6697D870286C1A6831A135B | SHA256:B08AAA0B0319C50F5614419752F4C45FA30B5E48137018E009672791447F4E6F | |||
| 7932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7932.23947\HOW TO CRACK.txt | text | |
MD5:9C4AB595A2ECB89DBC666EDD4F8565AC | SHA256:23F61C16E154600AF239FD1A37522D10D09E1119A59AABF5DDD838AAE3D4E781 | |||
| 7932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7932.23947\How to run the program.png | image | |
MD5:5C932F935AE20FE79D779A8F03D58A09 | SHA256:7CF3B5FE89C1DB2732AF19730AB1A1E91C9FBA9A1117E268578D4DC604152807 | |||
| 7932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7932.23947\Registration (Crack)\How it works.png | image | |
MD5:5C932F935AE20FE79D779A8F03D58A09 | SHA256:7CF3B5FE89C1DB2732AF19730AB1A1E91C9FBA9A1117E268578D4DC604152807 | |||
| 7932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7932.23947\language\diagerr.xml | csv | |
MD5:44317C4008BFB84314D098A68944A0D6 | SHA256:DD43C2C0A8F53036AA4B346DE52DA6C0254C4747D129FE4130ECE4E078BB0A10 | |||
| 7932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7932.23947\Registration (Crack)\Crack.bat | text | |
MD5:E90E30E3C6697D870286C1A6831A135B | SHA256:B08AAA0B0319C50F5614419752F4C45FA30B5E48137018E009672791447F4E6F | |||
| 7932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7932.23947\Registration (Crack)\Double-click, confirm to merge, done.reg | text | |
MD5:FF047B633DFA3AF4E5B5C78C1C84515B | SHA256:963E9DE4561957E19EB200C7446AABA4E59392040EAA5006717BF826A589CC21 | |||
| 7932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7932.23947\Registration (Crack)\language\diagerr.xml | csv | |
MD5:44317C4008BFB84314D098A68944A0D6 | SHA256:DD43C2C0A8F53036AA4B346DE52DA6C0254C4747D129FE4130ECE4E078BB0A10 | |||
| 7932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7932.23947\language\en-US\Devn.exe | executable | |
MD5:857F8A07B6C9AD9BD3BB6E4C047FEE45 | SHA256:7083023D5BA4768A6398A92DFC6F8A7556EFBEAFB6A4D60347AEA0F69B2E89AF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
227
DNS requests
111
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1660 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1660 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3804 | svchost.exe | HEAD | 200 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744950980&P2=404&P3=2&P4=Xleizx9VJB3Q8HkwzPrnBoNwpiSjr2Mq%2fT0%2bAfMVadWxAbcX0pi%2fbnvESP%2fHmwleZGA2gGuUfL9u3pB3gAy3kA%3d%3d | unknown | — | — | whitelisted |
3804 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744950980&P2=404&P3=2&P4=Xleizx9VJB3Q8HkwzPrnBoNwpiSjr2Mq%2fT0%2bAfMVadWxAbcX0pi%2fbnvESP%2fHmwleZGA2gGuUfL9u3pB3gAy3kA%3d%3d | unknown | — | — | whitelisted |
3804 | svchost.exe | HEAD | 200 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744950980&P2=404&P3=2&P4=WRCOteBcbwZ%2fE2BE9tYzMSoecaLSHcLT%2fRqPdGbQogRepawUXe7jayQkyaP%2flmOHmysZeDlErKyMKFv8QzACew%3d%3d | unknown | — | — | whitelisted |
3804 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744950980&P2=404&P3=2&P4=Xleizx9VJB3Q8HkwzPrnBoNwpiSjr2Mq%2fT0%2bAfMVadWxAbcX0pi%2fbnvESP%2fHmwleZGA2gGuUfL9u3pB3gAy3kA%3d%3d | unknown | — | — | whitelisted |
3804 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1744950980&P2=404&P3=2&P4=WRCOteBcbwZ%2fE2BE9tYzMSoecaLSHcLT%2fRqPdGbQogRepawUXe7jayQkyaP%2flmOHmysZeDlErKyMKFv8QzACew%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.5:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
almhm231.ddnsgeek.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.ddnsgeek .com Domain |
6652 | aspnet_compiler.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
6652 | aspnet_compiler.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
6652 | aspnet_compiler.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
6652 | aspnet_compiler.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.loseyourip .com Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.kozow .com Domain |
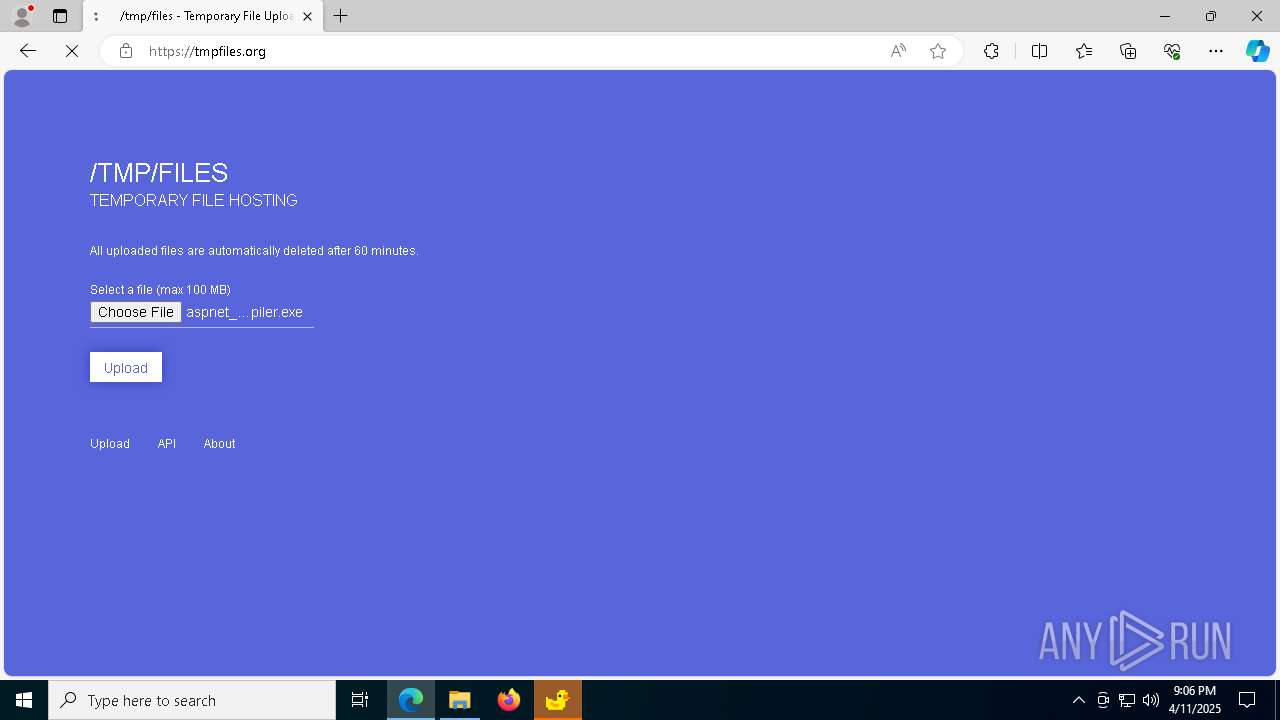
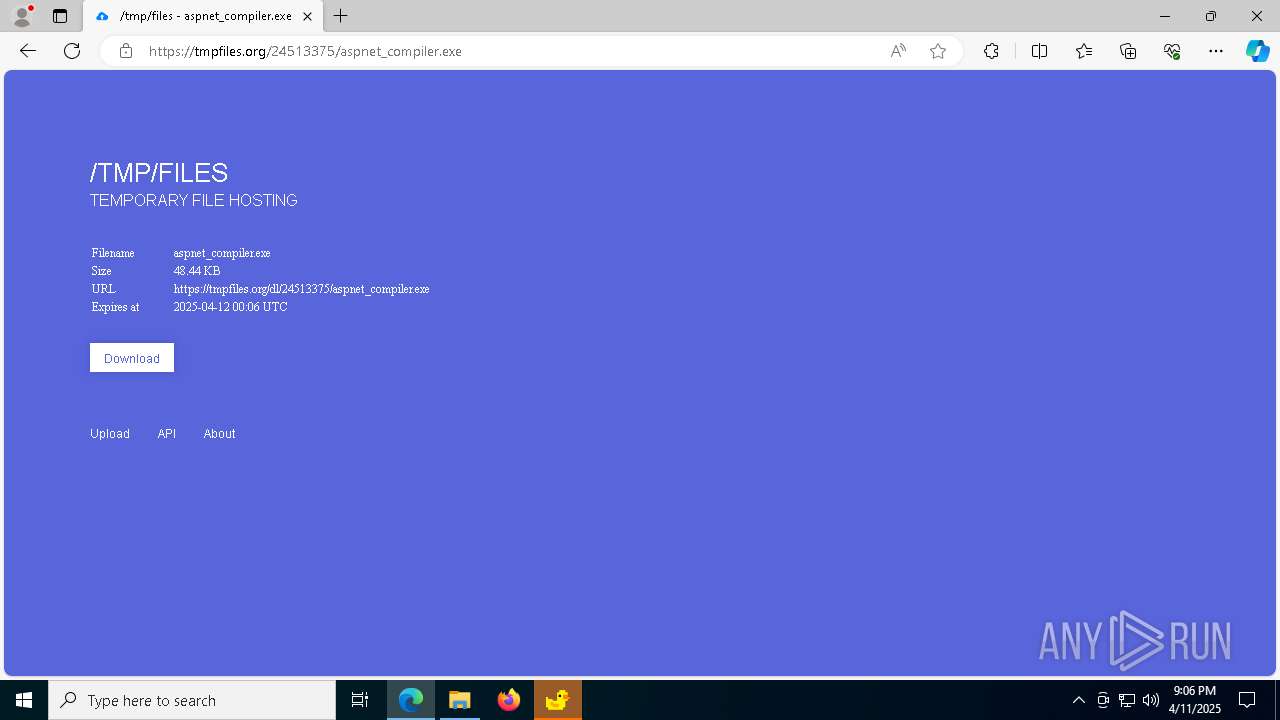
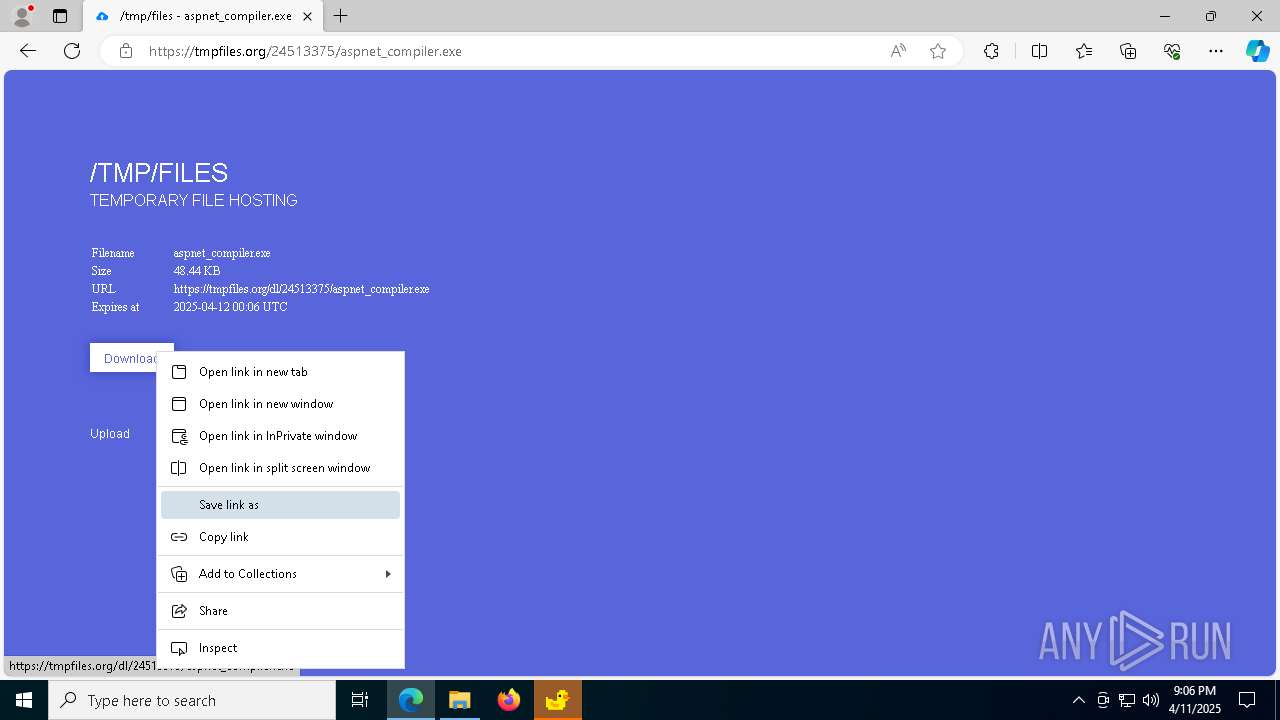
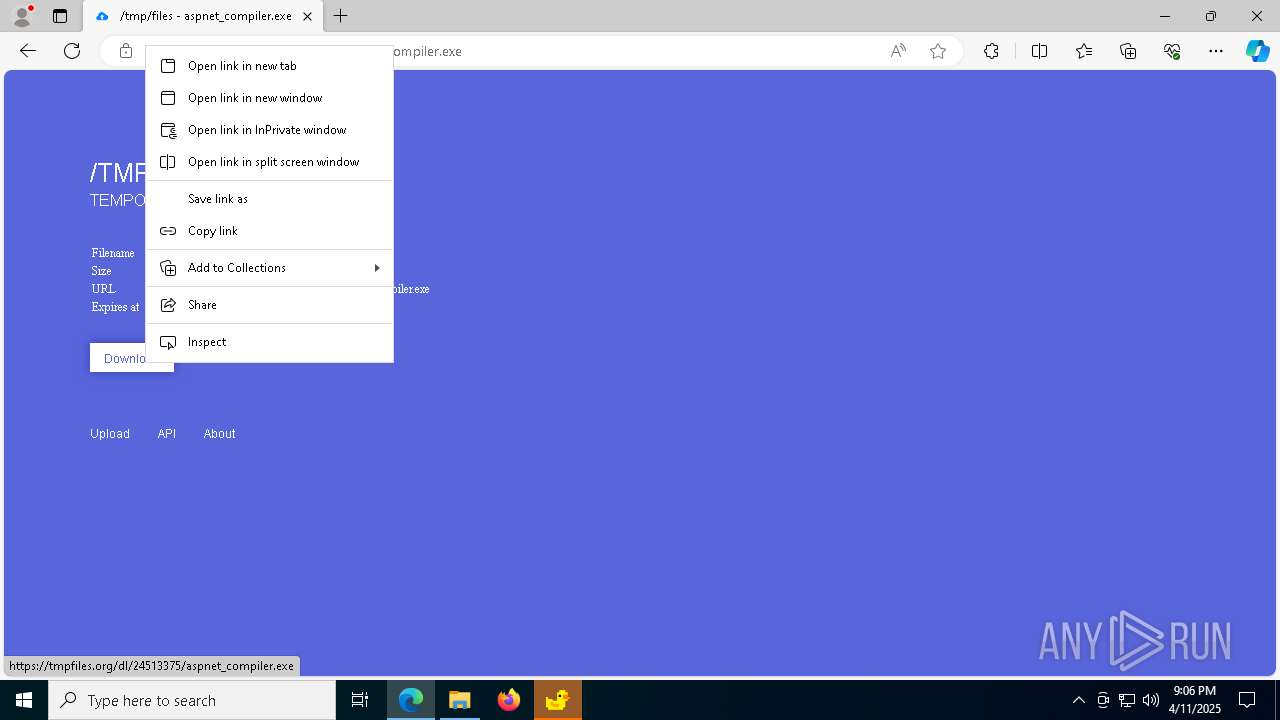
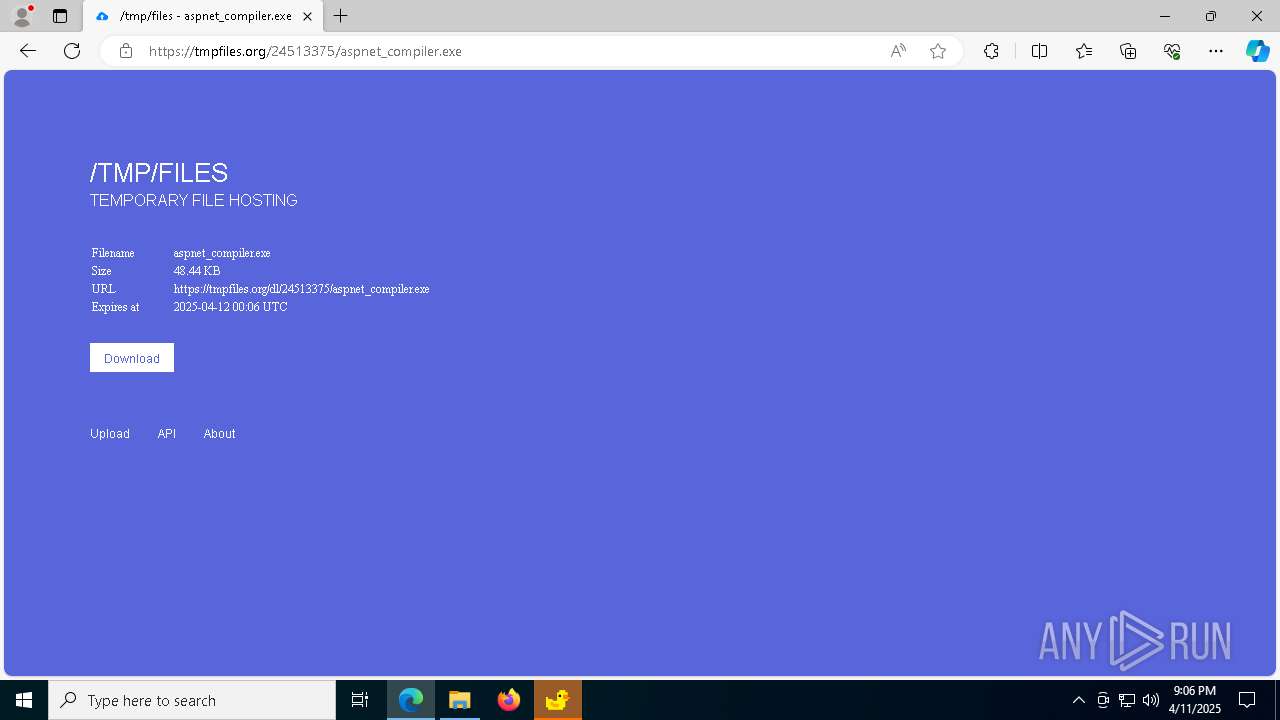
840 | msedge.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Domain Marked as Malicious (tmpfiles .org) |
840 | msedge.exe | Misc activity | ET INFO Temporary File Hosting Domain in DNS Lookup (tmpfiles .org) |
840 | msedge.exe | Misc activity | ET INFO Temporary File Hosting Domain in DNS Lookup (tmpfiles .org) |