| File name: | file.exe |
| Full analysis: | https://app.any.run/tasks/ec45f8d1-9b47-4b8a-9659-b1a000aeeae5 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | December 12, 2023, 17:43:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | DB9836AFC44B9A8FD086ABD3E882524E |
| SHA1: | F2DC67624413C9CDA2A154838066FD8FEF846EAC |
| SHA256: | BE07B7C16E488AD2E0FDF1348F2D0915CDC50337B32711B7FCD8A42413AD8A29 |
| SSDEEP: | 98304:uri81mkVr1XCzT7g5M+w7gi2JHC3g/ermojHmOJFDarUUIJC6wYSvGr1o1QxxTdW:i+kCV6kK |
MALICIOUS
LUMMA has been detected (SURICATA)
- RegSvcs.exe (PID: 1960)
Connects to the CnC server
- RegSvcs.exe (PID: 1960)
Drops the executable file immediately after the start
- file.exe (PID: 2736)
- RegSvcs.exe (PID: 1960)
- vonaxbfhlql.exe (PID: 2788)
- hvilvxbjxmhjap.exe (PID: 2092)
- Utsysc.exe (PID: 2952)
LUMMA has been detected (YARA)
- file.exe (PID: 2736)
- RegSvcs.exe (PID: 1960)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 1960)
- rundll32.exe (PID: 988)
Changes the autorun value in the registry
- Utsysc.exe (PID: 2952)
Uses Task Scheduler to run other applications
- Utsysc.exe (PID: 2952)
- XRJNZC.exe (PID: 2664)
AMADEY has been detected (SURICATA)
- Utsysc.exe (PID: 2952)
Steals credentials from Web Browsers
- rundll32.exe (PID: 988)
Unusual connection from system programs
- rundll32.exe (PID: 2396)
- rundll32.exe (PID: 988)
SUSPICIOUS
Reads browser cookies
- RegSvcs.exe (PID: 1960)
Connects to the server without a host name
- RegSvcs.exe (PID: 1960)
- Utsysc.exe (PID: 2952)
- rundll32.exe (PID: 988)
- rundll32.exe (PID: 2396)
Process requests binary or script from the Internet
- RegSvcs.exe (PID: 1960)
- Utsysc.exe (PID: 2952)
Reads the Internet Settings
- vonaxbfhlql.exe (PID: 2788)
- hvilvxbjxmhjap.exe (PID: 2092)
- Utsysc.exe (PID: 2952)
- XRJNZC.exe (PID: 2664)
- rundll32.exe (PID: 988)
- rundll32.exe (PID: 2396)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2652)
Executing commands from a ".bat" file
- hvilvxbjxmhjap.exe (PID: 2092)
Starts CMD.EXE for commands execution
- hvilvxbjxmhjap.exe (PID: 2092)
Reads the BIOS version
- vonaxbfhlql.exe (PID: 2788)
- hvilvxbjxmhjap.exe (PID: 2092)
- Utsysc.exe (PID: 2952)
- XRJNZC.exe (PID: 2664)
- Utsysc.exe (PID: 3012)
- Utsysc.exe (PID: 2100)
- XRJNZC.exe (PID: 1092)
- XRJNZC.exe (PID: 2432)
Searches for installed software
- RegSvcs.exe (PID: 1960)
Starts itself from another location
- vonaxbfhlql.exe (PID: 2788)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 2500)
Uses NETSH.EXE to obtain data on the network
- rundll32.exe (PID: 988)
The process executes via Task Scheduler
- Utsysc.exe (PID: 3012)
- XRJNZC.exe (PID: 2432)
- XRJNZC.exe (PID: 1092)
- Utsysc.exe (PID: 2100)
Loads DLL from Mozilla Firefox
- rundll32.exe (PID: 988)
Accesses Microsoft Outlook profiles
- rundll32.exe (PID: 988)
INFO
Reads the machine GUID from the registry
- file.exe (PID: 2736)
- vonaxbfhlql.exe (PID: 2788)
- Utsysc.exe (PID: 2952)
Reads the computer name
- file.exe (PID: 2736)
- RegSvcs.exe (PID: 1960)
- nfolrqdqlatcxa.exe (PID: 3020)
- hvilvxbjxmhjap.exe (PID: 2092)
- vonaxbfhlql.exe (PID: 2788)
- Utsysc.exe (PID: 2952)
- XRJNZC.exe (PID: 2664)
Checks supported languages
- file.exe (PID: 2736)
- RegSvcs.exe (PID: 1960)
- hvilvxbjxmhjap.exe (PID: 2092)
- nfolrqdqlatcxa.exe (PID: 3020)
- vonaxbfhlql.exe (PID: 2788)
- Utsysc.exe (PID: 2952)
- XRJNZC.exe (PID: 2664)
- XRJNZC.exe (PID: 2432)
- Utsysc.exe (PID: 3012)
- XRJNZC.exe (PID: 1092)
- Utsysc.exe (PID: 2100)
Create files in a temporary directory
- file.exe (PID: 2736)
- RegSvcs.exe (PID: 1960)
- hvilvxbjxmhjap.exe (PID: 2092)
- vonaxbfhlql.exe (PID: 2788)
- Utsysc.exe (PID: 2952)
Creates files in the program directory
- hvilvxbjxmhjap.exe (PID: 2092)
Checks proxy server information
- Utsysc.exe (PID: 2952)
- rundll32.exe (PID: 988)
- rundll32.exe (PID: 2396)
Creates files or folders in the user directory
- Utsysc.exe (PID: 2952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2047:03:20 03:55:24+01:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 4181504 |
| InitializedDataSize: | 79360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3fedbe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.2.0.0 |
| ProductVersionNumber: | 1.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
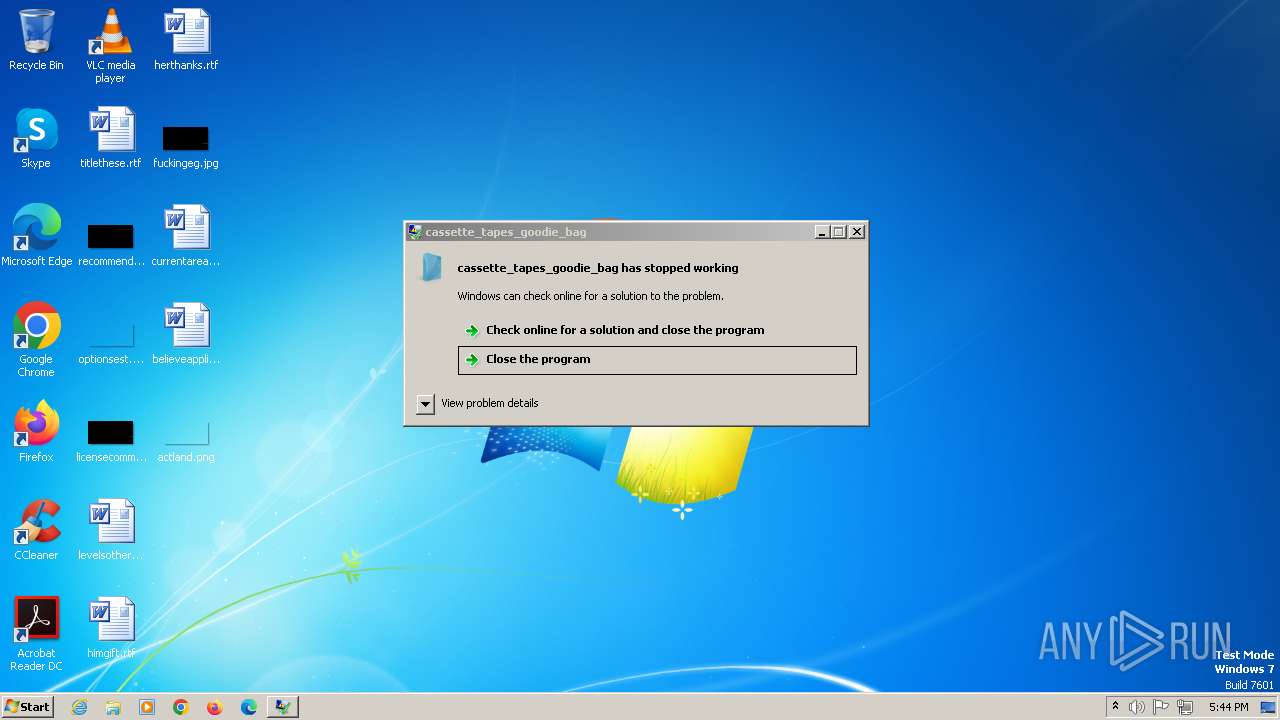
| FileDescription: | cassette_tapes_goodie_bag |
| FileVersion: | 1.2.0.0 |
| InternalName: | cassette_tapes_goodie_bag.exe |
| LegalCopyright: | Copyright © 2023 |
| LegalTrademarks: | - |
| OriginalFileName: | cassette_tapes_goodie_bag.exe |
| ProductName: | cassette_tapes_goodie_bag |
| ProductVersion: | 1.2.0.0 |
| AssemblyVersion: | 1.2.0.0 |
Total processes
59
Monitored processes
20
Malicious processes
8
Suspicious processes
6
Behavior graph
Click at the process to see the details
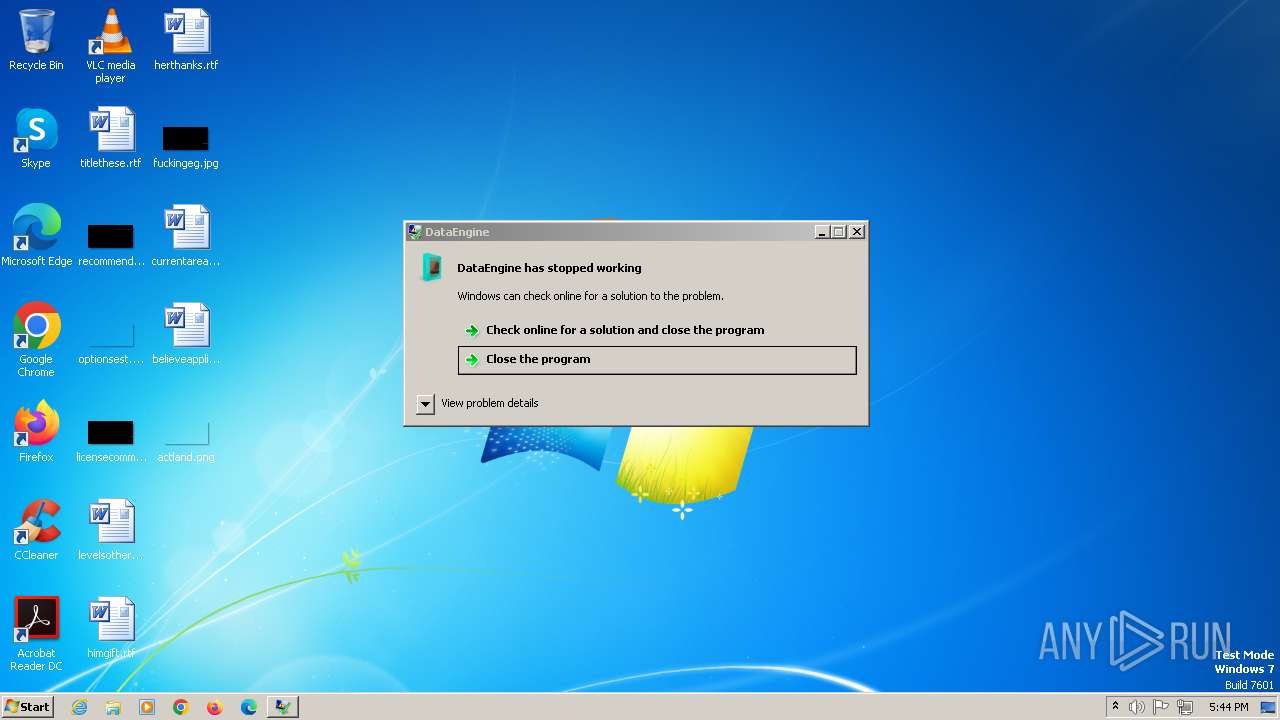
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 988 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\AppData\Roaming\80c6bf70bf3f8f\cred64.dll, Main | C:\Windows\System32\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1092 | C:\ProgramData\pinterests\XRJNZC.exe | C:\ProgramData\pinterests\XRJNZC.exe | — | taskeng.exe | |||||||||||
User: admin Company: DrayTek Corp. Integrity Level: MEDIUM Description: Smart VPN Client Exit code: 0 Version: 5.6.4 Modules
| |||||||||||||||
| 1960 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 2092 | "C:\Users\admin\AppData\Local\Temp\hvilvxbjxmhjap.exe" | C:\Users\admin\AppData\Local\Temp\hvilvxbjxmhjap.exe | — | RegSvcs.exe | |||||||||||
User: admin Company: DrayTek Corp. Integrity Level: MEDIUM Description: Smart VPN Client Exit code: 0 Version: 5.6.4 Modules
| |||||||||||||||
| 2100 | C:\Users\admin\AppData\Local\Temp\4fdb51ccdc\Utsysc.exe | C:\Users\admin\AppData\Local\Temp\4fdb51ccdc\Utsysc.exe | — | taskeng.exe | |||||||||||
User: admin Company: ZabKat Integrity Level: MEDIUM Description: xplorer² - explorer replacement Exit code: 0 Version: 2, 5, 0, 4 Modules
| |||||||||||||||
| 2396 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\AppData\Roaming\80c6bf70bf3f8f\clip64.dll, Main | C:\Windows\SysWOW64\rundll32.exe | Utsysc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2432 | C:\ProgramData\pinterests\XRJNZC.exe | C:\ProgramData\pinterests\XRJNZC.exe | — | taskeng.exe | |||||||||||
User: admin Company: DrayTek Corp. Integrity Level: MEDIUM Description: Smart VPN Client Exit code: 0 Version: 5.6.4 Modules
| |||||||||||||||
| 2500 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\AppData\Roaming\80c6bf70bf3f8f\cred64.dll, Main | C:\Windows\SysWOW64\rundll32.exe | — | Utsysc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2512 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | — | file.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 2568 | timeout 3 | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 647
Read events
3 532
Write events
115
Delete events
0
Modification events
| (PID) Process: | (2092) hvilvxbjxmhjap.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2092) hvilvxbjxmhjap.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2092) hvilvxbjxmhjap.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2092) hvilvxbjxmhjap.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2788) vonaxbfhlql.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2788) vonaxbfhlql.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2788) vonaxbfhlql.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2788) vonaxbfhlql.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2952) Utsysc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders |
| Operation: | write | Name: | Startup |
Value: %USERPROFILE%\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup | |||
| (PID) Process: | (2952) Utsysc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
10
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1960 | RegSvcs.exe | C:\Users\admin\AppData\Local\Temp\nfolrqdqlatcxa.exe | executable | |
MD5:FC8D23BC4223AD11E0A9640341D0A205 | SHA256:6FEAC159A45B4C24302F4B2CCBD56DB9ED3E84E75A4FEA806B6F5C523C349B37 | |||
| 1960 | RegSvcs.exe | C:\Users\admin\AppData\Local\Temp\hvilvxbjxmhjap.exe | executable | |
MD5:6A5C271E8D094FFF13789B60EE86D17E | SHA256:8C4168AD1AF64B1FD3665F0100824A1A74DFD629E417F14211018AB65A39F2D7 | |||
| 2736 | file.exe | C:\Users\admin\AppData\Local\Temp\Protect544cd51a.dll | executable | |
MD5:544CD51A596619B78E9B54B70088307D | SHA256:DFCE2D4D06DE6452998B3C5B2DC33EAA6DB2BD37810D04E3D02DC931887CFDDD | |||
| 2788 | vonaxbfhlql.exe | C:\Users\admin\AppData\Local\Temp\4fdb51ccdc\Utsysc.exe | executable | |
MD5:9F11BE6D846DFA9F9C511171B1A8D81B | SHA256:473EDD855B682E814F0CAA8AFC4BDEAE57D32EFAC1936AE07F12D60645D2F3D8 | |||
| 2092 | hvilvxbjxmhjap.exe | C:\ProgramData\pinterests\XRJNZC.exe | executable | |
MD5:6A5C271E8D094FFF13789B60EE86D17E | SHA256:8C4168AD1AF64B1FD3665F0100824A1A74DFD629E417F14211018AB65A39F2D7 | |||
| 2092 | hvilvxbjxmhjap.exe | C:\Users\admin\AppData\Local\Temp\s1m4.0.bat | text | |
MD5:3A4D05BE693A6C74E4C63EFEDB1CE07C | SHA256:F1DA50AA43950D08708118FAD49E734175D8FB6A2D29AE4B087C089F24B595D0 | |||
| 2952 | Utsysc.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HQYU0XHJ\clip64[1].dll | executable | |
MD5:C06513AF505F65393B4EBCD2A11A2EE4 | SHA256:F5D35A2366CF13312A30C9384F1AC30D9DC9CED46FA6B1B9C2D0621493CC2495 | |||
| 2952 | Utsysc.exe | C:\Users\admin\AppData\Local\Temp\896776584425 | image | |
MD5:DBDD70DDF9F1F120EDE9E90E5F3A93AE | SHA256:0C147AA840442A76A2A86CA42D57651DDF04FBD3D79D4898DD1ACDD3E602E026 | |||
| 2952 | Utsysc.exe | C:\Users\admin\AppData\Roaming\80c6bf70bf3f8f\clip64.dll | executable | |
MD5:C06513AF505F65393B4EBCD2A11A2EE4 | SHA256:F5D35A2366CF13312A30C9384F1AC30D9DC9CED46FA6B1B9C2D0621493CC2495 | |||
| 2952 | Utsysc.exe | C:\Users\admin\AppData\Roaming\80c6bf70bf3f8f\cred64.dll | executable | |
MD5:B5CDFC4CA11AA7705C605FD93538A310 | SHA256:92342E62A3F51B7E205863F58B6A0E0145C4FECC31D40049B91E97ED0BB710CA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
39
DNS requests
1
Threats
61
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1960 | RegSvcs.exe | POST | 200 | 104.21.7.219:80 | http://gatelistcoldyeisa.pw/api | unknown | text | 8.73 Kb | unknown |
1960 | RegSvcs.exe | POST | 200 | 104.21.7.219:80 | http://gatelistcoldyeisa.pw/api | unknown | text | 21 b | unknown |
1960 | RegSvcs.exe | POST | 200 | 104.21.7.219:80 | http://gatelistcoldyeisa.pw/api | unknown | text | 21 b | unknown |
1960 | RegSvcs.exe | POST | 200 | 104.21.7.219:80 | http://gatelistcoldyeisa.pw/api | unknown | text | 2 b | unknown |
1960 | RegSvcs.exe | POST | 200 | 104.21.7.219:80 | http://gatelistcoldyeisa.pw/api | unknown | text | 21 b | unknown |
1960 | RegSvcs.exe | POST | 200 | 104.21.7.219:80 | http://gatelistcoldyeisa.pw/api | unknown | text | 21 b | unknown |
1960 | RegSvcs.exe | POST | 200 | 104.21.7.219:80 | http://gatelistcoldyeisa.pw/api | unknown | text | 21 b | unknown |
1960 | RegSvcs.exe | POST | 200 | 104.21.7.219:80 | http://gatelistcoldyeisa.pw/api | unknown | text | 21 b | unknown |
1960 | RegSvcs.exe | POST | 200 | 104.21.7.219:80 | http://gatelistcoldyeisa.pw/api | unknown | text | 21 b | unknown |
1960 | RegSvcs.exe | POST | 200 | 104.21.7.219:80 | http://gatelistcoldyeisa.pw/api | unknown | text | 21 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1960 | RegSvcs.exe | 104.21.7.219:80 | gatelistcoldyeisa.pw | CLOUDFLARENET | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1960 | RegSvcs.exe | 185.172.128.8:80 | — | OOO Nadym Svyaz Service | RU | unknown |
2952 | Utsysc.exe | 185.172.128.5:80 | — | OOO Nadym Svyaz Service | RU | unknown |
988 | rundll32.exe | 185.172.128.5:80 | — | OOO Nadym Svyaz Service | RU | unknown |
2396 | rundll32.exe | 185.172.128.5:80 | — | OOO Nadym Svyaz Service | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gatelistcoldyeisa.pw |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
324 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1960 | RegSvcs.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
1960 | RegSvcs.exe | Malware Command and Control Activity Detected | ET MALWARE [ANY.RUN] Win32/Lumma Stealer Check-In |
1960 | RegSvcs.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Check-In |
1960 | RegSvcs.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
1960 | RegSvcs.exe | Malware Command and Control Activity Detected | ET MALWARE [ANY.RUN] Win32/Lumma Stealer Exfiltration |
1960 | RegSvcs.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Exfiltration |
1960 | RegSvcs.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
1960 | RegSvcs.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
1960 | RegSvcs.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
2 ETPRO signatures available at the full report