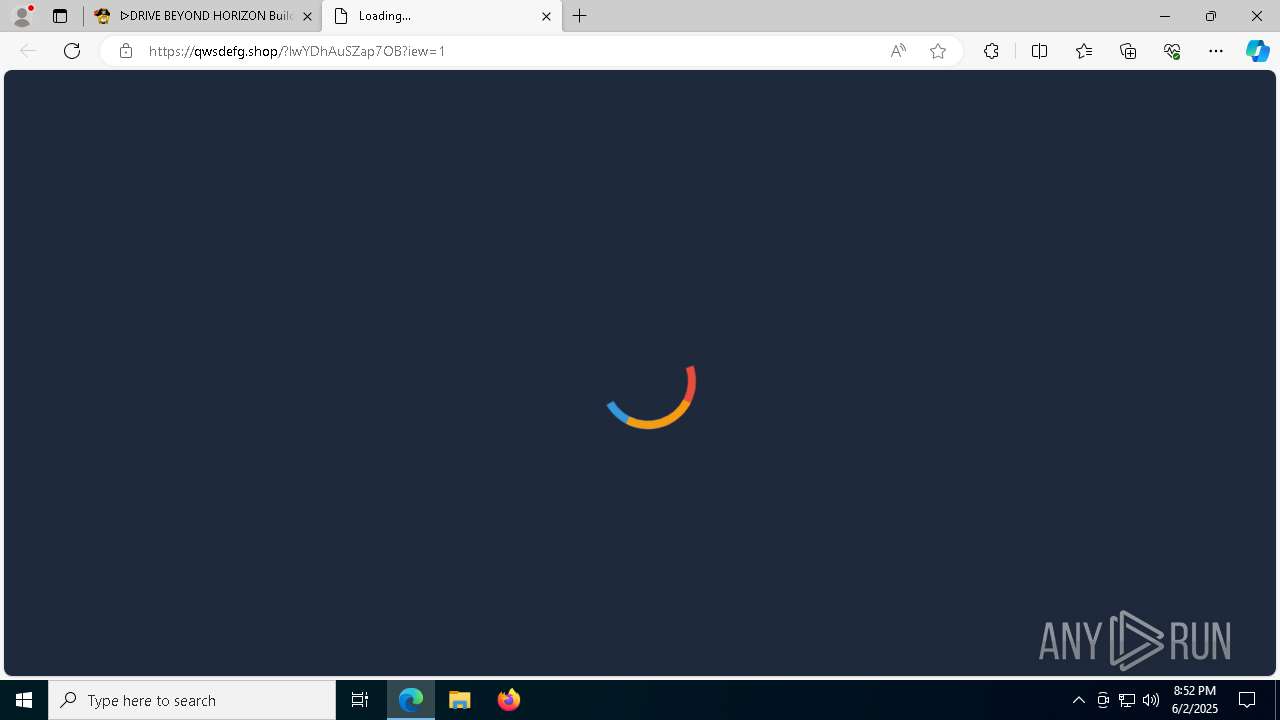
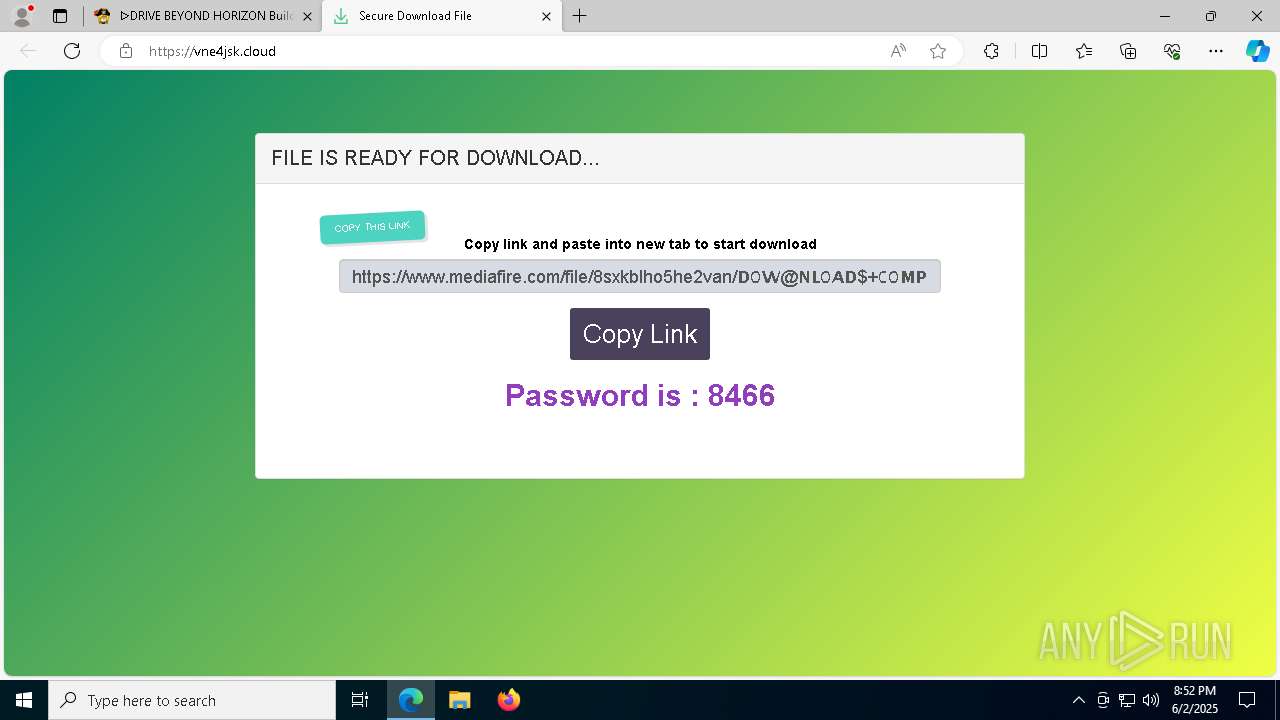
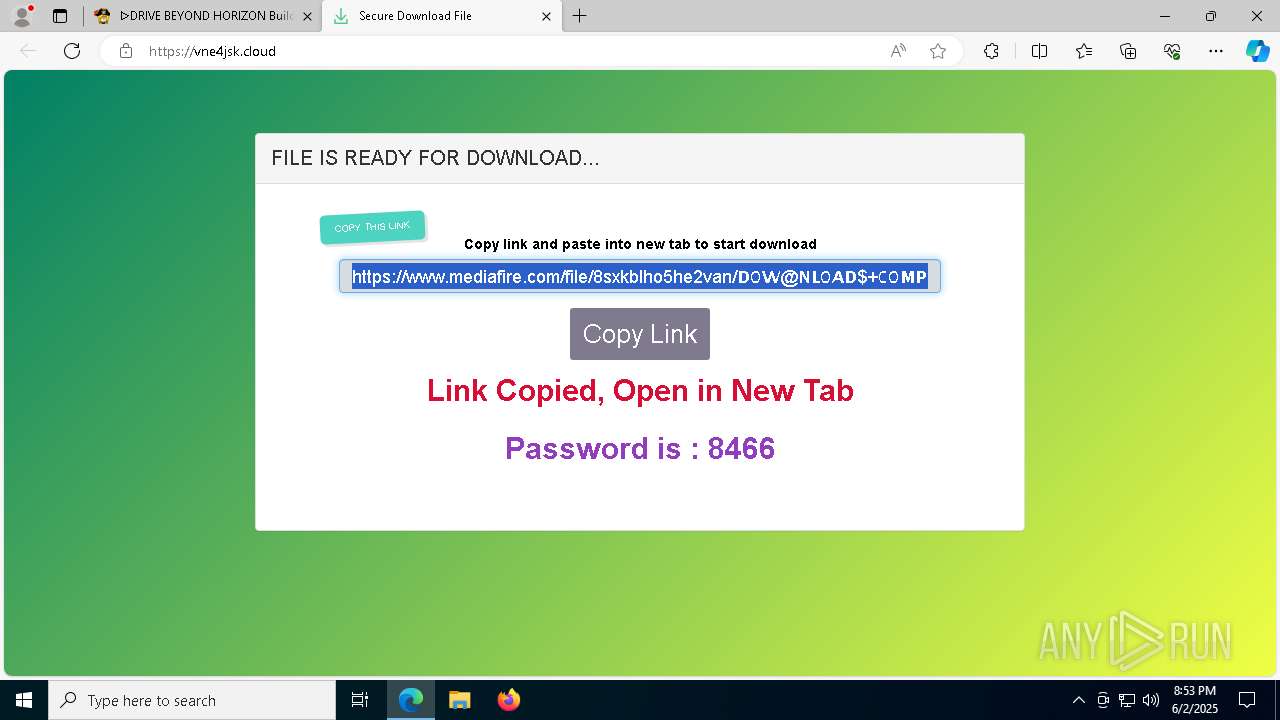
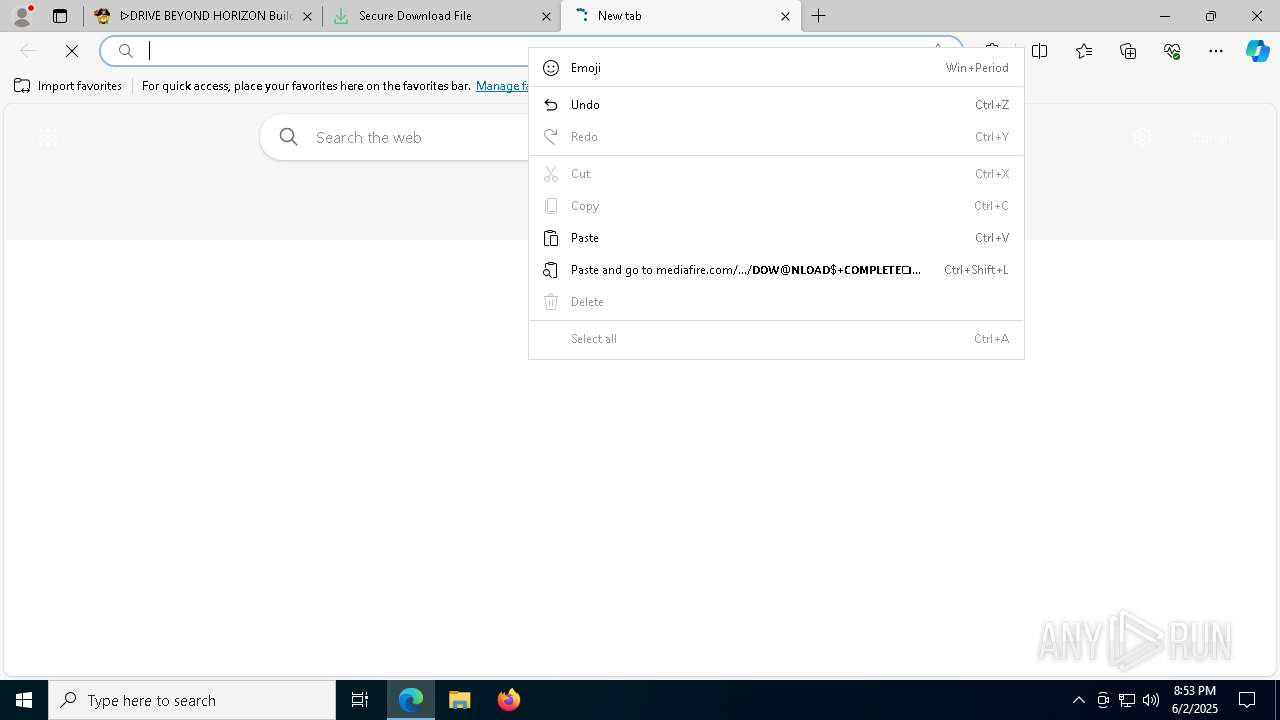
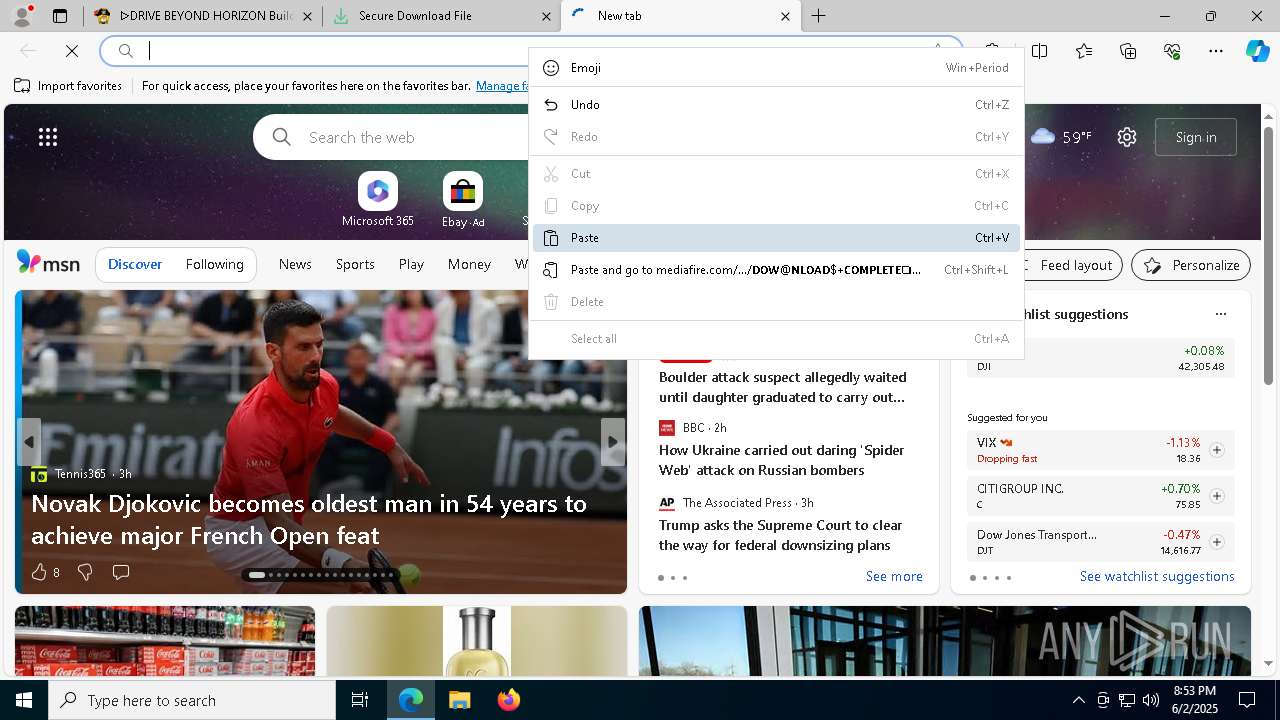
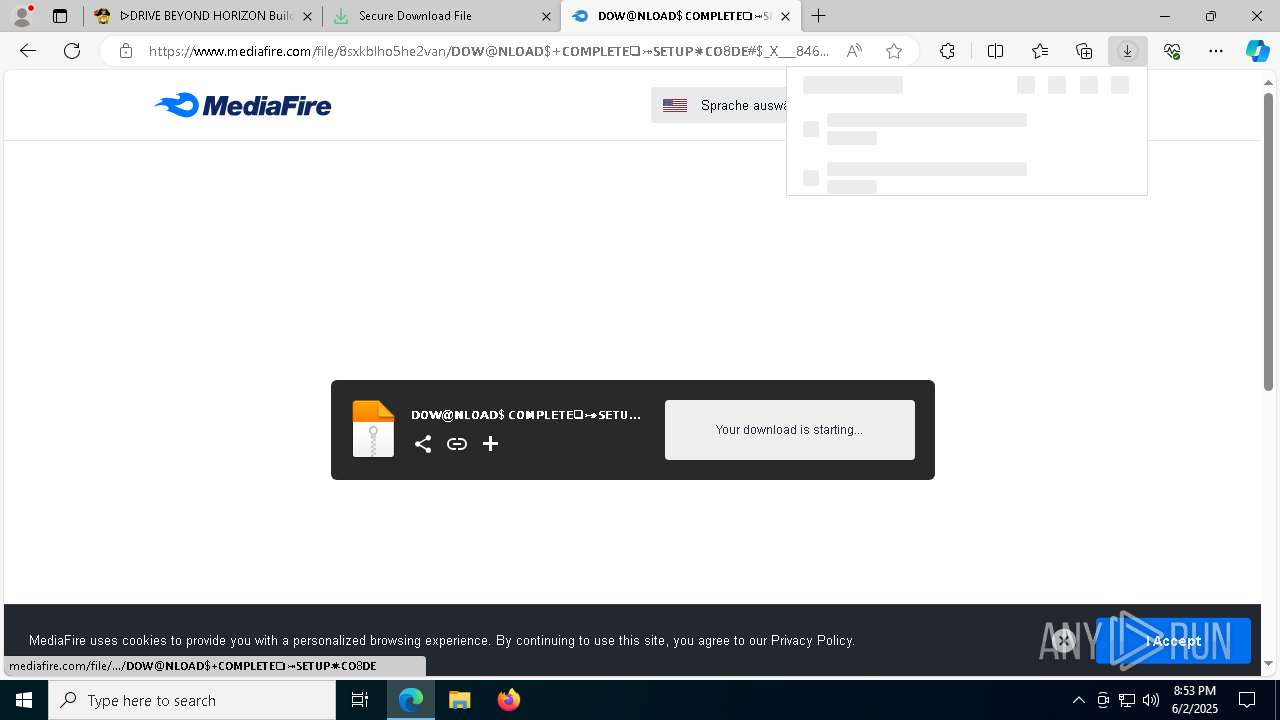
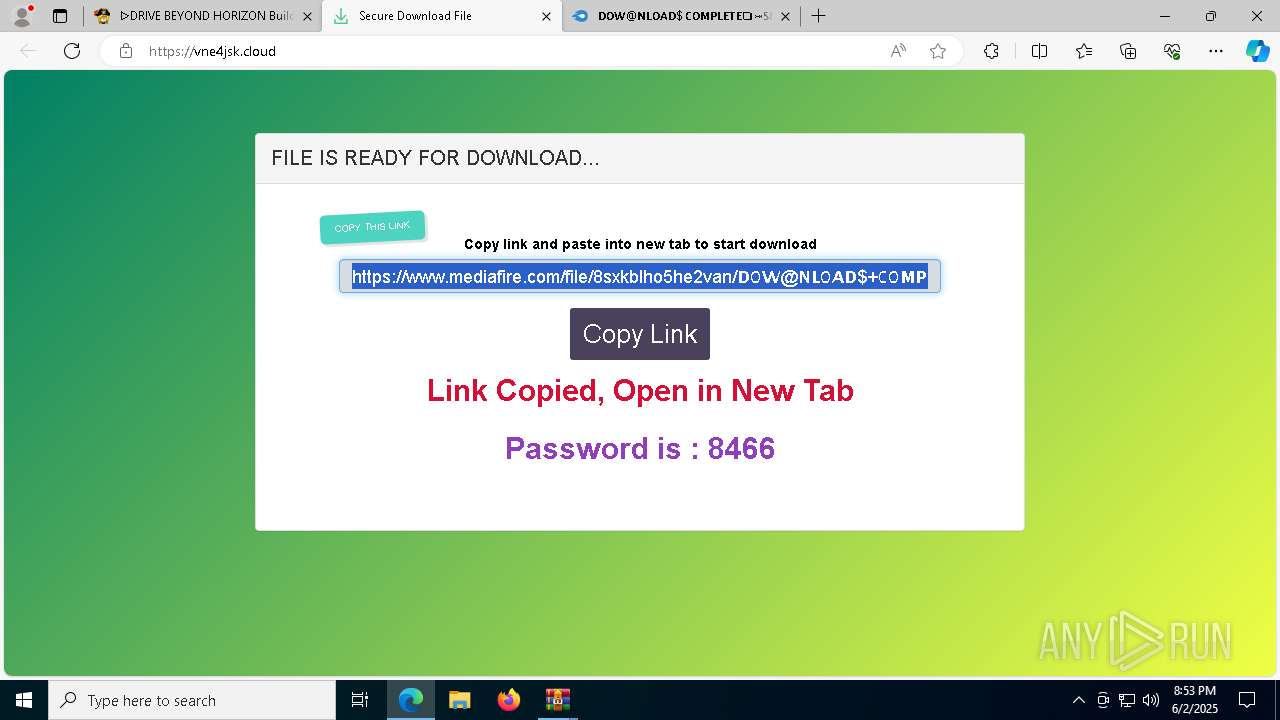
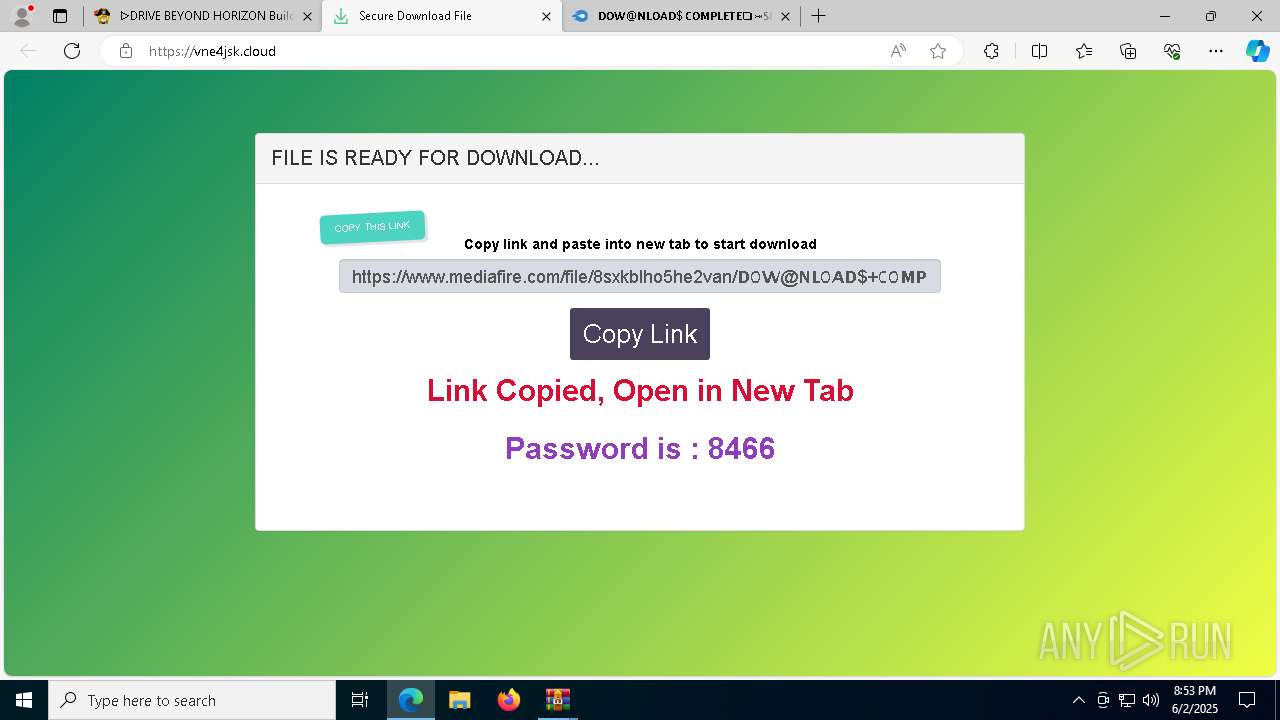
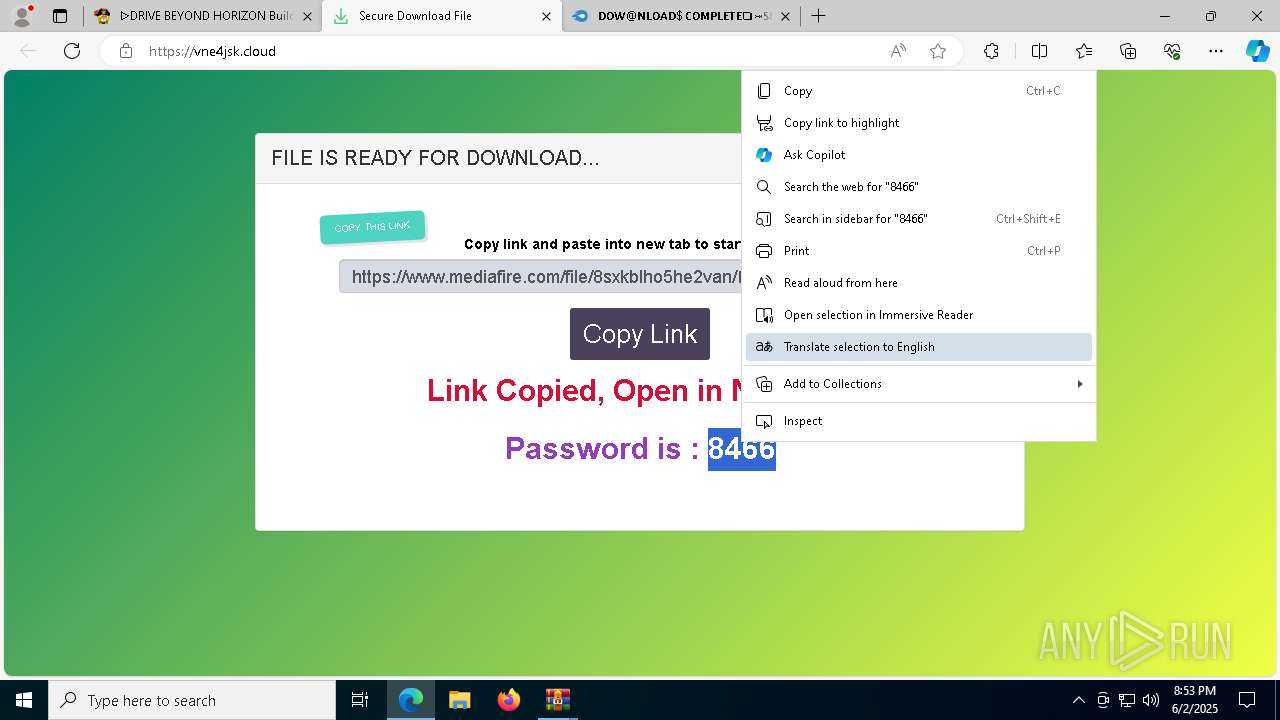
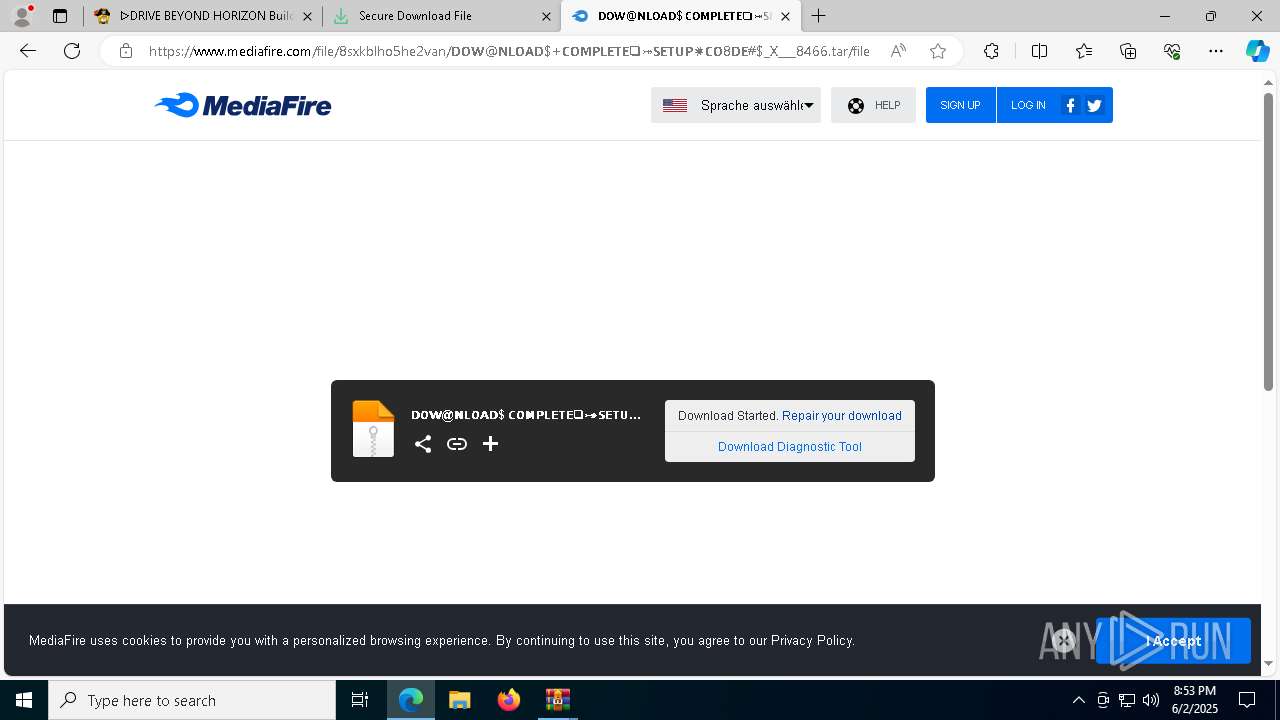
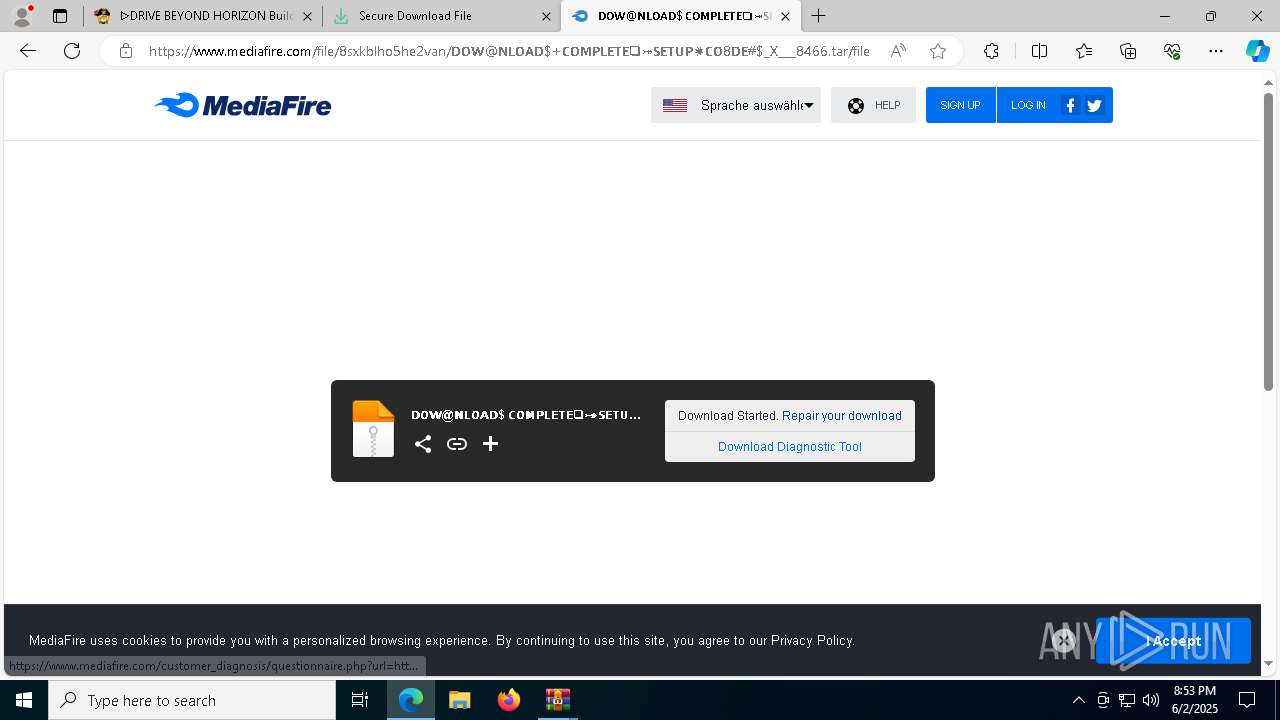
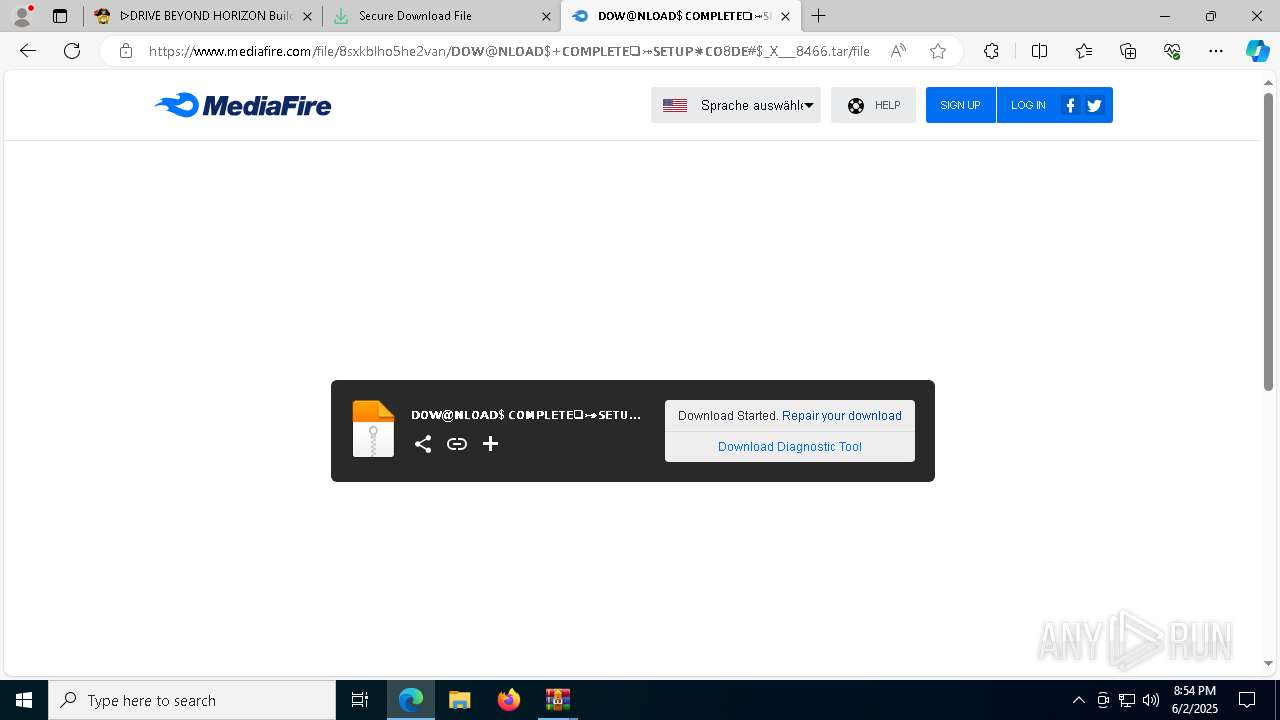
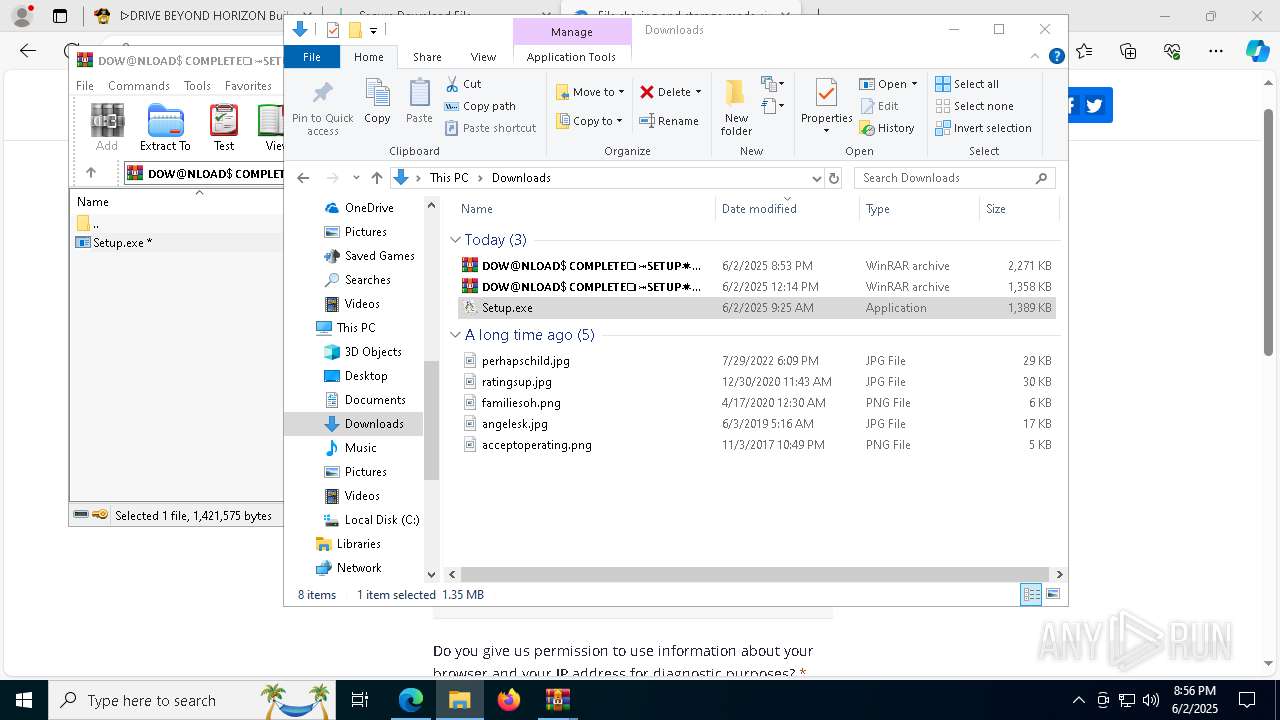
| URL: | https://pivigames.blog/drive-beyond-horizon-pc-espanol-online-steam/ |
| Full analysis: | https://app.any.run/tasks/6e2d67c8-f7f0-4d0b-a216-372ef48629e0 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | June 02, 2025, 20:52:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
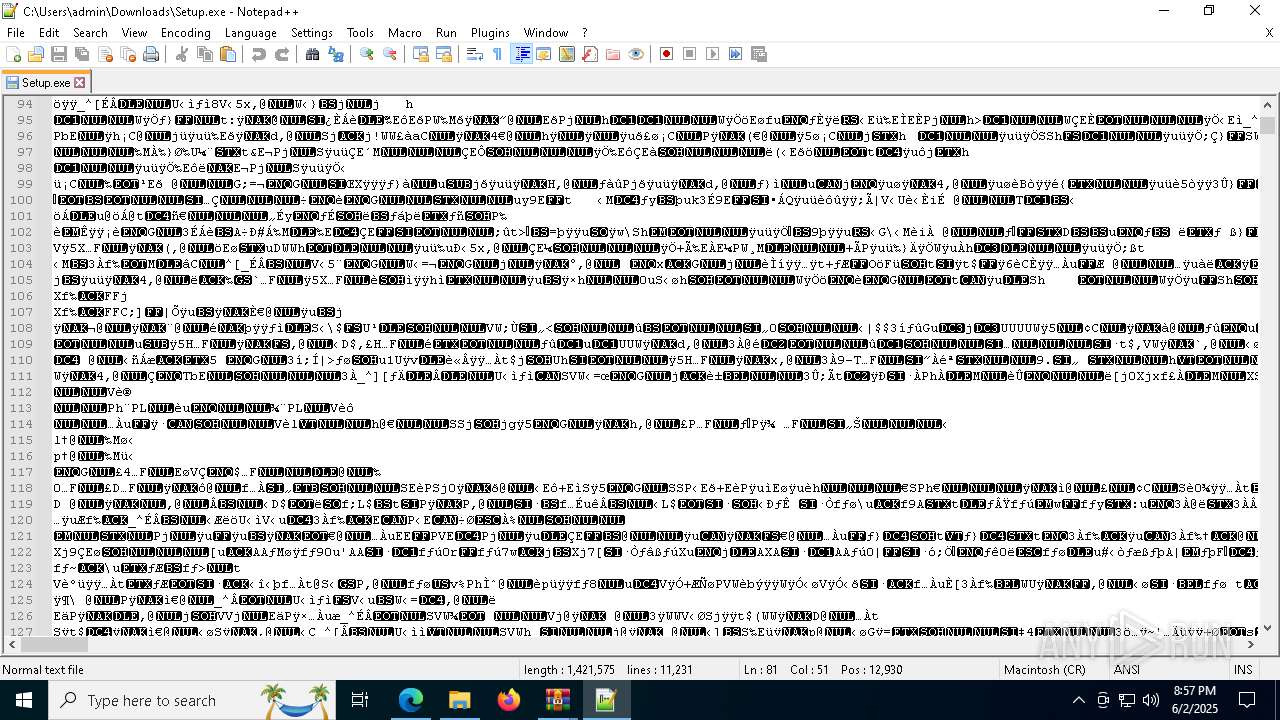
| MD5: | EF02505909FD186BE4732F9F961665CE |
| SHA1: | F76AD279B86C0459B3543CC4661C664FACA5E20A |
| SHA256: | BE032B8D6019682DFE0B86C58A5E1434E867D705ED3242FDB995D4898A3AB376 |
| SSDEEP: | 3:N8IAdWlZKsSpMVpvJ39MQzIK:2IWovSiVjuK |
MALICIOUS
LUMMA has been detected (SURICATA)
- msedge.exe (PID: 2852)
Stealers network behavior
- msedge.exe (PID: 2852)
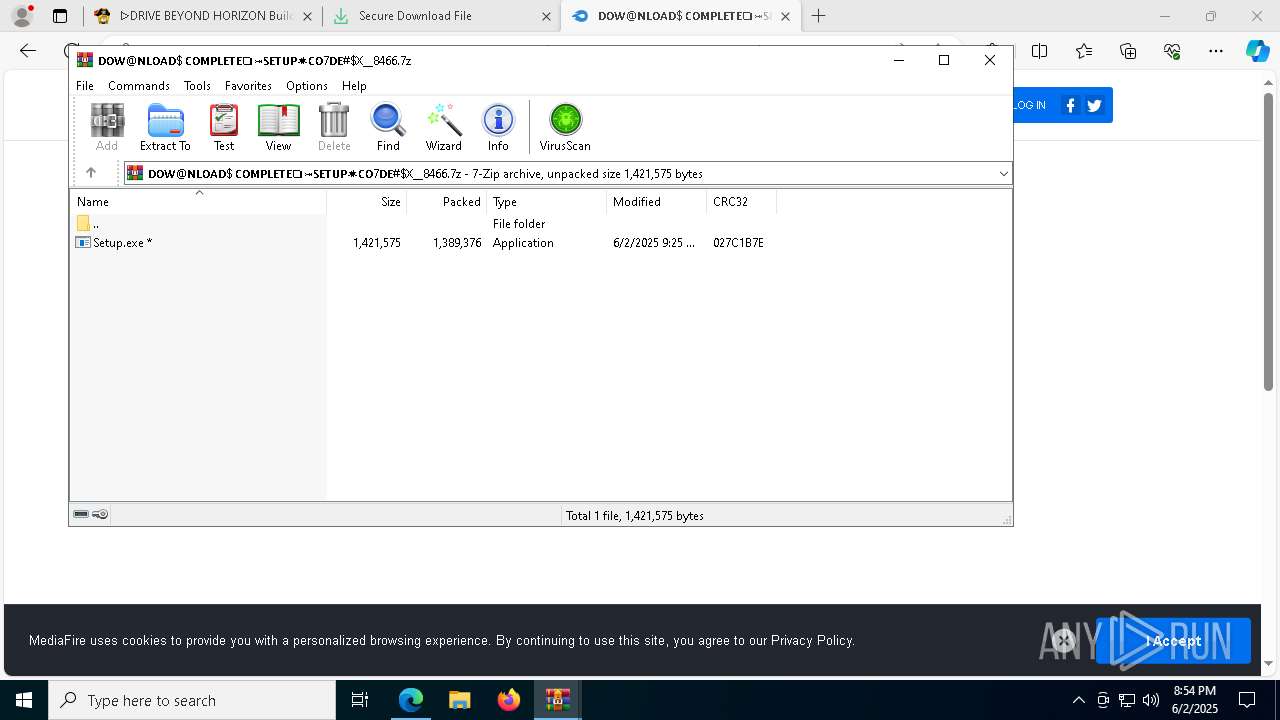
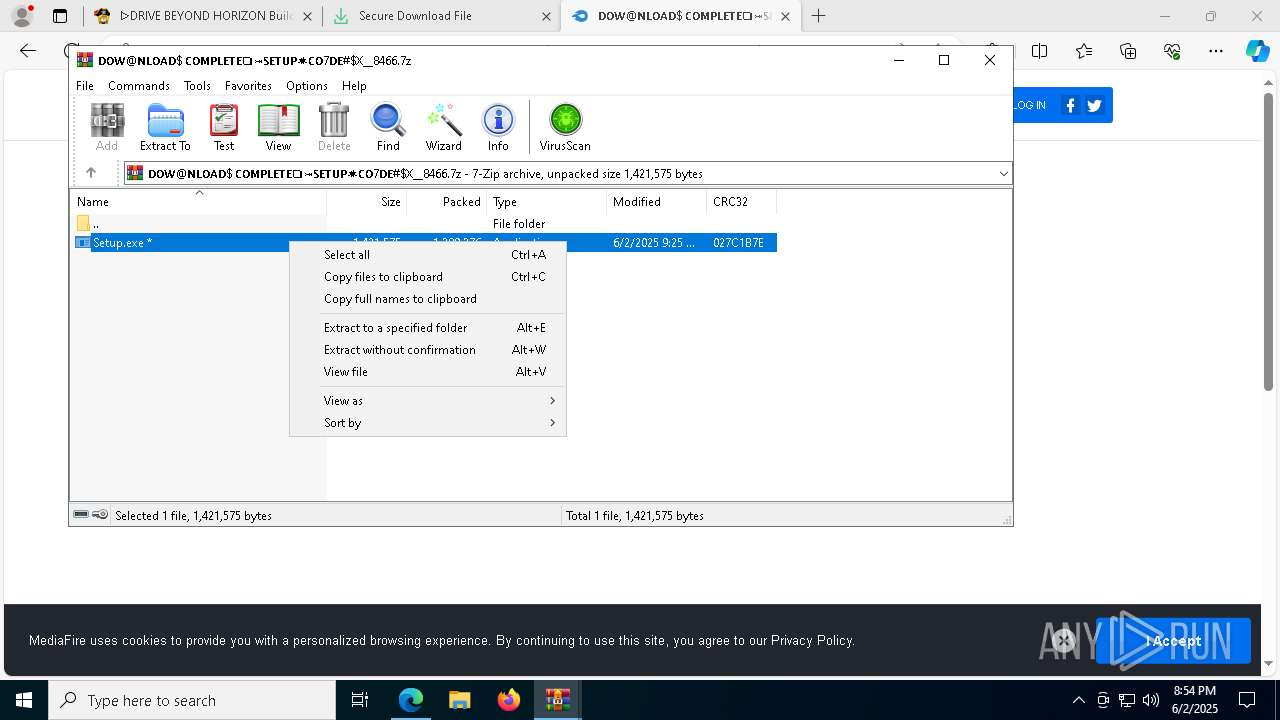
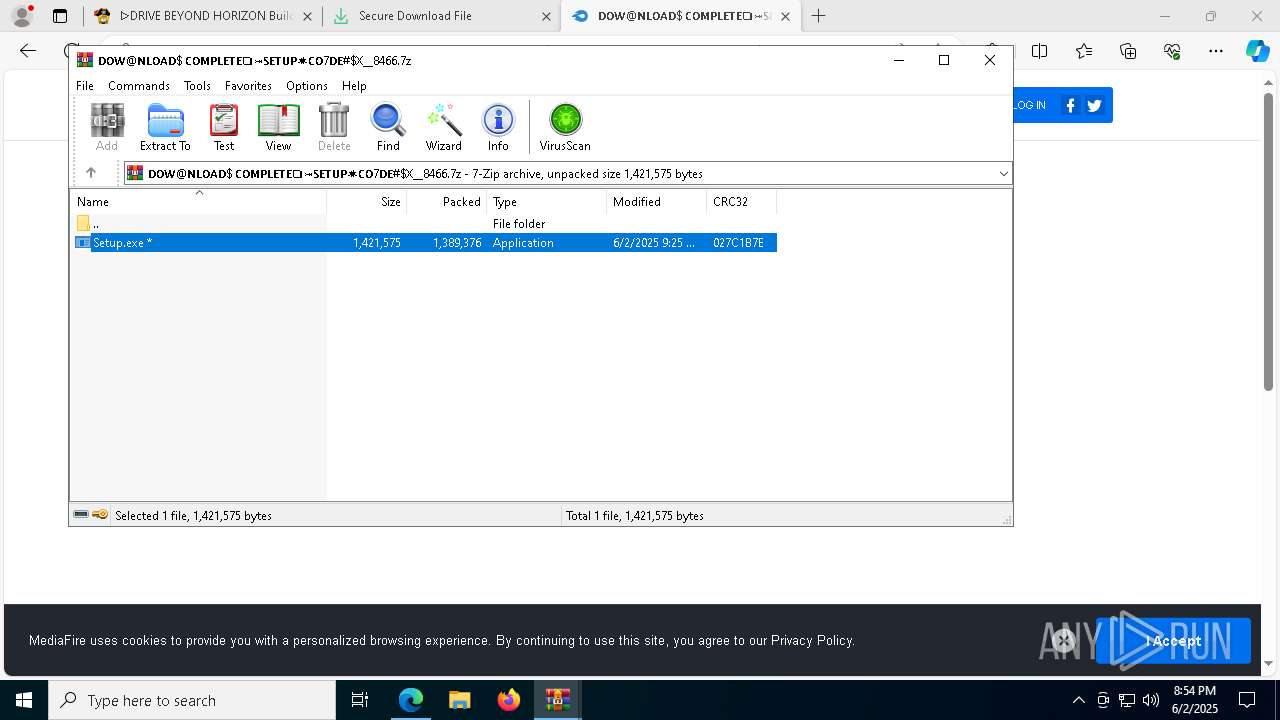
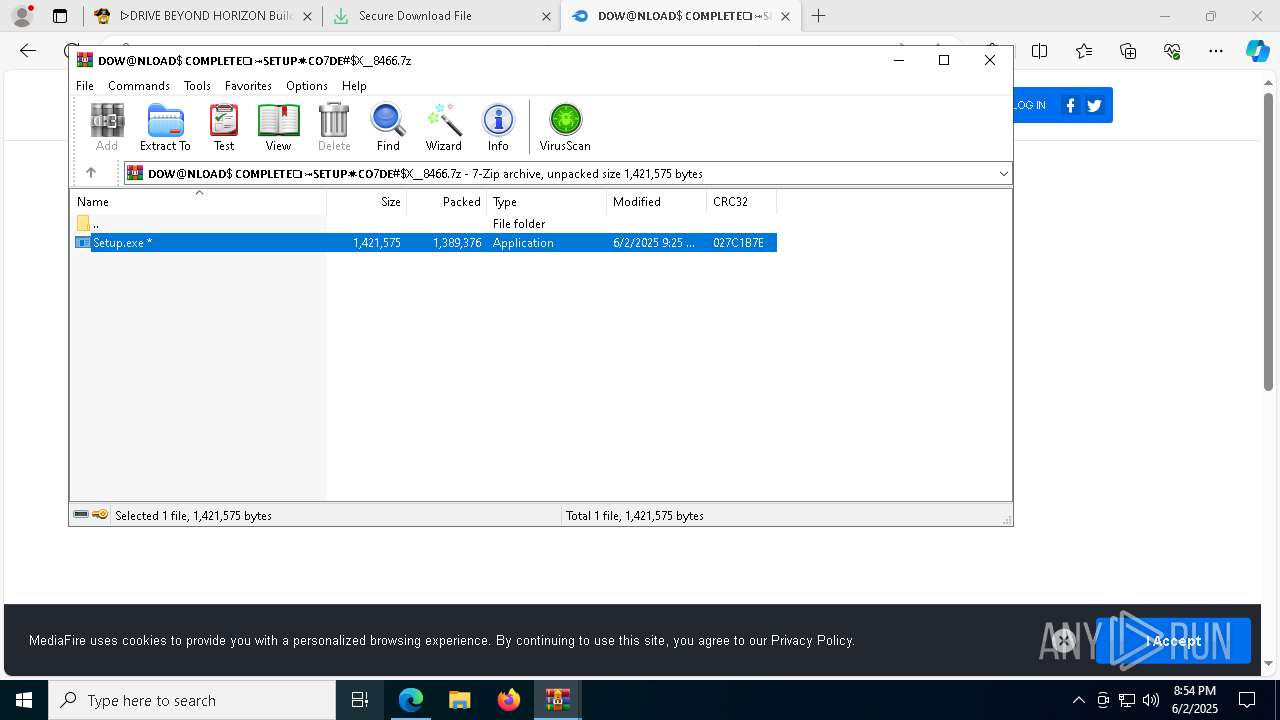
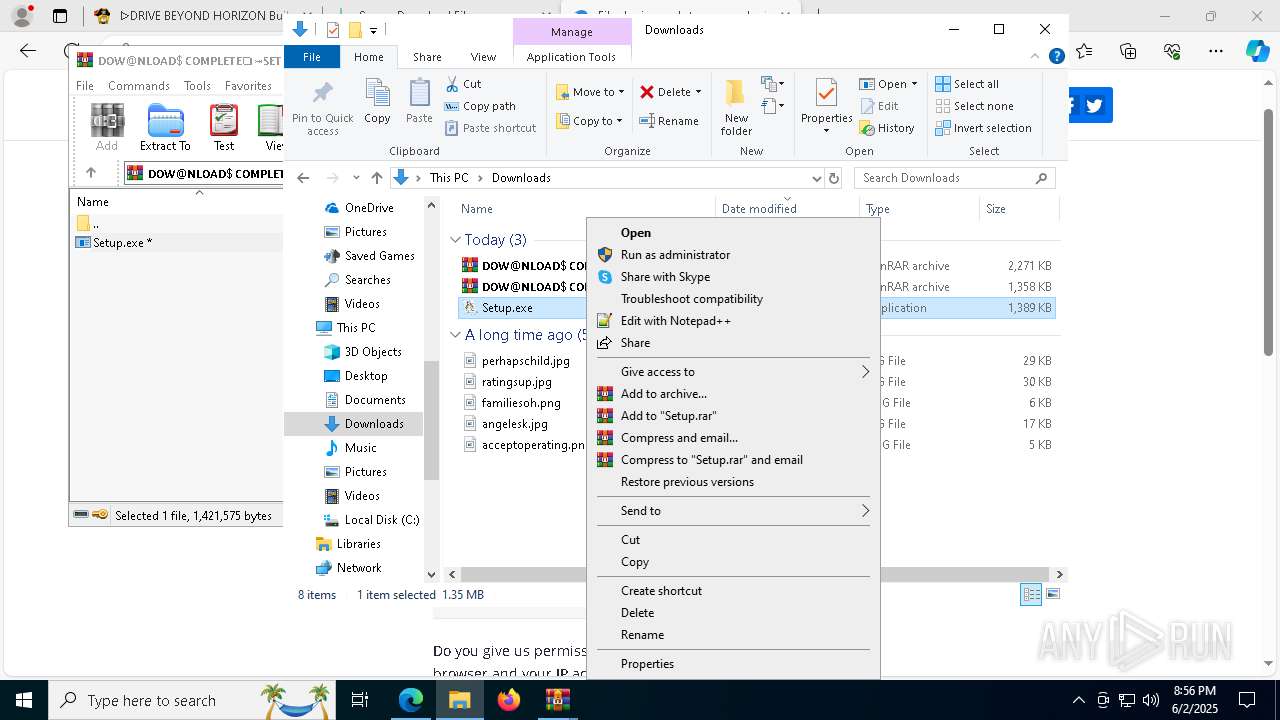
Executing a file with an untrusted certificate
- Setup.exe (PID: 8960)
- Setup.exe (PID: 864)
- Setup.exe (PID: 7928)
- Setup.exe (PID: 9776)
AutoIt loader has been detected (YARA)
- Integrate.com (PID: 5212)
- Integrate.com (PID: 8060)
- Integrate.com (PID: 9448)
- Integrate.com (PID: 9036)
RHADAMANTHYS has been detected (YARA)
- OOBE-Maintenance.exe (PID: 656)
- OOBE-Maintenance.exe (PID: 8588)
SUSPICIOUS
Contacting a server suspected of hosting an CnC
- msedge.exe (PID: 2852)
Application launched itself
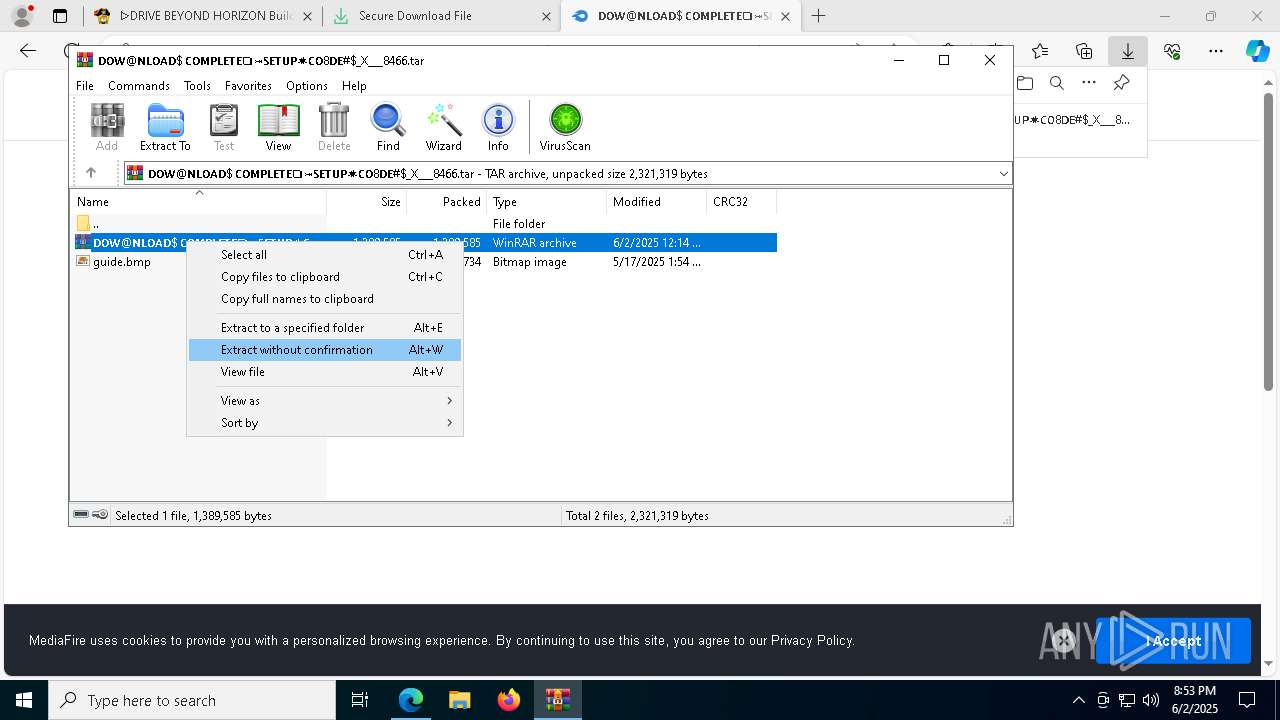
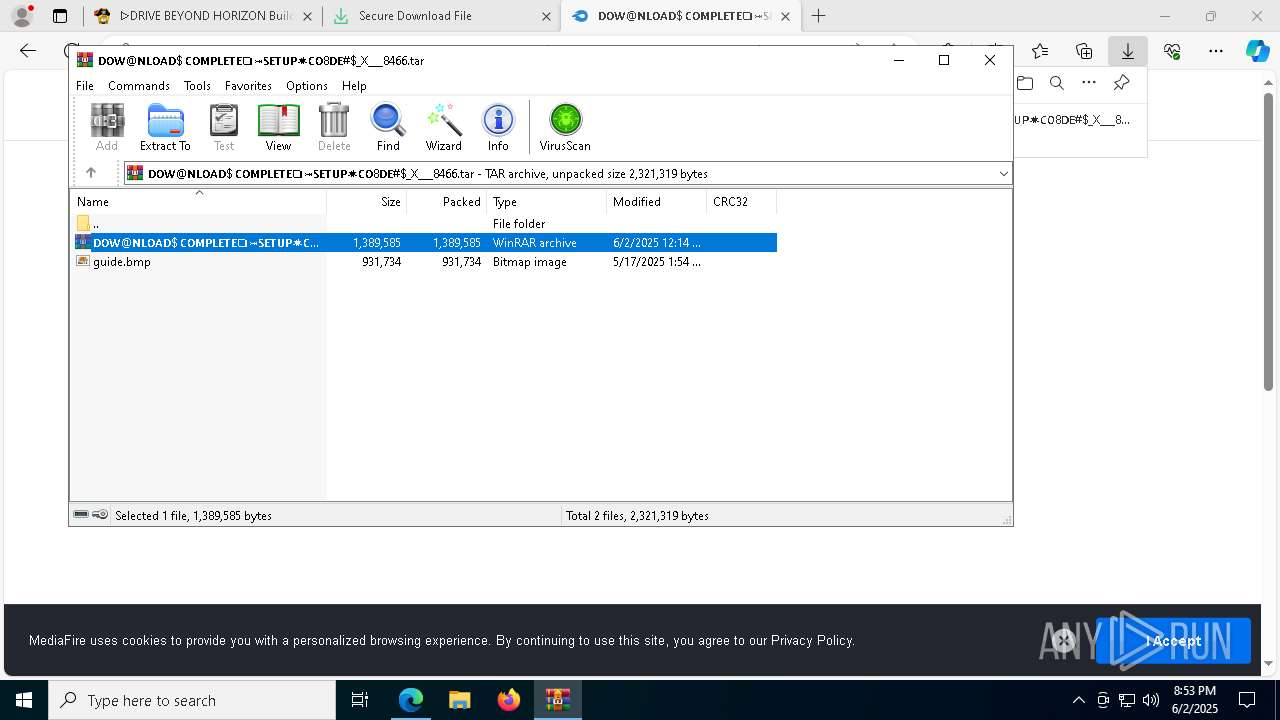
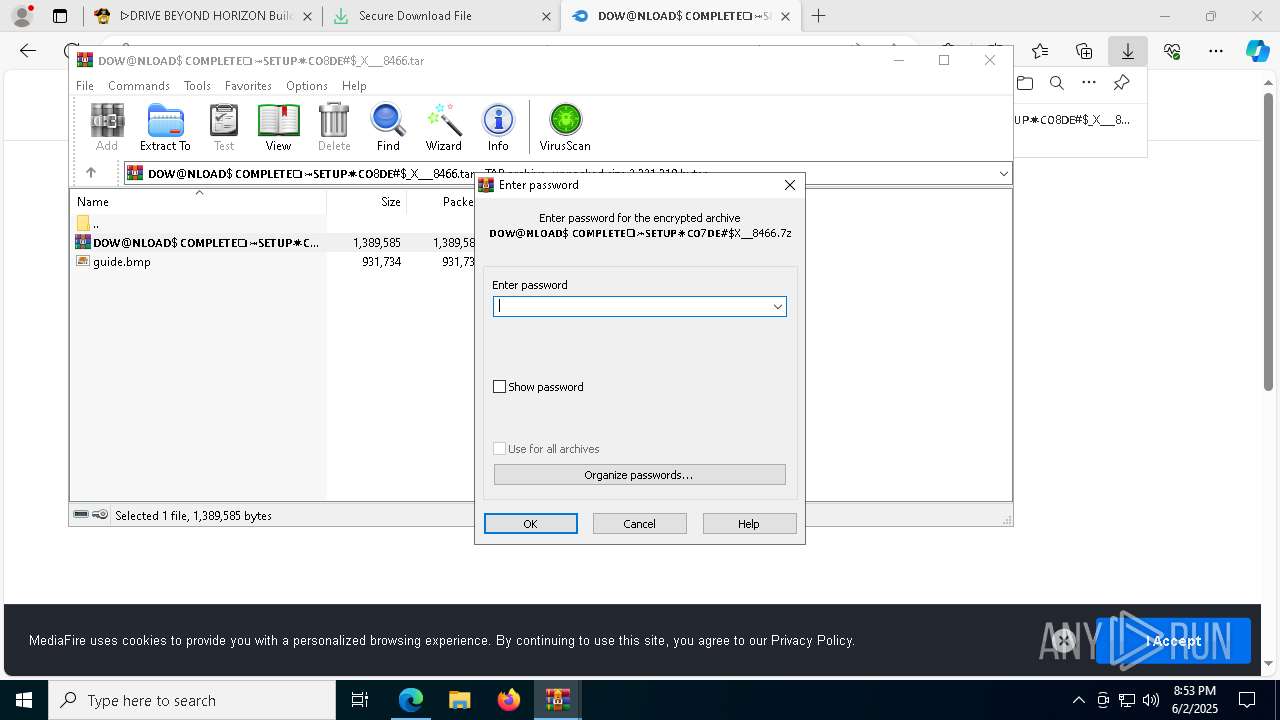
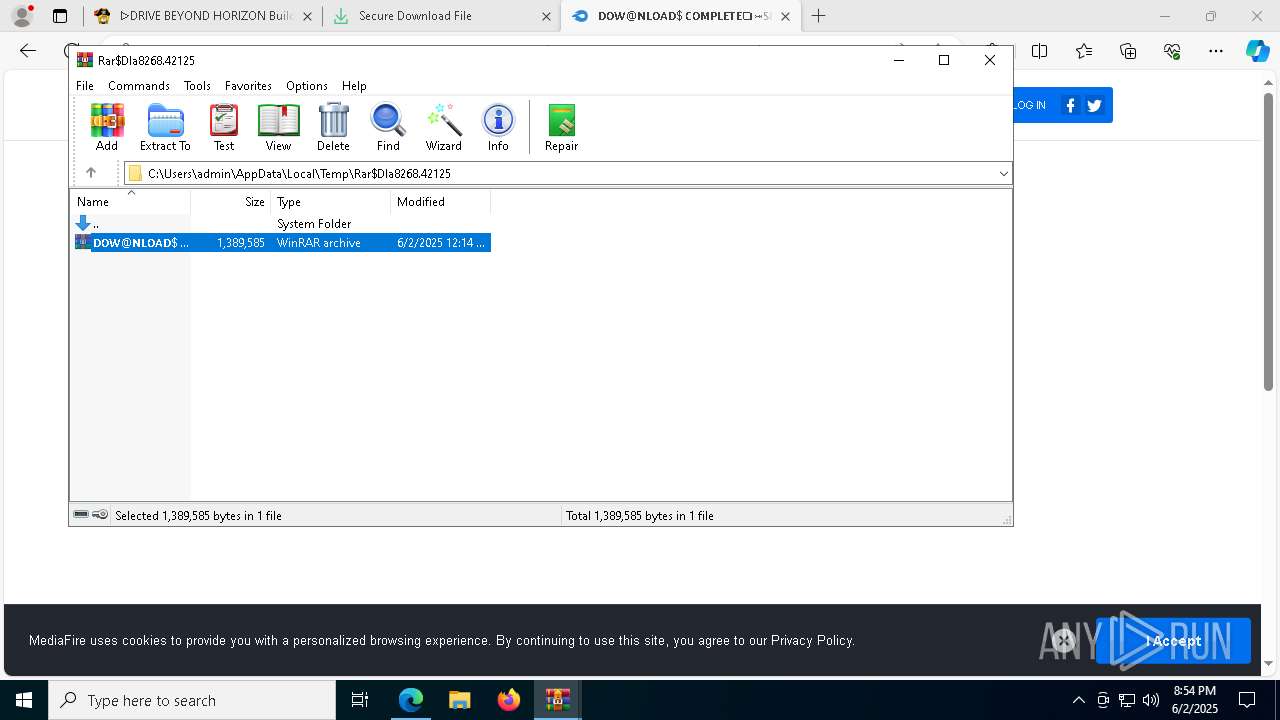
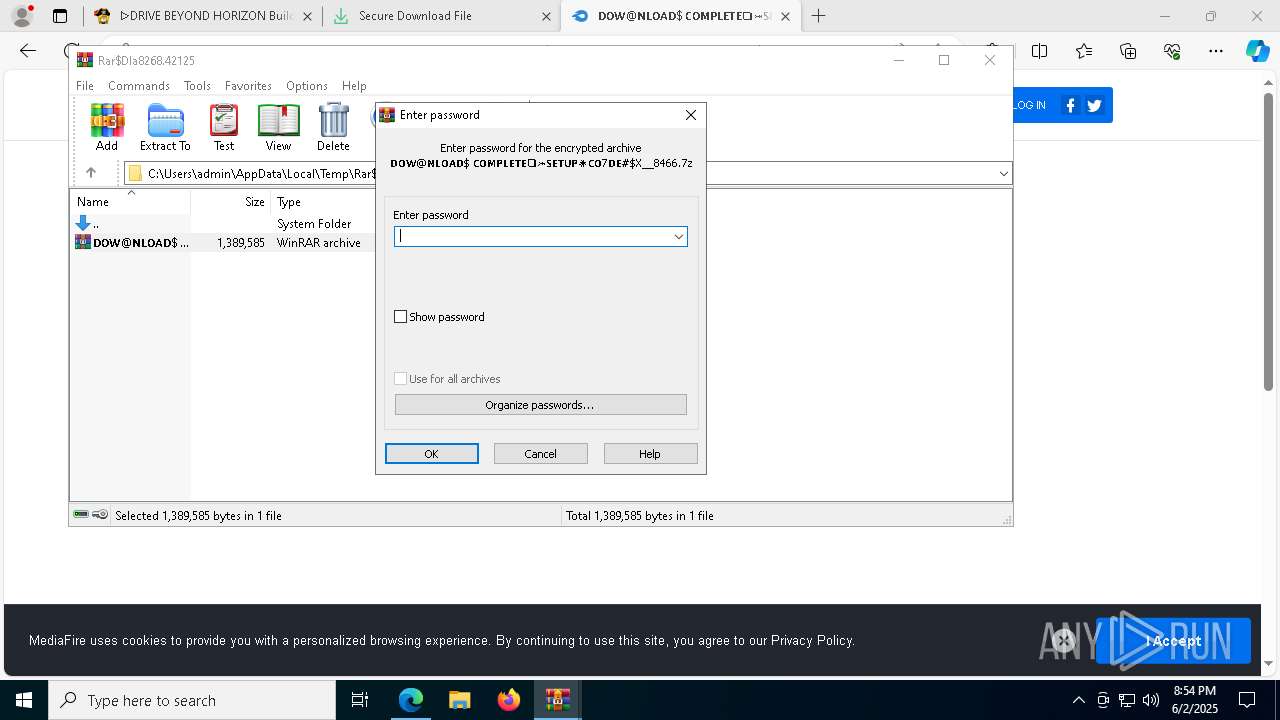
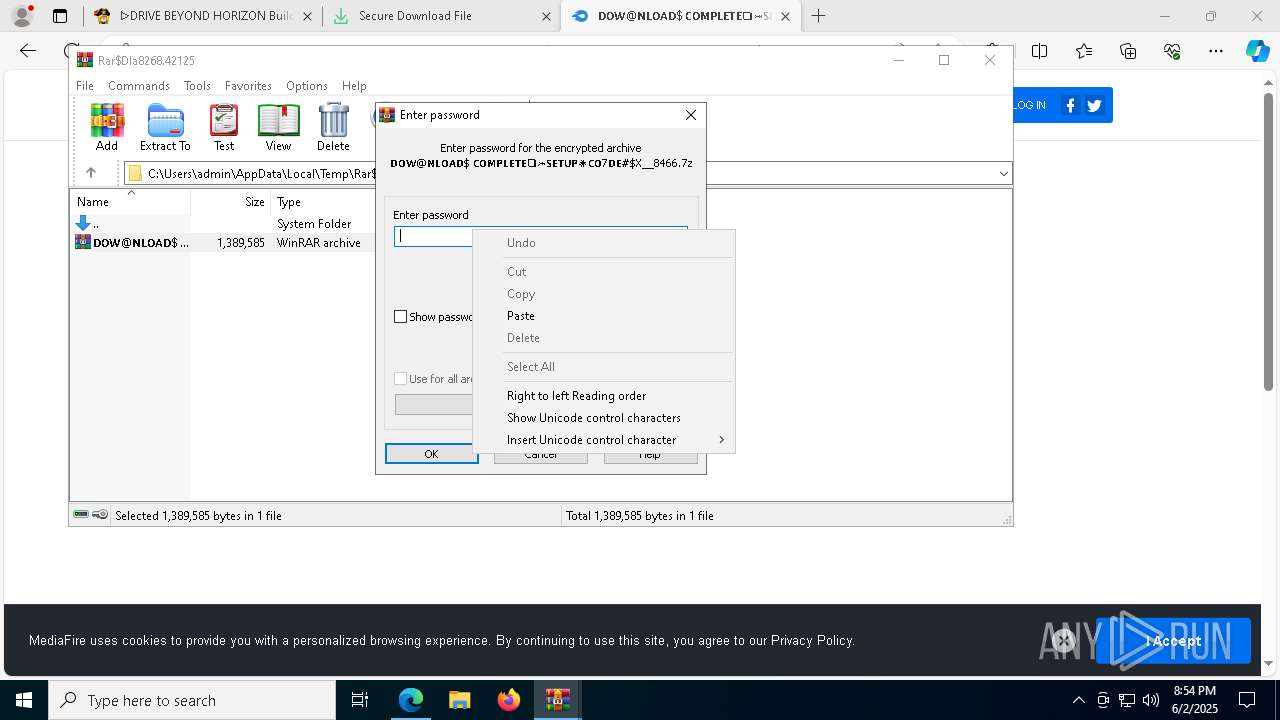
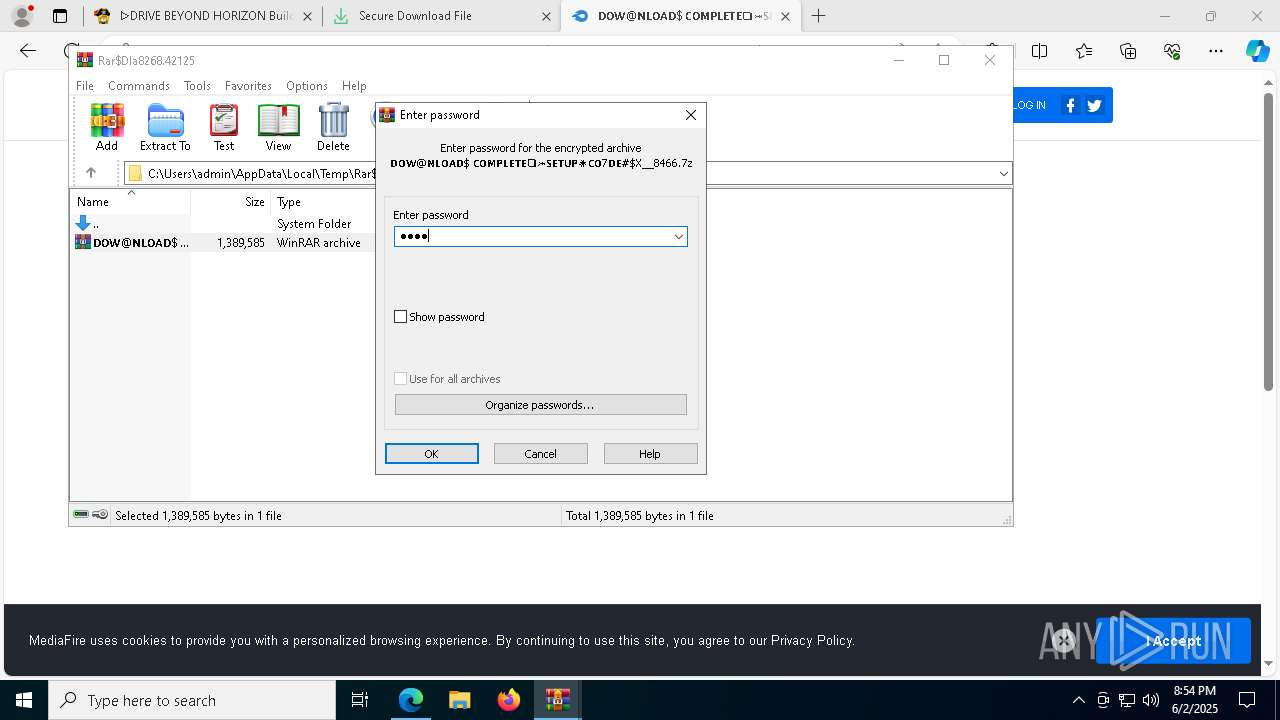
- WinRAR.exe (PID: 8268)
Starts CMD.EXE for commands execution
- Setup.exe (PID: 8960)
- Setup.exe (PID: 864)
- Setup.exe (PID: 7928)
- Setup.exe (PID: 9776)
Get information on the list of running processes
- cmd.exe (PID: 8576)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 10048)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 8576)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 10048)
- cmd.exe (PID: 7844)
Starts the AutoIt3 executable file
- cmd.exe (PID: 8576)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 10048)
- cmd.exe (PID: 7844)
Starts application with an unusual extension
- cmd.exe (PID: 8576)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 10048)
- cmd.exe (PID: 7844)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1696)
- WinRAR.exe (PID: 8268)
- Setup.exe (PID: 8960)
There is functionality for taking screenshot (YARA)
- Setup.exe (PID: 864)
- Integrate.com (PID: 8060)
- Setup.exe (PID: 8960)
- Integrate.com (PID: 5212)
- Setup.exe (PID: 7928)
- Integrate.com (PID: 9448)
- Setup.exe (PID: 9776)
- Integrate.com (PID: 9036)
Executing commands from a ".bat" file
- Setup.exe (PID: 864)
- Setup.exe (PID: 7928)
- Setup.exe (PID: 9776)
- Setup.exe (PID: 8960)
The executable file from the user directory is run by the CMD process
- Integrate.com (PID: 8060)
- Integrate.com (PID: 5212)
- Integrate.com (PID: 9036)
- Integrate.com (PID: 9448)
Executes application which crashes
- Integrate.com (PID: 5212)
- OOBE-Maintenance.exe (PID: 8588)
- Integrate.com (PID: 8060)
- OOBE-Maintenance.exe (PID: 656)
- Integrate.com (PID: 9448)
Multiple wallet extension IDs have been found
- OOBE-Maintenance.exe (PID: 656)
INFO
Checks supported languages
- identity_helper.exe (PID: 8252)
- Setup.exe (PID: 8960)
Application launched itself
- msedge.exe (PID: 7632)
- chrome.exe (PID: 5868)
- msedge.exe (PID: 8536)
- chrome.exe (PID: 6060)
- msedge.exe (PID: 9436)
Reads Environment values
- identity_helper.exe (PID: 8252)
Reads the computer name
- identity_helper.exe (PID: 8252)
- Setup.exe (PID: 8960)
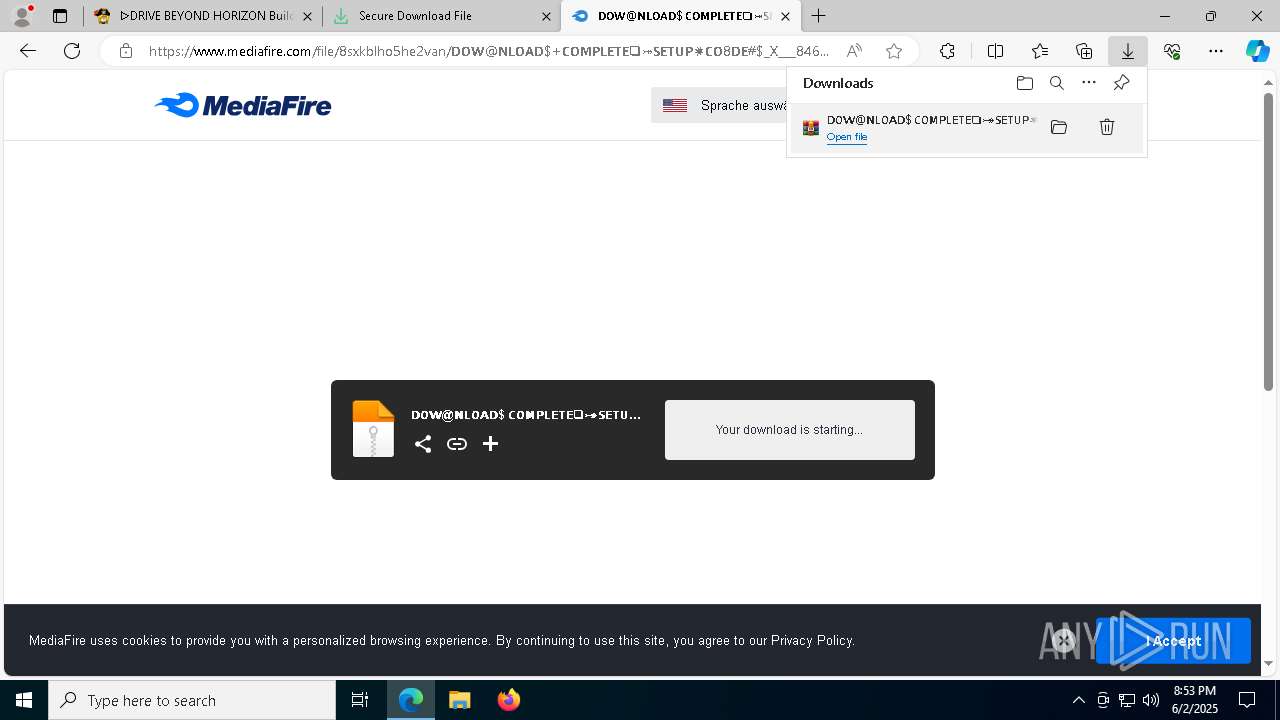
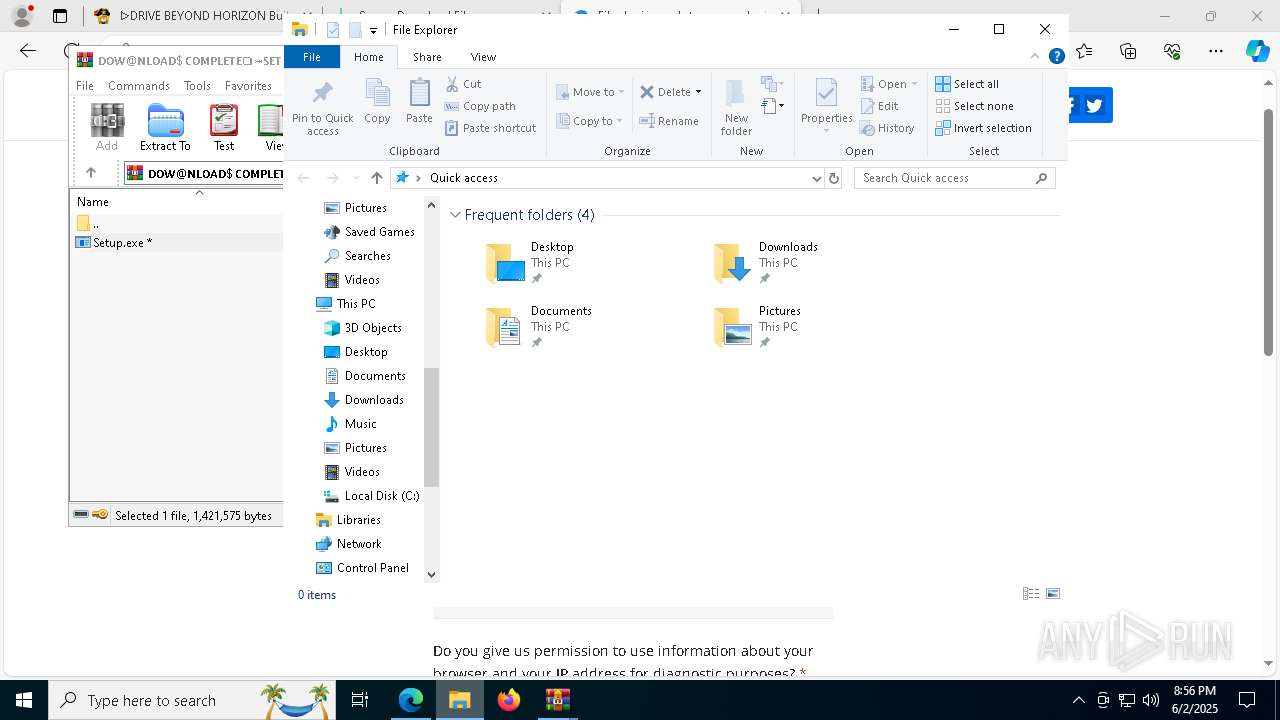
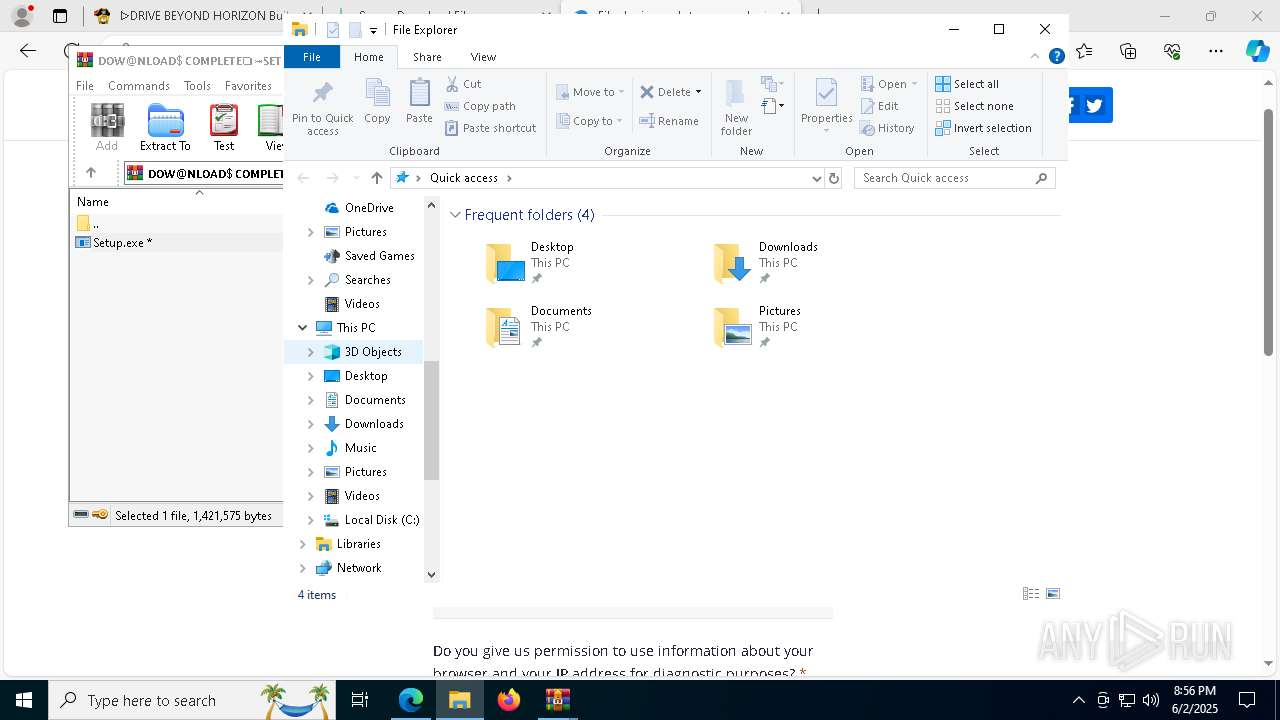
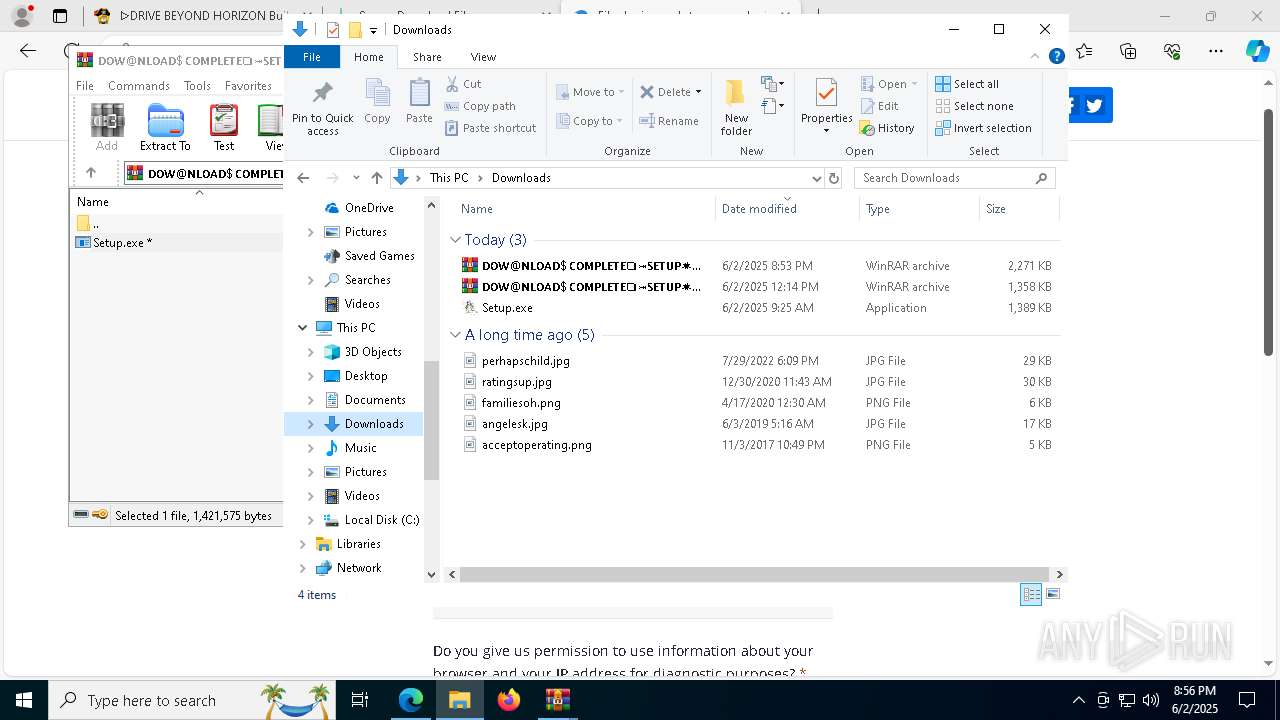
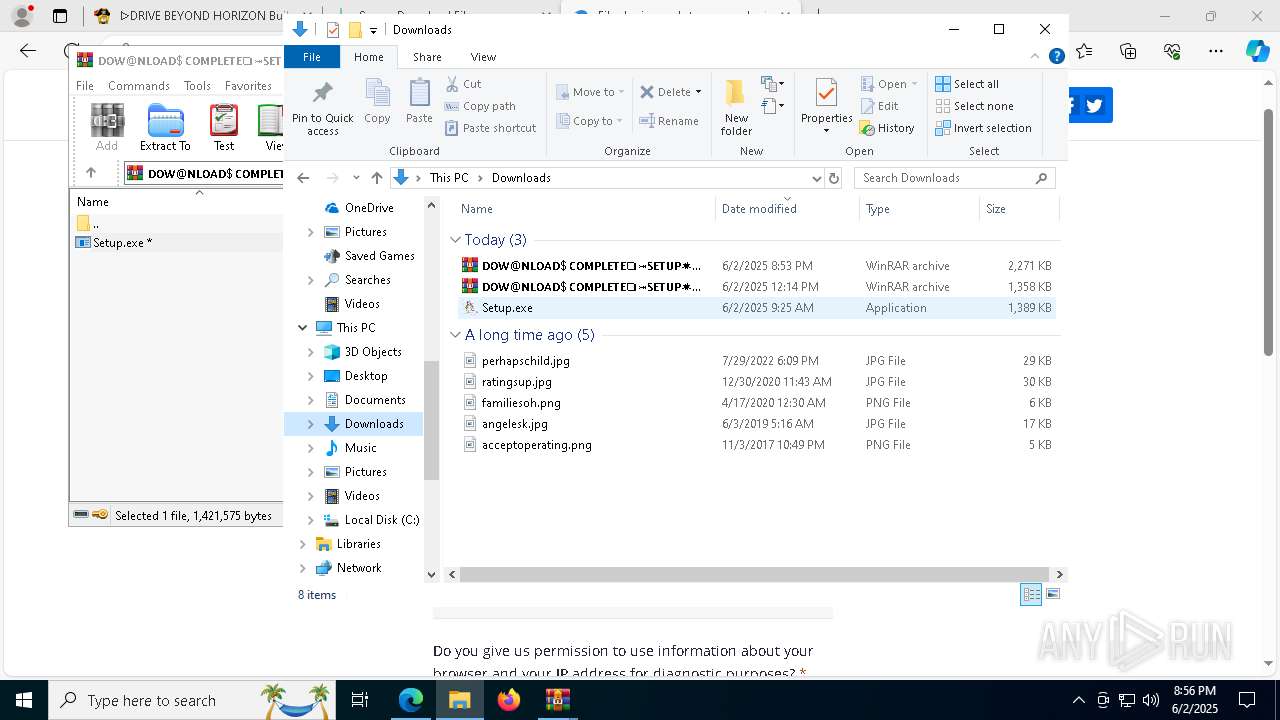
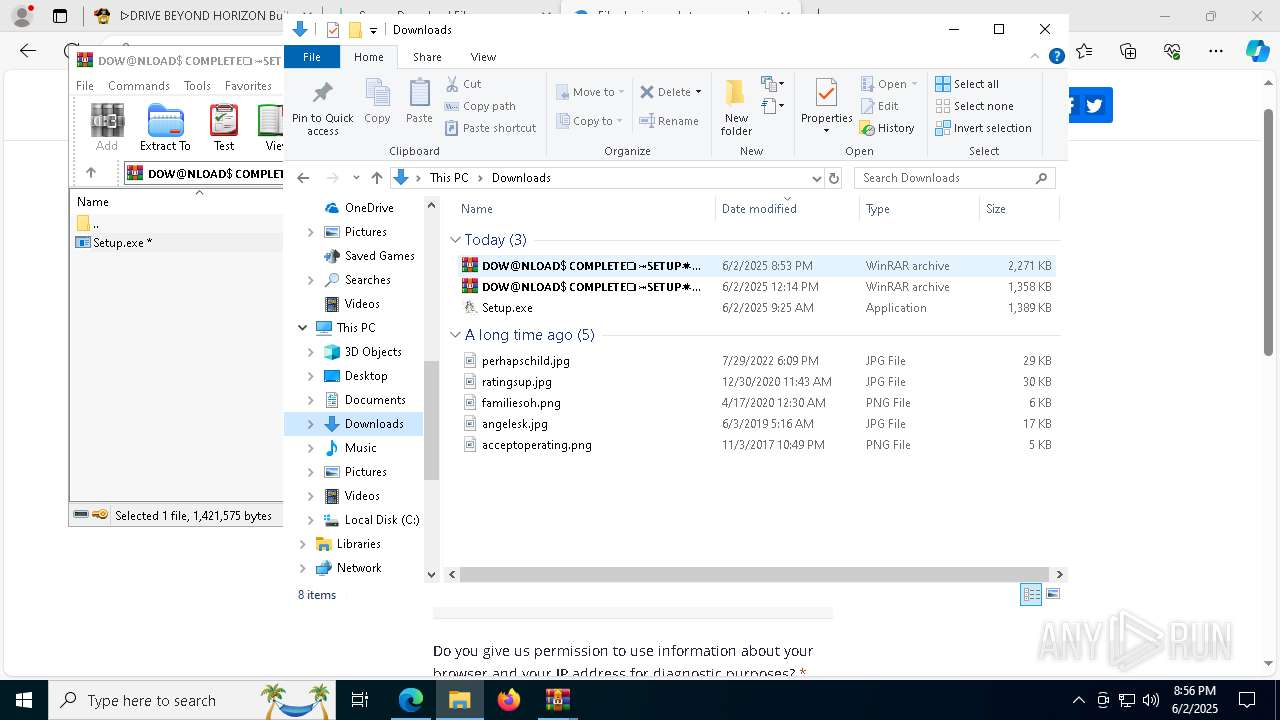
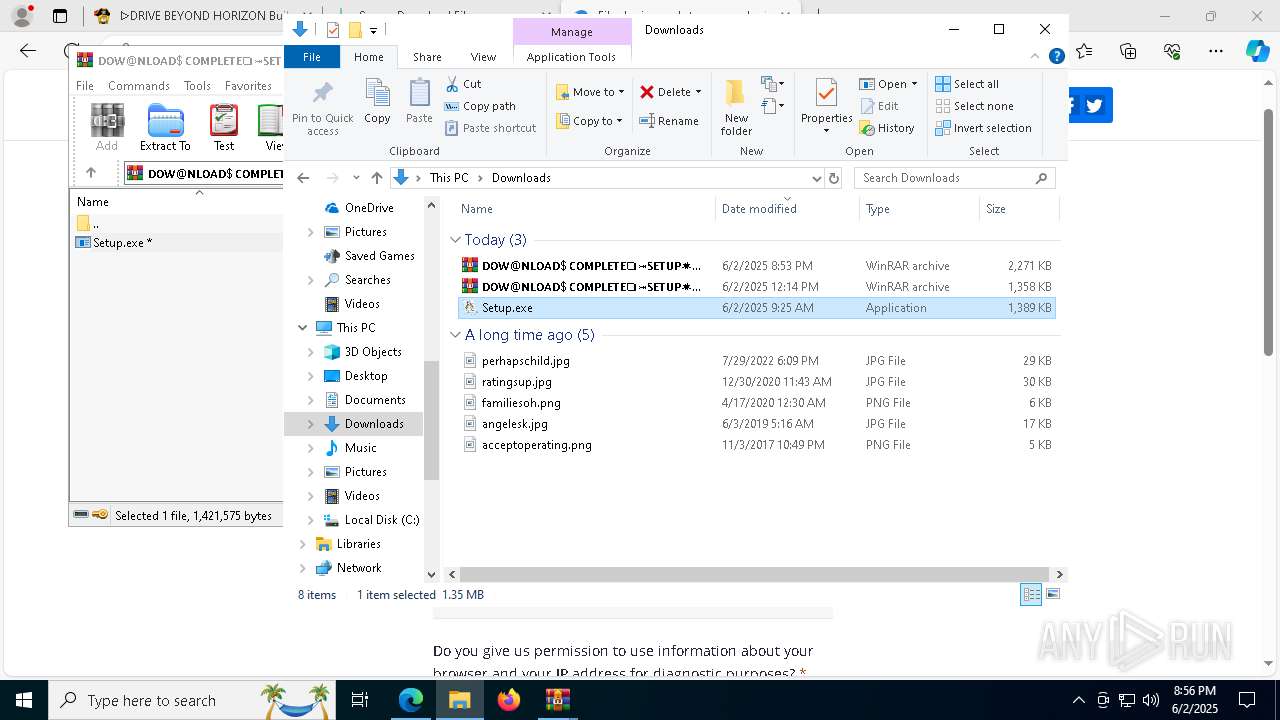
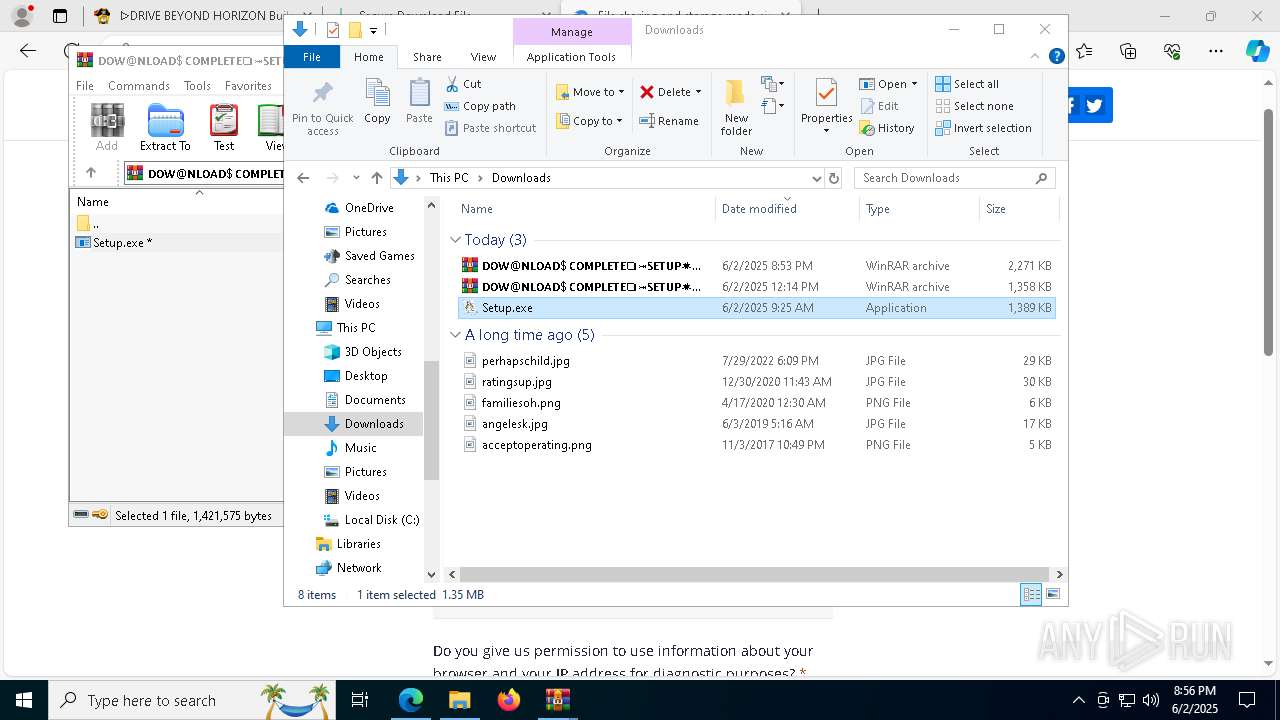
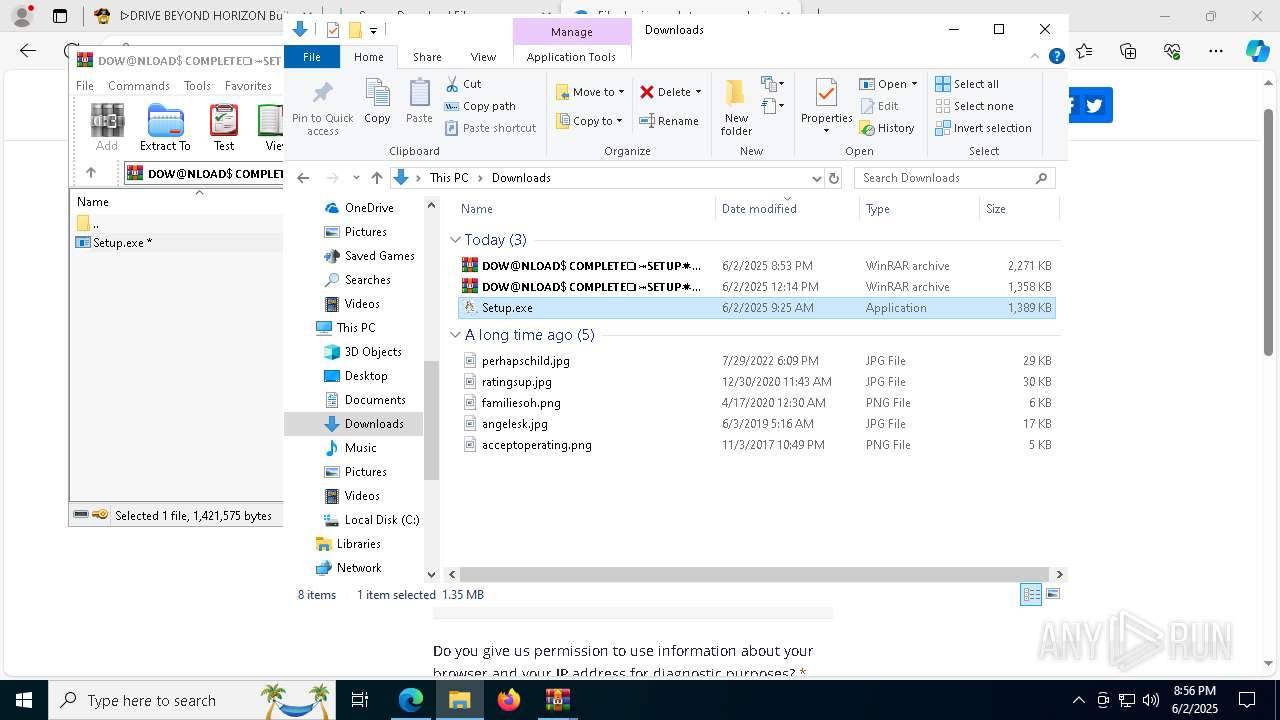
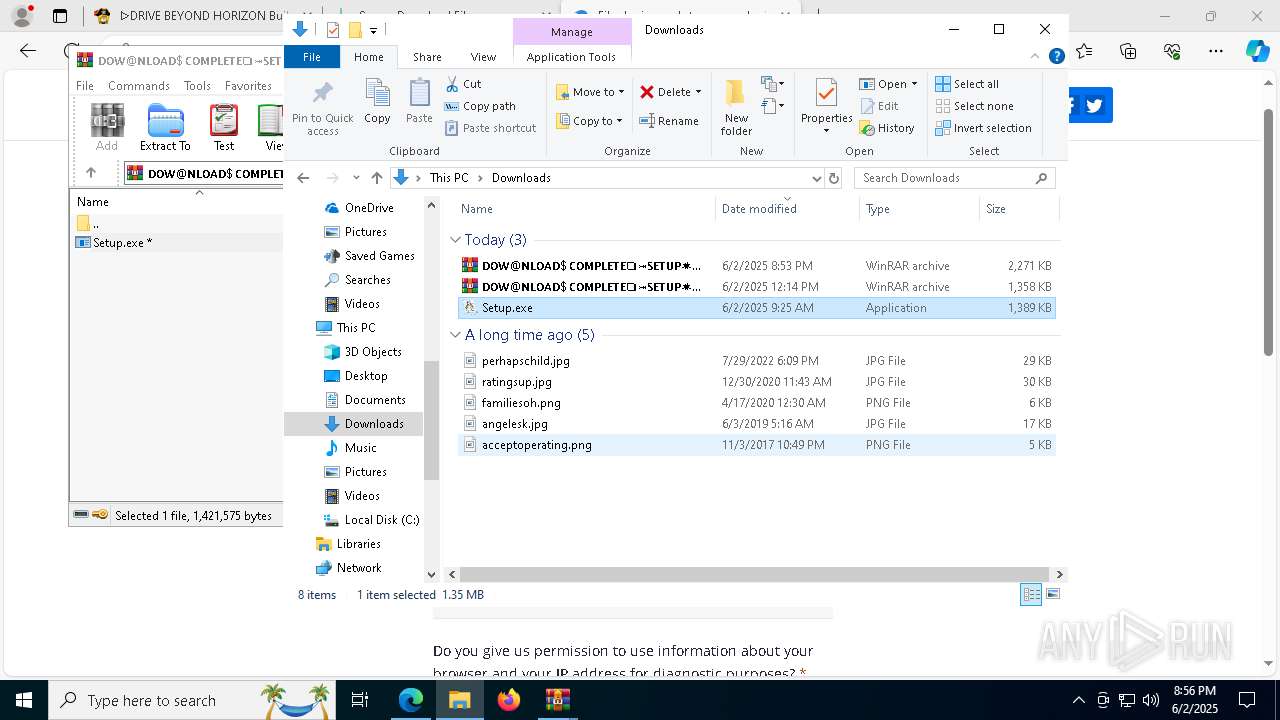
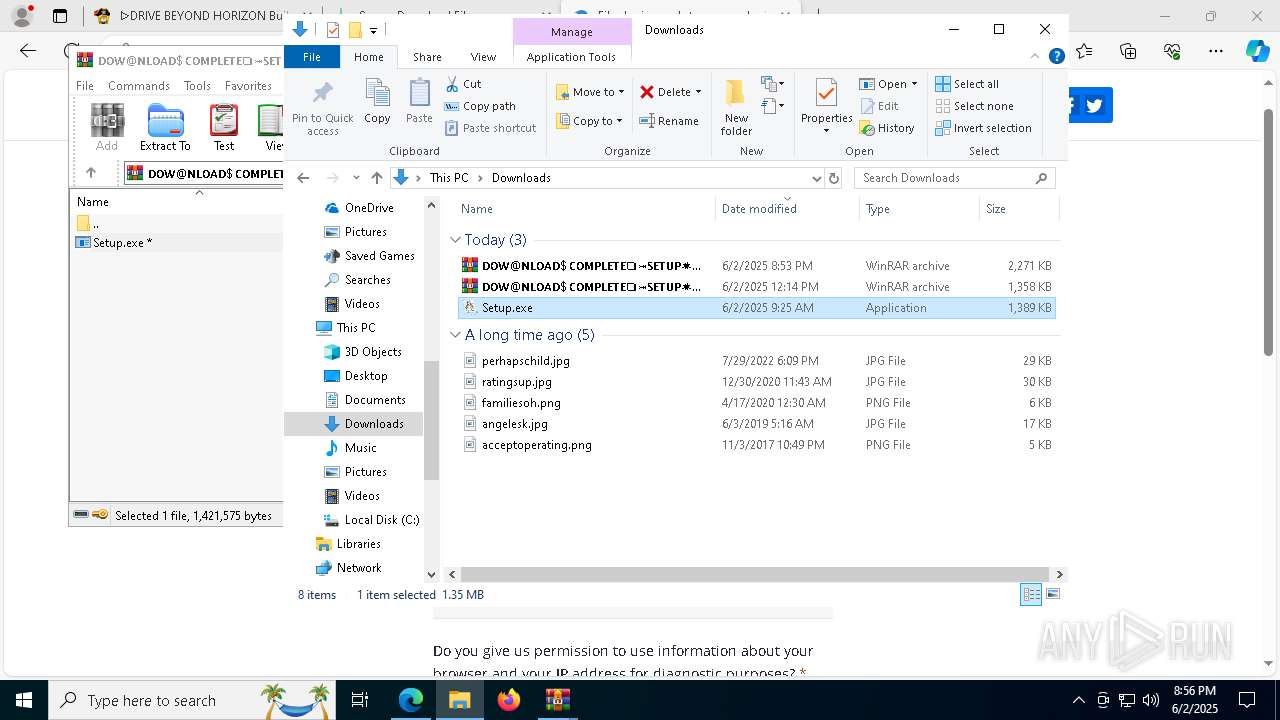
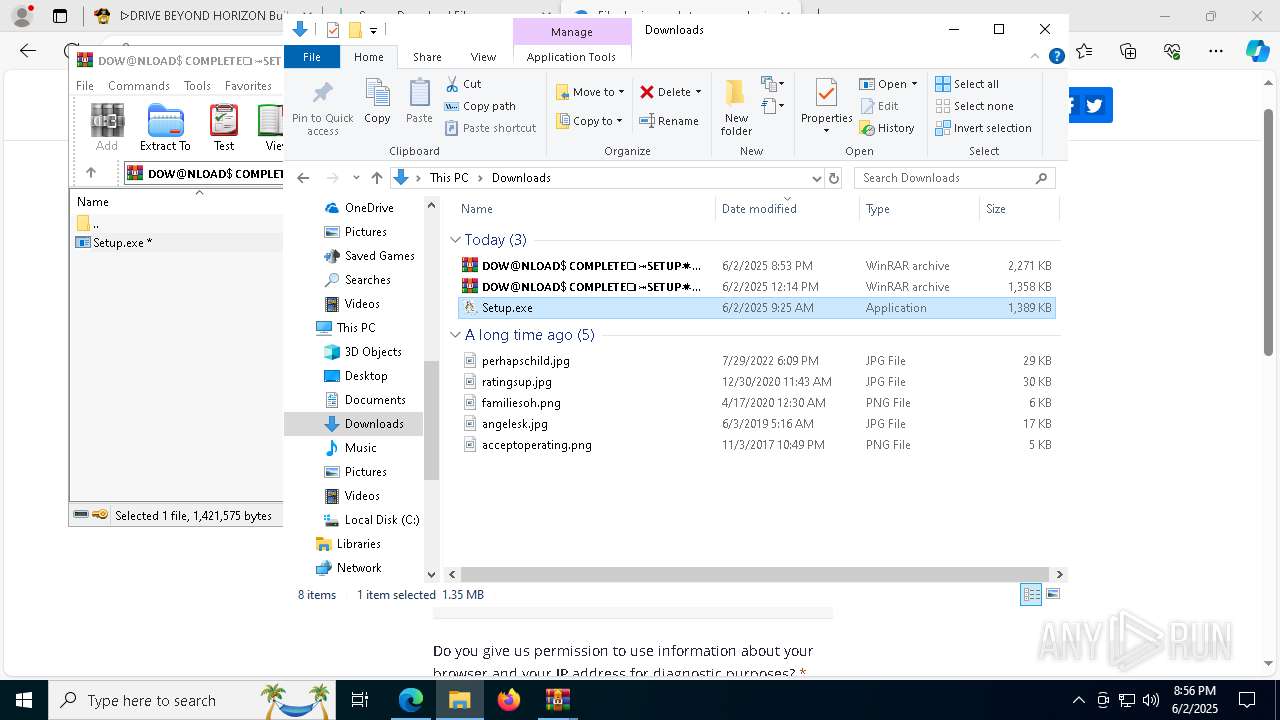
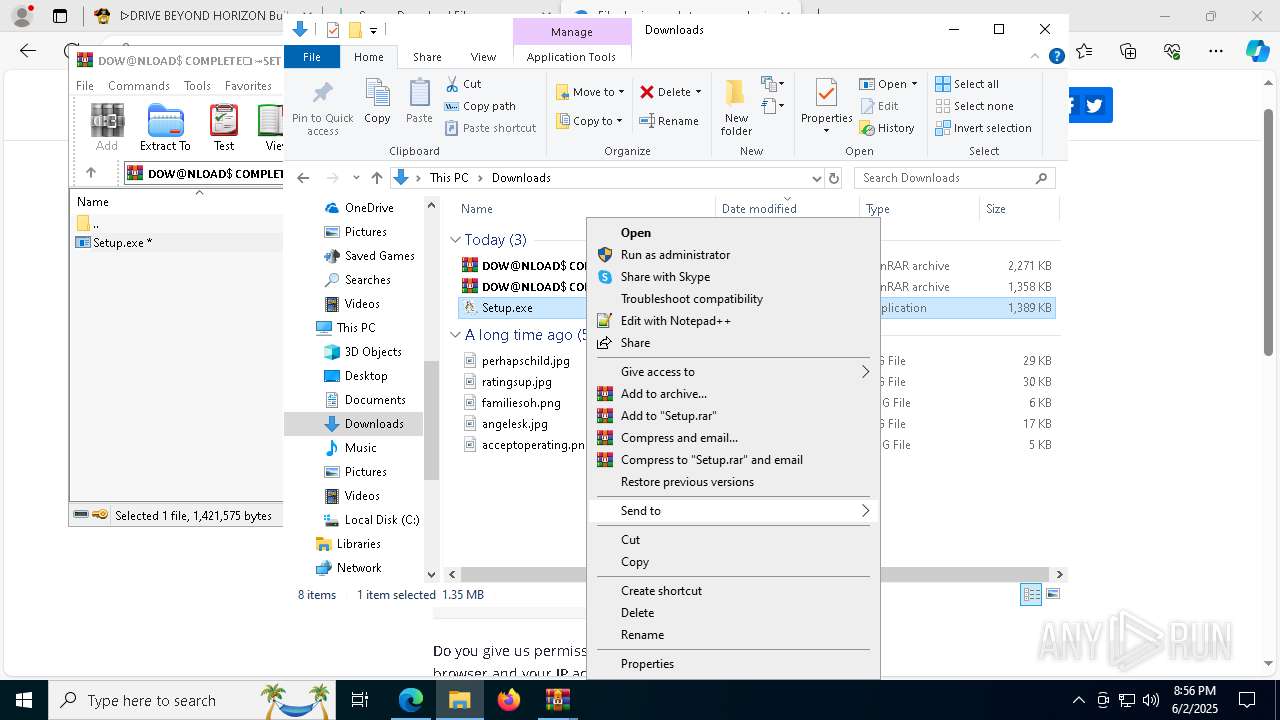
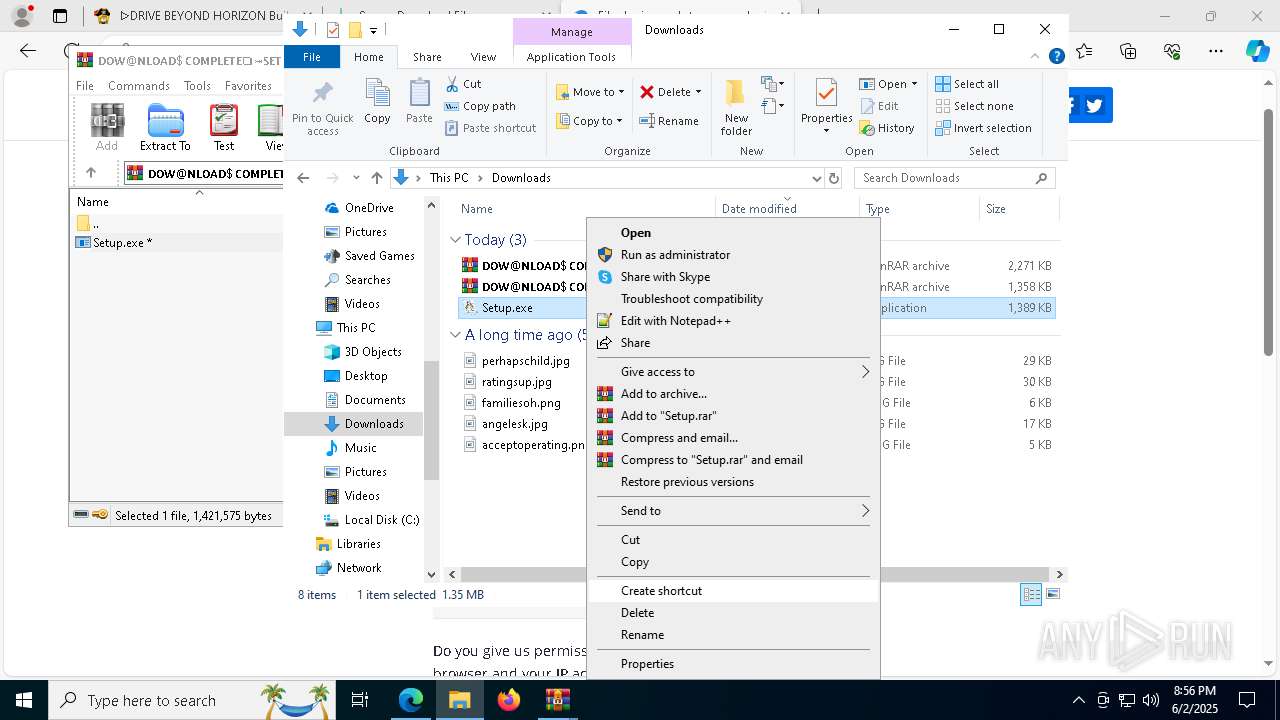
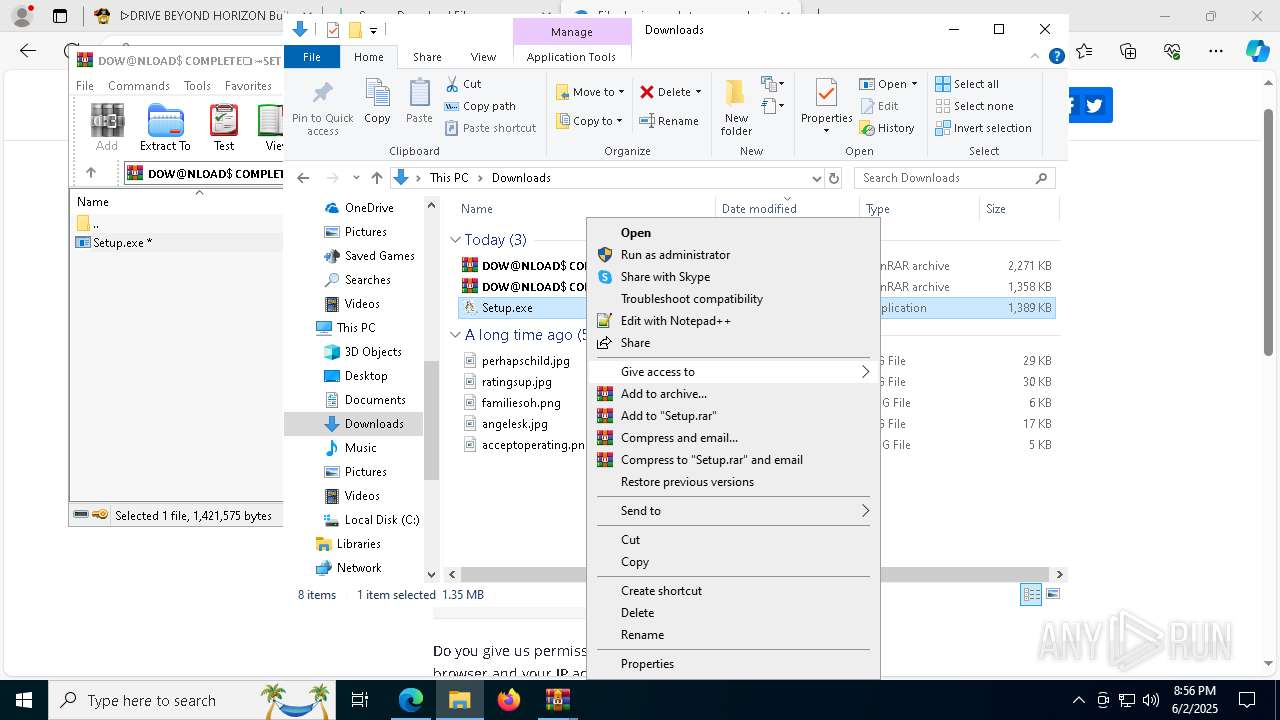
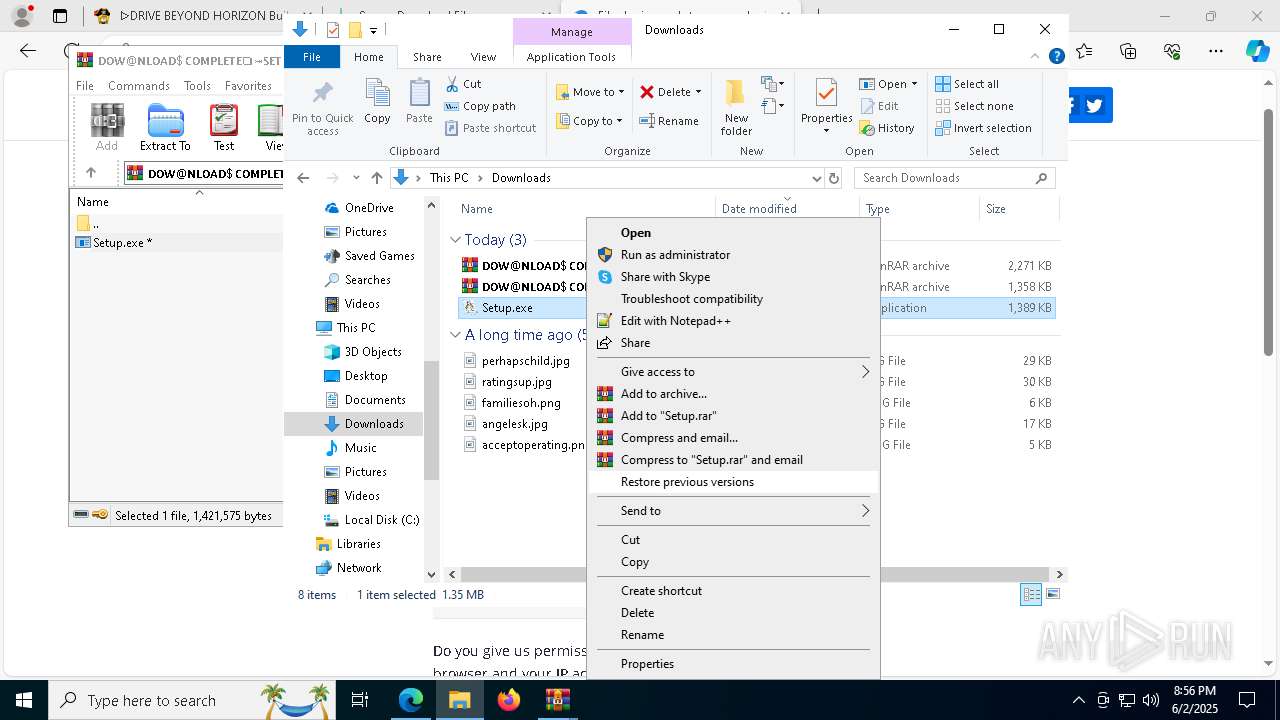
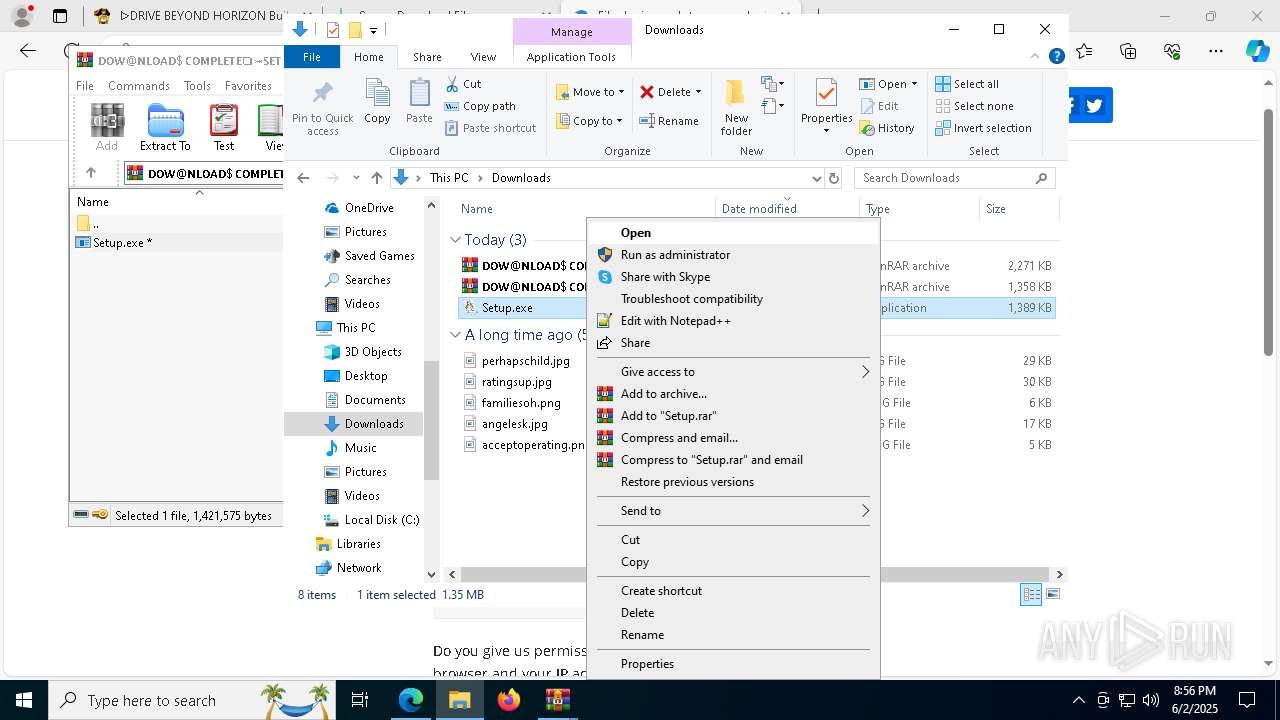
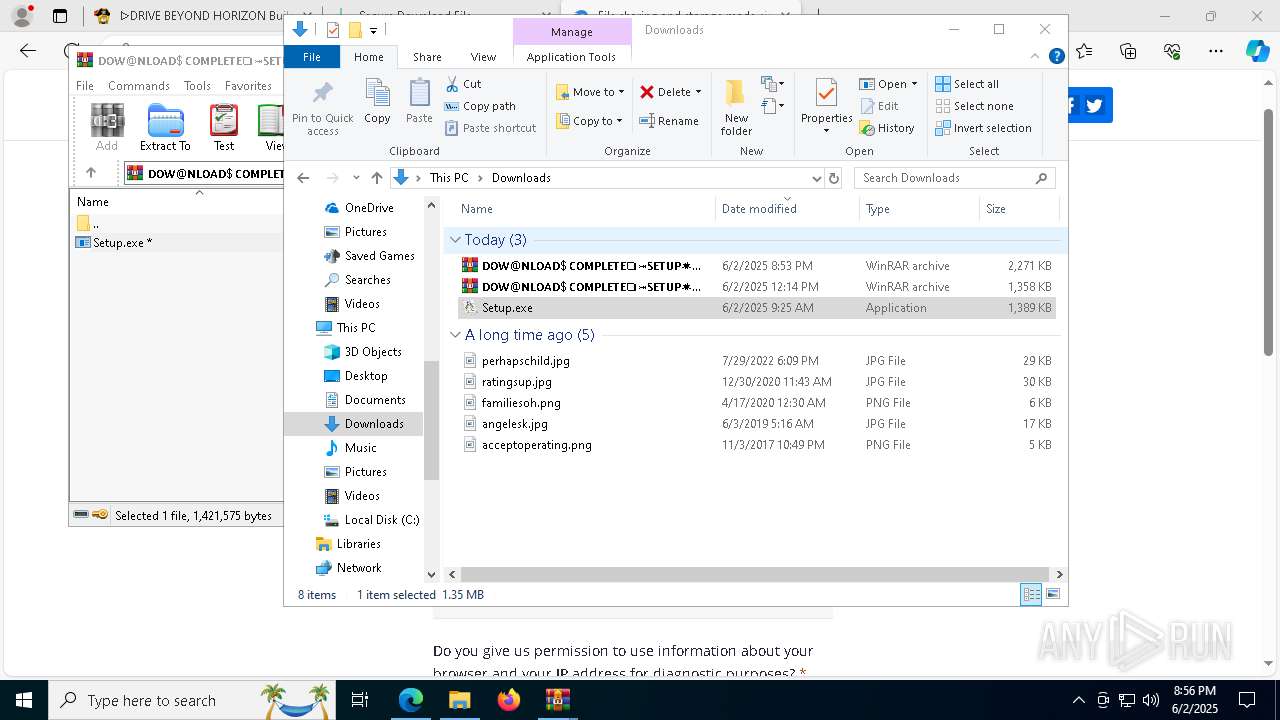
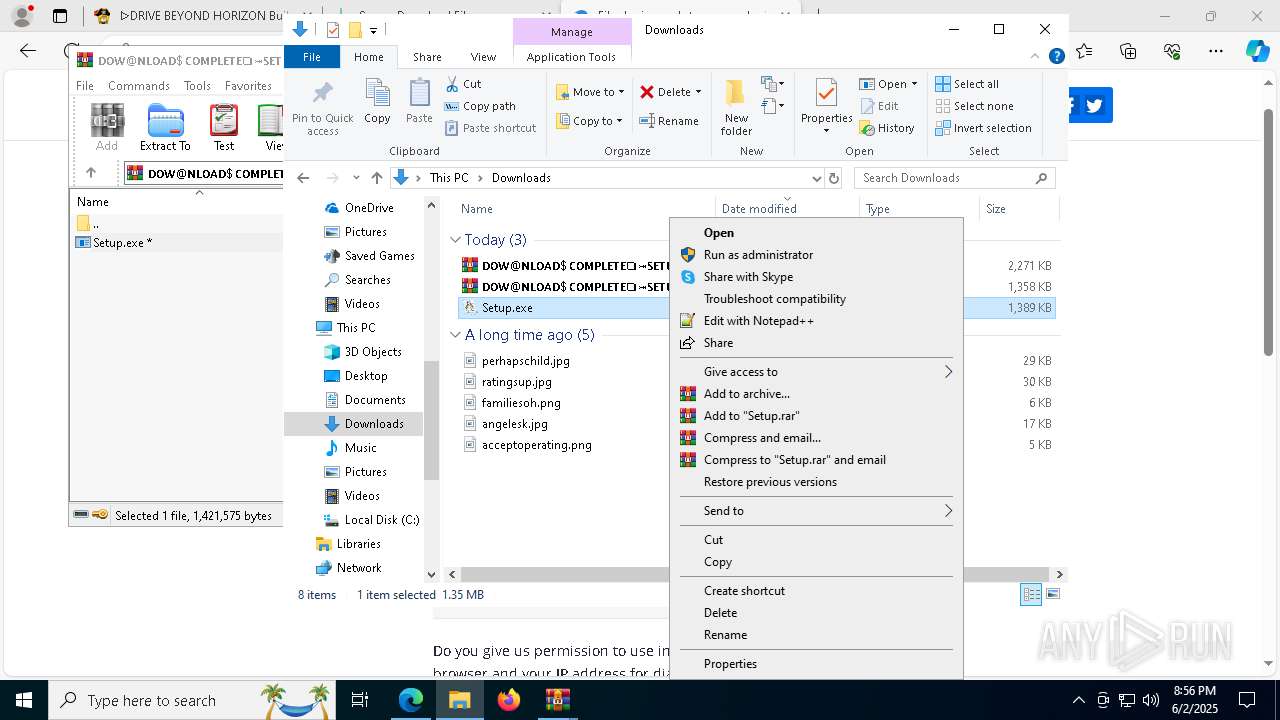
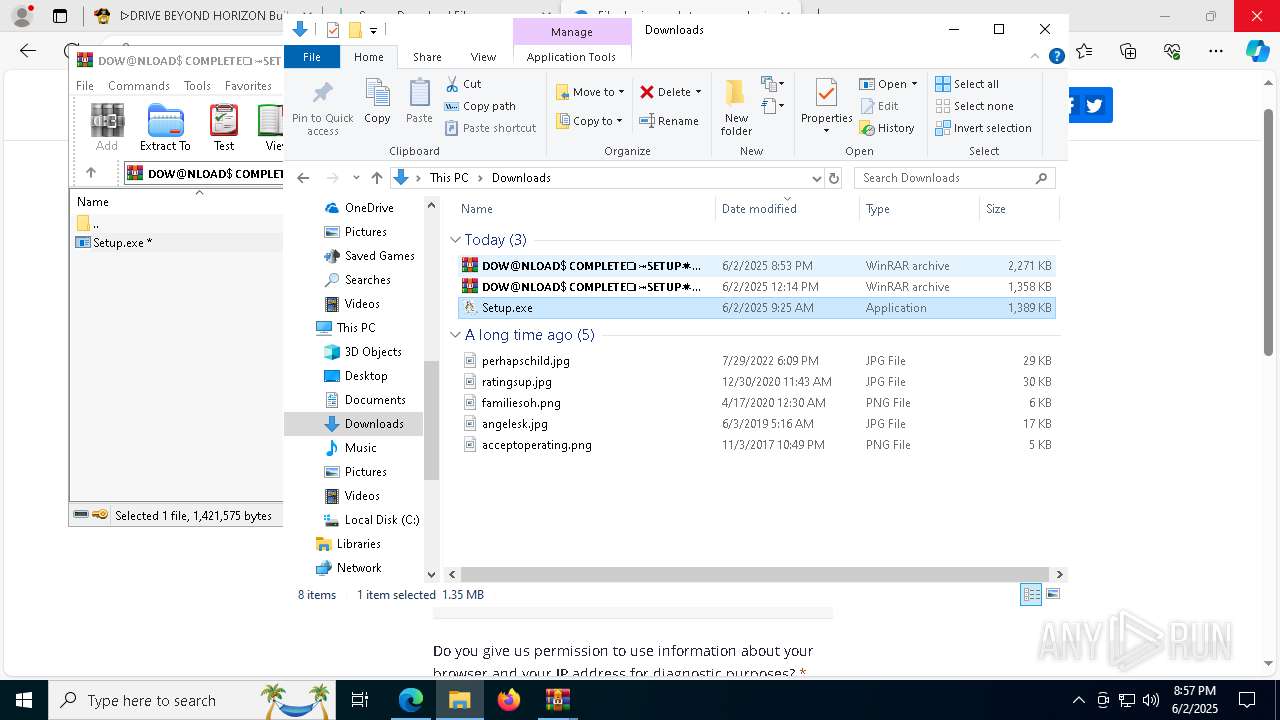
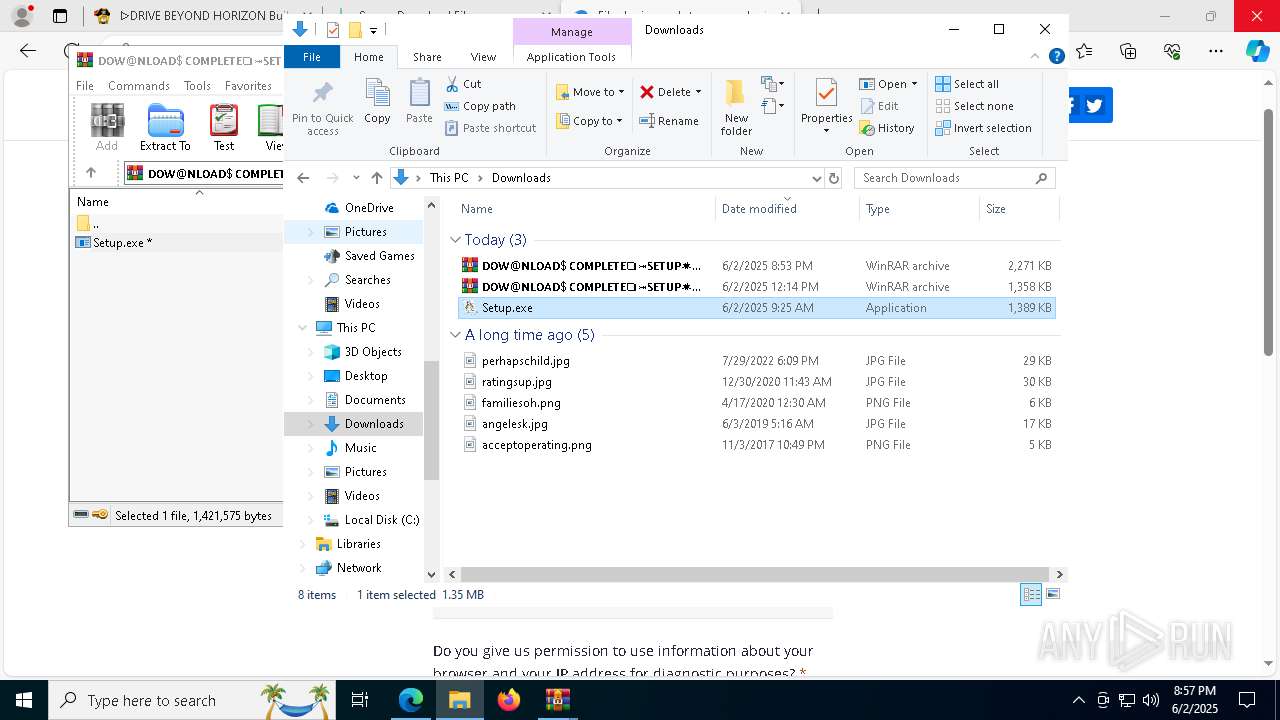
Launch of the file from Downloads directory
- msedge.exe (PID: 7632)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7632)
Reads the software policy settings
- slui.exe (PID: 1088)
Create files in a temporary directory
- Setup.exe (PID: 8960)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1696)
- msedge.exe (PID: 9564)
Process checks computer location settings
- Setup.exe (PID: 8960)
Manual execution by a user
- OOBE-Maintenance.exe (PID: 8588)
- OOBE-Maintenance.exe (PID: 656)
- Setup.exe (PID: 7928)
- Setup.exe (PID: 9776)
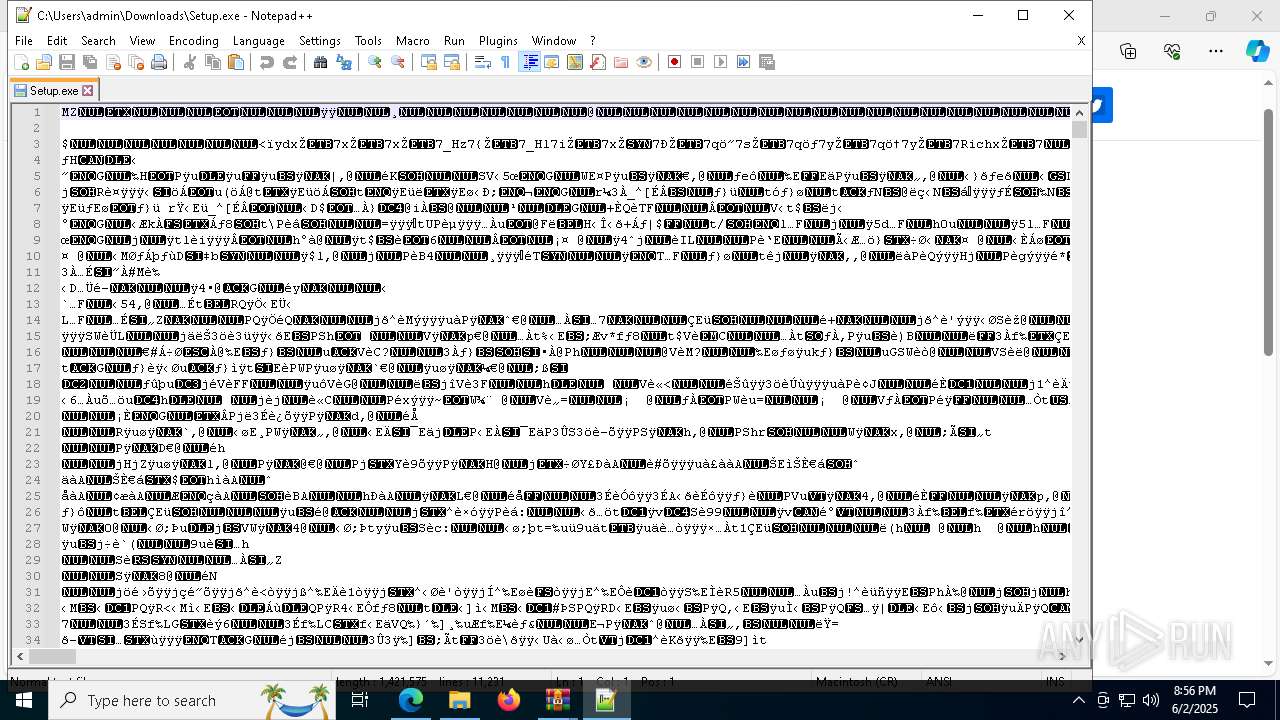
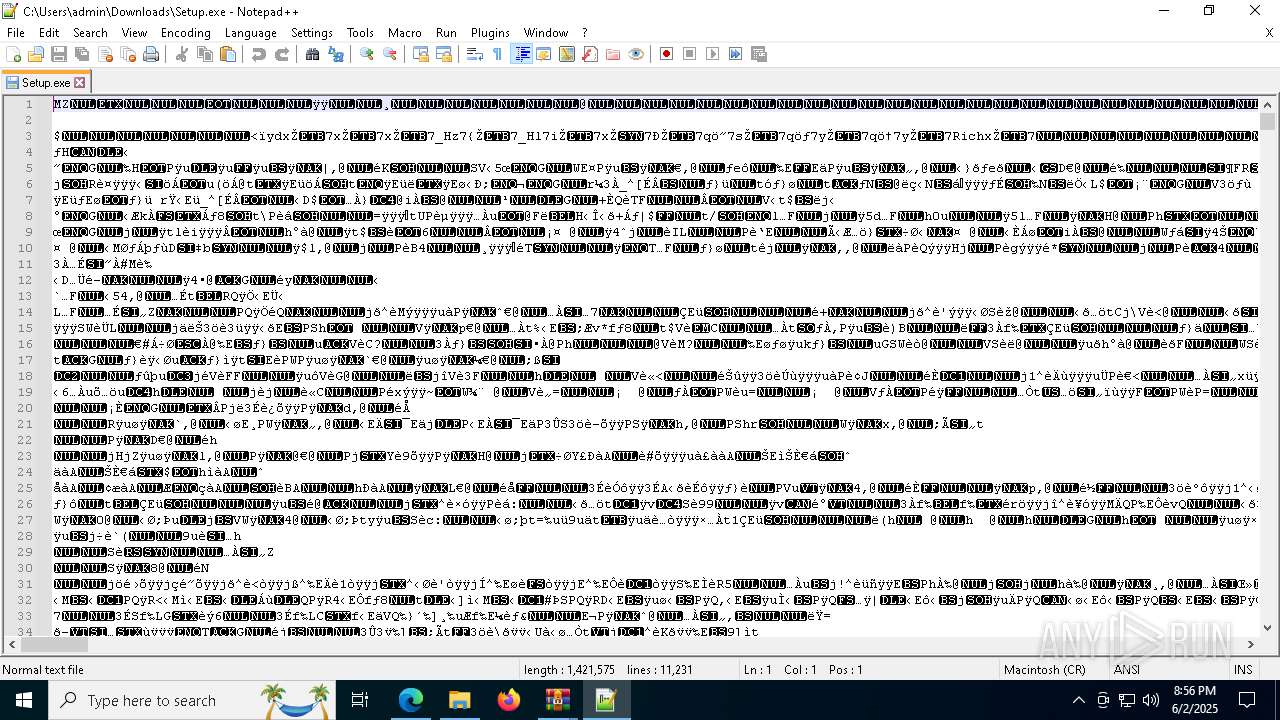
- notepad++.exe (PID: 3028)
- OOBE-Maintenance.exe (PID: 8064)
The sample compiled with english language support
- msedge.exe (PID: 9564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
337
Monitored processes
193
Malicious processes
18
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 656 | "C:\WINDOWS\system32\OOBE-Maintenance.exe" | C:\Windows\System32\OOBE-Maintenance.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: OOBE-Maintenance Exit code: 3221226356 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | findstr /V "Folders" Woman | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4308 --field-trial-handle=2236,i,4192248501089552282,8726606824296981027,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
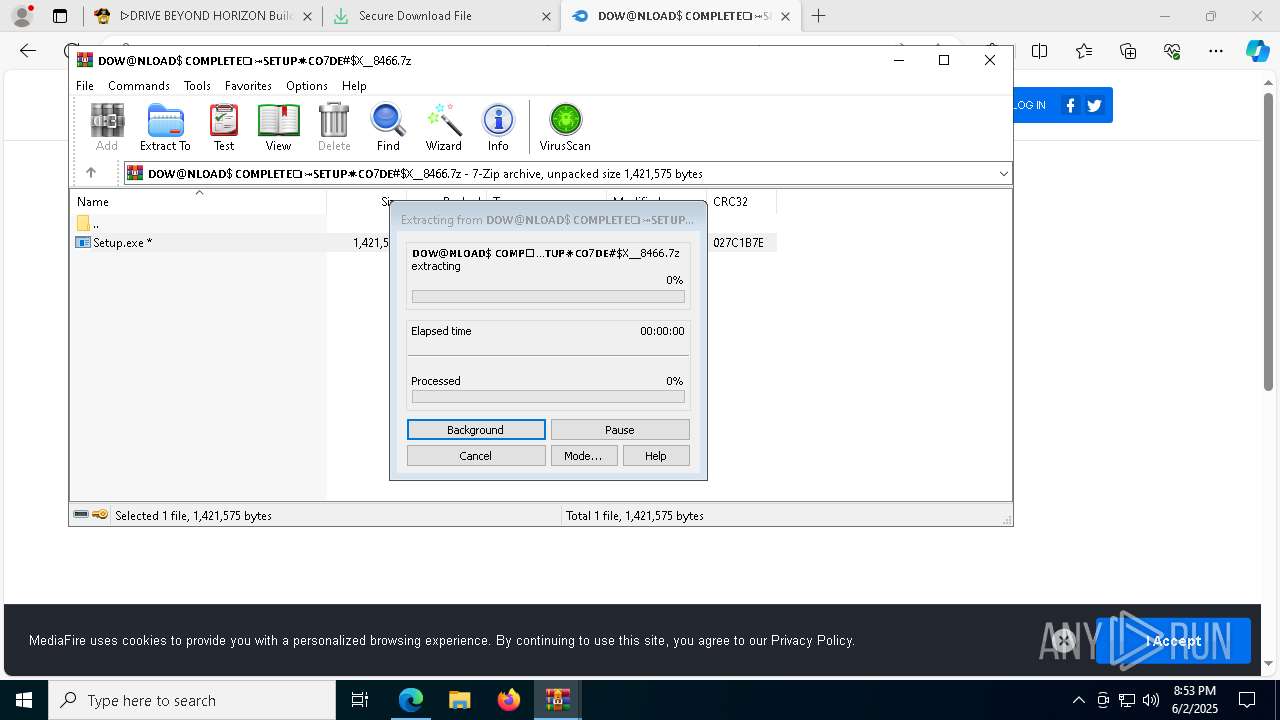
| 864 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb1696.46906\Setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb1696.46906\Setup.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1012 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | OOBE-Maintenance.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6264 --field-trial-handle=2236,i,4192248501089552282,8726606824296981027,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1312 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1504 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4764 --field-trial-handle=2236,i,4192248501089552282,8726606824296981027,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
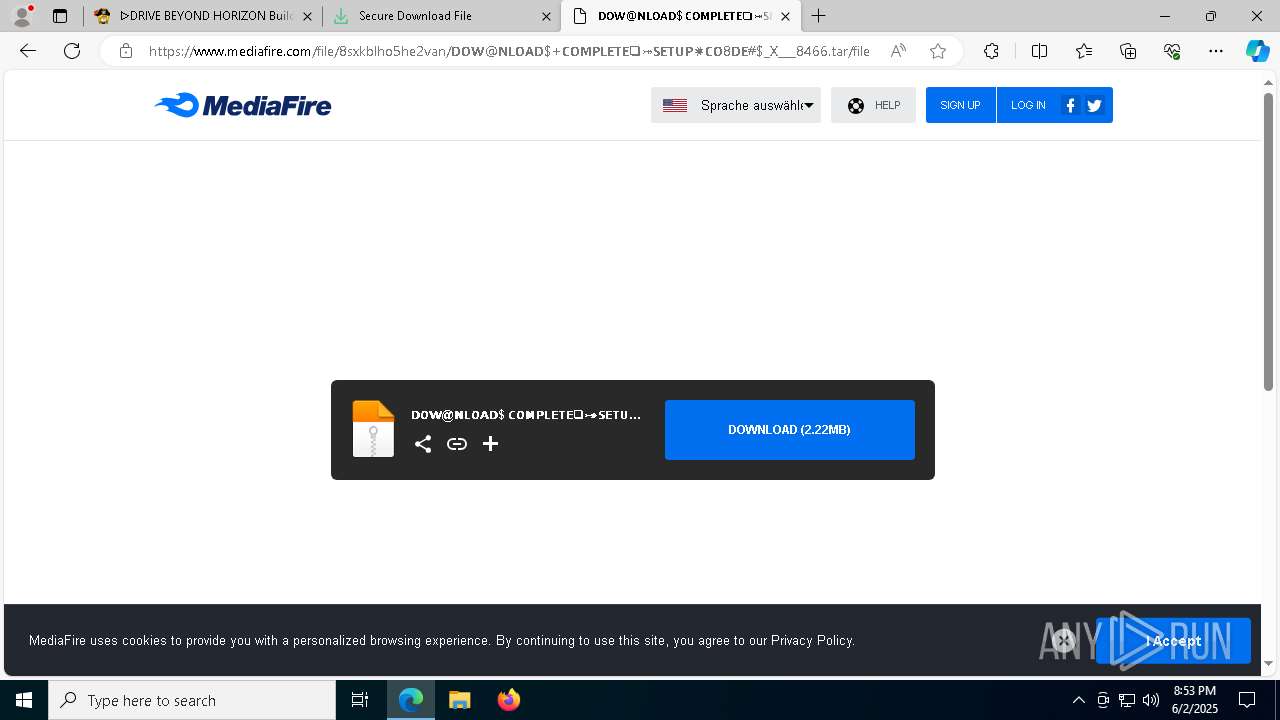
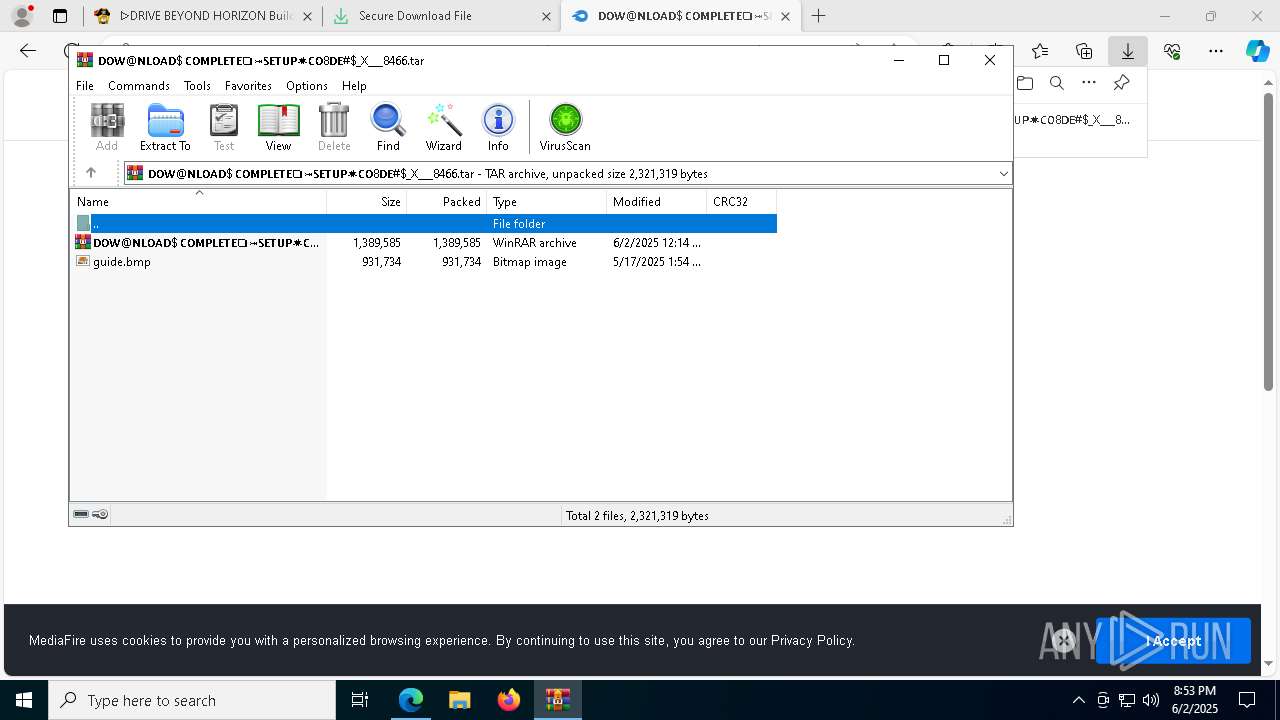
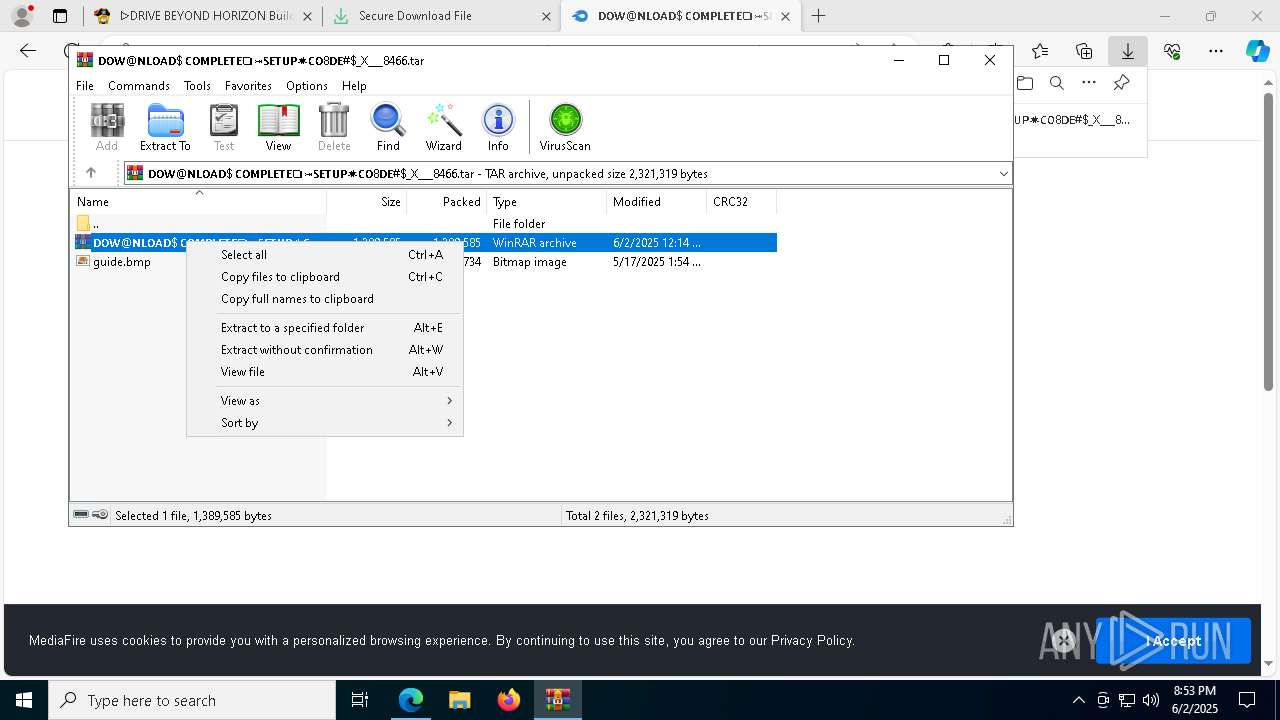
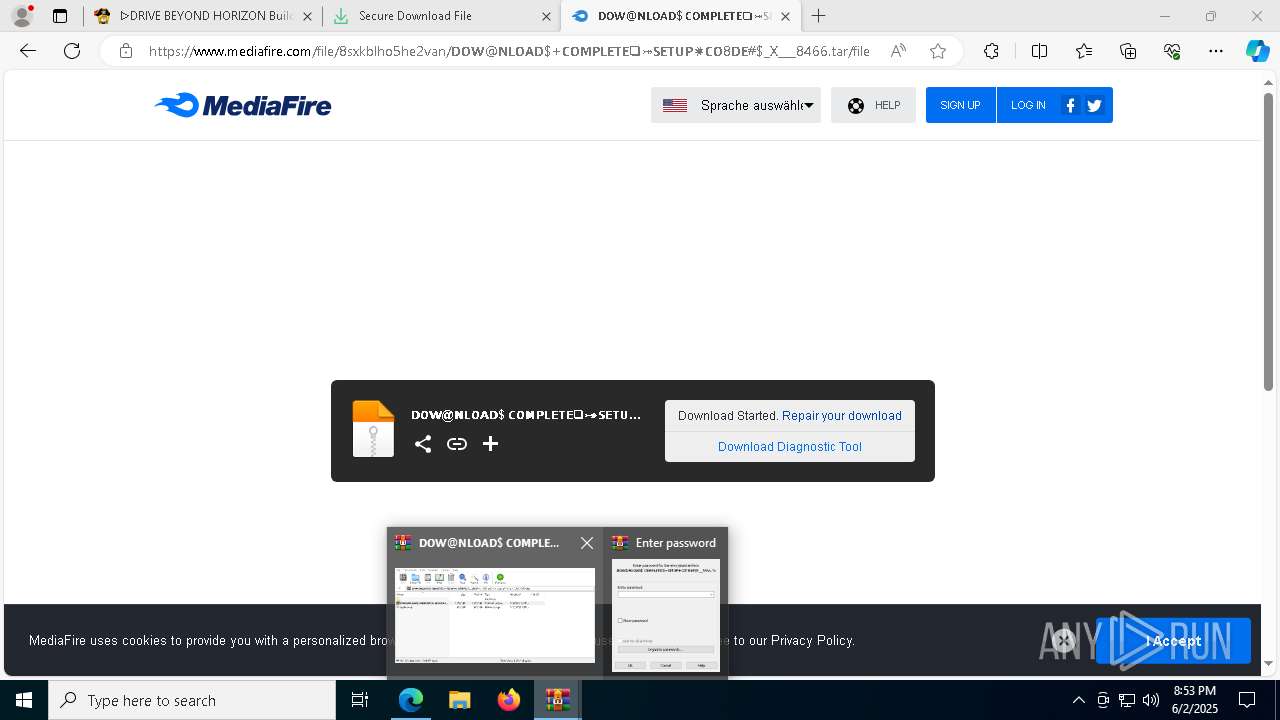
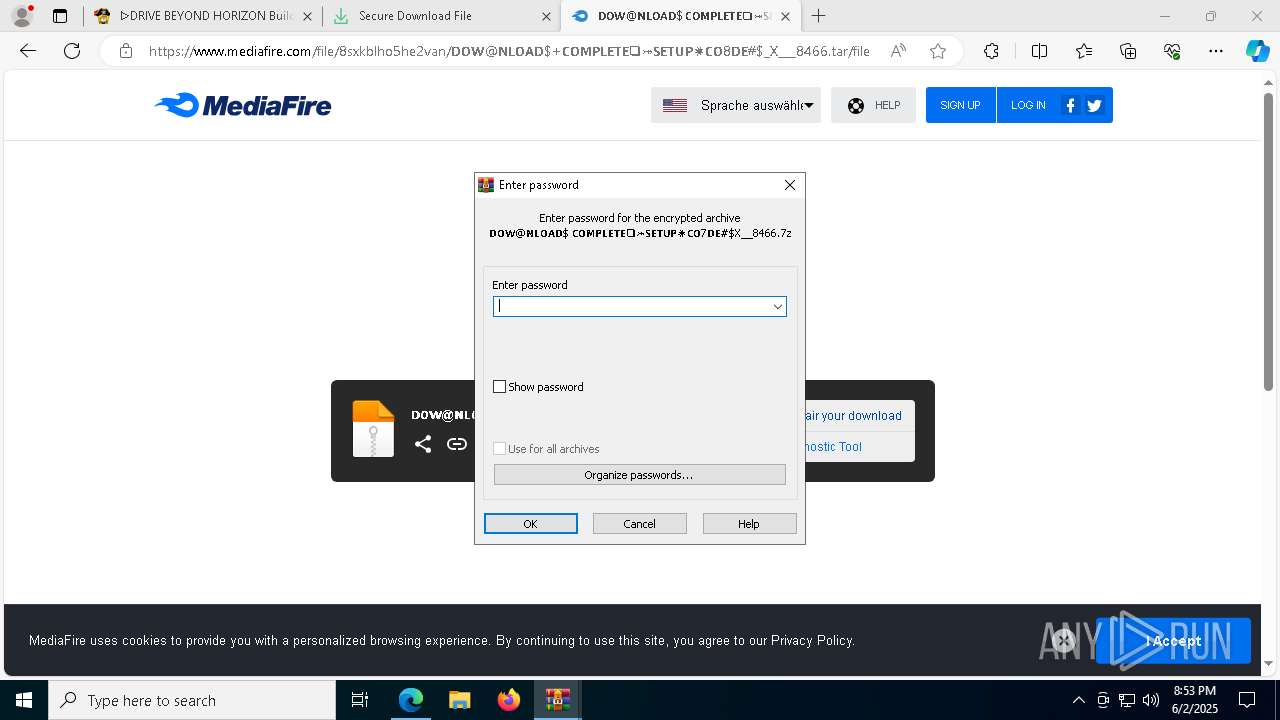
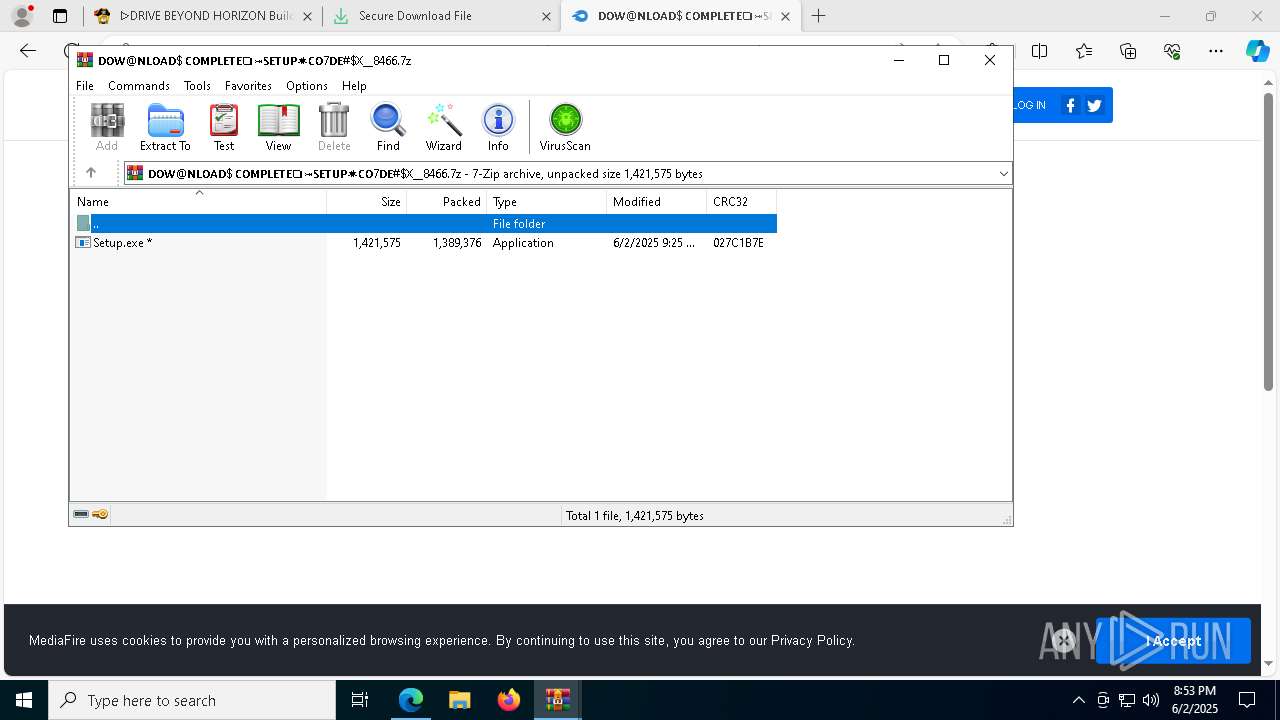
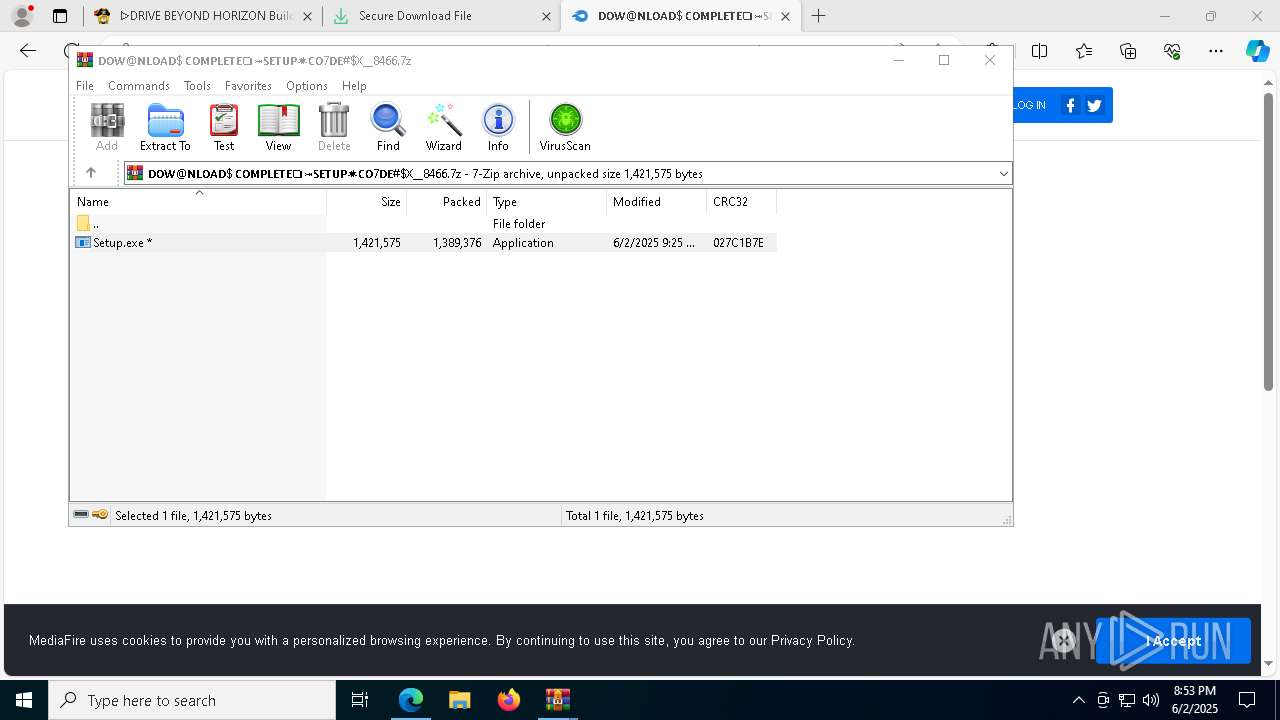
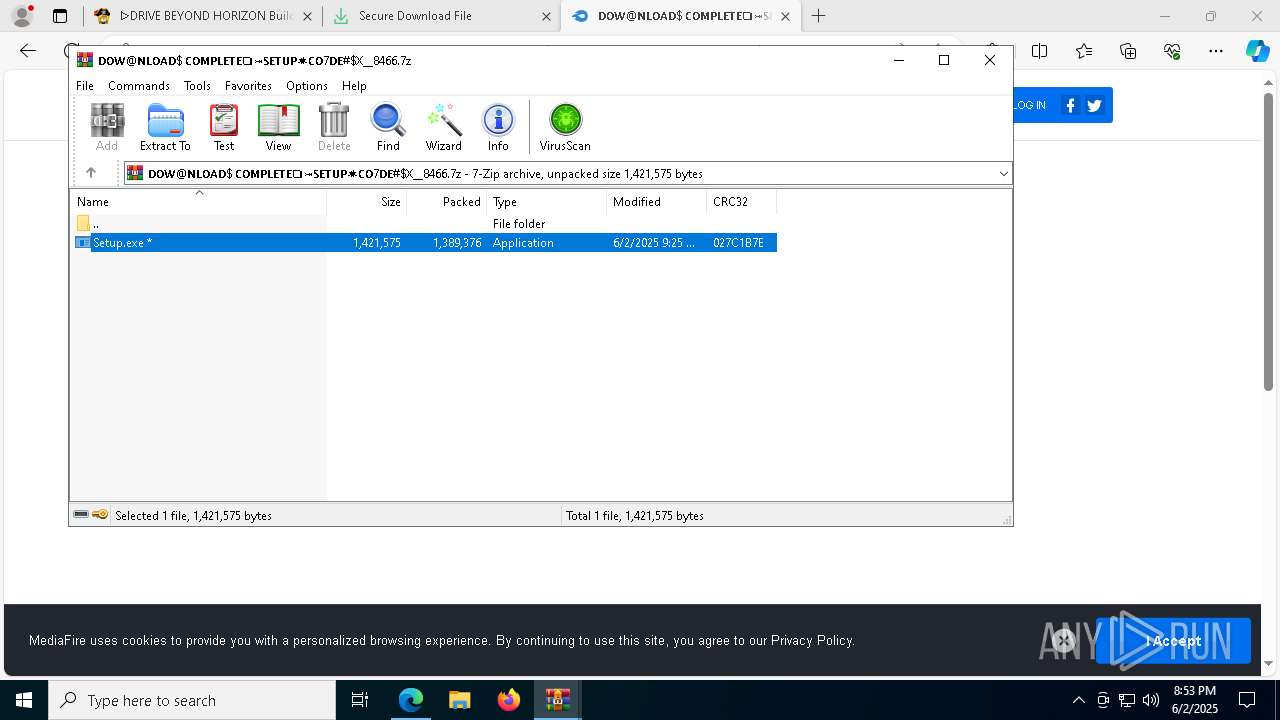
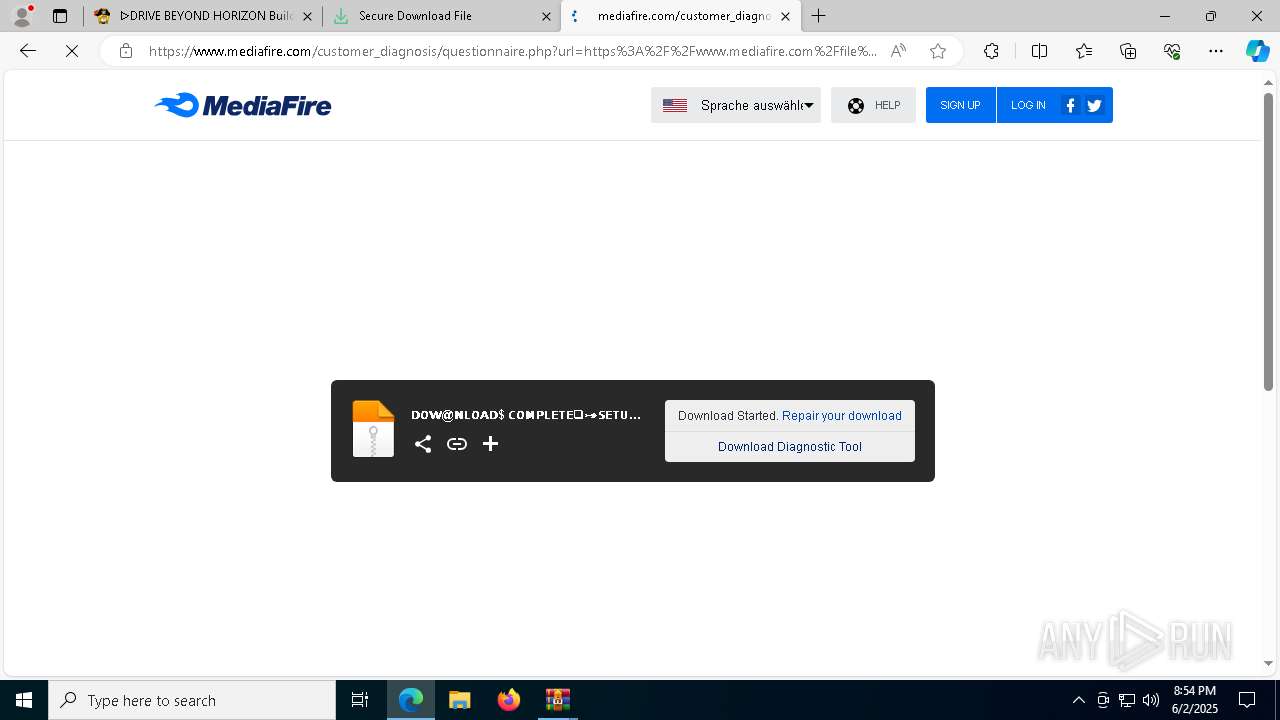
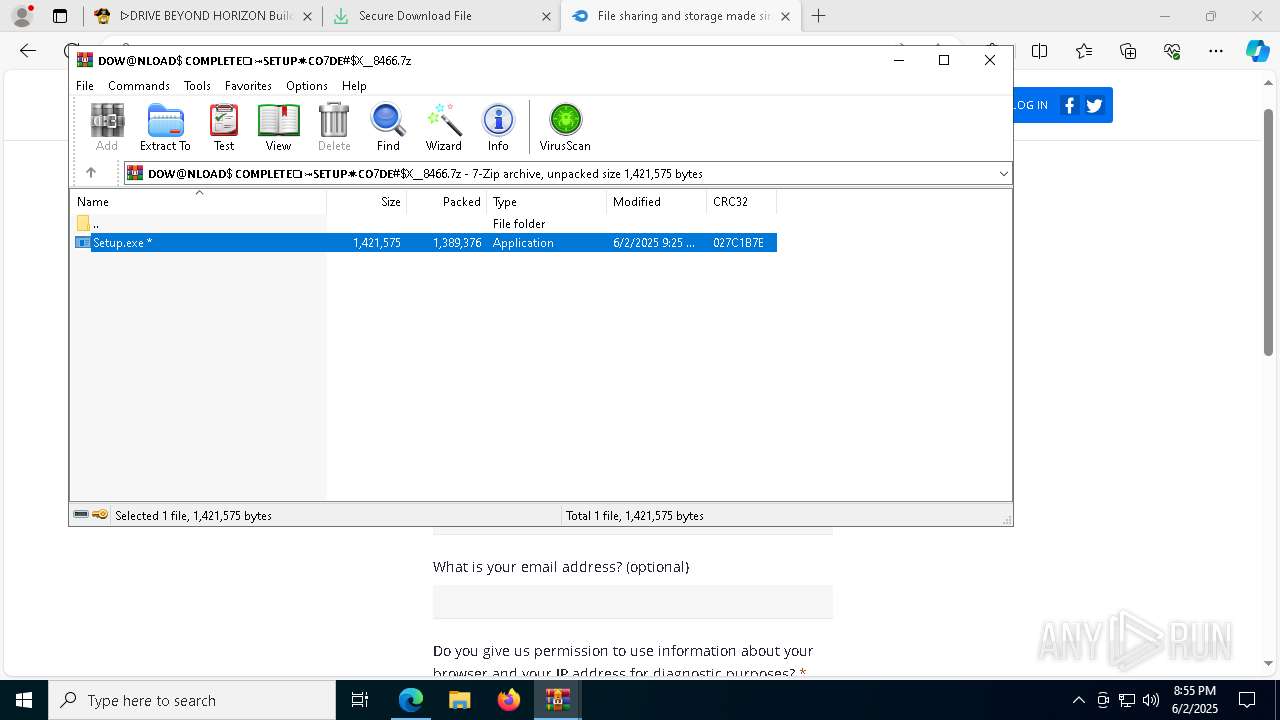
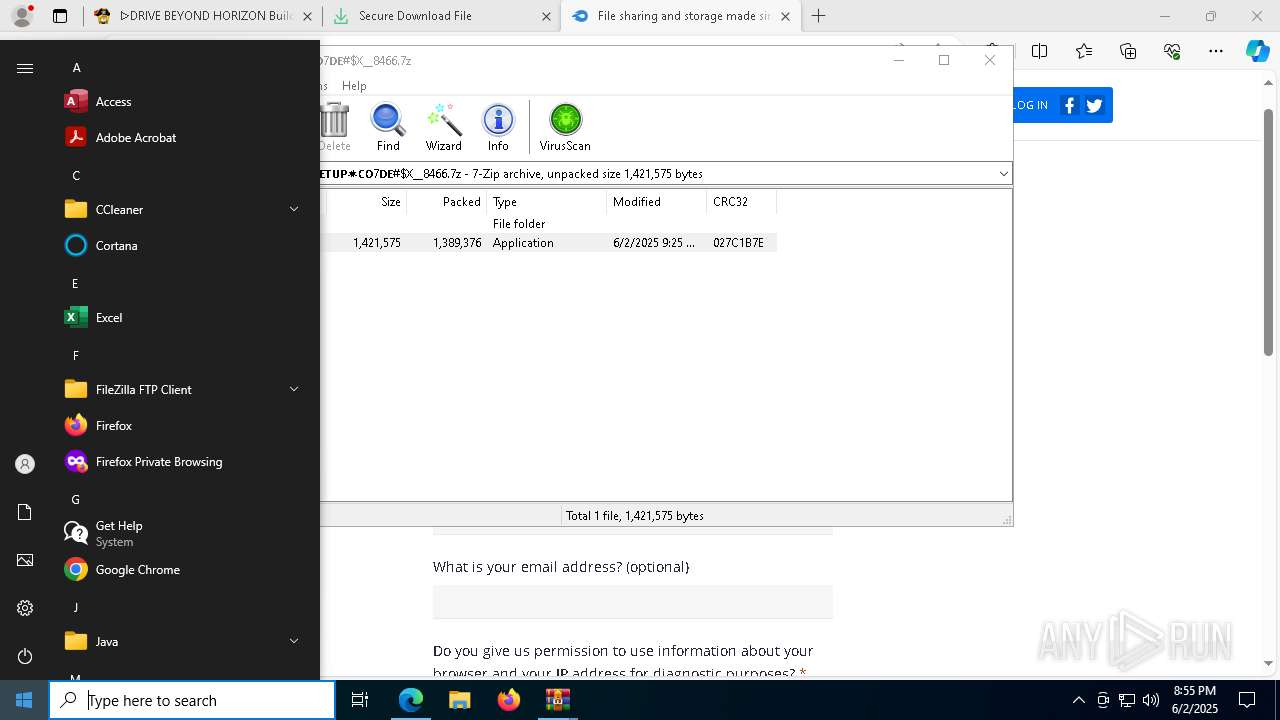
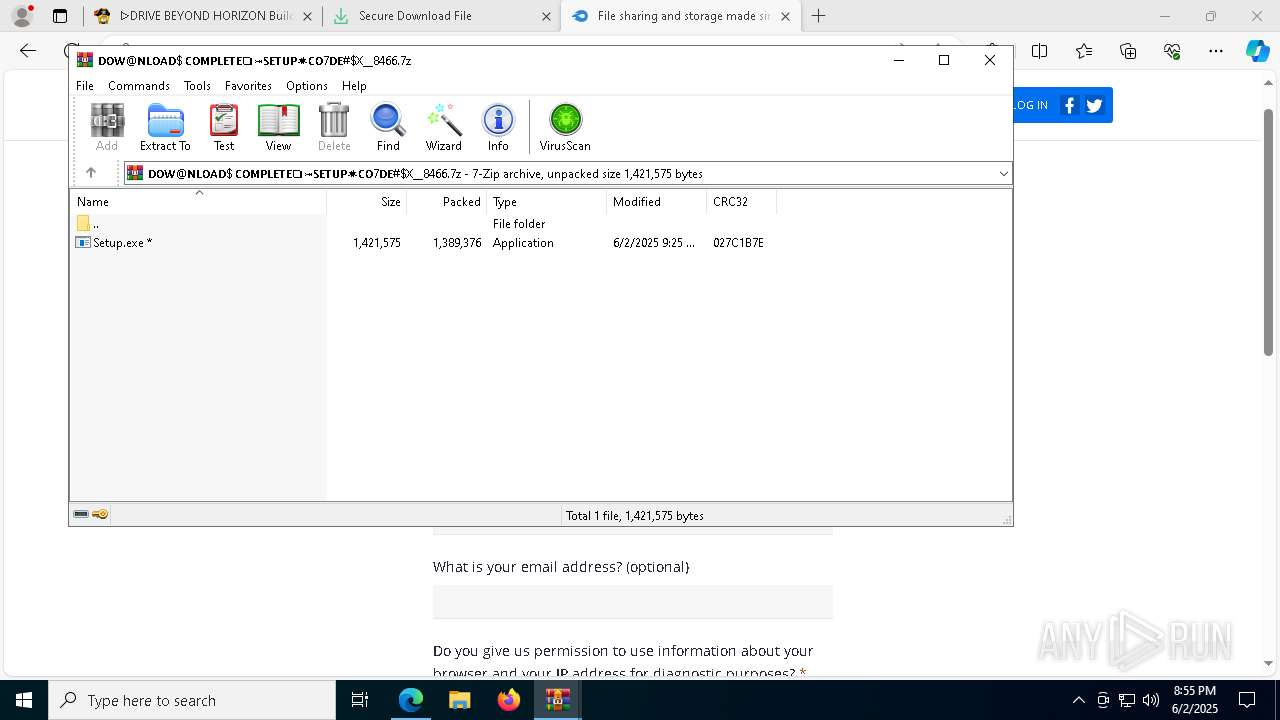
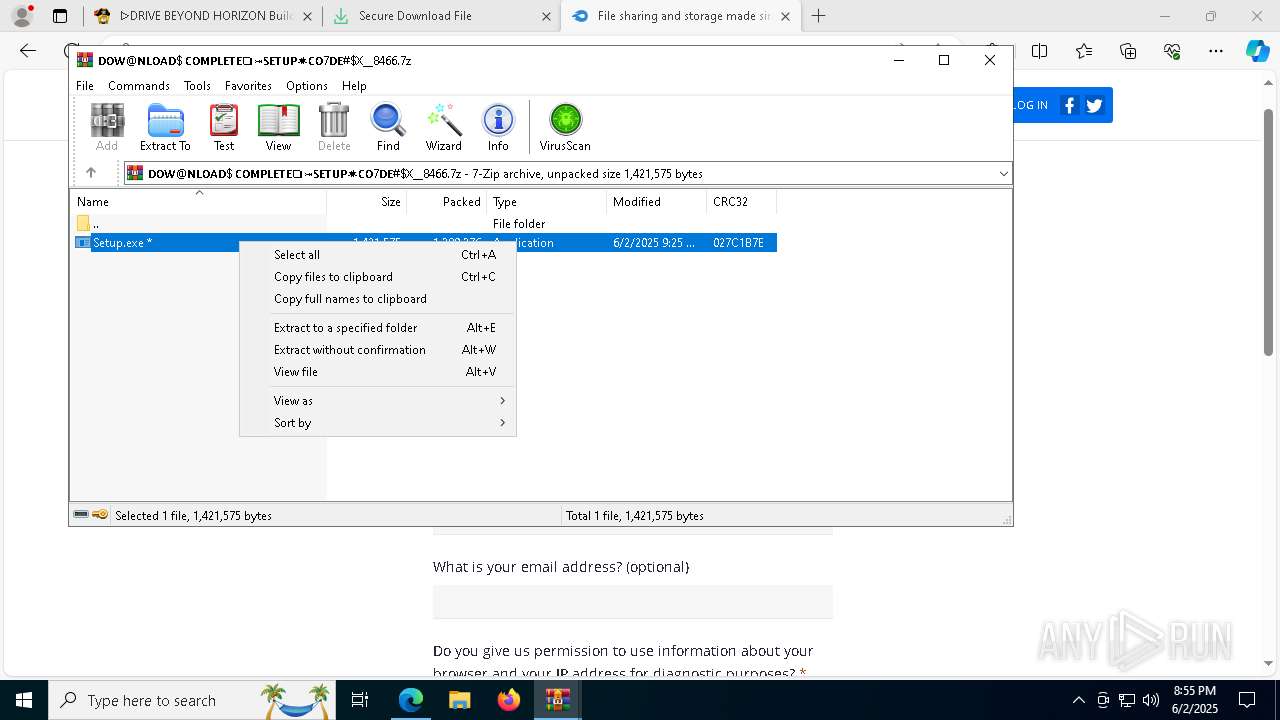
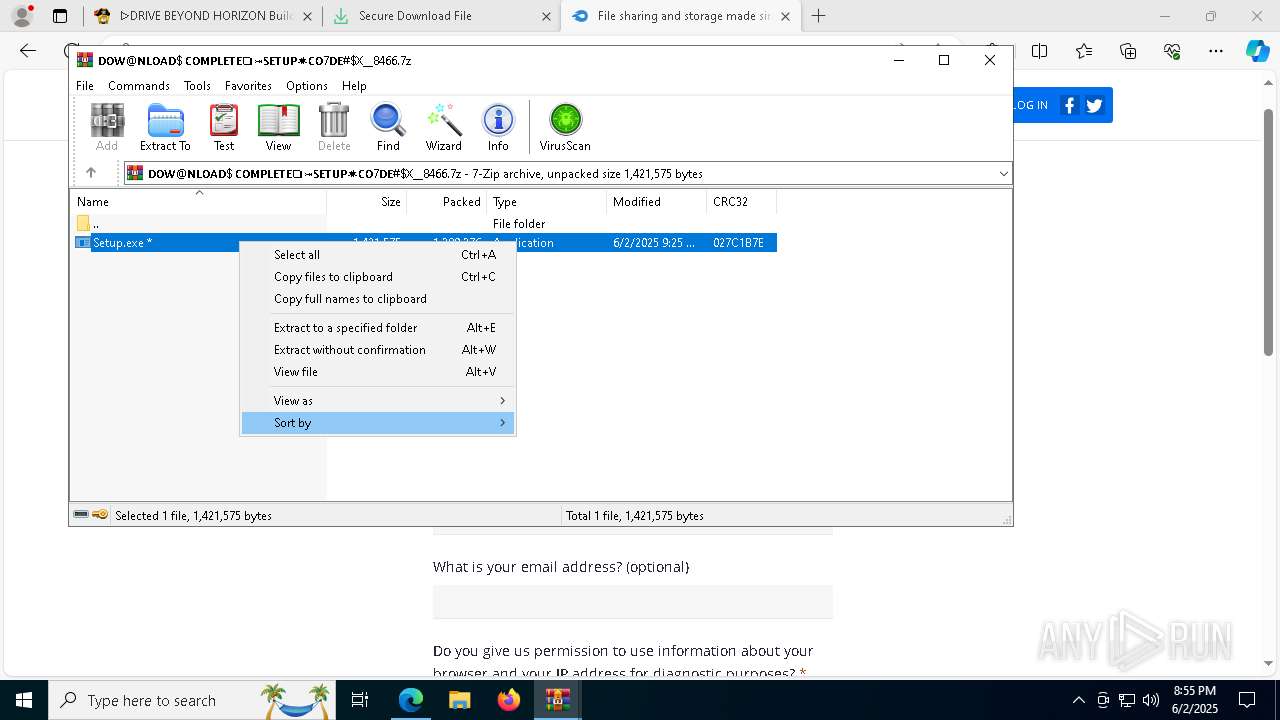
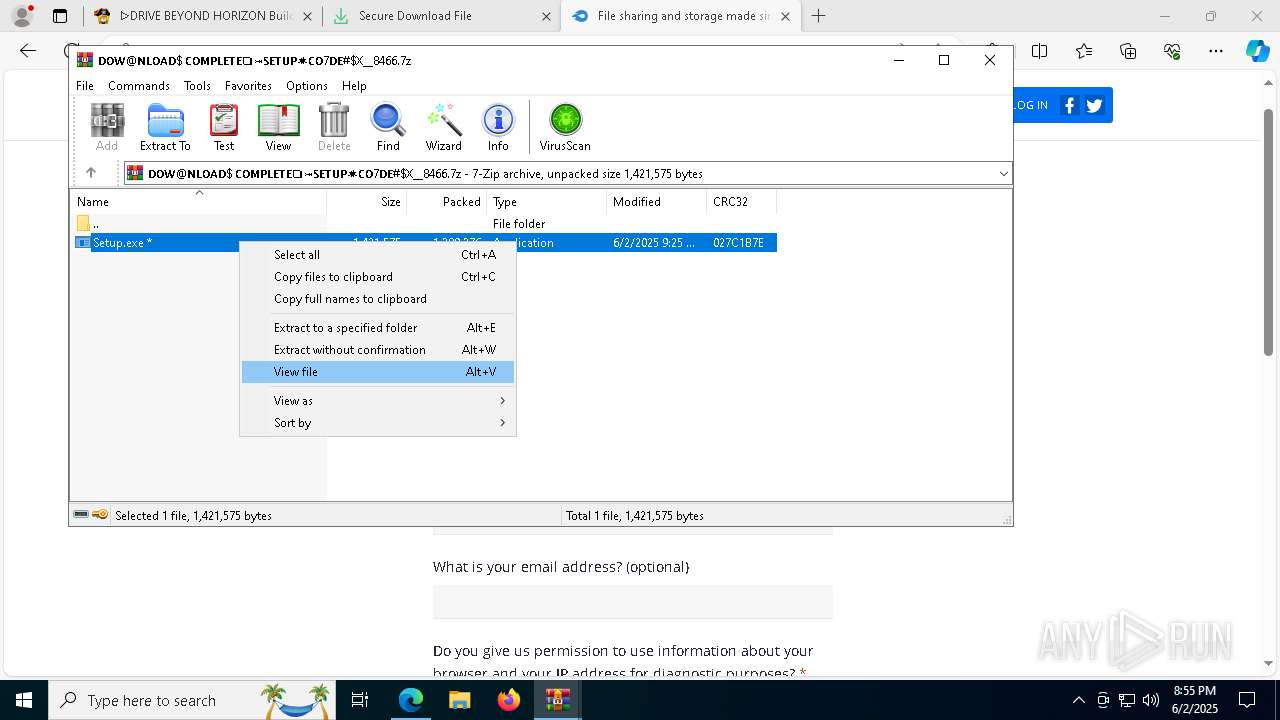
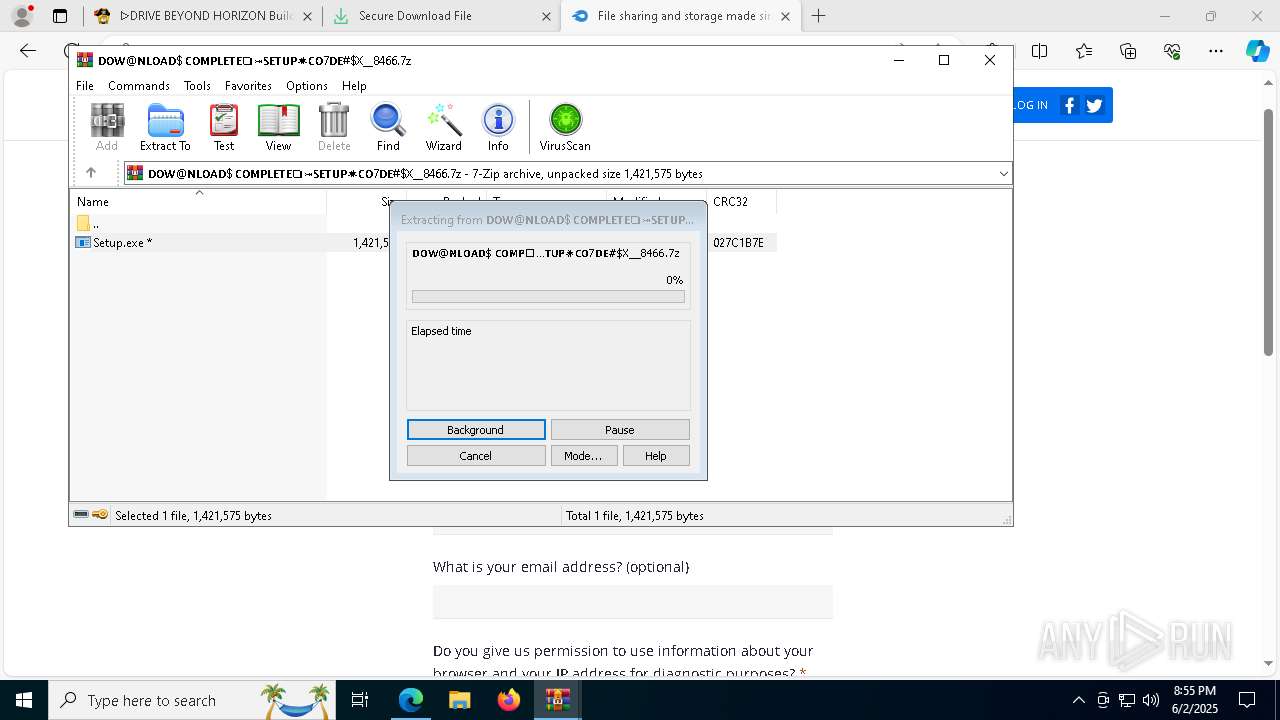
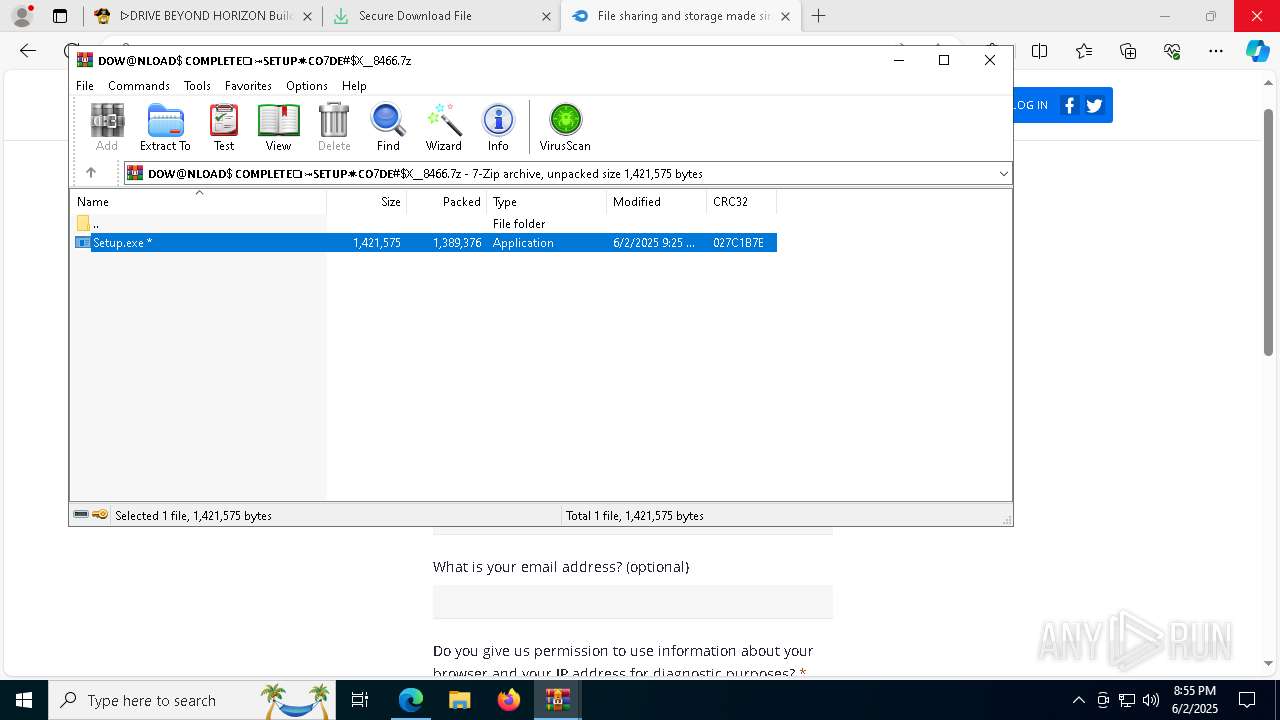
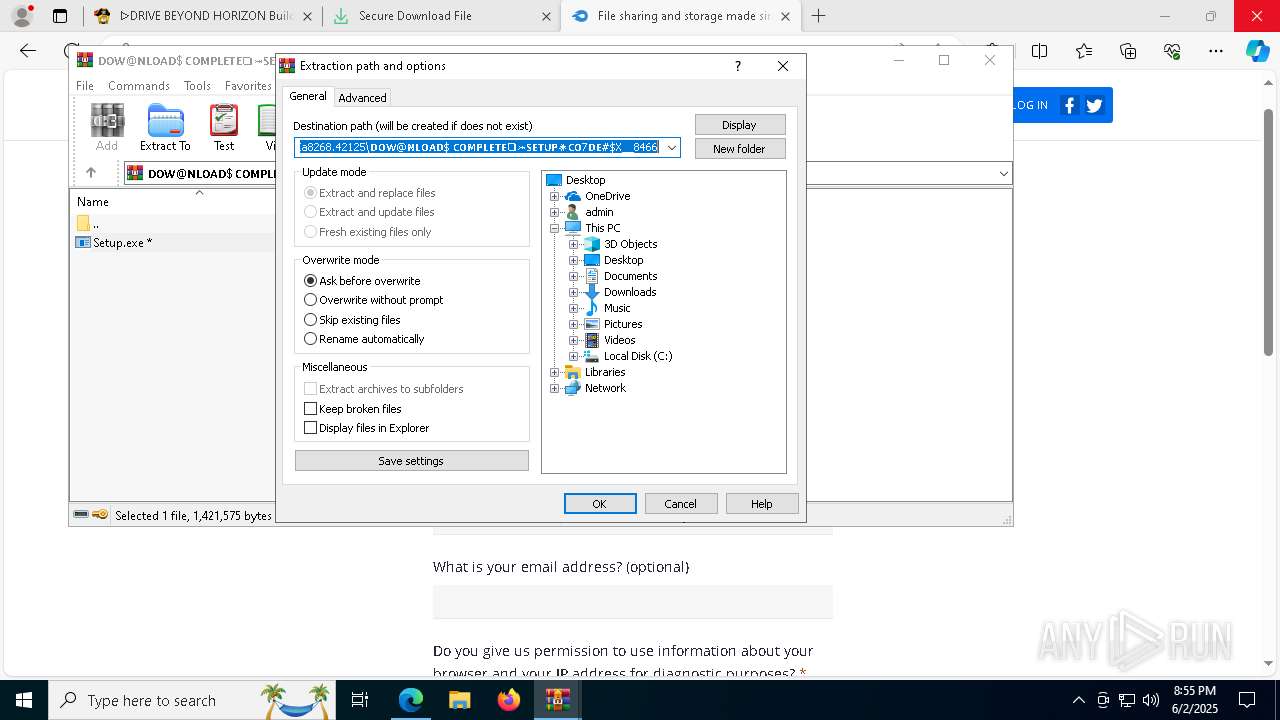
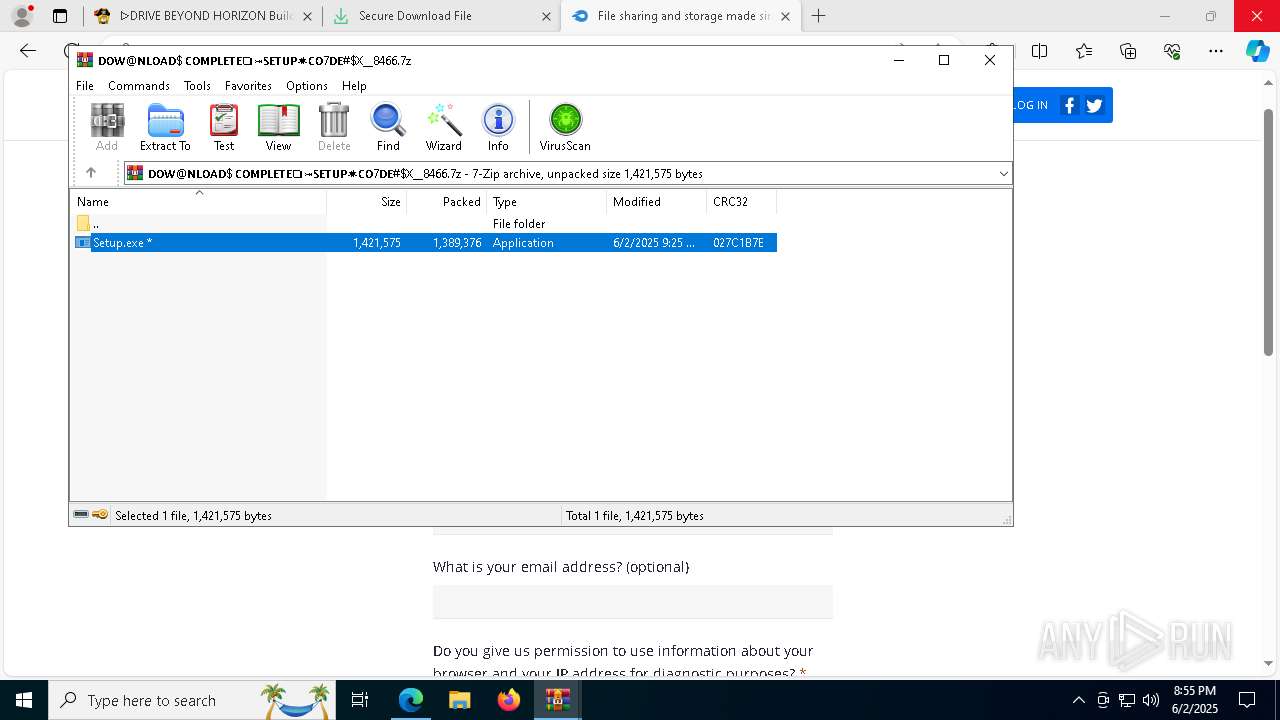
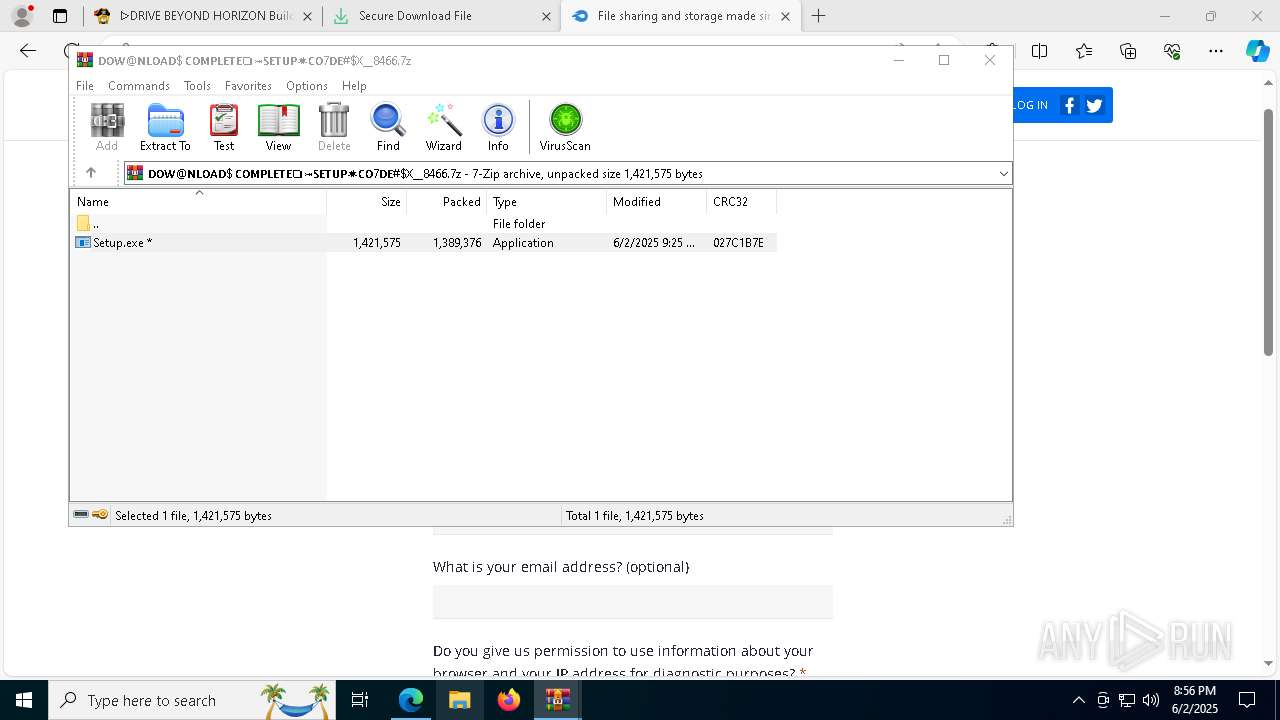
| 1696 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa8268.42125\𝗗𝗢𝗪@𝗡𝗟𝗢𝗔𝗗$ 𝗖𝗢𝗠𝗣𝗟𝗘𝗧𝗘❏⤖𝗦𝗘𝗧𝗨𝗣✷𝗖𝗢7𝗗𝗘#$X__8466.7z" | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
27 551
Read events
27 352
Write events
167
Delete events
32
Modification events
| (PID) Process: | (7632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7632) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D839423933952F00 | |||
| (PID) Process: | (7632) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A54B4B3933952F00 | |||
| (PID) Process: | (7632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\786944 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {72FBBA55-CFB5-483A-8A07-C1B6A18CBE90} | |||
| (PID) Process: | (7632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\786944 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {54825799-B1AB-49A5-9F1C-5024699A8428} | |||
| (PID) Process: | (7632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\786944 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {28D3F2A0-51E8-4B1B-8976-D2E1E56BC534} | |||
| (PID) Process: | (7632) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\786944 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {738E6A3C-874B-4545-86FA-50A925D2619B} | |||
Executable files
59
Suspicious files
1 498
Text files
313
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11f421.TMP | — | |
MD5:— | SHA256:— | |||
| 7632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f440.TMP | — | |
MD5:— | SHA256:— | |||
| 7632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11f450.TMP | — | |
MD5:— | SHA256:— | |||
| 7632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF11f46f.TMP | — | |
MD5:— | SHA256:— | |||
| 7632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF11f4ae.TMP | — | |
MD5:— | SHA256:— | |||
| 7632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7632 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11f4ae.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
295
DNS requests
367
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8656 | SIHClient.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5508 | svchost.exe | HEAD | 200 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748975639&P2=404&P3=2&P4=JjlGU8RbgE4ZNZxH6Tq4mMkiOMxly4KQNhMBr04%2b0uUggVlUak6P1kOkps3NqAm%2fO3U0UaLjdqXYLy%2ftJhLzQw%3d%3d | unknown | — | — | whitelisted |
8656 | SIHClient.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5508 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748975639&P2=404&P3=2&P4=JjlGU8RbgE4ZNZxH6Tq4mMkiOMxly4KQNhMBr04%2b0uUggVlUak6P1kOkps3NqAm%2fO3U0UaLjdqXYLy%2ftJhLzQw%3d%3d | unknown | — | — | whitelisted |
5508 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748975639&P2=404&P3=2&P4=JjlGU8RbgE4ZNZxH6Tq4mMkiOMxly4KQNhMBr04%2b0uUggVlUak6P1kOkps3NqAm%2fO3U0UaLjdqXYLy%2ftJhLzQw%3d%3d | unknown | — | — | whitelisted |
5508 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748975639&P2=404&P3=2&P4=JjlGU8RbgE4ZNZxH6Tq4mMkiOMxly4KQNhMBr04%2b0uUggVlUak6P1kOkps3NqAm%2fO3U0UaLjdqXYLy%2ftJhLzQw%3d%3d | unknown | — | — | whitelisted |
5508 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748975639&P2=404&P3=2&P4=JjlGU8RbgE4ZNZxH6Tq4mMkiOMxly4KQNhMBr04%2b0uUggVlUak6P1kOkps3NqAm%2fO3U0UaLjdqXYLy%2ftJhLzQw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.9:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7572 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2852 | msedge.exe | 142.250.186.74:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
7632 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2852 | msedge.exe | 172.67.175.78:443 | pivigames.blog | CLOUDFLARENET | US | whitelisted |
2852 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
pivigames.blog |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
2852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
2852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
2852 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |