| File name: | Sunny.exe |
| Full analysis: | https://app.any.run/tasks/e38c1917-d3a8-4b76-adea-001b097e771d |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | September 14, 2025, 13:18:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | E7B3AB537552AF4FEE9524795DC17039 |
| SHA1: | 9F0002D489D152C430CA09E53CAD5EF2E7BA6ACE |
| SHA256: | BDE2E44FCE18B40C376B567419758CD15551227E87E0FA6C916ACBA77971F14D |
| SSDEEP: | 49152:KP+qAy2X4iPepflGeBGLIHn+xnwSb42frKc2dnJIwMesXwqY75tDuHZyFOilmGe9:a+pyY4iPmflGeBH+J42f2c2VfMfXPm5w |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3460)
- cmd.exe (PID: 7780)
Create files in the Startup directory
- cmd.exe (PID: 472)
LUMMA mutex has been found
- Animal.pif (PID: 1468)
- MediKangaroo.bat (PID: 188)
Steals credentials from Web Browsers
- Animal.pif (PID: 1468)
Actions looks like stealing of personal data
- Animal.pif (PID: 1468)
SUSPICIOUS
Drops a file with a rarely used extension (PIF)
- cmd.exe (PID: 1508)
The executable file from the user directory is run by the CMD process
- Animal.pif (PID: 1468)
Application launched itself
- cmd.exe (PID: 5416)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1508)
Starts the AutoIt3 executable file
- cmd.exe (PID: 1508)
- explorer.exe (PID: 3540)
Starts application with an unusual extension
- cmd.exe (PID: 1508)
- explorer.exe (PID: 3540)
Executable content was dropped or overwritten
- Sunny.exe (PID: 4744)
- Animal.pif (PID: 1468)
There is functionality for taking screenshot (YARA)
- Sunny.exe (PID: 4744)
- Animal.pif (PID: 1468)
- MediKangaroo.bat (PID: 188)
Searches for installed software
- Animal.pif (PID: 1468)
The process executes via Task Scheduler
- explorer.exe (PID: 5140)
Reads command from file
- cmd.exe (PID: 5416)
Get information on the list of running processes
- cmd.exe (PID: 1508)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 5416)
- Sunny.exe (PID: 4744)
INFO
Checks supported languages
- Sunny.exe (PID: 4744)
- extrac32.exe (PID: 5744)
- Animal.pif (PID: 1468)
- MediKangaroo.bat (PID: 188)
Reads the computer name
- extrac32.exe (PID: 5744)
- Animal.pif (PID: 1468)
- MediKangaroo.bat (PID: 188)
- Sunny.exe (PID: 4744)
Reads mouse settings
- Animal.pif (PID: 1468)
- MediKangaroo.bat (PID: 188)
Create files in a temporary directory
- extrac32.exe (PID: 5744)
- Sunny.exe (PID: 4744)
Manual execution by a user
- cmd.exe (PID: 3460)
- explorer.exe (PID: 1160)
- cmd.exe (PID: 472)
- cmd.exe (PID: 7780)
Creates files or folders in the user directory
- Animal.pif (PID: 1468)
The sample compiled with english language support
- Animal.pif (PID: 1468)
Launching a file from Task Scheduler
- cmd.exe (PID: 3460)
- cmd.exe (PID: 7780)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4948)
- explorer.exe (PID: 3540)
Launching a file from the Startup directory
- cmd.exe (PID: 472)
Reads the software policy settings
- Animal.pif (PID: 1468)
- slui.exe (PID: 7532)
- MediKangaroo.bat (PID: 188)
Reads the machine GUID from the registry
- Animal.pif (PID: 1468)
- MediKangaroo.bat (PID: 188)
Application launched itself
- chrome.exe (PID: 7540)
- chrome.exe (PID: 3768)
- msedge.exe (PID: 6876)
- chrome.exe (PID: 4412)
- msedge.exe (PID: 3608)
- msedge.exe (PID: 3576)
- msedge.exe (PID: 8180)
- msedge.exe (PID: 5236)
- chrome.exe (PID: 7392)
- msedge.exe (PID: 8004)
- chrome.exe (PID: 7456)
- chrome.exe (PID: 5724)
- chrome.exe (PID: 3476)
Checks proxy server information
- slui.exe (PID: 7532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:03:28 07:27:09+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 27136 |
| InitializedDataSize: | 475136 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x3578 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
263
Monitored processes
116
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Users\admin\AppData\Local\HealthSync Innovations\MediKangaroo.bat" r | C:\Users\admin\AppData\Local\HealthSync Innovations\MediKangaroo.bat | explorer.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Version: 3, 3, 17, 0 Modules
| |||||||||||||||
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --instant-process --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3656,i,6413329369879372571,9314944311178705196,262144 --variations-seed-version --mojo-platform-channel-handle=3680 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2040,i,13802625986572145547,15454006892968400040,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2396 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 472 | cmd /k echo [InternetShortcut] > "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\MediKangaroo.url" & echo URL="C:\Users\admin\AppData\Local\HealthSync Innovations\MediKangaroo.lnk" >> "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\MediKangaroo.url" & exit | C:\Windows\SysWOW64\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3200,i,13802625986572145547,15454006892968400040,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3664 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x220,0x224,0x228,0x1fc,0x22c,0x7ffc4583fff8,0x7ffc45840004,0x7ffc45840010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --edge-skip-compat-layer-relaunch | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1160 | explorer.exe 'C:\Users\admin\AppData\Local\HealthSync Innovations\MediKangaroo.lnk' | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=4616,i,3673859643059381982,2804560066025105360,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=2024,i,3673859643059381982,2804560066025105360,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=1968 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
44 122
Read events
44 029
Write events
93
Delete events
0
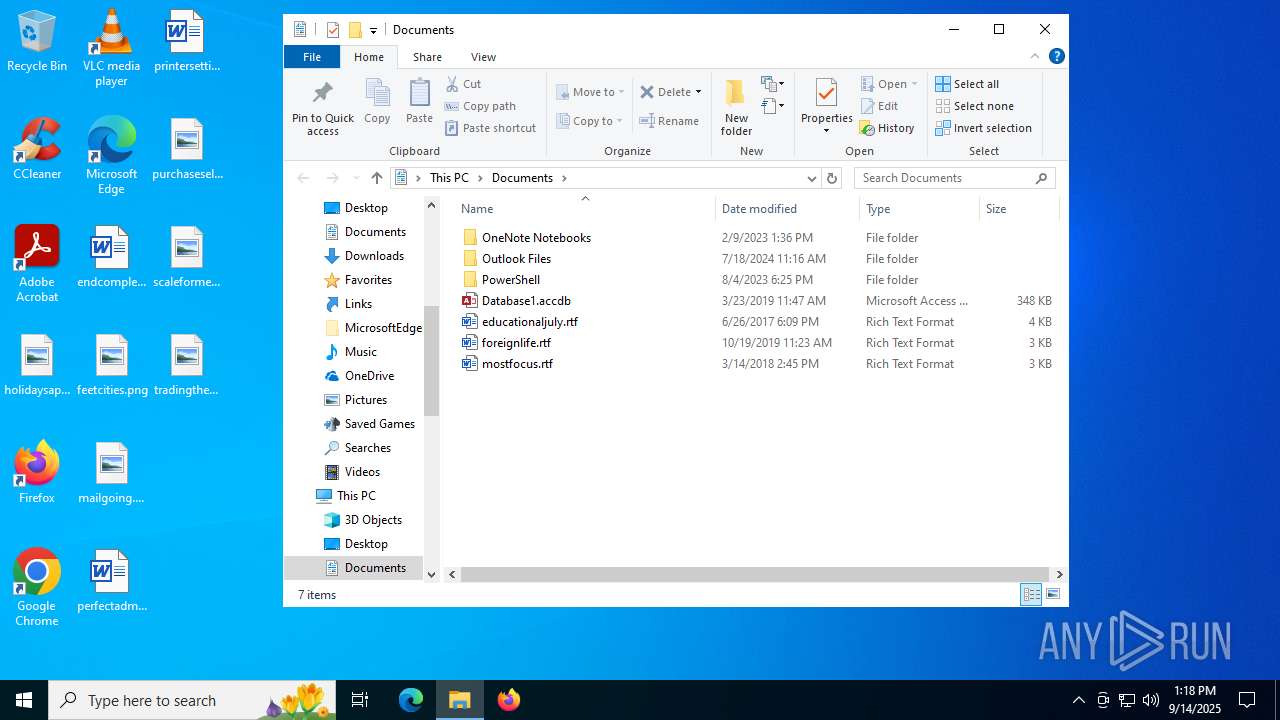
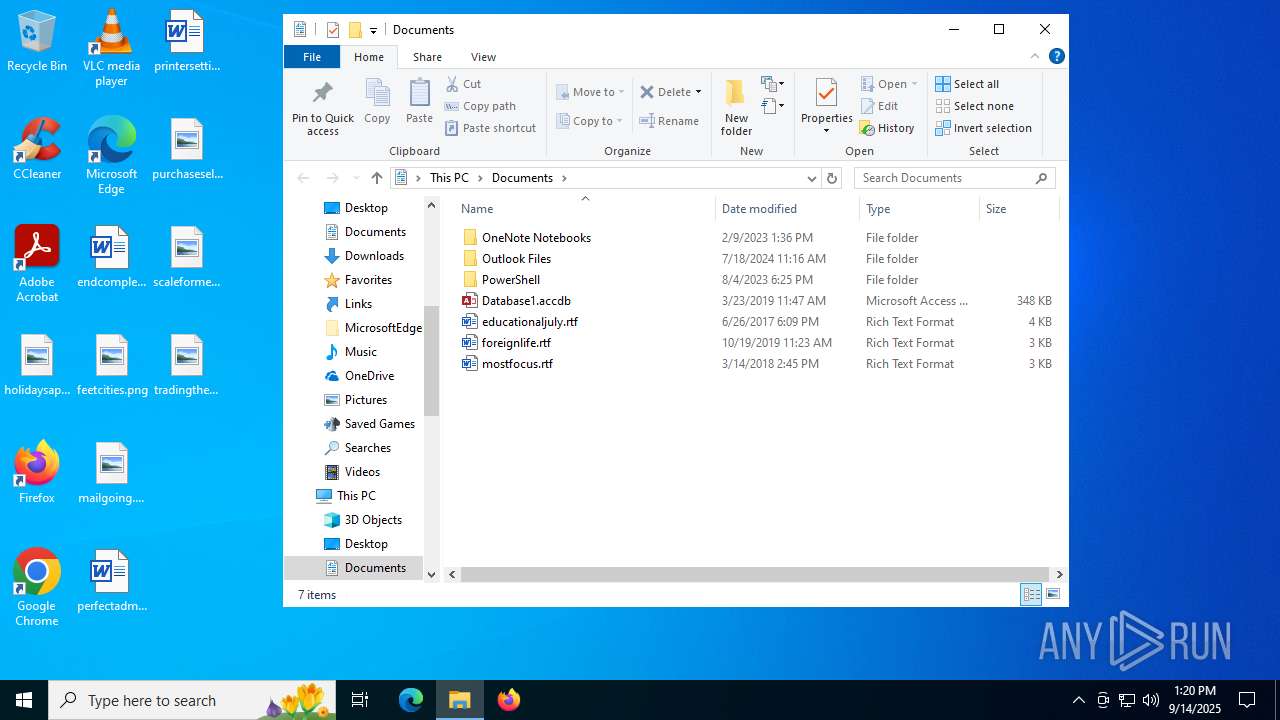
Modification events
| (PID) Process: | (4948) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (4948) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000003000000110000000E000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (4948) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000003000000050000000200000001000000FFFFFFFF | |||
| (PID) Process: | (4948) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (4948) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Ribbon |
| Operation: | write | Name: | MinimizedStateTabletModeOff |
Value: 0 | |||
| (PID) Process: | (4948) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Ribbon |
| Operation: | write | Name: | QatItems |
Value: 3C7369713A637573746F6D554920786D6C6E733A7369713D22687474703A2F2F736368656D61732E6D6963726F736F66742E636F6D2F77696E646F77732F323030392F726962626F6E2F716174223E3C7369713A726962626F6E206D696E696D697A65643D2266616C7365223E3C7369713A71617420706F736974696F6E3D2230223E3C7369713A736861726564436F6E74726F6C733E3C7369713A636F6E74726F6C206964513D227369713A3136313238222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3136313239222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333532222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333834222076697369626C653D22747275652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333336222076697369626C653D22747275652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333537222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C2F7369713A736861726564436F6E74726F6C733E3C2F7369713A7161743E3C2F7369713A726962626F6E3E3C2F7369713A637573746F6D55493E | |||
| (PID) Process: | (4948) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar\ShellBrowser |
| Operation: | write | Name: | ITBar7Layout |
Value: 13000000000000000000000020000000100000000000000001000000010700005E01000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4948) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Documents | |||
| (PID) Process: | (4948) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 121 | |||
| (PID) Process: | (4948) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: B7C0C66800000000 | |||
Executable files
34
Suspicious files
359
Text files
272
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4744 | Sunny.exe | C:\Users\admin\AppData\Local\Temp\Midi.pst | binary | |
MD5:— | SHA256:— | |||
| 4744 | Sunny.exe | C:\Users\admin\AppData\Local\Temp\Wilson.pst | binary | |
MD5:— | SHA256:— | |||
| 4744 | Sunny.exe | C:\Users\admin\AppData\Local\Temp\Separation.pst | binary | |
MD5:— | SHA256:— | |||
| 4744 | Sunny.exe | C:\Users\admin\AppData\Local\Temp\Pie.pst | text | |
MD5:— | SHA256:— | |||
| 4744 | Sunny.exe | C:\Users\admin\AppData\Local\Temp\nszCB0D.tmp\nsExec.dll | executable | |
MD5:— | SHA256:— | |||
| 4744 | Sunny.exe | C:\Users\admin\AppData\Local\Temp\Istanbul.pst | binary | |
MD5:— | SHA256:— | |||
| 5744 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Rap | binary | |
MD5:— | SHA256:— | |||
| 5744 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Periodic | binary | |
MD5:— | SHA256:— | |||
| 5744 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Workshops | binary | |
MD5:— | SHA256:— | |||
| 5744 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Republic | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
224
DNS requests
228
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1864 | svchost.exe | GET | 200 | 184.28.9.100:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.16.148:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 104.85.1.163:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7700 | chrome.exe | GET | 200 | 142.250.185.238:80 | http://clients2.google.com/time/1/current?cup2key=8:NWclupskIcIDZB4lxy42SY7X_SOkMWJ0X829i7wn7pI&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
4768 | chrome.exe | GET | 200 | 142.250.185.238:80 | http://clients2.google.com/time/1/current?cup2key=8:TNXFk4xjVeFh79aVyiDWWJ-YqsckNhFa2wFs4LZE72I&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
8016 | SIHClient.exe | GET | 200 | 95.100.165.206:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8016 | SIHClient.exe | GET | 200 | 95.100.165.206:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8016 | SIHClient.exe | GET | 200 | 184.25.102.145:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
8016 | SIHClient.exe | GET | 200 | 95.100.165.206:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
8016 | SIHClient.exe | GET | 200 | 95.100.165.206:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1636 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1864 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1864 | svchost.exe | 184.28.9.100:80 | ocsp.digicert.com | Akamai International B.V. | AU | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 2.16.16.148:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 104.85.1.163:80 | www.microsoft.com | AKAMAI-AS | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
TOmZaTDvxlzoxohWJRtpDU.TOmZaTDvxlzoxohWJRtpDU |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
jackaw.asia |
| malicious |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
— | — | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Win32/Lumma CnC HTTP Activity observed |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |