| File name: | 15652172347CFAD0094984499803524AA8637E27 |
| Full analysis: | https://app.any.run/tasks/774169f2-8c1c-41d9-9cb0-ad975edff316 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | May 20, 2022, 18:11:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/encrypted |
| File info: | CDFV2 Encrypted |
| MD5: | FEF382F6D04426A971985774A5A6D2E8 |
| SHA1: | 15652172347CFAD0094984499803524AA8637E27 |
| SHA256: | BDD4399373F751945BCB9C134787C685DF30E6E4B3AA6C08F09833754DB80592 |
| SSDEEP: | 6144:JV3/fry/q6PmDNi0Wirw0GJq0Ct4/EK/No7WB1J:Jw/q6PRFirPG8mEeoi |
MALICIOUS
Renames files like Ransomware
- Explorer.EXE (PID: 764)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 2484)
Drops executable file immediately after starts
- EQNEDT32.EXE (PID: 2484)
Runs app for hidden code execution
- Explorer.EXE (PID: 764)
Application was dropped or rewritten from another process
- vbc.exe (PID: 360)
FORMBOOK detected by memory dumps
- cmd.exe (PID: 2524)
FORMBOOK was detected
- Explorer.EXE (PID: 764)
Connects to CnC server
- Explorer.EXE (PID: 764)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- Explorer.EXE (PID: 764)
Checks supported languages
- vbc.exe (PID: 360)
- InstallUtil.exe (PID: 2872)
- cmd.exe (PID: 2524)
- EQNEDT32.EXE (PID: 2484)
Creates files in the user directory
- Explorer.EXE (PID: 764)
Reads the computer name
- vbc.exe (PID: 360)
- InstallUtil.exe (PID: 2872)
- cmd.exe (PID: 2524)
- EQNEDT32.EXE (PID: 2484)
Starts CMD.EXE for commands execution
- Explorer.EXE (PID: 764)
- cmd.exe (PID: 2524)
Application launched itself
- cmd.exe (PID: 2524)
Reads Environment values
- cmd.exe (PID: 2524)
Drops a file with a compile date too recent
- EQNEDT32.EXE (PID: 2484)
Executed via COM
- EQNEDT32.EXE (PID: 2484)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 2484)
INFO
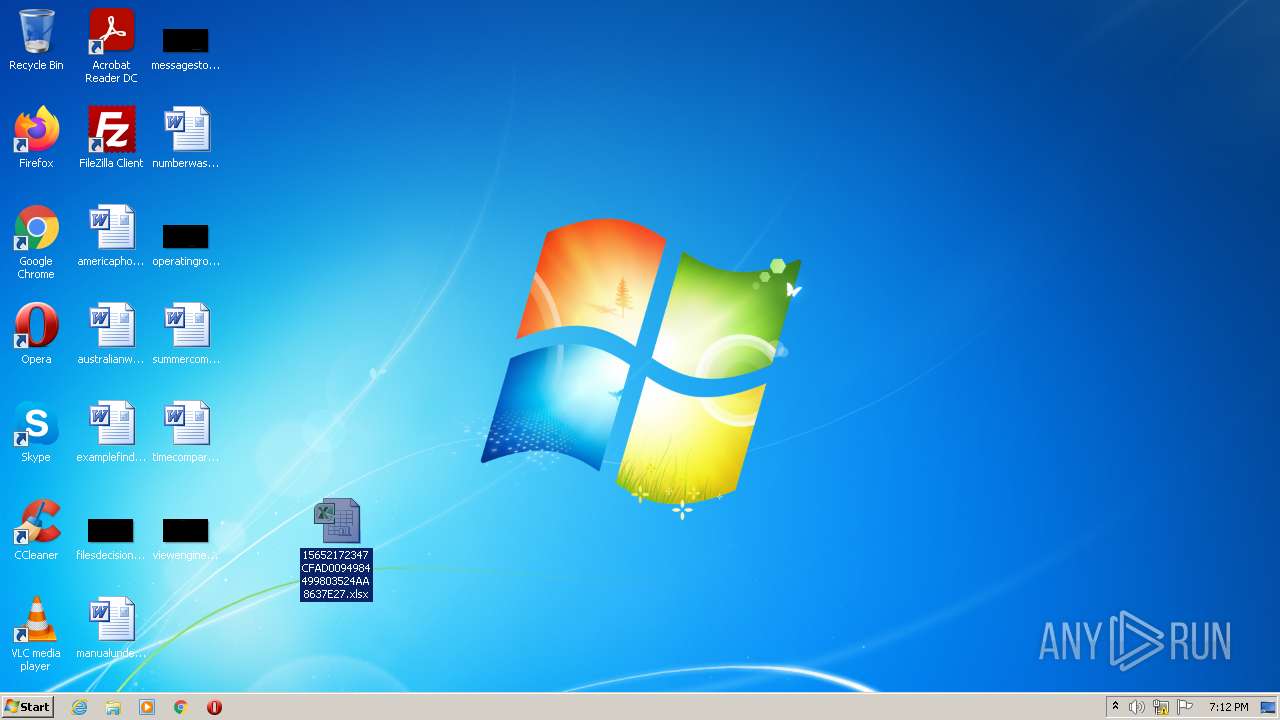
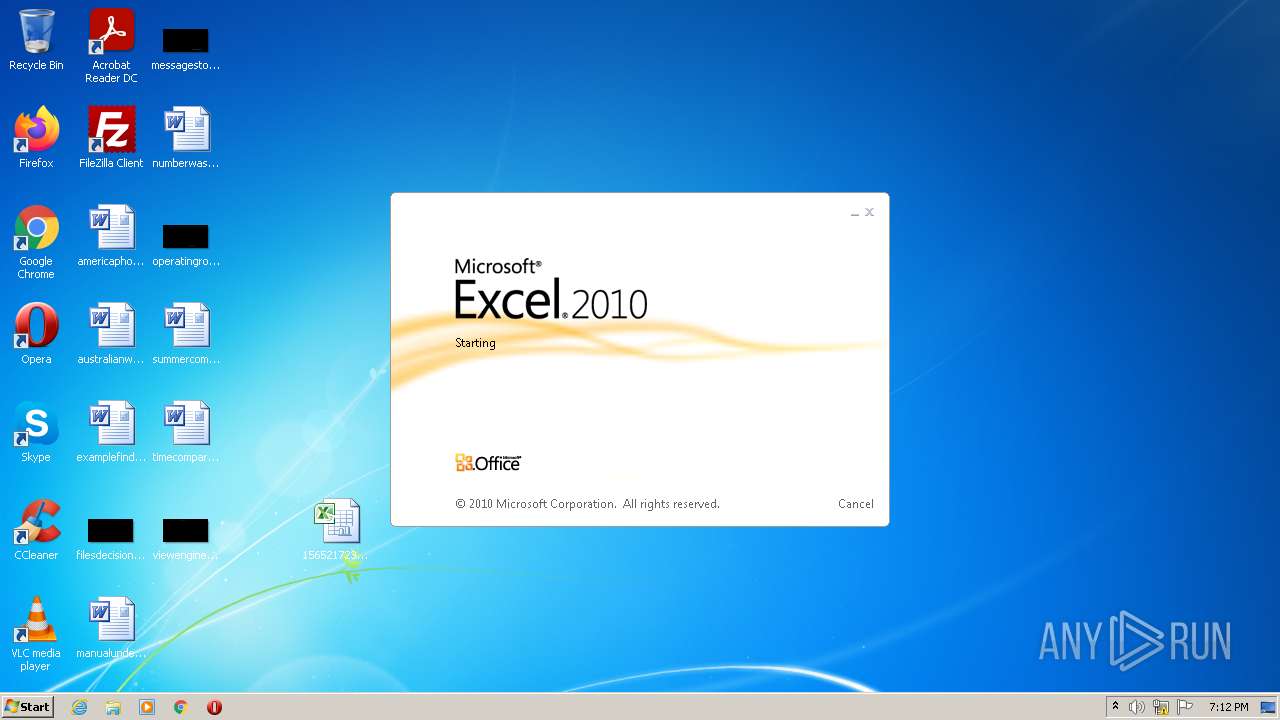
Manual execution by user
- EXCEL.EXE (PID: 504)
- cmd.exe (PID: 2524)
Starts Microsoft Office Application
- Explorer.EXE (PID: 764)
Reads Microsoft Office registry keys
- Explorer.EXE (PID: 764)
- EXCEL.EXE (PID: 504)
Reads the computer name
- rundll32.exe (PID: 1780)
- EXCEL.EXE (PID: 504)
Checks supported languages
- rundll32.exe (PID: 1780)
- Explorer.EXE (PID: 764)
- EXCEL.EXE (PID: 504)
- cmd.exe (PID: 1164)
Creates files in the user directory
- EXCEL.EXE (PID: 504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
8
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Users\Public\vbc.exe" | C:\Users\Public\vbc.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2554748 Modules
| |||||||||||||||
| 504 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 764 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1164 | /c del "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
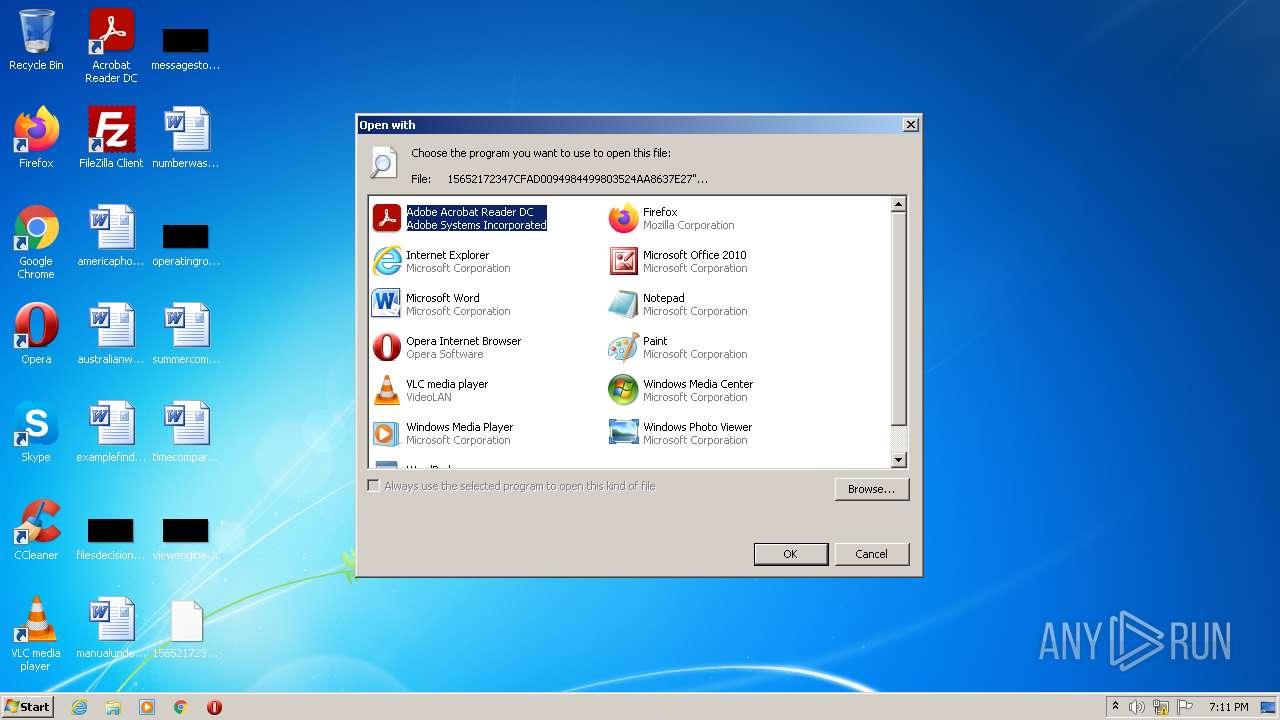
| 1780 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL "C:\Users\admin\Desktop\15652172347CFAD0094984499803524AA8637E27" | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2524 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2872 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | — | vbc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
Total events
5 883
Read events
5 769
Write events
102
Delete events
12
Modification events
| (PID) Process: | (1780) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (1780) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: Firefox | |||
| (PID) Process: | (1780) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (1780) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (1780) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (1780) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (1780) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (1780) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (1780) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (1780) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
2
Text files
1
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 504 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRC361.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 764 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\9839aec31243a928.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 504 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9FDDC6C8.emf | emf | |
MD5:— | SHA256:— | |||
| 764 | Explorer.EXE | C:\Users\admin\Desktop\15652172347CFAD0094984499803524AA8637E27.xlsx | binary | |
MD5:— | SHA256:— | |||
| 764 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\15652172347CFAD0094984499803524AA8637E27.xlsx.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2484 | EQNEDT32.EXE | C:\Users\Public\vbc.exe | executable | |
MD5:— | SHA256:— | |||
| 504 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:— | SHA256:— | |||
| 504 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\15652172347CFAD0094984499803524AA8637E27.xlsx.LNK | lnk | |
MD5:— | SHA256:— | |||
| 764 | Explorer.EXE | C:\Users\admin\Desktop\15652172347CFAD0094984499803524AA8637E27xlsx | binary | |
MD5:— | SHA256:— | |||
| 2484 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\vbc[1].exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
8
DNS requests
12
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
764 | Explorer.EXE | GET | — | 185.68.16.31:80 | http://www.wona-nyc.com/uu0p/?9rxHaNl=6EEcCW2hQlWMxHlsiJ/GZrjouJMXic+r2ls54VYWqIK+WcgvNzWiKeTB7hOFPcAqzPP6+g==&c8T=uTEDpv8Xel70 | UA | — | — | malicious |
764 | Explorer.EXE | GET | 302 | 3.140.13.188:80 | http://www.novusr.com/uu0p/?9rxHaNl=e4XY/j8oNfDX/vZPiWytQAMAvJIq83Y1oMxBu+CmSf1+v3GlpkJVyJdXoLuvOsx0jiUB1A==&c8T=uTEDpv8Xel70 | US | — | — | malicious |
2484 | EQNEDT32.EXE | GET | 200 | 180.214.236.4:80 | http://180.214.236.4/__cloud2protect/vbc.exe | VN | executable | 1.32 Mb | suspicious |
764 | Explorer.EXE | GET | 404 | 217.27.64.16:80 | http://www.sinvrealestate.com/uu0p/?9rxHaNl=lIGg60XplbK72kJ+rhqW67i0GoWKo2/R7K5es8l10ENkbzvb7Bl9r/tISrKBSvnycZfYHw==&c8T=uTEDpv8Xel70 | IT | html | 146 b | malicious |
764 | Explorer.EXE | GET | 403 | 34.102.136.180:80 | http://www.visionsbeyondthelight.com/uu0p/?9rxHaNl=+ASCvMgo2R4cOid86ZZM5l1IBfa8viXOpeohS1AtmMHXhrVsNnlYeEvcctmKX7/Dp9a77Q==&c8T=uTEDpv8Xel70 | US | html | 291 b | malicious |
764 | Explorer.EXE | GET | 400 | 209.17.116.163:80 | http://www.purintonco.online/uu0p/?9rxHaNl=60esvrGSlOLIHJKLh872WtxOApHCC3we459Vd3PBUCsbqkSfaqQKgCvIT58KSYvauKVK2Q==&c8T=uTEDpv8Xel70 | US | html | 163 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2484 | EQNEDT32.EXE | 180.214.236.4:80 | — | — | VN | suspicious |
764 | Explorer.EXE | 185.68.16.31:80 | www.wona-nyc.com | Hosting Ukraine LTD | UA | malicious |
764 | Explorer.EXE | 3.140.13.188:80 | www.novusr.com | — | US | malicious |
764 | Explorer.EXE | 34.102.136.180:80 | www.visionsbeyondthelight.com | — | US | whitelisted |
764 | Explorer.EXE | 217.27.64.16:80 | www.sinvrealestate.com | Telecom Italia | IT | malicious |
764 | Explorer.EXE | 209.17.116.163:80 | www.purintonco.online | Defense.Net, Inc | US | malicious |
— | — | 198.54.117.211:80 | www.oneclickmsp.com | Namecheap, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.wona-nyc.com |
| malicious |
www.novusr.com |
| malicious |
www.visionsbeyondthelight.com |
| malicious |
www.purintonco.online |
| malicious |
www.sinvrealestate.com |
| malicious |
www.jca-okayama.com |
| malicious |
www.oneclickmsp.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2484 | EQNEDT32.EXE | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2484 | EQNEDT32.EXE | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2484 | EQNEDT32.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M1 |
2484 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2484 | EQNEDT32.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M2 |
2484 | EQNEDT32.EXE | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
764 | Explorer.EXE | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
764 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
764 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
764 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |