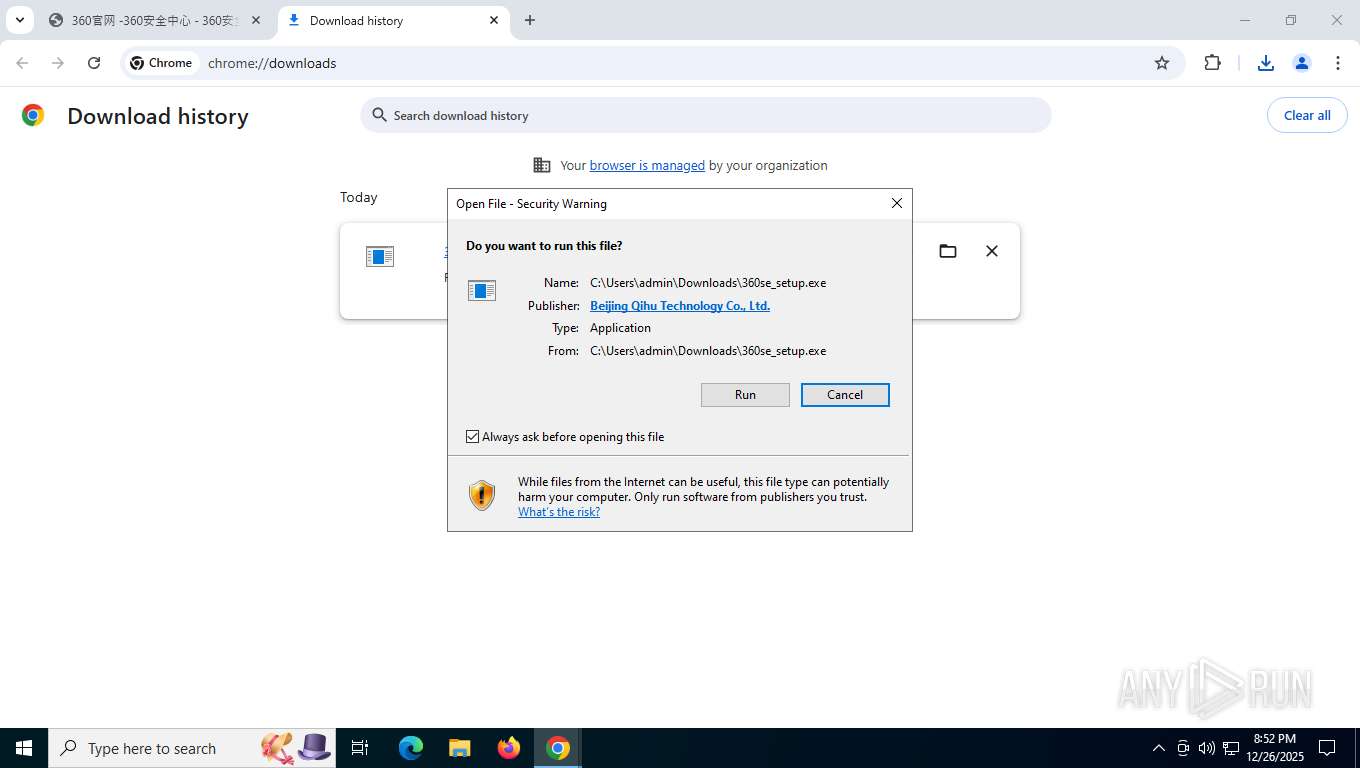
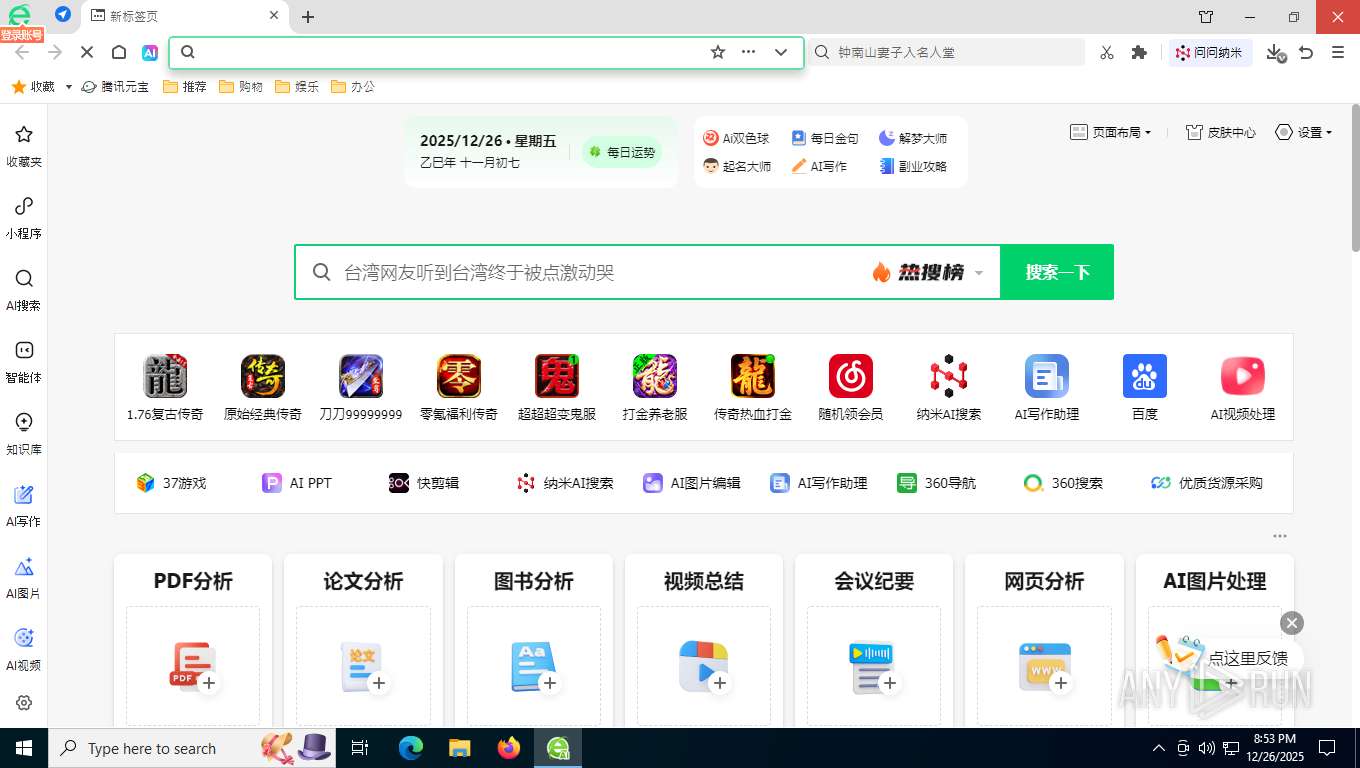
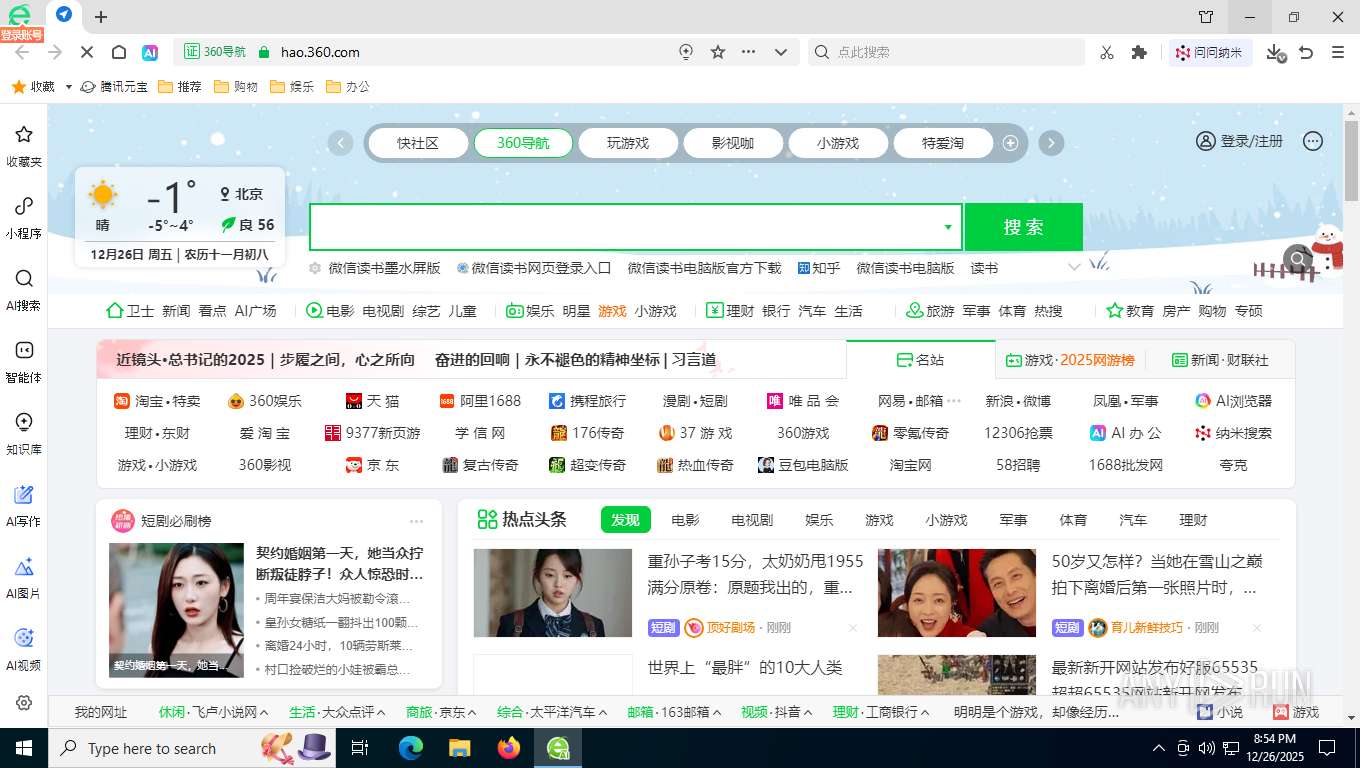
| URL: | 360.cn |
| Full analysis: | https://app.any.run/tasks/0673f300-9988-49d3-8dff-92a76ecafad9 |
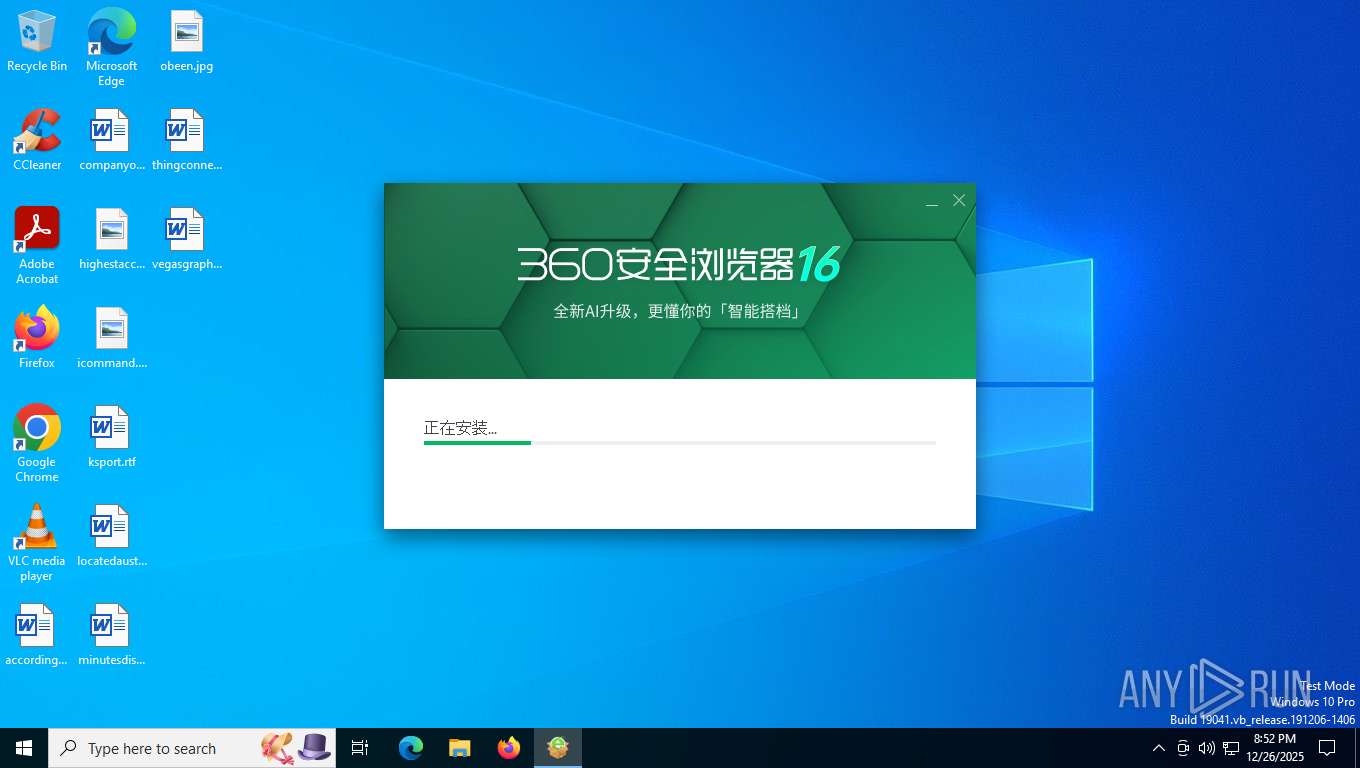
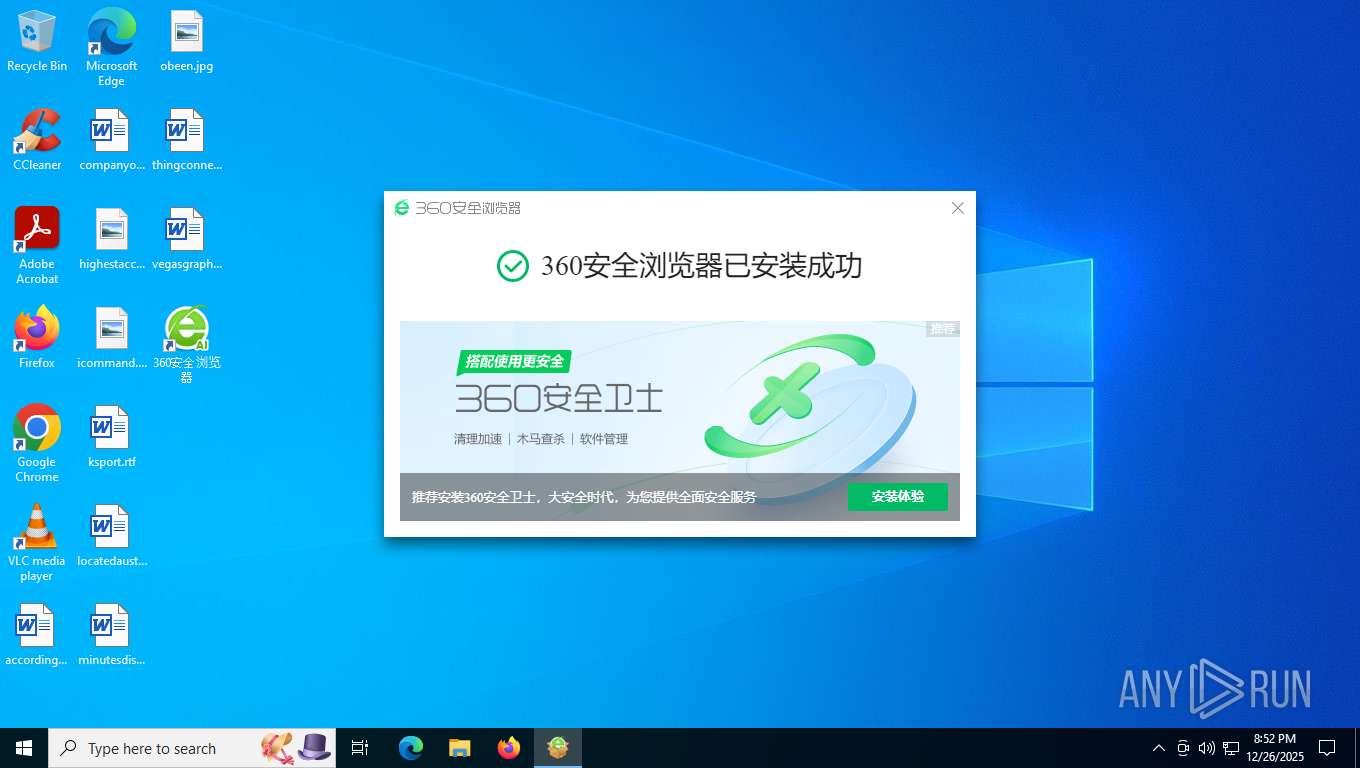
| Verdict: | Malicious activity |
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | December 27, 2025, 01:50:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0BDCB73D25C8F2039EA11D744F23E2DC |
| SHA1: | 248B5DC36BDFD12230FCA07E857B3BDD7B97F0A5 |
| SHA256: | BDBCF85428F41EDC79CED1C6075D23643134D59A6AB71CCB18429B996637F165 |
| SSDEEP: | 3:UhGLn:UhGL |
MALICIOUS
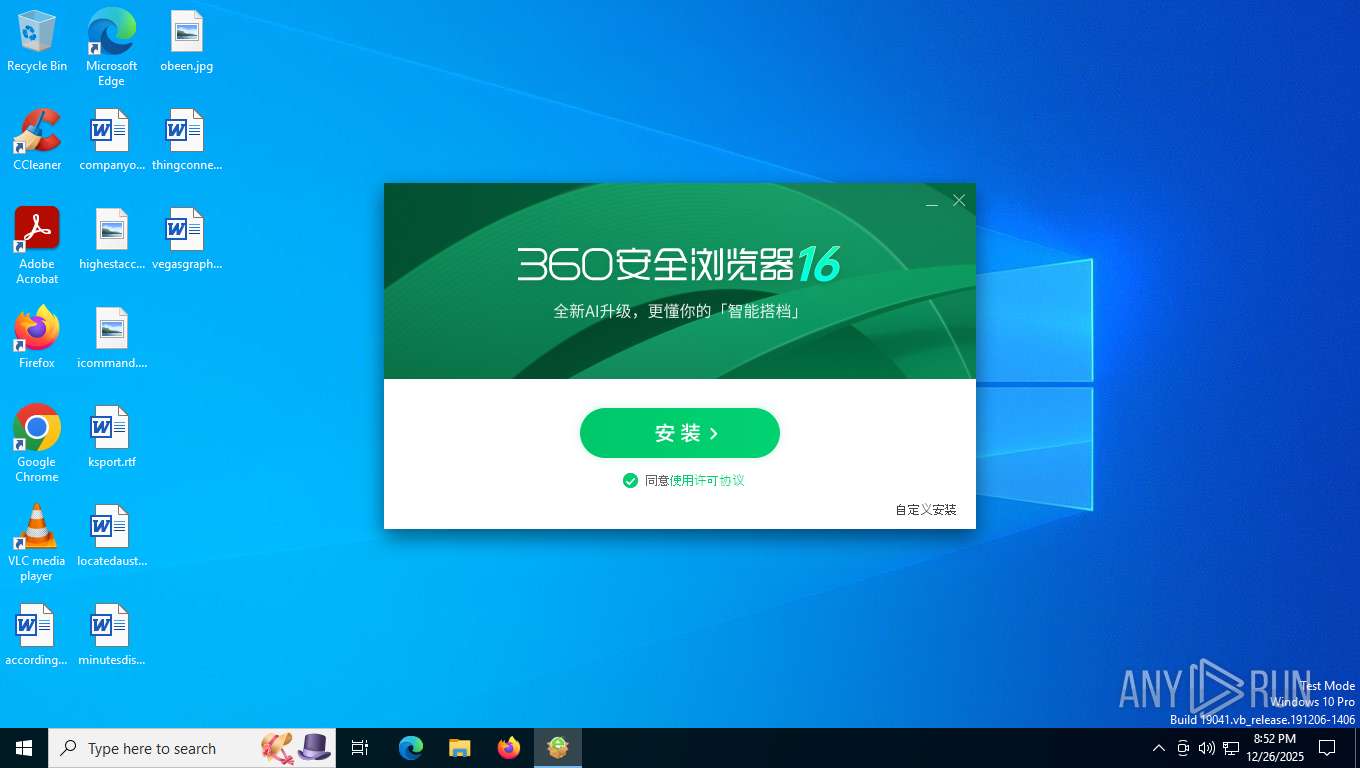
Changes the autorun value in the registry
- setup.exe (PID: 7364)
- 360huabaosetup.exe (PID: 4828)
Actions looks like stealing of personal data
- setup.exe (PID: 7364)
- 360se.exe (PID: 8364)
- 360se.exe (PID: 7880)
- 360se.exe (PID: 7920)
QIHOO360 mutex has been found
- 360se.exe (PID: 8364)
- sesvr.exe (PID: 8692)
- 360se.exe (PID: 7920)
- sesvr.exe (PID: 6664)
- 360se.exe (PID: 8672)
- sesvr.exe (PID: 5044)
SUSPICIOUS
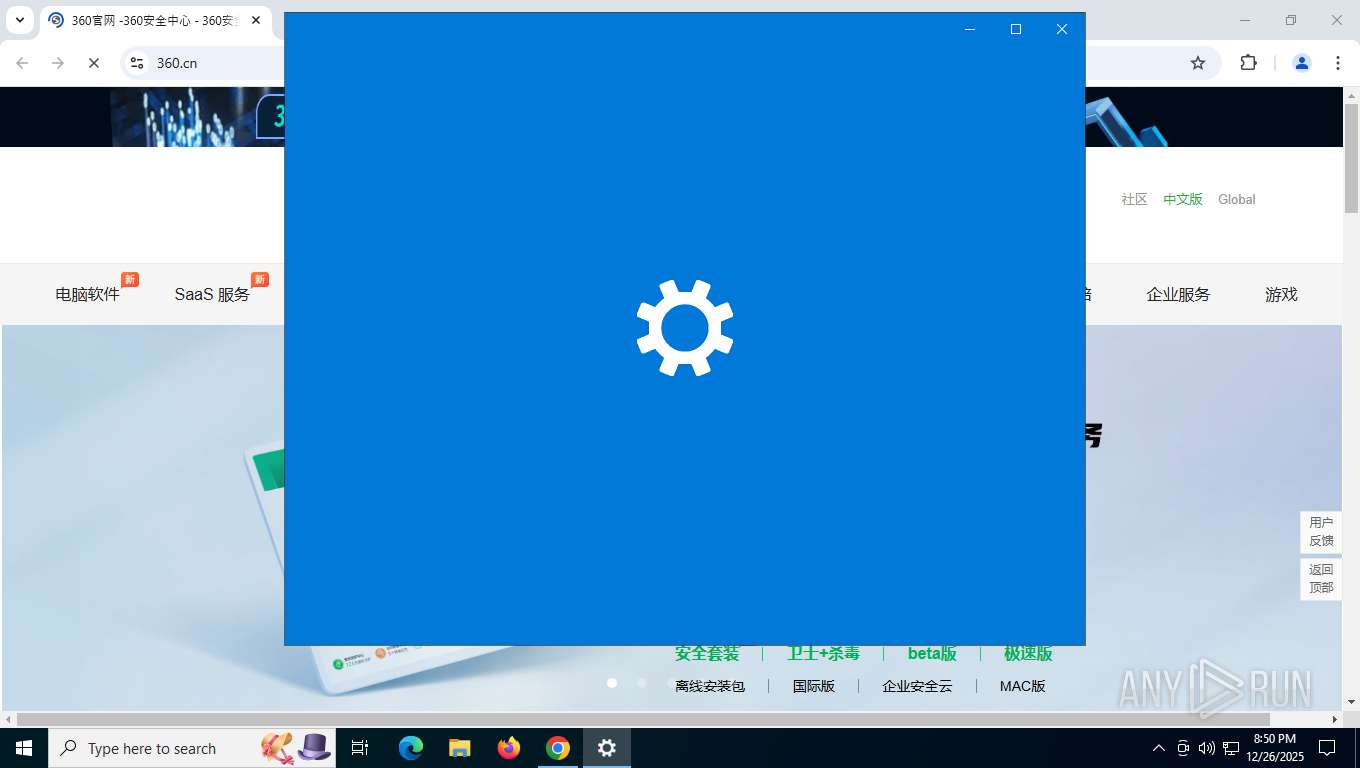
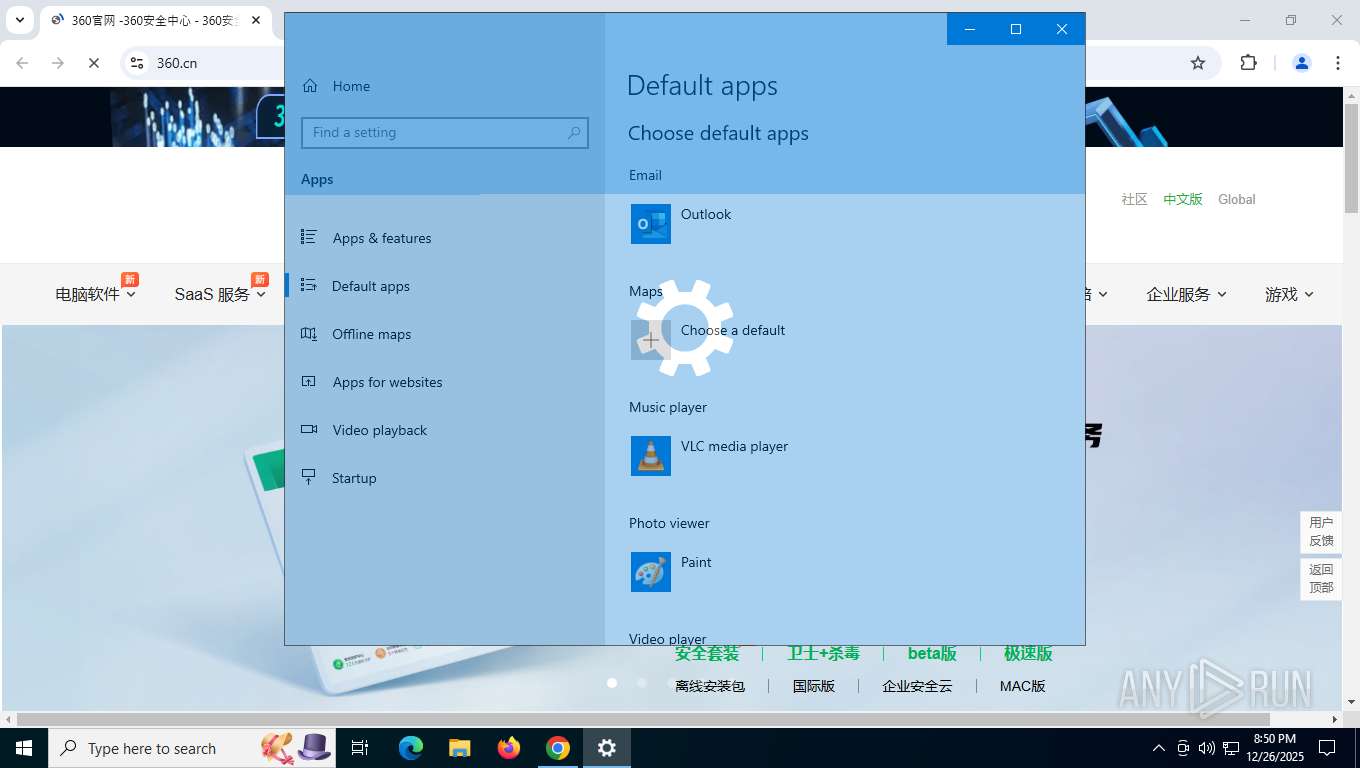
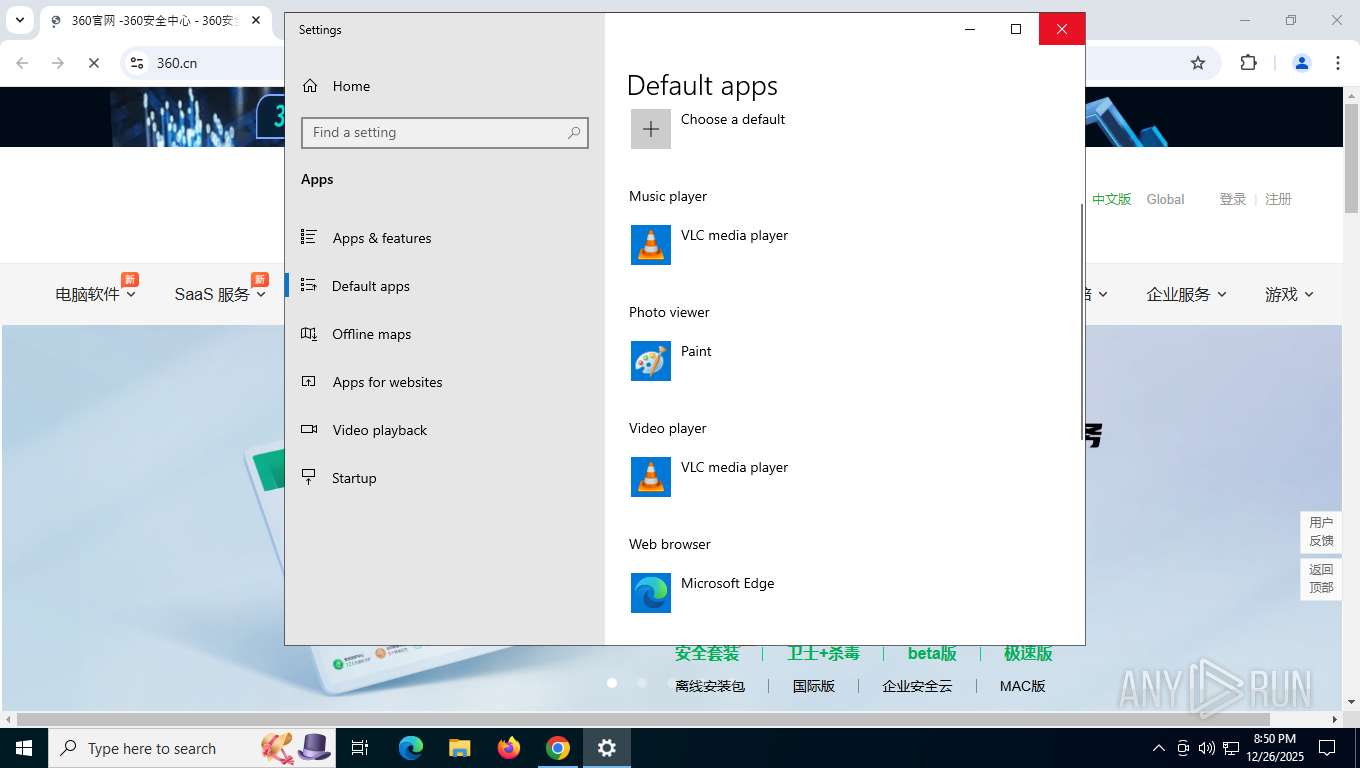
Reads the date of Windows installation
- SystemSettings.exe (PID: 6948)
- MPHelper.exe (PID: 7404)
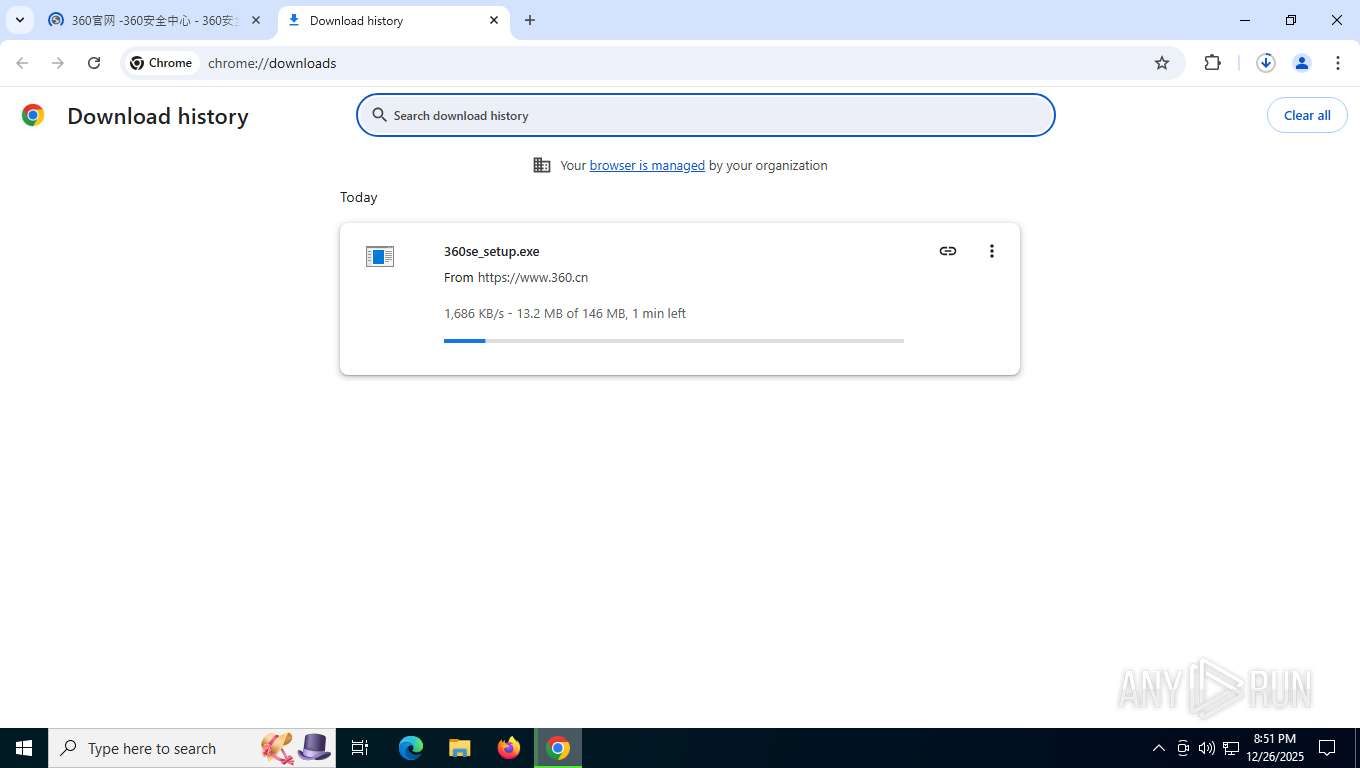
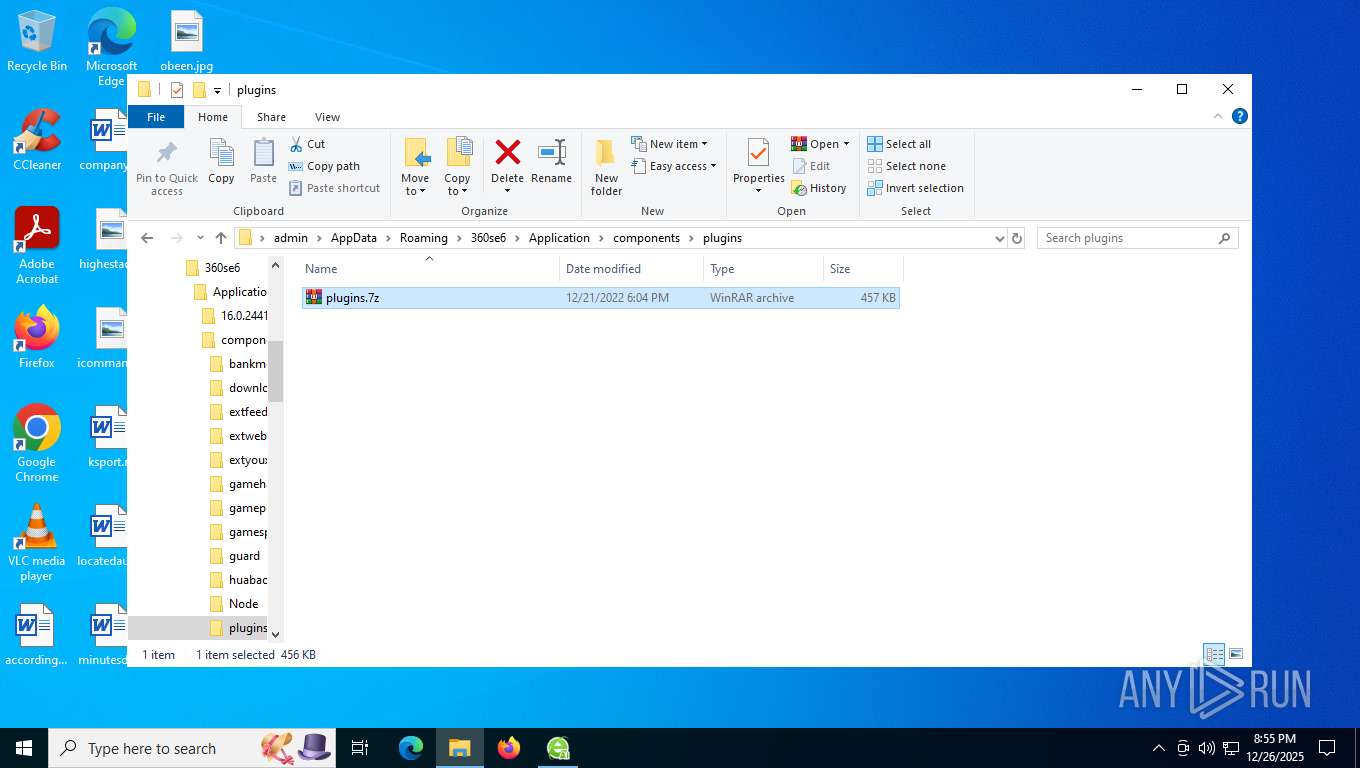
Executable content was dropped or overwritten
- 360se_setup.exe (PID: 6096)
- setup.exe (PID: 7364)
- 360bpsvc.exe (PID: 2992)
- 360bpsvc.exe (PID: 7264)
- 360se.exe (PID: 7880)
- 360se.exe (PID: 8364)
- 360huabaosetup.exe (PID: 4828)
- 360se.exe (PID: 7828)
- 360se.exe (PID: 7920)
Process drops legitimate windows executable
- setup.exe (PID: 7364)
- 360se.exe (PID: 8364)
Searches for installed software
- setup.exe (PID: 7364)
- 360se.exe (PID: 8364)
- 360se.exe (PID: 7920)
Reads security settings of Internet Explorer
- setup.exe (PID: 7364)
- 360se.exe (PID: 8364)
- sesvc.exe (PID: 8116)
- 360se.exe (PID: 7880)
- sesvc.exe (PID: 8112)
- 360bdoctor.exe (PID: 1600)
- 360bdoctor.exe (PID: 2432)
- 360huabaosetup.exe (PID: 4828)
- sesvc.exe (PID: 1772)
- 360huabao.exe (PID: 8572)
- 360huabao.exe (PID: 2420)
- 360huabaosetup.exe (PID: 8140)
- 360bdoctor.exe (PID: 4344)
- 360seupdate.exe (PID: 8292)
- 360se.exe (PID: 7920)
- sesvc.exe (PID: 8760)
- MPHelper.exe (PID: 7404)
- 360bdoctor.exe (PID: 1792)
- 360bdoctor.exe (PID: 7340)
- 360bdoctor.exe (PID: 5768)
- 360seupdate.exe (PID: 8424)
- 360se.exe (PID: 8672)
- sesvc.exe (PID: 5636)
- 360bdoctor.exe (PID: 8628)
- 360bdoctor.exe (PID: 8540)
Drops a system driver (possible attempt to evade defenses)
- setup.exe (PID: 7364)
The process creates files with name similar to system file names
- setup.exe (PID: 7364)
There is functionality for taking screenshot (YARA)
- setup.exe (PID: 7364)
- setup.exe (PID: 8616)
Application launched itself
- setup.exe (PID: 7364)
- 360se.exe (PID: 8364)
- sesvc.exe (PID: 8116)
- 360bdoctor.exe (PID: 1600)
- 360se.exe (PID: 7828)
- 360se.exe (PID: 7920)
- 360bdoctor.exe (PID: 2432)
- 360bdoctor.exe (PID: 3796)
- 360bdoctor.exe (PID: 1792)
- 360se.exe (PID: 8672)
- 360bdoctor.exe (PID: 4344)
- 360bdoctor.exe (PID: 5768)
- 360bdoctor.exe (PID: 408)
- 360bdoctor.exe (PID: 8628)
- 360bdoctor.exe (PID: 7340)
The process checks if it is being run in the virtual environment
- setup.exe (PID: 7364)
- 360se.exe (PID: 8364)
- MPHelper.exe (PID: 7404)
- 360se.exe (PID: 7920)
- 360se.exe (PID: 8672)
The process verifies whether the antivirus software is installed
- setup.exe (PID: 7364)
- 360se.exe (PID: 8364)
- 360se.exe (PID: 7880)
- 360huabaosetup.exe (PID: 4828)
- sesvc.exe (PID: 8112)
- MPHelper.exe (PID: 7404)
- 360se.exe (PID: 7920)
- 360huabaosetup.exe (PID: 8140)
- 360se.exe (PID: 8672)
Executes as Windows Service
- 360bpsvc.exe (PID: 7264)
Creates or modifies Windows services
- 360bpsvc.exe (PID: 2992)
- 360bpsvc.exe (PID: 7264)
Connects to unusual port
- 360se.exe (PID: 7880)
Creates file in the systems drive root
- MPHelper.exe (PID: 7404)
Reads the BIOS version
- MPHelper.exe (PID: 7404)
INFO
Application launched itself
- chrome.exe (PID: 7628)
Reads Microsoft Office registry keys
- SystemSettings.exe (PID: 6948)
Checks supported languages
- SystemSettings.exe (PID: 6948)
- TextInputHost.exe (PID: 9112)
- 360se_setup.exe (PID: 6096)
- setup.exe (PID: 7364)
- setup.exe (PID: 8616)
- setup.exe (PID: 8580)
- setup.exe (PID: 4336)
- setup.exe (PID: 3060)
- setup.exe (PID: 8888)
- 360se.exe (PID: 8364)
- 360se.exe (PID: 3656)
- 360se.exe (PID: 5736)
- 360se.exe (PID: 1312)
- 360se.exe (PID: 7548)
- 360se.exe (PID: 408)
- 360se.exe (PID: 1080)
- 360bpsvc.exe (PID: 2992)
- 360se.exe (PID: 8936)
- 360bpsvc.exe (PID: 7264)
- sesvc.exe (PID: 7972)
- 360se.exe (PID: 7880)
- sesvc.exe (PID: 8116)
- sesvc.exe (PID: 8112)
- SeAppService.exe (PID: 1956)
- 360bdoctor.exe (PID: 1600)
- 360bdoctor.exe (PID: 2432)
- 360se.exe (PID: 8208)
- sesvc.exe (PID: 1772)
- 360huabaosetup.exe (PID: 4828)
- sesvr.exe (PID: 8692)
- 360huabao.exe (PID: 8572)
- 360huabao.exe (PID: 7568)
- 360huabao.exe (PID: 1872)
- 360huabao.exe (PID: 7808)
- 360huabao.exe (PID: 3436)
- 360huabao.exe (PID: 4624)
- 360huabaosetup.exe (PID: 8140)
- 360se.exe (PID: 8216)
- 360se.exe (PID: 2712)
- 360se.exe (PID: 7828)
- 360bdoctor.exe (PID: 4344)
- 360se.exe (PID: 7920)
- 360se.exe (PID: 7936)
- 360se.exe (PID: 7784)
- 360se.exe (PID: 8040)
- 360se.exe (PID: 9000)
- 360se.exe (PID: 8004)
- 360seupdate.exe (PID: 8292)
- sesvc.exe (PID: 8760)
- sesvr.exe (PID: 6664)
- 360huabao.exe (PID: 5336)
- 360bdoctor.exe (PID: 7568)
- 360se.exe (PID: 4028)
- 360se.exe (PID: 2940)
- 360se.exe (PID: 8520)
- 360se.exe (PID: 2284)
- MPHelper.exe (PID: 7404)
- 360se.exe (PID: 3196)
- 360se.exe (PID: 1976)
- 360se.exe (PID: 6600)
- env_detect.exe (PID: 6300)
- 360se.exe (PID: 9180)
- 360se.exe (PID: 6792)
- 360se.exe (PID: 1176)
- env_detect.exe (PID: 7960)
- 360se.exe (PID: 4300)
- 360huabao.exe (PID: 2420)
- 360se.exe (PID: 7332)
- 360se.exe (PID: 4700)
- 360bdoctor.exe (PID: 3796)
- 360se.exe (PID: 2856)
- 360bdoctor.exe (PID: 1792)
- MPHelper.exe (PID: 6400)
- 360se.exe (PID: 4284)
- 360se.exe (PID: 3440)
- 360seupdate.exe (PID: 7360)
- 360bdoctor.exe (PID: 6504)
- 360se.exe (PID: 4336)
- 360se.exe (PID: 4088)
- 360se.exe (PID: 8708)
- 360se.exe (PID: 5604)
- 360se.exe (PID: 8236)
- 360se.exe (PID: 1184)
- 360se.exe (PID: 2564)
- 360se.exe (PID: 5612)
- 360se.exe (PID: 4340)
- 360se.exe (PID: 5772)
- 360se.exe (PID: 8900)
- 360se.exe (PID: 5356)
- 360se.exe (PID: 8572)
- 360se.exe (PID: 3304)
- 360bdoctor.exe (PID: 7340)
- 360se.exe (PID: 8672)
- 360se.exe (PID: 2144)
- 360se.exe (PID: 8808)
- 360se.exe (PID: 6548)
- 360se.exe (PID: 1164)
- 360se.exe (PID: 9180)
- 360seupdate.exe (PID: 8424)
- 360bdoctor.exe (PID: 8264)
- sesvc.exe (PID: 5636)
- 360bdoctor.exe (PID: 5768)
- 360huabao.exe (PID: 8360)
- 360bdoctor.exe (PID: 408)
- 360bdoctor.exe (PID: 8628)
- 360seupdate.exe (PID: 8296)
- 360bdoctor.exe (PID: 2688)
- 360se.exe (PID: 5788)
- 360se.exe (PID: 8820)
- sesvr.exe (PID: 5044)
- 360bdoctor.exe (PID: 8540)
Reads the machine GUID from the registry
- SystemSettings.exe (PID: 6948)
- setup.exe (PID: 7364)
- 360se.exe (PID: 8364)
- 360bpsvc.exe (PID: 2992)
- 360bpsvc.exe (PID: 7264)
- 360se.exe (PID: 7880)
- 360bdoctor.exe (PID: 1600)
- 360bdoctor.exe (PID: 2432)
- sesvr.exe (PID: 8692)
- 360huabaosetup.exe (PID: 4828)
- 360se.exe (PID: 7828)
- 360se.exe (PID: 7920)
- MPHelper.exe (PID: 7404)
- 360bdoctor.exe (PID: 1792)
- 360bdoctor.exe (PID: 4344)
- 360se.exe (PID: 8672)
- 360bdoctor.exe (PID: 5768)
- 360bdoctor.exe (PID: 8628)
Reads the computer name
- SystemSettings.exe (PID: 6948)
- TextInputHost.exe (PID: 9112)
- 360se_setup.exe (PID: 6096)
- setup.exe (PID: 7364)
- setup.exe (PID: 8580)
- setup.exe (PID: 4336)
- setup.exe (PID: 8616)
- setup.exe (PID: 8888)
- 360se.exe (PID: 8364)
- 360se.exe (PID: 3656)
- 360se.exe (PID: 5736)
- 360se.exe (PID: 1080)
- 360bpsvc.exe (PID: 2992)
- 360bpsvc.exe (PID: 7264)
- 360se.exe (PID: 7880)
- sesvc.exe (PID: 8116)
- 360bdoctor.exe (PID: 1600)
- sesvc.exe (PID: 8112)
- 360bdoctor.exe (PID: 2432)
- 360se.exe (PID: 8208)
- sesvc.exe (PID: 1772)
- 360huabaosetup.exe (PID: 4828)
- sesvr.exe (PID: 8692)
- 360huabao.exe (PID: 8572)
- 360huabao.exe (PID: 2420)
- 360huabaosetup.exe (PID: 8140)
- sesvc.exe (PID: 7972)
- 360bdoctor.exe (PID: 4344)
- 360se.exe (PID: 7828)
- 360se.exe (PID: 7784)
- 360se.exe (PID: 7936)
- 360se.exe (PID: 7920)
- 360seupdate.exe (PID: 8292)
- sesvc.exe (PID: 8760)
- MPHelper.exe (PID: 7404)
- sesvr.exe (PID: 6664)
- env_detect.exe (PID: 6300)
- 360se.exe (PID: 7332)
- 360bdoctor.exe (PID: 1792)
- 360se.exe (PID: 3440)
- 360bdoctor.exe (PID: 7340)
- 360se.exe (PID: 8672)
- 360se.exe (PID: 8808)
- 360se.exe (PID: 9180)
- 360bdoctor.exe (PID: 5768)
- 360seupdate.exe (PID: 8424)
- sesvc.exe (PID: 5636)
- sesvr.exe (PID: 5044)
- 360bdoctor.exe (PID: 8628)
- 360bdoctor.exe (PID: 8540)
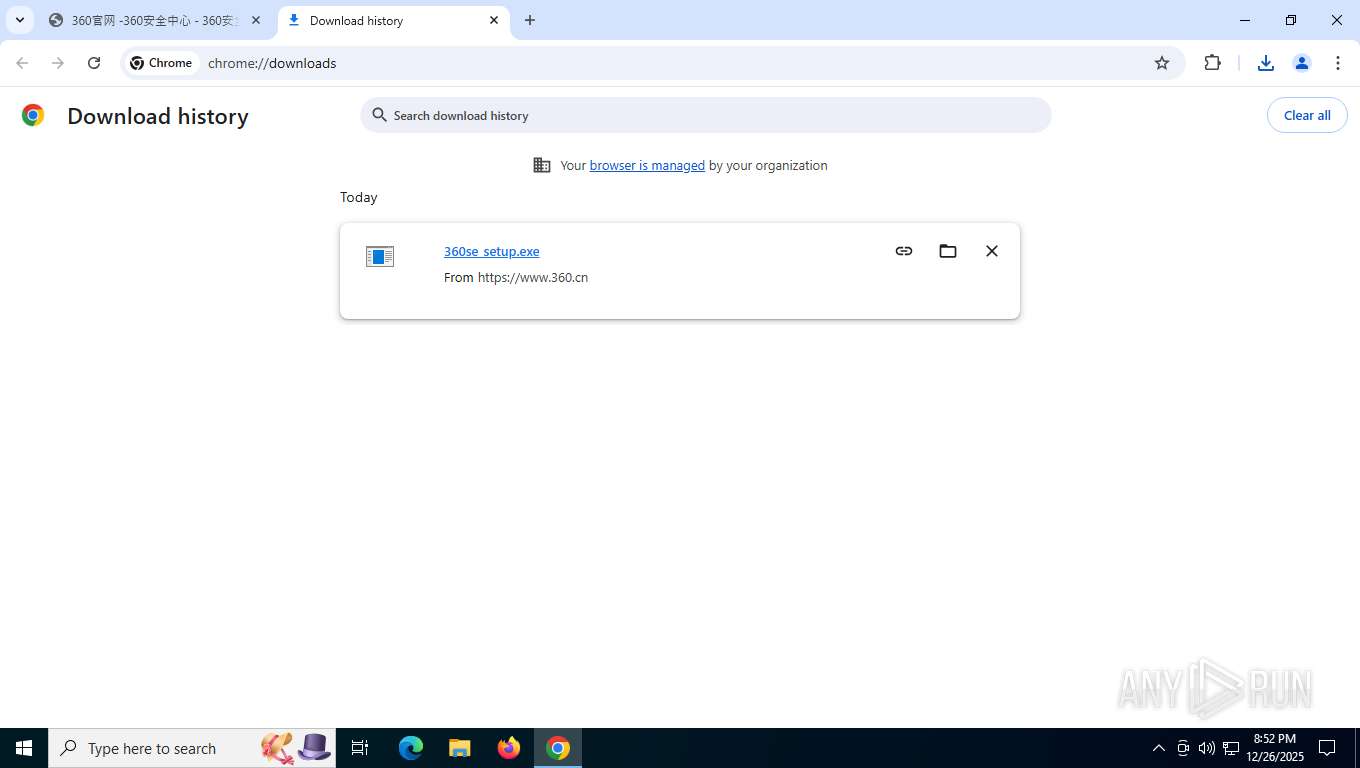
Executable content was dropped or overwritten
- chrome.exe (PID: 7628)
- chrome.exe (PID: 7448)
Create files in a temporary directory
- 360se_setup.exe (PID: 6096)
- setup.exe (PID: 7364)
- setup.exe (PID: 4336)
- setup.exe (PID: 8580)
- 360se.exe (PID: 8364)
- 360se.exe (PID: 7880)
- sesvc.exe (PID: 8112)
- 360se.exe (PID: 7920)
- MPHelper.exe (PID: 7404)
- 360huabaosetup.exe (PID: 8140)
- 360se.exe (PID: 8672)
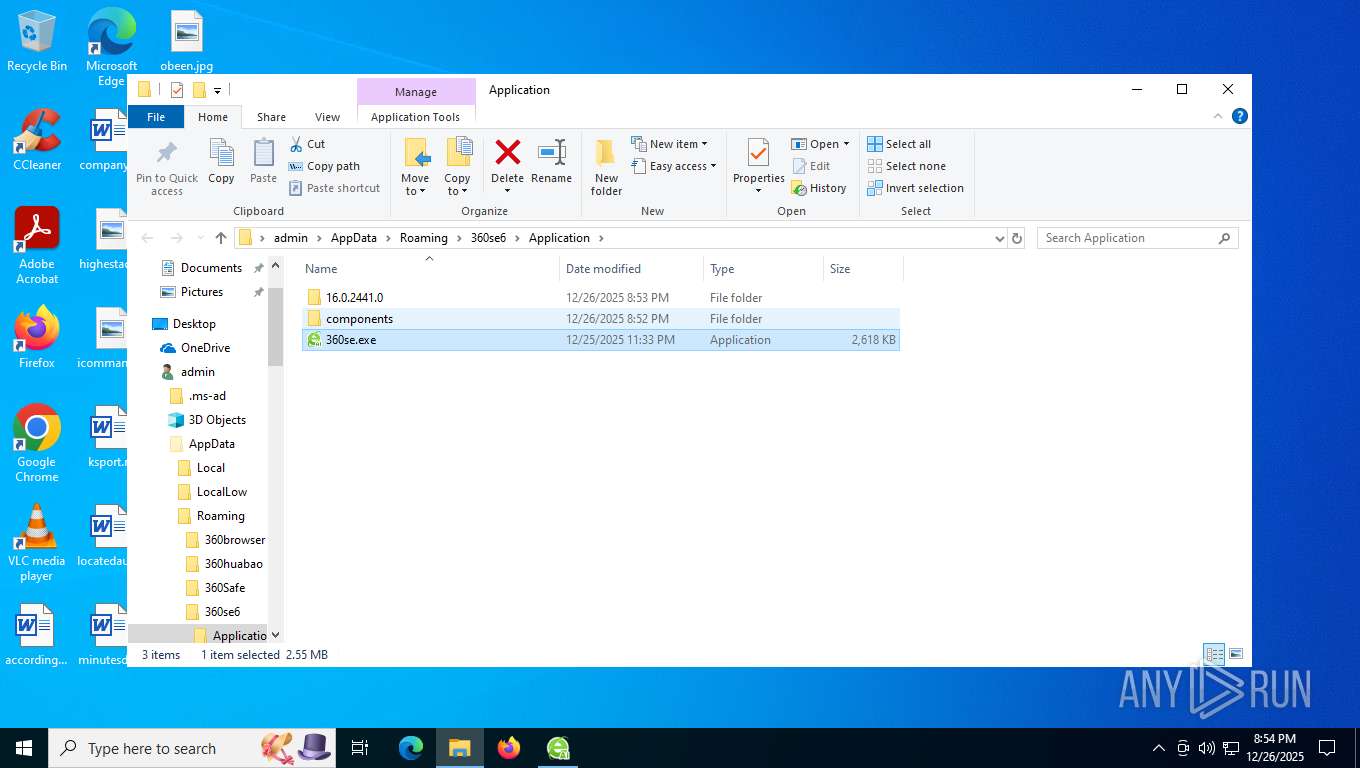
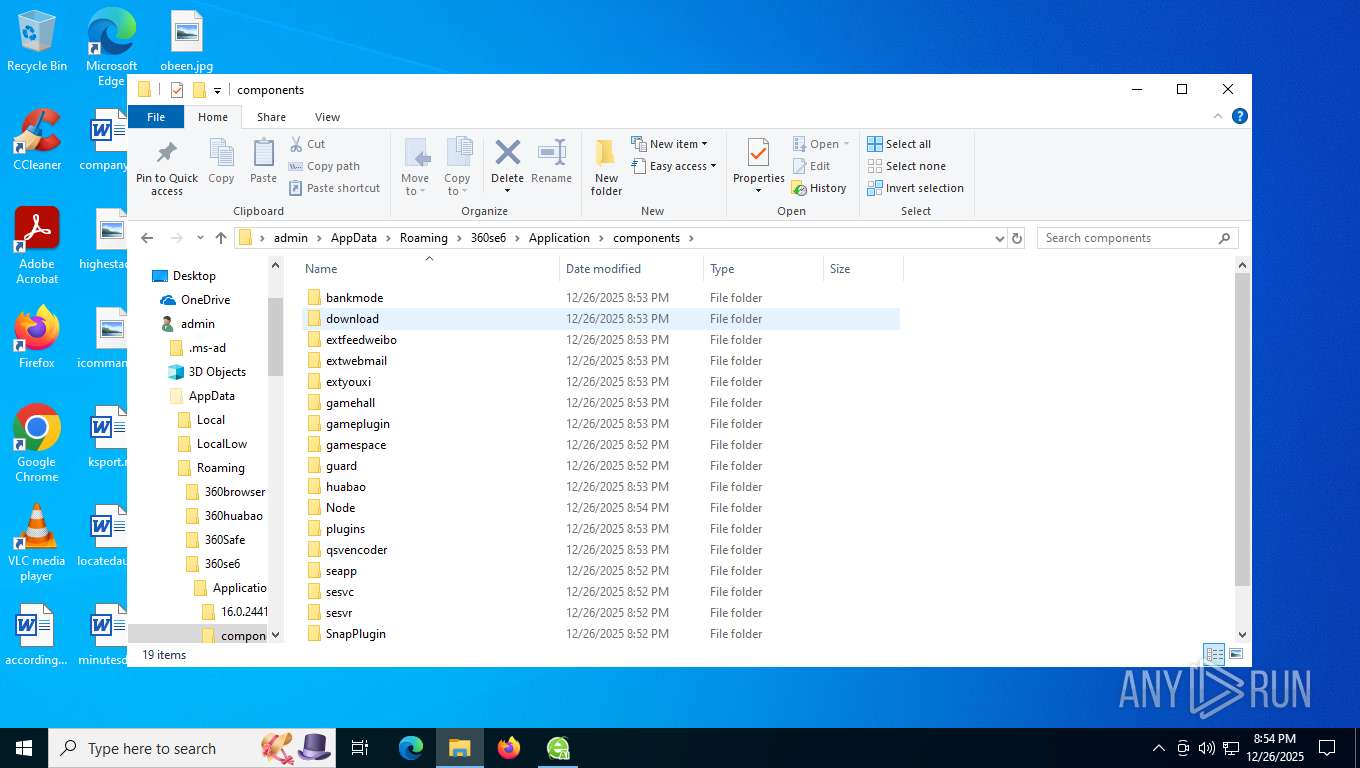
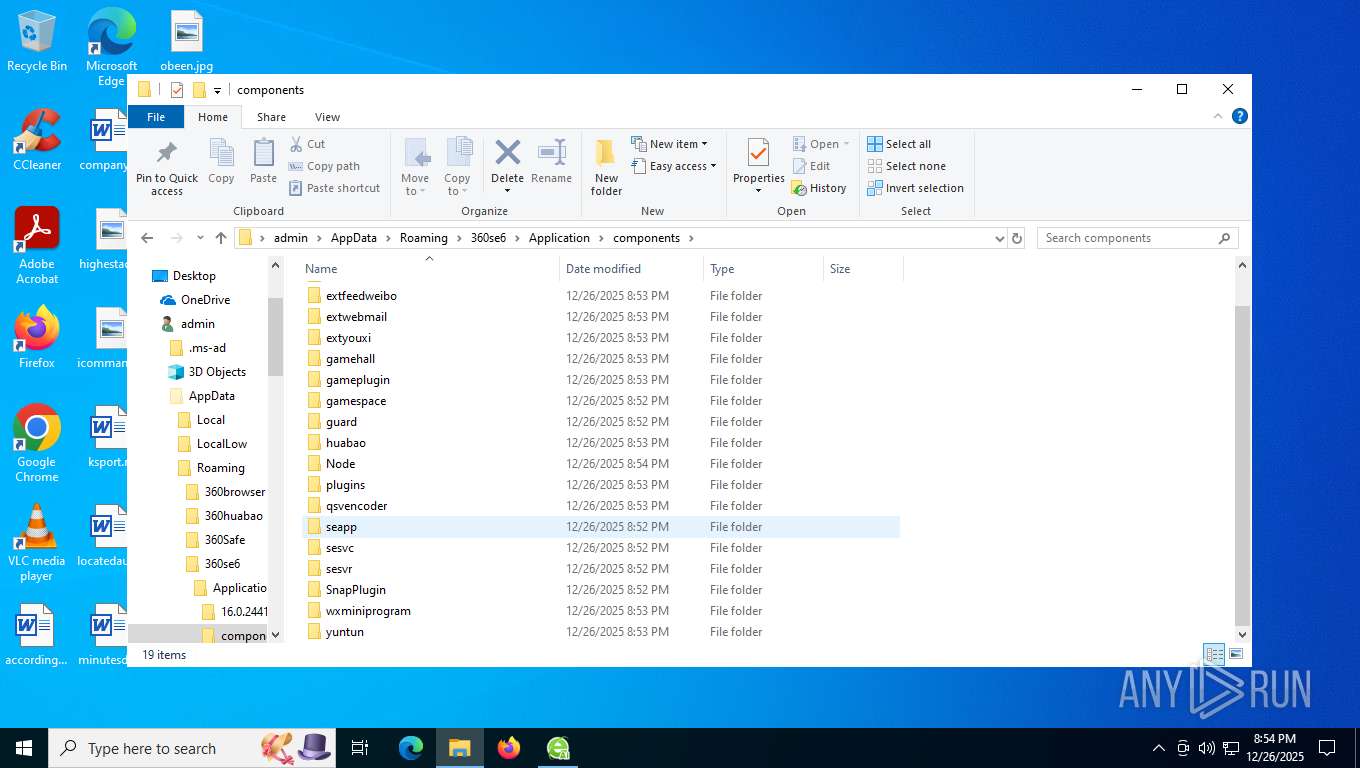
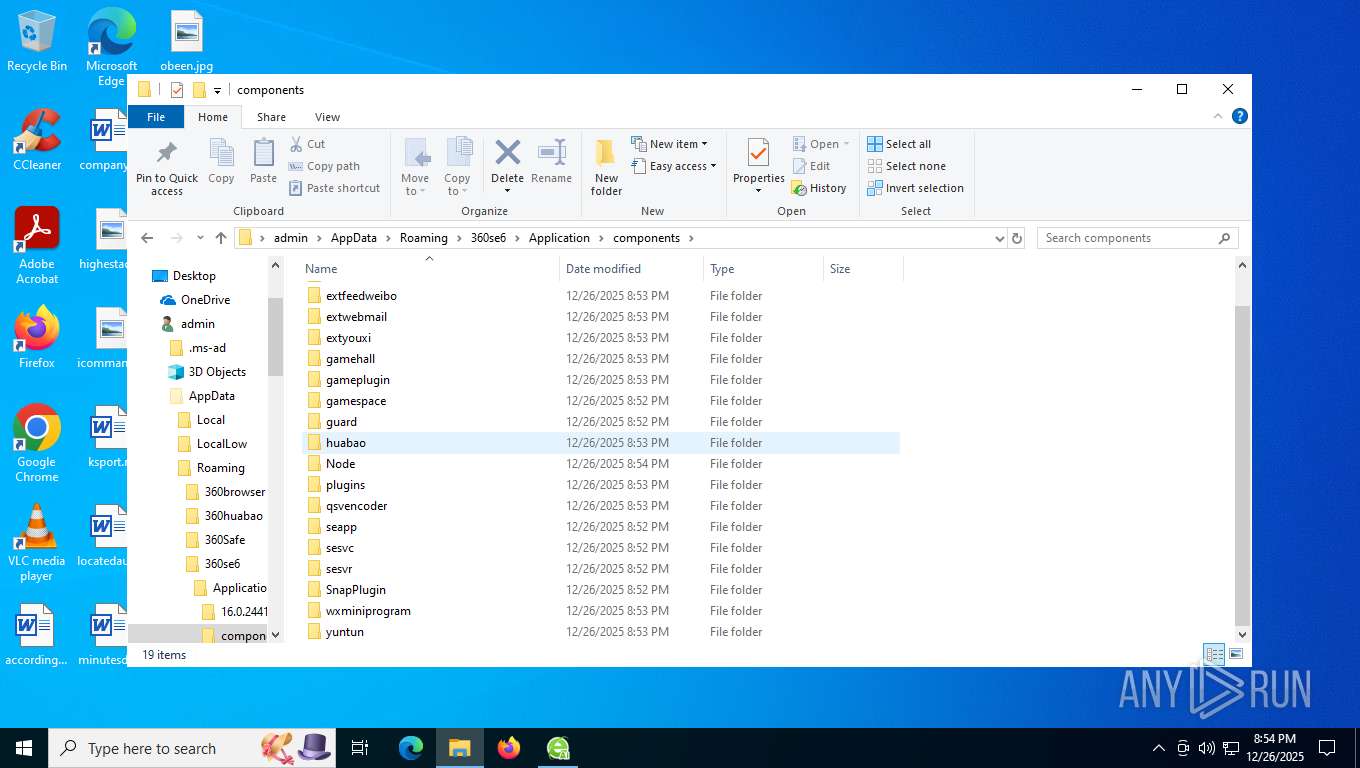
Creates files or folders in the user directory
- setup.exe (PID: 7364)
- setup.exe (PID: 8616)
- setup.exe (PID: 8580)
- setup.exe (PID: 4336)
- setup.exe (PID: 3060)
- setup.exe (PID: 8888)
- 360se.exe (PID: 8364)
- 360bpsvc.exe (PID: 2992)
- 360se.exe (PID: 5736)
- 360se.exe (PID: 7880)
- 360bpsvc.exe (PID: 7264)
- 360bdoctor.exe (PID: 1600)
- 360bdoctor.exe (PID: 2432)
- 360huabaosetup.exe (PID: 4828)
- 360se.exe (PID: 7828)
- 360se.exe (PID: 7920)
- 360se.exe (PID: 7784)
- MPHelper.exe (PID: 7404)
- 360bdoctor.exe (PID: 1792)
- 360huabaosetup.exe (PID: 8140)
- 360bdoctor.exe (PID: 7340)
- 360se.exe (PID: 8672)
- 360se.exe (PID: 9180)
- 360bdoctor.exe (PID: 4344)
- 360bdoctor.exe (PID: 5768)
- 360bdoctor.exe (PID: 8628)
- 360huabao.exe (PID: 2420)
The sample compiled with english language support
- chrome.exe (PID: 7448)
- 360se_setup.exe (PID: 6096)
- setup.exe (PID: 7364)
- 360bpsvc.exe (PID: 2992)
- 360se.exe (PID: 8364)
The sample compiled with chinese language support
- setup.exe (PID: 7364)
- 360bpsvc.exe (PID: 2992)
- 360bpsvc.exe (PID: 7264)
- 360se.exe (PID: 8364)
- 360se.exe (PID: 7880)
- 360huabaosetup.exe (PID: 4828)
- 360se.exe (PID: 7828)
- 360se.exe (PID: 7920)
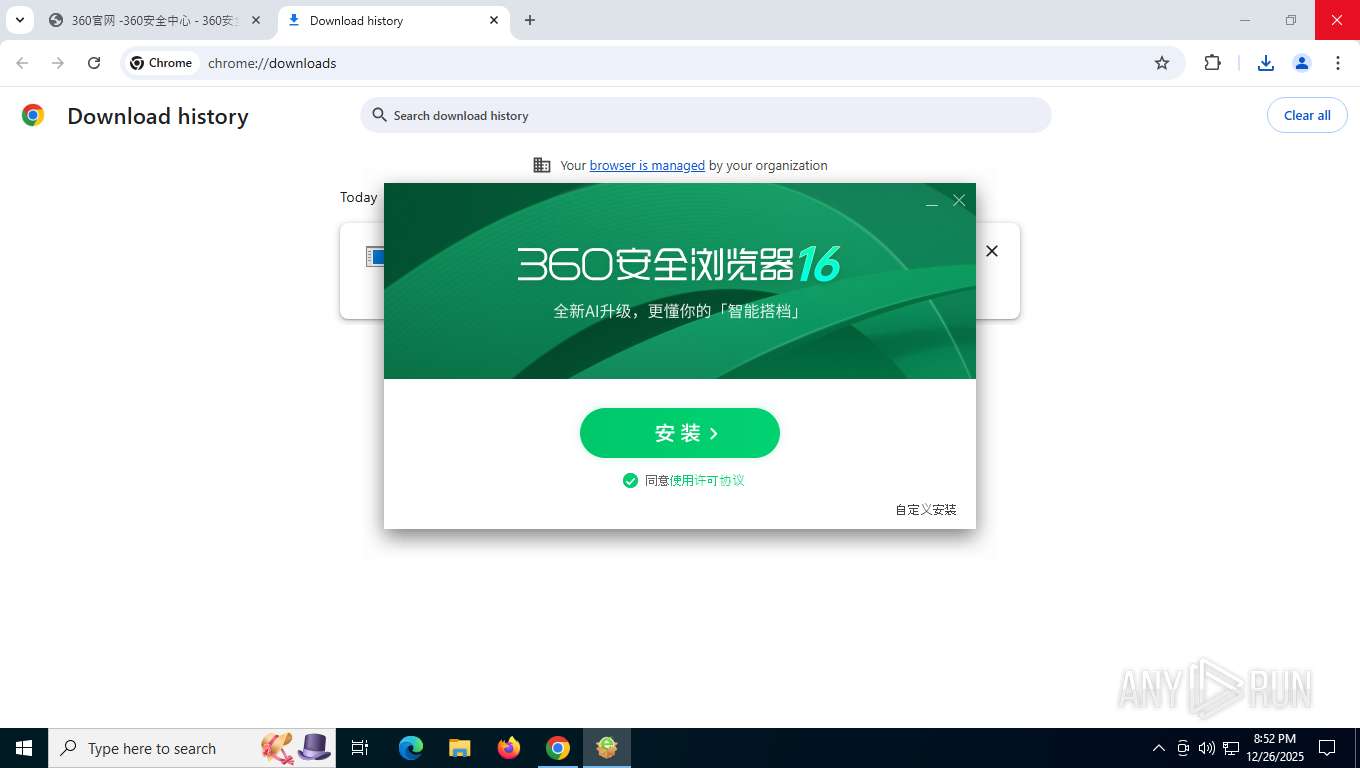
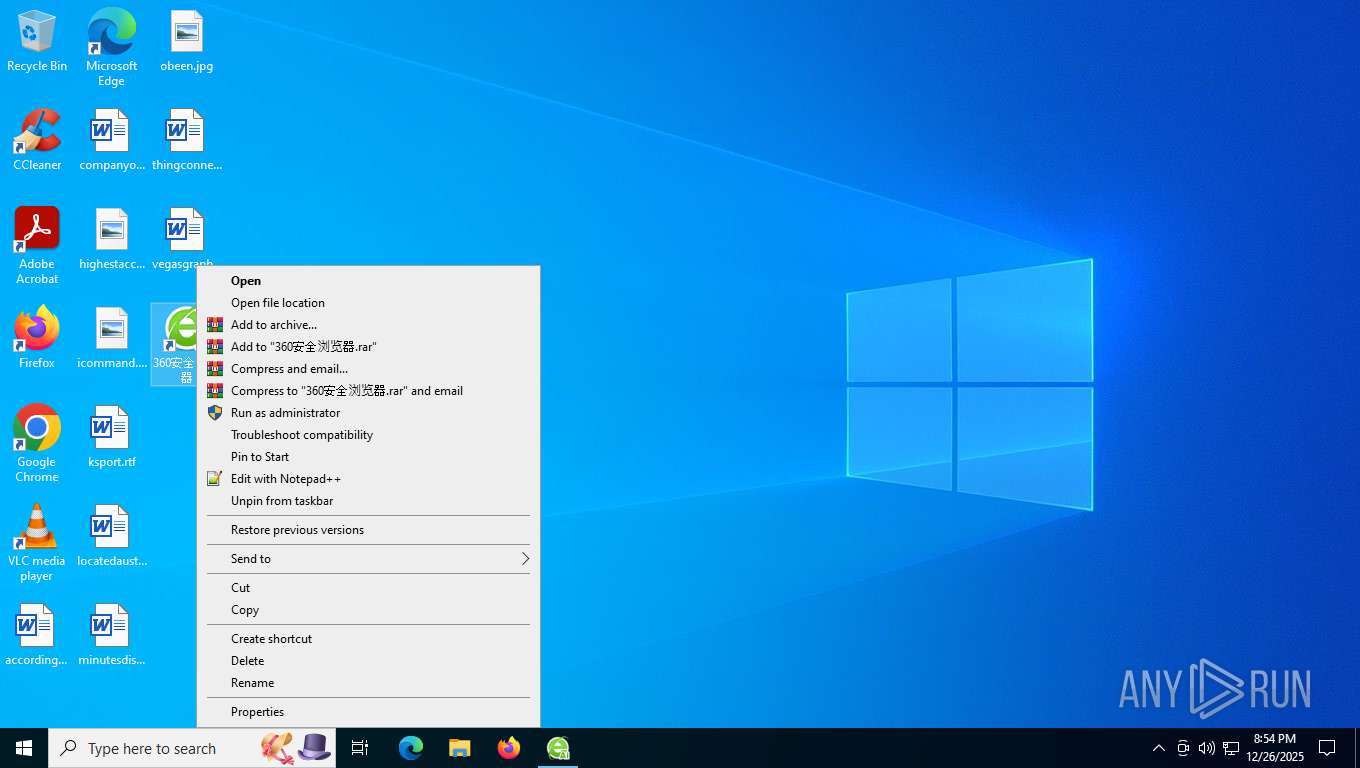
Creates a software uninstall entry
- setup.exe (PID: 7364)
Checks proxy server information
- setup.exe (PID: 7364)
- slui.exe (PID: 8176)
- 360se.exe (PID: 8364)
- 360se.exe (PID: 7880)
- 360bdoctor.exe (PID: 1600)
- 360bdoctor.exe (PID: 2432)
- 360huabaosetup.exe (PID: 4828)
- 360huabao.exe (PID: 8572)
- 360huabao.exe (PID: 2420)
- 360huabaosetup.exe (PID: 8140)
- 360bdoctor.exe (PID: 4344)
- sesvr.exe (PID: 8692)
- 360se.exe (PID: 7920)
- 360seupdate.exe (PID: 8292)
- MPHelper.exe (PID: 7404)
- 360bdoctor.exe (PID: 1792)
- 360bdoctor.exe (PID: 7340)
- 360se.exe (PID: 8672)
- 360bdoctor.exe (PID: 5768)
- 360seupdate.exe (PID: 8424)
- 360bdoctor.exe (PID: 8628)
- 360bdoctor.exe (PID: 8540)
Process checks computer location settings
- setup.exe (PID: 7364)
- setup.exe (PID: 3060)
- setup.exe (PID: 4336)
- 360se.exe (PID: 8364)
- 360se.exe (PID: 7548)
- 360se.exe (PID: 408)
- 360se.exe (PID: 8936)
- sesvc.exe (PID: 8116)
- sesvc.exe (PID: 8112)
- sesvc.exe (PID: 1772)
- 360huabao.exe (PID: 2420)
- 360se.exe (PID: 8216)
- 360se.exe (PID: 2712)
- 360se.exe (PID: 7920)
- 360se.exe (PID: 9000)
- 360se.exe (PID: 8004)
- sesvc.exe (PID: 8760)
- MPHelper.exe (PID: 7404)
- 360se.exe (PID: 6548)
- 360se.exe (PID: 1164)
- 360se.exe (PID: 8672)
- sesvc.exe (PID: 5636)
Launching a file from a Registry key
- setup.exe (PID: 7364)
- 360huabaosetup.exe (PID: 4828)
Disables trace logs
- 360bpsvc.exe (PID: 2992)
- 360bpsvc.exe (PID: 7264)
- 360se.exe (PID: 8364)
- 360se.exe (PID: 7880)
- sesvr.exe (PID: 8692)
- 360se.exe (PID: 7828)
- 360se.exe (PID: 7920)
- sesvr.exe (PID: 6664)
- 360se.exe (PID: 8672)
- sesvr.exe (PID: 5044)
Creates files in the program directory
- 360bpsvc.exe (PID: 7264)
- MPHelper.exe (PID: 7404)
Manual execution by a user
- sesvc.exe (PID: 1772)
- 360huabao.exe (PID: 4624)
- 360se.exe (PID: 7828)
- 360se.exe (PID: 8672)
- WinRAR.exe (PID: 8872)
Reads CPU info
- 360huabao.exe (PID: 2420)
Reads product name
- MPHelper.exe (PID: 7404)
Reads Environment values
- MPHelper.exe (PID: 7404)
Reads Windows Product ID
- MPHelper.exe (PID: 7404)
TeamViewer related mutex has been found
- MPHelper.exe (PID: 7404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
286
Monitored processes
128
Malicious processes
12
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
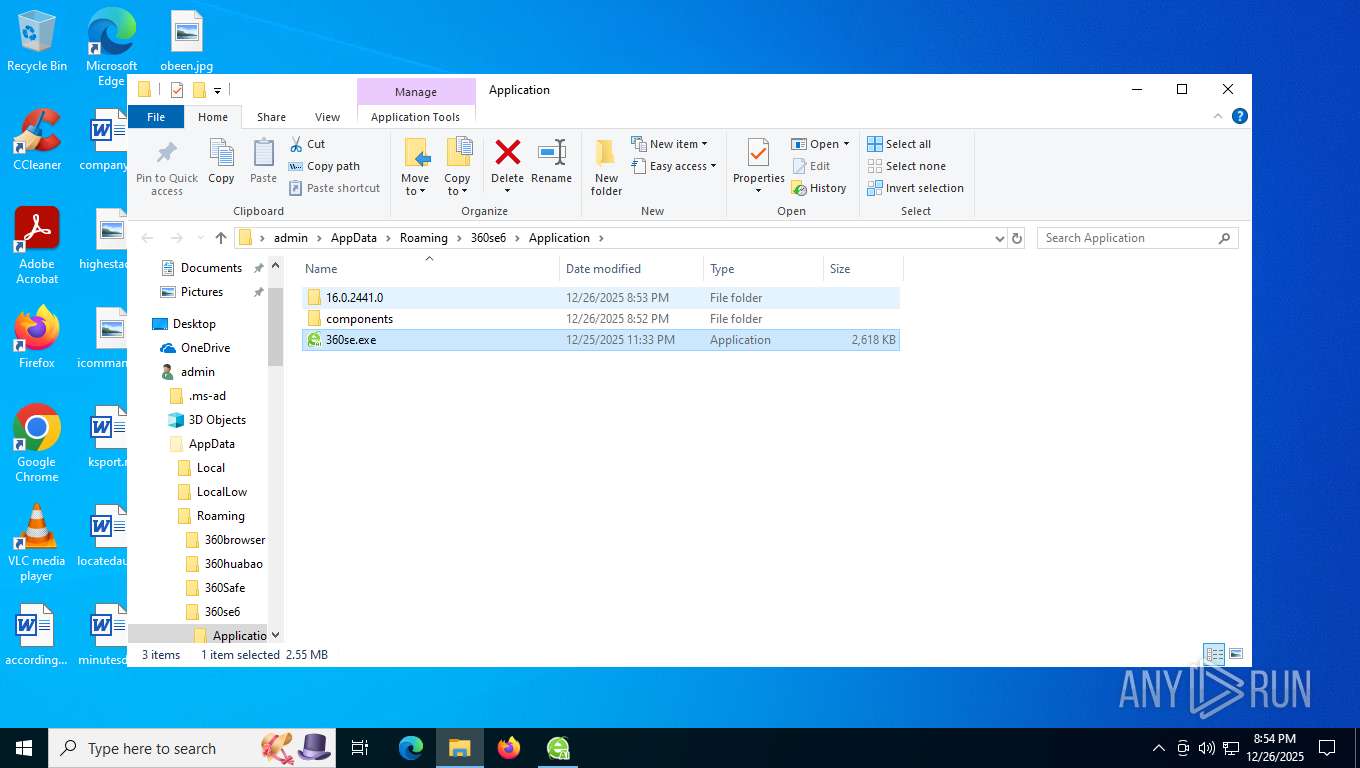
| 408 | "C:\Users\admin\AppData\Roaming\360se6\Application\360se.exe" --type=renderer --string-annotations --mainprocess-ver=16.0.2441.0 --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=4716,i,11734660713336805972,11886183435522713635,262144 --disable-features=HardwareMediaKeyHandling --variations-seed-version --mojo-platform-channel-handle=4700 /prefetch:1 | C:\Users\admin\AppData\Roaming\360se6\Application\360se.exe | — | 360se.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: LOW Description: 360安全浏览器 Exit code: 0 Version: 16.0.2441.0 Modules
| |||||||||||||||
| 408 | "C:\Users\admin\AppData\Roaming\360se6\Application\16.0.2441.0\360bdoctor.exe" /SE6_Frame="Start" | C:\Users\admin\AppData\Roaming\360se6\Application\16.0.2441.0\360bdoctor.exe | — | 360se.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: MEDIUM Description: 360浏览器医生 Exit code: 0 Version: 13.0.1094.0 Modules
| |||||||||||||||
| 1080 | "C:\Users\admin\AppData\Roaming\360se6\Application\360se.exe" --make-default-browser --install-by-self | C:\Users\admin\AppData\Roaming\360se6\Application\360se.exe | 360se.exe | ||||||||||||
User: admin Company: 360.cn Integrity Level: HIGH Description: 360安全浏览器 Exit code: 0 Version: 16.0.2441.0 Modules
| |||||||||||||||
| 1164 | "C:\Users\admin\AppData\Roaming\360se6\Application\360se.exe" --type=renderer --string-annotations --extension-process --mainprocess-ver=16.0.2441.0 --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3636,i,9216645752372019195,4069216158337707664,262144 --disable-features=HardwareMediaKeyHandling --variations-seed-version --mojo-platform-channel-handle=3640 /prefetch:2 | C:\Users\admin\AppData\Roaming\360se6\Application\360se.exe | — | 360se.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: LOW Description: 360安全浏览器 Version: 16.0.2441.0 Modules
| |||||||||||||||
| 1176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=3488,i,7198332371745331739,6281963878411615687,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=864 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1176 | "C:\Users\admin\AppData\Roaming\360se6\Application\360se.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --string-annotations --mainprocess-ver=16.0.2441.0 --field-trial-handle=6992,i,1550536676148461662,2059329943203427393,262144 --disable-features=HardwareMediaKeyHandling --variations-seed-version --mojo-platform-channel-handle=6800 /prefetch:8 | C:\Users\admin\AppData\Roaming\360se6\Application\360se.exe | — | 360se.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: LOW Description: 360安全浏览器 Exit code: 0 Version: 16.0.2441.0 Modules
| |||||||||||||||
| 1184 | "C:\Users\admin\AppData\Roaming\360se6\Application\360se.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --string-annotations --mainprocess-ver=16.0.2441.0 --field-trial-handle=7120,i,1550536676148461662,2059329943203427393,262144 --disable-features=HardwareMediaKeyHandling --variations-seed-version --mojo-platform-channel-handle=6848 /prefetch:8 | C:\Users\admin\AppData\Roaming\360se6\Application\360se.exe | — | 360se.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: LOW Description: 360安全浏览器 Exit code: 0 Version: 16.0.2441.0 Modules
| |||||||||||||||
| 1312 | "C:\Users\admin\AppData\Roaming\360se6\Application\360se.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --string-annotations --mainprocess-ver=16.0.2441.0 --field-trial-handle=3092,i,11734660713336805972,11886183435522713635,262144 --disable-features=HardwareMediaKeyHandling --variations-seed-version --mojo-platform-channel-handle=3060 /prefetch:8 | C:\Users\admin\AppData\Roaming\360se6\Application\360se.exe | — | 360se.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: LOW Description: 360安全浏览器 Exit code: 0 Version: 16.0.2441.0 Modules
| |||||||||||||||
| 1600 | "C:\Users\admin\AppData\Roaming\360se6\Application\16.0.2441.0\360bdoctor.exe" /SE6_Frame="Start" | C:\Users\admin\AppData\Roaming\360se6\Application\16.0.2441.0\360bdoctor.exe | 360se.exe | ||||||||||||
User: admin Company: 360.cn Integrity Level: MEDIUM Description: 360浏览器医生 Exit code: 0 Version: 13.0.1094.0 Modules
| |||||||||||||||
| 1772 | "C:\Users\admin\AppData\Roaming\360se6\Application\components\sesvc\sesvc.exe" /b:1 /c:1 | C:\Users\admin\AppData\Roaming\360se6\Application\components\sesvc\sesvc.exe | — | explorer.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: MEDIUM Description: 360安全浏览器 服务组件 Exit code: 4294967286 Version: 13.1.5088.0 Modules
| |||||||||||||||
Total events
52 278
Read events
51 417
Write events
789
Delete events
72
Modification events
| (PID) Process: | (6948) SystemSettings.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (6948) SystemSettings.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6948) SystemSettings.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6948) SystemSettings.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7364) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\360\360se6\Chrome |
| Operation: | write | Name: | sh_chid |
Value: Cvsi3L/NSjkOABEJFOiRrXKwYZ4zy/KlcLgEwBN/58jiua54DAJ/pm+FGDYjgaKa5w7nhP1pqPZVJPBeb2KMdBp4GqleqS2oxUiSfdQKfxw= | |||
| (PID) Process: | (7364) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\360\360se6\Chrome |
| Operation: | write | Name: | update_components |
Value: 1 | |||
| (PID) Process: | (7364) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\fbd30ee5-8150-549e-9aed-fd9d4443\05 |
| Operation: | write | Name: | inst_time |
Value: D43B4F6900000000 | |||
| (PID) Process: | (7364) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\fbd30ee5-8150-549e-9aed-fd9d4443\05 |
| Operation: | write | Name: | inst_times |
Value: 1 | |||
| (PID) Process: | (7364) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\360\360se6\Update\Clients\{02E720BD-2B50-4404-947C-65DBE64F6970} |
| Operation: | write | Name: | name |
Value: 360安全浏览器 | |||
| (PID) Process: | (7364) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\360\360se6\Update\Clients\{02E720BD-2B50-4404-947C-65DBE64F6970} |
| Operation: | write | Name: | pv |
Value: 16.0.2441.0 | |||
Executable files
117
Suspicious files
543
Text files
590
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RFfe11f.TMP | — | |
MD5:— | SHA256:— | |||
| 7628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RFfe11f.TMP | — | |
MD5:— | SHA256:— | |||
| 7628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RFfe12f.TMP | — | |
MD5:— | SHA256:— | |||
| 7628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RFfe12f.TMP | — | |
MD5:— | SHA256:— | |||
| 7628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old~RFfe12f.TMP | — | |
MD5:— | SHA256:— | |||
| 7628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RFfe12f.TMP | — | |
MD5:— | SHA256:— | |||
| 7628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1 493
TCP/UDP connections
905
DNS requests
773
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7876 | chrome.exe | GET | 200 | 142.250.186.110:80 | http://clients2.google.com/time/1/current?cup2key=8:DiCE2fRSfk67cOTEJ8eAunDSb4uMvQc-CiVFe65UZzM&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 106 b | whitelisted |
7876 | chrome.exe | GET | 200 | 216.58.212.138:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | US | binary | 41 b | whitelisted |
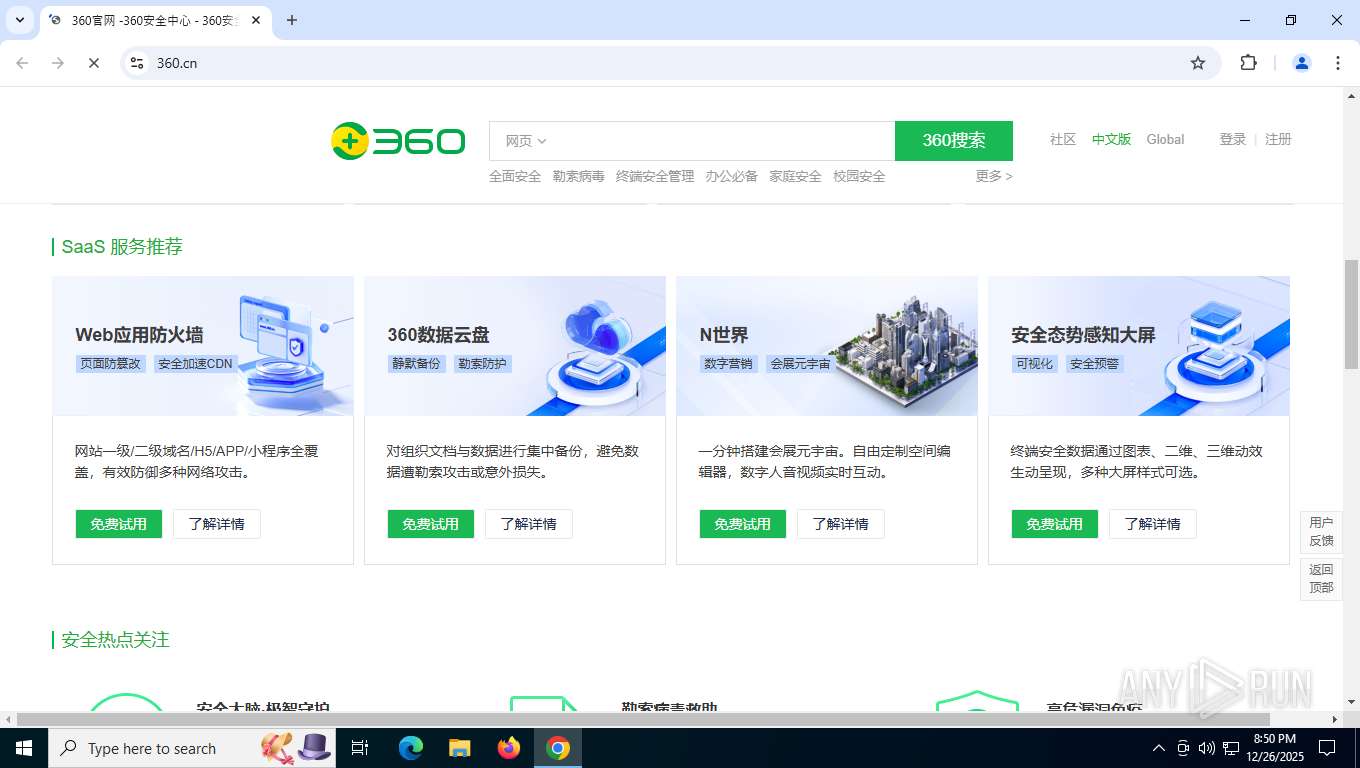
7876 | chrome.exe | GET | 301 | 36.99.171.154:80 | http://360.cn/ | CN | html | 178 b | unknown |
7876 | chrome.exe | GET | 200 | 47.89.195.194:443 | https://www.360.cn/ | CN | html | 91.1 Kb | unknown |
7876 | chrome.exe | GET | 200 | 18.238.243.4:443 | https://s.ssl.qhimg.com/static/20727b67b294c45a.css | US | text | 1.90 Kb | unknown |
7876 | chrome.exe | GET | 200 | 18.238.243.4:443 | https://s.ssl.qhimg.com/static/5026c8045e19af4c.css | US | text | 2.25 Kb | unknown |
7876 | chrome.exe | GET | 200 | 18.238.243.4:443 | https://s.ssl.qhimg.com/static/8df7607a0236a0b3.css | US | text | 42.5 Kb | unknown |
7876 | chrome.exe | GET | 200 | 18.238.243.4:443 | https://s.ssl.qhimg.com/static/0729c697c74a3b98.js | US | text | 125 b | unknown |
7876 | chrome.exe | GET | 200 | 157.185.129.27:443 | https://p1.ssl.qhimg.com/t0124ffc462e472bfd1.png | CA | image | 1.71 Kb | unknown |
7876 | chrome.exe | GET | 200 | 18.238.243.4:443 | https://s.ssl.qhimg.com/static/f5407c785655e6a1/monitor_analytic.js | US | text | 8.96 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
408 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6236 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7876 | chrome.exe | 142.250.186.110:80 | clients2.google.com | GOOGLE | US | whitelisted |
7876 | chrome.exe | 216.58.212.138:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
7876 | chrome.exe | 142.251.168.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7876 | chrome.exe | 36.99.171.154:80 | 360.cn | CHINANET-BACKBONE No.31,Jin-rong Street | CN | whitelisted |
7876 | chrome.exe | 106.63.103.5:443 | 360.cn | CHINATELECOM-IDC-BTHBD-AP China Telecom Beijing Tianjin Hebei Big Data Industry Park Branch | CN | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
360.cn |
| whitelisted |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.360.cn |
| whitelisted |
s.ssl.qhimg.com |
| whitelisted |
p3.ssl.qhimg.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
8692 | sesvr.exe | Potentially Bad Traffic | ET INFO HTTP traffic on port 443 (POST) |
— | — | Potentially Bad Traffic | ET HUNTING Zero Content-Length HTTP POST with data (outbound) |
Process | Message |
|---|---|
360se.exe | [desktop]ReadQcmDotData: |
sesvr.exe | sesvr:channel4:WTSRegisterSessionNotification:1 |
sesvr.exe | sesvr:channel4:CheckQueryInterByReg first time is 1 |
sesvr.exe | sesvr:channel4:UpdatePopupDataConfig |
sesvr.exe | sesvr:channel4:GetOBSProcessList:0 |
sesvr.exe | sesvr:channel4:OBS |
sesvr.exe | sesvr:channel4:Youth json data parsed successfully! |
sesvr.exe | sesvr:channel4:llq_pro_list size:0 r:0 |
sesvr.exe | sesvr:channel4:ws_pro_list size:140 r:0 |
sesvr.exe | sesvr:channel4:GetPBExeList:0 |