| File name: | 7a0eeda7628f3afea678a177e32ac46b.exe |
| Full analysis: | https://app.any.run/tasks/1fa710a9-9c27-490a-8a3c-2798efb5ea99 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | April 29, 2025, 06:21:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 7 sections |
| MD5: | 7A0EEDA7628F3AFEA678A177E32AC46B |
| SHA1: | 91212D5E51E0BE5473D401E2DC37E13B6223E73D |
| SHA256: | BDB6BCAE5AF5ED105AD0A4DF2FFB5C3670F52C5FA654BA3CD00B2F862BDC9B91 |
| SSDEEP: | 98304:Q7CnHRE7//jLTQ4m0F8MjO6n0OxVRjKCcWmKgNtkqDq7upZ8ElBOZ+DebQfNisHU:p |
MALICIOUS
Actions looks like stealing of personal data
- 7a0eeda7628f3afea678a177e32ac46b.exe (PID: 5608)
- zb7jDew.exe (PID: 2040)
- MSBuild.exe (PID: 7036)
- core.exe (PID: 1532)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- zb7jDew.exe (PID: 2040)
- MSBuild.exe (PID: 1096)
LUMMA mutex has been found
- 7a0eeda7628f3afea678a177e32ac46b.exe (PID: 5608)
- zb7jDew.exe (PID: 2040)
- core.exe (PID: 1532)
AMADEY has been found (auto)
- 7a0eeda7628f3afea678a177e32ac46b.exe (PID: 5608)
- 2OD7IBXQP627GMB3XPD7SSVSO.exe (PID: 6132)
Connects to the CnC server
- svchost.exe (PID: 2196)
- saved.exe (PID: 6540)
- laren.exe (PID: 5176)
- Microsoft Edge.exe (PID: 8272)
AMADEY has been detected (YARA)
- saved.exe (PID: 6540)
AMADEY has been detected (SURICATA)
- saved.exe (PID: 6540)
- laren.exe (PID: 5176)
Executing a file with an untrusted certificate
- core.exe (PID: 1532)
- d3wZ1ZwD9N.exe (PID: 7604)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
STEALER has been found (auto)
- saved.exe (PID: 6540)
VIDAR mutex has been found
- MSBuild.exe (PID: 7036)
AMADEY mutex has been found
- amnew.exe (PID: 5308)
- laren.exe (PID: 5176)
- laren.exe (PID: 7664)
Stealers network behavior
- svchost.exe (PID: 2196)
GENERIC has been found (auto)
- d6c4cc96ee.exe (PID: 6512)
- svchost015.exe (PID: 4696)
RHADAMANTHYS mutex has been found
- svchost.exe (PID: 7740)
- 040357508e.exe (PID: 7336)
GCLEANER has been detected (SURICATA)
- svchost015.exe (PID: 4696)
Bypass execution policy to execute commands
- powershell.exe (PID: 8136)
Changes powershell execution policy (Bypass)
- core.exe (PID: 1532)
UPATRE has been detected (SURICATA)
- svchost.exe (PID: 4976)
- svchost.exe (PID: 7740)
Uses Task Scheduler to run other applications
- MSBuild.exe (PID: 7584)
XWORM has been detected
- MSBuild.exe (PID: 7584)
XWORM has been detected (SURICATA)
- MSBuild.exe (PID: 7584)
QUASAR has been detected (SURICATA)
- Microsoft Edge.exe (PID: 8272)
SUSPICIOUS
Reads the BIOS version
- 7a0eeda7628f3afea678a177e32ac46b.exe (PID: 5608)
- d6c4cc96ee.exe (PID: 6512)
- 040357508e.exe (PID: 7336)
Executable content was dropped or overwritten
- 7a0eeda7628f3afea678a177e32ac46b.exe (PID: 5608)
- 2OD7IBXQP627GMB3XPD7SSVSO.exe (PID: 6132)
- saved.exe (PID: 6540)
- dfe10e0ea7.exe (PID: 2316)
- dfe10e0ea7.tmp (PID: 6112)
- amnew.exe (PID: 5308)
- d6c4cc96ee.exe (PID: 6512)
- cmd.exe (PID: 7528)
- svchost015.exe (PID: 4696)
- euvVK2Ss6Qrsl.exe (PID: 4228)
- euvVK2Ss6Qrsl.tmp (PID: 3124)
- filelistcreatorassist15.exe (PID: 7752)
- MSBuild.exe (PID: 7036)
- c2vkng4e3w.exe (PID: 9148)
- aF5pbXGeKw57aef3.exe (PID: 9164)
- kno8yc26xt.exe (PID: 8148)
- lng4w47g4e.exe (PID: 8480)
- NvidiaDriver.exe (PID: 2240)
- MSBuild.exe (PID: 7584)
- 2v3w47qq1n.exe (PID: 8584)
- 4w479zuk6p.exe (PID: 1184)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- saved.exe (PID: 6540)
- zb7jDew.exe (PID: 2040)
- laren.exe (PID: 5176)
- MSBuild.exe (PID: 1096)
- MSBuild.exe (PID: 7584)
- Microsoft Edge.exe (PID: 8272)
Process requests binary or script from the Internet
- 7a0eeda7628f3afea678a177e32ac46b.exe (PID: 5608)
- saved.exe (PID: 6540)
- MSBuild.exe (PID: 7036)
- NvidiaDriver.exe (PID: 2240)
- aF5pbXGeKw57aef3.exe (PID: 9164)
Searches for installed software
- 7a0eeda7628f3afea678a177e32ac46b.exe (PID: 5608)
- MSBuild.exe (PID: 7036)
- zb7jDew.exe (PID: 2040)
- core.exe (PID: 1532)
Potential Corporate Privacy Violation
- 7a0eeda7628f3afea678a177e32ac46b.exe (PID: 5608)
- saved.exe (PID: 6540)
- svchost015.exe (PID: 4696)
- MSBuild.exe (PID: 7036)
- aF5pbXGeKw57aef3.exe (PID: 9164)
- NvidiaDriver.exe (PID: 2240)
Connects to the server without a host name
- 7a0eeda7628f3afea678a177e32ac46b.exe (PID: 5608)
- saved.exe (PID: 6540)
- laren.exe (PID: 5176)
- svchost015.exe (PID: 4696)
- MSBuild.exe (PID: 7036)
- aF5pbXGeKw57aef3.exe (PID: 9164)
- NvidiaDriver.exe (PID: 2240)
Reads security settings of Internet Explorer
- 2OD7IBXQP627GMB3XPD7SSVSO.exe (PID: 6132)
- saved.exe (PID: 6540)
- dfe10e0ea7.tmp (PID: 6112)
- MSBuild.exe (PID: 7036)
- amnew.exe (PID: 5308)
- laren.exe (PID: 5176)
- svchost015.exe (PID: 4696)
Starts itself from another location
- 2OD7IBXQP627GMB3XPD7SSVSO.exe (PID: 6132)
- amnew.exe (PID: 5308)
- c2vkng4e3w.exe (PID: 9148)
- aF5pbXGeKw57aef3.exe (PID: 9164)
- lng4w47g4e.exe (PID: 8480)
- NvidiaDriver.exe (PID: 2240)
- 2v3w47qq1n.exe (PID: 8584)
- 4w479zuk6p.exe (PID: 1184)
There is functionality for enable RDP (YARA)
- saved.exe (PID: 6540)
There is functionality for taking screenshot (YARA)
- saved.exe (PID: 6540)
Reads the Windows owner or organization settings
- dfe10e0ea7.tmp (PID: 6112)
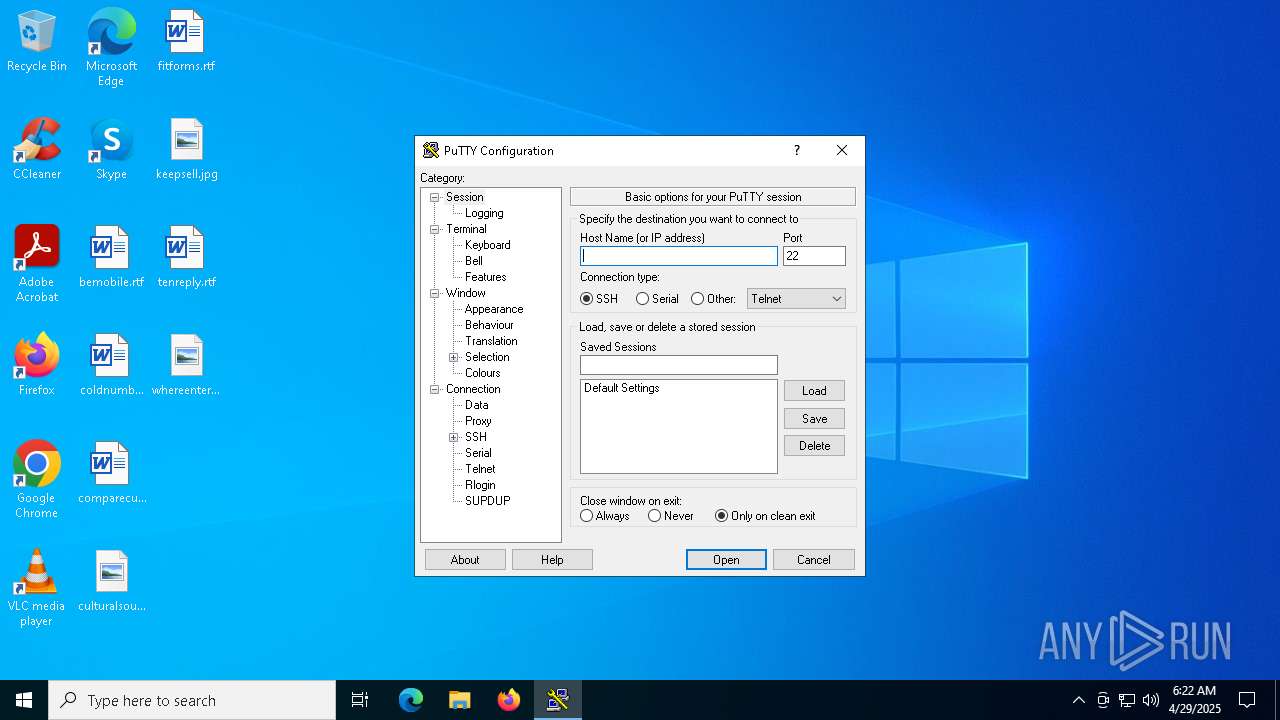
PUTTY has been detected
- putty.exe (PID: 2236)
Process drops legitimate windows executable
- saved.exe (PID: 6540)
- euvVK2Ss6Qrsl.tmp (PID: 3124)
- MSBuild.exe (PID: 7036)
- NvidiaDriver.exe (PID: 2240)
- aF5pbXGeKw57aef3.exe (PID: 9164)
- MSBuild.exe (PID: 7584)
Starts a Microsoft application from unusual location
- K2bpz1U.exe (PID: 5124)
- VisualCode.exe (PID: 6148)
- 47Q6wZM.exe (PID: 7916)
- xYMQ3dRKydU58tU9.exe (PID: 8412)
- fc3b4777d54d4d5e80b2741ebd5a74c2.exe (PID: 10908)
Connects to unusual port
- MSBuild.exe (PID: 2644)
- svchost.exe (PID: 7740)
- svchost.exe (PID: 4976)
- dllhost.exe (PID: 9000)
- aF5pbXGeKw57aef3.exe (PID: 9164)
- 1gdJZ6k4uNSRL3EQ.exe (PID: 8364)
- Microsoft Edge.exe (PID: 8272)
- MSBuild.exe (PID: 7584)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 7036)
- Vault.com (PID: 8848)
Hides command output
- cmd.exe (PID: 7272)
- cmd.exe (PID: 7528)
The process executes via Task Scheduler
- saved.exe (PID: 7612)
- laren.exe (PID: 7664)
- laren.exe (PID: 13012)
- saved.exe (PID: 12992)
- svchost.exe (PID: 13040)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7272)
- cmd.exe (PID: 7528)
Executes application which crashes
- 040357508e.exe (PID: 7336)
The process checks if it is being run in the virtual environment
- svchost.exe (PID: 7740)
Starts CMD.EXE for commands execution
- JSEVGJV.exe (PID: 4200)
- d3wZ1ZwD9N.exe (PID: 7604)
- cmd.exe (PID: 8404)
- MSBuild.exe (PID: 7036)
Starts POWERSHELL.EXE for commands execution
- core.exe (PID: 1532)
- filelistcreatorassist15.exe (PID: 7752)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7272)
The process drops C-runtime libraries
- euvVK2Ss6Qrsl.tmp (PID: 3124)
Executing commands from a ".bat" file
- d3wZ1ZwD9N.exe (PID: 7604)
Get information on the list of running processes
- cmd.exe (PID: 8404)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 8404)
Starts the AutoIt3 executable file
- cmd.exe (PID: 8404)
The executable file from the user directory is run by the CMD process
- Vault.com (PID: 8848)
Application launched itself
- cmd.exe (PID: 8404)
Starts application with an unusual extension
- cmd.exe (PID: 8404)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 10844)
Checks for external IP
- svchost.exe (PID: 2196)
INFO
Checks supported languages
- 7a0eeda7628f3afea678a177e32ac46b.exe (PID: 5608)
- 2OD7IBXQP627GMB3XPD7SSVSO.exe (PID: 6132)
- saved.exe (PID: 6540)
- dfe10e0ea7.exe (PID: 2316)
- dfe10e0ea7.tmp (PID: 6112)
- putty.exe (PID: 2236)
- d6c4cc96ee.exe (PID: 6512)
- core.exe (PID: 1532)
- info.exe (PID: 4452)
- K2bpz1U.exe (PID: 5124)
- MSBuild.exe (PID: 2644)
- zb7jDew.exe (PID: 2040)
- VisualCode.exe (PID: 6148)
- MSBuild.exe (PID: 7036)
- amnew.exe (PID: 5308)
- laren.exe (PID: 5176)
- svchost015.exe (PID: 4696)
- JSEVGJV.exe (PID: 4200)
- 040357508e.exe (PID: 7336)
- laren.exe (PID: 7664)
- saved.exe (PID: 7612)
Reads the computer name
- 7a0eeda7628f3afea678a177e32ac46b.exe (PID: 5608)
- 2OD7IBXQP627GMB3XPD7SSVSO.exe (PID: 6132)
- saved.exe (PID: 6540)
- putty.exe (PID: 2236)
- dfe10e0ea7.tmp (PID: 6112)
- info.exe (PID: 4452)
- MSBuild.exe (PID: 2644)
- amnew.exe (PID: 5308)
- zb7jDew.exe (PID: 2040)
- laren.exe (PID: 5176)
- MSBuild.exe (PID: 7036)
- d6c4cc96ee.exe (PID: 6512)
- JSEVGJV.exe (PID: 4200)
- svchost015.exe (PID: 4696)
- core.exe (PID: 1532)
Reads the software policy settings
- 7a0eeda7628f3afea678a177e32ac46b.exe (PID: 5608)
- MSBuild.exe (PID: 7036)
- zb7jDew.exe (PID: 2040)
- svchost015.exe (PID: 4696)
- core.exe (PID: 1532)
Create files in a temporary directory
- 7a0eeda7628f3afea678a177e32ac46b.exe (PID: 5608)
- 2OD7IBXQP627GMB3XPD7SSVSO.exe (PID: 6132)
- saved.exe (PID: 6540)
- dfe10e0ea7.exe (PID: 2316)
- dfe10e0ea7.tmp (PID: 6112)
- amnew.exe (PID: 5308)
- d6c4cc96ee.exe (PID: 6512)
Process checks computer location settings
- 2OD7IBXQP627GMB3XPD7SSVSO.exe (PID: 6132)
- saved.exe (PID: 6540)
- dfe10e0ea7.tmp (PID: 6112)
- amnew.exe (PID: 5308)
Checks proxy server information
- saved.exe (PID: 6540)
- MSBuild.exe (PID: 7036)
- laren.exe (PID: 5176)
- svchost015.exe (PID: 4696)
Creates files or folders in the user directory
- saved.exe (PID: 6540)
- dfe10e0ea7.tmp (PID: 6112)
- MSBuild.exe (PID: 7036)
- svchost015.exe (PID: 4696)
The sample compiled with english language support
- dfe10e0ea7.tmp (PID: 6112)
- saved.exe (PID: 6540)
- d6c4cc96ee.exe (PID: 6512)
- cmd.exe (PID: 7528)
- euvVK2Ss6Qrsl.tmp (PID: 3124)
- MSBuild.exe (PID: 7036)
- NvidiaDriver.exe (PID: 2240)
- aF5pbXGeKw57aef3.exe (PID: 9164)
- MSBuild.exe (PID: 7584)
Creates a software uninstall entry
- dfe10e0ea7.tmp (PID: 6112)
Compiled with Borland Delphi (YARA)
- d6c4cc96ee.exe (PID: 6512)
Reads the machine GUID from the registry
- MSBuild.exe (PID: 2644)
- MSBuild.exe (PID: 7036)
- JSEVGJV.exe (PID: 4200)
- svchost015.exe (PID: 4696)
Themida protector has been detected
- d6c4cc96ee.exe (PID: 6512)
Creates files in the program directory
- MSBuild.exe (PID: 7036)
Attempting to use instant messaging service
- MSBuild.exe (PID: 7036)
Reads product name
- MSBuild.exe (PID: 7036)
Reads Environment values
- MSBuild.exe (PID: 7036)
Reads CPU info
- MSBuild.exe (PID: 7036)
Application launched itself
- chrome.exe (PID: 6156)
- msedge.exe (PID: 7968)
- msedge.exe (PID: 5308)
- chrome.exe (PID: 3896)
NirSoft software is detected
- JSEVGJV.exe (PID: 4200)
- DNS.exe (PID: 8896)
Manual execution by a user
- svchost.exe (PID: 7740)
- svchost.exe (PID: 4976)
Changes the registry key values via Powershell
- filelistcreatorassist15.exe (PID: 7752)
Creates a new folder
- cmd.exe (PID: 8744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(6540) saved.exe
C2185.39.17.163
URLhttp://185.39.17.163/Su8kud7i/index.php
Version5.34
Options
Drop directoryc13dbdc4fa
Drop namesaved.exe
Strings (125)S-%lu-
og:
clip.dll
ProgramData\
shell32.dll
<c>
vs:
Programs
&&
VideoID
ESET
av:
\App
0000043f
Doctor Web
:::
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
------
rundll32.exe
00000422
185.39.17.163
0123456789
st=s
00000419
Content-Type: application/x-www-form-urlencoded
/Plugins/
msi
ar:
GetNativeSystemInfo
Norton
-%lu
Sophos
zip
SOFTWARE\Microsoft\Windows NT\CurrentVersion
"
Content-Type: application/octet-stream
|
+++
" && ren
pc:
#
d1
cmd /C RMDIR /s/q
Bitdefender
Comodo
<d>
Kaspersky Lab
DefaultSettings.YResolution
Main
c13dbdc4fa
-executionpolicy remotesigned -File "
&& Exit"
ProductName
&unit=
2022
Panda Security
=
Rem
cmd
\0000
id:
sd:
--
/quiet
rundll32
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
%-lu
random
GET
"taskkill /f /im "
Content-Disposition: form-data; name="data"; filename="
00000423
5.34
2016
?scr=1
ComputerName
Keyboard Layout\Preload
Powershell.exe
POST
http://
AVAST Software
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
ps1
DefaultSettings.XResolution
Startup
CurrentBuild
e3
cred.dll|clip.dll|
------
WinDefender
wb
https://
Avira
2025
" && timeout 1 && del
cred.dll
un:
SYSTEM\ControlSet001\Services\BasicDisplay\Video
rb
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
360TotalSecurity
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
saved.exe
e1
lv:
/Su8kud7i/index.php
shutdown -s -t 0
/k
e2
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
exe
%USERPROFILE%
-unicode-
r=
.jpg
dll
Content-Type: multipart/form-data; boundary=----
2019
bi:
\
"
kernel32.dll
os:
abcdefghijklmnopqrstuvwxyz0123456789-_
dm:
AVG
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:04:26 14:47:23+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 312320 |
| InitializedDataSize: | 38400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4a2000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
276
Monitored processes
140
Malicious processes
30
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x228,0x22c,0x230,0x204,0x234,0x7ffc8960dc40,0x7ffc8960dc4c,0x7ffc8960dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1844 --field-trial-handle=1816,i,13266419637360734000,8698770532702398608,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1096 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | 47Q6wZM.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2788 --field-trial-handle=2404,i,15980210354012936429,4129124100603291721,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | "C:\ProgramData\4w479zuk6p.exe" | C:\ProgramData\4w479zuk6p.exe | MSBuild.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 3 Version: 1.4.1 Modules
| |||||||||||||||
| 1196 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3356 --field-trial-handle=2120,i,5870624230619006231,17292608596242312329,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1276 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2548 --field-trial-handle=2404,i,15980210354012936429,4129124100603291721,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1532 | "C:\Users\admin\AppData\Roaming\MyApp\core.exe" | C:\Users\admin\AppData\Roaming\MyApp\core.exe | dfe10e0ea7.tmp | ||||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Stremio Server JavaScript Runtime Version: 14.15.0 Modules
| |||||||||||||||
| 2040 | "C:\Users\admin\AppData\Local\Temp\10053530101\zb7jDew.exe" | C:\Users\admin\AppData\Local\Temp\10053530101\zb7jDew.exe | saved.exe | ||||||||||||
User: admin Company: Code Sector Integrity Level: MEDIUM Description: TeraCopy Installer Exit code: 0 Version: 3.17 Modules
| |||||||||||||||
Total events
40 256
Read events
40 077
Write events
149
Delete events
30
Modification events
| (PID) Process: | (6540) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6540) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6540) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6112) dfe10e0ea7.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.4.0 | |||
| (PID) Process: | (6112) dfe10e0ea7.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Users\admin\AppData\Roaming\MyApp | |||
| (PID) Process: | (6112) dfe10e0ea7.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Roaming\MyApp\ | |||
| (PID) Process: | (6112) dfe10e0ea7.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: MyApp | |||
| (PID) Process: | (6112) dfe10e0ea7.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (6112) dfe10e0ea7.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: default | |||
| (PID) Process: | (6112) dfe10e0ea7.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyApp_is1 |
| Operation: | write | Name: | DisplayName |
Value: MyApp version 1.0 | |||
Executable files
130
Suspicious files
451
Text files
180
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6112 | dfe10e0ea7.tmp | C:\Users\admin\AppData\Roaming\MyApp\is-2FT50.tmp | — | |
MD5:— | SHA256:— | |||
| 6112 | dfe10e0ea7.tmp | C:\Users\admin\AppData\Roaming\MyApp\core.exe | — | |
MD5:— | SHA256:— | |||
| 6540 | saved.exe | C:\Users\admin\AppData\Local\Temp\10053500101\dfe10e0ea7.exe | executable | |
MD5:FAF551A93829A709A7174F6AE283CBDE | SHA256:35D825988B4411C29DBF9360578872C722C58D63C8AE1967153C9A28DFE45375 | |||
| 6112 | dfe10e0ea7.tmp | C:\Users\admin\AppData\Roaming\MyApp\info.exe | executable | |
MD5:EE0334F3083FED56762CE148E23EFAAA | SHA256:5E57CD5C98F41A350D15D833494DDCF6E58D0616753D8F80E5949BB6B53E2D45 | |||
| 6112 | dfe10e0ea7.tmp | C:\Users\admin\AppData\Roaming\MyApp\is-DFI0L.tmp | executable | |
MD5:4134EC81A9D645602B1FA265F98FBF35 | SHA256:69966257CE41717F2121EA1F03F8BFA1486423ACECFCC977DD9F1E157C911AD4 | |||
| 6540 | saved.exe | C:\Users\admin\AppData\Local\Temp\10053510101\d6c4cc96ee.exe | executable | |
MD5:91F629D1329C528BB987FB52A1C0195A | SHA256:2F871AE3AAB7B37F933F48059A975C34FC629AC2946AC39247E54D6D3BE5B6D6 | |||
| 6132 | 2OD7IBXQP627GMB3XPD7SSVSO.exe | C:\Windows\Tasks\saved.job | binary | |
MD5:6C020BE21B75D469906F57DE68C6F5C7 | SHA256:F9D52F69CB443EAE8203CEBC74A79B4834FB1ACBA50E9B10A7EC30F061BA7501 | |||
| 6540 | saved.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\random[1].exe | executable | |
MD5:FAF551A93829A709A7174F6AE283CBDE | SHA256:35D825988B4411C29DBF9360578872C722C58D63C8AE1967153C9A28DFE45375 | |||
| 6112 | dfe10e0ea7.tmp | C:\Users\admin\AppData\Roaming\MyApp\data\putty.exe | executable | |
MD5:36E31F610EEF3223154E6E8FD074190F | SHA256:16CBE40FB24CE2D422AFDDB5A90A5801CED32EF52C22C2FC77B25A90837F28AD | |||
| 2316 | dfe10e0ea7.exe | C:\Users\admin\AppData\Local\Temp\is-L0Q2V.tmp\dfe10e0ea7.tmp | executable | |
MD5:E4C43138CCB8240276872FD1AEC369BE | SHA256:46BE5E3F28A5E4ED63D66B901D927C25944B4DA36EFFEA9C97FB05994360EDF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
204
DNS requests
116
Threats
105
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5608 | 7a0eeda7628f3afea678a177e32ac46b.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/mine/random.exe | unknown | — | — | malicious |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6540 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
6540 | saved.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/files/unique1/random.exe | unknown | — | — | malicious |
6540 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
6540 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
6540 | saved.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/files/unique2/random.exe | unknown | — | — | malicious |
5512 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5176 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5608 | 7a0eeda7628f3afea678a177e32ac46b.exe | 172.67.190.162:443 | zenithcorde.top | CLOUDFLARENET | US | unknown |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
clarmodq.top |
| malicious |
zenithcorde.top |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (clarmodq .top) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (clarmodq .top) |
5608 | 7a0eeda7628f3afea678a177e32ac46b.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
5608 | 7a0eeda7628f3afea678a177e32ac46b.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
5608 | 7a0eeda7628f3afea678a177e32ac46b.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
5608 | 7a0eeda7628f3afea678a177e32ac46b.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
5608 | 7a0eeda7628f3afea678a177e32ac46b.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 31 |
5608 | 7a0eeda7628f3afea678a177e32ac46b.exe | Misc activity | ET INFO Packed Executable Download |
6540 | saved.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 31 |