| File name: | file |
| Full analysis: | https://app.any.run/tasks/6cd8a9b4-06f0-4a21-a052-484e11a6c411 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | August 10, 2024, 20:58:10 |
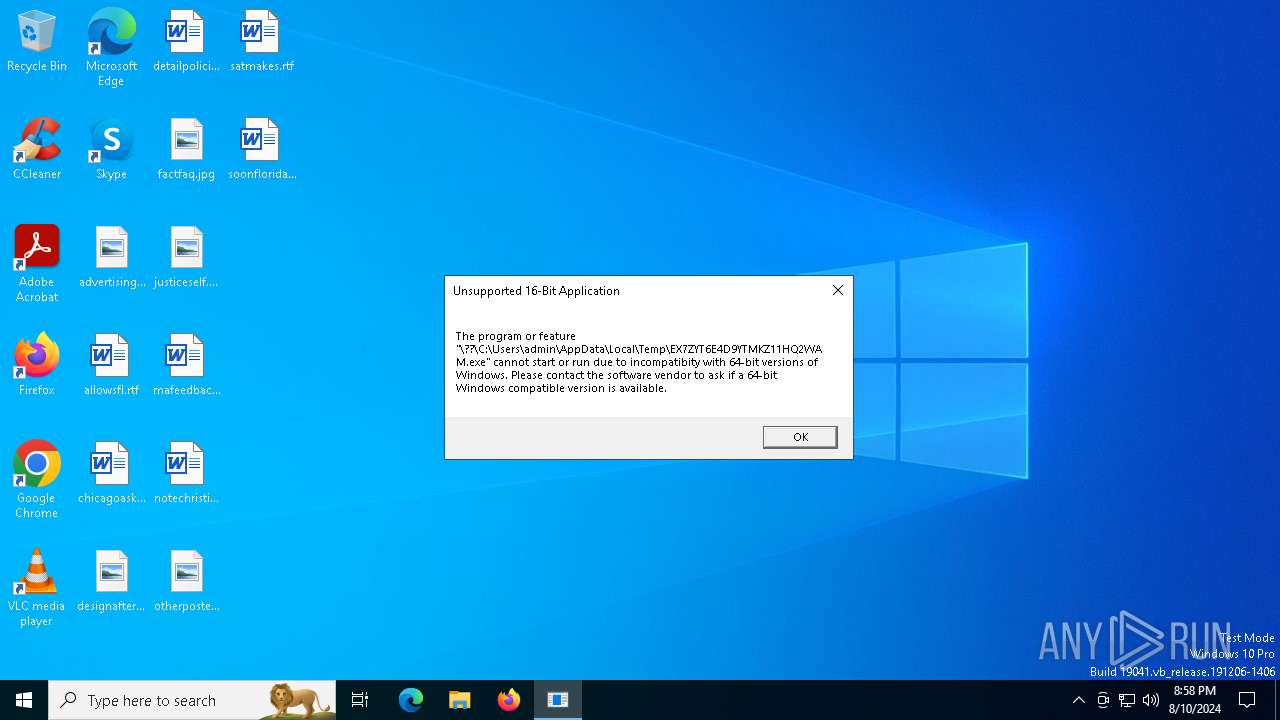
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 4F1B08B2DE97134EA899BEDE6F28098E |
| SHA1: | 7707C795230A38E58BFA0073A12336A1A235F954 |
| SHA256: | BCC2BF333F69425C0B61F8D48A3CD7C931DEFF82AA796229CF47764878DC4E3B |
| SSDEEP: | 3072:V8lWAowkQrYVthKSS64kOro12Gzex33jPWX49VuPZW:SWHwkQwAWOxlzWXxPZ |
MALICIOUS
REDLINE has been detected (YARA)
- RegAsm.exe (PID: 6356)
Steals credentials from Web Browsers
- RegAsm.exe (PID: 6356)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 6356)
- RegAsm.exe (PID: 6172)
- RegAsm.exe (PID: 6168)
REDLINE has been detected (SURICATA)
- RegAsm.exe (PID: 6356)
Stealers network behavior
- RegAsm.exe (PID: 6356)
METASTEALER has been detected (SURICATA)
- RegAsm.exe (PID: 6356)
LEFTHOOK has been detected (SURICATA)
- RegAsm.exe (PID: 6356)
LUMMA has been detected (SURICATA)
- RegAsm.exe (PID: 6172)
- svchost.exe (PID: 2256)
Connects to the CnC server
- svchost.exe (PID: 2256)
ASYNCRAT has been detected (SURICATA)
- RegAsm.exe (PID: 6168)
PUREHVNC has been detected (YARA)
- RegAsm.exe (PID: 6168)
LUMMA has been detected (YARA)
- RegAsm.exe (PID: 6172)
SUSPICIOUS
Drops the executable file immediately after the start
- file.exe (PID: 6324)
- RegAsm.exe (PID: 6356)
- RegAsm.exe (PID: 5092)
Contacting a server suspected of hosting an CnC
- RegAsm.exe (PID: 6356)
- svchost.exe (PID: 2256)
- RegAsm.exe (PID: 6168)
- RegAsm.exe (PID: 6172)
Connects to unusual port
- RegAsm.exe (PID: 6356)
- RegAsm.exe (PID: 6168)
Checks for external IP
- RegAsm.exe (PID: 6356)
- svchost.exe (PID: 2256)
Potential Corporate Privacy Violation
- RegAsm.exe (PID: 6356)
Searches for installed software
- RegAsm.exe (PID: 6356)
- RegAsm.exe (PID: 6172)
Reads the date of Windows installation
- RegAsm.exe (PID: 6356)
- RegAsm.exe (PID: 5092)
Executable content was dropped or overwritten
- RegAsm.exe (PID: 6356)
- RegAsm.exe (PID: 5092)
Reads security settings of Internet Explorer
- RegAsm.exe (PID: 6356)
- RegAsm.exe (PID: 5092)
Application launched itself
- RegAsm.exe (PID: 6828)
INFO
Checks supported languages
- RegAsm.exe (PID: 6356)
- file.exe (PID: 6324)
- elton.exe (PID: 5044)
- RegAsm.exe (PID: 5092)
- RegAsm.exe (PID: 6828)
- S7ZHjmfE7I.exe (PID: 300)
- PtMAYGd0GR.exe (PID: 4016)
- RegAsm.exe (PID: 6172)
- RegAsm.exe (PID: 6168)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 6356)
- RegAsm.exe (PID: 6168)
Reads the computer name
- file.exe (PID: 6324)
- RegAsm.exe (PID: 6356)
- RegAsm.exe (PID: 6828)
- elton.exe (PID: 5044)
- RegAsm.exe (PID: 5092)
- PtMAYGd0GR.exe (PID: 4016)
- S7ZHjmfE7I.exe (PID: 300)
- RegAsm.exe (PID: 6168)
- RegAsm.exe (PID: 6172)
Disables trace logs
- RegAsm.exe (PID: 6356)
Reads Environment values
- RegAsm.exe (PID: 6356)
- RegAsm.exe (PID: 6168)
Checks proxy server information
- RegAsm.exe (PID: 6356)
Reads the software policy settings
- RegAsm.exe (PID: 6356)
- RegAsm.exe (PID: 6172)
- RegAsm.exe (PID: 6168)
Create files in a temporary directory
- RegAsm.exe (PID: 6356)
- RegAsm.exe (PID: 6172)
Process checks computer location settings
- RegAsm.exe (PID: 6356)
- RegAsm.exe (PID: 5092)
Creates files or folders in the user directory
- RegAsm.exe (PID: 5092)
.NET Reactor protector has been detected
- RegAsm.exe (PID: 6168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(6356) RegAsm.exe
C2 (1)45.66.231.184:1334
BotnetExodusmarket
Keys
Xor
Options
ErrorMessage
Lumma
(PID) Process(6172) RegAsm.exe
C2 (9)bassizcellskz.shop
deallerospfosu.shop
complaintsipzzx.shop
hookybeamngwskow.xyz
languagedscie.shop
writerospzm.shop
mennyudosirso.shop
celebratioopz.shop
quialitsuzoxm.shop
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:08:10 20:27:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 103936 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1b5ee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Photoreceptor |
| CompanyName: | Volatilization Swellings |
| FileDescription: | Interruptible marbleised |
| FileVersion: | 1.0.0.0 |
| InternalName: | MSG.exe |
| LegalCopyright: | Copyright © 2024 |
| OriginalFileName: | MSG.exe |
| ProductName: | Good resorters |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
145
Monitored processes
13
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Users\admin\AppData\Roaming\S7ZHjmfE7I.exe" | C:\Users\admin\AppData\Roaming\S7ZHjmfE7I.exe | — | RegAsm.exe | |||||||||||
User: admin Company: Lacerate Integrity Level: MEDIUM Description: Environing Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4016 | "C:\Users\admin\AppData\Roaming\PtMAYGd0GR.exe" | C:\Users\admin\AppData\Roaming\PtMAYGd0GR.exe | — | RegAsm.exe | |||||||||||
User: admin Company: Lacerate Integrity Level: MEDIUM Description: Environing Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5044 | "C:\Users\admin\AppData\Local\Temp\elton.exe" | C:\Users\admin\AppData\Local\Temp\elton.exe | — | RegAsm.exe | |||||||||||
User: admin Company: Lacerate Integrity Level: MEDIUM Description: Environing Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5092 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 6168 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | PtMAYGd0GR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 6172 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | S7ZHjmfE7I.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
Lumma(PID) Process(6172) RegAsm.exe C2 (9)bassizcellskz.shop deallerospfosu.shop complaintsipzzx.shop hookybeamngwskow.xyz languagedscie.shop writerospzm.shop mennyudosirso.shop celebratioopz.shop quialitsuzoxm.shop | |||||||||||||||
| 6324 | "C:\Users\admin\AppData\Local\Temp\file.exe" | C:\Users\admin\AppData\Local\Temp\file.exe | — | explorer.exe | |||||||||||
User: admin Company: Volatilization Swellings Integrity Level: MEDIUM Description: Interruptible marbleised Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6356 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
RedLine(PID) Process(6356) RegAsm.exe C2 (1)45.66.231.184:1334 BotnetExodusmarket Keys Xor Options ErrorMessage | |||||||||||||||
| 6368 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | RegAsm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 145
Read events
14 114
Write events
31
Delete events
0
Modification events
| (PID) Process: | (6356) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6356) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6356) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6356) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6356) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6356) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6356) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6356) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6356) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6356) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegAsm_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
3
Suspicious files
19
Text files
1
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6356 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\tmp7493.tmp | sqlite | |
MD5:A45465CDCDC6CB30C8906F3DA4EC114C | SHA256:4412319EF944EBCCA9581CBACB1D4E1DC614C348D1DFC5D2FAAAAD863D300209 | |||
| 6356 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\tmp7491.tmp | binary | |
MD5:A45465CDCDC6CB30C8906F3DA4EC114C | SHA256:4412319EF944EBCCA9581CBACB1D4E1DC614C348D1DFC5D2FAAAAD863D300209 | |||
| 6356 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\tmp74A5.tmp | binary | |
MD5:F6C33AC5E1032A0873BE7BFC65169287 | SHA256:D97895CEDED32E33D57BDCACCDBE144E58AA87AF4D2F8855D630286CE30A8D83 | |||
| 6356 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\tmp74C7.tmp | sqlite | |
MD5:F6C33AC5E1032A0873BE7BFC65169287 | SHA256:D97895CEDED32E33D57BDCACCDBE144E58AA87AF4D2F8855D630286CE30A8D83 | |||
| 6356 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\tmp74C8.tmp | sqlite | |
MD5:F6C33AC5E1032A0873BE7BFC65169287 | SHA256:D97895CEDED32E33D57BDCACCDBE144E58AA87AF4D2F8855D630286CE30A8D83 | |||
| 6356 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\tmp74FB.tmp | sqlite | |
MD5:F6C33AC5E1032A0873BE7BFC65169287 | SHA256:D97895CEDED32E33D57BDCACCDBE144E58AA87AF4D2F8855D630286CE30A8D83 | |||
| 6356 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\tmp74B6.tmp | sqlite | |
MD5:F6C33AC5E1032A0873BE7BFC65169287 | SHA256:D97895CEDED32E33D57BDCACCDBE144E58AA87AF4D2F8855D630286CE30A8D83 | |||
| 6356 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\tmp74D9.tmp | sqlite | |
MD5:F6C33AC5E1032A0873BE7BFC65169287 | SHA256:D97895CEDED32E33D57BDCACCDBE144E58AA87AF4D2F8855D630286CE30A8D83 | |||
| 6356 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\tmp74E9.tmp | sqlite | |
MD5:F6C33AC5E1032A0873BE7BFC65169287 | SHA256:D97895CEDED32E33D57BDCACCDBE144E58AA87AF4D2F8855D630286CE30A8D83 | |||
| 6356 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\tmp74FA.tmp | sqlite | |
MD5:F6C33AC5E1032A0873BE7BFC65169287 | SHA256:D97895CEDED32E33D57BDCACCDBE144E58AA87AF4D2F8855D630286CE30A8D83 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
53
DNS requests
21
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6356 | RegAsm.exe | POST | 200 | 45.66.231.184:1334 | http://45.66.231.184:1334/ | unknown | — | — | unknown |
6356 | RegAsm.exe | POST | 200 | 45.66.231.184:1334 | http://45.66.231.184:1334/ | unknown | — | — | unknown |
6356 | RegAsm.exe | POST | 200 | 45.66.231.184:1334 | http://45.66.231.184:1334/ | unknown | — | — | unknown |
3276 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6968 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3276 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7036 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6356 | RegAsm.exe | POST | 200 | 45.66.231.184:1334 | http://45.66.231.184:1334/ | unknown | — | — | unknown |
6356 | RegAsm.exe | GET | 200 | 45.66.231.184:80 | http://45.66.231.184/elton.exe | unknown | — | — | malicious |
6356 | RegAsm.exe | POST | 200 | 45.66.231.184:1334 | http://45.66.231.184:1334/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1292 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3068 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6356 | RegAsm.exe | 45.66.231.184:1334 | — | Enes Koken | BG | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1292 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6356 | RegAsm.exe | 172.67.75.172:443 | api.ip.sb | CLOUDFLARENET | US | unknown |
5336 | SearchApp.exe | 184.86.251.22:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
api.ip.sb |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
hookybeamngwskow.xyz |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6356 | RegAsm.exe | Malware Command and Control Activity Detected | ET MALWARE RedLine Stealer - CheckConnect Response |
6356 | RegAsm.exe | Malware Command and Control Activity Detected | ET MALWARE Win32/LeftHook Stealer Browser Extension Config Inbound |
6356 | RegAsm.exe | A Network Trojan was detected | AV TROJAN RedLine Stealer Config Download |
6356 | RegAsm.exe | A Network Trojan was detected | ET MALWARE Redline Stealer/MetaStealer Family Activity (Response) |
6356 | RegAsm.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6356 | RegAsm.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6356 | RegAsm.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6356 | RegAsm.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Lumma Stealer Related CnC Domain in DNS Lookup (hookybeamngwskow .xyz) |
6172 | RegAsm.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Lumma Stealer Related Domain (hookybeamngwskow .xyz in TLS SNI) |
6 ETPRO signatures available at the full report