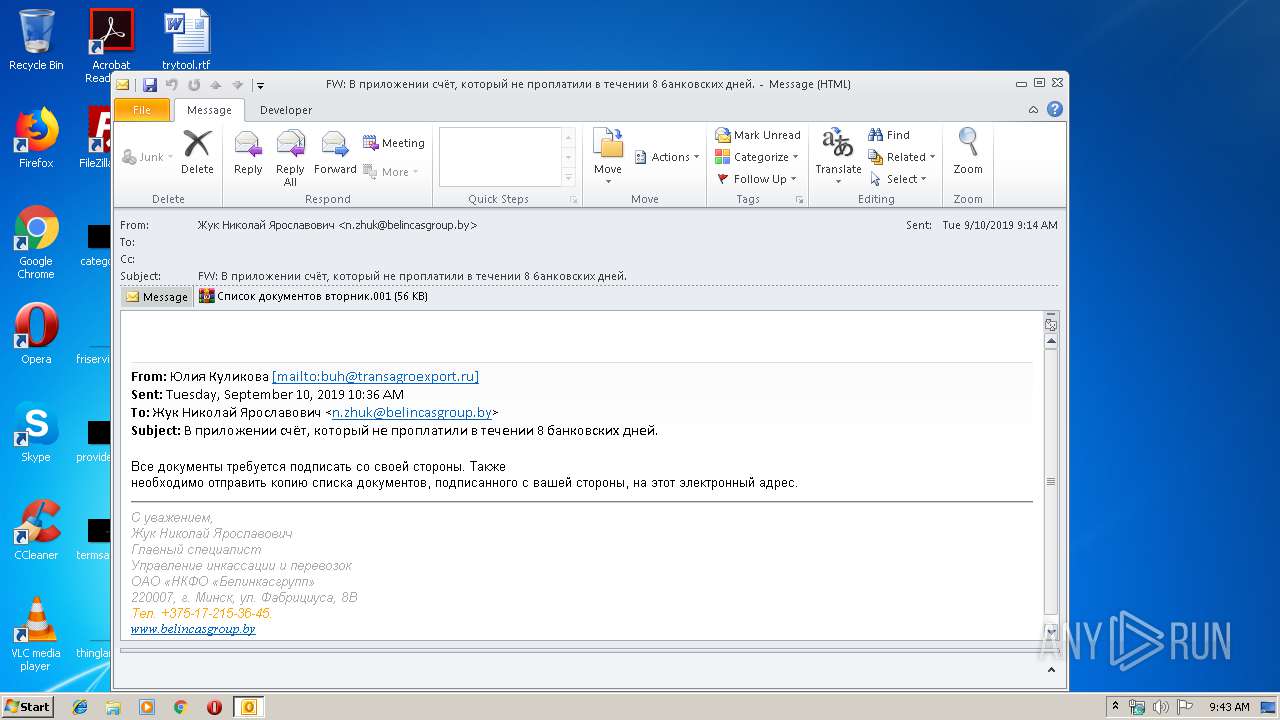
| File name: | 4.eml |
| Full analysis: | https://app.any.run/tasks/750bf52b-f004-447d-badc-bfc985b9ef6a |
| Verdict: | Malicious activity |
| Threats: | Pony is a malware with two main functions — stealing information and dropping other viruses with different tasks on infected machines. It has been around since 2011, and it still actively attacks users in Europe and America. |
| Analysis date: | September 11, 2019, 08:43:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | MIME entity, ASCII text, with CRLF line terminators |
| MD5: | B0DB89787917BAA067A46748D60D7FC8 |
| SHA1: | 3DED4B9A0C4D66CA118077A19445159D3675F295 |
| SHA256: | BC33CA5DB26345BDBBFC36B1800EA578EF46E2447359FAFBD6F79D6621A6E514 |
| SSDEEP: | 1536:W77AWaNAw/FcVrONMto9h5cpwVFWGgV91v7Uyu7Ay0jjvfFGt:U7AWbwtcVCNMtobCwVNgV91v7Ub90vS |
MALICIOUS
Application was dropped or rewritten from another process
- Список документов вторник.exe (PID: 2504)
- Список документов вторник.exe (PID: 3144)
Detected Pony/Fareit Trojan
- Список документов вторник.exe (PID: 3144)
PONY was detected
- Список документов вторник.exe (PID: 3144)
Downloads executable files from the Internet
- Список документов вторник.exe (PID: 3144)
Downloads executable files from IP
- Список документов вторник.exe (PID: 3144)
Connects to CnC server
- Список документов вторник.exe (PID: 3144)
Actions looks like stealing of personal data
- Список документов вторник.exe (PID: 3144)
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3284)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3284)
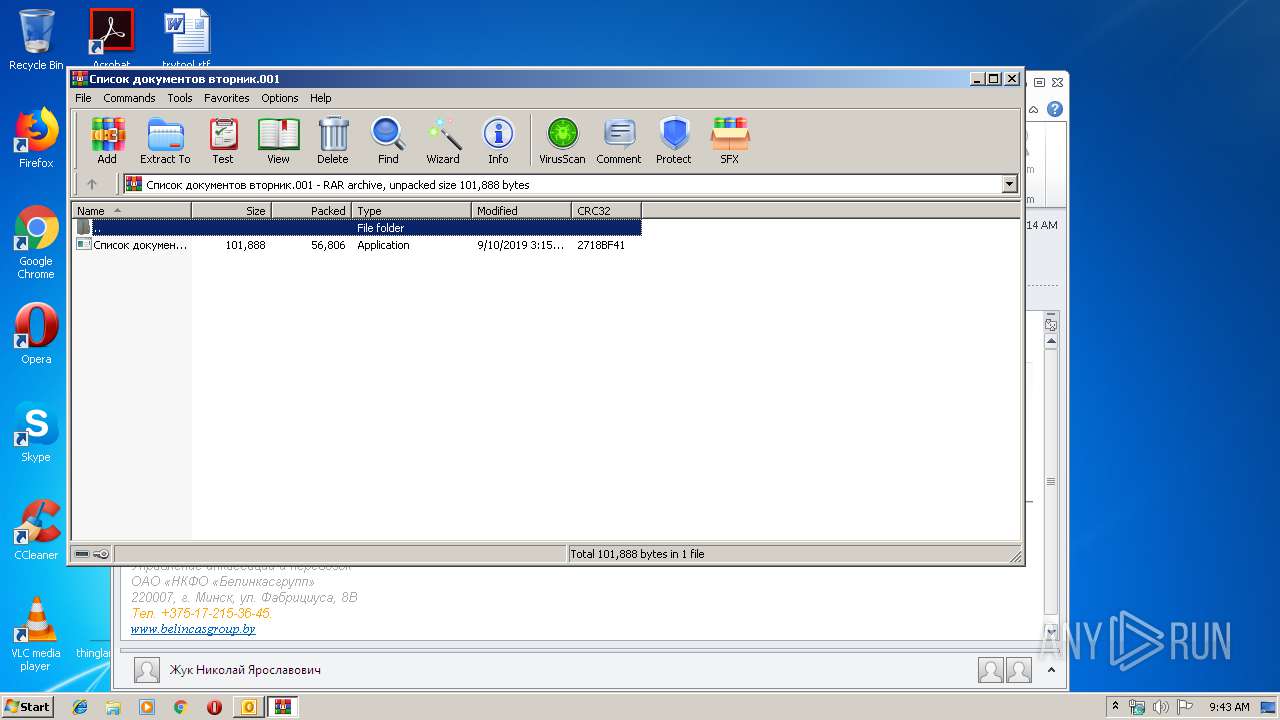
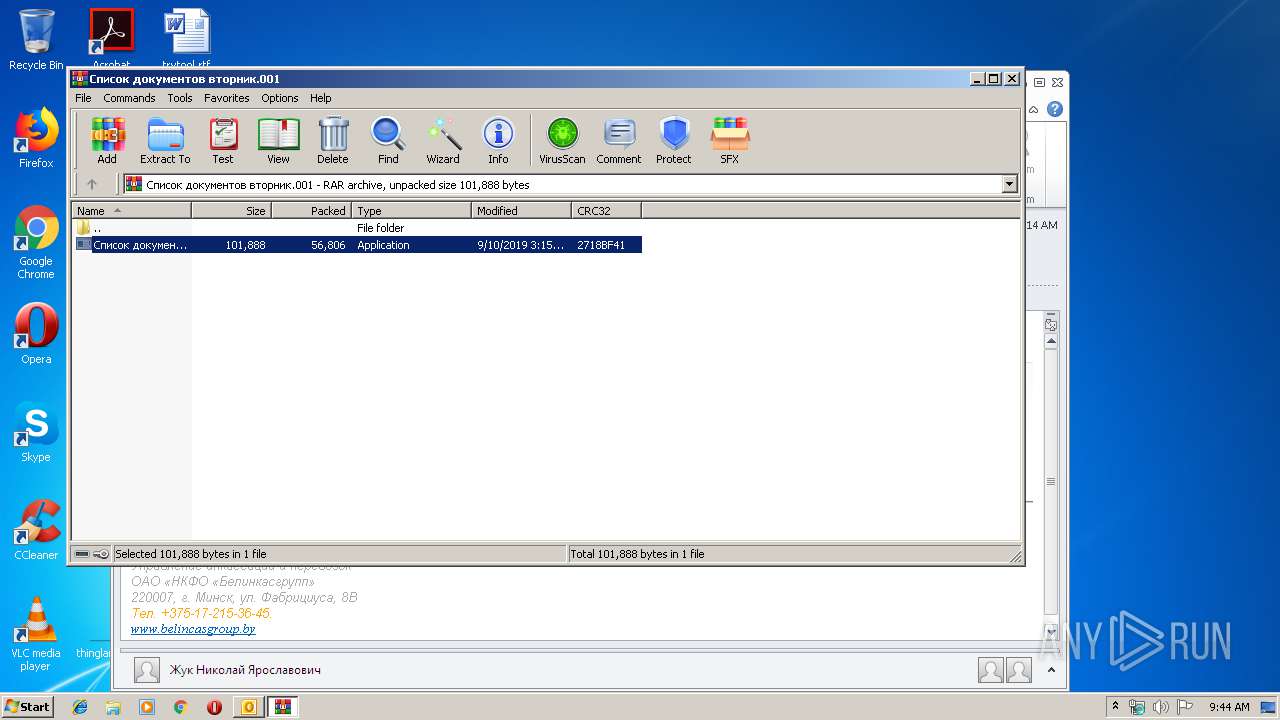
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3792)
Searches for installed software
- Список документов вторник.exe (PID: 3144)
Connects to server without host name
- Список документов вторник.exe (PID: 3144)
INFO
Application was crashed
- Список документов вторник.exe (PID: 2504)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2504 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3792.44208\Список документов вторник.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3792.44208\Список документов вторник.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 3144 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3792.44208\Список документов вторник.exe" dfsr | C:\Users\admin\AppData\Local\Temp\Rar$EXa3792.44208\Список документов вторник.exe | Список документов вторник.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3284 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\4.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3792 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\ZZN0RTN8\Список документов вторник.001" | C:\Program Files\WinRAR\WinRAR.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
2 055
Read events
1 601
Write events
435
Delete events
19
Modification events
| (PID) Process: | (3284) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3284) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3284) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | +p# |
Value: 2B702300D40C0000010000000000000000000000 | |||
| (PID) Process: | (3284) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: D40C000036A1F3047D68D50100000000 | |||
| (PID) Process: | (3284) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3284) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220210560 | |||
| (PID) Process: | (3284) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3284) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3284) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3284) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1328218133 | |||
Executable files
1
Suspicious files
2
Text files
24
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3284 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR987C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3284 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\ZZN0RTN8\Список документов вторник (2).001\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3284 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3284 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\ZZN0RTN8\Список документов вторник.001 | compressed | |
MD5:— | SHA256:— | |||
| 3284 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\ZZN0RTN8\Список документов вторник (2).001 | compressed | |
MD5:— | SHA256:— | |||
| 3792 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3792.44208\Список документов вторник.exe | executable | |
MD5:— | SHA256:— | |||
| 3284 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_7633CBDAA7580D4B95947978F3541FAD.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
| 3284 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ContactPrefs_2_2B91ED779D84BD47AD92F0B003646151.dat | xml | |
MD5:BBCF400BD7AE536EB03054021D6A6398 | SHA256:383020065C1F31F4FB09F448599A6D5E532C390AF4E5B8AF0771FE17A23222AD | |||
| 3284 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_C2E1CE8B78547648B8F5C16C28B03147.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 3284 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_8906F323CE71674DA070AAA58F54D943.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
11
DNS requests
3
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3284 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3144 | Список документов вторник.exe | GET | 200 | 91.200.100.136:80 | http://91.200.100.136/index.php?id=0&un=61646d696e&cn=555345522d5043 | unknown | executable | 97.0 Kb | malicious |
3144 | Список документов вторник.exe | POST | — | 195.123.227.99:80 | http://195.123.227.99/g_38472341.php | BG | — | — | malicious |
3144 | Список документов вторник.exe | POST | — | 195.123.227.99:80 | http://195.123.227.99/g_38472341.php | BG | — | — | malicious |
3144 | Список документов вторник.exe | POST | — | 195.123.227.99:80 | http://195.123.227.99/g_38472341.php | BG | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3144 | Список документов вторник.exe | 104.16.54.3:443 | blockchain.info | Cloudflare Inc | US | shared |
3284 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3144 | Список документов вторник.exe | 104.16.55.3:443 | blockchain.info | Cloudflare Inc | US | shared |
3144 | Список документов вторник.exe | 52.86.198.63:443 | api.blockcypher.com | Amazon.com, Inc. | US | malicious |
3144 | Список документов вторник.exe | 91.200.100.136:80 | — | — | — | malicious |
3144 | Список документов вторник.exe | 195.123.227.99:80 | — | ITL Company | BG | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
blockchain.info |
| shared |
api.blockcypher.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3144 | Список документов вторник.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3144 | Список документов вторник.exe | A Network Trojan was detected | ET CURRENT_EVENTS WinHttpRequest Downloading EXE |
3144 | Список документов вторник.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
3144 | Список документов вторник.exe | A Network Trojan was detected | ET TROJAN Pony DLL Download M2 |
3144 | Список документов вторник.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
3144 | Список документов вторник.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
3144 | Список документов вторник.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |