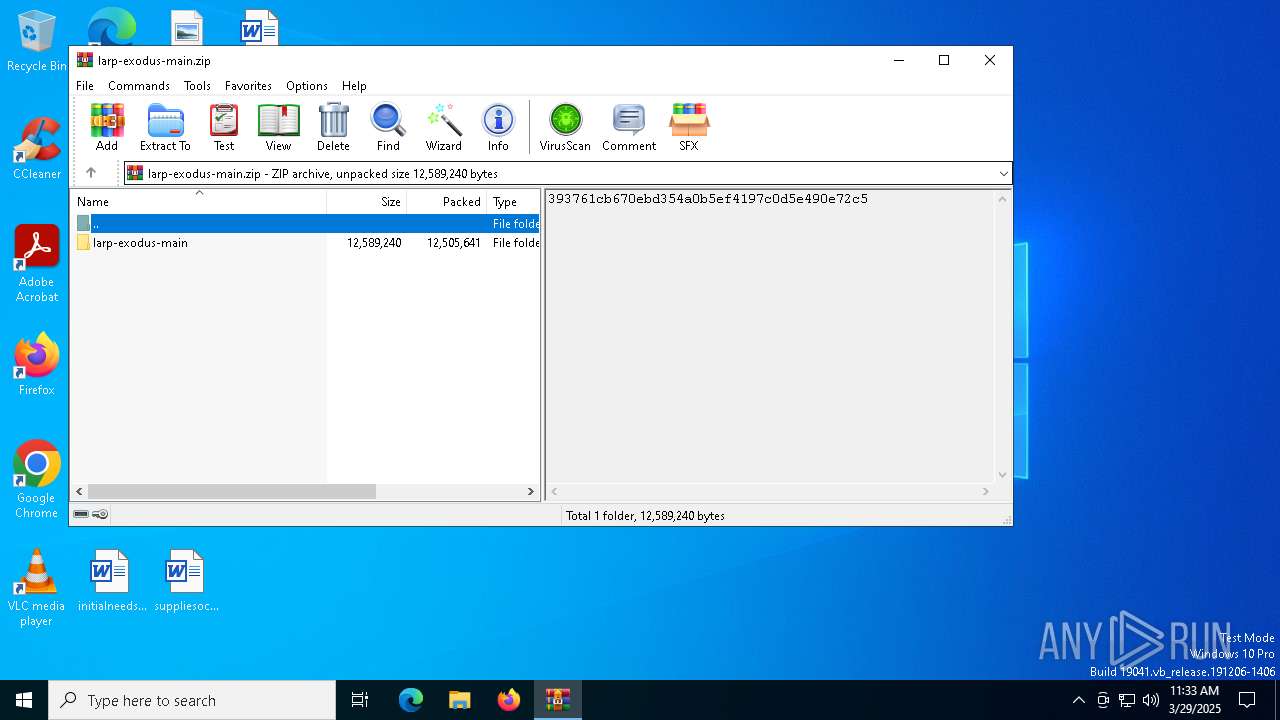
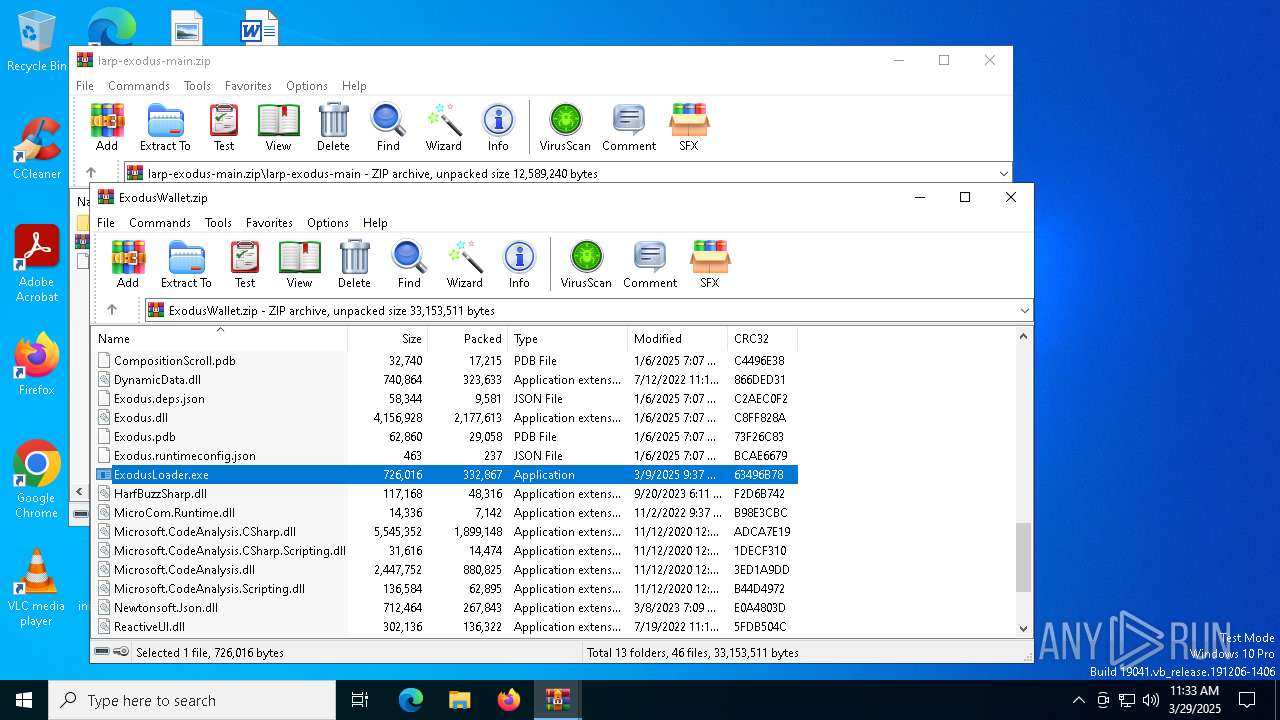
| File name: | larp-exodus-main.zip |
| Full analysis: | https://app.any.run/tasks/7cd88839-e6b3-4cb4-82b9-414243be5ba1 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | March 29, 2025, 11:33:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 8570C81C807180EC423404FB7908AE99 |
| SHA1: | 34287E0115DDE607C4A25AAEF771C762A591A6BD |
| SHA256: | BBA5F53C405C572979A2A250CE8883BA44C80ED31366D8E8A5447CC822A00C3B |
| SSDEEP: | 98304:S2HlCAskP4fWOW3xXpS7CrW2uM/Cfru+UYBByuX2teJoHHrlvl/bjTCjcFuXsd6F:3ehgI2kLZXKtK8AVZjOC6q |
MALICIOUS
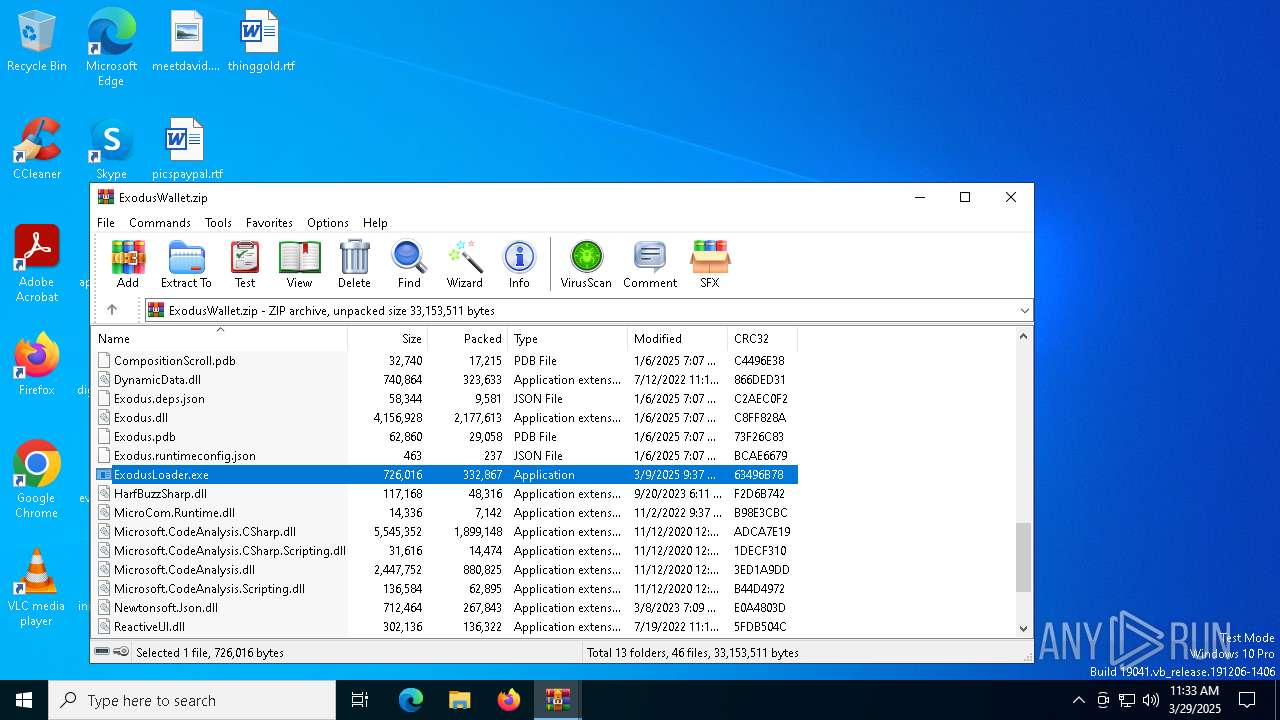
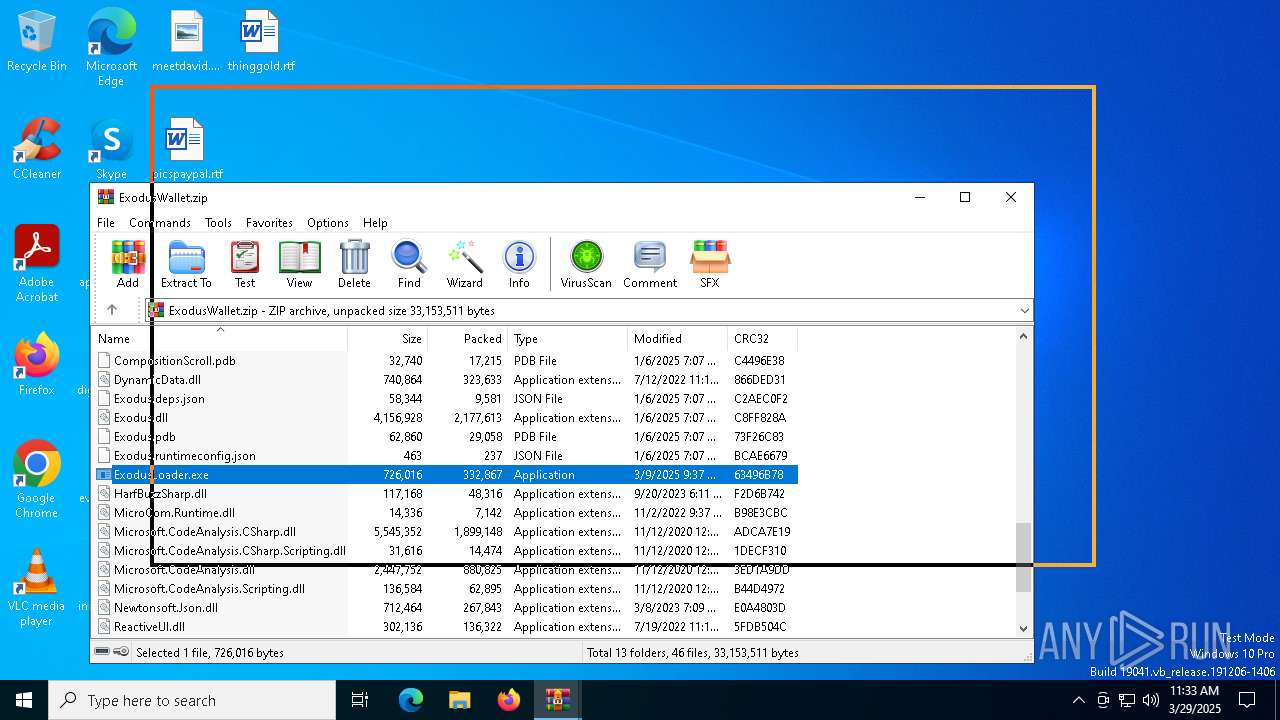
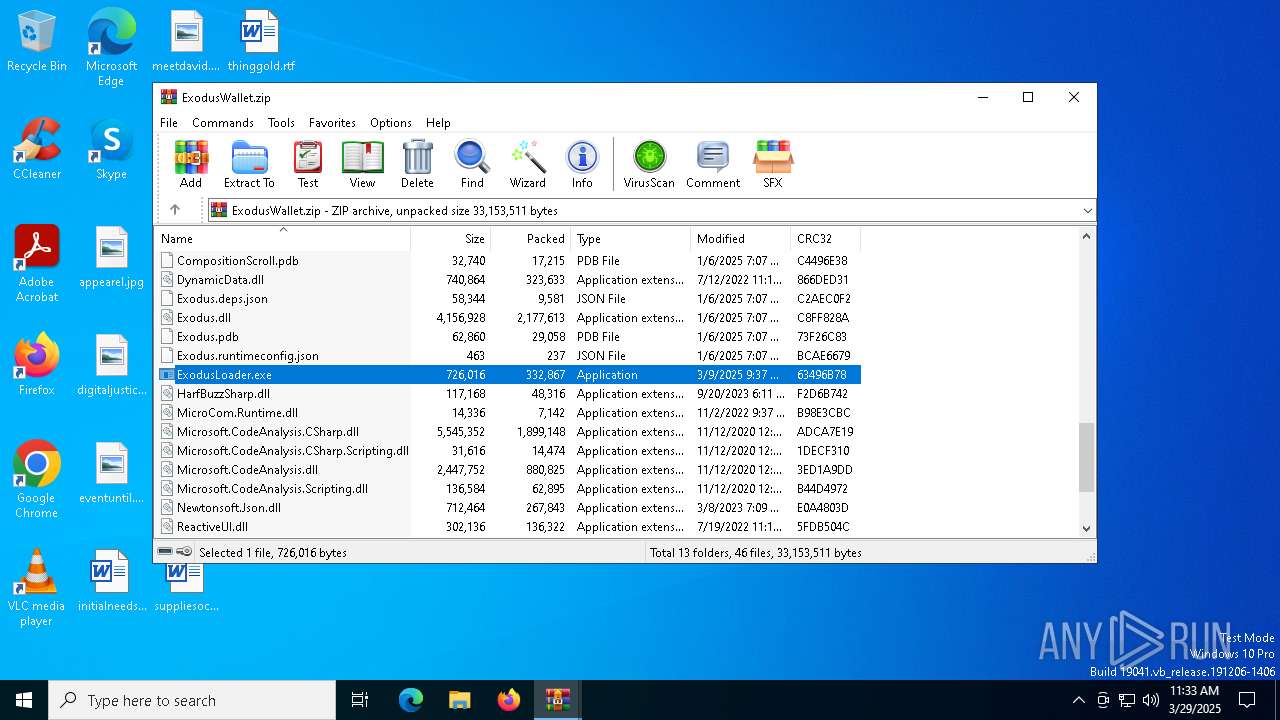
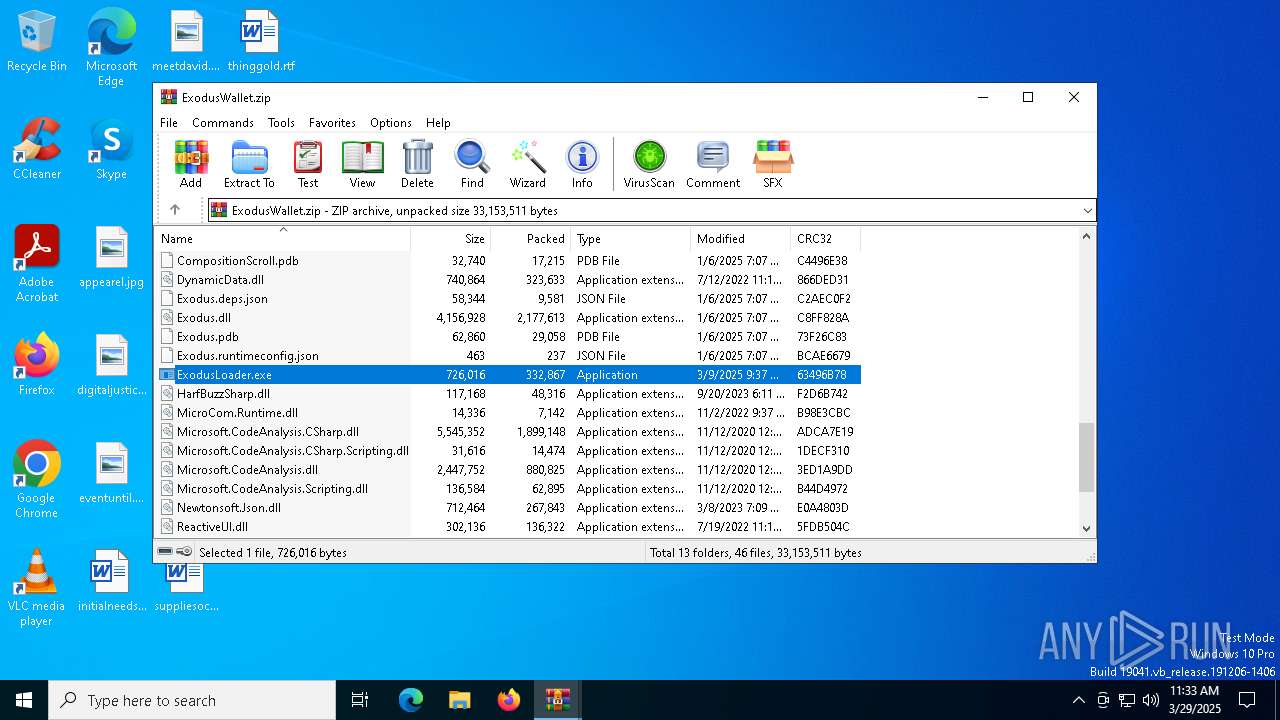
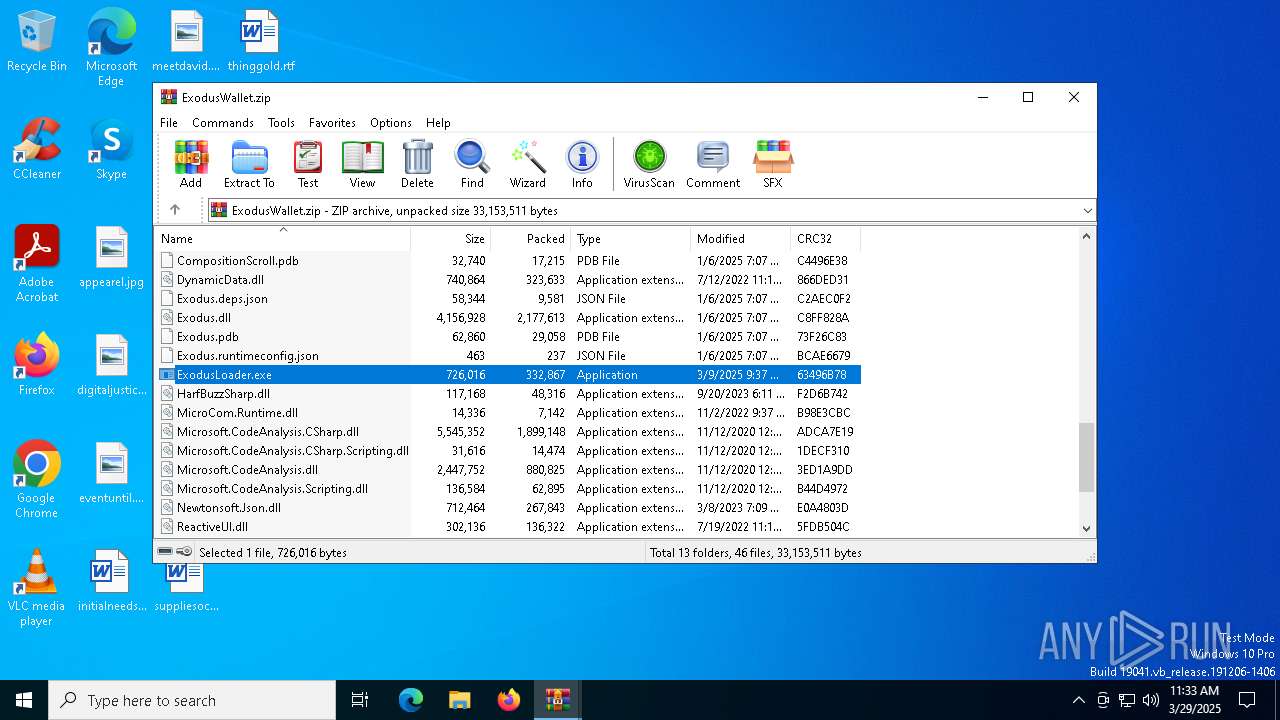
QUASAR has been detected (YARA)
- ExodusLoader.exe (PID: 4112)
SUSPICIOUS
Application launched itself
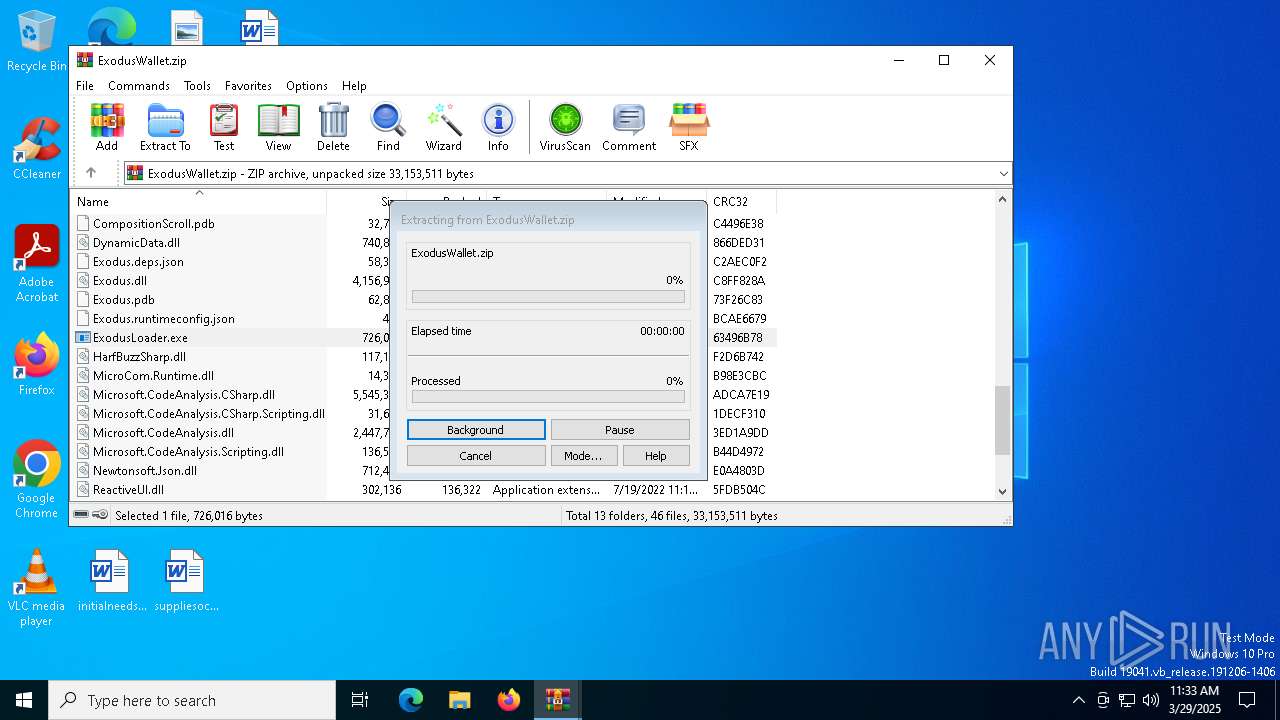
- WinRAR.exe (PID: 1180)
Process drops legitimate windows executable
- WinRAR.exe (PID: 3020)
- WinRAR.exe (PID: 1180)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1180)
- WinRAR.exe (PID: 3020)
There is functionality for taking screenshot (YARA)
- ExodusLoader.exe (PID: 4112)
Connects to unusual port
- ExodusLoader.exe (PID: 4112)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3020)
Checks supported languages
- ExodusLoader.exe (PID: 4112)
Reads the computer name
- ExodusLoader.exe (PID: 4112)
Reads Environment values
- ExodusLoader.exe (PID: 4112)
Reads the machine GUID from the registry
- ExodusLoader.exe (PID: 4112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:03:09 03:04:06 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | larp-exodus-main/ |
Total processes
124
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
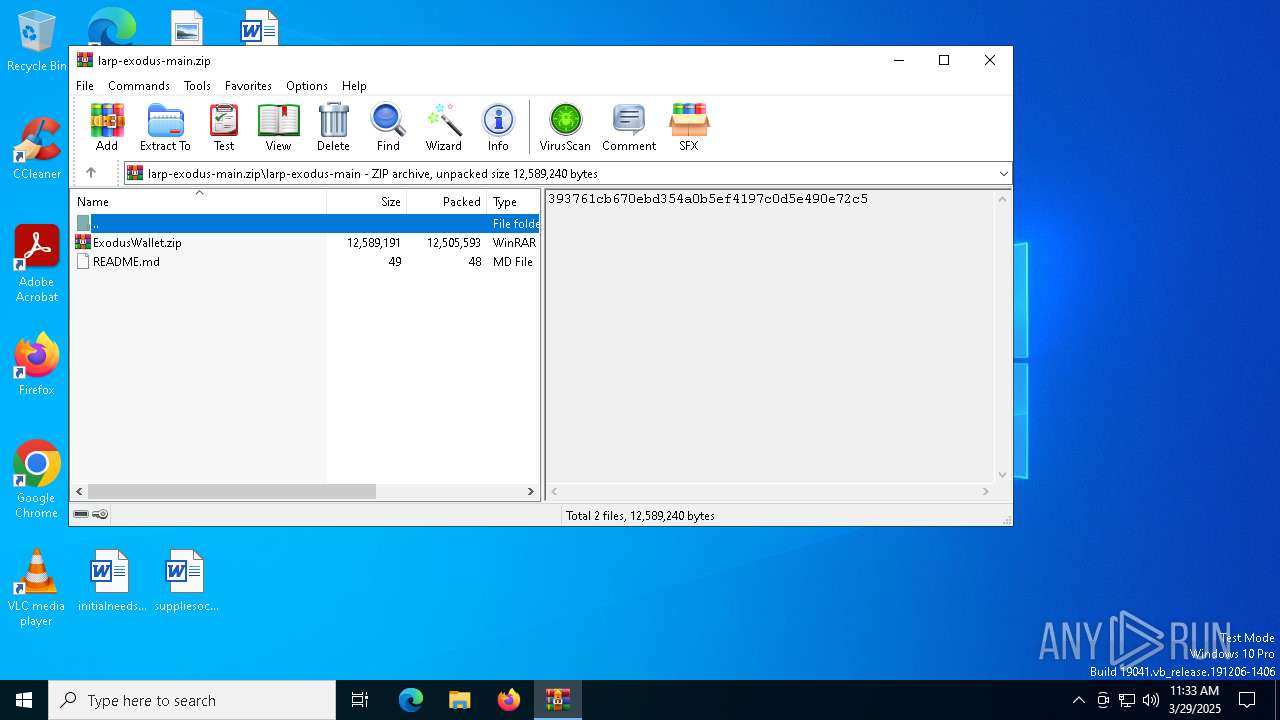
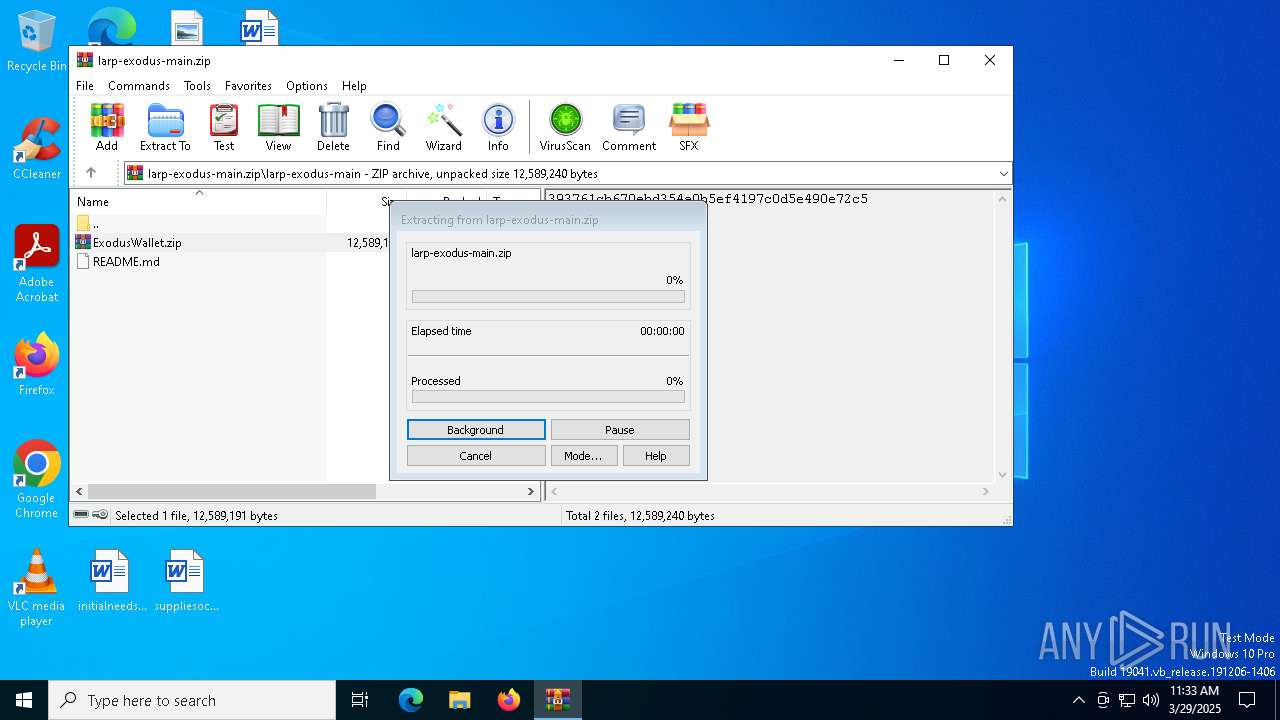
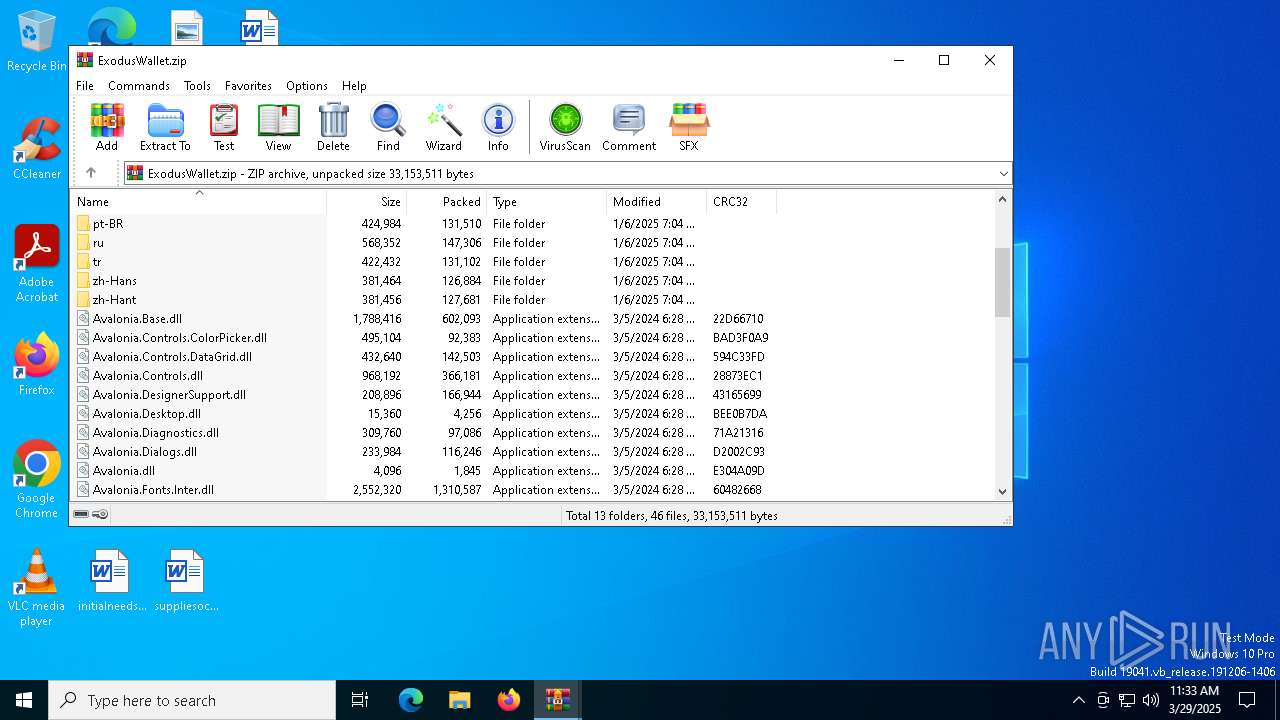
| 1180 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\larp-exodus-main.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2096 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
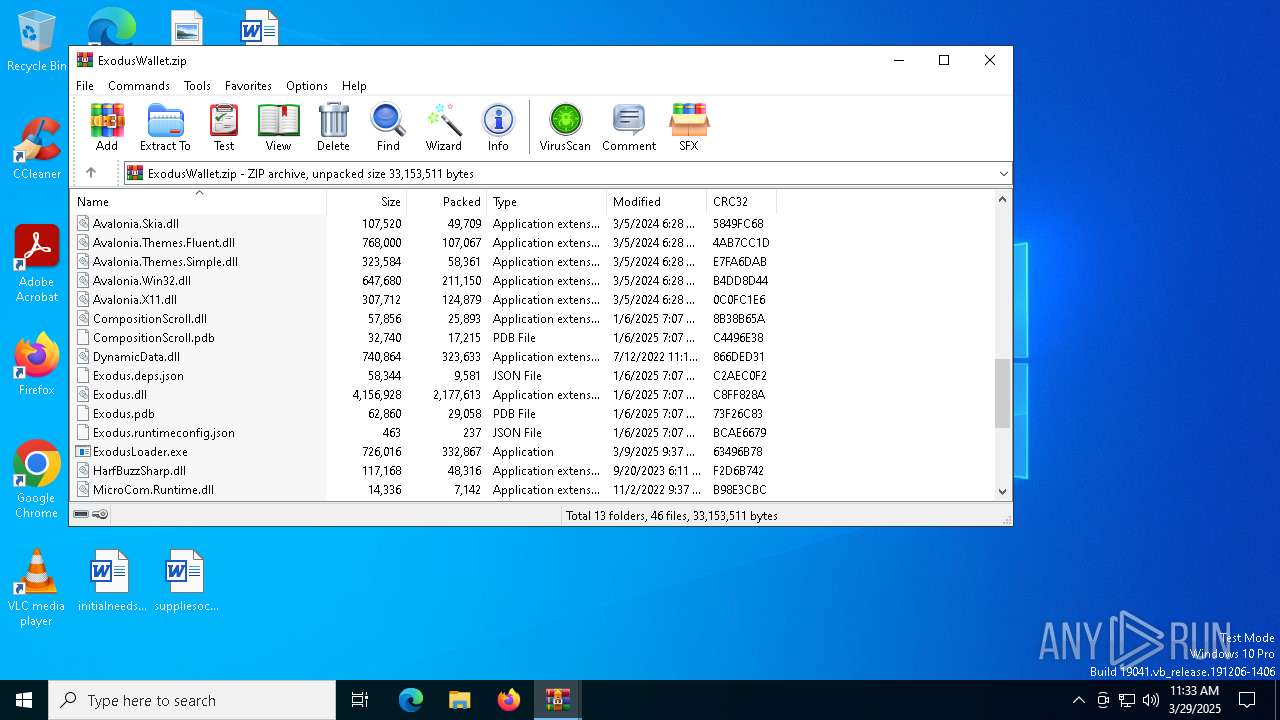
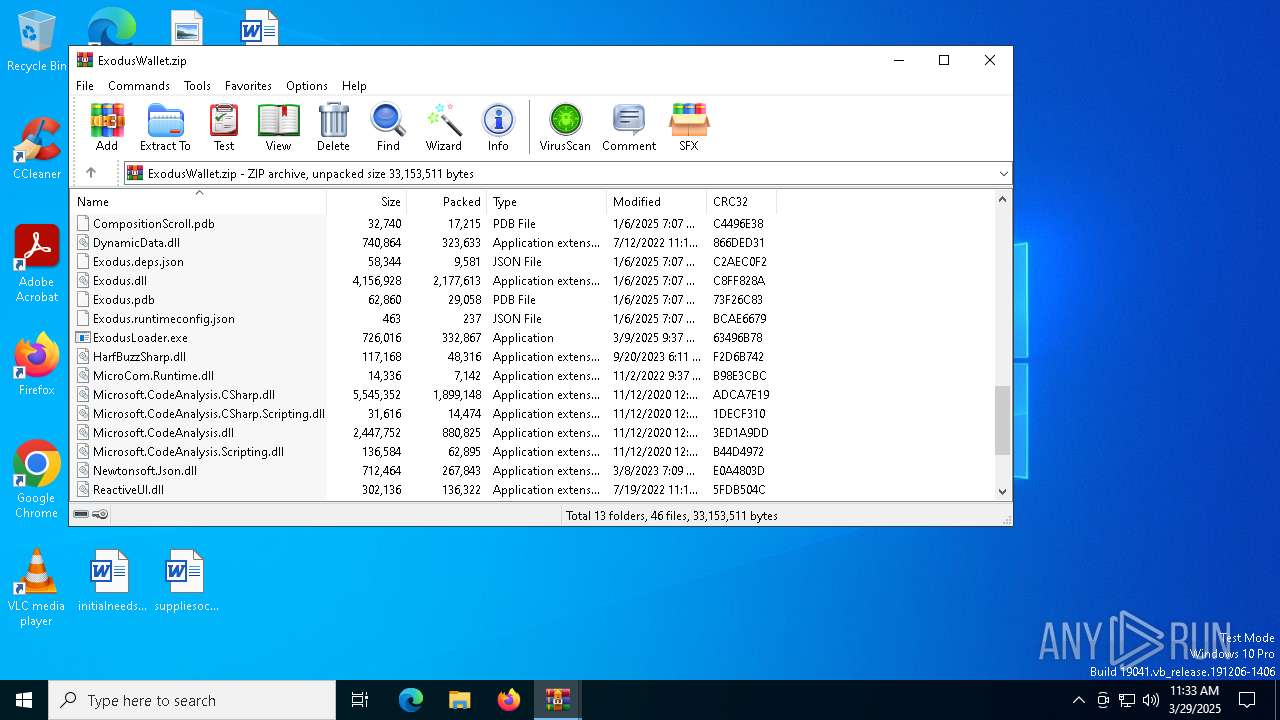
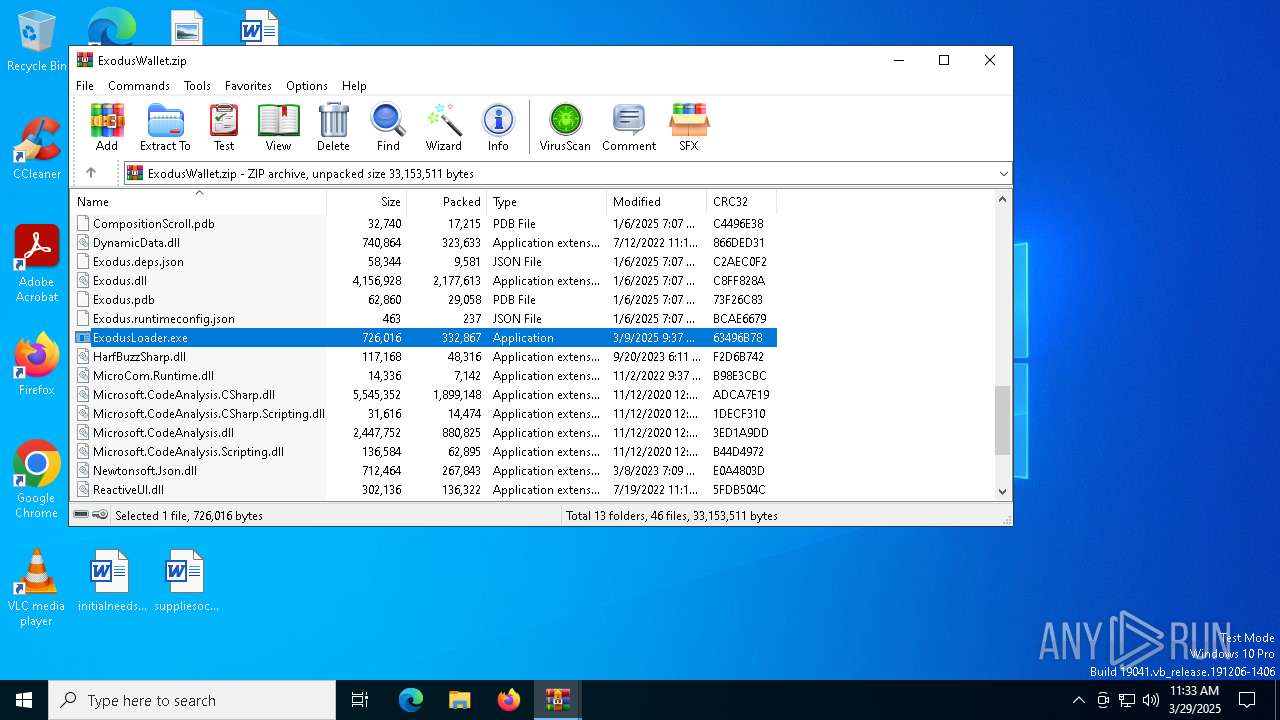
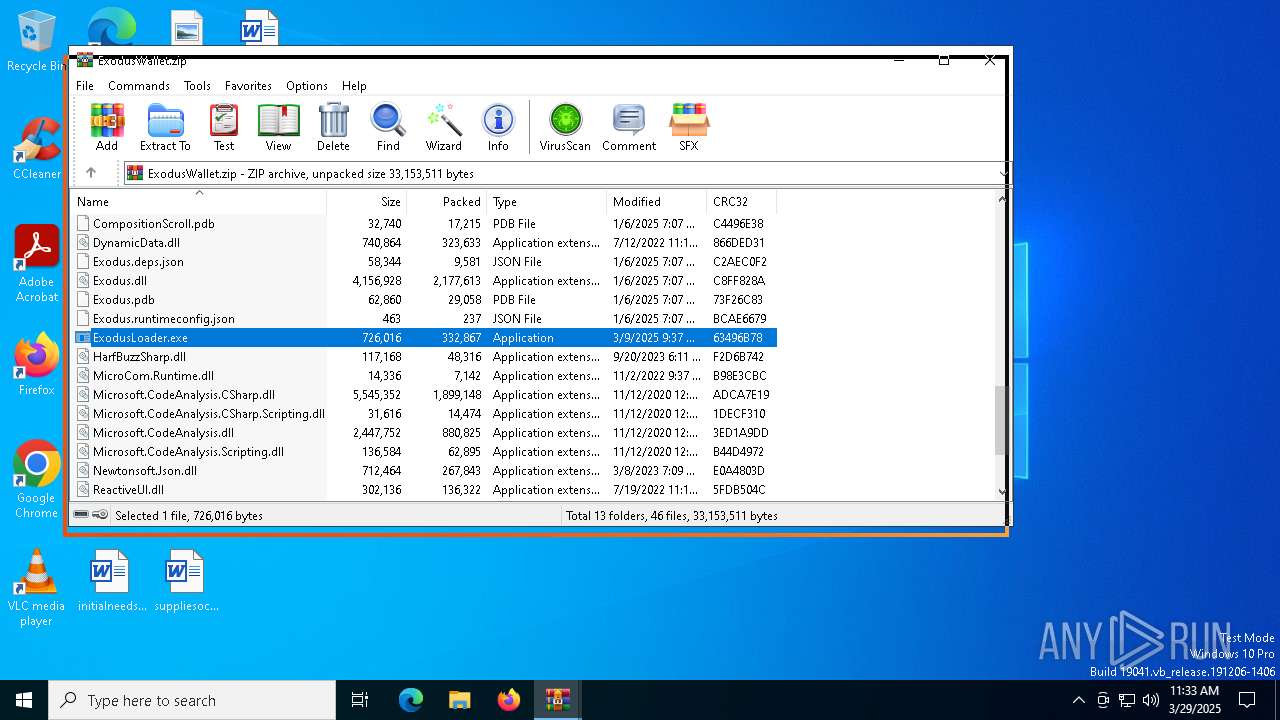
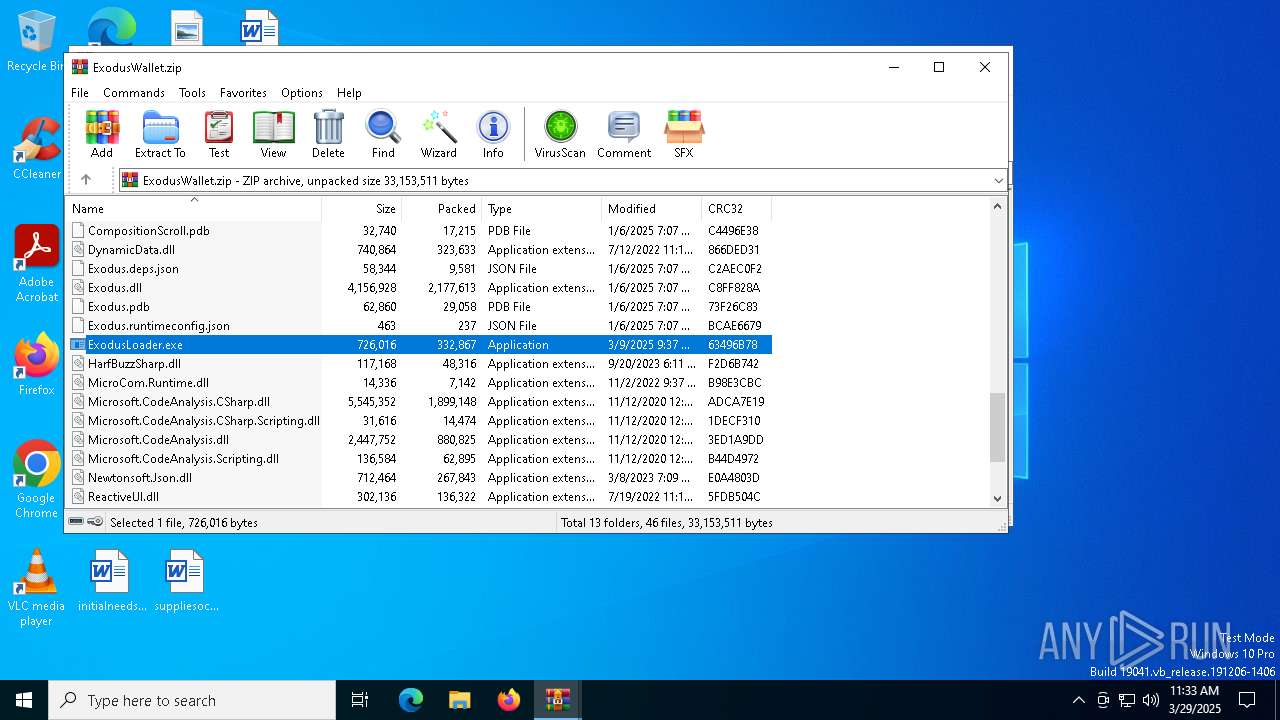
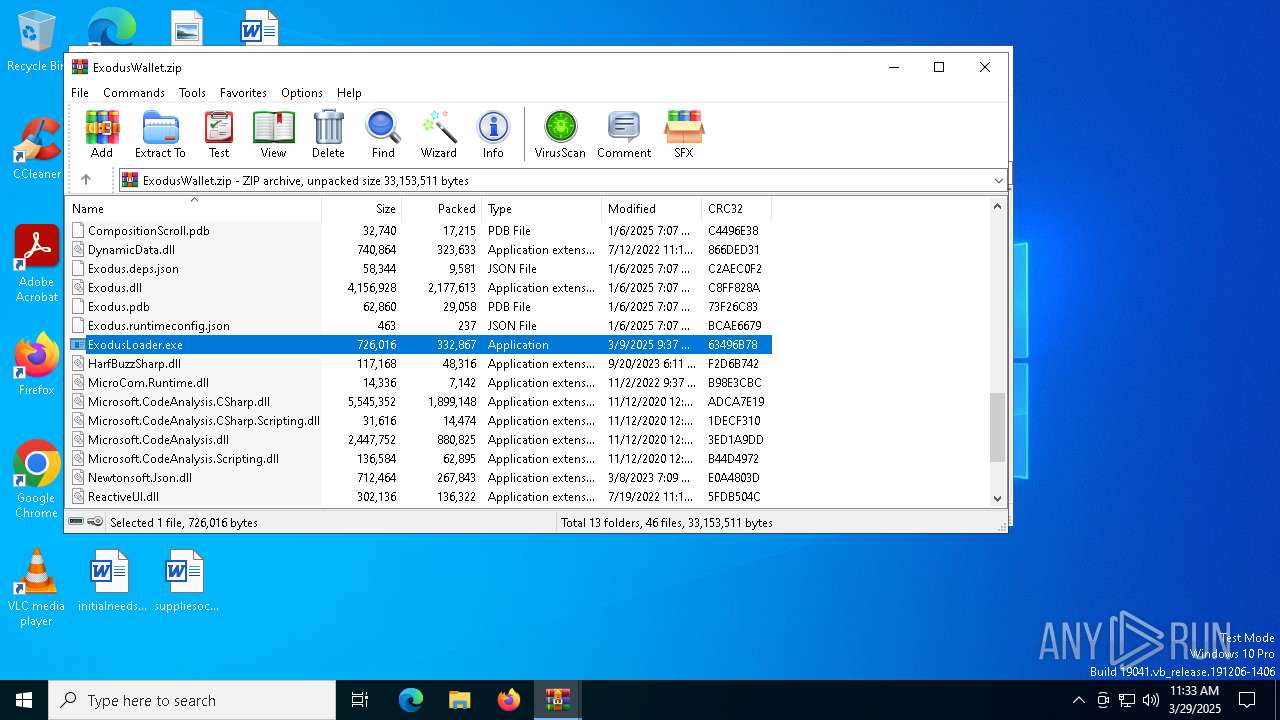
| 3020 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa1180.31395\ExodusWallet.zip | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4112 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3020.31899\ExodusLoader.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3020.31899\ExodusLoader.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.4.1 Modules
| |||||||||||||||
Total events
4 336
Read events
4 320
Write events
16
Delete events
0
Modification events
| (PID) Process: | (1180) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1180) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1180) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1180) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\larp-exodus-main.zip | |||
| (PID) Process: | (1180) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1180) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1180) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1180) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
93
Suspicious files
6
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
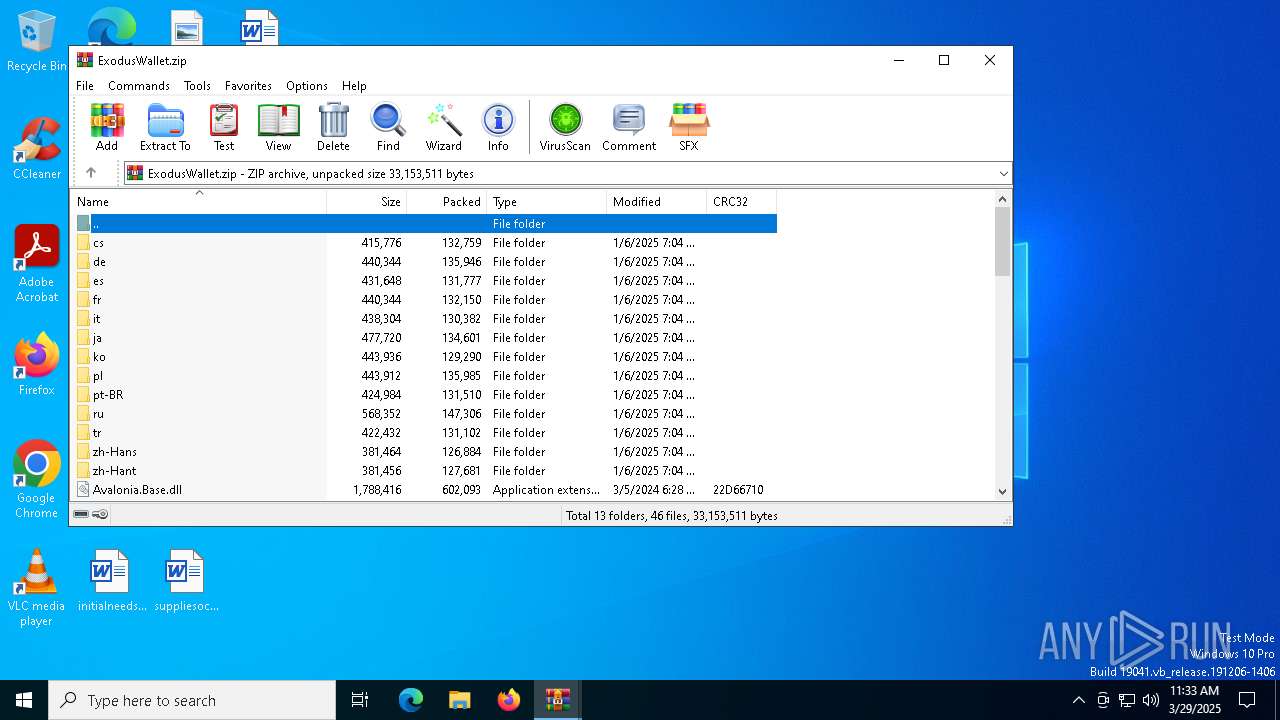
| 3020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3020.31899\MicroCom.Runtime.dll | executable | |
MD5:C27B01D179AB856B42E910496FE749F9 | SHA256:59839E18E46B06AB23B633944AE3C3B552A300C5DA389DA870DFA980BCEF93C1 | |||
| 3020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3020.31899\ReactiveUI.Fody.Helpers.dll | executable | |
MD5:2276DC006B3C86F136CAC75E73EA0756 | SHA256:184BB1A17A1F30C38BD039FF776C3C6FE7A3F680A2B30D8785D3FF90E5FBD14E | |||
| 3020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3020.31899\Microsoft.CodeAnalysis.CSharp.dll | executable | |
MD5:808F5815F7E3B7092924F6C58C38A212 | SHA256:AD26FBE3B2DDE93520C5425F74EA3D17AFF2EE045C659455F5172181B890A726 | |||
| 3020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3020.31899\cs\Microsoft.CodeAnalysis.resources.dll | executable | |
MD5:E98E218B28C34B4C863C23B99C0419CB | SHA256:3F01D8BD84718F05E6CFCF1396F11B91B11FA93E5E9B07B2236E0D1E7E8C16D5 | |||
| 3020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3020.31899\Newtonsoft.Json.dll | executable | |
MD5:ADF3E3EECDE20B7C9661E9C47106A14A | SHA256:22C649F75FCE5BE7C7CCDA8880473B634EF69ECF33F5D1AB8AD892CAF47D5A07 | |||
| 3020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3020.31899\Tmds.DBus.Protocol.dll | executable | |
MD5:492783813953BF82E43C2083BF262A7C | SHA256:6A38C93A728FA33DD1EE35EA5E12EBEF9E9365C2A550D2A1C3D54E46DF8594BA | |||
| 3020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3020.31899\ReactiveUI.dll | executable | |
MD5:CB35EE743A0D1CB032849A15824F3EB1 | SHA256:620B8AEB14CDD6143D3FCB5273AF510CD898E50B08B6DD717BA124EB64E77BB5 | |||
| 3020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3020.31899\Splat.dll | executable | |
MD5:5378F7B03620F7ED4275AC5D73FB86C0 | SHA256:626E82D8797EAE368DC11347DF2425D3F9860FCA8BA52DF741139895DFFA92A5 | |||
| 3020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3020.31899\SkiaSharp.dll | executable | |
MD5:7431676C90A5D584D50C8F209DEA9DFD | SHA256:6C38973434C742D65A0E2B82C6F5471E53EA1D85FB0CA058274ECD4F7D51B839 | |||
| 3020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3020.31899\Microsoft.CodeAnalysis.Scripting.dll | executable | |
MD5:F8485604C7AF6A2FD52A49DB2CBD6629 | SHA256:14AFC4797218A849C71E88760DE14D5AA4EB25EA0F8CE0C6CAC693BAC681B539 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
61
DNS requests
10
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4120 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4120 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 20.198.162.78:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
4112 | ExodusLoader.exe | 195.177.94.58:7000 | — | WINDSTREAM | US | malicious |
4120 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4120 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4120 | SIHClient.exe | 20.3.187.198:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4112 | ExodusLoader.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 37 |