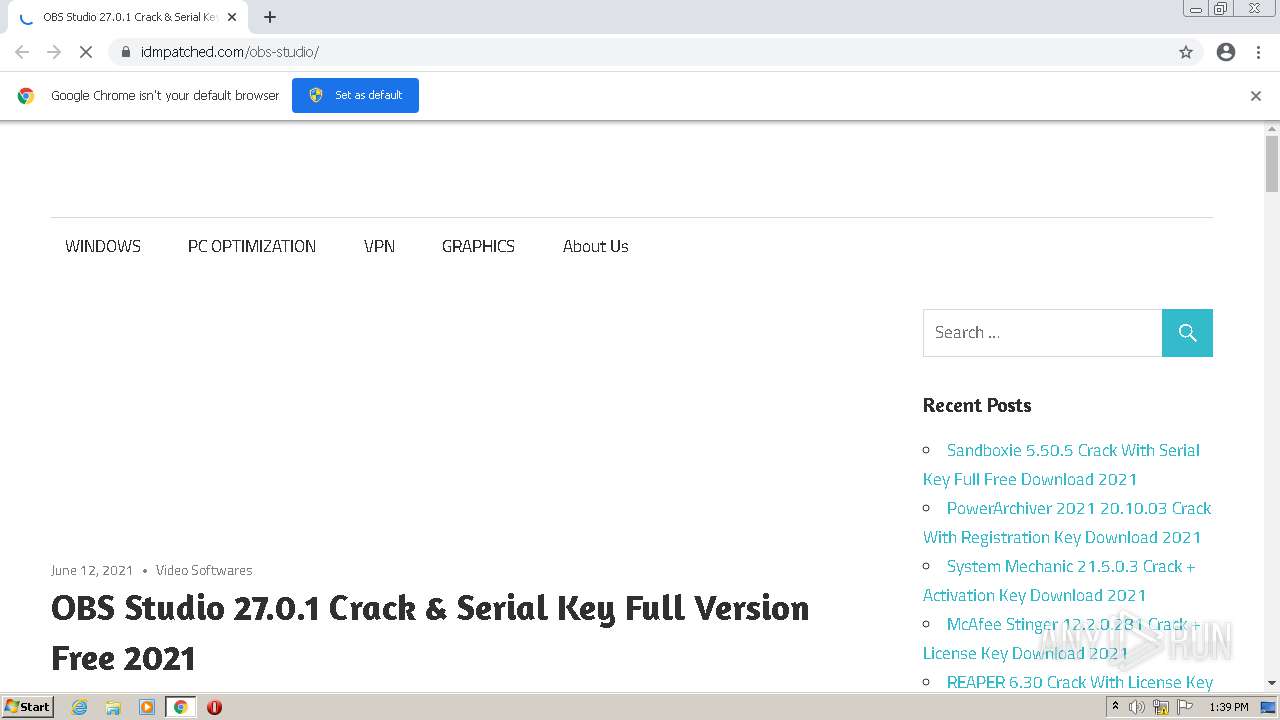
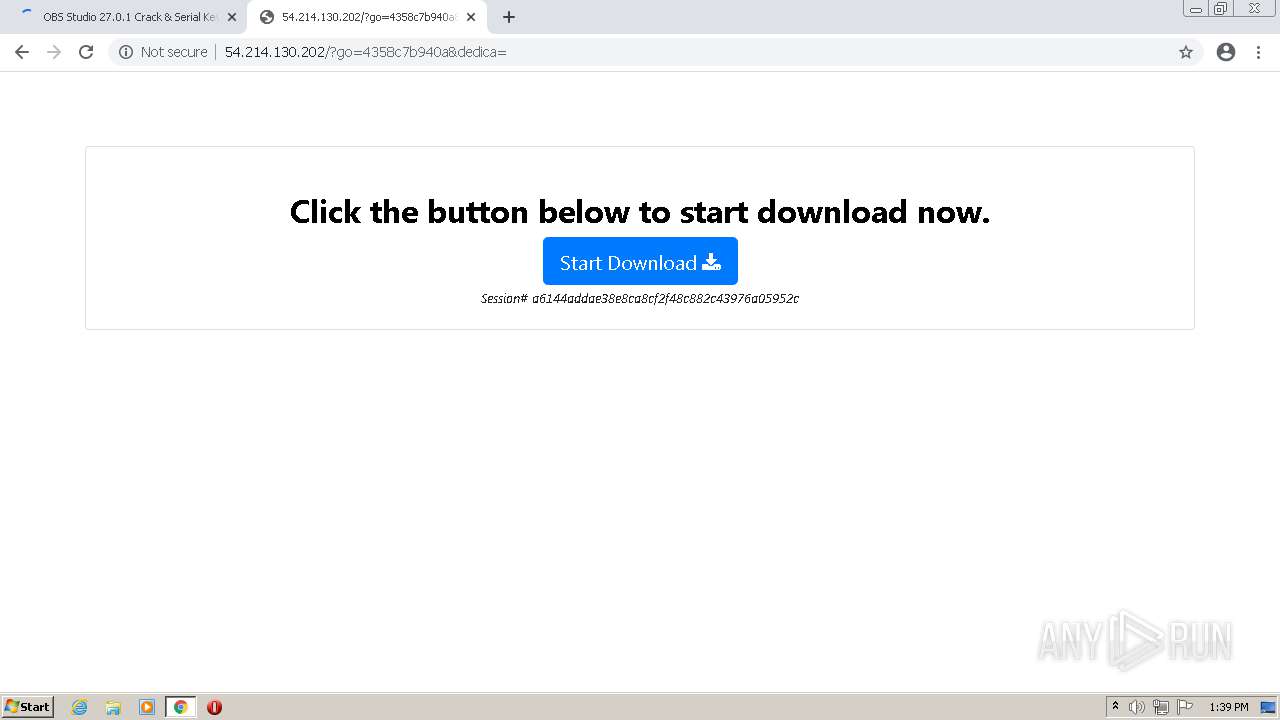
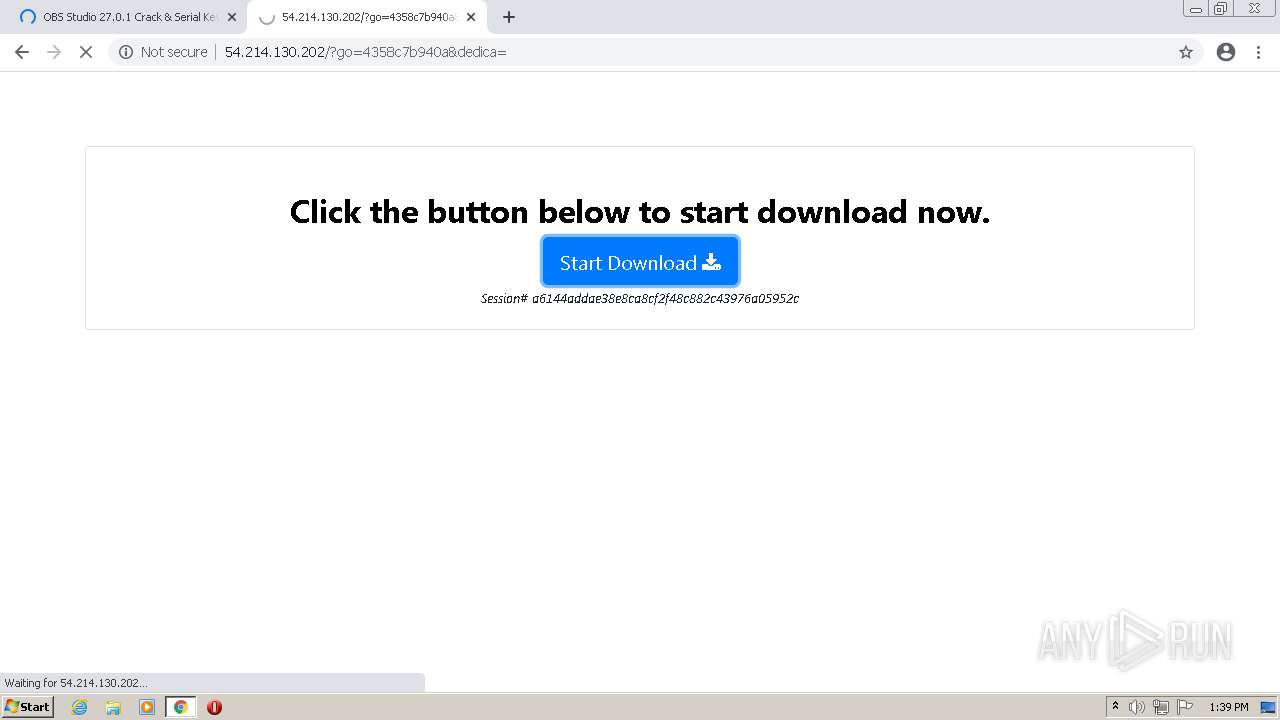
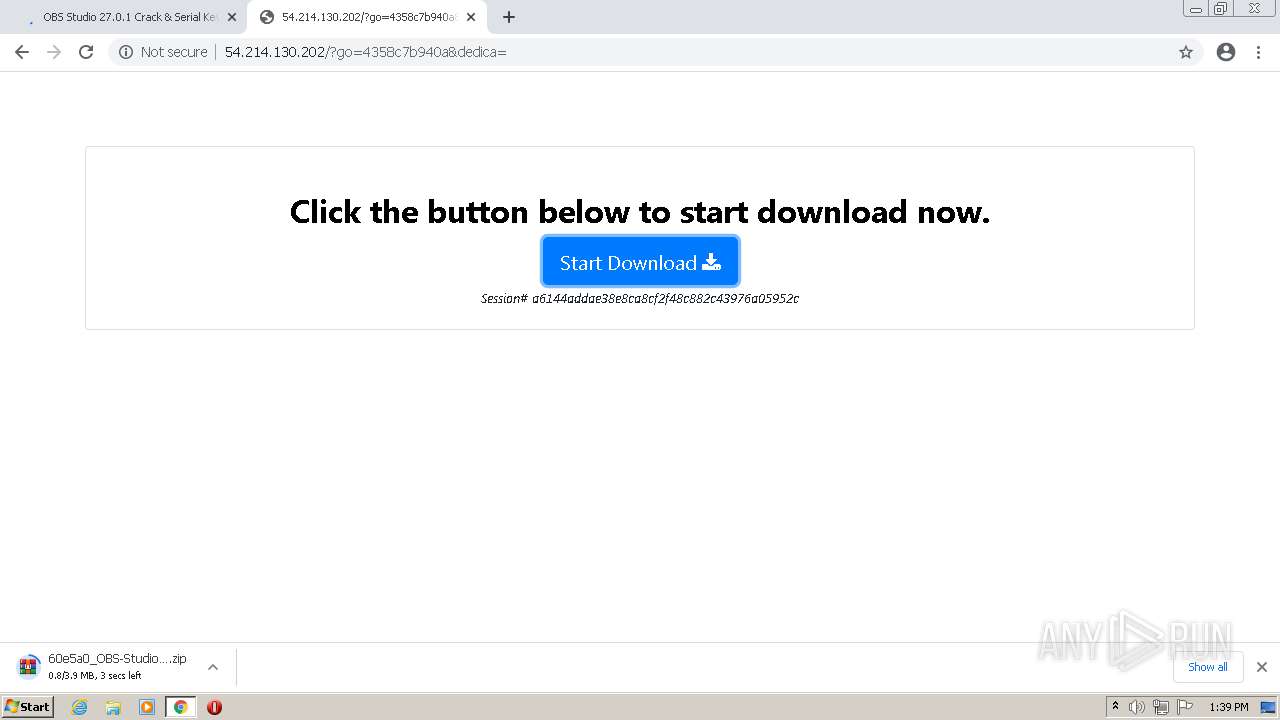
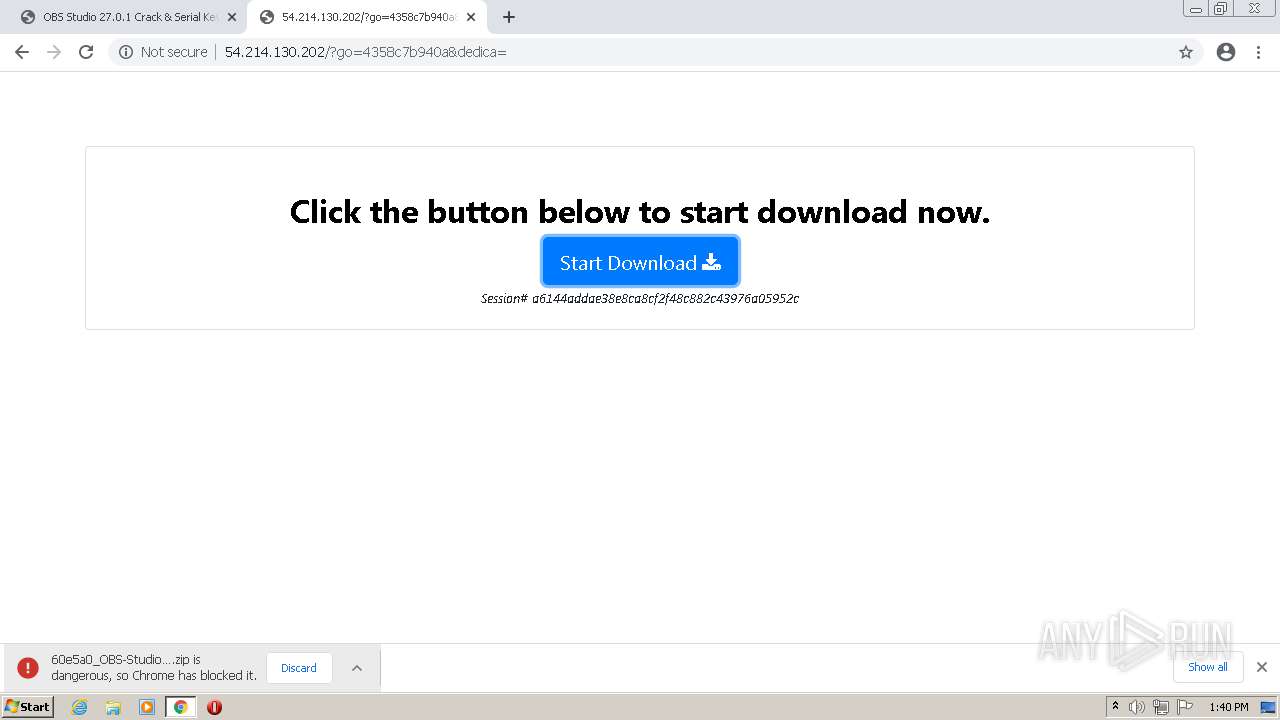
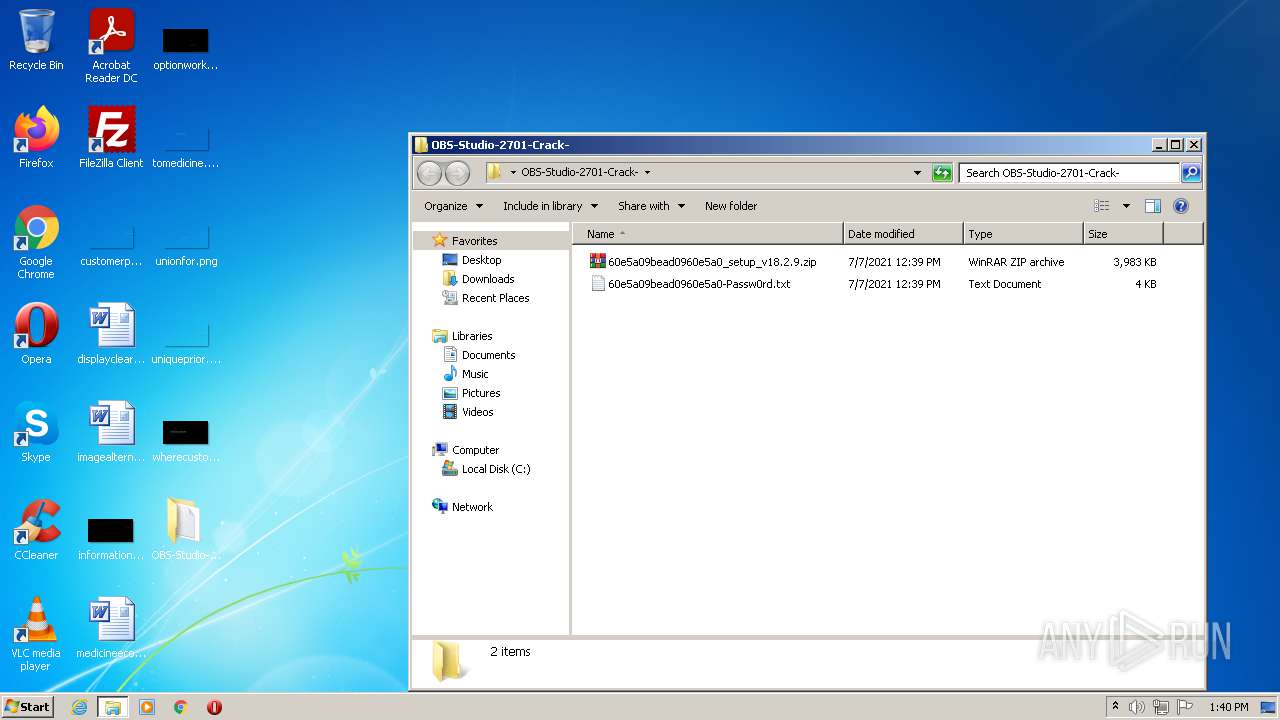
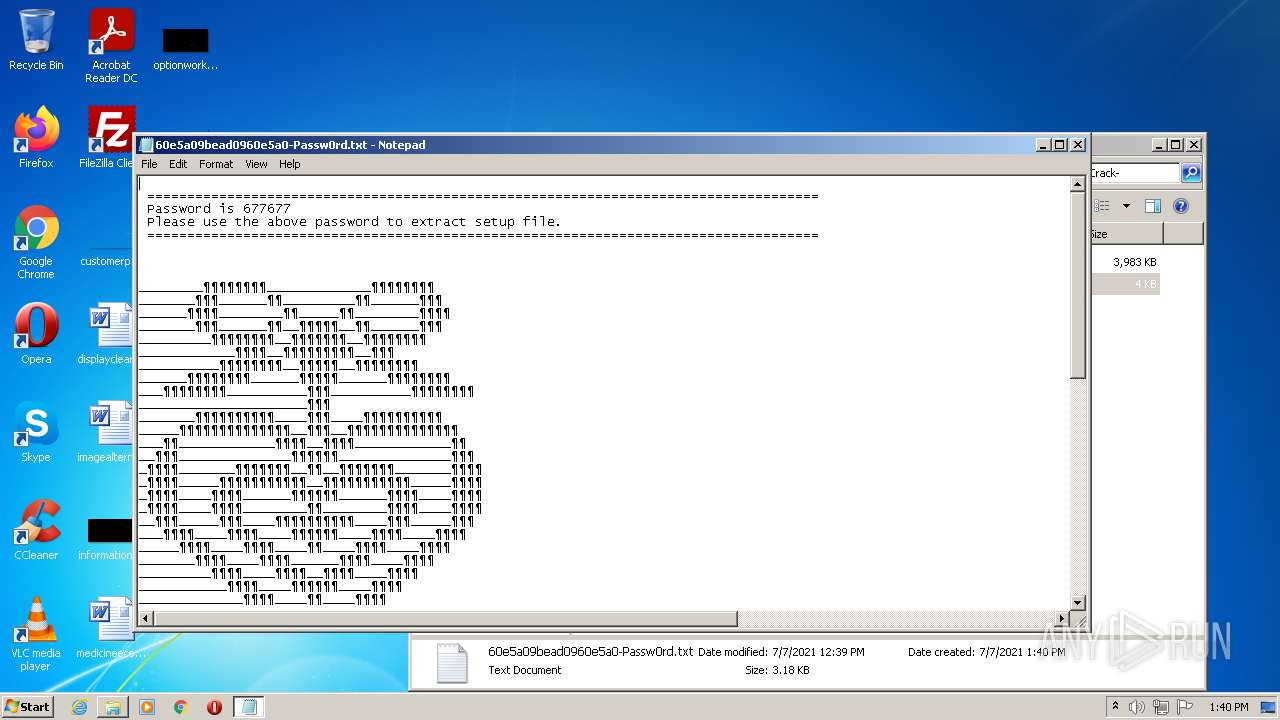
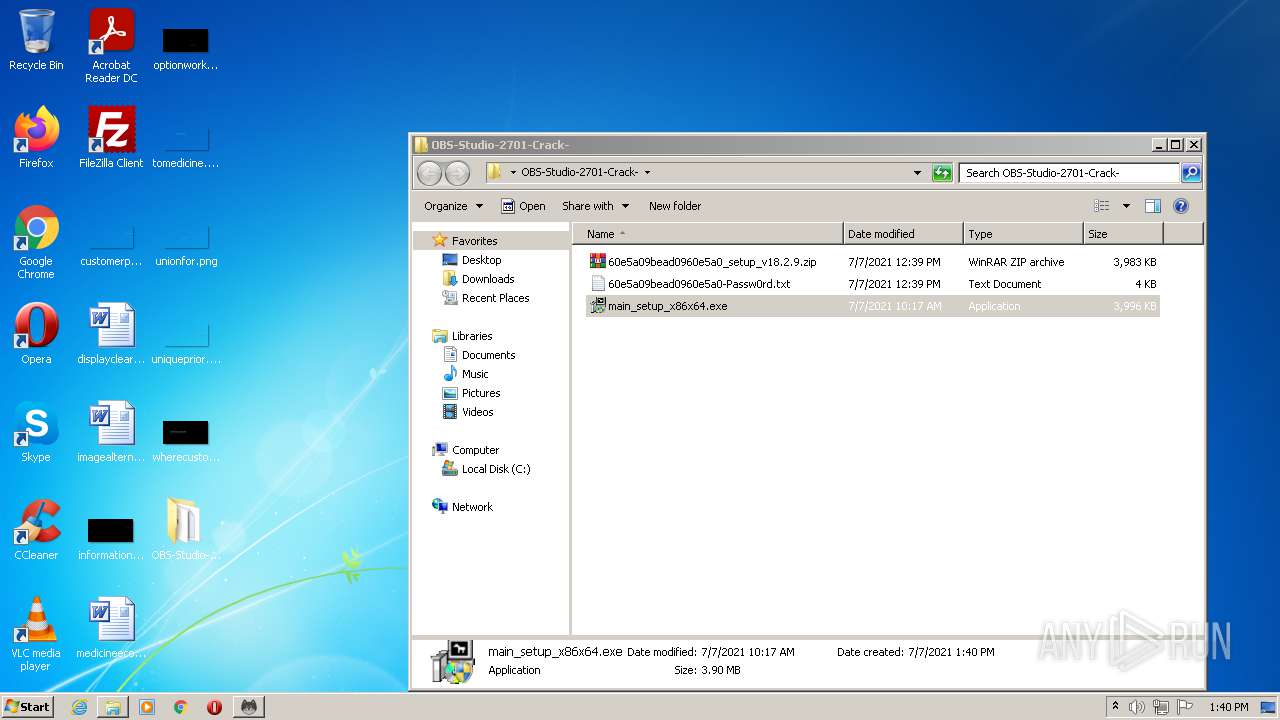
| URL: | https://idmpatched.com/obs-studio/ |
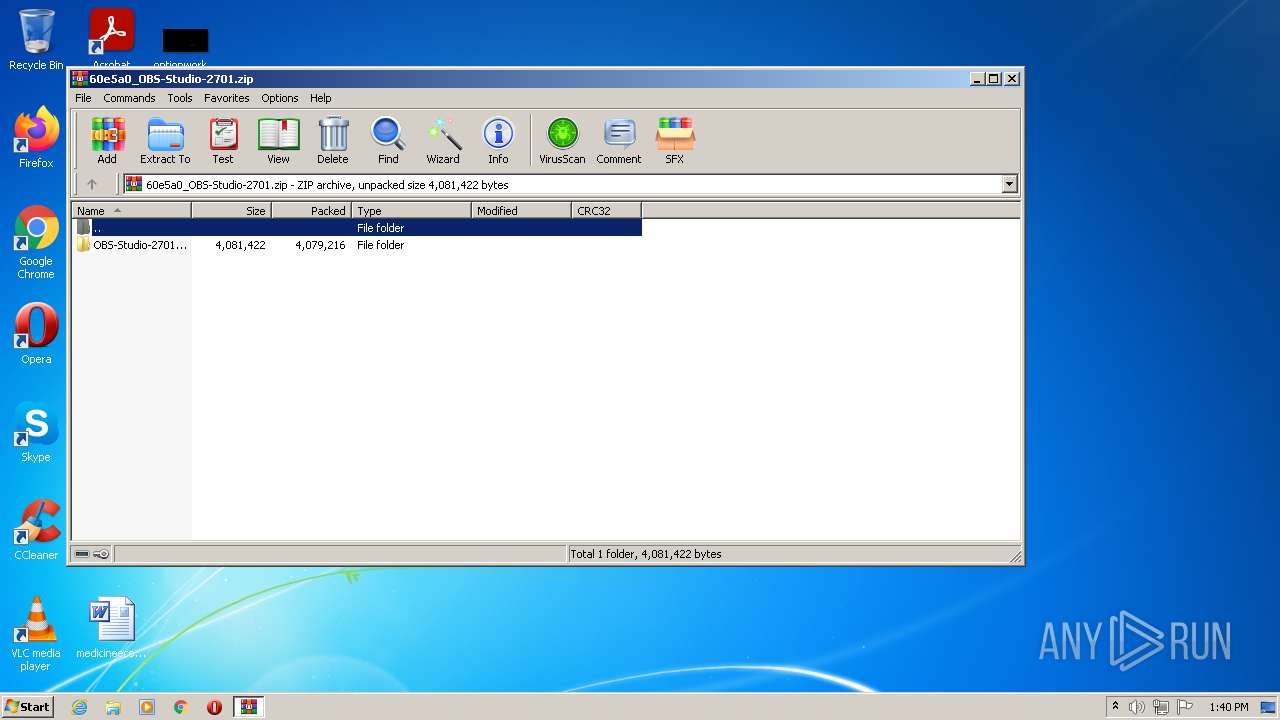
| Full analysis: | https://app.any.run/tasks/4e21697a-1a8c-45a1-950b-ee008e2f588f |
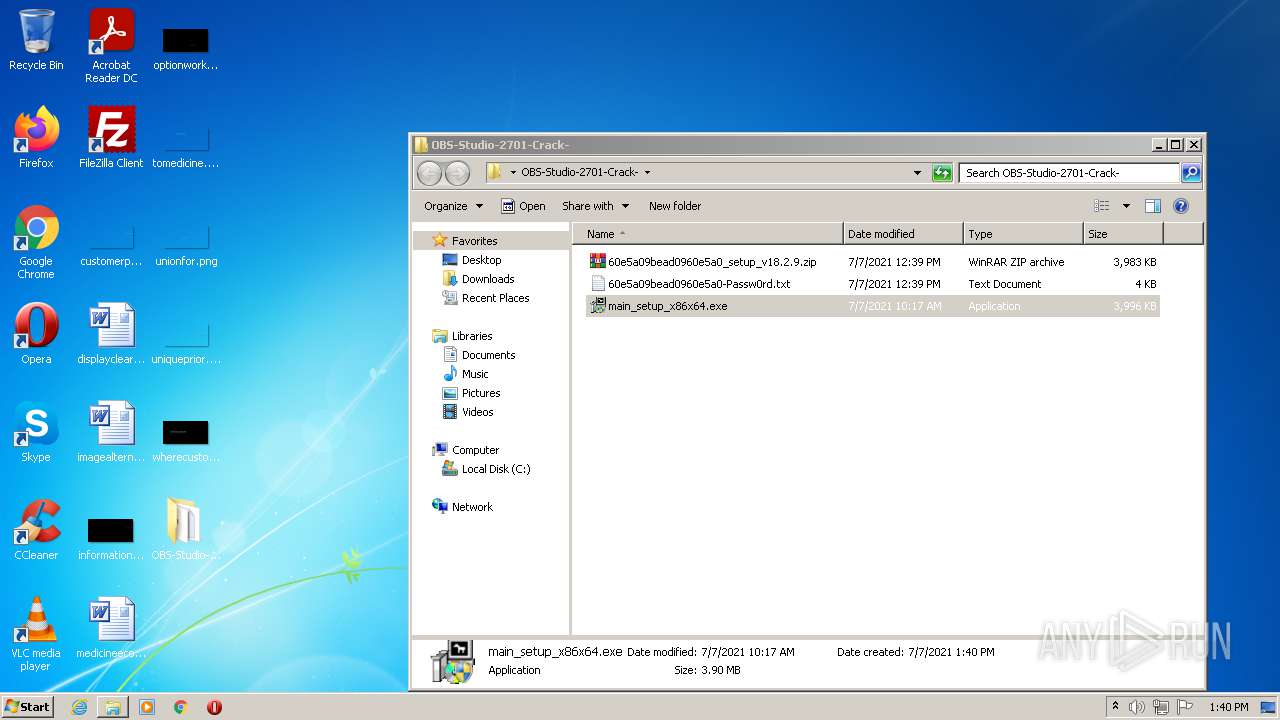
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | July 07, 2021, 12:39:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 449E717CD1C8C9B8D8BB911F02746AD0 |
| SHA1: | 50BB4A7F642A094A7AC4AC1DD5B21D7F1FC659AA |
| SHA256: | BB6D9BAD1CD4F64DC93FB6E986F95CFF0BEEF00534A8BD0D4EE7272DD90B2882 |
| SSDEEP: | 3:N8CLByTKcPWQcn:2CLByTKceP |
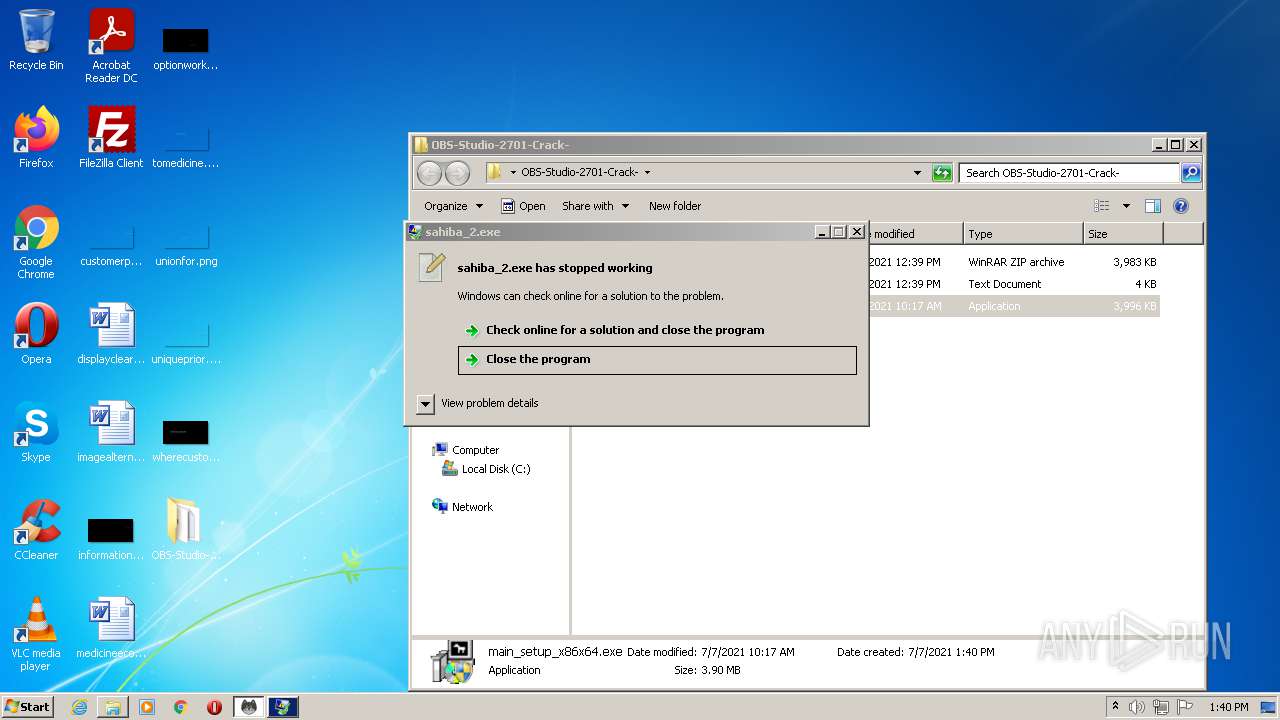
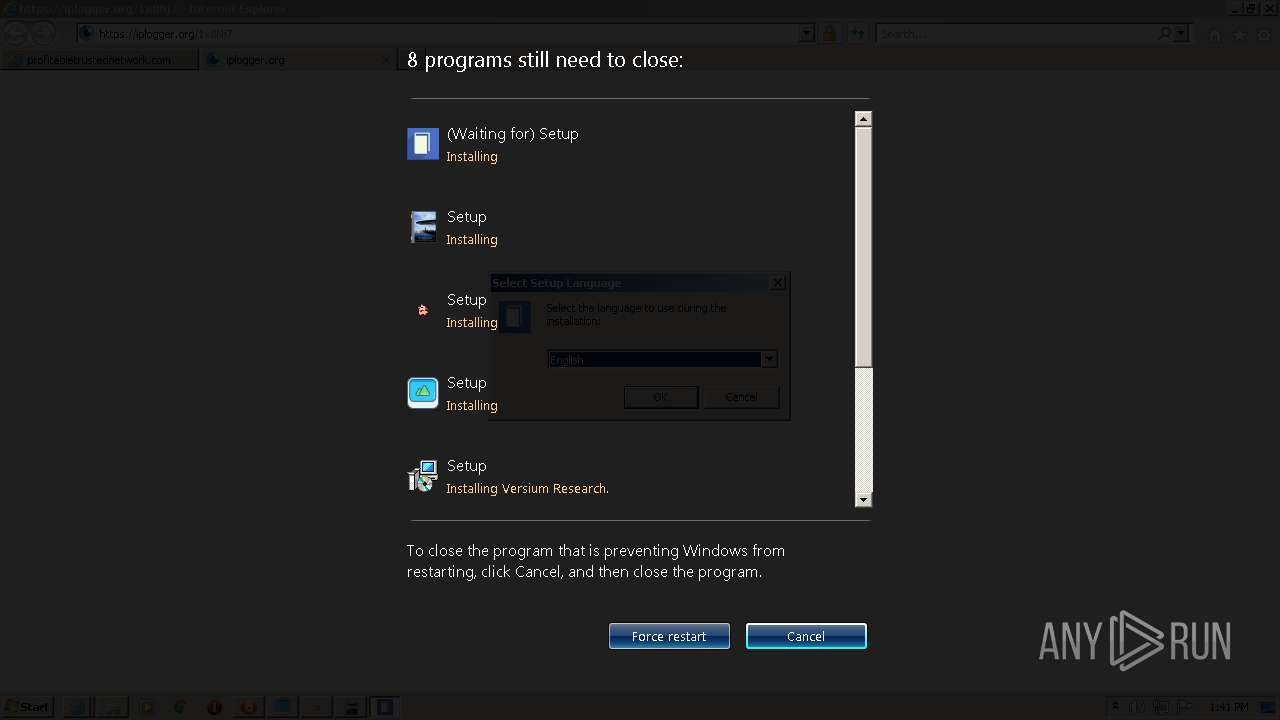
MALICIOUS
Application was dropped or rewritten from another process
- main_setup_x86x64.exe (PID: 1452)
- main_setup_x86x64.exe (PID: 2840)
- setup_installer.exe (PID: 400)
- sahiba_1.exe (PID: 3304)
- sahiba_2.exe (PID: 2684)
- sahiba_5.exe (PID: 2376)
- sahiba_1.exe (PID: 3668)
- sahiba_6.exe (PID: 3680)
- sahiba_10.exe (PID: 3700)
- sahiba_9.exe (PID: 3904)
- setup_install.exe (PID: 3368)
- sahiba_3.exe (PID: 2636)
- sahiba_8.exe (PID: 4020)
- sahiba_7.exe (PID: 3080)
- sahiba_4.exe (PID: 2124)
- sahiba_9.exe (PID: 2284)
- jfiag3g_gg.exe (PID: 660)
- qgRieigRJBBcVN4NkeX6SlpC.exe (PID: 1124)
- TCDUdNYbyNRCuYogsbUP5uDx.exe (PID: 1764)
- TCDUdNYbyNRCuYogsbUP5uDx.exe (PID: 1768)
- hR2phX9R4psDgLTytFScSA78.exe (PID: 676)
- 5075929.exe (PID: 3932)
- 6332060.exe (PID: 2316)
- 8565390.exe (PID: 3180)
- WinHoster.exe (PID: 3488)
- jfiag3g_gg.exe (PID: 3696)
- CL2GGLruMiQhagp54ShuBydy.exe (PID: 3256)
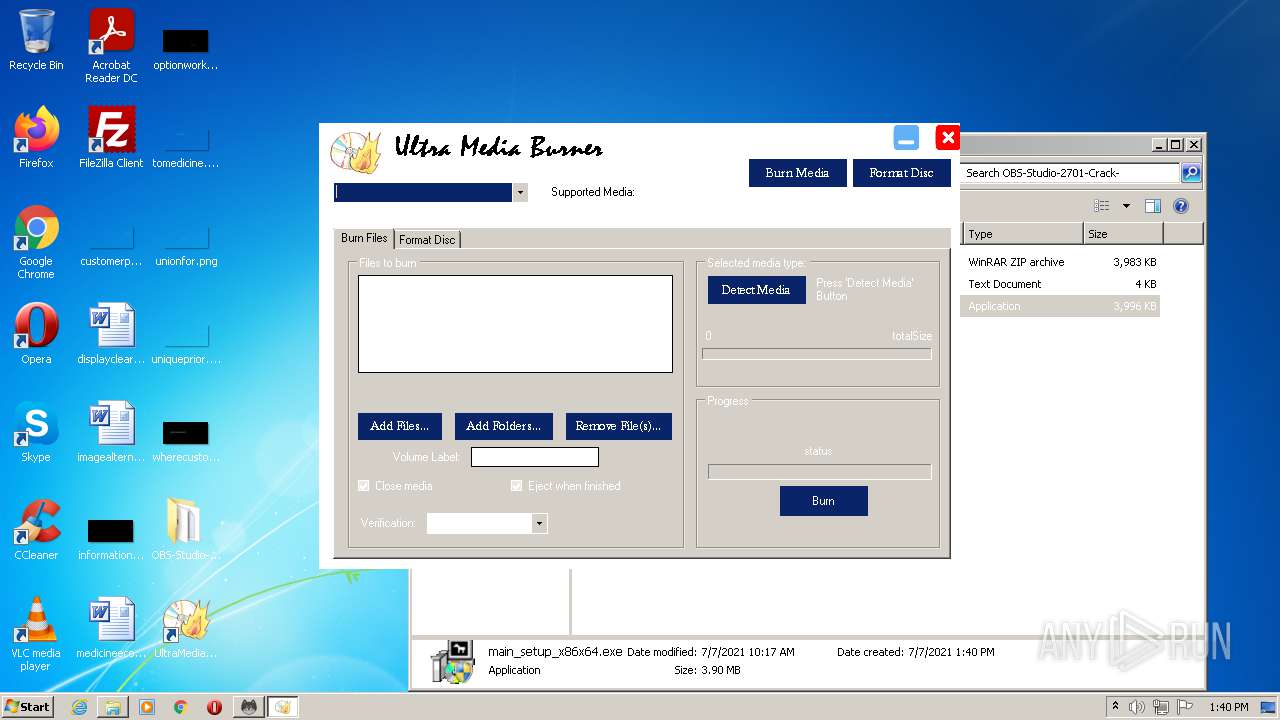
- ultramediaburner.exe (PID: 3852)
- hR2phX9R4psDgLTytFScSA78.exe (PID: 3148)
- 7536611.exe (PID: 320)
- KNF426i_LnuvRjCRn67btkSt.exe (PID: 2348)
- Vaxaefytaeli.exe (PID: 2764)
- 4613966.exe (PID: 3344)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- c47f7cjLMfWJJgWv3X6oDlyU.exe (PID: 2848)
- c47f7cjLMfWJJgWv3X6oDlyU.exe (PID: 2204)
- 4065056.exe (PID: 3880)
- dsEIW6jGafchr6yo61uOgvMx.exe (PID: 3696)
- 92dRgtcSJUitRfKmavFzP9YY.exe (PID: 4644)
- Mepasowikae.exe (PID: 4620)
- 87864724032.exe (PID: 1348)
- vSfsmZQiwu_m83vcAzKfCP55.exe (PID: 4960)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4456)
- 5993665.exe (PID: 2324)
- UltraMediaBurner.exe (PID: 3824)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3292)
- jfiag3g_gg.exe (PID: 5460)
- uuPQOCOMexhx3yxa1N9mqtPQ.exe (PID: 1768)
- uuPQOCOMexhx3yxa1N9mqtPQ.exe (PID: 4440)
- DK2u8J8s6Y_OKtryFL3tUKvl.exe (PID: 320)
- n1Bdoav4ePwmk39pjYjra7rp.exe (PID: 4304)
- jfiag3g_gg.exe (PID: 4940)
- n1Bdoav4ePwmk39pjYjra7rp.exe (PID: 3416)
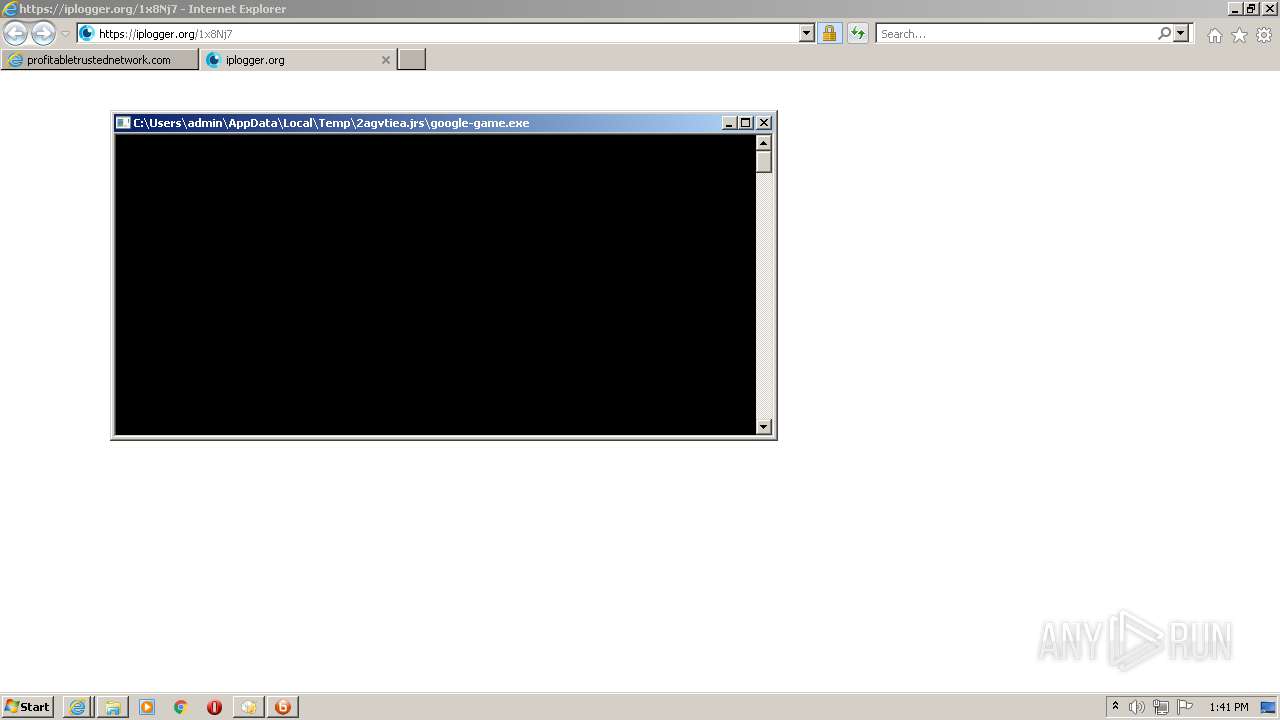
- google-game.exe (PID: 5020)
- google-game.exe (PID: 5572)
- 98827784354.exe (PID: 5852)
- MTgxHjQIwa0xNQWeg6cCDRvX.exe (PID: 5356)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5104)
- 86810264062.exe (PID: 5764)
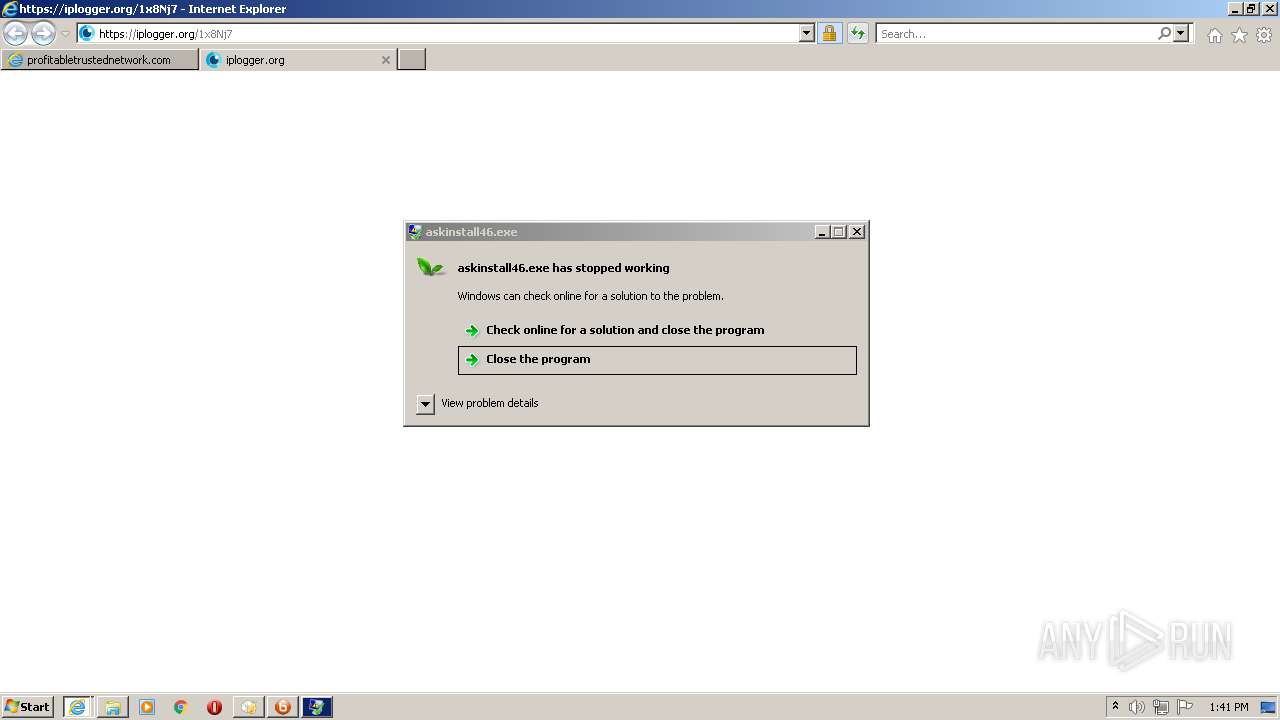
- askinstall46.exe (PID: 1356)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5940)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5560)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5832)
- _u73G1XXPC5iG3vd_ds6OnIc.exe (PID: 4580)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5720)
- 3754144.exe (PID: 6048)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4216)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4544)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 356)
- 7296437.exe (PID: 3952)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2812)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4968)
- VJvJmRSXUxWEsi.exe (PID: 3424)
- JoSetp.exe (PID: 4720)
- Setup3310.exe (PID: 4480)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5564)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3280)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5776)
- 1127893.exe (PID: 2352)
- 6o7inj8hsSfNINZjJNZQpADc.exe (PID: 1760)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2092)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4848)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2316)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 1580)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5992)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4420)
- edspolishpp.exe (PID: 4568)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4148)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3332)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4880)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5680)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5072)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 668)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4152)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 908)
- tpobqkuunp.exe (PID: 2236)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5588)
- LabPicV3.exe (PID: 968)
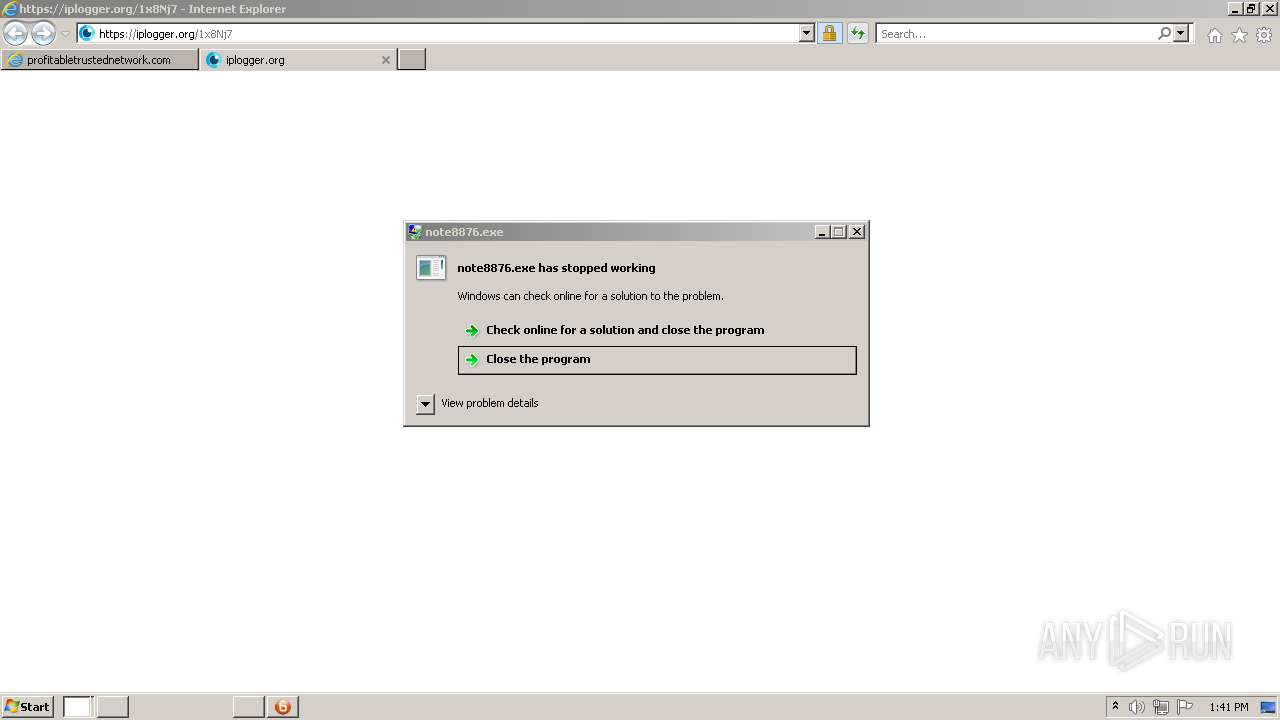
- note8876.exe (PID: 4860)
- guihuali-game.exe (PID: 3940)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3660)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5096)
- app.exe (PID: 4740)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2456)
- guihuali-game.exe (PID: 4540)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4576)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4720)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5488)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3756)
- jfiag3g_gg.exe (PID: 4696)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3304)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5884)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4808)
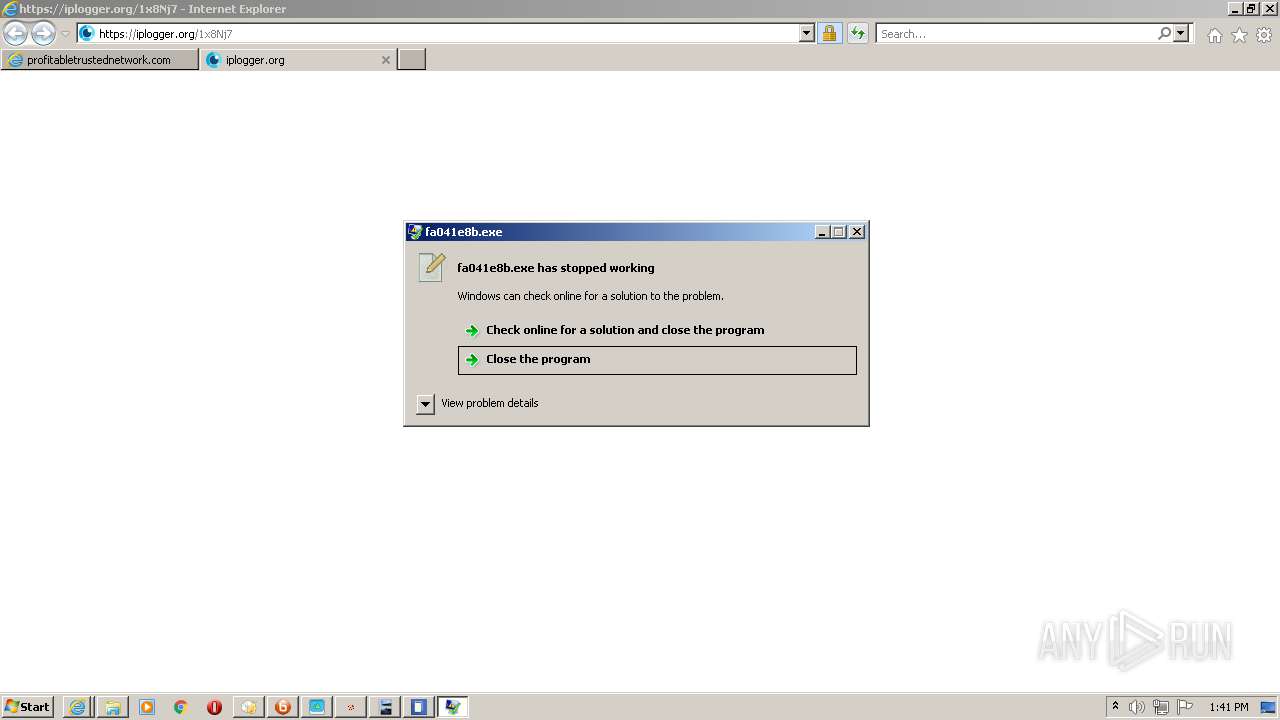
- fa041e8b.exe (PID: 5876)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3540)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4404)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2856)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5188)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 1336)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 860)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4228)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5904)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2584)
- 3346707.exe (PID: 3608)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5712)
- jfiag3g_gg.exe (PID: 3656)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4608)
- UcSb7jo9o_iViBtNSe78kPEu.exe (PID: 3576)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 1212)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5708)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5496)
- ultramediaburner.exe (PID: 4736)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 1476)
- UltraMediaBurner.exe (PID: 4176)
- 7534436.exe (PID: 2388)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5732)
- Qaejelaefomae.exe (PID: 5012)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4892)
- Vareshedema.exe (PID: 468)
- prolab.exe (PID: 4996)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2620)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6040)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5768)
- Paducaehaexy.exe (PID: 1880)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2788)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6136)
- Nucaedimele.exe (PID: 4640)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 1476)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3520)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5932)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5304)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4280)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2744)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4860)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5988)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 756)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5012)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4648)
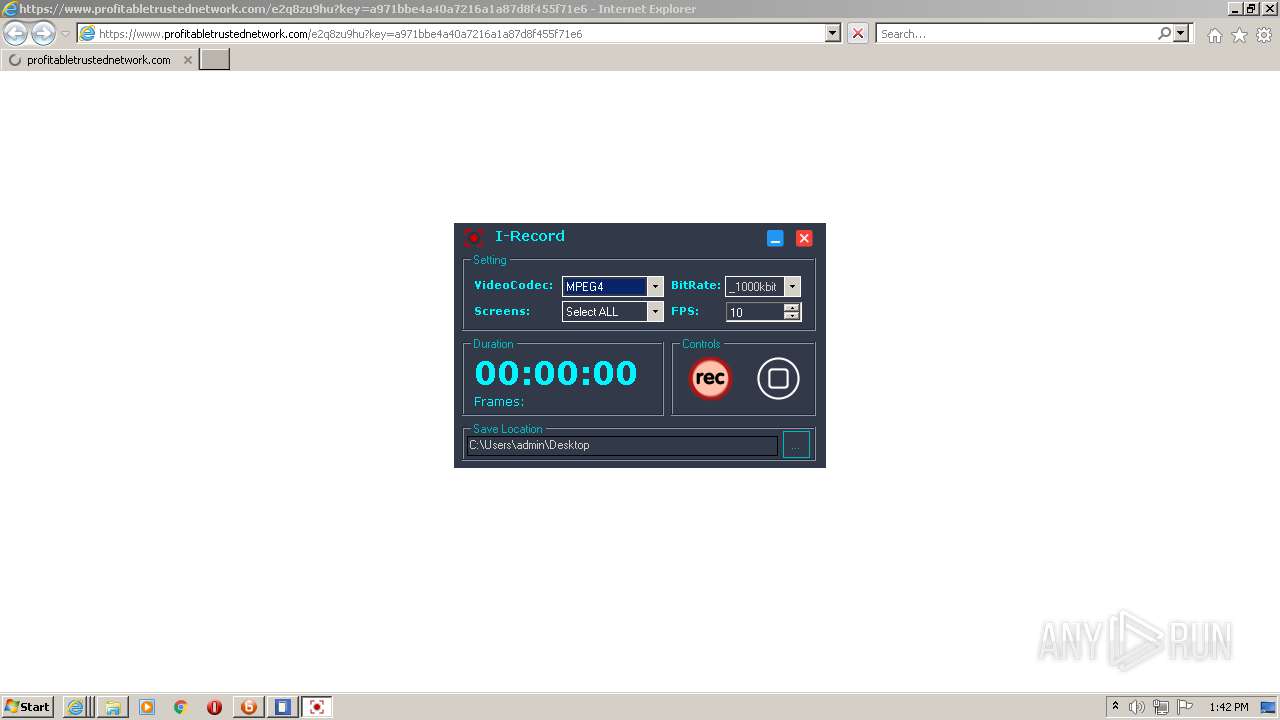
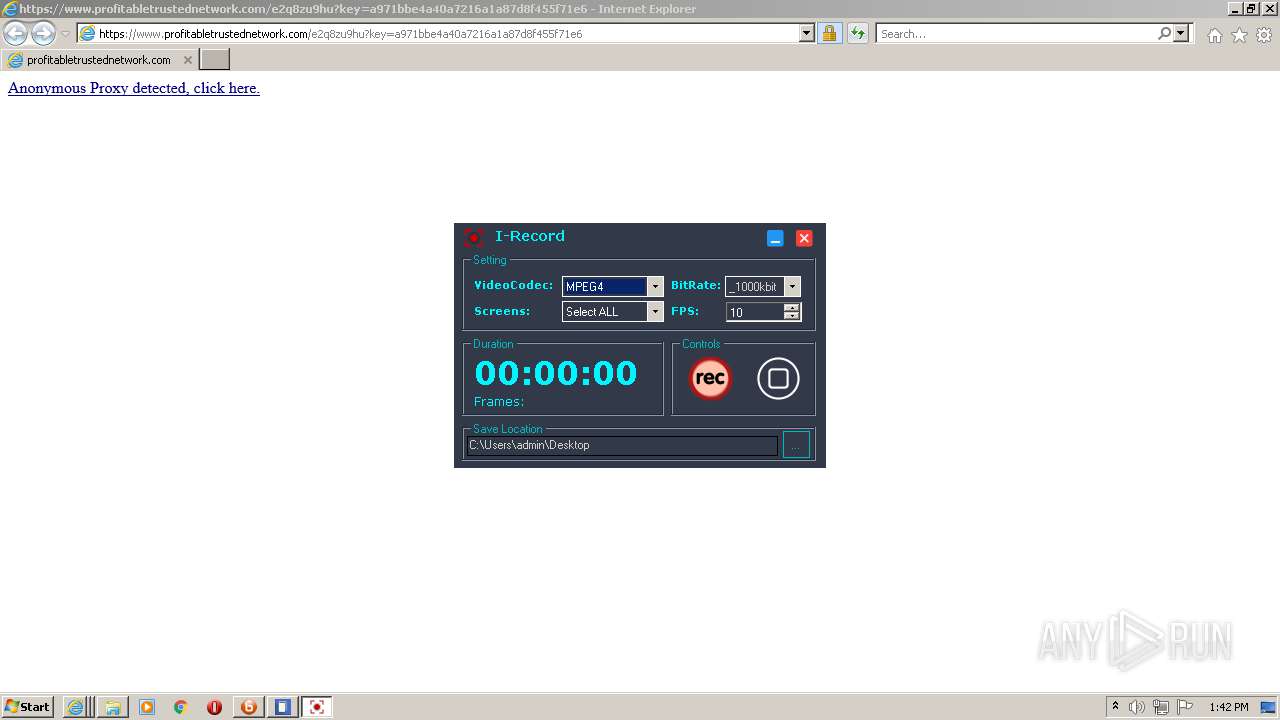
- irecord.exe (PID: 1356)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5628)
- Qashevishudy.exe (PID: 3084)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4352)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 1348)
- Maebumyzhymu.exe (PID: 4328)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 364)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4652)
- SunLabsPlayer.exe (PID: 1172)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5080)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4572)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5036)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4752)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2028)
- toolspab1.exe (PID: 3252)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5124)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6160)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3268)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 748)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6368)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7428)
- toolspab1.exe (PID: 7704)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8264)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9132)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3704)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9304)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 10124)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7724)
- Setup3310.exe (PID: 5292)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8204)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2192)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8632)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9756)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 10224)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7720)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 1376)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3316)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2792)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2388)
- libravpn_setup.exe (PID: 7324)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9124)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9404)
- google-game.exe (PID: 10104)
- google-game.exe (PID: 9420)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5716)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7856)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8336)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7644)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5296)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8588)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7252)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7024)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9640)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7892)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2432)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7144)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6492)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8788)
- app.exe (PID: 7784)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5412)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 10108)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9036)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7660)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6808)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9624)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3784)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8488)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6232)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5740)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5952)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8912)
- SunLabsPlayer.exe (PID: 7596)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8992)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9012)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4996)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5480)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6304)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 336)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9724)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8784)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9424)
- toolspab1.exe (PID: 7608)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7696)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7832)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8056)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7412)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2240)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7172)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9924)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3956)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9428)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5140)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6156)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8156)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2836)
- toolspab1.exe (PID: 5424)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6888)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9104)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3768)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6236)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6204)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6428)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9536)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9972)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8288)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6580)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8284)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7920)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 1448)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7148)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6456)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2712)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4224)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6604)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6744)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9064)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4536)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9284)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9488)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9692)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7292)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3668)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9260)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7912)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8004)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4000)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4424)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 428)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7320)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7748)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6956)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 1764)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8856)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5128)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6844)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8400)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9516)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7132)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9088)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8060)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9040)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6212)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5604)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5464)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2036)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4036)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6800)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 852)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5208)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6796)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8708)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8956)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7580)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9232)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7628)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 10148)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6116)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 10220)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2436)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4548)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6968)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6392)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8824)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7032)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4800)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8260)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7532)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9100)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4368)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6172)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6088)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 1140)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3700)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7592)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7068)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6396)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9292)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6872)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 1412)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3080)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7472)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 10156)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6020)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7800)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9600)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7700)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6628)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6684)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 1164)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3584)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3404)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8232)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9076)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8420)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9256)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8620)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6892)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4952)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5008)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6584)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7400)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8172)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8928)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6168)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9484)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3648)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6300)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6320)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4708)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 1844)
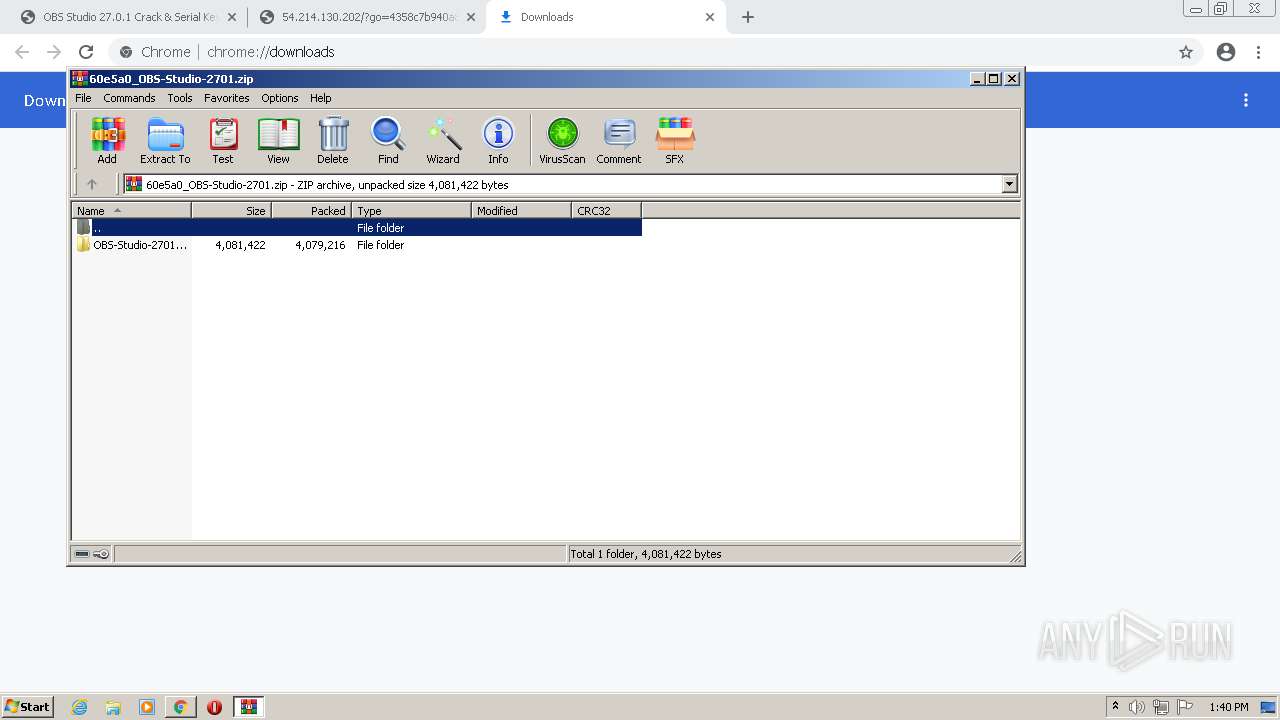
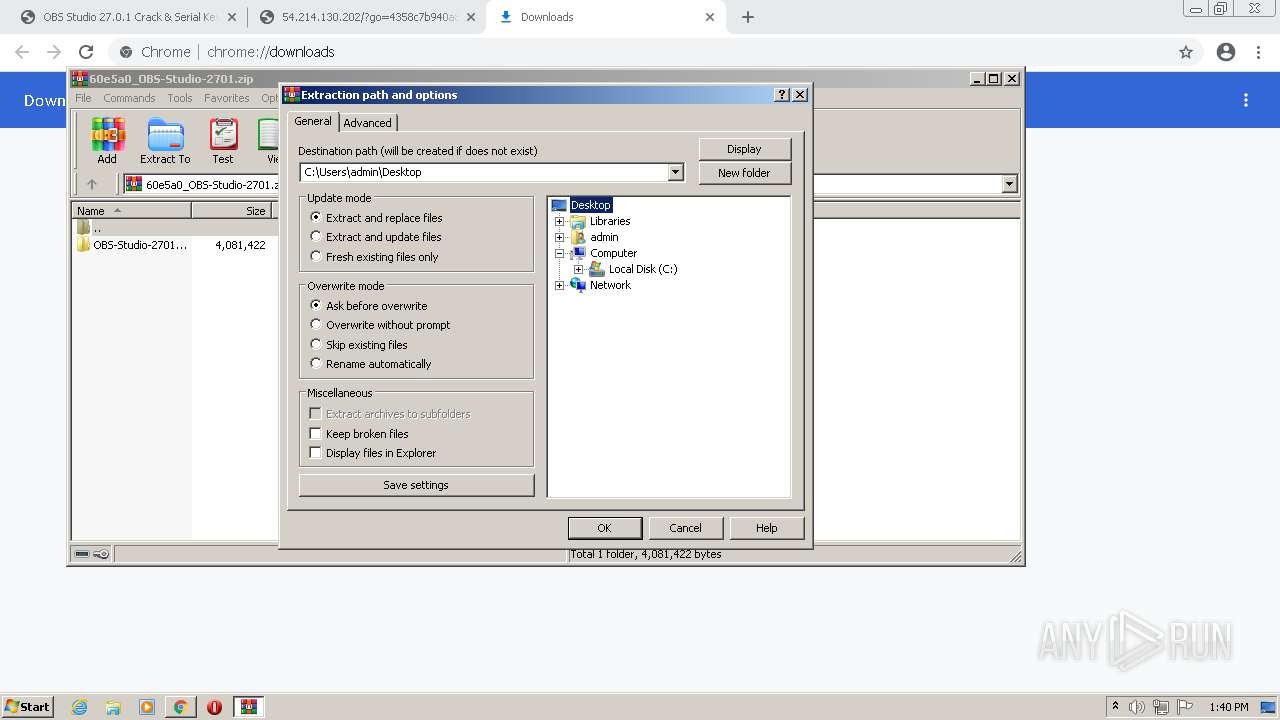
Drops executable file immediately after starts
- setup_installer.exe (PID: 400)
- setup_install.exe (PID: 3368)
- sahiba_5.exe (PID: 2376)
- sahiba_5.tmp (PID: 496)
- sahiba_1.exe (PID: 3668)
- ultramediaburner.exe (PID: 3852)
- ultramediaburner.tmp (PID: 3396)
Loads dropped or rewritten executable
- setup_install.exe (PID: 3368)
- rUNdlL32.eXe (PID: 3520)
- sahiba_3.exe (PID: 2636)
- cmd.exe (PID: 2768)
- conhost.exe (PID: 2276)
- cmd.exe (PID: 968)
- DllHost.exe (PID: 2224)
- chrome.exe (PID: 2164)
- WinRAR.exe (PID: 2108)
- sahiba_1.exe (PID: 3668)
- DllHost.exe (PID: 1960)
- sahiba_10.exe (PID: 3700)
- cmd.exe (PID: 3592)
- main_setup_x86x64.exe (PID: 2840)
- wmiprvse.exe (PID: 2708)
- cmd.exe (PID: 2780)
- sahiba_8.exe (PID: 4020)
- chrome.exe (PID: 2448)
- sahiba_1.exe (PID: 3304)
- chrome.exe (PID: 2060)
- chrome.exe (PID: 4088)
- 6332060.exe (PID: 2316)
- cmd.exe (PID: 2808)
- sahiba_9.exe (PID: 3904)
- chrome.exe (PID: 1264)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 3288)
- sahiba_2.exe (PID: 2684)
- chrome.exe (PID: 568)
- 5075929.exe (PID: 3932)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 1080)
- cmd.exe (PID: 1944)
- chrome.exe (PID: 3004)
- DllHost.exe (PID: 3056)
- sahiba_9.exe (PID: 2284)
- cmd.exe (PID: 1164)
- chrome.exe (PID: 2832)
- svchost.exe (PID: 3992)
- DllHost.exe (PID: 312)
- DllHost.exe (PID: 2028)
- NOTEPAD.EXE (PID: 2328)
- jfiag3g_gg.exe (PID: 660)
- cmd.exe (PID: 1536)
- chrome.exe (PID: 3292)
- sahiba_7.exe (PID: 3080)
- conhost.exe (PID: 2796)
- chrome.exe (PID: 1512)
- sahiba_4.exe (PID: 2124)
- svchost.exe (PID: 3360)
- WinRAR.exe (PID: 520)
- 8565390.exe (PID: 3180)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 3812)
- sahiba_6.exe (PID: 3680)
- DllHost.exe (PID: 2396)
- consent.exe (PID: 2164)
- chrome.exe (PID: 3132)
- sahiba_5.exe (PID: 2376)
- setup_installer.exe (PID: 400)
- chrome.exe (PID: 3312)
- cmd.exe (PID: 468)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 3656)
- WerFault.exe (PID: 2668)
- main_setup_x86x64.exe (PID: 1452)
- cmd.exe (PID: 748)
- conhost.exe (PID: 2696)
- qgRieigRJBBcVN4NkeX6SlpC.exe (PID: 1124)
- hR2phX9R4psDgLTytFScSA78.exe (PID: 676)
- TCDUdNYbyNRCuYogsbUP5uDx.exe (PID: 1764)
- jfiag3g_gg.exe (PID: 3696)
- WinHoster.exe (PID: 3488)
- KNF426i_LnuvRjCRn67btkSt.exe (PID: 2348)
- CL2GGLruMiQhagp54ShuBydy.exe (PID: 3256)
- 7536611.exe (PID: 320)
- TCDUdNYbyNRCuYogsbUP5uDx.exe (PID: 1768)
- ultramediaburner.exe (PID: 3852)
- 4613966.exe (PID: 3344)
- UltraMediaBurner.exe (PID: 3824)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- DllHost.exe (PID: 1348)
- hR2phX9R4psDgLTytFScSA78.exe (PID: 3148)
- Vaxaefytaeli.exe (PID: 2764)
- dsEIW6jGafchr6yo61uOgvMx.exe (PID: 3696)
- Browzar.exe (PID: 3056)
- MrGh6bEH0L0a.exe (PID: 1304)
- DllHost.exe (PID: 3352)
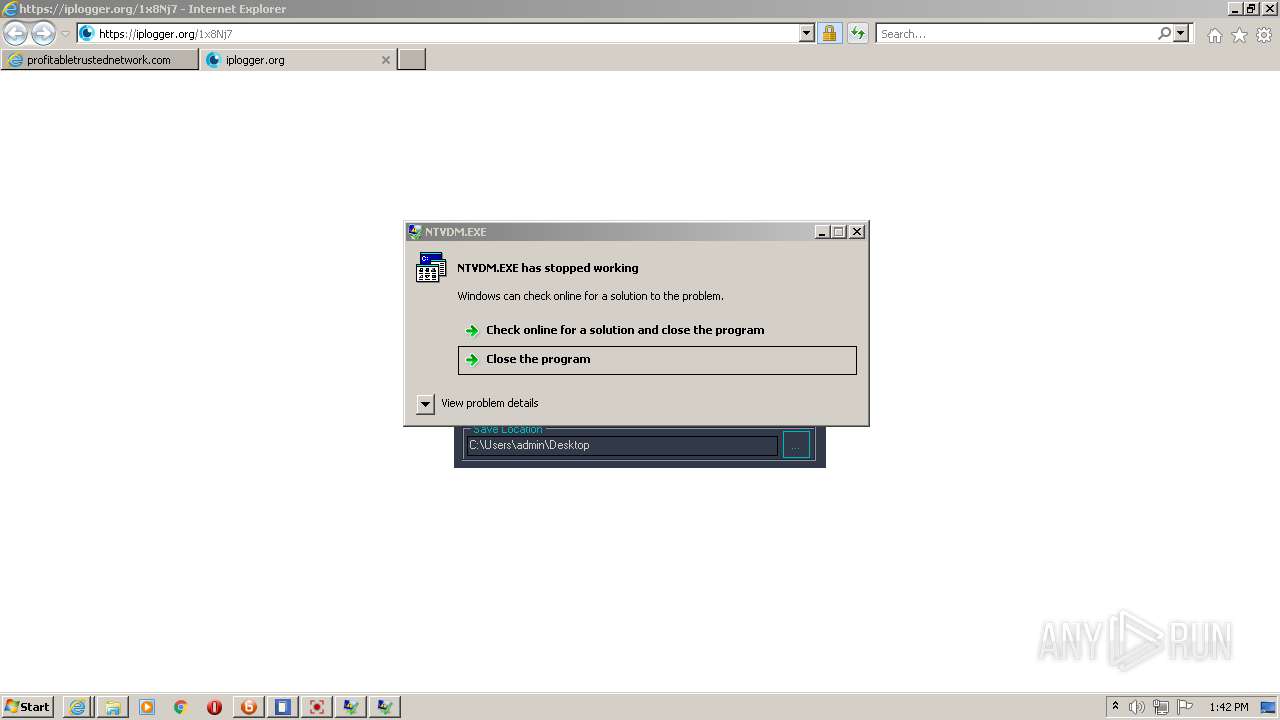
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 3380)
- 4065056.exe (PID: 3880)
- conhost.exe (PID: 3276)
- c47f7cjLMfWJJgWv3X6oDlyU.exe (PID: 2848)
- c47f7cjLMfWJJgWv3X6oDlyU.exe (PID: 2204)
- Mepasowikae.exe (PID: 4620)
- rUNdlL32.eXe (PID: 4388)
- 92dRgtcSJUitRfKmavFzP9YY.exe (PID: 4644)
- conhost.exe (PID: 3584)
- SearchProtocolHost.exe (PID: 5836)
- 5993665.exe (PID: 2324)
- vSfsmZQiwu_m83vcAzKfCP55.exe (PID: 4960)
- cmd.exe (PID: 4576)
- conhost.exe (PID: 2120)
- 87864724032.exe (PID: 1348)
- conhost.exe (PID: 6104)
- iexplore.exe (PID: 5772)
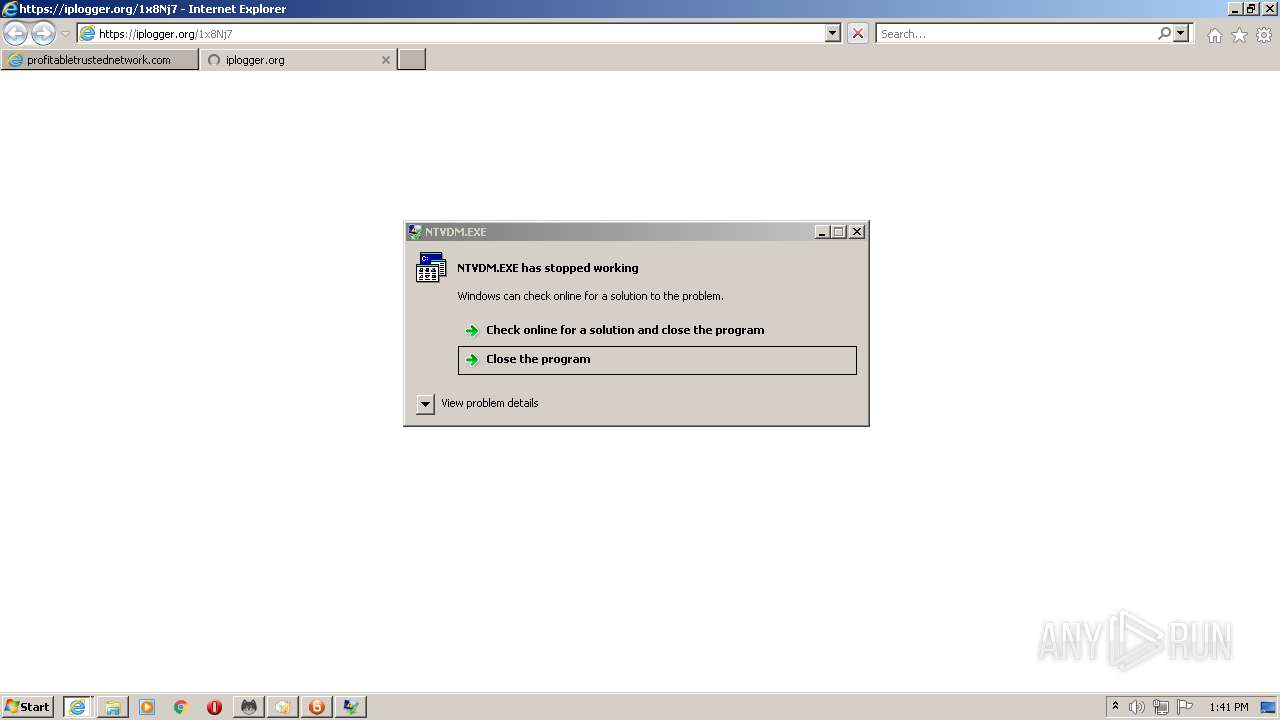
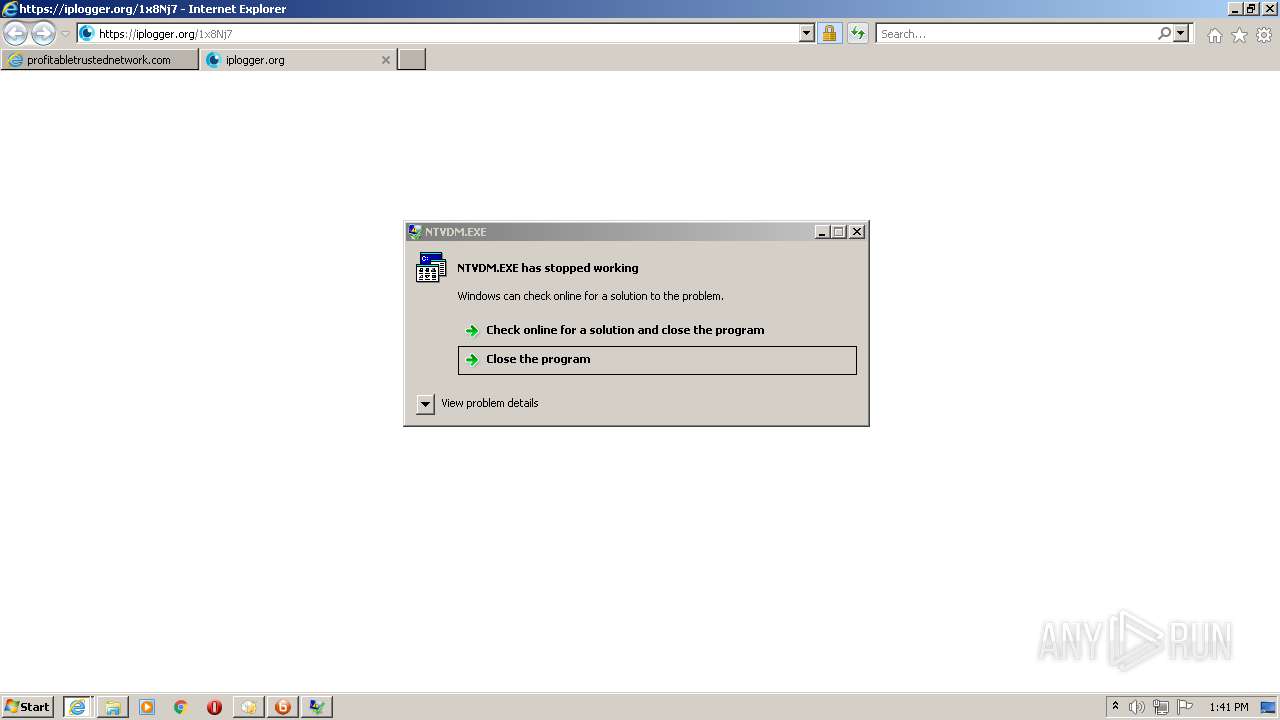
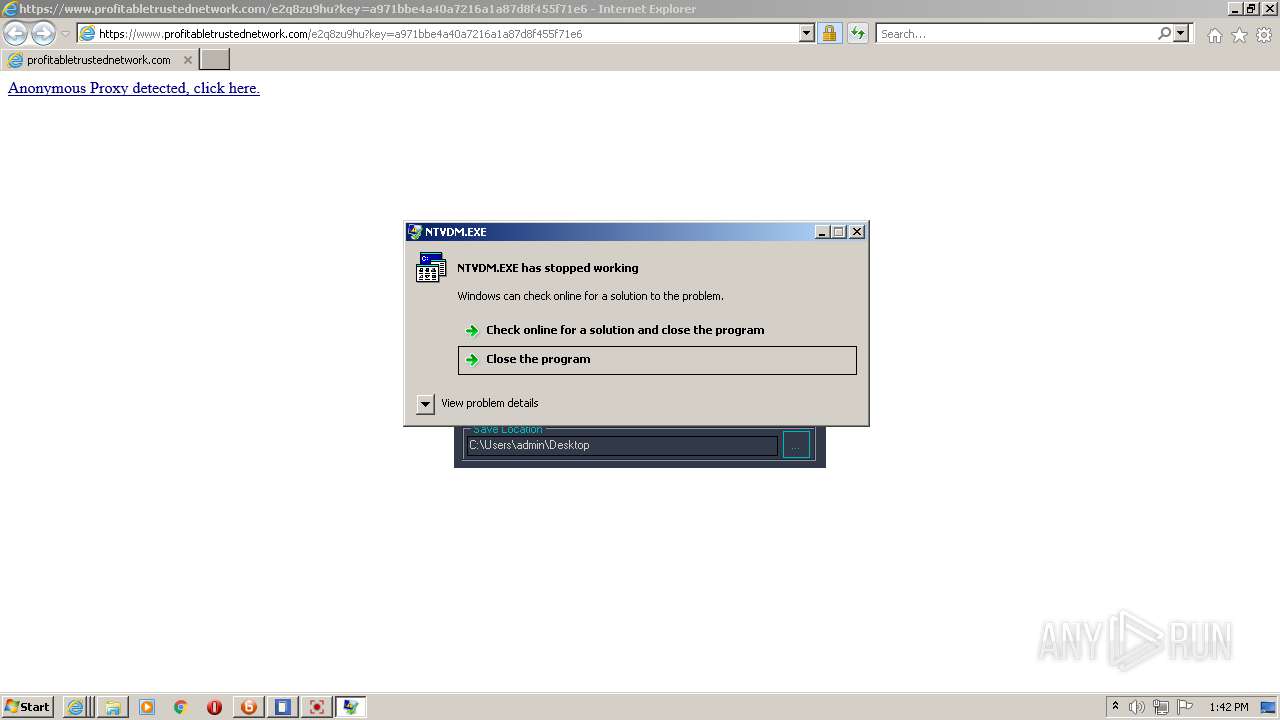
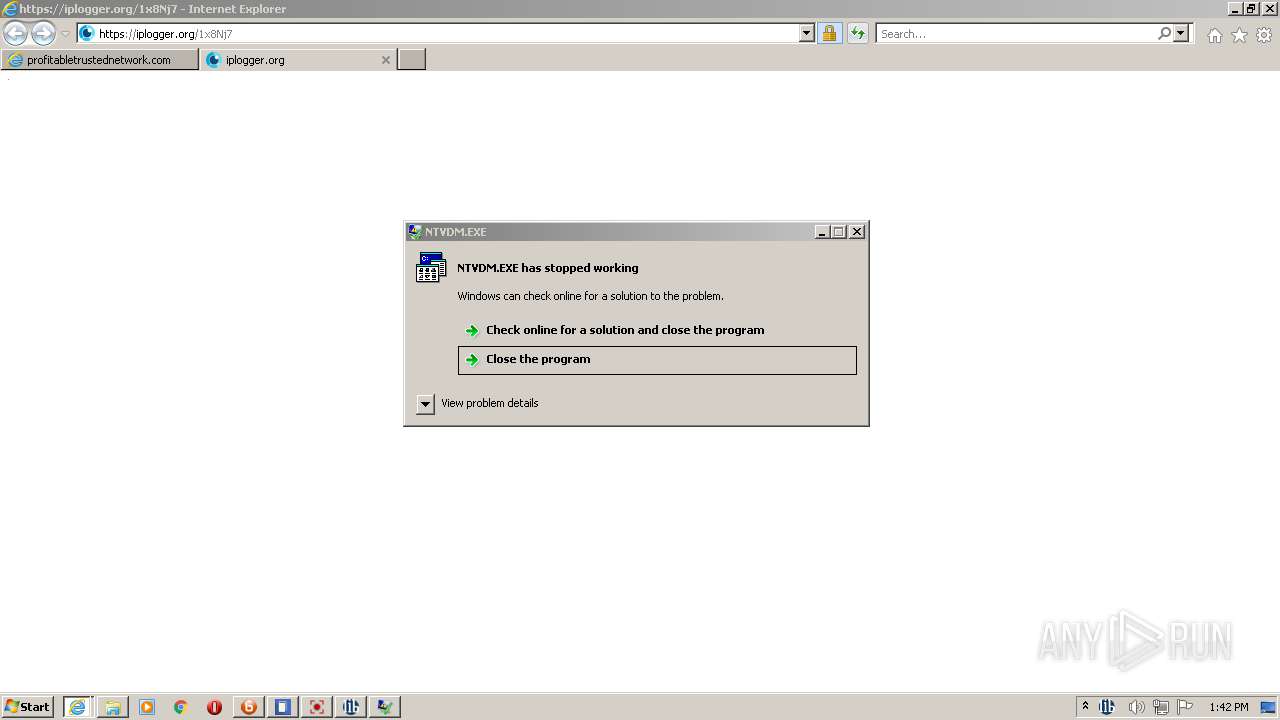
- ntvdm.exe (PID: 4212)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4456)
- cmd.exe (PID: 5992)
- WerFault.exe (PID: 4768)
- ntvdm.exe (PID: 5880)
- WerFault.exe (PID: 2756)
- DllHost.exe (PID: 756)
- conhost.exe (PID: 2488)
- cmd.exe (PID: 3460)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3292)
- MTgxHjQIwa0xNQWeg6cCDRvX.exe (PID: 5356)
- file4.exe (PID: 6124)
- jooyu.exe (PID: 5804)
- jingzhang.exe (PID: 2668)
- conhost.exe (PID: 400)
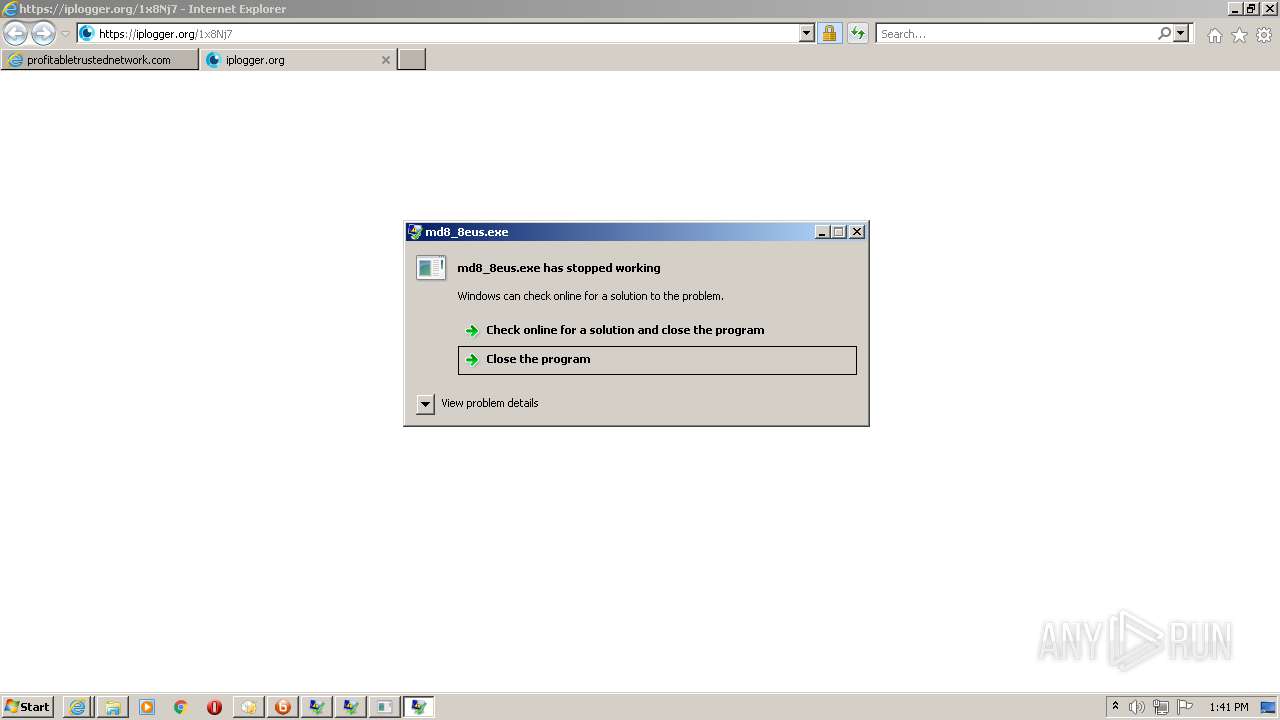
- md8_8eus.exe (PID: 4540)
- WerFault.exe (PID: 5168)
- jfiag3g_gg.exe (PID: 5460)
- conhost.exe (PID: 4124)
- cmd.exe (PID: 5932)
- rUNdlL32.eXe (PID: 4320)
- JoSetp.exe (PID: 4720)
- DllHost.exe (PID: 6012)
- uuPQOCOMexhx3yxa1N9mqtPQ.exe (PID: 1768)
- conhost.exe (PID: 1116)
- conhost.exe (PID: 4536)
- Setup3310.exe (PID: 4480)
- DK2u8J8s6Y_OKtryFL3tUKvl.exe (PID: 320)
- cmd.exe (PID: 2052)
- n1Bdoav4ePwmk39pjYjra7rp.exe (PID: 3416)
- conhost.exe (PID: 5752)
- jfiag3g_gg.exe (PID: 4940)
- uuPQOCOMexhx3yxa1N9mqtPQ.exe (PID: 4440)
- cmd.exe (PID: 4280)
- conhost.exe (PID: 2584)
- cmd.exe (PID: 2252)
- conhost.exe (PID: 2236)
- n1Bdoav4ePwmk39pjYjra7rp.exe (PID: 4304)
- taskkill.exe (PID: 5632)
- timeout.exe (PID: 3656)
- timeout.exe (PID: 4064)
- MrGh6bEH0L0a.exe (PID: 1512)
- taskkill.exe (PID: 4984)
- MrGh6bEH0L0a.exe (PID: 5460)
- _u73G1XXPC5iG3vd_ds6OnIc.exe (PID: 4580)
- conhost.exe (PID: 4764)
- cmd.exe (PID: 4760)
- google-game.exe (PID: 5020)
- google-game.exe (PID: 5572)
- conhost.exe (PID: 3492)
- MrGh6bEH0L0a.exe (PID: 4508)
- conhost.exe (PID: 3112)
- cmd.exe (PID: 4896)
- 98827784354.exe (PID: 5852)
- MrGh6bEH0L0a.exe (PID: 6028)
- rUNdlL32.eXe (PID: 3424)
- MrGh6bEH0L0a.exe (PID: 5924)
- MrGh6bEH0L0a.exe (PID: 5472)
- MrGh6bEH0L0a.exe (PID: 3588)
- conhost.exe (PID: 5140)
- cmd.exe (PID: 3188)
- askinstall46.exe (PID: 1356)
- cmd.exe (PID: 416)
- conhost.exe (PID: 5668)
- 86810264062.exe (PID: 5764)
- MrGh6bEH0L0a.exe (PID: 3088)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5104)
- 1127893.exe (PID: 2352)
- MrGh6bEH0L0a.exe (PID: 5060)
- conhost.exe (PID: 4016)
- cmd.exe (PID: 1212)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5940)
- taskkill.exe (PID: 1140)
- MrGh6bEH0L0a.exe (PID: 5996)
- MrGh6bEH0L0a.exe (PID: 5112)
- 4783549.exe (PID: 1812)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5560)
- MrGh6bEH0L0a.exe (PID: 3616)
- 3754144.exe (PID: 6048)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5832)
- WerFault.exe (PID: 3656)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5720)
- MrGh6bEH0L0a.exe (PID: 5356)
- 7296437.exe (PID: 3952)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4216)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4544)
- VJvJmRSXUxWEsi.exe (PID: 3424)
- 4.exe (PID: 4964)
- vpn.exe (PID: 2324)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 356)
- MrGh6bEH0L0a.exe (PID: 3484)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2812)
- MrGh6bEH0L0a.exe (PID: 5880)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5776)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4968)
- 6o7inj8hsSfNINZjJNZQpADc.exe (PID: 1760)
- SearchFilterHost.exe (PID: 2216)
- MrGh6bEH0L0a.exe (PID: 5492)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5564)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3280)
- conhost.exe (PID: 5644)
- cmd.exe (PID: 1032)
- taskkill.exe (PID: 5800)
- edspolishpp.exe (PID: 4568)
- MrGh6bEH0L0a.exe (PID: 5660)
- timeout.exe (PID: 5080)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2092)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4848)
- MrGh6bEH0L0a.exe (PID: 2600)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 1580)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2316)
- MrGh6bEH0L0a.exe (PID: 4788)
- cmd.exe (PID: 5440)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5992)
- conhost.exe (PID: 2616)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4420)
- app.exe (PID: 4740)
- MrGh6bEH0L0a.exe (PID: 3348)
- MrGh6bEH0L0a.exe (PID: 4476)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4148)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3332)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4880)
- ns7CAD.tmp (PID: 5604)
- conhost.exe (PID: 4632)
- SmartClock.exe (PID: 5136)
- powershell.exe (PID: 696)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5680)
- MrGh6bEH0L0a.exe (PID: 2420)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5072)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 668)
- tpobqkuunp.exe (PID: 2236)
- conhost.exe (PID: 4676)
- cmd.exe (PID: 4884)
- note8876.exe (PID: 4860)
- WScript.exe (PID: 6084)
- WerFault.exe (PID: 3932)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4152)
- MrGh6bEH0L0a.exe (PID: 4396)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 908)
- NMemo3Setp.exe (PID: 3924)
- guihuali-game.exe (PID: 3940)
- lylal220.exe (PID: 3820)
- hjjgaa.exe (PID: 1260)
- LabPicV3.exe (PID: 968)
- RunWW.exe (PID: 6100)
- conhost.exe (PID: 5144)
- MrGh6bEH0L0a.exe (PID: 4936)
- app.exe (PID: 2884)
- DllHost.exe (PID: 464)
- MediaBurner.exe (PID: 3376)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3660)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5096)
- guihuali-game.exe (PID: 4540)
- conhost.exe (PID: 5224)
- MrGh6bEH0L0a.exe (PID: 4776)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2456)
- MrGh6bEH0L0a.exe (PID: 2540)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4576)
- ns8F3C.tmp (PID: 756)
- conhost.exe (PID: 5132)
- lighteningplayer-cache-gen.exe (PID: 5464)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5488)
- rUNdlL32.eXe (PID: 3864)
- jfiag3g_gg.exe (PID: 4696)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5884)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4720)
- MrGh6bEH0L0a.exe (PID: 4840)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3756)
- fa041e8b.exe (PID: 5876)
- cmd.exe (PID: 6020)
- conhost.exe (PID: 5768)
- DllHost.exe (PID: 2984)
- MrGh6bEH0L0a.exe (PID: 4636)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3304)
- MrGh6bEH0L0a.exe (PID: 2220)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4808)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3540)
- cmd.exe (PID: 1944)
- conhost.exe (PID: 4696)
- rundll32.exe (PID: 2796)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4404)
- ntvdm.exe (PID: 5892)
- WerFault.exe (PID: 4224)
- MrGh6bEH0L0a.exe (PID: 1496)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5188)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2856)
- 6966994.exe (PID: 2256)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 1336)
- MrGh6bEH0L0a.exe (PID: 4956)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 860)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4228)
- 3346707.exe (PID: 3608)
- MrGh6bEH0L0a.exe (PID: 5508)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5904)
- jfiag3g_gg.exe (PID: 3656)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2584)
- MrGh6bEH0L0a.exe (PID: 5676)
- UcSb7jo9o_iViBtNSe78kPEu.exe (PID: 3576)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5712)
- conhost.exe (PID: 5592)
- cmd.exe (PID: 5604)
- taskkill.exe (PID: 1356)
- WerFault.exe (PID: 4204)
- timeout.exe (PID: 3668)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4608)
- MrGh6bEH0L0a.exe (PID: 5584)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 1212)
- ultramediaburner.exe (PID: 4736)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5708)
- LogonUI.exe (PID: 6084)
- UltraMediaBurner.exe (PID: 4176)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 1476)
- MrGh6bEH0L0a.exe (PID: 2296)
- MrGh6bEH0L0a.exe (PID: 1268)
- 7534436.exe (PID: 2388)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5496)
- prolab.exe (PID: 4996)
- Qaejelaefomae.exe (PID: 5012)
- Vareshedema.exe (PID: 468)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4892)
- MrGh6bEH0L0a.exe (PID: 6100)
- Paducaehaexy.exe (PID: 1880)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5732)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2620)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6040)
- MrGh6bEH0L0a.exe (PID: 5752)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5768)
- Nucaedimele.exe (PID: 4640)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2788)
- MrGh6bEH0L0a.exe (PID: 4176)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6136)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 1476)
- WScript.exe (PID: 3084)
- MrGh6bEH0L0a.exe (PID: 6032)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3520)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5304)
- MrGh6bEH0L0a.exe (PID: 2064)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5932)
- MrGh6bEH0L0a.exe (PID: 2544)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4280)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2744)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4860)
- MrGh6bEH0L0a.exe (PID: 5896)
- irecord.exe (PID: 1356)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5988)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 756)
- MrGh6bEH0L0a.exe (PID: 5968)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5012)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4648)
- I-Record.exe (PID: 5260)
- MrGh6bEH0L0a.exe (PID: 4428)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5628)
- Maebumyzhymu.exe (PID: 4328)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4352)
- Qashevishudy.exe (PID: 3084)
- MrGh6bEH0L0a.exe (PID: 3376)
- conhost.exe (PID: 536)
- cmd.exe (PID: 2344)
- SunLabsPlayer.exe (PID: 1172)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 1348)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 364)
- MrGh6bEH0L0a.exe (PID: 4988)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4652)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5080)
- conhost.exe (PID: 4388)
- cmd.exe (PID: 2156)
- toolspab1.exe (PID: 3252)
- iexplore.exe (PID: 5504)
- iexplore.exe (PID: 4640)
- MrGh6bEH0L0a.exe (PID: 1944)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5036)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4572)
- MrGh6bEH0L0a.exe (PID: 3960)
- nsEF8B.tmp (PID: 5512)
- conhost.exe (PID: 4944)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4752)
- cmd.exe (PID: 6436)
- MrGh6bEH0L0a.exe (PID: 4440)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5124)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3268)
- MrGh6bEH0L0a.exe (PID: 5420)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 748)
- powershell.exe (PID: 4068)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2028)
- conhost.exe (PID: 6500)
- conhost.exe (PID: 7728)
- ntvdm.exe (PID: 6688)
- WerFault.exe (PID: 7020)
- nsF876.tmp (PID: 7044)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8264)
- toolspab1.exe (PID: 7704)
- MrGh6bEH0L0a.exe (PID: 8700)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9132)
- lighteningplayer-cache-gen.exe (PID: 6764)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6160)
- MrGh6bEH0L0a.exe (PID: 7448)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6368)
- conhost.exe (PID: 6492)
- ntvdm.exe (PID: 7012)
- WerFault.exe (PID: 7116)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7428)
- MrGh6bEH0L0a.exe (PID: 8072)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3704)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9304)
- MrGh6bEH0L0a.exe (PID: 9492)
- cmd.exe (PID: 6408)
- Setup3310.exe (PID: 5292)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7724)
- MrGh6bEH0L0a.exe (PID: 8044)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 10124)
- cmd.exe (PID: 1448)
- conhost.exe (PID: 4208)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2192)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8204)
- MrGh6bEH0L0a.exe (PID: 8552)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8632)
- cmd.exe (PID: 8312)
- conhost.exe (PID: 8388)
- libravpn_setup.exe (PID: 7324)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9756)
- MrGh6bEH0L0a.exe (PID: 10000)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 10224)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7720)
- MrGh6bEH0L0a.exe (PID: 7844)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7856)
- LibraVPN.exe (PID: 4784)
- conhost.exe (PID: 6192)
- cmd.exe (PID: 4384)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3316)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 1376)
- MrGh6bEH0L0a.exe (PID: 3124)
- cmd.exe (PID: 4272)
- netsh.exe (PID: 6852)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2792)
- chcp.com (PID: 6996)
- conhost.exe (PID: 7700)
- MrGh6bEH0L0a.exe (PID: 6264)
- cmd.exe (PID: 8976)
- google-game.exe (PID: 9420)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2388)
- cmd.exe (PID: 10056)
- google-game.exe (PID: 10104)
- conhost.exe (PID: 10176)
- chcp.com (PID: 7384)
- conhost.exe (PID: 10148)
- netsh.exe (PID: 7204)
- rUNdlL32.eXe (PID: 7180)
- cmd.exe (PID: 9976)
- chcp.com (PID: 5740)
- cmd.exe (PID: 5480)
- conhost.exe (PID: 3240)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9124)
- cmd.exe (PID: 4700)
- netsh.exe (PID: 5308)
- MrGh6bEH0L0a.exe (PID: 9272)
- cmd.exe (PID: 6024)
- chcp.com (PID: 5512)
- conhost.exe (PID: 6392)
- cmd.exe (PID: 2736)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9404)
- cmd.exe (PID: 8448)
- conhost.exe (PID: 8400)
- chcp.com (PID: 8424)
- cmd.exe (PID: 8520)
- netsh.exe (PID: 5956)
- conhost.exe (PID: 9364)
- cmd.exe (PID: 9184)
- chcp.com (PID: 9536)
- cmd.exe (PID: 9328)
- netsh.exe (PID: 9704)
- netsh.exe (PID: 6412)
- conhost.exe (PID: 7520)
- cmd.exe (PID: 7416)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5716)
- chcp.com (PID: 8752)
- cmd.exe (PID: 9796)
- netsh.exe (PID: 10040)
- conhost.exe (PID: 8028)
- MrGh6bEH0L0a.exe (PID: 4856)
- cmd.exe (PID: 7976)
- chcp.com (PID: 4844)
- cmd.exe (PID: 3464)
- ipconfig.exe (PID: 4536)
- conhost.exe (PID: 2784)
- taskkill.exe (PID: 276)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8336)
- cmd.exe (PID: 6228)
- conhost.exe (PID: 4952)
- ntvdm.exe (PID: 6804)
- cmd.exe (PID: 3580)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7644)
- WerFault.exe (PID: 8196)
- DllHost.exe (PID: 6960)
- MrGh6bEH0L0a.exe (PID: 7896)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5296)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8588)
- MrGh6bEH0L0a.exe (PID: 9000)
- MrGh6bEH0L0a.exe (PID: 9892)
- cmd.exe (PID: 10156)
- conhost.exe (PID: 10104)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7252)
- app.exe (PID: 7784)
- cmd.exe (PID: 4168)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7144)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7024)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9640)
- conhost.exe (PID: 7160)
- cmd.exe (PID: 7716)
- cmd.exe (PID: 5480)
- MrGh6bEH0L0a.exe (PID: 9768)
- conhost.exe (PID: 6576)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7892)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2432)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6492)
- MrGh6bEH0L0a.exe (PID: 2588)
- conhost.exe (PID: 4340)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6808)
- MrGh6bEH0L0a.exe (PID: 9164)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9624)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 10108)
- MrGh6bEH0L0a.exe (PID: 7372)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5412)
- MrGh6bEH0L0a.exe (PID: 8404)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8788)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9036)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7660)
- MrGh6bEH0L0a.exe (PID: 7948)
- conhost.exe (PID: 4484)
- cmd.exe (PID: 3320)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5740)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3784)
- MrGh6bEH0L0a.exe (PID: 7012)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8992)
- MrGh6bEH0L0a.exe (PID: 9244)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9012)
- conhost.exe (PID: 8820)
- cmd.exe (PID: 5936)
- SunLabsPlayer.exe (PID: 7596)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6232)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8488)
- MrGh6bEH0L0a.exe (PID: 6772)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8912)
- MrGh6bEH0L0a.exe (PID: 9648)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9724)
- conhost.exe (PID: 6248)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 336)
- cmd.exe (PID: 4928)
- MrGh6bEH0L0a.exe (PID: 5168)
- ns5F4D.tmp (PID: 6316)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4996)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5952)
- conhost.exe (PID: 8740)
- MrGh6bEH0L0a.exe (PID: 6980)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5480)
- powershell.exe (PID: 6912)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6304)
- conhost.exe (PID: 7220)
- cmd.exe (PID: 8324)
- ns6662.tmp (PID: 8060)
- MrGh6bEH0L0a.exe (PID: 9156)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9424)
- conhost.exe (PID: 7900)
- lighteningplayer-cache-gen.exe (PID: 4232)
- MrGh6bEH0L0a.exe (PID: 7240)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7696)
- toolspab1.exe (PID: 7608)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8784)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8056)
- MrGh6bEH0L0a.exe (PID: 7092)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3956)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9428)
- conhost.exe (PID: 7472)
- cmd.exe (PID: 7360)
- MrGh6bEH0L0a.exe (PID: 9864)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2240)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7412)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7832)
- MrGh6bEH0L0a.exe (PID: 7196)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7172)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9924)
- MrGh6bEH0L0a.exe (PID: 7984)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5140)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6156)
- toolspab1.exe (PID: 5424)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2836)
- MrGh6bEH0L0a.exe (PID: 3248)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3768)
- conhost.exe (PID: 8444)
- cmd.exe (PID: 6424)
- MrGh6bEH0L0a.exe (PID: 6592)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6888)
- MrGh6bEH0L0a.exe (PID: 3128)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8156)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6236)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6204)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6428)
- MrGh6bEH0L0a.exe (PID: 6148)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6580)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9536)
- MrGh6bEH0L0a.exe (PID: 9764)
- conhost.exe (PID: 9788)
- cmd.exe (PID: 7616)
- MrGh6bEH0L0a.exe (PID: 6748)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9104)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9972)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8288)
- MrGh6bEH0L0a.exe (PID: 7476)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7148)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8284)
- cmd.exe (PID: 9992)
- conhost.exe (PID: 9976)
- MrGh6bEH0L0a.exe (PID: 7680)
- chcp.com (PID: 3388)
- MrGh6bEH0L0a.exe (PID: 6004)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4536)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6456)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4224)
- MrGh6bEH0L0a.exe (PID: 8132)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2712)
- MrGh6bEH0L0a.exe (PID: 6984)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6604)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7920)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 1448)
- MrGh6bEH0L0a.exe (PID: 10236)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9064)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9260)
- cmd.exe (PID: 9600)
- MrGh6bEH0L0a.exe (PID: 8940)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9284)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9488)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6744)
- MrGh6bEH0L0a.exe (PID: 8524)
- conhost.exe (PID: 9672)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7292)
- MrGh6bEH0L0a.exe (PID: 7048)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3668)
- MrGh6bEH0L0a.exe (PID: 8664)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7320)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7748)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7912)
- MrGh6bEH0L0a.exe (PID: 9108)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4000)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8004)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9692)
- MrGh6bEH0L0a.exe (PID: 6344)
- MrGh6bEH0L0a.exe (PID: 6120)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4424)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 428)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6956)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5128)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 1764)
- MrGh6bEH0L0a.exe (PID: 7008)
- cmd.exe (PID: 4944)
- conhost.exe (PID: 6124)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8856)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8400)
- MrGh6bEH0L0a.exe (PID: 9388)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8060)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9516)
- conhost.exe (PID: 7728)
- cmd.exe (PID: 8980)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6844)
- MrGh6bEH0L0a.exe (PID: 8832)
- MrGh6bEH0L0a.exe (PID: 4992)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9040)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7132)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9088)
- MrGh6bEH0L0a.exe (PID: 9760)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4036)
- MrGh6bEH0L0a.exe (PID: 7872)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6212)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 852)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5208)
- MrGh6bEH0L0a.exe (PID: 6900)
- conhost.exe (PID: 7032)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 2036)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5464)
- MrGh6bEH0L0a.exe (PID: 5392)
- MrGh6bEH0L0a.exe (PID: 7716)
- cmd.exe (PID: 6184)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 5604)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6796)
- iexplore.exe (PID: 8816)
- DllHost.exe (PID: 9740)
- MrGh6bEH0L0a.exe (PID: 8512)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8708)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8956)
- MrGh6bEH0L0a.exe (PID: 6280)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6800)
- MrGh6bEH0L0a.exe (PID: 9712)
- MrGh6bEH0L0a.exe (PID: 10188)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 10148)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6116)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 10220)
- cmd.exe (PID: 5232)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9232)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7580)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7628)
- conhost.exe (PID: 2392)
- MrGh6bEH0L0a.exe (PID: 868)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 2436)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4548)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6392)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6968)
- MrGh6bEH0L0a.exe (PID: 4500)
- MrGh6bEH0L0a.exe (PID: 368)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4800)
- chcp.com (PID: 9748)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9100)
- MrGh6bEH0L0a.exe (PID: 8996)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4368)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7032)
- MrGh6bEH0L0a.exe (PID: 9024)
- conhost.exe (PID: 8800)
- cmd.exe (PID: 6436)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8824)
- MrGh6bEH0L0a.exe (PID: 8904)
- conhost.exe (PID: 7364)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7532)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6172)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7592)
- MrGh6bEH0L0a.exe (PID: 7384)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6088)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8260)
- cmd.exe (PID: 8728)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3700)
- MrGh6bEH0L0a.exe (PID: 6652)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6396)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 1412)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3080)
- MrGh6bEH0L0a.exe (PID: 1168)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7068)
- cmd.exe (PID: 6556)
- conhost.exe (PID: 8844)
- MrGh6bEH0L0a.exe (PID: 4172)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 1140)
- MrGh6bEH0L0a.exe (PID: 9552)
- MrGh6bEH0L0a.exe (PID: 9772)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6872)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9600)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7700)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7472)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 10156)
- MrGh6bEH0L0a.exe (PID: 6184)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9292)
- conhost.exe (PID: 2884)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6020)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 1164)
- SearchProtocolHost.exe (PID: 6432)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3584)
- cmd.exe (PID: 8656)
- MrGh6bEH0L0a.exe (PID: 9312)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 7800)
- MrGh6bEH0L0a.exe (PID: 4208)
- MrGh6bEH0L0a.exe (PID: 8988)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8420)
- MrGh6bEH0L0a.exe (PID: 9636)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8620)
- MrGh6bEH0L0a.exe (PID: 2360)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6628)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6684)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9256)
- MrGh6bEH0L0a.exe (PID: 8144)
- cmd.exe (PID: 6188)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5008)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6584)
- conhost.exe (PID: 8576)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8232)
- MrGh6bEH0L0a.exe (PID: 7560)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3404)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 9076)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 8928)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6168)
- MrGh6bEH0L0a.exe (PID: 8800)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 9484)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 7400)
- MrGh6bEH0L0a.exe (PID: 4944)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 6892)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 4952)
- MrGh6bEH0L0a.exe (PID: 6252)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 8172)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4708)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 6300)
- conhost.exe (PID: 8828)
- cmd.exe (PID: 6896)
- MrGh6bEH0L0a.exe (PID: 7364)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 3648)
- MrGh6bEH0L0a.exe (PID: 7964)
- MrGh6bEH0L0a.exe (PID: 6552)
Changes settings of System certificates
- sahiba_7.exe (PID: 3080)
- sahiba_3.exe (PID: 2636)
Connects to CnC server
- setup_install.exe (PID: 3368)
- sahiba_4.exe (PID: 2124)
- jooyu.exe (PID: 5804)
- KNF426i_LnuvRjCRn67btkSt.exe (PID: 2348)
- hjjgaa.exe (PID: 1260)
Disables Windows Defender
- sahiba_7.exe (PID: 3080)
Changes the autorun value in the registry
- 8565390.exe (PID: 3180)
- JFHGSFGSIUGFSUIG.exe (PID: 1812)
- _____________bob.exe (PID: 308)
- 12(((((.exe (PID: 6072)
- �e�rgegd�_���_)))_.exe (PID: 2372)
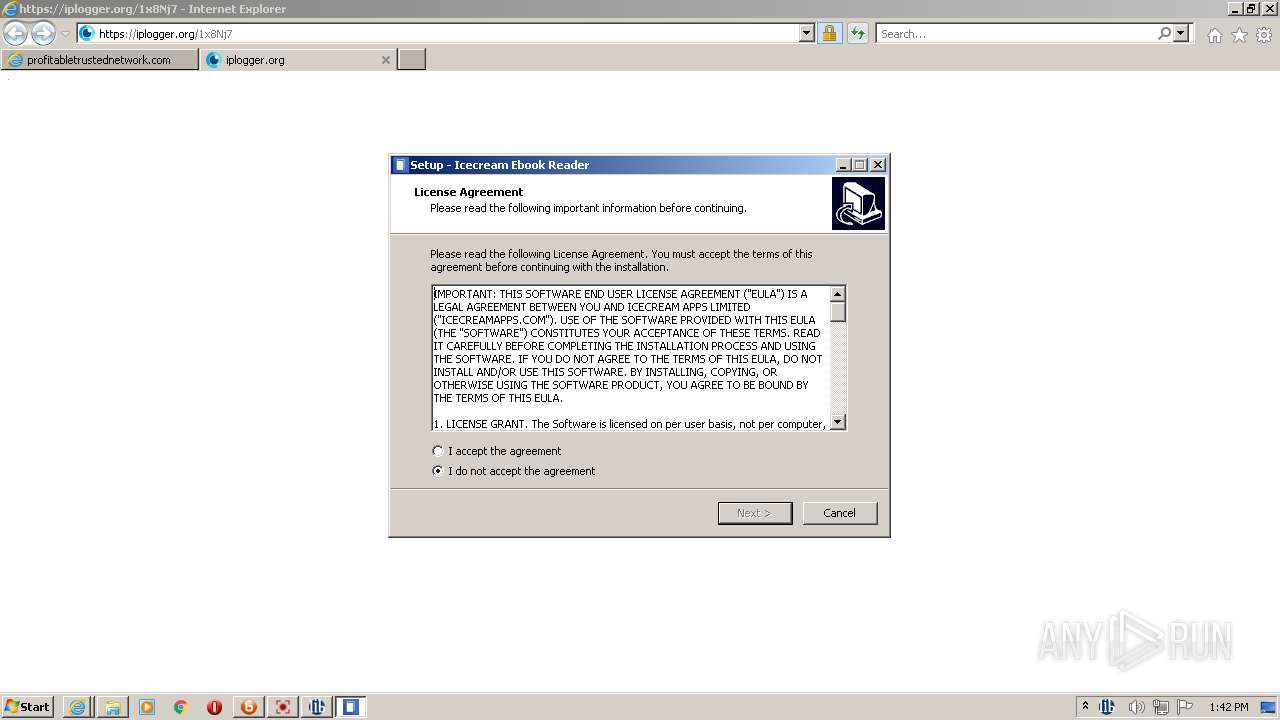
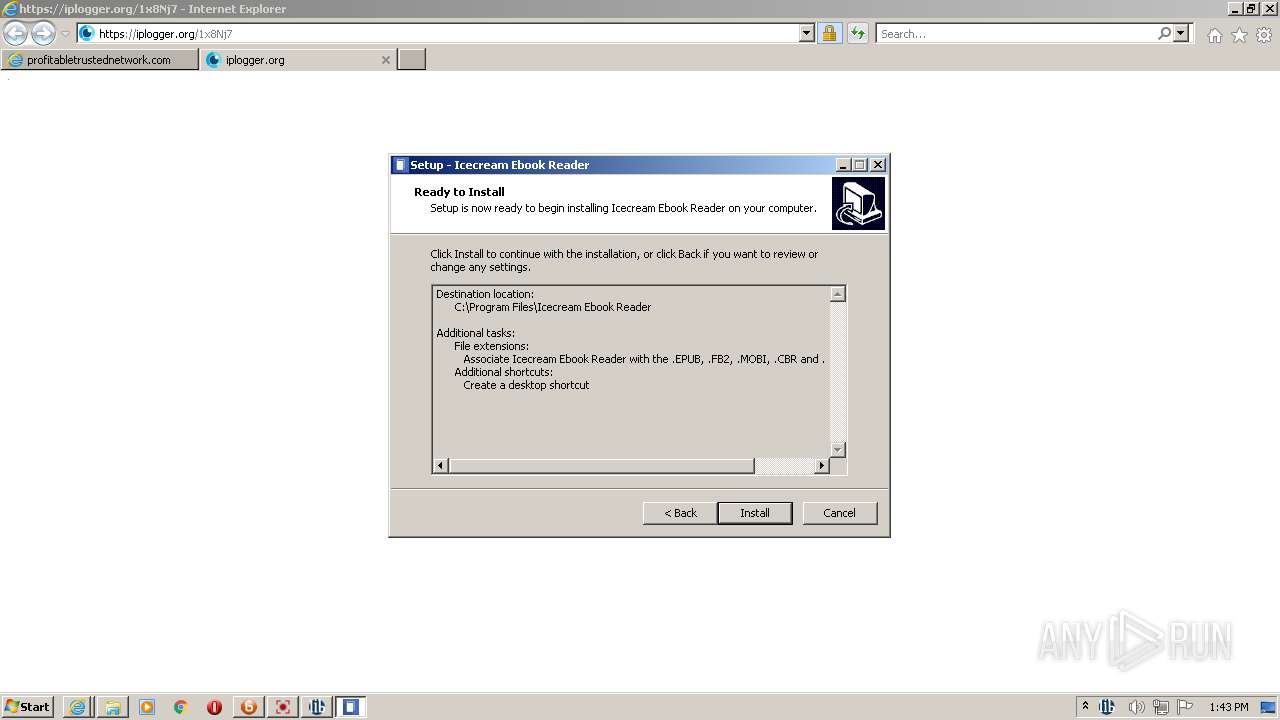
Unusual execution from Microsoft Office
- ultramediaburner.exe (PID: 3852)
Stealing of credential data
- svchost.exe (PID: 3360)
- TCDUdNYbyNRCuYogsbUP5uDx.exe (PID: 1768)
- qgRieigRJBBcVN4NkeX6SlpC.exe (PID: 1124)
- CL2GGLruMiQhagp54ShuBydy.exe (PID: 3256)
- sahiba_9.exe (PID: 2284)
- 7536611.exe (PID: 320)
- sahiba_8.exe (PID: 4020)
- 6332060.exe (PID: 2316)
- sahiba_3.exe (PID: 2636)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- 4613966.exe (PID: 3344)
- 5075929.exe (PID: 3932)
- edspolishpp.exe (PID: 4568)
Actions looks like stealing of personal data
- svchost.exe (PID: 3360)
- sahiba_9.exe (PID: 2284)
- CL2GGLruMiQhagp54ShuBydy.exe (PID: 3256)
- TCDUdNYbyNRCuYogsbUP5uDx.exe (PID: 1768)
- qgRieigRJBBcVN4NkeX6SlpC.exe (PID: 1124)
- 7536611.exe (PID: 320)
- 92dRgtcSJUitRfKmavFzP9YY.exe (PID: 4644)
- sahiba_8.exe (PID: 4020)
- 5993665.exe (PID: 2324)
- 6332060.exe (PID: 2316)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- sahiba_3.exe (PID: 2636)
- vSfsmZQiwu_m83vcAzKfCP55.exe (PID: 4960)
- 87864724032.exe (PID: 1348)
- 4613966.exe (PID: 3344)
- 5075929.exe (PID: 3932)
- uuPQOCOMexhx3yxa1N9mqtPQ.exe (PID: 4440)
- n1Bdoav4ePwmk39pjYjra7rp.exe (PID: 4304)
- 98827784354.exe (PID: 5852)
- 1127893.exe (PID: 2352)
- Setup3310.tmp (PID: 4700)
- RunWW.exe (PID: 6100)
- 7296437.exe (PID: 3952)
- 4783549.exe (PID: 1812)
- 6966994.exe (PID: 2256)
- Setup3310.tmp (PID: 6212)
- edspolishpp.exe (PID: 4568)
Steals credentials from Web Browsers
- svchost.exe (PID: 3360)
- 6332060.exe (PID: 2316)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- sahiba_3.exe (PID: 2636)
- 4613966.exe (PID: 3344)
- 5075929.exe (PID: 3932)
- 98827784354.exe (PID: 5852)
- 1127893.exe (PID: 2352)
- RunWW.exe (PID: 6100)
- 4783549.exe (PID: 1812)
- 6966994.exe (PID: 2256)
VIDAR was detected
- sahiba_3.exe (PID: 2636)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- 1127893.exe (PID: 2352)
- RunWW.exe (PID: 6100)
REDLINE was detected
- sahiba_9.exe (PID: 2284)
- qgRieigRJBBcVN4NkeX6SlpC.exe (PID: 1124)
- 7536611.exe (PID: 320)
- sahiba_8.exe (PID: 4020)
- CL2GGLruMiQhagp54ShuBydy.exe (PID: 3256)
- TCDUdNYbyNRCuYogsbUP5uDx.exe (PID: 1768)
- 92dRgtcSJUitRfKmavFzP9YY.exe (PID: 4644)
- 5993665.exe (PID: 2324)
- vSfsmZQiwu_m83vcAzKfCP55.exe (PID: 4960)
- 87864724032.exe (PID: 1348)
- uuPQOCOMexhx3yxa1N9mqtPQ.exe (PID: 4440)
- n1Bdoav4ePwmk39pjYjra7rp.exe (PID: 4304)
- DK2u8J8s6Y_OKtryFL3tUKvl.exe (PID: 320)
- 7296437.exe (PID: 3952)
- edspolishpp.exe (PID: 4568)
Writes to a start menu file
- 4.exe (PID: 4964)
Loads the Task Scheduler COM API
- 4.exe (PID: 4964)
DANABOT was detected
- rundll32.exe (PID: 2796)
SUSPICIOUS
Reads the computer name
- wmiprvse.exe (PID: 2708)
- WinRAR.exe (PID: 2108)
- WinRAR.exe (PID: 520)
- main_setup_x86x64.exe (PID: 2840)
- setup_installer.exe (PID: 400)
- setup_install.exe (PID: 3368)
- sahiba_4.exe (PID: 2124)
- sahiba_7.exe (PID: 3080)
- sahiba_10.exe (PID: 3700)
- sahiba_9.exe (PID: 3904)
- sahiba_1.exe (PID: 3304)
- sahiba_6.exe (PID: 3680)
- sahiba_1.exe (PID: 3668)
- sahiba_5.tmp (PID: 496)
- jfiag3g_gg.exe (PID: 660)
- JFHGSFGSIUGFSUIG.exe (PID: 1812)
- sahiba_9.exe (PID: 2284)
- 5075929.exe (PID: 3932)
- 6332060.exe (PID: 2316)
- 8565390.exe (PID: 3180)
- sahiba_8.exe (PID: 4020)
- sahiba_3.exe (PID: 2636)
- TCDUdNYbyNRCuYogsbUP5uDx.exe (PID: 1764)
- WinHoster.exe (PID: 3488)
- qgRieigRJBBcVN4NkeX6SlpC.exe (PID: 1124)
- 7536611.exe (PID: 320)
- CL2GGLruMiQhagp54ShuBydy.exe (PID: 3256)
- KNF426i_LnuvRjCRn67btkSt.exe (PID: 2348)
- TCDUdNYbyNRCuYogsbUP5uDx.exe (PID: 1768)
- 4613966.exe (PID: 3344)
- ultramediaburner.tmp (PID: 3396)
- UltraMediaBurner.exe (PID: 3824)
- Vaxaefytaeli.exe (PID: 2764)
- dsEIW6jGafchr6yo61uOgvMx.exe (PID: 3696)
- MrGh6bEH0L0a.exe (PID: 1304)
- Browzar.exe (PID: 3056)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- 4065056.exe (PID: 3880)
- c47f7cjLMfWJJgWv3X6oDlyU.exe (PID: 2848)
- c47f7cjLMfWJJgWv3X6oDlyU.exe (PID: 2204)
- Mepasowikae.exe (PID: 4620)
- 92dRgtcSJUitRfKmavFzP9YY.exe (PID: 4644)
- 5993665.exe (PID: 2324)
- vSfsmZQiwu_m83vcAzKfCP55.exe (PID: 4960)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4456)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3292)
- 87864724032.exe (PID: 1348)
- MTgxHjQIwa0xNQWeg6cCDRvX.exe (PID: 5356)
- jooyu.exe (PID: 5804)
- jingzhang.exe (PID: 2668)
- jfiag3g_gg.exe (PID: 5460)
- JoSetp.exe (PID: 4720)
- uuPQOCOMexhx3yxa1N9mqtPQ.exe (PID: 1768)
- Setup3310.tmp (PID: 4700)
- n1Bdoav4ePwmk39pjYjra7rp.exe (PID: 3416)
- uuPQOCOMexhx3yxa1N9mqtPQ.exe (PID: 4440)
- DK2u8J8s6Y_OKtryFL3tUKvl.exe (PID: 320)
- n1Bdoav4ePwmk39pjYjra7rp.exe (PID: 4304)
- google-game.exe (PID: 5020)
- google-game.exe (PID: 5572)
- _u73G1XXPC5iG3vd_ds6OnIc.exe (PID: 4580)
- 98827784354.exe (PID: 5852)
- askinstall46.exe (PID: 1356)
- 1127893.exe (PID: 2352)
- 4783549.exe (PID: 1812)
- 3754144.exe (PID: 6048)
- 7296437.exe (PID: 3952)
- VJvJmRSXUxWEsi.exe (PID: 3424)
- 86810264062.exe (PID: 5764)
- 6o7inj8hsSfNINZjJNZQpADc.exe (PID: 1760)
- edspolishpp.exe (PID: 4568)
- vpn.exe (PID: 2324)
- 4.exe (PID: 4964)
- powershell.exe (PID: 696)
- Setup.exe (PID: 2636)
- WScript.exe (PID: 6084)
- NMemo3Setp.exe (PID: 3924)
- LabPicV3.tmp (PID: 5152)
- lylal220.tmp (PID: 4752)
- guihuali-game.exe (PID: 3940)
- hjjgaa.exe (PID: 1260)
- guihuali-game.exe (PID: 4540)
- MediaBurner.tmp (PID: 5700)
- RunWW.exe (PID: 6100)
- jfiag3g_gg.exe (PID: 4696)
- app.exe (PID: 4740)
- 12(((((.exe (PID: 6072)
- �e�rgegd�_���_)))_.exe (PID: 2372)
- _____________bob.exe (PID: 308)
- 6966994.exe (PID: 2256)
- app.exe (PID: 2884)
- 3346707.exe (PID: 3608)
- ultramediaburner.tmp (PID: 4056)
- ultramediaburner.exe (PID: 3852)
- irecord.tmp (PID: 5812)
- I-Record.exe (PID: 5260)
- Maebumyzhymu.exe (PID: 4328)
- Qashevishudy.exe (PID: 3084)
- SunLabsPlayer.exe (PID: 1172)
- powershell.exe (PID: 4068)
- Setup3310.tmp (PID: 6212)
- LibraVPN.exe (PID: 4784)
- google-game.exe (PID: 9420)
- google-game.exe (PID: 10104)
- libravpn_setup.tmp (PID: 9884)
- Setup.exe (PID: 7564)
- app.exe (PID: 7784)
- SunLabsPlayer.exe (PID: 7596)
- powershell.exe (PID: 6912)
- UcSb7jo9o_iViBtNSe78kPEu.tmp (PID: 3044)
Checks supported languages
- wmiprvse.exe (PID: 2708)
- WinRAR.exe (PID: 2108)
- WinRAR.exe (PID: 520)
- main_setup_x86x64.exe (PID: 2840)
- setup_installer.exe (PID: 400)
- conhost.exe (PID: 2276)
- setup_install.exe (PID: 3368)
- cmd.exe (PID: 1536)
- cmd.exe (PID: 2768)
- cmd.exe (PID: 1944)
- cmd.exe (PID: 2780)
- sahiba_2.exe (PID: 2684)
- cmd.exe (PID: 748)
- cmd.exe (PID: 968)
- sahiba_3.exe (PID: 2636)
- cmd.exe (PID: 3592)
- sahiba_4.exe (PID: 2124)
- cmd.exe (PID: 2808)
- sahiba_6.exe (PID: 3680)
- sahiba_1.exe (PID: 3304)
- sahiba_9.exe (PID: 3904)
- cmd.exe (PID: 468)
- cmd.exe (PID: 1164)
- sahiba_5.exe (PID: 2376)
- sahiba_10.exe (PID: 3700)
- sahiba_8.exe (PID: 4020)
- sahiba_7.exe (PID: 3080)
- conhost.exe (PID: 2796)
- sahiba_5.tmp (PID: 496)
- sahiba_1.exe (PID: 3668)
- jfiag3g_gg.exe (PID: 660)
- JFHGSFGSIUGFSUIG.exe (PID: 1812)
- sahiba_9.exe (PID: 2284)
- 5075929.exe (PID: 3932)
- 6332060.exe (PID: 2316)
- 8565390.exe (PID: 3180)
- conhost.exe (PID: 2696)
- hR2phX9R4psDgLTytFScSA78.exe (PID: 676)
- qgRieigRJBBcVN4NkeX6SlpC.exe (PID: 1124)
- TCDUdNYbyNRCuYogsbUP5uDx.exe (PID: 1764)
- WinHoster.exe (PID: 3488)
- jfiag3g_gg.exe (PID: 3696)
- 7536611.exe (PID: 320)
- KNF426i_LnuvRjCRn67btkSt.exe (PID: 2348)
- CL2GGLruMiQhagp54ShuBydy.exe (PID: 3256)
- TCDUdNYbyNRCuYogsbUP5uDx.exe (PID: 1768)
- ultramediaburner.exe (PID: 3852)
- ultramediaburner.tmp (PID: 3396)
- 4613966.exe (PID: 3344)
- UltraMediaBurner.exe (PID: 3824)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- hR2phX9R4psDgLTytFScSA78.exe (PID: 3148)
- Vaxaefytaeli.exe (PID: 2764)
- MrGh6bEH0L0a.exe (PID: 1304)
- dsEIW6jGafchr6yo61uOgvMx.exe (PID: 3696)
- Browzar.exe (PID: 3056)
- 4065056.exe (PID: 3880)
- conhost.exe (PID: 3276)
- c47f7cjLMfWJJgWv3X6oDlyU.exe (PID: 2848)
- conhost.exe (PID: 3584)
- c47f7cjLMfWJJgWv3X6oDlyU.exe (PID: 2204)
- Mepasowikae.exe (PID: 4620)
- 92dRgtcSJUitRfKmavFzP9YY.exe (PID: 4644)
- 5993665.exe (PID: 2324)
- conhost.exe (PID: 2120)
- cmd.exe (PID: 4576)
- 87864724032.exe (PID: 1348)
- vSfsmZQiwu_m83vcAzKfCP55.exe (PID: 4960)
- cmd.exe (PID: 5992)
- conhost.exe (PID: 6104)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4456)
- conhost.exe (PID: 2488)
- cmd.exe (PID: 3460)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3292)
- MTgxHjQIwa0xNQWeg6cCDRvX.exe (PID: 5356)
- conhost.exe (PID: 400)
- jooyu.exe (PID: 5804)
- md8_8eus.exe (PID: 4540)
- jingzhang.exe (PID: 2668)
- file4.exe (PID: 6124)
- conhost.exe (PID: 4124)
- cmd.exe (PID: 5932)
- jfiag3g_gg.exe (PID: 5460)
- JoSetp.exe (PID: 4720)
- conhost.exe (PID: 1116)
- uuPQOCOMexhx3yxa1N9mqtPQ.exe (PID: 1768)
- conhost.exe (PID: 4536)
- cmd.exe (PID: 2052)
- Setup3310.exe (PID: 4480)
- Setup3310.tmp (PID: 4700)
- DK2u8J8s6Y_OKtryFL3tUKvl.exe (PID: 320)
- conhost.exe (PID: 5752)
- n1Bdoav4ePwmk39pjYjra7rp.exe (PID: 3416)
- jfiag3g_gg.exe (PID: 4940)
- uuPQOCOMexhx3yxa1N9mqtPQ.exe (PID: 4440)
- conhost.exe (PID: 2584)
- conhost.exe (PID: 2236)
- cmd.exe (PID: 2252)
- n1Bdoav4ePwmk39pjYjra7rp.exe (PID: 4304)
- cmd.exe (PID: 4280)
- conhost.exe (PID: 4764)
- _u73G1XXPC5iG3vd_ds6OnIc.exe (PID: 4580)
- google-game.exe (PID: 5020)
- cmd.exe (PID: 4760)
- conhost.exe (PID: 3492)
- google-game.exe (PID: 5572)
- conhost.exe (PID: 3112)
- cmd.exe (PID: 4896)
- 98827784354.exe (PID: 5852)
- cmd.exe (PID: 3188)
- conhost.exe (PID: 5140)
- askinstall46.exe (PID: 1356)
- cmd.exe (PID: 416)
- conhost.exe (PID: 5668)
- 86810264062.exe (PID: 5764)
- conhost.exe (PID: 4016)
- cmd.exe (PID: 1212)
- 1127893.exe (PID: 2352)
- 4783549.exe (PID: 1812)
- 3754144.exe (PID: 6048)
- 7296437.exe (PID: 3952)
- VJvJmRSXUxWEsi.exe (PID: 3424)
- 4.exe (PID: 4964)
- vpn.exe (PID: 2324)
- 6o7inj8hsSfNINZjJNZQpADc.exe (PID: 1760)
- conhost.exe (PID: 5644)
- cmd.exe (PID: 1032)
- edspolishpp.exe (PID: 4568)
- conhost.exe (PID: 2616)
- cmd.exe (PID: 5440)
- app.exe (PID: 4740)
- conhost.exe (PID: 4632)
- powershell.exe (PID: 696)
- ns7CAD.tmp (PID: 5604)
- SmartClock.exe (PID: 5136)
- Setup.exe (PID: 2636)
- conhost.exe (PID: 4676)
- cmd.exe (PID: 4884)
- note8876.exe (PID: 4860)
- WScript.exe (PID: 6084)
- tpobqkuunp.exe (PID: 2236)
- NMemo3Setp.exe (PID: 3924)
- lylal220.exe (PID: 3820)
- RunWW.exe (PID: 6100)
- MediaBurner.exe (PID: 3376)
- hjjgaa.exe (PID: 1260)
- LabPicV3.exe (PID: 968)
- conhost.exe (PID: 5144)
- guihuali-game.exe (PID: 3940)
- LabPicV3.tmp (PID: 5152)
- app.exe (PID: 2884)
- lylal220.tmp (PID: 4752)
- MediaBurner.tmp (PID: 5700)
- conhost.exe (PID: 5224)
- conhost.exe (PID: 5132)
- ns8F3C.tmp (PID: 756)
- lighteningplayer-cache-gen.exe (PID: 5464)
- guihuali-game.exe (PID: 4540)
- jfiag3g_gg.exe (PID: 4696)
- fa041e8b.exe (PID: 5876)
- 12(((((.exe (PID: 6072)
- cmd.exe (PID: 6020)
- conhost.exe (PID: 5768)
- �e�rgegd�_���_)))_.exe (PID: 2372)
- _____________bob.exe (PID: 308)
- conhost.exe (PID: 4696)
- cmd.exe (PID: 1944)
- 6966994.exe (PID: 2256)
- 3346707.exe (PID: 3608)
- jfiag3g_gg.exe (PID: 3656)
- UcSb7jo9o_iViBtNSe78kPEu.exe (PID: 3576)
- UcSb7jo9o_iViBtNSe78kPEu.tmp (PID: 3044)
- conhost.exe (PID: 5592)
- cmd.exe (PID: 5604)
- ultramediaburner.exe (PID: 4736)
- ultramediaburner.tmp (PID: 4056)
- UltraMediaBurner.exe (PID: 4176)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 1476)
- MrGh6bEH0L0a.exe (PID: 1268)
- 7534436.exe (PID: 2388)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5496)
- prolab.exe (PID: 4996)
- Qaejelaefomae.exe (PID: 5012)
- Vareshedema.exe (PID: 468)
- Paducaehaexy.exe (PID: 1880)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 5732)
- Nucaedimele.exe (PID: 4640)
- WScript.exe (PID: 3084)
- irecord.exe (PID: 1356)
- irecord.tmp (PID: 5812)
- Qashevishudy.exe (PID: 3084)
- I-Record.exe (PID: 5260)
- Maebumyzhymu.exe (PID: 4328)
- cmd.exe (PID: 2344)
- conhost.exe (PID: 536)
- SunLabsPlayer.exe (PID: 1172)
- conhost.exe (PID: 4388)
- cmd.exe (PID: 2156)
- conhost.exe (PID: 4944)
- toolspab1.exe (PID: 3252)
- nsEF8B.tmp (PID: 5512)
- powershell.exe (PID: 4068)
- conhost.exe (PID: 7728)
- conhost.exe (PID: 6500)
- cmd.exe (PID: 6436)
- toolspab1.exe (PID: 7704)
- conhost.exe (PID: 6492)
- nsF876.tmp (PID: 7044)
- lighteningplayer-cache-gen.exe (PID: 6764)
- cmd.exe (PID: 6408)
- cmd.exe (PID: 1448)
- conhost.exe (PID: 4208)
- Setup3310.tmp (PID: 6212)
- Setup3310.exe (PID: 5292)
- conhost.exe (PID: 8388)
- cmd.exe (PID: 8312)
- libravpn_setup.exe (PID: 7324)
- libravpn_setup.tmp (PID: 9884)
- LibraVPN.exe (PID: 4784)
- cmd.exe (PID: 4384)
- conhost.exe (PID: 6192)
- chcp.com (PID: 6996)
- cmd.exe (PID: 4272)
- conhost.exe (PID: 7700)
- cmd.exe (PID: 8976)
- google-game.exe (PID: 9420)
- cmd.exe (PID: 10056)
- conhost.exe (PID: 10176)
- google-game.exe (PID: 10104)
- chcp.com (PID: 7384)
- conhost.exe (PID: 10148)
- cmd.exe (PID: 9976)
- chcp.com (PID: 5740)
- cmd.exe (PID: 4700)
- conhost.exe (PID: 3240)
- cmd.exe (PID: 5480)
- conhost.exe (PID: 6392)
- cmd.exe (PID: 6024)
- chcp.com (PID: 5512)
- cmd.exe (PID: 2736)
- chcp.com (PID: 8424)
- cmd.exe (PID: 8448)
- conhost.exe (PID: 8400)
- cmd.exe (PID: 8520)
- conhost.exe (PID: 9364)
- cmd.exe (PID: 9184)
- chcp.com (PID: 9536)
- cmd.exe (PID: 9328)
- conhost.exe (PID: 7520)
- cmd.exe (PID: 7416)
- chcp.com (PID: 8752)
- cmd.exe (PID: 9796)
- cmd.exe (PID: 7976)
- conhost.exe (PID: 8028)
- chcp.com (PID: 4844)
- cmd.exe (PID: 3464)
- cmd.exe (PID: 3580)
- cmd.exe (PID: 6228)
- conhost.exe (PID: 4952)
- conhost.exe (PID: 2784)
- conhost.exe (PID: 7160)
- cmd.exe (PID: 10156)
- conhost.exe (PID: 10104)
- cmd.exe (PID: 7716)
- app.exe (PID: 7784)
- conhost.exe (PID: 4340)
- conhost.exe (PID: 6576)
- cmd.exe (PID: 5480)
- cmd.exe (PID: 4168)
- Setup.exe (PID: 7564)
- cmd.exe (PID: 3320)
- conhost.exe (PID: 4484)
- conhost.exe (PID: 8820)
- cmd.exe (PID: 5936)
- SunLabsPlayer.exe (PID: 7596)
- cmd.exe (PID: 4928)
- conhost.exe (PID: 6248)
- conhost.exe (PID: 8740)
- ns5F4D.tmp (PID: 6316)
- cmd.exe (PID: 8324)
- powershell.exe (PID: 6912)
- conhost.exe (PID: 7900)
- ns6662.tmp (PID: 8060)
- lighteningplayer-cache-gen.exe (PID: 4232)
- conhost.exe (PID: 7220)
- toolspab1.exe (PID: 7608)
- conhost.exe (PID: 7472)
- cmd.exe (PID: 7360)
- toolspab1.exe (PID: 5424)
- conhost.exe (PID: 8444)
- cmd.exe (PID: 6424)
- conhost.exe (PID: 9788)
- chcp.com (PID: 3388)
- conhost.exe (PID: 9976)
- cmd.exe (PID: 9992)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 9600)
- conhost.exe (PID: 9672)
- cmd.exe (PID: 4944)
- conhost.exe (PID: 6124)
- cmd.exe (PID: 8980)
- conhost.exe (PID: 7728)
- conhost.exe (PID: 7032)
- cmd.exe (PID: 6184)
- conhost.exe (PID: 2392)
- cmd.exe (PID: 5232)
- cmd.exe (PID: 6436)
- chcp.com (PID: 9748)
- conhost.exe (PID: 8800)
- cmd.exe (PID: 8728)
- conhost.exe (PID: 7364)
- cmd.exe (PID: 6556)
- conhost.exe (PID: 8844)
- conhost.exe (PID: 2884)
- cmd.exe (PID: 8656)
- conhost.exe (PID: 8576)
- cmd.exe (PID: 6188)
- cmd.exe (PID: 6896)
- conhost.exe (PID: 8828)
Reads Windows owner or organization settings
- wmiprvse.exe (PID: 2708)
- sahiba_5.tmp (PID: 496)
- ultramediaburner.tmp (PID: 3396)
- Setup3310.tmp (PID: 4700)
- LabPicV3.tmp (PID: 5152)
- MediaBurner.tmp (PID: 5700)
- lylal220.tmp (PID: 4752)
- ultramediaburner.tmp (PID: 4056)
- irecord.tmp (PID: 5812)
- Setup3310.tmp (PID: 6212)
- libravpn_setup.tmp (PID: 9884)
- UcSb7jo9o_iViBtNSe78kPEu.tmp (PID: 3044)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 520)
- main_setup_x86x64.exe (PID: 2840)
- setup_installer.exe (PID: 400)
- setup_install.exe (PID: 3368)
- sahiba_5.exe (PID: 2376)
- sahiba_5.tmp (PID: 496)
- sahiba_1.exe (PID: 3668)
- sahiba_4.exe (PID: 2124)
- sahiba_10.exe (PID: 3700)
- sahiba_6.exe (PID: 3680)
- sahiba_2.exe (PID: 2684)
- sahiba_7.exe (PID: 3080)
- 8565390.exe (PID: 3180)
- JFHGSFGSIUGFSUIG.exe (PID: 1812)
- ultramediaburner.exe (PID: 3852)
- ultramediaburner.tmp (PID: 3396)
- sahiba_3.exe (PID: 2636)
- Browzar.exe (PID: 3056)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- KNF426i_LnuvRjCRn67btkSt.exe (PID: 2348)
- 6332060.exe (PID: 2316)
- Mepasowikae.exe (PID: 4620)
- 4613966.exe (PID: 3344)
- 5075929.exe (PID: 3932)
- UcSb7jo9o_iViBtNSe78kPEu.tmp (PID: 3044)
Drops a file with a compile date too recent
- setup_installer.exe (PID: 400)
- setup_install.exe (PID: 3368)
- sahiba_1.exe (PID: 3668)
- sahiba_10.exe (PID: 3700)
- sahiba_6.exe (PID: 3680)
- 8565390.exe (PID: 3180)
- JFHGSFGSIUGFSUIG.exe (PID: 1812)
- Browzar.exe (PID: 3056)
- sahiba_7.exe (PID: 3080)
- Mepasowikae.exe (PID: 4620)
Drops a file that was compiled in debug mode
- setup_installer.exe (PID: 400)
- setup_install.exe (PID: 3368)
- sahiba_1.exe (PID: 3668)
- sahiba_5.tmp (PID: 496)
- sahiba_2.exe (PID: 2684)
- sahiba_7.exe (PID: 3080)
- ultramediaburner.tmp (PID: 3396)
- sahiba_3.exe (PID: 2636)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- KNF426i_LnuvRjCRn67btkSt.exe (PID: 2348)
- 6332060.exe (PID: 2316)
- 4613966.exe (PID: 3344)
- 5075929.exe (PID: 3932)
- Mepasowikae.exe (PID: 4620)
- UcSb7jo9o_iViBtNSe78kPEu.tmp (PID: 3044)
Drops a file with too old compile date
- setup_installer.exe (PID: 400)
- setup_install.exe (PID: 3368)
- sahiba_5.exe (PID: 2376)
- sahiba_5.tmp (PID: 496)
- sahiba_7.exe (PID: 3080)
- JFHGSFGSIUGFSUIG.exe (PID: 1812)
- ultramediaburner.exe (PID: 3852)
- ultramediaburner.tmp (PID: 3396)
- Mepasowikae.exe (PID: 4620)
Starts CMD.EXE for commands execution
- setup_install.exe (PID: 3368)
- KNF426i_LnuvRjCRn67btkSt.exe (PID: 2348)
- Mepasowikae.exe (PID: 4620)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- sahiba_3.exe (PID: 2636)
- 1127893.exe (PID: 2352)
- RunWW.exe (PID: 6100)
- Maebumyzhymu.exe (PID: 4328)
- LibraVPN.exe (PID: 4784)
- cmd.exe (PID: 4384)
- cmd.exe (PID: 10056)
- cmd.exe (PID: 4700)
- cmd.exe (PID: 6024)
- cmd.exe (PID: 8448)
- cmd.exe (PID: 9184)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 7976)
Application launched itself
- sahiba_1.exe (PID: 3304)
- sahiba_9.exe (PID: 3904)
- TCDUdNYbyNRCuYogsbUP5uDx.exe (PID: 1764)
- hR2phX9R4psDgLTytFScSA78.exe (PID: 676)
- c47f7cjLMfWJJgWv3X6oDlyU.exe (PID: 2848)
- uuPQOCOMexhx3yxa1N9mqtPQ.exe (PID: 1768)
- n1Bdoav4ePwmk39pjYjra7rp.exe (PID: 3416)
- MrGh6bEH0L0a.exe (PID: 1304)
- google-game.exe (PID: 5020)
- sCvSX5Npg_ODcTpciw8DPCry.exe (PID: 4456)
- 8_WUt7Q24AJOgmydqB0qCIT1.exe (PID: 3292)
- guihuali-game.exe (PID: 3940)
- toolspab1.exe (PID: 3252)
- cmd.exe (PID: 4384)
- google-game.exe (PID: 9420)
- cmd.exe (PID: 10056)
- cmd.exe (PID: 4700)
- cmd.exe (PID: 6024)
- cmd.exe (PID: 8448)
- cmd.exe (PID: 9184)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 7976)
- toolspab1.exe (PID: 7608)
Reads the Windows organization settings
- sahiba_5.tmp (PID: 496)
- ultramediaburner.tmp (PID: 3396)
- wmiprvse.exe (PID: 2708)
- Setup3310.tmp (PID: 4700)
- LabPicV3.tmp (PID: 5152)
- lylal220.tmp (PID: 4752)
- MediaBurner.tmp (PID: 5700)
- ultramediaburner.tmp (PID: 4056)
- irecord.tmp (PID: 5812)
- Setup3310.tmp (PID: 6212)
- libravpn_setup.tmp (PID: 9884)
- UcSb7jo9o_iViBtNSe78kPEu.tmp (PID: 3044)
Reads Environment values
- sahiba_10.exe (PID: 3700)
- sahiba_6.exe (PID: 3680)
- JFHGSFGSIUGFSUIG.exe (PID: 1812)
- 6332060.exe (PID: 2316)
- 5075929.exe (PID: 3932)
- sahiba_8.exe (PID: 4020)
- sahiba_9.exe (PID: 2284)
- 4613966.exe (PID: 3344)
- Vaxaefytaeli.exe (PID: 2764)
- qgRieigRJBBcVN4NkeX6SlpC.exe (PID: 1124)
- 7536611.exe (PID: 320)
- TCDUdNYbyNRCuYogsbUP5uDx.exe (PID: 1768)
- CL2GGLruMiQhagp54ShuBydy.exe (PID: 3256)
- Mepasowikae.exe (PID: 4620)
- 92dRgtcSJUitRfKmavFzP9YY.exe (PID: 4644)
- 5993665.exe (PID: 2324)
- vSfsmZQiwu_m83vcAzKfCP55.exe (PID: 4960)
- JoSetp.exe (PID: 4720)
- sahiba_3.exe (PID: 2636)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- 87864724032.exe (PID: 1348)
- DK2u8J8s6Y_OKtryFL3tUKvl.exe (PID: 320)
- uuPQOCOMexhx3yxa1N9mqtPQ.exe (PID: 4440)
- n1Bdoav4ePwmk39pjYjra7rp.exe (PID: 4304)
- 98827784354.exe (PID: 5852)
- 4783549.exe (PID: 1812)
- 1127893.exe (PID: 2352)
- 86810264062.exe (PID: 5764)
- 7296437.exe (PID: 3952)
- edspolishpp.exe (PID: 4568)
- NMemo3Setp.exe (PID: 3924)
- 12(((((.exe (PID: 6072)
- �e�rgegd�_���_)))_.exe (PID: 2372)
- _____________bob.exe (PID: 308)
- RunWW.exe (PID: 6100)
- 6966994.exe (PID: 2256)
- Qashevishudy.exe (PID: 3084)
- Maebumyzhymu.exe (PID: 4328)
- LibraVPN.exe (PID: 4784)
- netsh.exe (PID: 6852)
- netsh.exe (PID: 7204)
- netsh.exe (PID: 5308)
- netsh.exe (PID: 5956)
- netsh.exe (PID: 6412)
- netsh.exe (PID: 10040)
- netsh.exe (PID: 9704)
Adds / modifies Windows certificates
- sahiba_7.exe (PID: 3080)
- sahiba_3.exe (PID: 2636)
Uses RUNDLL32.EXE to load library
- wmiprvse.exe (PID: 2708)
- jingzhang.exe (PID: 2668)
- tpobqkuunp.exe (PID: 2236)
Executed via WMI
- rUNdlL32.eXe (PID: 3520)
Checks for external IP
- sahiba_4.exe (PID: 2124)
- sahiba_7.exe (PID: 3080)
- sahiba_9.exe (PID: 2284)
- svchost.exe (PID: 3360)
- jooyu.exe (PID: 5804)
- Setup3310.tmp (PID: 4700)
- n1Bdoav4ePwmk39pjYjra7rp.exe (PID: 4304)
- vpn.exe (PID: 2324)
- hjjgaa.exe (PID: 1260)
- Setup3310.tmp (PID: 6212)
Creates files in the user directory
- sahiba_10.exe (PID: 3700)
- sahiba_6.exe (PID: 3680)
- 8565390.exe (PID: 3180)
- sahiba_7.exe (PID: 3080)
- Browzar.exe (PID: 3056)
- svchost.exe (PID: 3360)
- JoSetp.exe (PID: 4720)
- 86810264062.exe (PID: 5764)
- 6o7inj8hsSfNINZjJNZQpADc.exe (PID: 1760)
- 4.exe (PID: 4964)
- vpn.exe (PID: 2324)
- powershell.exe (PID: 696)
- NMemo3Setp.exe (PID: 3924)
- powershell.exe (PID: 4068)
- libravpn_setup.tmp (PID: 9884)
- powershell.exe (PID: 6912)
Starts itself from another location
- 8565390.exe (PID: 3180)
- 4.exe (PID: 4964)
Creates a directory in Program Files
- JFHGSFGSIUGFSUIG.exe (PID: 1812)
- ultramediaburner.tmp (PID: 3396)
- dsEIW6jGafchr6yo61uOgvMx.exe (PID: 3696)
- MTgxHjQIwa0xNQWeg6cCDRvX.exe (PID: 5356)
- VJvJmRSXUxWEsi.exe (PID: 3424)
- 6o7inj8hsSfNINZjJNZQpADc.exe (PID: 1760)
- Setup.exe (PID: 2636)
- �e�rgegd�_���_)))_.exe (PID: 2372)
- _____________bob.exe (PID: 308)
- 12(((((.exe (PID: 6072)
- irecord.tmp (PID: 5812)
- LibraVPN.exe (PID: 4784)
- libravpn_setup.tmp (PID: 9884)
- UcSb7jo9o_iViBtNSe78kPEu.tmp (PID: 3044)
Starts Microsoft Office Application
- JFHGSFGSIUGFSUIG.exe (PID: 1812)
Creates files in the program directory
- WerFault.exe (PID: 2668)
- dsEIW6jGafchr6yo61uOgvMx.exe (PID: 3696)
- sahiba_3.exe (PID: 2636)
- 6332060.exe (PID: 2316)
- MTgxHjQIwa0xNQWeg6cCDRvX.exe (PID: 5356)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- WerFault.exe (PID: 5168)
- 4613966.exe (PID: 3344)
- WerFault.exe (PID: 2756)
- WerFault.exe (PID: 4768)
- 5075929.exe (PID: 3932)
- 1127893.exe (PID: 2352)
- VJvJmRSXUxWEsi.exe (PID: 3424)
- 6o7inj8hsSfNINZjJNZQpADc.exe (PID: 1760)
- WerFault.exe (PID: 3656)
- lighteningplayer-cache-gen.exe (PID: 5464)
- 4783549.exe (PID: 1812)
- WerFault.exe (PID: 3932)
- RunWW.exe (PID: 6100)
- WerFault.exe (PID: 4224)
- 6966994.exe (PID: 2256)
- lighteningplayer-cache-gen.exe (PID: 6764)
- WerFault.exe (PID: 7116)
- LibraVPN.exe (PID: 4784)
- WerFault.exe (PID: 7020)
- WerFault.exe (PID: 8196)
- lighteningplayer-cache-gen.exe (PID: 4232)
Searches for installed software
- svchost.exe (PID: 3360)
- qgRieigRJBBcVN4NkeX6SlpC.exe (PID: 1124)
- TCDUdNYbyNRCuYogsbUP5uDx.exe (PID: 1768)
- sahiba_9.exe (PID: 2284)
- CL2GGLruMiQhagp54ShuBydy.exe (PID: 3256)
- 7536611.exe (PID: 320)
- 92dRgtcSJUitRfKmavFzP9YY.exe (PID: 4644)
- 5993665.exe (PID: 2324)
- sahiba_8.exe (PID: 4020)
- 6332060.exe (PID: 2316)
- sahiba_3.exe (PID: 2636)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- vSfsmZQiwu_m83vcAzKfCP55.exe (PID: 4960)
- 4613966.exe (PID: 3344)
- 87864724032.exe (PID: 1348)
- 5075929.exe (PID: 3932)
- uuPQOCOMexhx3yxa1N9mqtPQ.exe (PID: 4440)
- 98827784354.exe (PID: 5852)
- n1Bdoav4ePwmk39pjYjra7rp.exe (PID: 4304)
- 1127893.exe (PID: 2352)
- RunWW.exe (PID: 6100)
- 4783549.exe (PID: 1812)
- 7296437.exe (PID: 3952)
- ultramediaburner.tmp (PID: 4056)
- 6966994.exe (PID: 2256)
- edspolishpp.exe (PID: 4568)
Creates a software uninstall entry
- dsEIW6jGafchr6yo61uOgvMx.exe (PID: 3696)
- MTgxHjQIwa0xNQWeg6cCDRvX.exe (PID: 5356)
- 6o7inj8hsSfNINZjJNZQpADc.exe (PID: 1760)
- SunLabsPlayer.exe (PID: 1172)
- SunLabsPlayer.exe (PID: 7596)
Reads internet explorer settings
- Browzar.exe (PID: 3056)
- LibraVPN.exe (PID: 4784)
Reads Microsoft Outlook installation path
- Browzar.exe (PID: 3056)
- iexplore.exe (PID: 3380)
- iexplore.exe (PID: 5772)
- iexplore.exe (PID: 4640)
- LibraVPN.exe (PID: 4784)
Starts Internet Explorer
- Vaxaefytaeli.exe (PID: 2764)
- Qashevishudy.exe (PID: 3084)
- UcSb7jo9o_iViBtNSe78kPEu.tmp (PID: 3044)
Reads the cookies of Mozilla Firefox
- svchost.exe (PID: 3360)
Reads Windows Product ID
- wmiprvse.exe (PID: 2708)
Reads the date of Windows installation
- wmiprvse.exe (PID: 2708)
- jingzhang.exe (PID: 2668)
- powershell.exe (PID: 696)
- powershell.exe (PID: 4068)
- powershell.exe (PID: 6912)
Reads CPU info
- wmiprvse.exe (PID: 2708)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- sahiba_3.exe (PID: 2636)
- 98827784354.exe (PID: 5852)
- 1127893.exe (PID: 2352)
- 86810264062.exe (PID: 5764)
- vpn.exe (PID: 2324)
- RunWW.exe (PID: 6100)
Executes application which crashes
- cmd.exe (PID: 5992)
- cmd.exe (PID: 3460)
- cmd.exe (PID: 1944)
- cmd.exe (PID: 6436)
- cmd.exe (PID: 6408)
- cmd.exe (PID: 6228)
Starts CMD.EXE for self-deleting
- sahiba_3.exe (PID: 2636)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- 1127893.exe (PID: 2352)
- RunWW.exe (PID: 6100)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 4280)
- cmd.exe (PID: 2252)
- cmd.exe (PID: 1212)
- cmd.exe (PID: 1032)
- cmd.exe (PID: 5604)
- cmd.exe (PID: 3580)
Executes PowerShell scripts
- ns7CAD.tmp (PID: 5604)
- nsEF8B.tmp (PID: 5512)
- ns5F4D.tmp (PID: 6316)
Starts application with an unusual extension
- 6o7inj8hsSfNINZjJNZQpADc.exe (PID: 1760)
- SunLabsPlayer.exe (PID: 1172)
- cmd.exe (PID: 4384)
- cmd.exe (PID: 10056)
- cmd.exe (PID: 4700)
- cmd.exe (PID: 6024)
- cmd.exe (PID: 8448)
- cmd.exe (PID: 9184)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 7976)
- SunLabsPlayer.exe (PID: 7596)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 6436)
Executes scripts
- vpn.exe (PID: 2324)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 4272)
- cmd.exe (PID: 9976)
- cmd.exe (PID: 5480)
- cmd.exe (PID: 2736)
- cmd.exe (PID: 8520)
- cmd.exe (PID: 9328)
- cmd.exe (PID: 9796)
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 3464)
Changes default file association
- UcSb7jo9o_iViBtNSe78kPEu.tmp (PID: 3044)
INFO
Application launched itself
- chrome.exe (PID: 568)
- iexplore.exe (PID: 2968)
Checks supported languages
- chrome.exe (PID: 568)
- chrome.exe (PID: 2832)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 1264)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 3312)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 1512)
- chrome.exe (PID: 2164)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 2448)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 1080)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 3292)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 2060)
- chrome.exe (PID: 3288)
- DllHost.exe (PID: 1960)
- NOTEPAD.EXE (PID: 2328)
- DllHost.exe (PID: 2224)
- DllHost.exe (PID: 312)
- consent.exe (PID: 2164)
- DllHost.exe (PID: 3056)
- DllHost.exe (PID: 2028)
- DllHost.exe (PID: 2396)
- svchost.exe (PID: 3360)
- rUNdlL32.eXe (PID: 3520)
- svchost.exe (PID: 3992)
- WerFault.exe (PID: 2668)
- DllHost.exe (PID: 1348)
- DllHost.exe (PID: 3352)
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 3380)
- rUNdlL32.eXe (PID: 4388)
- SearchProtocolHost.exe (PID: 5836)
- iexplore.exe (PID: 5772)
- ntvdm.exe (PID: 4212)
- WerFault.exe (PID: 4768)
- ntvdm.exe (PID: 5880)
- DllHost.exe (PID: 756)
- WerFault.exe (PID: 2756)
- WerFault.exe (PID: 5168)
- rUNdlL32.eXe (PID: 4320)
- DllHost.exe (PID: 6012)
- timeout.exe (PID: 3656)
- timeout.exe (PID: 4064)
- taskkill.exe (PID: 4984)
- taskkill.exe (PID: 5632)
- rUNdlL32.eXe (PID: 3424)
- taskkill.exe (PID: 1140)
- WerFault.exe (PID: 3656)
- taskkill.exe (PID: 5800)
- SearchFilterHost.exe (PID: 2216)
- timeout.exe (PID: 5080)
- WerFault.exe (PID: 3932)
- DllHost.exe (PID: 464)
- rUNdlL32.eXe (PID: 3864)
- DllHost.exe (PID: 2984)
- rundll32.exe (PID: 2796)
- ntvdm.exe (PID: 5892)
- WerFault.exe (PID: 4224)
- WerFault.exe (PID: 4204)
- taskkill.exe (PID: 1356)
- timeout.exe (PID: 3668)
- LogonUI.exe (PID: 6084)
- iexplore.exe (PID: 4640)
- iexplore.exe (PID: 5504)
- ntvdm.exe (PID: 6688)
- WerFault.exe (PID: 7020)
- ntvdm.exe (PID: 7012)
- WerFault.exe (PID: 7116)
- netsh.exe (PID: 6852)
- netsh.exe (PID: 7204)
- rUNdlL32.eXe (PID: 7180)
- netsh.exe (PID: 5308)
- netsh.exe (PID: 5956)
- netsh.exe (PID: 6412)
- netsh.exe (PID: 10040)
- netsh.exe (PID: 9704)
- ipconfig.exe (PID: 4536)
- taskkill.exe (PID: 276)
- ntvdm.exe (PID: 6804)
- WerFault.exe (PID: 8196)
- DllHost.exe (PID: 6960)
- iexplore.exe (PID: 8816)
- DllHost.exe (PID: 9740)
- SearchProtocolHost.exe (PID: 6432)
Reads the hosts file
- chrome.exe (PID: 568)
- chrome.exe (PID: 2880)
Reads the computer name
- chrome.exe (PID: 568)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 2832)
- chrome.exe (PID: 2164)
- chrome.exe (PID: 2060)
- chrome.exe (PID: 3004)
- DllHost.exe (PID: 1960)
- chrome.exe (PID: 3288)
- DllHost.exe (PID: 2224)
- DllHost.exe (PID: 312)
- DllHost.exe (PID: 3056)
- consent.exe (PID: 2164)
- DllHost.exe (PID: 2028)
- DllHost.exe (PID: 2396)
- svchost.exe (PID: 3360)
- rUNdlL32.eXe (PID: 3520)
- svchost.exe (PID: 3992)
- WerFault.exe (PID: 2668)
- DllHost.exe (PID: 1348)
- DllHost.exe (PID: 3352)
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 3380)
- rUNdlL32.eXe (PID: 4388)
- SearchProtocolHost.exe (PID: 5836)
- iexplore.exe (PID: 5772)
- WerFault.exe (PID: 4768)
- DllHost.exe (PID: 756)
- WerFault.exe (PID: 2756)
- WerFault.exe (PID: 5168)
- rUNdlL32.eXe (PID: 4320)
- DllHost.exe (PID: 6012)
- taskkill.exe (PID: 4984)
- taskkill.exe (PID: 5632)
- rUNdlL32.eXe (PID: 3424)
- taskkill.exe (PID: 1140)
- WerFault.exe (PID: 3656)
- taskkill.exe (PID: 5800)
- SearchFilterHost.exe (PID: 2216)
- WerFault.exe (PID: 3932)
- DllHost.exe (PID: 464)
- rUNdlL32.eXe (PID: 3864)
- DllHost.exe (PID: 2984)
- WerFault.exe (PID: 4224)
- taskkill.exe (PID: 1356)
- WerFault.exe (PID: 4204)
- LogonUI.exe (PID: 6084)
- iexplore.exe (PID: 5504)
- iexplore.exe (PID: 4640)
- WerFault.exe (PID: 7020)
- WerFault.exe (PID: 7116)
- netsh.exe (PID: 6852)
- netsh.exe (PID: 7204)
- rUNdlL32.eXe (PID: 7180)
- netsh.exe (PID: 5308)
- netsh.exe (PID: 5956)
- netsh.exe (PID: 6412)
- netsh.exe (PID: 9704)
- netsh.exe (PID: 10040)
- ipconfig.exe (PID: 4536)
- taskkill.exe (PID: 276)
- DllHost.exe (PID: 6960)
- WerFault.exe (PID: 8196)
- iexplore.exe (PID: 8816)
- DllHost.exe (PID: 9740)
- SearchProtocolHost.exe (PID: 6432)
Reads settings of System Certificates
- chrome.exe (PID: 2880)
- sahiba_7.exe (PID: 3080)
- sahiba_6.exe (PID: 3680)
- sahiba_10.exe (PID: 3700)
- sahiba_4.exe (PID: 2124)
- JFHGSFGSIUGFSUIG.exe (PID: 1812)
- 5075929.exe (PID: 3932)
- sahiba_3.exe (PID: 2636)
- 6332060.exe (PID: 2316)
- sahiba_9.exe (PID: 2284)
- Vaxaefytaeli.exe (PID: 2764)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- 4613966.exe (PID: 3344)
- iexplore.exe (PID: 3380)
- qgRieigRJBBcVN4NkeX6SlpC.exe (PID: 1124)
- TCDUdNYbyNRCuYogsbUP5uDx.exe (PID: 1768)
- CL2GGLruMiQhagp54ShuBydy.exe (PID: 3256)
- Mepasowikae.exe (PID: 4620)
- iexplore.exe (PID: 2968)
- 7536611.exe (PID: 320)
- iexplore.exe (PID: 5772)
- 92dRgtcSJUitRfKmavFzP9YY.exe (PID: 4644)
- 5993665.exe (PID: 2324)
- sahiba_8.exe (PID: 4020)
- vSfsmZQiwu_m83vcAzKfCP55.exe (PID: 4960)
- Setup3310.tmp (PID: 4700)
- jooyu.exe (PID: 5804)
- 87864724032.exe (PID: 1348)
- uuPQOCOMexhx3yxa1N9mqtPQ.exe (PID: 4440)
- JoSetp.exe (PID: 4720)
- n1Bdoav4ePwmk39pjYjra7rp.exe (PID: 4304)
- askinstall46.exe (PID: 1356)
- KNF426i_LnuvRjCRn67btkSt.exe (PID: 2348)
- 1127893.exe (PID: 2352)
- 4783549.exe (PID: 1812)
- 86810264062.exe (PID: 5764)
- vpn.exe (PID: 2324)
- RunWW.exe (PID: 6100)
- NMemo3Setp.exe (PID: 3924)
- hjjgaa.exe (PID: 1260)
- 7296437.exe (PID: 3952)
- 12(((((.exe (PID: 6072)
- �e�rgegd�_���_)))_.exe (PID: 2372)
- _____________bob.exe (PID: 308)
- 6966994.exe (PID: 2256)
- Qashevishudy.exe (PID: 3084)
- Maebumyzhymu.exe (PID: 4328)
- iexplore.exe (PID: 4640)
- Setup3310.tmp (PID: 6212)
- LibraVPN.exe (PID: 4784)
- libravpn_setup.tmp (PID: 9884)
- edspolishpp.exe (PID: 4568)
Reads the date of Windows installation
- chrome.exe (PID: 3004)
- iexplore.exe (PID: 2968)
Manual execution by user
- NOTEPAD.EXE (PID: 2328)
- WinRAR.exe (PID: 520)
- main_setup_x86x64.exe (PID: 1452)
- main_setup_x86x64.exe (PID: 2840)
Checks Windows Trust Settings
- consent.exe (PID: 2164)
- sahiba_7.exe (PID: 3080)
- sahiba_3.exe (PID: 2636)
- hpwauLouHaiRtXIhHAM5jUGD.exe (PID: 3424)
- iexplore.exe (PID: 3380)
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 5772)
- askinstall46.exe (PID: 1356)
- 1127893.exe (PID: 2352)
- vpn.exe (PID: 2324)
- powershell.exe (PID: 696)
- WScript.exe (PID: 6084)
- RunWW.exe (PID: 6100)
- iexplore.exe (PID: 4640)
- powershell.exe (PID: 4068)
- LibraVPN.exe (PID: 4784)
- powershell.exe (PID: 6912)
Application was dropped or rewritten from another process
- sahiba_5.tmp (PID: 496)
- JFHGSFGSIUGFSUIG.exe (PID: 1812)
- ultramediaburner.tmp (PID: 3396)
- Setup.exe (PID: 2636)
- LabPicV3.tmp (PID: 5152)
- 12(((((.exe (PID: 6072)
- �e�rgegd�_���_)))_.exe (PID: 2372)
- _____________bob.exe (PID: 308)
- ultramediaburner.tmp (PID: 4056)
- Setup.exe (PID: 7564)
- UcSb7jo9o_iViBtNSe78kPEu.tmp (PID: 3044)
Loads dropped or rewritten executable
- sahiba_5.tmp (PID: 496)
- JFHGSFGSIUGFSUIG.exe (PID: 1812)
- ultramediaburner.tmp (PID: 3396)
- Setup3310.tmp (PID: 4700)
- Setup.exe (PID: 2636)
- LabPicV3.tmp (PID: 5152)
- MediaBurner.tmp (PID: 5700)
- lylal220.tmp (PID: 4752)
- 12(((((.exe (PID: 6072)
- �e�rgegd�_���_)))_.exe (PID: 2372)
- _____________bob.exe (PID: 308)
- UcSb7jo9o_iViBtNSe78kPEu.tmp (PID: 3044)
- ultramediaburner.tmp (PID: 4056)
- irecord.tmp (PID: 5812)
- Setup3310.tmp (PID: 6212)
- libravpn_setup.tmp (PID: 9884)
- Setup.exe (PID: 7564)
Dropped object may contain Bitcoin addresses
- sahiba_6.exe (PID: 3680)
- UcSb7jo9o_iViBtNSe78kPEu.tmp (PID: 3044)
Reads CPU info
- svchost.exe (PID: 3360)
Creates files in the program directory
- JFHGSFGSIUGFSUIG.exe (PID: 1812)
- ultramediaburner.tmp (PID: 3396)
- Setup.exe (PID: 2636)
- _____________bob.exe (PID: 308)
- ultramediaburner.tmp (PID: 4056)
- 12(((((.exe (PID: 6072)
- �e�rgegd�_���_)))_.exe (PID: 2372)
- irecord.tmp (PID: 5812)
- libravpn_setup.tmp (PID: 9884)
- UcSb7jo9o_iViBtNSe78kPEu.tmp (PID: 3044)
Creates a software uninstall entry
- ultramediaburner.tmp (PID: 3396)
- Setup.exe (PID: 2636)
- ultramediaburner.tmp (PID: 4056)
- irecord.tmp (PID: 5812)
- libravpn_setup.tmp (PID: 9884)
- UcSb7jo9o_iViBtNSe78kPEu.tmp (PID: 3044)
Changes internet zones settings
- iexplore.exe (PID: 2968)
Reads internet explorer settings
- iexplore.exe (PID: 3380)
- iexplore.exe (PID: 5772)
- iexplore.exe (PID: 4640)
Creates files in the user directory
- iexplore.exe (PID: 3380)
- iexplore.exe (PID: 5772)
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 4640)
Changes settings of System certificates
- iexplore.exe (PID: 2968)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
851
Monitored processes
819
Malicious processes
140
Suspicious processes
324
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | taskkill /f /im wireguard.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 308 | "C:\Users\admin\AppData\Local\Temp\is-3E4HC.tmp\_____________bob.exe" /S /UID=burnerch1 | C:\Users\admin\AppData\Local\Temp\is-3E4HC.tmp\_____________bob.exe | MediaBurner.tmp | ||||||||||||
User: admin Company: Burner_ID__6bcewmegqhc267pz5w2c5gvww Integrity Level: HIGH Description: Burner_ID__6bcewmegqhc267pz5w2c5gvww Exit code: 0 Version: 8.87.7.8 Modules
| |||||||||||||||
| 312 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 320 | "C:\Users\admin\AppData\Roaming\7536611.exe" | C:\Users\admin\AppData\Roaming\7536611.exe | sahiba_6.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Defective Exit code: 0 Version: 3.1.0.0 Modules
| |||||||||||||||
| 320 | "C:\Users\admin\Documents\DK2u8J8s6Y_OKtryFL3tUKvl.exe" | C:\Users\admin\Documents\DK2u8J8s6Y_OKtryFL3tUKvl.exe | sahiba_7.exe | ||||||||||||
User: admin Company: Kiff devel. Integrity Level: HIGH Description: MyKiff Exit code: 0 Version: 3.5.7.9 Modules
| |||||||||||||||
| 336 | C:\Users\admin\Documents\8_WUt7Q24AJOgmydqB0qCIT1.exe | C:\Users\admin\Documents\8_WUt7Q24AJOgmydqB0qCIT1.exe | — | 8_WUt7Q24AJOgmydqB0qCIT1.exe | |||||||||||
User: admin Company: NList Corporation. Integrity Level: HIGH Description: Net Listing App Exit code: 0 Version: 124.698.302.190 Modules
| |||||||||||||||
| 356 | C:\Users\admin\Documents\sCvSX5Npg_ODcTpciw8DPCry.exe | C:\Users\admin\Documents\sCvSX5Npg_ODcTpciw8DPCry.exe | — | sCvSX5Npg_ODcTpciw8DPCry.exe | |||||||||||
User: admin Company: NList Corporation. Integrity Level: HIGH Description: Net Listing App Exit code: 0 Version: 606.784.33.599 Modules
| |||||||||||||||
| 364 | C:\Users\admin\Documents\8_WUt7Q24AJOgmydqB0qCIT1.exe | C:\Users\admin\Documents\8_WUt7Q24AJOgmydqB0qCIT1.exe | — | 8_WUt7Q24AJOgmydqB0qCIT1.exe | |||||||||||
User: admin Company: NList Corporation. Integrity Level: HIGH Description: Net Listing App Exit code: 0 Version: 124.698.302.190 Modules
| |||||||||||||||
| 368 | "C:\Program Files\Browzar\MrGh6bEH0L0a.exe" | C:\Program Files\Browzar\MrGh6bEH0L0a.exe | — | MrGh6bEH0L0a.exe | |||||||||||
User: admin Company: LFS Corporation. Integrity Level: HIGH Description: Ferz Universal App Exit code: 0 Version: 950.469.10.696 Modules
| |||||||||||||||
| 400 | "C:\Users\admin\AppData\Local\Temp\setup_installer.exe" | C:\Users\admin\AppData\Local\Temp\setup_installer.exe | main_setup_x86x64.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Setup SFX Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
Total events
629 270
Read events
625 991
Write events
3 213
Delete events
66
Modification events
| (PID) Process: | (568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (568) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
264
Suspicious files
87
Text files
192
Unknown types
365
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60E5A088-238.pma | — | |
MD5:— | SHA256:— | |||
| 568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9133bf6d-4196-47e8-a156-160d6c247b97.tmp | text | |
MD5:— | SHA256:— | |||
| 568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8135a1a5-8025-46eb-80aa-623c3288355e.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 1264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF10a8e4.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
416
TCP/UDP connections
523
DNS requests
185
Threats
632
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2880 | chrome.exe | GET | 301 | 172.67.183.55:80 | http://centomor.xyz/?s=163&q=OBS-Studio-2701-Crack-&g=4448d149e5ad185d11fb11eee8c78b7e&mode= | US | — | — | malicious |
496 | sahiba_5.tmp | HEAD | 200 | 63.250.33.126:80 | http://requested404.com/C_Pirlo/UltraMediaBurner.exe | US | — | — | suspicious |
3080 | sahiba_7.exe | HEAD | 200 | 136.144.41.201:80 | http://136.144.41.201/WW/file10.exe | NL | — | — | suspicious |
3368 | setup_install.exe | GET | 200 | 104.21.86.8:80 | http://razino.xyz/addInstall.php?key=125478824515ADNxu2ccbwe&ip=&oid=139&oname[]=7July220PM&oname[]=7&oname[]=1&oname[]=2&oname[]=3&oname[]=4&oname[]=5&oname[]=6&oname[]=8&oname[]=9&oname[]=10&cnt=10 | US | text | 10 b | malicious |
2880 | chrome.exe | GET | 302 | 54.214.130.202:80 | http://54.214.130.202/?00bcb3becb49f270b481397fd524e4c2365901f4=592d520959078c2a6d2e16efccf4bff314b74a5f&m=163&q=OBS-Studio-2701-Crack-&dedica= | US | html | 19.0 Kb | unknown |
2880 | chrome.exe | POST | 200 | 54.214.130.202:80 | http://54.214.130.202/?go=4358c7b940a&dedica= | US | html | 670 b | unknown |
3080 | sahiba_7.exe | GET | 200 | 2.56.59.245:80 | http://2.56.59.245/server.txt | unknown | text | 18 b | suspicious |
3080 | sahiba_7.exe | POST | 200 | 79.174.12.174:80 | http://79.174.12.174/base/api/getData.php | unknown | text | 263 b | malicious |
3080 | sahiba_7.exe | POST | 200 | 79.174.12.174:80 | http://79.174.12.174/base/api/getData.php | unknown | text | 263 b | malicious |
3080 | sahiba_7.exe | POST | 200 | 79.174.12.174:80 | http://79.174.12.174/base/api/getData.php | unknown | text | 263 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2880 | chrome.exe | 142.250.186.110:443 | — | Google Inc. | US | whitelisted |
2880 | chrome.exe | 142.250.186.77:443 | clients2.google.com | Google Inc. | US | suspicious |
2880 | chrome.exe | 80.82.77.242:443 | — | Quasi Networks LTD. | SC | suspicious |
2880 | chrome.exe | 192.0.76.3:443 | stats.wp.com | Automattic, Inc | US | suspicious |
2880 | chrome.exe | 192.0.77.2:443 | i1.wp.com | Automattic, Inc | US | suspicious |
2880 | chrome.exe | 192.0.77.37:443 | c0.wp.com | Automattic, Inc | US | suspicious |
2880 | chrome.exe | 104.22.70.197:443 | — | Cloudflare Inc | US | unknown |
2880 | chrome.exe | 192.0.73.2:443 | — | Automattic, Inc | US | whitelisted |
2880 | chrome.exe | 192.0.78.27:443 | href.li | Automattic, Inc | US | suspicious |
2880 | chrome.exe | 104.21.65.112:443 | singhost.online | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
idmpatched.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
c0.wp.com |
| whitelisted |
i1.wp.com |
| whitelisted |
i0.wp.com |
| whitelisted |
i2.wp.com |
| whitelisted |
stats.wp.com |
| whitelisted |
static.addtoany.com |
| whitelisted |
secure.gravatar.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2880 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3368 | setup_install.exe | A Network Trojan was detected | AV TROJAN GCleaner Downloader CnC Activity |
3368 | setup_install.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3080 | sahiba_7.exe | A Network Trojan was detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
3080 | sahiba_7.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
2124 | sahiba_4.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2124 | sahiba_4.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
496 | sahiba_5.tmp | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3080 | sahiba_7.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
3080 | sahiba_7.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
173 ETPRO signatures available at the full report
Process | Message |
|---|---|
lighteningplayer-cache-gen.exe | main libvlc debug: VLC media player - 3.0.7 Vetinari
|
lighteningplayer-cache-gen.exe | main libvlc debug: Copyright � 1996-2018 the VideoLAN team
|
lighteningplayer-cache-gen.exe | main libvlc debug: revision 3.0.2-225-gc9e3360dd4
|
lighteningplayer-cache-gen.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-twolame' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-x264' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=i686-w64-mingw32' '--build=x86_64-pc-linux-gnu' 'build_alias=x86_64-pc-linux-gnu' 'host_alias=i686-w64-mingw32'
|
lighteningplayer-cache-gen.exe | main libvlc debug: using multimedia timers as clock source
|
lighteningplayer-cache-gen.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
lighteningplayer-cache-gen.exe | main libvlc debug: searching plug-in modules
|
lighteningplayer-cache-gen.exe | main libvlc debug: ignoring plugins cache file
|
lighteningplayer-cache-gen.exe | main libvlc debug: recursively browsing `C:\Program Files\lighteningplayer\plugins'
|
lighteningplayer-cache-gen.exe | main libvlc debug: saving plugins cache C:\Program Files\lighteningplayer\plugins\plugins.dat
|