| File name: | Purchase Enquiry.rar |
| Full analysis: | https://app.any.run/tasks/e6110853-8208-4738-9f62-039f34cad4d6 |
| Verdict: | Malicious activity |
| Threats: | Pony is a malware with two main functions — stealing information and dropping other viruses with different tasks on infected machines. It has been around since 2011, and it still actively attacks users in Europe and America. |
| Analysis date: | May 20, 2019, 12:54:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
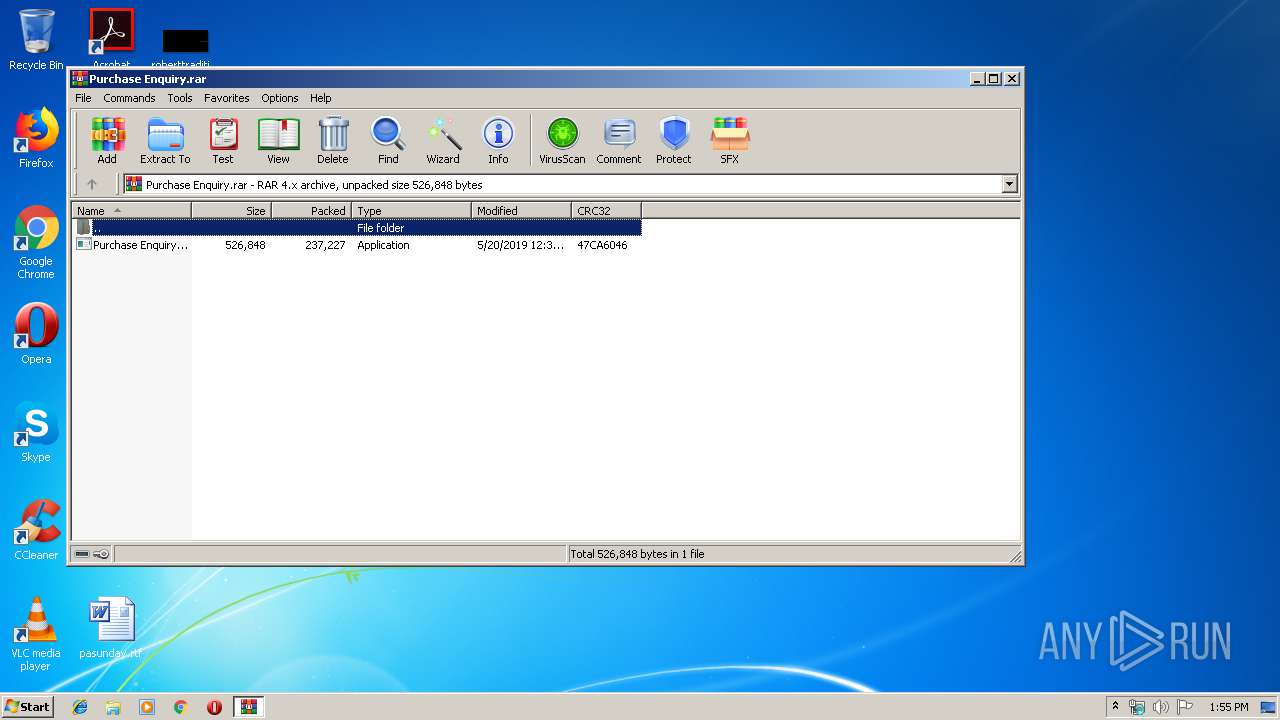
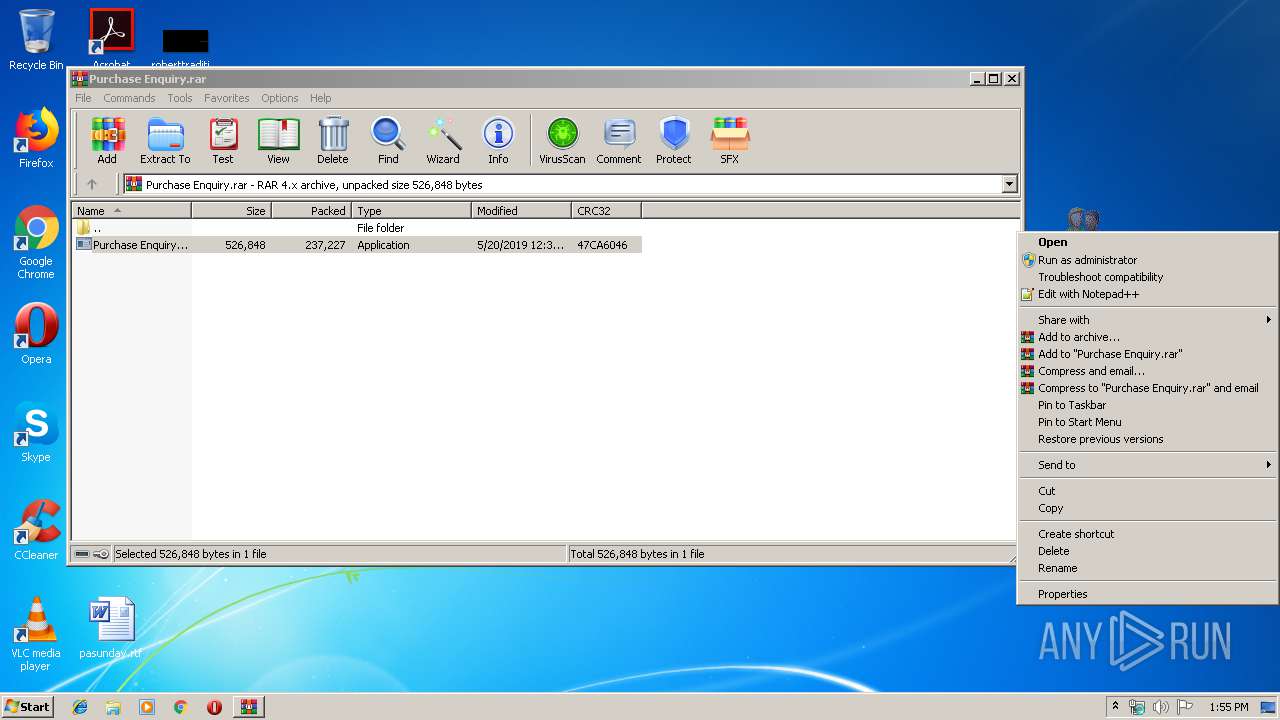
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 861E5C666A3078DE8E56BF54152DB1E1 |
| SHA1: | DC188840DC6C24D4F79F326DE8FC4CA393BA546F |
| SHA256: | BB58F89004B077ECC4D4185B7DE02A46ADA661174816C6ACDD6B2D5808DE6711 |
| SSDEEP: | 6144:R9tWci3PV8RaPmIfurmiExs5JAYXVz3Wcrnq+z:5Wc4V80mMurmwJBZGGq+z |
MALICIOUS
Application was dropped or rewritten from another process
- Purchase Enquiry.exe (PID: 2244)
- qzosn.exe (PID: 2340)
- qzosn.exe (PID: 3080)
Connects to CnC server
- qzosn.exe (PID: 3080)
Actions looks like stealing of personal data
- qzosn.exe (PID: 3080)
Writes to a start menu file
- qzosn.exe (PID: 2340)
Detected Pony/Fareit Trojan
- qzosn.exe (PID: 3080)
SUSPICIOUS
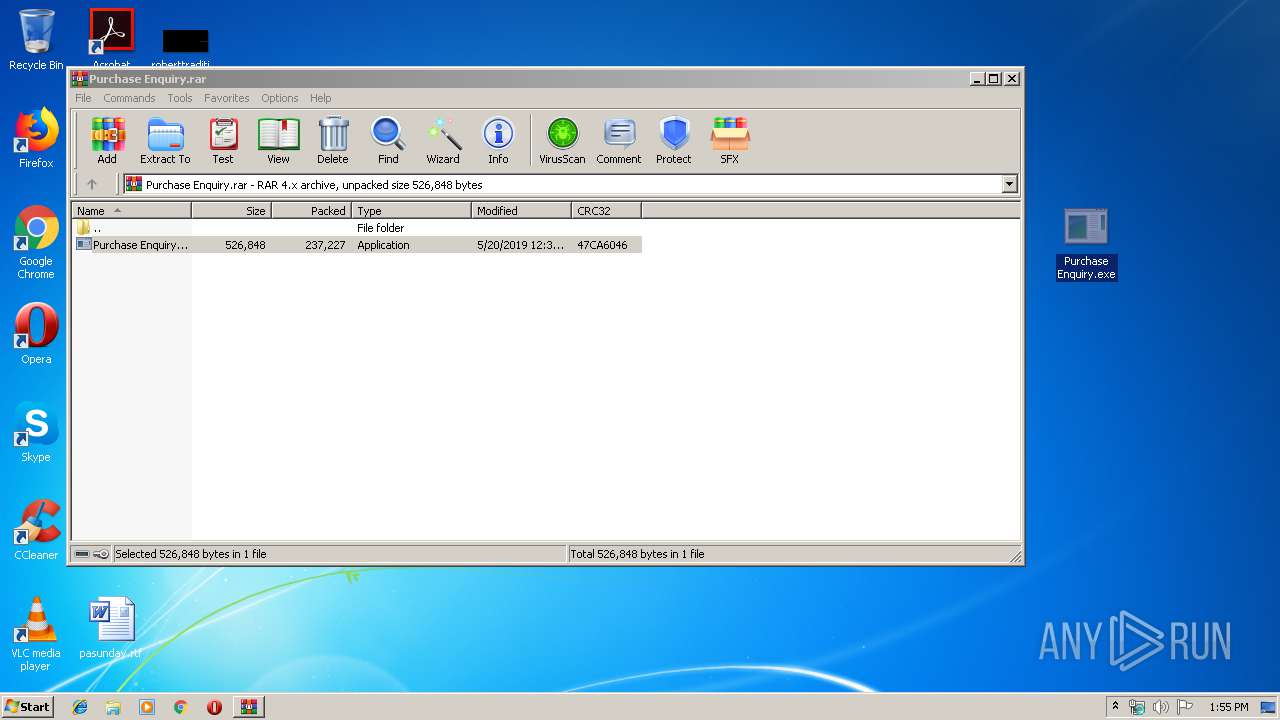
Starts itself from another location
- Purchase Enquiry.exe (PID: 2244)
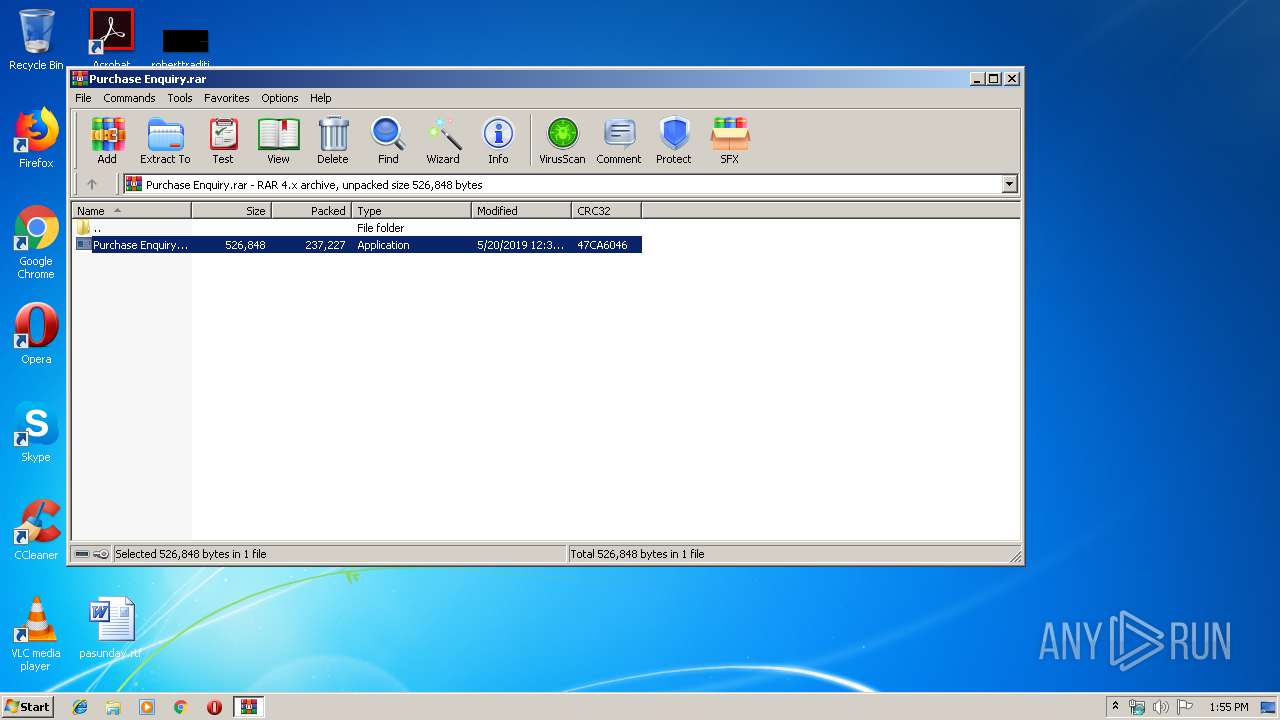
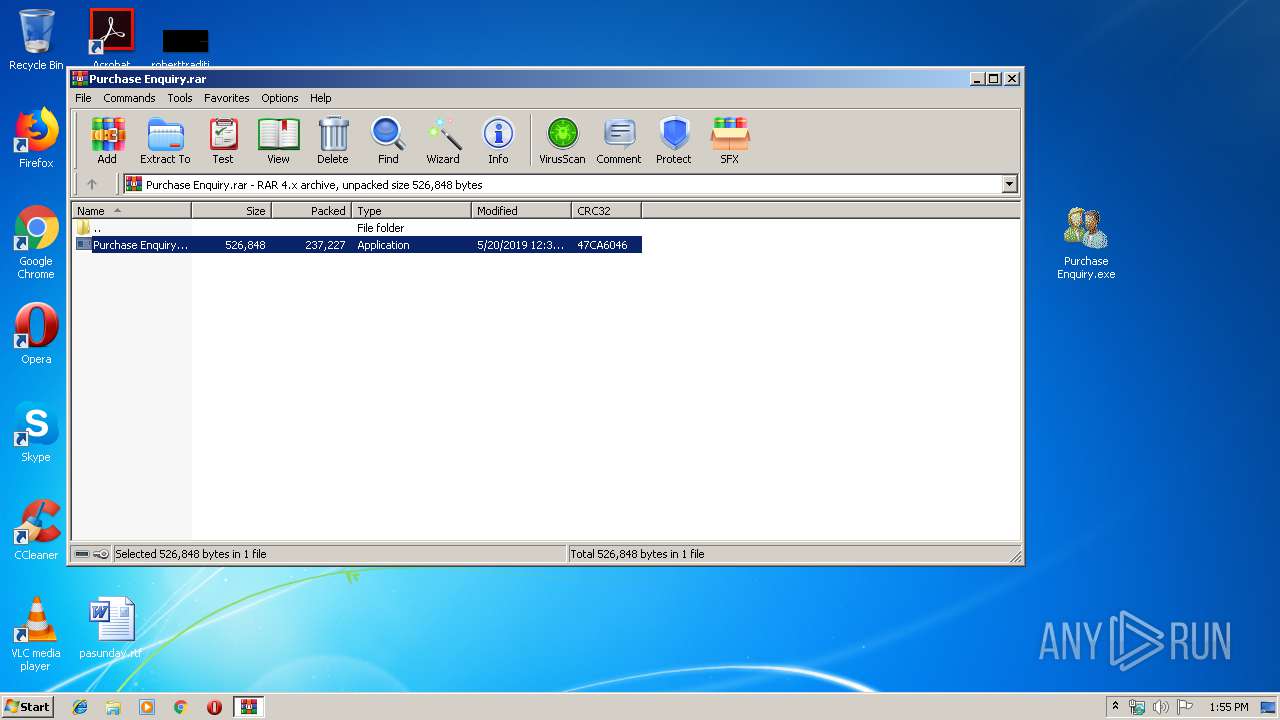
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2832)
- Purchase Enquiry.exe (PID: 2244)
Creates files in the user directory
- Purchase Enquiry.exe (PID: 2244)
- qzosn.exe (PID: 2340)
Starts CMD.EXE for commands execution
- qzosn.exe (PID: 3080)
Application launched itself
- qzosn.exe (PID: 2340)
Reads Internet Cache Settings
- qzosn.exe (PID: 3080)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 237268 |
|---|---|
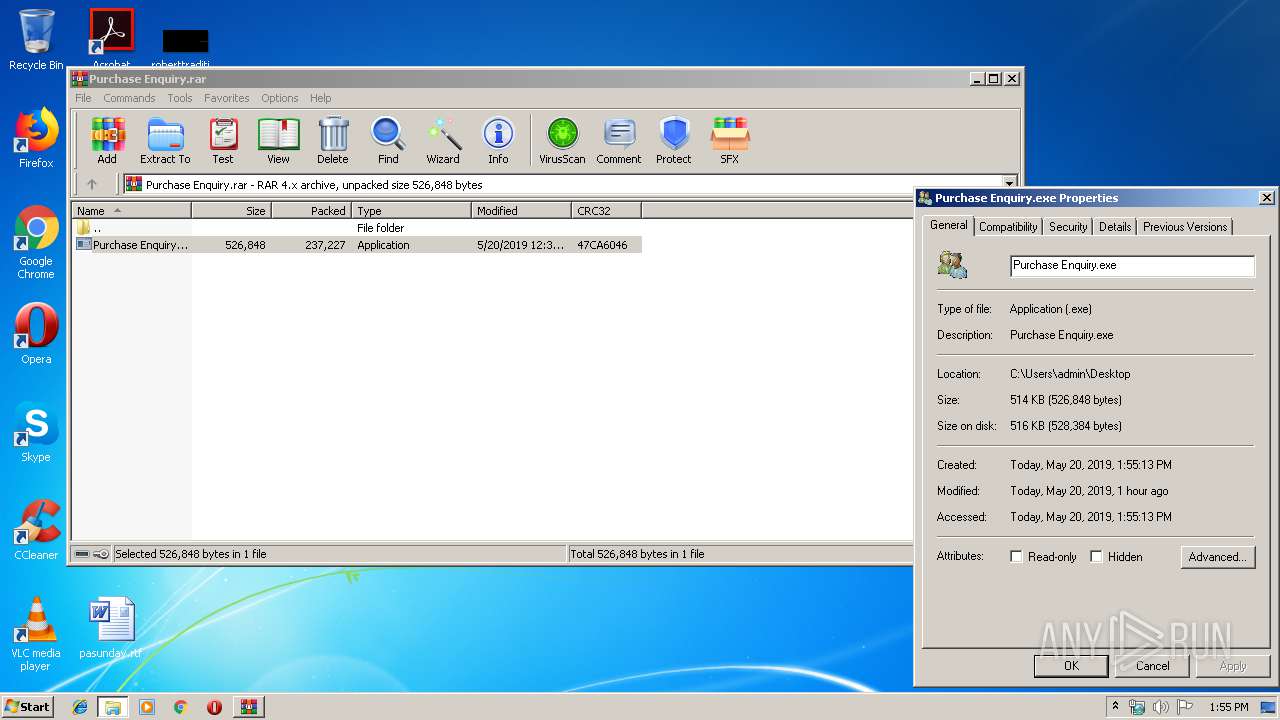
| UncompressedSize: | 526848 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2019:05:20 12:32:21 |
| PackingMethod: | Normal |
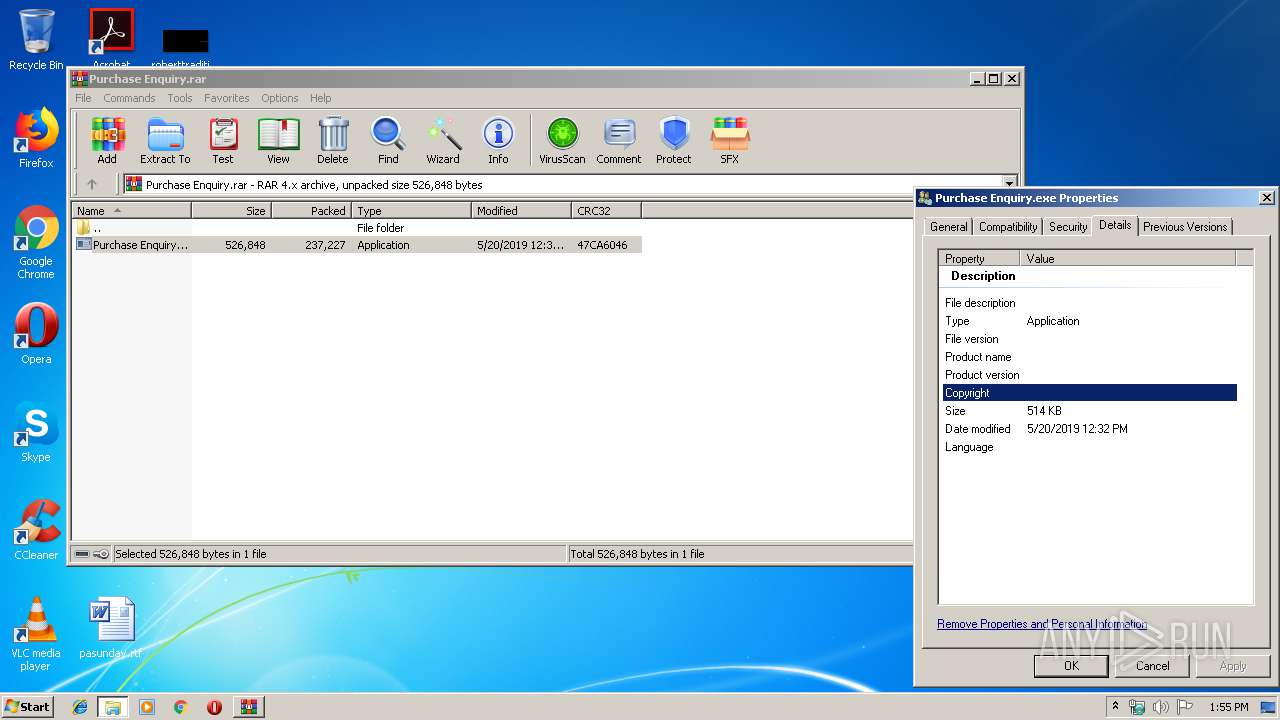
| ArchivedFileName: | Purchase Enquiry.exe |
Total processes
38
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2244 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2832.40872\Purchase Enquiry.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2832.40872\Purchase Enquiry.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\AppData\Roaming\obhn\qzosn.exe" | C:\Users\admin\AppData\Roaming\obhn\qzosn.exe | Purchase Enquiry.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2832 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Purchase Enquiry.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2880 | cmd /c ""C:\Users\admin\AppData\Local\Temp\1414328.bat" "C:\Users\admin\AppData\Roaming\obhn\qzosn.exe" " | C:\Windows\system32\cmd.exe | — | qzosn.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3080 | "C:\Users\admin\AppData\Roaming\obhn\qzosn.exe" | C:\Users\admin\AppData\Roaming\obhn\qzosn.exe | qzosn.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
813
Read events
795
Write events
18
Delete events
0
Modification events
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Purchase Enquiry.rar | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2832) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2832 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2832.41433\Purchase Enquiry.exe | — | |
MD5:— | SHA256:— | |||
| 2244 | Purchase Enquiry.exe | C:\Users\admin\AppData\Roaming\obhn\qzosn.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 2832 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2832.40872\Purchase Enquiry.exe | executable | |
MD5:— | SHA256:— | |||
| 3080 | qzosn.exe | C:\Users\admin\AppData\Local\Temp\1414328.bat | text | |
MD5:3880EEB1C736D853EB13B44898B718AB | SHA256:936D9411D5226B7C5A150ECAF422987590A8870C8E095E1CAA072273041A86E7 | |||
| 2340 | qzosn.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\obhn.vbs | text | |
MD5:— | SHA256:— | |||
| 2244 | Purchase Enquiry.exe | C:\Users\admin\AppData\Roaming\obhn\qzosn.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
4
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3080 | qzosn.exe | POST | 200 | 23.227.196.26:85 | http://gdres.tk:85/work/gate.php | US | text | 16 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3080 | qzosn.exe | 23.227.196.26:85 | gdres.tk | Swiftway Sp. z o.o. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gdres.tk |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3080 | qzosn.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
3080 | qzosn.exe | Potential Corporate Privacy Violation | ET POLICY Windows 98 User-Agent Detected - Possible Malware or Non-Updated System |
3080 | qzosn.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Internet Explorer Version MSIE 5. |
3080 | qzosn.exe | A Network Trojan was detected | ET TROJAN Trojan Generic - POST To gate.php with no referer |
3080 | qzosn.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3080 | qzosn.exe | A Network Trojan was detected | ET TROJAN Pony Downloader HTTP Library MSIE 5 Win98 |
3080 | qzosn.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony Downloader Checkin |
3080 | qzosn.exe | Potentially Bad Traffic | ET TROJAN Generic -POST To gate.php w/Extended ASCII Characters (Likely Zeus Derivative) |
3080 | qzosn.exe | A Network Trojan was detected | ET TROJAN Pony Downloader check-in response STATUS-IMPORT-OK |