| File name: | ba |
| Full analysis: | https://app.any.run/tasks/9ce3af6b-446c-4a99-b759-654e22d77e3b |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
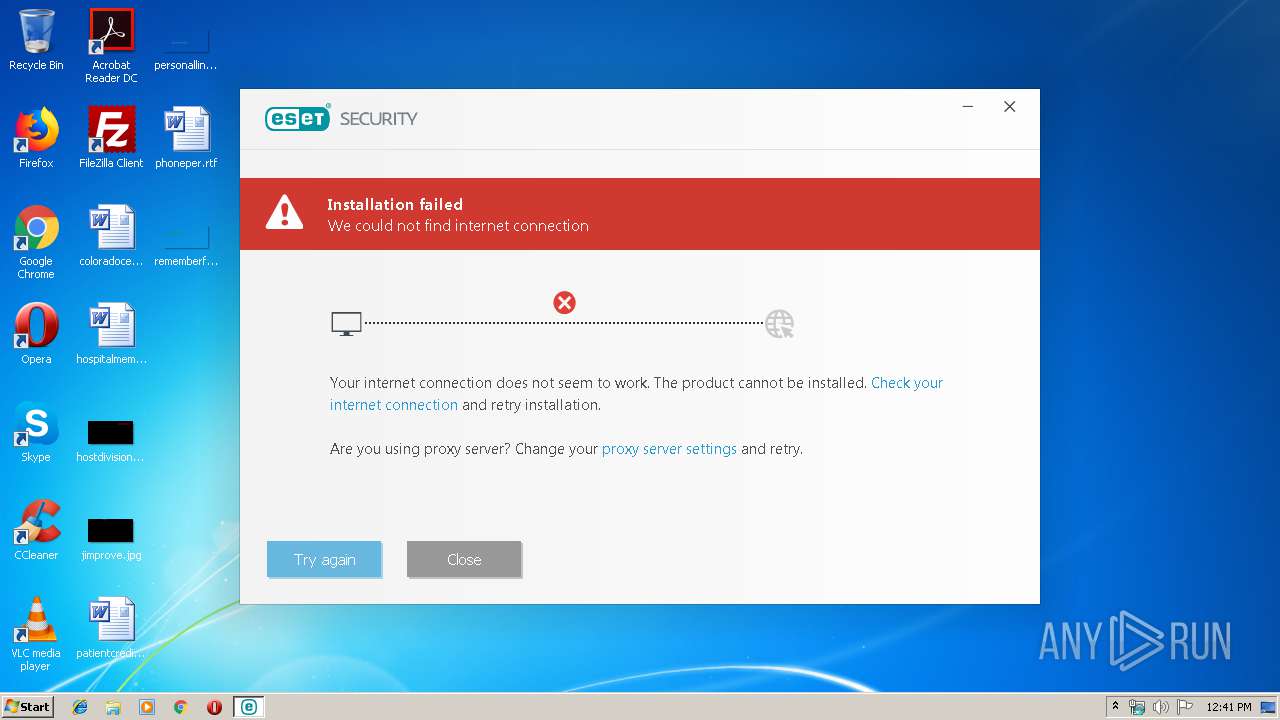
| Analysis date: | December 06, 2019, 12:41:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 8A2F7A4227679C0028288796A25A7274 |
| SHA1: | D6A2982E3B57991F1ECFA668DB241348E005B345 |
| SHA256: | BAFBD1C06DB40DD644351CFCE23C4E93C85848398C8D03ED09C7F0D0AA0E7543 |
| SSDEEP: | 3072:10R5CJPb7U0NQZ3Qh0UkJqsDQMq6f4LjB01o+mhhajwOXF2i3z00IHbRLB:eR5CJXNqgh0U8XznajB01o/ajYij00Iv |
MALICIOUS
Application was dropped or rewritten from another process
- eset_nod32_antivirus_live_installer.exe (PID: 2848)
- eset_nod32_antivirus_live_installer.exe (PID: 3728)
- BootHelper.exe (PID: 3580)
Changes the Startup folder
- REG.exe (PID: 3196)
AMADEY was detected
- ba.exe (PID: 2124)
- vbcoon.exe (PID: 2912)
Loads dropped or rewritten executable
- eset_nod32_antivirus_live_installer.exe (PID: 3728)
Connects to CnC server
- vbcoon.exe (PID: 2912)
SUSPICIOUS
Executable content was dropped or overwritten
- ba.exe (PID: 2124)
- eset_nod32_antivirus_live_installer.exe (PID: 2848)
- vbcoon.exe (PID: 2912)
- eset_nod32_antivirus_live_installer.exe (PID: 3728)
Starts itself from another location
- ba.exe (PID: 2124)
Creates files in the program directory
- ba.exe (PID: 2124)
Uses REG.EXE to modify Windows registry
- vbcoon.exe (PID: 2912)
Connects to server without host name
- vbcoon.exe (PID: 2912)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (39.5) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (38.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.4) |
| .exe | | | Win32 Executable (generic) (6.4) |
| .exe | | | Generic Win/DOS Executable (2.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:02 12:53:36+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 167936 |
| InitializedDataSize: | 53248 |
| UninitializedDataSize: | 147456 |
| EntryPoint: | 0x4d030 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.2.8.6 |
| ProductVersionNumber: | 7.2.8.6 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Sopcast |
| PrivateBuild: | 7.2.8.6 |
| Languages: | English |
| FileDescription: | Prohibit Encouraging Exceptiondispatch Economy Linqs |
| Comments: | Prohibit Encouraging Exceptiondispatch Economy Linqs |
| ProductName: | Infosets |
| LegalCopyright: | Sopcast Copyright (c) 2014 - . All rights reserved. |
| ProductVersion: | 7.2.8.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Dec-2019 11:53:36 |
| Detected languages: |
|
| CompanyName: | Sopcast |
| PrivateBuild: | 7.2.8.6 |
| Languages: | English |
| FileDescription: | Prohibit Encouraging Exceptiondispatch Economy Linqs |
| Comments: | Prohibit Encouraging Exceptiondispatch Economy Linqs |
| ProductName: | Infosets |
| LegalCopyright: | Sopcast Copyright (c) 2014 - . All rights reserved. |
| ProductVersion: | 7.2.8.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 02-Dec-2019 11:53:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00024000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00025000 | 0x00029000 | 0x00028400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.84426 |
.rsrc | 0x0004E000 | 0x0000D000 | 0x0000C400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.76221 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.14589 | 864 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.80529 | 11432 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.32387 | 5672 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.57887 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.27569 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 6.37118 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.92246 | 90 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
383 | 7.73526 | 8515 | Latin 1 / Western European | English - United States | 800 |
412 | 7.88893 | 15808 | Latin 1 / Western European | English - United States | TEMPLATES |
413 | 7.84744 | 10405 | Latin 1 / Western European | English - United States | TEMPLATES |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
GLU32.dll |
KERNEL32.DLL |
NETAPI32.dll |
OLEAUT32.dll |
OPENGL32.dll |
RASAPI32.dll |
Total processes
43
Monitored processes
6
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2124 | "C:\Users\admin\AppData\Local\Temp\ba.exe" | C:\Users\admin\AppData\Local\Temp\ba.exe | explorer.exe | ||||||||||||
User: admin Company: Sopcast Integrity Level: MEDIUM Description: Prohibit Encouraging Exceptiondispatch Economy Linqs Exit code: 0 Modules
| |||||||||||||||
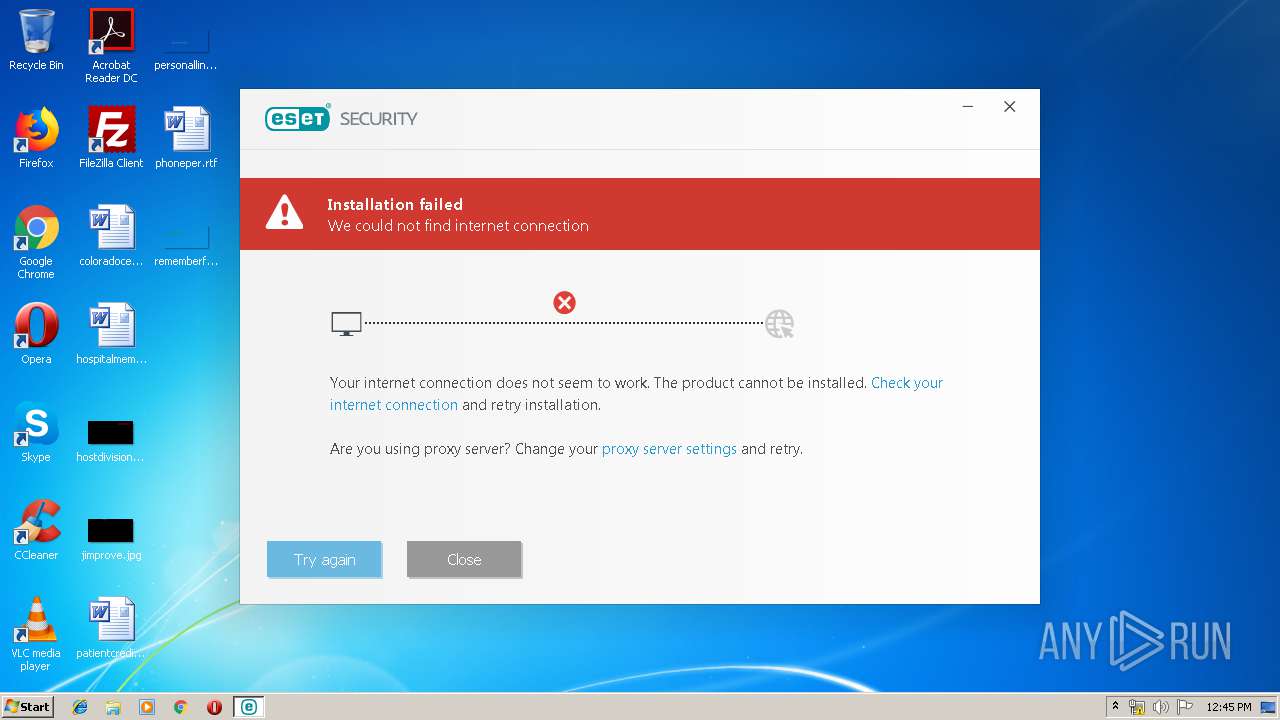
| 2848 | C:\Users\admin\AppData\Local\Temp\eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset_nod32_antivirus_live_installer.exe | vbcoon.exe | ||||||||||||
User: admin Company: ESET Integrity Level: MEDIUM Description: ESET Live Installer Exit code: 0 Version: 10.10.58.0 Modules
| |||||||||||||||
| 2912 | c:\programdata\0555a0d867\vbcoon.exe | c:\programdata\0555a0d867\vbcoon.exe | ba.exe | ||||||||||||
User: admin Company: Sopcast Integrity Level: MEDIUM Description: Prohibit Encouraging Exceptiondispatch Economy Linqs Exit code: 0 Modules
| |||||||||||||||
| 3196 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders" /f /v Startup /t REG_SZ /d C:\ProgramData\0555a0d867 | C:\Windows\system32\REG.exe | vbcoon.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3580 | BootHelper.exe --watchdog 3728 --product "ESET Live Installer" 13.0.4.0 1033 | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-B3D7-667A-B4DE-28CDAD2B36F2}\BootHelper.exe | — | eset_nod32_antivirus_live_installer.exe | |||||||||||
User: admin Company: ESET Integrity Level: HIGH Description: ESET Live Installer Exit code: 0 Version: 10.10.58.0 Modules
| |||||||||||||||
| 3728 | "C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-B3D7-667A-B4DE-28CDAD2B36F2}\eset_nod32_antivirus_live_installer.exe" --bts-container 2848 "C:\Users\admin\AppData\Local\Temp\eset_nod32_antivirus_live_installer.exe" | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-B3D7-667A-B4DE-28CDAD2B36F2}\eset_nod32_antivirus_live_installer.exe | eset_nod32_antivirus_live_installer.exe | ||||||||||||
User: admin Company: ESET Integrity Level: HIGH Description: ESET Live Installer Exit code: 0 Version: 10.10.58.0 Modules
| |||||||||||||||
Total events
500
Read events
446
Write events
54
Delete events
0
Modification events
| (PID) Process: | (2124) ba.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ba_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2124) ba.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ba_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2124) ba.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ba_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2124) ba.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ba_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2124) ba.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ba_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2124) ba.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ba_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2912) vbcoon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vbcoon_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2912) vbcoon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vbcoon_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2912) vbcoon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vbcoon_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2912) vbcoon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vbcoon_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
10
Suspicious files
1
Text files
87
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2124 | ba.exe | C:\ProgramData\0 | — | |
MD5:— | SHA256:— | |||
| 2124 | ba.exe | C:\programdata\0555a0d867\vbcoon.exe:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2912 | vbcoon.exe | C:\ProgramData\0 | — | |
MD5:— | SHA256:— | |||
| 2912 | vbcoon.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2912 | vbcoon.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\eset_nod32_antivirus_live_installer[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2848 | eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-B3D7-667A-B4DE-28CDAD2B36F2}\eset_nod32_antivirus_live_installer.exe | executable | |
MD5:— | SHA256:— | |||
| 3728 | eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-B3D7-667A-B4DE-28CDAD2B36F2}\.res\main\CommonCSY.xml | xml | |
MD5:— | SHA256:— | |||
| 3728 | eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-B3D7-667A-B4DE-28CDAD2B36F2}\.erm\epi-base.zip | compressed | |
MD5:— | SHA256:— | |||
| 3728 | eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-B3D7-667A-B4DE-28CDAD2B36F2}\.res\main\CommonARE.xml | xml | |
MD5:— | SHA256:— | |||
| 3728 | eset_nod32_antivirus_live_installer.exe | C:\Users\admin\AppData\Local\Temp\eset\bts.session\{02D83BBE-B3D7-667A-B4DE-28CDAD2B36F2}\.res\main\CommonBGR.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
7
DNS requests
2
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2912 | vbcoon.exe | POST | 200 | 217.8.117.61:80 | http://217.8.117.61/index.php | unknown | — | — | malicious |
2912 | vbcoon.exe | POST | 200 | 217.8.117.61:80 | http://217.8.117.61/index.php | unknown | text | 124 b | malicious |
3728 | eset_nod32_antivirus_live_installer.exe | GET | 200 | 91.228.167.125:80 | http://iploc.eset.com:80/ip_locate_iso2 | SK | xml | 248 b | whitelisted |
2912 | vbcoon.exe | POST | 200 | 217.8.117.61:80 | http://217.8.117.61/index.php | unknown | text | 6 b | malicious |
2912 | vbcoon.exe | POST | 200 | 217.8.117.61:80 | http://217.8.117.61/index.php | unknown | text | 6 b | malicious |
2912 | vbcoon.exe | POST | 200 | 217.8.117.61:80 | http://217.8.117.61/index.php | unknown | text | 6 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2912 | vbcoon.exe | 217.8.117.61:80 | — | — | — | malicious |
2912 | vbcoon.exe | 91.228.167.110:443 | download.eset.com | ESET, spol. s r.o. | SK | suspicious |
3728 | eset_nod32_antivirus_live_installer.exe | 91.228.167.125:80 | iploc.eset.com | ESET, spol. s r.o. | SK | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.eset.com |
| whitelisted |
iploc.eset.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2912 | vbcoon.exe | A Network Trojan was detected | ET TROJAN Amadey CnC Check-In |
2912 | vbcoon.exe | A Network Trojan was detected | AV TROJAN Agent.DHOA System Info Exfiltration |
2912 | vbcoon.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2912 | vbcoon.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2912 | vbcoon.exe | A Network Trojan was detected | ET TROJAN Amadey CnC Check-In |
2912 | vbcoon.exe | A Network Trojan was detected | AV TROJAN Agent.DHOA System Info Exfiltration |
2912 | vbcoon.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2912 | vbcoon.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2912 | vbcoon.exe | A Network Trojan was detected | ET TROJAN Amadey CnC Check-In |
2912 | vbcoon.exe | A Network Trojan was detected | AV TROJAN Agent.DHOA System Info Exfiltration |
2 ETPRO signatures available at the full report