| File name: | id65gv.exe |
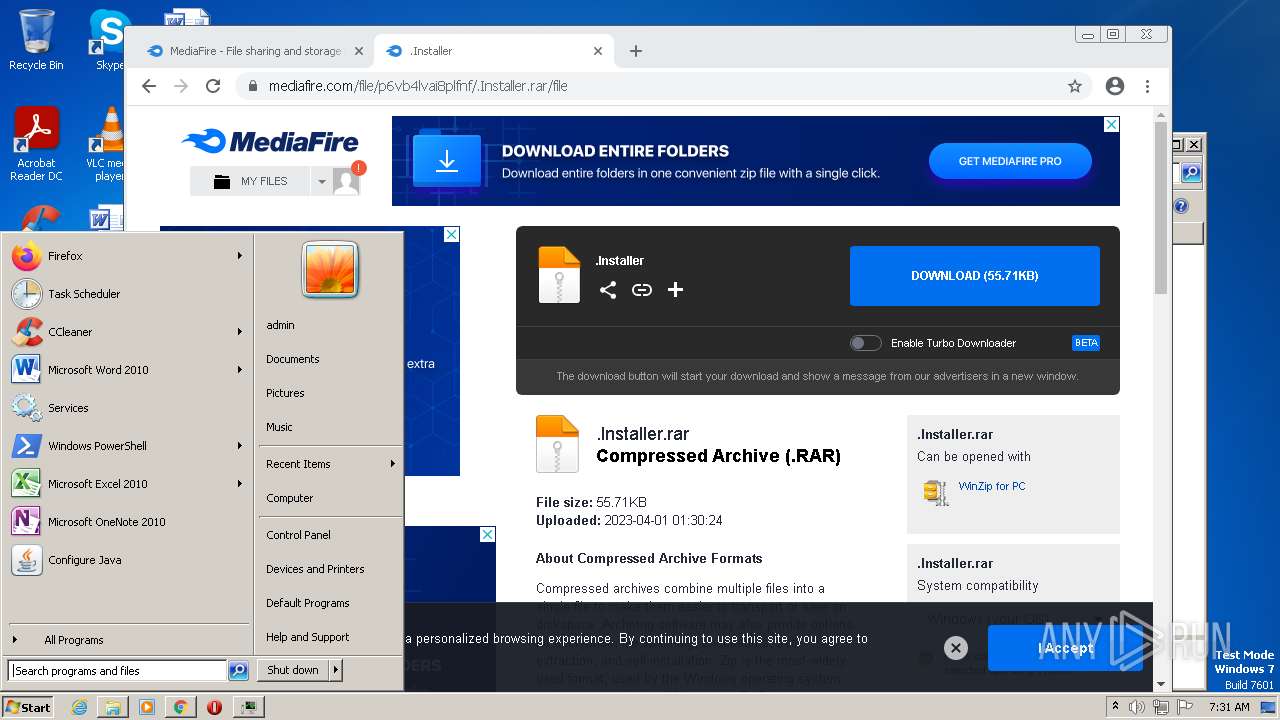
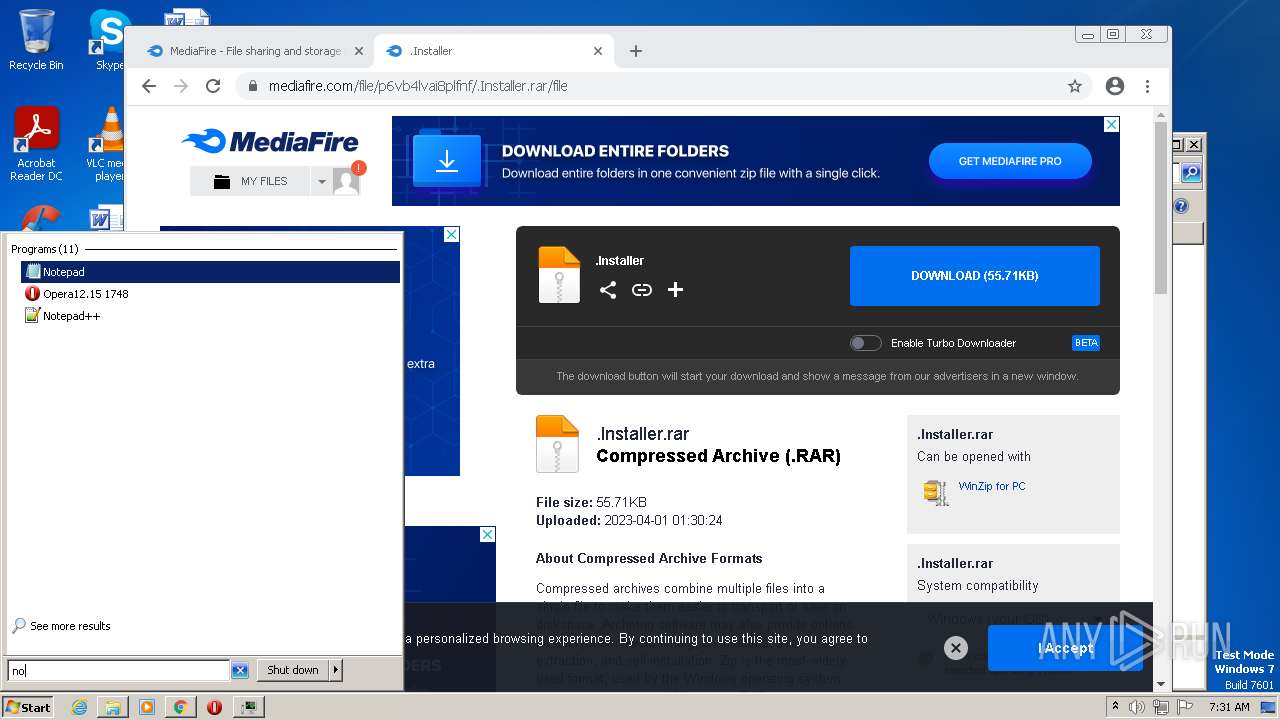
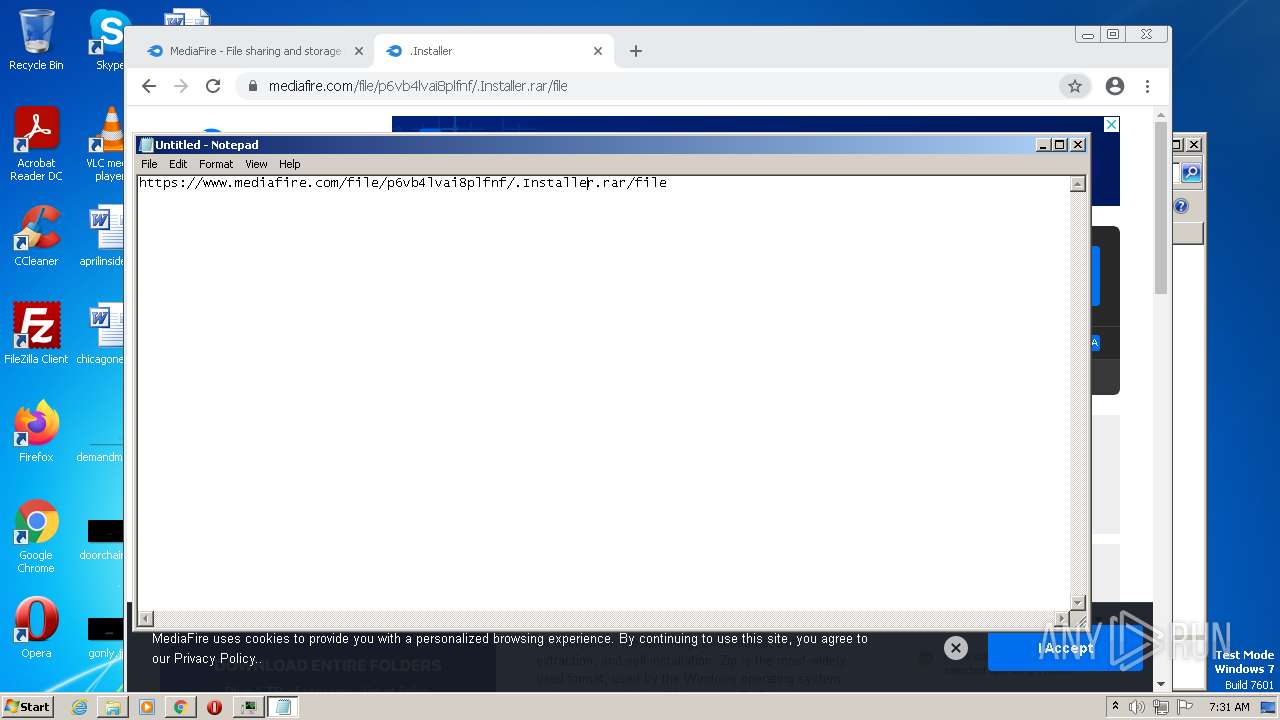
| Full analysis: | https://app.any.run/tasks/7b17151b-c5dd-4dc5-966b-a3f051460217 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 01, 2023, 06:27:04 |
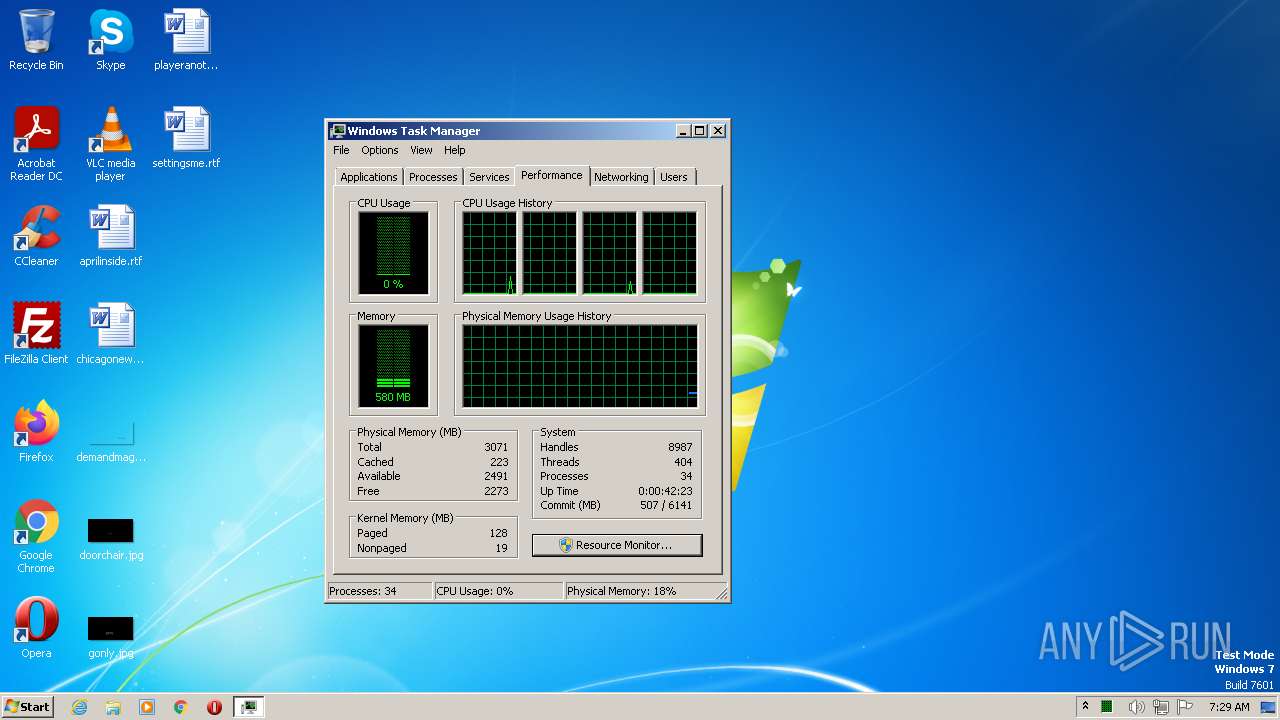
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 101023D30C7A9ABCBC6215D42DFF4C37 |
| SHA1: | F14A2E8943D48418D0C6C07516C5886483E6E5D7 |
| SHA256: | B93B6F677A941B530DBEC8B1ABE68C75315D2C1F536D21AF726274810C2A10D6 |
| SSDEEP: | 3072:ubOKrClE0kow0sERAeumu+tDryuYOn6GLKdV7k30P+Gborp42xL:ubOKrClE0sGyy6na0lboBL |
MALICIOUS
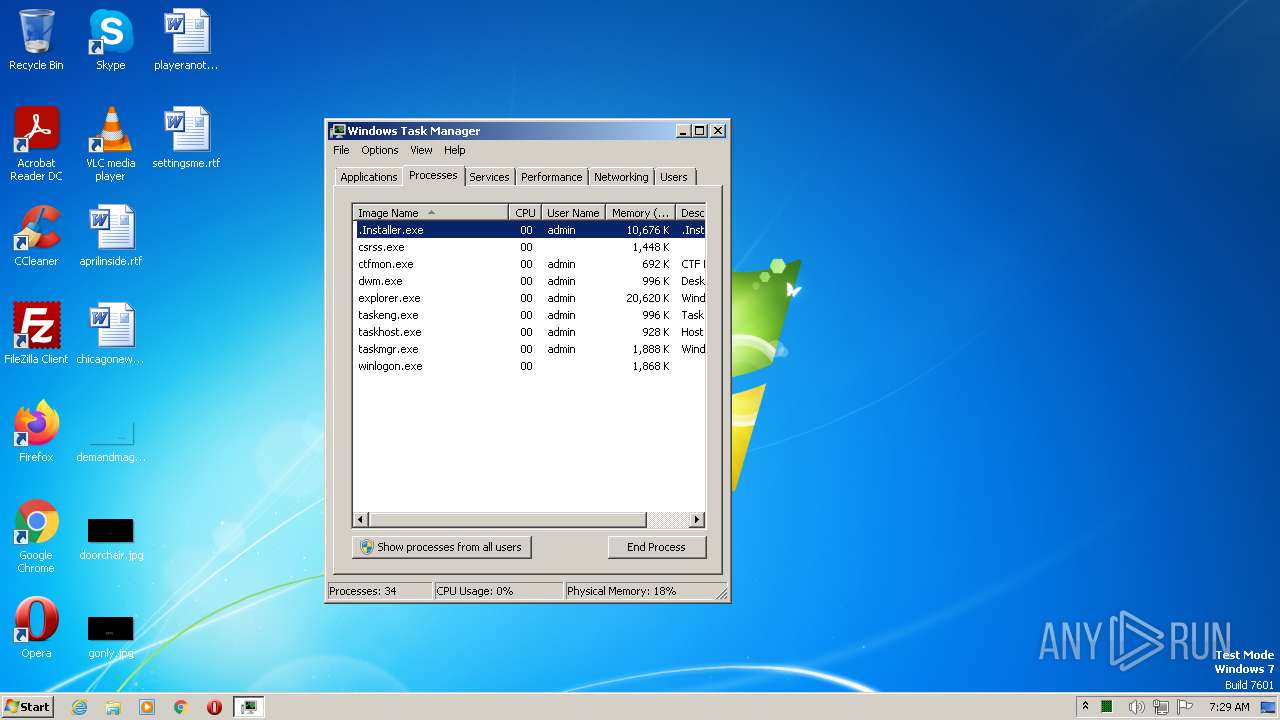
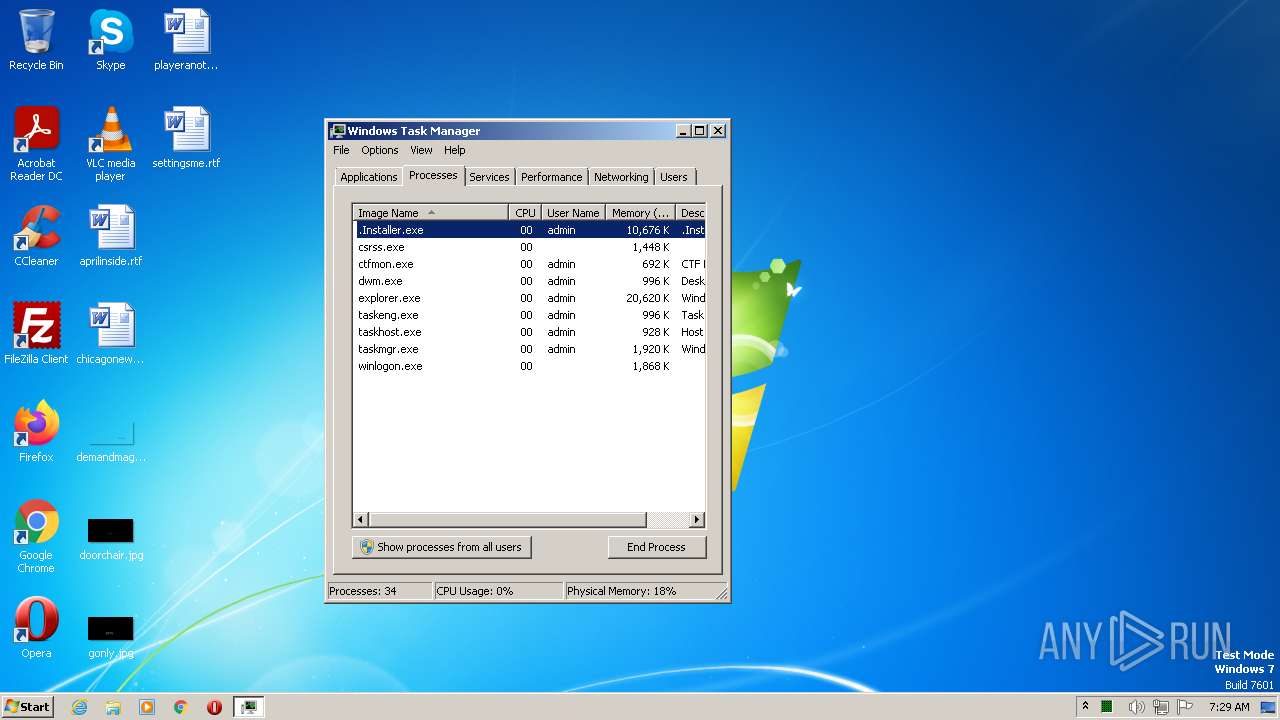
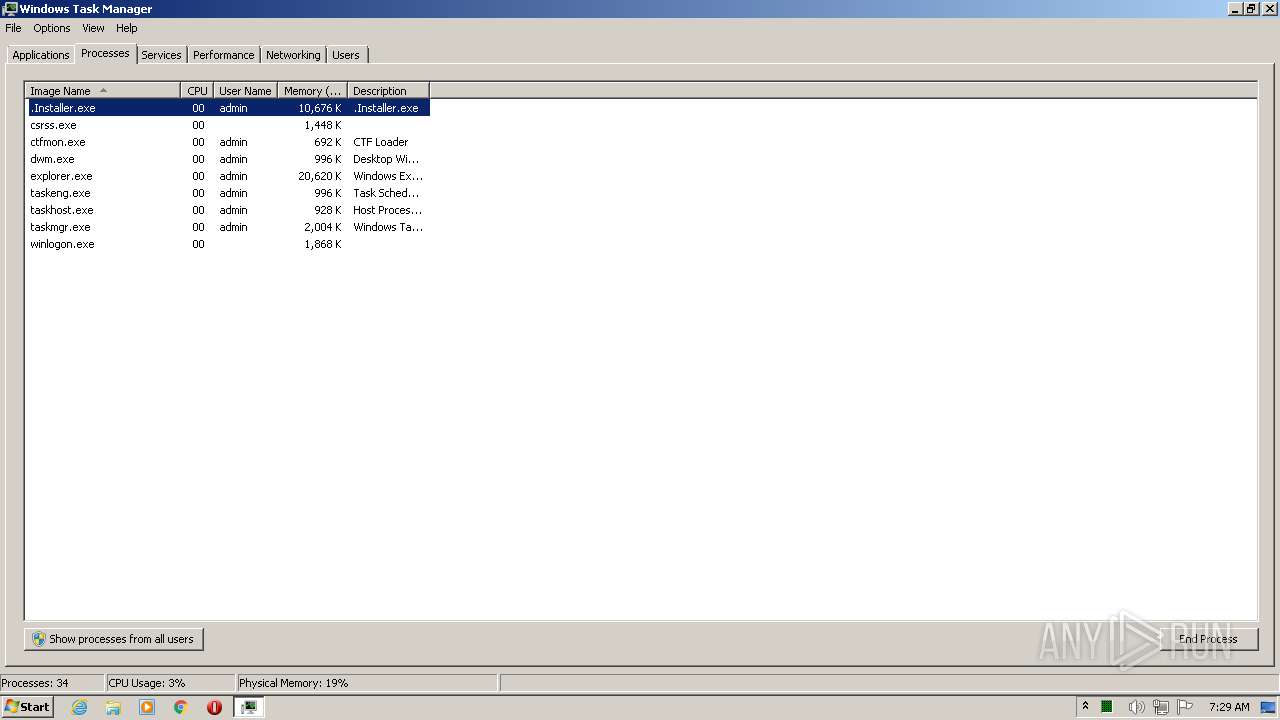
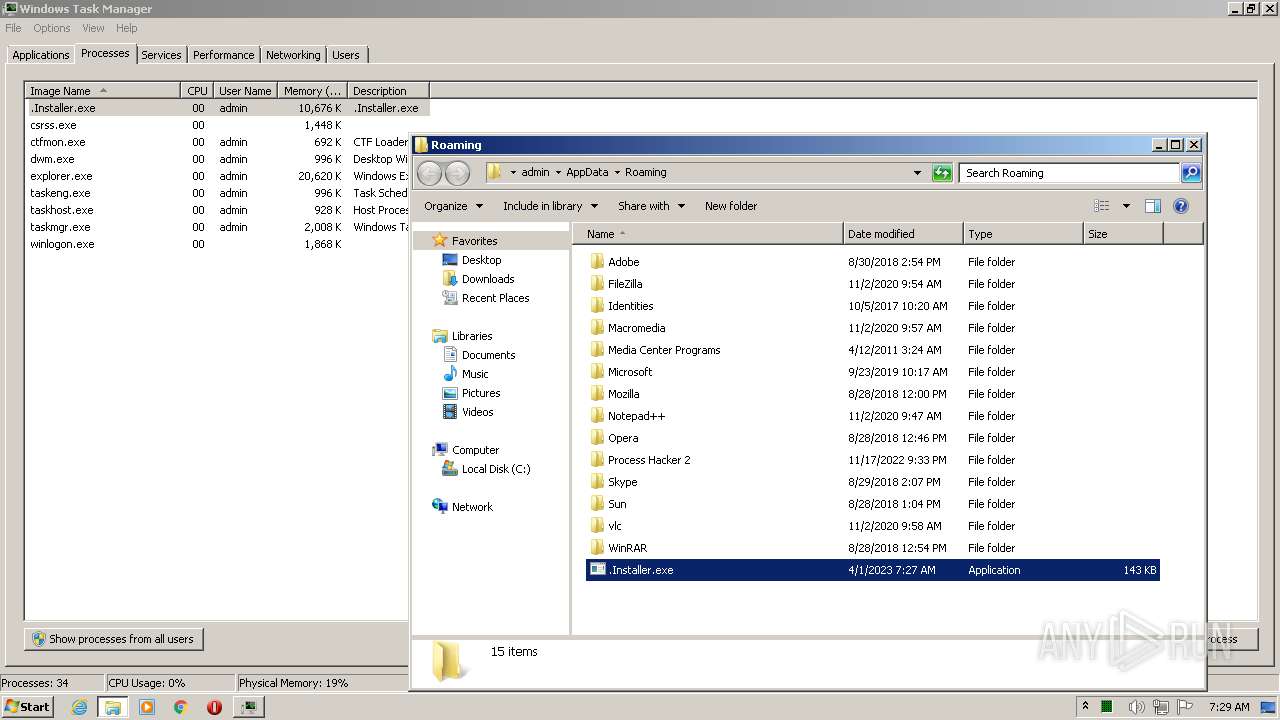
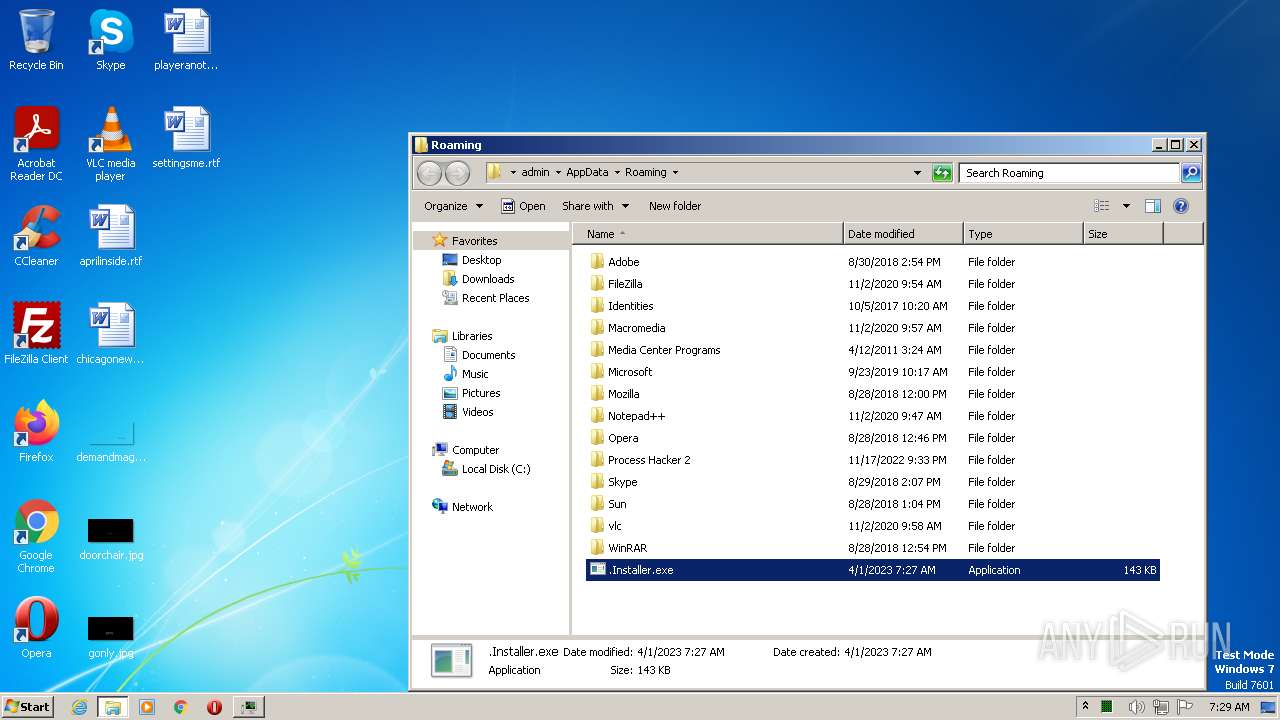
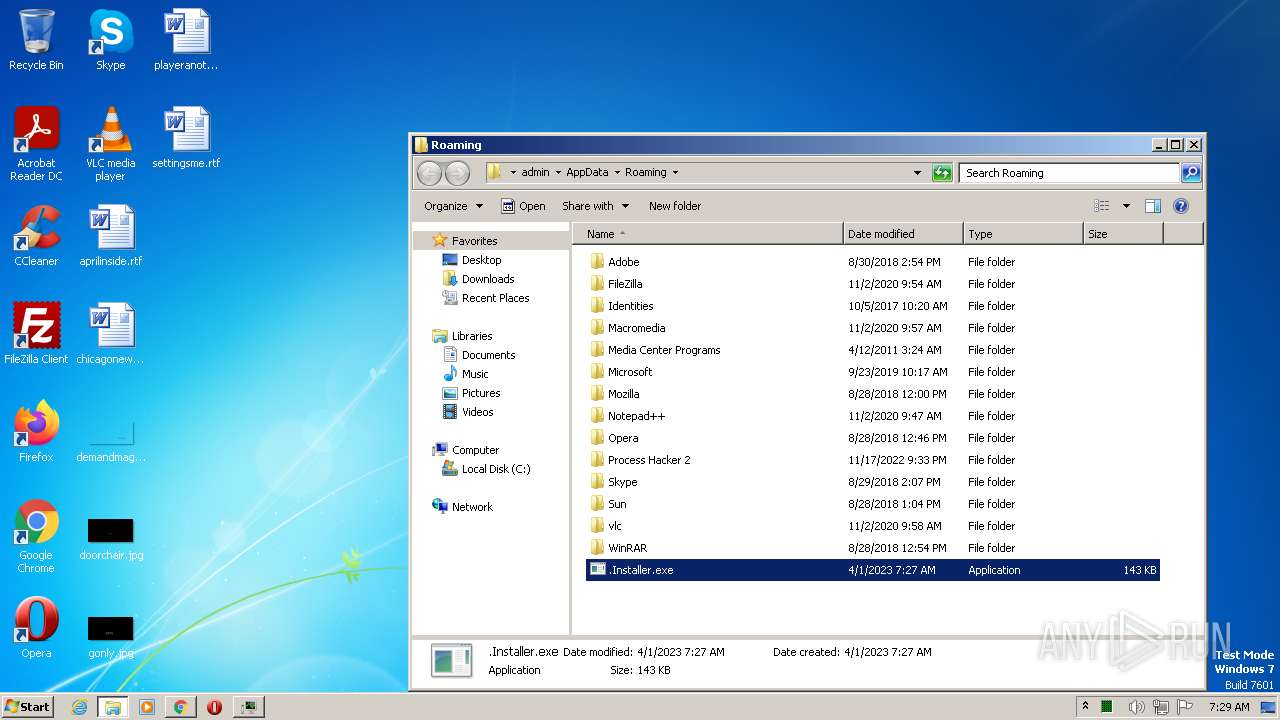
ASYNCRAT detected by memory dumps
- .Installer.exe (PID: 3848)
SUSPICIOUS
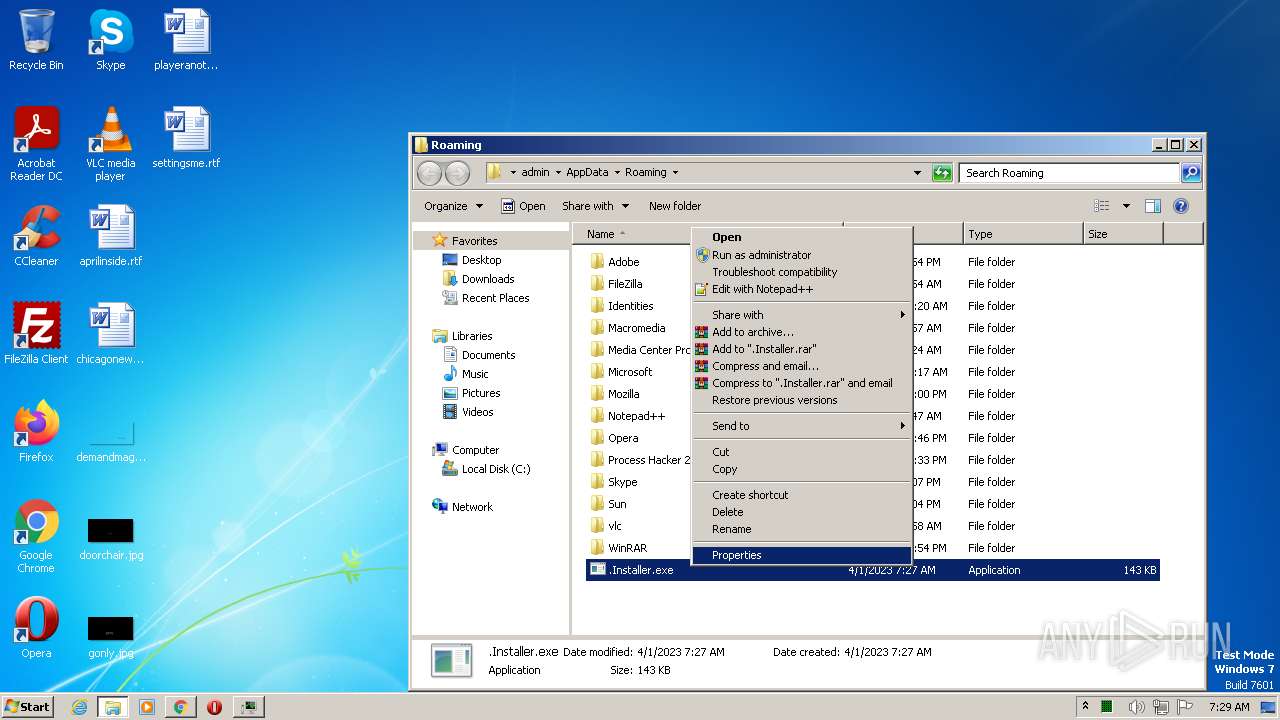
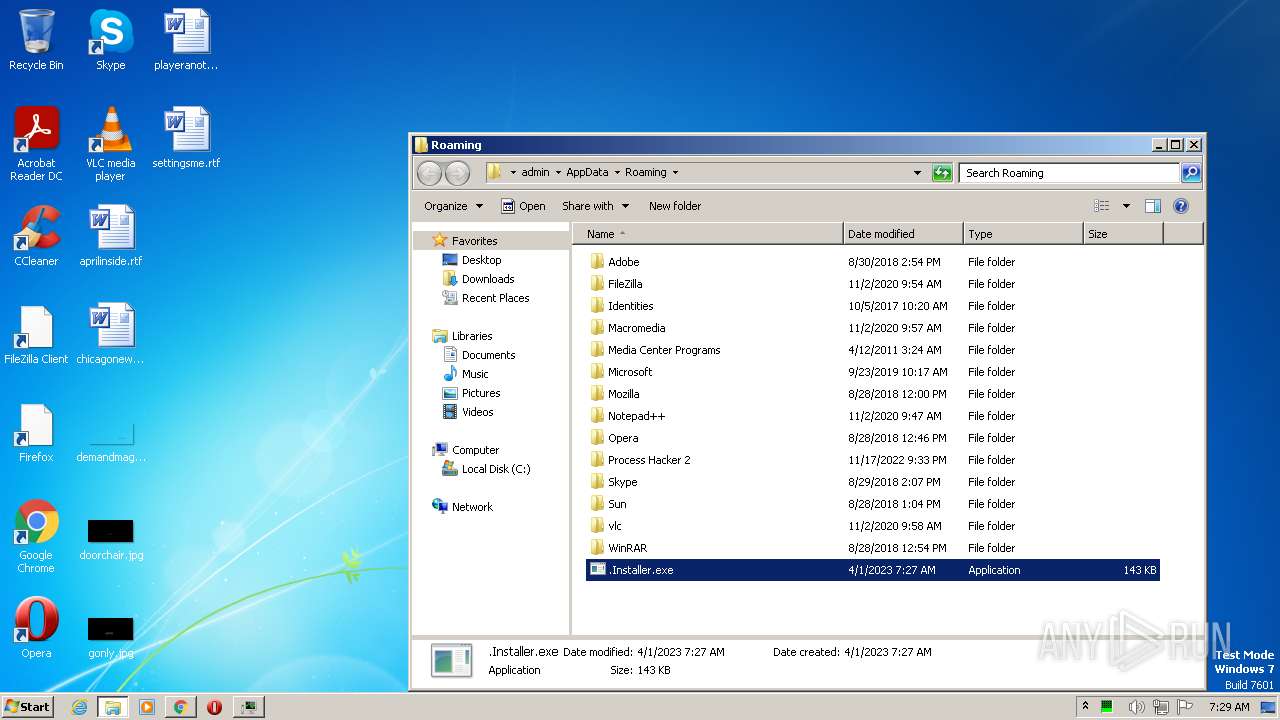
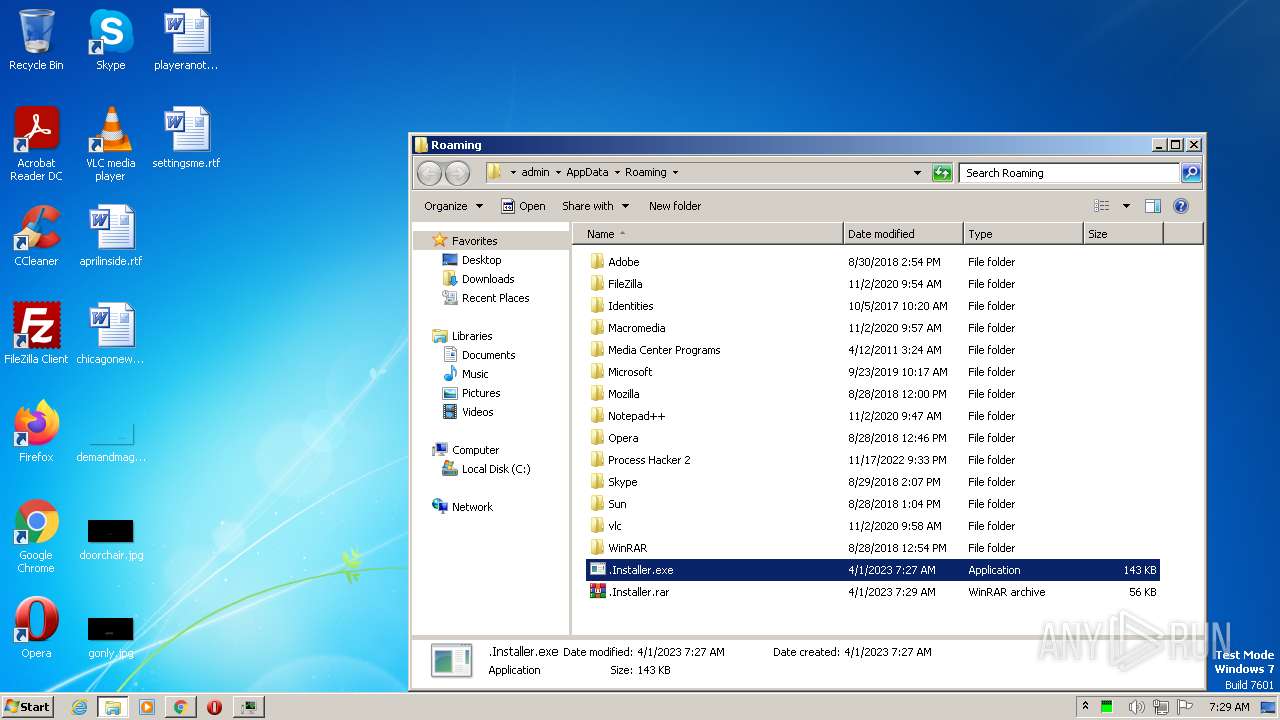
Executable content was dropped or overwritten
- id65gv.exe (PID: 2688)
Starts CMD.EXE for commands execution
- id65gv.exe (PID: 2688)
Executing commands from a ".bat" file
- id65gv.exe (PID: 2688)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3428)
Reads settings of System Certificates
- .Installer.exe (PID: 3848)
Reads the Internet Settings
- .Installer.exe (PID: 3848)
Connects to unusual port
- .Installer.exe (PID: 3848)
INFO
Checks supported languages
- id65gv.exe (PID: 2688)
- .Installer.exe (PID: 3848)
- wmpnscfg.exe (PID: 2840)
Reads the machine GUID from the registry
- id65gv.exe (PID: 2688)
- .Installer.exe (PID: 3848)
- wmpnscfg.exe (PID: 2840)
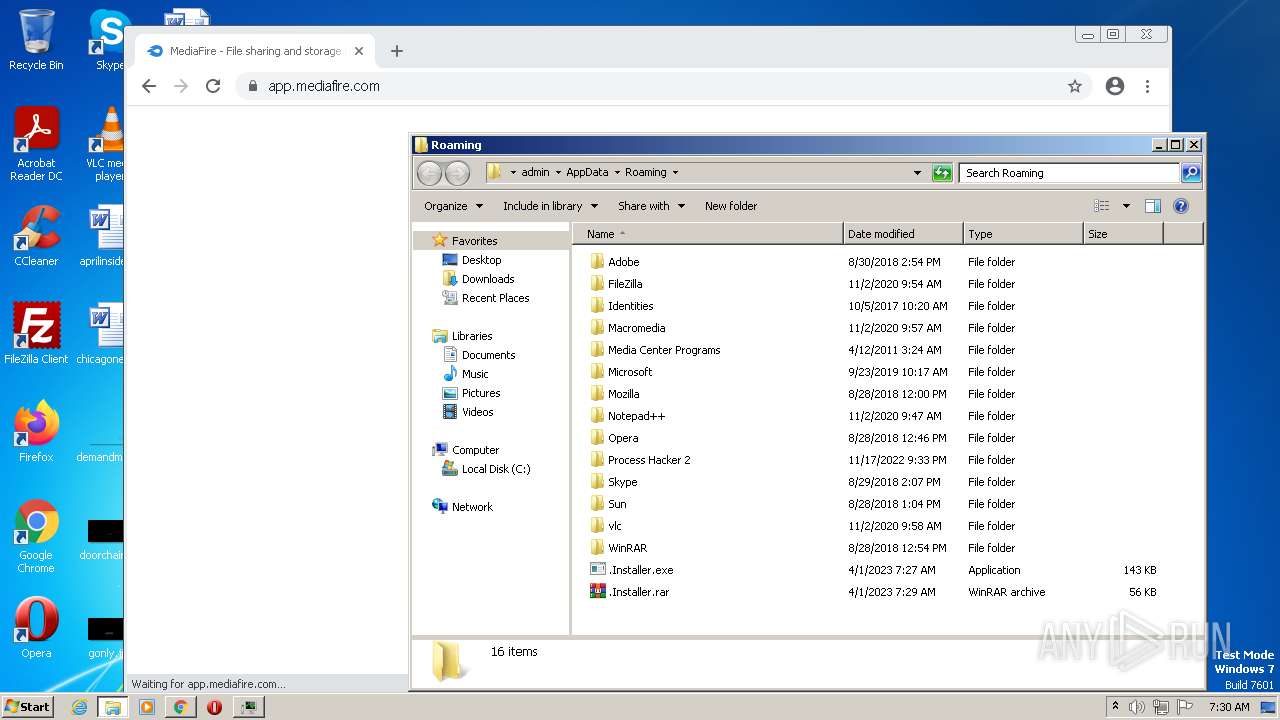
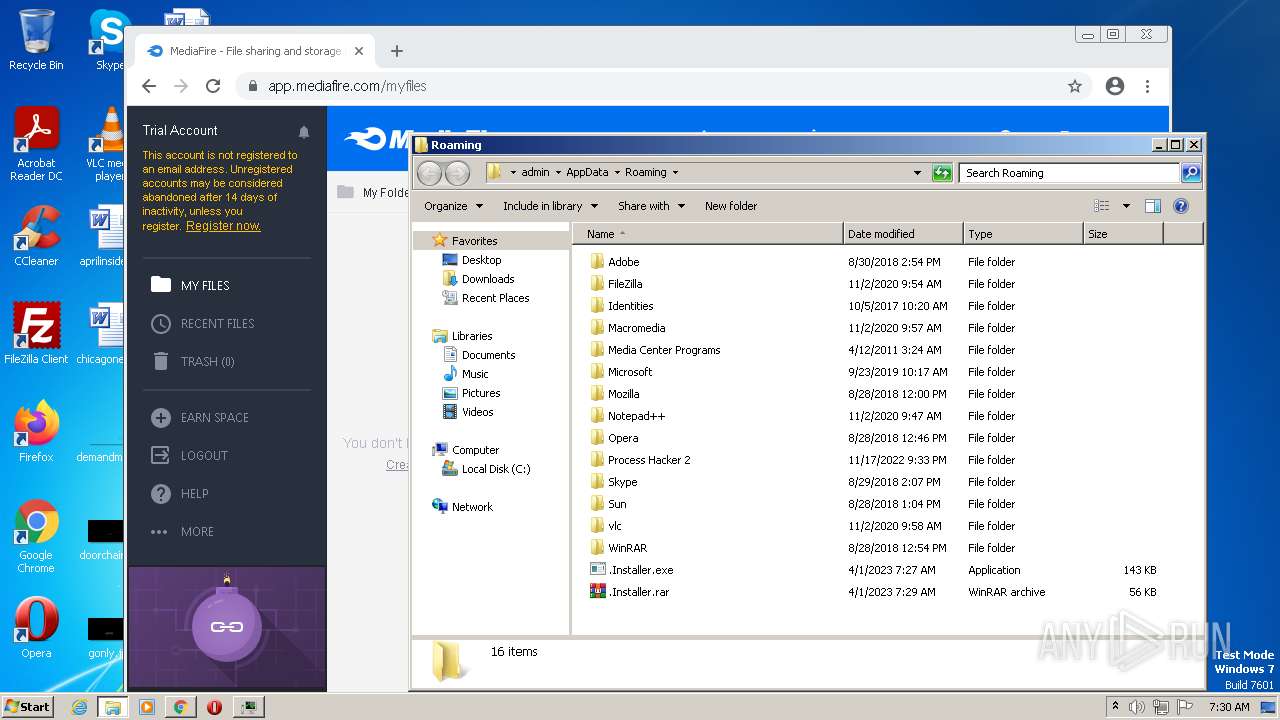
Creates files or folders in the user directory
- id65gv.exe (PID: 2688)
The process checks LSA protection
- id65gv.exe (PID: 2688)
- .Installer.exe (PID: 3848)
- wmpnscfg.exe (PID: 2840)
- taskmgr.exe (PID: 1436)
Create files in a temporary directory
- id65gv.exe (PID: 2688)
- chrome.exe (PID: 2824)
- chrome.exe (PID: 2300)
Reads the computer name
- .Installer.exe (PID: 3848)
- id65gv.exe (PID: 2688)
- wmpnscfg.exe (PID: 2840)
Reads Environment values
- .Installer.exe (PID: 3848)
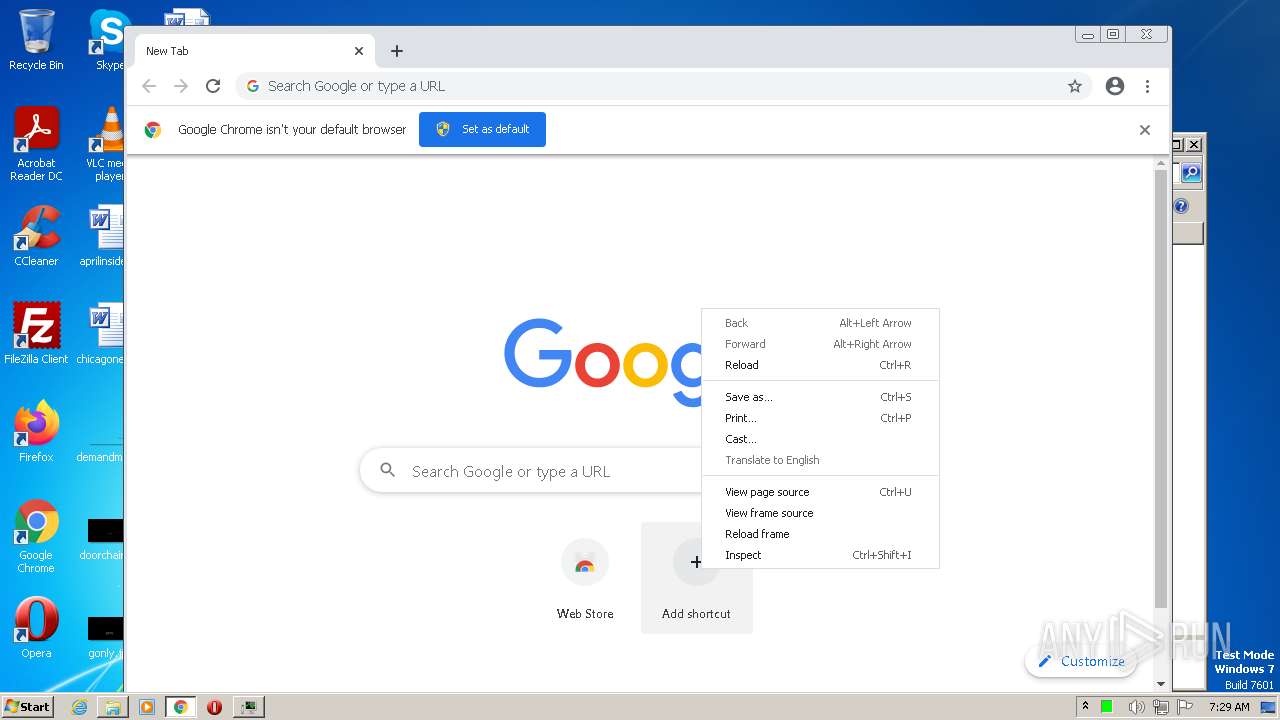
Manual execution by a user
- wmpnscfg.exe (PID: 2840)
- taskmgr.exe (PID: 1436)
- chrome.exe (PID: 2300)
- notepad.exe (PID: 3932)
- WinRAR.exe (PID: 2560)
Application launched itself
- chrome.exe (PID: 2300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(3848) .Installer.exe
BotnetDefault
Version0.5.7B
Options
AutoRuntrue
MutexDltcrx2.0
InstallFolder%AppData%
BSoDfalse
AntiVMtrue
Certificates
Cert1MIIE2jCCAsKgAwIBAgIQAOWwggtdXsxf/wQcXLkjKTANBgkqhkiG9w0BAQ0FADAOMQwwCgYDVQQDDAMxMjMwIBcNMjEwMjE5MTA1MzU1WhgPOTk5OTEyMzEyMzU5NTlaMA4xDDAKBgNVBAMMAzEyMzCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBALW3XoQkEp3kKUDFSWuh7sM/a7Po6MQ74WzHfWULlpi6Dc8RuR4pNQDMSmLl2/GiNrRQPtfPefjXzH4TCDVDNdKaWUJ5A9A/Wr2hOquXiWUq...
Server_SignatureI4+gIfiBwhpATlS7aUmS+0w6ao1Lx0ZgxotJiwpzpLK1zBEry0i3LN8VEicA0MX3DneWodm3EFa/Bs6Iq/KQAkGHKqxbI22ASdOHm2GWmw9nvNaKEr7z+7iy2AvsDLDqBQ+nd7Ov3tu4yn96KgOmahKLF7J1ssSeMVHObzevL2hFpBSZmqp8PShST3xogWklQHeGwmlHmHnMYy8Fmnktfnwfz/5vj3ZL/4LA4Z7g/FbbOdyGw5qq/j4hkerBT7c46jiMMvAetTInOh5sANm//dxe2U63UCYdvGYWyFRAKbDU...
Keys
AES8ddbe037d3d4e60c4353d45262928ee5547ed82de2be036ad232c2c3a68c1091
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
Credentials
Protocolpastebin
URLhttps://pastebin.com/raw/4iZFbp5M
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | - |
| OriginalFileName: | Stub.exe |
| LegalTrademarks: | - |
| LegalCopyright: | - |
| InternalName: | Stub.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | - |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x24e1e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 2560 |
| CodeSize: | 143360 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2020:05:10 05:24:51+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-May-2020 05:24:51 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | Stub.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | Stub.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 10-May-2020 05:24:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00022E24 | 0x00023000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.79978 |
.rsrc | 0x00026000 | 0x00000800 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.88827 |
.reloc | 0x00028000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.668238 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22615 | 1171 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
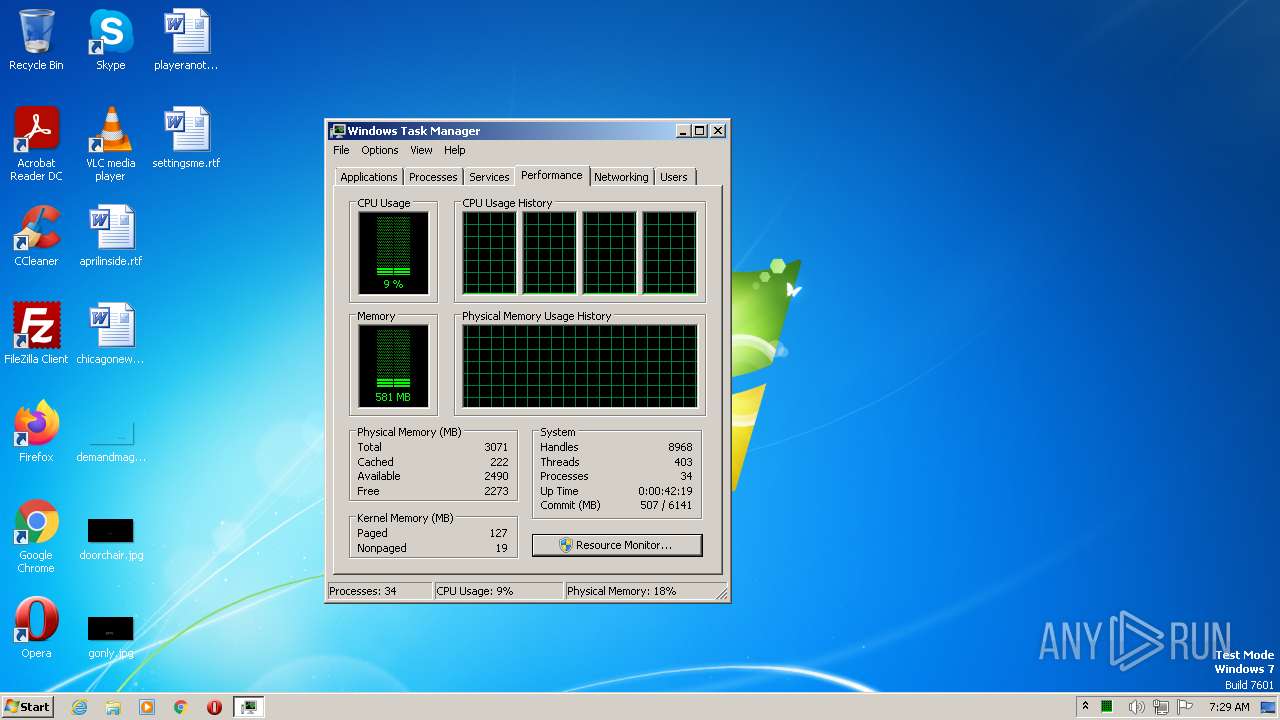
Total processes
107
Monitored processes
70
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1104,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3416 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1104,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=55 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1104,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2664 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1104,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3960 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1104,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=108 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1104,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3424 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1436 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1104,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3408 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1104,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1104,18284560192121655813,17626597665919381332,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=45 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
56 366
Read events
56 012
Write events
332
Delete events
22
Modification events
| (PID) Process: | (2688) id65gv.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3848) .Installer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2840) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{3703B576-889A-4867-BC01-DABA581579C6}\{0EFCDF5B-D0FD-43E5-ADAB-EE5C0E0A7CF0} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2840) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{3703B576-889A-4867-BC01-DABA581579C6} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2840) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{4AC78AE7-C31C-46D6-80EC-801AC342BB43} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
Executable files
2
Suspicious files
488
Text files
356
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6427CF4C-8FC.pma | — | |
MD5:— | SHA256:— | |||
| 2688 | id65gv.exe | C:\Users\admin\AppData\Roaming\.Installer.exe | executable | |
MD5:— | SHA256:— | |||
| 2688 | id65gv.exe | C:\Users\admin\AppData\Local\Temp\tmp470.tmp.bat | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\99613d50-192b-4854-86e4-7f67e6309b09.tmp | text | |
MD5:— | SHA256:— | |||
| 2824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF27230b.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF27232a.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
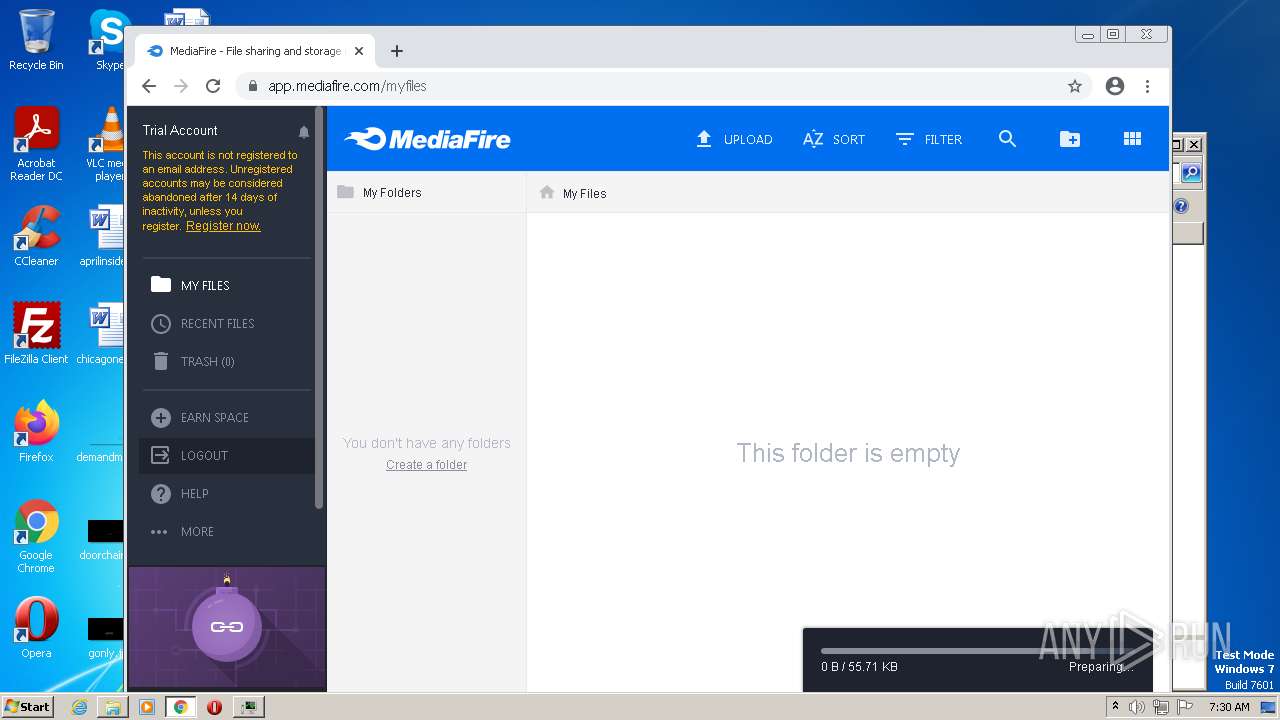
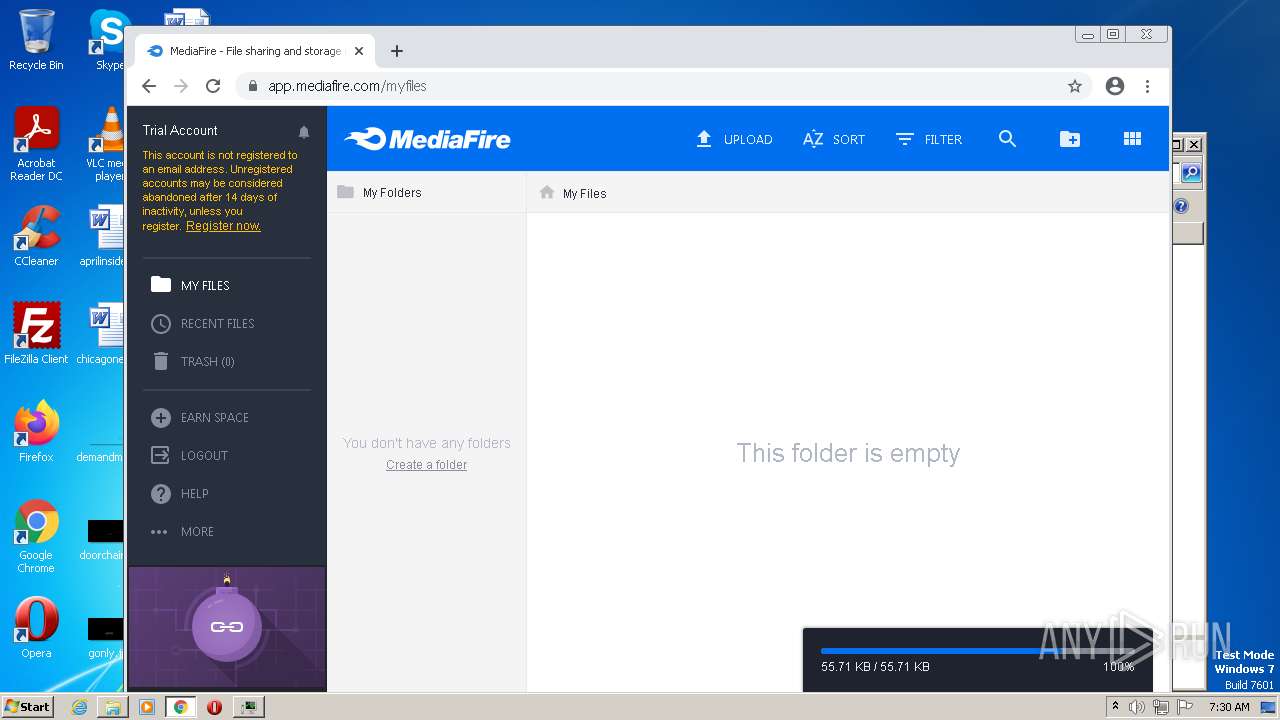
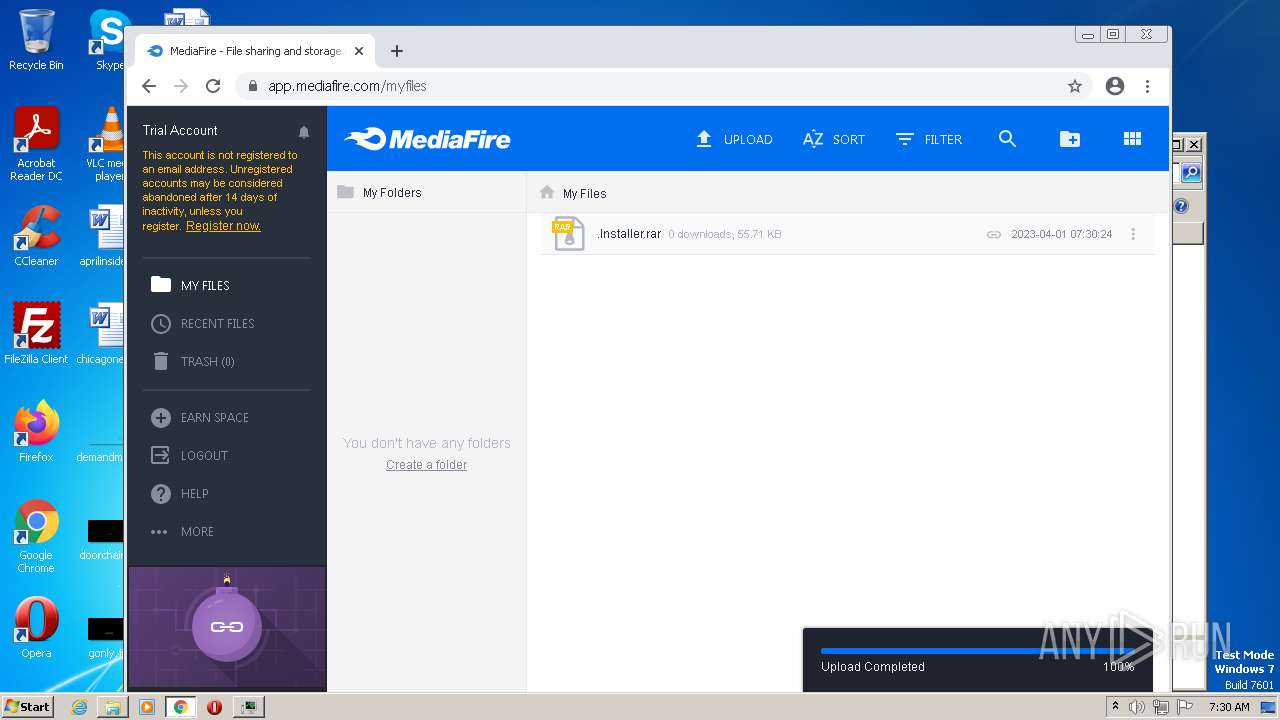
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
185
DNS requests
123
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
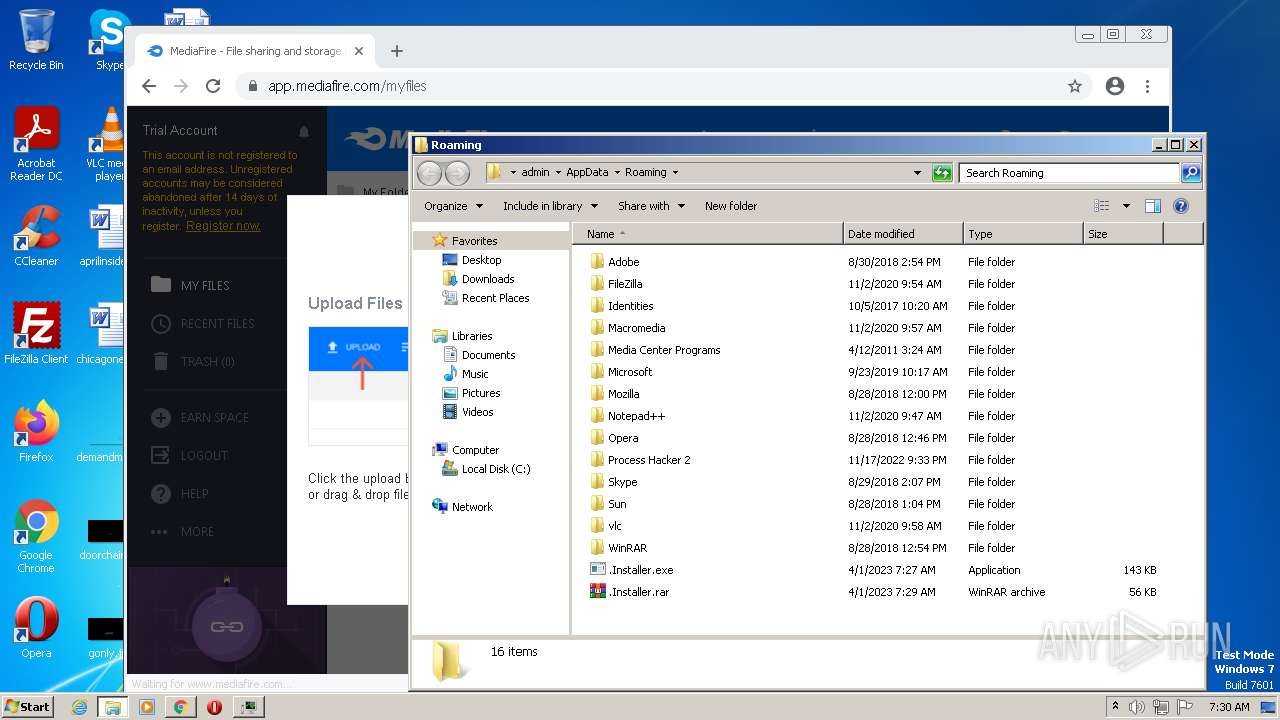
2824 | chrome.exe | GET | 301 | 104.16.53.48:80 | http://mediafire.com/ | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.27 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 8.36 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | vc | 9.75 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 34.5 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 93.8 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 402 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 52.3 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 25.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3848 | .Installer.exe | 18.139.9.214:17520 | 0.tcp.ap.ngrok.io | AMAZON-02 | SG | malicious |
3848 | .Installer.exe | 13.229.3.203:17520 | 0.tcp.ap.ngrok.io | AMAZON-02 | SG | malicious |
2824 | chrome.exe | 172.217.16.196:443 | www.google.com | GOOGLE | US | whitelisted |
2824 | chrome.exe | 142.250.186.77:443 | accounts.google.com | GOOGLE | US | suspicious |
2824 | chrome.exe | 142.250.185.193:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
2824 | chrome.exe | 142.250.186.110:443 | clients2.google.com | GOOGLE | US | whitelisted |
2824 | chrome.exe | 142.250.184.195:443 | update.googleapis.com | GOOGLE | US | whitelisted |
— | — | 34.104.35.123:80 | edgedl.me.gvt1.com | GOOGLE | US | whitelisted |
2824 | chrome.exe | 142.250.185.67:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
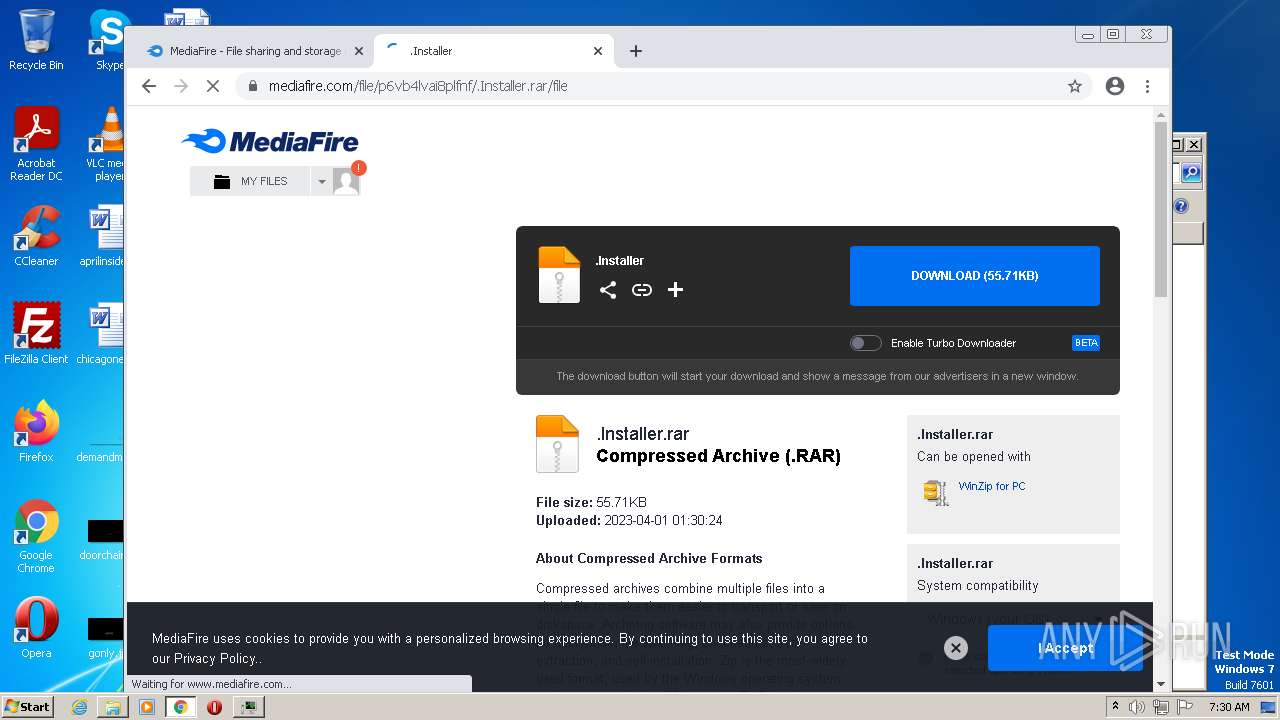
2824 | chrome.exe | 104.16.53.48:80 | mediafire.com | CLOUDFLARENET | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
0.tcp.ap.ngrok.io |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
clients2.googleusercontent.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |
— | — | Potential Corporate Privacy Violation | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |
— | — | Potential Corporate Privacy Violation | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |
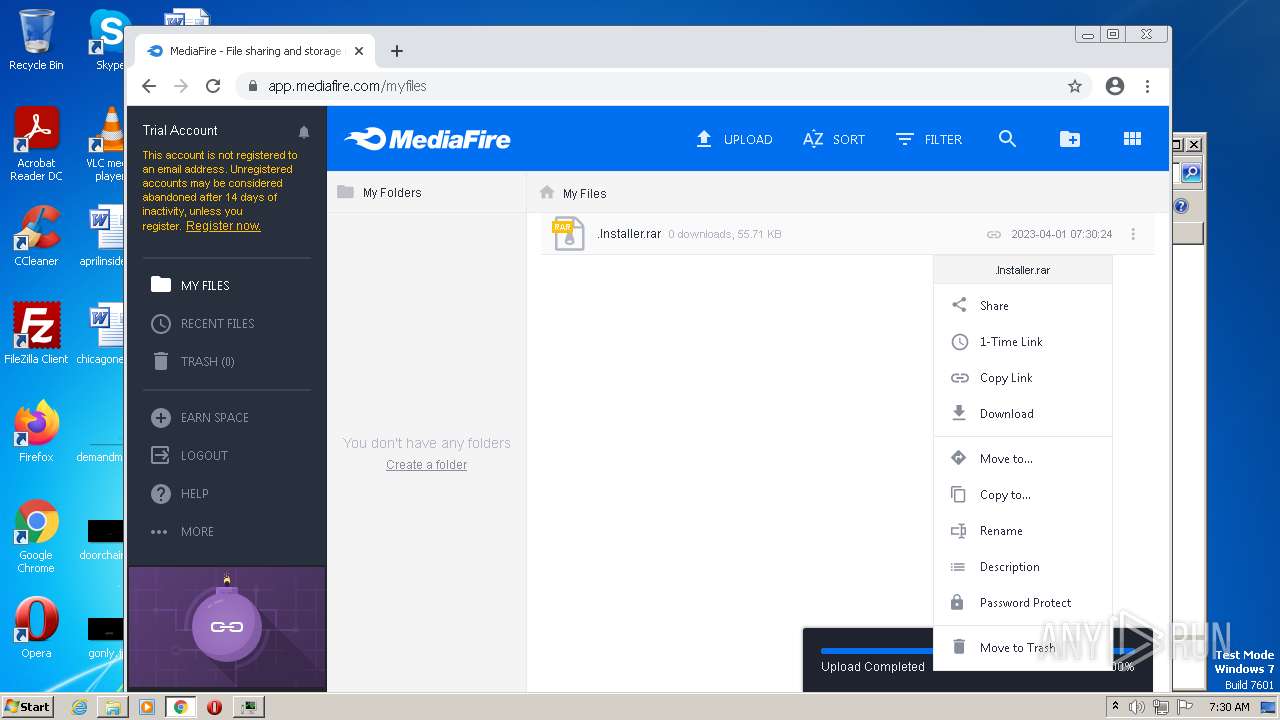
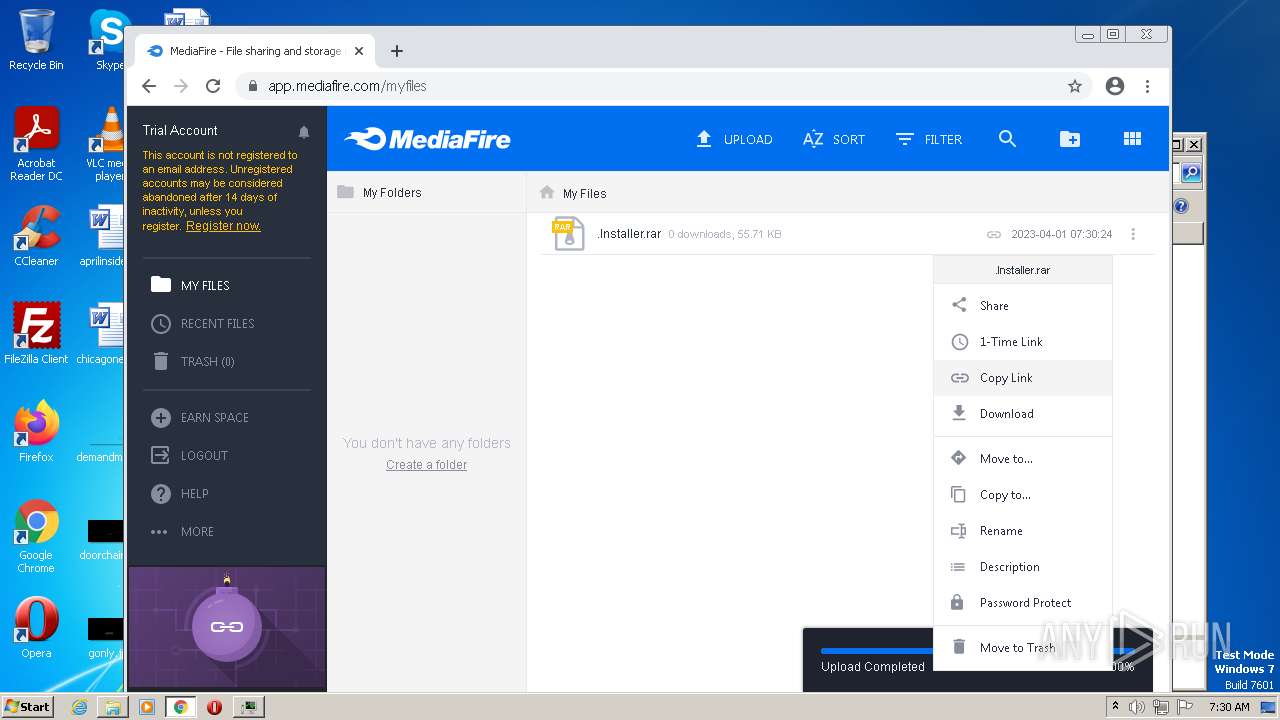
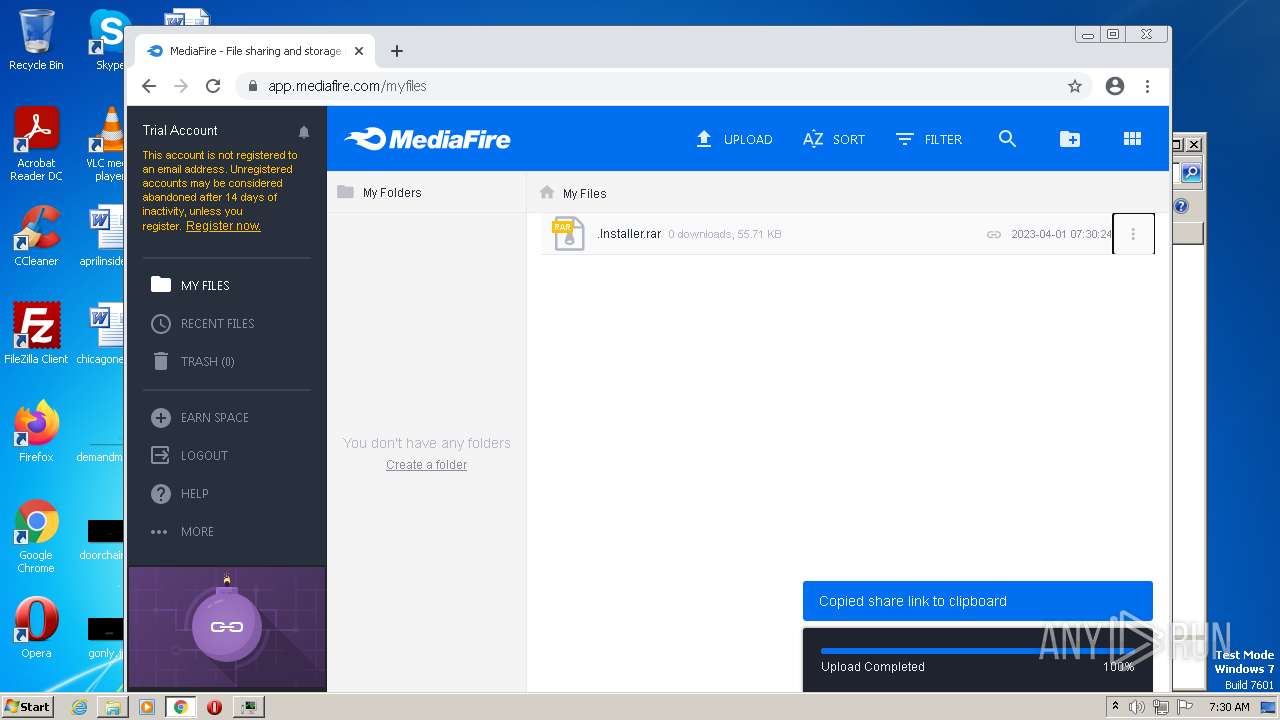
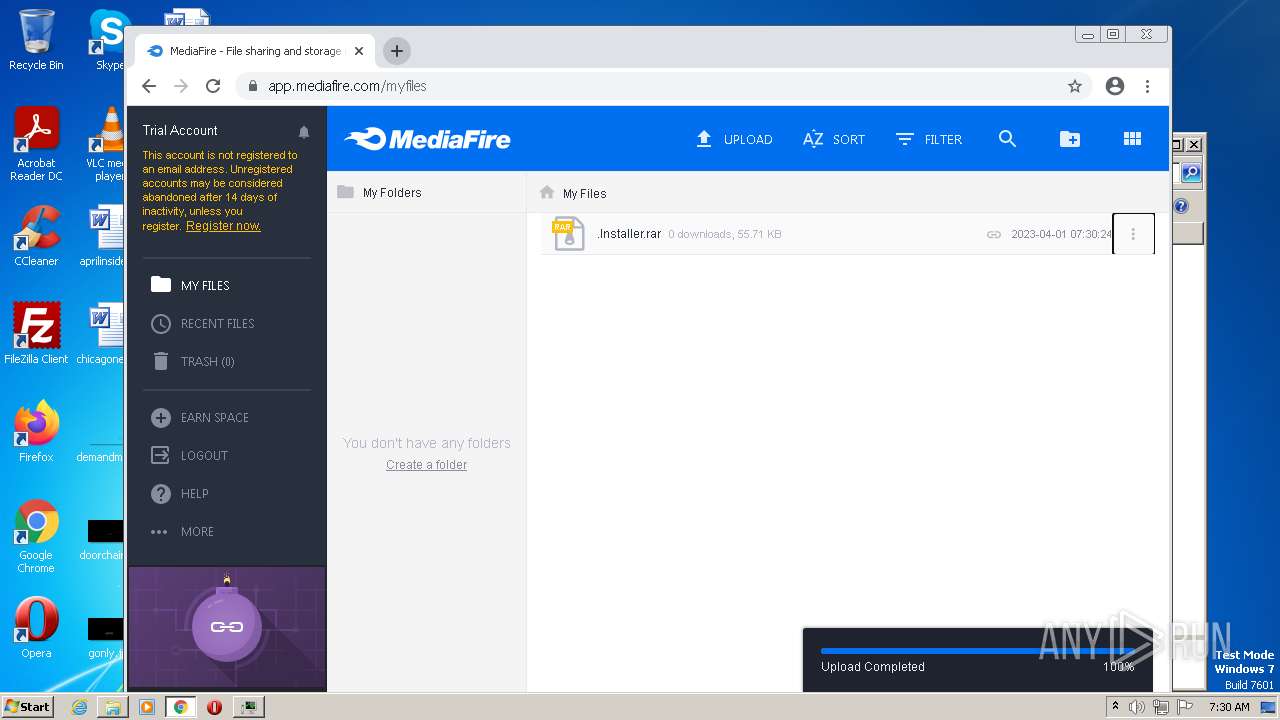
— | — | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
— | — | Potential Corporate Privacy Violation | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |
— | — | Potentially Bad Traffic | ET INFO Commonly Abused Content Delivery Network Domain in DNS Lookup (btloader .com) |
2824 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Abused Content Delivery Network Domain (btloader .com in TLS SNI) |
— | — | Potentially Bad Traffic | ET INFO Commonly Abused Content Delivery Network Domain in DNS Lookup (btloader .com) |
2824 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Abused Content Delivery Network Domain (btloader .com in TLS SNI) |
2824 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Abused Content Delivery Network Domain (btloader .com in TLS SNI) |