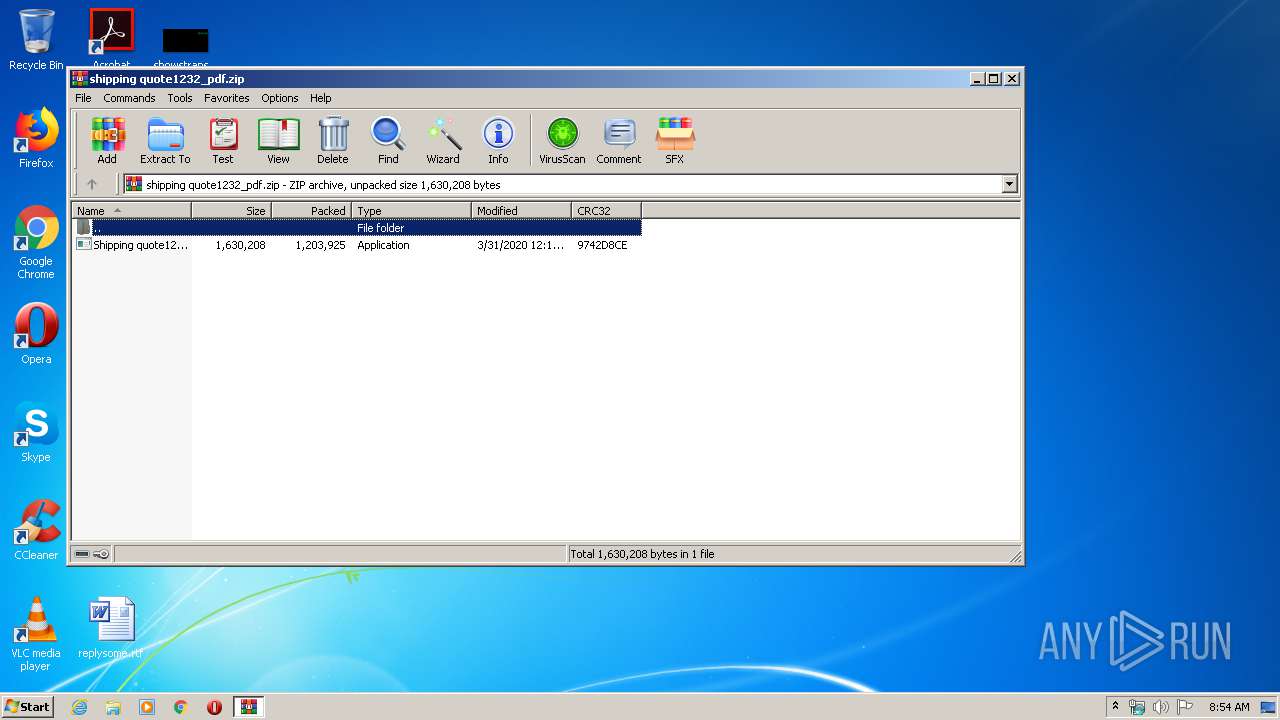
| File name: | shipping quote1232_pdf.zip |
| Full analysis: | https://app.any.run/tasks/57f991b2-1caf-45cc-a1e0-98156bb8fb4d |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | March 31, 2020, 07:54:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 167D29FD346B734B545586D15C291D79 |
| SHA1: | 10B16D594A426B9FCEE9B39F693262A3DC378B0E |
| SHA256: | B937A3F01C12690106D2A5C9A85E8793852B2F63A134A50C0BA8AB25080DB2D1 |
| SSDEEP: | 24576:2M3vNPUzs2zqX2UXFpdzghOQKeSyBmjidorWLAvu2xfkMlit:x1czsLXtQOc1EEMfHlit |
MALICIOUS
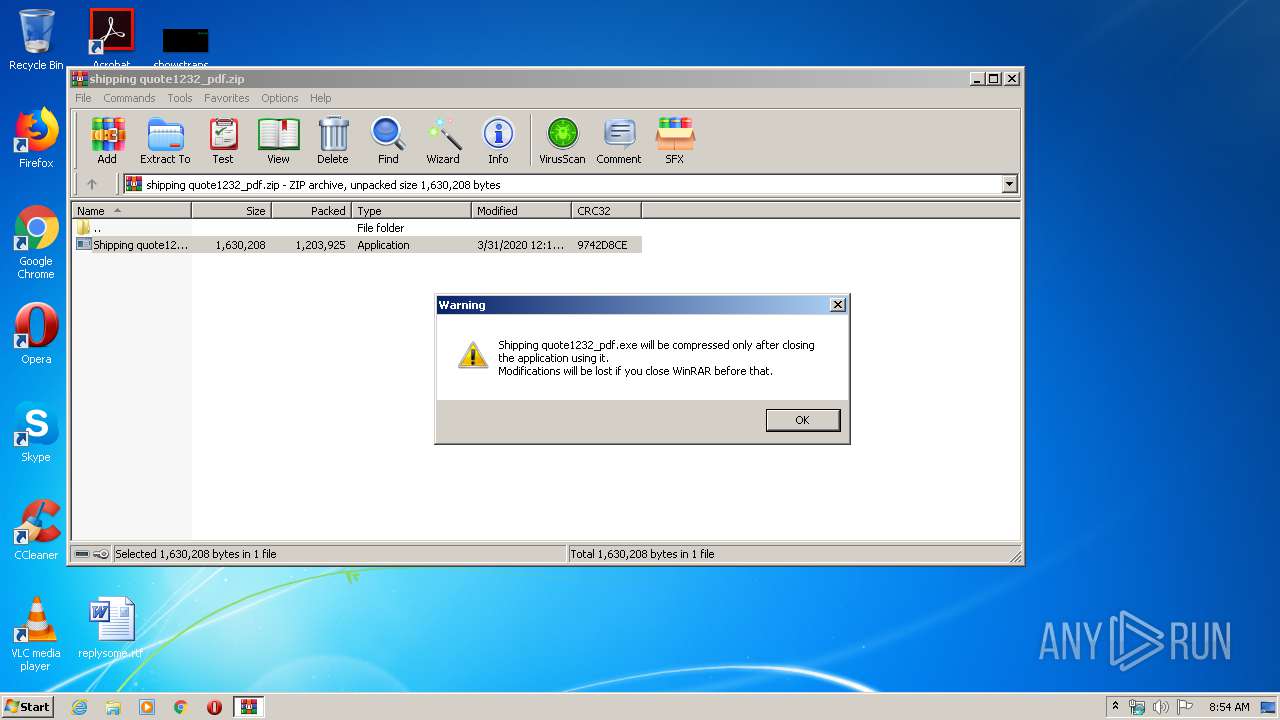
Application was dropped or rewritten from another process
- Shipping quote1232_pdf.exe (PID: 1348)
- Shipping quote1232_pdf.exe (PID: 2720)
Connects to CnC server
- explorer.exe (PID: 372)
FORMBOOK was detected
- explorer.exe (PID: 372)
- msdt.exe (PID: 3620)
- Firefox.exe (PID: 2692)
Actions looks like stealing of personal data
- msdt.exe (PID: 3620)
Changes the autorun value in the registry
- msdt.exe (PID: 3620)
Stealing of credential data
- msdt.exe (PID: 3620)
SUSPICIOUS
Application launched itself
- Shipping quote1232_pdf.exe (PID: 1348)
Executable content was dropped or overwritten
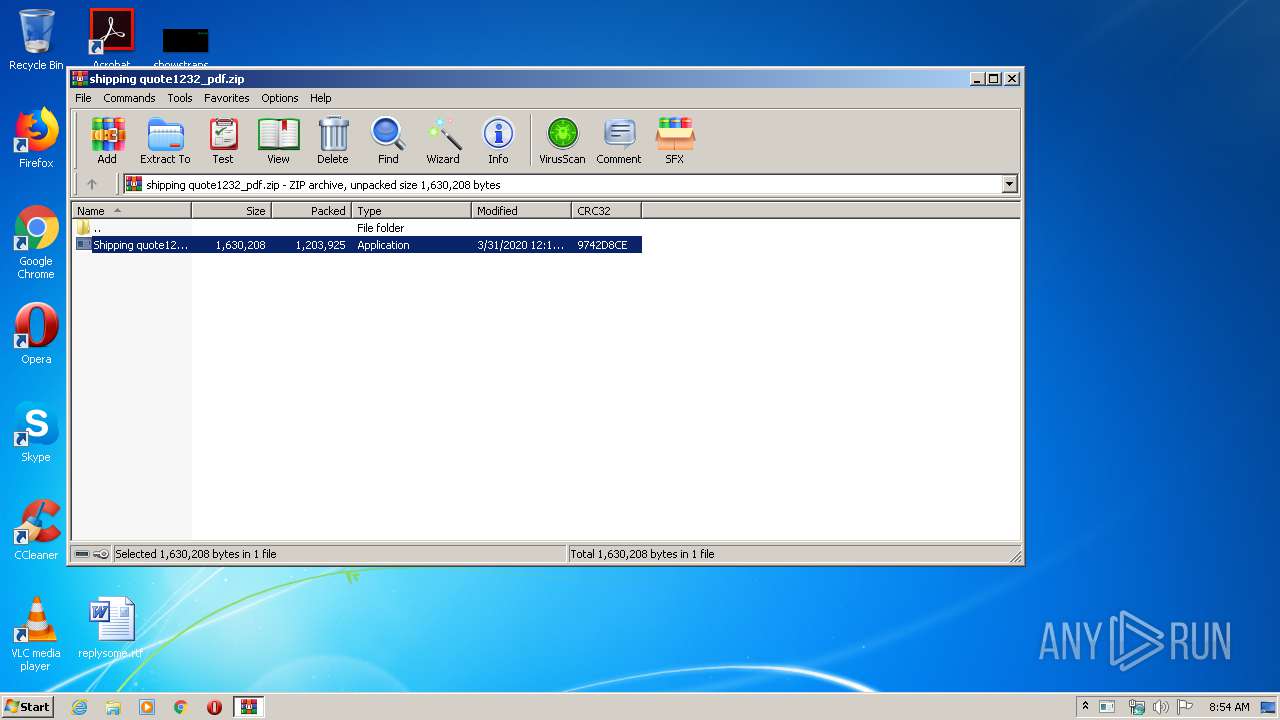
- WinRAR.exe (PID: 3808)
Creates files in the user directory
- msdt.exe (PID: 3620)
Loads DLL from Mozilla Firefox
- msdt.exe (PID: 3620)
Starts CMD.EXE for commands execution
- msdt.exe (PID: 3620)
INFO
Reads the hosts file
- msdt.exe (PID: 3620)
Manual execution by user
- msdt.exe (PID: 3620)
Creates files in the user directory
- Firefox.exe (PID: 2692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:03:31 00:14:13 |
| ZipCRC: | 0x9742d8ce |
| ZipCompressedSize: | 1203925 |
| ZipUncompressedSize: | 1630208 |
| ZipFileName: | Shipping quote1232_pdf.exe |
Total processes
40
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1348 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3808.10821\Shipping quote1232_pdf.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3808.10821\Shipping quote1232_pdf.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1844 | /c del "C:\Users\admin\AppData\Local\Temp\Rar$EXa3808.10821\Shipping quote1232_pdf.exe" | C:\Windows\System32\cmd.exe | — | msdt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | msdt.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2720 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3808.10821\Shipping quote1232_pdf.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3808.10821\Shipping quote1232_pdf.exe | — | Shipping quote1232_pdf.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3620 | "C:\Windows\System32\msdt.exe" | C:\Windows\System32\msdt.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3808 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\shipping quote1232_pdf.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
464
Read events
444
Write events
20
Delete events
0
Modification events
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\shipping quote1232_pdf.zip | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
1
Suspicious files
73
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3808 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3808.10821\Shipping quote1232_pdf.exe | executable | |
MD5:— | SHA256:— | |||
| 3620 | msdt.exe | C:\Users\admin\AppData\Roaming\4QN086VE\4QNlogri.ini | binary | |
MD5:D63A82E5D81E02E399090AF26DB0B9CB | SHA256:EAECE2EBA6310253249603033C744DD5914089B0BB26BDE6685EC9813611BAAE | |||
| 3620 | msdt.exe | C:\Users\admin\AppData\Roaming\4QN086VE\4QNlogim.jpeg | image | |
MD5:— | SHA256:— | |||
| 2692 | Firefox.exe | C:\Users\admin\AppData\Roaming\4QN086VE\4QNlogrf.ini | binary | |
MD5:— | SHA256:— | |||
| 3620 | msdt.exe | C:\Users\admin\AppData\Roaming\4QN086VE\4QNlogrc.ini | binary | |
MD5:— | SHA256:— | |||
| 3620 | msdt.exe | C:\Users\admin\AppData\Roaming\4QN086VE\4QNlogrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
21
DNS requests
7
Threats
66
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
372 | explorer.exe | GET | — | 184.168.221.88:80 | http://www.guideonwebs.com/k8g/?0ph=Xn9dmeINecPQ+IwFR1eHYb2x98hoRafi5f8Y11XvFF/o1l0h7/6YQbHiuLp49VJQqg2HJQ==&00=Kxd09b7XJ | US | — | — | malicious |
372 | explorer.exe | GET | — | 198.54.117.210:80 | http://www.matabishi.com/k8g/?0ph=KXYIa96KmMLkH/9ukUAZ9nByBsayi1UQmYcHYFNcpj2uJC2CRbRNPGCNFNU/4ae7xcfw8w==&00=Kxd09b7XJ | US | — | — | malicious |
372 | explorer.exe | POST | — | 184.168.221.88:80 | http://www.guideonwebs.com/k8g/ | US | — | — | malicious |
372 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.sanfranciscosound.com/k8g/ | US | — | — | shared |
372 | explorer.exe | GET | 302 | 23.20.239.12:80 | http://www.sanfranciscosound.com/k8g/?0ph=HFT/yqDra9GCYrZMXg9yOuPz9+GBS5G6qwo4xxaIGSDg11JlZ0lUqJWlINryMEVwAIzuOQ==&00=Kxd09b7XJ | US | html | 193 b | shared |
372 | explorer.exe | POST | — | 184.168.221.88:80 | http://www.guideonwebs.com/k8g/ | US | — | — | malicious |
372 | explorer.exe | POST | — | 199.192.27.69:80 | http://www.crokve.com/k8g/ | US | — | — | malicious |
372 | explorer.exe | POST | — | 198.54.117.210:80 | http://www.matabishi.com/k8g/ | US | — | — | malicious |
372 | explorer.exe | POST | — | 103.247.11.208:80 | http://www.mediamazballon.com/k8g/ | ID | — | — | malicious |
372 | explorer.exe | POST | — | 103.247.11.208:80 | http://www.mediamazballon.com/k8g/ | ID | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
372 | explorer.exe | 154.90.167.87:80 | www.xuanyu-tj.com | MULTACOM CORPORATION | US | malicious |
372 | explorer.exe | 199.192.27.69:80 | www.crokve.com | — | US | malicious |
372 | explorer.exe | 23.20.239.12:80 | www.sanfranciscosound.com | Amazon.com, Inc. | US | shared |
372 | explorer.exe | 184.168.221.88:80 | www.guideonwebs.com | GoDaddy.com, LLC | US | malicious |
372 | explorer.exe | 103.247.11.208:80 | www.mediamazballon.com | Rumahweb Indonesia CV. | ID | malicious |
372 | explorer.exe | 198.54.117.210:80 | www.matabishi.com | Namecheap, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.xuanyu-tj.com |
| malicious |
www.crokve.com |
| malicious |
www.guideonwebs.com |
| malicious |
www.accstandard.com |
| unknown |
www.sanfranciscosound.com |
| shared |
www.matabishi.com |
| malicious |
www.mediamazballon.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
372 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
372 | explorer.exe | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
16 ETPRO signatures available at the full report