| File name: | decoded_ps1 |
| Full analysis: | https://app.any.run/tasks/bd507295-64b2-4dea-ab52-d2b29e3f0f05 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | November 20, 2018, 12:20:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF, LF line terminators |
| MD5: | 72C0AAAC257F6DE8BDB9F2CBDD05E47B |
| SHA1: | D76A8A78352357398BFF570663C326C84B969686 |
| SHA256: | B926D9A9231C4A1E7E031A6A7CA4DF8018F6DCDBBDB956D7E3DA3B45BE20650C |
| SSDEEP: | 12288:gG6x3u0OkeDq/H/HPZtL88YwQVj1z7qDFxEUj8XdrhscrdbSL:g3lLIyH/HH8TwQVZz7qDbjK2 |
MALICIOUS
Application was dropped or rewritten from another process
- WTKOd.exe (PID: 3712)
- WTKOd.exe (PID: 3872)
Detected artifacts of LokiBot
- WTKOd.exe (PID: 3872)
Changes the autorun value in the registry
- WTKOd.exe (PID: 3712)
LOKIBOT was detected
- WTKOd.exe (PID: 3872)
Connects to CnC server
- WTKOd.exe (PID: 3872)
Actions looks like stealing of personal data
- WTKOd.exe (PID: 3872)
SUSPICIOUS
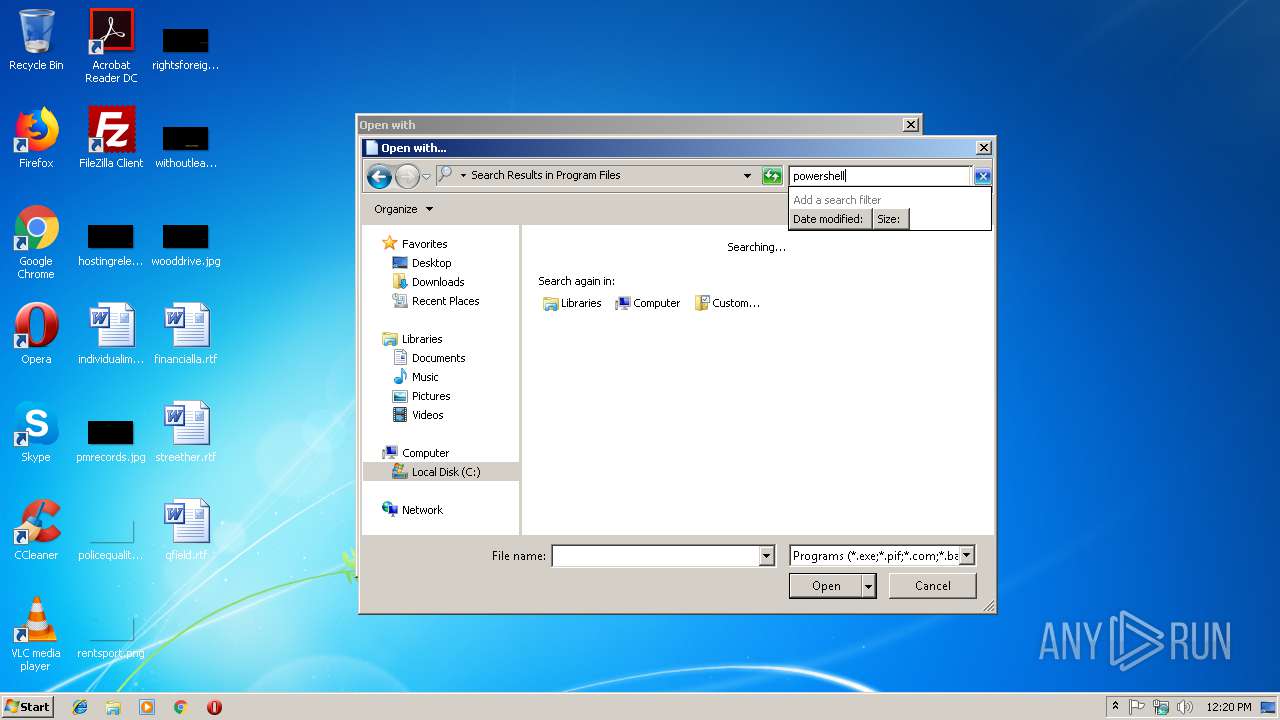
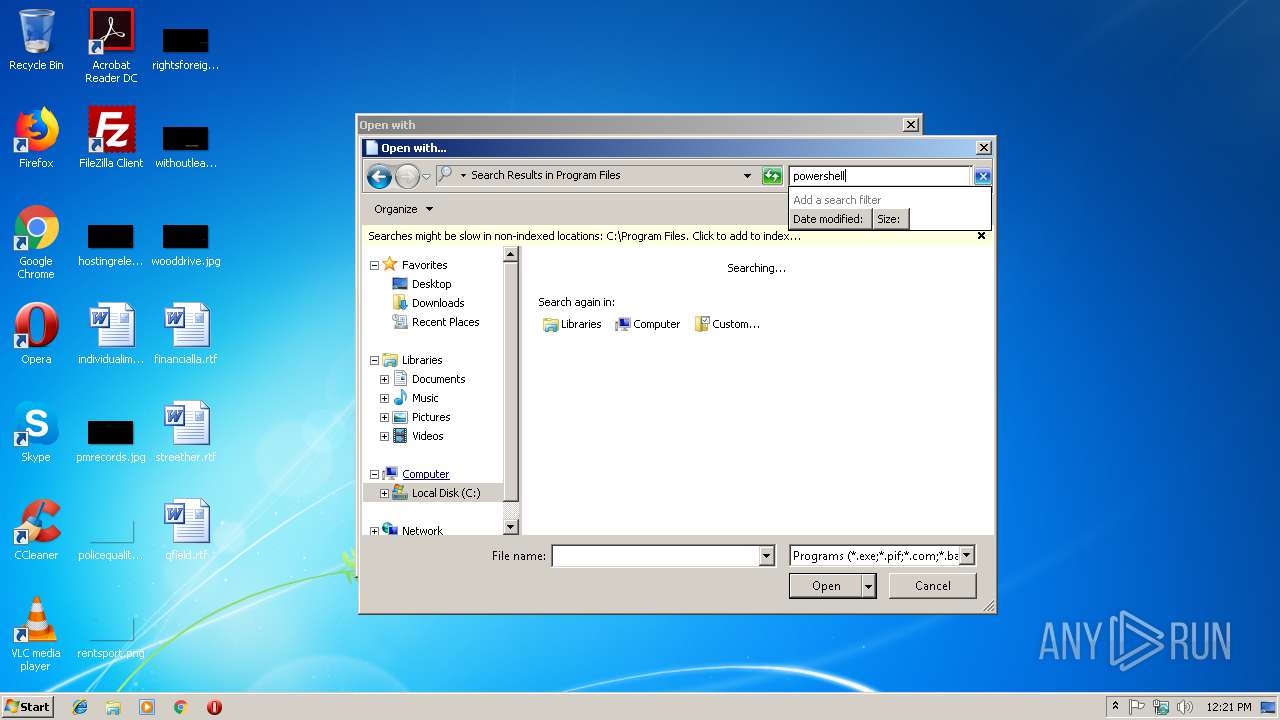
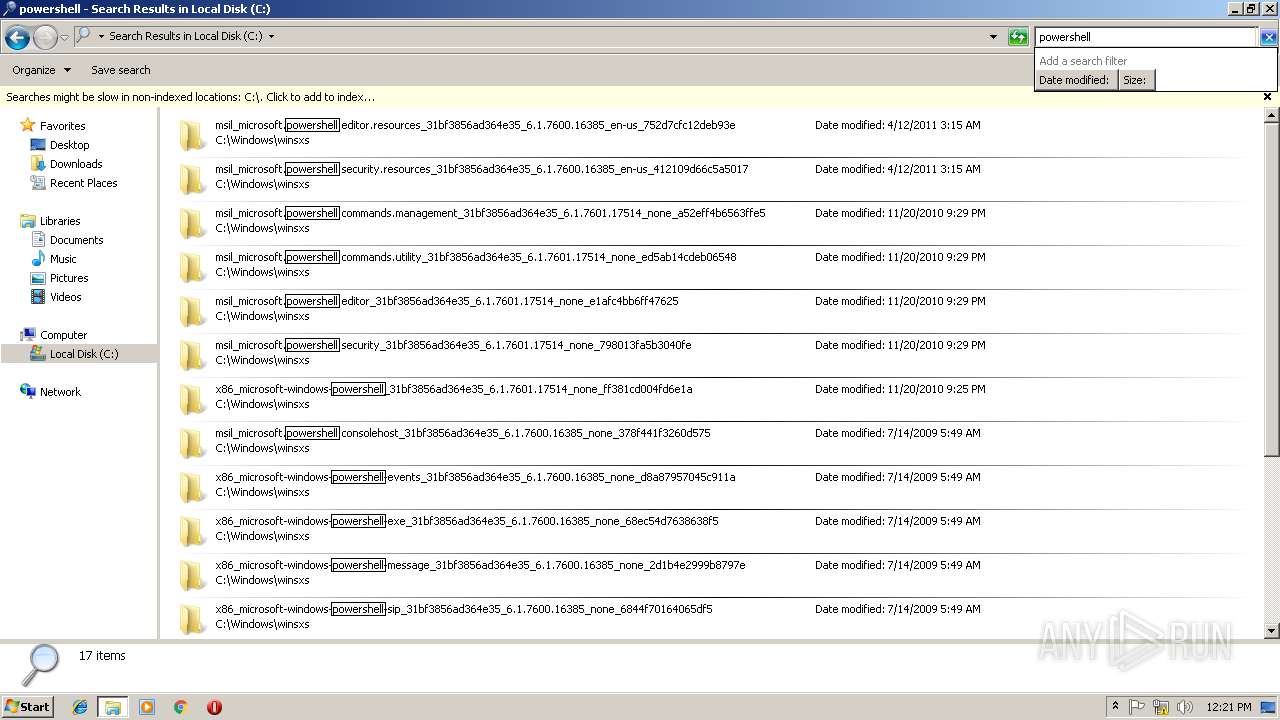
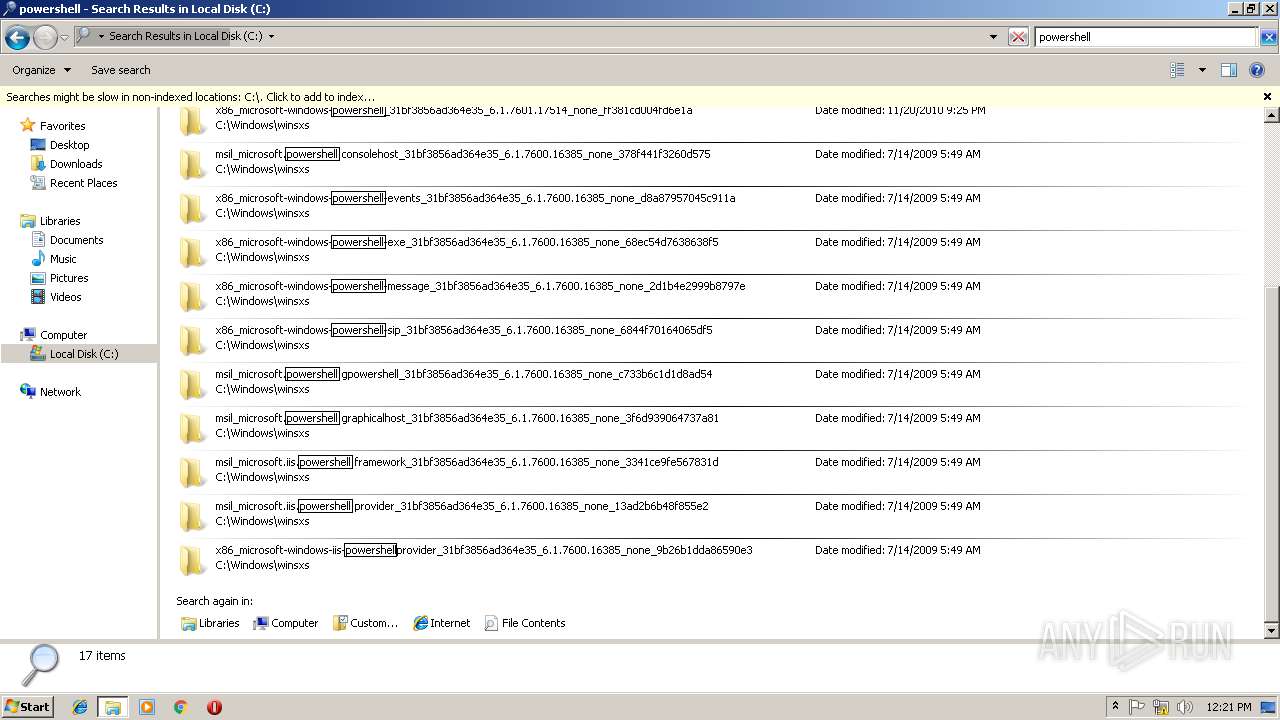
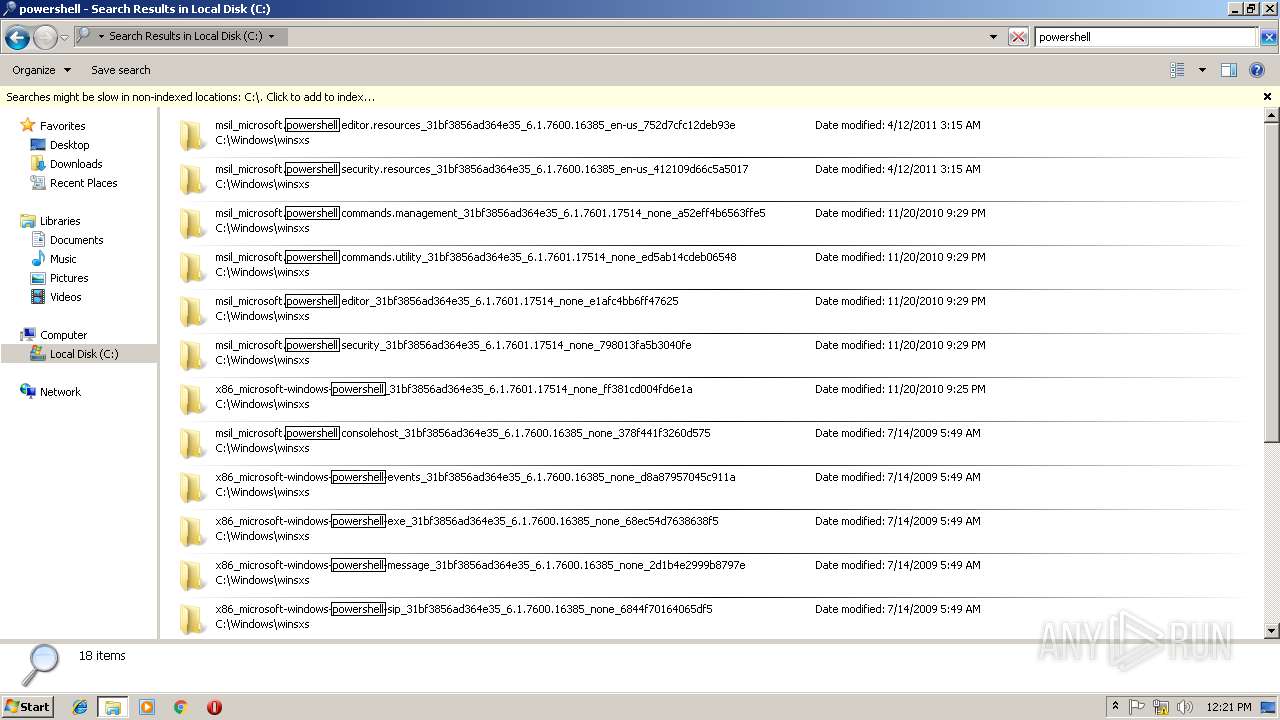
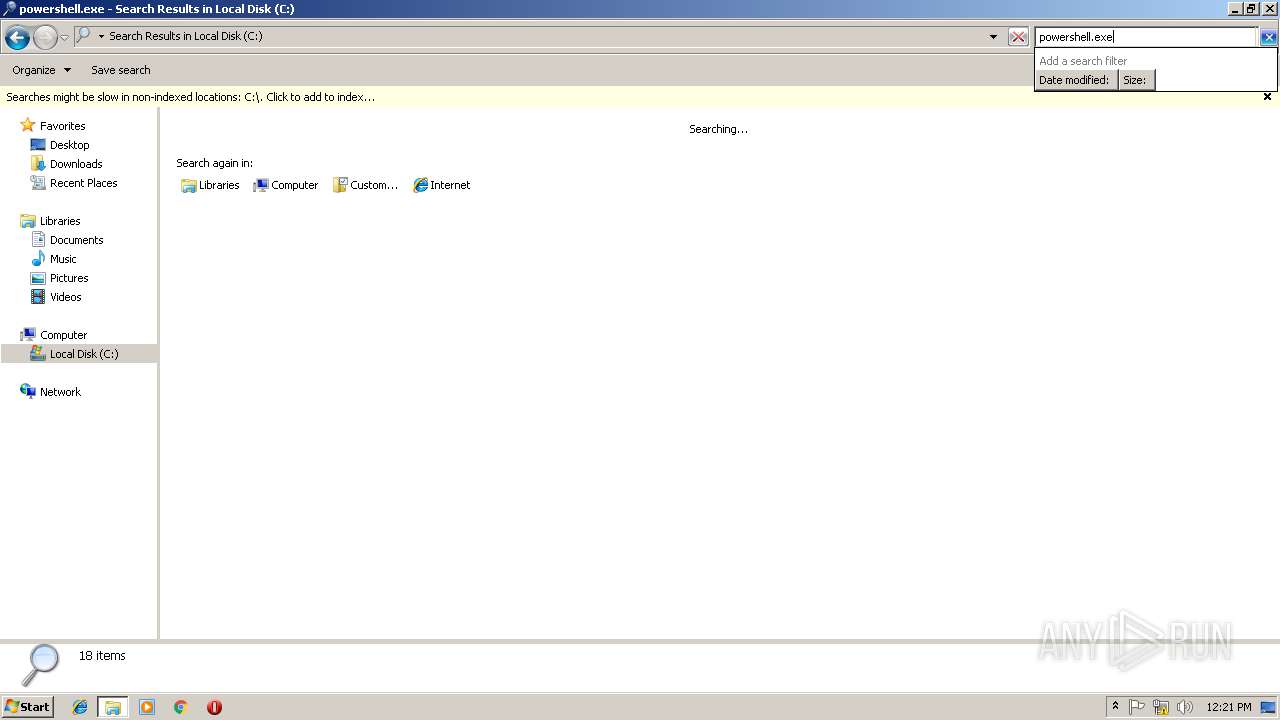
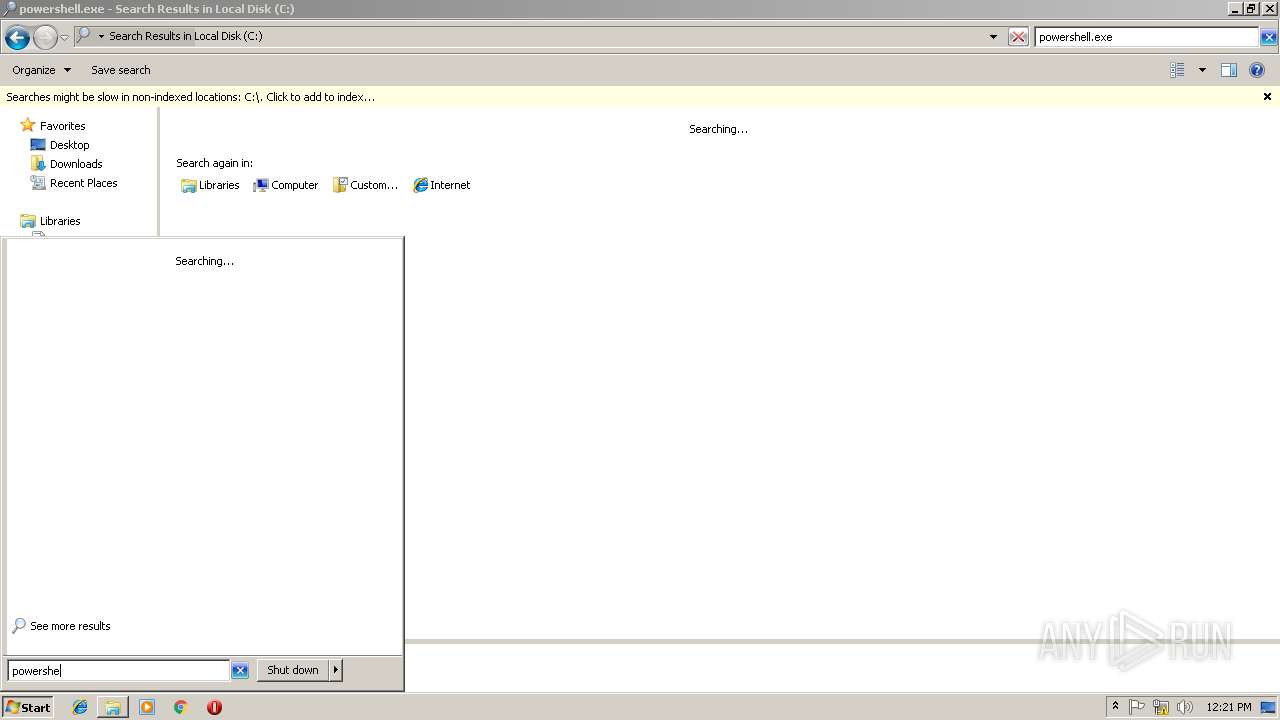
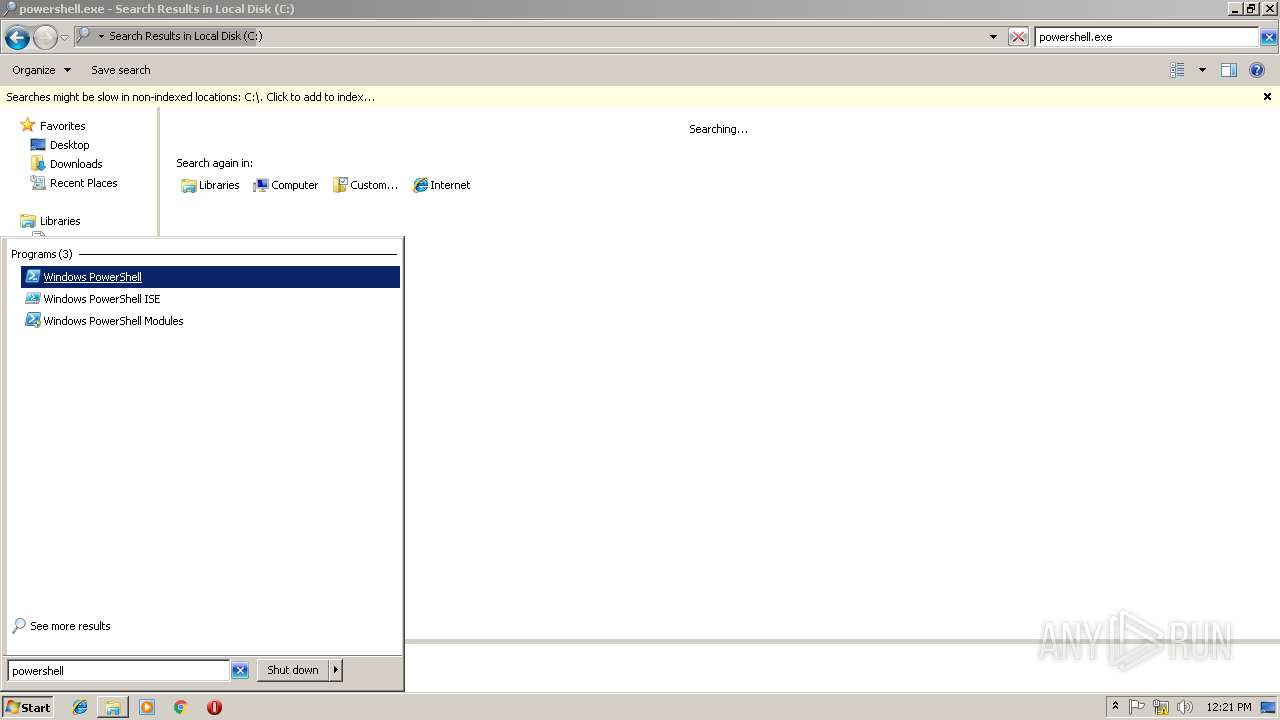
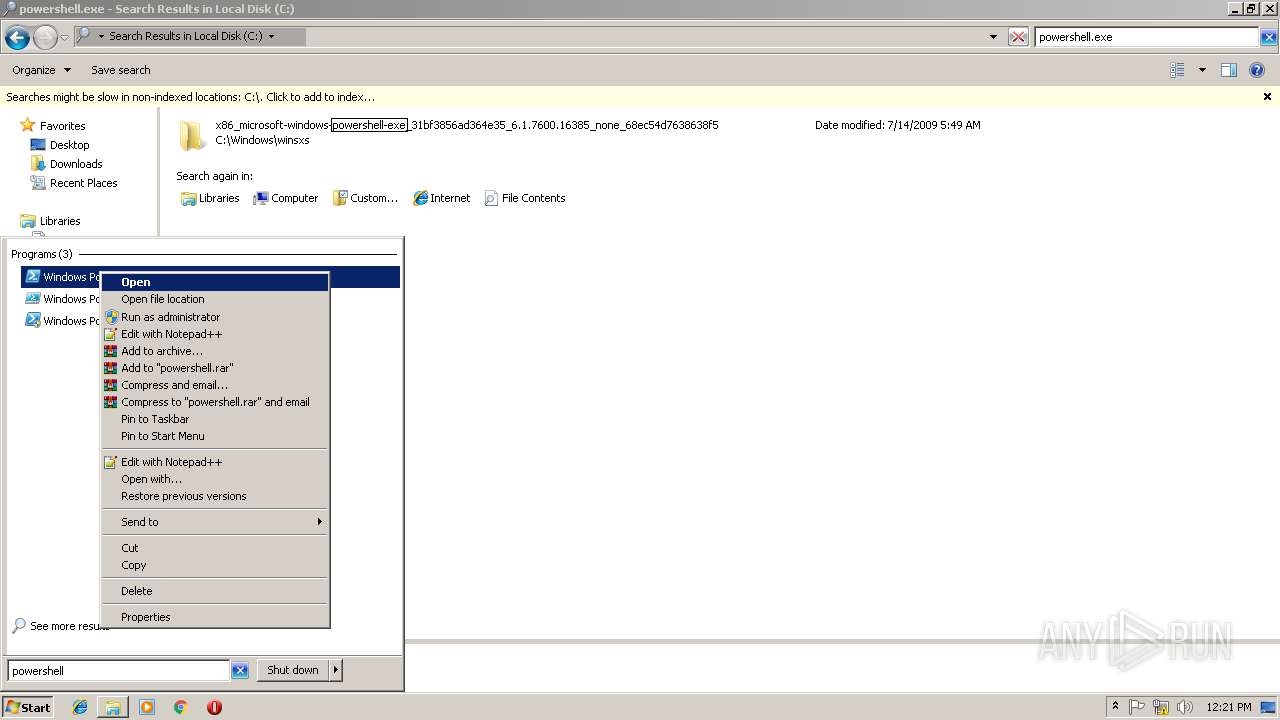
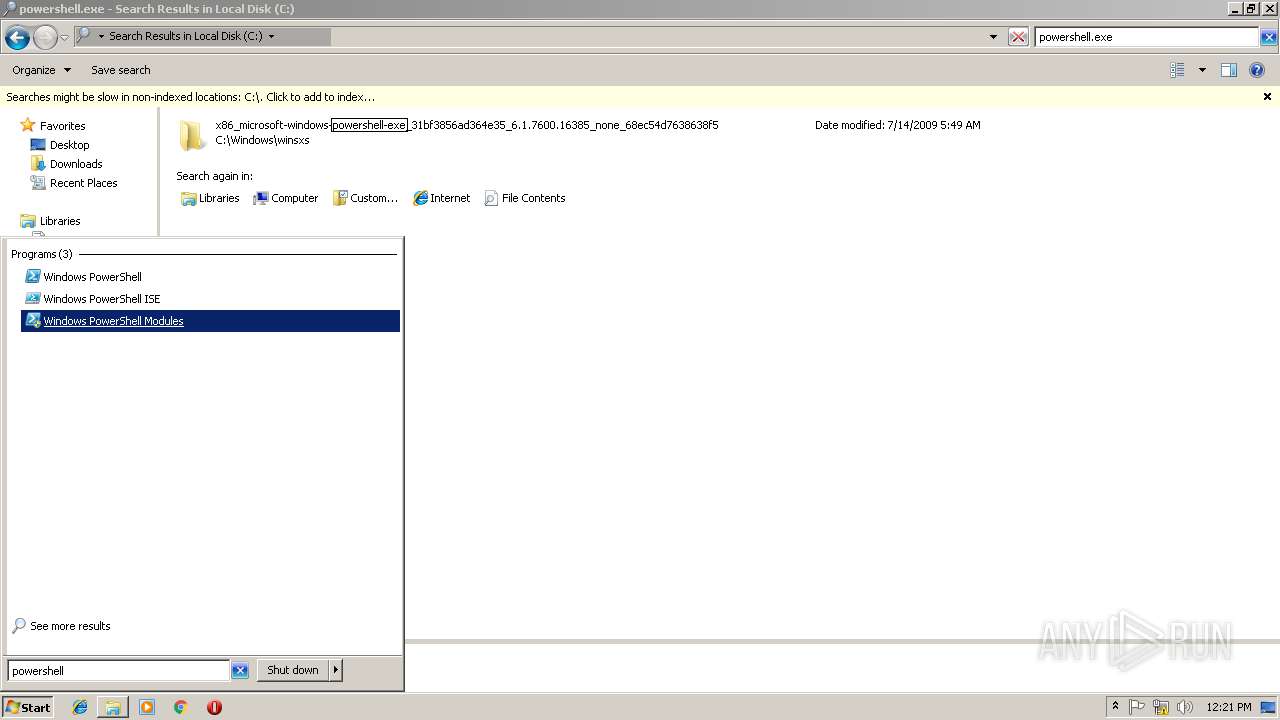
Application launched itself
- powershell.exe (PID: 4080)
- WTKOd.exe (PID: 3712)
Uses RUNDLL32.EXE to load library
- powershell.exe (PID: 4080)
Executable content was dropped or overwritten
- WTKOd.exe (PID: 3872)
- powershell.exe (PID: 3568)
- WTKOd.exe (PID: 3712)
Creates files in the user directory
- powershell.exe (PID: 4080)
- powershell.exe (PID: 800)
- powershell.exe (PID: 3568)
- powershell.exe (PID: 3876)
- WTKOd.exe (PID: 3872)
Executes PowerShell scripts
- powershell.exe (PID: 4080)
Loads DLL from Mozilla Firefox
- WTKOd.exe (PID: 3872)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
9
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
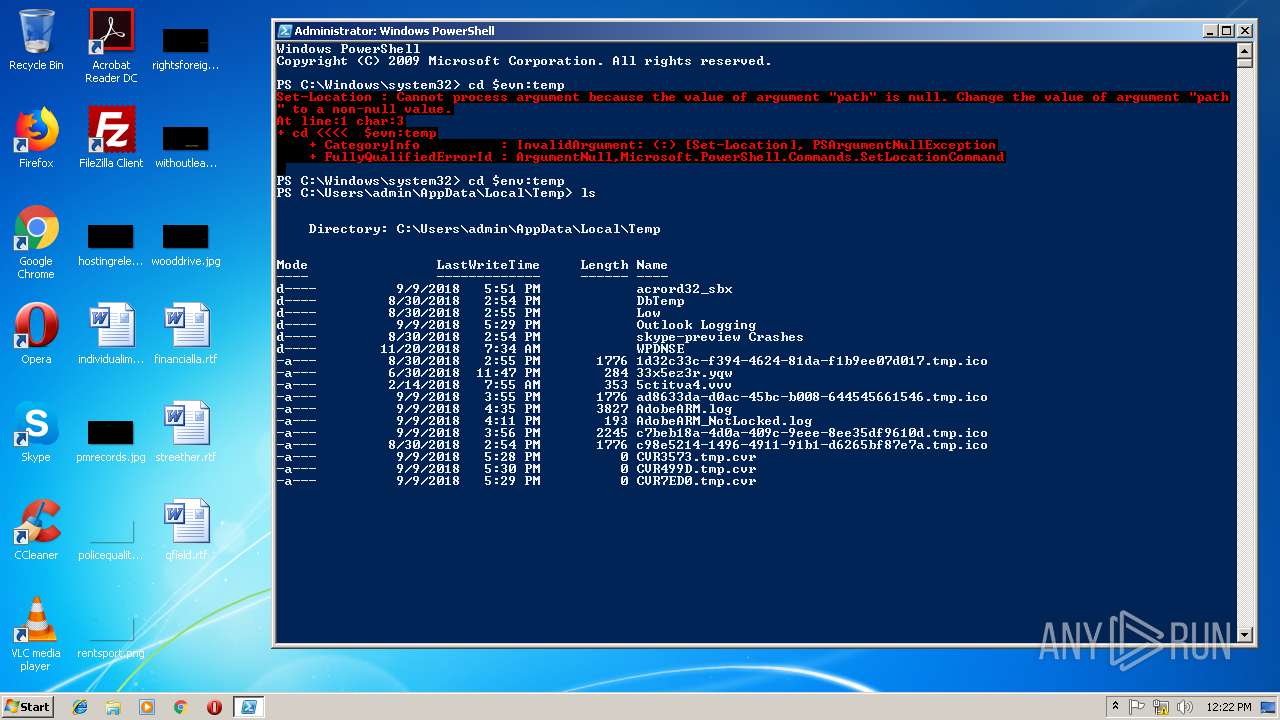
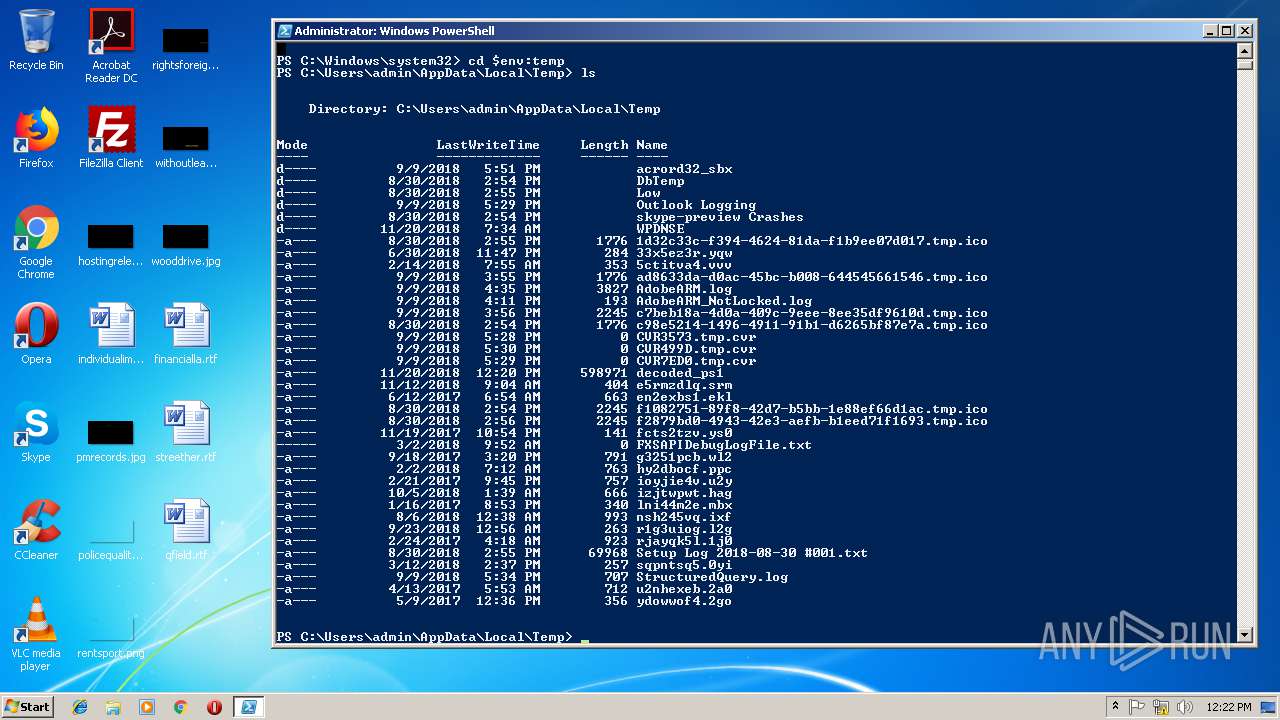
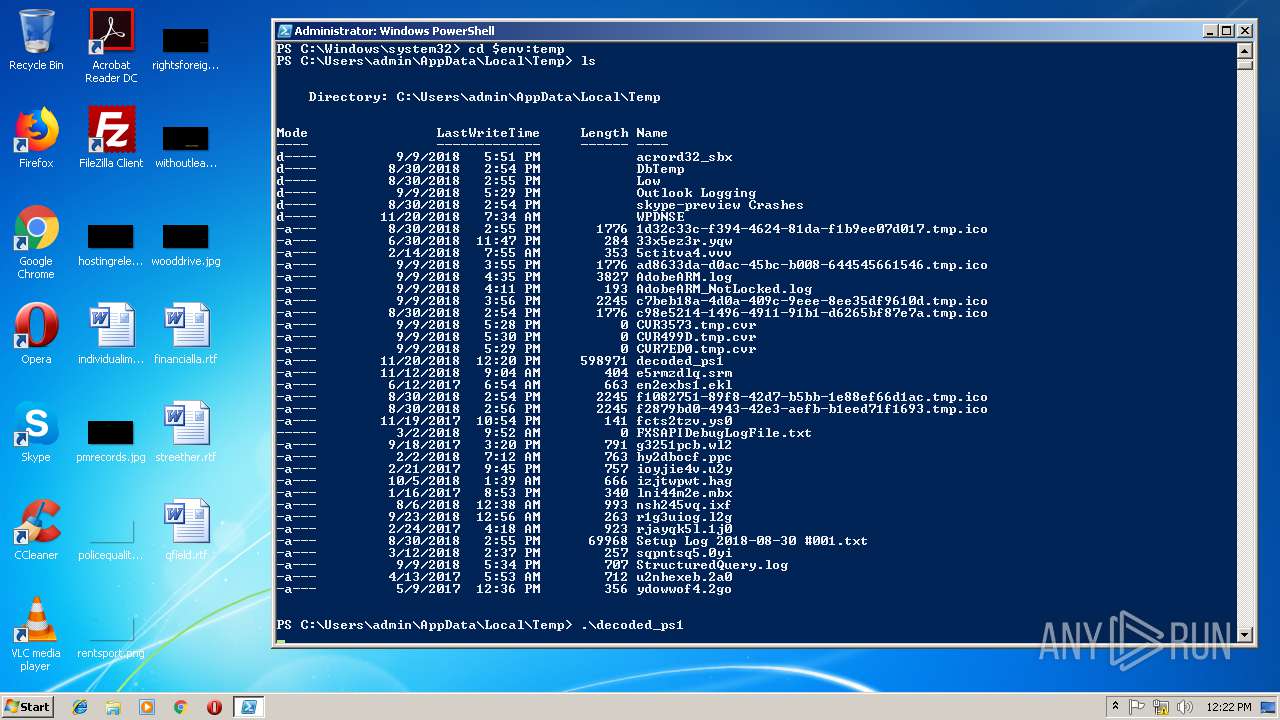
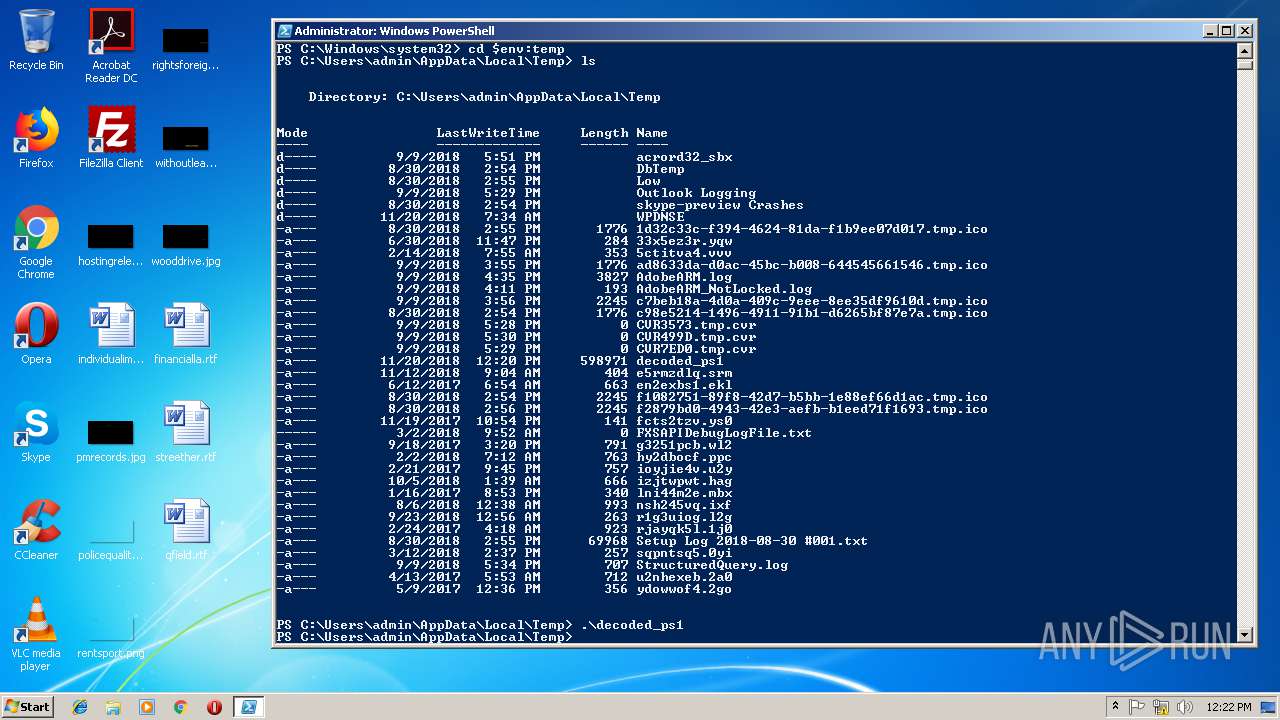
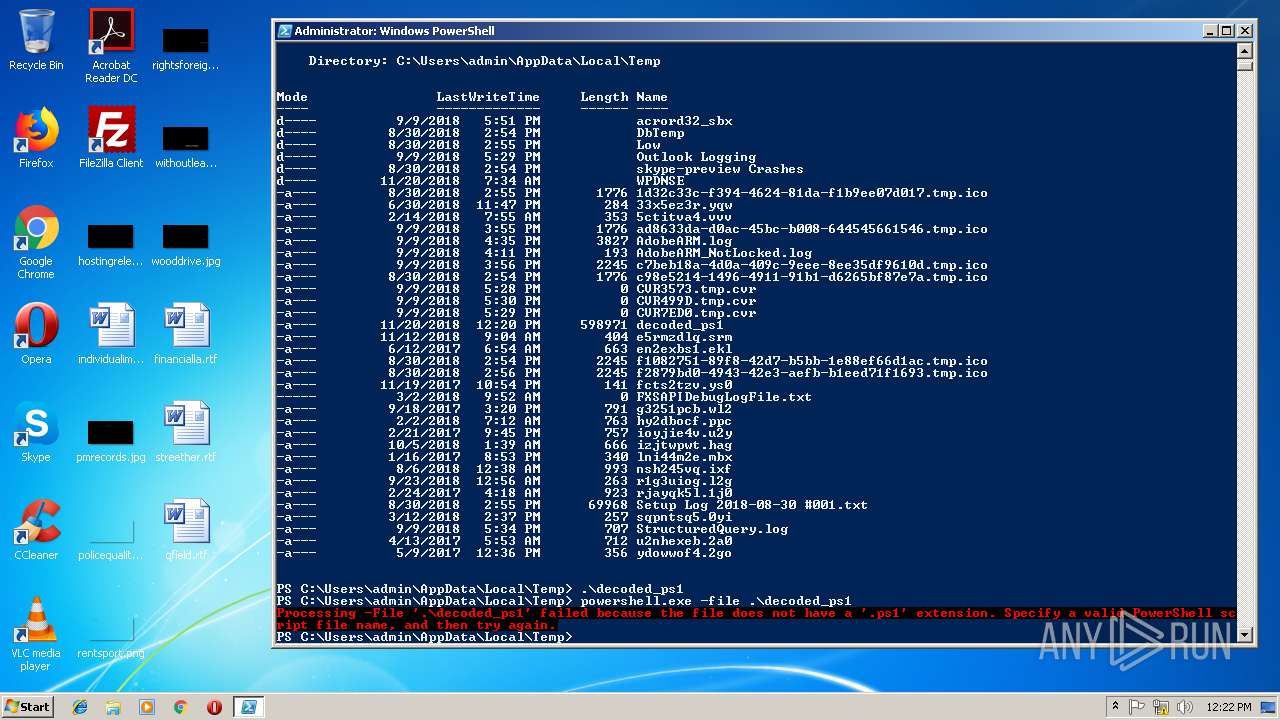
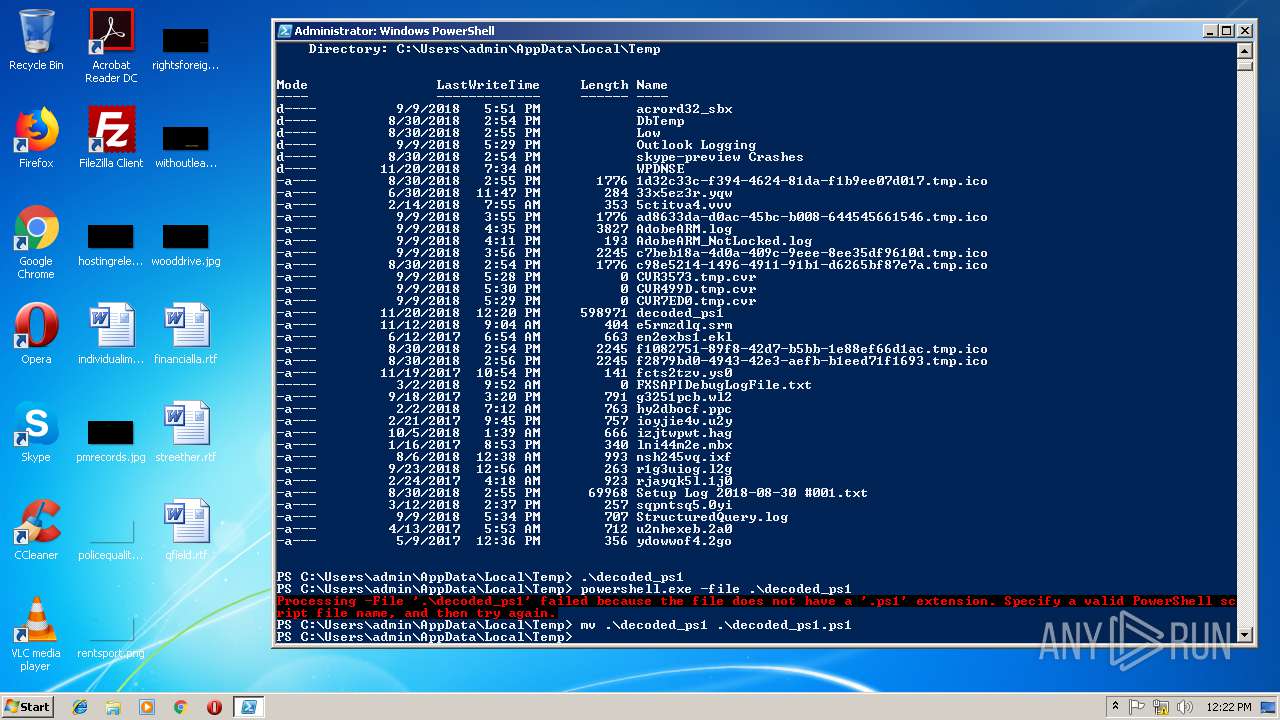
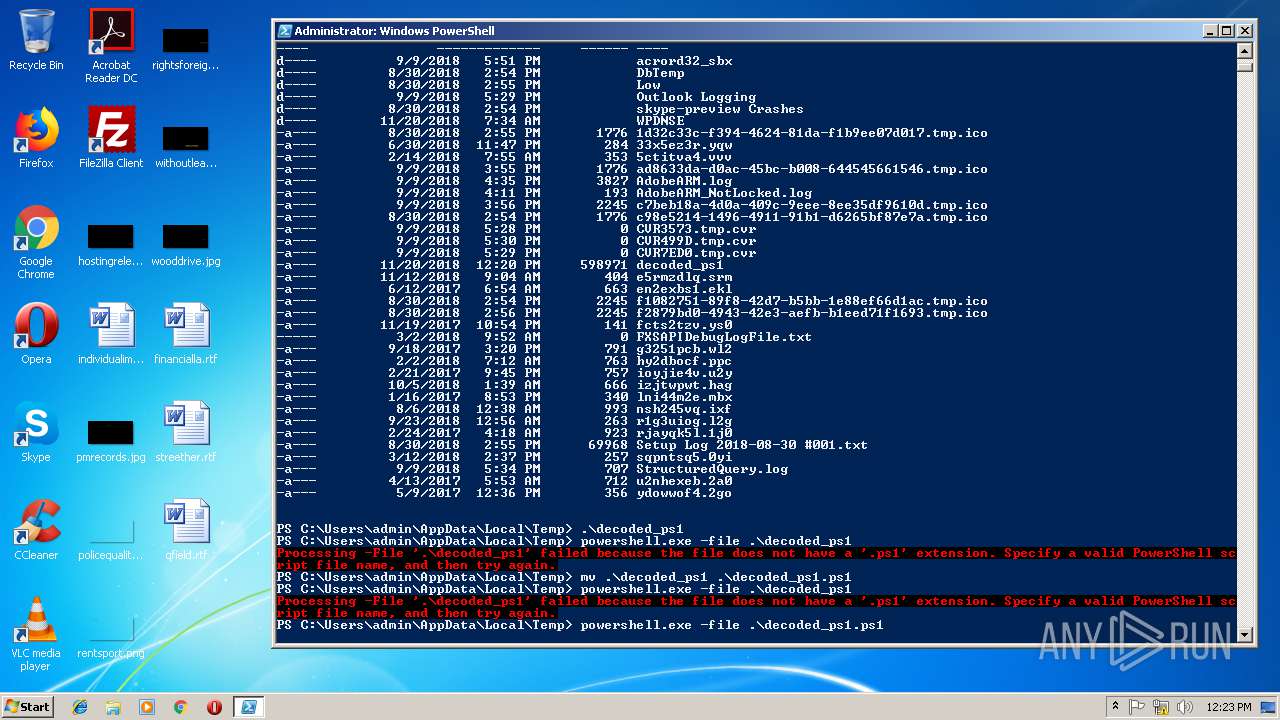
| 800 | "C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe" -file .\decoded_ps1 | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 4294770688 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
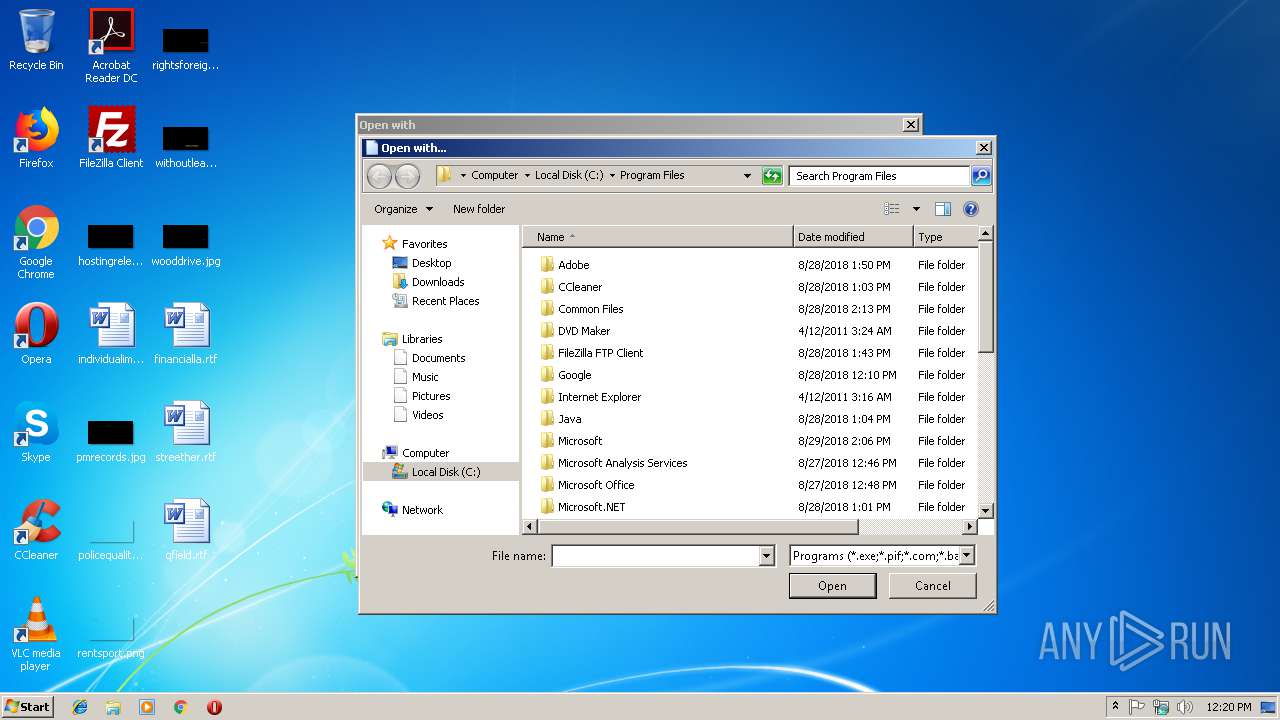
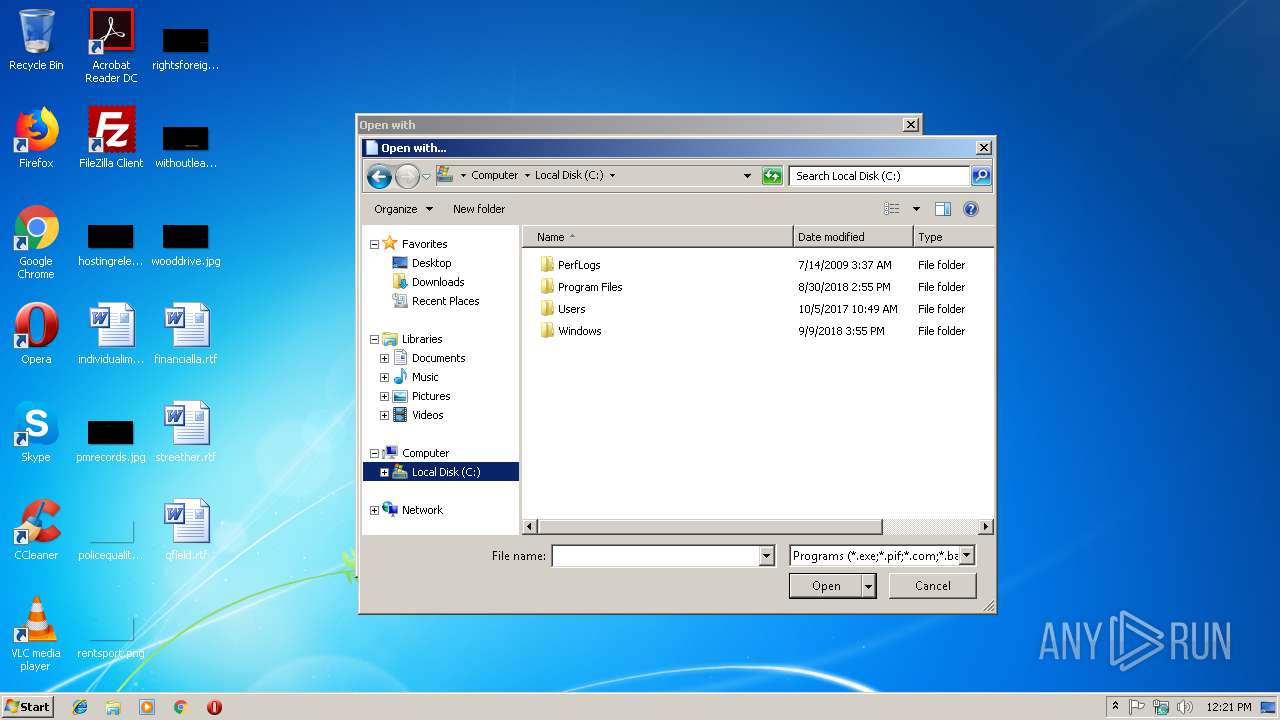
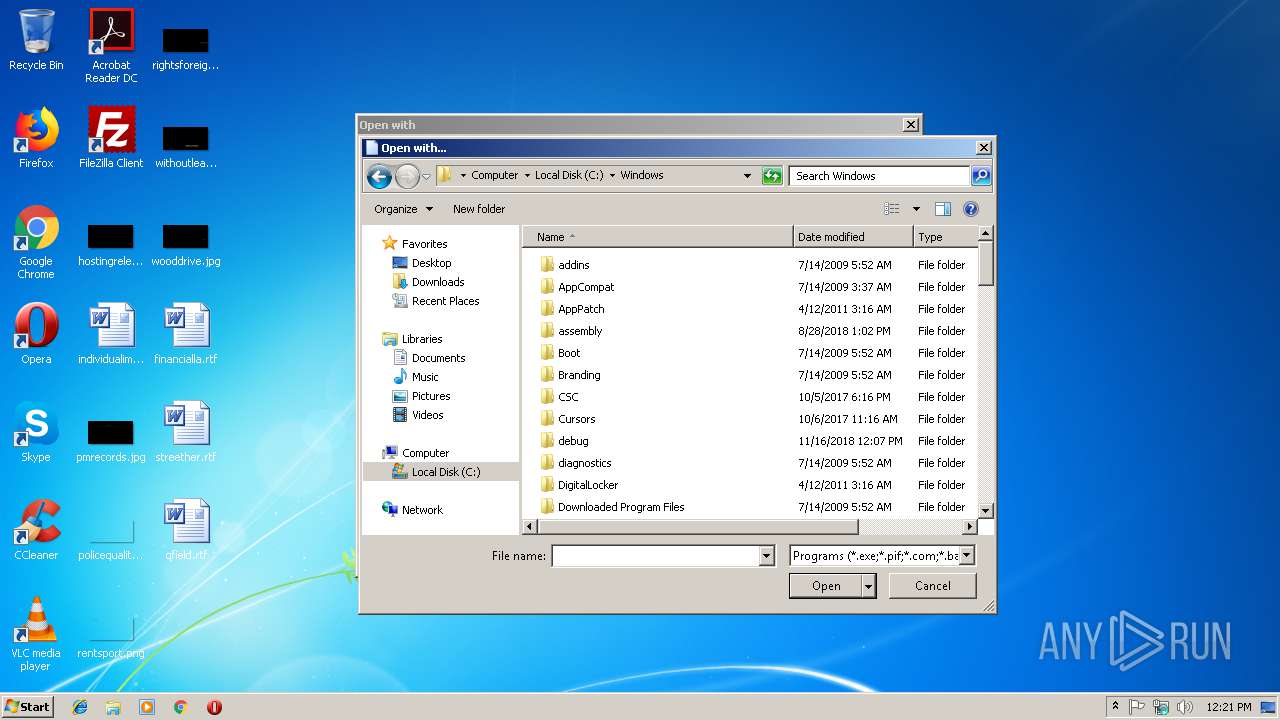
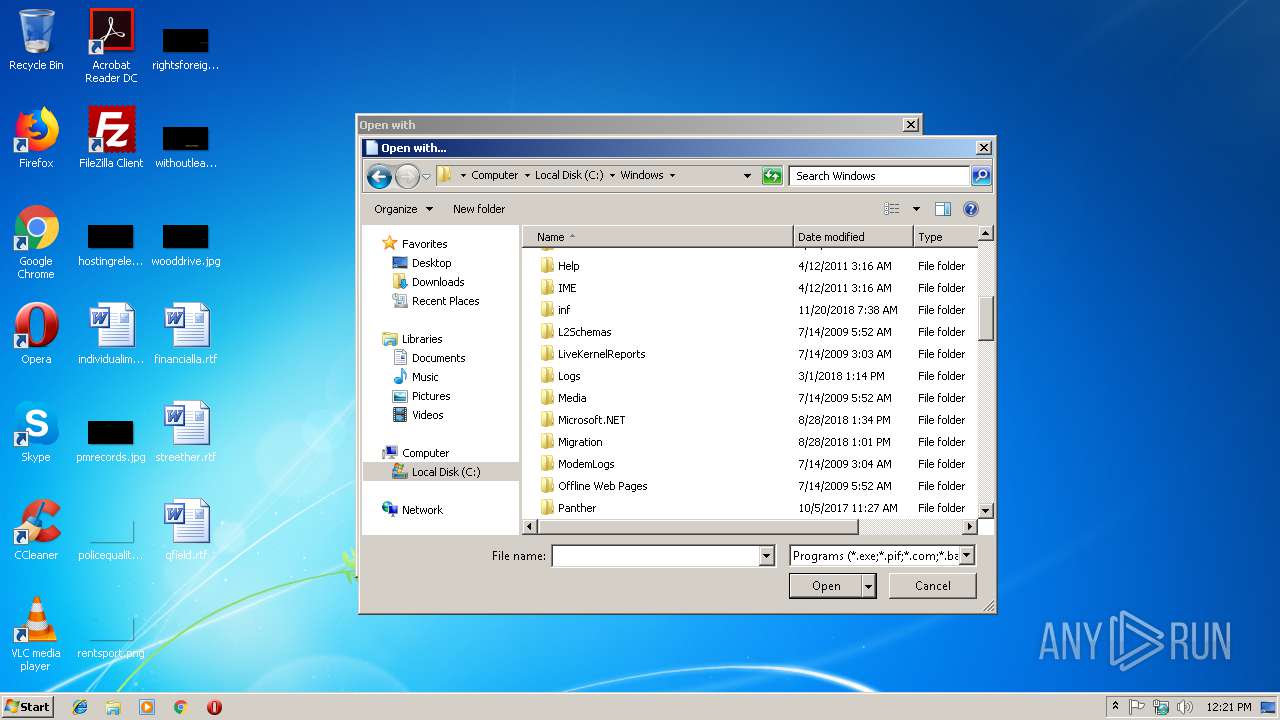
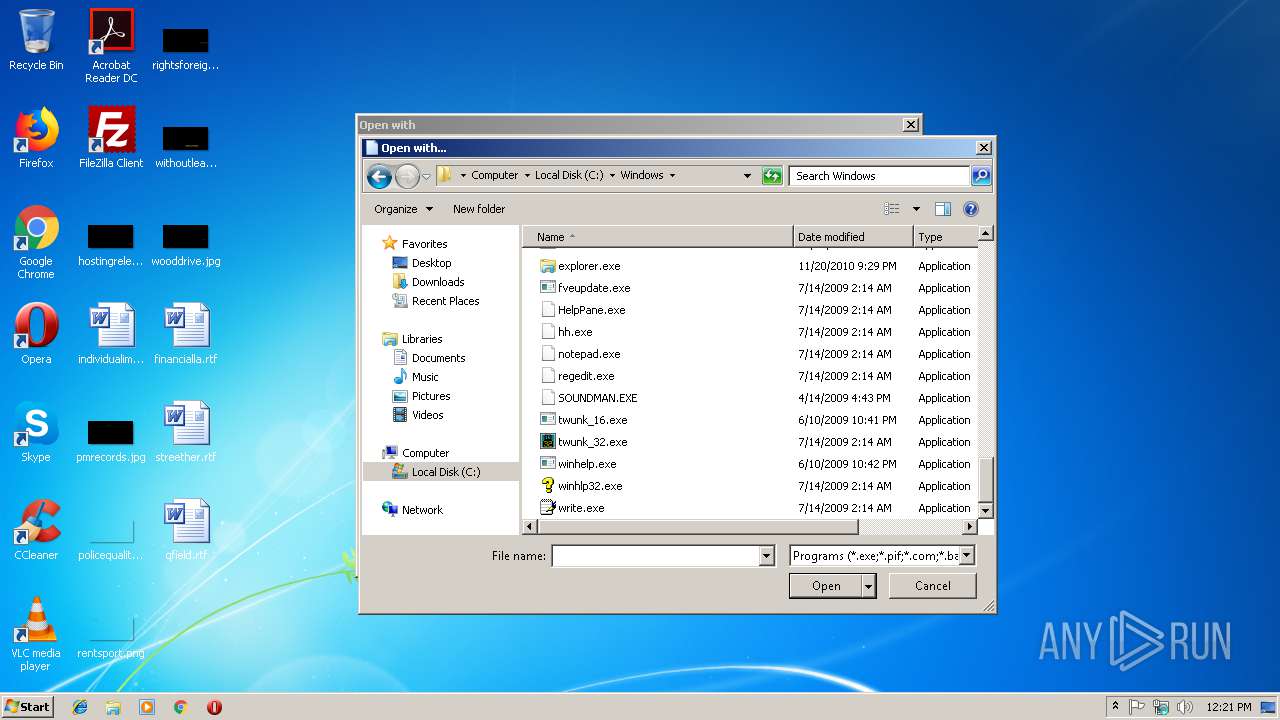
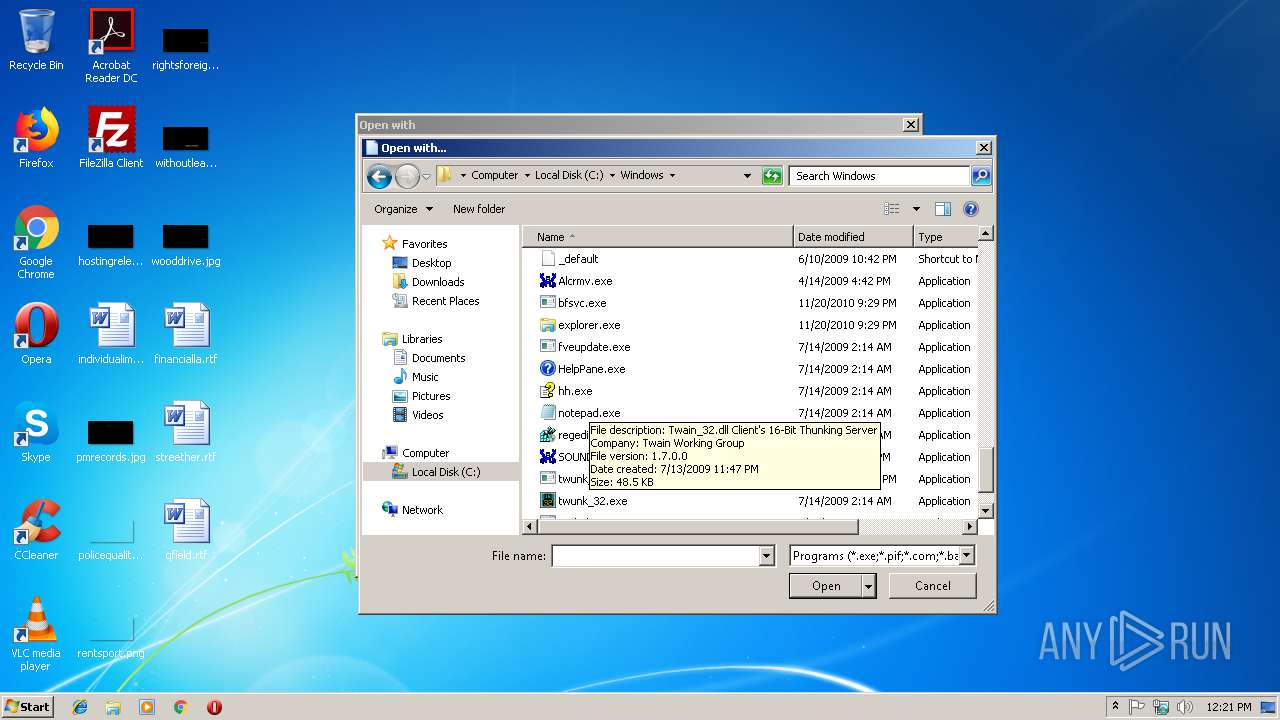
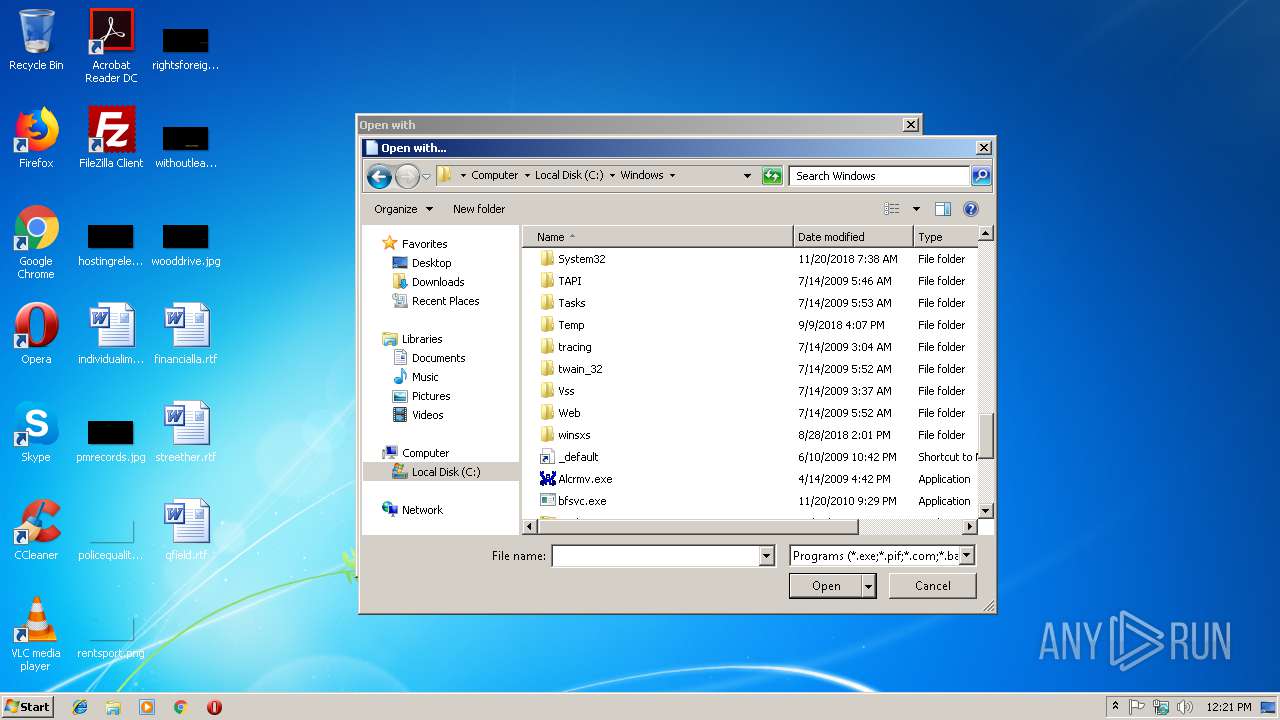
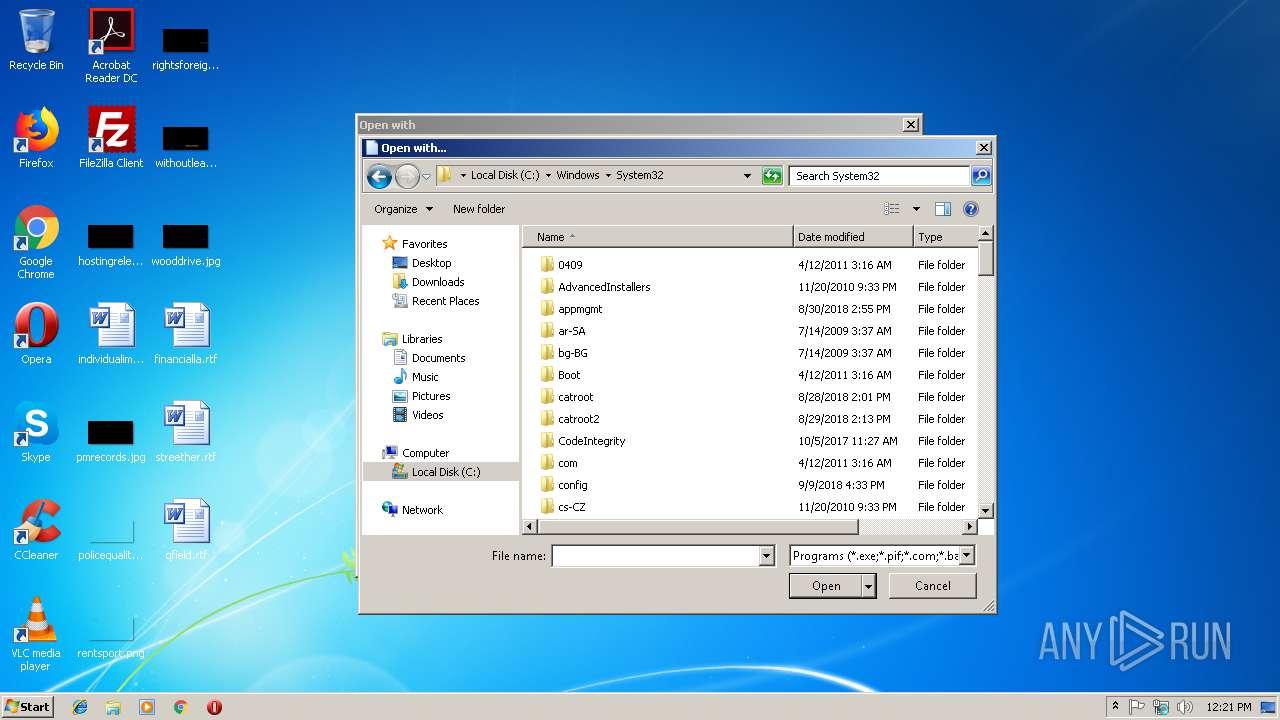
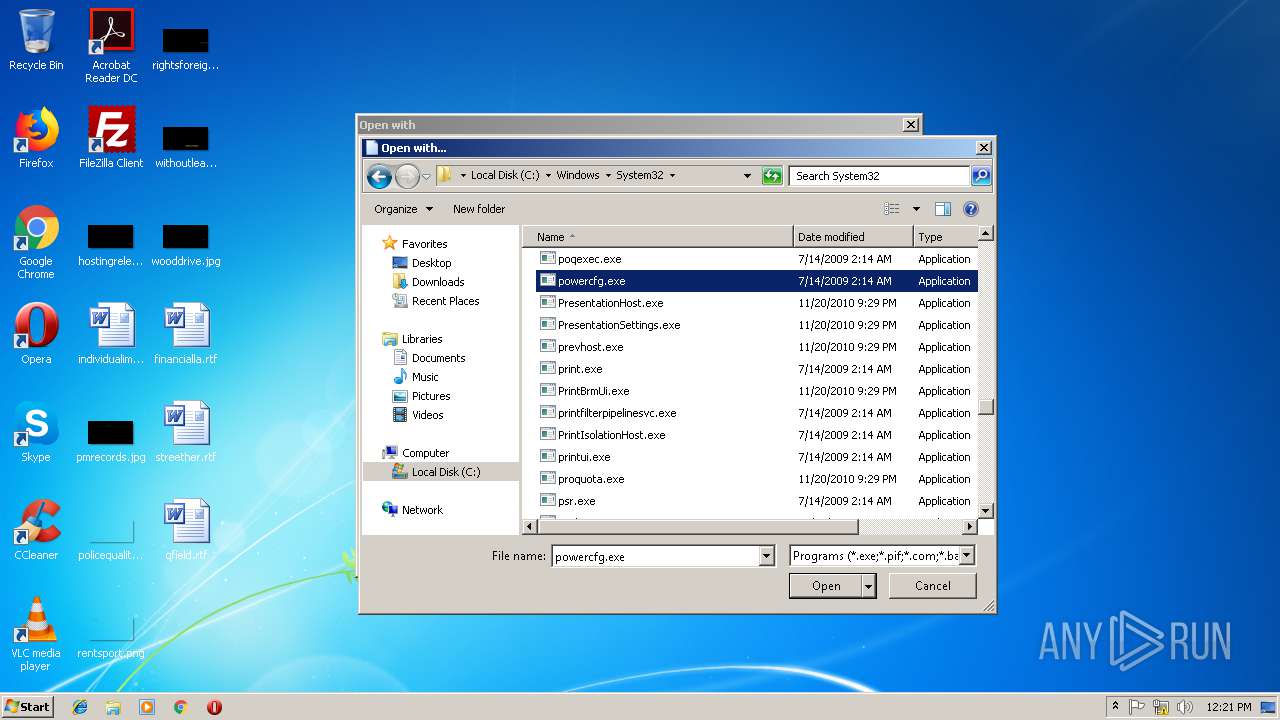
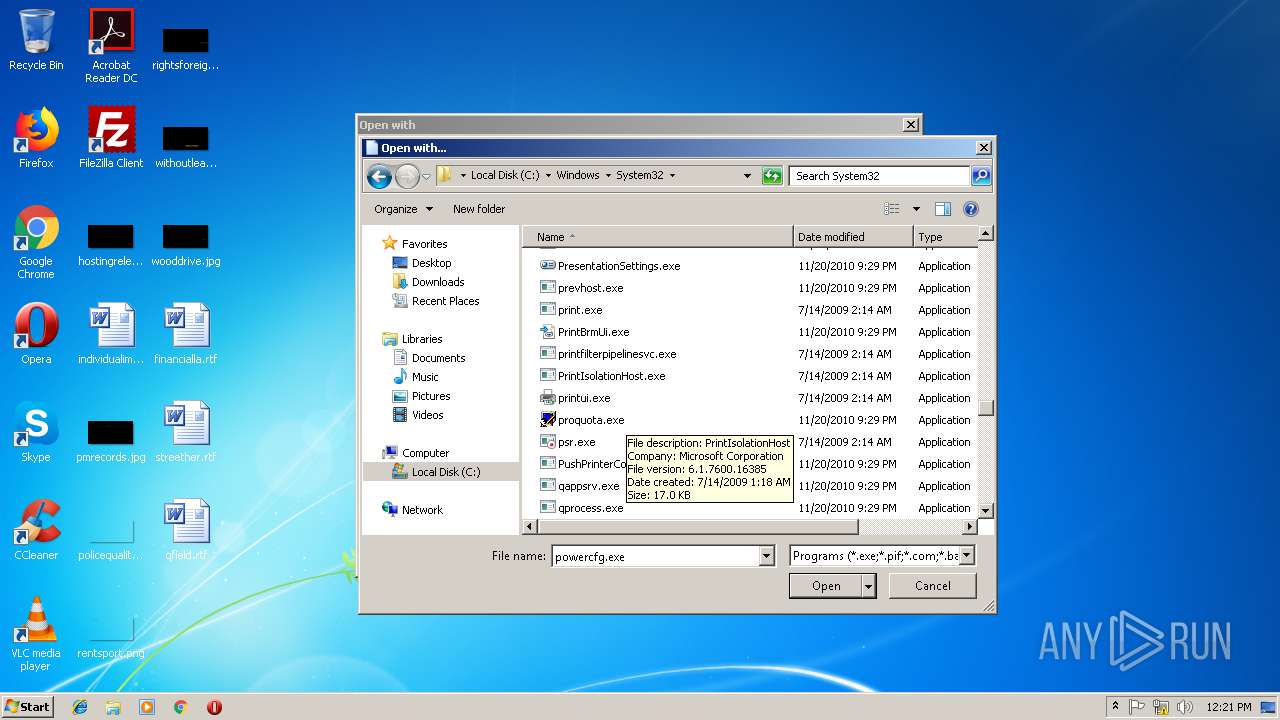
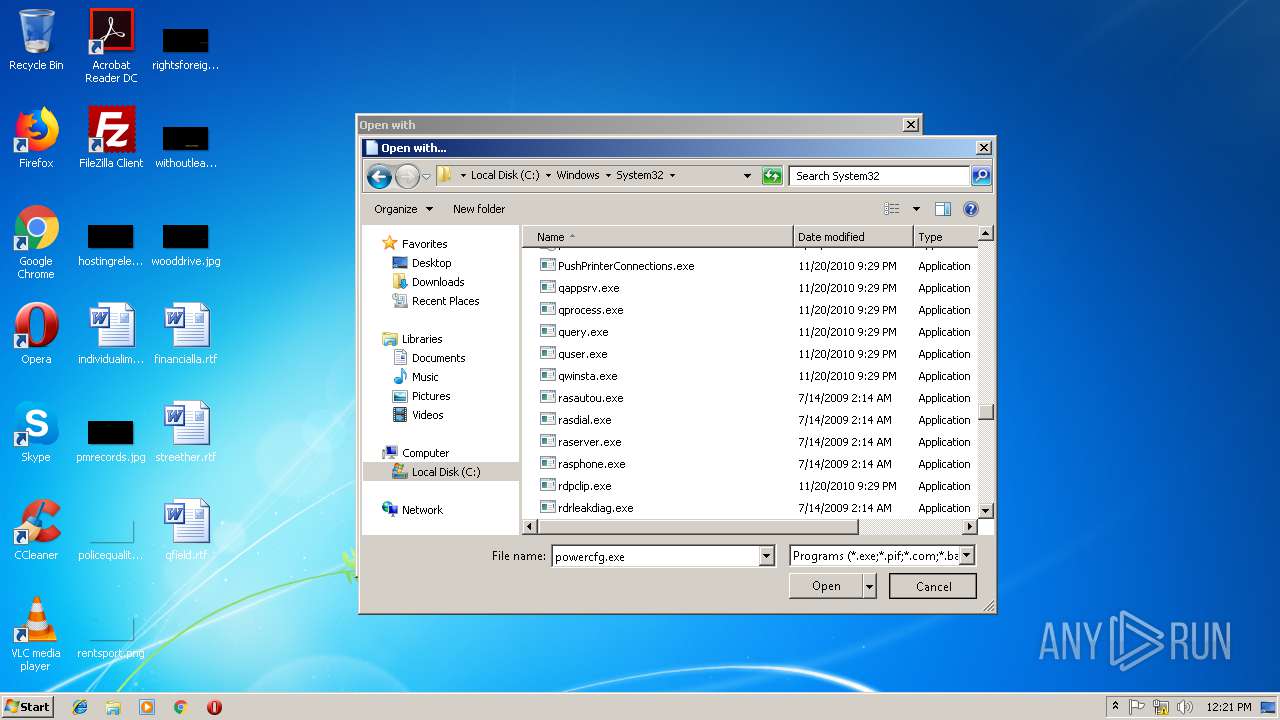
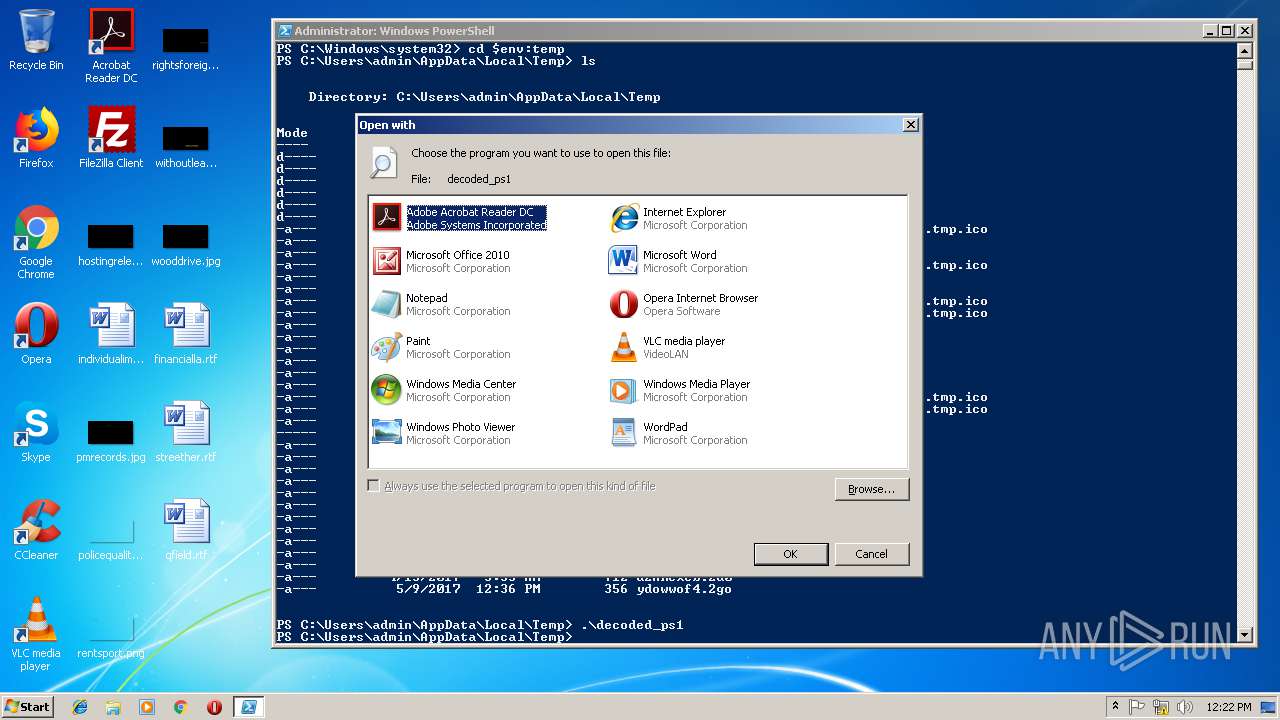
| 2996 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\decoded_ps1 | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3236 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
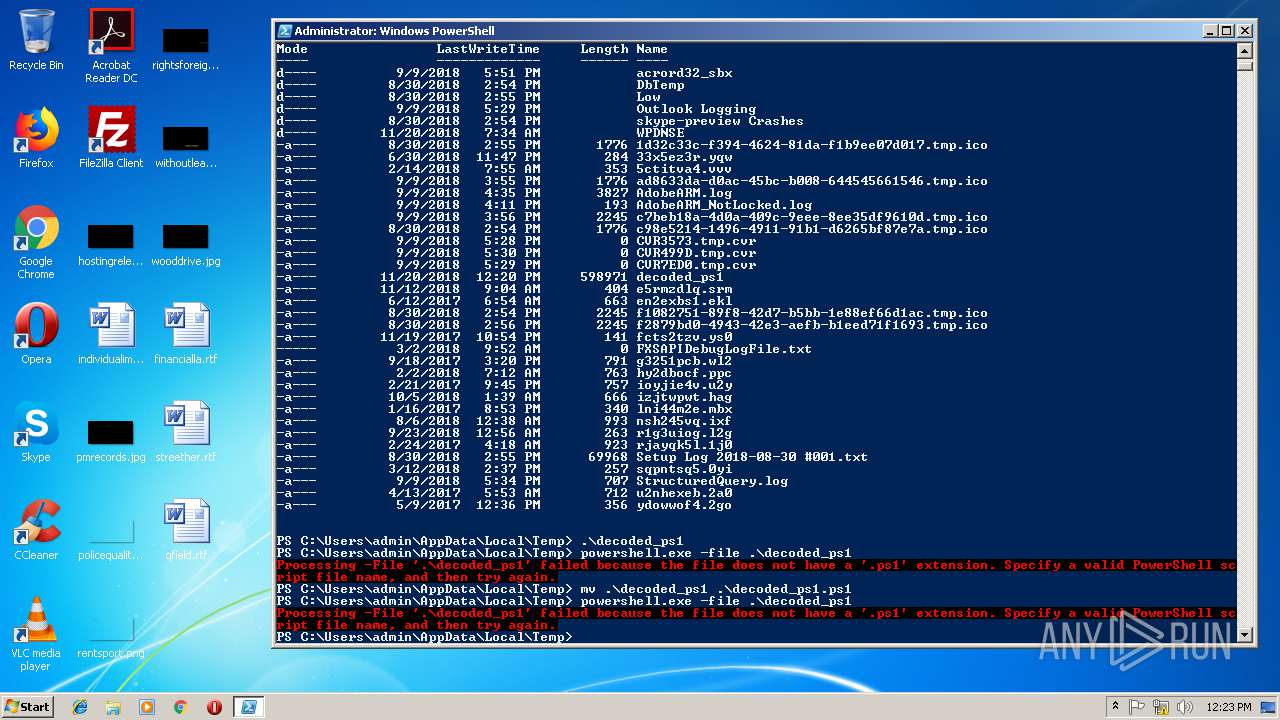
| 3568 | "C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe" -file .\decoded_ps1.ps1 | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3684 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\decoded_ps1 | C:\Windows\system32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3712 | "C:\Users\admin\AppData\Roaming\WTKOd.exe" | C:\Users\admin\AppData\Roaming\WTKOd.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3872 | "C:\Users\admin\AppData\Roaming\WTKOd.exe" | C:\Users\admin\AppData\Roaming\WTKOd.exe | WTKOd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3876 | "C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe" -file .\decoded_ps1 | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 4294770688 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4080 | "C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe" | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 373
Read events
1 969
Write events
402
Delete events
2
Modification events
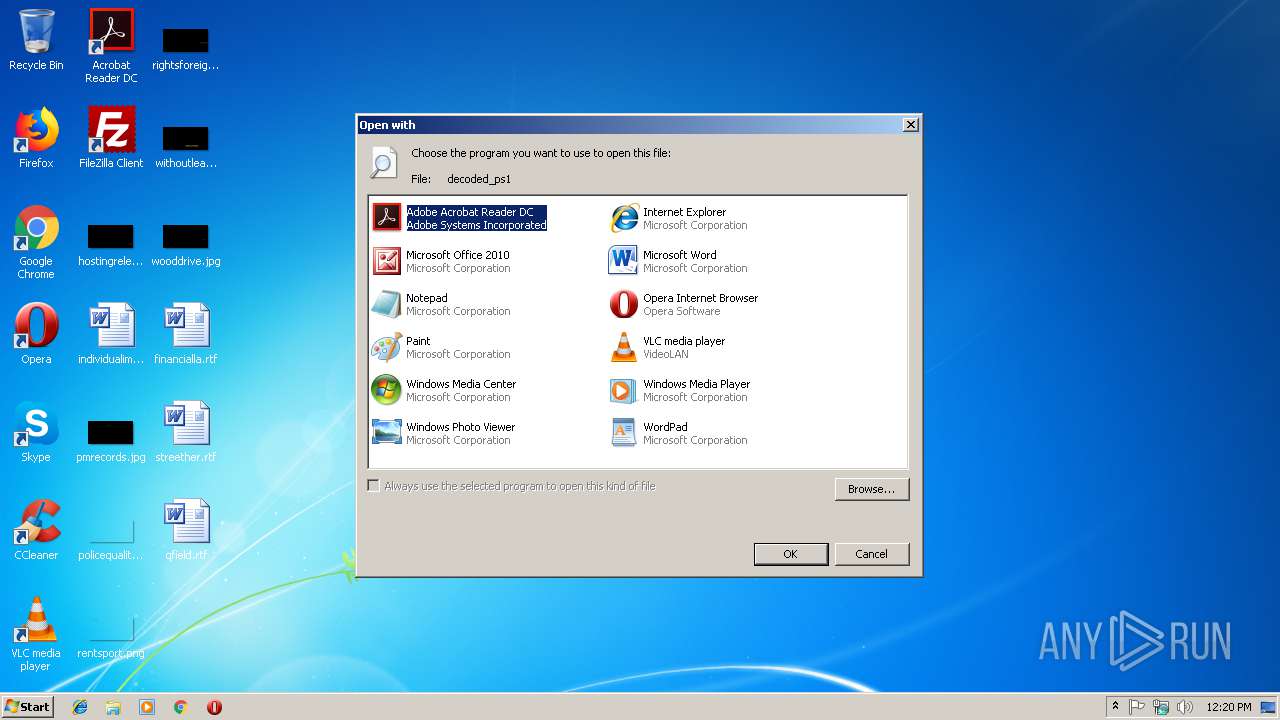
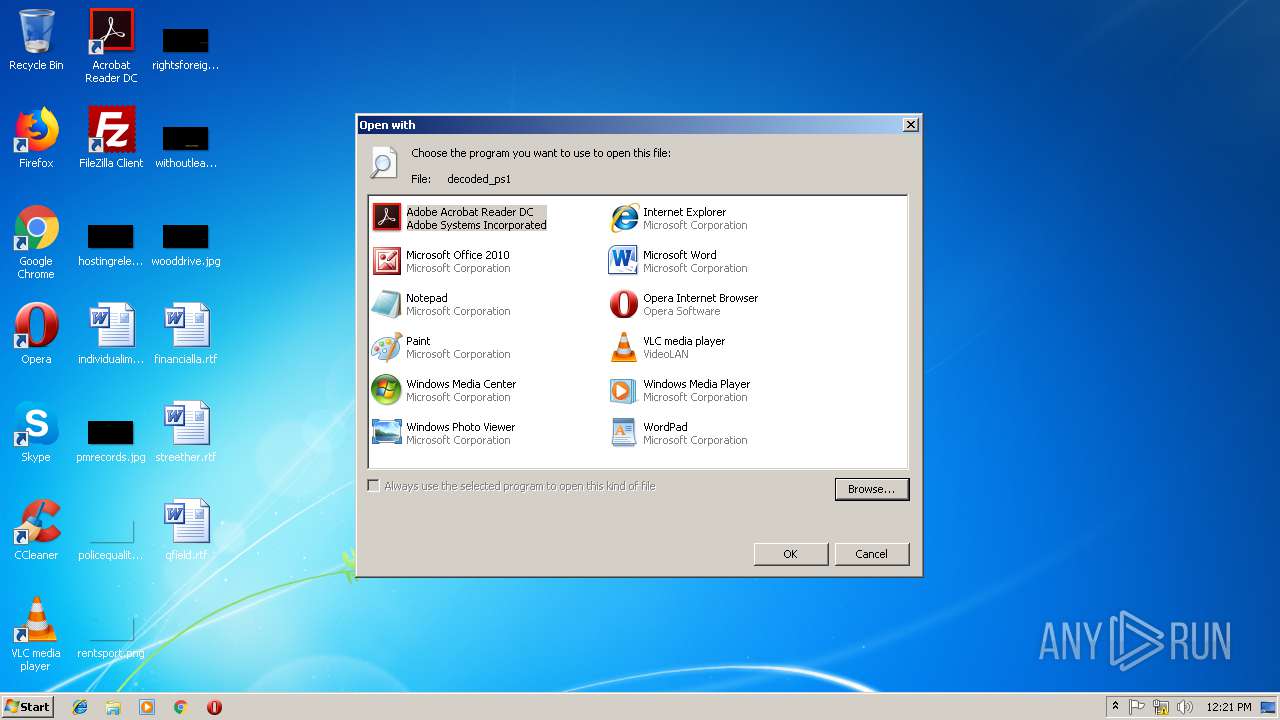
| (PID) Process: | (2996) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (2996) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2996) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (2996) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2996) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2996) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (2996) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (2996) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (2996) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (2996) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
4
Suspicious files
8
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RBR65024KMK3AHZD0WOB.temp | — | |
MD5:— | SHA256:— | |||
| 800 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\U1BYLTNHA8YGJCLAC2V0.temp | — | |
MD5:— | SHA256:— | |||
| 3876 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RL26FRGA9YTIN7OX8X8R.temp | — | |
MD5:— | SHA256:— | |||
| 3568 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\IKEQFDDLYC89PWAJ81P5.temp | — | |
MD5:— | SHA256:— | |||
| 3872 | WTKOd.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 800 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF26aca2.TMP | binary | |
MD5:— | SHA256:— | |||
| 4080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF25d230.TMP | binary | |
MD5:— | SHA256:— | |||
| 3568 | powershell.exe | C:\Users\admin\AppData\Roaming\WTKOd.exe | executable | |
MD5:— | SHA256:— | |||
| 3872 | WTKOd.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.hdb | text | |
MD5:— | SHA256:— | |||
| 3712 | WTKOd.exe | C:\Users\admin\AppData\Local\Temp\Disk.sys | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
1
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3872 | WTKOd.exe | POST | — | 142.44.213.212:80 | http://apolovapers.com/app/images/five/fre.php | CA | — | — | malicious |
3872 | WTKOd.exe | POST | — | 142.44.213.212:80 | http://apolovapers.com/app/images/five/fre.php | CA | — | — | malicious |
3872 | WTKOd.exe | POST | — | 142.44.213.212:80 | http://apolovapers.com/app/images/five/fre.php | CA | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3872 | WTKOd.exe | 142.44.213.212:80 | apolovapers.com | OVH SAS | CA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
apolovapers.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3872 | WTKOd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki/Pony Bot Artifact Check-in |
3872 | WTKOd.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3872 | WTKOd.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3872 | WTKOd.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3872 | WTKOd.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
3872 | WTKOd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
3872 | WTKOd.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
3872 | WTKOd.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
3872 | WTKOd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki/Pony Bot Artifact Check-in |
3872 | WTKOd.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
3 ETPRO signatures available at the full report