| File name: | 2b1b7b6c06a8f60211331cffaa78a8d1.exe |
| Full analysis: | https://app.any.run/tasks/199e6b83-c8aa-4600-b625-7ddc6183e5ff |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | December 28, 2024, 13:34:02 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 2B1B7B6C06A8F60211331CFFAA78A8D1 |
| SHA1: | D1EBA81DBDAC3E30DF2256BB4C929C41C24BD7C6 |
| SHA256: | B90F802252D6DFAF25FCB579649ECB7013EC459EEC96941CA6E835719D037CCB |
| SSDEEP: | 6144:Kjy+bnr+2p0yN90QEos8XdDL1s/aso3eQwAV50vBWg/Lcrx/10zr0a/THAiD:5Mr+y90U3dsseTG0vcAcrx/6zr0a/TzD |
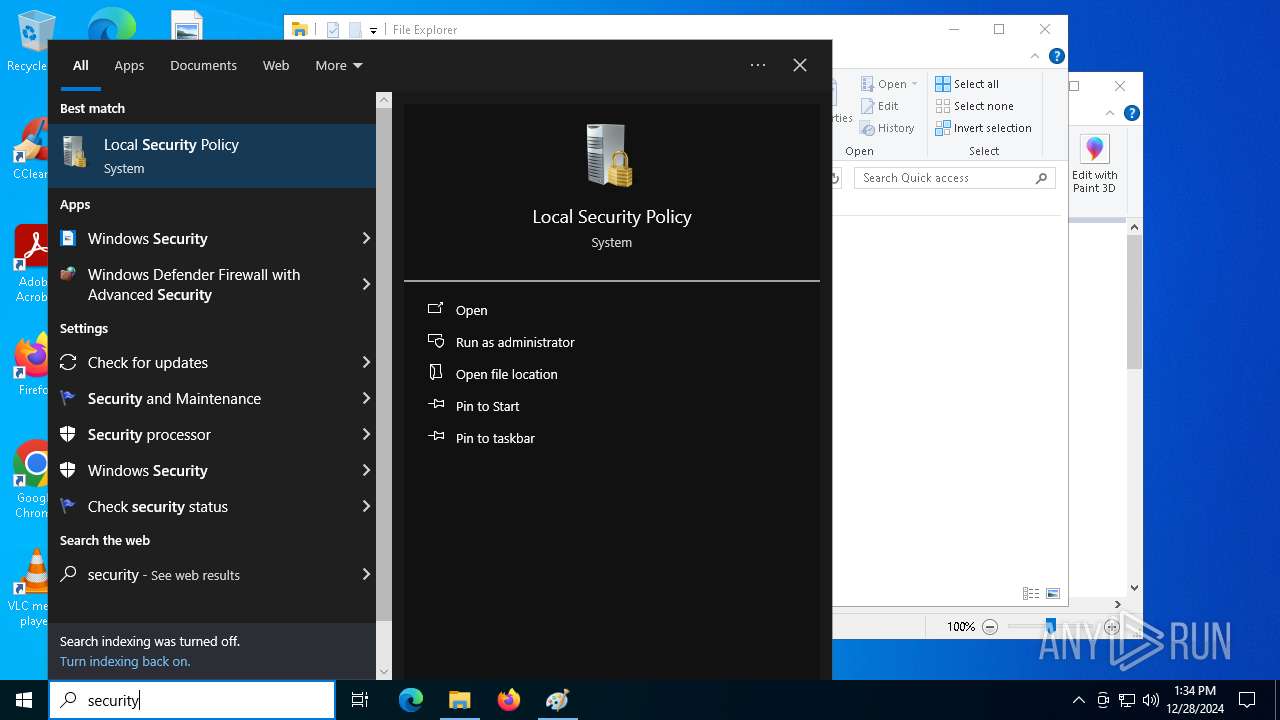
MALICIOUS
Changes the autorun value in the registry
- danke.exe (PID: 6296)
Uses Task Scheduler to run other applications
- danke.exe (PID: 6296)
Runs injected code in another process
- c6795757.exe (PID: 6324)
AMADEY mutex has been found
- danke.exe (PID: 6296)
- danke.exe (PID: 6520)
SMOKE mutex has been found
- explorer.exe (PID: 4488)
AMADEY has been detected (YARA)
- danke.exe (PID: 6296)
Application was injected by another process
- explorer.exe (PID: 4488)
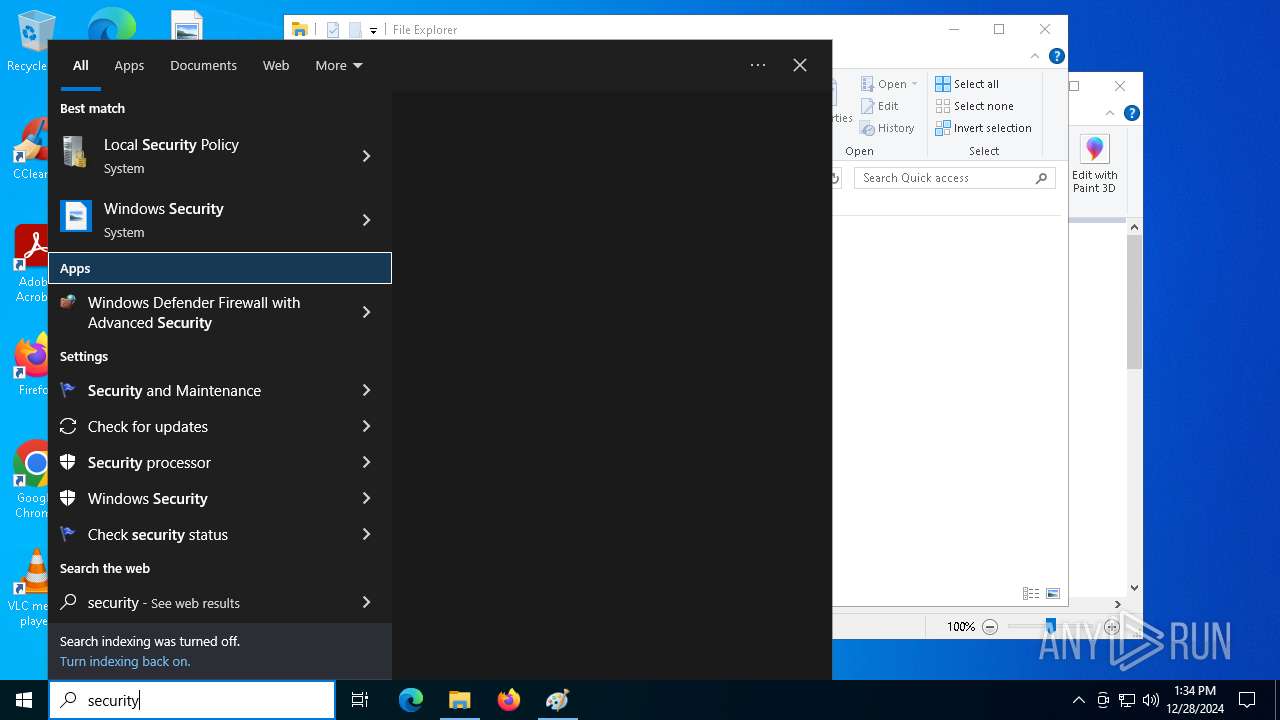
SUSPICIOUS
Process drops legitimate windows executable
- 2b1b7b6c06a8f60211331cffaa78a8d1.exe (PID: 4640)
Starts a Microsoft application from unusual location
- 2b1b7b6c06a8f60211331cffaa78a8d1.exe (PID: 4640)
- v2006608.exe (PID: 5400)
Executable content was dropped or overwritten
- 2b1b7b6c06a8f60211331cffaa78a8d1.exe (PID: 4640)
- v2006608.exe (PID: 5400)
- b0457861.exe (PID: 204)
Reads security settings of Internet Explorer
- b0457861.exe (PID: 204)
- danke.exe (PID: 6296)
- SecHealthUI.exe (PID: 5000)
Starts itself from another location
- b0457861.exe (PID: 204)
Starts CMD.EXE for commands execution
- danke.exe (PID: 6296)
- cmd.exe (PID: 6412)
Application launched itself
- cmd.exe (PID: 6412)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 6412)
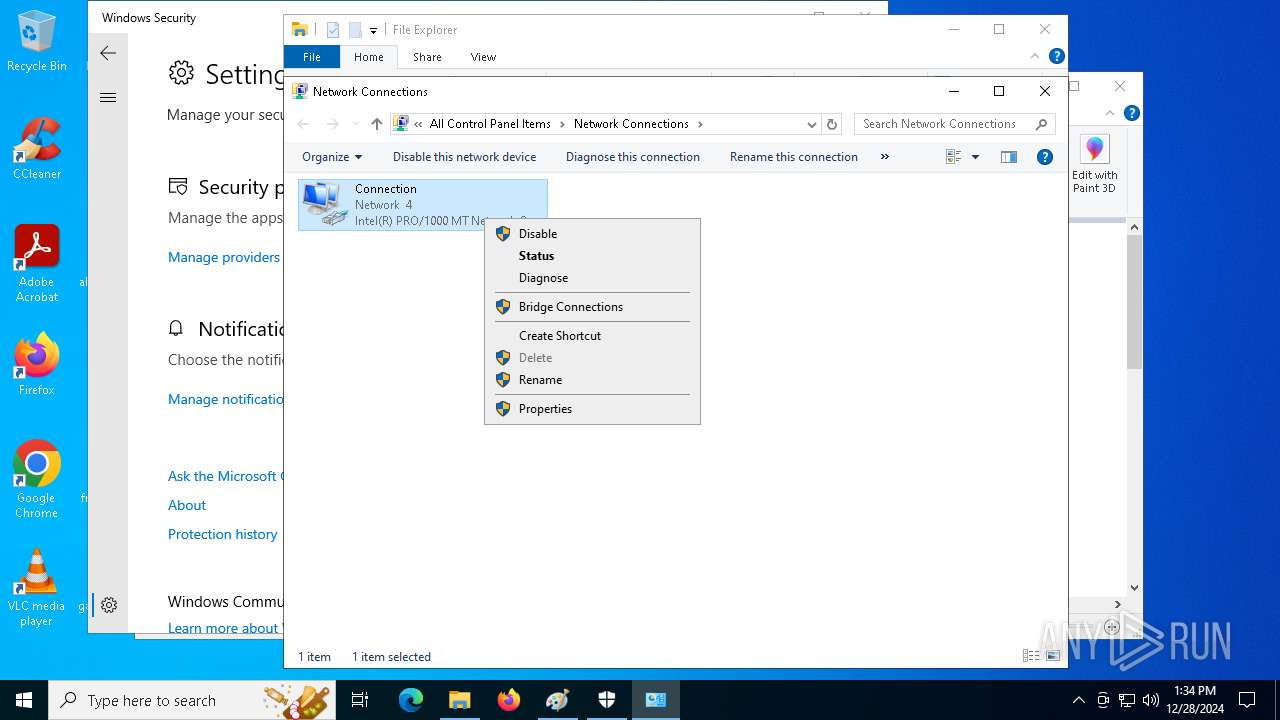
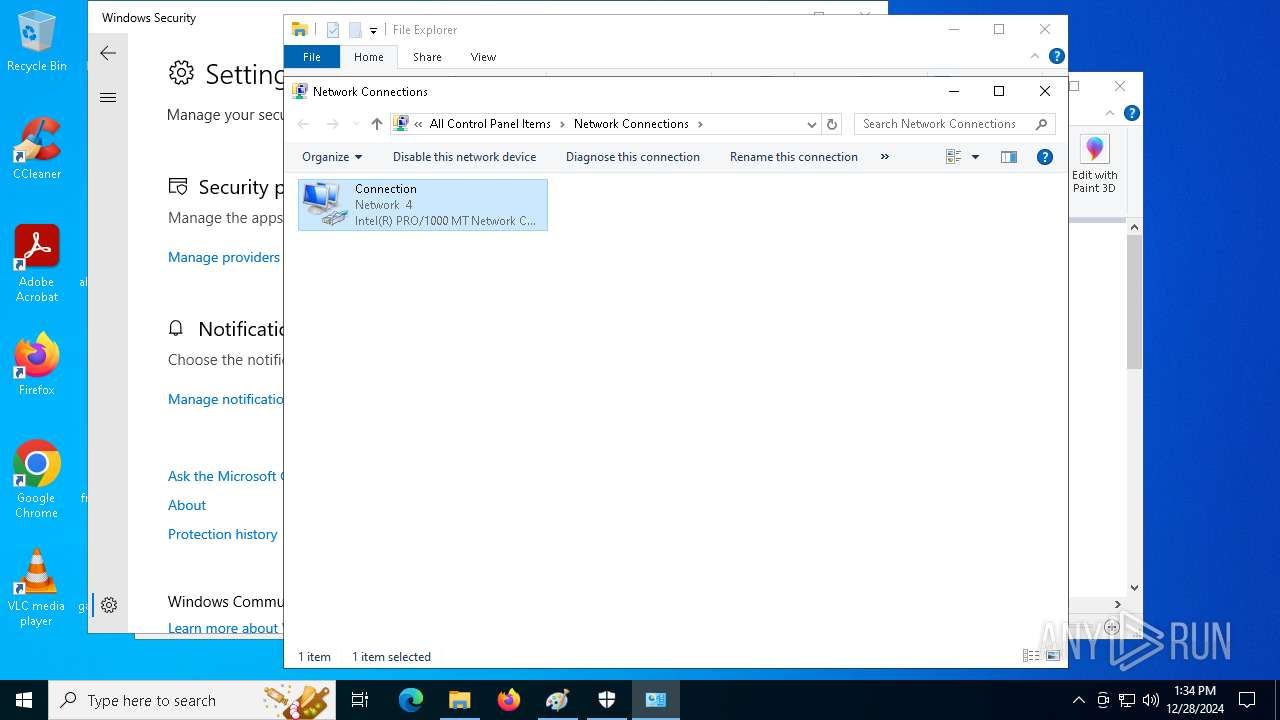
Uses RUNDLL32.EXE to load library
- control.exe (PID: 4976)
The process executes via Task Scheduler
- danke.exe (PID: 6520)
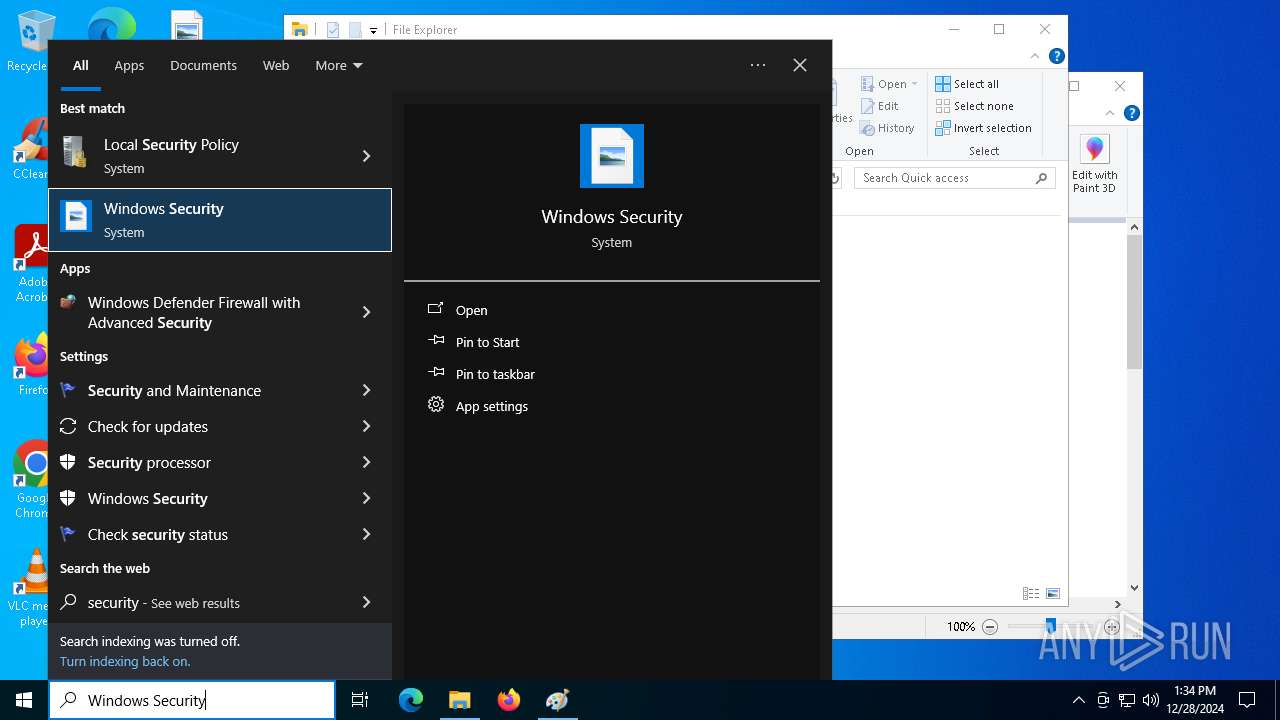
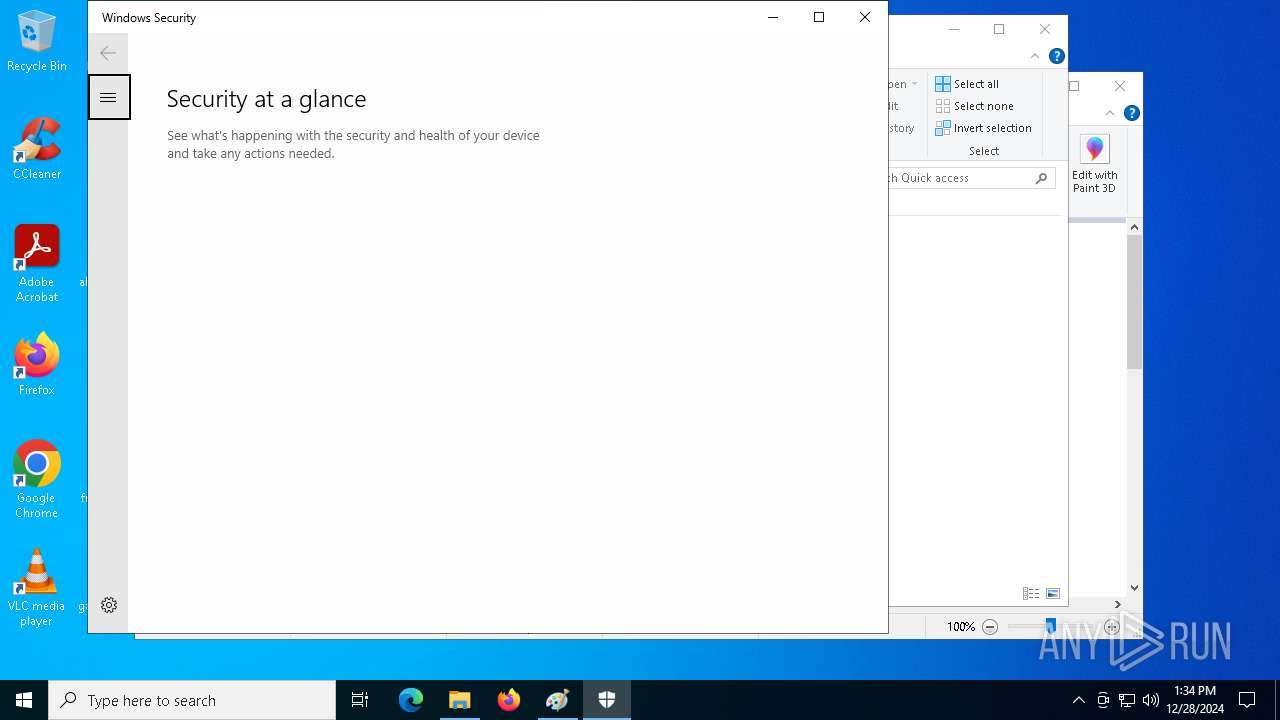
INFO
Checks supported languages
- 2b1b7b6c06a8f60211331cffaa78a8d1.exe (PID: 4640)
- v2006608.exe (PID: 5400)
- a8012580.exe (PID: 4056)
- b0457861.exe (PID: 204)
- c6795757.exe (PID: 6324)
- danke.exe (PID: 6296)
- SecHealthUI.exe (PID: 5000)
- danke.exe (PID: 6520)
Create files in a temporary directory
- 2b1b7b6c06a8f60211331cffaa78a8d1.exe (PID: 4640)
- v2006608.exe (PID: 5400)
- b0457861.exe (PID: 204)
The sample compiled with english language support
- 2b1b7b6c06a8f60211331cffaa78a8d1.exe (PID: 4640)
Reads the computer name
- b0457861.exe (PID: 204)
- a8012580.exe (PID: 4056)
- danke.exe (PID: 6296)
- SecHealthUI.exe (PID: 5000)
The process uses the downloaded file
- b0457861.exe (PID: 204)
- danke.exe (PID: 6296)
- control.exe (PID: 4976)
- explorer.exe (PID: 4488)
Process checks computer location settings
- danke.exe (PID: 6296)
- b0457861.exe (PID: 204)
Checks proxy server information
- danke.exe (PID: 6296)
- explorer.exe (PID: 4488)
Reads security settings of Internet Explorer
- control.exe (PID: 4976)
- explorer.exe (PID: 5916)
- explorer.exe (PID: 4488)
Sends debugging messages
- SecHealthUI.exe (PID: 5000)
Creates files or folders in the user directory
- danke.exe (PID: 6296)
Reads Microsoft Office registry keys
- explorer.exe (PID: 4488)
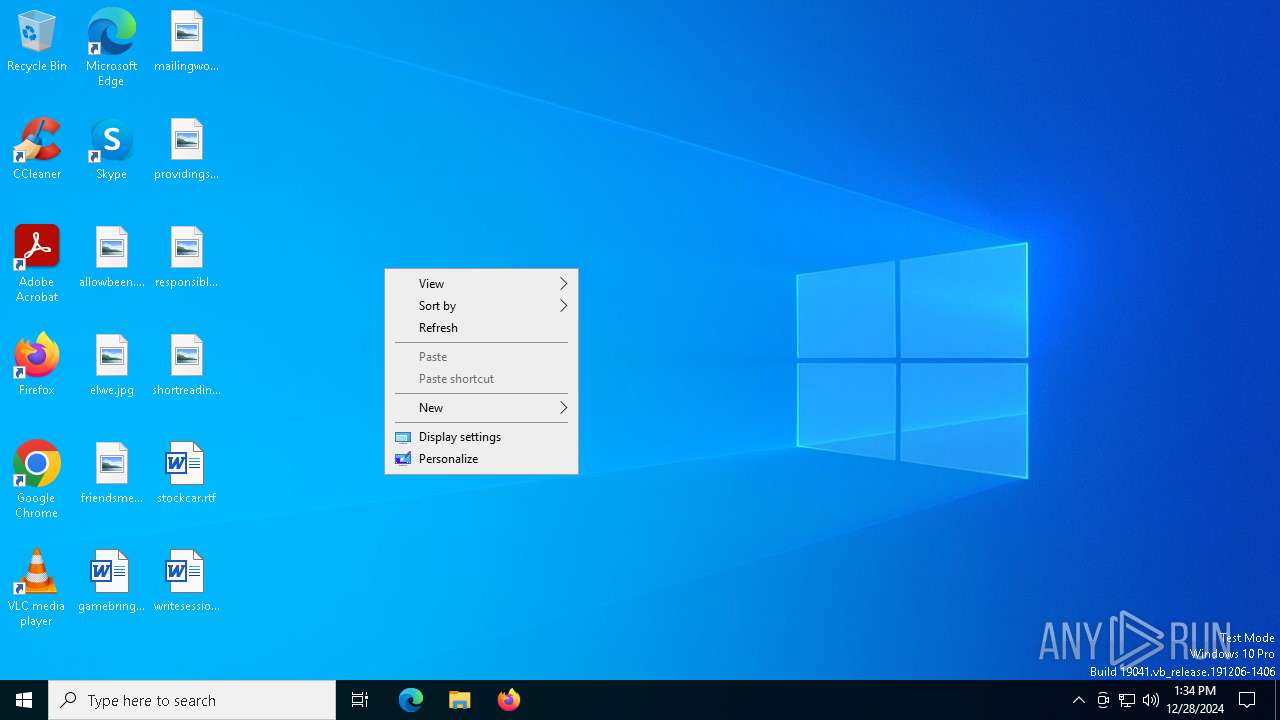
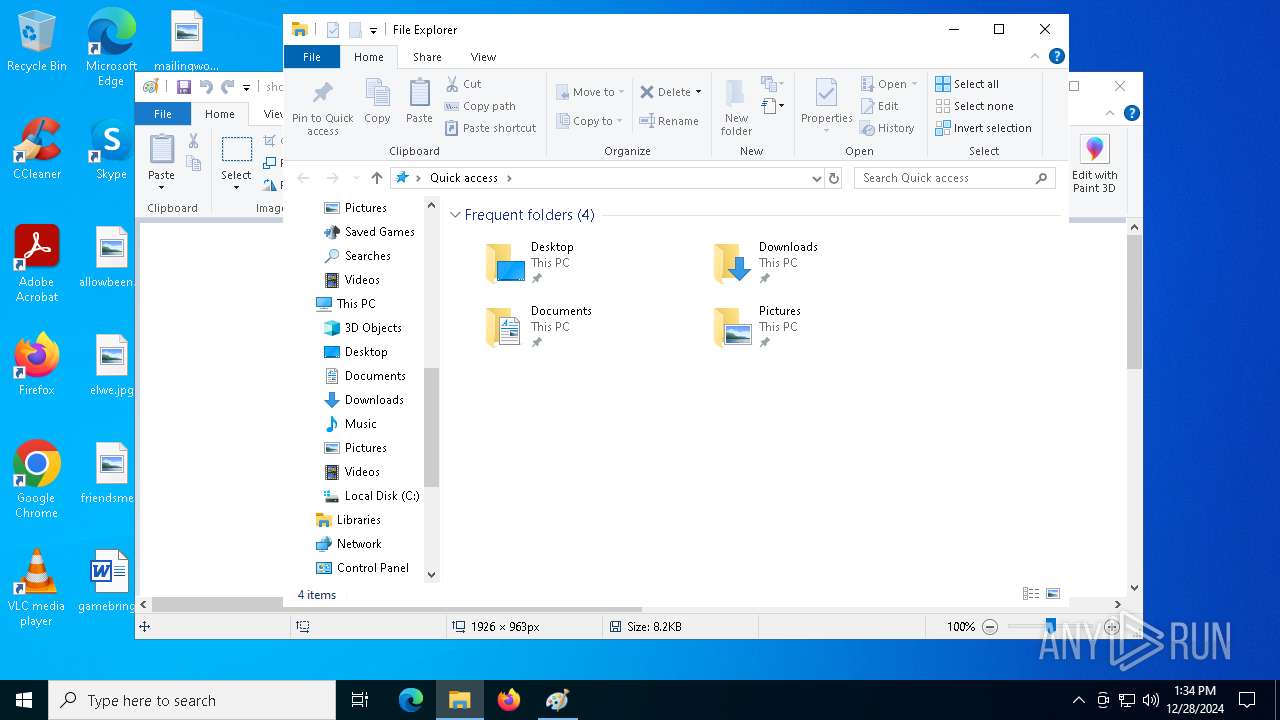
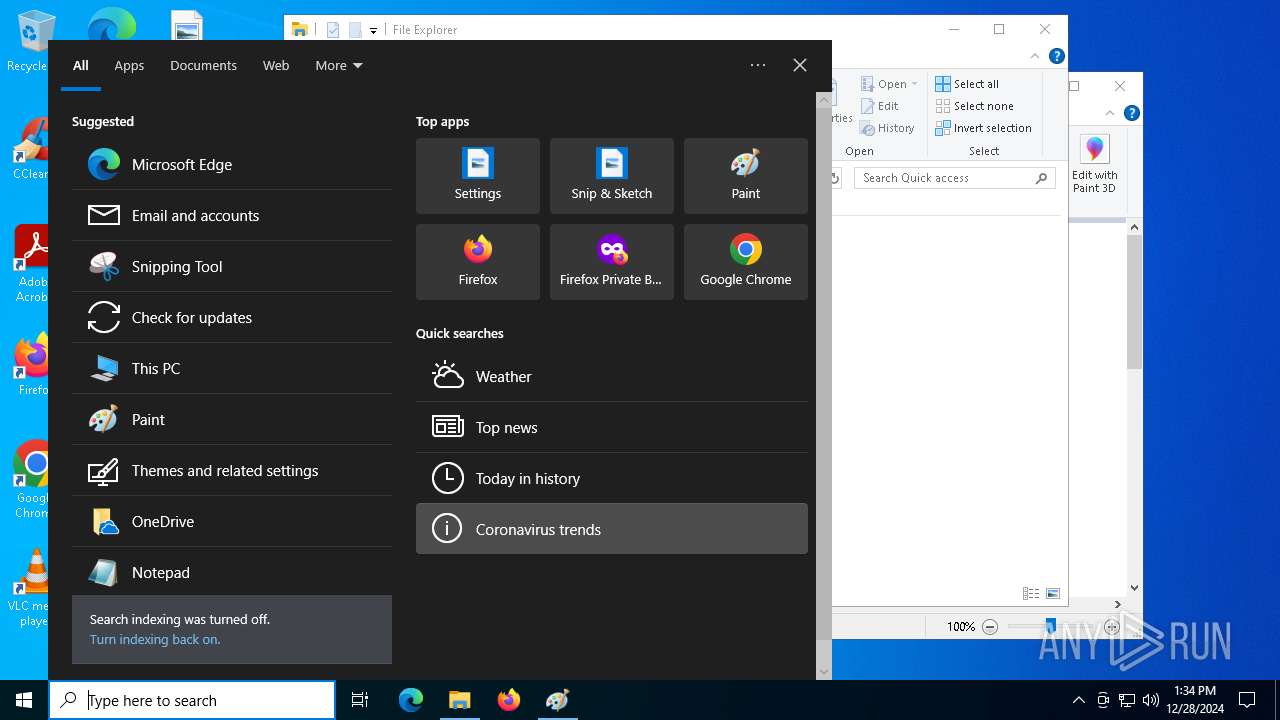
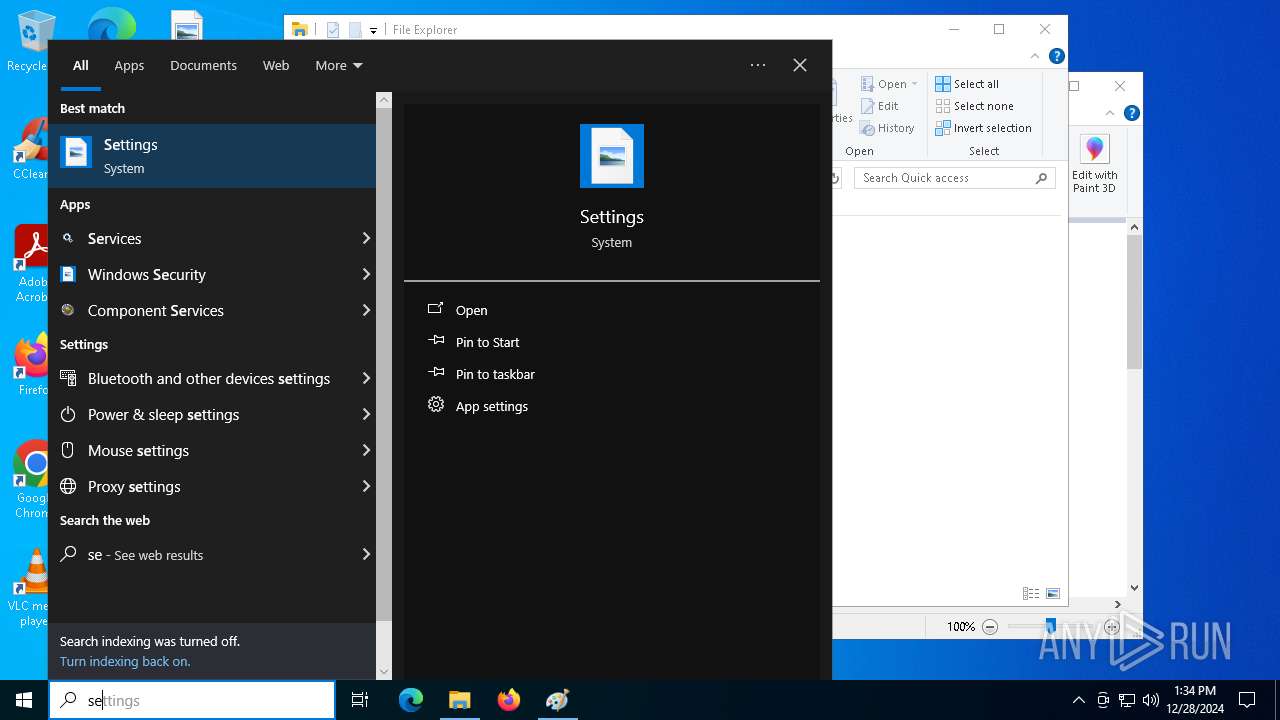
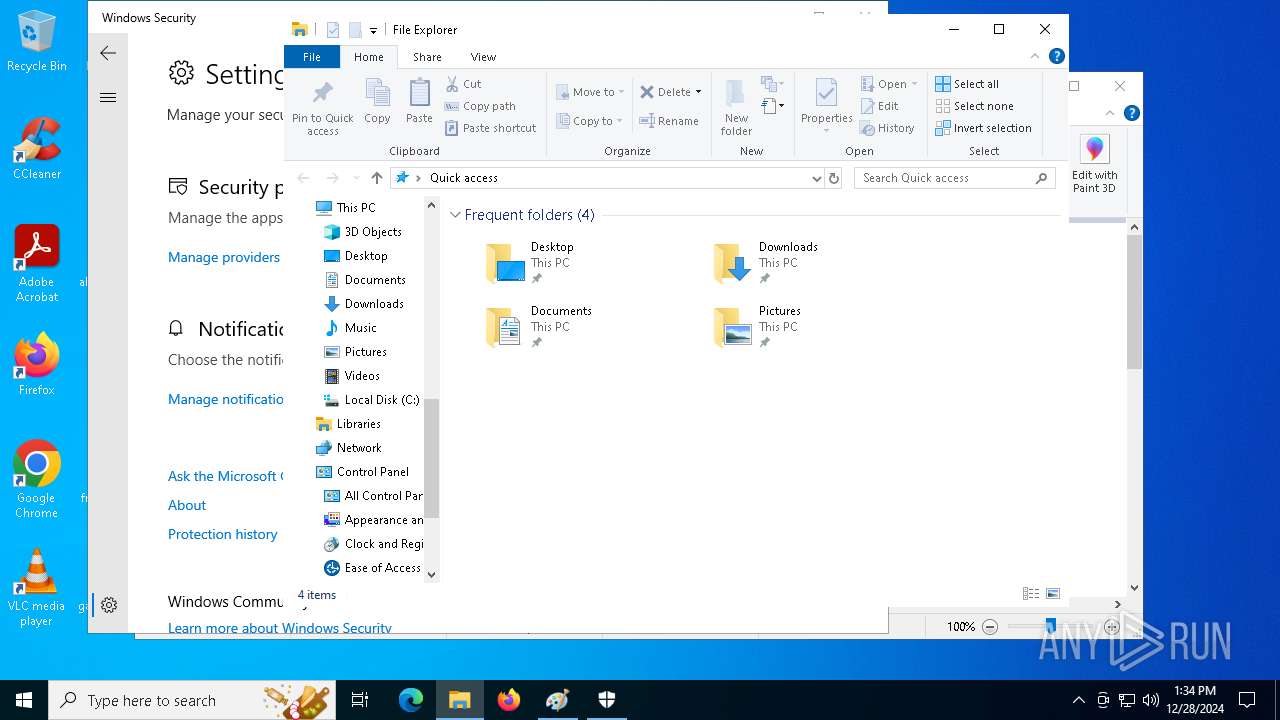
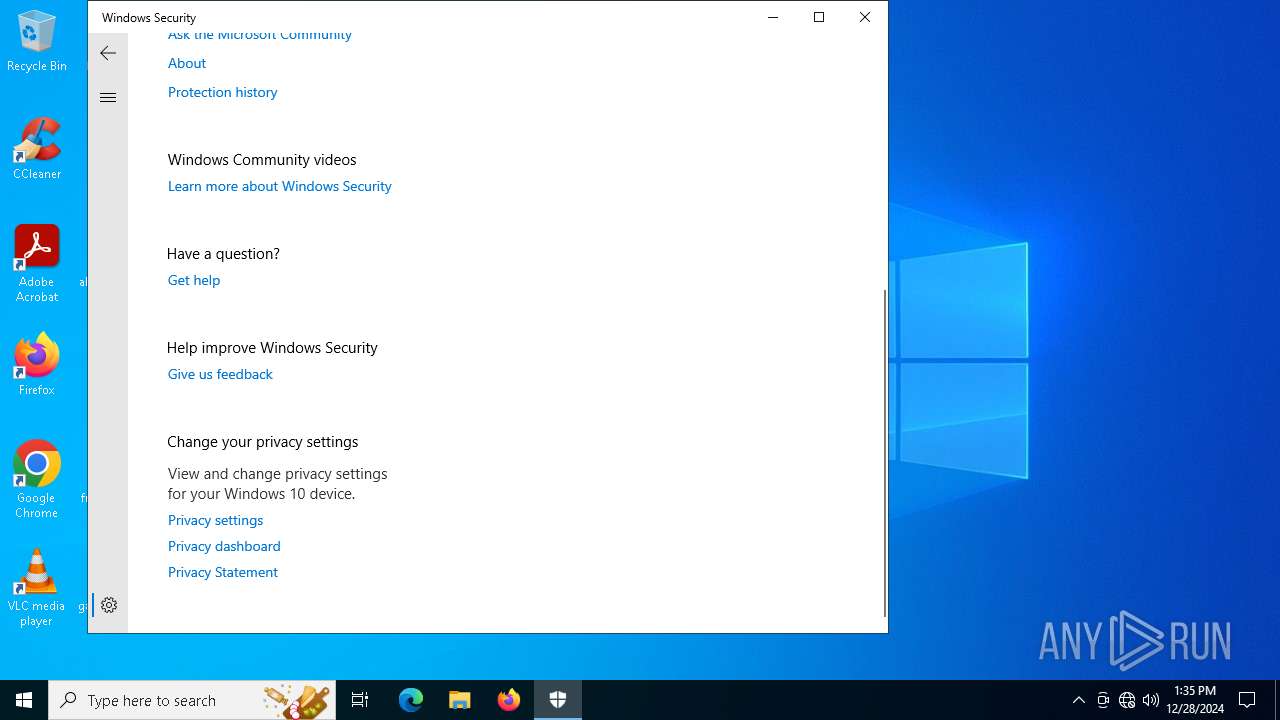
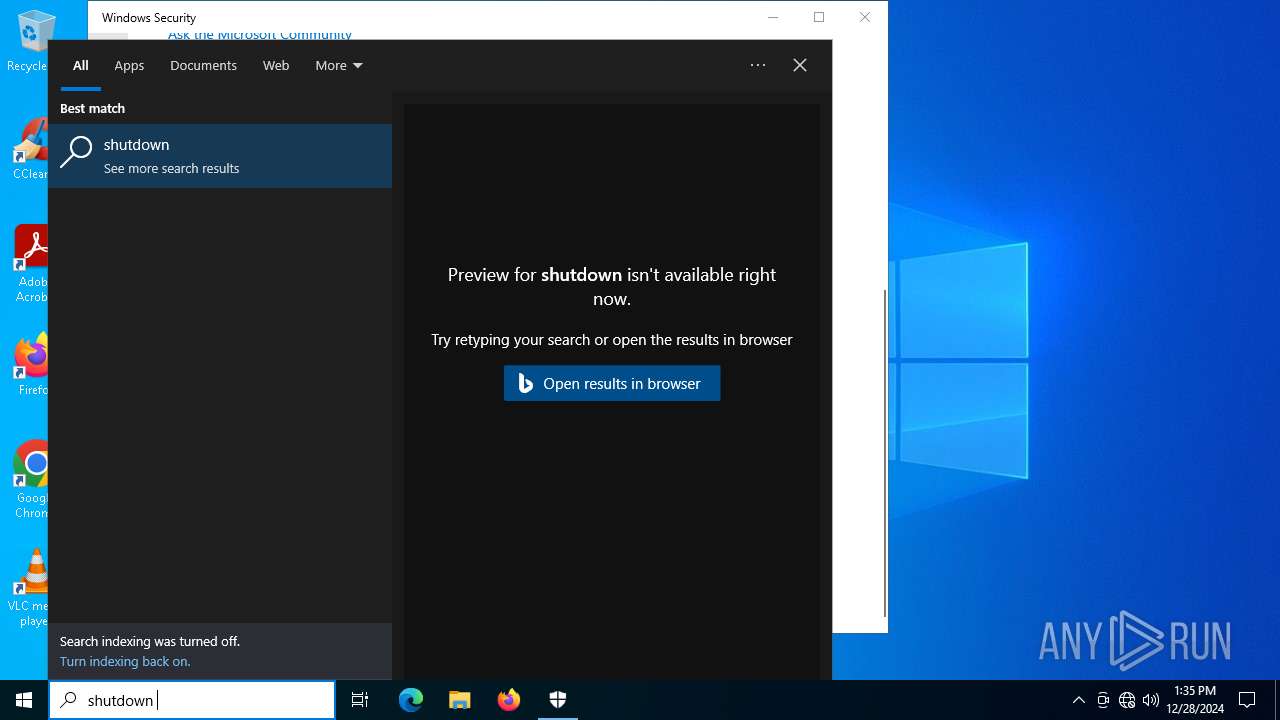
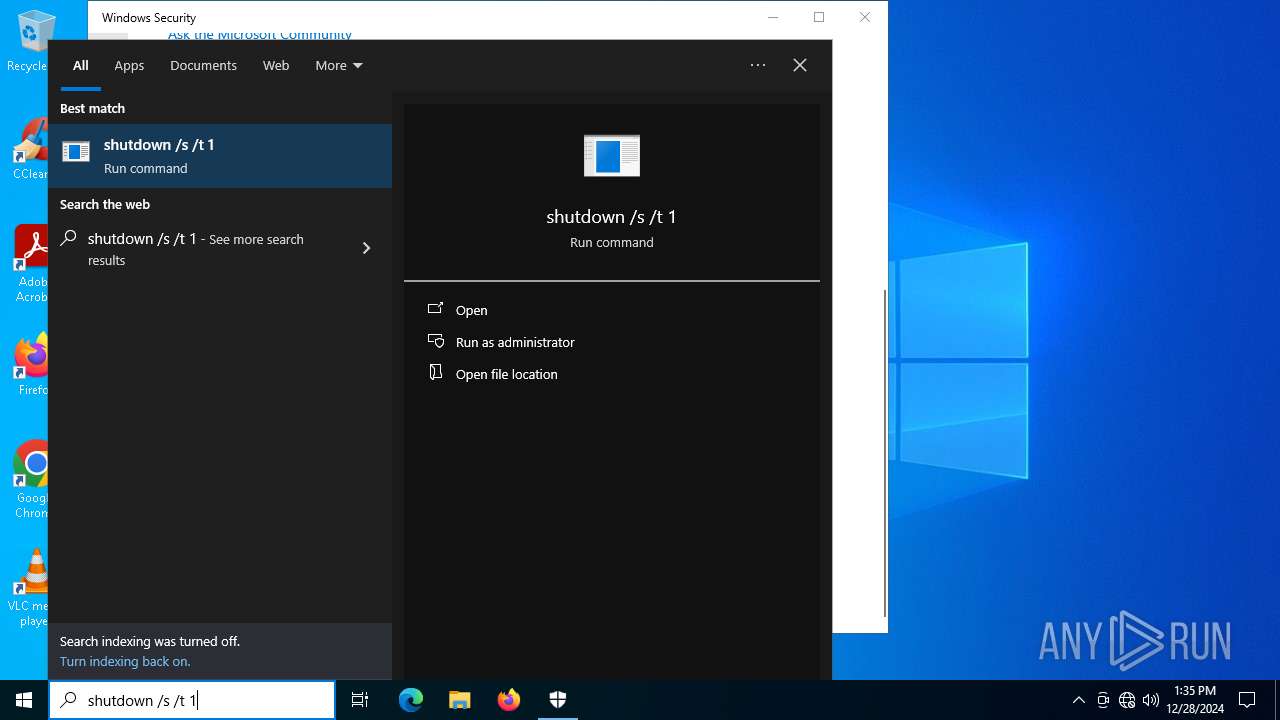
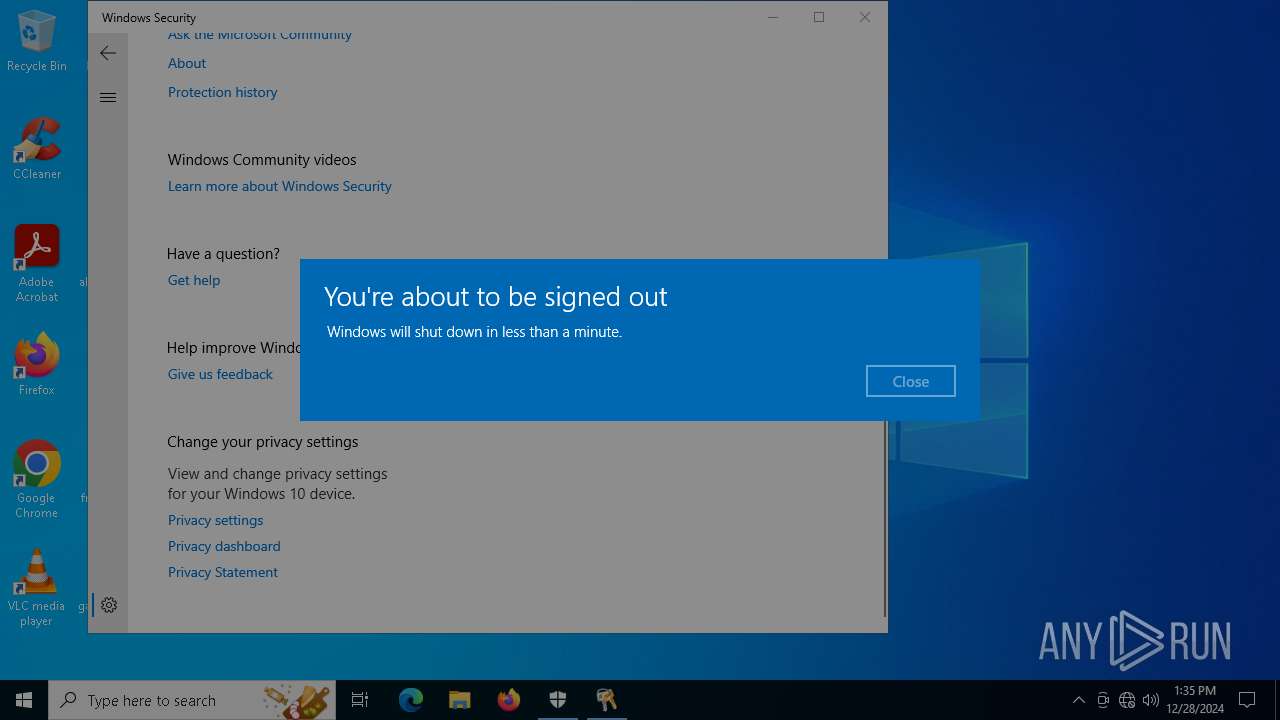
Manual execution by a user
- mspaint.exe (PID: 7136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:05:24 22:49:06+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.13 |
| CodeSize: | 25600 |
| InitializedDataSize: | 340992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6a60 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.17763.1 |
| ProductVersionNumber: | 11.0.17763.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.17763.1 (WinBuild.160101.0800) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.17763.1 |
Total processes
164
Monitored processes
27
Malicious processes
6
Suspicious processes
2
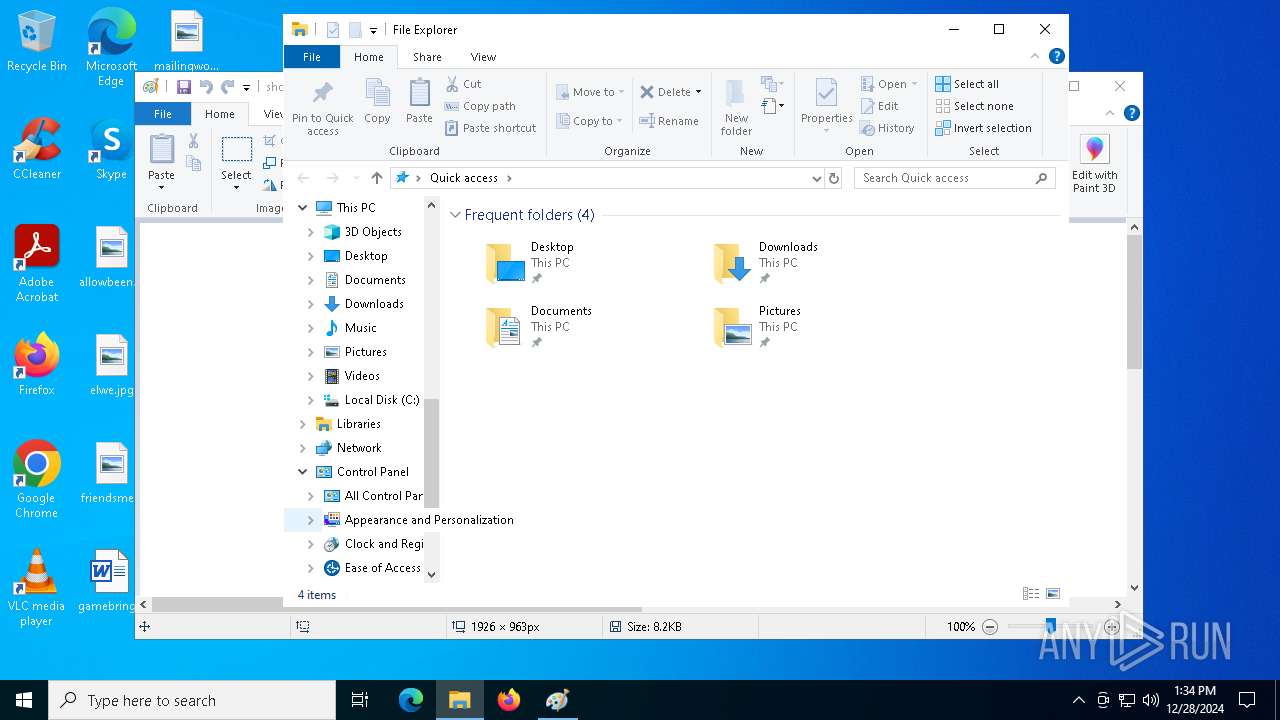
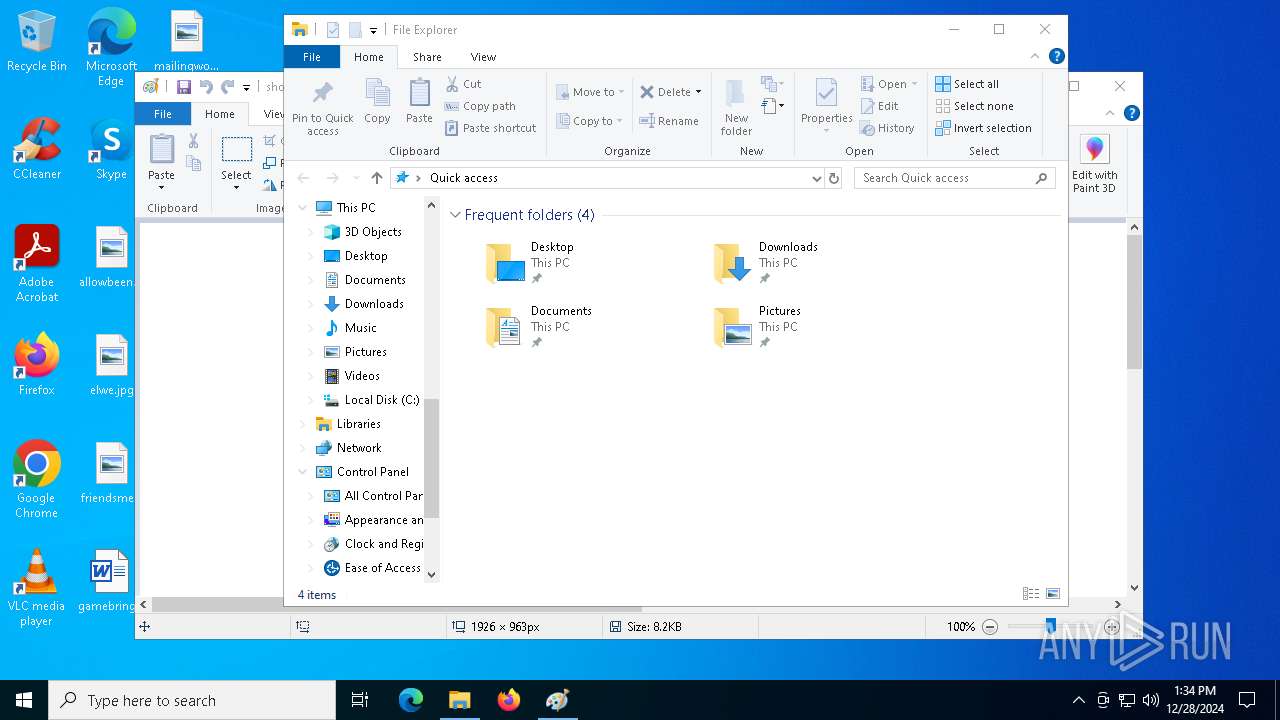
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\b0457861.exe | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\b0457861.exe | v2006608.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1224 | C:\WINDOWS\system32\DllHost.exe /Processid:{BA126F01-2166-11D1-B1D0-00805FC1270E} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 1073807364 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3928 | C:\Windows\System32\SecurityHealthHost.exe {E041C90B-68BA-42C9-991E-477B73A75C90} -Embedding | C:\Windows\System32\SecurityHealthHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Security Health Host Exit code: 0 Version: 4.18.1907.16384 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4056 | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\a8012580.exe | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\a8012580.exe | — | v2006608.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
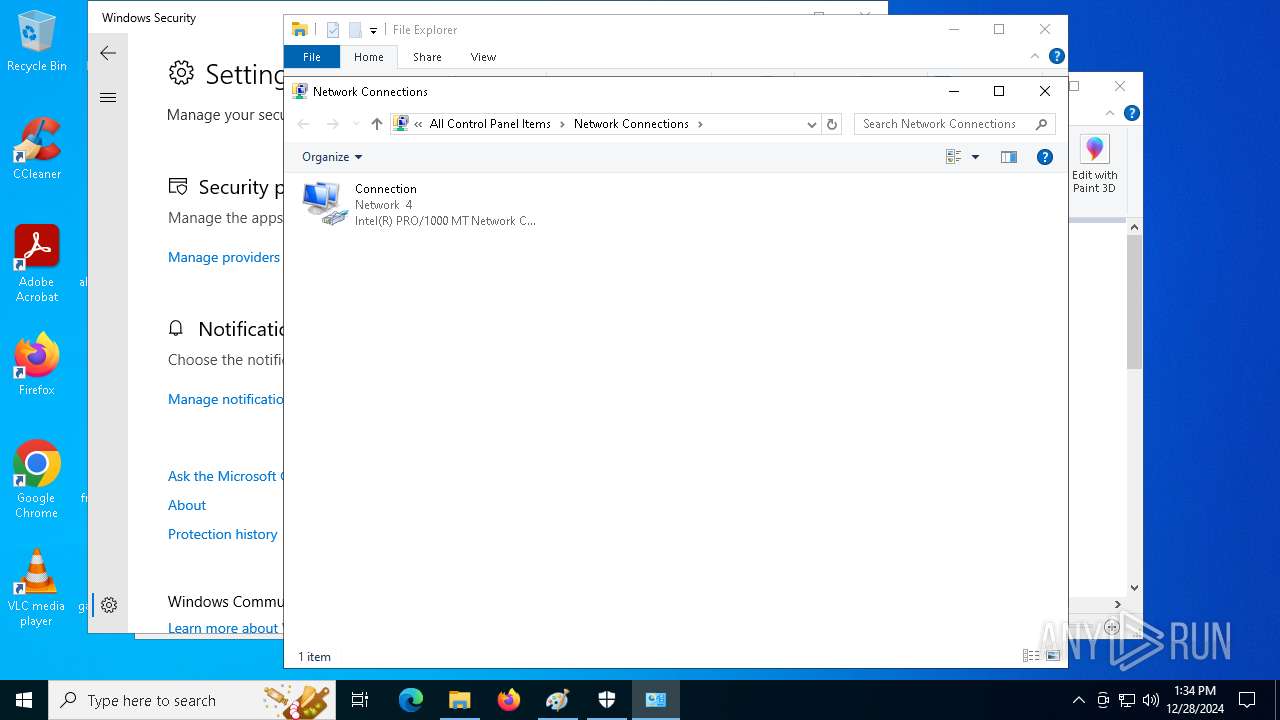
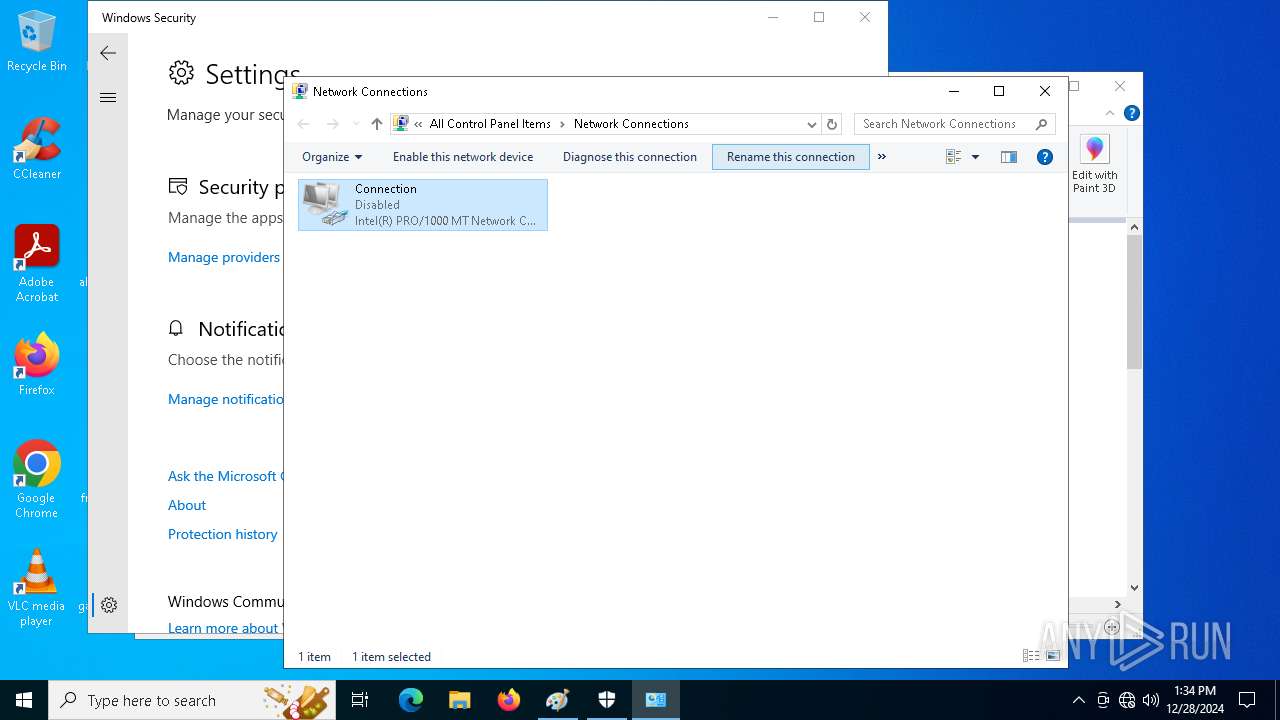
| 4400 | "C:\WINDOWS\system32\rundll32.exe" Shell32.dll,Control_RunDLL "C:\Windows\System32\ncpa.cpl", | C:\Windows\System32\rundll32.exe | — | control.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4488 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1073807364 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4640 | "C:\Users\admin\AppData\Local\Temp\2b1b7b6c06a8f60211331cffaa78a8d1.exe" | C:\Users\admin\AppData\Local\Temp\2b1b7b6c06a8f60211331cffaa78a8d1.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4976 | "C:\WINDOWS\System32\control.exe" "C:\Windows\System32\ncpa.cpl", | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5000 | "C:\WINDOWS\SystemApps\Microsoft.Windows.SecHealthUI_cw5n1h2txyewy\SecHealthUI.exe" -ServerName:SecHealthUI.AppXep4x2tbtjws1v9qqs0rmb3hxykvkpqtn.mca | C:\Windows\SystemApps\Microsoft.Windows.SecHealthUI_cw5n1h2txyewy\SecHealthUI.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Defender application Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5400 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\v2006608.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\v2006608.exe | 2b1b7b6c06a8f60211331cffaa78a8d1.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 681
Read events
20 457
Write events
193
Delete events
31
Modification events
| (PID) Process: | (6296) danke.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders |
| Operation: | write | Name: | Startup |
Value: C:\Users\admin\AppData\Local\Temp\3ec1f323b5\ | |||
| (PID) Process: | (6296) danke.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6296) danke.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6296) danke.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 57FE6F6700000000 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\ShellNew |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\ShellNew |
| Operation: | write | Name: | Classes |
Value: .accdb | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\ShellNew |
| Operation: | write | Name: | ~reserved~ |
Value: 0800000000000600 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | Mode |
Value: 1 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | LogicalViewMode |
Value: 3 | |||
Executable files
5
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5400 | v2006608.exe | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\b0457861.exe | executable | |
MD5:DFD425BB718FD5598806A365791AD900 | SHA256:B9610BB907370C978C0C8E09A410244E36F203001CFA4F8F8A0DEE4673311C37 | |||
| 4488 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 204 | b0457861.exe | C:\Users\admin\AppData\Local\Temp\3ec1f323b5\danke.exe | executable | |
MD5:DFD425BB718FD5598806A365791AD900 | SHA256:B9610BB907370C978C0C8E09A410244E36F203001CFA4F8F8A0DEE4673311C37 | |||
| 4640 | 2b1b7b6c06a8f60211331cffaa78a8d1.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\v2006608.exe | executable | |
MD5:0D040781BB1E99E506FFD5B3D2A1B6C3 | SHA256:33F2E65DE5ECA3099B1DC855C4C73403A416660D96CAE1E0866032F032CD6B4B | |||
| 4488 | explorer.exe | C:\Users\admin\AppData\Local\IconCache.db | binary | |
MD5:7EE0780D09AFA485F60318DC44FA085A | SHA256:FF6EB7C94C21D73D33EE04B64525DAE2B8776C8966FAD6799A2CE359FE88C9D9 | |||
| 4640 | 2b1b7b6c06a8f60211331cffaa78a8d1.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\c6795757.exe | executable | |
MD5:9198BB9E782738F0C6A45D307E949721 | SHA256:D6D0531A839A815E3CEC3310F3FAD3AD9FA56C5F763CC7DF3B5A9D9A21D8372F | |||
| 5400 | v2006608.exe | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\a8012580.exe | executable | |
MD5:DA79D7584C838B8FB518181B99D7D104 | SHA256:A195E57F700AA491B3EB1CF2F84A98348251F69661FCE9BF506DDD2620B97C9F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
54
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6184 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7132 | SIHClient.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7132 | SIHClient.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2356 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.140:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6296 | danke.exe | 77.91.68.3:80 | — | Foton Telecom CJSC | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
r.bing.com |
| whitelisted |
fp.msedge.net |
| whitelisted |